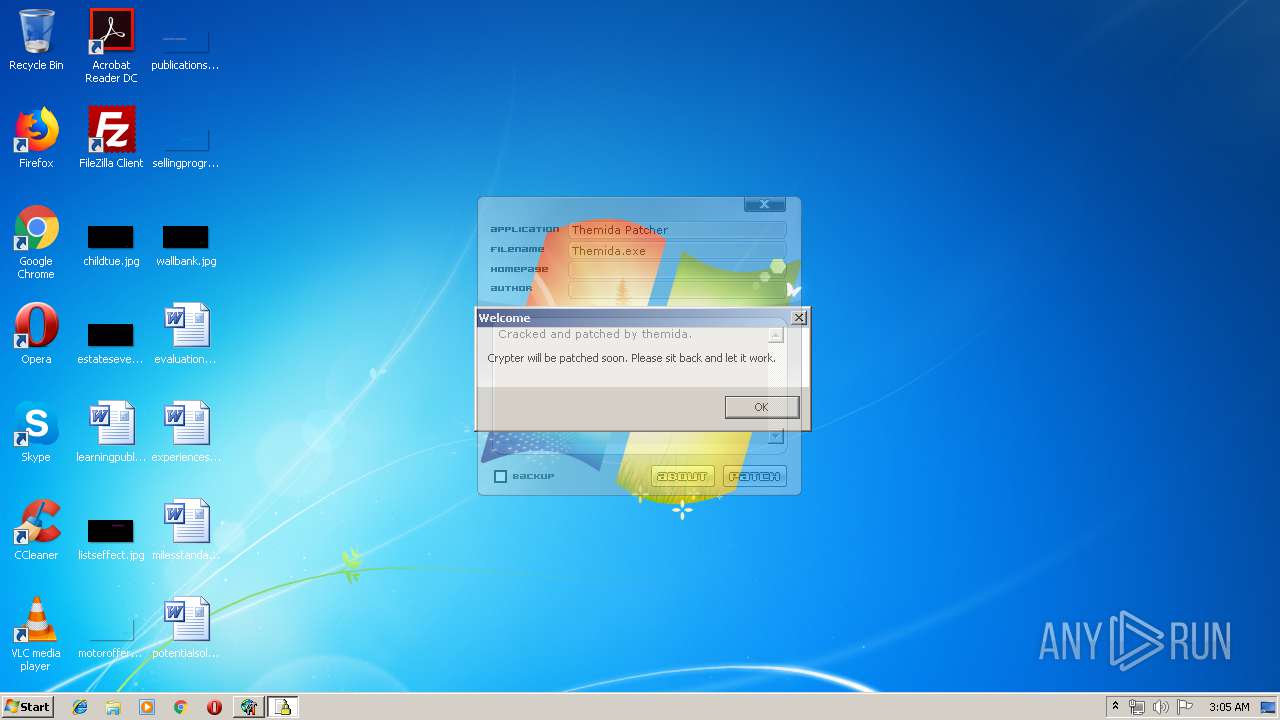
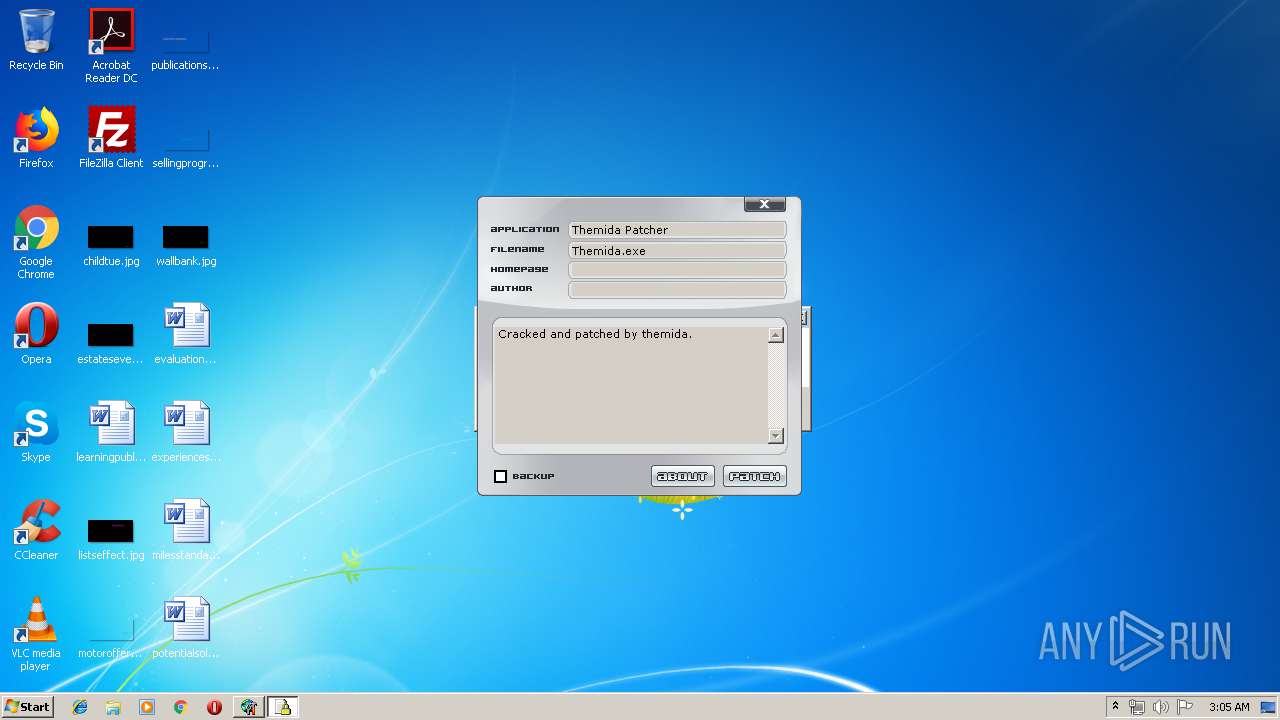
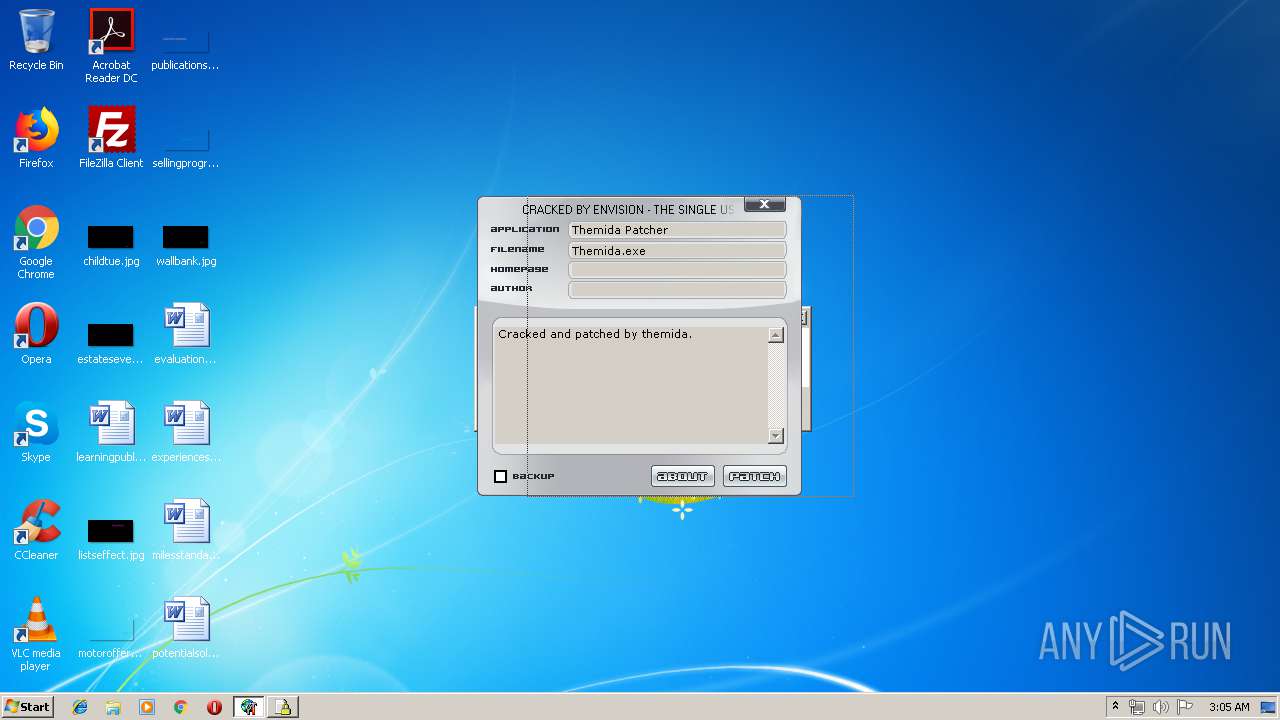
| File name: | Themida Patcher_protected.exe |
| Full analysis: | https://app.any.run/tasks/8cd98a24-2c66-4511-810d-5386b65ee904 |
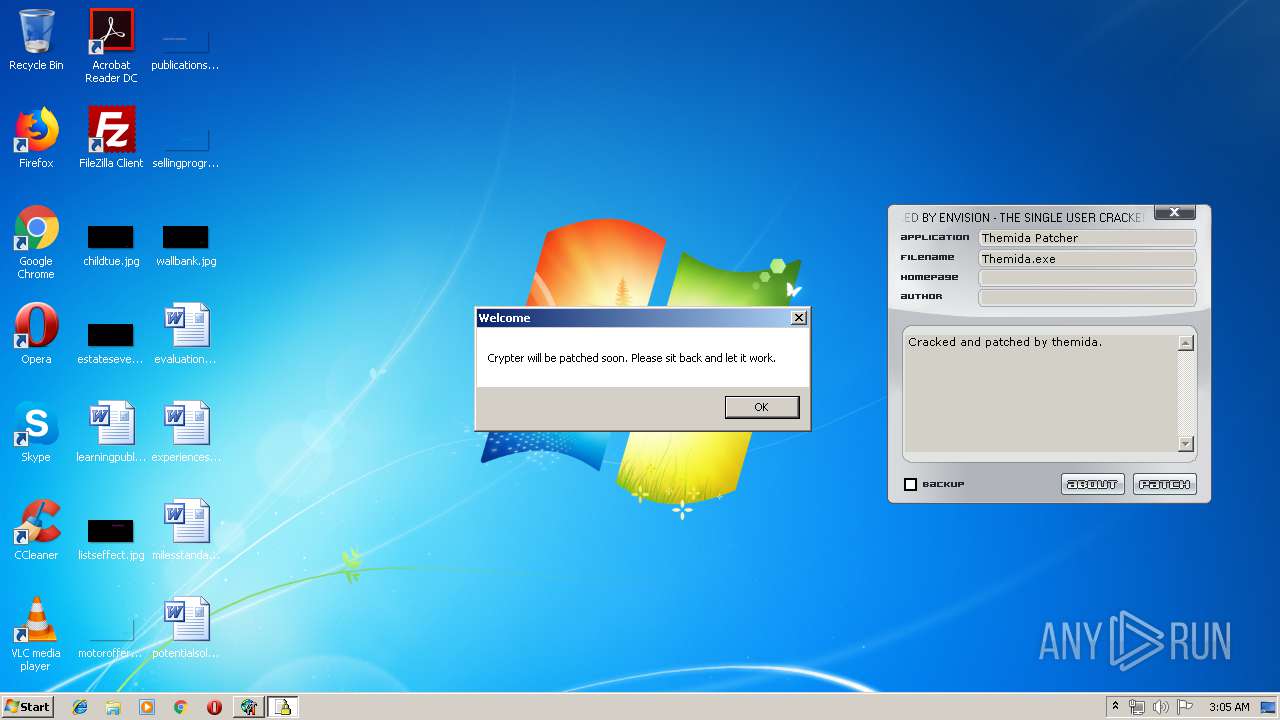
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | April 21, 2019, 02:05:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 10E3D17AAAF58D702A44C761500F5B85 |
| SHA1: | 853348D929AB0945DB969620361017747ABBE262 |
| SHA256: | 39CC23E33E630428F4E6070C004DC0ADB1DC89D4DE86717FFDD38ECCC50A55BF |
| SSDEEP: | 49152:0qb8HuQ6We61jG4erAQ8rvbbTyggQ1FMwkm:0C8HuVWe61q3kQ8rjbJl1 |
MALICIOUS
Changes the autorun value in the registry
- PATCHER.EXE (PID: 2520)
- svchost.exe (PID: 2324)
Changes the login/logoff helper path in the registry
- PATCHER.EXE (PID: 2520)
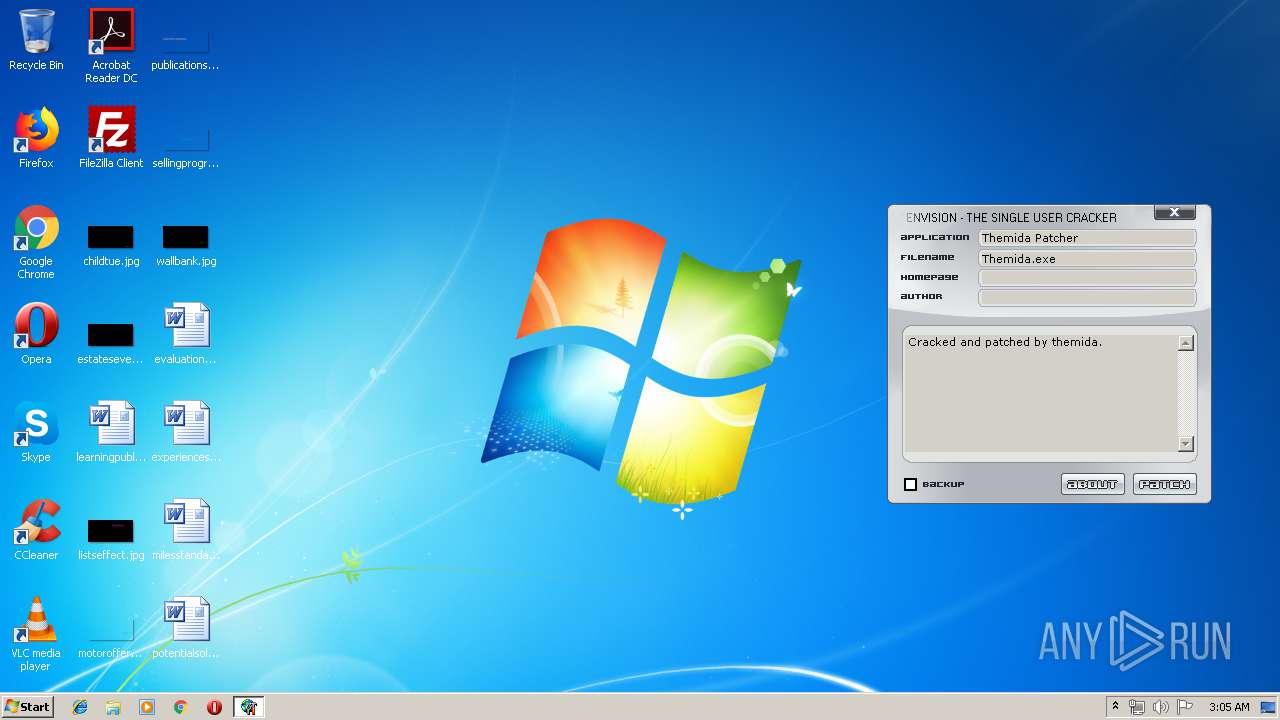
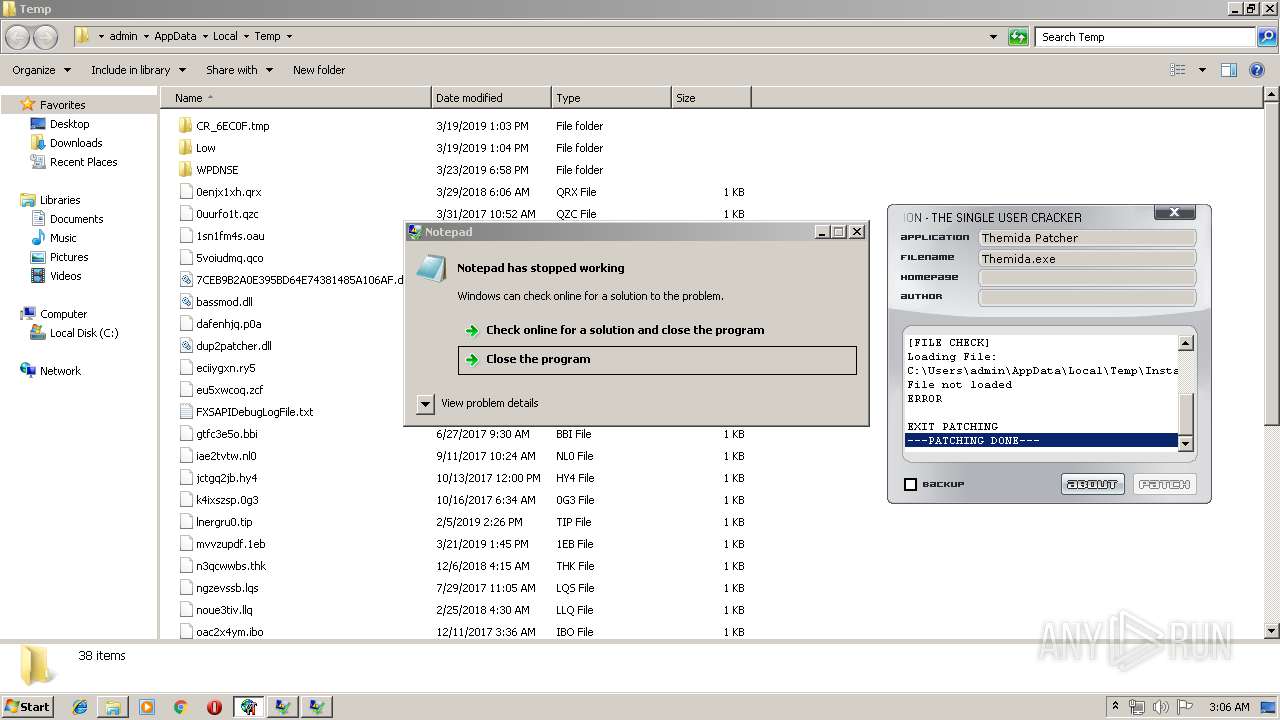
Application was dropped or rewritten from another process
- PATCHER.EXE (PID: 2520)
- THEMIDA.PATCHER.EXE (PID: 252)
- svchost.exe (PID: 2324)
Loads dropped or rewritten executable
- THEMIDA.PATCHER.EXE (PID: 252)
Disables registry editing tools (regedit)
- svchost.exe (PID: 2324)
DARKCOMET was detected
- svchost.exe (PID: 2324)
SUSPICIOUS
Creates executable files which already exist in Windows
- PATCHER.EXE (PID: 2520)
Executable content was dropped or overwritten
- Themida Patcher_protected.exe (PID: 3708)
- THEMIDA.PATCHER.EXE (PID: 252)
- PATCHER.EXE (PID: 2520)
Creates files in the user directory
- PATCHER.EXE (PID: 2520)
Starts CMD.EXE for commands execution
- PATCHER.EXE (PID: 2520)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2824)
- cmd.exe (PID: 1972)
Starts itself from another location
- PATCHER.EXE (PID: 2520)
INFO
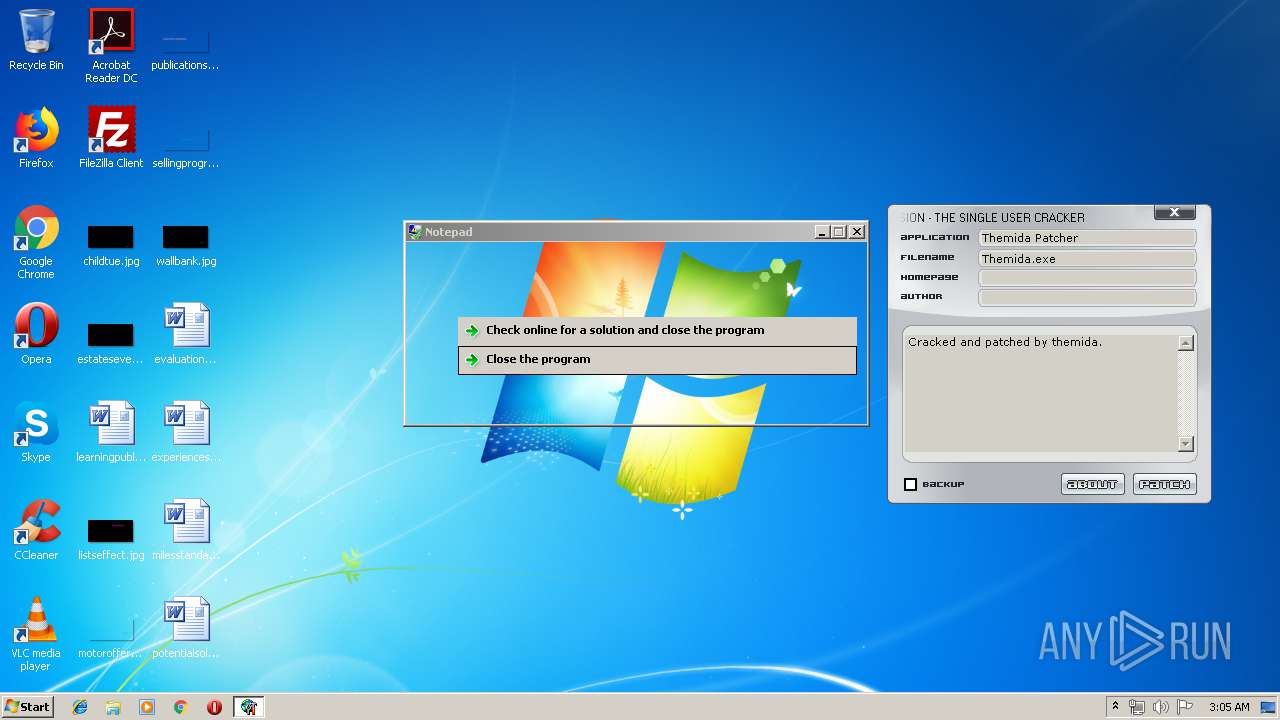
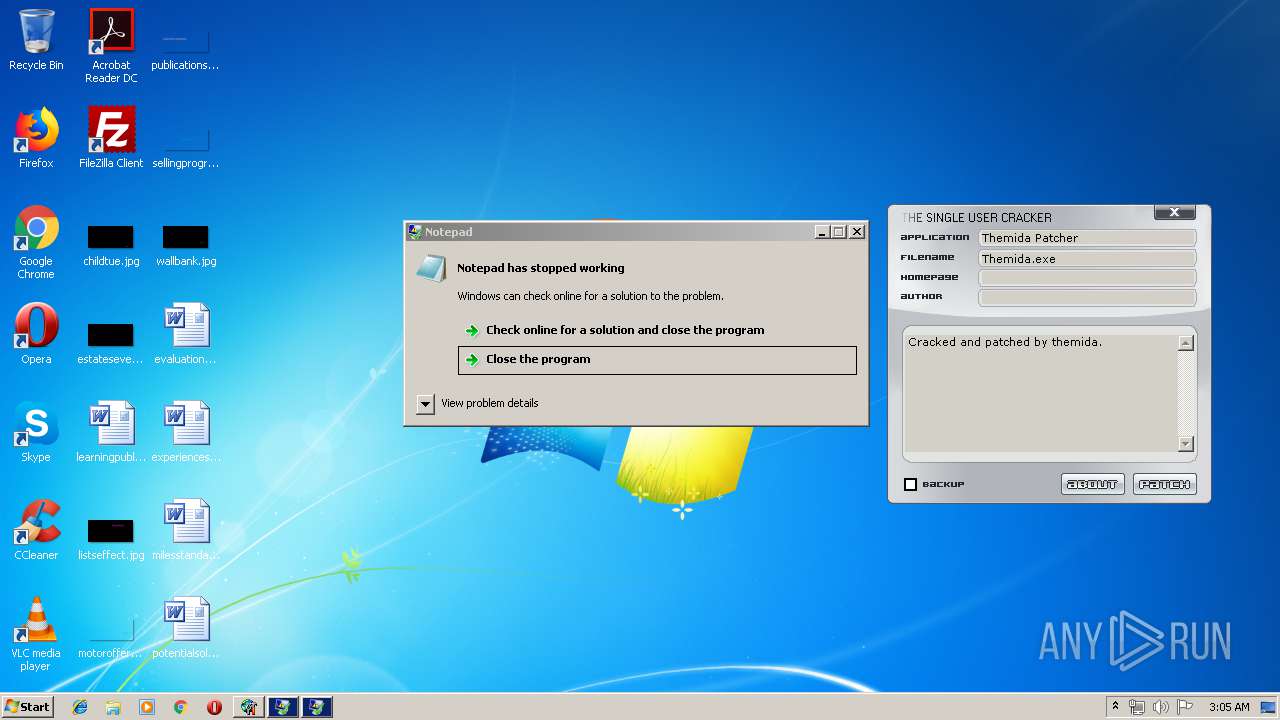
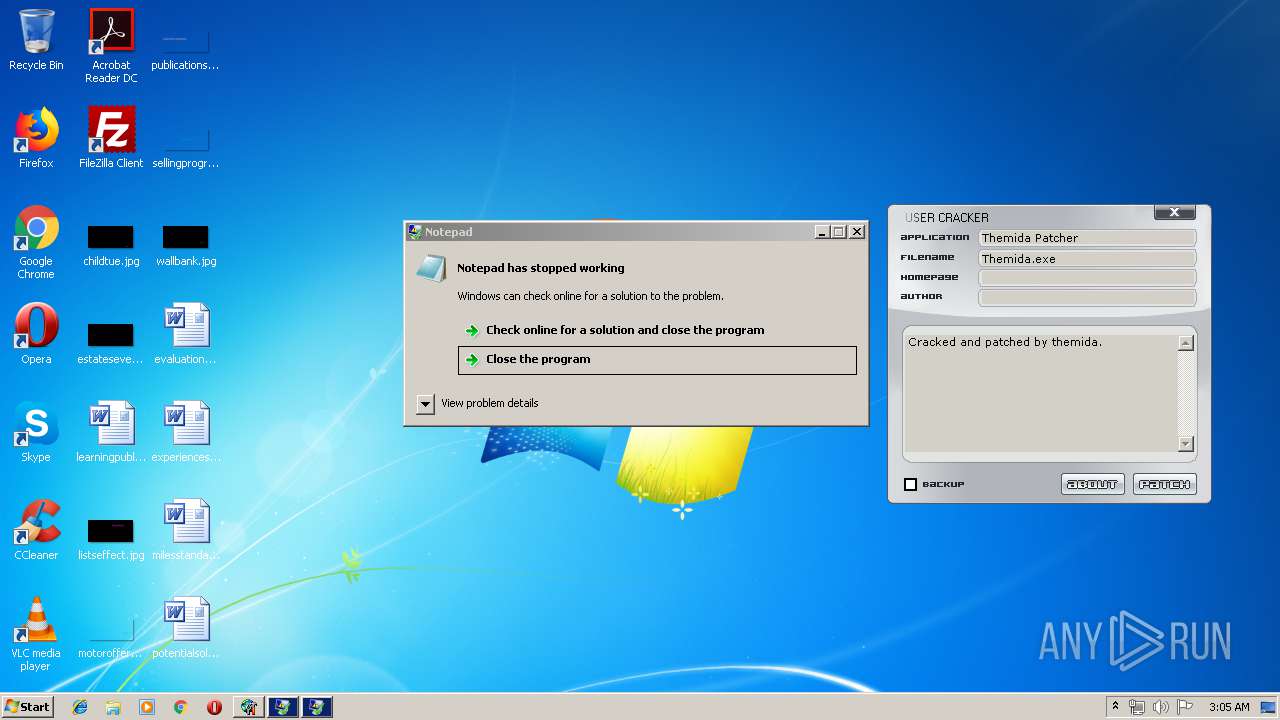
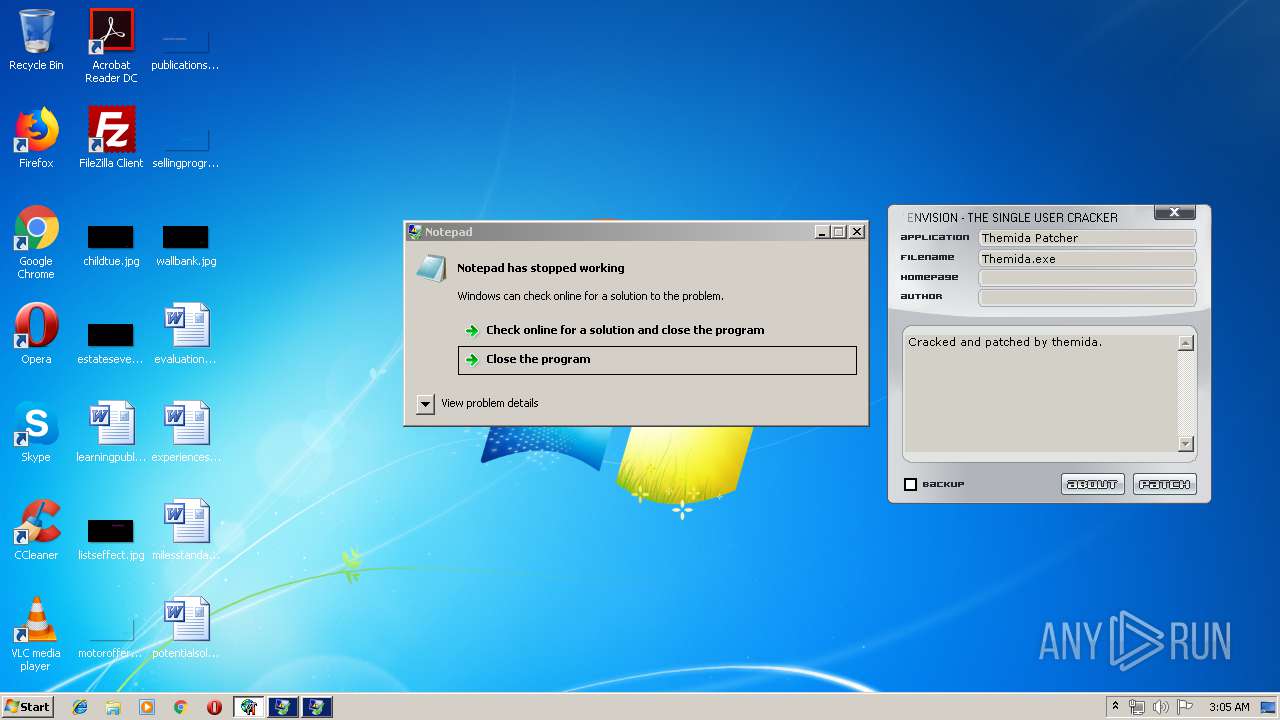
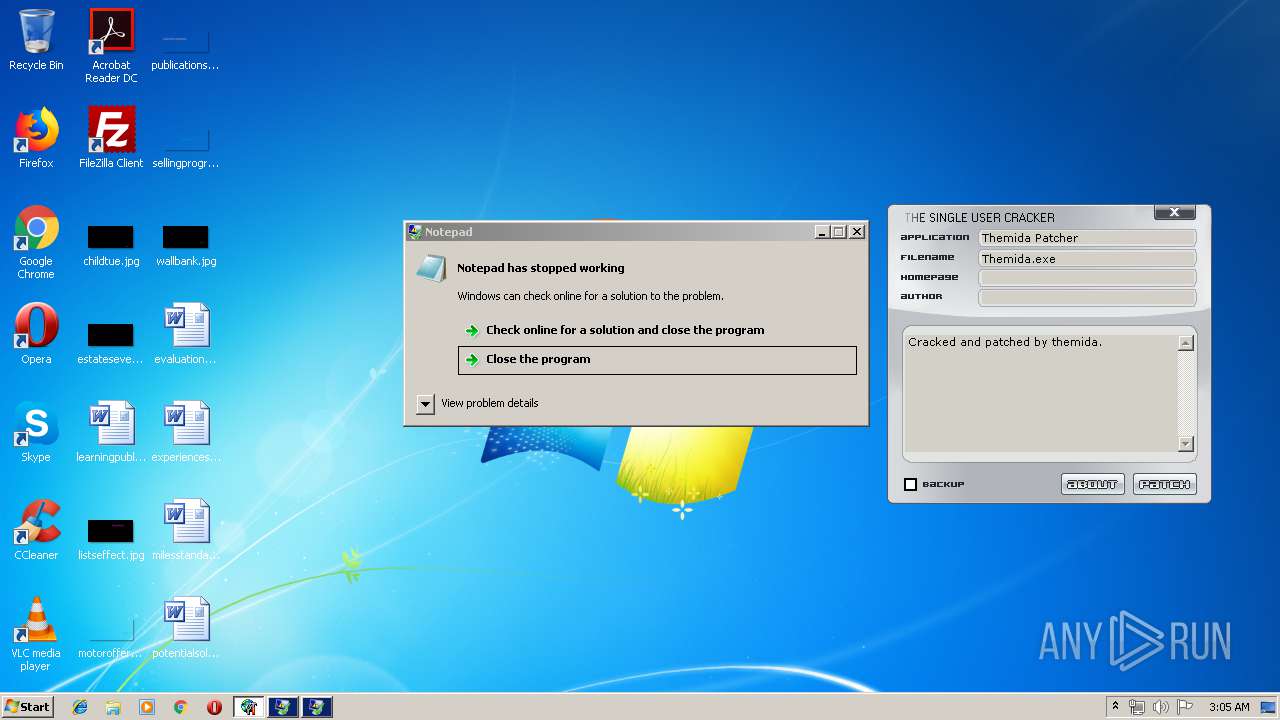
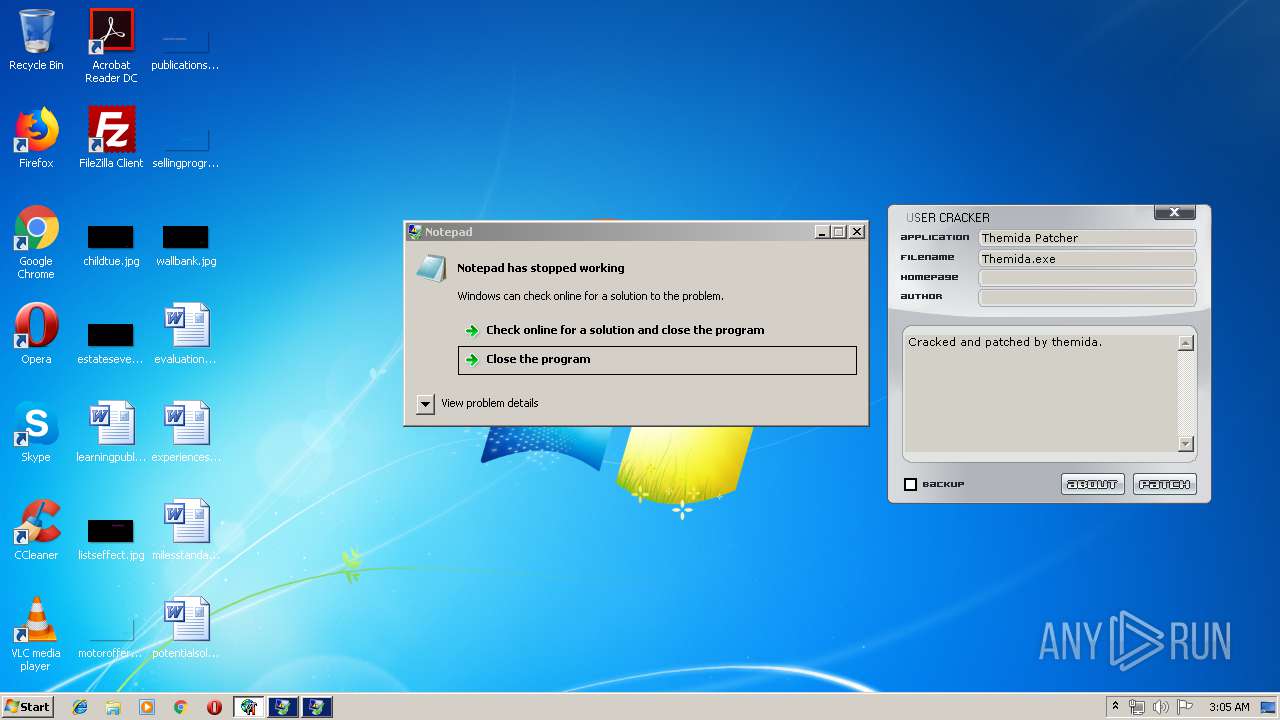
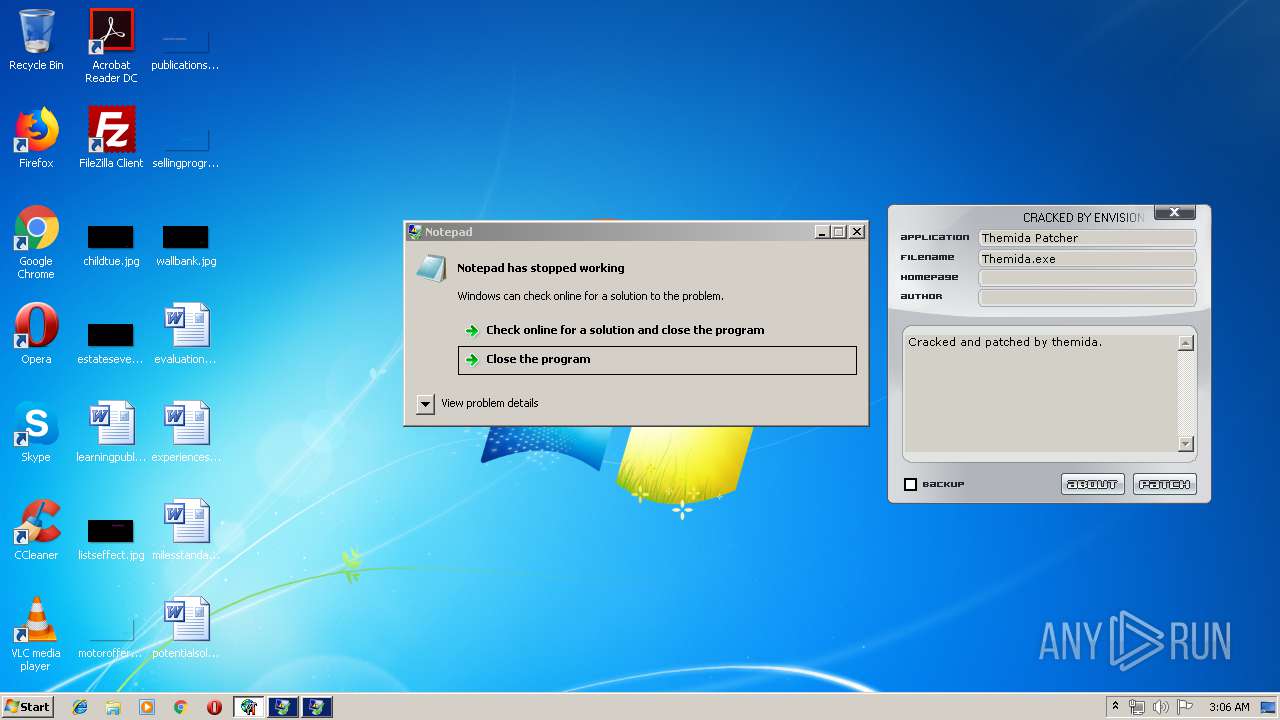
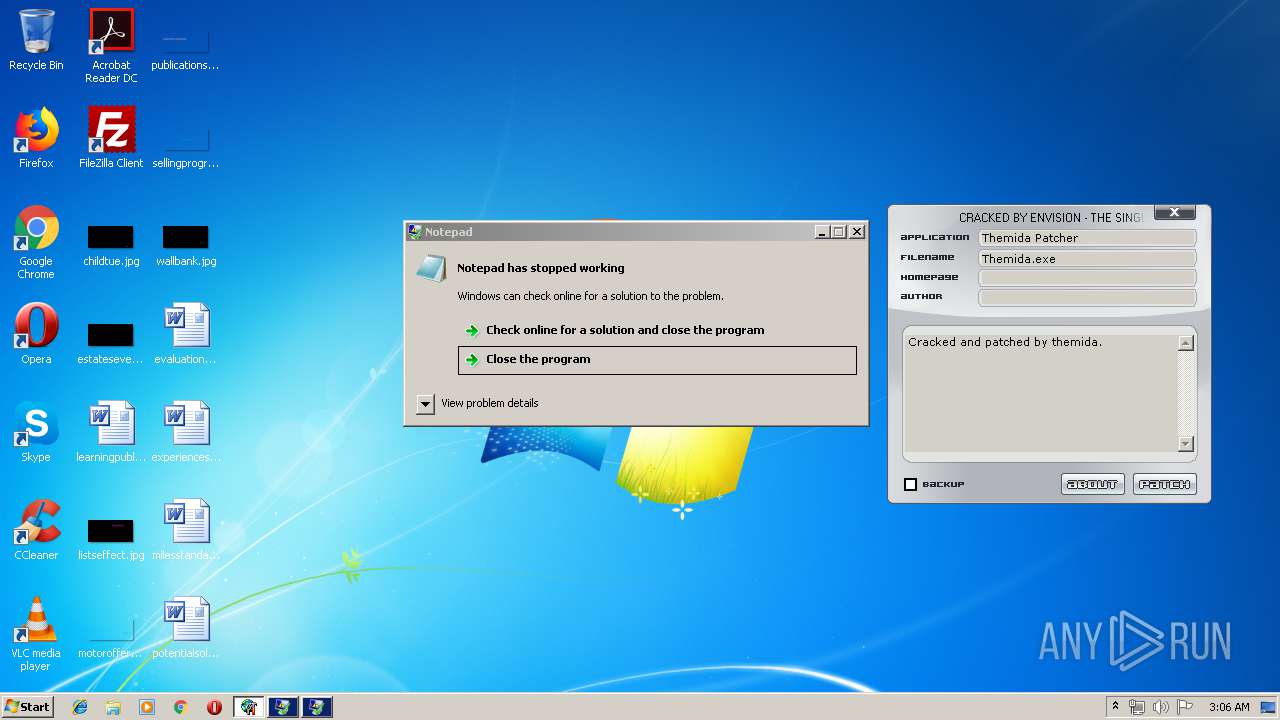
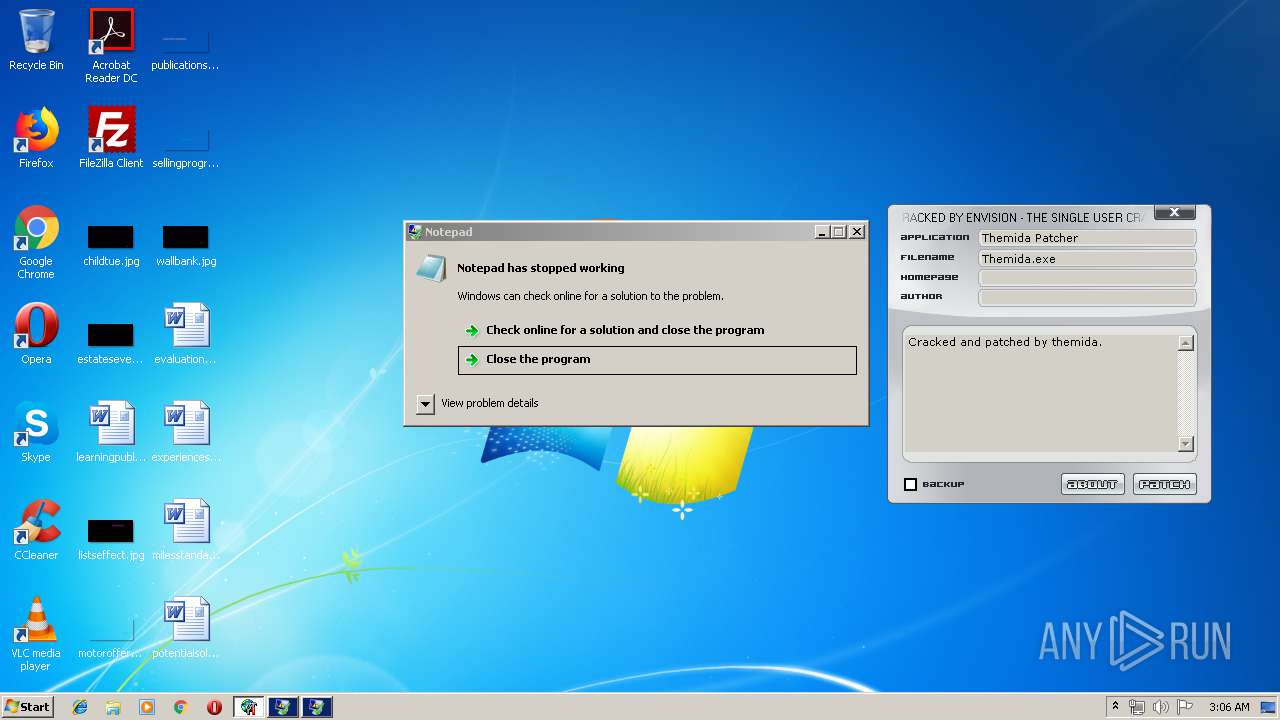
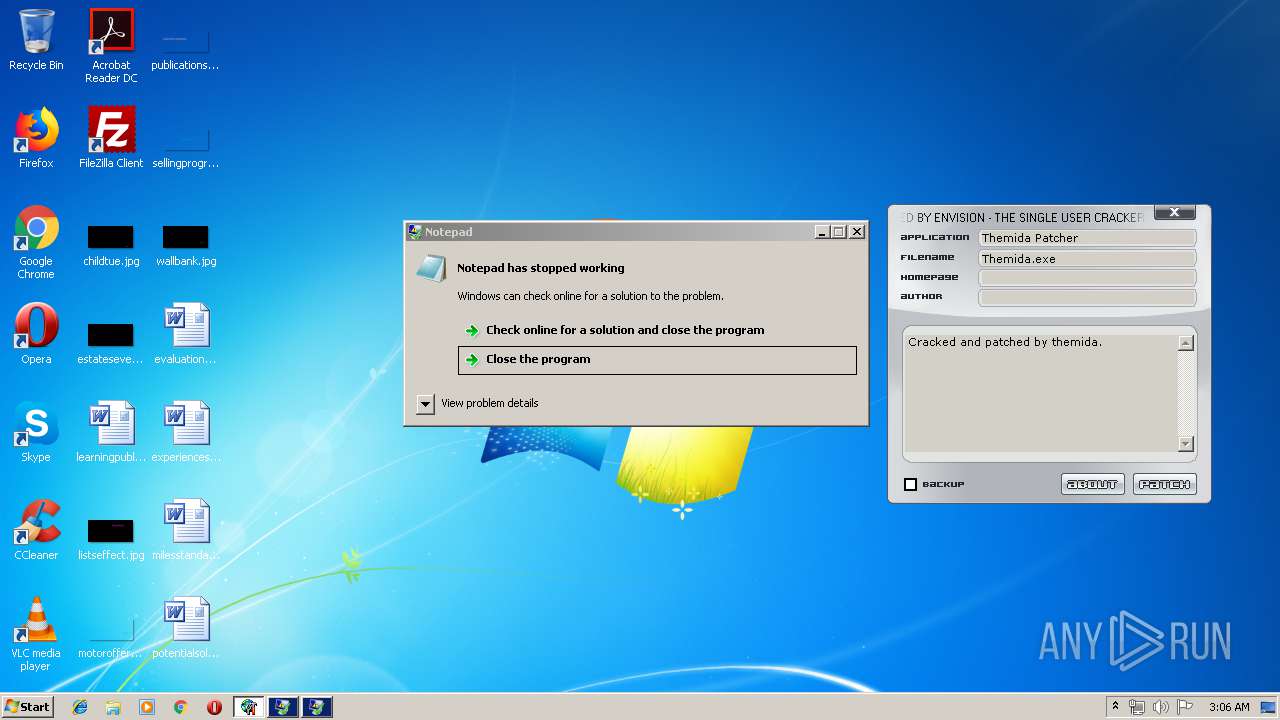
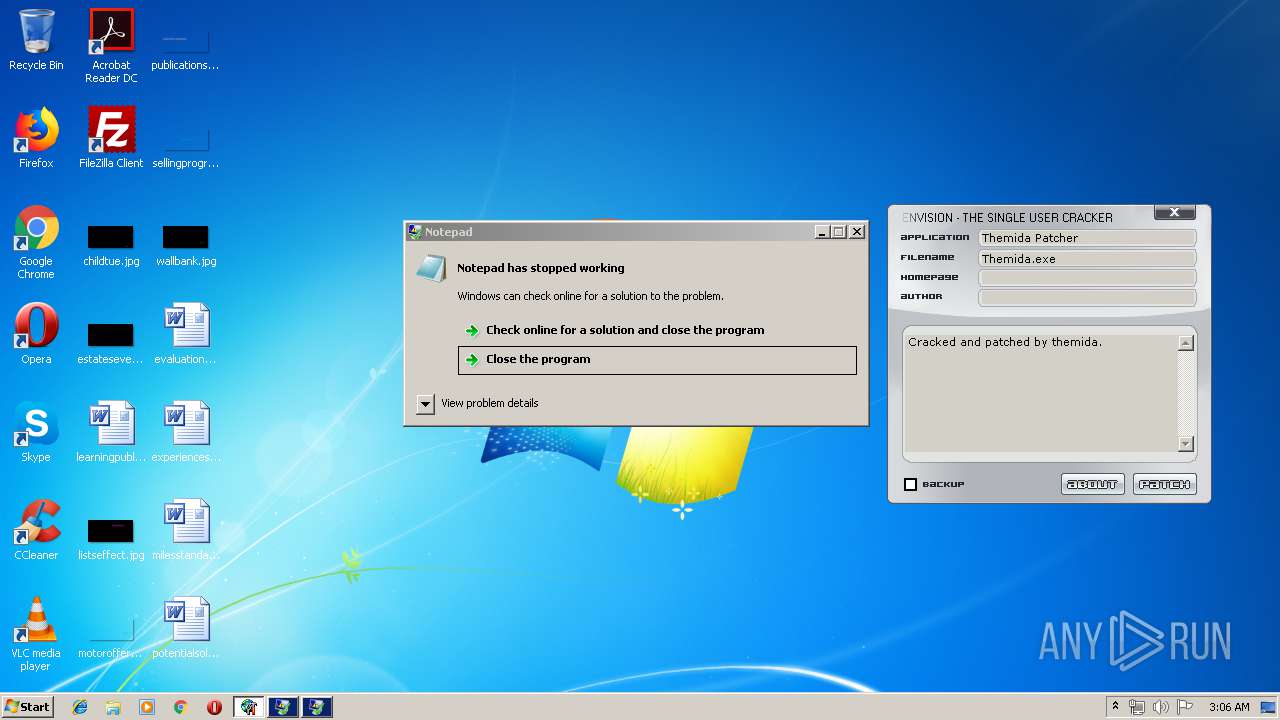
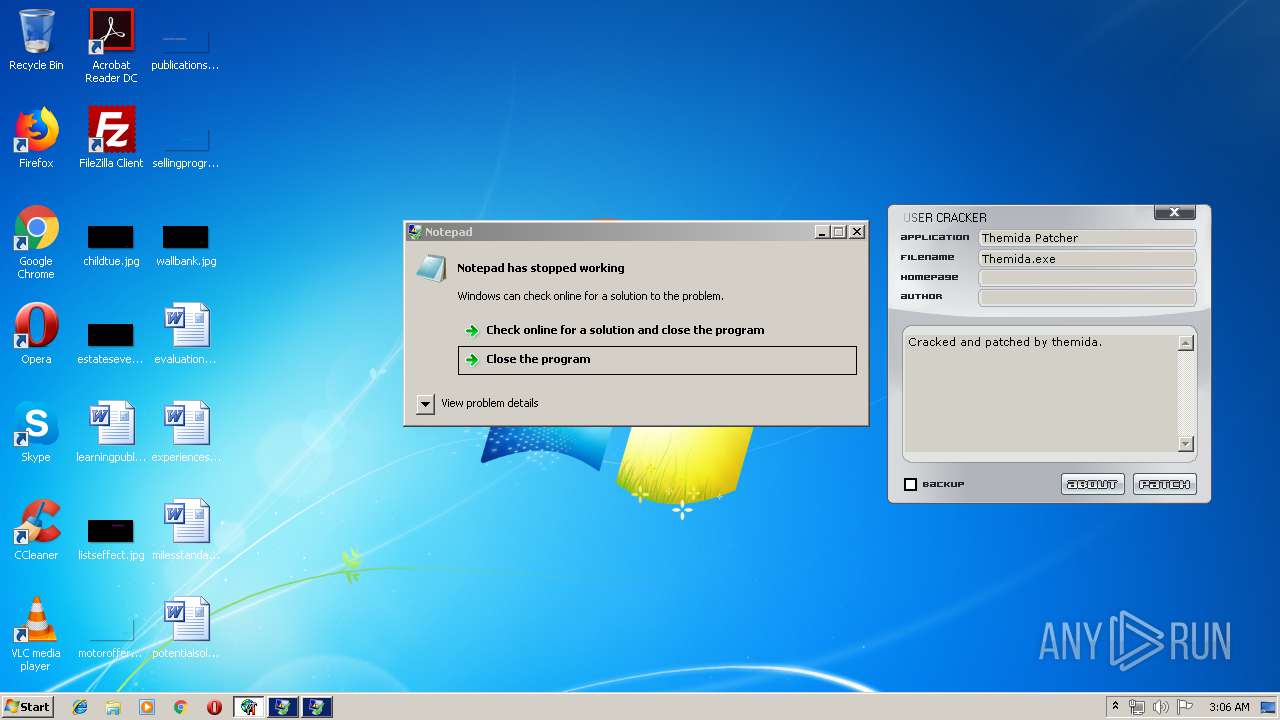
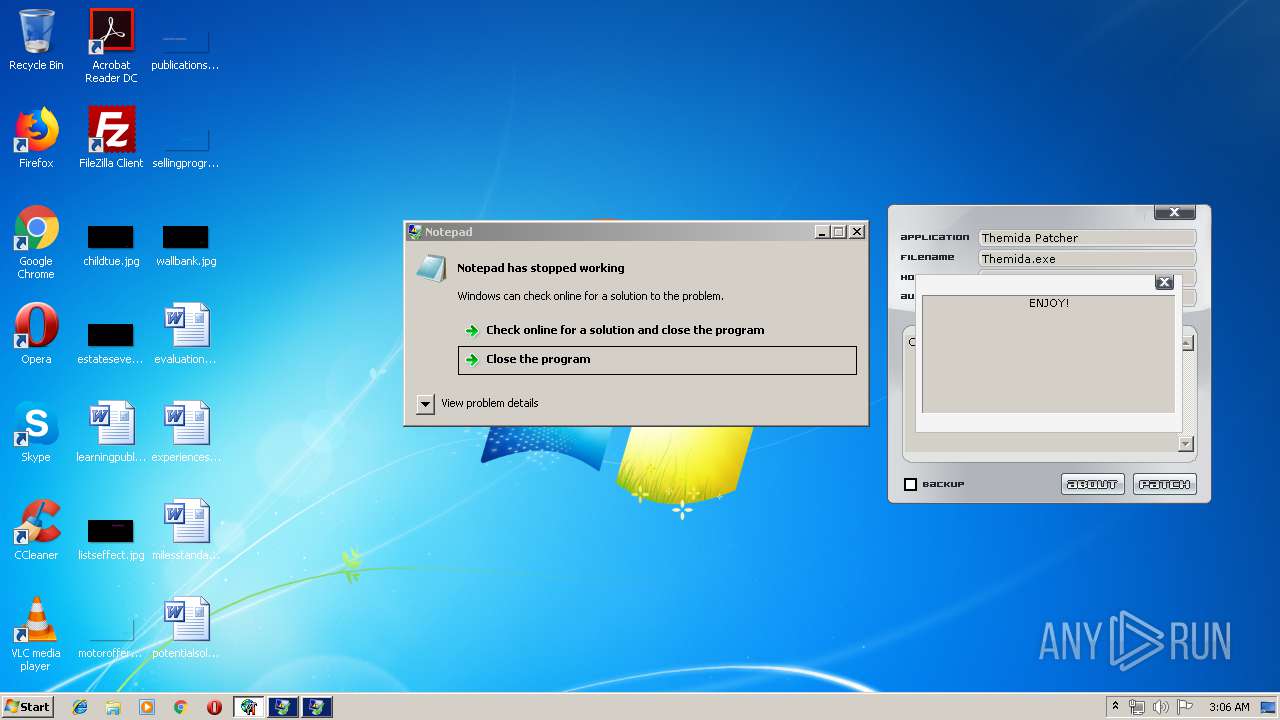
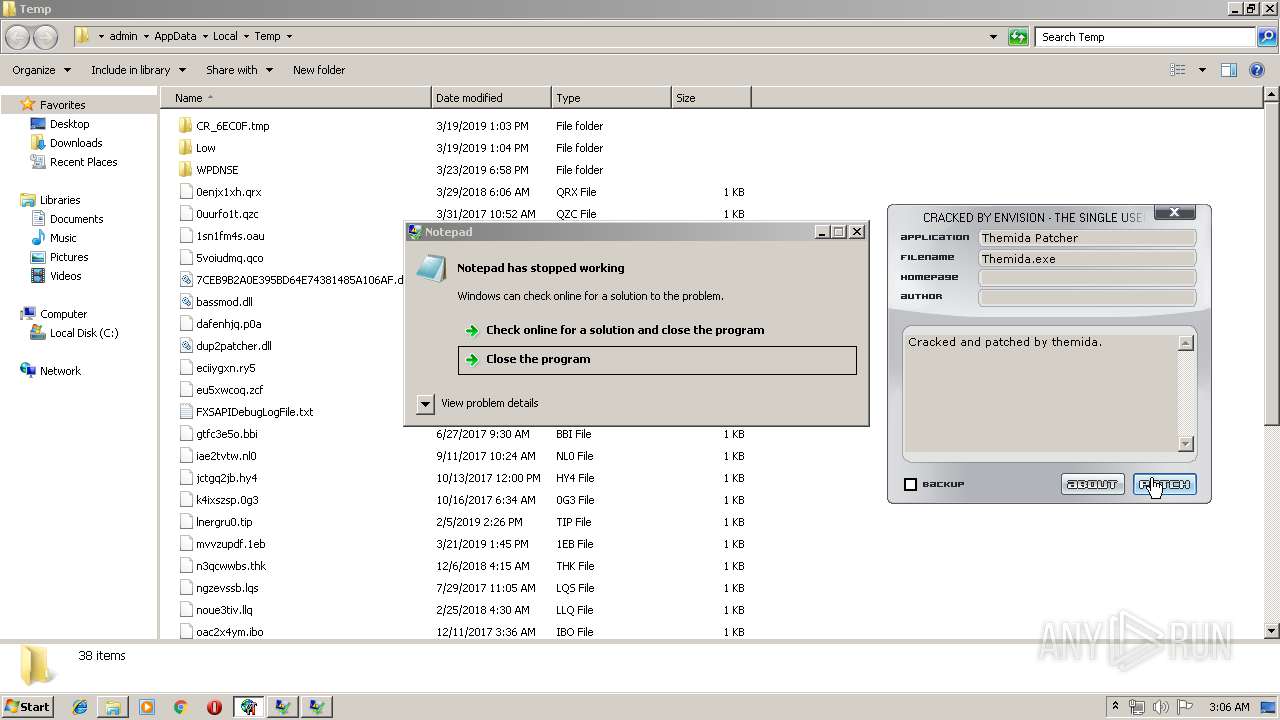
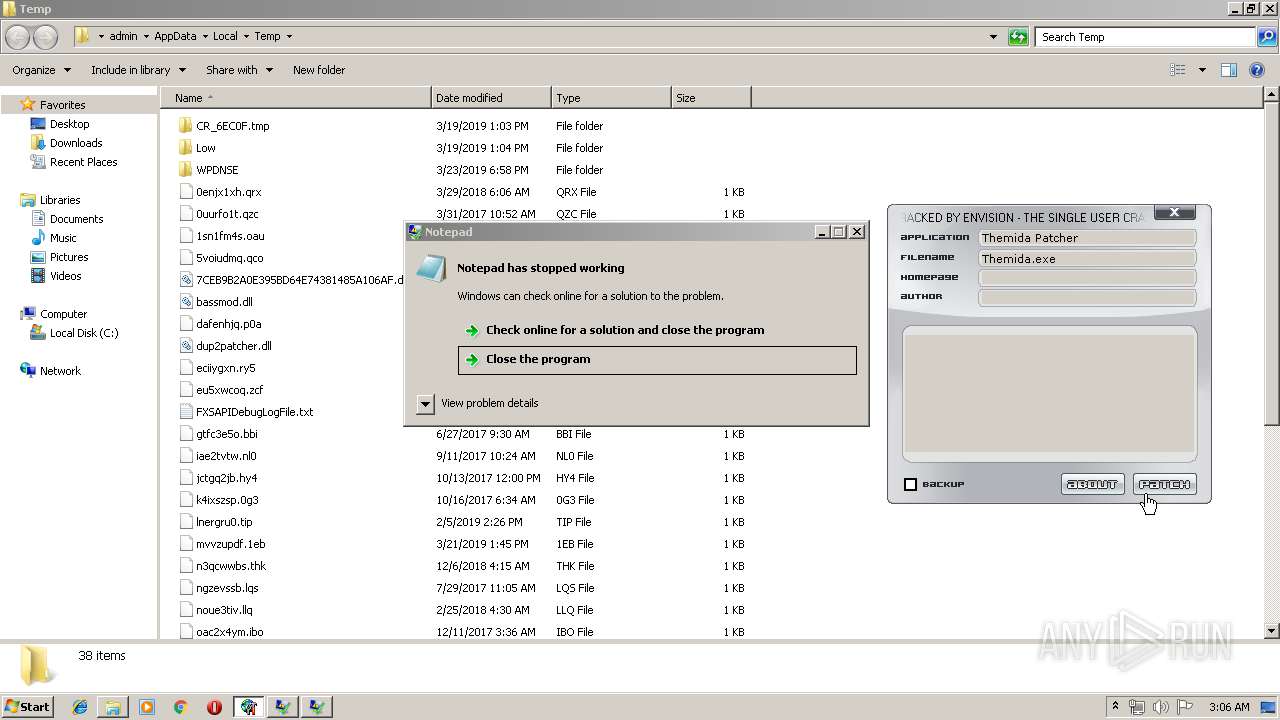
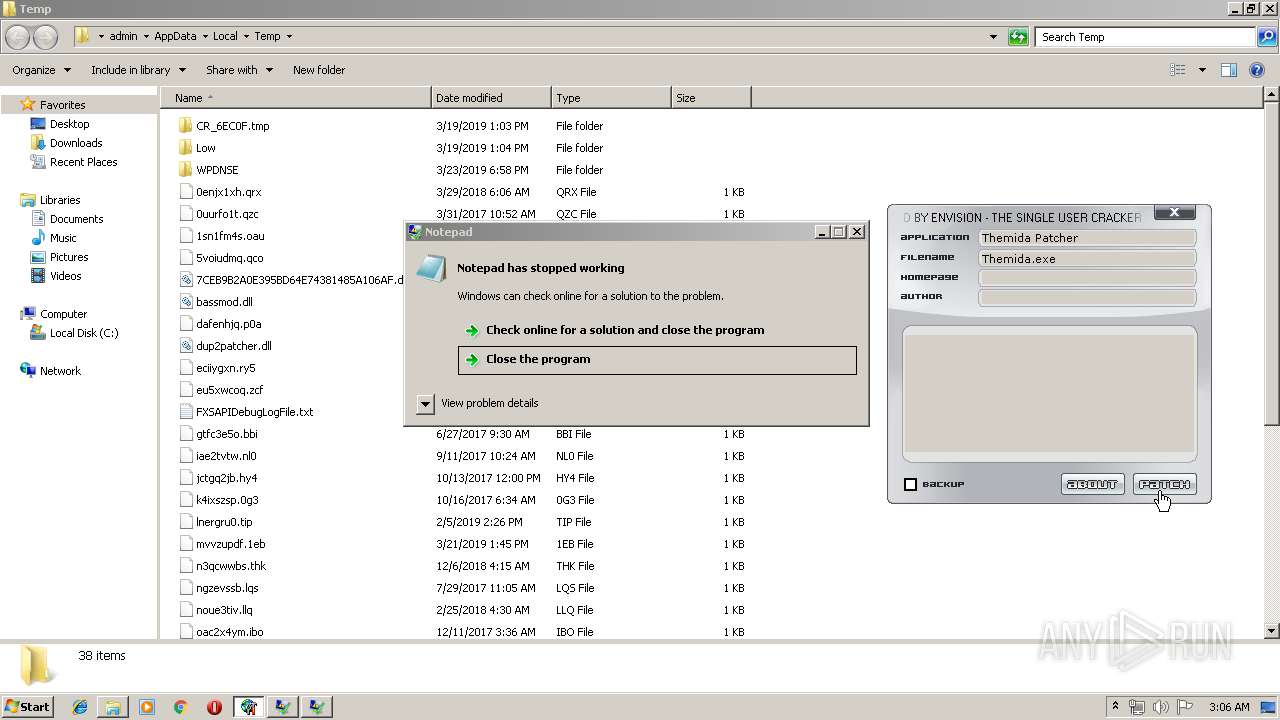
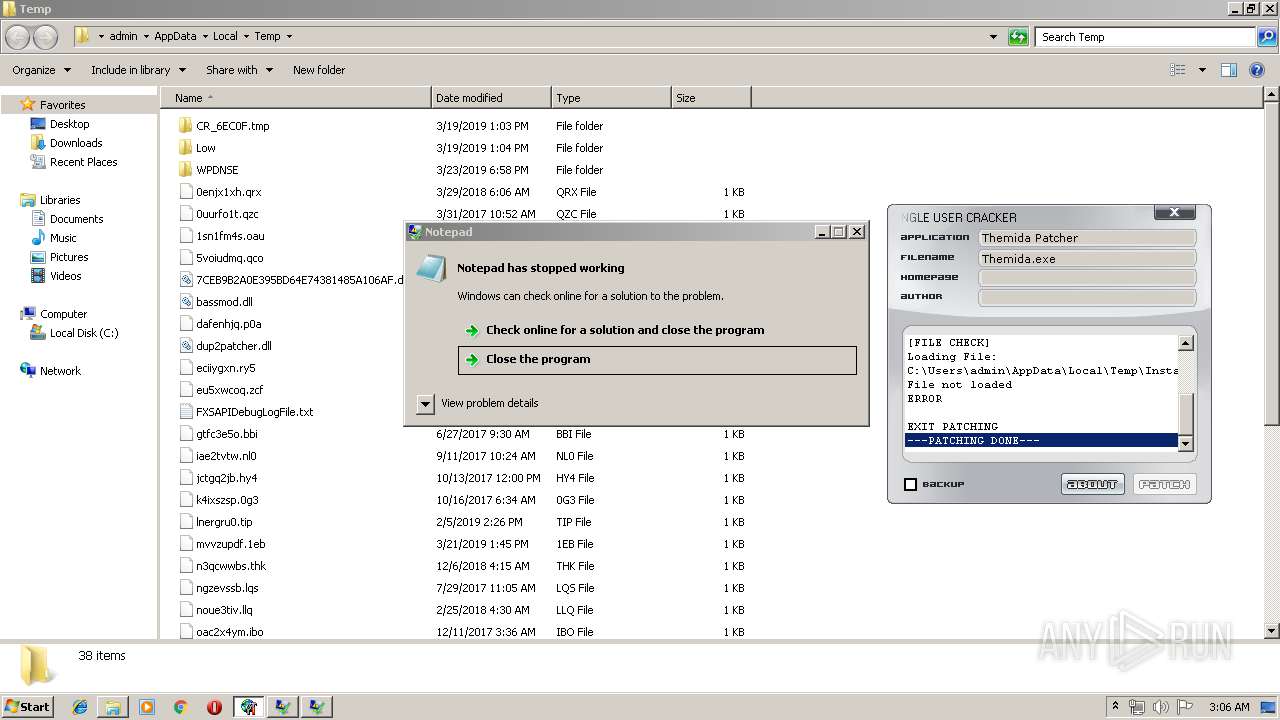
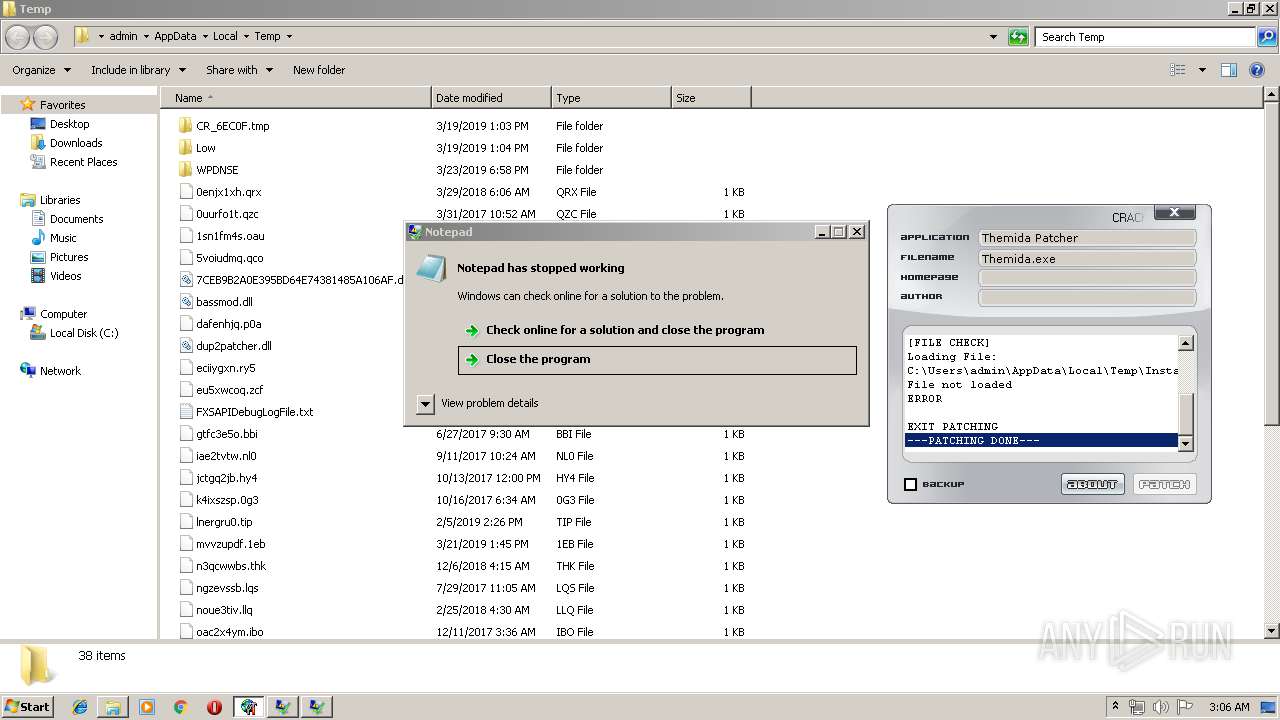
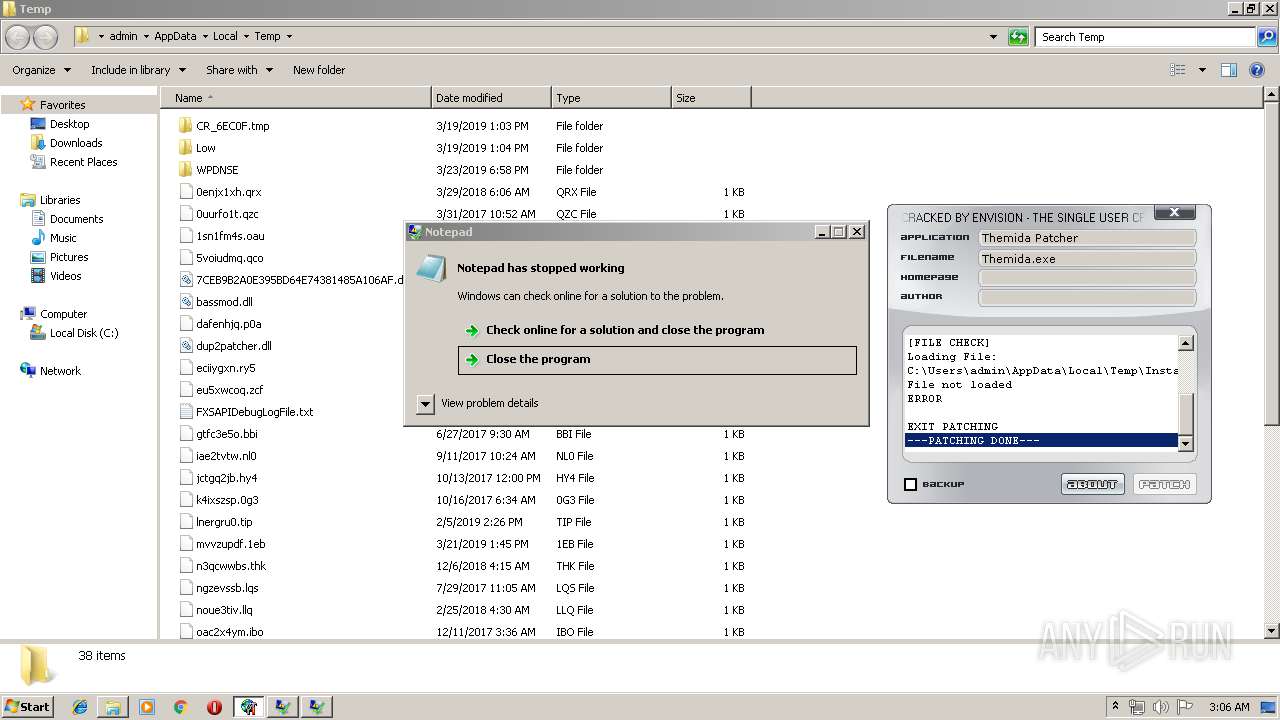
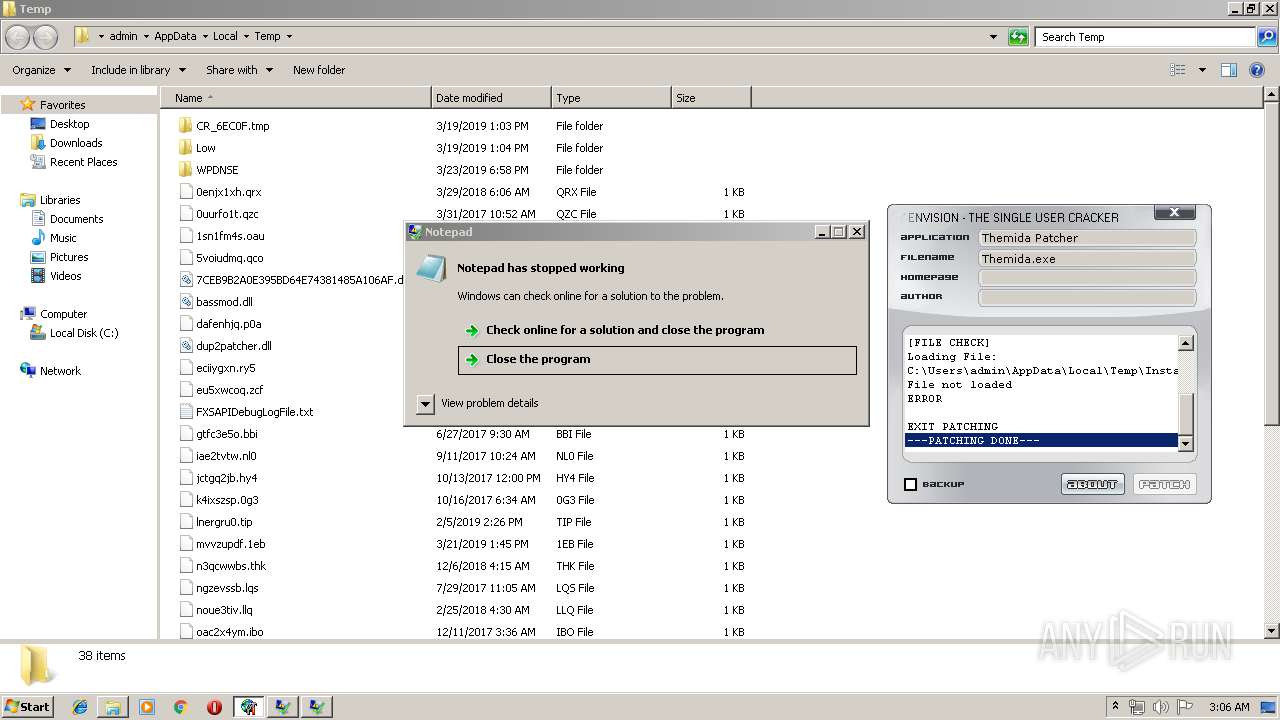
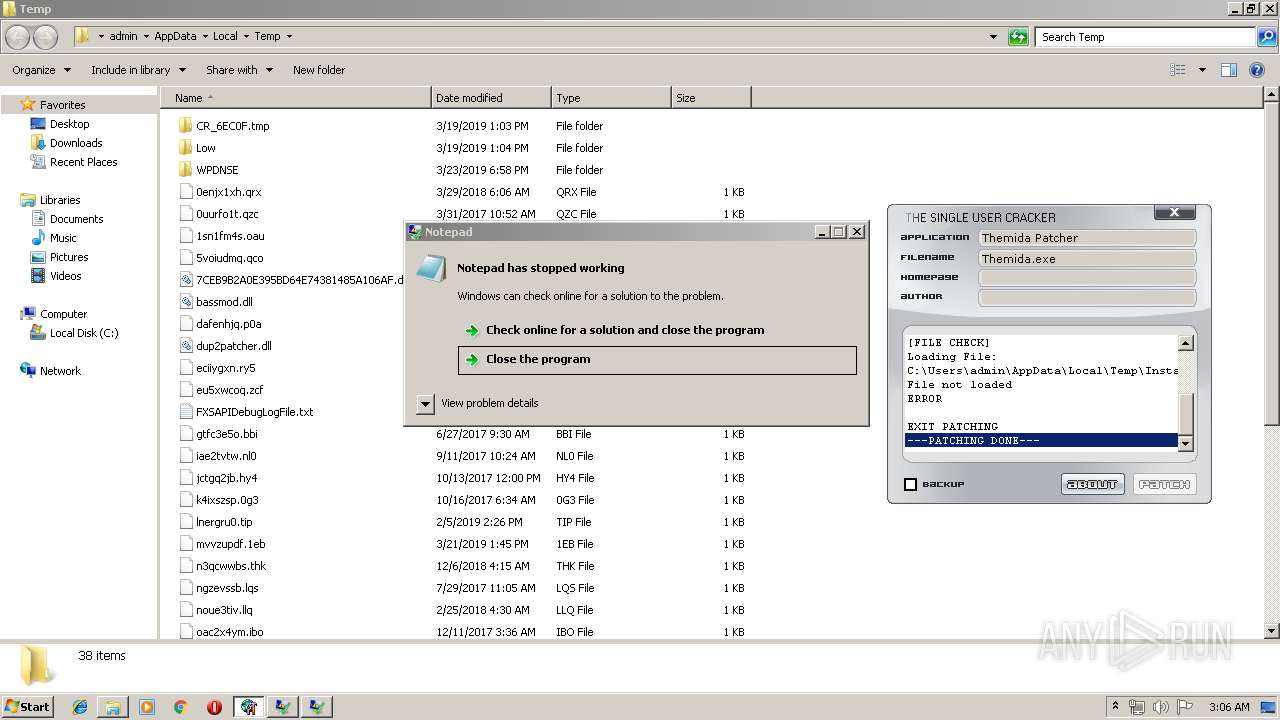
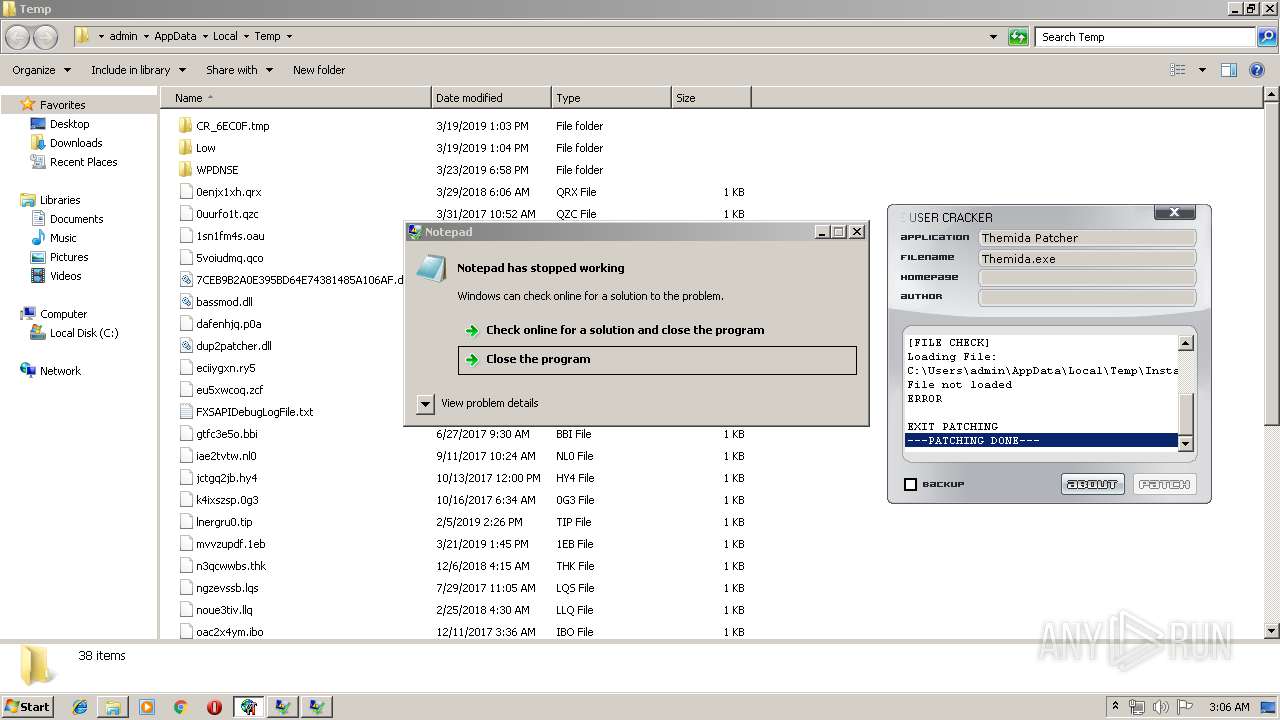
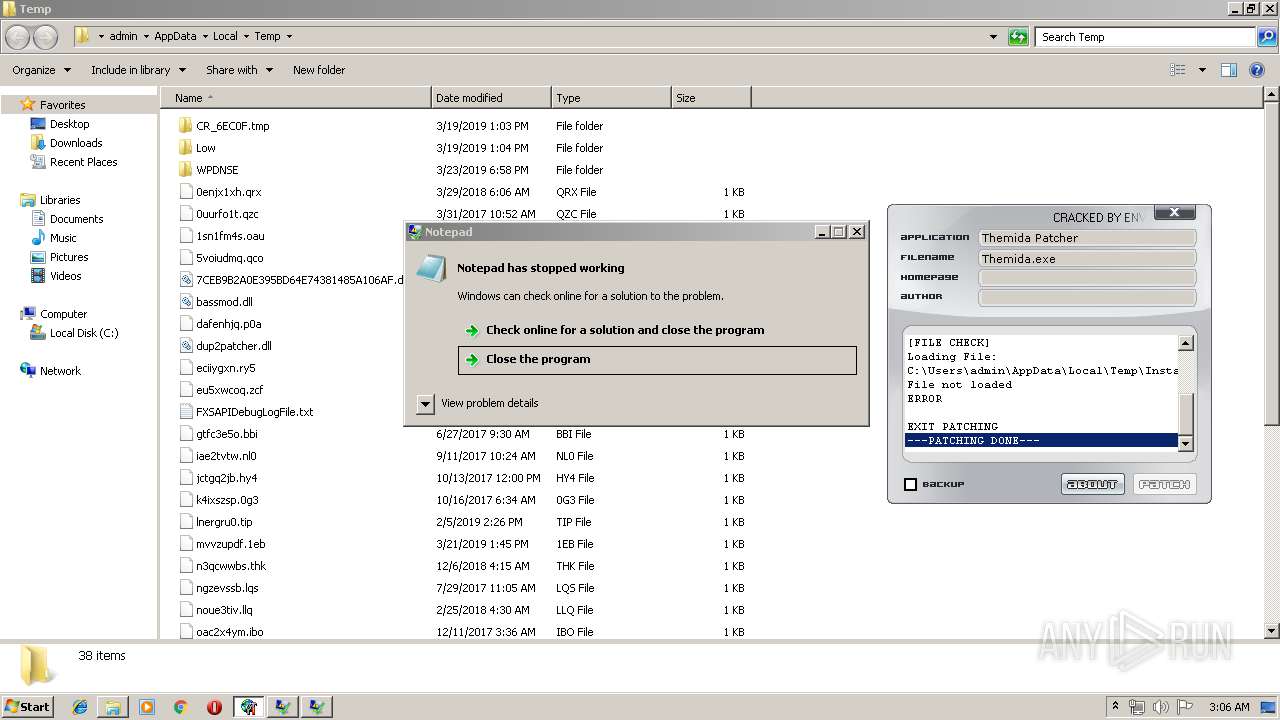
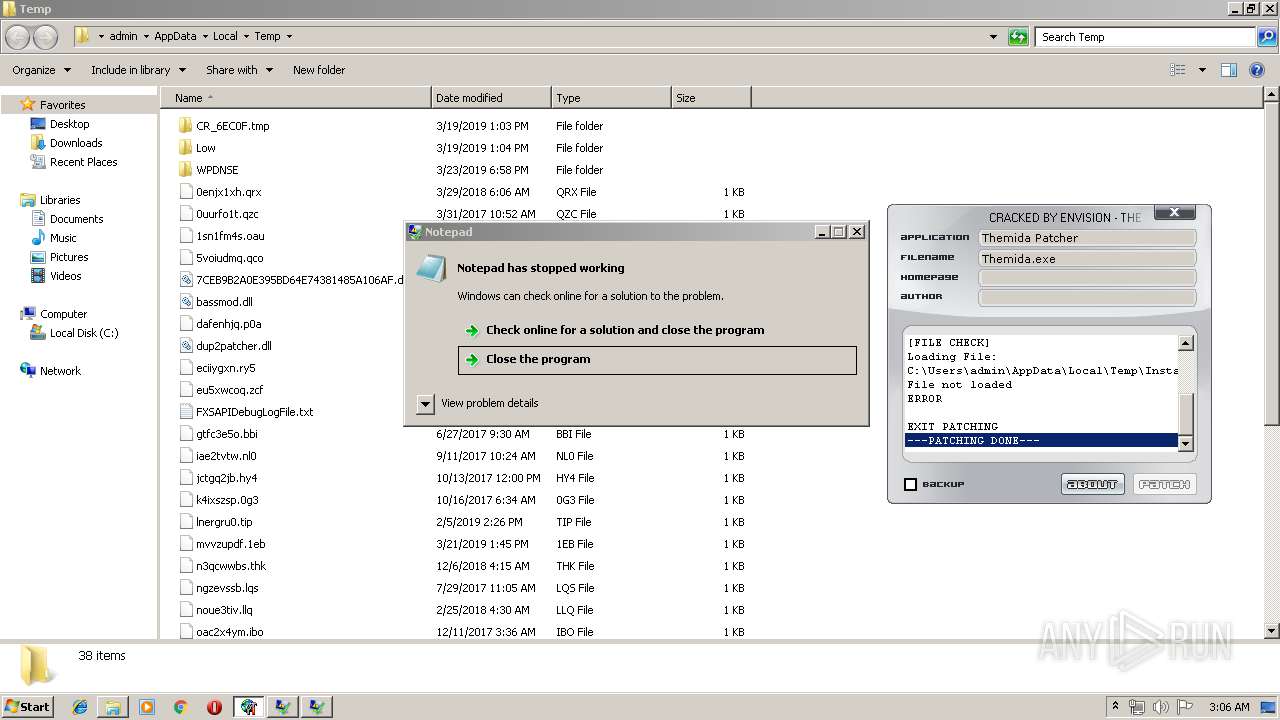
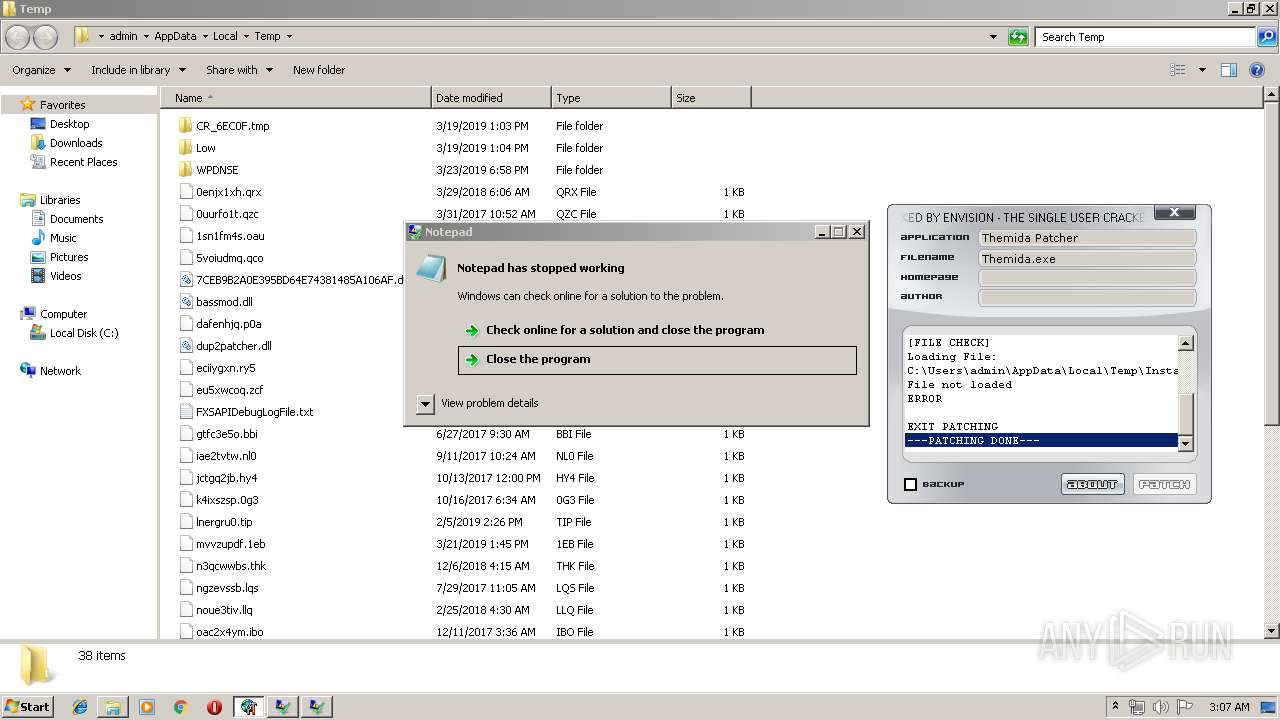
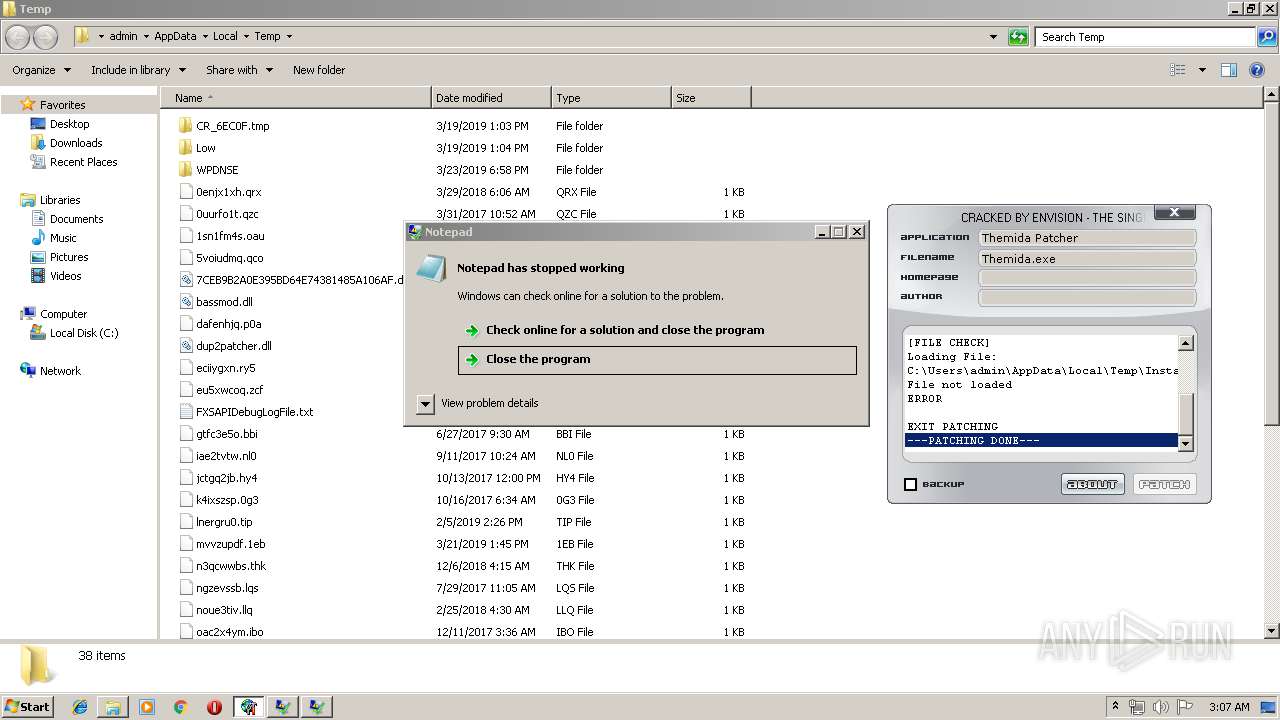
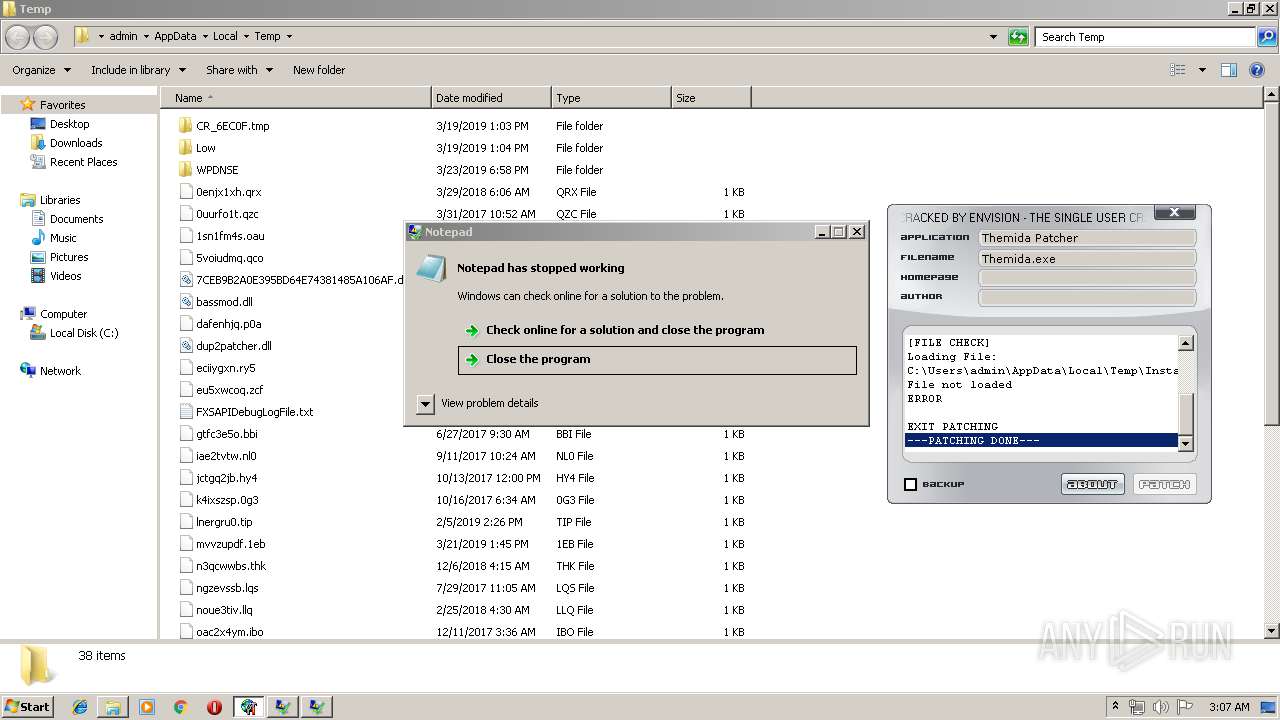
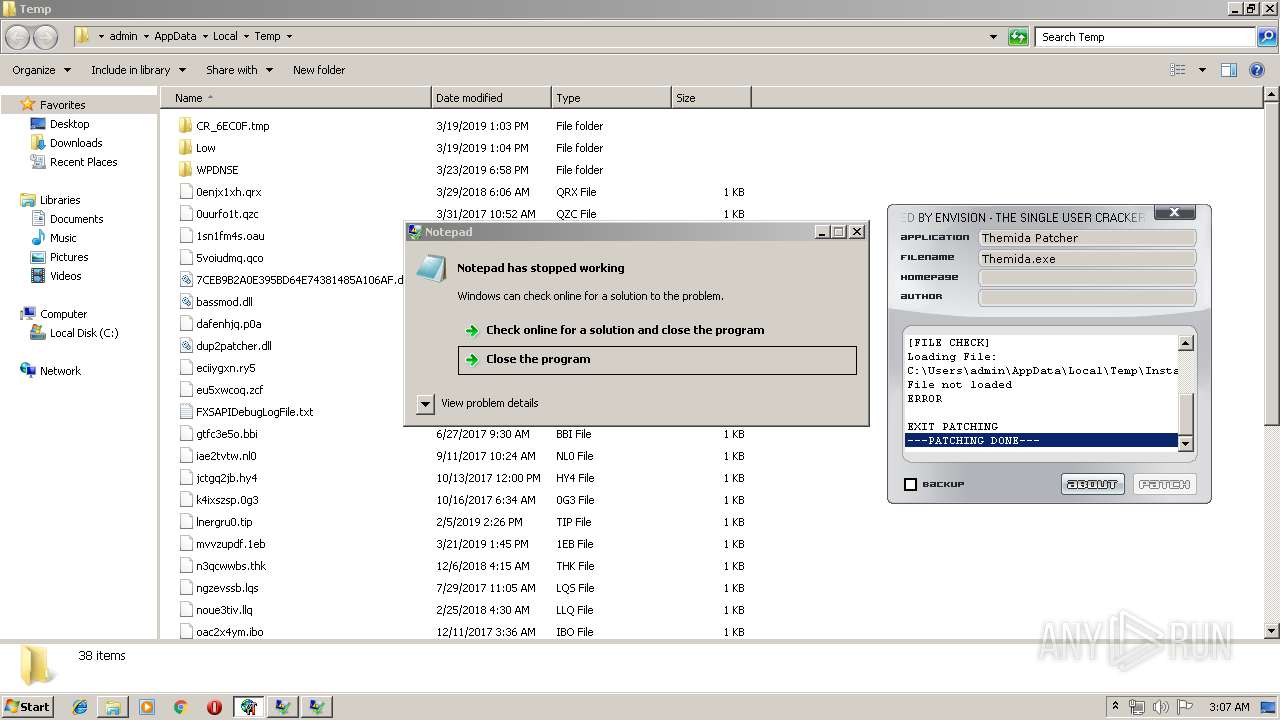
Application was crashed
- notepad.exe (PID: 1640)
- notepad.exe (PID: 596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:07:03 11:05:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 31232 |
| InitializedDataSize: | 854016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16ce |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | msupport313 |
| FileDescription: | msupport313 |
| FileVersion: | 1.0.0.0 |
| InternalName: | RouteTracer |
| LegalCopyright: | Copyrights (C) 2002-2009 Vladimir Sukhov |
| LegalTrademarks: | - |
| OriginalFileName: | routetracerv1.exe |
| ProductName: | Route Traceing |
| ProductVersion: | 1.0.0.0 |
| Comments: | msupport313.com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jul-2011 09:05:04 |
| Detected languages: |
|
| CompanyName: | msupport313 |
| FileDescription: | msupport313 |
| FileVersion: | 1.0.0.0 |
| InternalName: | RouteTracer |
| LegalCopyright: | Copyrights (C) 2002-2009 Vladimir Sukhov |
| LegalTrademarks: | - |
| OriginalFilename: | routetracerv1.exe |
| ProductName: | Route Traceing |
| ProductVersion: | 1.0.0.0 |
| Comments: | msupport313.com |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 03-Jul-2011 09:05:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x000DE000 | 0x002B6000 | 0x0002BA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99802 | |
.rsrc | 0x000DD000 | 0x00001000 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.94812 |
.data | 0x00394000 | 0x000EF000 | 0x000EE400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98702 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.37838 | 856 | UNKNOWN | English - United States | RT_VERSION |
PATCHER.EXE | 7.99925 | 260608 | Latin 1 / Western European | UNKNOWN | RBIND |
THEMIDA.PATCHER.EXE | 7.99969 | 571392 | Latin 1 / Western European | UNKNOWN | RBIND |
DROPIN | 2.58496 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
EXEC | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
advapi32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Total processes
50
Monitored processes
11
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Users\admin\AppData\Local\Temp\THEMIDA.PATCHER.EXE" | C:\Users\admin\AppData\Local\Temp\THEMIDA.PATCHER.EXE | Themida Patcher_protected.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 596 | notepad | C:\Windows\system32\notepad.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1640 | notepad | C:\Windows\system32\notepad.exe | PATCHER.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1972 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\AppData\Local\Temp" +s +h | C:\Windows\System32\cmd.exe | — | PATCHER.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\AppData\Roaming\MSDCSC\svchost.exe" | C:\Users\admin\AppData\Roaming\MSDCSC\svchost.exe | PATCHER.EXE | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: HIGH Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Local\Temp\PATCHER.EXE" | C:\Users\admin\AppData\Local\Temp\PATCHER.EXE | Themida Patcher_protected.exe | ||||||||||||
User: admin Company: Microsoft Corp. Integrity Level: HIGH Description: Remote Service Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2824 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\AppData\Local\Temp\PATCHER.EXE" +s +h | C:\Windows\System32\cmd.exe | — | PATCHER.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3580 | attrib "C:\Users\admin\AppData\Local\Temp\PATCHER.EXE" +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\AppData\Local\Temp\Themida Patcher_protected.exe" | C:\Users\admin\AppData\Local\Temp\Themida Patcher_protected.exe | explorer.exe | ||||||||||||
User: admin Company: msupport313 Integrity Level: HIGH Description: msupport313 Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3716 | attrib "C:\Users\admin\AppData\Local\Temp" +s +h | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 388
Read events
1 293
Write events
95
Delete events
0
Modification events
| (PID) Process: | (2520) PATCHER.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | svchost |
Value: C:\Users\admin\AppData\Roaming\MSDCSC\svchost.exe | |||
| (PID) Process: | (2520) PATCHER.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | UserInit |
Value: C:\Windows\system32\userinit.exe,C:\Users\admin\AppData\Roaming\MSDCSC\svchost.exe | |||
| (PID) Process: | (3708) Themida Patcher_protected.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3708) Themida Patcher_protected.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2520) PATCHER.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2520) PATCHER.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2520) PATCHER.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2324) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | svchost |
Value: C:\Users\admin\AppData\Roaming\MSDCSC\svchost.exe | |||
| (PID) Process: | (2324) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 1 | |||
| (PID) Process: | (2520) PATCHER.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\ntshrui.dll,-103 |
Value: S&hare with | |||
Executable files
6
Suspicious files
0
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3708 | Themida Patcher_protected.exe | C:\Users\admin\AppData\Local\Temp\PATCHER.EXE | executable | |
MD5:— | SHA256:— | |||
| 2520 | PATCHER.EXE | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
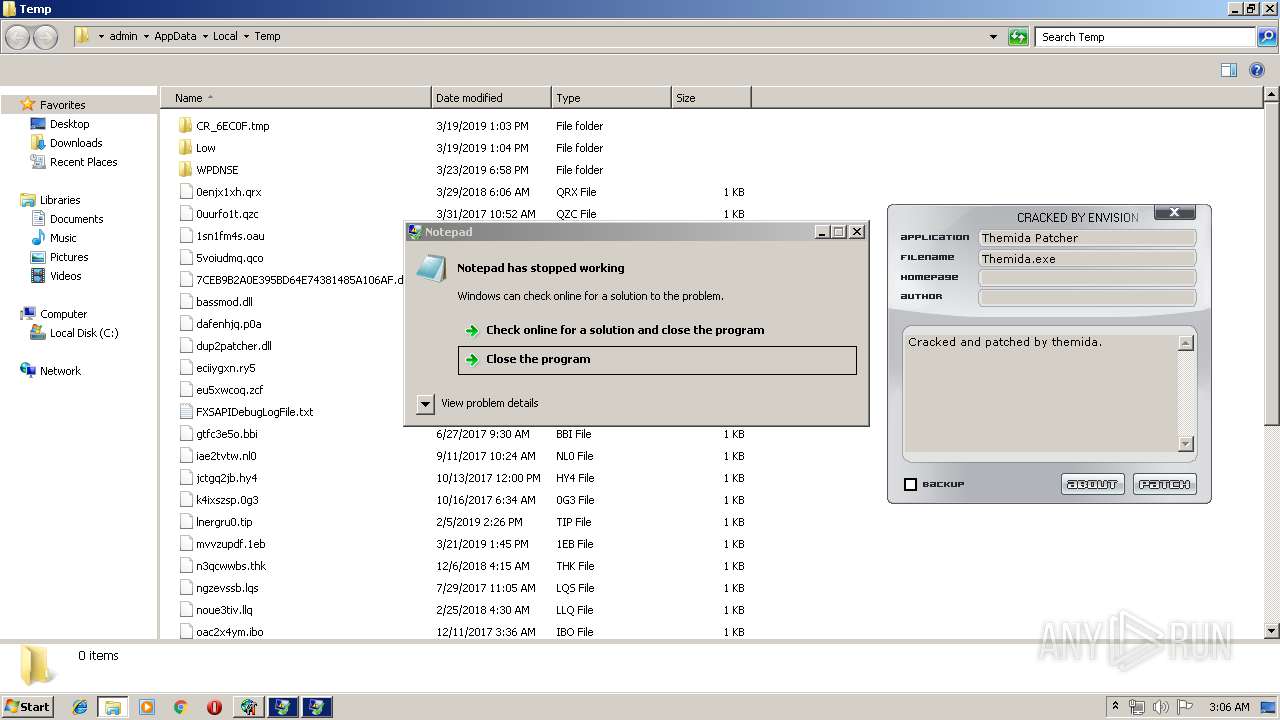
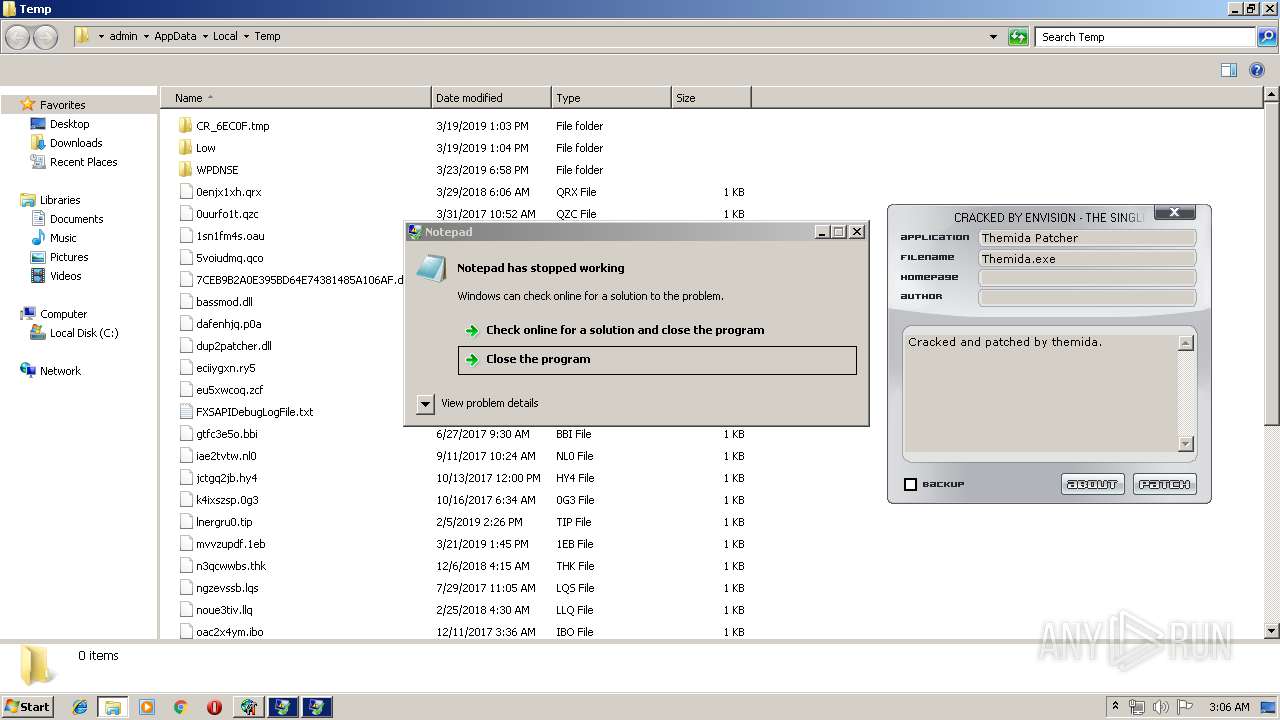
| 252 | THEMIDA.PATCHER.EXE | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:— | SHA256:— | |||
| 2520 | PATCHER.EXE | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat | hiv | |
MD5:— | SHA256:— | |||
| 2520 | PATCHER.EXE | C:\Users\admin\AppData\Roaming\MSDCSC\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 2520 | PATCHER.EXE | C:\Users\Administrator\AppData\Local\Microsoft\Windows\UsrClass.dat.LOG1 | log | |
MD5:— | SHA256:— | |||
| 2520 | PATCHER.EXE | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 3708 | Themida Patcher_protected.exe | C:\Users\admin\AppData\Local\Temp\THEMIDA.PATCHER.EXE | executable | |
MD5:— | SHA256:— | |||
| 252 | THEMIDA.PATCHER.EXE | C:\Users\admin\AppData\Local\Temp\7CEB9B2A0E395BD64E74381485A106AF.dll | executable | |
MD5:5AFB011D9DB047BB0400C5C5CA2E450B | SHA256:125FC74E03435B3E0EDE0FF523D625D9C1FBB299286E9E2DBD1442E506150DA6 | |||
| 252 | THEMIDA.PATCHER.EXE | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:D55F25972291D5AF43940B4BCA124774 | SHA256:FFD0A2F5161E459FCF34EEECA9F777E8DCDEC11712B3ECEE4B4243D06FADC189 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
19
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2324 | svchost.exe | 24.89.119.57:27016 | bidasci.duckdns.org | Access Communications Co-operative Limited | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bidasci.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
2324 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] DarkComet-RAT Inbound connection |
2324 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Win32.DarkKomet!O outbound stream |
2324 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible DarkComet-RAT activity |
2324 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible DarkComet-RAT activity |
2324 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible DarkComet-RAT activity |
2324 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible DarkComet-RAT activity |
2324 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible DarkComet-RAT activity |
2324 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Possible DarkComet-RAT activity |
1068 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
8 ETPRO signatures available at the full report
Process | Message |
|---|---|
Themida Patcher_protected.exe | C:\Users\admin\AppData\Local\Temp\PATCHER.EXE |
Themida Patcher_protected.exe | C:\Users\admin\AppData\Local\Temp\THEMIDA.PATCHER.EXE |