| File name: | d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.gz |
| Full analysis: | https://app.any.run/tasks/f12b980d-1d89-45a5-8fb9-65f65d150726 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 15, 2019, 07:28:44 |
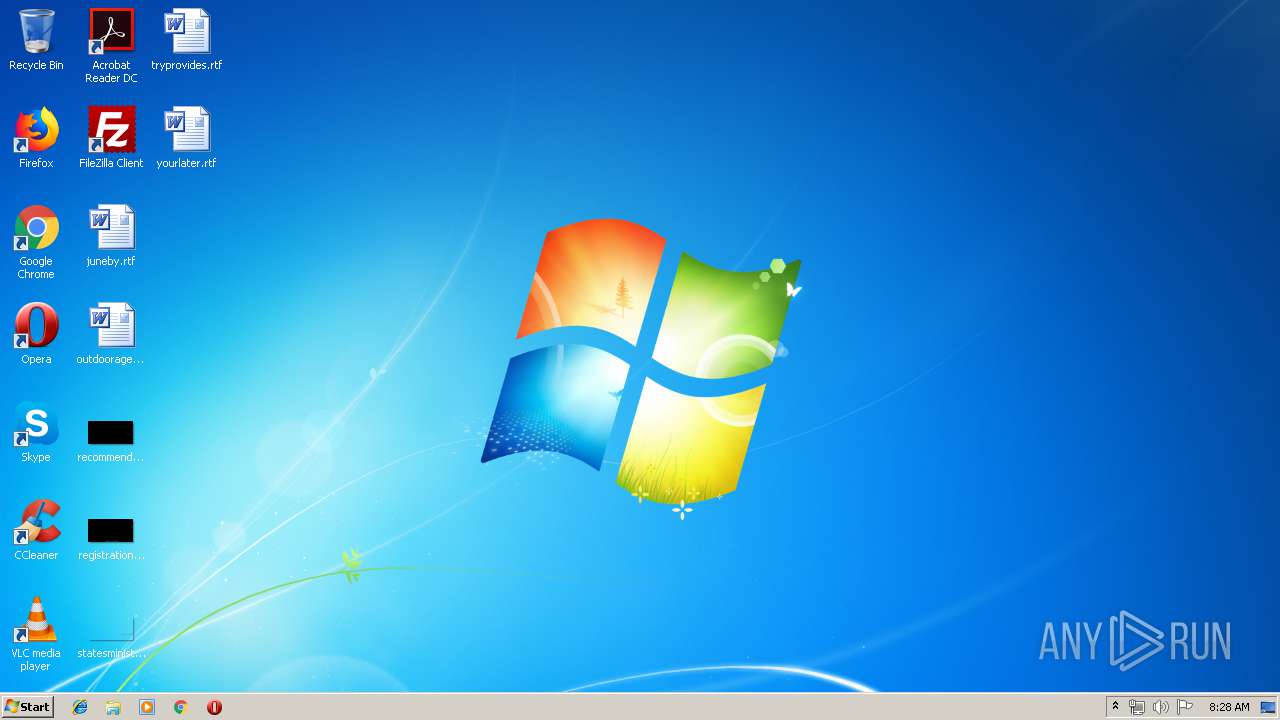
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/gzip |
| File info: | gzip compressed data, max compression, from Unix |
| MD5: | 4282F98ADF1CD388108E3704D0E97FA0 |
| SHA1: | 5D58A2BBABD2AFE84517E95C9A929DD5CF539596 |
| SHA256: | 3980460CA8046DC4BF9674F6CA3517DC82F01DAB95744781DDFFEC268EA20317 |
| SSDEEP: | 3072:YZhH490GdyBnkp3I39BcwIPQsmPaA3H7QW6gRklYLauO/eZNQaiCy7G27:YZhHW/UNkp4NBvIe1HMWyE+/eZN1im27 |
MALICIOUS
Application was dropped or rewritten from another process
- d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe (PID: 3628)
Actions looks like stealing of personal data
- d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe (PID: 3628)
AGENTTESLA was detected
- d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe (PID: 3628)
SUSPICIOUS
Checks for external IP
- d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe (PID: 3628)
Changes tracing settings of the file or console
- d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe (PID: 3628)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .z/gz/gzip | | | GZipped data (100) |
|---|
EXIF
ZIP
| Compression: | Deflated |
|---|---|
| Flags: | (none) |
| ModifyDate: | 0000:00:00 00:00:00 |
| ExtraFlags: | Maximum Compression |
| OperatingSystem: | Unix |
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
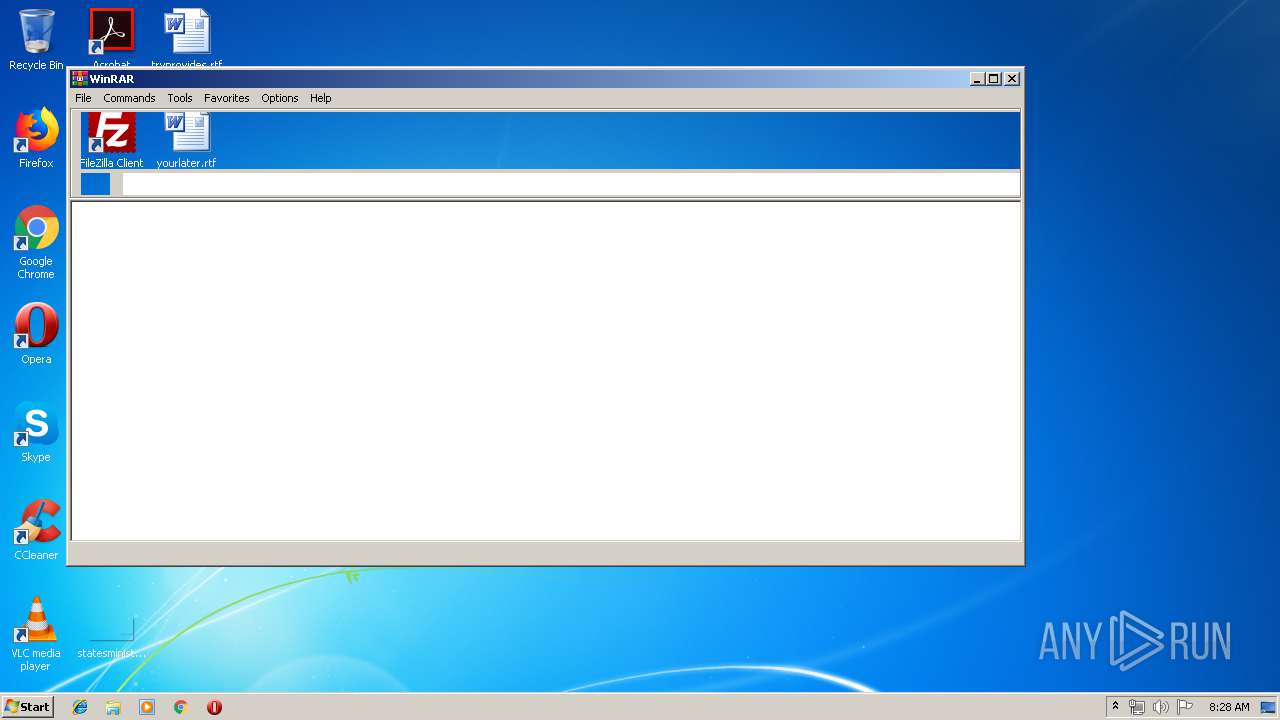
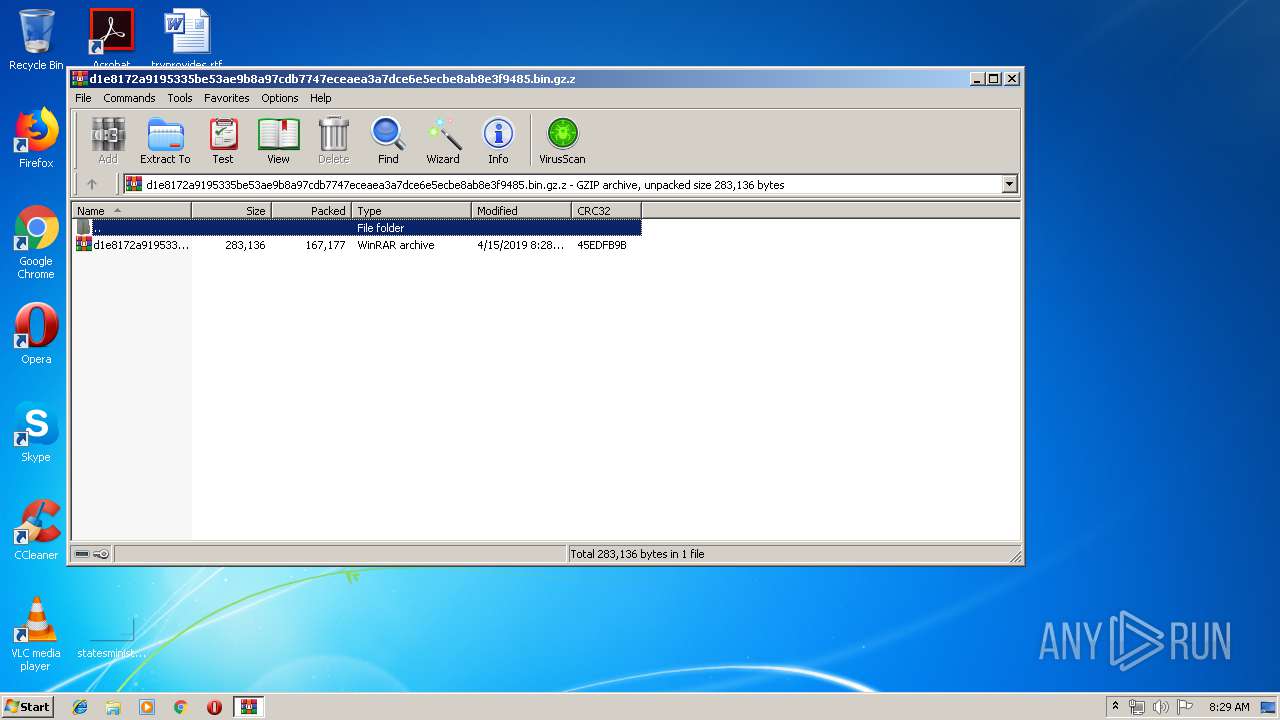
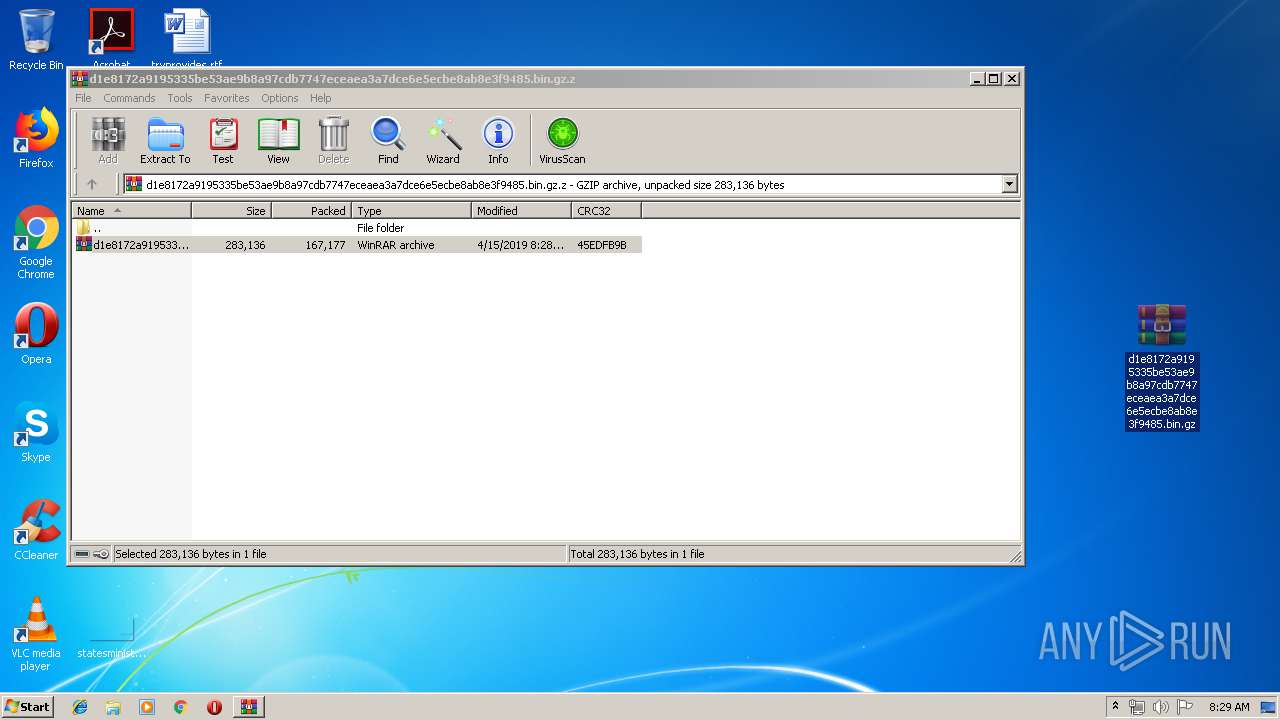
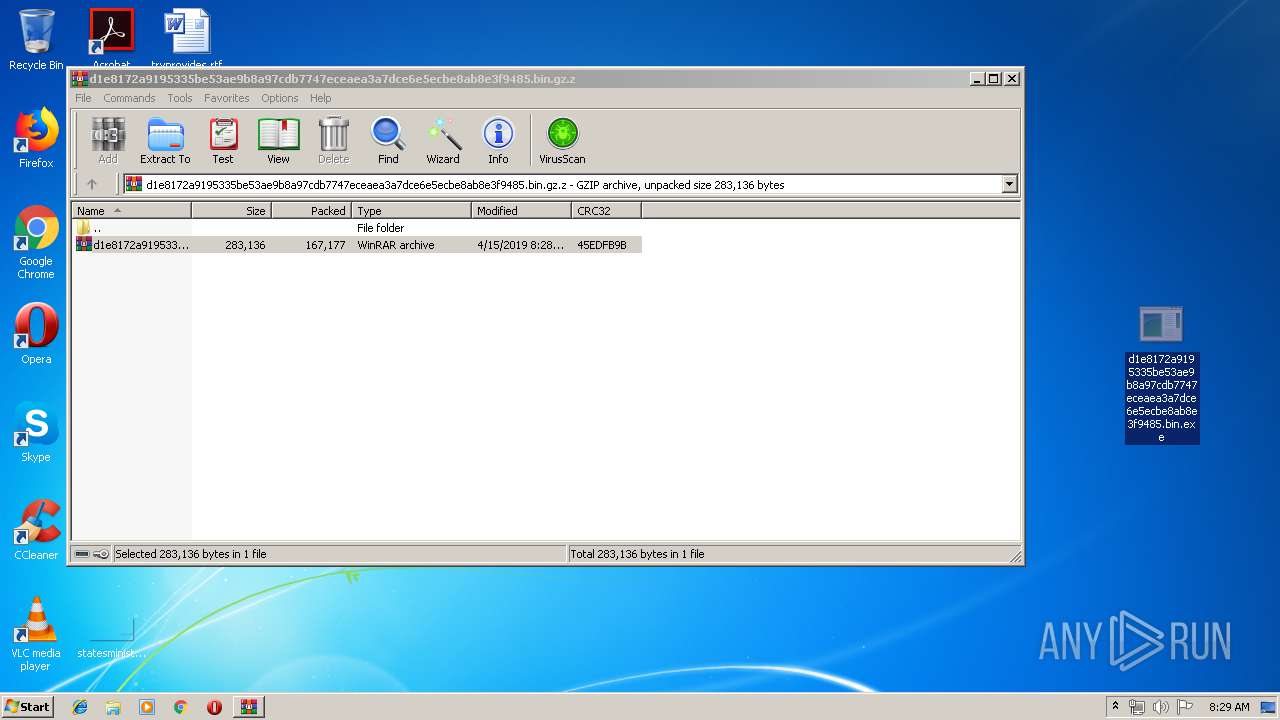
| 3352 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.gz.z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3628 | "C:\Users\admin\Desktop\d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe" | C:\Users\admin\Desktop\d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
487
Read events
467
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3352) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.gz.z | |||
| (PID) Process: | (3352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3352) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3628) d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3628) d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3352 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3352.34732\d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.gz | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3628 | d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | GET | 200 | 18.211.215.84:80 | http://checkip.amazonaws.com/ | US | text | 15 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3628 | d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | 18.211.215.84:80 | checkip.amazonaws.com | — | US | shared |
3628 | d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | 208.91.199.224:587 | smtp.amchlk.com | PDR | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
smtp.amchlk.com |
| shared |
checkip.amazonaws.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3628 | d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3628 | d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
3628 | d1e8172a9195335be53ae9b8a97cdb7747eceaea3a7dce6e5ecbe8ab8e3f9485.bin.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan-Spy.Keylogger.AgentTesla Exfiltration by SMTP |
2 ETPRO signatures available at the full report