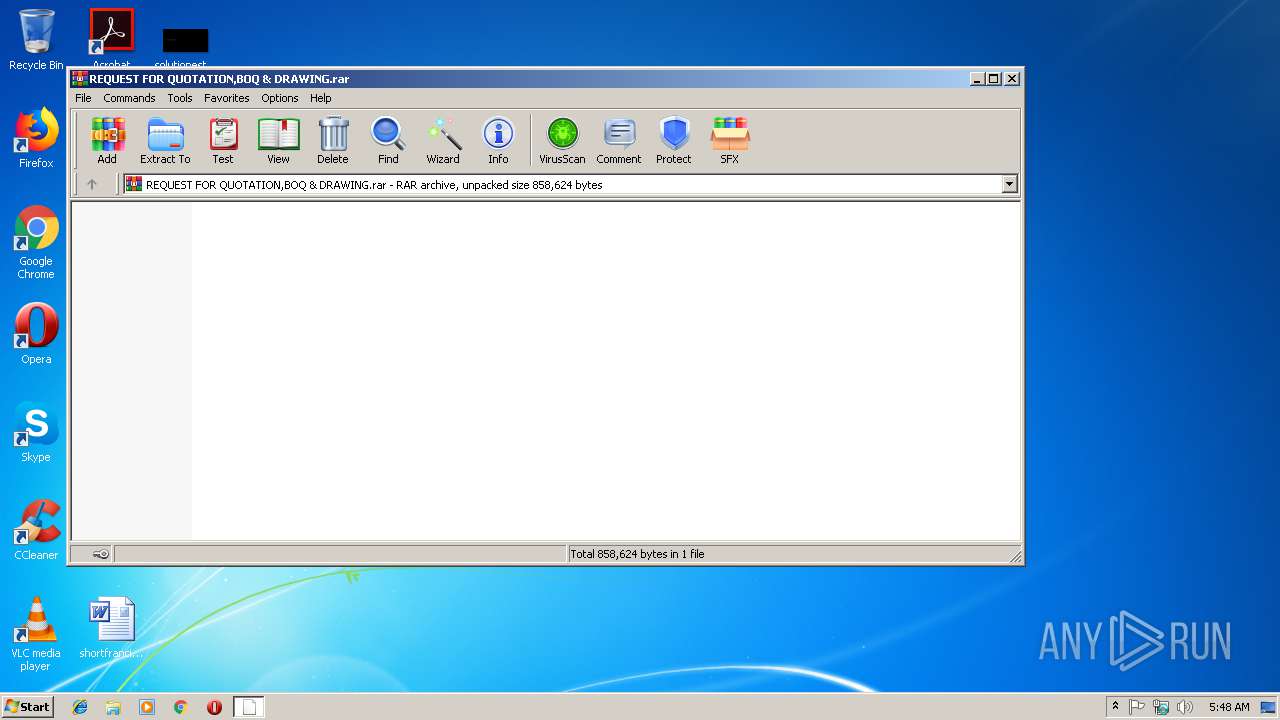
| File name: | REQUEST FOR QUOTATION,BOQ & DRAWING.rar |
| Full analysis: | https://app.any.run/tasks/3a682561-89fb-4689-aab6-fe865ad94fbf |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
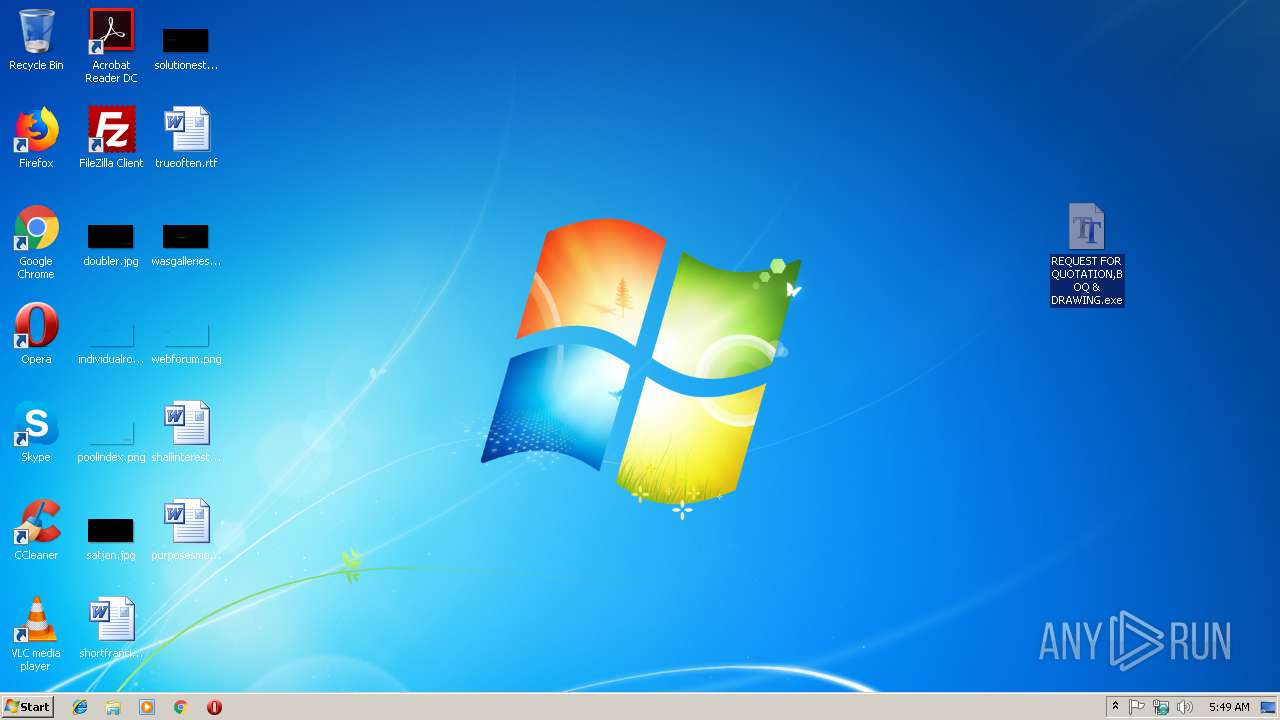
| Analysis date: | February 19, 2019, 05:48:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | D275FB6084AC707A19C3BF1E7305DC05 |
| SHA1: | 3B86A309B7BAB82635F3274E354D20A4C5015F29 |
| SHA256: | 38E7FBE4F8CC87E3EF412D1B9E1574C2E8A09497D1E08C2FB1A0900240800683 |
| SSDEEP: | 12288:Onf97oCzZrZtDc2zmXywWA/zPYlsORi9wWPFC5+X+59i0lL:k71lrZtDc2zmXyPAElsORkbn+5A4L |
MALICIOUS
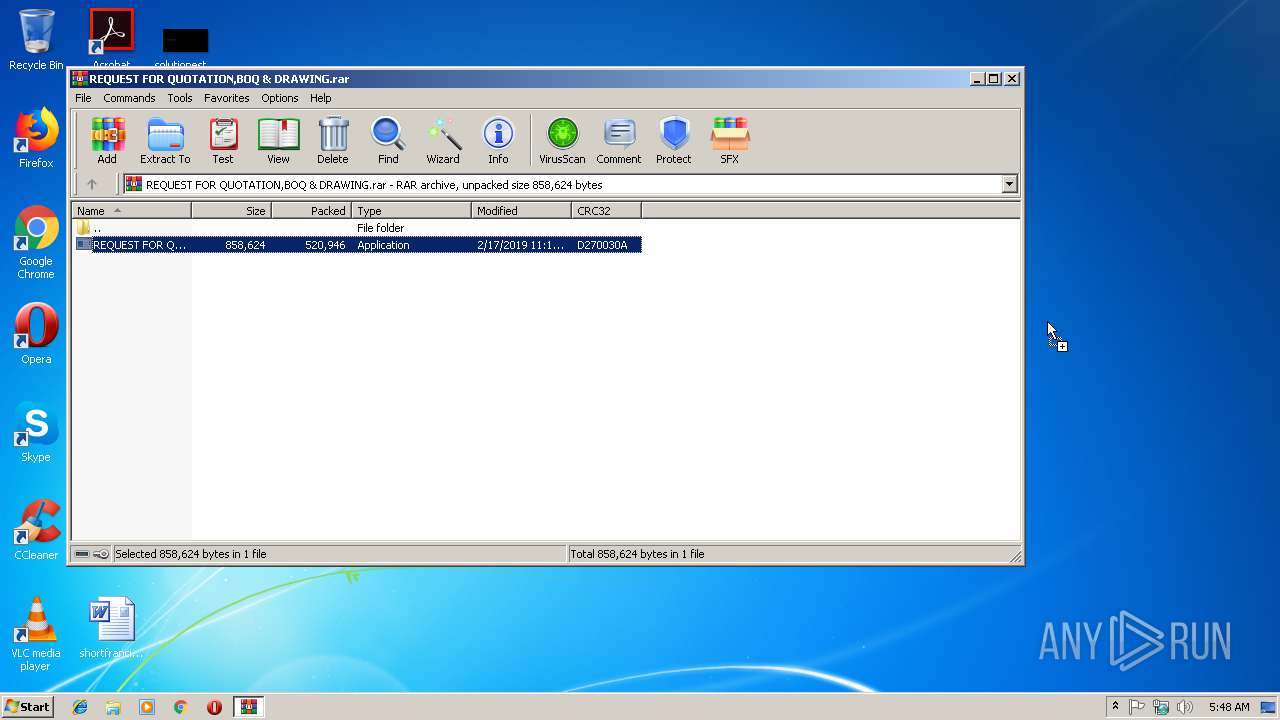
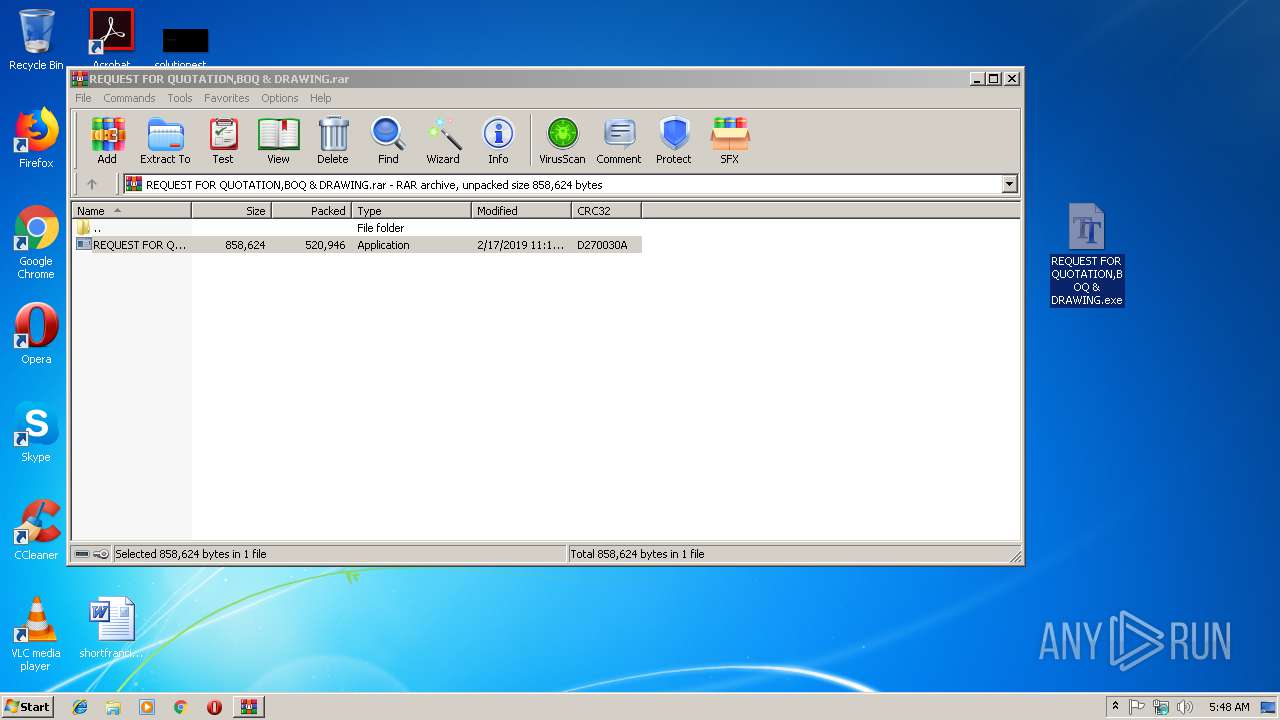
Application was dropped or rewritten from another process
- REQUEST FOR QUOTATION,BOQ & DRAWING.exe (PID: 2936)
- REQUEST FOR QUOTATION,BOQ & DRAWING.exe (PID: 3104)
Actions looks like stealing of personal data
- vbc.exe (PID: 2996)
Detected Hawkeye Keylogger
- REQUEST FOR QUOTATION,BOQ & DRAWING.exe (PID: 3104)
SUSPICIOUS
Checks for external IP
- REQUEST FOR QUOTATION,BOQ & DRAWING.exe (PID: 3104)
Connects to SMTP port
- REQUEST FOR QUOTATION,BOQ & DRAWING.exe (PID: 3104)
Executes scripts
- REQUEST FOR QUOTATION,BOQ & DRAWING.exe (PID: 3104)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 2780)
Creates files in the user directory
- REQUEST FOR QUOTATION,BOQ & DRAWING.exe (PID: 3104)
Application launched itself
- REQUEST FOR QUOTATION,BOQ & DRAWING.exe (PID: 2936)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
36
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2780 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holderwb.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | — | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 2936 | "C:\Users\admin\Desktop\REQUEST FOR QUOTATION,BOQ & DRAWING.exe" | C:\Users\admin\Desktop\REQUEST FOR QUOTATION,BOQ & DRAWING.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2988 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\REQUEST FOR QUOTATION,BOQ & DRAWING.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2996 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe /stext "C:\Users\admin\AppData\Local\Temp\holdermail.txt" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\Desktop\REQUEST FOR QUOTATION,BOQ & DRAWING.exe" | C:\Users\admin\Desktop\REQUEST FOR QUOTATION,BOQ & DRAWING.exe | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
522
Read events
490
Write events
32
Delete events
0
Modification events
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\REQUEST FOR QUOTATION,BOQ & DRAWING.rar | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2988) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2988.33967\REQUEST FOR QUOTATION,BOQ & DRAWING.exe | — | |
MD5:— | SHA256:— | |||
| 2996 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holdermail.txt | — | |
MD5:— | SHA256:— | |||
| 2780 | vbc.exe | C:\Users\admin\AppData\Local\Temp\holderwb.txt | — | |
MD5:— | SHA256:— | |||
| 3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | C:\Users\admin\AppData\Roaming\pidloc.txt | text | |
MD5:— | SHA256:— | |||
| 3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | C:\Users\admin\AppData\Roaming\pid.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | GET | 403 | 104.16.154.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | 104.16.154.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | 208.91.198.143:587 | smtp.t1si.com | PDR | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
smtp.t1si.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spyware.HawkEyeKeyLogger (IP Chck) |
3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | A Network Trojan was detected | MALWARE [PTsecurity] MSIL/Golroted.B/Hawkeye Keylogger Sending Data via SMTP |
3104 | REQUEST FOR QUOTATION,BOQ & DRAWING.exe | A Network Trojan was detected | MALWARE [PTsecurity] MSIL/Golroted.B/Hawkeye Keylogger Sending Data via SMTP |
3 ETPRO signatures available at the full report