| File name: | lostboy.exe |
| Full analysis: | https://app.any.run/tasks/e98073d3-e6c1-434a-942e-c071a5c3a793 |
| Verdict: | Malicious activity |
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | May 11, 2023, 08:02:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F5B12F5F6625413BB87C228282C53F9B |
| SHA1: | 50AE6529F8F63E06C50157CE7AABE158495043B5 |
| SHA256: | 3891281145B998066D1C906CDB0DB4C2185257DEC45F459F17D4AFCBA17A50C9 |
| SSDEEP: | 24576:kRmJkcoQricOIQxiZY1iaIiZgPx3gMn4L3lpD2J9yU0ze/Fm7ojDybqVgeAOG06z:hJZoQrbTFZY1iaIiZgPZg136zXByoPy/ |
MALICIOUS
DARKCOMET detected by memory dumps
- lostboy.exe (PID: 3688)
- msdcsc.exe (PID: 3120)
Changes the autorun value in the registry
- lostboy.exe (PID: 3324)
- lostboy.exe (PID: 4024)
- lostboy.exe (PID: 3552)
- msdcsc.exe (PID: 3120)
- lostboy.exe (PID: 3424)
SUSPICIOUS
Application launched itself
- lostboy.exe (PID: 3360)
- msdcsc.exe (PID: 1024)
- lostboy.exe (PID: 3324)
- lostboy.exe (PID: 3552)
Reads the Internet Settings
- lostboy.exe (PID: 3688)
Executable content was dropped or overwritten
- lostboy.exe (PID: 3688)
Starts CMD.EXE for commands execution
- lostboy.exe (PID: 3688)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1592)
- cmd.exe (PID: 312)
Starts itself from another location
- lostboy.exe (PID: 3688)
Start notepad (likely ransomware note)
- msdcsc.exe (PID: 3120)
INFO
Create files in a temporary directory
- lostboy.exe (PID: 3360)
- lostboy.exe (PID: 3688)
- msdcsc.exe (PID: 1024)
- lostboy.exe (PID: 3324)
- lostboy.exe (PID: 3552)
Reads the computer name
- lostboy.exe (PID: 3360)
- lostboy.exe (PID: 3688)
- msdcsc.exe (PID: 1024)
- lostboy.exe (PID: 3324)
- msdcsc.exe (PID: 3120)
- lostboy.exe (PID: 4024)
- lostboy.exe (PID: 3552)
- lostboy.exe (PID: 3424)
Checks supported languages
- lostboy.exe (PID: 3360)
- lostboy.exe (PID: 3688)
- msdcsc.exe (PID: 1024)
- lostboy.exe (PID: 3324)
- msdcsc.exe (PID: 3120)
- lostboy.exe (PID: 4024)
- lostboy.exe (PID: 3552)
- lostboy.exe (PID: 3424)
Reads mouse settings
- lostboy.exe (PID: 3360)
- msdcsc.exe (PID: 1024)
- lostboy.exe (PID: 3324)
- lostboy.exe (PID: 3552)
The process checks LSA protection
- lostboy.exe (PID: 3360)
- lostboy.exe (PID: 3688)
- msdcsc.exe (PID: 1024)
- lostboy.exe (PID: 3324)
- lostboy.exe (PID: 3552)
- msdcsc.exe (PID: 3120)
Reads the machine GUID from the registry
- lostboy.exe (PID: 3360)
- lostboy.exe (PID: 3688)
- msdcsc.exe (PID: 1024)
- lostboy.exe (PID: 3324)
- lostboy.exe (PID: 3552)
Creates files or folders in the user directory
- lostboy.exe (PID: 3360)
- msdcsc.exe (PID: 1024)
- lostboy.exe (PID: 3552)
- lostboy.exe (PID: 3324)
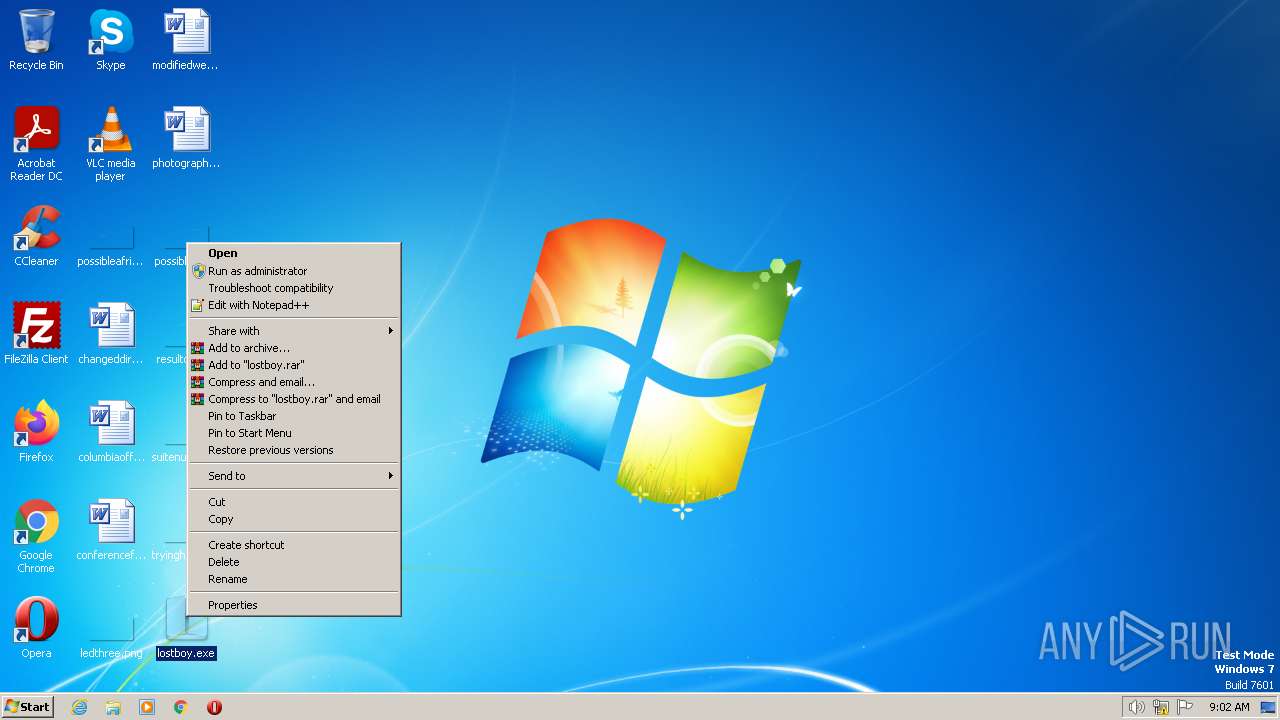
Manual execution by a user
- lostboy.exe (PID: 3324)
- lostboy.exe (PID: 3552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DarkComet
(PID) Process(3688) lostboy.exe
C2 (1)ajensen.no-ip.biz:742
Version#KCMDDC51#
MutexDC_MUTEX-1B5YY6N
sidPet
FWB0
gencodesRiwXMGwfFsv
InstallTrue
COMBOPATH10
Install pathMSDCSC\msdcsc.exe
Registry keyrundll32
Edit date2012-06-16
PersistanceTrue
MELT0
Change Date1
Directory attributesTrue
File attrubutesTrue
FAKEMSG1
MSGTITLEError
MSGCORE57696E646F7773206861732072756E206F7574206F66206D656D6F7279
MSGICON16
SH11
CHIDEF1
CHIDED1
PERS1
Offline keyloggerTrue
(PID) Process(3120) msdcsc.exe
C2 (1)ajensen.no-ip.biz:742
Version#KCMDDC51#
MutexDC_MUTEX-1B5YY6N
sidPet
FWB0
gencodesRiwXMGwfFsv
InstallTrue
COMBOPATH10
Install pathMSDCSC\msdcsc.exe
Registry keyrundll32
Edit date2012-06-16
PersistanceTrue
MELT0
Change Date1
Directory attributesTrue
File attrubutesTrue
FAKEMSG1
MSGTITLEError
MSGCORE57696E646F7773206861732072756E206F7574206F66206D656D6F7279
MSGICON16
SH11
CHIDEF1
CHIDED1
PERS1
Offline keyloggerTrue
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| CompiledScript: | AutoIt v3 Script: 3, 3, 8, 1 |
|---|---|
| FileVersion: | 3, 3, 8, 1 |
| FileDescription: | - |
| CharacterSet: | Unicode |
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0017 |
| ProductVersionNumber: | 3.3.8.1 |
| FileVersionNumber: | 3.3.8.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x165c1 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 121856 |
| CodeSize: | 526336 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| TimeStamp: | 2012:01:29 21:32:28+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jan-2012 21:32:28 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 3, 3, 8, 1 |
| CompiledScript: | AutoIt v3 Script: 3, 3, 8, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 29-Jan-2012 21:32:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008061C | 0x00080800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68469 |
.rdata | 0x00082000 | 0x0000DFC0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.79974 |
.data | 0x00090000 | 0x0001A758 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.15007 |
.rsrc | 0x000AB000 | 0x0001C7B0 | 0x0001C800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.70969 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01246 | 620 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.66371 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 5.40671 | 67624 | UNKNOWN | English - United Kingdom | RT_ICON |
5 | 6.03129 | 21640 | UNKNOWN | English - United Kingdom | RT_ICON |
6 | 5.98208 | 9640 | UNKNOWN | English - United Kingdom | RT_ICON |
7 | 3.31436 | 1328 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.28624 | 1680 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.2836 | 1232 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
Total processes
53
Monitored processes
13
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\Desktop" +s +h | C:\Windows\System32\cmd.exe | — | lostboy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 572 | attrib "C:\Users\admin\Desktop\lostboy.exe" +s +h | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe" | C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | — | lostboy.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 1592 | "C:\Windows\System32\cmd.exe" /k attrib "C:\Users\admin\Desktop\lostboy.exe" +s +h | C:\Windows\System32\cmd.exe | — | lostboy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1840 | attrib "C:\Users\admin\Desktop" +s +h | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3120 | C:\Windows\system32\notepad.exe | C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | msdcsc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
DarkComet(PID) Process(3120) msdcsc.exe C2 (1)ajensen.no-ip.biz:742 Version#KCMDDC51# MutexDC_MUTEX-1B5YY6N sidPet FWB0 gencodesRiwXMGwfFsv InstallTrue COMBOPATH10 Install pathMSDCSC\msdcsc.exe Registry keyrundll32 Edit date2012-06-16 PersistanceTrue MELT0 Change Date1 Directory attributesTrue File attrubutesTrue FAKEMSG1 MSGTITLEError MSGCORE57696E646F7773206861732072756E206F7574206F66206D656D6F7279 MSGICON16 SH11 CHIDEF1 CHIDED1 PERS1 Offline keyloggerTrue | |||||||||||||||
| 3324 | "C:\Users\admin\Desktop\lostboy.exe" | C:\Users\admin\Desktop\lostboy.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 3360 | "C:\Users\admin\Desktop\lostboy.exe" | C:\Users\admin\Desktop\lostboy.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 3424 | C:\Windows\system32\notepad.exe | C:\Users\admin\Desktop\lostboy.exe | lostboy.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
| 3552 | "C:\Users\admin\Desktop\lostboy.exe" | C:\Users\admin\Desktop\lostboy.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 3, 3, 8, 1 Modules
| |||||||||||||||
Total events
4 406
Read events
4 258
Write events
148
Delete events
0
Modification events
| (PID) Process: | (3688) lostboy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3688) lostboy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3688) lostboy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3688) lostboy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3688) lostboy.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3324) lostboy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | lostboy.exe |
Value: C:\Users\admin\Desktop\lostboy.exe | |||
| (PID) Process: | (3120) msdcsc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | rundll32 |
Value: C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (4024) lostboy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | rundll32 |
Value: C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | |||
| (PID) Process: | (3552) lostboy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | lostboy.exe |
Value: C:\Users\admin\Desktop\lostboy.exe | |||
| (PID) Process: | (3424) lostboy.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | rundll32 |
Value: C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | |||
Executable files
2
Suspicious files
16
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1024 | msdcsc.exe | C:\Users\admin\AppData\Roaming\fk1xxx.e2ts | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 3360 | lostboy.exe | C:\Users\admin\AppData\Local\Temp\aut8ED4.tmp | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 3360 | lostboy.exe | C:\Users\admin\AppData\Roaming\fk1xxx.e2ts | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 3324 | lostboy.exe | C:\Users\admin\AppData\Roaming\fk1xxx.e2ts | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 3552 | lostboy.exe | C:\Users\admin\AppData\Roaming\fk1xxx.e2ts | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 1024 | msdcsc.exe | C:\Users\admin\AppData\Local\Temp\autB4EA.tmp | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 3324 | lostboy.exe | C:\Users\admin\AppData\Local\Temp\autCC1C.tmp | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
| 3688 | lostboy.exe | C:\Users\admin\AppData\Local\Temp\MSDCSC\msdcsc.exe | executable | |
MD5:F5B12F5F6625413BB87C228282C53F9B | SHA256:3891281145B998066D1C906CDB0DB4C2185257DEC45F459F17D4AFCBA17A50C9 | |||
| 3552 | lostboy.exe | C:\Users\admin\AppData\Local\Temp\aut2A78.tmp | binary | |
MD5:9CA7C235BCA9376B9F192BC0956FC0B9 | SHA256:12112797DD4B7B685A2733FB9DEC6DE1F86087F3192523ED9A7693A8A3415F1D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
ajensen.no-ip.biz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Misc activity | ET INFO DYNAMIC_DNS Query to a Suspicious no-ip Domain |