| File name: | Step 3 - Setup_Install.exe |
| Full analysis: | https://app.any.run/tasks/476cb342-d1f9-48bb-bc19-2dd1ff3cc7ae |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | August 28, 2024, 15:28:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A0023254D52F0F0AE306EAA788F4D628 |
| SHA1: | 43C3058F6C9F64BCC7DA8F2D8E0A5DA0076B4948 |
| SHA256: | 383ED6C9CDF8590845730198DFDE66CD799EC047CA8850CB5ECDFED293FA287C |
| SSDEEP: | 98304:CO7UY7BGRmoqWseW/sygVXIGdPdxy5sYOvYDNBzAUpXc/5jZDPBpjhPbh896J45A:VBNmt |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6824)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 6988)
Connects to the CnC server
- cmd.exe (PID: 6576)
MINER has been detected (SURICATA)
- cmd.exe (PID: 6576)
SUSPICIOUS
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1640)
- Step 3 - Setup_Install.exe (PID: 4644)
Process drops legitimate windows executable
- Step 3 - Setup_Install.exe (PID: 4644)
Drops the executable file immediately after the start
- msiexec.exe (PID: 1640)
- Step 3 - Setup_Install.exe (PID: 4644)
- WindowsService.exe (PID: 5112)
Executable content was dropped or overwritten
- Step 3 - Setup_Install.exe (PID: 4644)
- WindowsService.exe (PID: 5112)
Creates FileSystem object to access computer's file system (SCRIPT)
- msiexec.exe (PID: 6792)
Checks whether a specific file exists (SCRIPT)
- msiexec.exe (PID: 6792)
Runs shell command (SCRIPT)
- msiexec.exe (PID: 6792)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 6988)
The process executes Powershell scripts
- msiexec.exe (PID: 6988)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 6988)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 6988)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 6824)
Drops a system driver (possible attempt to evade defenses)
- WindowsService.exe (PID: 5112)
Starts CMD.EXE for commands execution
- WindowsService.exe (PID: 5112)
Connects to unusual port
- WindowsService.exe (PID: 5112)
- cmd.exe (PID: 6576)
Reads security settings of Internet Explorer
- WindowsService.exe (PID: 5112)
Potential Corporate Privacy Violation
- cmd.exe (PID: 6576)
Crypto Currency Mining Activity Detected
- cmd.exe (PID: 6576)
INFO
Creates files or folders in the user directory
- Step 3 - Setup_Install.exe (PID: 4644)
- msiexec.exe (PID: 1640)
- WindowsService.exe (PID: 5112)
Create files in a temporary directory
- Step 3 - Setup_Install.exe (PID: 4644)
- powershell.exe (PID: 6824)
Reads the computer name
- msiexec.exe (PID: 6928)
- msiexec.exe (PID: 6792)
- Step 3 - Setup_Install.exe (PID: 4644)
- msiexec.exe (PID: 1640)
- msiexec.exe (PID: 6988)
- WindowsService.exe (PID: 5112)
Checks supported languages
- msiexec.exe (PID: 1640)
- msiexec.exe (PID: 6928)
- msiexec.exe (PID: 6792)
- Step 3 - Setup_Install.exe (PID: 4644)
- msiexec.exe (PID: 6988)
- WindowsService.exe (PID: 5112)
Reads Environment values
- msiexec.exe (PID: 6928)
- msiexec.exe (PID: 6792)
- Step 3 - Setup_Install.exe (PID: 4644)
- msiexec.exe (PID: 6988)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1640)
Reads the software policy settings
- powershell.exe (PID: 6824)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6824)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6824)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6824)
Checks proxy server information
- WindowsService.exe (PID: 5112)
Creates files in the program directory
- cmd.exe (PID: 6576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:11:15 13:33:00+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.37 |
| CodeSize: | 2604032 |
| InitializedDataSize: | 1423360 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f0aa6 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Getintopc.com |
| FileDescription: | EXE - Step 3 - Setup_Install Installer |
| FileVersion: | 1.0.0 |
| InternalName: | Step 3 - Setup_Install |
| LegalCopyright: | Copyright (C) 2024 Getintopc.com |
| OriginalFileName: | Step 3 - Setup_Install.exe |
| ProductName: | EXE - Step 3 - Setup_Install |
| ProductVersion: | 1.0.0 |
Total processes
140
Monitored processes
12
Malicious processes
4
Suspicious processes
3
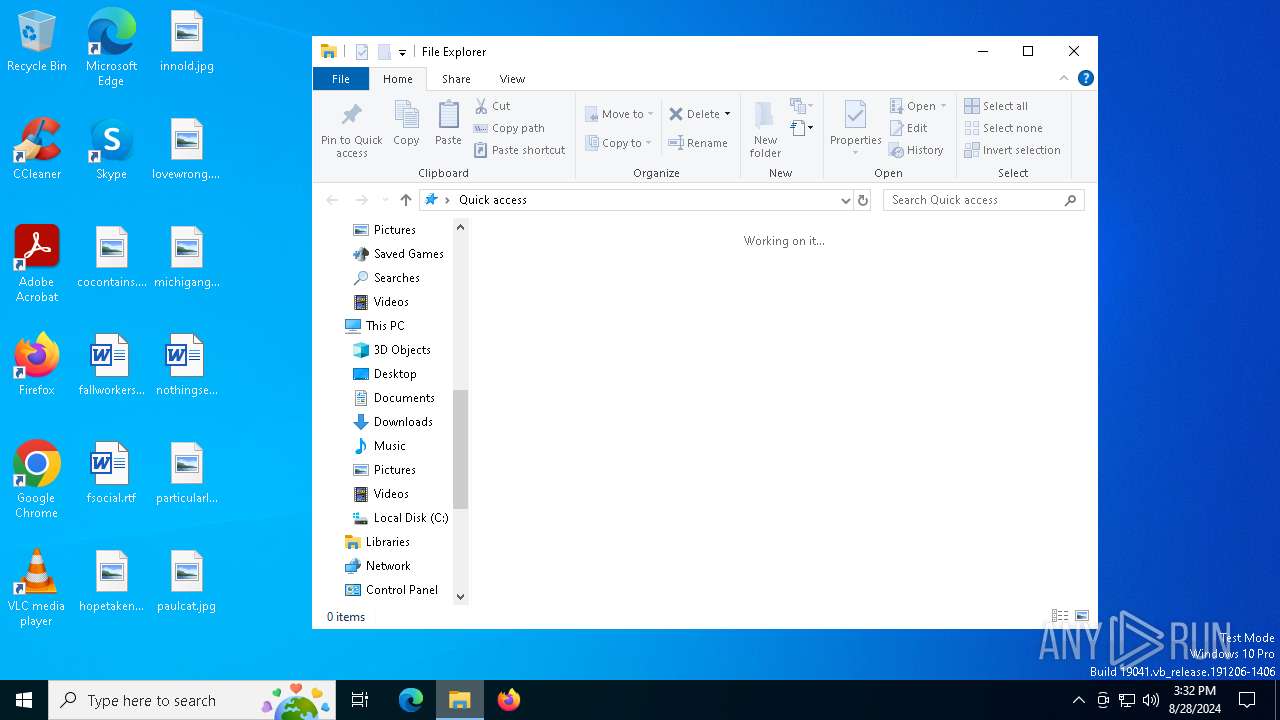
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 488 | "C:\Users\admin\AppData\Local\Temp\Step 3 - Setup_Install.exe" | C:\Users\admin\AppData\Local\Temp\Step 3 - Setup_Install.exe | — | explorer.exe | |||||||||||
User: admin Company: Getintopc.com Integrity Level: MEDIUM Description: EXE - Step 3 - Setup_Install Installer Exit code: 3221226540 Version: 1.0.0 Modules
| |||||||||||||||
| 1640 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WindowsService.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | "C:\WINDOWS\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Getintopc.com\EXE - Step 3 - Setup_Install 1.0.0\install\A9F990C\GetintoPC-Top-EXE.msi" /quiet /qn AI_SETUPEXEPATH="C:\Users\admin\AppData\Local\Temp\Step 3 - Setup_Install.exe" SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1724857685 " AI_EUIMSI="" | C:\Windows\SysWOW64\msiexec.exe | — | Step 3 - Setup_Install.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4644 | "C:\Users\admin\AppData\Local\Temp\Step 3 - Setup_Install.exe" | C:\Users\admin\AppData\Local\Temp\Step 3 - Setup_Install.exe | explorer.exe | ||||||||||||
User: admin Company: Getintopc.com Integrity Level: HIGH Description: EXE - Step 3 - Setup_Install Installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 5112 | "C:\Users\admin\AppData\Local\Updates\WindowsService.exe" | C:\Users\admin\AppData\Local\Updates\WindowsService.exe | msiexec.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6576 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | WindowsService.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6792 | C:\Windows\syswow64\MsiExec.exe -Embedding 9836F6AD7089894B1C794A2572322212 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6824 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\WINDOWS\SystemTemp\pssAFC3.ps1" -propFile "C:\WINDOWS\SystemTemp\msiAFC0.txt" -scriptFile "C:\WINDOWS\SystemTemp\scrAFC1.ps1" -scriptArgsFile "C:\WINDOWS\SystemTemp\scrAFC2.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6840 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 560
Read events
10 517
Write events
31
Delete events
12
Modification events
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 680600001330D3ED5EF9DA01 | |||
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: CFA38E4442346344ABF72E2D56E73BC647AB2D2CDEF734534B4EBA18B829BAA3 | |||
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (6792) msiexec.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings |
| Operation: | write | Name: | JITDebug |
Value: 0 | |||
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\12ab3e.rbs |
Value: 31127902 | |||
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\12ab3e.rbsLow |
Value: | |||
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\2AEC9905082166A41AE800A133AA11EE |
| Operation: | write | Name: | BF8B869D6524AE643A392D53AEF999C0 |
Value: C:\Program Files (x86)\Getintopc.com\EXE - Step 3 - Setup_Install\ | |||
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\B0D81A4A3166692499415EA8808C2636 |
| Operation: | write | Name: | BF8B869D6524AE643A392D53AEF999C0 |
Value: 02:\Software\Getintopc.com\EXE - Step 3 - Setup_Install\Version | |||
| (PID) Process: | (1640) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\ACBF36D1F3800964284AF8DF83CE4E9A |
| Operation: | write | Name: | BF8B869D6524AE643A392D53AEF999C0 |
Value: C:\Users\admin\AppData\Local\Updates\WindowsService.exe | |||
Executable files
17
Suspicious files
19
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4644 | Step 3 - Setup_Install.exe | C:\Users\admin\AppData\Roaming\Getintopc.com\EXE - Step 3 - Setup_Install 1.0.0\install\A9F990C\GetintoPC-Top-EXE.msi | executable | |
MD5:412AB643D36494C1BEE50FA456BB7E72 | SHA256:BD0D85EE49DFE1715698BB723F8B451E8A3E95CE8B2191C9D56227F593665218 | |||
| 6988 | msiexec.exe | C:\Windows\SystemTemp\msiAFC0.txt | — | |
MD5:— | SHA256:— | |||
| 6988 | msiexec.exe | C:\Windows\SystemTemp\scrAFC1.ps1 | — | |
MD5:— | SHA256:— | |||
| 6988 | msiexec.exe | C:\Windows\SystemTemp\scrAFC2.txt | — | |
MD5:— | SHA256:— | |||
| 6988 | msiexec.exe | C:\Windows\SystemTemp\pssAFC3.ps1 | — | |
MD5:— | SHA256:— | |||
| 4644 | Step 3 - Setup_Install.exe | C:\Users\admin\AppData\Local\Temp\MSIA9C6.tmp | executable | |
MD5:5A1F2196056C0A06B79A77AE981C7761 | SHA256:52F41817669AF7AC55B1516894EE705245C3148F2997FA0E6617E9CC6353E41E | |||
| 4644 | Step 3 - Setup_Install.exe | C:\Users\admin\AppData\Local\Temp\MSIAA92.tmp | executable | |
MD5:5A1F2196056C0A06B79A77AE981C7761 | SHA256:52F41817669AF7AC55B1516894EE705245C3148F2997FA0E6617E9CC6353E41E | |||
| 1640 | msiexec.exe | C:\Windows\Installer\MSIABD8.tmp | executable | |
MD5:5A1F2196056C0A06B79A77AE981C7761 | SHA256:52F41817669AF7AC55B1516894EE705245C3148F2997FA0E6617E9CC6353E41E | |||
| 4644 | Step 3 - Setup_Install.exe | C:\Users\admin\AppData\Local\Temp\MSIAAB2.tmp | executable | |
MD5:5A1F2196056C0A06B79A77AE981C7761 | SHA256:52F41817669AF7AC55B1516894EE705245C3148F2997FA0E6617E9CC6353E41E | |||
| 4644 | Step 3 - Setup_Install.exe | C:\Users\admin\AppData\Roaming\Getintopc.com\EXE - Step 3 - Setup_Install 1.0.0\install\holder0.aiph | binary | |
MD5:CFE6990A2F2B0B5EC97664C0C1254941 | SHA256:7A969B59C111DD71554D970CB44E87EABB8E30EF0A651882EC92AF7DE5070D21 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
36
DNS requests
19
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1780 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6440 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2208 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2208 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5112 | WindowsService.exe | GET | 200 | 188.138.125.61:83 | http://www.google.com.q9unkmhgvoatwzfs.fast-dns-host.com:83/md5_GIP.txt | unknown | — | — | unknown |
5112 | WindowsService.exe | GET | 200 | 188.138.125.57:83 | http://www.google.com.h04a536yqvsm2dgu.fast-dns-host.com:83/Resource_GIP.bin | unknown | — | — | unknown |
5112 | WindowsService.exe | GET | 200 | 188.138.125.61:83 | http://www.google.com.q9unkmhgvoatwzfs.fast-dns-host.com:83/md5_GIP.txt | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6880 | svchost.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6552 | RUXIMICS.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4324 | svchost.exe | 20.72.205.209:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1780 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1780 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com.tgme3ohcnbyxjpia.fast-dns-host.com |
| unknown |
www.google.com.q9unkmhgvoatwzfs.fast-dns-host.com |
| unknown |
www.google.com.h04a536yqvsm2dgu.fast-dns-host.com |
| unknown |
www.google.com.backend-aplha.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6576 | cmd.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
6576 | cmd.exe | Potential Corporate Privacy Violation | ET POLICY Cryptocurrency Miner Checkin |
1 ETPRO signatures available at the full report