| File name: | 3836110e0db89062a3b5a1200606e8d3d20485aa9f95ea46fda3c29433ae159a.doc |
| Full analysis: | https://app.any.run/tasks/a1e220a4-8c6c-4b15-881d-afa1ebc319e1 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 19, 2019, 01:41:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 12C0F92CA2BE142A1364705F6AA5CC78 |
| SHA1: | CEA51953E3DA71C3CB2922036139BAFA1A3A2498 |
| SHA256: | 3836110E0DB89062A3B5A1200606E8D3D20485AA9F95EA46FDA3C29433AE159A |
| SSDEEP: | 1536:toeSqQBxLRZMOZ5H4mV9P0yQKFTVk25uO5c:SeS1Bx3Mev9P5Qw95K |
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3236)
Application was dropped or rewritten from another process
- vbc.exe (PID: 3048)
- vbc.exe (PID: 2120)
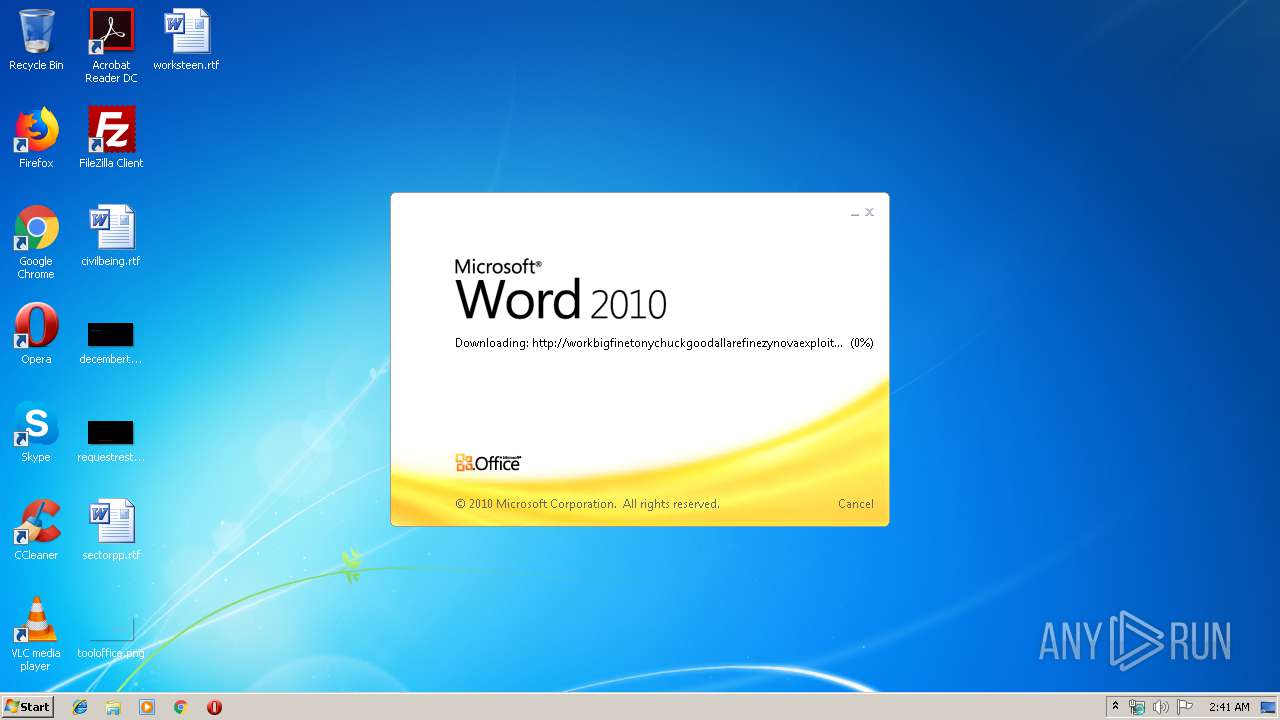
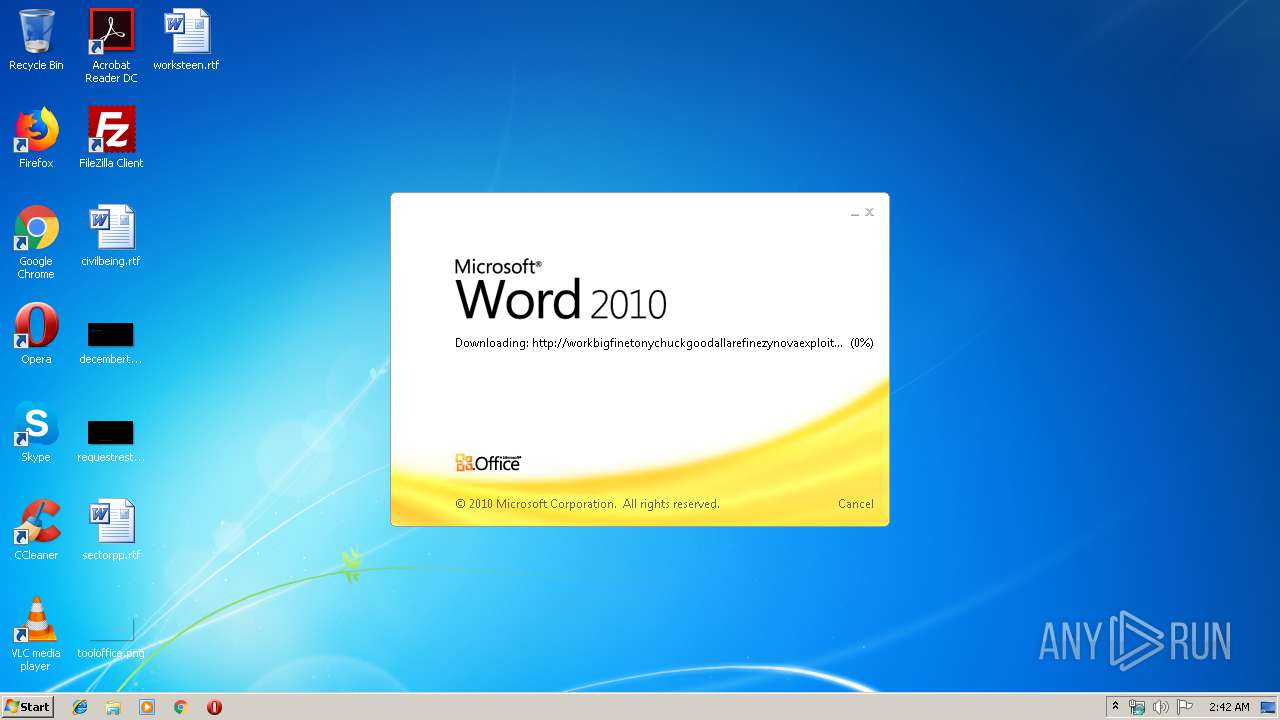
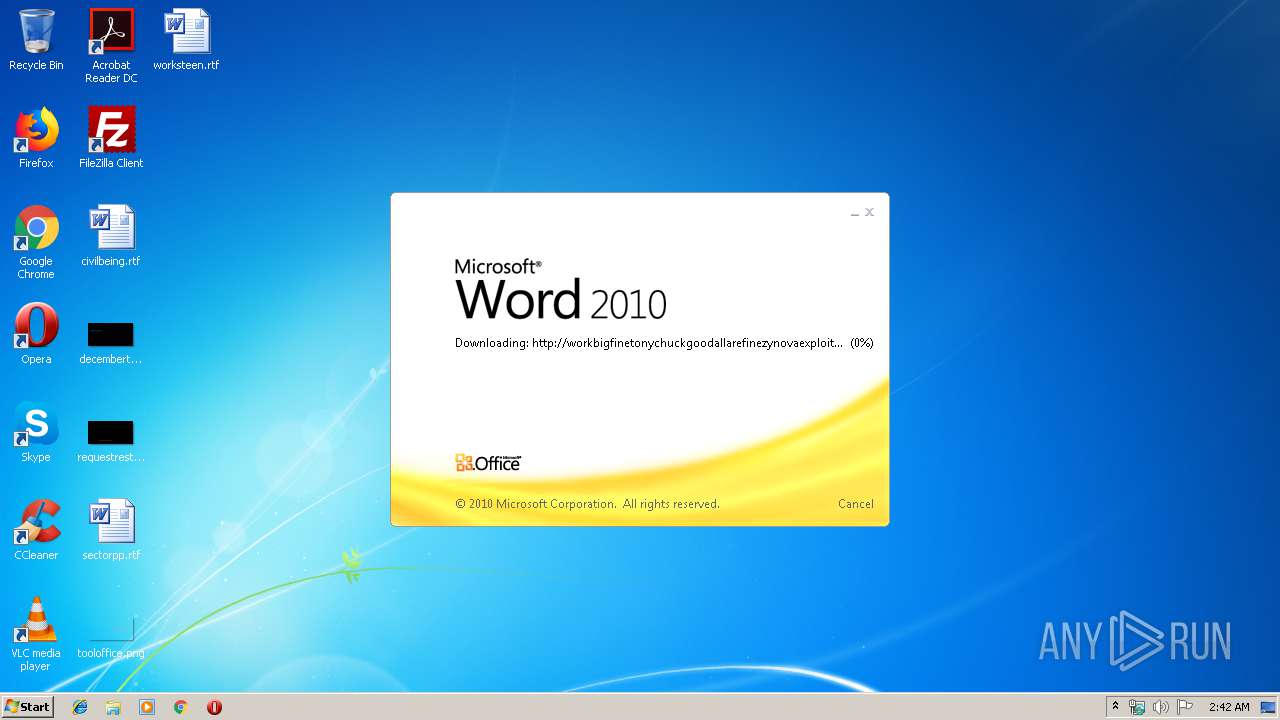
Downloads executable files from the Internet
- EQNEDT32.EXE (PID: 3236)
Downloads executable files from IP
- EQNEDT32.EXE (PID: 3236)
Changes the autorun value in the registry
- vbc.exe (PID: 2120)
Disables Windows System Restore
- vbc.exe (PID: 2120)
AGENTTESLA was detected
- vbc.exe (PID: 2120)
Actions looks like stealing of personal data
- vbc.exe (PID: 2120)
Changes settings of System certificates
- vbc.exe (PID: 2120)
SUSPICIOUS
Creates files in the user directory
- EQNEDT32.EXE (PID: 3236)
- vbc.exe (PID: 2120)
Executed via COM
- EQNEDT32.EXE (PID: 3236)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3236)
- vbc.exe (PID: 2120)
Application launched itself
- vbc.exe (PID: 3048)
Uses REG.EXE to modify Windows registry
- vbc.exe (PID: 2120)
Checks for external IP
- vbc.exe (PID: 2120)
Adds / modifies Windows certificates
- vbc.exe (PID: 2120)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3484)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3484)
Dropped object may contain Bitcoin addresses
- EQNEDT32.EXE (PID: 3236)
- vbc.exe (PID: 2120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xa6b173a8 |
| ZipCompressedSize: | 452 |
| ZipUncompressedSize: | 2448 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 12 |
| LastModifiedBy: | whiteDevil |
| RevisionNumber: | 1 |
| CreateDate: | 2019:09:18 11:05:00Z |
| ModifyDate: | 2019:09:18 11:06:00Z |
XMP
| Creator: | whiteDevil |
|---|
Total processes
39
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1688 | REG add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableTaskMgr /t REG_DWORD /d 1 /f | C:\Windows\system32\REG.exe | — | vbc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2120 | "C:\Users\admin\AppData\Roaming\vbc.exe" | C:\Users\admin\AppData\Roaming\vbc.exe | vbc.exe | ||||||||||||
User: admin Company: malchijah8biraud6 Integrity Level: MEDIUM Exit code: 0 Version: 7.09.0003 Modules
| |||||||||||||||
| 3048 | "C:\Users\admin\AppData\Roaming\vbc.exe" | C:\Users\admin\AppData\Roaming\vbc.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: malchijah8biraud6 Integrity Level: MEDIUM Exit code: 0 Version: 7.09.0003 Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3484 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\3836110e0db89062a3b5a1200606e8d3d20485aa9f95ea46fda3c29433ae159a.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 771
Read events
1 351
Write events
407
Delete events
13
Modification events
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }:$ |
Value: 7D3A24009C0D0000010000000000000000000000 | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1328742430 | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742544 | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1328742545 | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 9C0D000074FD396A8B6ED50100000000 | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | v;$ |
Value: 763B24009C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | v;$ |
Value: 763B24009C0D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3484) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
24
Text files
6
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9ADD.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{8D807323-AF2E-4813-8BA2-31CAEAD8115B} | — | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{22C6C4E5-06D4-4B30-9692-5883A7BD1E2C} | — | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E45F1D99.doc | — | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\29FEEC0F.doc | — | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$36110e0db89062a3b5a1200606e8d3d20485aa9f95ea46fda3c29433ae159a.doc | pgc | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\......................................................doc.url | text | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\0................................................................0 on workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com.url | text | |
MD5:— | SHA256:— | |||
| 3484 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\52809FF5.doc | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
18
DNS requests
5
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | WINWORD.EXE | OPTIONS | 200 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0/ | US | — | — | malicious |
3484 | WINWORD.EXE | HEAD | 200 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0/......................................................doc | US | — | — | malicious |
3484 | WINWORD.EXE | HEAD | 200 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0/......................................................doc | US | — | — | malicious |
3484 | WINWORD.EXE | GET | 304 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0/......................................................doc | US | — | — | malicious |
3484 | WINWORD.EXE | HEAD | 200 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0/......................................................doc | US | — | — | malicious |
3484 | WINWORD.EXE | HEAD | 200 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0/......................................................doc | US | — | — | malicious |
984 | svchost.exe | OPTIONS | 301 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0 | US | html | 506 b | malicious |
984 | svchost.exe | OPTIONS | 200 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0/ | US | html | 506 b | malicious |
984 | svchost.exe | PROPFIND | 301 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0 | US | html | 506 b | malicious |
984 | svchost.exe | PROPFIND | 405 | 23.249.165.218:80 | http://workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com/0................................................................0/ | US | xml | 1.01 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3484 | WINWORD.EXE | 23.249.165.218:80 | workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com | ColoCrossing | US | malicious |
3236 | EQNEDT32.EXE | 88.150.175.104:80 | — | iomart Cloud Services Limited. | GB | suspicious |
2120 | vbc.exe | 52.55.255.113:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
2120 | vbc.exe | 192.185.41.47:587 | mail.dormakeba.com | CyrusOne LLC | US | malicious |
984 | svchost.exe | 23.249.165.218:80 | workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com | ColoCrossing | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
workbigfinetonychuckgoodallarefinezynovaexploitgood.warzonedns.com |
| malicious |
dns.msftncsi.com |
| shared |
checkip.amazonaws.com |
| malicious |
mail.dormakeba.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3236 | EQNEDT32.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3236 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
3236 | EQNEDT32.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3236 | EQNEDT32.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
3236 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2120 | vbc.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2120 | vbc.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3 ETPRO signatures available at the full report