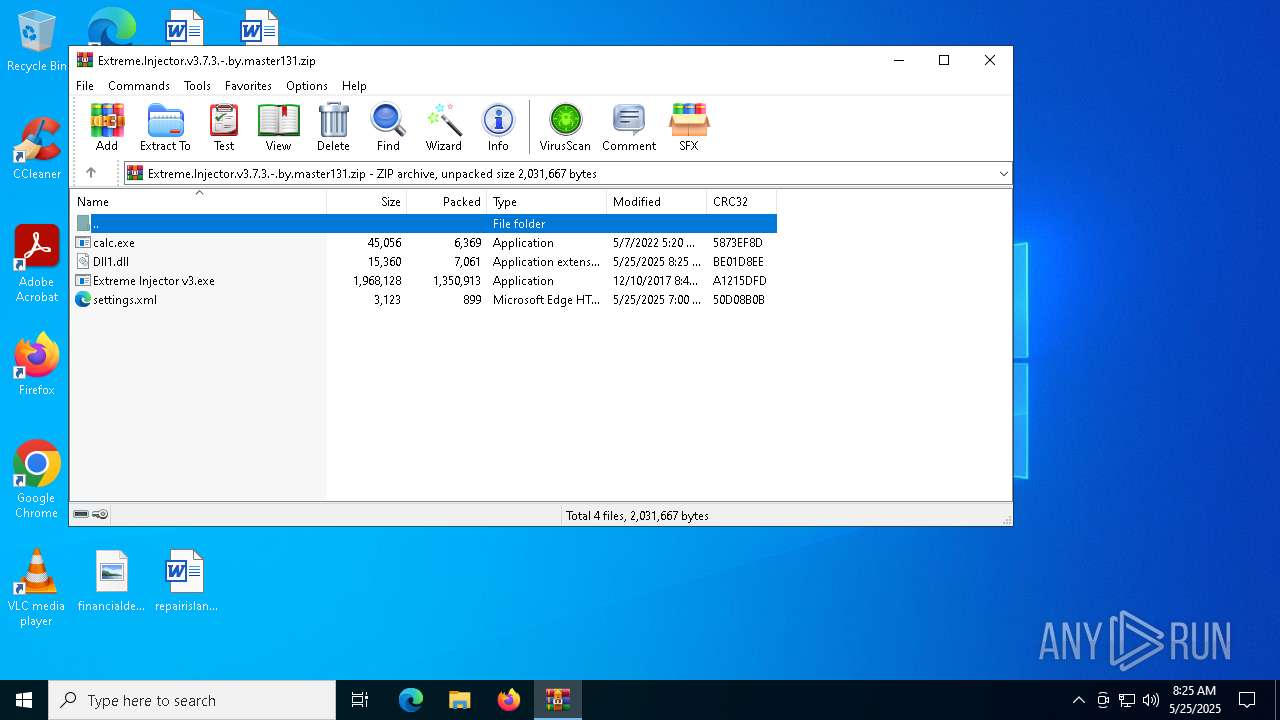
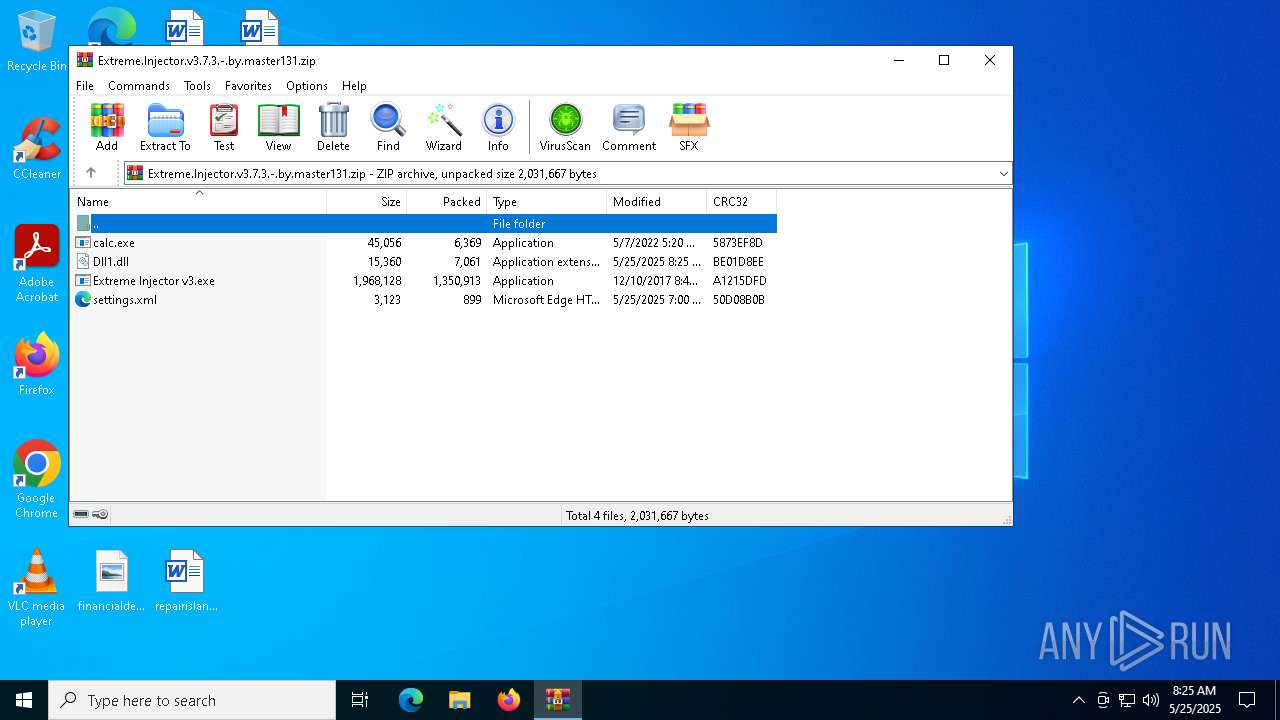
| File name: | Extreme.Injector.v3.7.3.-.by.master131.zip |
| Full analysis: | https://app.any.run/tasks/3b10f6ce-7190-4139-89a2-60640d3b0539 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 25, 2025, 08:25:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 820D6E121CC4268353AE943F6AB43D9F |
| SHA1: | E5F75C10FFAFE434F836D3BA81E65CF7A842B753 |
| SHA256: | 37E82CE37CAAB3B9BA357742779226058D4432087176A0EC80CE7AD49AD78F45 |
| SSDEEP: | 49152:hTeaeClT7d5OqHGI/cu4S7WsFlXif8brt3OZOQ0gTejhxzvAOYI6LammnsPnWneE:BZ5T7doqHVh4UFlSf8vtymj7jAFHF8eE |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7332)
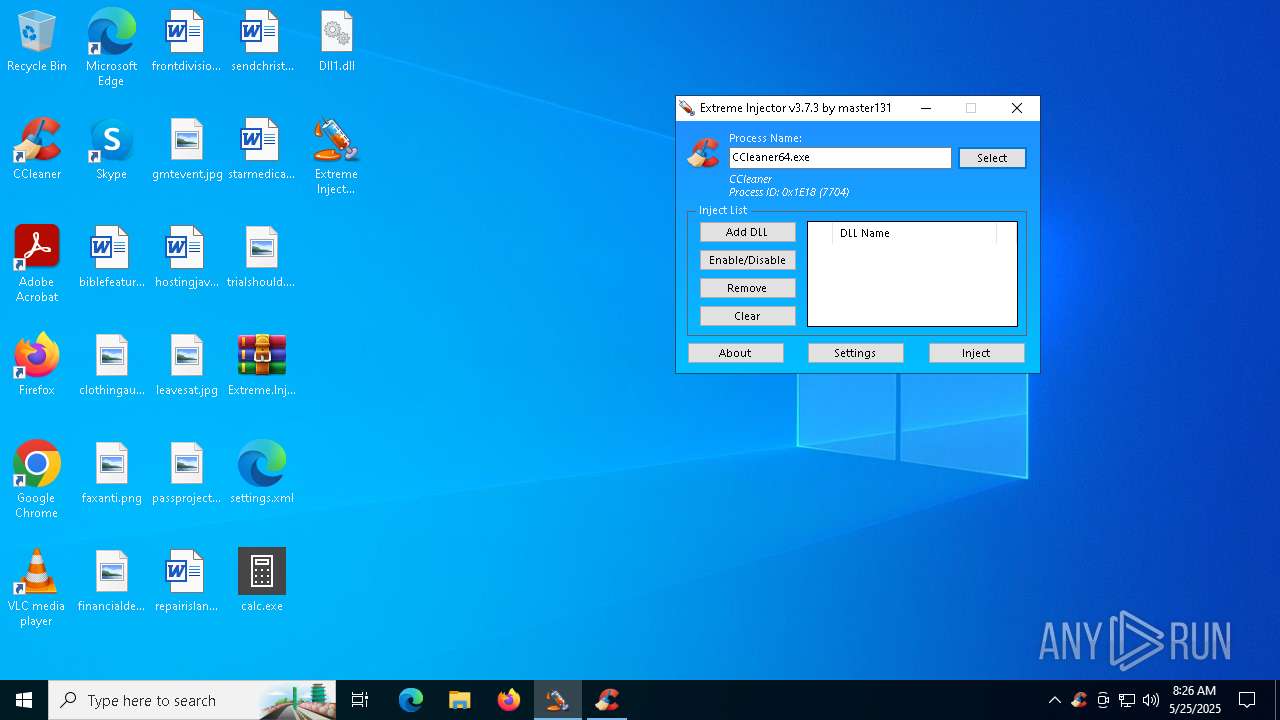
Changes the autorun value in the registry
- CCleaner64.exe (PID: 7948)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 4724)
Connects to the CnC server
- svchost.exe (PID: 2196)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 7332)
Reads security settings of Internet Explorer
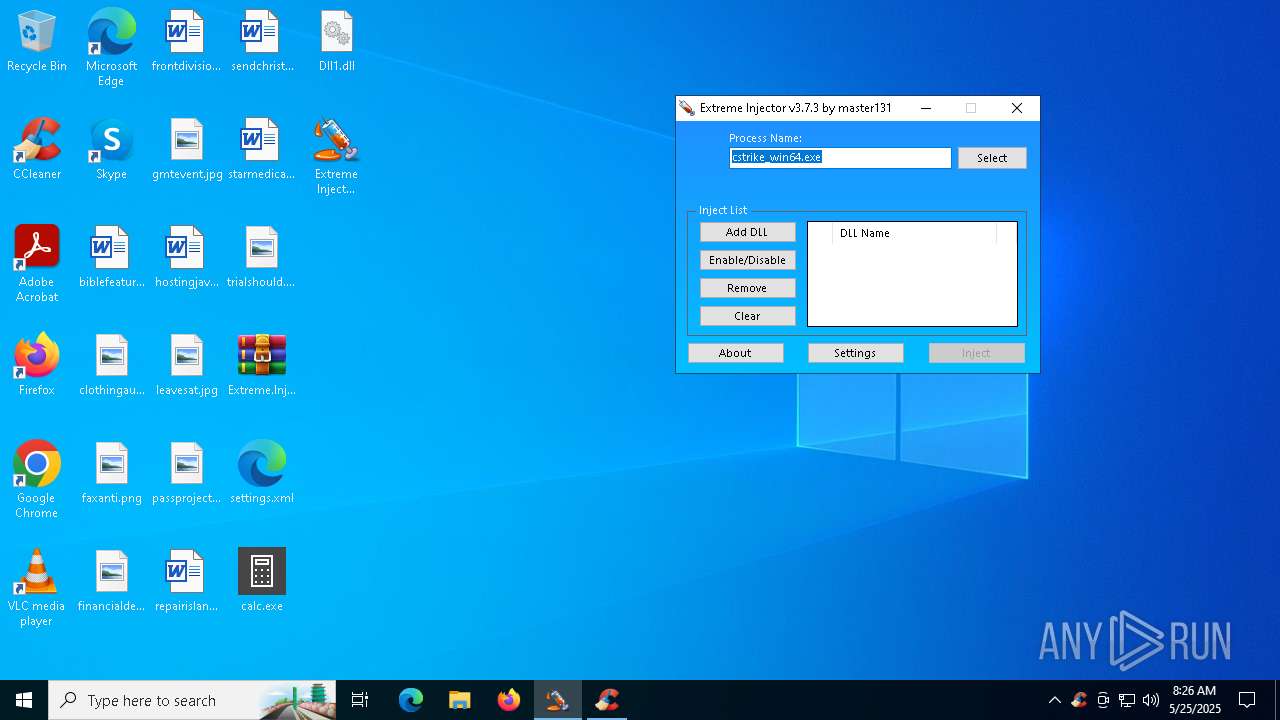
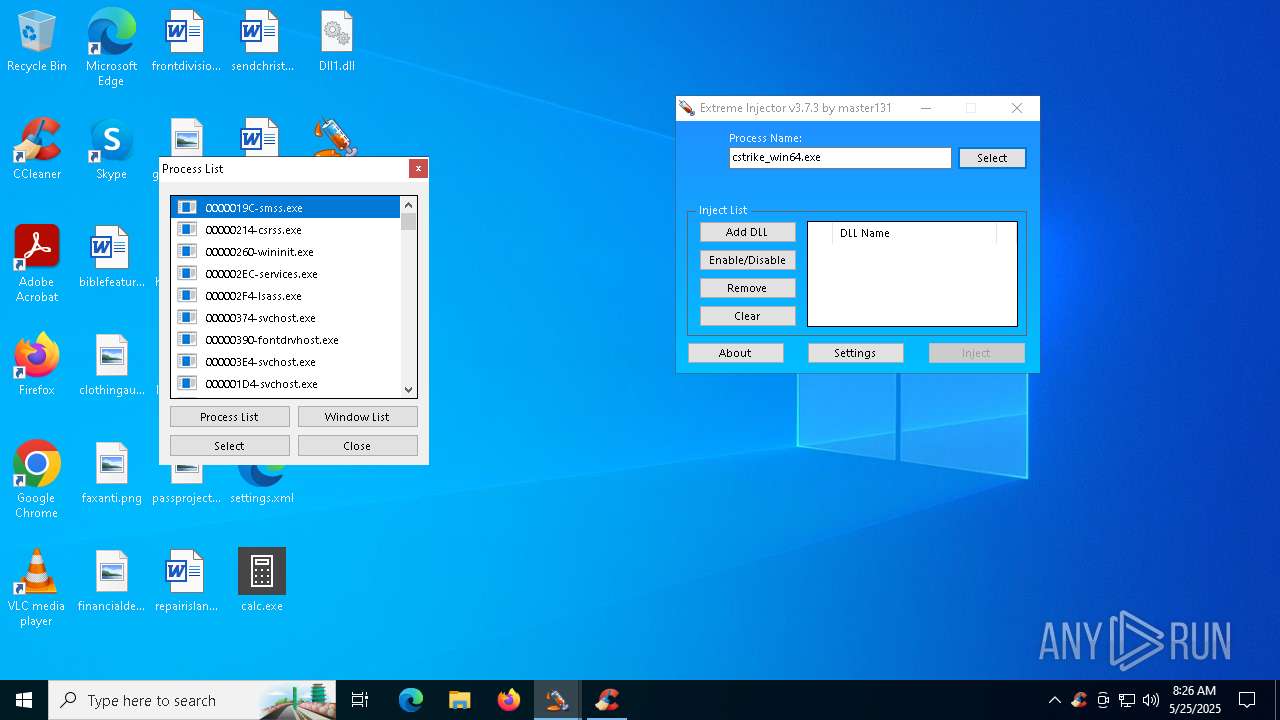
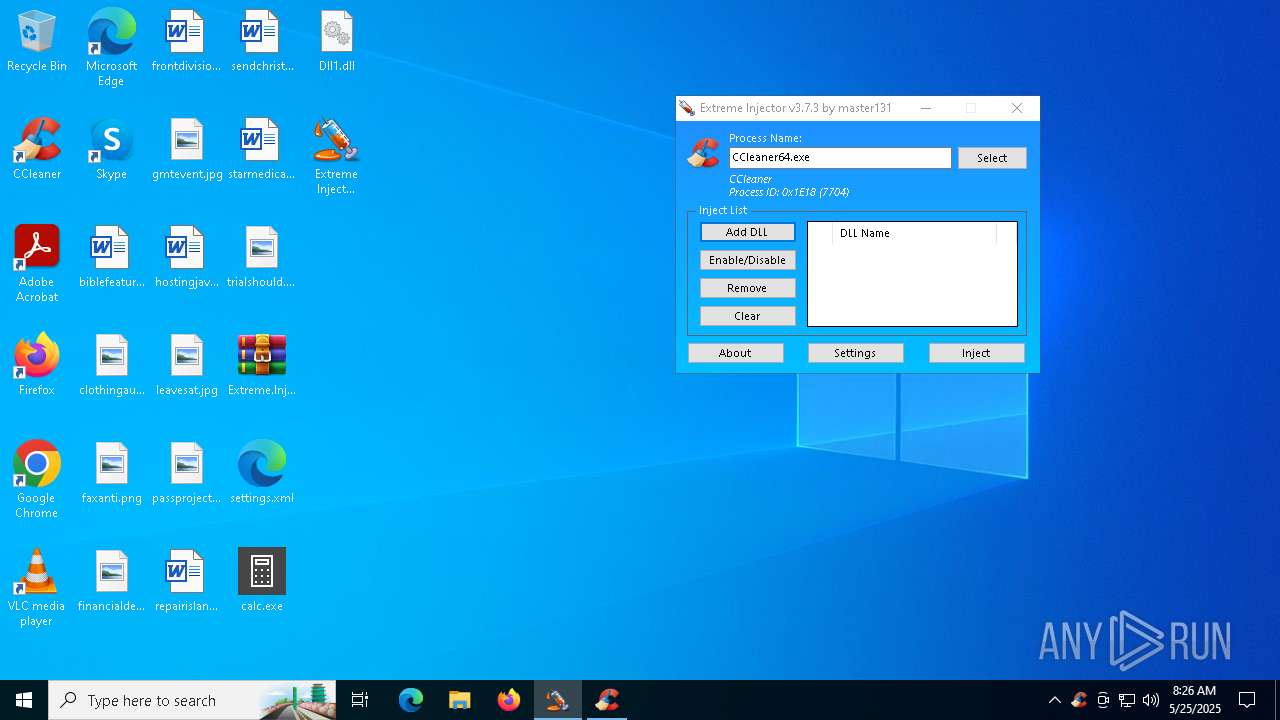
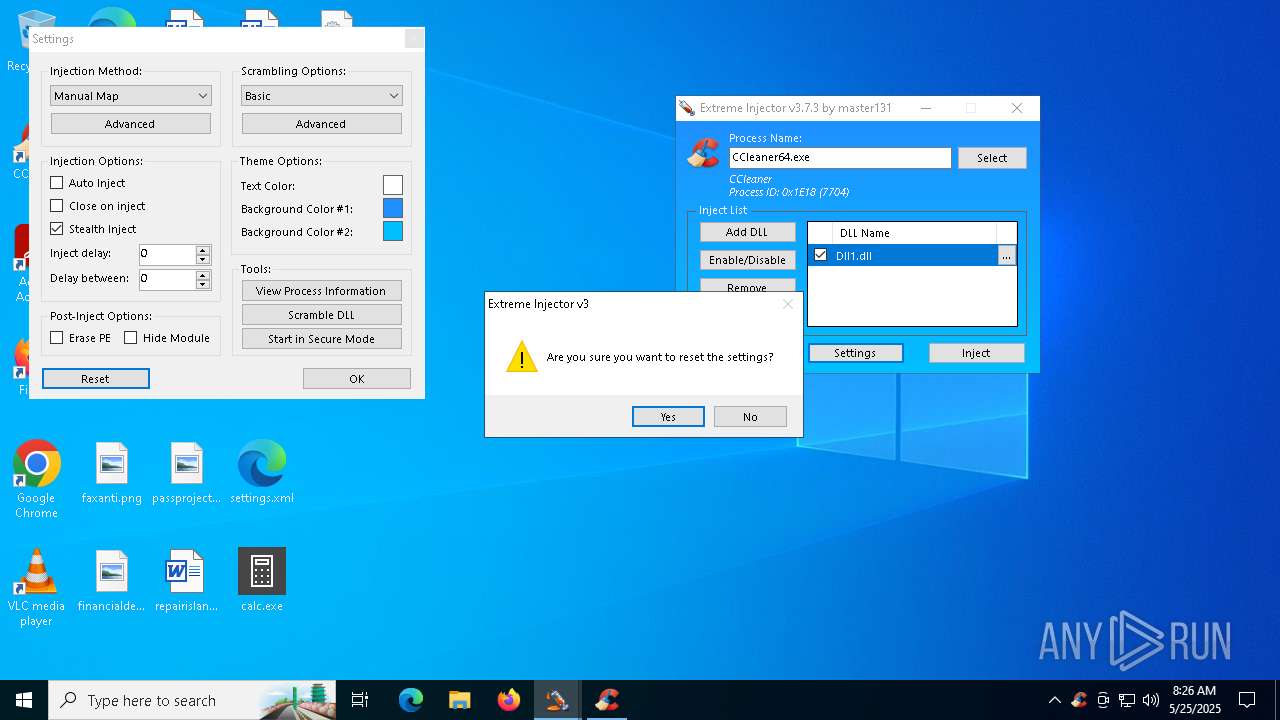
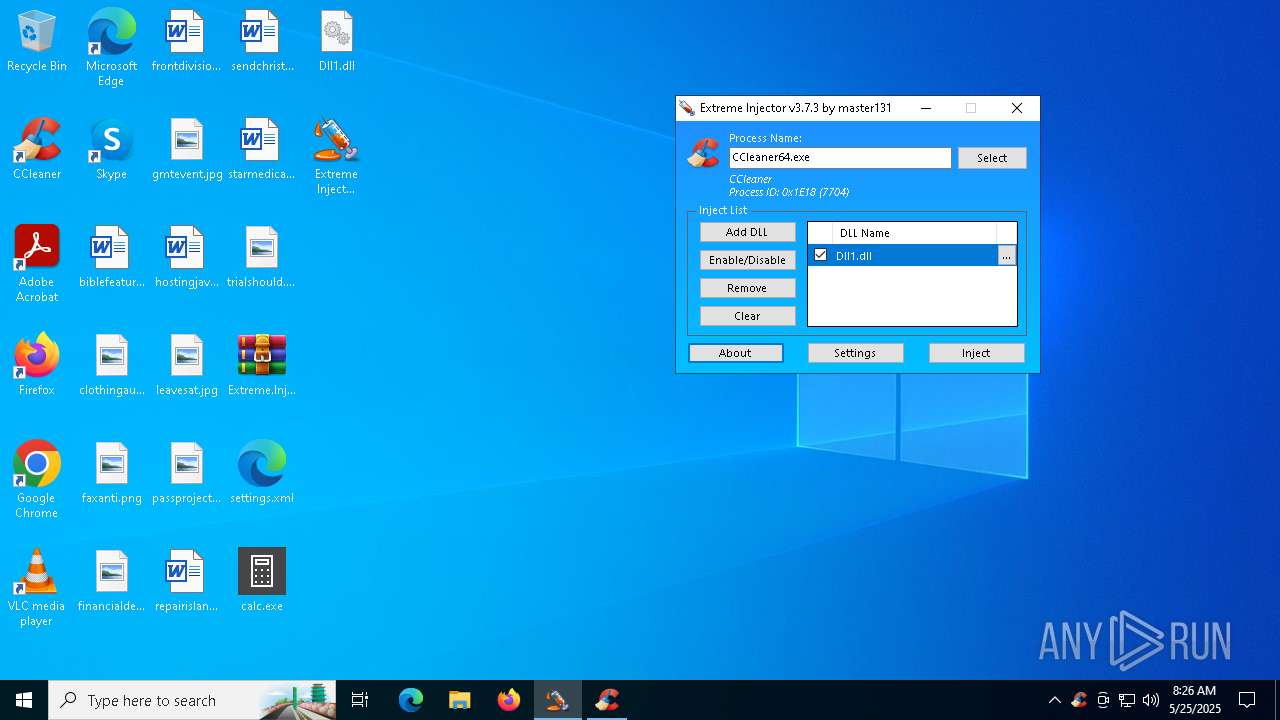
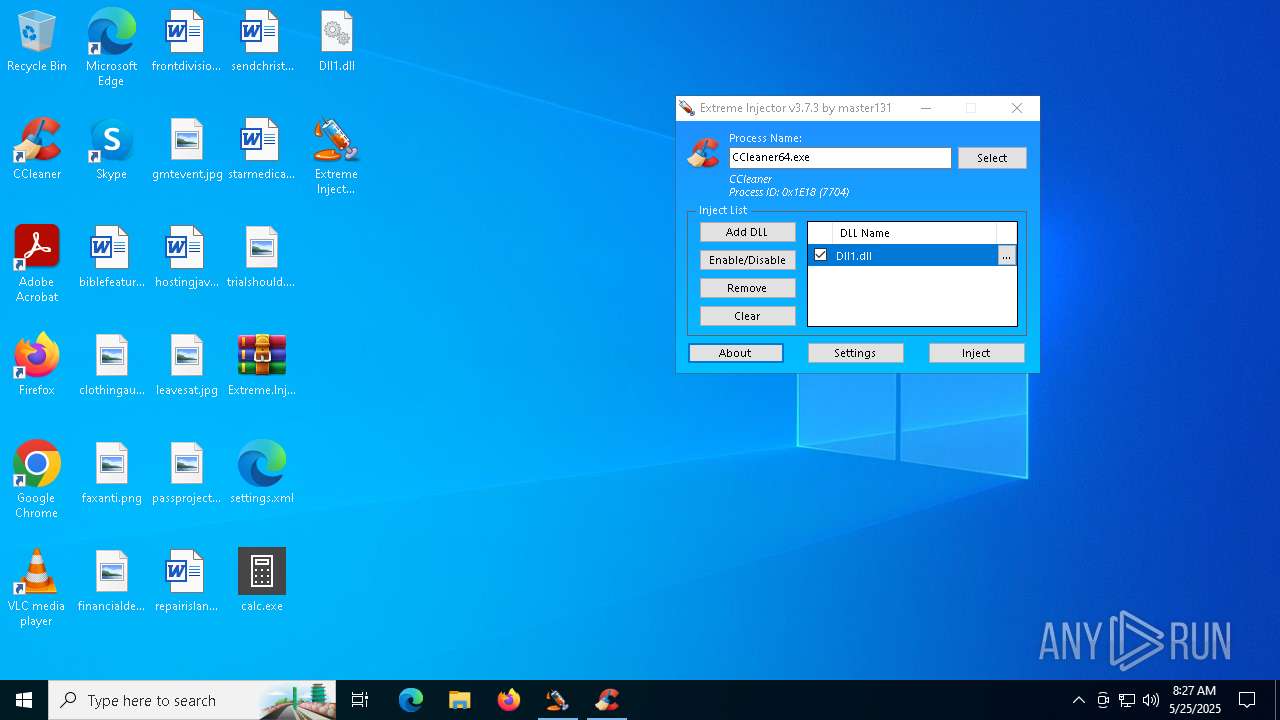
- Extreme Injector v3.exe (PID: 1452)
- CCleaner64.exe (PID: 7556)
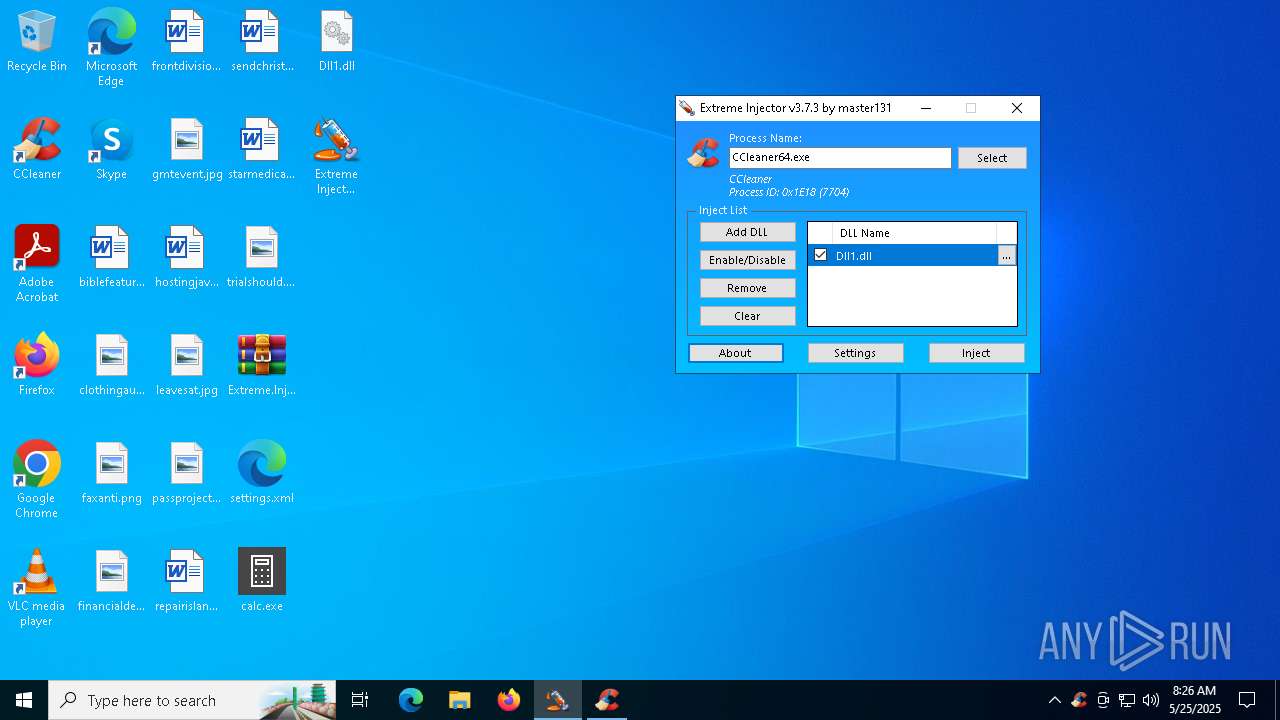
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
- Extreme Injector v3.exe (PID: 7244)
Reads the date of Windows installation
- Extreme Injector v3.exe (PID: 1452)
- CCleaner64.exe (PID: 7556)
- CCleaner64.exe (PID: 7704)
Application launched itself
- Extreme Injector v3.exe (PID: 1452)
- CCleaner64.exe (PID: 7556)
- CCleaner64.exe (PID: 7704)
Reads Internet Explorer settings
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
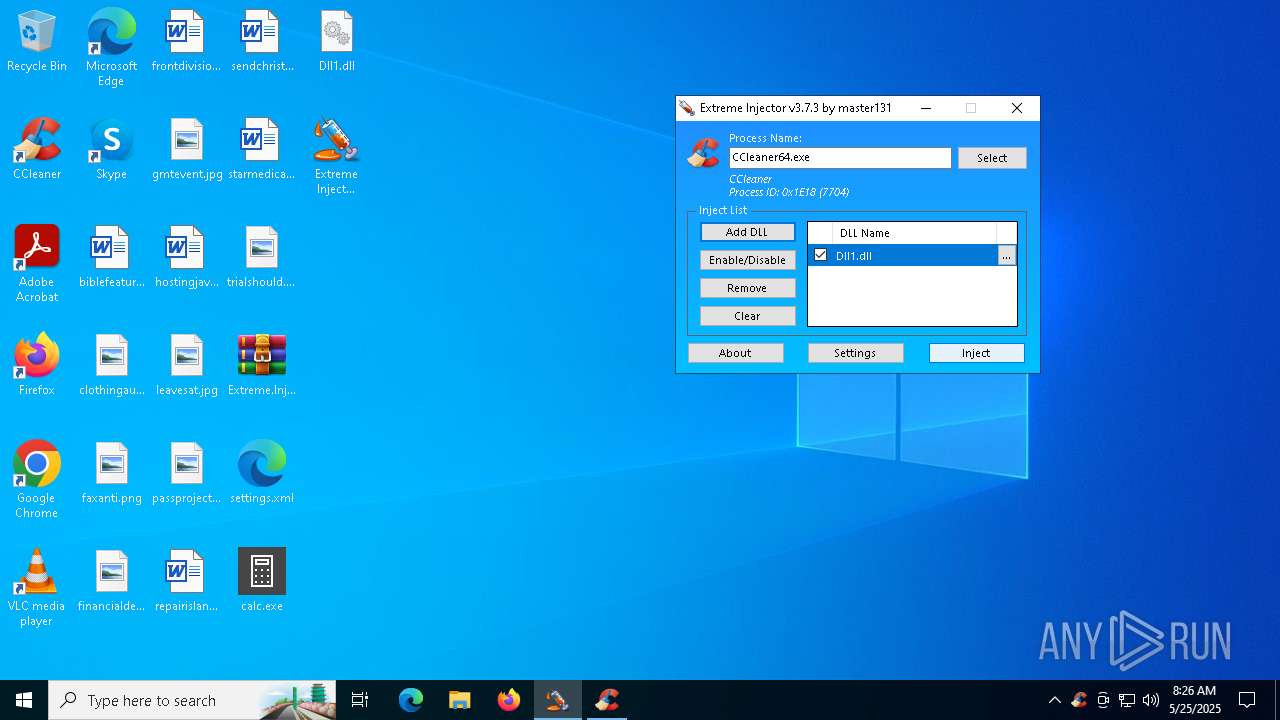
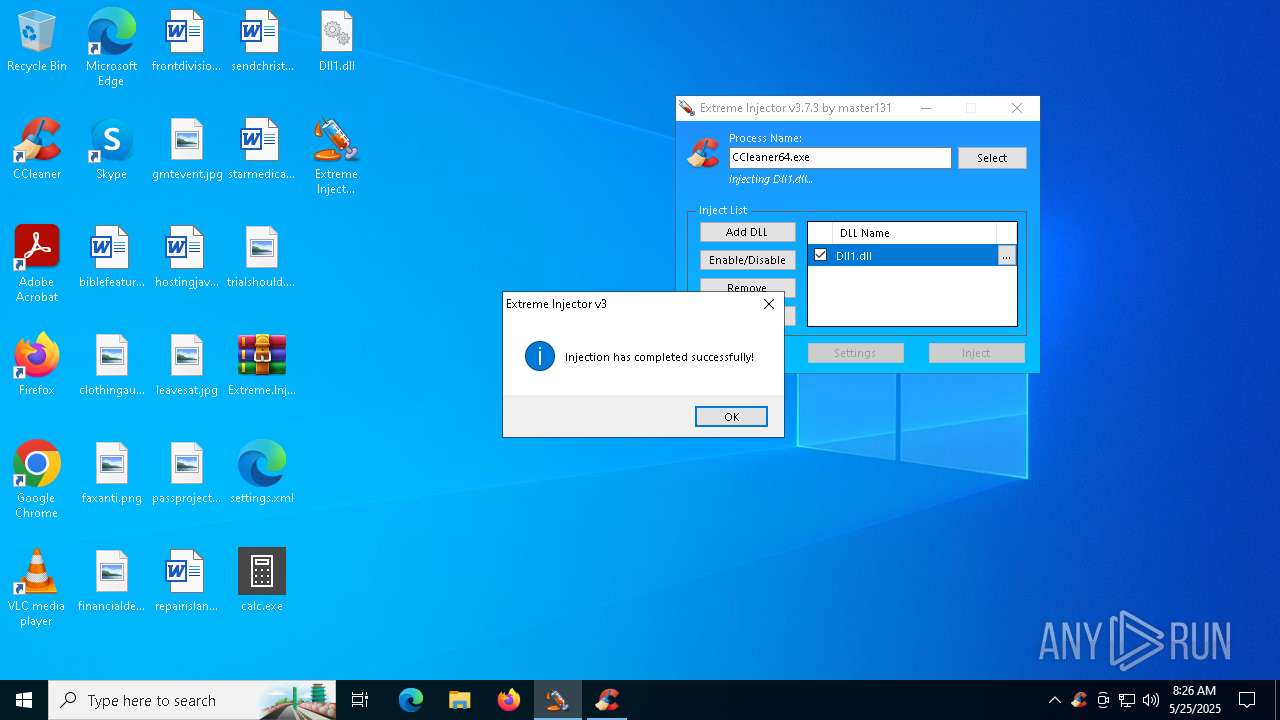
Executable content was dropped or overwritten
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Checks for external IP
- svchost.exe (PID: 2196)
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Searches for installed software
- CCleaner64.exe (PID: 7948)
- CCleaner64.exe (PID: 7704)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 4724)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 4724)
The process verifies whether the antivirus software is installed
- CCleaner64.exe (PID: 7948)
INFO
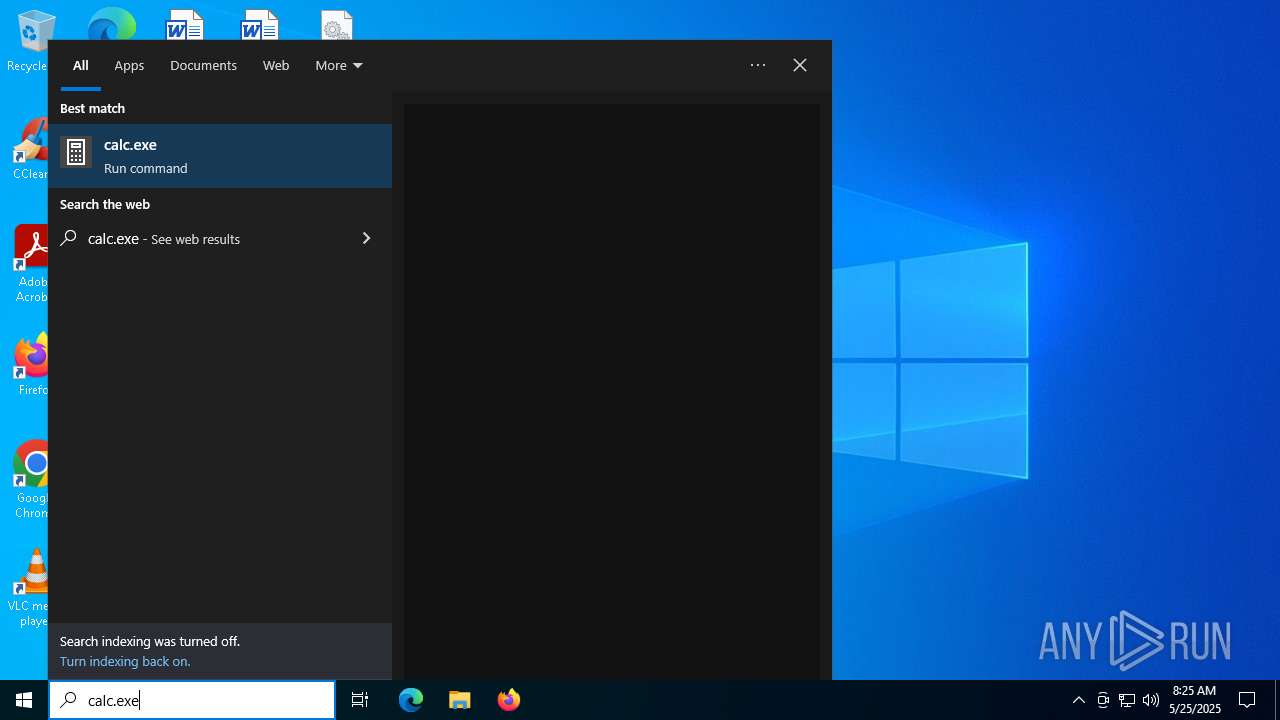
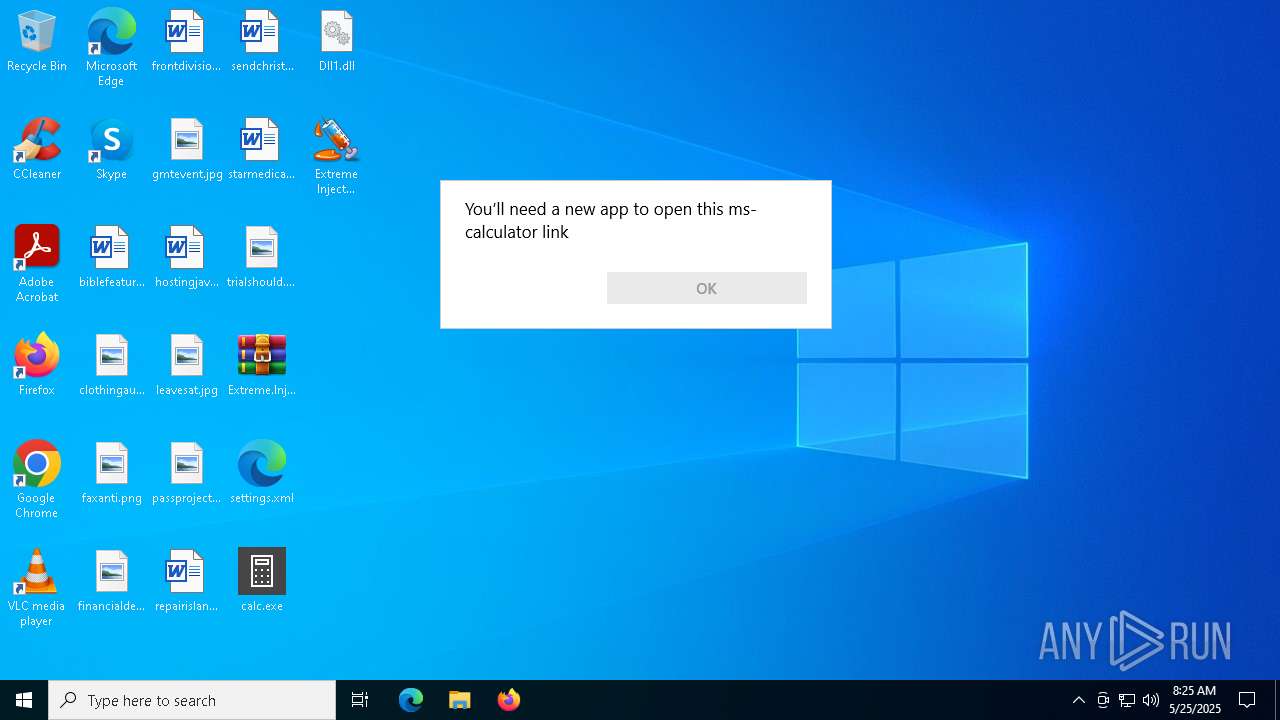
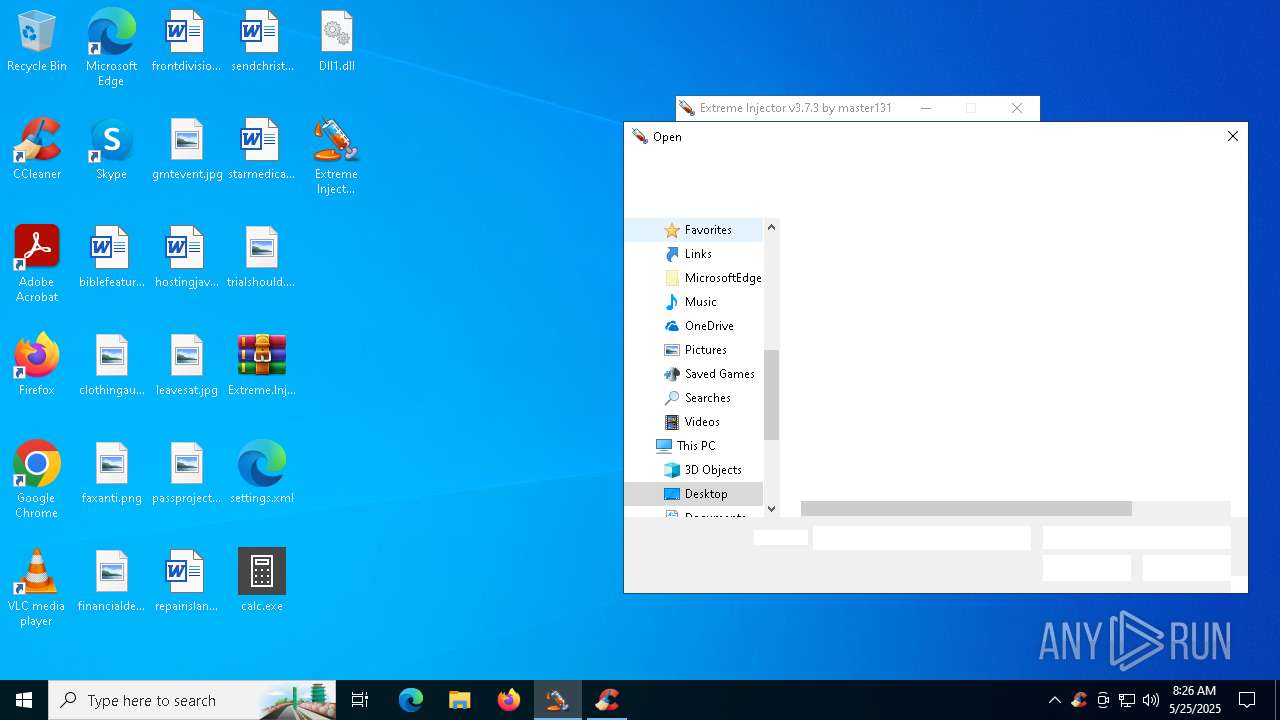
Manual execution by a user
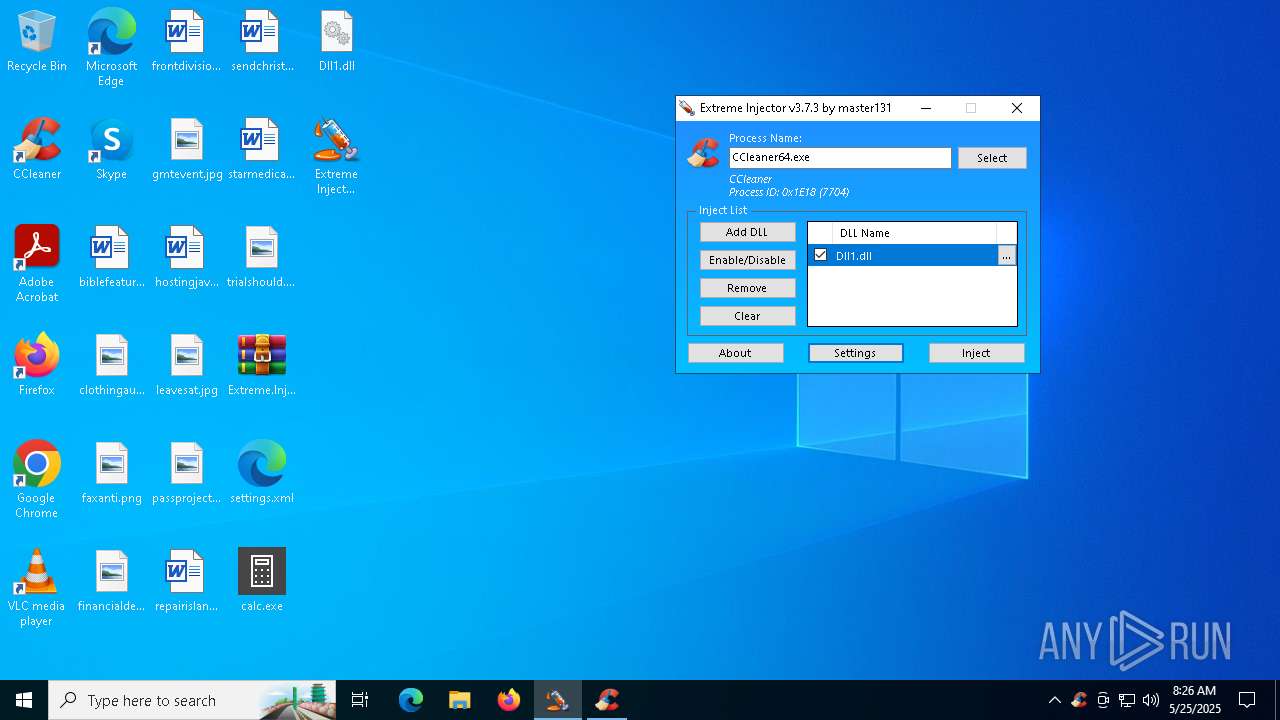
- Extreme Injector v3.exe (PID: 1452)
- CCleaner64.exe (PID: 7556)
Checks supported languages
- Extreme Injector v3.exe (PID: 1452)
- Extreme Injector v3.exe (PID: 7244)
- CCleaner64.exe (PID: 7556)
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7332)
The sample compiled with english language support
- WinRAR.exe (PID: 7332)
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 2140)
Reads the computer name
- Extreme Injector v3.exe (PID: 1452)
- Extreme Injector v3.exe (PID: 7244)
- CCleaner64.exe (PID: 7556)
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Reads the machine GUID from the registry
- Extreme Injector v3.exe (PID: 1452)
- Extreme Injector v3.exe (PID: 7244)
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Process checks computer location settings
- Extreme Injector v3.exe (PID: 1452)
- CCleaner64.exe (PID: 7556)
- CCleaner64.exe (PID: 7704)
Reads Environment values
- CCleaner64.exe (PID: 7556)
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Reads the software policy settings
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Reads CPU info
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Reads product name
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Creates files in the program directory
- CCleaner64.exe (PID: 7704)
- CCleaner64.exe (PID: 7948)
Creates files or folders in the user directory
- CCleaner64.exe (PID: 7704)
Checks proxy server information
- CCleaner64.exe (PID: 7948)
- CCleaner64.exe (PID: 7704)
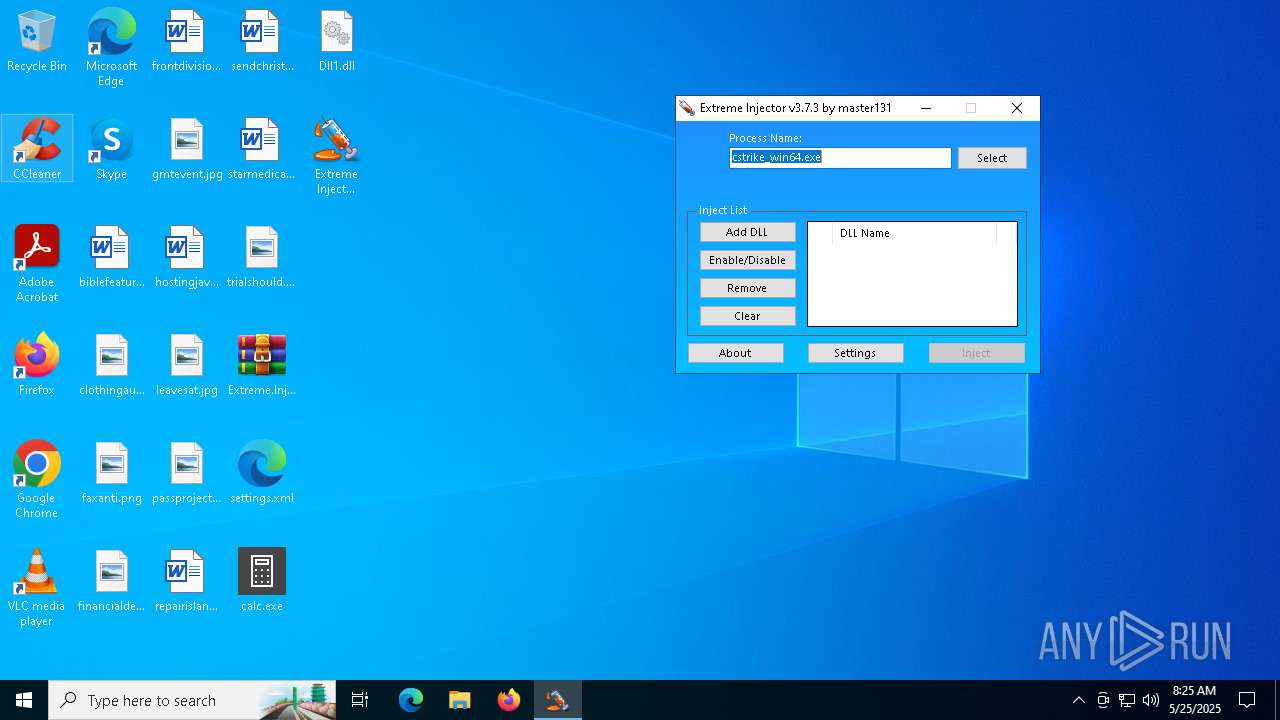
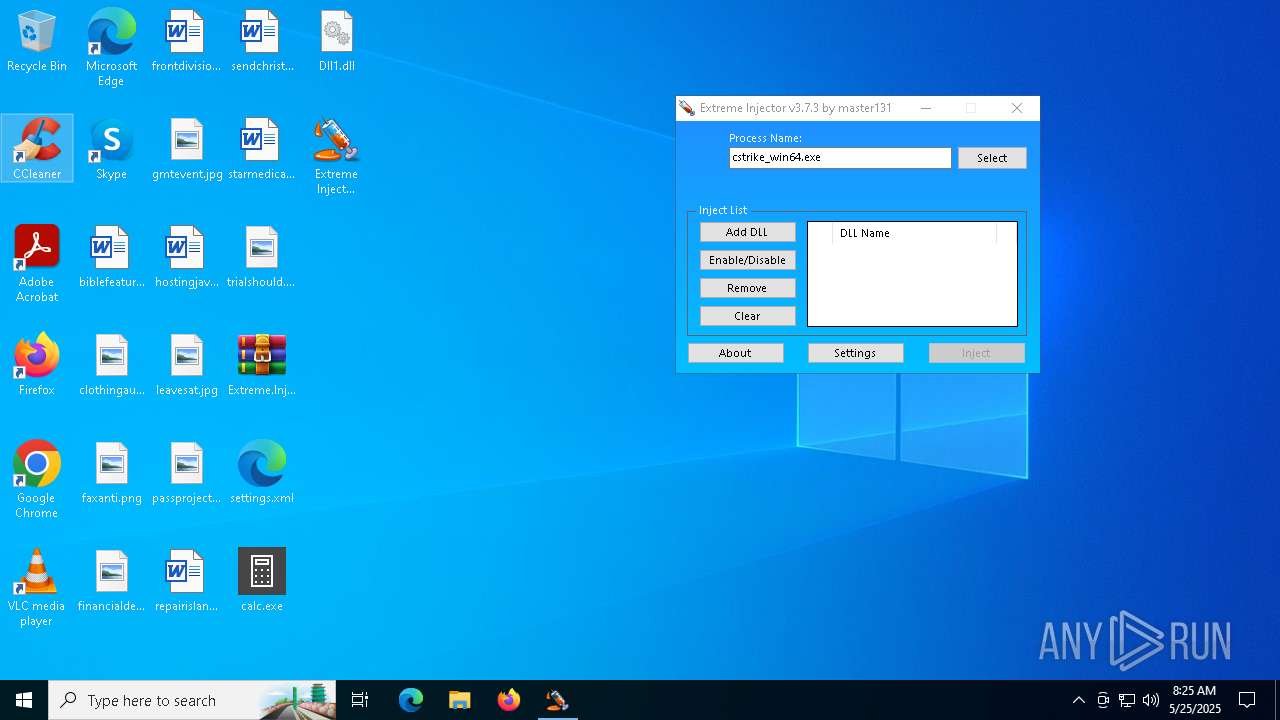
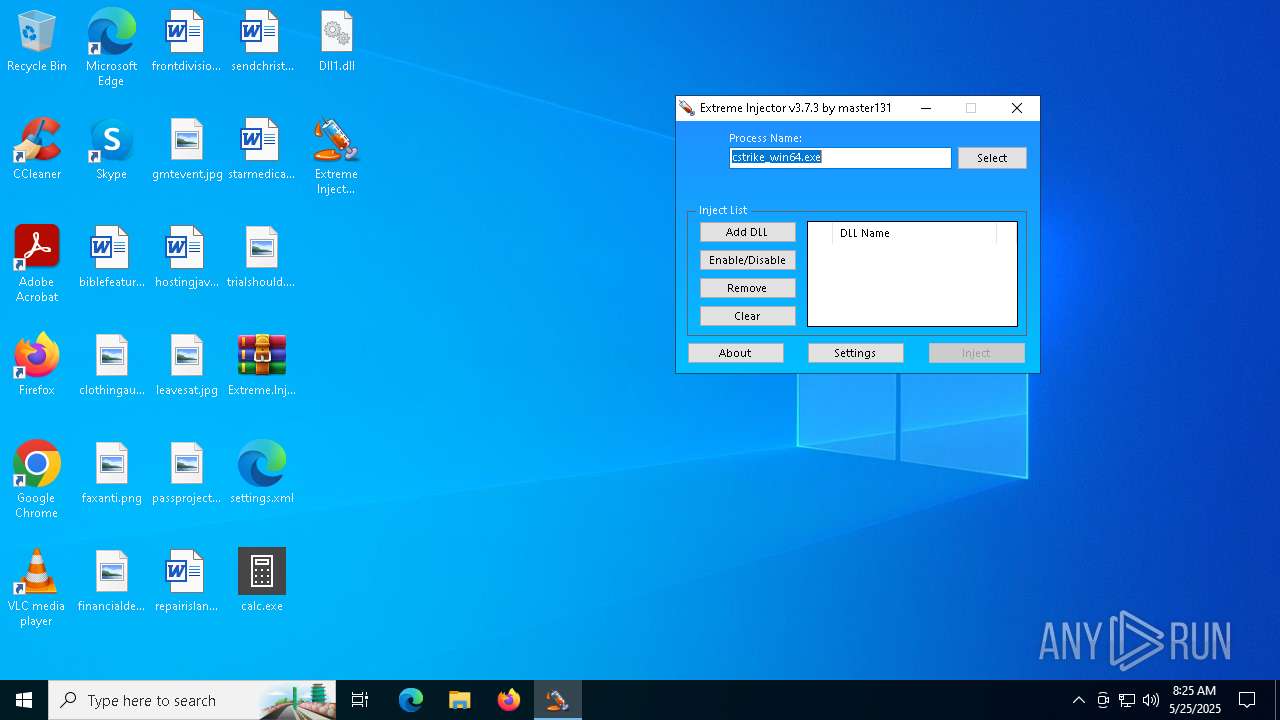
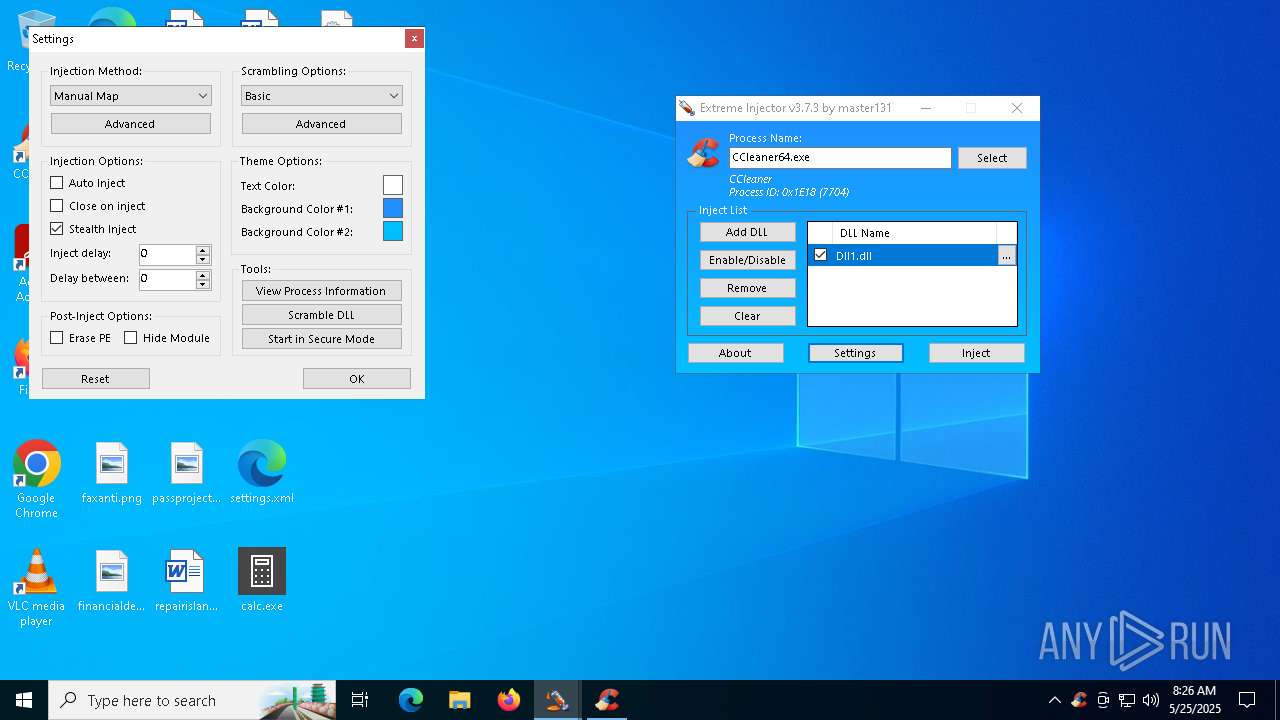
Potential library load (Base64 Encoded 'LoadLibrary')
- Extreme Injector v3.exe (PID: 7244)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- Extreme Injector v3.exe (PID: 7244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:25 09:00:42 |
| ZipCRC: | 0x50d08b0b |
| ZipCompressedSize: | 899 |
| ZipUncompressedSize: | 3123 |
| ZipFileName: | settings.xml |
Total processes
149
Monitored processes
14
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Users\admin\AppData\Local\Temp\loader.exe" | C:\Users\admin\AppData\Local\Temp\loader.exe | — | CCleaner64.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1452 | "C:\Users\admin\Desktop\Extreme Injector v3.exe" | C:\Users\admin\Desktop\Extreme Injector v3.exe | — | explorer.exe | |||||||||||
User: admin Company: master131 Integrity Level: MEDIUM Description: Extreme Injector Exit code: 0 Version: 3.7.3.0 Modules
| |||||||||||||||
| 2140 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | loader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5056 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7244 | "C:\Users\admin\Desktop\Extreme Injector v3.exe" | C:\Users\admin\Desktop\Extreme Injector v3.exe | Extreme Injector v3.exe | ||||||||||||
User: admin Company: master131 Integrity Level: HIGH Description: Extreme Injector Version: 3.7.3.0 Modules
| |||||||||||||||
| 7260 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
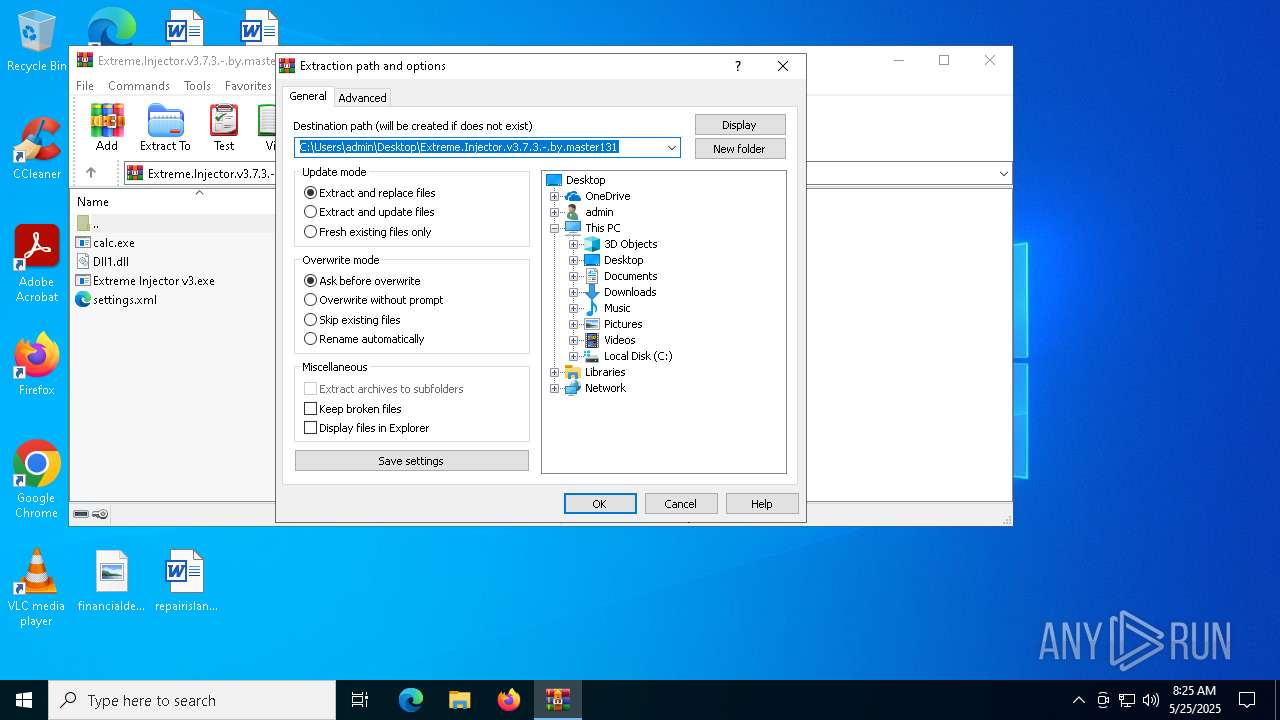
| 7332 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Extreme.Injector.v3.7.3.-.by.master131.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7460 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 573
Read events
25 463
Write events
78
Delete events
32
Modification events
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Extreme.Injector.v3.7.3.-.by.master131.zip | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (7332) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
Executable files
9
Suspicious files
17
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7332 | WinRAR.exe | C:\Users\admin\Desktop\Extreme Injector v3.exe | executable | |
MD5:EC801A7D4B72A288EC6C207BB9FF0131 | SHA256:B65F40618F584303CA0BCF9B5F88C233CC4237699C0C4BF40BA8FACBE8195A46 | |||
| 7704 | CCleaner64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ccc0fa1b9f86f7b3.customDestinations-ms | binary | |
MD5:78EE1B44B762EAD7212AA088775AC763 | SHA256:C4D1C081BED922AD4352C47DE8AC8659F69E0E91267CDE8186D5D855E7BE72AB | |||
| 7332 | WinRAR.exe | C:\Users\admin\Desktop\Dll1.dll | executable | |
MD5:146C04A8667B6AE69F911F7ED9AF7B74 | SHA256:A574CDD2FC47C08A69C70AD9BAD9F2B8F61D1031E914DDB9B18F9897EA48C0A4 | |||
| 7704 | CCleaner64.exe | C:\Program Files\CCleaner\gcapi_dll.dll | executable | |
MD5:F17F96322F8741FE86699963A1812897 | SHA256:8B6CE3A640E2D6F36B0001BE2A1ABB765AE51E62C314A15911E75138CBB544BB | |||
| 7704 | CCleaner64.exe | C:\Program Files\CCleaner\gcapi_17481615587704.dll | executable | |
MD5:F17F96322F8741FE86699963A1812897 | SHA256:8B6CE3A640E2D6F36B0001BE2A1ABB765AE51E62C314A15911E75138CBB544BB | |||
| 7704 | CCleaner64.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RP11VN3GFHOH0EB8OTPR.temp | binary | |
MD5:78EE1B44B762EAD7212AA088775AC763 | SHA256:C4D1C081BED922AD4352C47DE8AC8659F69E0E91267CDE8186D5D855E7BE72AB | |||
| 7704 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:A3DBD3F6785297EB28AB7297FFB52CC0 | SHA256:4CBB47BB715C0D9C9C6A626C4AB6D804CD4377C785E604B10C5DA6BAA3F21851 | |||
| 7704 | CCleaner64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:C09A539C08083232DA6CCA29F43A0E87 | SHA256:7083D1E505ADE30D5619BD2EEC3A4A4C8A5634A2AC8E787C8EE4D65DFFD20F3C | |||
| 7704 | CCleaner64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\ccupdate635_free[1].exe | — | |
MD5:— | SHA256:— | |||
| 7704 | CCleaner64.exe | C:\Program Files\CCleaner\temp_ccupdate\ccupdate635_free.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
97
DNS requests
39
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7704 | CCleaner64.exe | GET | 200 | 2.16.168.113:80 | http://ncc.avast.com/ncc.txt | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7704 | CCleaner64.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
7704 | CCleaner64.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | whitelisted |
7704 | CCleaner64.exe | GET | 200 | 142.250.185.67:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | whitelisted |
7948 | CCleaner64.exe | GET | 200 | 2.16.168.113:80 | http://ncc.avast.com/ncc.txt | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2924 | SearchApp.exe | 2.16.204.158:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6544 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
7704 | CCleaner64.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
7948 | CCleaner64.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
4724 | MSBuild.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (phoucc .digital) |
4724 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (phoucc .digital) in TLS SNI |
4724 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (phoucc .digital) in TLS SNI |
4724 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (phoucc .digital) in TLS SNI |
4724 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (phoucc .digital) in TLS SNI |
4724 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (phoucc .digital) in TLS SNI |