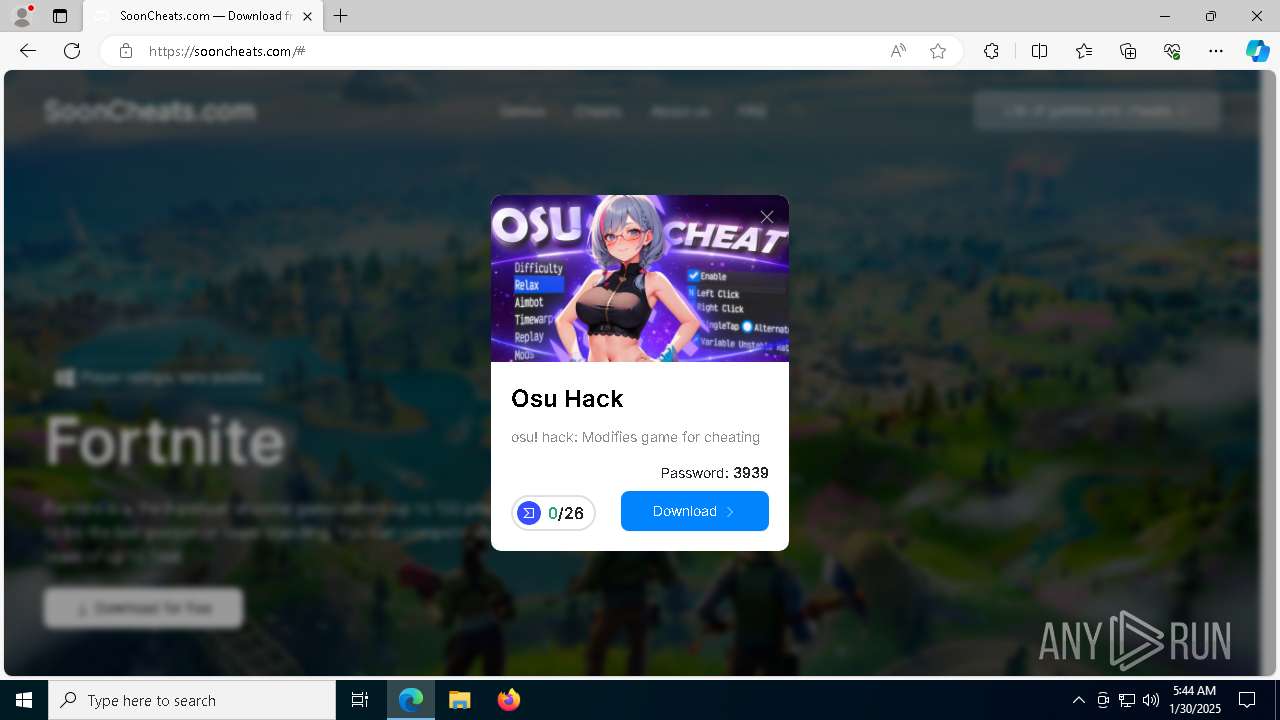
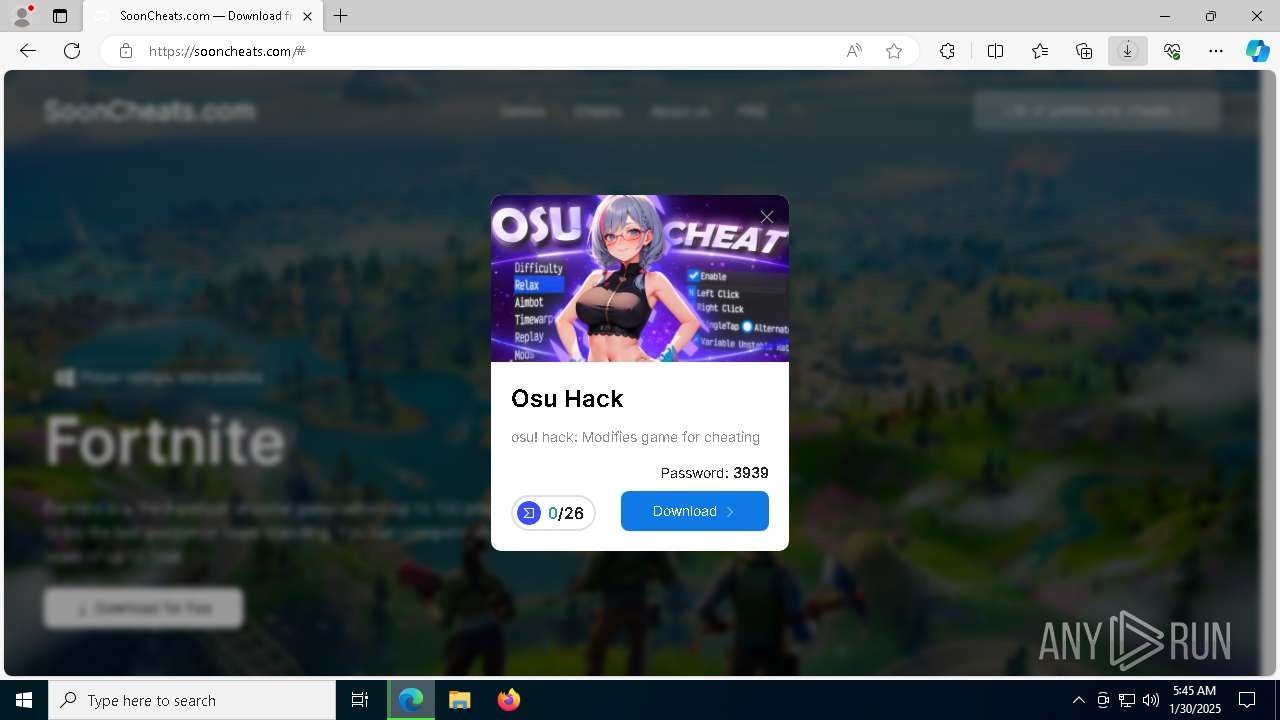
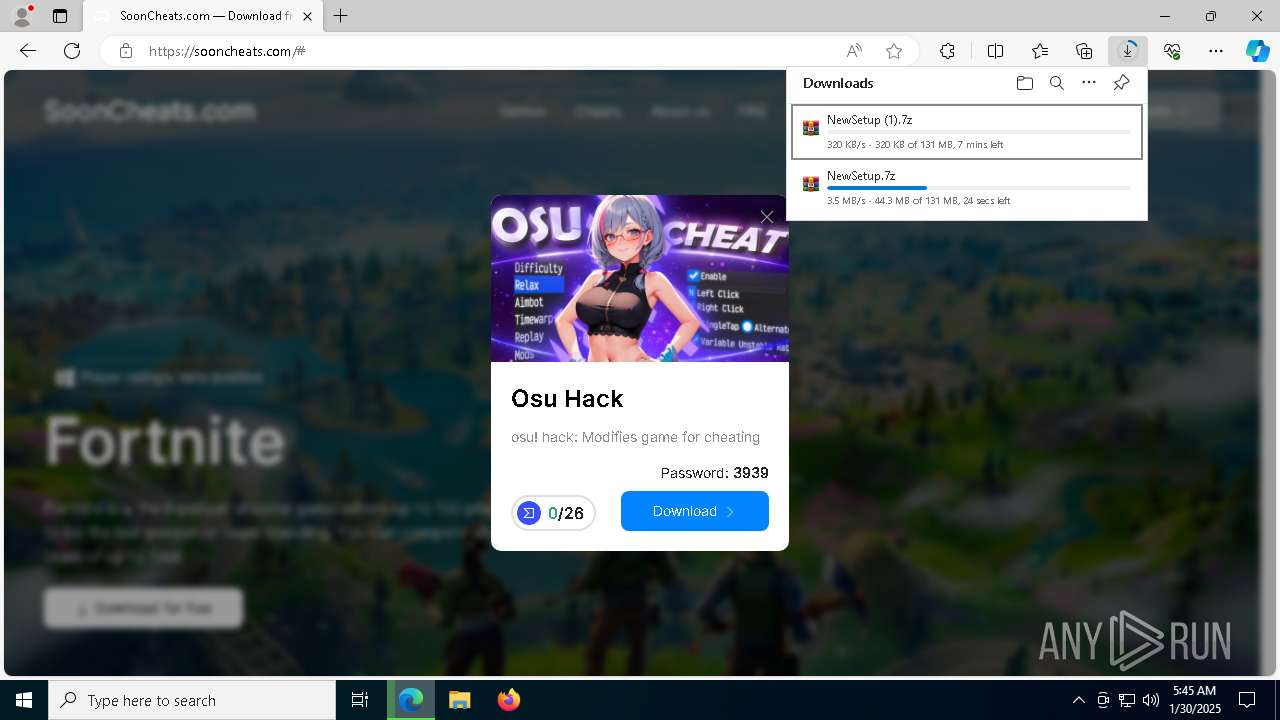
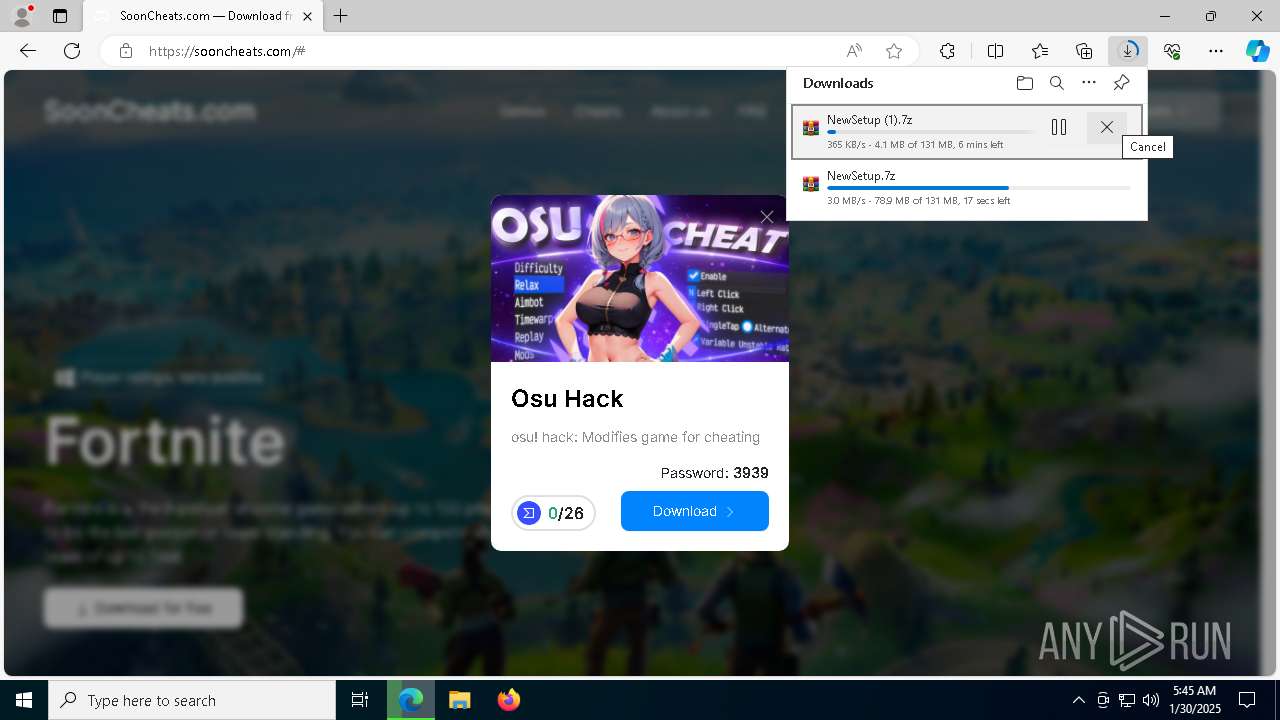
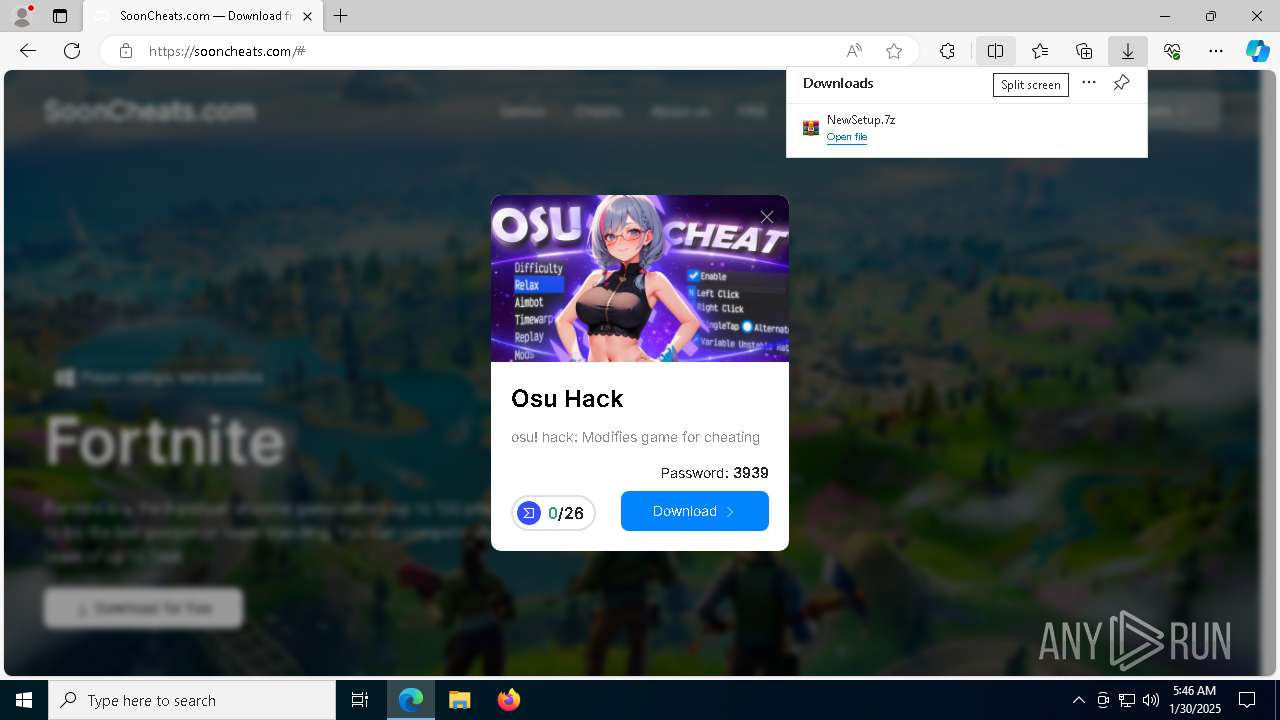
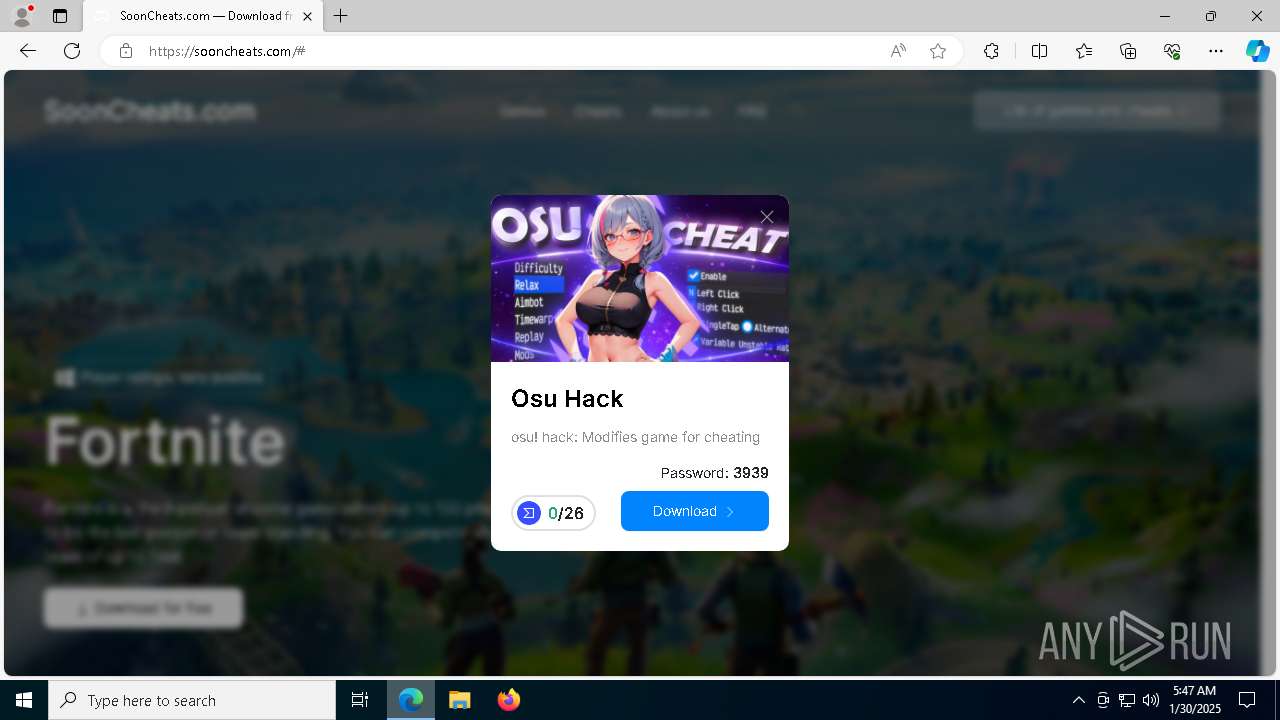
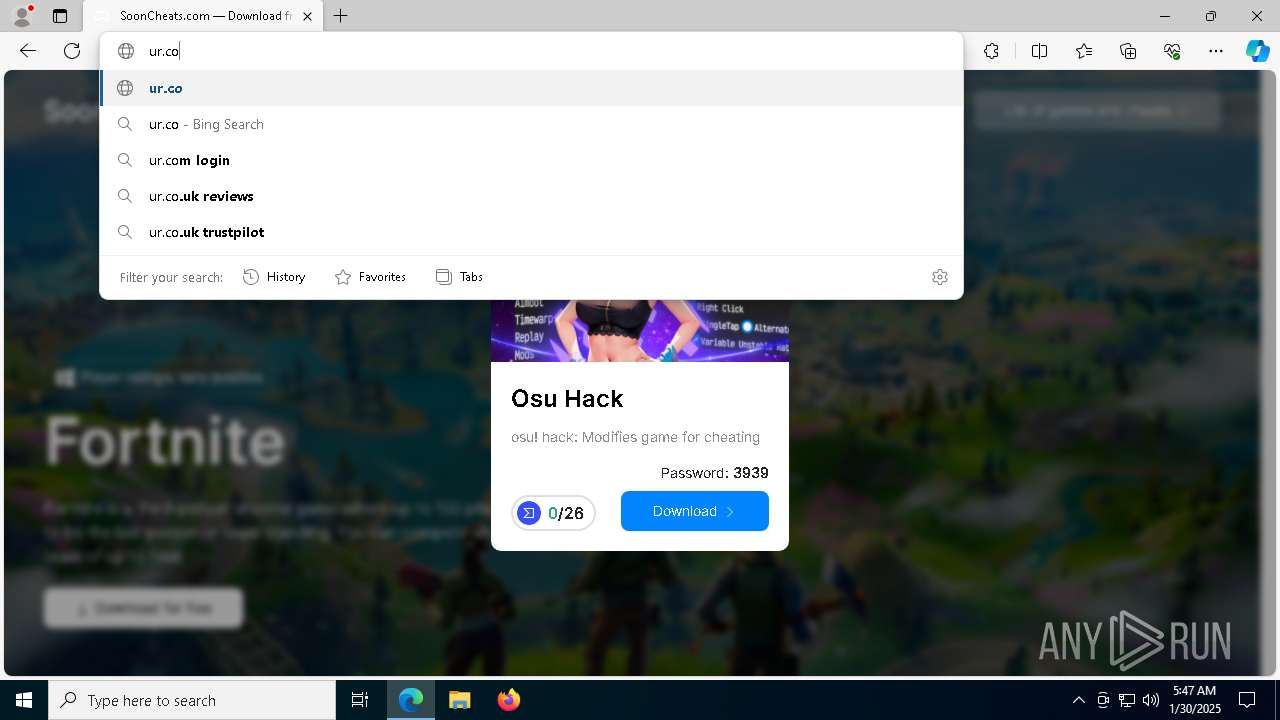
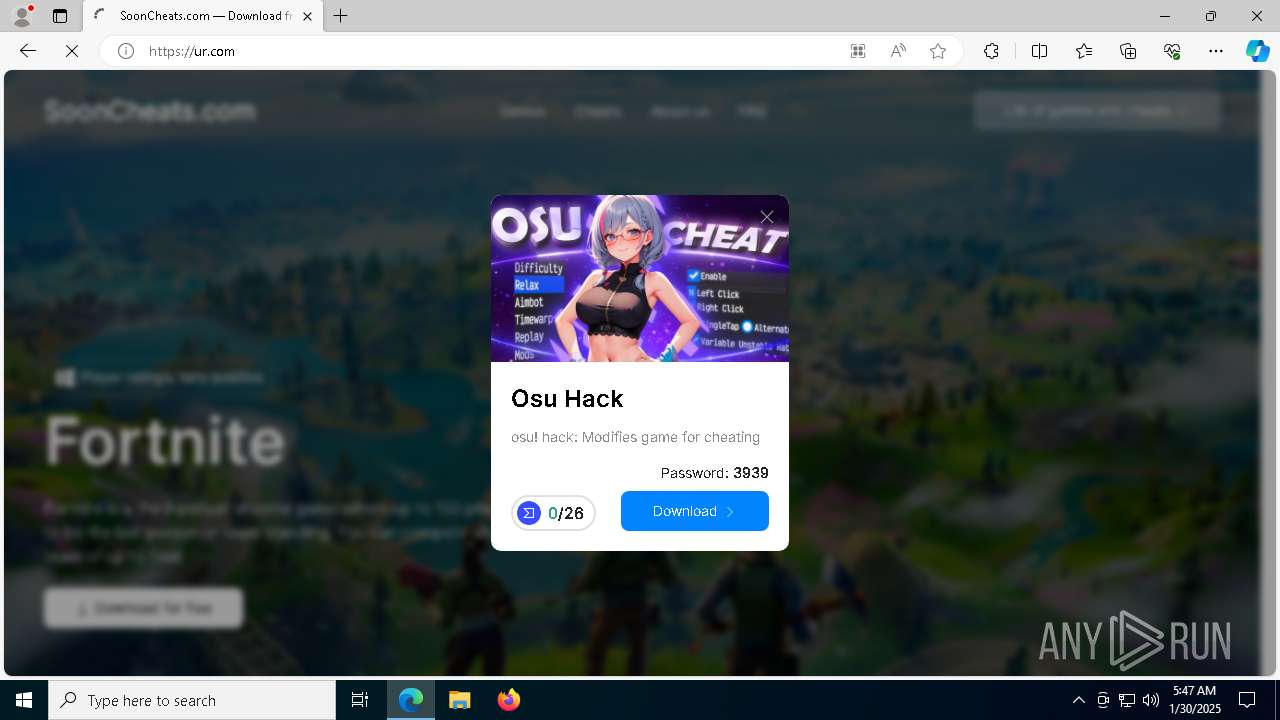
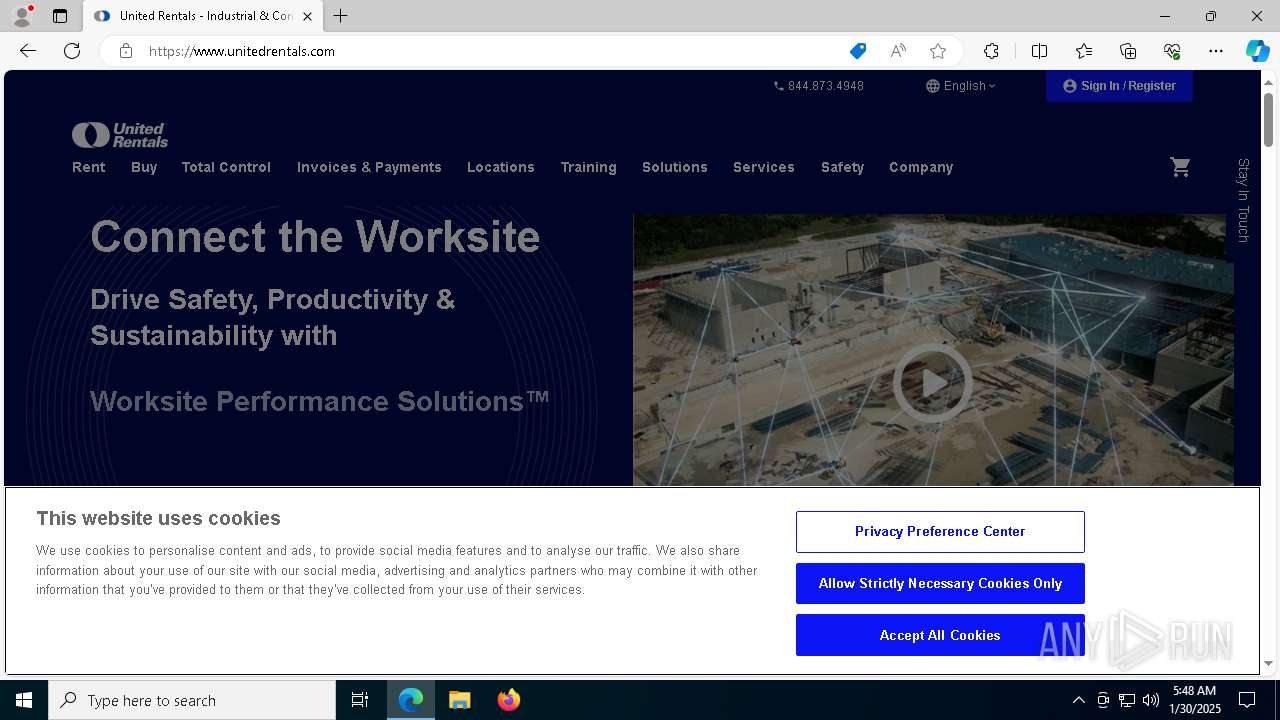
| URL: | https://sooncheats.com/ |
| Full analysis: | https://app.any.run/tasks/6ccd78b5-6797-47d6-a1a7-96e8dd37d35a |
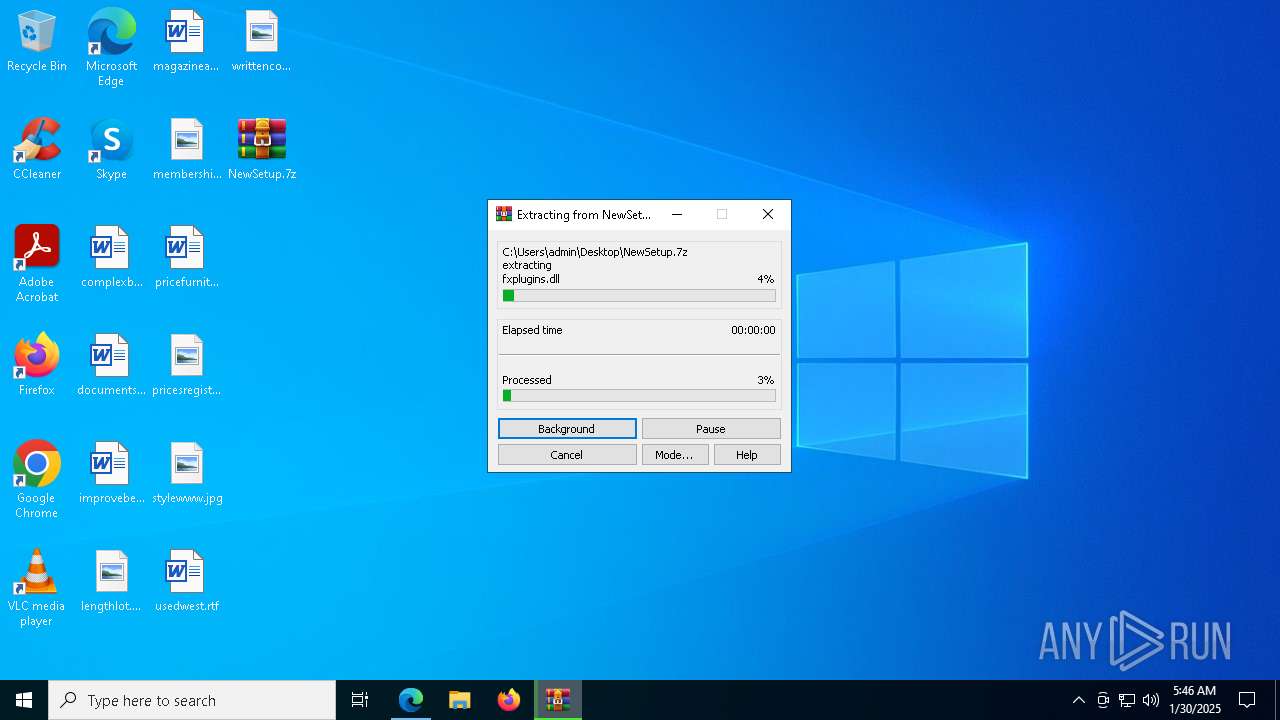
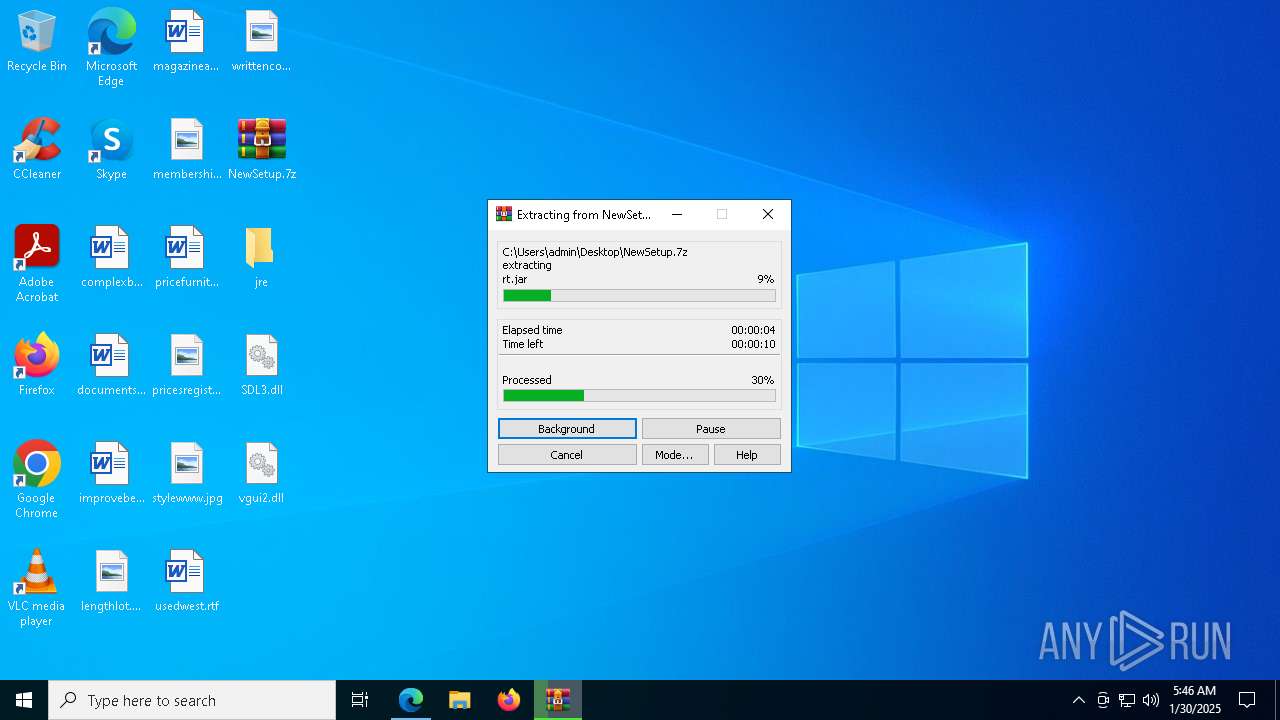
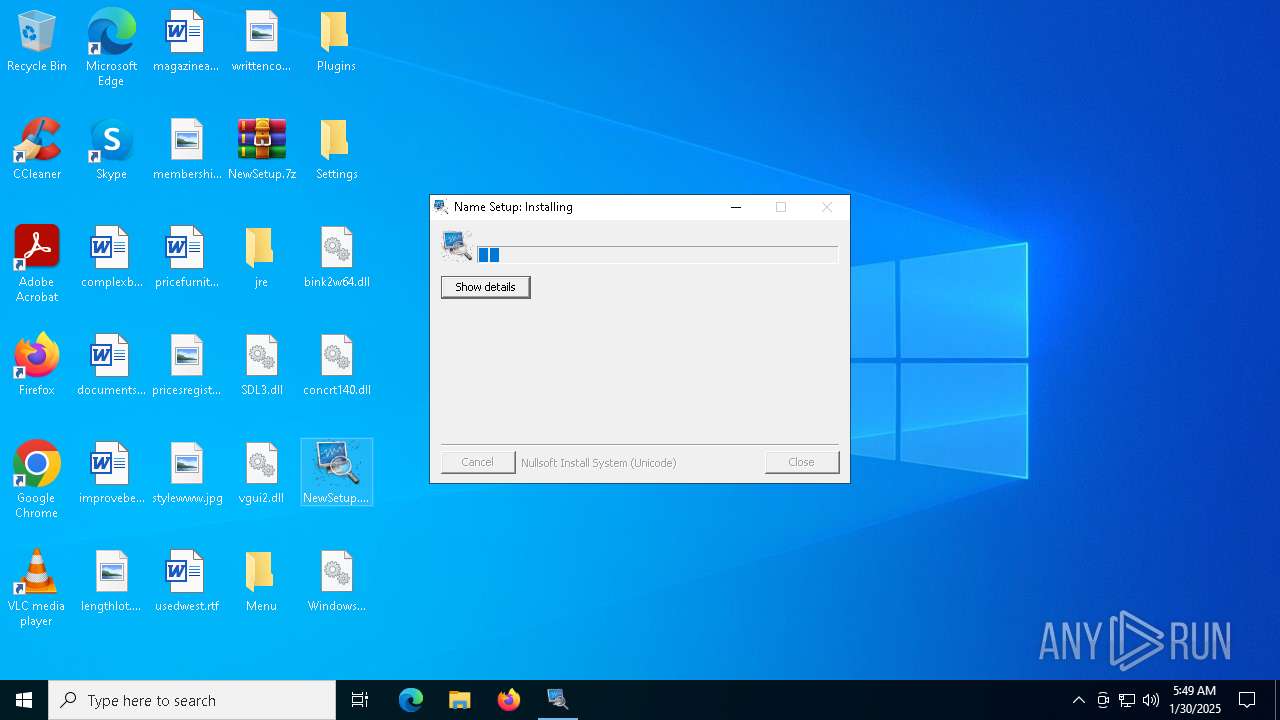
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
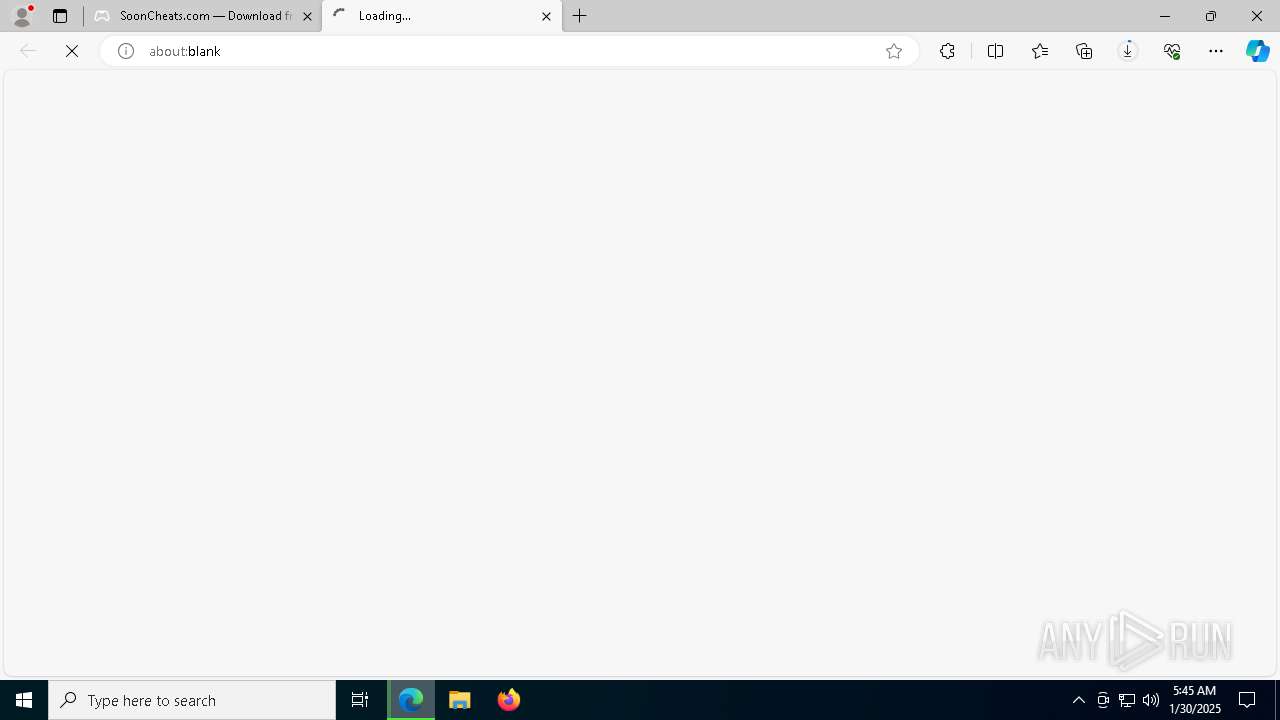
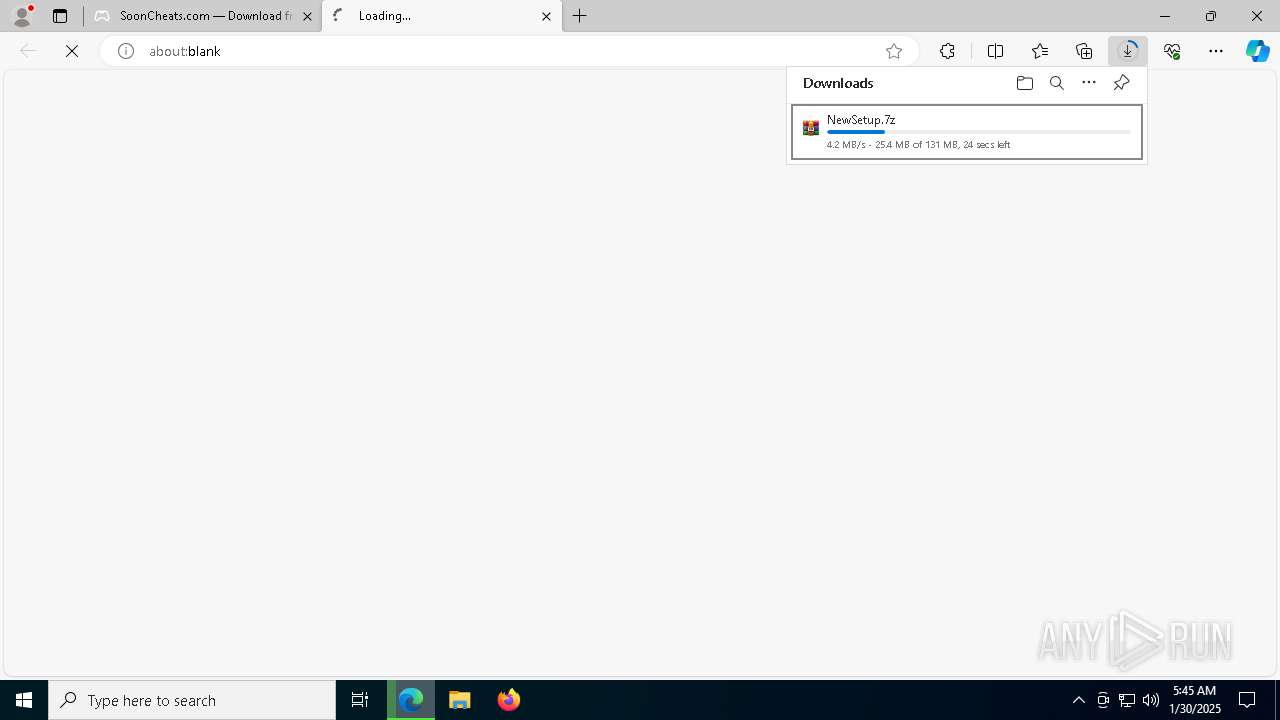
| Analysis date: | January 30, 2025, 05:44:31 |
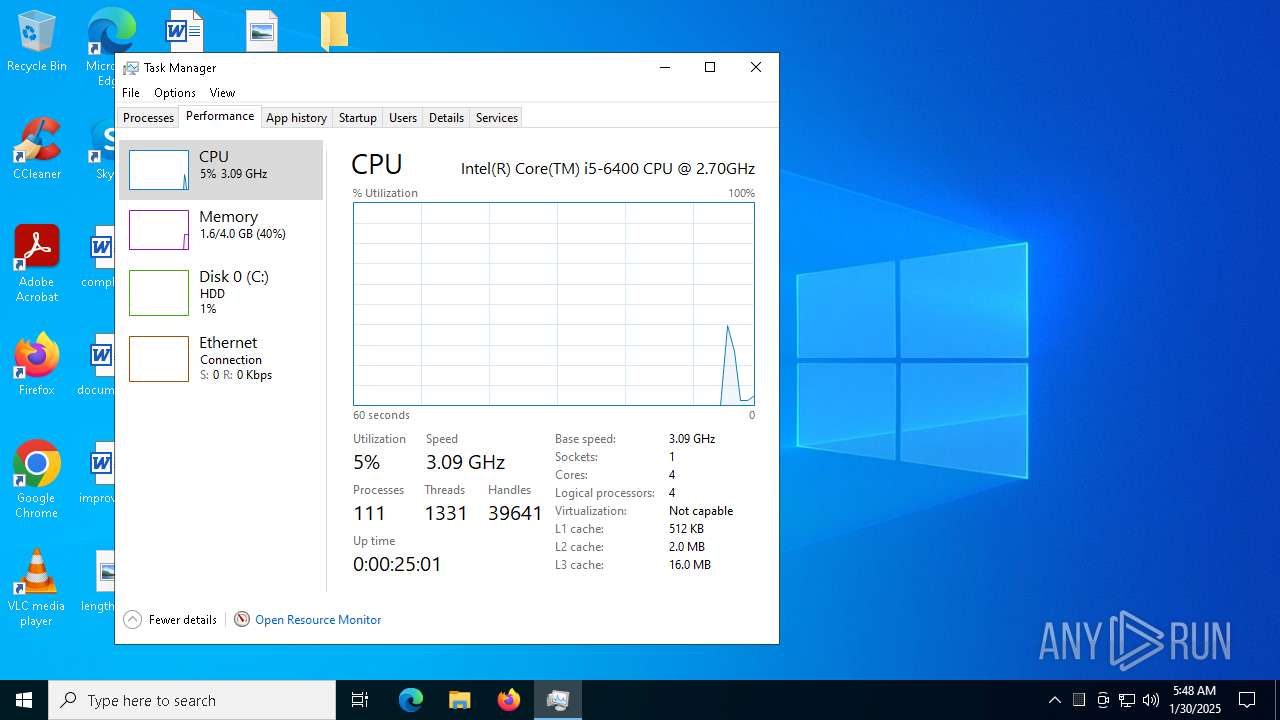
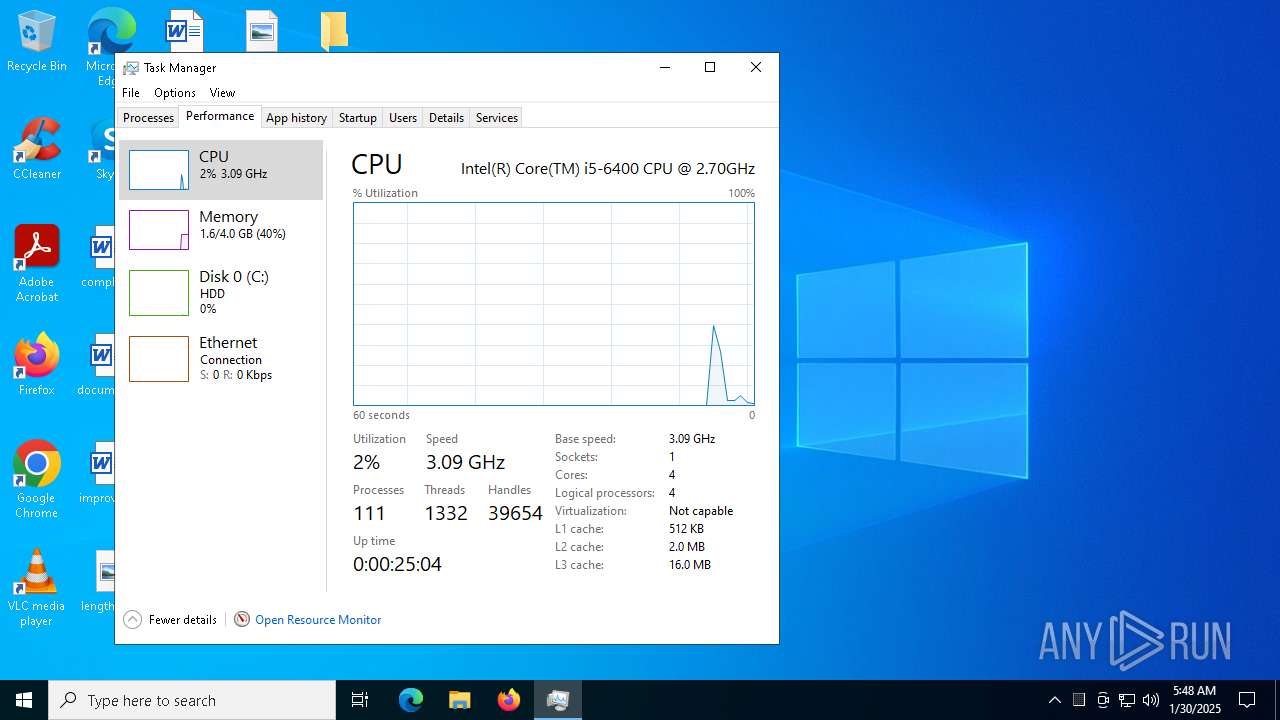
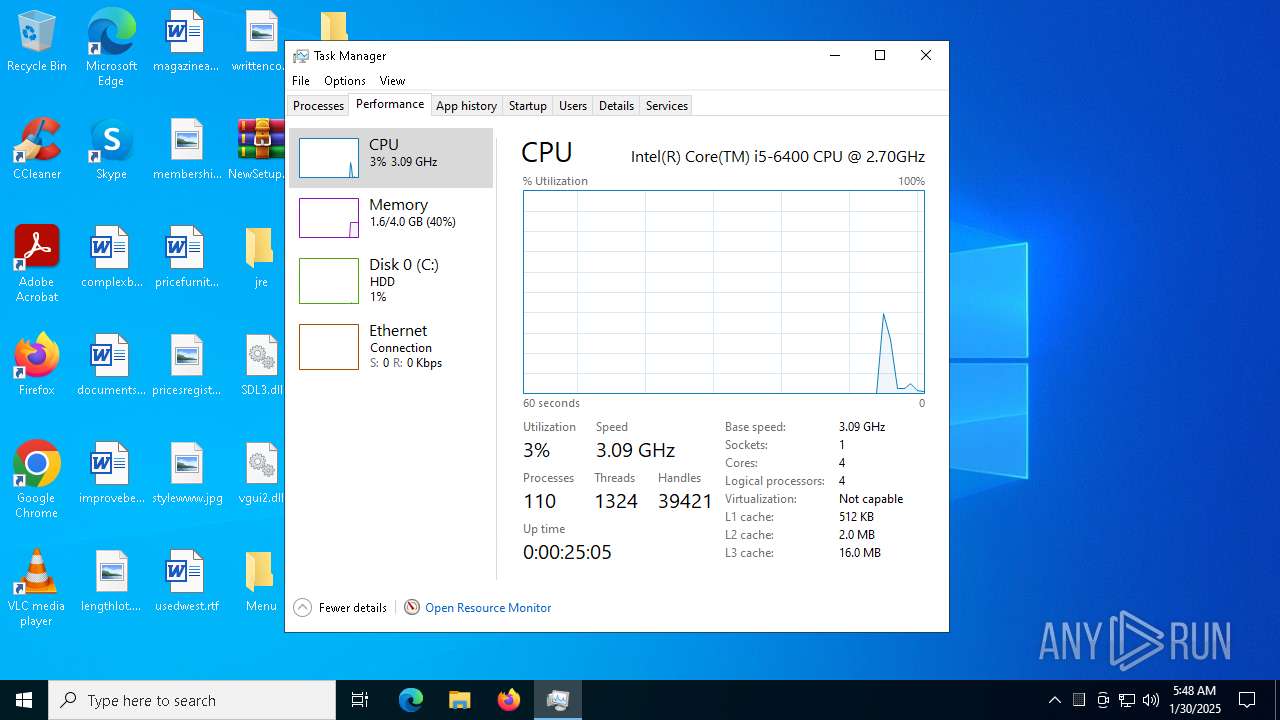
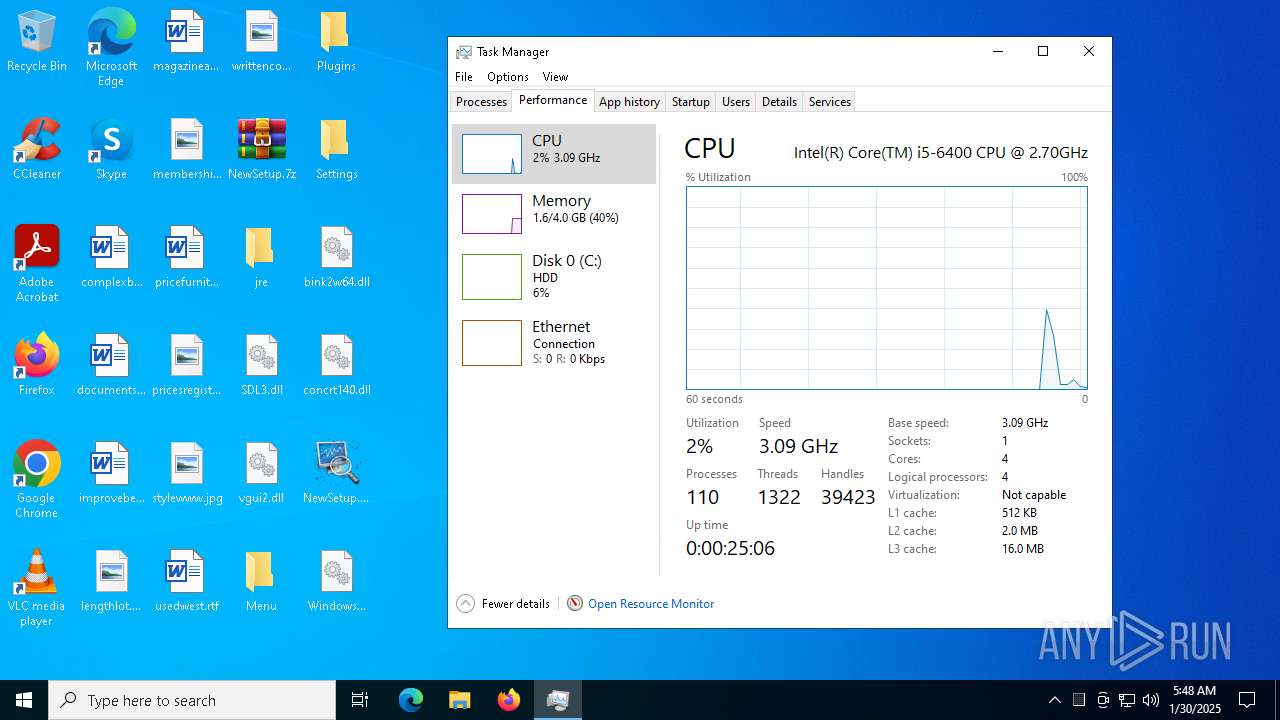
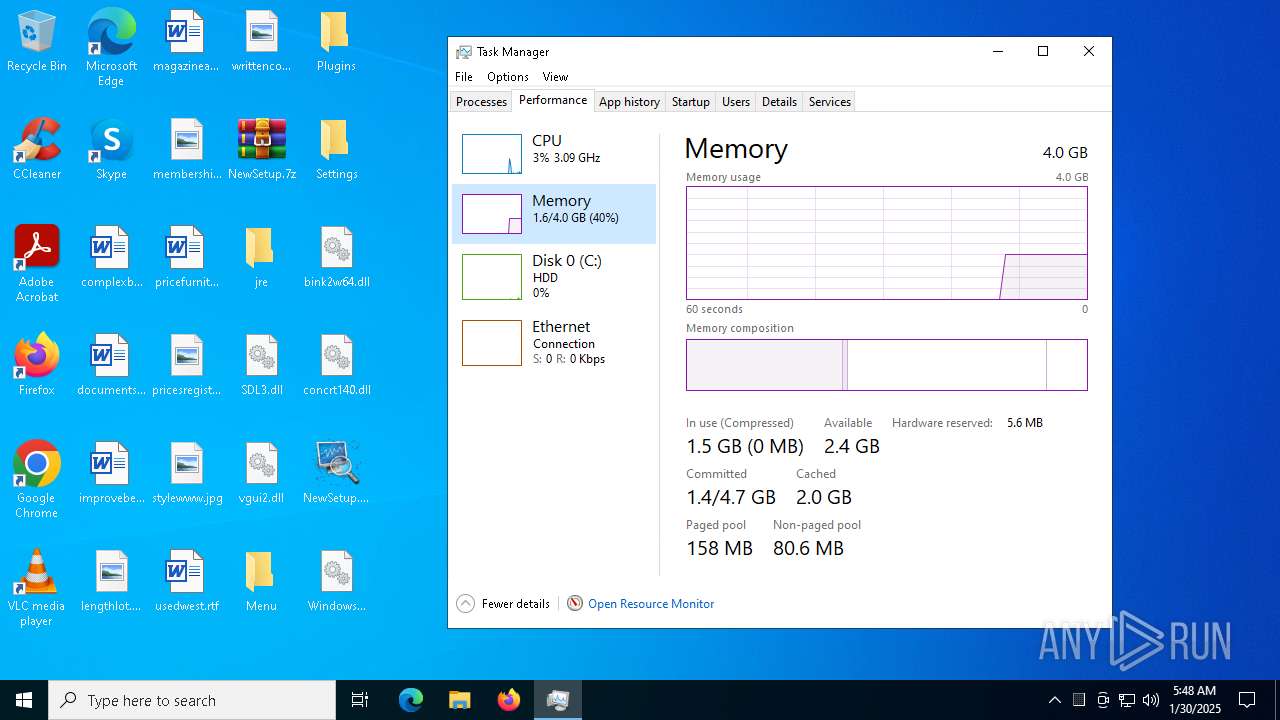
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0DA369E4144B2F2DBC10F4255631C24B |
| SHA1: | B2E2FB9521865CA66AF430353A7D3812D71F92E1 |
| SHA256: | 37C95D8D7FFFF47C061C0745690CB63426E3F8749091D39BFB4FF4243947E82F |
| SSDEEP: | 3:N8H2V3n:2I |
MALICIOUS
LUMMA mutex has been found
- Ur.com (PID: 1668)
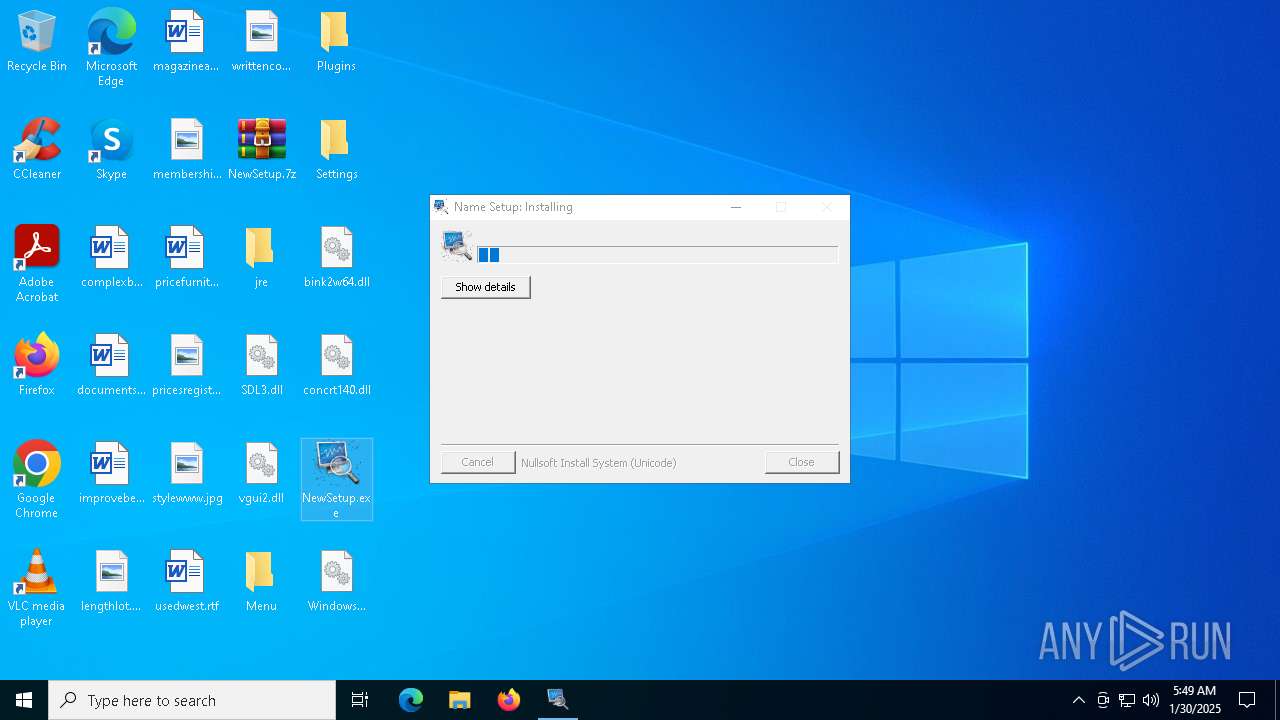
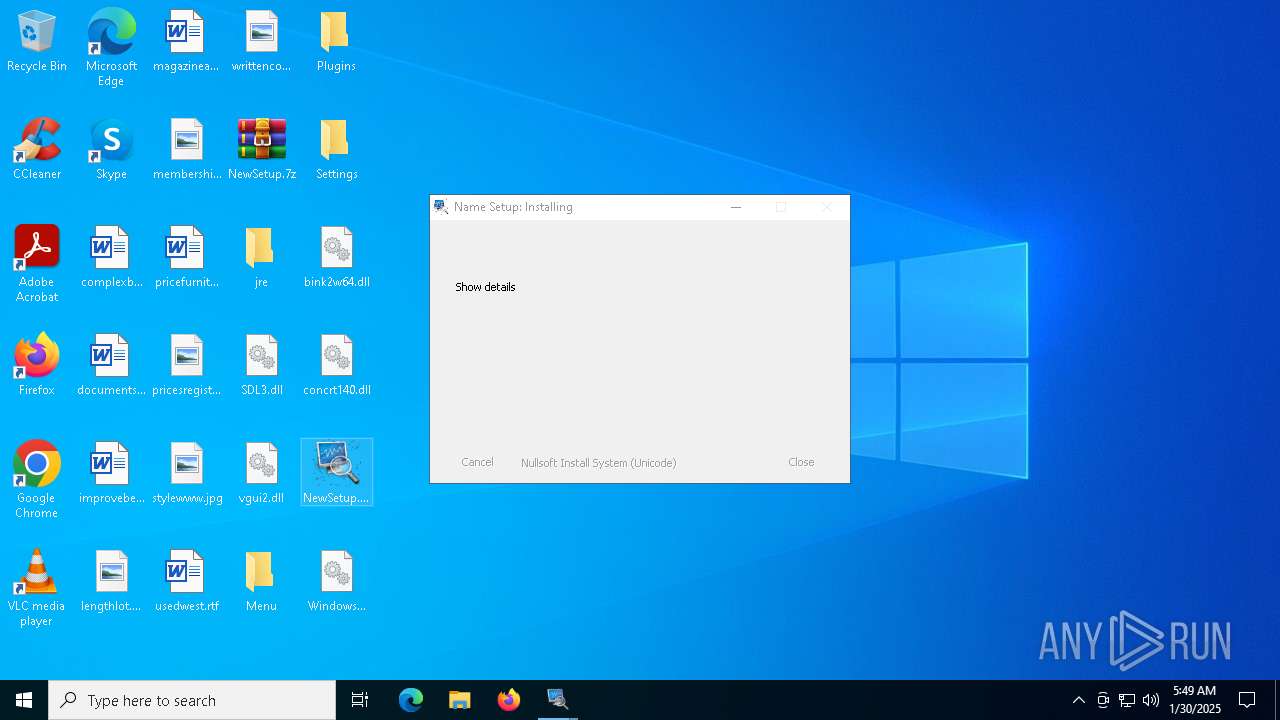
Executing a file with an untrusted certificate
- NewSetup.exe (PID: 3820)
- NewSetup.exe (PID: 1448)
- NewSetup.exe (PID: 7288)
- NewSetup.exe (PID: 8140)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 7016)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6760)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 7180)
- NewSetup.exe (PID: 1344)
- NewSetup.exe (PID: 1140)
- NewSetup.exe (PID: 6780)
Steals credentials from Web Browsers
- Ur.com (PID: 1668)
Actions looks like stealing of personal data
- Ur.com (PID: 1668)
SUSPICIOUS
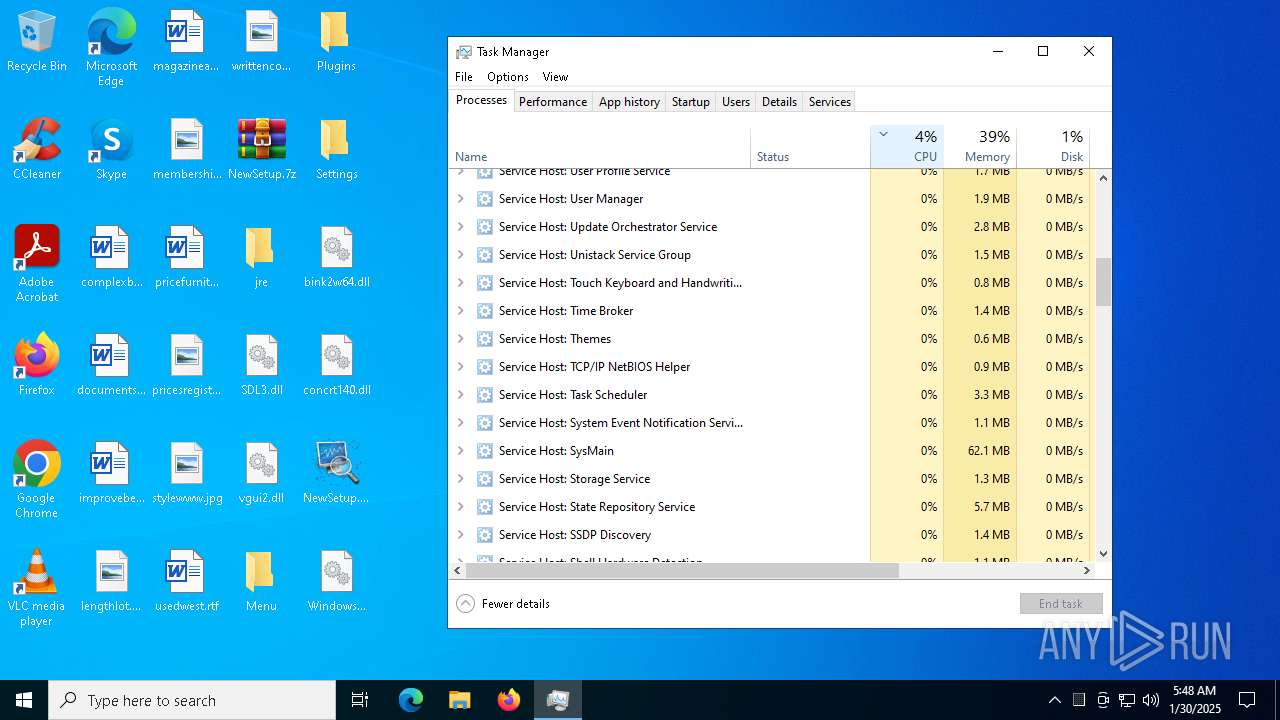
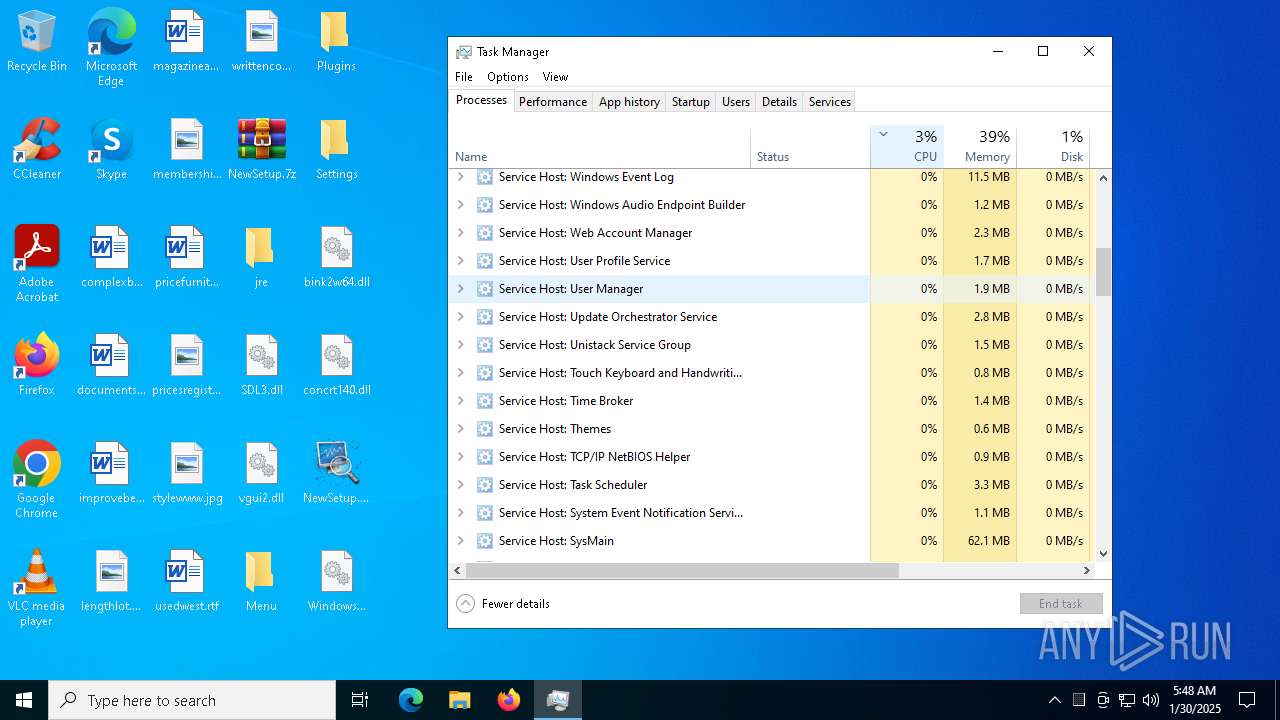
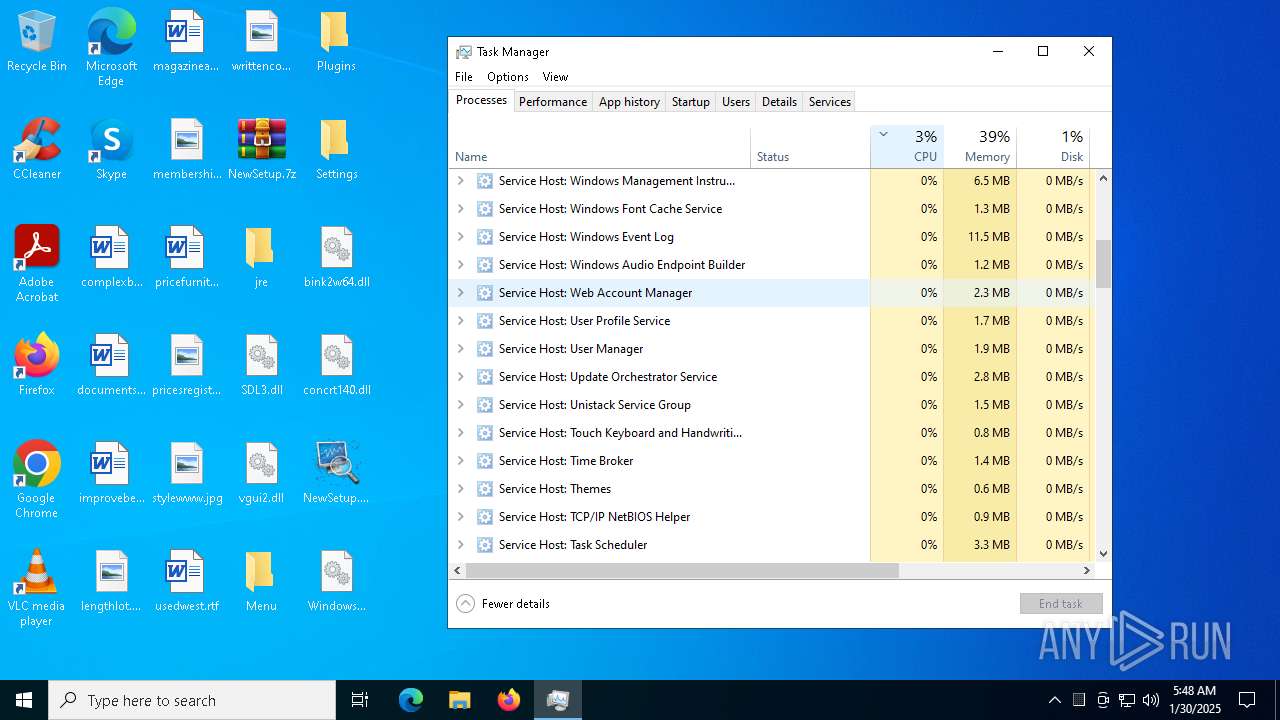
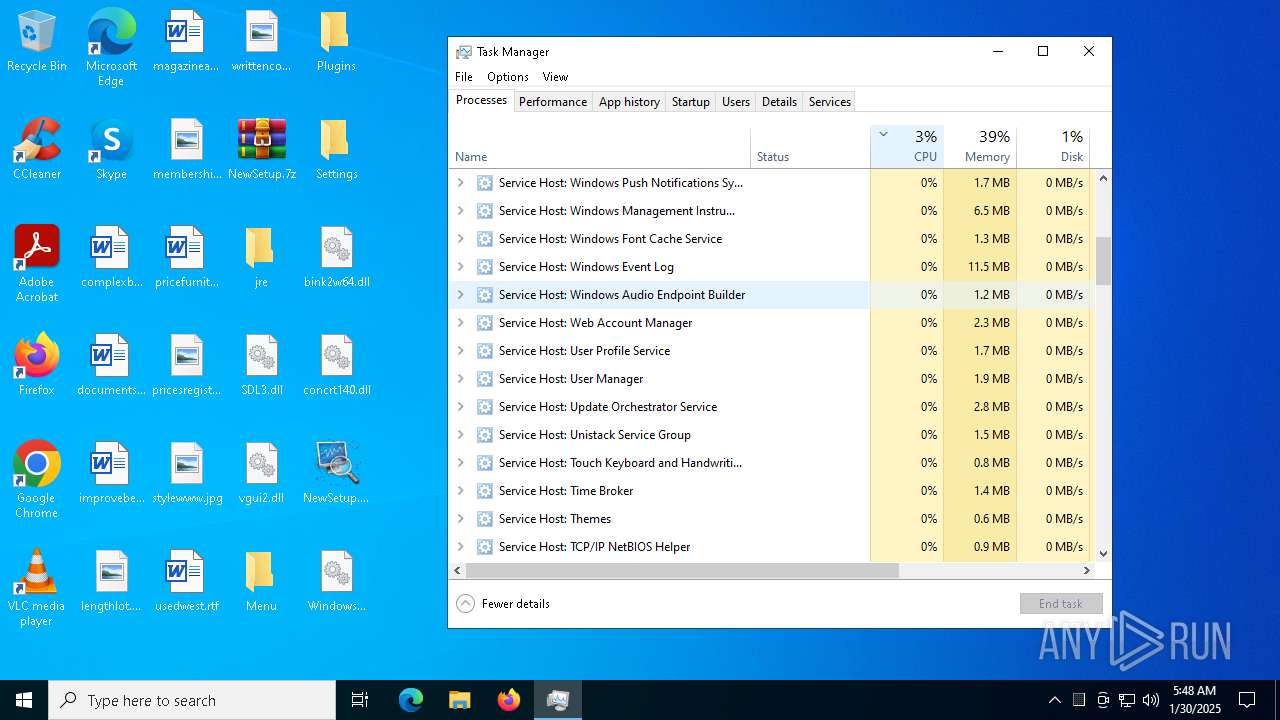
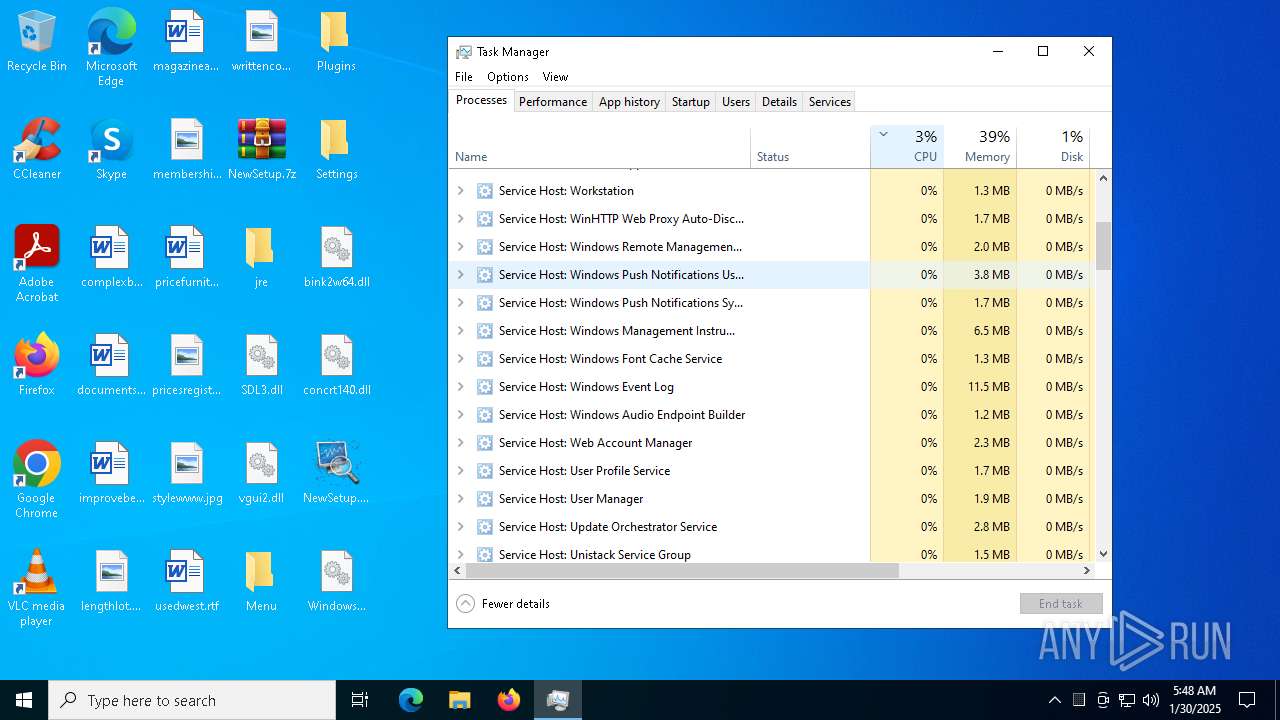
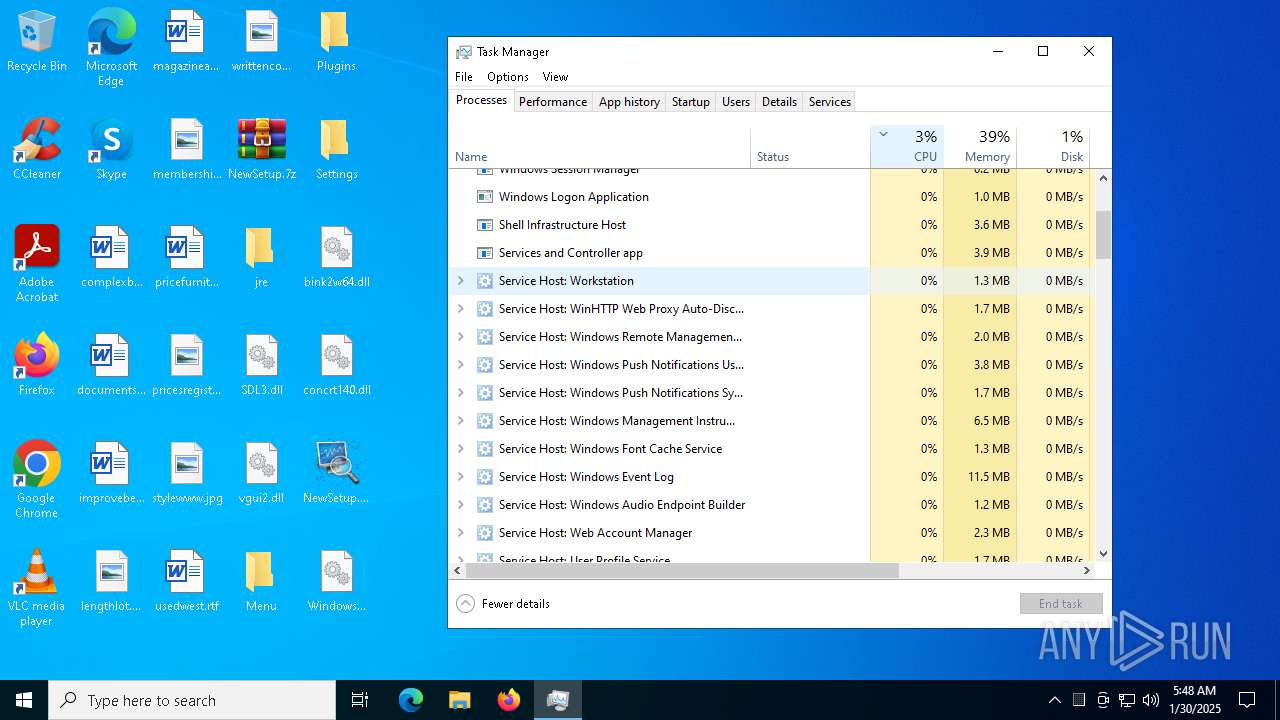
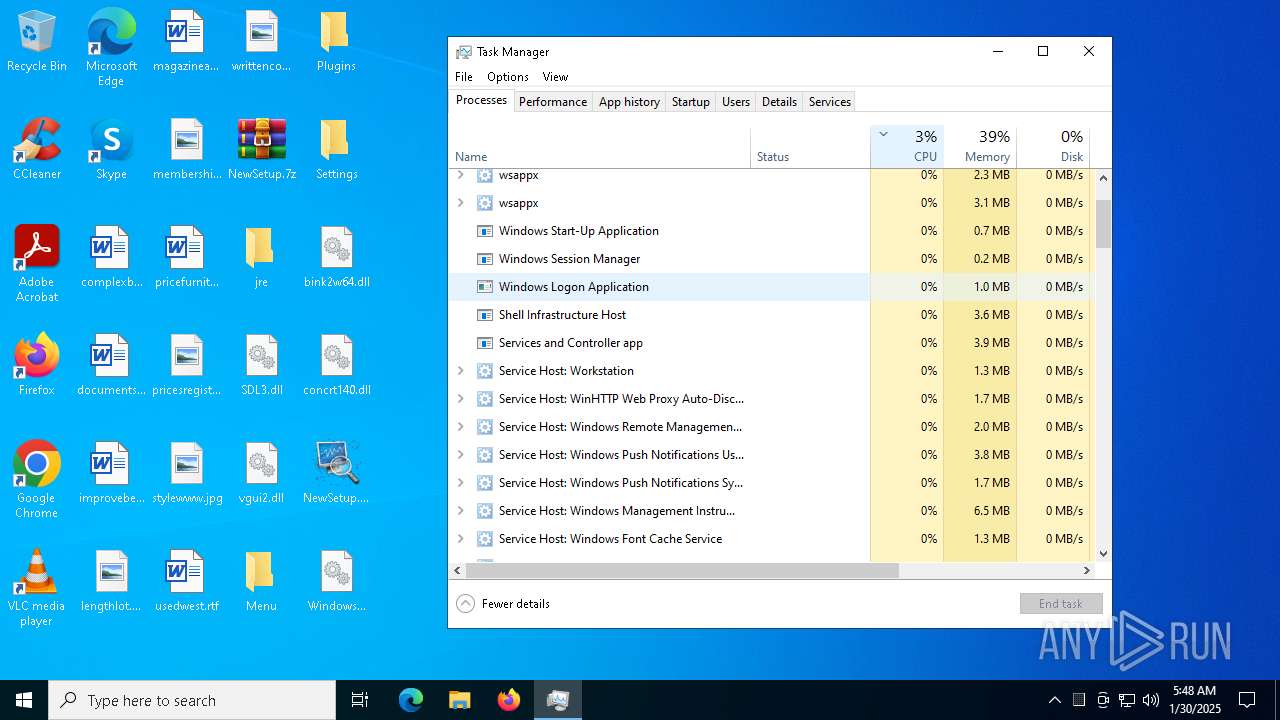
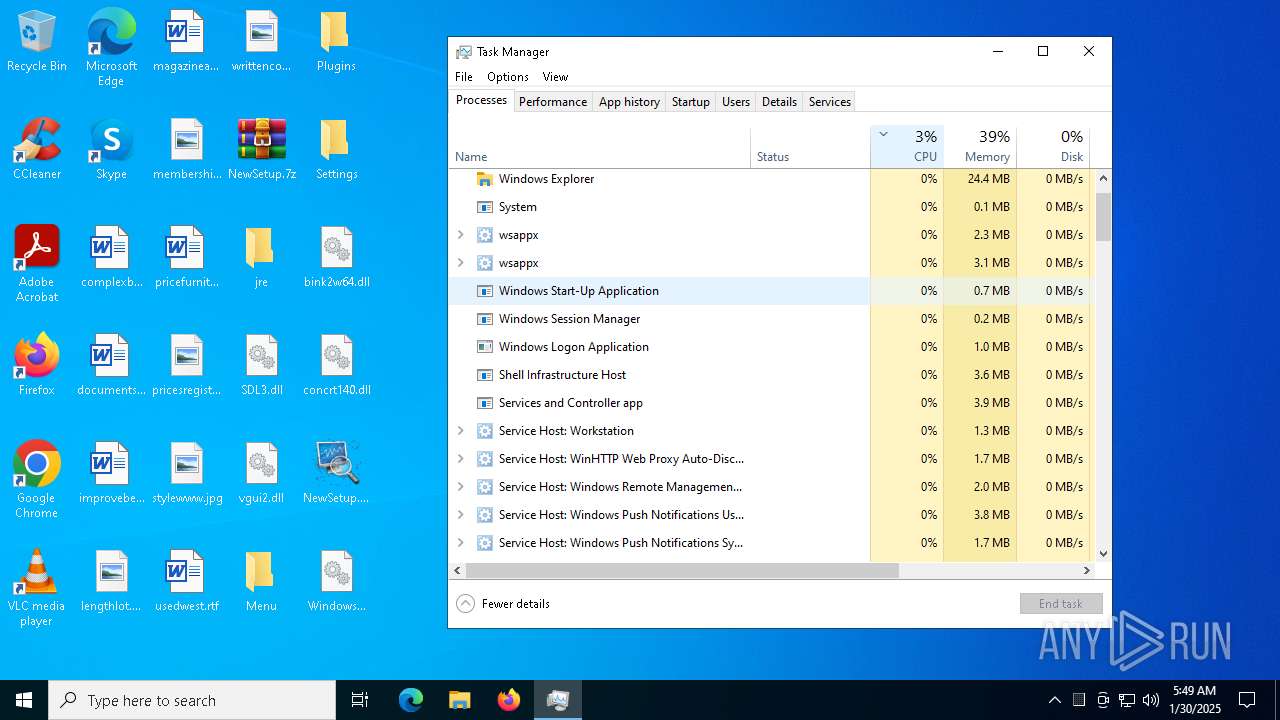
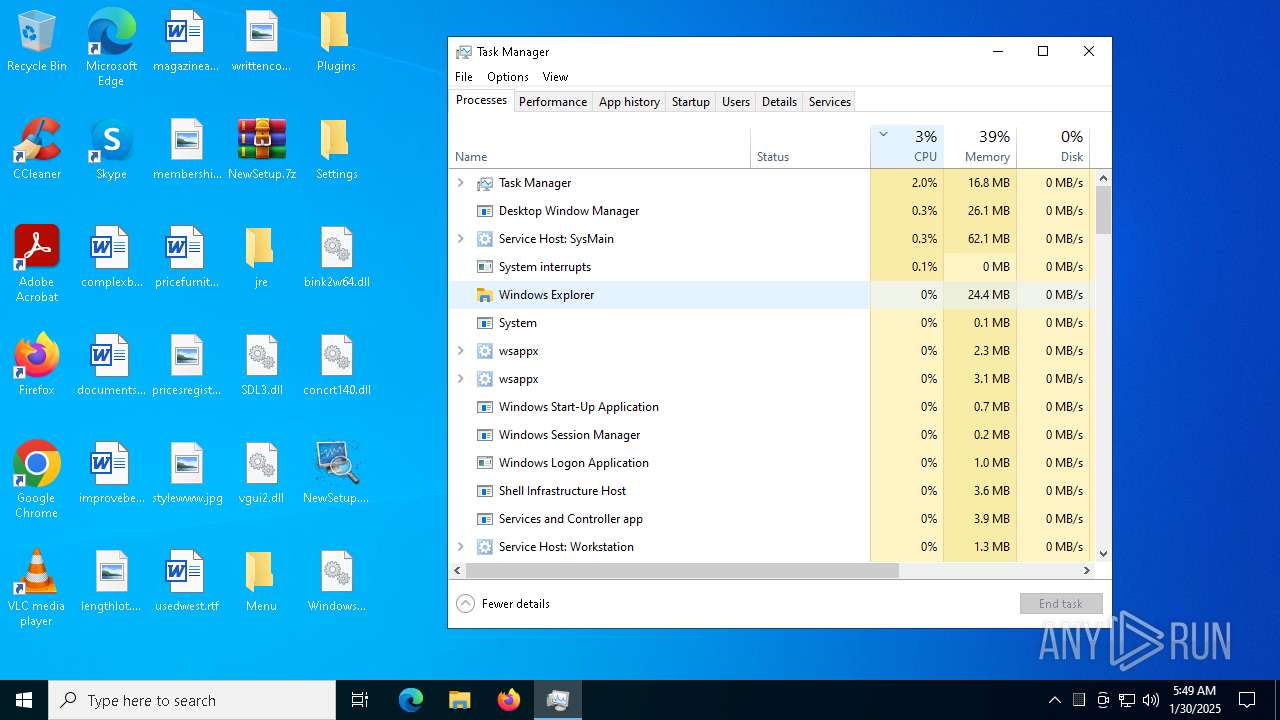
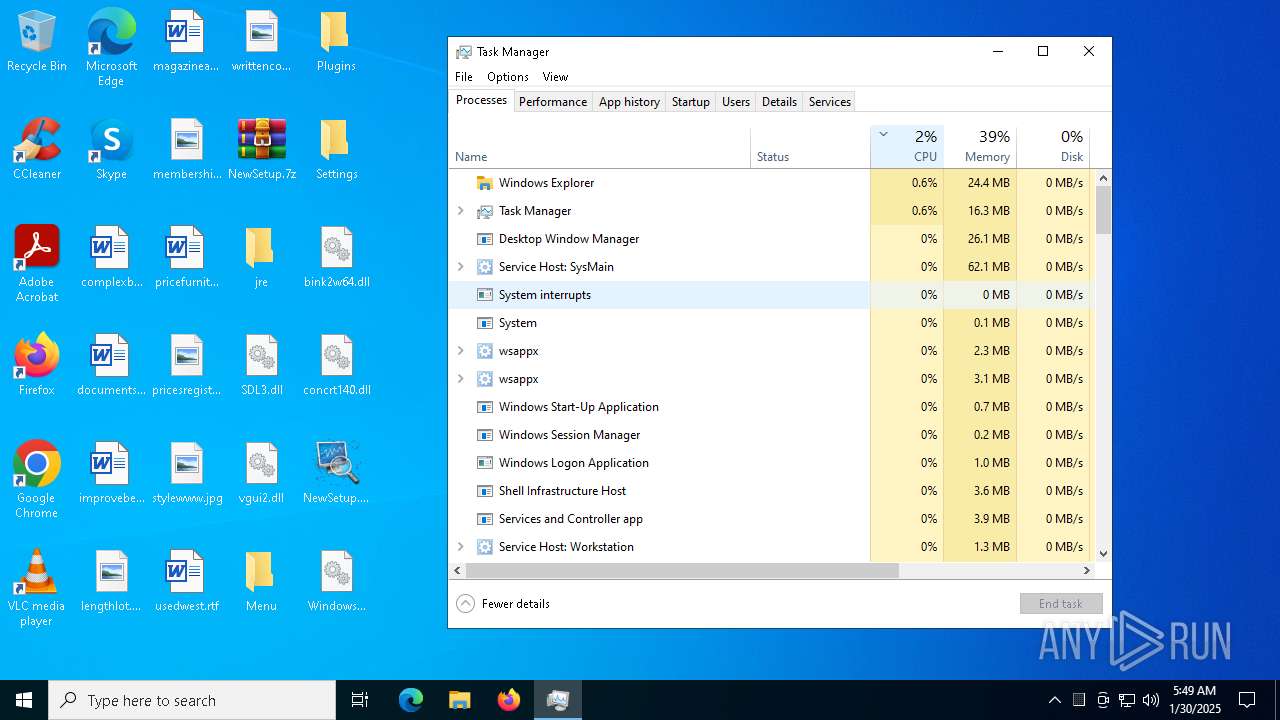
Get information on the list of running processes
- cmd.exe (PID: 7316)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7940)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7316)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7756)
Starts CMD.EXE for commands execution
- NewSetup.exe (PID: 3820)
- cmd.exe (PID: 7316)
- NewSetup.exe (PID: 1448)
- cmd.exe (PID: 6408)
- NewSetup.exe (PID: 7288)
- NewSetup.exe (PID: 8140)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 7016)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6760)
- NewSetup.exe (PID: 6780)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 7180)
- NewSetup.exe (PID: 1344)
- cmd.exe (PID: 7756)
- NewSetup.exe (PID: 1140)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 7812)
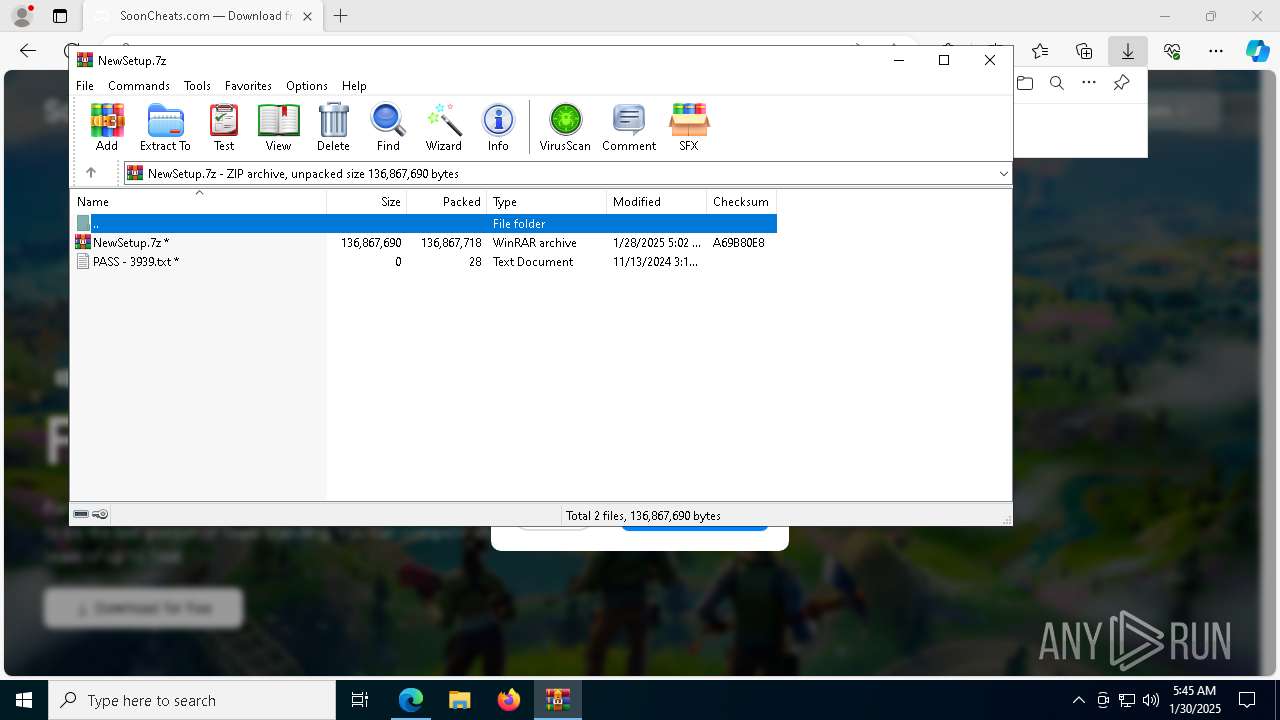
Process drops legitimate windows executable
- WinRAR.exe (PID: 7520)
Executing commands from ".cmd" file
- NewSetup.exe (PID: 3820)
- NewSetup.exe (PID: 1448)
- NewSetup.exe (PID: 7288)
- NewSetup.exe (PID: 8140)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 7016)
- NewSetup.exe (PID: 1140)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6760)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 7180)
- NewSetup.exe (PID: 1344)
- NewSetup.exe (PID: 6780)
Application launched itself
- cmd.exe (PID: 7316)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7940)
The executable file from the user directory is run by the CMD process
- Ur.com (PID: 1668)
- Ur.com (PID: 2148)
- Ur.com (PID: 244)
- Ur.com (PID: 8136)
- Ur.com (PID: 7284)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7316)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7940)
Starts application with an unusual extension
- cmd.exe (PID: 7316)
- cmd.exe (PID: 6408)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7940)
Reads security settings of Internet Explorer
- NewSetup.exe (PID: 3820)
- NewSetup.exe (PID: 7288)
- NewSetup.exe (PID: 8140)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 1448)
- NewSetup.exe (PID: 1140)
- NewSetup.exe (PID: 7016)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6780)
- NewSetup.exe (PID: 6760)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 7180)
- NewSetup.exe (PID: 1344)
There is functionality for taking screenshot (YARA)
- NewSetup.exe (PID: 3820)
- NewSetup.exe (PID: 1448)
Searches for installed software
- Ur.com (PID: 1668)
INFO
Reads Environment values
- identity_helper.exe (PID: 8068)
- identity_helper.exe (PID: 1572)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6472)
Checks supported languages
- identity_helper.exe (PID: 8068)
- NewSetup.exe (PID: 3820)
- extrac32.exe (PID: 5980)
- Ur.com (PID: 1668)
- identity_helper.exe (PID: 1572)
- NewSetup.exe (PID: 1448)
- NewSetup.exe (PID: 7288)
- extrac32.exe (PID: 1172)
- Ur.com (PID: 2148)
- NewSetup.exe (PID: 1140)
- NewSetup.exe (PID: 8140)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 7016)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 6780)
- NewSetup.exe (PID: 7180)
- NewSetup.exe (PID: 1344)
- extrac32.exe (PID: 3812)
- extrac32.exe (PID: 1192)
- Ur.com (PID: 244)
- Ur.com (PID: 8136)
- NewSetup.exe (PID: 6760)
- extrac32.exe (PID: 1668)
- Ur.com (PID: 7284)
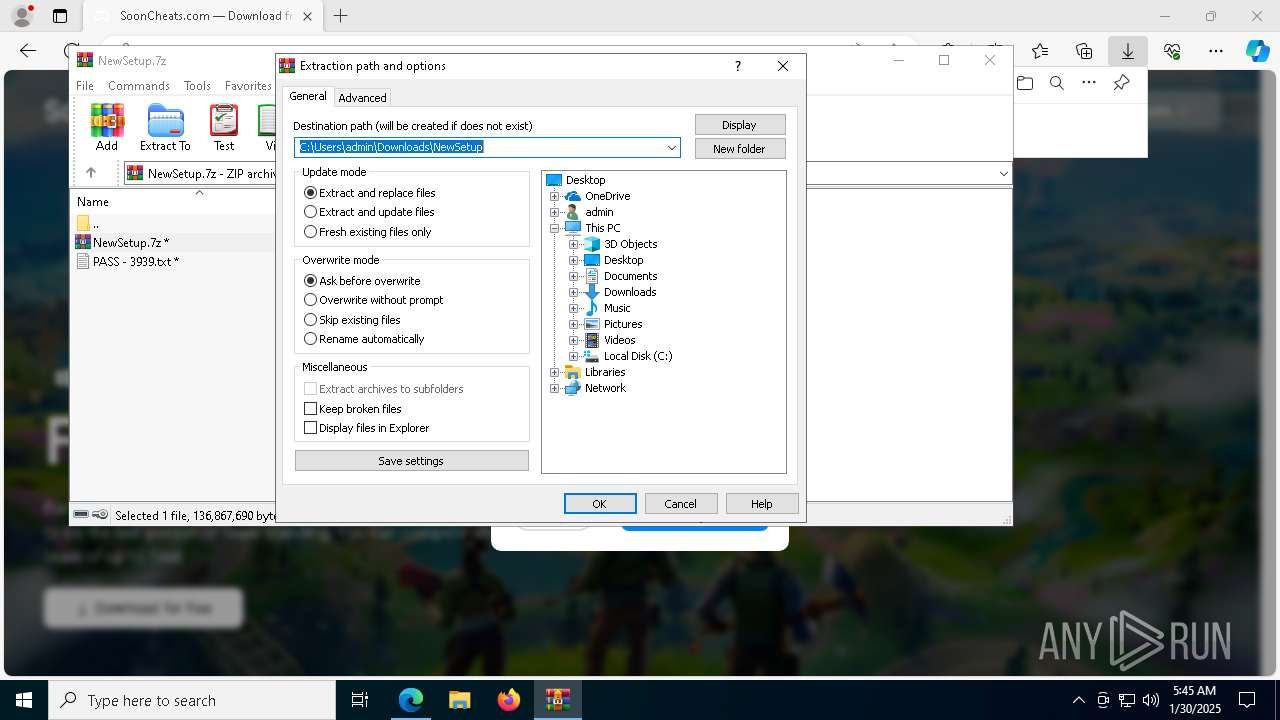
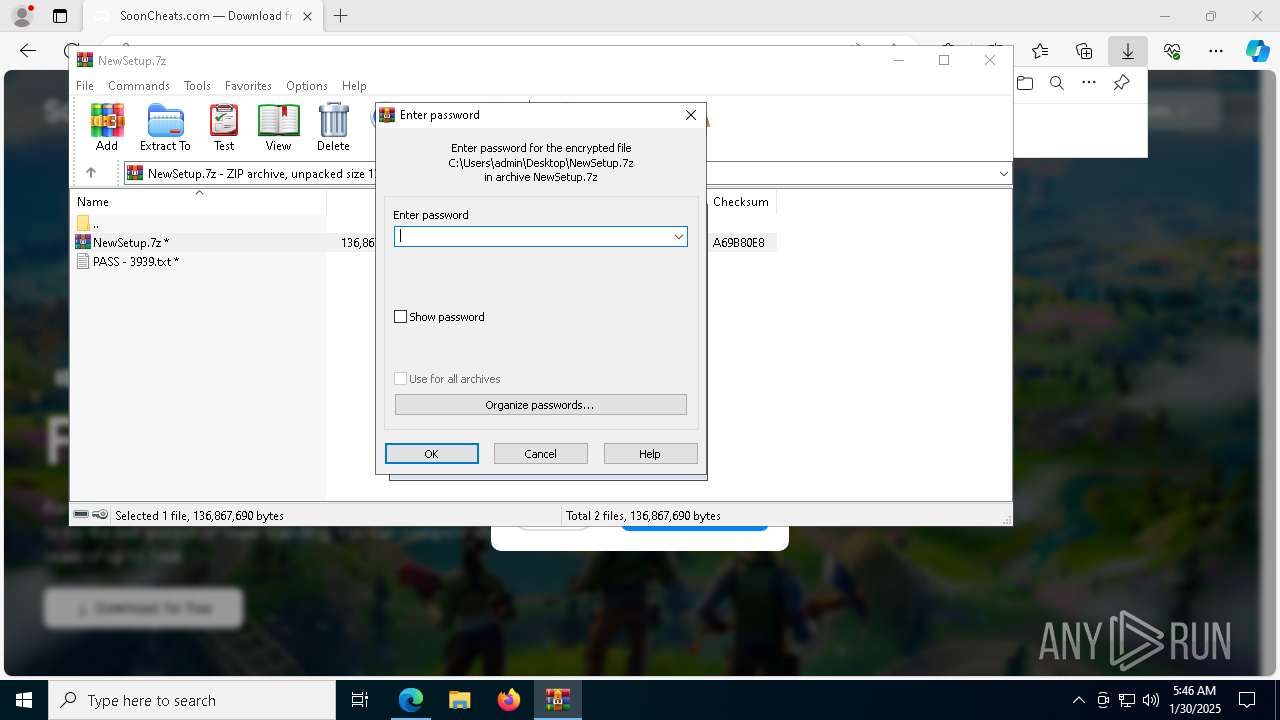
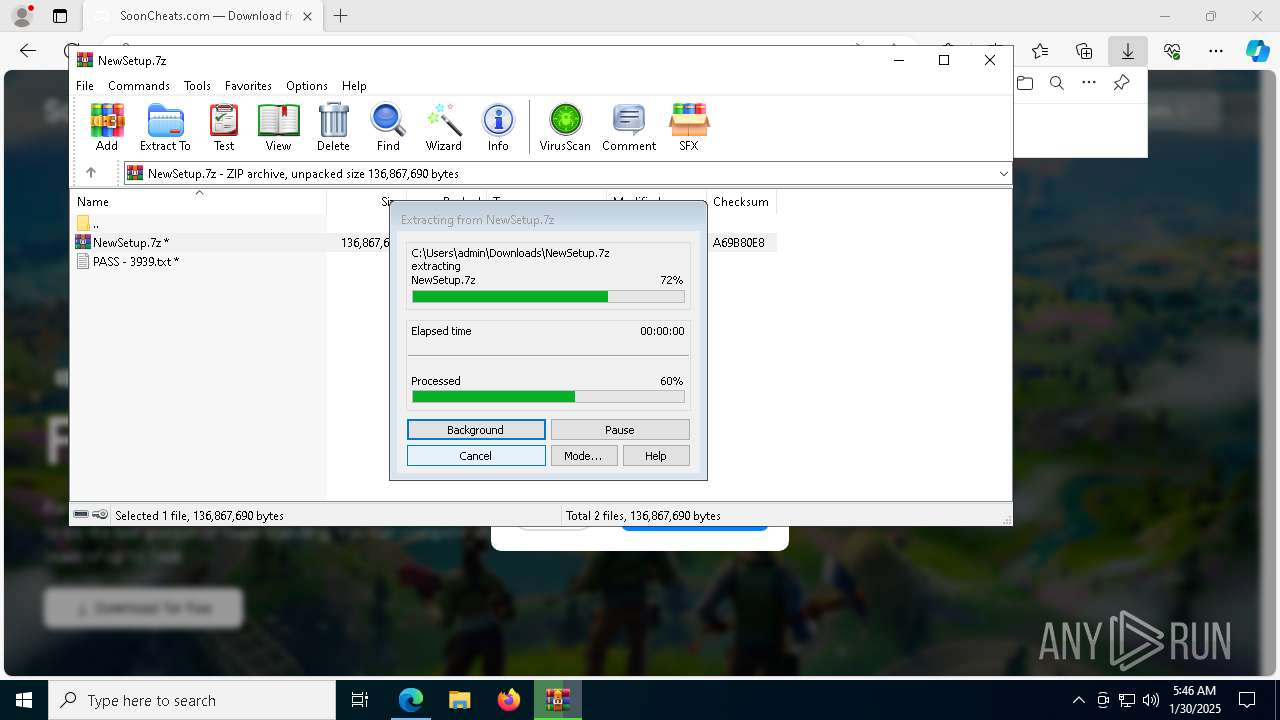
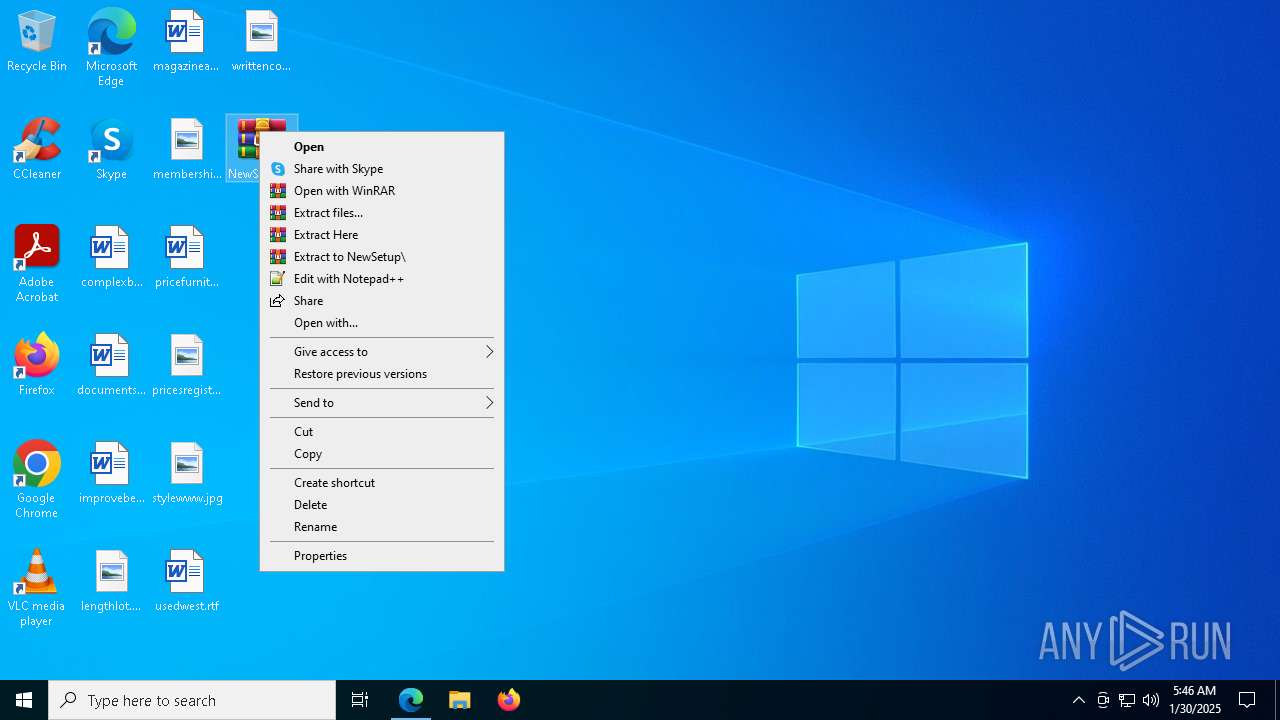
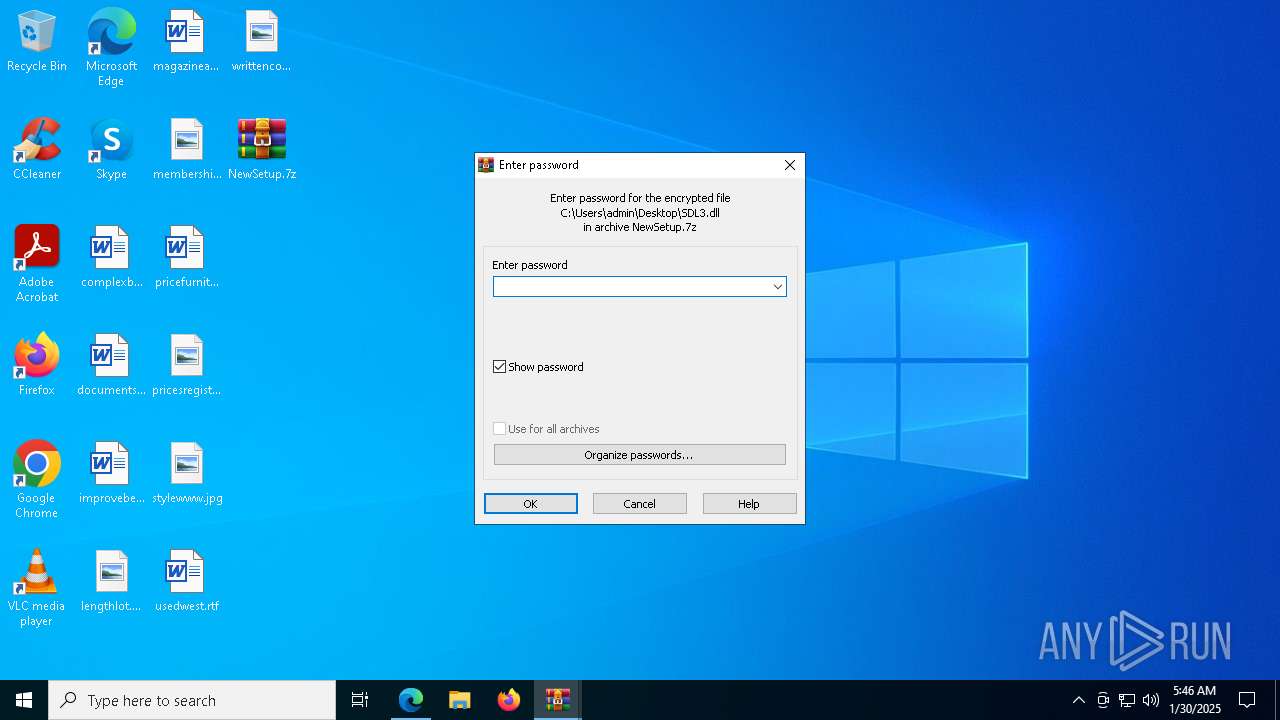
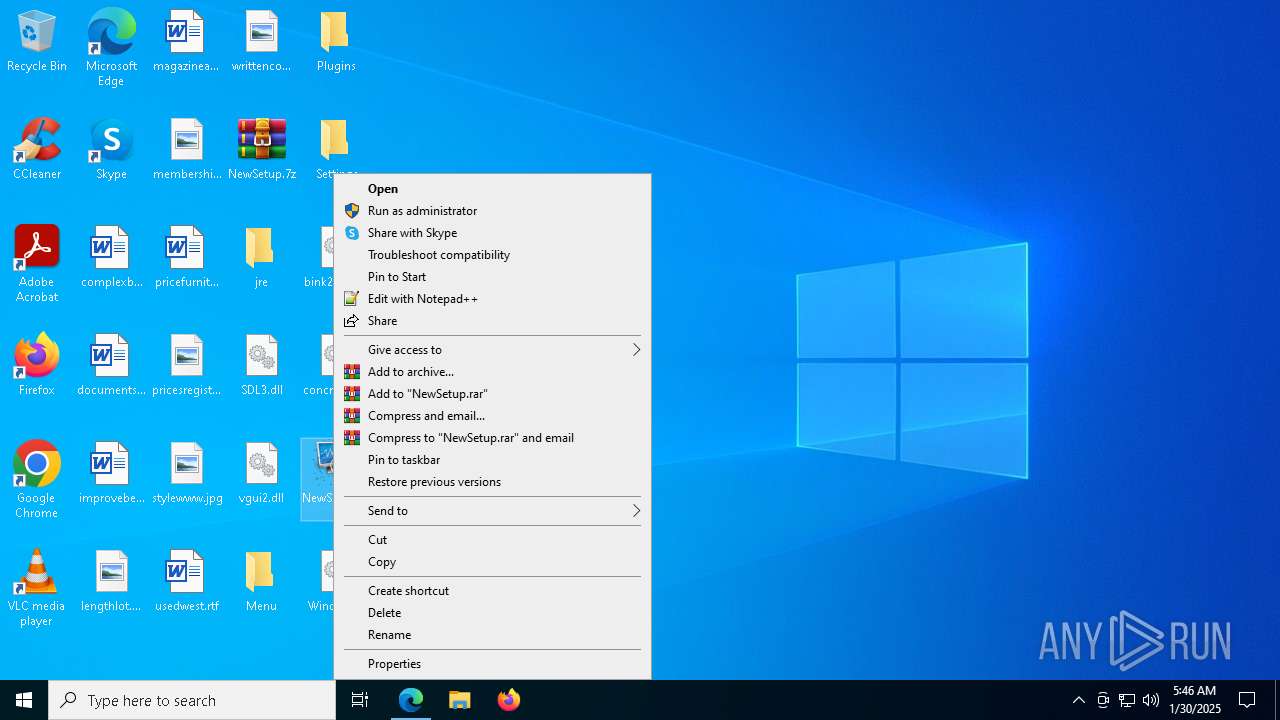
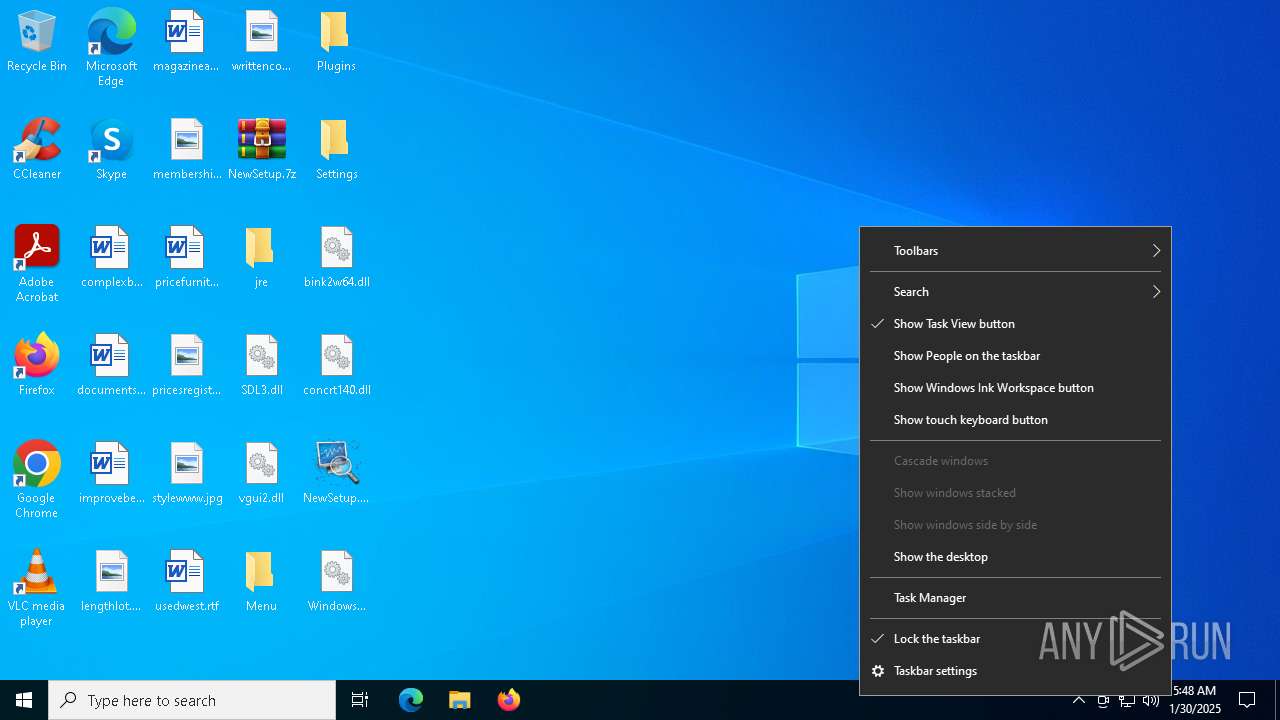
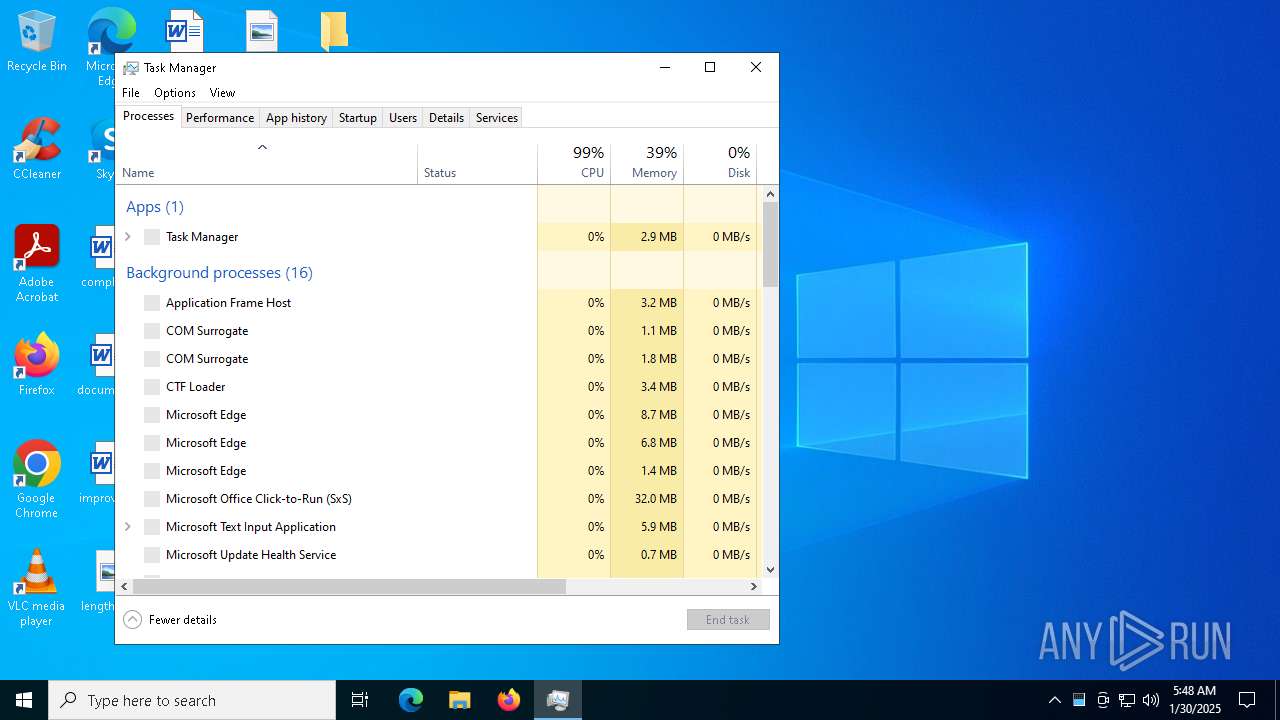
Manual execution by a user
- WinRAR.exe (PID: 7520)
- NewSetup.exe (PID: 3820)
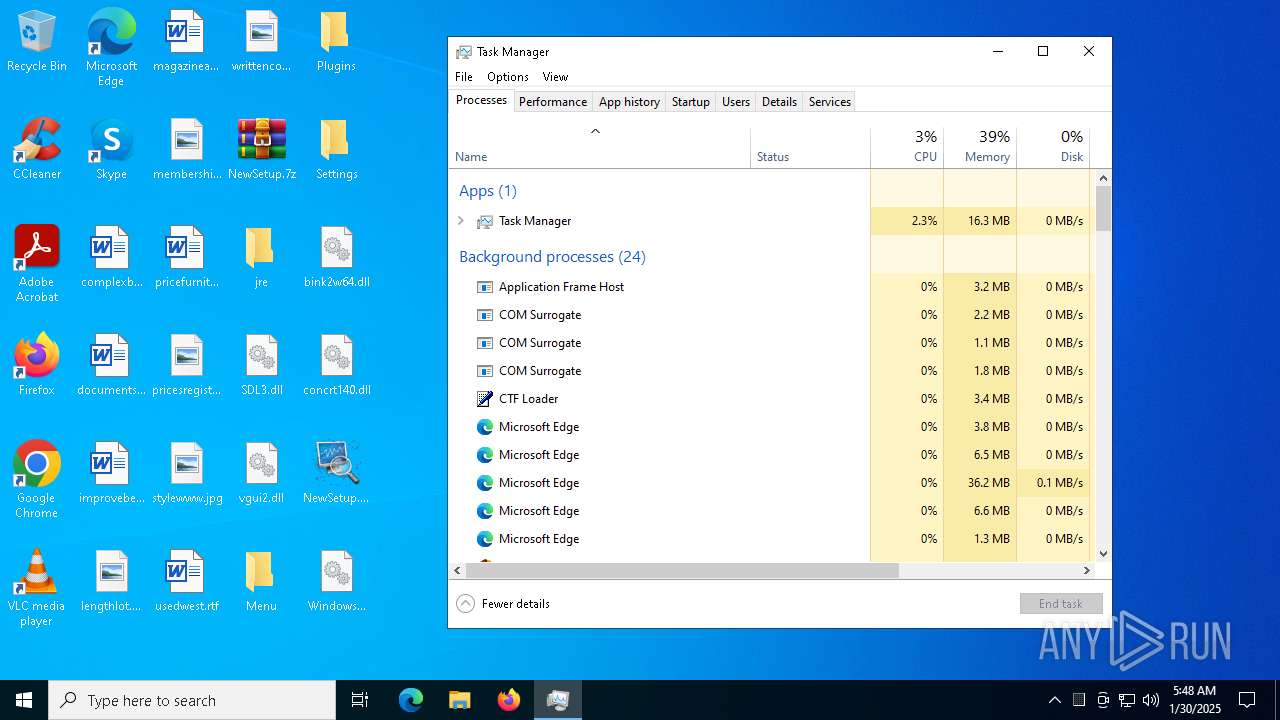
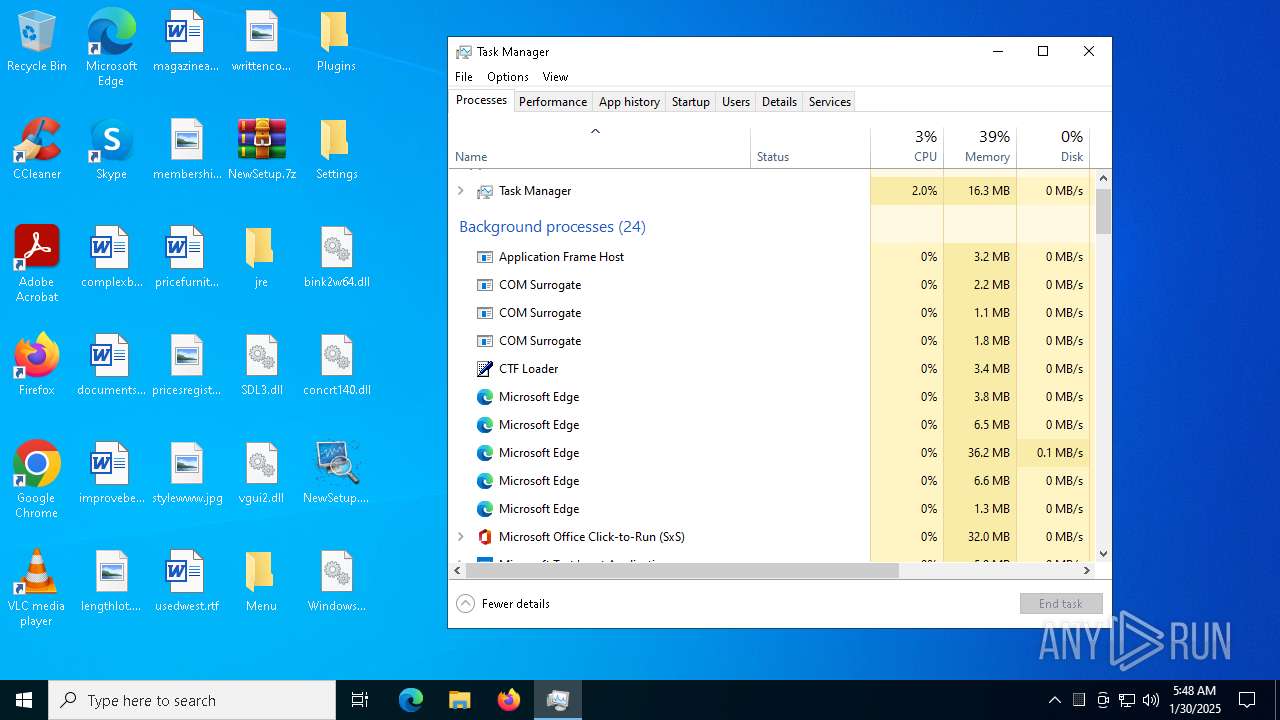
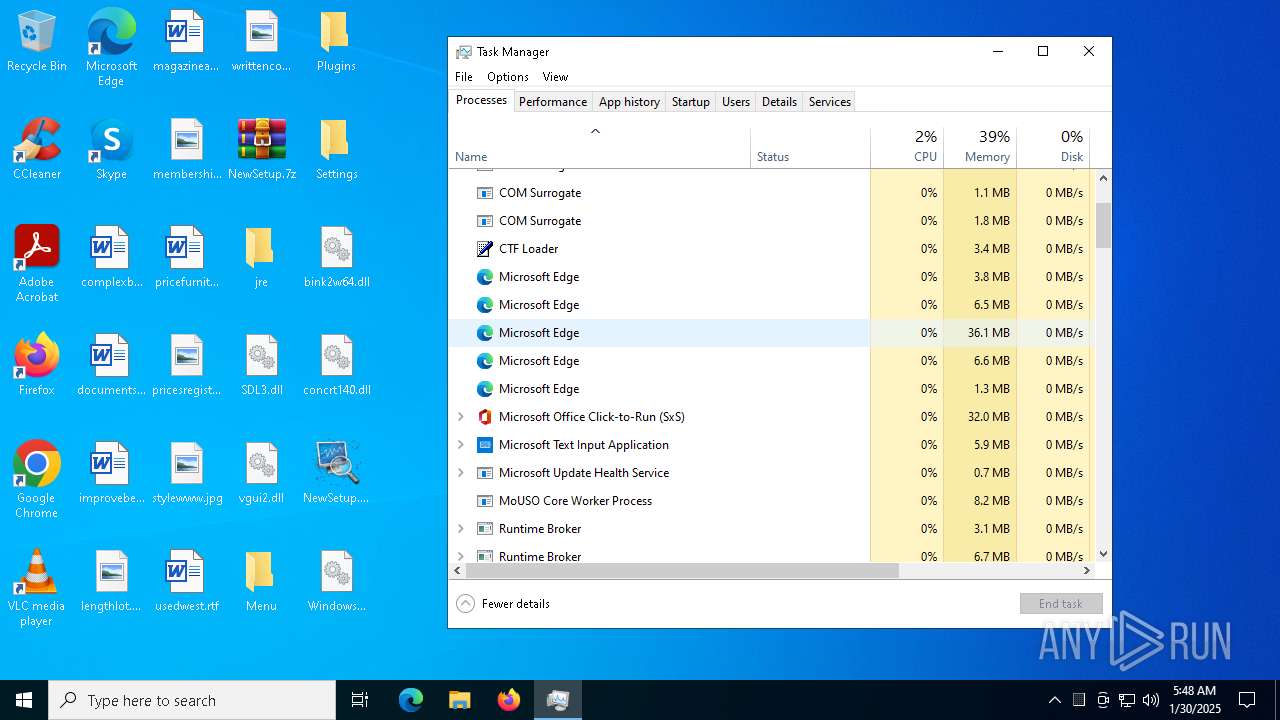
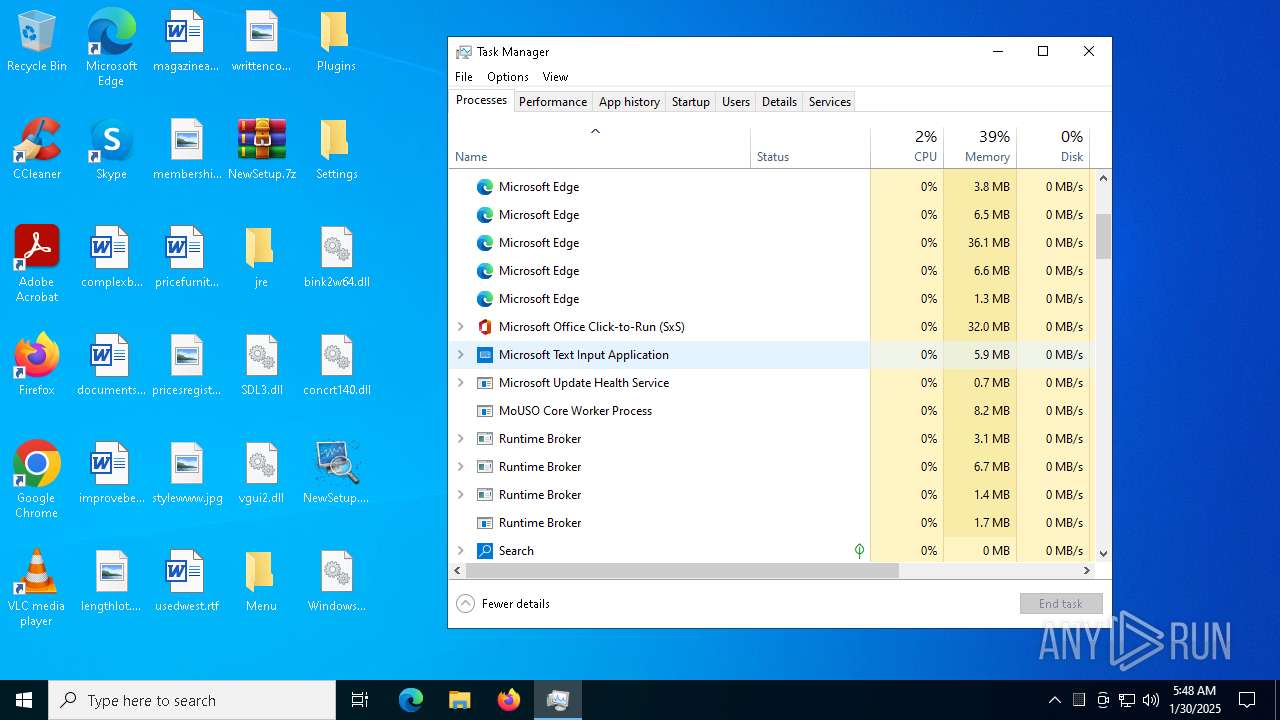
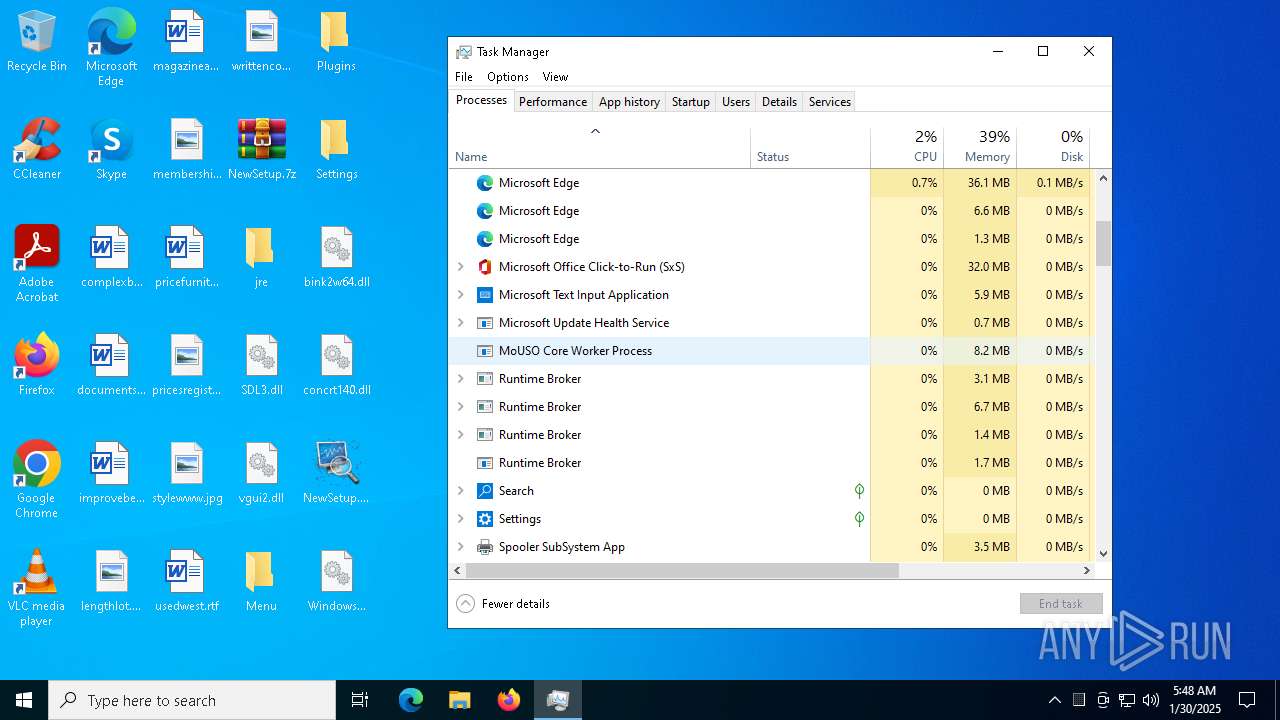
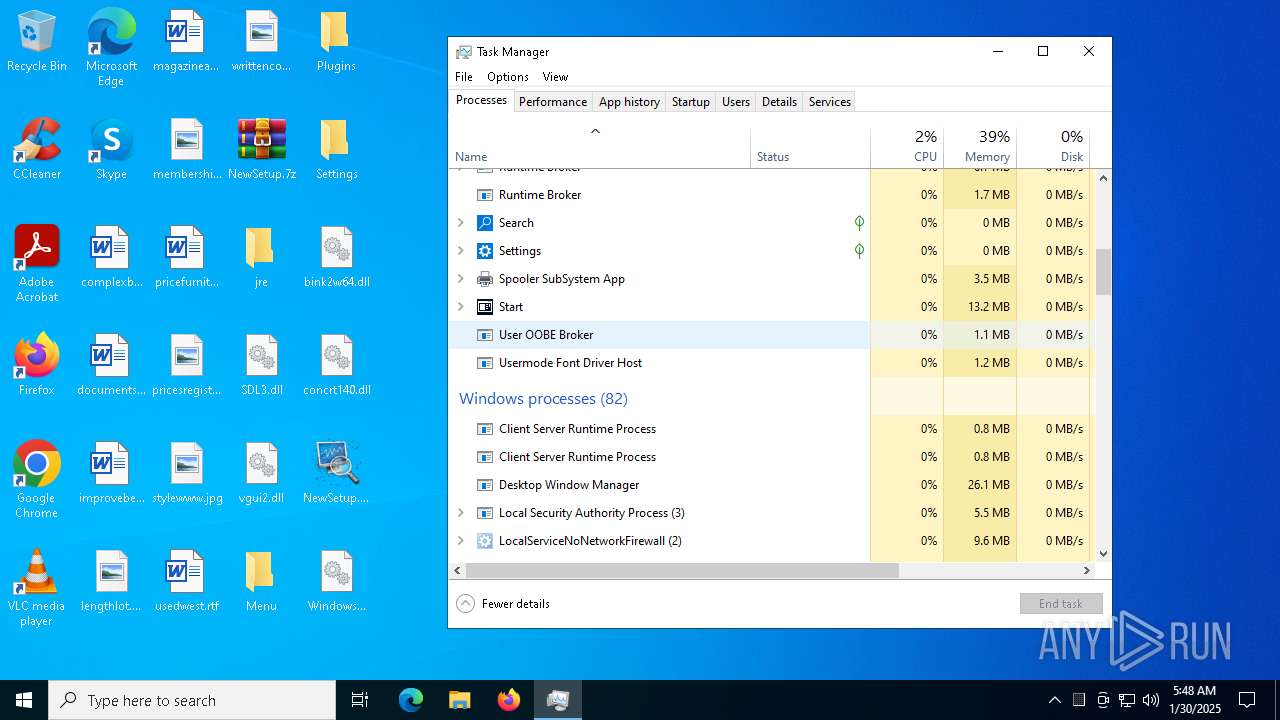
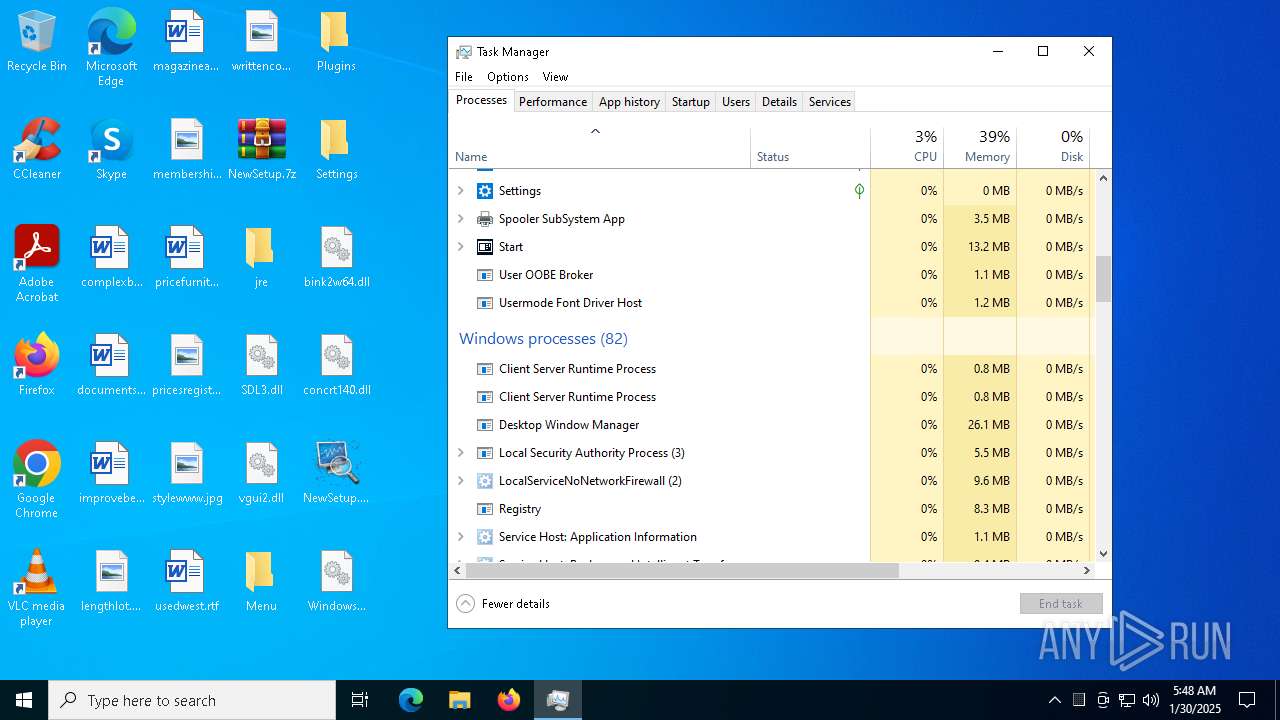
- Taskmgr.exe (PID: 6312)
- Taskmgr.exe (PID: 7604)
- NewSetup.exe (PID: 1448)
- NewSetup.exe (PID: 7288)
- NewSetup.exe (PID: 8140)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 1140)
- NewSetup.exe (PID: 7016)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6760)
- NewSetup.exe (PID: 6780)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 7180)
- NewSetup.exe (PID: 1344)
Reads the computer name
- identity_helper.exe (PID: 8068)
- Ur.com (PID: 1668)
- extrac32.exe (PID: 5980)
- NewSetup.exe (PID: 3820)
- identity_helper.exe (PID: 1572)
- NewSetup.exe (PID: 1448)
- NewSetup.exe (PID: 7288)
- NewSetup.exe (PID: 8140)
- Ur.com (PID: 2148)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 1140)
- NewSetup.exe (PID: 7016)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6760)
- extrac32.exe (PID: 1172)
- NewSetup.exe (PID: 6780)
- NewSetup.exe (PID: 7180)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 1344)
- extrac32.exe (PID: 3812)
- Ur.com (PID: 244)
- extrac32.exe (PID: 1668)
- Ur.com (PID: 8136)
- Ur.com (PID: 7284)
- extrac32.exe (PID: 1192)
Application launched itself
- msedge.exe (PID: 6472)
- msedge.exe (PID: 5388)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7520)
- msedge.exe (PID: 7328)
The sample compiled with english language support
- WinRAR.exe (PID: 7520)
- msedge.exe (PID: 7328)
Process checks computer location settings
- NewSetup.exe (PID: 3820)
- NewSetup.exe (PID: 1448)
- NewSetup.exe (PID: 7288)
- NewSetup.exe (PID: 8140)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 7016)
- NewSetup.exe (PID: 1140)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6760)
- NewSetup.exe (PID: 6780)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 7180)
- NewSetup.exe (PID: 1344)
Create files in a temporary directory
- NewSetup.exe (PID: 3820)
- extrac32.exe (PID: 5980)
- NewSetup.exe (PID: 1448)
- NewSetup.exe (PID: 7288)
- NewSetup.exe (PID: 8140)
- NewSetup.exe (PID: 7904)
- NewSetup.exe (PID: 1140)
- NewSetup.exe (PID: 7016)
- extrac32.exe (PID: 1172)
- NewSetup.exe (PID: 6964)
- NewSetup.exe (PID: 6760)
- NewSetup.exe (PID: 6780)
- NewSetup.exe (PID: 6700)
- NewSetup.exe (PID: 7180)
- extrac32.exe (PID: 3812)
- extrac32.exe (PID: 1192)
- extrac32.exe (PID: 1668)
- NewSetup.exe (PID: 1344)
Creates a new folder
- cmd.exe (PID: 1080)
- cmd.exe (PID: 6212)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 1080)
- cmd.exe (PID: 1796)
Reads mouse settings
- Ur.com (PID: 1668)
- Ur.com (PID: 2148)
- Ur.com (PID: 244)
- Ur.com (PID: 8136)
- Ur.com (PID: 7284)
Reads the software policy settings
- Ur.com (PID: 1668)
- Ur.com (PID: 2148)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 6312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
312
Monitored processes
179
Malicious processes
19
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 244 | Ur.com y | C:\Users\admin\AppData\Local\Temp\173968\Ur.com | — | cmd.exe | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 648 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3872 --field-trial-handle=2384,i,4733320453079115399,8746045362274607706,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1080 | cmd /c md 173968 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | cmd /c md 173968 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1140 | "C:\Users\admin\Desktop\NewSetup.exe" | C:\Users\admin\Desktop\NewSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1172 | extrac32 /Y /E Tree | C:\Windows\SysWOW64\extrac32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® CAB File Extract Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | extrac32 /Y /E Tree | C:\Windows\SysWOW64\extrac32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® CAB File Extract Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | cmd /c copy /b 173968\Ur.com + Clarke + Suggesting + Io + Interpreted + Ser + Integral + Nose + Nam + Sellers + Capability 173968\Ur.com | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | "C:\Users\admin\Desktop\NewSetup.exe" | C:\Users\admin\Desktop\NewSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
22 642
Read events
22 557
Write events
71
Delete events
14
Modification events
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 158F78347C8B2F00 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3C549A347C8B2F00 | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {75EC8E55-2BAD-41AB-8961-4253F8A0D163} | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F7F28997-FD67-4347-925C-A6DF1ECE7E70} | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7394BE86-4341-4561-B10B-5161ADD0B0F2} | |||
| (PID) Process: | (6472) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2937EB347C8B2F00 | |||
Executable files
154
Suspicious files
578
Text files
256
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1360a1.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1360a1.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1360b1.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1360a1.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1360c1.TMP | — | |
MD5:— | SHA256:— | |||
| 6472 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
53
TCP/UDP connections
161
DNS requests
258
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6384 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7232 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738727179&P2=404&P3=2&P4=W3WvuxobLmH6w%2bWkKCCLvGFJgcnRblj3ejD0o%2b7wXktNz%2f8LgqSjITBMPpDeqOClzKLsk%2b%2bg1fbQr6ibr7OyqA%3d%3d | unknown | — | — | whitelisted |
7232 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738727179&P2=404&P3=2&P4=W3WvuxobLmH6w%2bWkKCCLvGFJgcnRblj3ejD0o%2b7wXktNz%2f8LgqSjITBMPpDeqOClzKLsk%2b%2bg1fbQr6ibr7OyqA%3d%3d | unknown | — | — | whitelisted |
6092 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7232 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738727179&P2=404&P3=2&P4=W3WvuxobLmH6w%2bWkKCCLvGFJgcnRblj3ejD0o%2b7wXktNz%2f8LgqSjITBMPpDeqOClzKLsk%2b%2bg1fbQr6ibr7OyqA%3d%3d | unknown | — | — | whitelisted |
7232 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1738727179&P2=404&P3=2&P4=W3WvuxobLmH6w%2bWkKCCLvGFJgcnRblj3ejD0o%2b7wXktNz%2f8LgqSjITBMPpDeqOClzKLsk%2b%2bg1fbQr6ibr7OyqA%3d%3d | unknown | — | — | whitelisted |
7408 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6092 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1076 | svchost.exe | 184.30.18.9:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
6472 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6808 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6808 | msedge.exe | 151.101.193.111:443 | i.guim.co.uk | FASTLY | US | whitelisted |
6808 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
config.edge.skype.com |
| whitelisted |
sooncheats.com |
| unknown |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
i.playground.ru |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
6808 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6808 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |