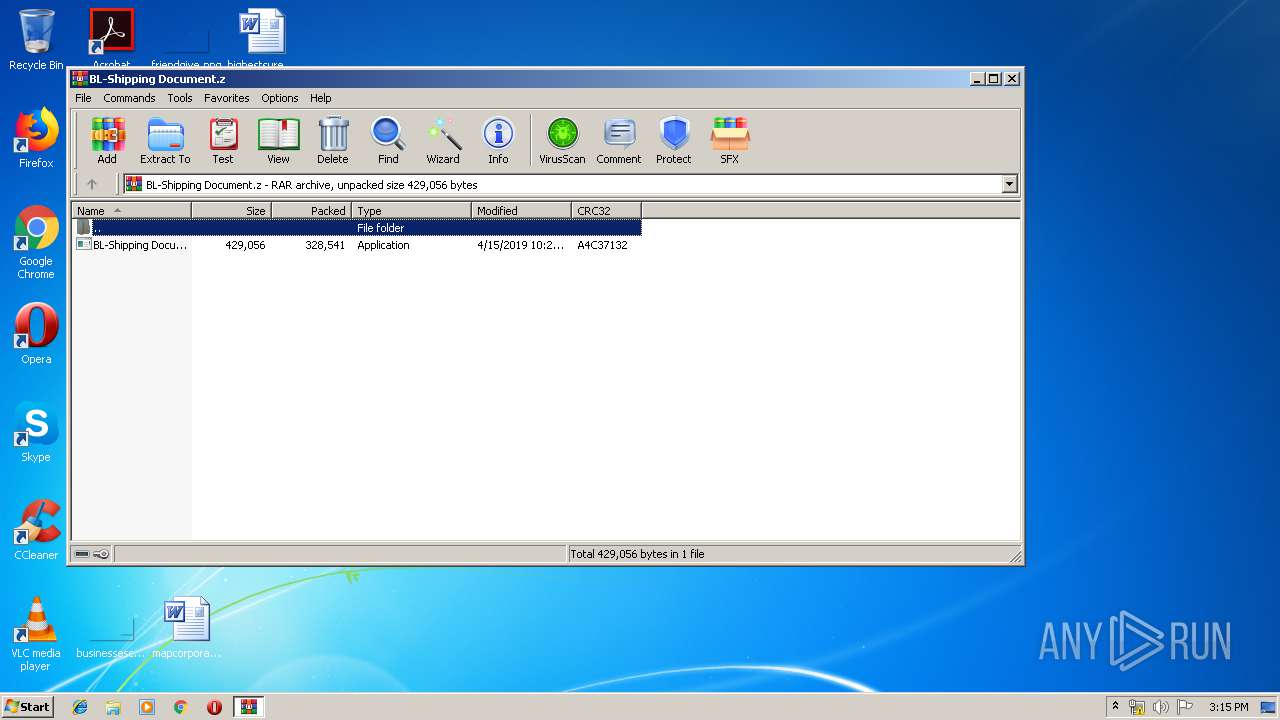
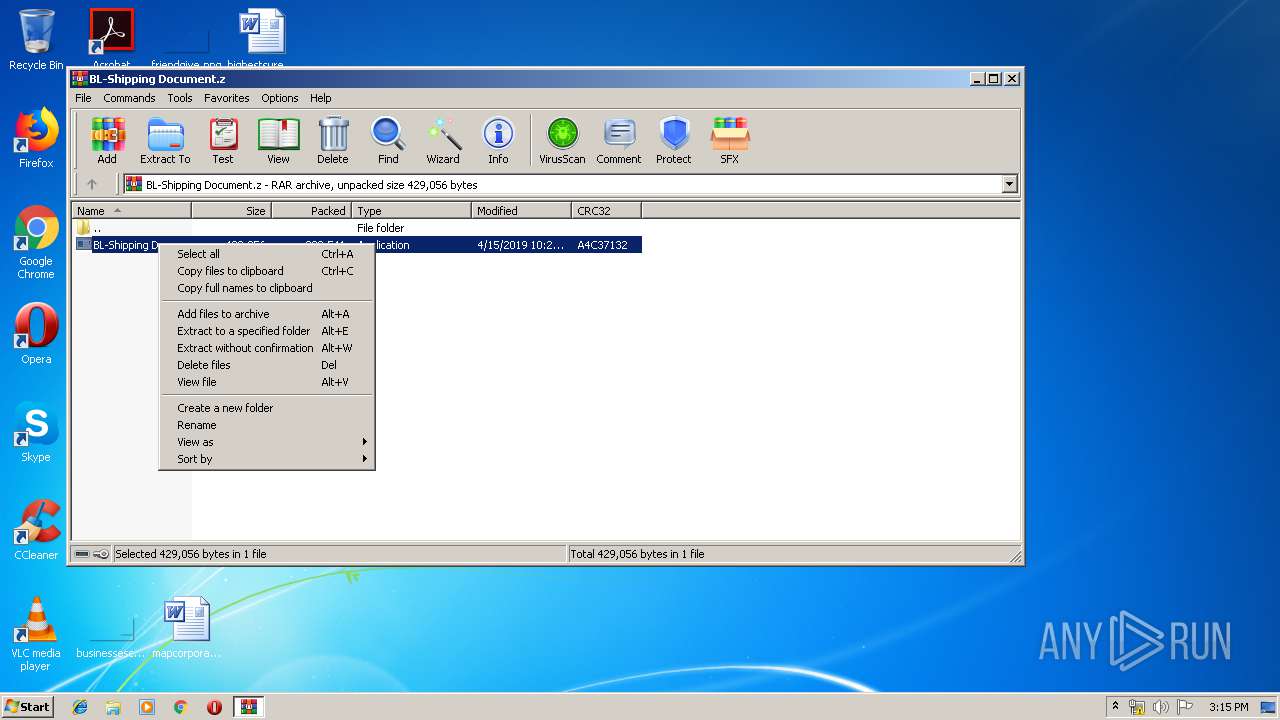
| File name: | BL-Shipping Document.z |
| Full analysis: | https://app.any.run/tasks/68c6d268-e0c7-4cdf-85e9-41308e75a155 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | April 15, 2019, 14:14:35 |
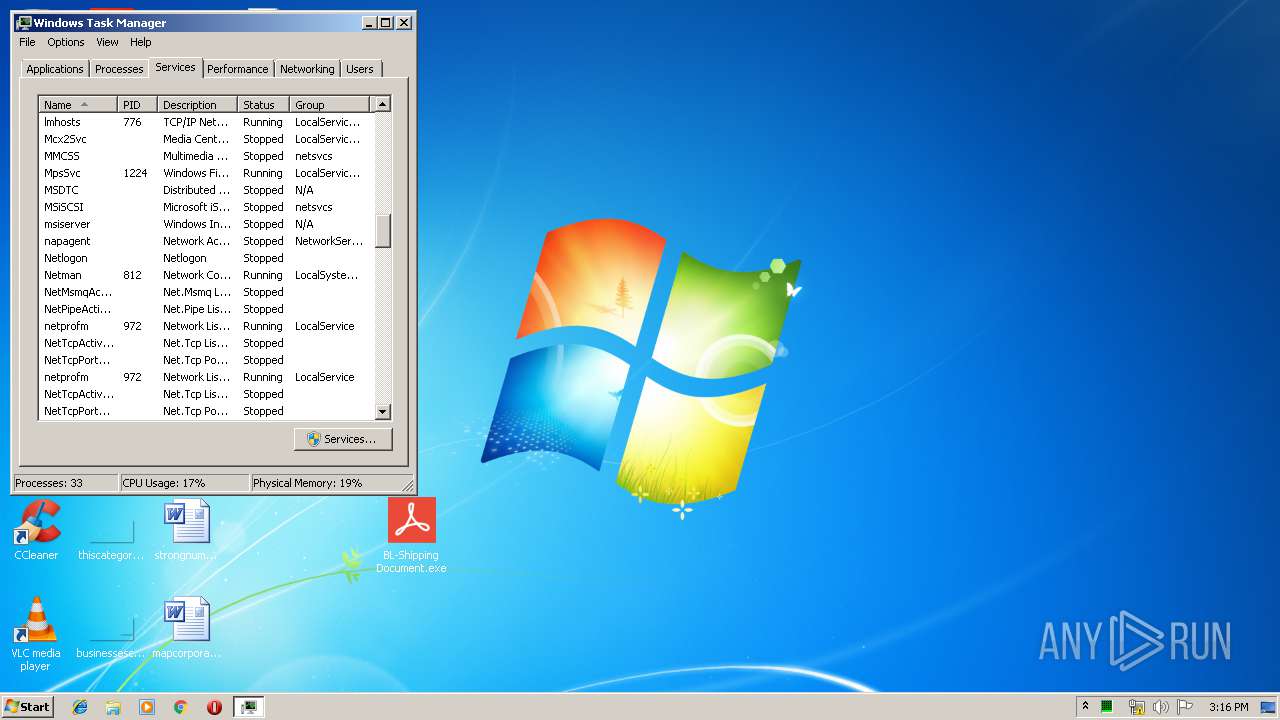
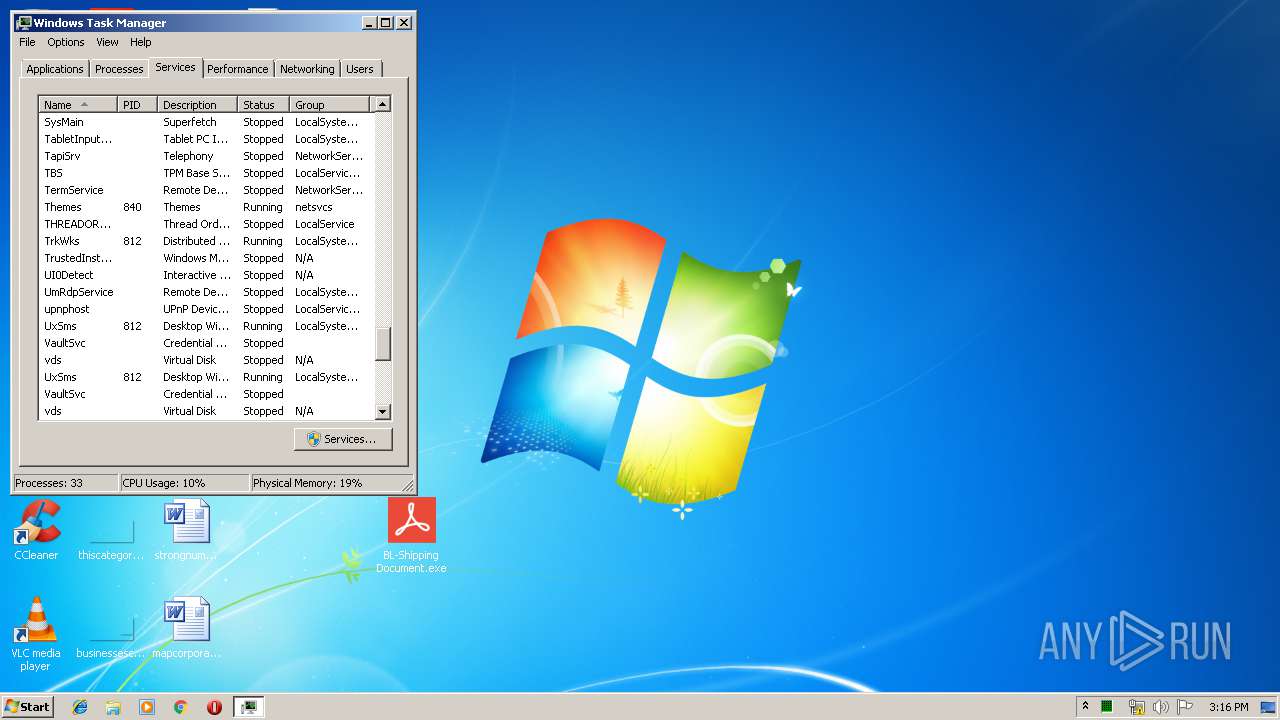
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
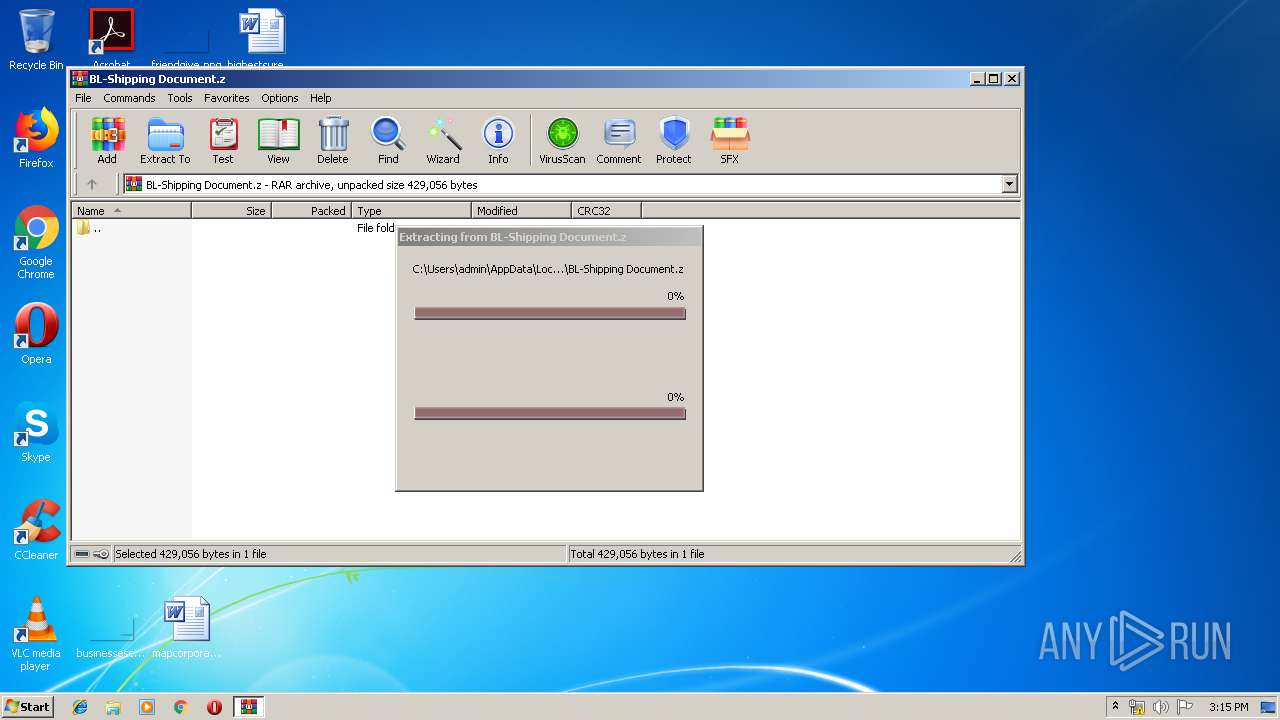
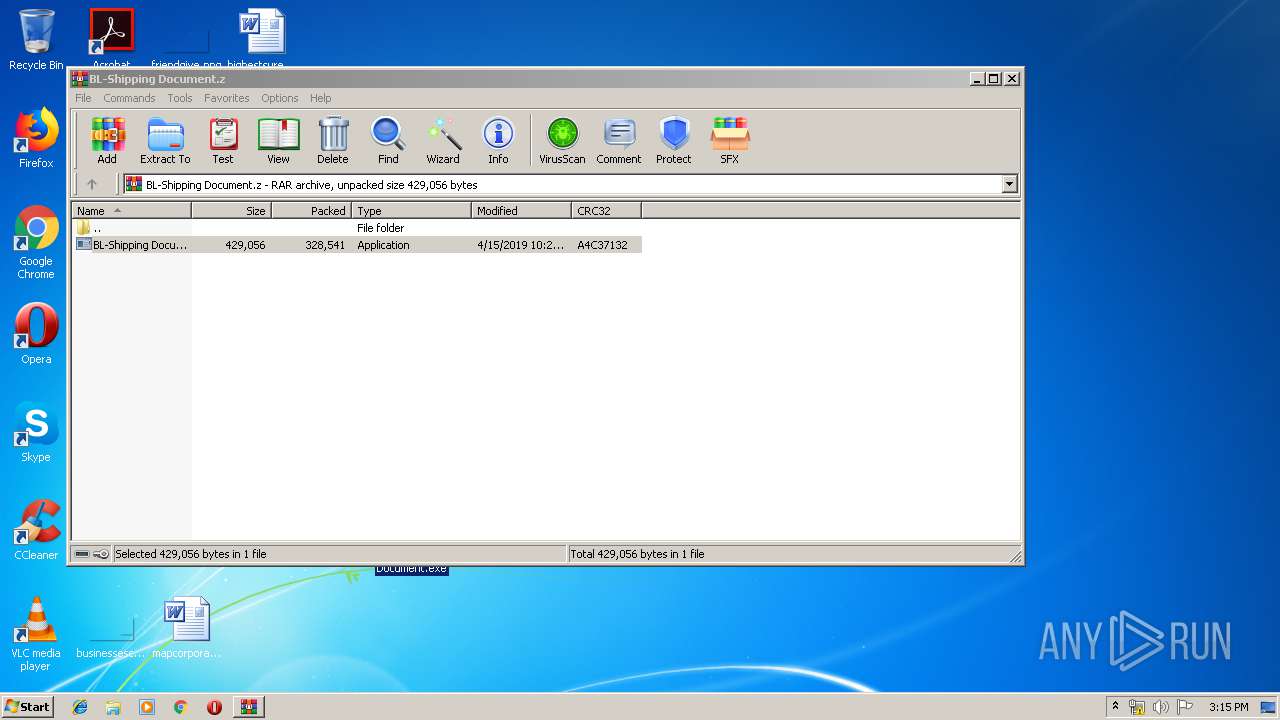
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7F661B3BCB97F60BF0A2E14A1E0250BD |
| SHA1: | 534D39327BF46B9610A2C37BCA8358521E2BD329 |
| SHA256: | 379D004FDAEC6621395A116D8204EDEDC39DE34EE304788BE6A722F0C0C3740A |
| SSDEEP: | 6144:bay3UP6ry+qzjd8pRv+2YtSA7bTpKhA1qyRGIrk7frlRoQjUPoJfGsRG9QL:bay3k62+cGpN+Tssbt9TrkDsI2oJfG0L |
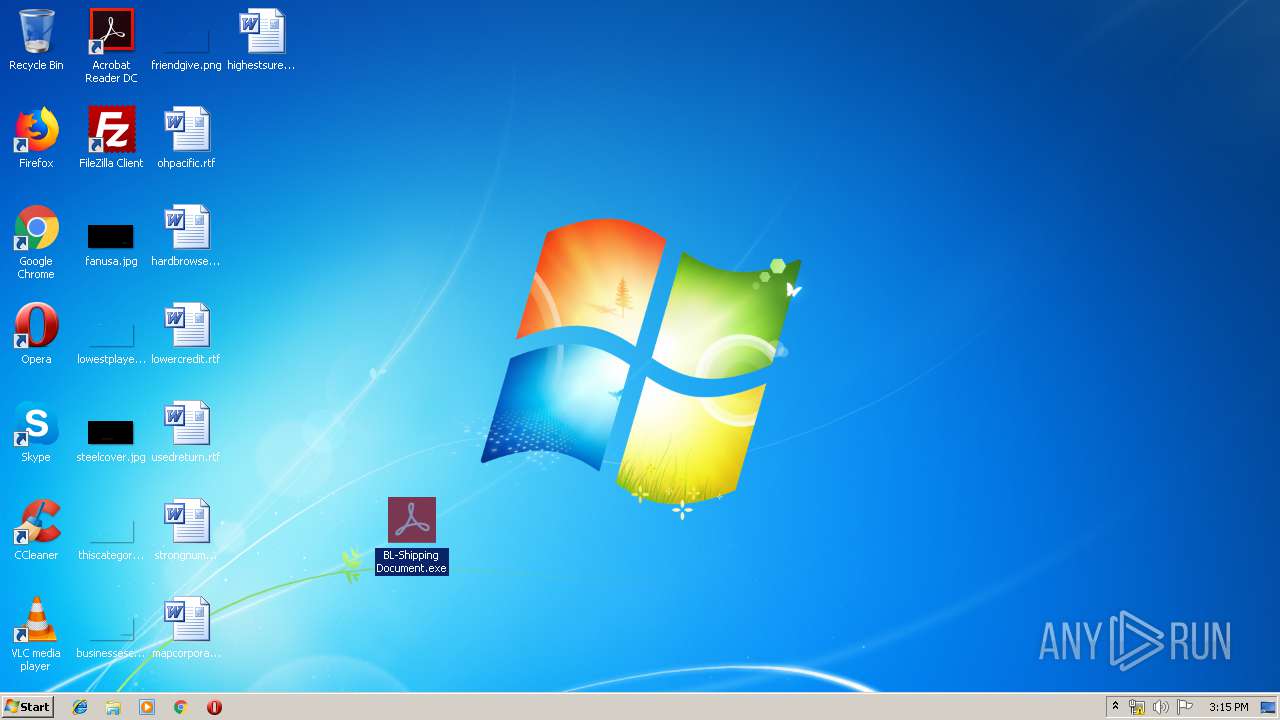
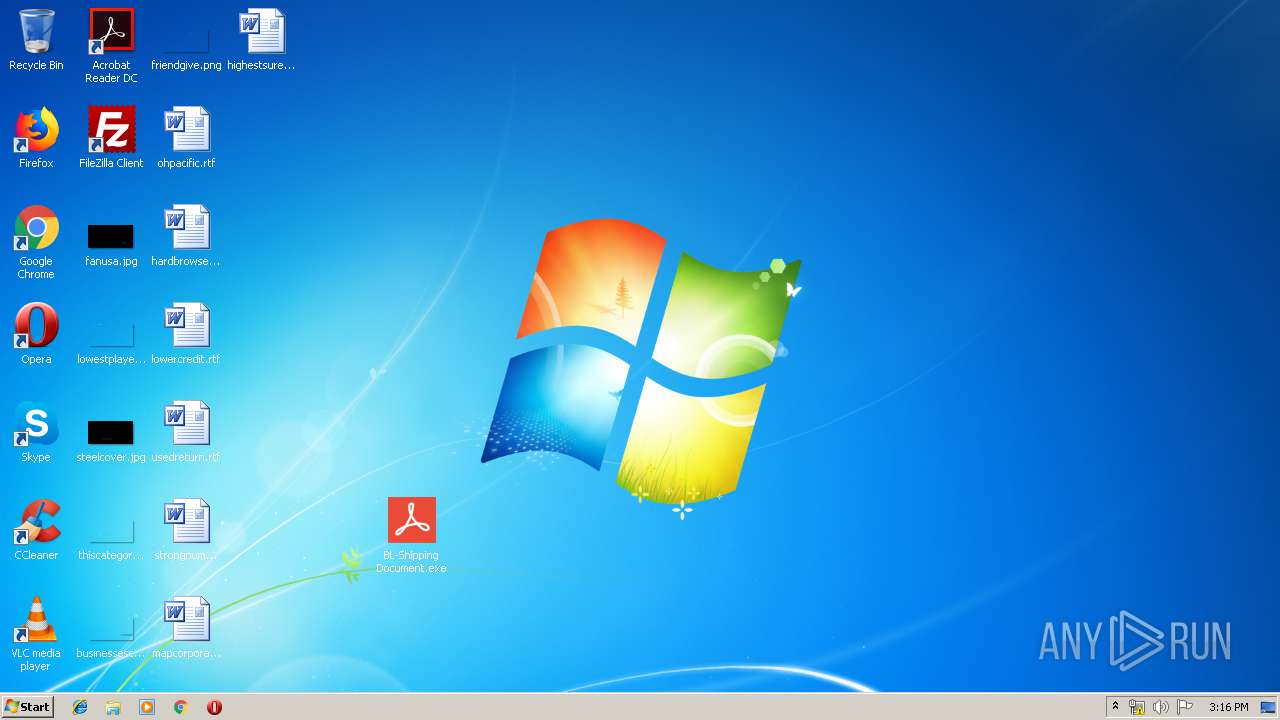
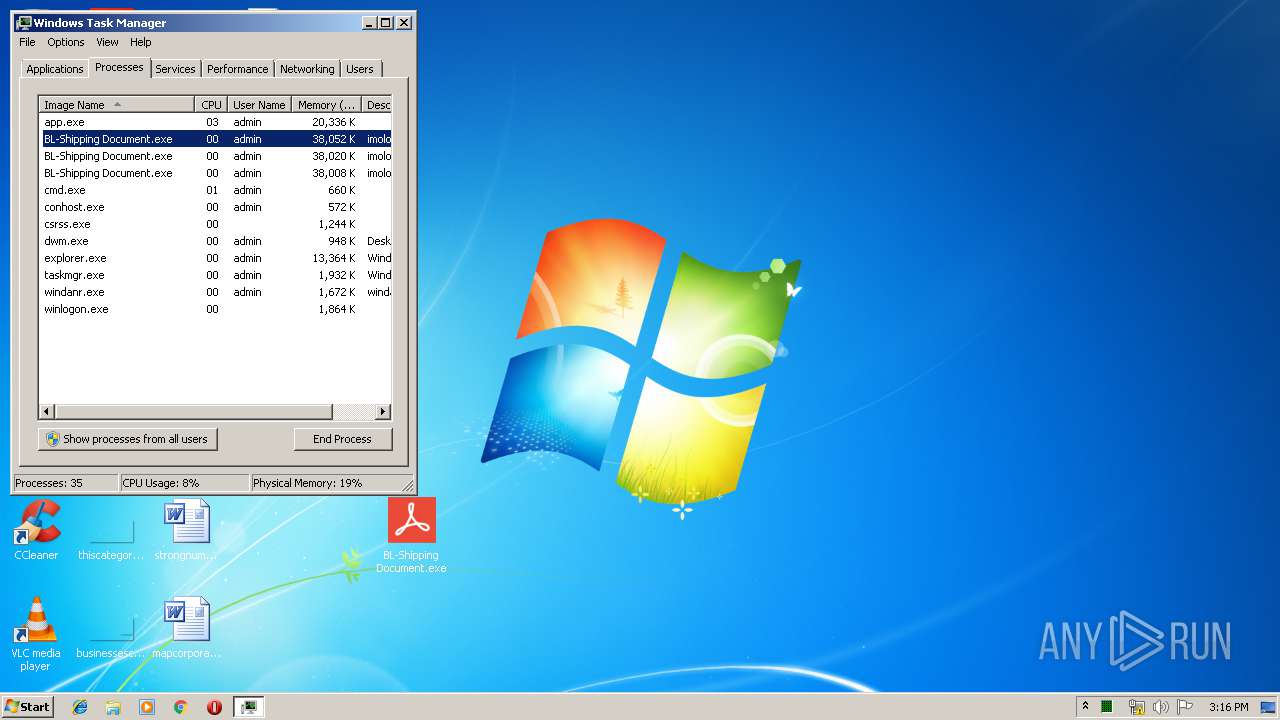
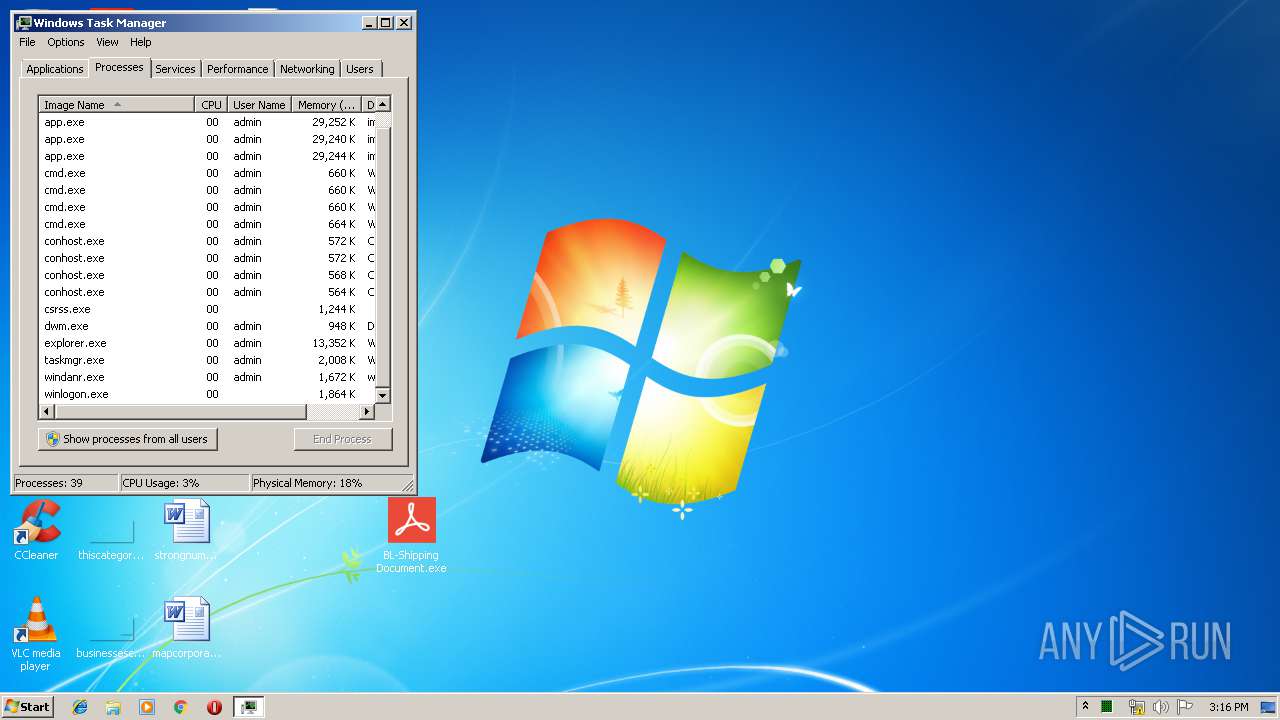
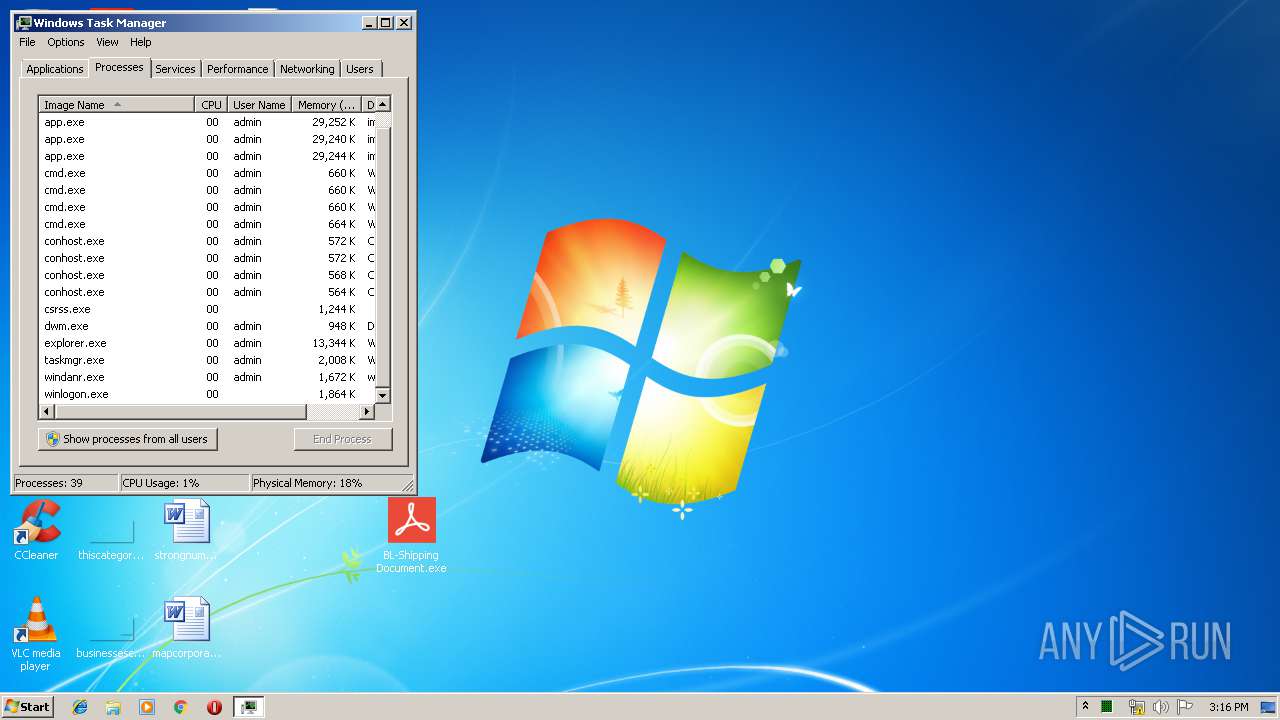
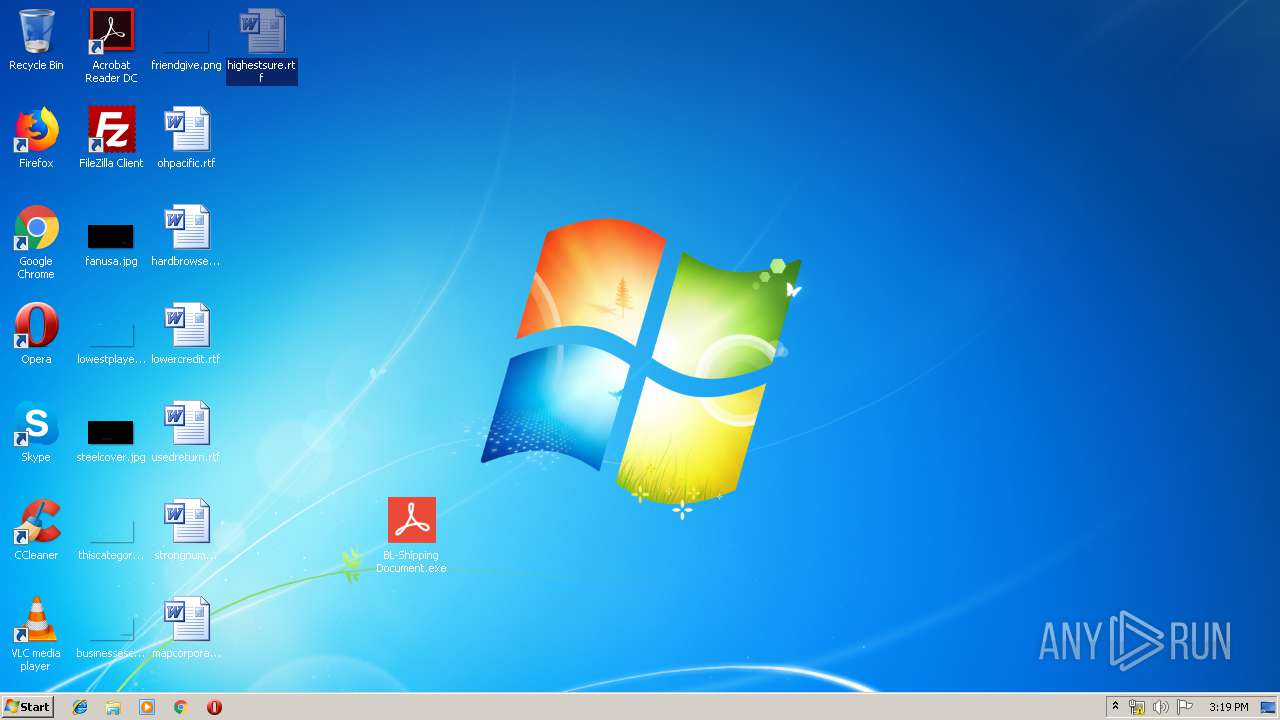
MALICIOUS
Application was dropped or rewritten from another process
- BL-Shipping Document.exe (PID: 1712)
- BL-Shipping Document.exe (PID: 3092)
- BL-Shipping Document.exe (PID: 1724)
- app.exe (PID: 1976)
- BL-Shipping Document.exe (PID: 3592)
- BL-Shipping Document.exe (PID: 3876)
- app.exe (PID: 3932)
- BL-Shipping Document.exe (PID: 2484)
- app.exe (PID: 1892)
- app.exe (PID: 2604)
- app.exe (PID: 2504)
- app.exe (PID: 2120)
- app.exe (PID: 2564)
- app.exe (PID: 2140)
- app.exe (PID: 356)
- BL-Shipping Document.exe (PID: 3156)
- mfcnvch.exe (PID: 1732)
- app.exe (PID: 3804)
- app.exe (PID: 4036)
Changes the autorun value in the registry
- app.exe (PID: 2504)
- wuapp.exe (PID: 2476)
Formbook was detected
- wuapp.exe (PID: 2476)
- Firefox.exe (PID: 3440)
FORMBOOK was detected
- explorer.exe (PID: 116)
Connects to CnC server
- explorer.exe (PID: 116)
Actions looks like stealing of personal data
- wuapp.exe (PID: 2476)
Stealing of credential data
- wuapp.exe (PID: 2476)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2580)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 2172)
- explorer.exe (PID: 116)
- DllHost.exe (PID: 332)
- cmd.exe (PID: 912)
Starts CMD.EXE for commands execution
- BL-Shipping Document.exe (PID: 1712)
- BL-Shipping Document.exe (PID: 3092)
- BL-Shipping Document.exe (PID: 3592)
- BL-Shipping Document.exe (PID: 3156)
- BL-Shipping Document.exe (PID: 2484)
- BL-Shipping Document.exe (PID: 3876)
- wuapp.exe (PID: 2476)
- mfcnvch.exe (PID: 1732)
Creates files in the user directory
- cmd.exe (PID: 4036)
- cmd.exe (PID: 2556)
- cmd.exe (PID: 2844)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 3424)
- cmd.exe (PID: 2172)
- wuapp.exe (PID: 2476)
- cmd.exe (PID: 912)
- explorer.exe (PID: 116)
Application launched itself
- app.exe (PID: 2504)
- app.exe (PID: 2120)
- app.exe (PID: 2564)
- app.exe (PID: 4036)
Uses NETSH.EXE for network configuration
- explorer.exe (PID: 116)
Creates files in the program directory
- DllHost.exe (PID: 332)
Loads DLL from Mozilla Firefox
- wuapp.exe (PID: 2476)
Reads Internet Cache Settings
- explorer.exe (PID: 116)
INFO
Creates files in the user directory
- Firefox.exe (PID: 3440)
- WINWORD.EXE (PID: 2772)
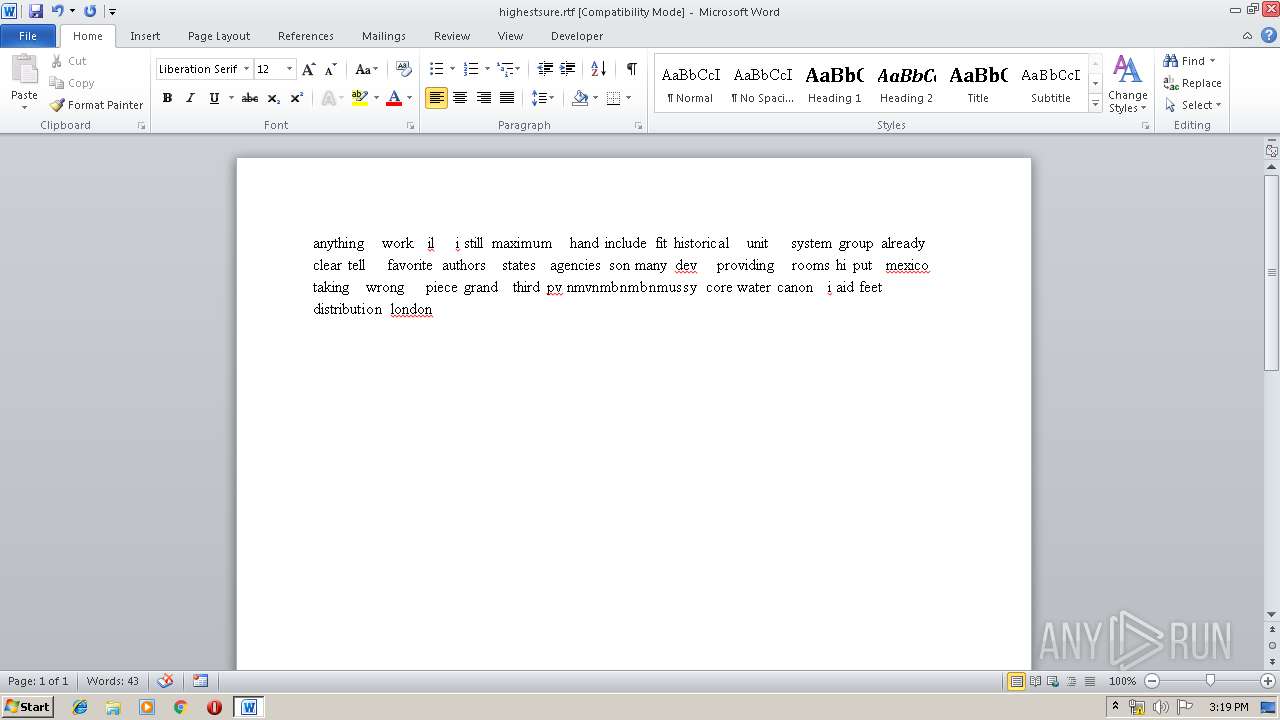
Starts Microsoft Office Application
- explorer.exe (PID: 116)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
95
Monitored processes
44
Malicious processes
12
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 332 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 356 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe | — | app.exe | |||||||||||
User: admin Company: ukojovacosocahoqozomusew Integrity Level: MEDIUM Description: imolowuv Exit code: 0 Version: 7.10.14.17 Modules
| |||||||||||||||
| 896 | "C:\Windows\System32\NAPSTAT.EXE" | C:\Windows\System32\NAPSTAT.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Access Protection Client UI Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 912 | "C:\Windows\System32\cmd.exe" /c copy "C:\Program Files\Rmnvd\mfcnvch.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe" | C:\Windows\System32\cmd.exe | mfcnvch.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 928 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1712 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2580.21486\BL-Shipping Document.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2580.21486\BL-Shipping Document.exe | WinRAR.exe | ||||||||||||
User: admin Company: ukojovacosocahoqozomusew Integrity Level: MEDIUM Description: imolowuv Exit code: 0 Version: 7.10.14.17 Modules
| |||||||||||||||
| 1724 | "C:\Users\admin\Desktop\BL-Shipping Document.exe" | C:\Users\admin\Desktop\BL-Shipping Document.exe | explorer.exe | ||||||||||||
User: admin Company: ukojovacosocahoqozomusew Integrity Level: MEDIUM Description: imolowuv Exit code: 0 Version: 7.10.14.17 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Rmnvd\mfcnvch.exe" | C:\Program Files\Rmnvd\mfcnvch.exe | explorer.exe | ||||||||||||
User: admin Company: ukojovacosocahoqozomusew Integrity Level: MEDIUM Description: imolowuv Exit code: 0 Version: 7.10.14.17 Modules
| |||||||||||||||
| 1892 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe | cmd.exe | ||||||||||||
User: admin Company: ukojovacosocahoqozomusew Integrity Level: MEDIUM Description: imolowuv Exit code: 0 Version: 7.10.14.17 Modules
| |||||||||||||||
Total events
4 485
Read events
4 324
Write events
150
Delete events
11
Modification events
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\BL-Shipping Document.z | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2580) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.z\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
| (PID) Process: | (116) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.z\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
Executable files
10
Suspicious files
72
Text files
4
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2580.24295\BL-Shipping Document.exe | — | |
MD5:— | SHA256:— | |||
| 3808 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe | — | |
MD5:— | SHA256:— | |||
| 3424 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe | — | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC490.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2580 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2580.21486\BL-Shipping Document.exe | executable | |
MD5:— | SHA256:— | |||
| 4036 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe | executable | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\Desktop\BL-Shipping Document.exe | executable | |
MD5:— | SHA256:— | |||
| 116 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Rmnvd\mfcnvch.exe | executable | |
MD5:— | SHA256:— | |||
| 2844 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\app.exe | executable | |
MD5:— | SHA256:— | |||
| 2772 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{17642523-9474-4F78-A910-98A412839836}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
21
DNS requests
8
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
116 | explorer.exe | GET | — | 94.136.40.82:80 | http://www.havenfundingplc.com/ro/?kJ_hzl=gngtuFTmm1cjhukovIVuwodNiZOgQl36WLWns8zxRUfuBnYnpdKkcebkCZMt73TFkXaaow==&KtcDu=LXyLw0&sql=1 | GB | — | — | malicious |
116 | explorer.exe | GET | — | 35.246.6.109:80 | http://www.juchheimcosmetic.com/ro/?kJ_hzl=hjG4RSAFHz+4InyBNYj4hFQuhT7AQs3Ek6ZK6i/WXe5652yoLuLBGbQxkdV988dkBZmJGA==&KtcDu=LXyLw0&sql=1 | US | — | — | malicious |
116 | explorer.exe | POST | — | 94.136.40.82:80 | http://www.havenfundingplc.com/ro/ | GB | — | — | malicious |
116 | explorer.exe | GET | 403 | 23.227.38.64:80 | http://www.ootdinsider.com/ro/?kJ_hzl=ZkaziJdOjxrCyGeBMSXGsMhNMvo3uWQFChLTqVbtF0hmt6KhW/zPNTejh8AL+q0KJpEgyg==&KtcDu=LXyLw0 | CA | html | 1.74 Kb | malicious |
116 | explorer.exe | POST | — | 94.136.40.82:80 | http://www.havenfundingplc.com/ro/ | GB | — | — | malicious |
116 | explorer.exe | POST | — | 94.136.40.82:80 | http://www.havenfundingplc.com/ro/ | GB | — | — | malicious |
116 | explorer.exe | POST | — | 104.217.167.211:80 | http://www.lerensex.com/ro/ | US | — | — | malicious |
116 | explorer.exe | POST | — | 104.217.167.211:80 | http://www.lerensex.com/ro/ | US | — | — | malicious |
116 | explorer.exe | POST | — | 104.217.167.211:80 | http://www.lerensex.com/ro/ | US | — | — | malicious |
116 | explorer.exe | POST | — | 192.0.78.203:80 | http://www.globalartistdigitall.com/ro/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
116 | explorer.exe | 104.217.167.211:80 | www.lerensex.com | Psychz Networks | US | malicious |
116 | explorer.exe | 192.0.78.203:80 | www.globalartistdigitall.com | Automattic, Inc | US | malicious |
116 | explorer.exe | 35.246.6.109:80 | www.juchheimcosmetic.com | — | US | malicious |
116 | explorer.exe | 5.133.220.154:80 | www.newcasinouk.com | Obenetwork AB | SE | malicious |
— | — | 23.227.38.64:80 | www.ootdinsider.com | Shopify, Inc. | CA | malicious |
116 | explorer.exe | 94.136.40.82:80 | www.havenfundingplc.com | Host Europe GmbH | GB | malicious |
— | — | 94.136.40.82:80 | www.havenfundingplc.com | Host Europe GmbH | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ootdinsider.com |
| malicious |
www.lerensex.com |
| malicious |
www.workrowser.net |
| unknown |
www.globalartistdigitall.com |
| malicious |
www.juchheimcosmetic.com |
| malicious |
www.newcasinouk.com |
| malicious |
www.havenfundingplc.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
116 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
15 ETPRO signatures available at the full report
Process | Message |
|---|---|
BL-Shipping Document.exe |
*** Status originated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\id_parser.cpp, line 590
|
BL-Shipping Document.exe |
*** Status propagated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 147
|
BL-Shipping Document.exe |
*** Status originated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\id_parser.cpp, line 590
|
BL-Shipping Document.exe |
*** Status propagated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 147
|
app.exe |
*** Status originated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\id_parser.cpp, line 590
|
app.exe |
*** Status propagated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 147
|
BL-Shipping Document.exe |
*** Status originated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\id_parser.cpp, line 590
|
BL-Shipping Document.exe |
*** Status propagated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 147
|
app.exe |
*** Status originated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\id_parser.cpp, line 590
|
app.exe |
*** Status propagated: -1072365543
*** Source File: d:\iso_whid\x86fre\base\isolation\com\identityauthority.cpp, line 147
|