| File name: | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe |
| Full analysis: | https://app.any.run/tasks/4a83f865-c587-4020-84ec-20f96f44b4fd |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | March 28, 2026, 01:26:54 |
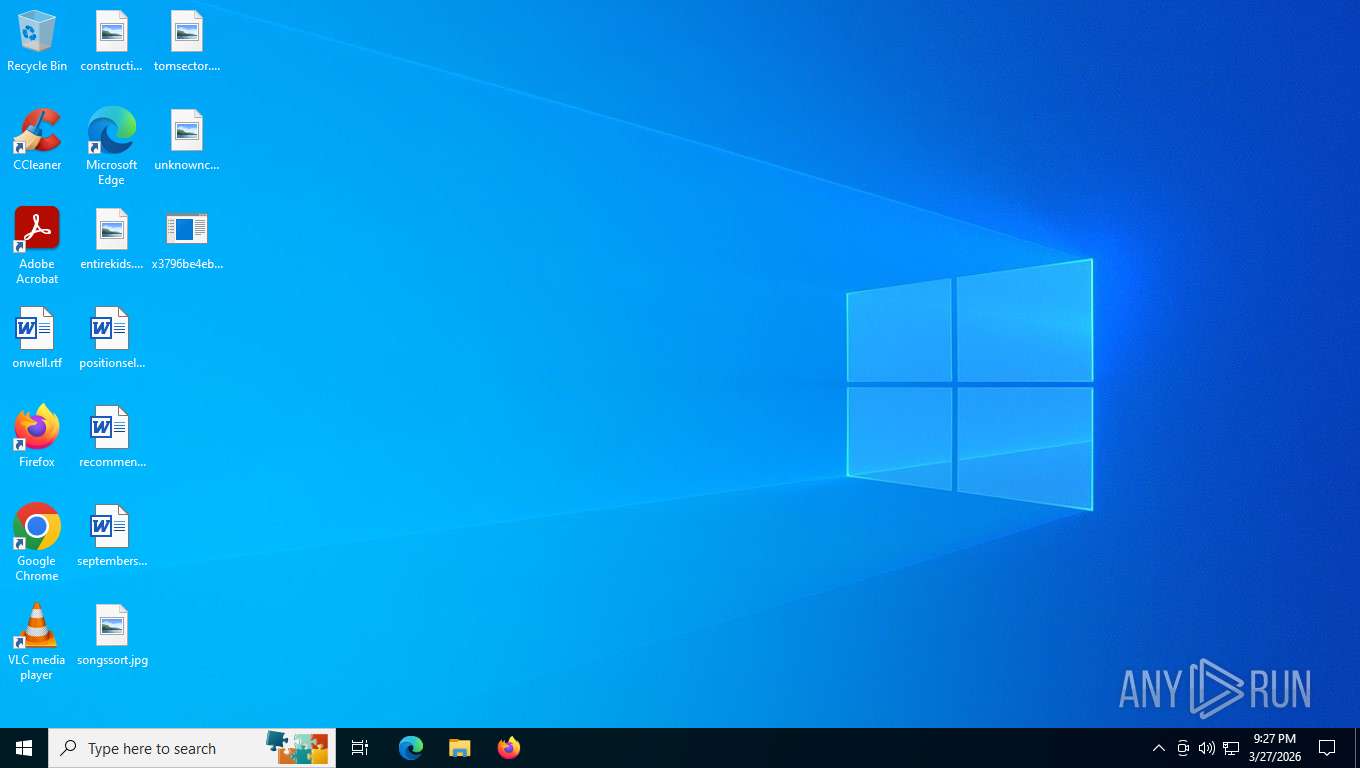
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | EB588BA6234A49D3EA880C5B558ED414 |
| SHA1: | D3136B025ED88CD2B3C03379CC996812380459DE |
| SHA256: | 3796BE4EBC1A08E81DD74FC30DF7DC2D8B9C37154AAB8F068098EF9C9A45ED6B |
| SSDEEP: | 98304:q7C+N4pq0PzS3LiZlFoeaSsBxm/wFNj5:lqc |
MALICIOUS
PHORPIEX has been found (auto)
- 121C.exe (PID: 4684)
PHORPHIEX has been detected
- 121C.exe (PID: 4684)
- 293651205.exe (PID: 2116)
Changes the autorun value in the registry
- 2502817624.exe (PID: 2648)
PHORPIEX has been detected (SURICATA)
- syscvnrhost.exe (PID: 7616)
PHORPIEX has been detected (YARA)
- syscvnrhost.exe (PID: 7616)
SUSPICIOUS
Checks for external IP
- svchost.exe (PID: 2232)
The process creates files with name similar to system file names
- 2502817624.exe (PID: 2648)
Contacting a server suspected of hosting an CnC
- syscvnrhost.exe (PID: 7616)
The process executes files with name similar to system file names
- 2502817624.exe (PID: 2648)
Starts itself from another location
- 2502817624.exe (PID: 2648)
Connects to SMTP port
- 934130349.exe (PID: 2880)
There is functionality for capture public ip (YARA)
- 934130349.exe (PID: 2880)
INFO
Checks supported languages
- 121C.exe (PID: 4684)
- x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe (PID: 7188)
- 293651205.exe (PID: 2116)
- 2502817624.exe (PID: 2648)
- syscvnrhost.exe (PID: 7616)
- syscvnrhost.exe (PID: 7456)
- 4121918530.exe (PID: 5564)
- 3238135667.exe (PID: 7992)
- 934130349.exe (PID: 2880)
- 1489510613.exe (PID: 7512)
Creates files or folders in the user directory
- x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe (PID: 7188)
- 121C.exe (PID: 4684)
- 293651205.exe (PID: 2116)
- syscvnrhost.exe (PID: 7616)
- 4121918530.exe (PID: 5564)
- 1489510613.exe (PID: 7512)
Reads the computer name
- x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe (PID: 7188)
- 121C.exe (PID: 4684)
- 293651205.exe (PID: 2116)
- syscvnrhost.exe (PID: 7616)
- 934130349.exe (PID: 2880)
Reads security settings of Internet Explorer
- x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe (PID: 7188)
- 121C.exe (PID: 4684)
- 293651205.exe (PID: 2116)
- syscvnrhost.exe (PID: 7616)
Create files in a temporary directory
- 121C.exe (PID: 4684)
- x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe (PID: 7188)
- 293651205.exe (PID: 2116)
- syscvnrhost.exe (PID: 7616)
Failed to create an executable file in Windows directory
- 2502817624.exe (PID: 2648)
Launching a file from a Registry key
- 2502817624.exe (PID: 2648)
Manual execution by a user
- syscvnrhost.exe (PID: 7456)
Reads the machine GUID from the registry
- syscvnrhost.exe (PID: 7616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 1970:01:01 15:50:05+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 1370112 |
| InitializedDataSize: | 2689024 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3e3000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
145
Monitored processes
12
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2116 | C:\Users\admin\AppData\Local\Temp\293651205.exe | C:\Users\admin\AppData\Local\Temp\293651205.exe | 121C.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | C:\Users\admin\AppData\Local\Temp\2502817624.exe | C:\Users\admin\AppData\Local\Temp\2502817624.exe | 293651205.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2880 | C:\Users\admin\AppData\Local\Temp\934130349.exe | C:\Users\admin\AppData\Local\Temp\934130349.exe | syscvnrhost.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2956 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4684 | "C:\Users\admin\AppData\Local\Temp\121C.exe" | C:\Users\admin\AppData\Local\Temp\121C.exe | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5564 | C:\Users\admin\AppData\Local\Temp\4121918530.exe | C:\Users\admin\AppData\Local\Temp\4121918530.exe | — | syscvnrhost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 7188 | "C:\Users\admin\Desktop\x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe" | C:\Users\admin\Desktop\x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7456 | C:\Users\admin\syscvnrhost.exe | C:\Users\admin\syscvnrhost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7512 | C:\Users\admin\AppData\Local\Temp\1489510613.exe | C:\Users\admin\AppData\Local\Temp\1489510613.exe | — | syscvnrhost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 306
Read events
4 291
Write events
14
Delete events
1
Modification events
| (PID) Process: | (7188) x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7188) x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7188) x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4684) 121C.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4684) 121C.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4684) 121C.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2116) 293651205.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2116) 293651205.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2116) 293651205.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2648) 2502817624.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Windows Settings |
Value: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2116 | 293651205.exe | C:\Users\admin\AppData\Local\Temp\2502817624.exe | binary | |
MD5:4D2D3B04CF612C15CF5815BE0FBEAC51 | SHA256:AD9CD916566C52D3045FEA0120900A9F2F460A4BFBC01D0BAC236F3CC9344739 | |||
| 4684 | 121C.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\newtpp[1].exe | binary | |
MD5:D56881C9EFD4FDE5BABAEA7B074B4B2B | SHA256:0BE73BE4DDE470CB4FB9BAFC5604D12A044BE5285FA10ADCFA9B742E48308C87 | |||
| 4684 | 121C.exe | C:\Users\admin\AppData\Local\Temp\293651205.exe | binary | |
MD5:D56881C9EFD4FDE5BABAEA7B074B4B2B | SHA256:0BE73BE4DDE470CB4FB9BAFC5604D12A044BE5285FA10ADCFA9B742E48308C87 | |||
| 7188 | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | C:\Users\admin\AppData\Local\Temp\121C.exe | binary | |
MD5:362FC53AFBDA6450184B73746802A6FA | SHA256:8E2B78E7C586E36DC3B27C78466FAD735F86CDD9B4E7ECBC4C650D934A9A176B | |||
| 7188 | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\64[1].exe | binary | |
MD5:362FC53AFBDA6450184B73746802A6FA | SHA256:8E2B78E7C586E36DC3B27C78466FAD735F86CDD9B4E7ECBC4C650D934A9A176B | |||
| 7616 | syscvnrhost.exe | C:\Users\admin\AppData\Local\Temp\1489510613.exe | binary | |
MD5:E41CDD1CC32DAE87215ECA979CEAF5F1 | SHA256:DE2864603AD32EF7E5C6D3F94F81955C3B8CFE4A8206839C4A737227E0BC936F | |||
| 2648 | 2502817624.exe | C:\Users\admin\syscvnrhost.exe | binary | |
MD5:4D2D3B04CF612C15CF5815BE0FBEAC51 | SHA256:AD9CD916566C52D3045FEA0120900A9F2F460A4BFBC01D0BAC236F3CC9344739 | |||
| 7616 | syscvnrhost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\3[1] | binary | |
MD5:CE1CF5EAA8BED2F2455F5D2287ED6956 | SHA256:36CB118926AD880A6F83AD5C8469AC6BBFB782A473587BB659AC04BB74A76A46 | |||
| 7616 | syscvnrhost.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\1[1] | binary | |
MD5:6596E41BE67822B6DE7EFFD8C220658D | SHA256:321335D58682DADFB8CF750D880920B020DC8A653CA4B3734B64CDF7E5D07D64 | |||
| 5564 | 4121918530.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | binary | |
MD5:283D4E1E269F2833E8C5905872B7C4F5 | SHA256:7AA698997974D52F08E7E53C9087556DEFCB5F9A5CF5DBB5F34AD1DF8971564C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
70
DNS requests
25
Threats
42
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8044 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6844 | SIHClient.exe | GET | 304 | 135.232.92.137:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8044 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7096 | slui.exe | POST | 500 | 128.24.231.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | binary | 512 b | whitelisted |
7188 | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | GET | 200 | 178.16.54.109:80 | http://178.16.54.109/64.exe | unknown | — | — | malicious |
7096 | slui.exe | POST | 500 | 48.192.1.65:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | 512 b | whitelisted |
5316 | svchost.exe | POST | 200 | 20.190.160.14:443 | https://login.live.com/RST2.srf | unknown | binary | 1.24 Kb | whitelisted |
5316 | svchost.exe | POST | 200 | 40.126.32.76:443 | https://login.live.com/RST2.srf | unknown | binary | 1.24 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8044 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
8044 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
8044 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ip-api.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7188 | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | Misc activity | INFO [ANY.RUN] Connection to IP from commonly abused ASN (AS214943 RAILNET) |
7188 | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 34 |
7188 | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | Misc activity | ET INFO Observed UA-CPU Header |
7188 | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | A Network Trojan was detected | ET MALWARE JS/Nemucod requesting EXE payload 2016-02-01 |
7188 | x3796be4ebc1a08e81dd74fc30df7dc2d8b9c37154aab8f068098ef9c9a45ed6b.exe | A Network Trojan was detected | ET MALWARE Possible Malicious Macro DL EXE Feb 2016 |
2232 | svchost.exe | Misc activity | INFO [ANY.RUN] External IP Check (ip-api .com) |
2232 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
4684 | 121C.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
4684 | 121C.exe | Misc activity | ET INFO Packed Executable Download |
7616 | syscvnrhost.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Phorpiex CnC Communication |