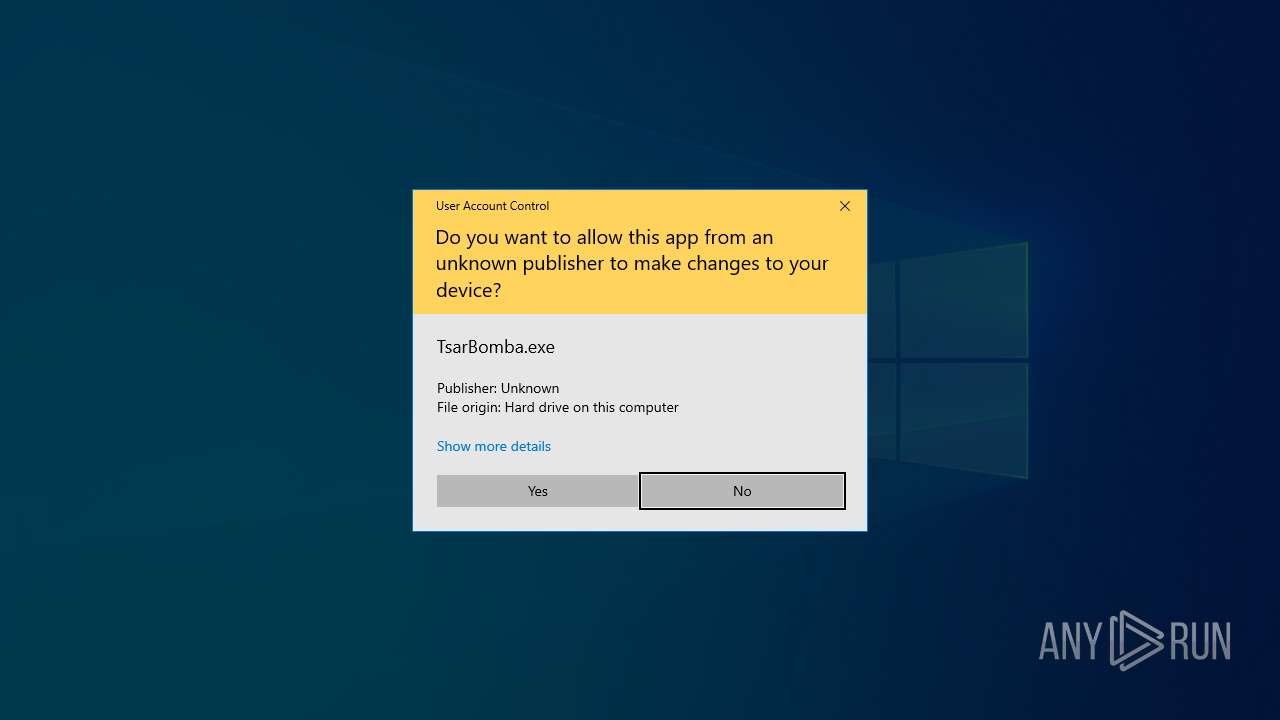
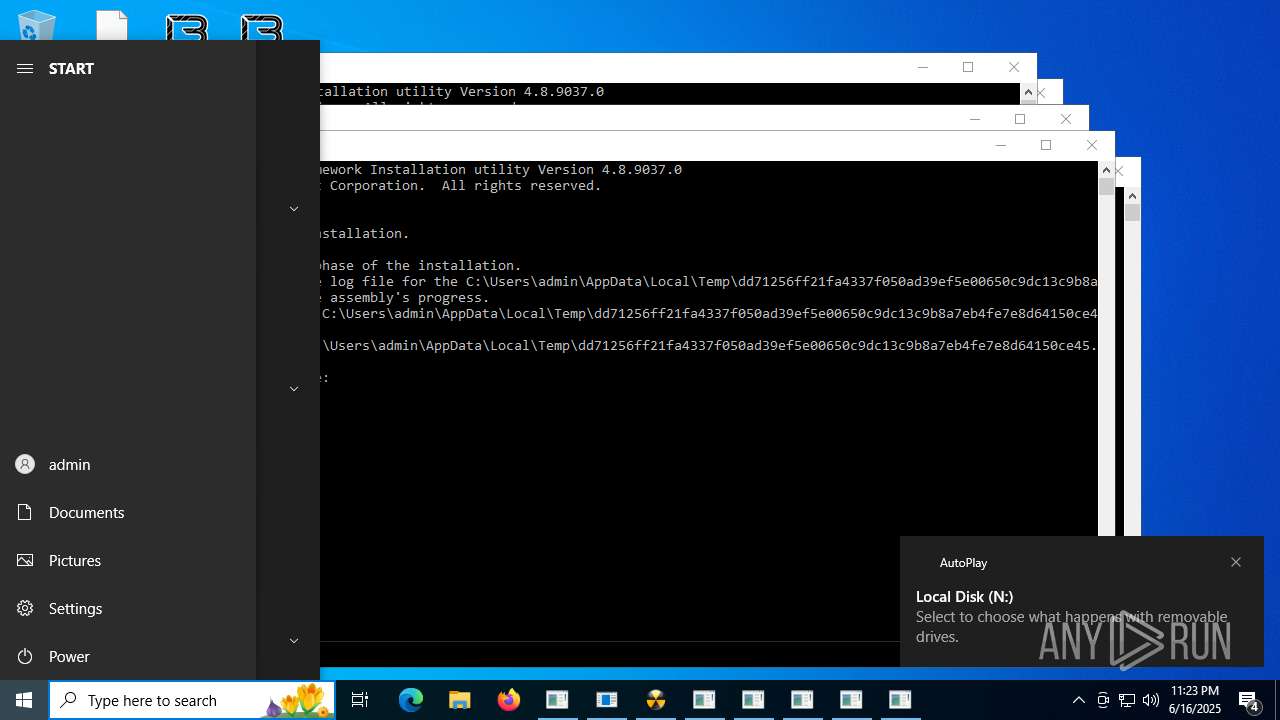
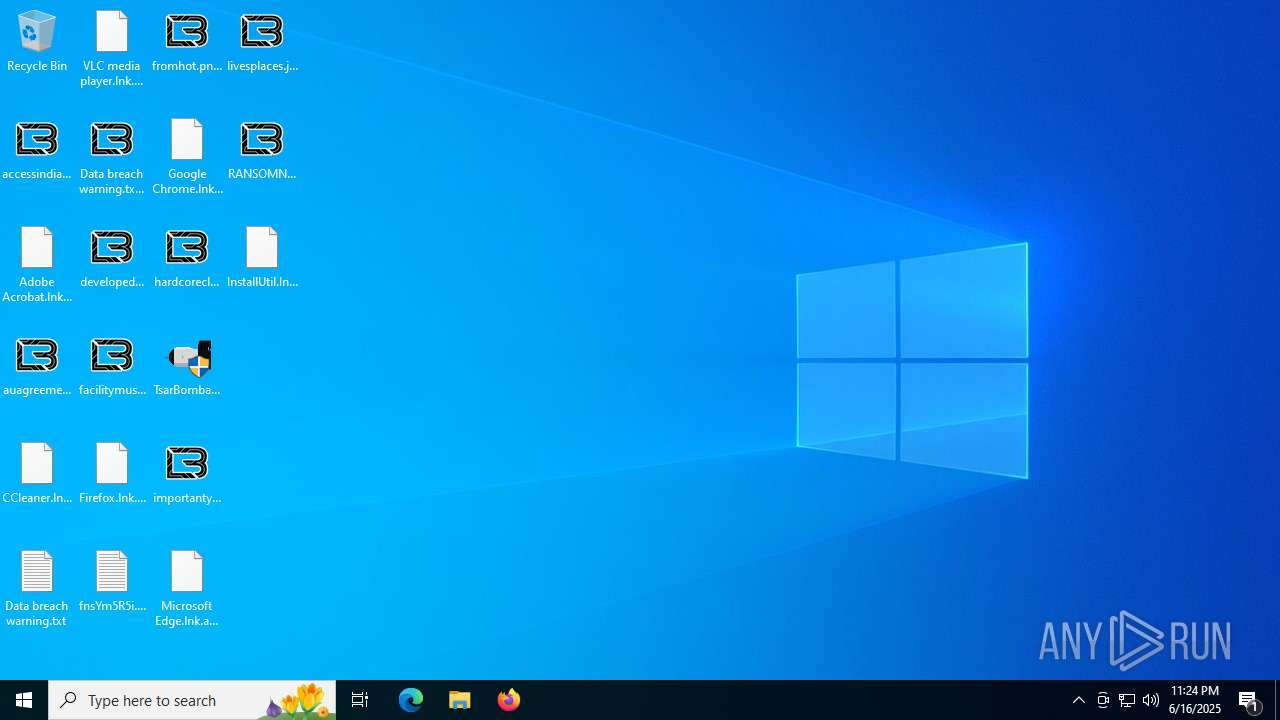
| File name: | TsarBomba.exe |
| Full analysis: | https://app.any.run/tasks/4a3bea12-40c4-4392-8df9-69e60aae0f4d |
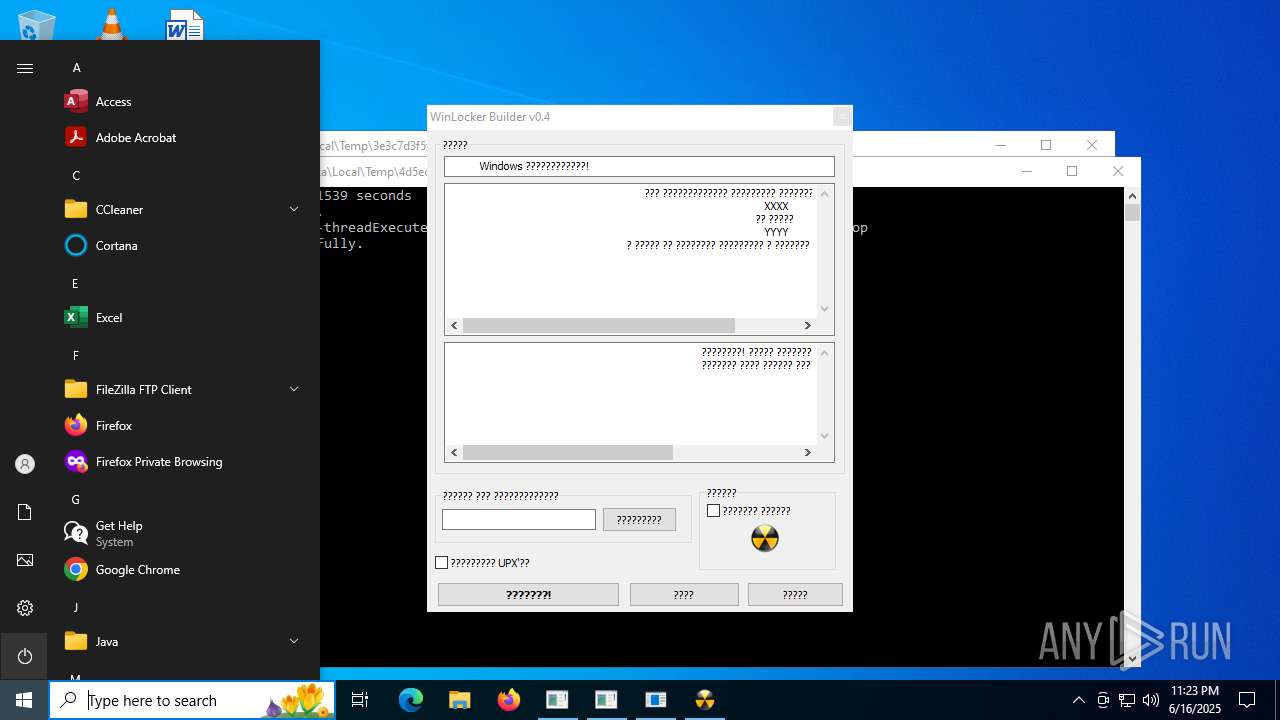
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | June 16, 2025, 23:22:47 |
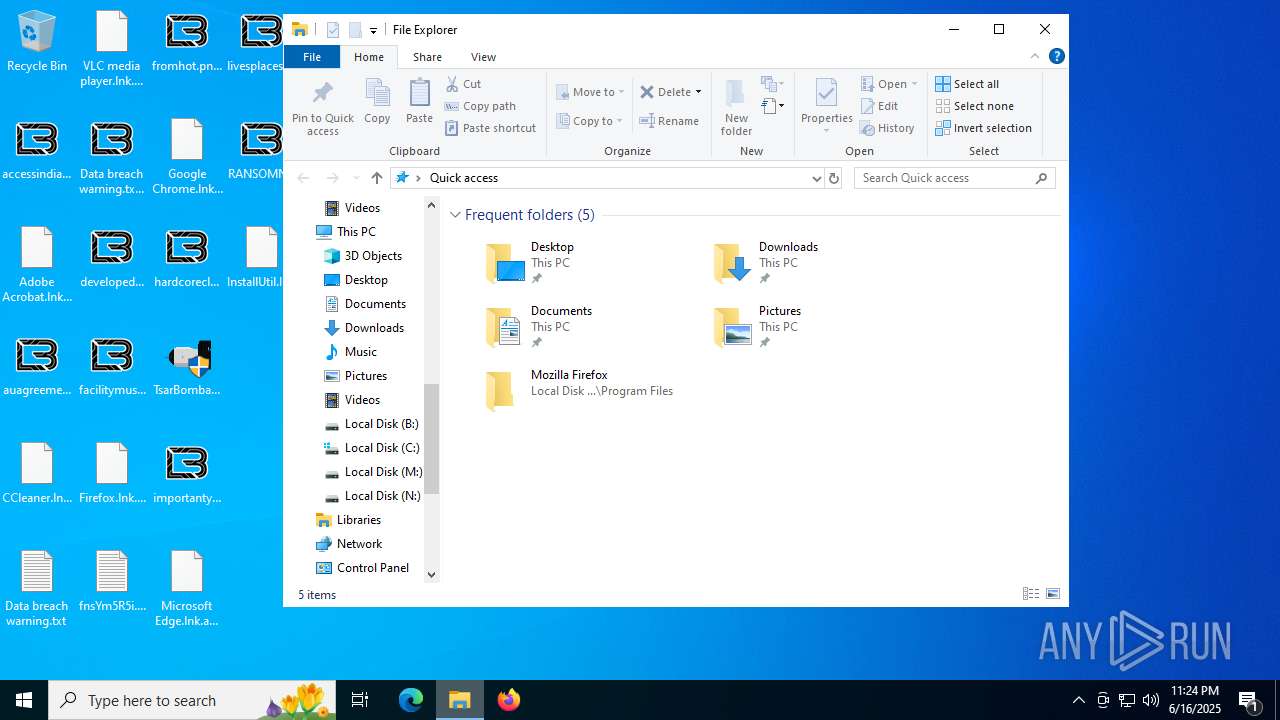
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, 4 sections |
| MD5: | 91025D6F02E542F2E37FFCE7D0CE8B51 |
| SHA1: | E2D80EF6075556CD23CE0445473C061F200B5DD4 |
| SHA256: | 3755718DB9D33F4ABA2563DE454D4530A308B41B1096C904102D08E2101F2020 |
| SSDEEP: | 196608:OhuvCqhWk4mEsw8VKcgdiyXXLO7Lz30zVKHfXk7ra62OIkwYTQUR2NA:gg4t8VrgTioVcfXka62Bk7TQUR2NA |
MALICIOUS
REDLINE has been found (auto)
- TsarBomba.exe (PID: 2552)
FRAMEWORK has been found (auto)
- TsarBomba.exe (PID: 2552)
Executing a file with an untrusted certificate
- 7a8c864ed8b7ca908d3f317d7e63a30a85fb3e8c94070f23f2cf0bfa01c5e0b5.exe (PID: 4836)
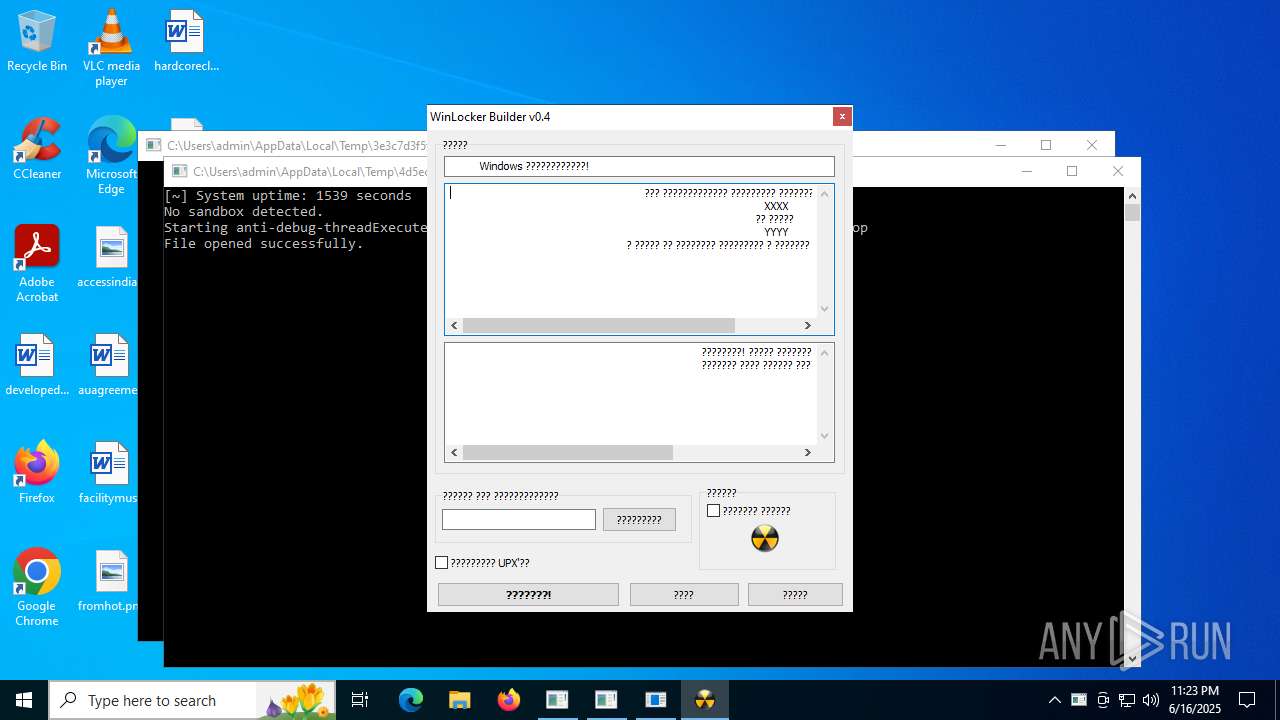
RANSOMWARE has been found (auto)
- TsarBomba.exe (PID: 2552)
GENERIC has been found (auto)
- TsarBomba.exe (PID: 2552)
- TsarBomba.exe (PID: 2552)
VALLEY has been found (auto)
- TsarBomba.exe (PID: 2552)
RAWORLD mutex has been found
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
COBALTSTRIKE has been found (auto)
- TsarBomba.exe (PID: 2552)
STEALER has been found (auto)
- TsarBomba.exe (PID: 2552)
Deletes shadow copies
- cmd.exe (PID: 3844)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 8184)
CHAOS has been found (auto)
- TsarBomba.exe (PID: 2552)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7300)
- cmd.exe (PID: 8736)
RANSOMWARE has been detected
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
VIPKEYLOGGER has been found (auto)
- TsarBomba.exe (PID: 2552)
Actions looks like stealing of personal data
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
Renames files like ransomware
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 77ebb550f38da3f28a65940a4c665ae3a679249ad906aa39387568a1f7ddd3fa.exe (PID: 5712)
- 771a06e3a1bdb42a7249d1c888e740c2bc46ba30b54490188c17f6c84ca96e26.exe (PID: 7288)
Steals credentials from Web Browsers
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
DCRAT has been found (auto)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
VIDAR mutex has been found
- MSBuild.exe (PID: 7536)
Changes Windows Defender settings
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- cmd.exe (PID: 8704)
Adds path to the Windows Defender exclusion list
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- c81ece0b60ed50db7d3769388f34ba051a05c95bd026e78dabb6ce08ff91bbba.exe (PID: 5432)
- cmd.exe (PID: 8704)
- 01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe (PID: 1812)
- 4797cb80b22ba0da0ede6593bfc16399a5ffc289400155115c8de7786ea0db49.exe (PID: 7824)
ADWARE has been found (auto)
- TsarBomba.exe (PID: 2552)
Run PowerShell with an invisible window
- powershell.exe (PID: 8836)
RAT has been found (auto)
- TsarBomba.exe (PID: 2552)
- TsarBomba.exe (PID: 2552)
- svchost.exe (PID: 7560)
Gets startup folder path (SCRIPT)
- wscript.exe (PID: 8388)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 8388)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 8388)
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 8388)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 8388)
Checks whether a specified folder exists (SCRIPT)
- wscript.exe (PID: 8388)
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 8388)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- wscript.exe (PID: 8388)
Modifies registry startup key (SCRIPT)
- wscript.exe (PID: 8388)
Opens a text file (SCRIPT)
- wscript.exe (PID: 8388)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 8388)
WSHRAT has been detected
- wscript.exe (PID: 8388)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 8388)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 8388)
REDLINE has been detected (YARA)
- TsarBomba.exe (PID: 2552)
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
XORed URL has been found (YARA)
- TsarBomba.exe (PID: 2552)
[YARA] LockBit is detected
- TsarBomba.exe (PID: 2552)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2200)
DISCORDGRABBER has been detected (YARA)
- TsarBomba.exe (PID: 2552)
UMBRALSTEALER has been detected (YARA)
- TsarBomba.exe (PID: 2552)
NANOCORE has been found (auto)
- TsarBomba.exe (PID: 2552)
XORIST has been found (auto)
- TsarBomba.exe (PID: 2552)
JLOCKER has been found (auto)
- TsarBomba.exe (PID: 2552)
DISCORDTOKEN has been found (auto)
- TsarBomba.exe (PID: 2552)
HIDDENTEAR has been found (auto)
- TsarBomba.exe (PID: 2552)
Connects to the CnC server
- svchost.exe (PID: 7560)
- svchost.exe (PID: 2200)
- svchost.exe (PID: 5656)
Starts NET.EXE for service management
- 1bad2b6e8ab16c5a692b2d05f68f7924a73a5818ddf3a9678ca8caab3568a78e.exe (PID: 2032)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 9448)
DARKVISION has been detected (SURICATA)
- svchost.exe (PID: 7560)
- svchost.exe (PID: 5656)
SNAKEKEYLOGGER has been detected (SURICATA)
- 53055b6d2651d5c6b4a0bf9ee2f50c73918e65c9d36acfd10eb2eefb0d3e957f.exe (PID: 8808)
SUSPICIOUS
Process drops legitimate windows executable
- TsarBomba.exe (PID: 2552)
- InstallUtil.exe (PID: 6972)
- 01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe (PID: 1812)
- MSBuild.exe (PID: 9024)
Starts a Microsoft application from unusual location
- 01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe (PID: 1812)
- c81ece0b60ed50db7d3769388f34ba051a05c95bd026e78dabb6ce08ff91bbba.exe (PID: 5432)
Starts POWERSHELL.EXE for commands execution
- 1bad2b6e8ab16c5a692b2d05f68f7924a73a5818ddf3a9678ca8caab3568a78e.exe (PID: 2032)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- mshta.exe (PID: 7480)
- cmd.exe (PID: 8704)
Reads security settings of Internet Explorer
- TsarBomba.exe (PID: 2552)
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
- 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.exe (PID: 7212)
- CasPol.exe (PID: 7816)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- MSBuild.exe (PID: 7536)
- ShellExperienceHost.exe (PID: 8224)
Reads the date of Windows installation
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
Executable content was dropped or overwritten
- TsarBomba.exe (PID: 2552)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- aead1f538ae65044f17554b188d4d1f88d7c4840bb554f3d70a2fe3ab86f6abf.exe (PID: 7300)
- InstallUtil.exe (PID: 6972)
- 01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe (PID: 1812)
- MSBuild.exe (PID: 9024)
- svchost.exe (PID: 7560)
- slui.exe (PID: 1108)
Starts CMD.EXE for commands execution
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 188c3798b6d41bdfa3981bb61a40b81f4fe123c64b9bed2d4c40951de2064f19.exe (PID: 1208)
- 80e3a04fa68be799b3c91737e1918f8394b250603a231a251524244e4d7f77d9.exe (PID: 592)
- ab0acdb0c45ccafcc0ec594d30dc8153936574dde9ebe4e0b22504770361c666.exe (PID: 8336)
- c81ece0b60ed50db7d3769388f34ba051a05c95bd026e78dabb6ce08ff91bbba.exe (PID: 5432)
Creates file in the systems drive root
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 771a06e3a1bdb42a7249d1c888e740c2bc46ba30b54490188c17f6c84ca96e26.exe (PID: 7288)
Start notepad (likely ransomware note)
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
Creates or modifies Windows services
- 539b377d4a33d1e884f18ecf0e0b0330e5dc26023b7ae051843cac8014142d98.exe (PID: 5480)
Executes as Windows Service
- VSSVC.exe (PID: 7720)
Connects to unusual port
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
- 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.exe (PID: 7212)
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
- 9c65d850589e6ab34c6c8e65b8a3b4aa26fa913ca850472023a3b708f95c226b.exe (PID: 1352)
- 145289accb8c684e583ca3d99532d64d0a6a40142062e648c65ffd8da070c4c9.exe (PID: 8232)
The process creates files with name similar to system file names
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
Script adds exclusion path to Windows Defender
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- cmd.exe (PID: 8704)
Write to the desktop.ini file (may be used to cloak folders)
- 771a06e3a1bdb42a7249d1c888e740c2bc46ba30b54490188c17f6c84ca96e26.exe (PID: 7288)
Executed via WMI
- schtasks.exe (PID: 8612)
- schtasks.exe (PID: 7304)
- schtasks.exe (PID: 8088)
- schtasks.exe (PID: 7072)
- schtasks.exe (PID: 5020)
- schtasks.exe (PID: 9728)
- schtasks.exe (PID: 6180)
- schtasks.exe (PID: 2980)
- schtasks.exe (PID: 9816)
Executes application which crashes
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- 0379d402a94f960380d7d91e3bfa106eeac01cd39ae7b0ba5010ba737088a215.exe (PID: 4412)
The process executes VB scripts
- CasPol.exe (PID: 7816)
Probably download files using WebClient
- mshta.exe (PID: 7480)
Manipulates environment variables
- powershell.exe (PID: 8836)
Starts process via Powershell
- powershell.exe (PID: 8836)
Found IP address in command line
- powershell.exe (PID: 8836)
Connects to the server without a host name
- 4895f3e5549c1333698e23707fb39c0d24c33c31d1bc089b7970911fba3dc0f7.exe (PID: 7948)
- svchost.exe (PID: 7560)
- svchost.exe (PID: 5656)
Reads the BIOS version
- aa76b4db29cf929b4b22457ccb8cd77308191f091cde2f69e578ade9708d7949.exe (PID: 9104)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 8388)
Accesses local storage devices (Win32_LogicalDisk) via WMI (SCRIPT)
- wscript.exe (PID: 8388)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 7536)
- MSBuild.exe (PID: 9448)
Checks for Java to be installed
- b066d97c63093902c0debe32ed5a001cc150eae3fb841d87a58408762d32466e.exe (PID: 8816)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8388)
Checks whether the drive is ready (SCRIPT)
- wscript.exe (PID: 8388)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 8388)
Gets disk free space (SCRIPT)
- wscript.exe (PID: 8388)
Gets the drive type (SCRIPT)
- wscript.exe (PID: 8388)
Gets a collection of all available drive names (SCRIPT)
- wscript.exe (PID: 8388)
Multiple wallet extension IDs have been found
- TsarBomba.exe (PID: 2552)
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
Starts application with an unusual extension
- mshta.exe (PID: 8804)
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- TsarBomba.exe (PID: 2552)
- 01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe (PID: 1812)
- 4797cb80b22ba0da0ede6593bfc16399a5ffc289400155115c8de7786ea0db49.exe (PID: 7824)
- wscript.exe (PID: 3796)
Checks for external IP
- svchost.exe (PID: 2200)
- 06922dd72ff4f3e3cffcfe8a6f2070672c341588f3a8ea1f847a0cdf601854d5.exe (PID: 8096)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- 53055b6d2651d5c6b4a0bf9ee2f50c73918e65c9d36acfd10eb2eefb0d3e957f.exe (PID: 8808)
Found regular expressions for crypto-addresses (YARA)
- TsarBomba.exe (PID: 2552)
Application launched itself
- 53055b6d2651d5c6b4a0bf9ee2f50c73918e65c9d36acfd10eb2eefb0d3e957f.exe (PID: 4216)
- 4797cb80b22ba0da0ede6593bfc16399a5ffc289400155115c8de7786ea0db49.exe (PID: 7824)
- updater.exe (PID: 1068)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 8388)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 1184)
- updater.exe (PID: 1068)
- slui.exe (PID: 1108)
- conhost.exe (PID: 1212)
- MoUsoCoreWorker.exe (PID: 3020)
- aitstatic.exe (PID: 5600)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 9448)
INFO
The sample compiled with english language support
- TsarBomba.exe (PID: 2552)
- InstallUtil.exe (PID: 6972)
- MSBuild.exe (PID: 9024)
- svchost.exe (PID: 7560)
Reads the computer name
- 01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe (PID: 1812)
- TsarBomba.exe (PID: 2552)
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- 7a8c864ed8b7ca908d3f317d7e63a30a85fb3e8c94070f23f2cf0bfa01c5e0b5.exe (PID: 4836)
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- 9c65d850589e6ab34c6c8e65b8a3b4aa26fa913ca850472023a3b708f95c226b.exe (PID: 1352)
- 65fd5041c1a1c4115b0c59995221023486f02e5e5d8e313c3e48f3a42ef9a623.exe (PID: 6232)
- 60e76eda46185d1d2e9463d15e31d4c87eb03535d368cc3471c55992bc99ad5f.exe (PID: 6612)
- 188c3798b6d41bdfa3981bb61a40b81f4fe123c64b9bed2d4c40951de2064f19.exe (PID: 1208)
- 577b3a152ddc9d6558ad1b38ef6da89257229adf06d298ea025048a6d5d2fcea.exe (PID: 1192)
- 539b377d4a33d1e884f18ecf0e0b0330e5dc26023b7ae051843cac8014142d98.exe (PID: 5480)
- 876ba1145745c2e088c0df36f8241a20916a092211d05646eae5c7004dd4d429.exe (PID: 7464)
- 954d8fcd6b74d76999f9ec033ca855ffdab6595be23039f03bc4c6017fa3932c.exe (PID: 7632)
- 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.exe (PID: 7212)
- 80e3a04fa68be799b3c91737e1918f8394b250603a231a251524244e4d7f77d9.exe (PID: 592)
- 77ebb550f38da3f28a65940a4c665ae3a679249ad906aa39387568a1f7ddd3fa.exe (PID: 5712)
- 4797cb80b22ba0da0ede6593bfc16399a5ffc289400155115c8de7786ea0db49.exe (PID: 7824)
- CasPol.exe (PID: 7816)
- 4895f3e5549c1333698e23707fb39c0d24c33c31d1bc089b7970911fba3dc0f7.exe (PID: 7948)
- 06922dd72ff4f3e3cffcfe8a6f2070672c341588f3a8ea1f847a0cdf601854d5.exe (PID: 8096)
- MSBuild.exe (PID: 7536)
- 53055b6d2651d5c6b4a0bf9ee2f50c73918e65c9d36acfd10eb2eefb0d3e957f.exe (PID: 4216)
- 145289accb8c684e583ca3d99532d64d0a6a40142062e648c65ffd8da070c4c9.exe (PID: 8232)
- 0379d402a94f960380d7d91e3bfa106eeac01cd39ae7b0ba5010ba737088a215.exe (PID: 4412)
- 771a06e3a1bdb42a7249d1c888e740c2bc46ba30b54490188c17f6c84ca96e26.exe (PID: 7288)
- aa76b4db29cf929b4b22457ccb8cd77308191f091cde2f69e578ade9708d7949.exe (PID: 9104)
- ab0acdb0c45ccafcc0ec594d30dc8153936574dde9ebe4e0b22504770361c666.exe (PID: 8336)
- ShellExperienceHost.exe (PID: 8224)
- aead1f538ae65044f17554b188d4d1f88d7c4840bb554f3d70a2fe3ab86f6abf.exe (PID: 7300)
- Chrome_boostrap.exe (PID: 4112)
Checks supported languages
- 1bad2b6e8ab16c5a692b2d05f68f7924a73a5818ddf3a9678ca8caab3568a78e.exe (PID: 2032)
- 0fd46aca09c54c256d22420d2ac3e947ff204a42a24158dfcb562de18a77f3f1.exe (PID: 1512)
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
- TsarBomba.exe (PID: 2552)
- 9c65d850589e6ab34c6c8e65b8a3b4aa26fa913ca850472023a3b708f95c226b.exe (PID: 1352)
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- 60e76eda46185d1d2e9463d15e31d4c87eb03535d368cc3471c55992bc99ad5f.exe (PID: 6612)
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
- 7a8c864ed8b7ca908d3f317d7e63a30a85fb3e8c94070f23f2cf0bfa01c5e0b5.exe (PID: 4836)
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe (PID: 1812)
- 80e3a04fa68be799b3c91737e1918f8394b250603a231a251524244e4d7f77d9.exe (PID: 592)
- 182fb9756b66963f458ebbe0f20ff2715a758825ac6655fc56ec85579df61330.exe (PID: 6376)
- 65fd5041c1a1c4115b0c59995221023486f02e5e5d8e313c3e48f3a42ef9a623.exe (PID: 6232)
- 188c3798b6d41bdfa3981bb61a40b81f4fe123c64b9bed2d4c40951de2064f19.exe (PID: 1208)
- 577b3a152ddc9d6558ad1b38ef6da89257229adf06d298ea025048a6d5d2fcea.exe (PID: 1192)
- 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.exe (PID: 7212)
- 77ebb550f38da3f28a65940a4c665ae3a679249ad906aa39387568a1f7ddd3fa.exe (PID: 5712)
- 0379d402a94f960380d7d91e3bfa106eeac01cd39ae7b0ba5010ba737088a215.exe (PID: 4412)
- 539b377d4a33d1e884f18ecf0e0b0330e5dc26023b7ae051843cac8014142d98.exe (PID: 5480)
- 771a06e3a1bdb42a7249d1c888e740c2bc46ba30b54490188c17f6c84ca96e26.exe (PID: 7288)
- 876ba1145745c2e088c0df36f8241a20916a092211d05646eae5c7004dd4d429.exe (PID: 7464)
- 954d8fcd6b74d76999f9ec033ca855ffdab6595be23039f03bc4c6017fa3932c.exe (PID: 7632)
- 4797cb80b22ba0da0ede6593bfc16399a5ffc289400155115c8de7786ea0db49.exe (PID: 7824)
- CasPol.exe (PID: 7816)
- 4895f3e5549c1333698e23707fb39c0d24c33c31d1bc089b7970911fba3dc0f7.exe (PID: 7948)
- 06922dd72ff4f3e3cffcfe8a6f2070672c341588f3a8ea1f847a0cdf601854d5.exe (PID: 8096)
- 53055b6d2651d5c6b4a0bf9ee2f50c73918e65c9d36acfd10eb2eefb0d3e957f.exe (PID: 4216)
- MSBuild.exe (PID: 7536)
- 145289accb8c684e583ca3d99532d64d0a6a40142062e648c65ffd8da070c4c9.exe (PID: 8232)
- a0da672fdaf8943fc0453424197c5ae5539ed1cc86a47e955ea706a3e8365fe7.exe (PID: 8536)
- aa76b4db29cf929b4b22457ccb8cd77308191f091cde2f69e578ade9708d7949.exe (PID: 9104)
- ab0acdb0c45ccafcc0ec594d30dc8153936574dde9ebe4e0b22504770361c666.exe (PID: 8336)
- aead1f538ae65044f17554b188d4d1f88d7c4840bb554f3d70a2fe3ab86f6abf.exe (PID: 7300)
- b066d97c63093902c0debe32ed5a001cc150eae3fb841d87a58408762d32466e.exe (PID: 8816)
- Chrome_boostrap.exe (PID: 4112)
- javaw.exe (PID: 684)
- ShellExperienceHost.exe (PID: 8224)
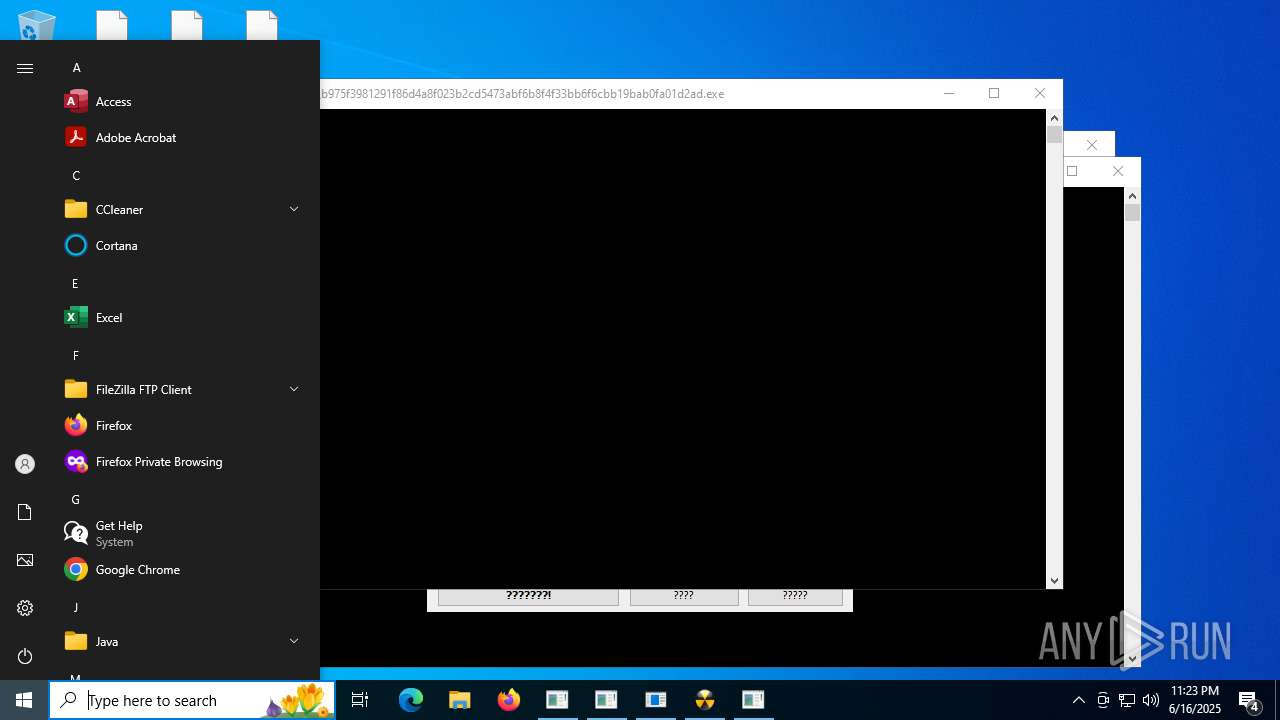
- b975f3981291f86d4a8f023b2cd5473abf6b8f4f33bb6f6cbb19bab0fa01d2ad.exe (PID: 7316)
Disables trace logs
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
- 876ba1145745c2e088c0df36f8241a20916a092211d05646eae5c7004dd4d429.exe (PID: 7464)
- 06922dd72ff4f3e3cffcfe8a6f2070672c341588f3a8ea1f847a0cdf601854d5.exe (PID: 8096)
- 4895f3e5549c1333698e23707fb39c0d24c33c31d1bc089b7970911fba3dc0f7.exe (PID: 7948)
Reads Environment values
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
- 876ba1145745c2e088c0df36f8241a20916a092211d05646eae5c7004dd4d429.exe (PID: 7464)
Process checks computer location settings
- TsarBomba.exe (PID: 2552)
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
- CasPol.exe (PID: 7816)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
Reads the machine GUID from the registry
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe (PID: 1812)
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- 577b3a152ddc9d6558ad1b38ef6da89257229adf06d298ea025048a6d5d2fcea.exe (PID: 1192)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.exe (PID: 7212)
- 876ba1145745c2e088c0df36f8241a20916a092211d05646eae5c7004dd4d429.exe (PID: 7464)
- 80e3a04fa68be799b3c91737e1918f8394b250603a231a251524244e4d7f77d9.exe (PID: 592)
- 4797cb80b22ba0da0ede6593bfc16399a5ffc289400155115c8de7786ea0db49.exe (PID: 7824)
- 06922dd72ff4f3e3cffcfe8a6f2070672c341588f3a8ea1f847a0cdf601854d5.exe (PID: 8096)
- 4895f3e5549c1333698e23707fb39c0d24c33c31d1bc089b7970911fba3dc0f7.exe (PID: 7948)
- 53055b6d2651d5c6b4a0bf9ee2f50c73918e65c9d36acfd10eb2eefb0d3e957f.exe (PID: 4216)
- 145289accb8c684e583ca3d99532d64d0a6a40142062e648c65ffd8da070c4c9.exe (PID: 8232)
- MSBuild.exe (PID: 7536)
- aead1f538ae65044f17554b188d4d1f88d7c4840bb554f3d70a2fe3ab86f6abf.exe (PID: 7300)
- aa76b4db29cf929b4b22457ccb8cd77308191f091cde2f69e578ade9708d7949.exe (PID: 9104)
Checks proxy server information
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
- 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.exe (PID: 7212)
- 876ba1145745c2e088c0df36f8241a20916a092211d05646eae5c7004dd4d429.exe (PID: 7464)
- 4895f3e5549c1333698e23707fb39c0d24c33c31d1bc089b7970911fba3dc0f7.exe (PID: 7948)
- MSBuild.exe (PID: 7536)
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
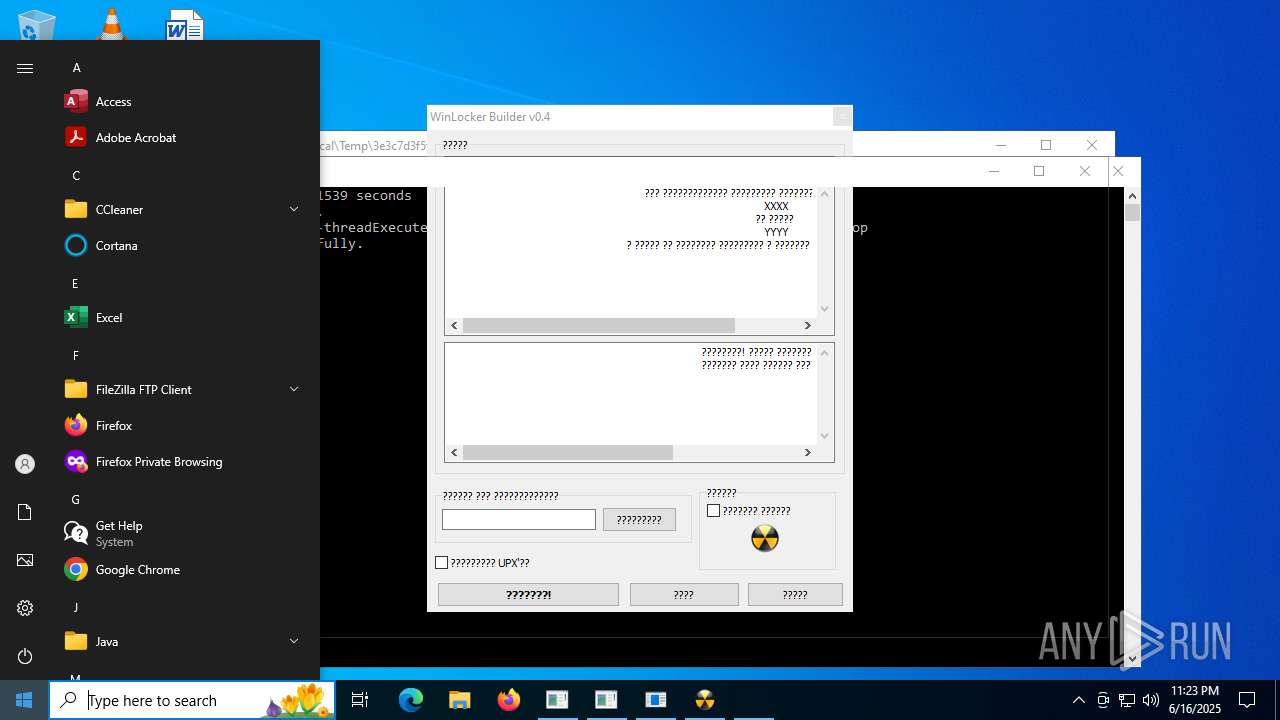
The sample compiled with russian language support
- TsarBomba.exe (PID: 2552)
Create files in a temporary directory
- TsarBomba.exe (PID: 2552)
- 188c3798b6d41bdfa3981bb61a40b81f4fe123c64b9bed2d4c40951de2064f19.exe (PID: 1208)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
- ab0acdb0c45ccafcc0ec594d30dc8153936574dde9ebe4e0b22504770361c666.exe (PID: 8336)
- javaw.exe (PID: 684)
Reads mouse settings
- 188c3798b6d41bdfa3981bb61a40b81f4fe123c64b9bed2d4c40951de2064f19.exe (PID: 1208)
- ab0acdb0c45ccafcc0ec594d30dc8153936574dde9ebe4e0b22504770361c666.exe (PID: 8336)
Reads the software policy settings
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- 876ba1145745c2e088c0df36f8241a20916a092211d05646eae5c7004dd4d429.exe (PID: 7464)
- MSBuild.exe (PID: 7536)
- aa76b4db29cf929b4b22457ccb8cd77308191f091cde2f69e578ade9708d7949.exe (PID: 9104)
Reads Microsoft Office registry keys
- 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe (PID: 3576)
Attempting to use instant messaging service
- 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe (PID: 2532)
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 7536)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2072)
- WMIC.exe (PID: 7548)
Launching a file from Task Scheduler
- cmd.exe (PID: 7300)
- cmd.exe (PID: 8736)
Creates files or folders in the user directory
- 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe (PID: 4684)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
- CasPol.exe (PID: 7816)
- WerFault.exe (PID: 8932)
- 77ebb550f38da3f28a65940a4c665ae3a679249ad906aa39387568a1f7ddd3fa.exe (PID: 5712)
Creates files in the program directory
- 771a06e3a1bdb42a7249d1c888e740c2bc46ba30b54490188c17f6c84ca96e26.exe (PID: 7288)
- 77ebb550f38da3f28a65940a4c665ae3a679249ad906aa39387568a1f7ddd3fa.exe (PID: 5712)
- 5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe (PID: 7124)
- MSBuild.exe (PID: 7536)
- 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe (PID: 5644)
- javaw.exe (PID: 684)
Reads Internet Explorer settings
- mshta.exe (PID: 7480)
- mshta.exe (PID: 8804)
Application based on Java
- javaw.exe (PID: 684)
Compiled with Borland Delphi (YARA)
- TsarBomba.exe (PID: 2552)
- 0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe (PID: 1212)
Manual execution by a user
- svchost.com (PID: 5408)
- svchost.com (PID: 5696)
- svchost.com (PID: 4724)
- svchost.com (PID: 6044)
- wscript.exe (PID: 3796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 5632 |
| InitializedDataSize: | 26406400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2321 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.6.6.6 |
| ProductVersionNumber: | 6.6.6.6 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | HELL |
| FileTitle: | RAT Pack |
| FileDescription: | Tsar Bomba RAT PACK |
| FileVersion: | 6,6,6,6 |
| LegalCopyright: | 2025 |
| LegalTrademark: | HELL |
| ProductName: | Tsar Bomba |
| ProductVersion: | 6,6,6,6 |
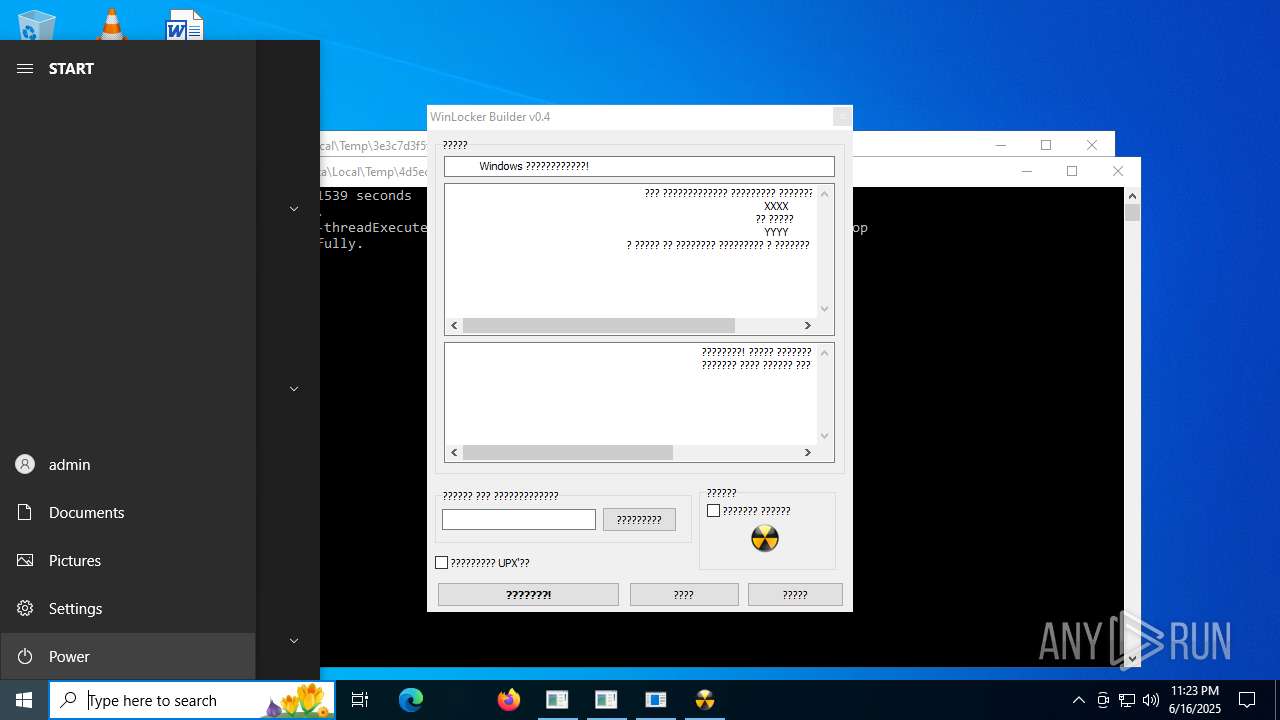
Total processes
404
Monitored processes
158
Malicious processes
25
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Users\admin\AppData\Local\Temp\80e3a04fa68be799b3c91737e1918f8394b250603a231a251524244e4d7f77d9.exe" | C:\Users\admin\AppData\Local\Temp\80e3a04fa68be799b3c91737e1918f8394b250603a231a251524244e4d7f77d9.exe | — | TsarBomba.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\b066d97c63093902c0debe32ed5a001cc150eae3fb841d87a58408762d32466e.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | b066d97c63093902c0debe32ed5a001cc150eae3fb841d87a58408762d32466e.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 760 | powershell -Command "& { }" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 1bad2b6e8ab16c5a692b2d05f68f7924a73a5818ddf3a9678ca8caab3568a78e.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | svchost.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 1108 | "C:\Users\All Users\WindowsHolographicDevices\SpatialStore\slui.exe" | C:\ProgramData\WindowsHolographicDevices\SpatialStore\slui.exe | svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4294967295 Version: 1.2.7.1277 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | "C:\Users\admin\AppData\Local\Temp\577b3a152ddc9d6558ad1b38ef6da89257229adf06d298ea025048a6d5d2fcea.exe" | C:\Users\admin\AppData\Local\Temp\577b3a152ddc9d6558ad1b38ef6da89257229adf06d298ea025048a6d5d2fcea.exe | — | TsarBomba.exe | |||||||||||
User: admin Integrity Level: HIGH Description: NNjJ887 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1208 | "C:\Users\admin\AppData\Local\Temp\188c3798b6d41bdfa3981bb61a40b81f4fe123c64b9bed2d4c40951de2064f19.exe" | C:\Users\admin\AppData\Local\Temp\188c3798b6d41bdfa3981bb61a40b81f4fe123c64b9bed2d4c40951de2064f19.exe | — | TsarBomba.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1212 | "C:\Users\admin\AppData\Local\Temp\0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe" | C:\Users\admin\AppData\Local\Temp\0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe | TsarBomba.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 1073807364 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
78 947
Read events
78 783
Write events
148
Delete events
16
Modification events
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (2532) 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
87
Suspicious files
687
Text files
776
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2552 | TsarBomba.exe | C:\Users\admin\AppData\Local\Temp\0f78a658b60f0879acccf0933d9ae8a5d2c188e9f16b8e6f7b01bd0cc9b5c4e1.exe | executable | |
MD5:A85DED286361BD125CDFCEB0B6C93108 | SHA256:0F78A658B60F0879ACCCF0933D9AE8A5D2C188E9F16B8E6F7B01BD0CC9B5C4E1 | |||
| 2552 | TsarBomba.exe | C:\Users\admin\AppData\Local\Temp\80e3a04fa68be799b3c91737e1918f8394b250603a231a251524244e4d7f77d9.exe | executable | |
MD5:F0410358A0D9DBD0DFF3113D9C744CA7 | SHA256:80E3A04FA68BE799B3C91737E1918F8394B250603A231A251524244E4D7F77D9 | |||
| 2552 | TsarBomba.exe | C:\Users\admin\AppData\Local\Temp\182fb9756b66963f458ebbe0f20ff2715a758825ac6655fc56ec85579df61330.exe | executable | |
MD5:48FA36C2C1ADA2127CEAE0BD75B71BFE | SHA256:182FB9756B66963F458EBBE0F20FF2715A758825AC6655FC56EC85579DF61330 | |||
| 2552 | TsarBomba.exe | C:\Users\admin\AppData\Local\Temp\59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe | executable | |
MD5:1395D639E30F4DDC816CCF11B2AD0F28 | SHA256:59AB63C99285E35679153E299E411AA32A94D25482566428A6FD7D908F04D4AD | |||
| 2552 | TsarBomba.exe | C:\Users\admin\AppData\Local\Temp\01ec7b1066df7c55e262dc375bff5fd13a1fc9706c3db4b3522ac8b9d2453b52.exe | executable | |
MD5:9C7B97EB3958D4309E6BA38BB1A99471 | SHA256:01EC7B1066DF7C55E262DC375BFF5FD13A1FC9706C3DB4B3522AC8B9D2453B52 | |||
| 2552 | TsarBomba.exe | C:\Users\admin\AppData\Local\Temp\65fd5041c1a1c4115b0c59995221023486f02e5e5d8e313c3e48f3a42ef9a623.exe | executable | |
MD5:63D835764D036DB9502A8FB315895B66 | SHA256:65FD5041C1A1C4115B0C59995221023486F02E5E5D8E313C3E48F3A42EF9A623 | |||
| 2552 | TsarBomba.exe | C:\Users\admin\AppData\Local\Temp\60e76eda46185d1d2e9463d15e31d4c87eb03535d368cc3471c55992bc99ad5f.exe | executable | |
MD5:81DD862410AF80C9D2717AF912778332 | SHA256:60E76EDA46185D1D2E9463D15E31D4C87EB03535D368CC3471C55992BC99AD5F | |||
| 2552 | TsarBomba.exe | C:\Users\admin\AppData\Local\Temp\5f7dbb2374af6314df4cd22c830ffaced38bc2ea8ec16775e502d7422ca74f35.exe | executable | |
MD5:0C14B5BB56A334CF17EF9B247EA1134E | SHA256:5F7DBB2374AF6314DF4CD22C830FFACED38BC2EA8EC16775E502D7422CA74F35 | |||
| 4684 | 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe | \\?\Volume{2f5c5e71-85a9-11eb-90a8-9a9b76358421}\EFI\Microsoft\Recovery\BCD.LOG1.aosIt | — | |
MD5:— | SHA256:— | |||
| 4684 | 3e3c7d3f5f93d7bf260aca7612b4dbc5d0e90992841f7e6826d7fb7fa3abe044.exe | \\?\Volume{2f5c5e71-85a9-11eb-90a8-9a9b76358421}\EFI\Microsoft\Recovery\BCD.LOG2.aosIt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
123
DNS requests
36
Threats
43
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5644 | 59ab63c99285e35679153e299e411aa32a94d25482566428a6fd7d908f04d4ad.exe | GET | 404 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | whitelisted |
8808 | 53055b6d2651d5c6b4a0bf9ee2f50c73918e65c9d36acfd10eb2eefb0d3e957f.exe | GET | 404 | 158.101.44.242:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
5656 | svchost.exe | GET | 404 | 107.174.192.179:80 | http://107.174.192.179/data/003 | unknown | — | — | unknown |
5656 | svchost.exe | GET | 404 | 107.174.192.179:80 | http://107.174.192.179/data/003 | unknown | — | — | unknown |
8096 | 06922dd72ff4f3e3cffcfe8a6f2070672c341588f3a8ea1f847a0cdf601854d5.exe | GET | 404 | 158.101.44.242:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
7560 | svchost.exe | GET | 404 | 107.174.192.179:80 | http://107.174.192.179/data/003 | unknown | — | — | unknown |
7560 | svchost.exe | GET | 404 | 107.174.192.179:80 | http://107.174.192.179/clean | unknown | — | — | unknown |
5656 | svchost.exe | GET | 404 | 107.174.192.179:80 | http://107.174.192.179/data/003 | unknown | — | — | unknown |
5656 | svchost.exe | GET | 404 | 107.174.192.179:80 | http://107.174.192.179/data/003 | unknown | — | — | unknown |
8808 | 53055b6d2651d5c6b4a0bf9ee2f50c73918e65c9d36acfd10eb2eefb0d3e957f.exe | GET | 404 | 158.101.44.242:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6936 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2532 | 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | 162.159.136.234:443 | gateway.discord.gg | CLOUDFLARENET | — | whitelisted |
3576 | 4d5ecf3d1955458195771630f03f6ef42f5f62e66ed8e0681f8311d25aecc2bb.exe | 98.177.107.142:60446 | — | ASN-CXA-ALL-CCI-22773-RDC | US | unknown |
5328 | SearchApp.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
7212 | 755b9e89416a664f52a0dfee6de54687f15ae900a7317763b0a4144996724f6a.exe | 103.171.35.26:9443 | — | VH Global Limited | HK | unknown |
— | — | 192.168.100.5:49722 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
gateway.discord.gg |
| whitelisted |
www.bing.com |
| whitelisted |
gstatic.com |
| whitelisted |
t.me |
| whitelisted |
steamcommunity.com |
| whitelisted |
api.pcloud.com |
| whitelisted |
cloud-api.yandex.net |
| whitelisted |
checkip.dyndns.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (gateway .discord .gg) |
2532 | 6ca05da8350d9f5e5d3a7547c0d4693ebc1190e3b76f58f4196021d0c080c722.exe | Misc activity | ET INFO Observed Discord Service Domain (gateway .discord .gg) in TLS SNI |
7536 | MSBuild.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
7536 | MSBuild.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2200 | svchost.exe | Potentially Bad Traffic | ET INFO Cloud Storage API Related Domain in DNS Lookup (api .pcloud .com) |
2200 | svchost.exe | Misc activity | ET INFO Commonly Abused File Sharing Site Domain Observed in DNS Lookup (pcloud .com) |
9104 | aa76b4db29cf929b4b22457ccb8cd77308191f091cde2f69e578ade9708d7949.exe | Misc activity | ET INFO Observed Commonly Abused File Sharing Site Domain (pcloud .com) in TLS SNI |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET DYN_DNS External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Timeweb Cloud Platform |
8096 | 06922dd72ff4f3e3cffcfe8a6f2070672c341588f3a8ea1f847a0cdf601854d5.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |