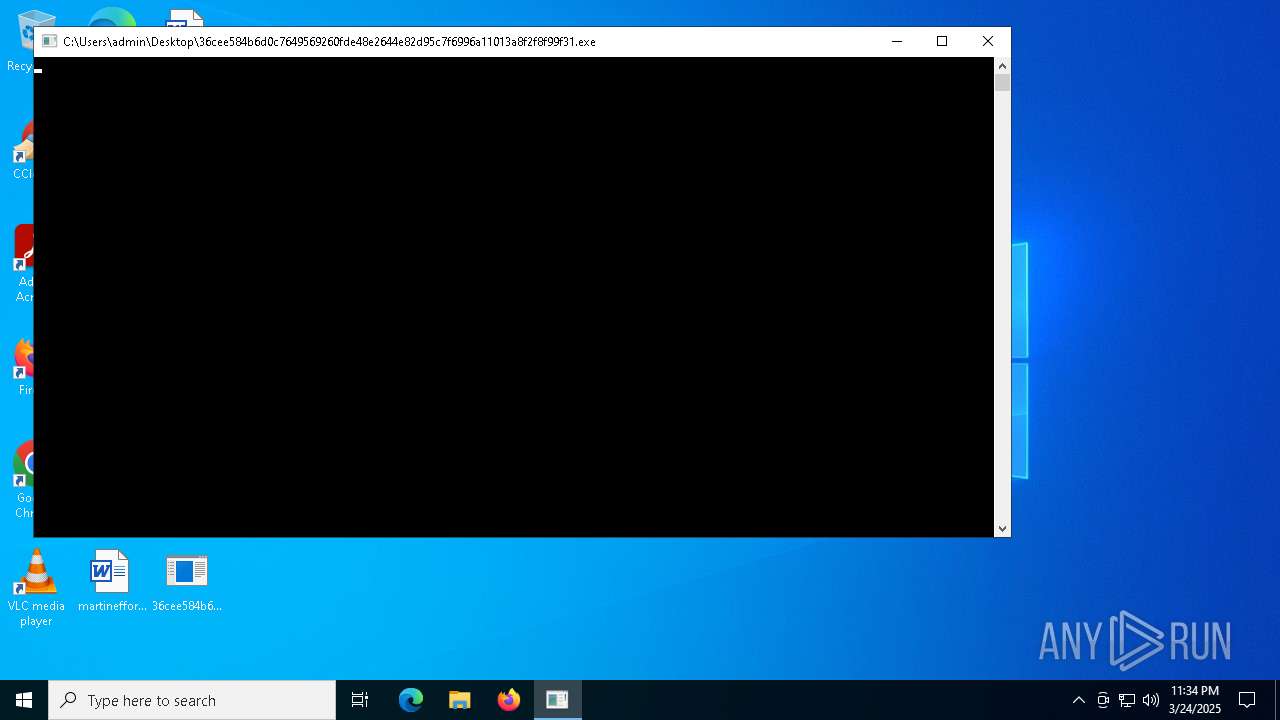
| File name: | 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31 |
| Full analysis: | https://app.any.run/tasks/51b70f8f-b9b7-40d1-9e1a-d4a504bd11e1 |
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
| Analysis date: | March 24, 2025, 23:34:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows, 13 sections |
| MD5: | DF380ABD0E70C18A7463BE2762C440C0 |
| SHA1: | F1E088A164BFC1B52DFA6D70349AFDBB8B46B9DD |
| SHA256: | 36CEE584B6D0C7649569260FDE48E2644E82D95C7F6996A11013A8F2F8F99F31 |
| SSDEEP: | 98304:/i6phhlaOhMkaIGzDJseMoC+xudYv3FE/ao3PYIuPZHaTH7inCnVl:w0JT |
MALICIOUS
RANSOMWARE has been detected
- 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe (PID: 7020)
SUSPICIOUS
Executable content was dropped or overwritten
- 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe (PID: 7020)
Write to the desktop.ini file (may be used to cloak folders)
- 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe (PID: 7020)
INFO
Checks supported languages
- 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe (PID: 7020)
Application based on Golang
- 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe (PID: 7020)
Detects GO elliptic curve encryption (YARA)
- 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe (PID: 7020)
Reads the software policy settings
- slui.exe (PID: 6272)
Checks proxy server information
- slui.exe (PID: 6272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 1319424 |
| InitializedDataSize: | 226816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x63740 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows command line |
Total processes
121
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4164 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6272 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7020 | "C:\Users\admin\Desktop\36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe" | C:\Users\admin\Desktop\36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
3 542
Read events
3 542
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7020 | 36cee584b6d0c7649569260fde48e2644e82d95c7f6996a11013a8f2f8f99f31.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\desktop.ini | executable | |
MD5:D9C8906CD30A2ED6A6B8D05D90E5B7F3 | SHA256:DEE3F98A35D2AC31291FF8EB1073A86B398F8DFBC3132C4D92846914380A83D6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
22
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6272 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |