| File name: | info_10_09.doc |
| Full analysis: | https://app.any.run/tasks/d29c20e1-0c45-41d8-bef4-cd147fb11b46 |
| Verdict: | Malicious activity |
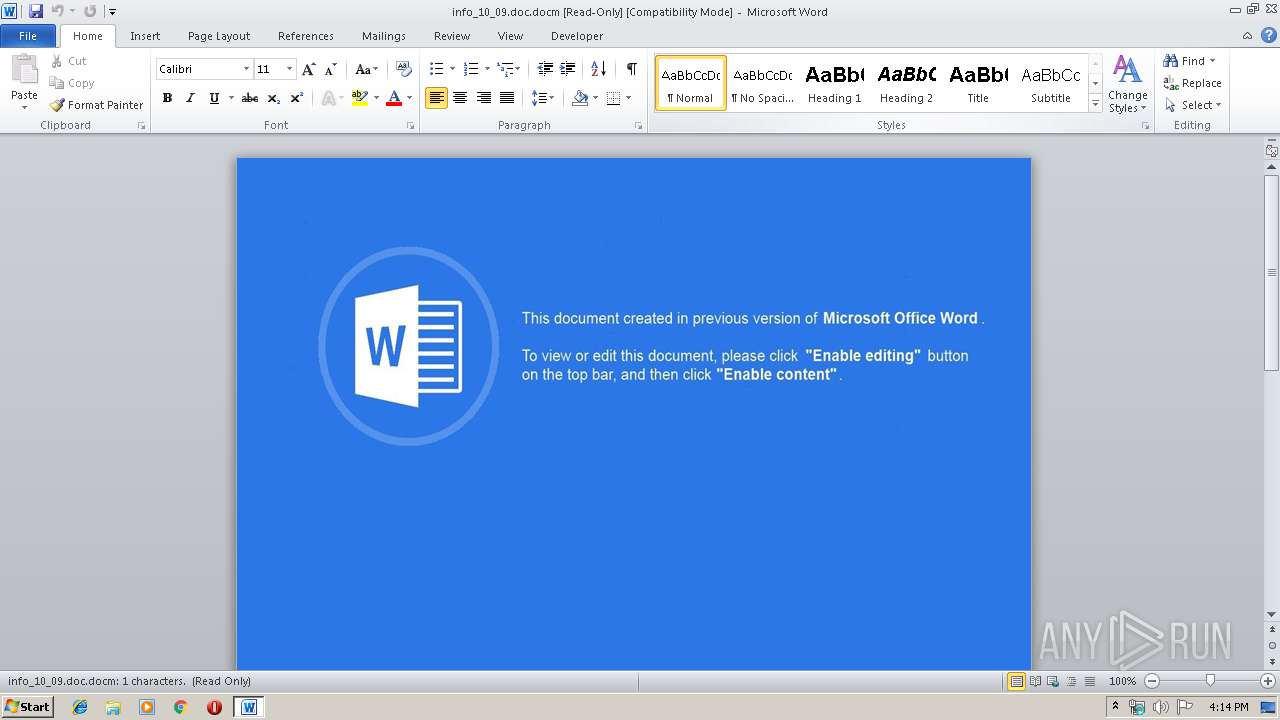
| Threats: | Ursnif is a banking Trojan that usually infects corporate victims. It is based on an old malware but was substantially updated over the years and became quite powerful. Today Ursnif is one of the most widely spread banking Trojans in the world. |
| Analysis date: | October 09, 2019, 15:14:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 6011C90753EBE147A0C377F7C08F91A2 |
| SHA1: | 2A8E6FD9A180691AB6C36762D0E335D62D246AD6 |
| SHA256: | 36A5A228C57917222A042A52C0B05E9FD66E0CE0C70BF261F849B5CE719A57A9 |
| SSDEEP: | 1536:oJSa14kxM0u4v5p60ALayARQGpnTb76bd6Rd1yywQmB9lSraJDv:oJr1xxM0oaPFTb76bd8d1jC9lyaJL |
MALICIOUS
URSNIF was detected
- WMIC.exe (PID: 3924)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2728)
SUSPICIOUS
Uses WMIC.EXE to obtain a system information
- WINWORD.EXE (PID: 2728)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2728)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x01119293 |
| ZipCompressedSize: | 445 |
| ZipUncompressedSize: | 1901 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | - |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| Manager: | - |
| Company: | home |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | admin |
| RevisionNumber: | 2 |
| CreateDate: | 2019:10:09 08:32:00Z |
| ModifyDate: | 2019:10:09 08:32:00Z |
| Category: | - |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | mcbid |
| Description: | - |
| Language: | en-US |
Total processes
36
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2728 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Windows\info_10_09.doc.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3924 | "C:\Windows\System32\wbem\WMIC.exe" process list /format:"C:\Users\admin\AppData\Local\Temp\avPi0" | C:\Windows\System32\wbem\WMIC.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147500037 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 419
Read events
673
Write events
713
Delete events
33
Modification events
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :+: |
Value: 3A2B3A00A80A0000010000000000000000000000 | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330184243 | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184359 | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330184360 | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: A80A00005A444F44B47ED50100000000 | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | %,: |
Value: 252C3A00A80A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | %,: |
Value: 252C3A00A80A000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2728) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB9A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\93A9AB85.jpeg | — | |
MD5:— | SHA256:— | |||
| 2728 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2728 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2728 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\info_10_09.doc.docm.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\avPi0.xsl | xml | |
MD5:— | SHA256:— | |||
| 2728 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3924 | WMIC.exe | GET | 404 | 85.143.216.162:80 | http://fornomonse.com/angosz/cecolf.php?l=icath4.tar | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 85.143.216.162:80 | fornomonse.com | Trader soft LLC | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fornomonse.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3924 | WMIC.exe | A Network Trojan was detected | MALWARE [PTsecurity] MalDoc Requesting Ursnif Payload |
1 ETPRO signatures available at the full report