| File name: | 35f3f9e4d43cd037feadf2d7c81f9d90 |
| Full analysis: | https://app.any.run/tasks/f1356a48-d0dd-4d65-9308-a5b9292c5254 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | December 05, 2022, 20:24:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 35F3F9E4D43CD037FEADF2D7C81F9D90 |
| SHA1: | 41AC8250A318FCBE930B5F19A8191A24B7BFD1FA |
| SHA256: | 3677DDB0CDA755E0CCA757A2EA20C794B836877B1ED6BD14E0BCD4DFD721751C |
| SSDEEP: | 12288:KPuYd+V6b1momPZeft0UA6aX9h8ktLNxH6EldpAlus6rjv8hcpJePuYd+V6b:KPuYd+V6bIomxit0b9JNxVAyrT8ipJeJ |
MALICIOUS
Writes to the Start menu file
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
Avemaria is detected
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
- 1mages.exe (PID: 3432)
Drops the executable file immediately after the start
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
Changes the autorun value in the registry
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
Runs injected code in another process
- 1mages.exe (PID: 3432)
Application was injected by another process
- Explorer.EXE (PID: 1100)
The process bypass UAC
- dism.exe (PID: 3148)
- dism.exe (PID: 3800)
- dism.exe (PID: 3688)
Loads dropped or rewritten executable
- dism.exe (PID: 3148)
- dism.exe (PID: 3800)
- dism.exe (PID: 3688)
AVEMARIA was detected
- 1mages.exe (PID: 3432)
SUSPICIOUS
Application launched itself
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 1860)
- 1mages.exe (PID: 1144)
Creates a directory in Program Files
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
Detected use of alternative data streams (AltDS)
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
Starts CMD.EXE for commands execution
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
- 1mages.exe (PID: 3432)
Executable content was dropped or overwritten
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
Starts itself from another location
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
INFO
Checks supported languages
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 1860)
- 1mages.exe (PID: 1144)
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 3940)
- 1mages.exe (PID: 3432)
- 1mages.exe (PID: 3572)
- 1mages.exe (PID: 3288)
- 1mages.exe (PID: 1320)
Reads the computer name
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 1860)
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
- 1mages.exe (PID: 1144)
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 3940)
- 1mages.exe (PID: 3432)
- 1mages.exe (PID: 3572)
- 1mages.exe (PID: 3288)
- 1mages.exe (PID: 1320)
Executable content was dropped or overwritten
- cmd.exe (PID: 3812)
- cmd.exe (PID: 2984)
Drops the executable file immediately after the start
- cmd.exe (PID: 3812)
- cmd.exe (PID: 2984)
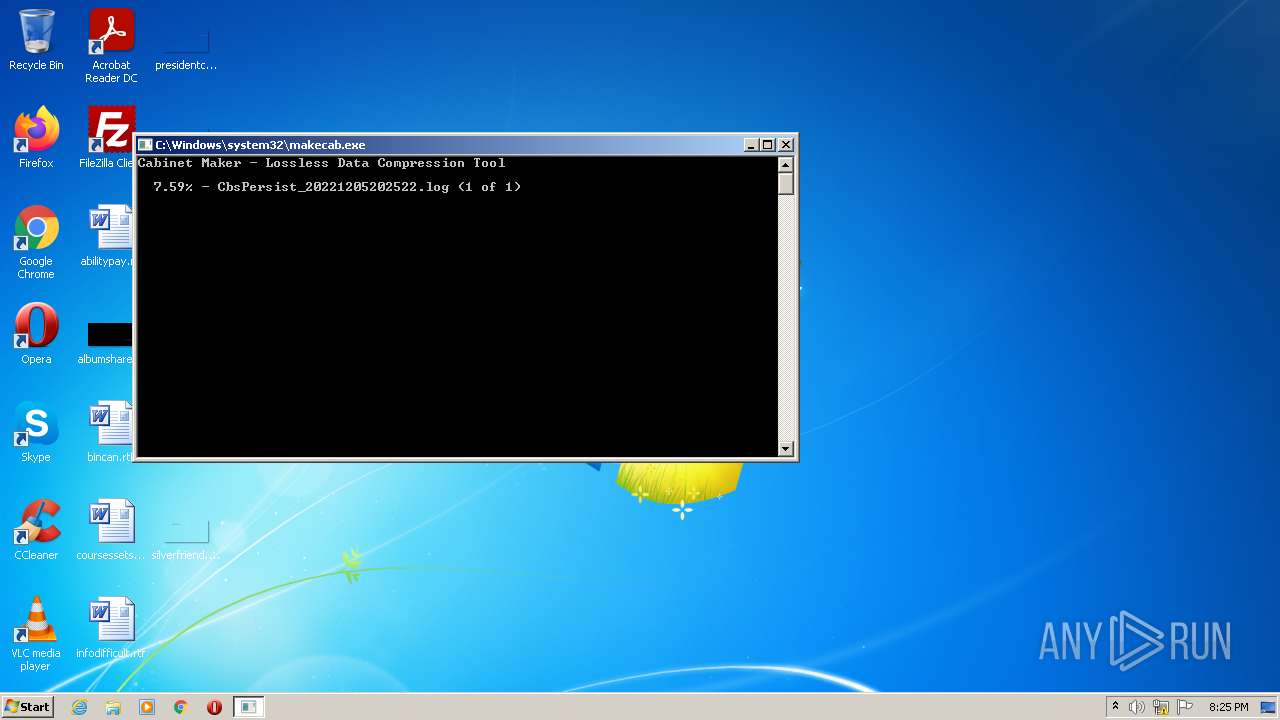
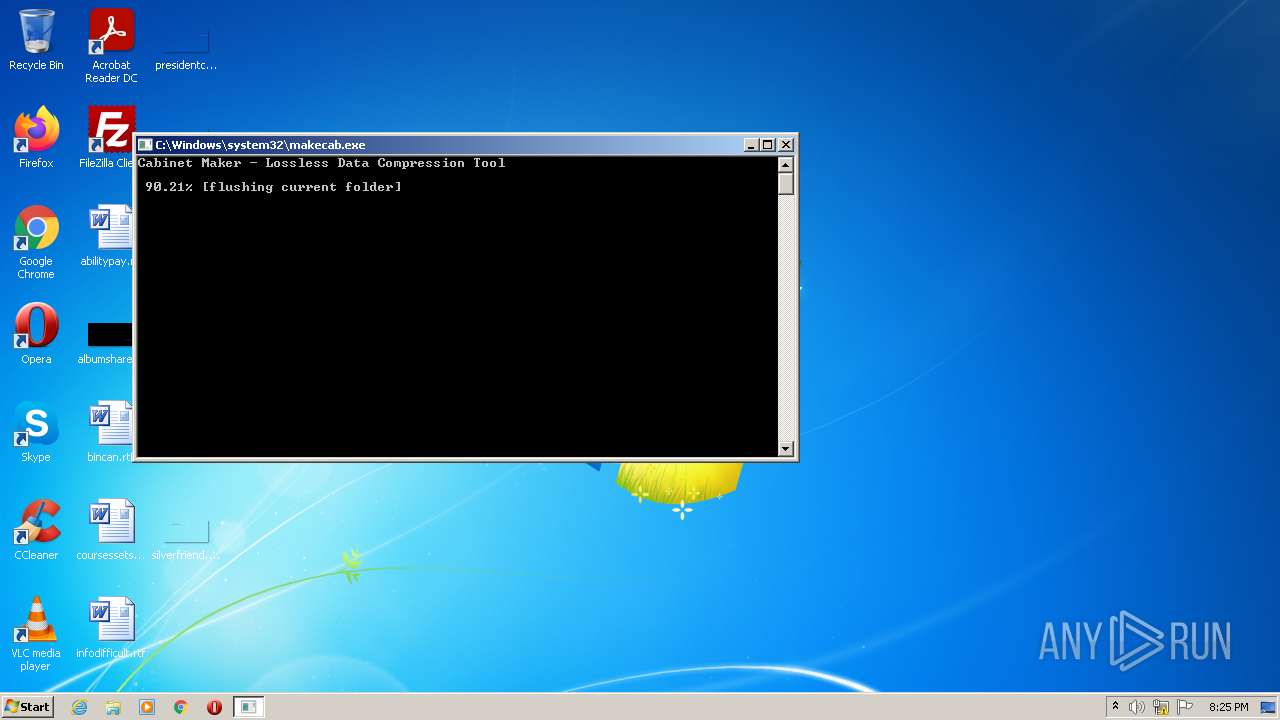
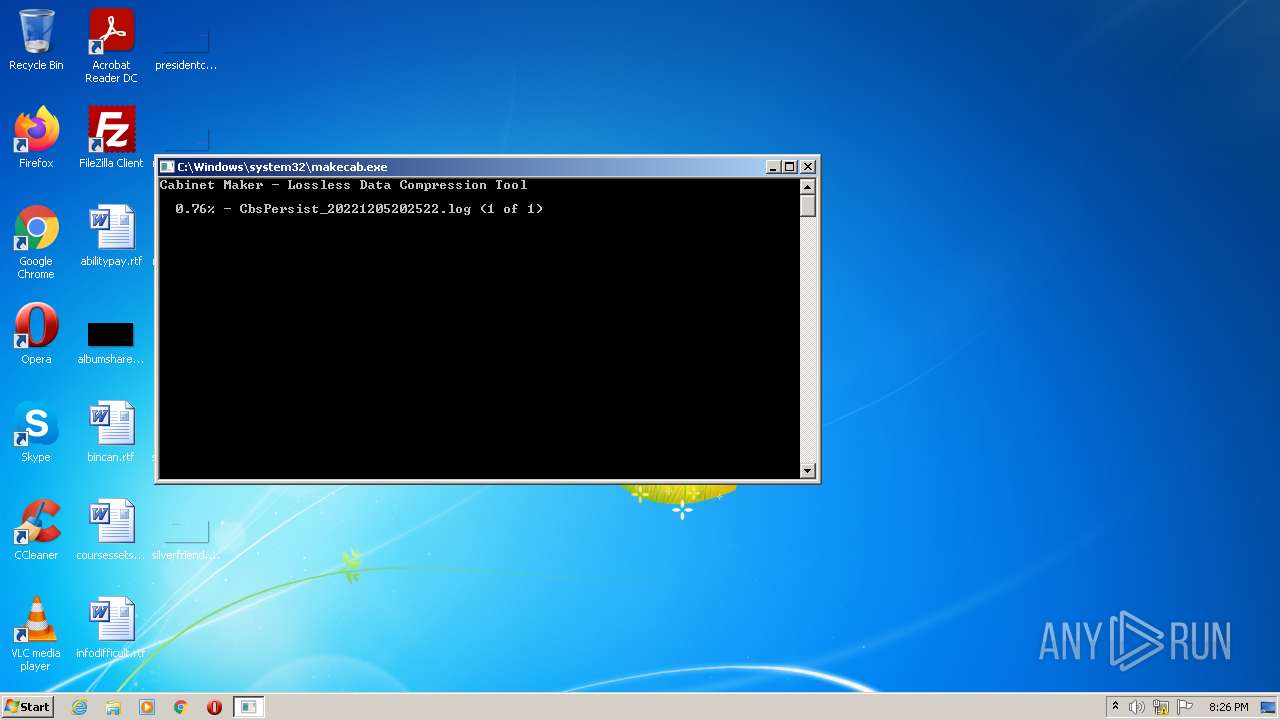
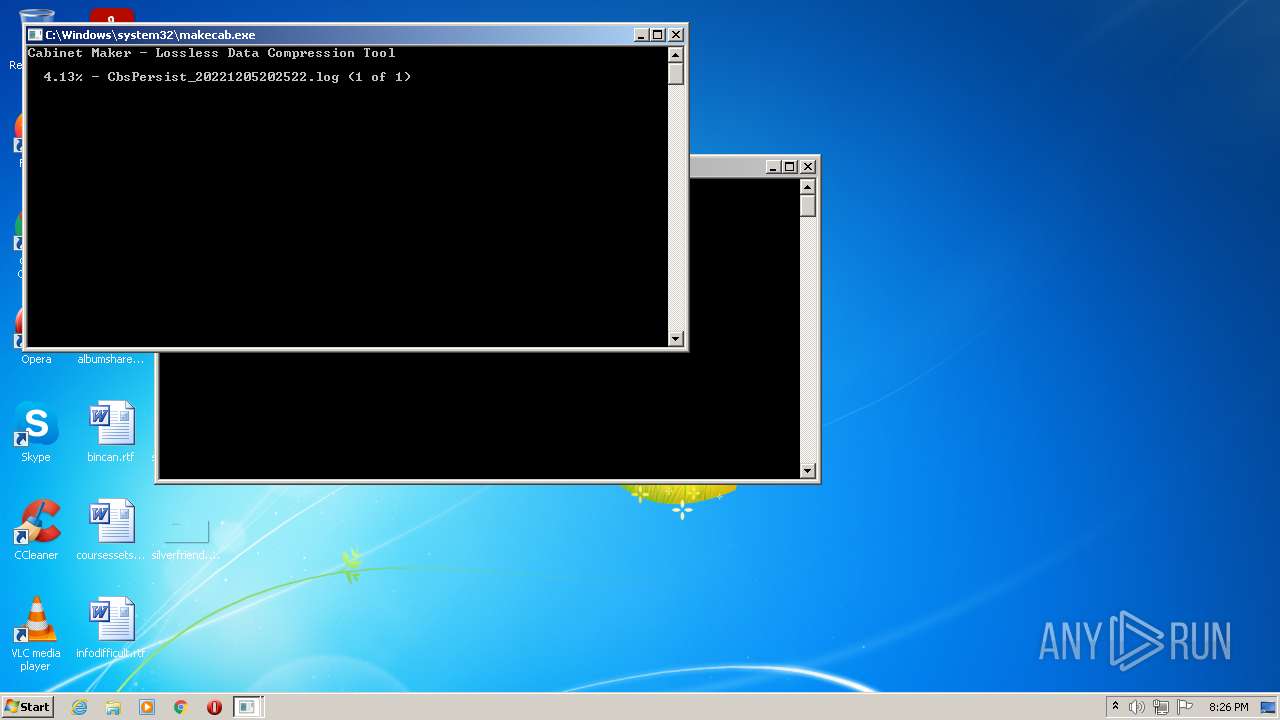
Creates a file in a temporary directory
- cmd.exe (PID: 3812)
- makecab.exe (PID: 2488)
- makecab.exe (PID: 2588)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 2984)
- makecab.exe (PID: 3068)
Drops a file that was compiled in debug mode
- 35f3f9e4d43cd037feadf2d7c81f9d90.exe (PID: 2220)
Checks transactions between databases Windows and Oracle
- cmd.exe (PID: 3812)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 2984)
Creates files in the Windows directory
- pkgmgr.exe (PID: 2104)
- makecab.exe (PID: 2488)
Manual execution by a user
- 1mages.exe (PID: 1320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2022-Dec-05 07:12:41 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | Home |
| FileDescription: | ElectionVotingSystem |
| FileVersion: | 1.0.0.0 |
| InternalName: | dFZj.exe |
| LegalCopyright: | Copyright © Home 2011 |
| LegalTrademarks: | - |
| OriginalFilename: | dFZj.exe |
| ProductName: | ElectionVotingSystem |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2022-Dec-05 07:12:41 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 548468 | 548864 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.57439 |
.rsrc | 557056 | 68724 | 69120 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.33604 |
.reloc | 630784 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.30609 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 1.98048 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 3.28128 | 844 | UNKNOWN | UNKNOWN | RT_VERSION |
Imports
mscoree.dll |
Total processes
74
Monitored processes
26
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 824 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1100 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1144 | "C:\Users\admin\Documents\1mages.exe" | C:\Users\admin\Documents\1mages.exe | — | 35f3f9e4d43cd037feadf2d7c81f9d90.exe | |||||||||||
User: admin Company: Home Integrity Level: MEDIUM Description: ElectionVotingSystem Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1320 | "C:\Users\admin\Documents\1mages.exe" | C:\Users\admin\Documents\1mages.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Home Integrity Level: MEDIUM Description: ElectionVotingSystem Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1336 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1860 | "C:\Users\admin\AppData\Local\Temp\35f3f9e4d43cd037feadf2d7c81f9d90.exe" | C:\Users\admin\AppData\Local\Temp\35f3f9e4d43cd037feadf2d7c81f9d90.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Home Integrity Level: MEDIUM Description: ElectionVotingSystem Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2104 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2220 | "C:\Users\admin\AppData\Local\Temp\35f3f9e4d43cd037feadf2d7c81f9d90.exe" | C:\Users\admin\AppData\Local\Temp\35f3f9e4d43cd037feadf2d7c81f9d90.exe | 35f3f9e4d43cd037feadf2d7c81f9d90.exe | ||||||||||||
User: admin Company: Home Integrity Level: MEDIUM Description: ElectionVotingSystem Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2488 | "C:\Windows\system32\makecab.exe" C:\Windows\Logs\CBS\CbsPersist_20221205202522.log C:\Windows\Logs\CBS\CbsPersist_20221205202522.cab | C:\Windows\system32\makecab.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 052
Read events
4 003
Write events
49
Delete events
0
Modification events
| (PID) Process: | (2220) 35f3f9e4d43cd037feadf2d7c81f9d90.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (2220) 35f3f9e4d43cd037feadf2d7c81f9d90.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (2220) 35f3f9e4d43cd037feadf2d7c81f9d90.exe | Key: | HKEY_CURRENT_USER\Software\_rptls |
| Operation: | write | Name: | Install |
Value: C:\Users\admin\AppData\Local\Temp\35f3f9e4d43cd037feadf2d7c81f9d90.exe | |||
| (PID) Process: | (2220) 35f3f9e4d43cd037feadf2d7c81f9d90.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\PRZKN0OOBI |
| Operation: | write | Name: | inst |
Value: 0A0EADF8B10D576066E173DC67D32EF8C40486A0F619863BFBCEE9C12C3F05DEBFFF6D3C9466F2EA0D96002FD1B2EB18A379B1FB7DF28EFAC5C13175CB76BC17F69EE4B45498CE13 | |||
| (PID) Process: | (2220) 35f3f9e4d43cd037feadf2d7c81f9d90.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 1mages |
Value: C:\Users\admin\Documents\1mages.exe | |||
| (PID) Process: | (3812) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3812) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3812) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3812) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3432) 1mages.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
Executable files
8
Suspicious files
6
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | pkgmgr.exe | C:\Windows\Logs\CBS\CbsPersist_20221205202522.log | — | |
MD5:— | SHA256:— | |||
| 2220 | 35f3f9e4d43cd037feadf2d7c81f9d90.exe | C:\Users\admin\Documents\1mages.exe | executable | |
MD5:— | SHA256:— | |||
| 2220 | 35f3f9e4d43cd037feadf2d7c81f9d90.exe | C:\Users\admin\Documents\Documents:ApplicationData | executable | |
MD5:— | SHA256:— | |||
| 2488 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2488_3 | binary | |
MD5:— | SHA256:— | |||
| 2104 | pkgmgr.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:— | SHA256:— | |||
| 2488 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2488_5 | binary | |
MD5:— | SHA256:— | |||
| 2488 | makecab.exe | C:\Windows\Logs\CBS\CbsPersist_20221205202522.cab | compressed | |
MD5:— | SHA256:— | |||
| 3272 | DllHost.exe | C:\Windows\System32\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 4024 | cmd.exe | C:\Users\admin\AppData\Local\Temp\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 2220 | 35f3f9e4d43cd037feadf2d7c81f9d90.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\programs.bat | text | |
MD5:08723FDD18DA4274C4B0A3D71EA6BF20 | SHA256:27BE5CFBAAB7E724BCBB0703A72DD6B7397EF6E03139C349872D78C0ADAD3EF0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3432 | 1mages.exe | 51.178.11.185:5200 | — | OVH SAS | FR | malicious |
DNS requests
Threats
1 ETPRO signatures available at the full report