| File name: | 1234.bin |
| Full analysis: | https://app.any.run/tasks/0638d56d-340c-4e8b-98e0-9aaa2db7db7f |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | April 01, 2023, 15:53:53 |
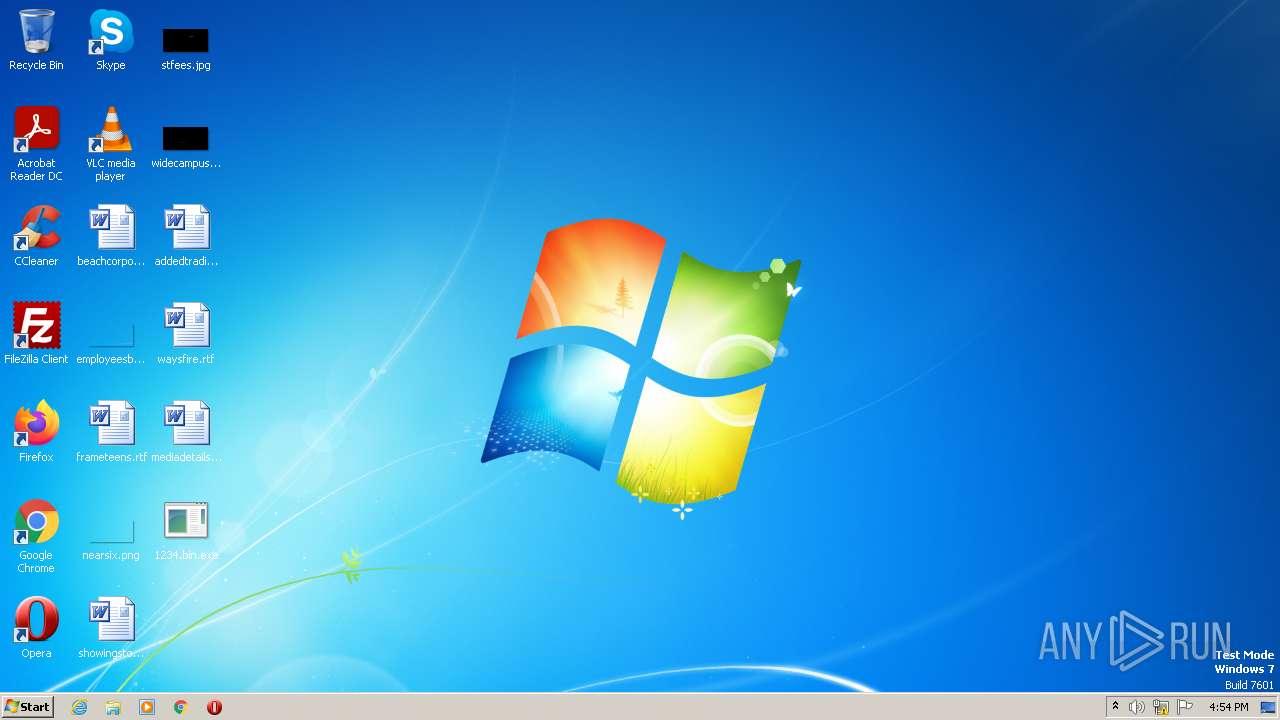
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0C86D90E27B215F73B4BFBF01DF55300 |
| SHA1: | 8A6C675E4AD0CF9E87B71CCA0FD33CE662F66493 |
| SHA256: | 35CAC46427A2BA75C114DEF3C77F0C7A39421C6CAF5C7639164F8778862B1DFE |
| SSDEEP: | 24576:i+5T4MROxnFm5bHKTlQYrZlI0AilFEvxHiz9:H50MiAYrZlI0AilFEvxHi |
MALICIOUS
Starts Visual C# compiler
- 1234.bin.exe (PID: 2956)
- 1234.bin.exe (PID: 848)
Orcus is detected
- 1234.bin.exe (PID: 2956)
- 1234.bin.exe (PID: 848)
ORCUS detected by memory dumps
- 1234.bin.exe (PID: 848)
SUSPICIOUS
Uses .NET C# to load dll
- 1234.bin.exe (PID: 2956)
- 1234.bin.exe (PID: 848)
Executable content was dropped or overwritten
- csc.exe (PID: 3156)
- csc.exe (PID: 2180)
Reads the Internet Settings
- 1234.bin.exe (PID: 2956)
- eventvwr.exe (PID: 1636)
- 1234.bin.exe (PID: 848)
INFO
Create files in a temporary directory
- 1234.bin.exe (PID: 2956)
- cvtres.exe (PID: 3072)
- 1234.bin.exe (PID: 848)
- csc.exe (PID: 3156)
- csc.exe (PID: 2180)
- cvtres.exe (PID: 2436)
Checks supported languages
- 1234.bin.exe (PID: 2956)
- csc.exe (PID: 3156)
- cvtres.exe (PID: 3072)
- 1234.bin.exe (PID: 848)
- csc.exe (PID: 2180)
- cvtres.exe (PID: 2436)
Reads the machine GUID from the registry
- 1234.bin.exe (PID: 2956)
- csc.exe (PID: 3156)
- cvtres.exe (PID: 3072)
- 1234.bin.exe (PID: 848)
- cvtres.exe (PID: 2436)
- csc.exe (PID: 2180)
The process checks LSA protection
- csc.exe (PID: 3156)
- cvtres.exe (PID: 3072)
- 1234.bin.exe (PID: 848)
- 1234.bin.exe (PID: 2956)
- eventvwr.exe (PID: 1636)
- cvtres.exe (PID: 2436)
- csc.exe (PID: 2180)
Reads the computer name
- 1234.bin.exe (PID: 2956)
- 1234.bin.exe (PID: 848)
Reads Environment values
- 1234.bin.exe (PID: 848)
Creates files or folders in the user directory
- 1234.bin.exe (PID: 848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Orcus
(PID) Process(848) 1234.bin.exe
C2 (1)192.168.0.200:1604
Keys
AES68a325664bceb9b16306f4c1aef06bb0c016f8e479dfd2fe6c22e1c24a980fe6
Salt
Options
AutostartBuilderProperty
AutostartMethodDisable
TaskSchedulerTaskNameOrcus
TaskHighestPrivilegestrue
RegistryHiddenStarttrue
RegistryKeyNameOrcus
TryAllAutostartMethodsOnFailtrue
ChangeAssemblyInformationBuilderProperty
ChangeAssemblyInformationfalse
AssemblyTitlenull
AssemblyDescriptionnull
AssemblyCompanyNamenull
AssemblyProductNamenull
AssemblyCopyrightnull
AssemblyTrademarksnull
AssemblyProductVersion1.0.0.0
AssemblyFileVersion1.0.0.0
ChangeCreationDateBuilderProperty
IsEnabledfalse
NewCreationDate2023-04-01T13:17:42.4814158+03:00
ChangeIconBuilderProperty
ChangeIconfalse
IconPathnull
ClientTagBuilderProperty
ClientTagnull
DataFolderBuilderProperty
Path%appdata%\Orcus
DefaultPrivilegesBuilderProperty
RequireAdministratorRightsfalse
DisableInstallationPromptBuilderProperty
IsDisabledfalse
FrameworkVersionBuilderProperty
FrameworkVersionNET35
HideFileBuilderProperty
HideFilefalse
InstallationLocationBuilderProperty
Path%programfiles%\Orcus\Orcus.exe
InstallBuilderProperty
Installtrue
KeyloggerBuilderProperty
IsEnabledfalse
MutexBuilderProperty
Mutex82ccc5fb388f44aa869844f2adc5290d
ProxyBuilderProperty
ProxyOptionNone
ProxyAddressnull
ProxyPort1080
ProxyType2
ReconnectDelayProperty
Delay10000
RequireAdministratorPrivilegesInstallerBuilderProperty
RequireAdministratorPrivilegestrue
RespawnTaskBuilderProperty
IsEnabledfalse
TaskNameOrcus Respawner
ServiceBuilderProperty
Installfalse
SetRunProgramAsAdminFlagBuilderProperty
SetFlagfalse
WatchdogBuilderProperty
IsEnabledfalse
NameOrcusWatchdog.exe
WatchdogLocationAppData
PreventFileDeletionfalse
Plugins
PluginNameBSoD Protection
PluginVersion2.0
ResourceNamec50ffc6c9613411bb21099a690fc228d
ResourceTypeClientPlugin
Guiddccbc1db-f7d1-413d-bba4-72611d485d3a
PluginNameDisable Webcam Lights
PluginVersion1.0
ResourceName666535df0e3b41c8a78db9a86f920d79
ResourceTypeClientPlugin
Guide6ee5674-bb94-46c7-8bbc-5729af6e2c28
PluginNameSilent Elevation
PluginVersion1.5
ResourceName0101e2157338472983d661dc1af22aee
ResourceTypeClientPlugin
Guid0a189c79-87ca-4d8d-bfb5-fac811f4048e
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | - |
| OriginalFileName: | Orcus.exe |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | Orcus.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | - |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xe506e |
| UninitializedDataSize: | - |
| InitializedDataSize: | 4608 |
| CodeSize: | 930304 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:04:01 10:18:07+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2023 10:18:07 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Orcus.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Orcus.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Apr-2023 10:18:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000E3074 | 0x000E3200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.15535 |
.rsrc | 0x000E6000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99406 |
.reloc | 0x000E8000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99793 | 3128 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
48
Monitored processes
8
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Users\admin\Desktop\1234.bin.exe" | C:\Users\admin\Desktop\1234.bin.exe | eventvwr.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
Orcus(PID) Process(848) 1234.bin.exe C2 (1)192.168.0.200:1604 Keys AES68a325664bceb9b16306f4c1aef06bb0c016f8e479dfd2fe6c22e1c24a980fe6 Salt Options AutostartBuilderProperty AutostartMethodDisable TaskSchedulerTaskNameOrcus TaskHighestPrivilegestrue RegistryHiddenStarttrue RegistryKeyNameOrcus TryAllAutostartMethodsOnFailtrue ChangeAssemblyInformationBuilderProperty ChangeAssemblyInformationfalse AssemblyTitlenull AssemblyDescriptionnull AssemblyCompanyNamenull AssemblyProductNamenull AssemblyCopyrightnull AssemblyTrademarksnull AssemblyProductVersion1.0.0.0 AssemblyFileVersion1.0.0.0 ChangeCreationDateBuilderProperty IsEnabledfalse NewCreationDate2023-04-01T13:17:42.4814158+03:00 ChangeIconBuilderProperty ChangeIconfalse IconPathnull ClientTagBuilderProperty ClientTagnull DataFolderBuilderProperty Path%appdata%\Orcus DefaultPrivilegesBuilderProperty RequireAdministratorRightsfalse DisableInstallationPromptBuilderProperty IsDisabledfalse FrameworkVersionBuilderProperty FrameworkVersionNET35 HideFileBuilderProperty HideFilefalse InstallationLocationBuilderProperty Path%programfiles%\Orcus\Orcus.exe InstallBuilderProperty Installtrue KeyloggerBuilderProperty IsEnabledfalse MutexBuilderProperty Mutex82ccc5fb388f44aa869844f2adc5290d ProxyBuilderProperty ProxyOptionNone ProxyAddressnull ProxyPort1080 ProxyType2 ReconnectDelayProperty Delay10000 RequireAdministratorPrivilegesInstallerBuilderProperty RequireAdministratorPrivilegestrue RespawnTaskBuilderProperty IsEnabledfalse TaskNameOrcus Respawner ServiceBuilderProperty Installfalse SetRunProgramAsAdminFlagBuilderProperty SetFlagfalse WatchdogBuilderProperty IsEnabledfalse NameOrcusWatchdog.exe WatchdogLocationAppData PreventFileDeletionfalse Plugins PluginNameBSoD Protection PluginVersion2.0 ResourceNamec50ffc6c9613411bb21099a690fc228d ResourceTypeClientPlugin Guiddccbc1db-f7d1-413d-bba4-72611d485d3a PluginNameDisable Webcam Lights PluginVersion1.0 ResourceName666535df0e3b41c8a78db9a86f920d79 ResourceTypeClientPlugin Guide6ee5674-bb94-46c7-8bbc-5729af6e2c28 PluginNameSilent Elevation PluginVersion1.5 ResourceName0101e2157338472983d661dc1af22aee ResourceTypeClientPlugin Guid0a189c79-87ca-4d8d-bfb5-fac811f4048e | |||||||||||||||
| 1636 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | 1234.bin.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Event Viewer Snapin Launcher Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2180 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\fenmuwrj.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | 1234.bin.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2436 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESFC63.tmp" "c:\Users\admin\AppData\Local\Temp\CSCFC62.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\Desktop\1234.bin.exe" | C:\Users\admin\Desktop\1234.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3072 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESF7CF.tmp" "c:\Users\admin\AppData\Local\Temp\CSCF7BE.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 3156 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\4wke0pjl.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | 1234.bin.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 3516 | "C:\Windows\System32\eventvwr.exe" | C:\Windows\System32\eventvwr.exe | — | 1234.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Event Viewer Snapin Launcher Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 274
Read events
2 240
Write events
32
Delete events
2
Modification events
| (PID) Process: | (2956) 1234.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2956) 1234.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2956) 1234.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2956) 1234.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1636) eventvwr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1636) eventvwr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1636) eventvwr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1636) eventvwr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (848) 1234.bin.exe | Key: | HKEY_CLASSES_ROOT\mscfile\shell\open\command |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
4
Suspicious files
0
Text files
14
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2956 | 1234.bin.exe | C:\Users\admin\AppData\Local\Temp\4wke0pjl.cmdline | text | |
MD5:— | SHA256:— | |||
| 3156 | csc.exe | C:\Users\admin\AppData\Local\Temp\4wke0pjl.dll | executable | |
MD5:— | SHA256:— | |||
| 2956 | 1234.bin.exe | C:\Users\admin\AppData\Local\Temp\4wke0pjl.0.cs | text | |
MD5:— | SHA256:— | |||
| 3072 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESF7CF.tmp | o | |
MD5:— | SHA256:— | |||
| 3156 | csc.exe | C:\Users\admin\AppData\Local\Temp\4wke0pjl.out | text | |
MD5:— | SHA256:— | |||
| 3156 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCF7BE.tmp | res | |
MD5:— | SHA256:— | |||
| 848 | 1234.bin.exe | C:\Users\admin\AppData\Local\Temp\fenmuwrj.0.cs | text | |
MD5:— | SHA256:— | |||
| 848 | 1234.bin.exe | C:\Users\admin\AppData\Local\Temp\fenmuwrj.cmdline | text | |
MD5:— | SHA256:— | |||
| 2180 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCFC62.tmp | res | |
MD5:— | SHA256:— | |||
| 2436 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESFC63.tmp | o | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.n1ckna.me |
| unknown |