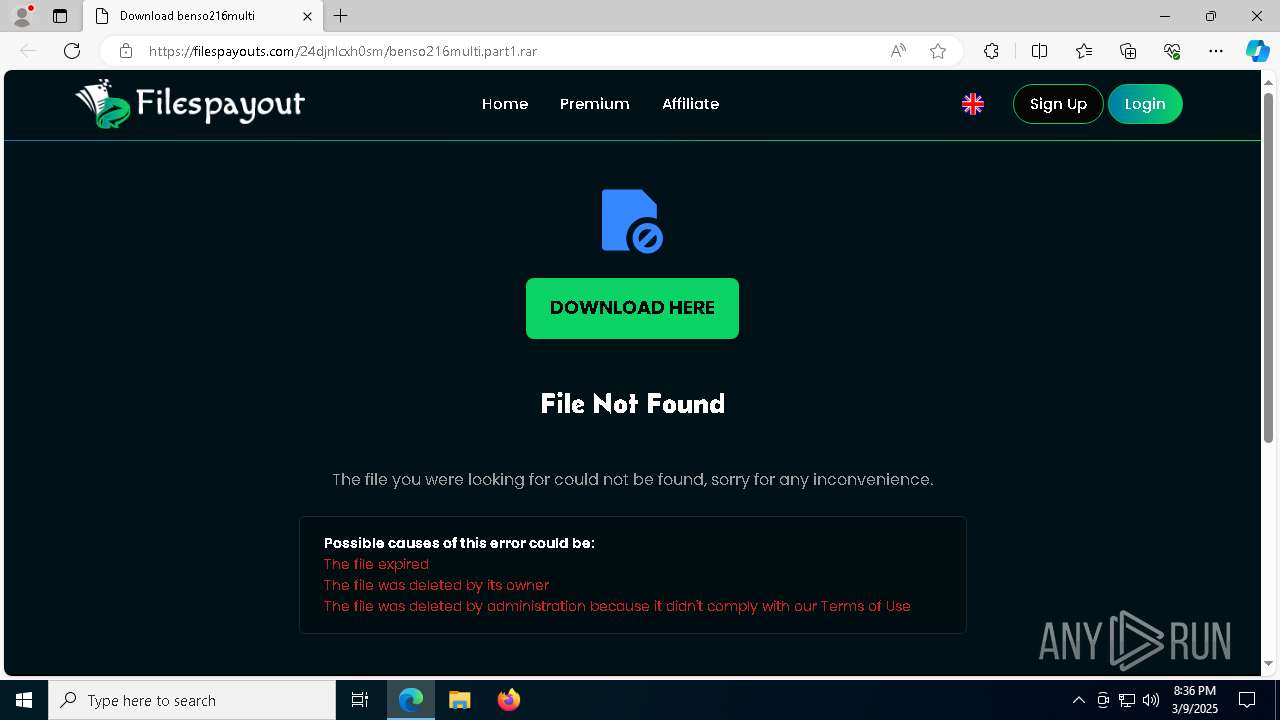
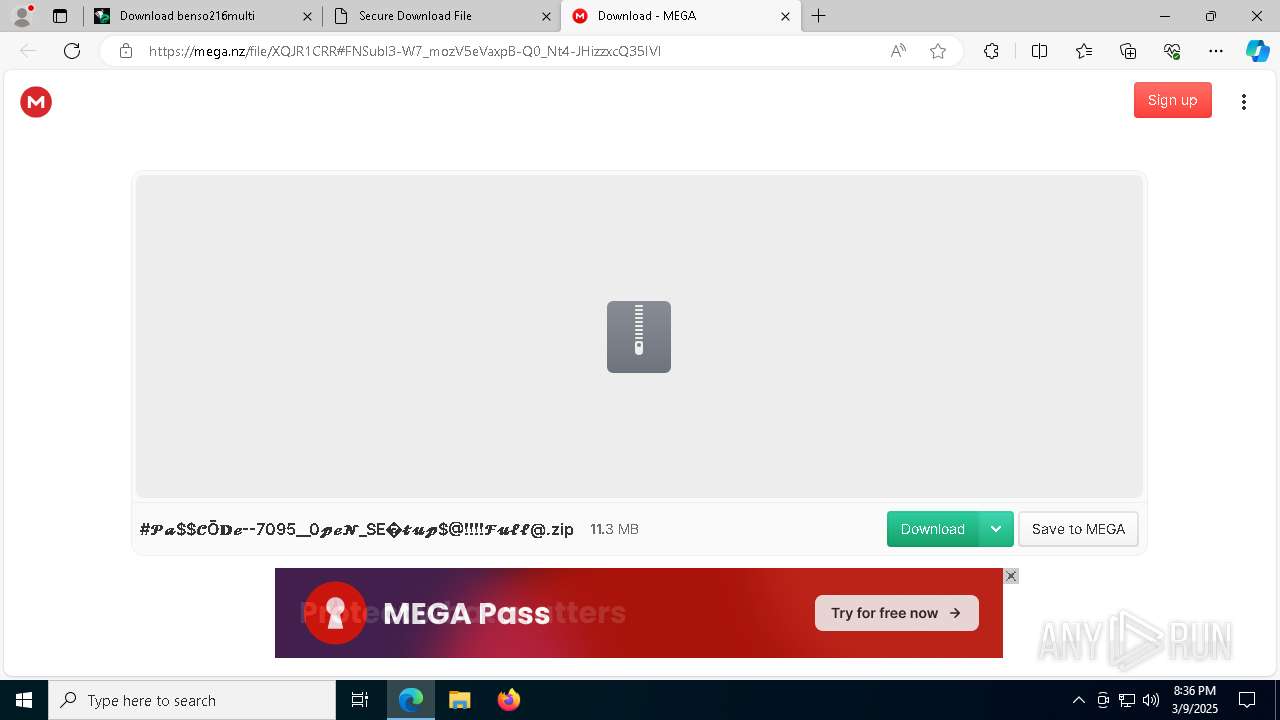
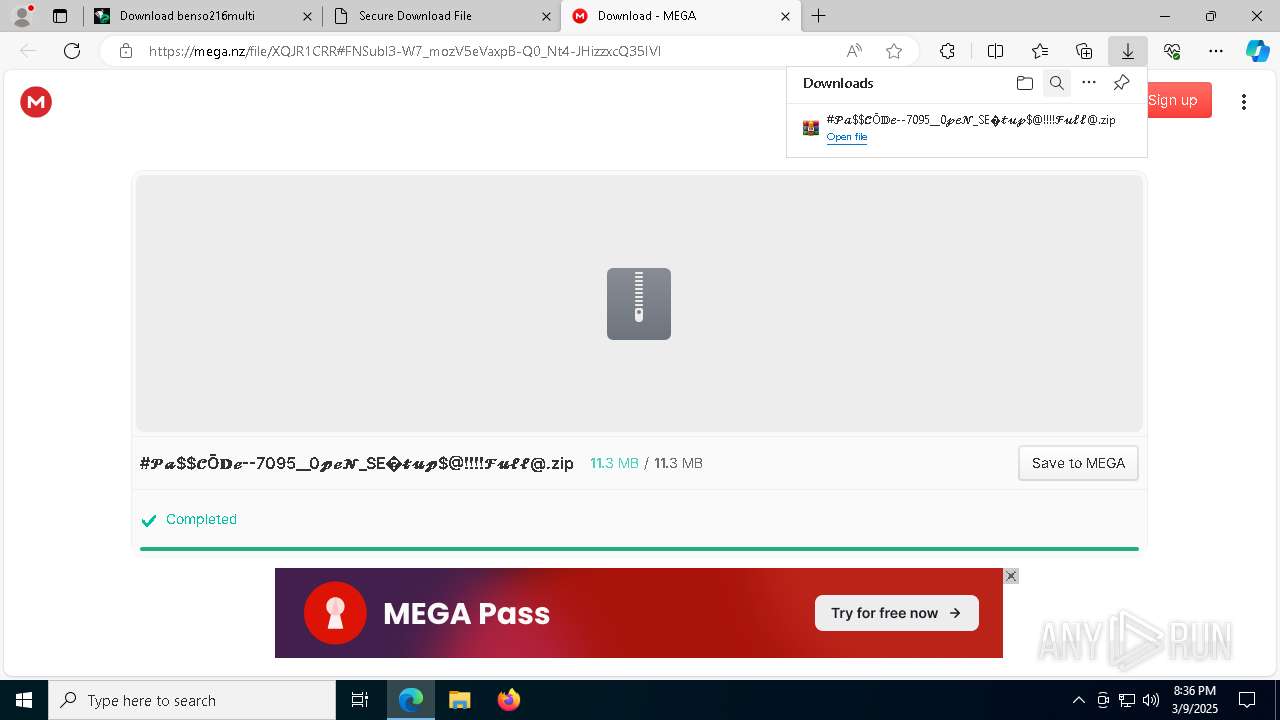
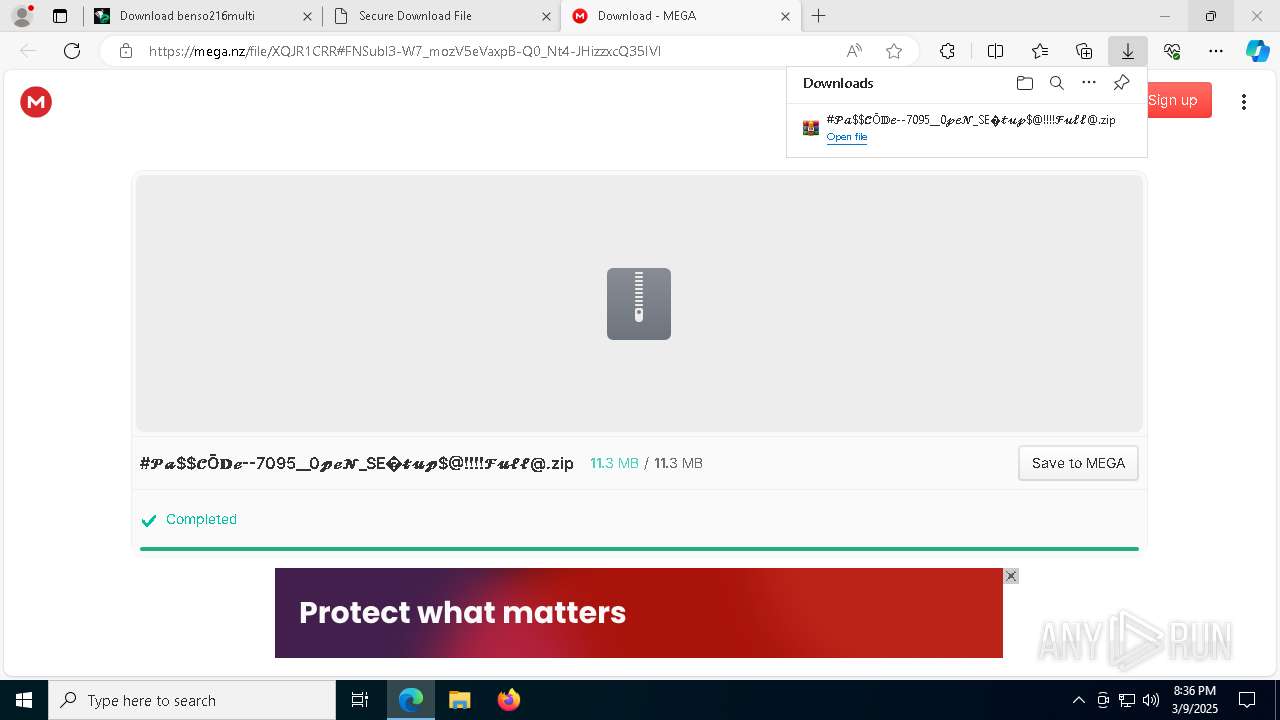
| URL: | https://filespayout.com/24djnlcxh0sm/benso216multi.part1.rar |
| Full analysis: | https://app.any.run/tasks/840bc890-27fd-4090-9f63-19713bd8397d |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 09, 2025, 20:36:08 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | EBD86CA88D23F3CFE813483D792320CC |
| SHA1: | 23BCC8C5863A6EEDAE521A1C72B7D84D73998B41 |
| SHA256: | 355F7F2363BB10678F0A152AD0AB4F287D1FA8B454D3741CC18FA97541C7B14C |
| SSDEEP: | 3:N83cwMzgNVPEMABFn:23cwMgHPrCFn |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7328)
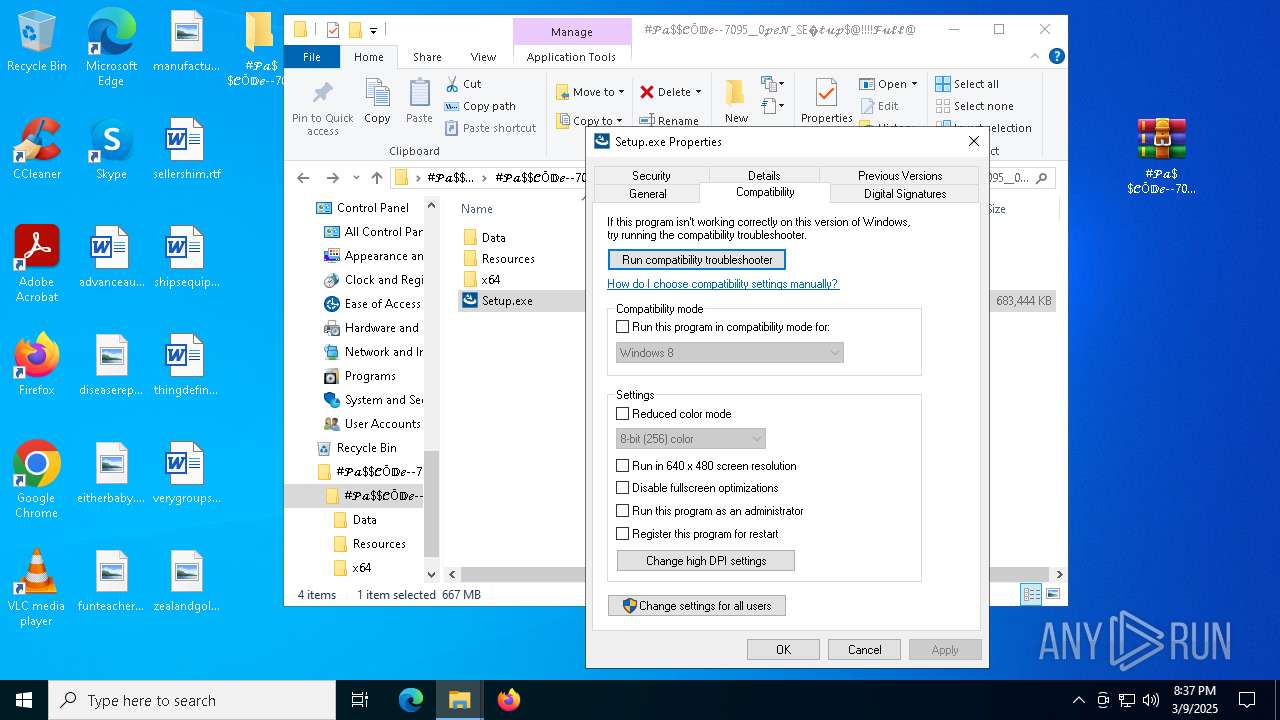
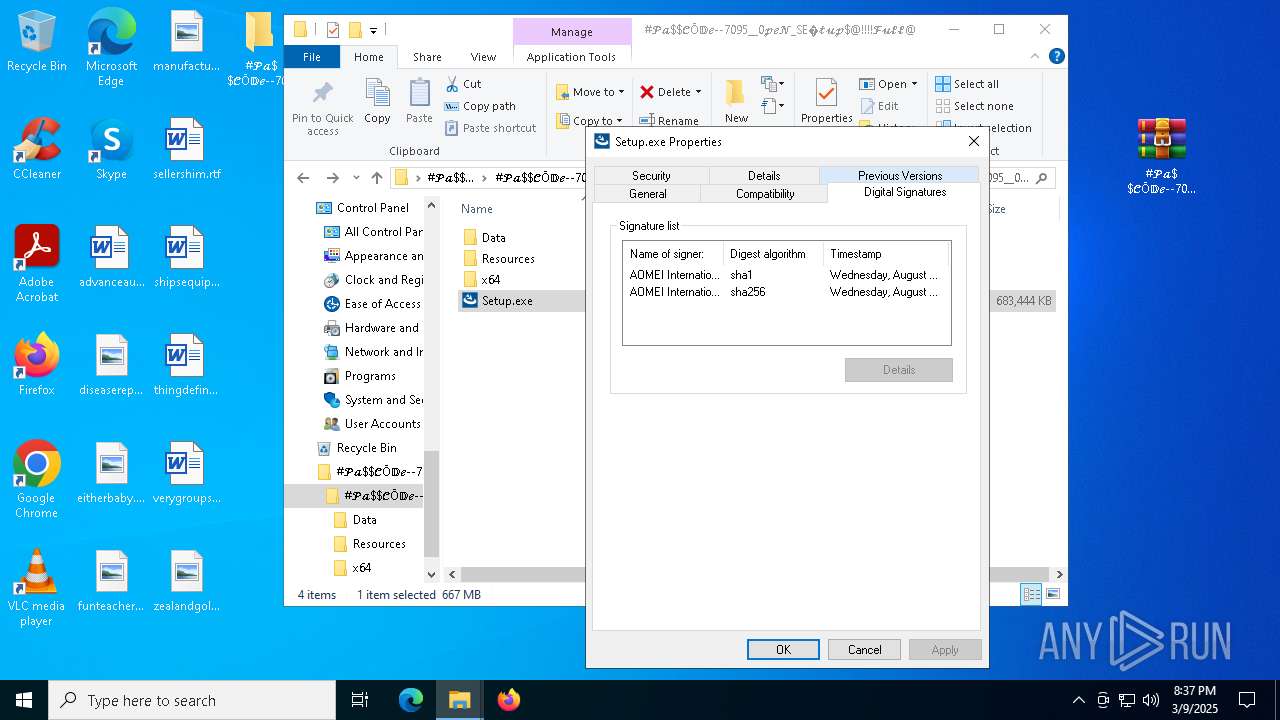
Executing a file with an untrusted certificate
- Setup.exe (PID: 5964)
- ISBEW64.exe (PID: 8564)
- ISBEW64.exe (PID: 8692)
- ISBEW64.exe (PID: 8812)
- ISBEW64.exe (PID: 1764)
- ISBEW64.exe (PID: 7180)
- ISBEW64.exe (PID: 7280)
LUMMA mutex has been found
- svchost.exe (PID: 8496)
Steals credentials from Web Browsers
- svchost.exe (PID: 8496)
Known privilege escalation attack
- dllhost.exe (PID: 7592)
SUSPICIOUS
Searches for installed software
- Setup.exe (PID: 5964)
- setup.exe (PID: 1184)
- svchost.exe (PID: 8496)
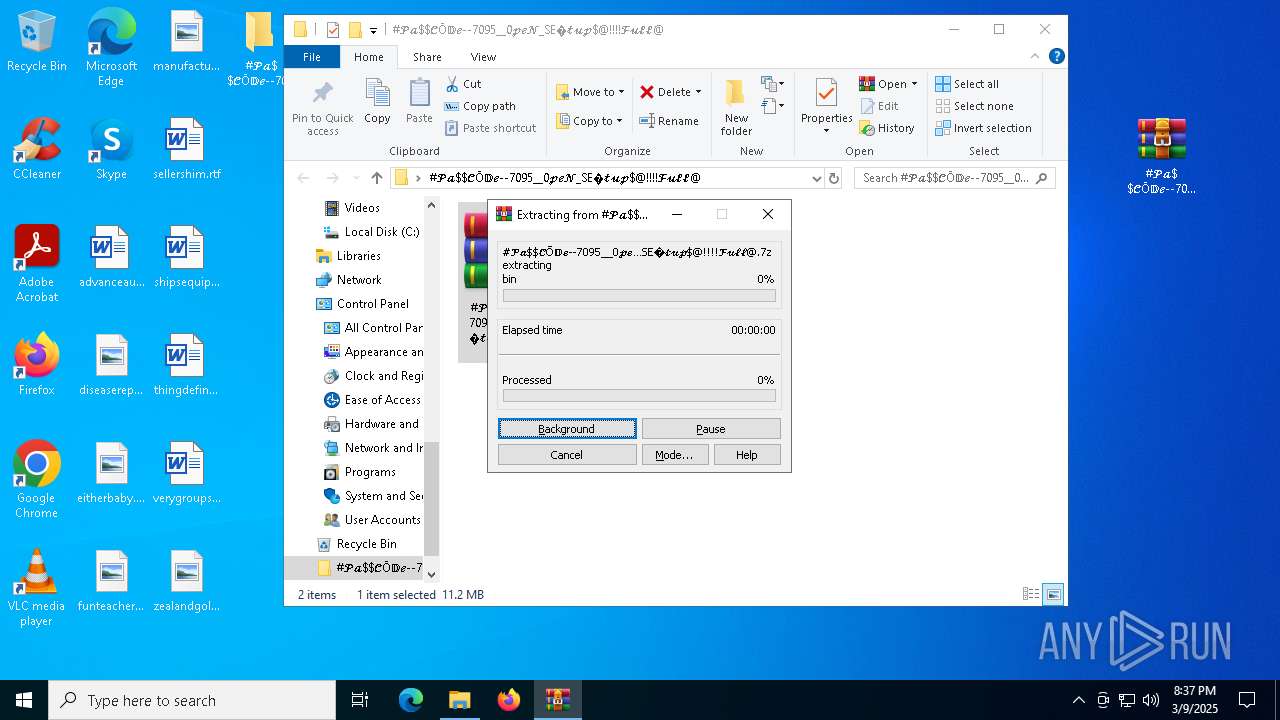
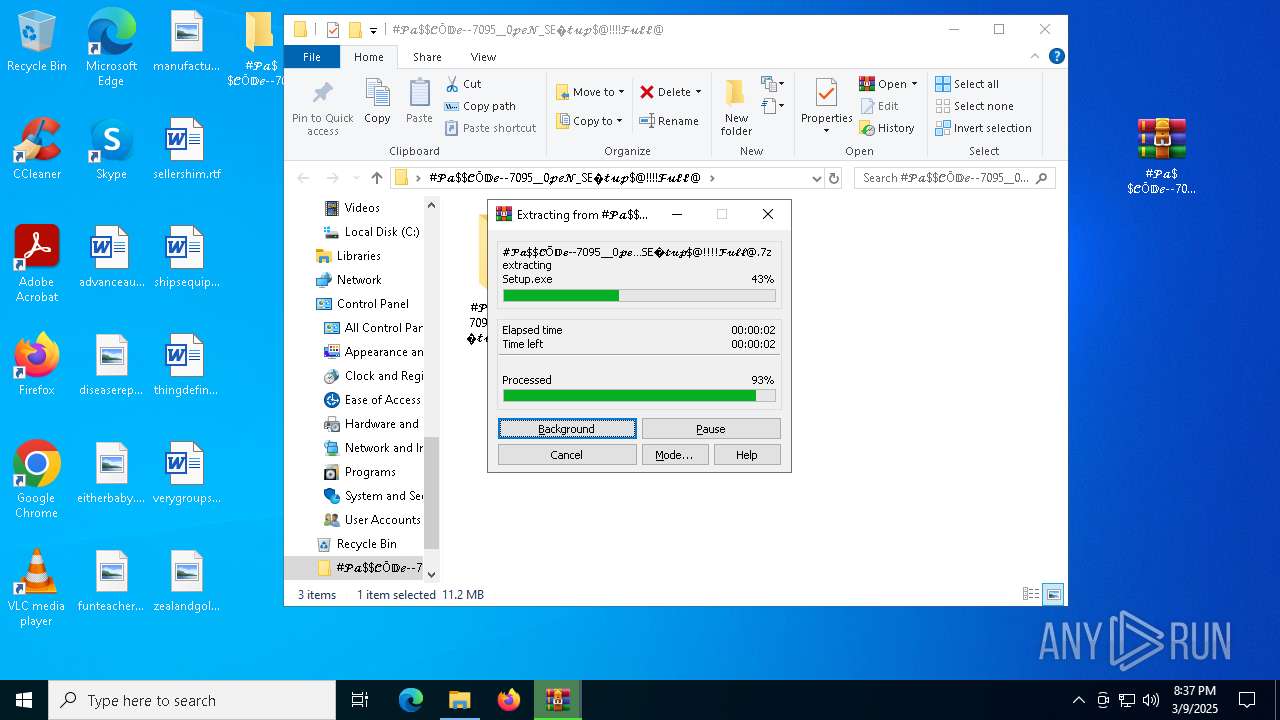
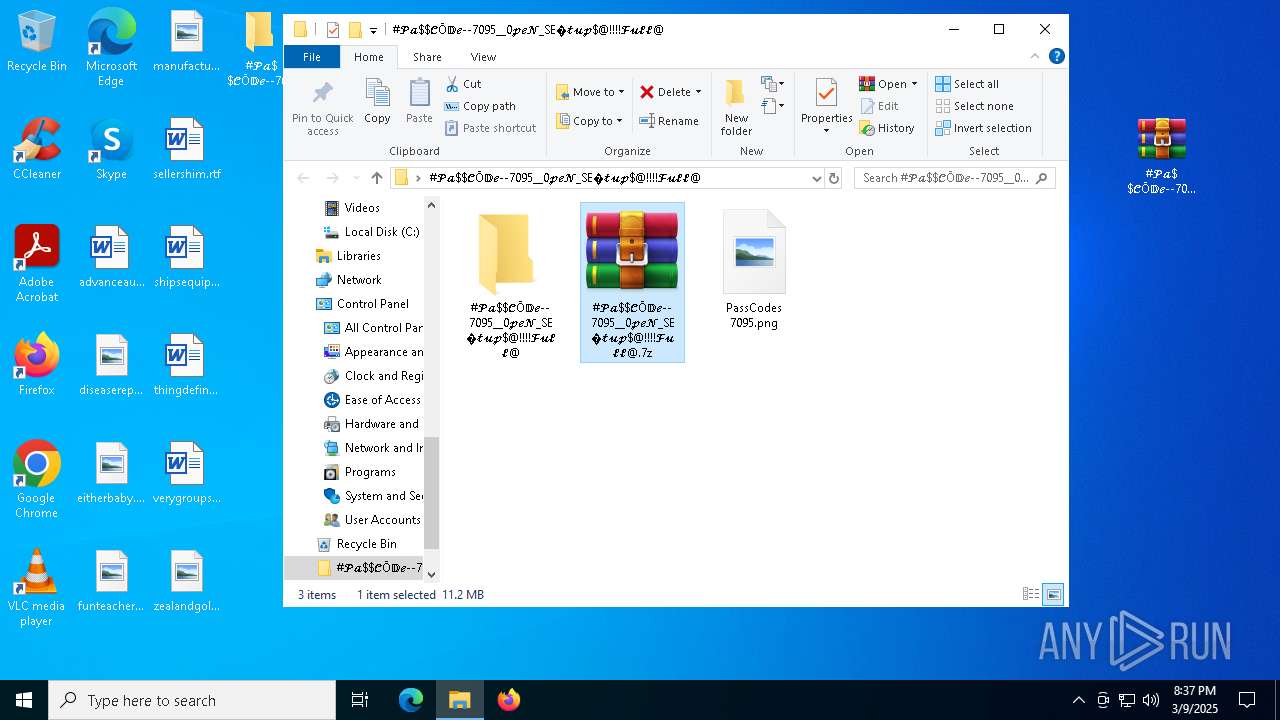
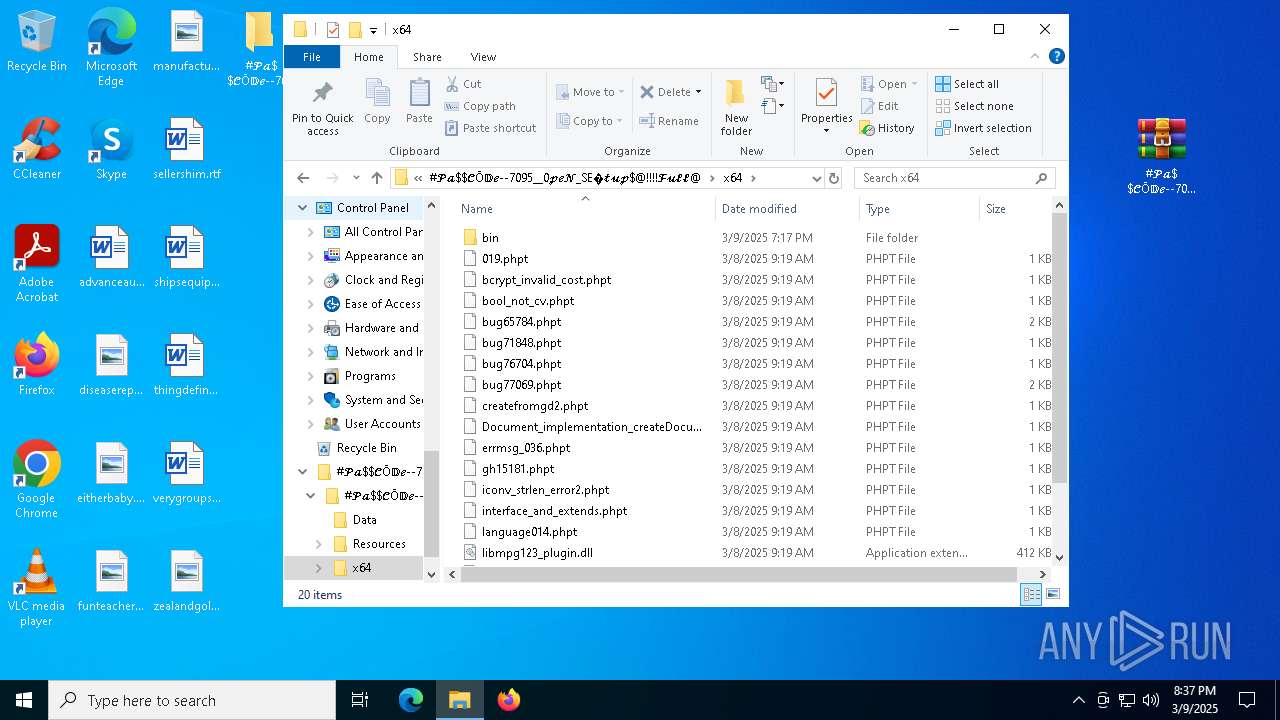
Executable content was dropped or overwritten
- Setup.exe (PID: 5964)
- setup.exe (PID: 1184)
- ABSchedhlp.exe (PID: 7260)
- svchost.exe (PID: 8496)
- Frame.exe (PID: 6964)
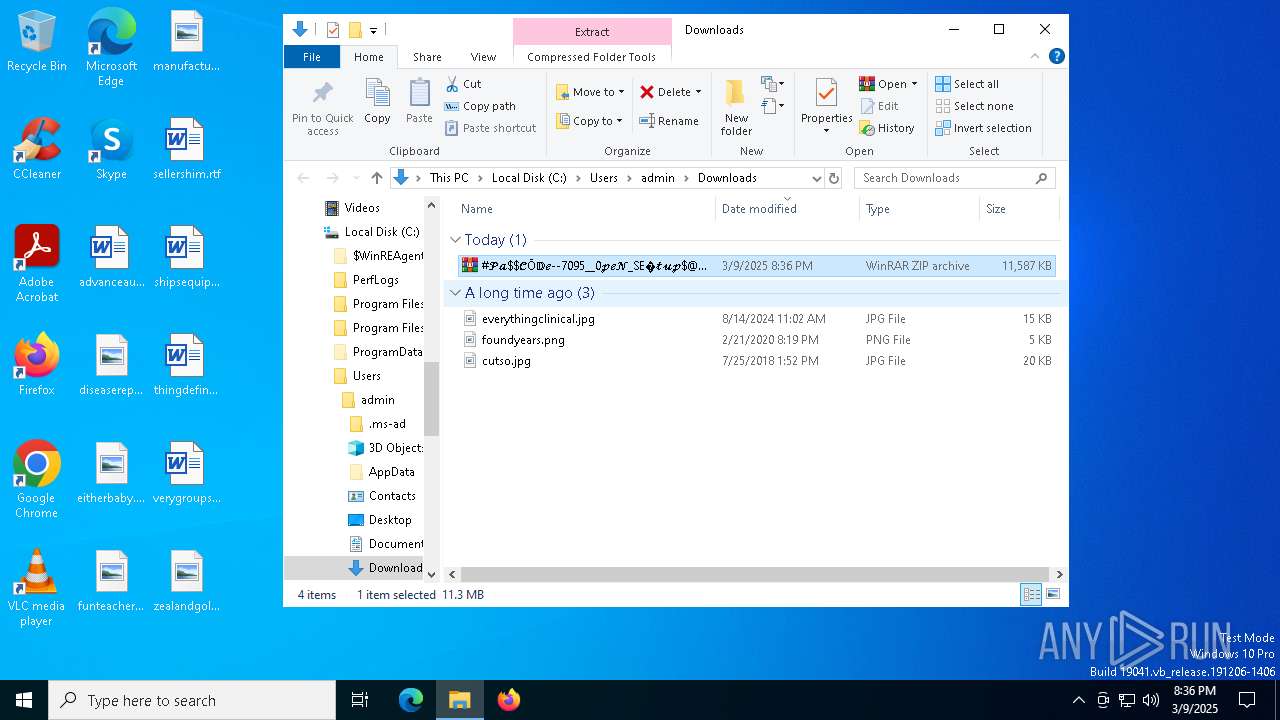
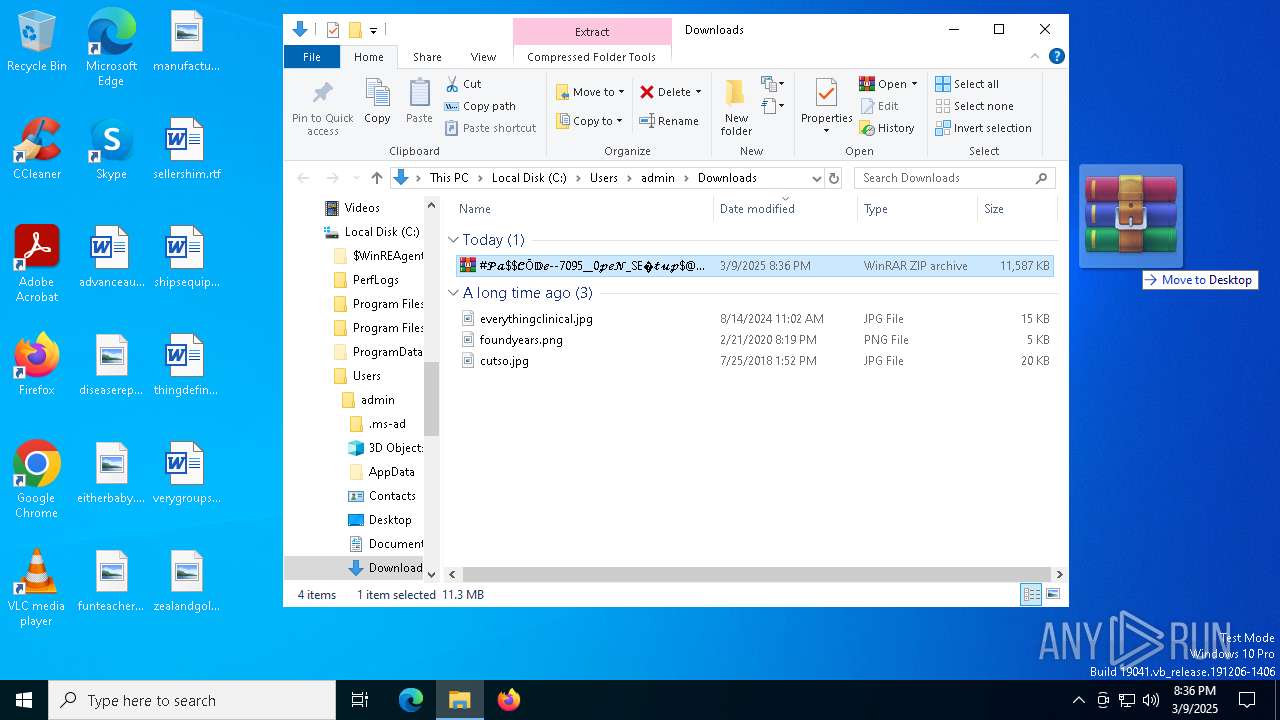
The process creates files with name similar to system file names
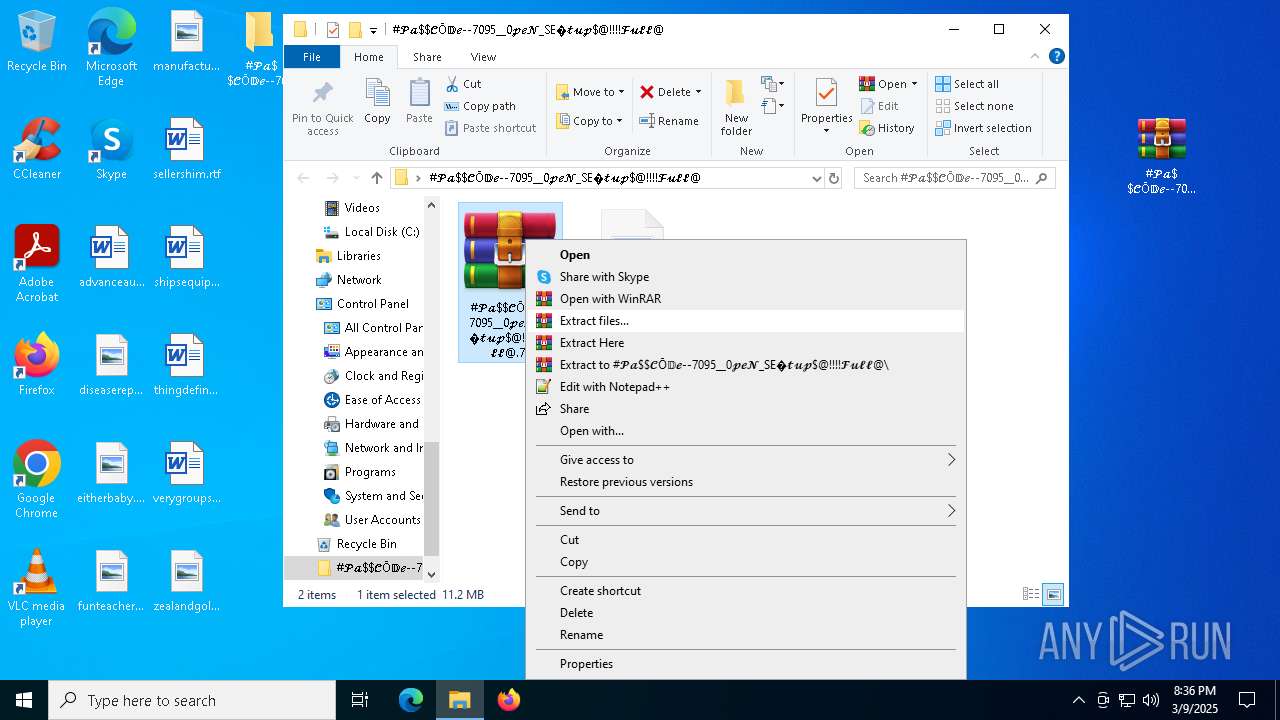
- WinRAR.exe (PID: 660)
Process drops legitimate windows executable
- WinRAR.exe (PID: 660)
- setup.exe (PID: 1184)
- ABSchedhlp.exe (PID: 7260)
- Frame.exe (PID: 6964)
The process drops C-runtime libraries
- setup.exe (PID: 1184)
- ABSchedhlp.exe (PID: 7260)
- svchost.exe (PID: 8496)
- Frame.exe (PID: 6964)
Starts itself from another location
- ABSchedhlp.exe (PID: 7260)
Starts application with an unusual extension
- ABSchedhlp.exe (PID: 7412)
- Frame.exe (PID: 4652)
- Frame.exe (PID: 6964)
There is functionality for taking screenshot (YARA)
- setup.exe (PID: 1184)
- Setup.exe (PID: 5964)
INFO
Checks supported languages
- identity_helper.exe (PID: 3332)
- identity_helper.exe (PID: 9012)
- Setup.exe (PID: 5964)
- setup.exe (PID: 1184)
- ISBEW64.exe (PID: 8692)
- ISBEW64.exe (PID: 8564)
- ISBEW64.exe (PID: 8812)
- ISBEW64.exe (PID: 1764)
- ABSchedhlp.exe (PID: 7412)
- ABSchedhlp.exe (PID: 7260)
- more.com (PID: 5596)
- ISBEW64.exe (PID: 7180)
- ISBEW64.exe (PID: 7280)
- Frame.exe (PID: 4652)
- more.com (PID: 8204)
- Frame.exe (PID: 6964)
- more.com (PID: 5304)
Reads the computer name
- identity_helper.exe (PID: 9012)
- identity_helper.exe (PID: 3332)
- setup.exe (PID: 1184)
- Setup.exe (PID: 5964)
- ISBEW64.exe (PID: 8692)
- ISBEW64.exe (PID: 8564)
- ISBEW64.exe (PID: 8812)
- ISBEW64.exe (PID: 1764)
- ISBEW64.exe (PID: 7180)
- ABSchedhlp.exe (PID: 7412)
- ISBEW64.exe (PID: 7280)
- ABSchedhlp.exe (PID: 7260)
- Frame.exe (PID: 4652)
- more.com (PID: 8204)
- more.com (PID: 5596)
- Frame.exe (PID: 6964)
- more.com (PID: 5304)
Reads Environment values
- identity_helper.exe (PID: 3332)
- identity_helper.exe (PID: 9012)
Application launched itself
- msedge.exe (PID: 2140)
- msedge.exe (PID: 1568)
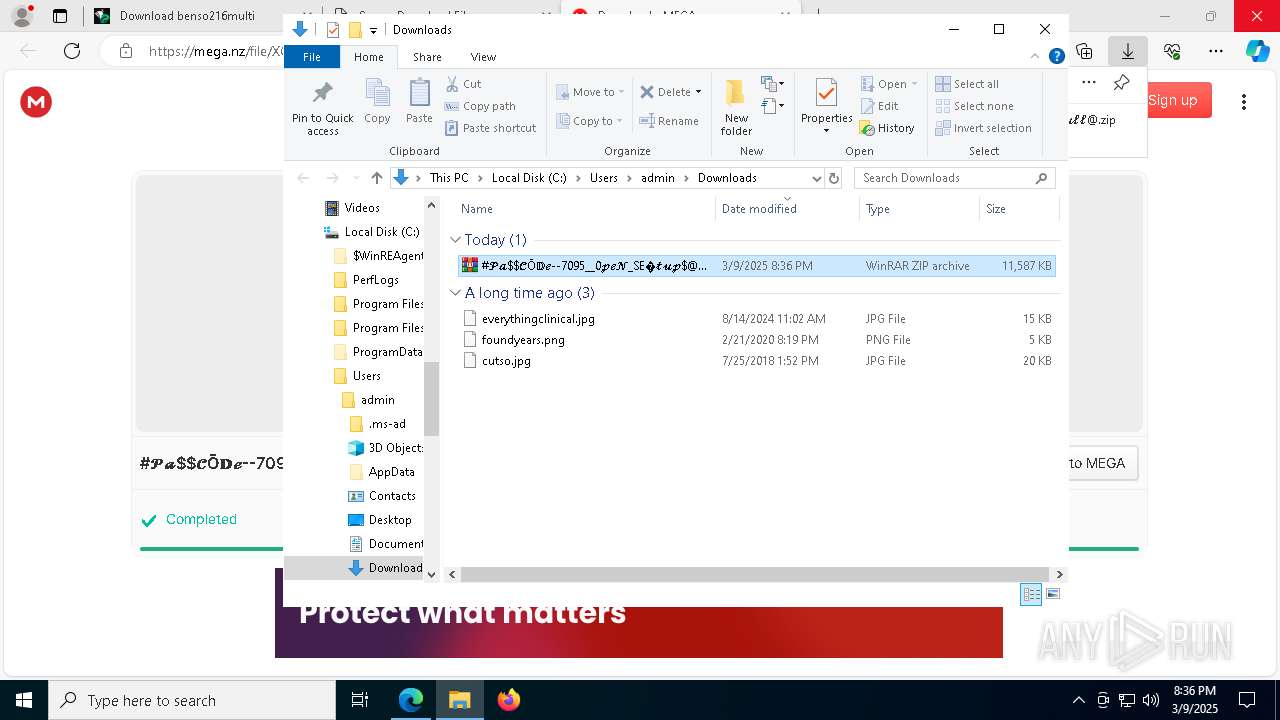
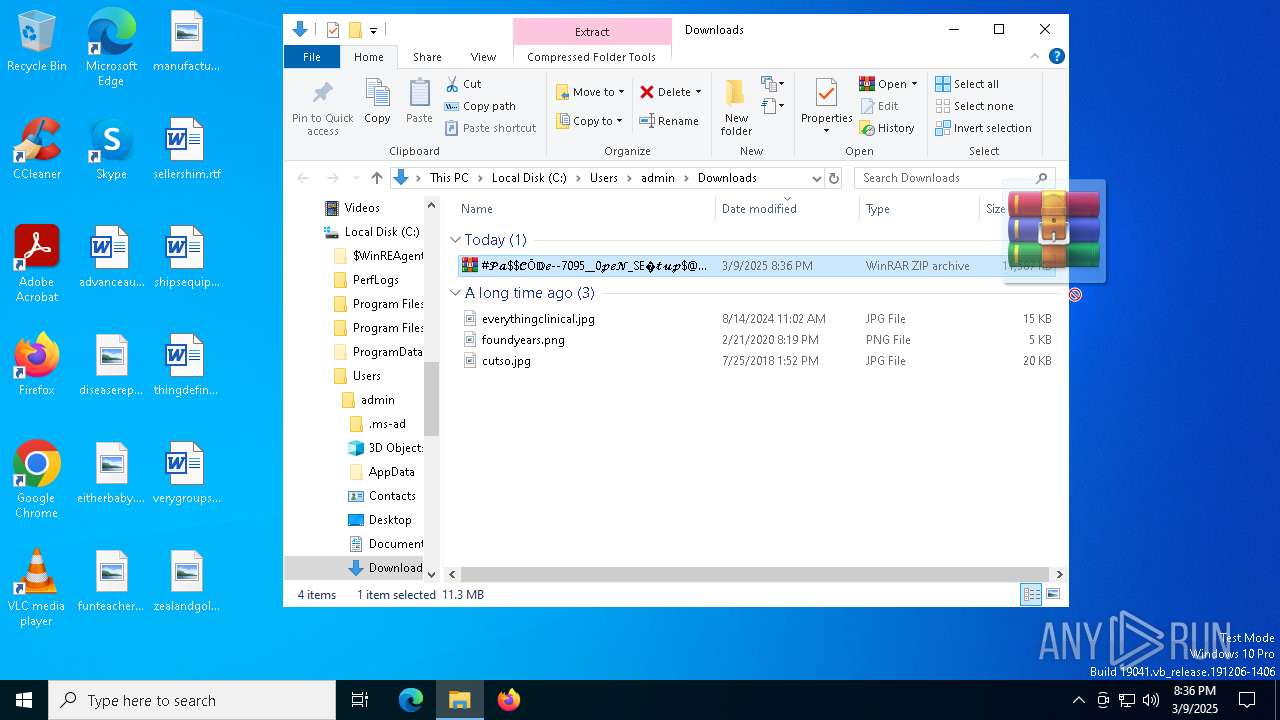
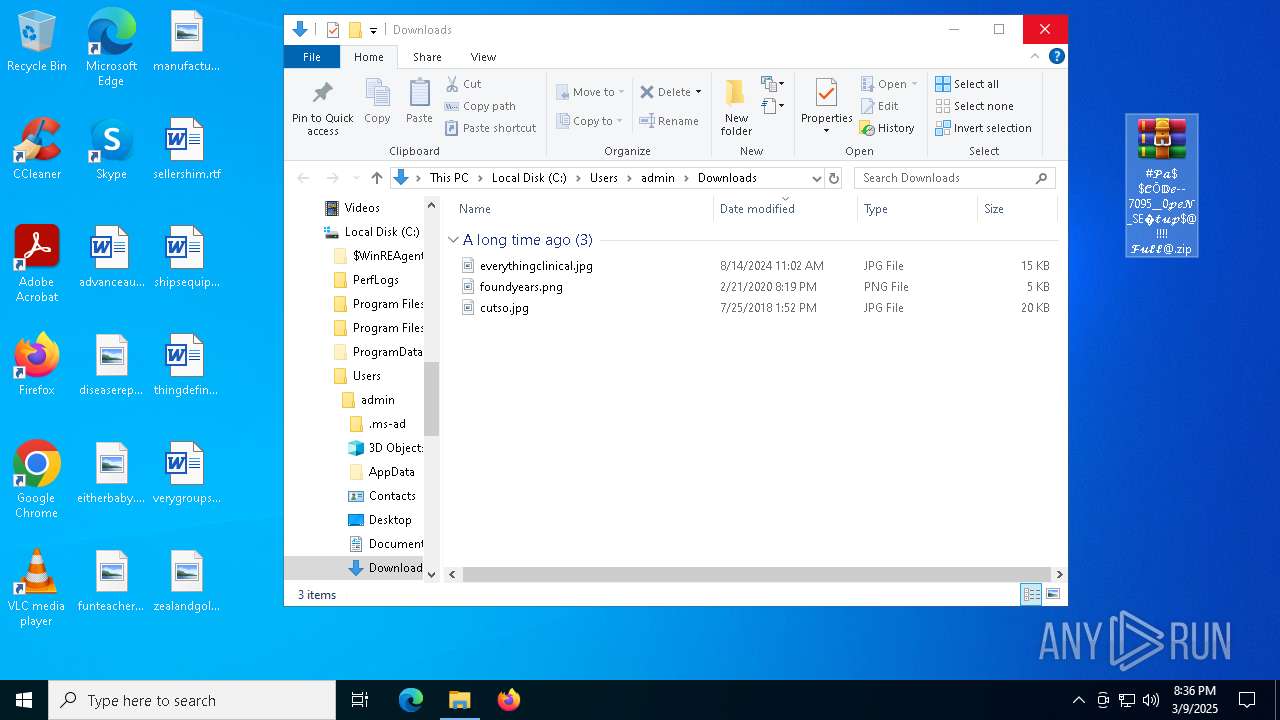
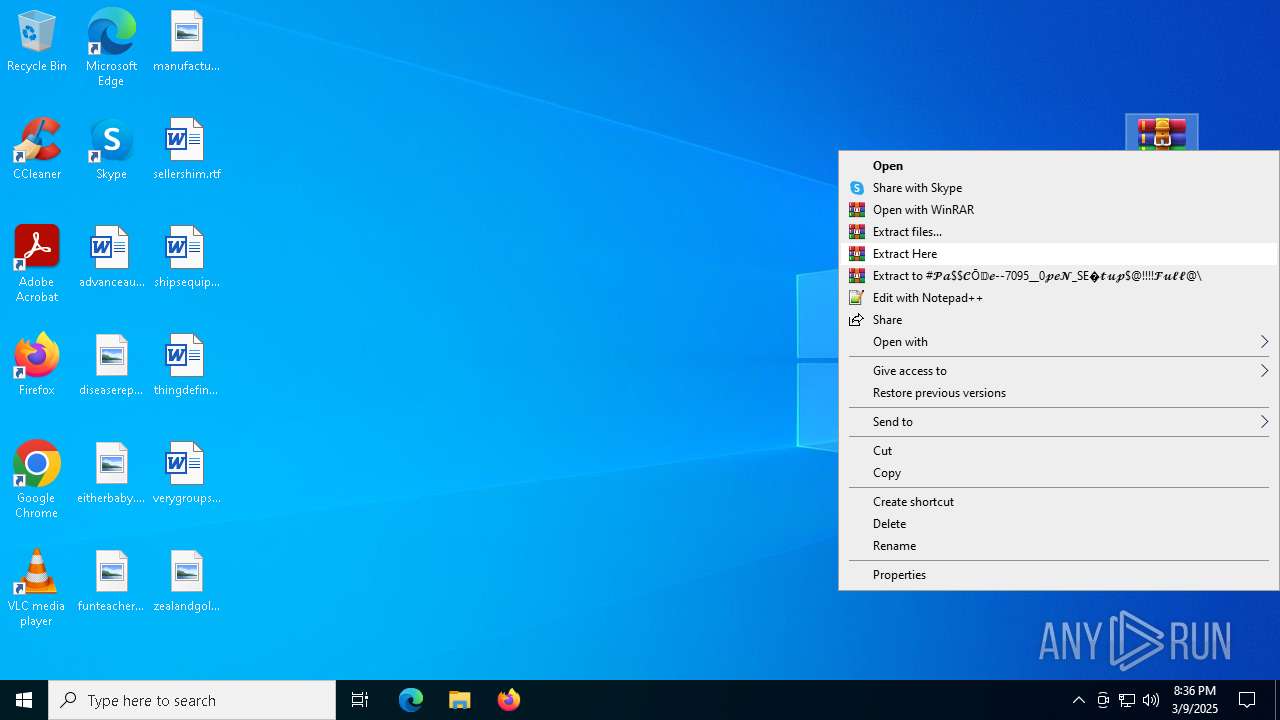
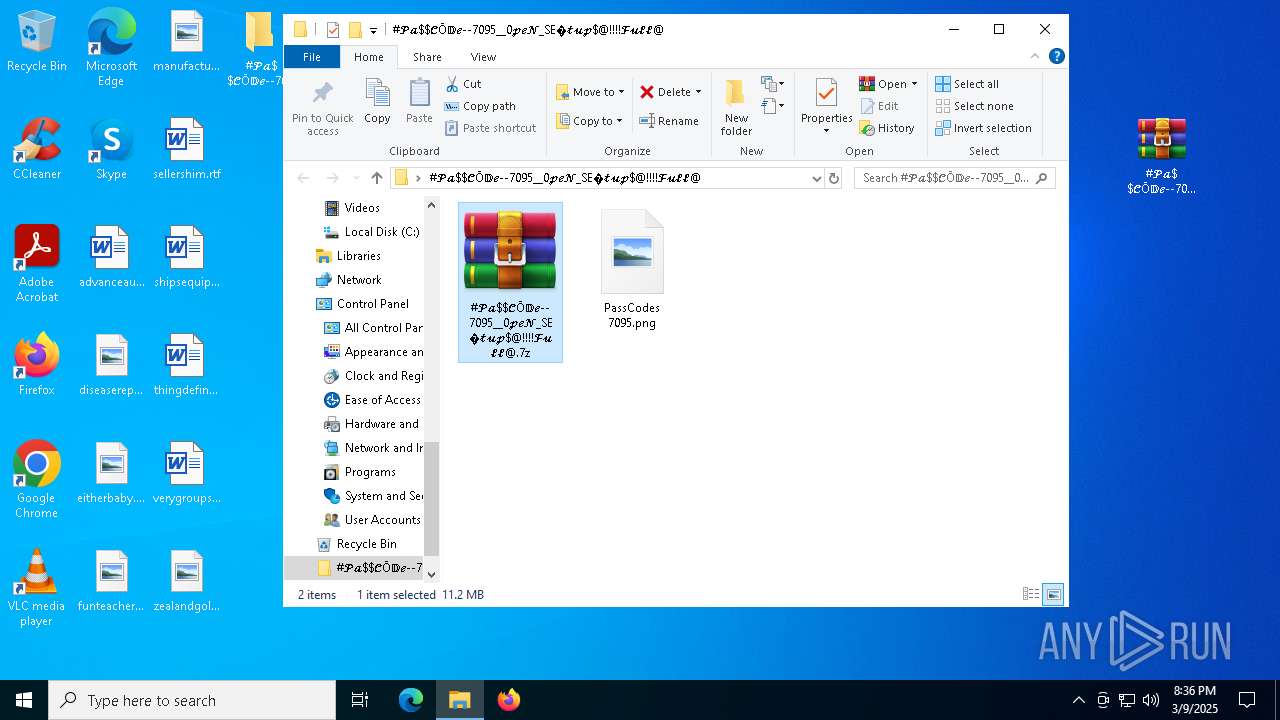
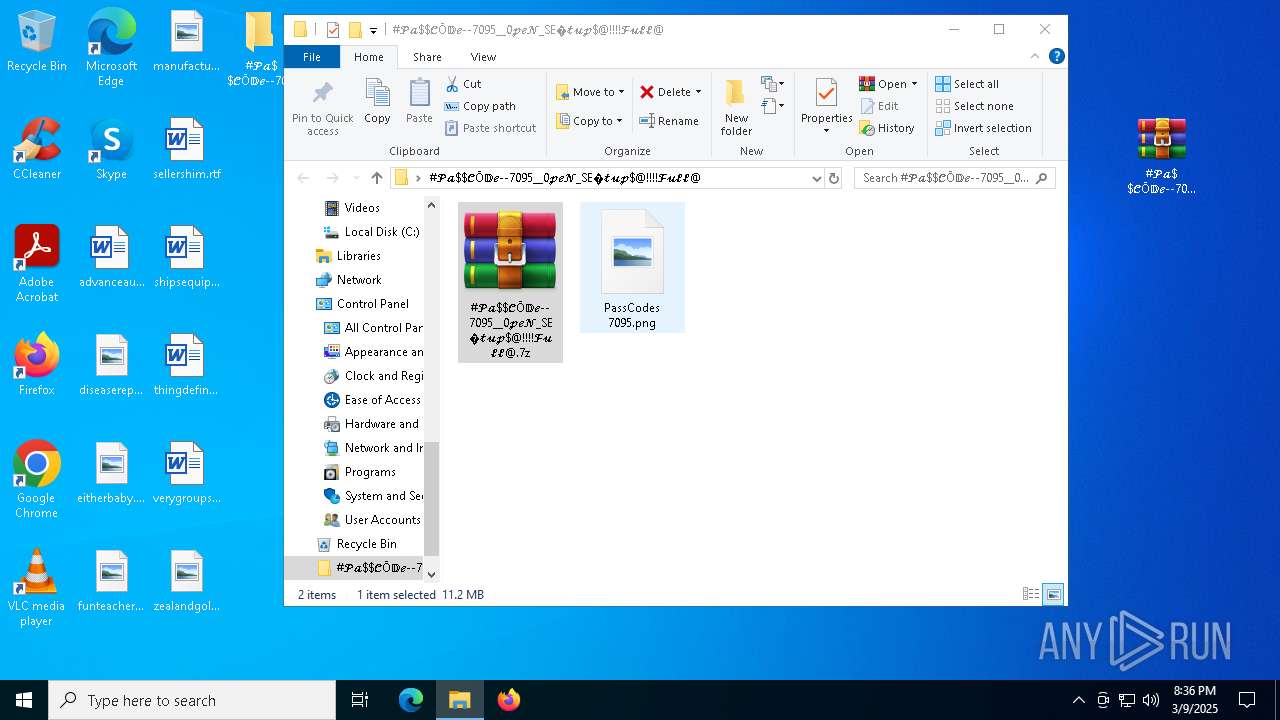
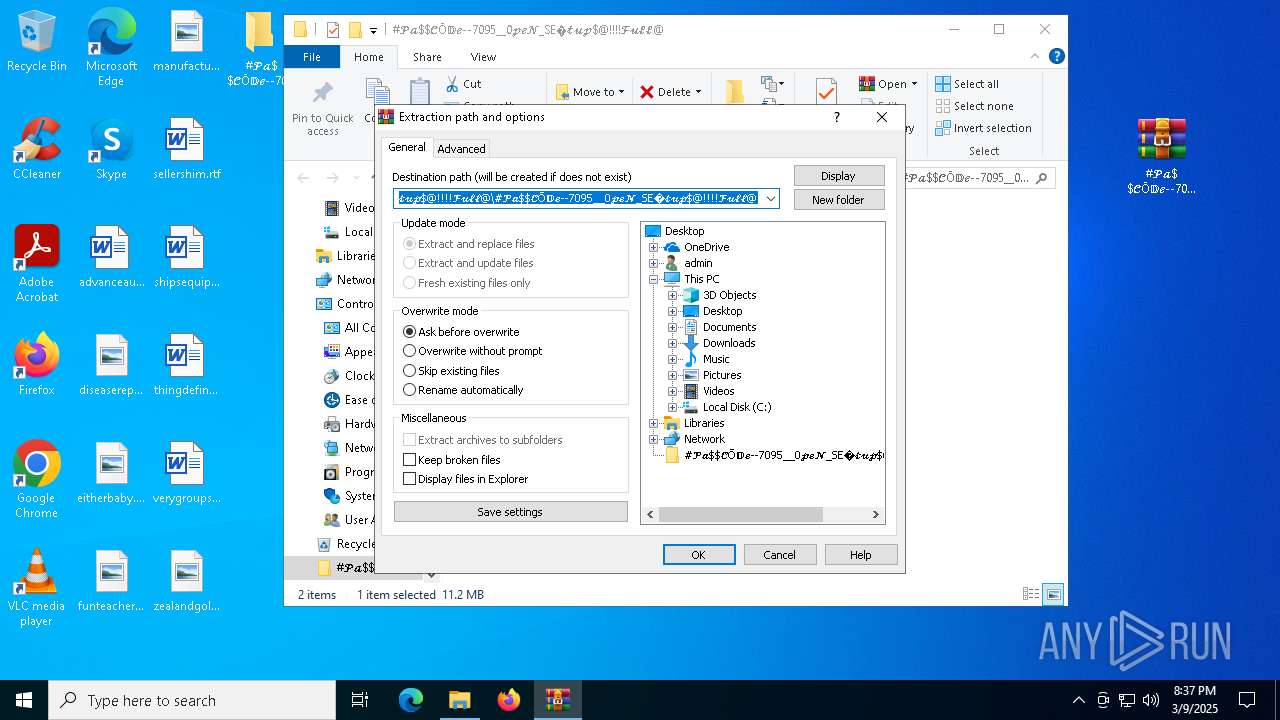
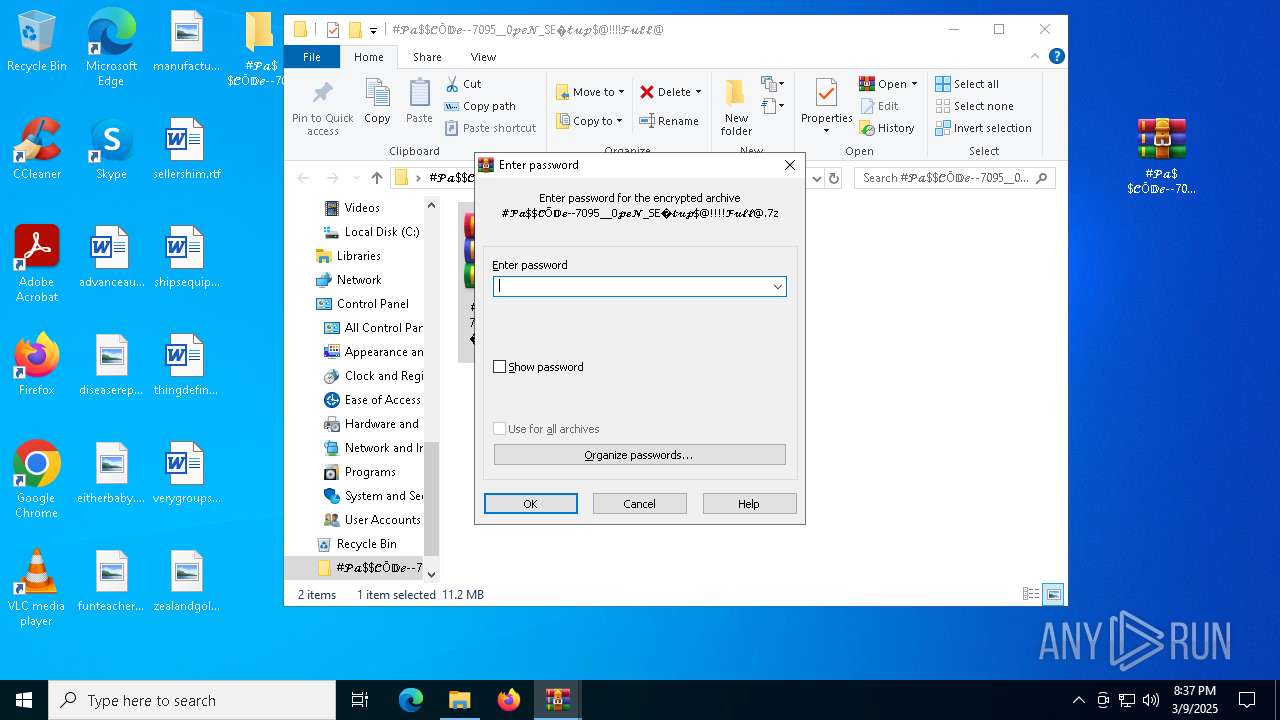
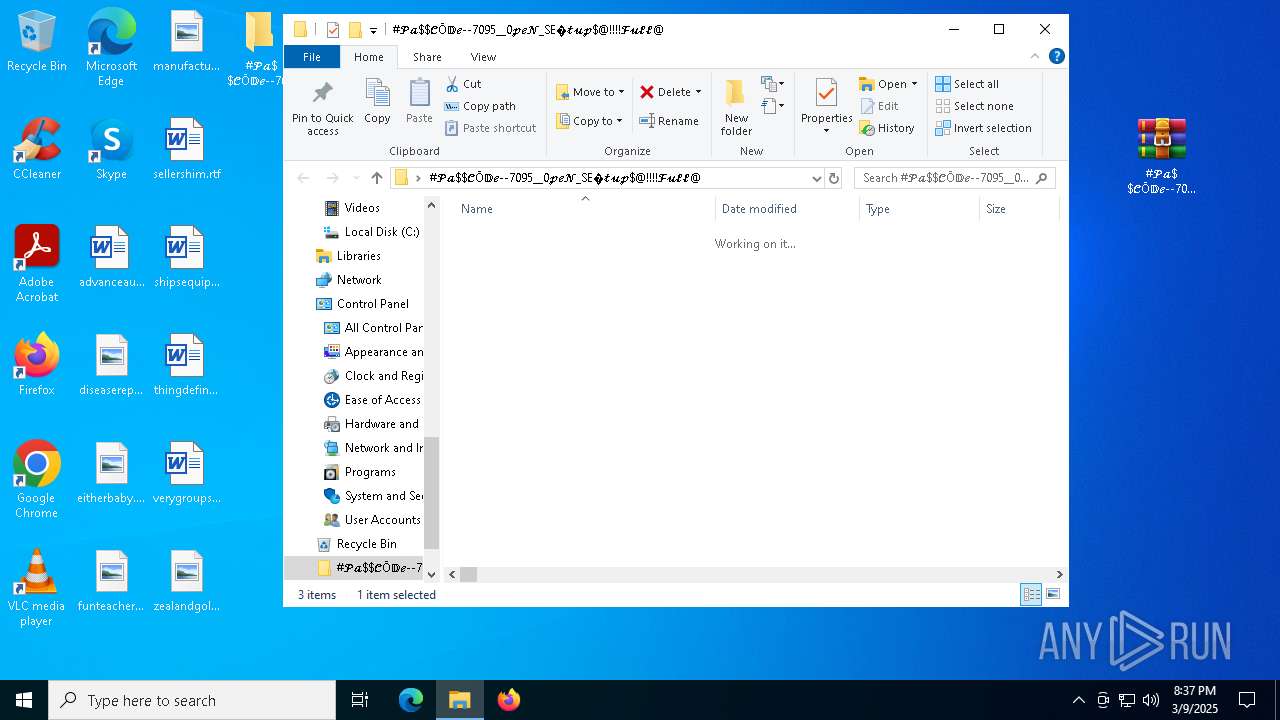
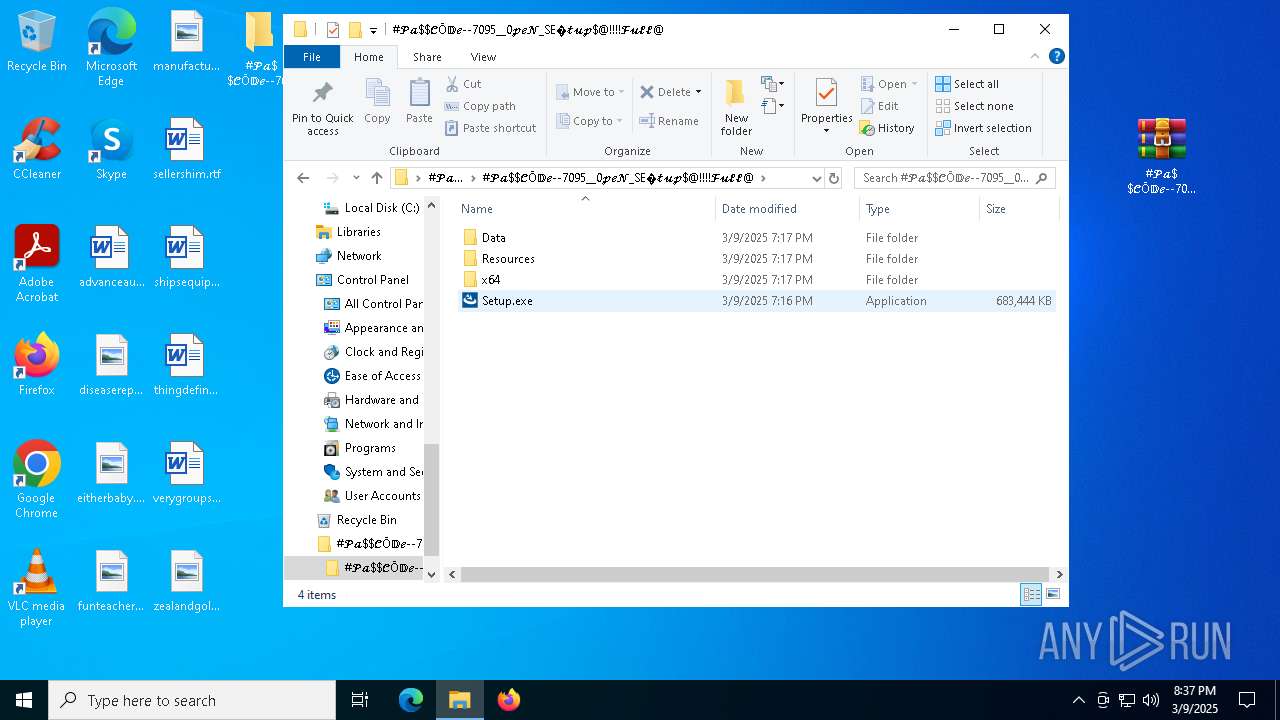
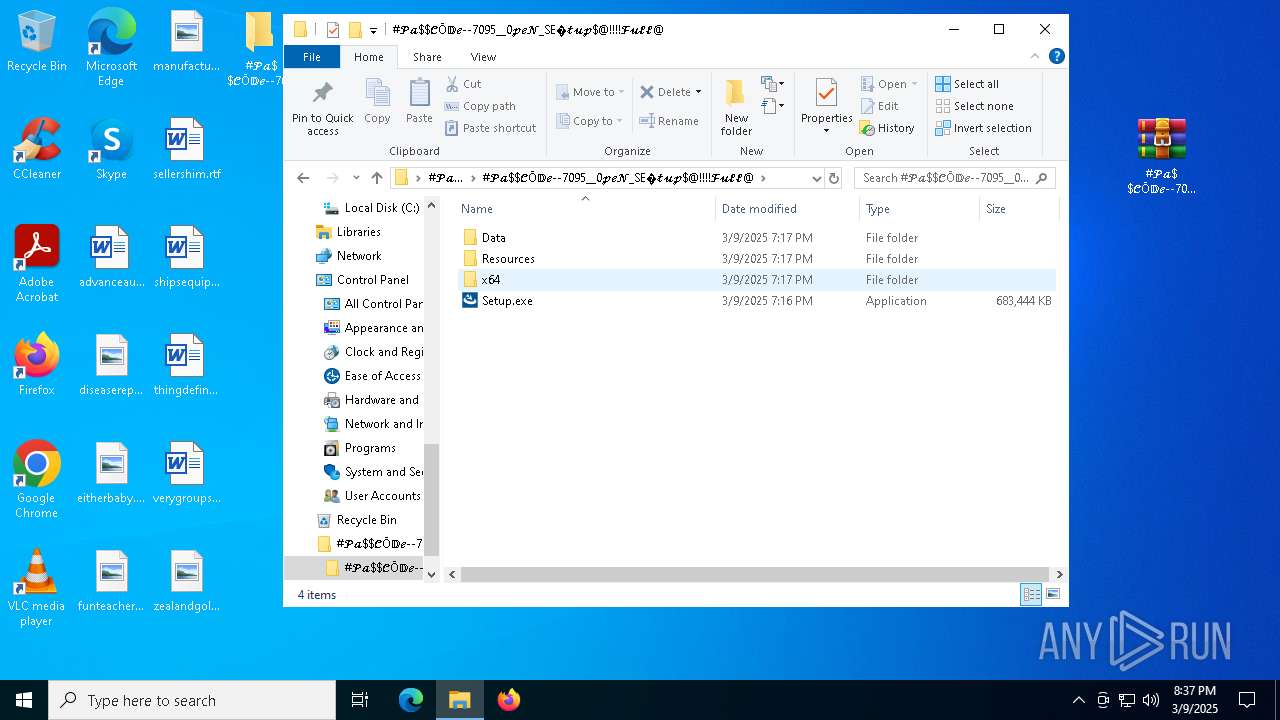
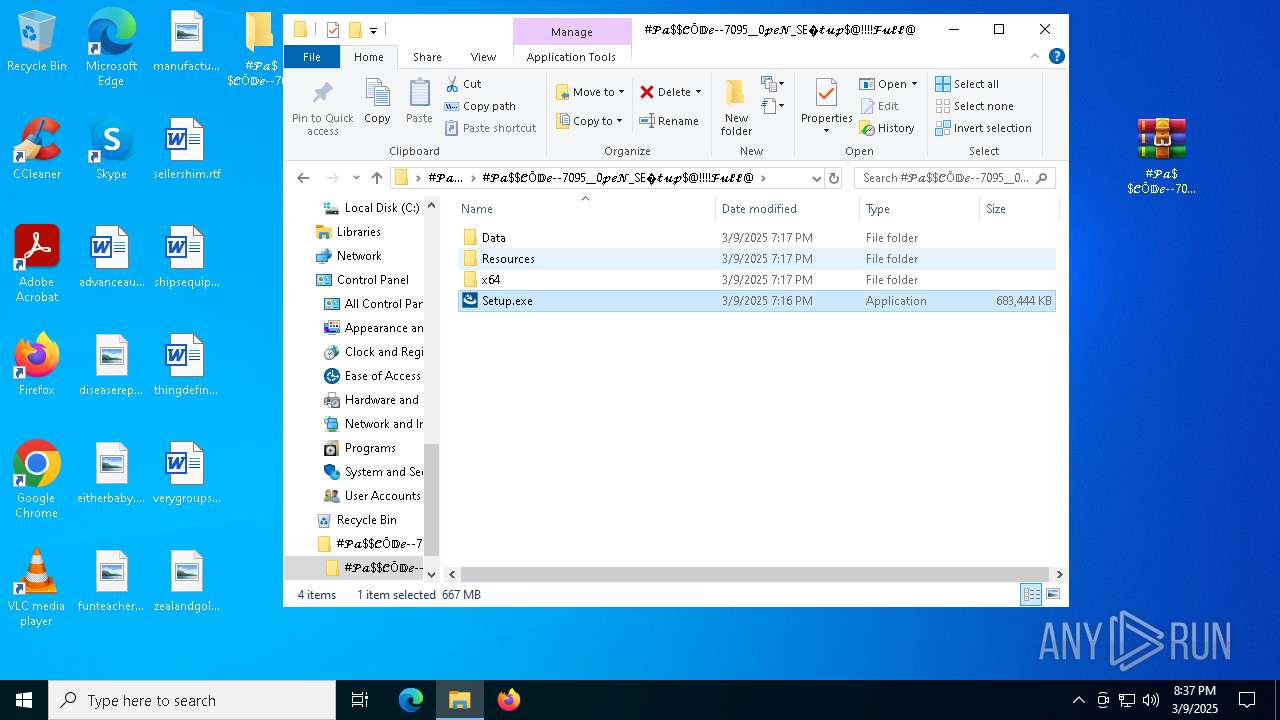
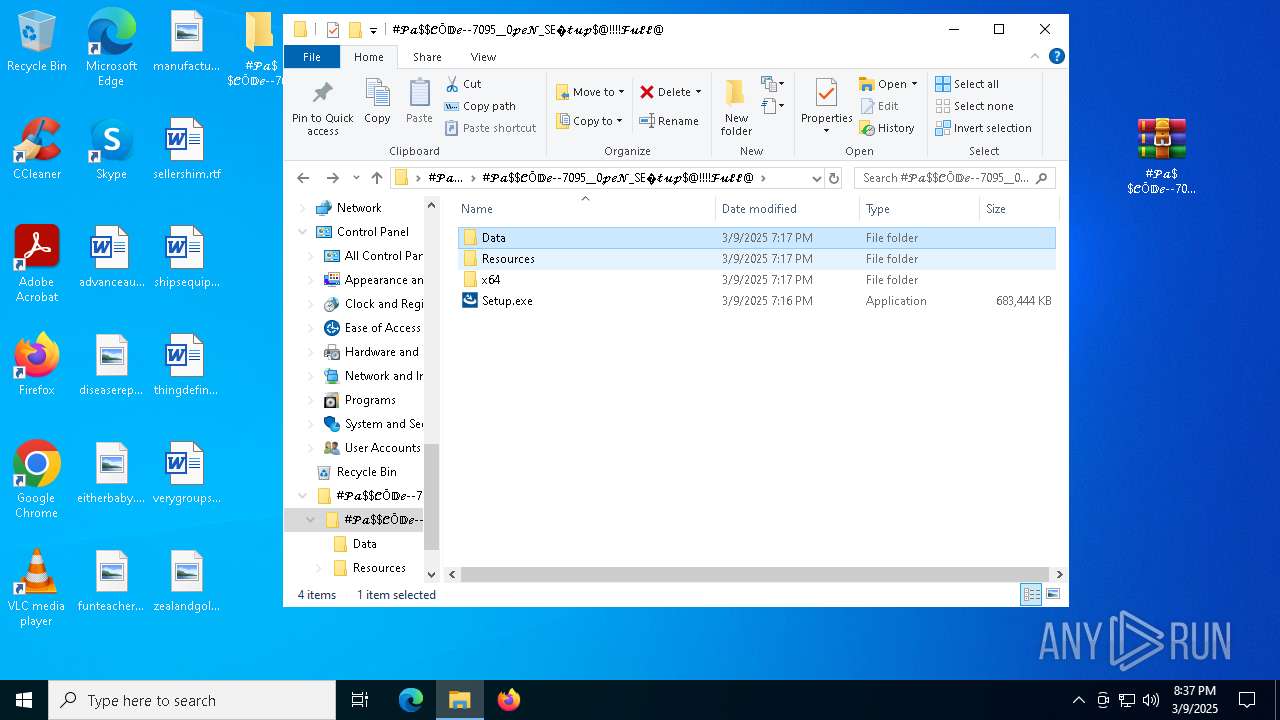
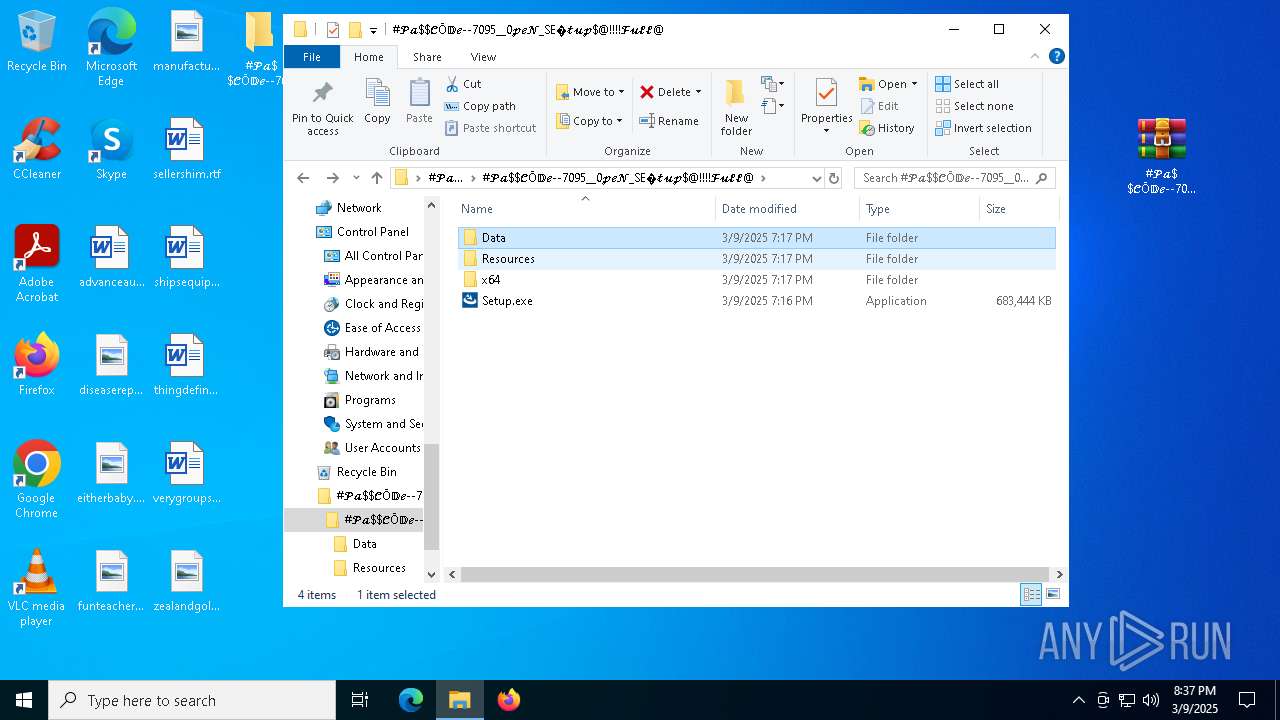
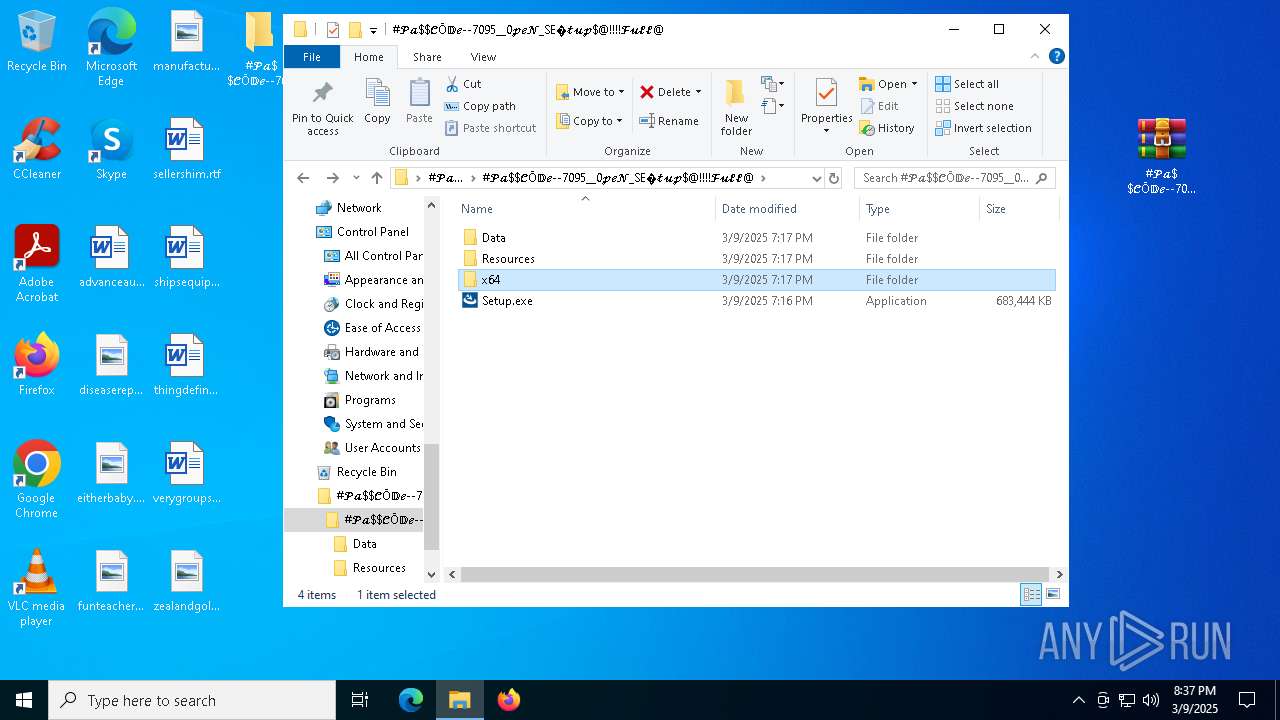
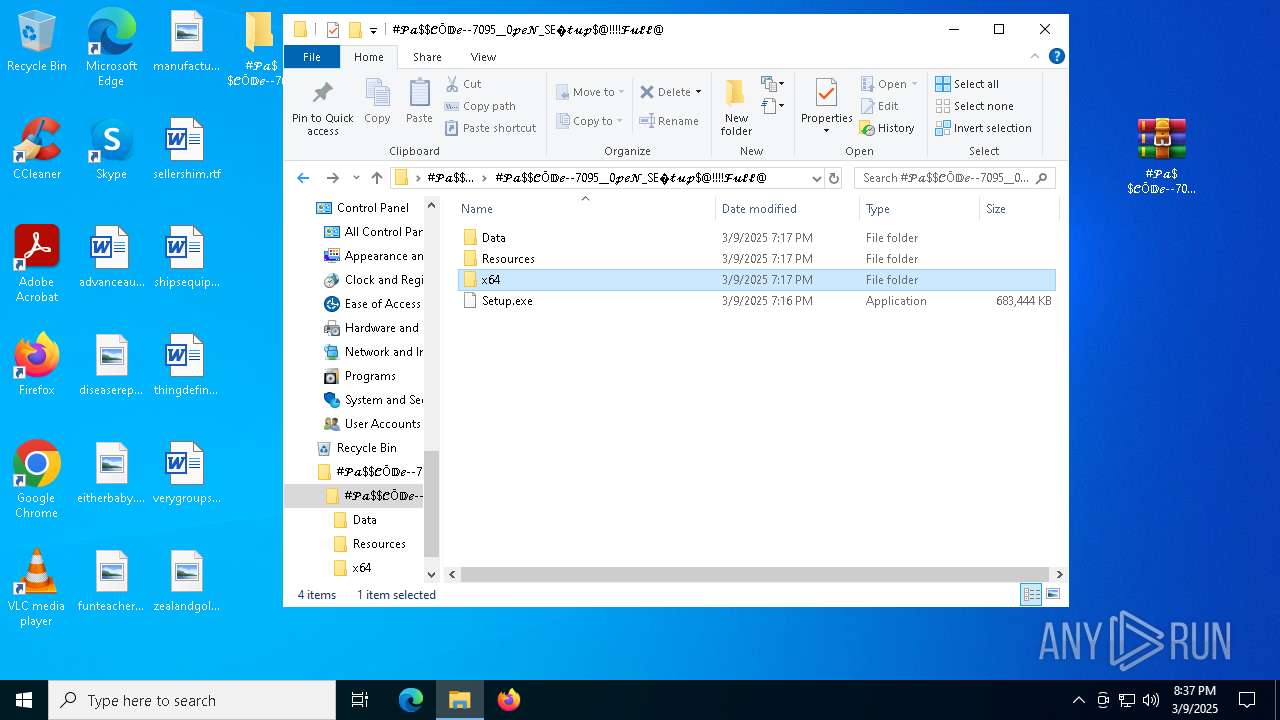
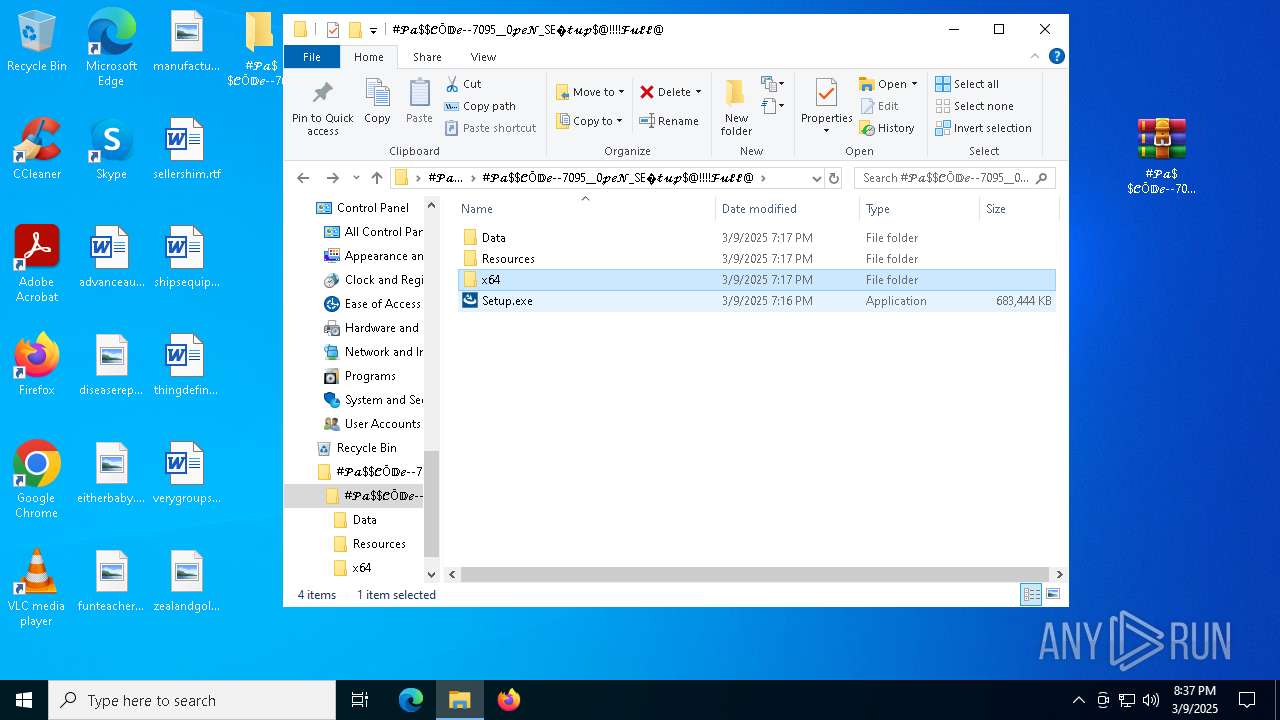
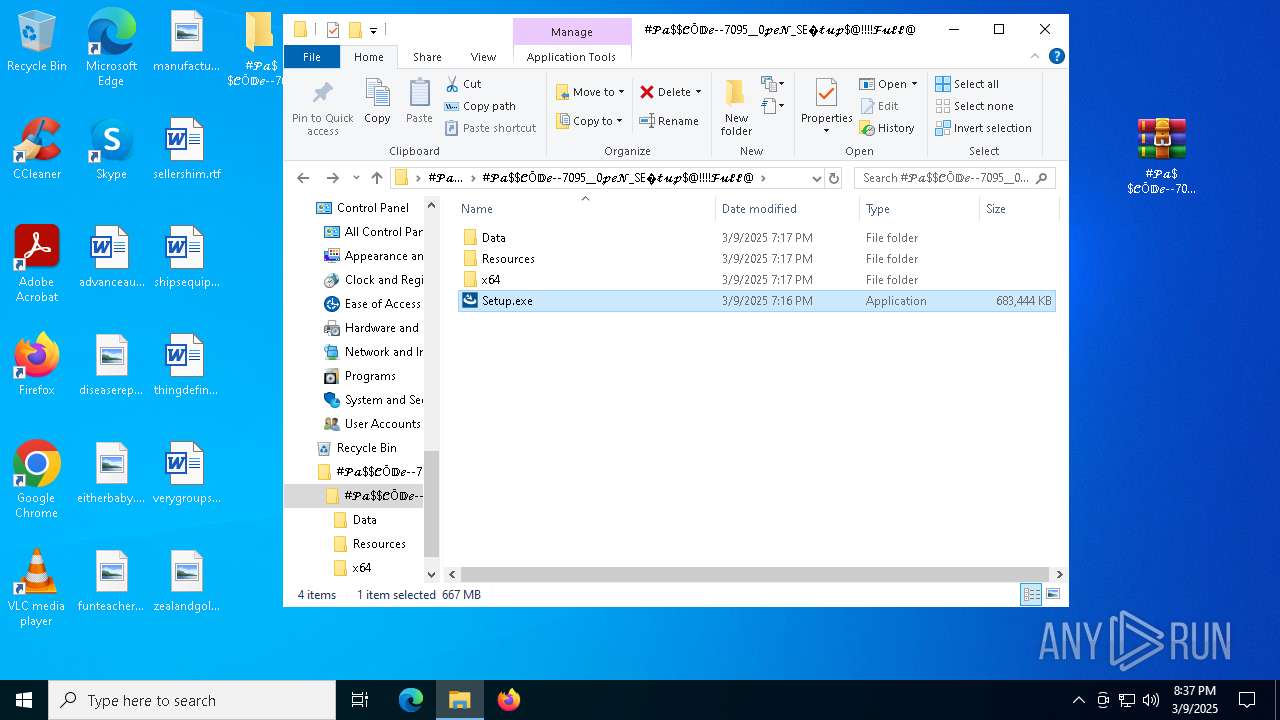
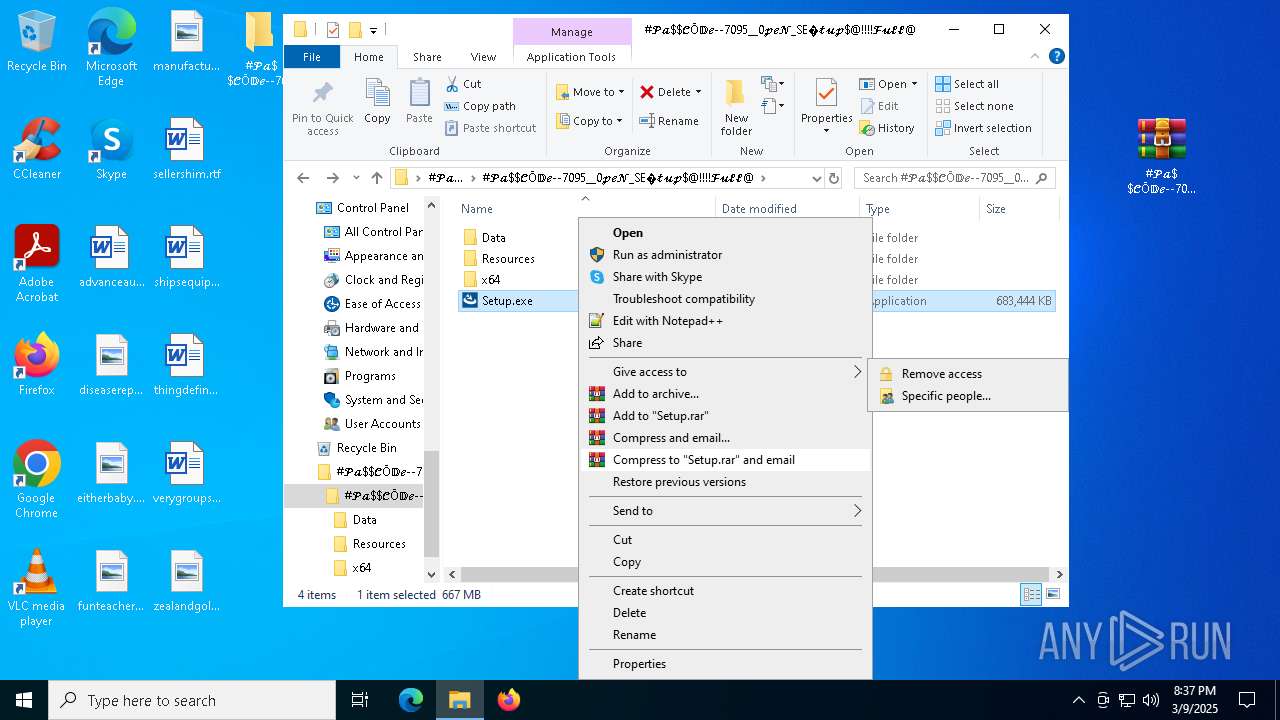
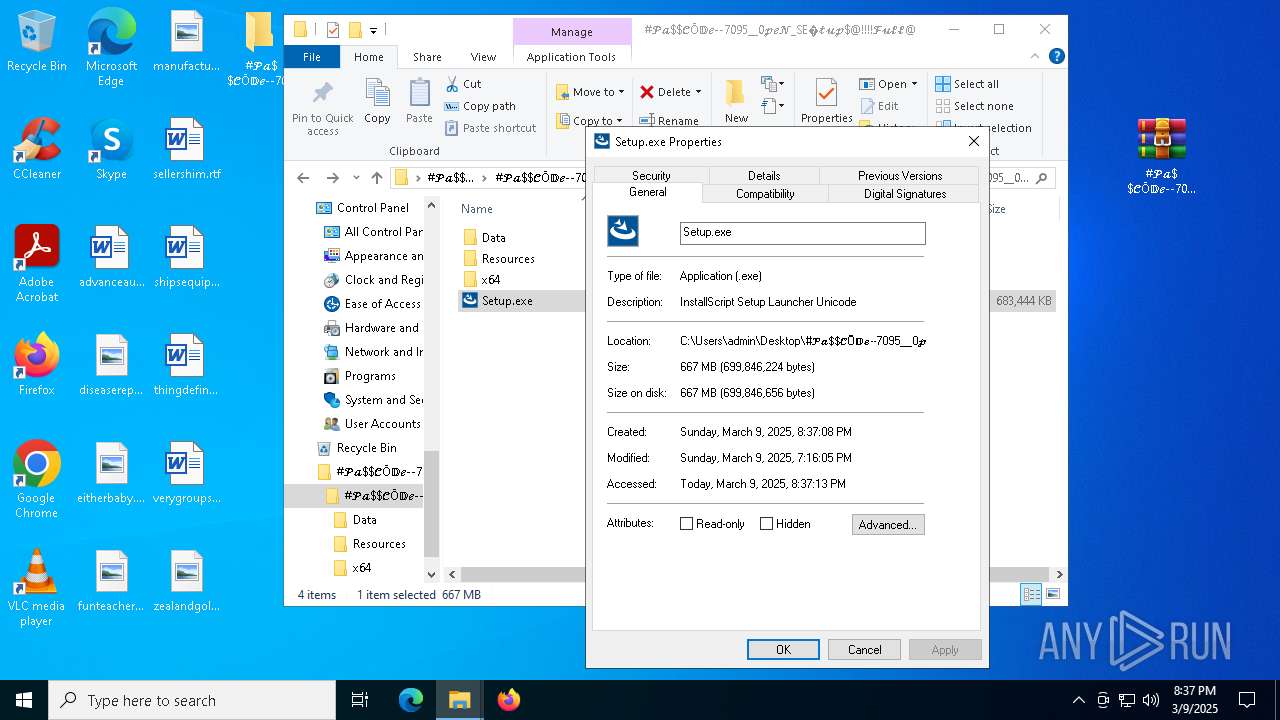
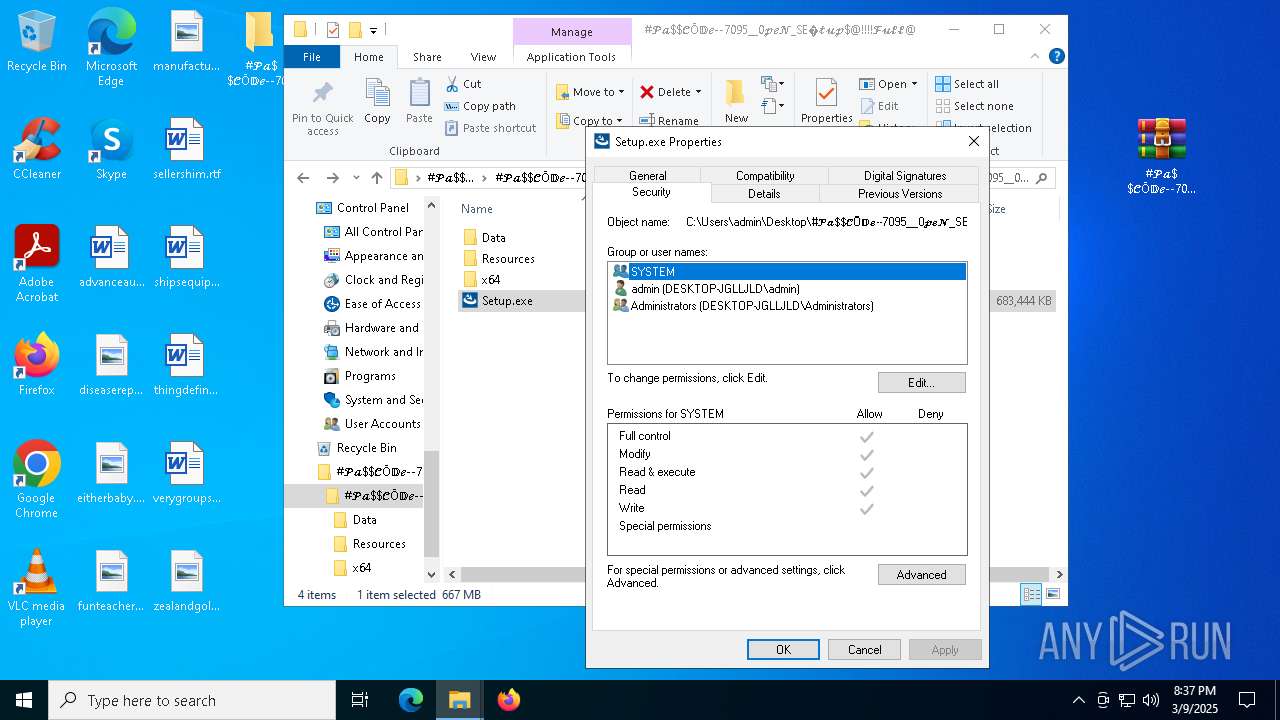
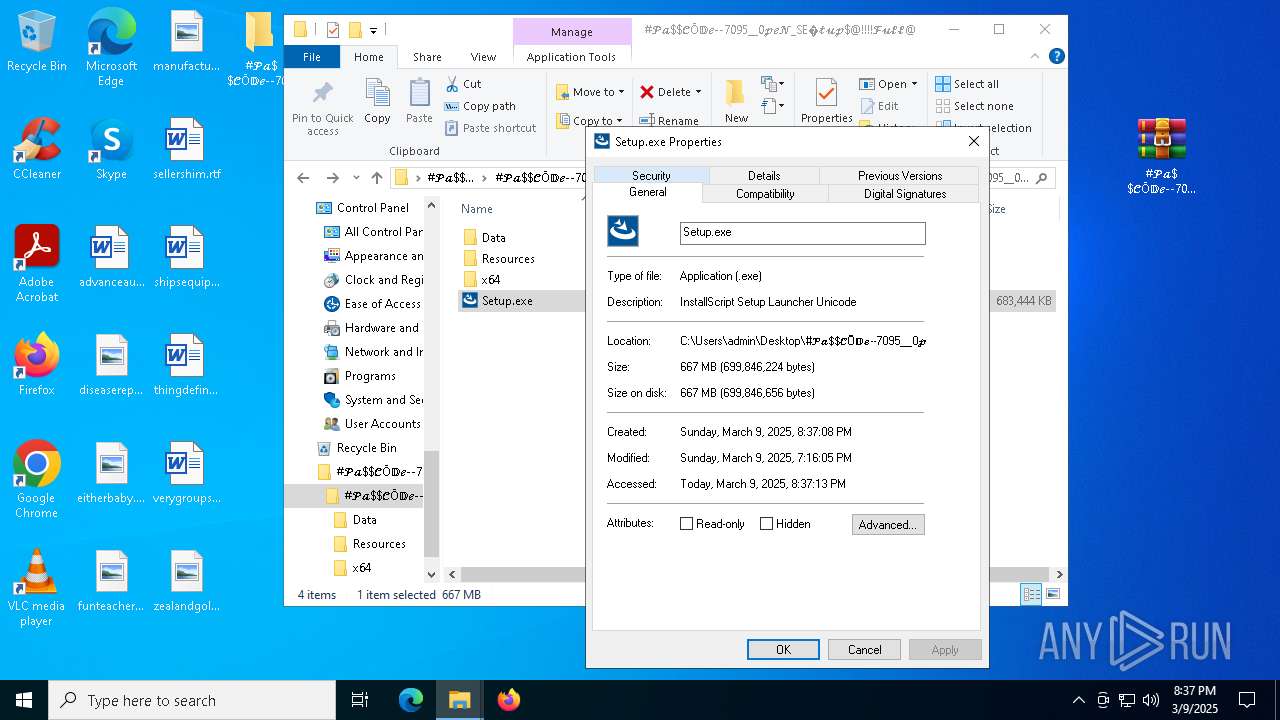
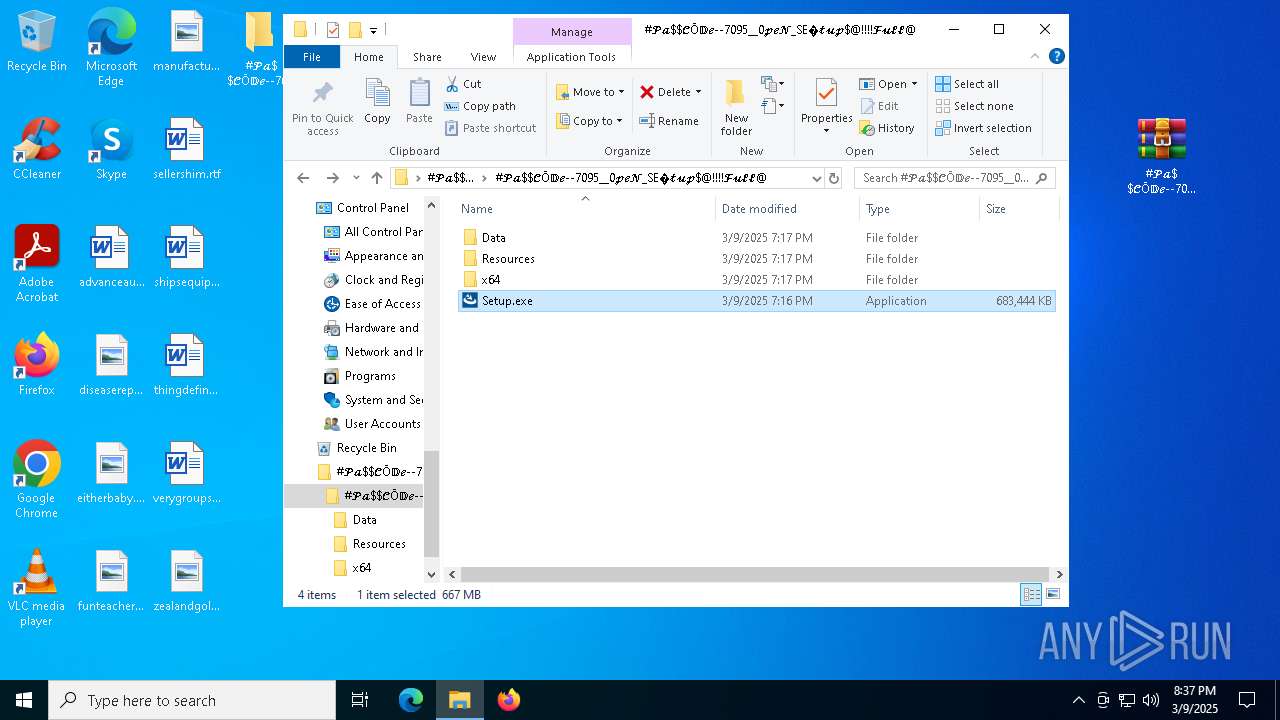
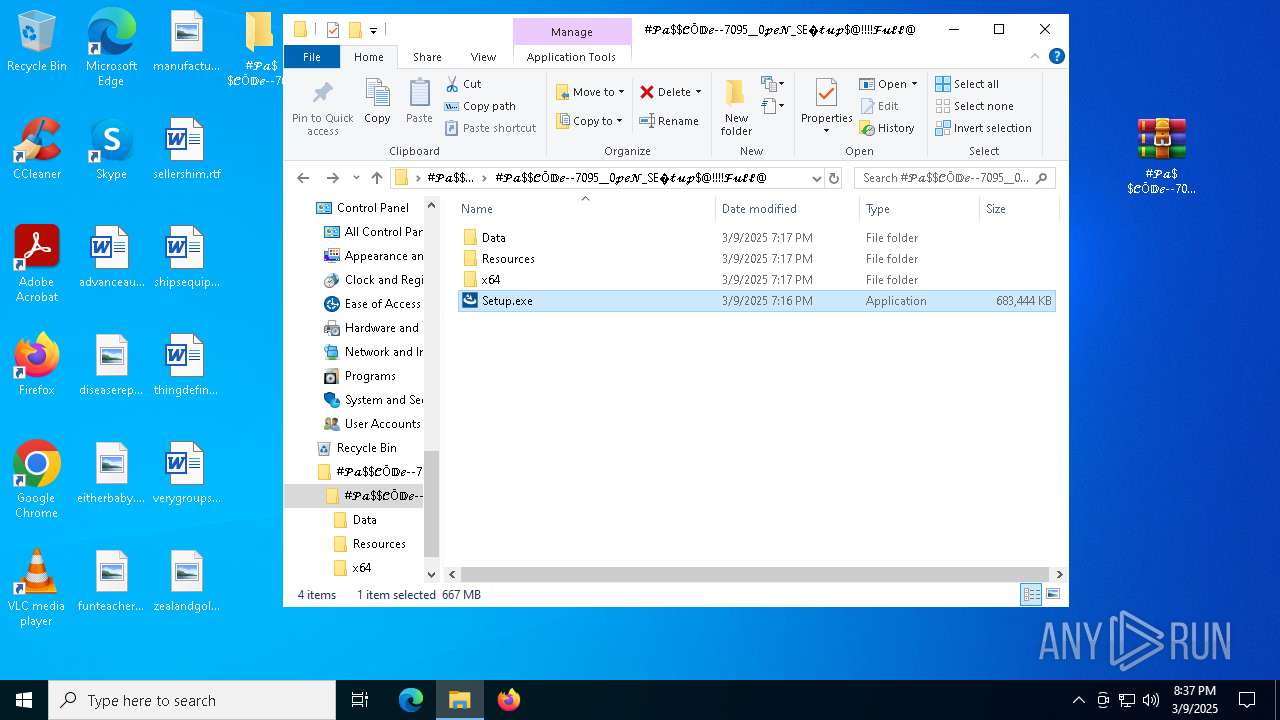
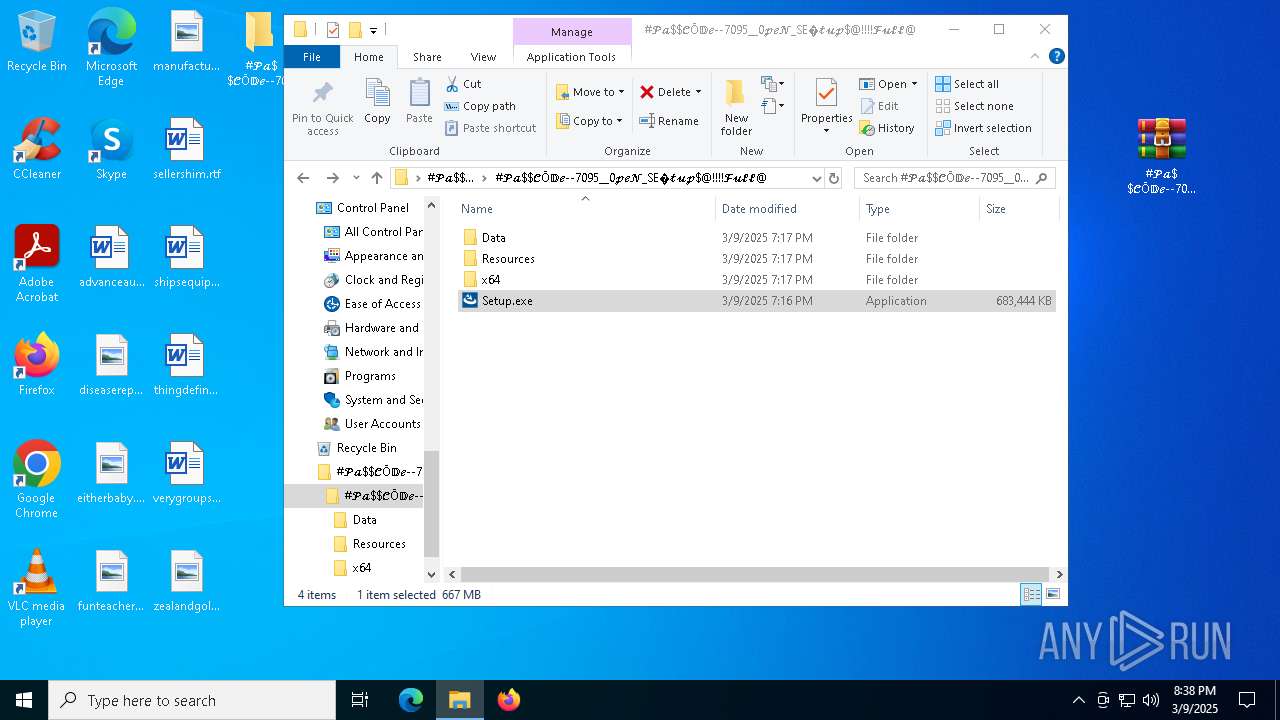
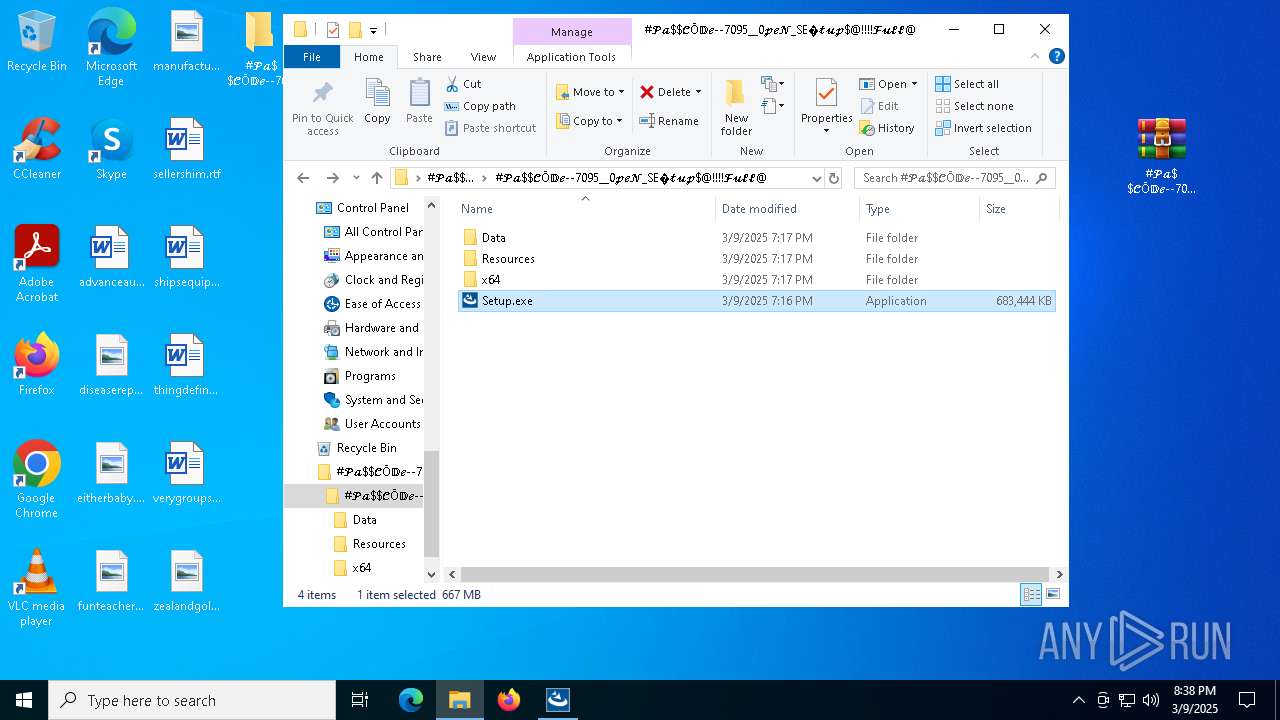
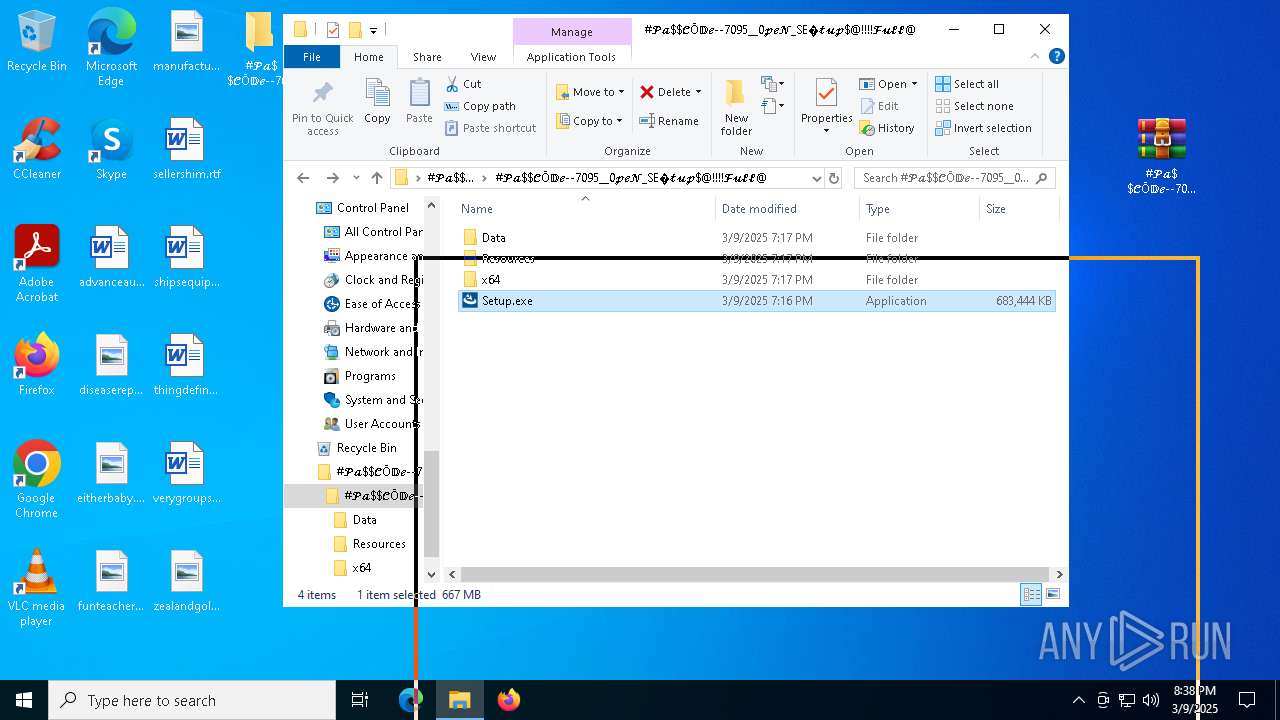
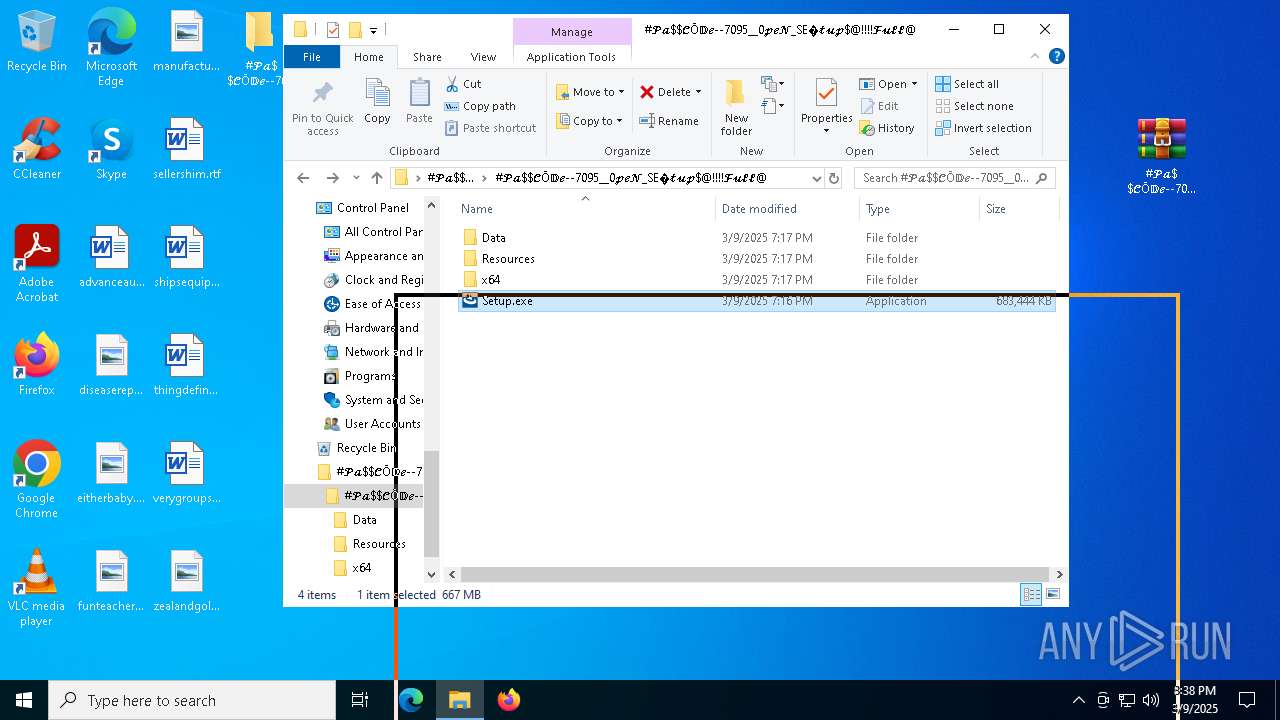
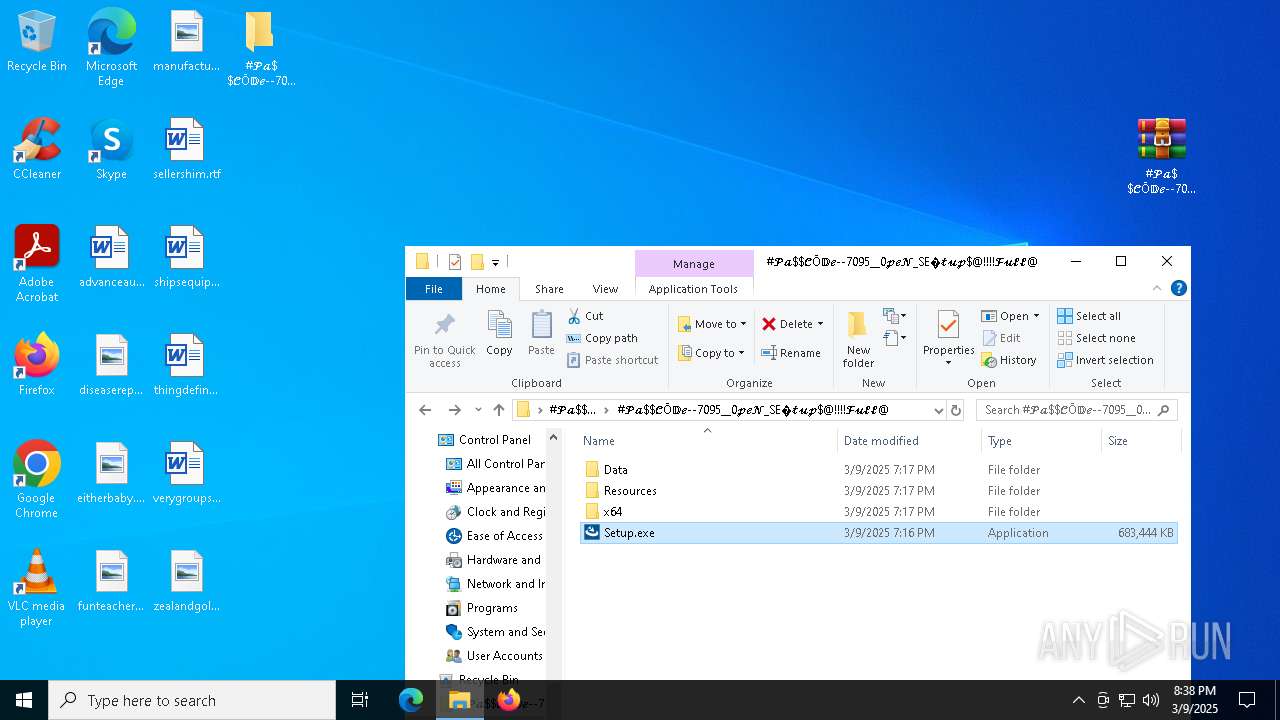
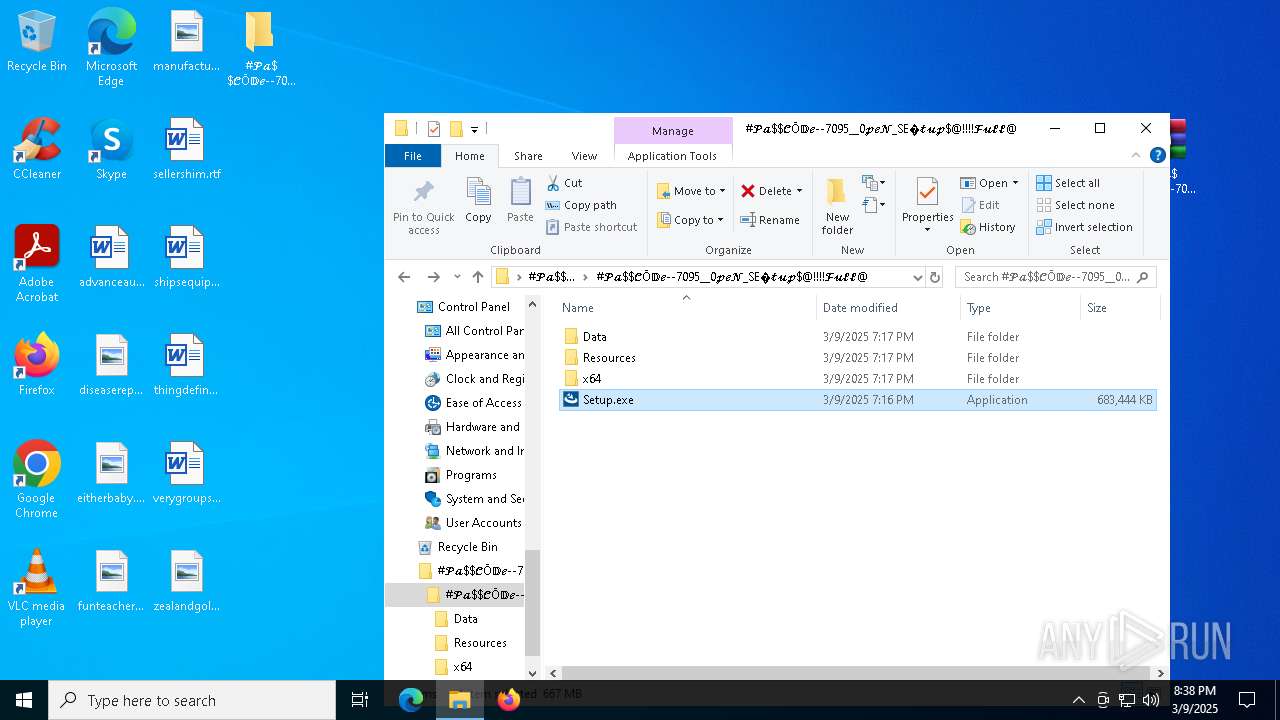
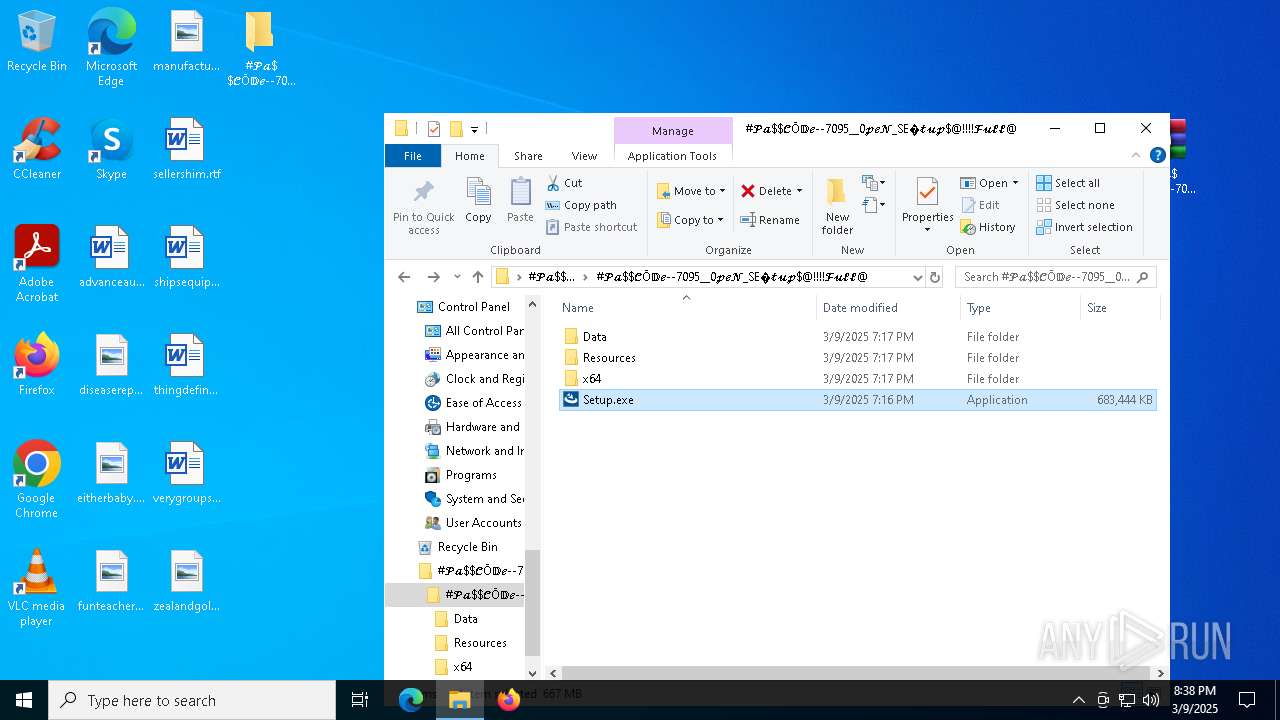
Manual execution by a user
- WinRAR.exe (PID: 660)
- WinRAR.exe (PID: 5304)
- Setup.exe (PID: 5964)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 660)
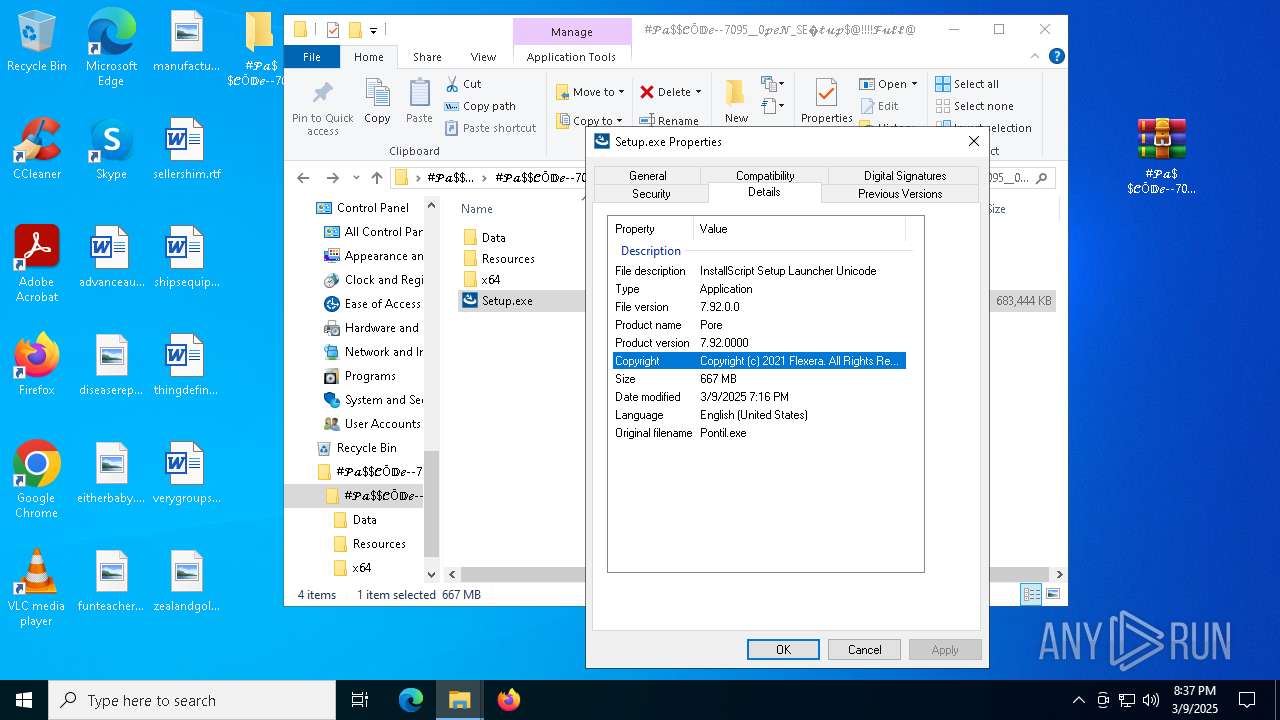
The sample compiled with english language support
- Setup.exe (PID: 5964)
- WinRAR.exe (PID: 660)
- setup.exe (PID: 1184)
- ABSchedhlp.exe (PID: 7260)
- svchost.exe (PID: 8496)
- Frame.exe (PID: 6964)
Create files in a temporary directory
- setup.exe (PID: 1184)
- Setup.exe (PID: 5964)
- ABSchedhlp.exe (PID: 7412)
- svchost.exe (PID: 8496)
- Frame.exe (PID: 4652)
- more.com (PID: 5596)
- Frame.exe (PID: 6964)
- more.com (PID: 5304)
Reads the software policy settings
- slui.exe (PID: 7608)
- slui.exe (PID: 9128)
Creates files or folders in the user directory
- ABSchedhlp.exe (PID: 7260)
- Frame.exe (PID: 6964)
Checks proxy server information
- slui.exe (PID: 9128)
Reads the machine GUID from the registry
- more.com (PID: 8204)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 7592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
226
Monitored processes
89
Malicious processes
8
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=136 --field-trial-handle=2332,i,5248598713767327106,9894521588116354950,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
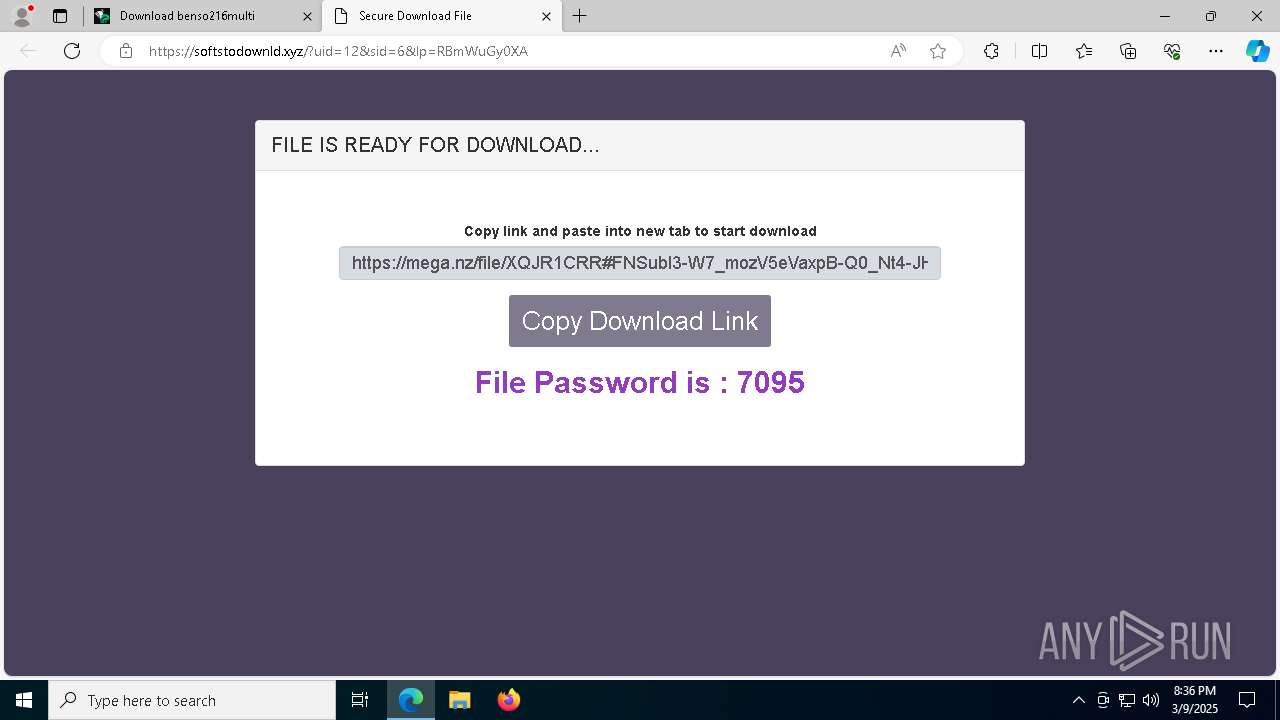
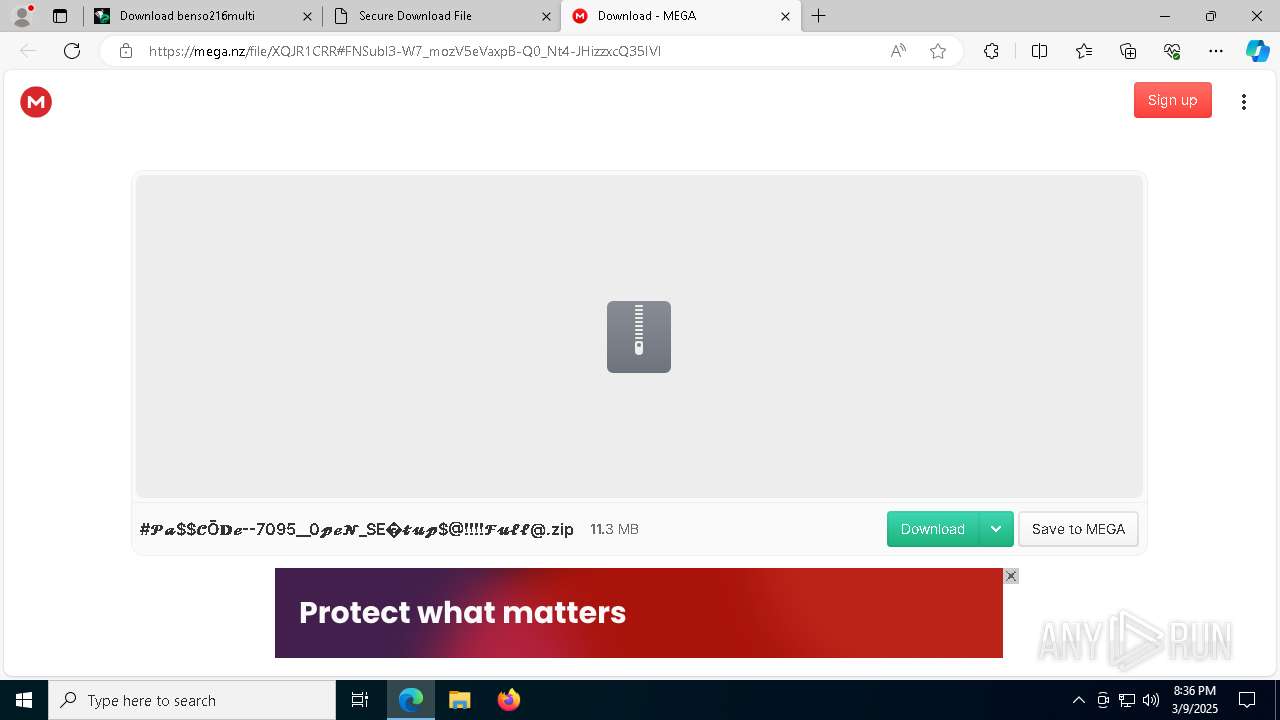
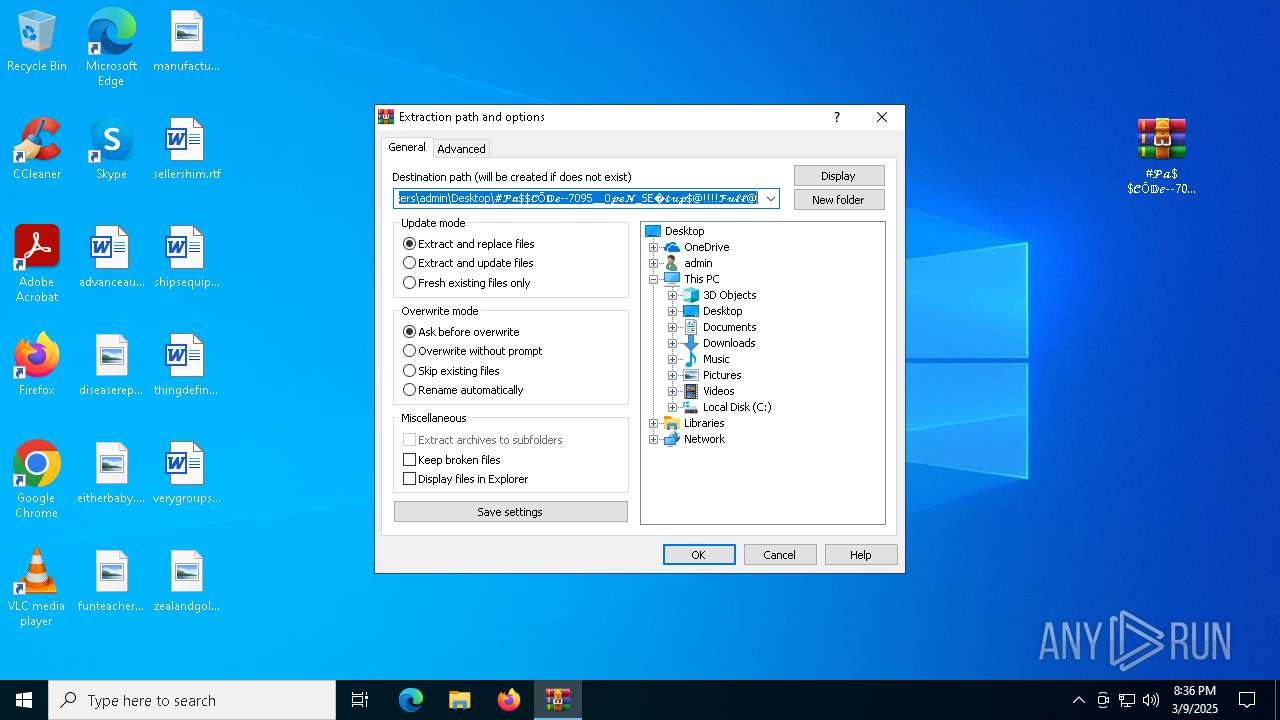
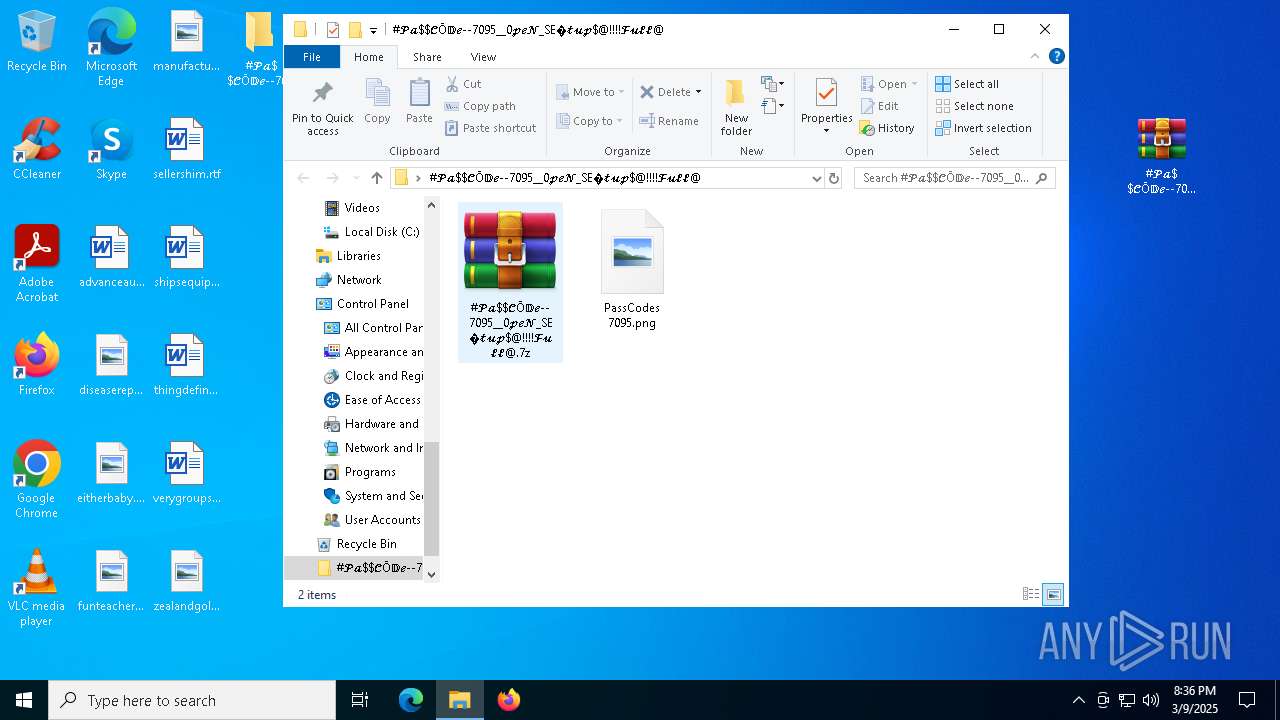
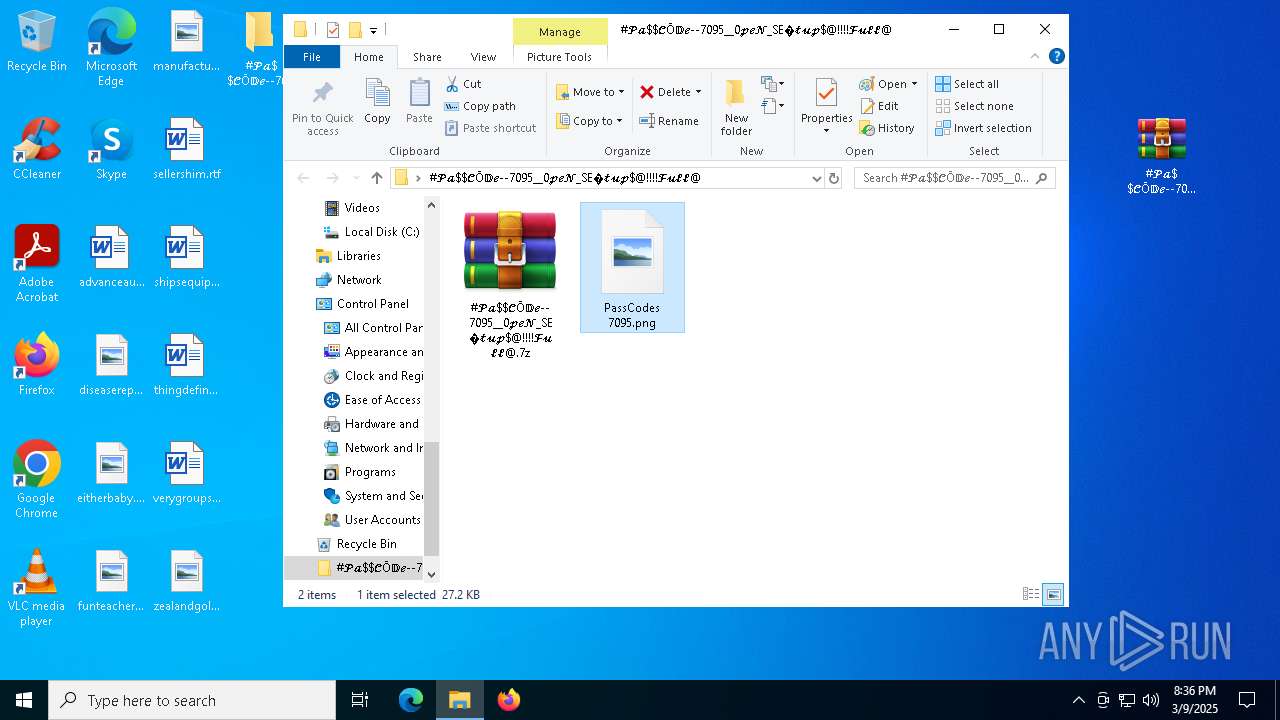
| 660 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\#𝓟𝓪$𝓒Ō𝔻𝓮--7095__0𝓹𝓮𝓝_SE�𝓽𝓾𝓹$@!!!!𝓕𝓾𝓵𝓵@\#𝓟𝓪$𝓒Ō𝔻𝓮--7095__0𝓹𝓮𝓝_SE�𝓽𝓾𝓹$@!!!!𝓕𝓾𝓵𝓵@.7z" "?\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5624 --field-trial-handle=2236,i,11391443976092835164,3615685178703268766,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5396 --field-trial-handle=2332,i,5248598713767327106,9894521588116354950,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
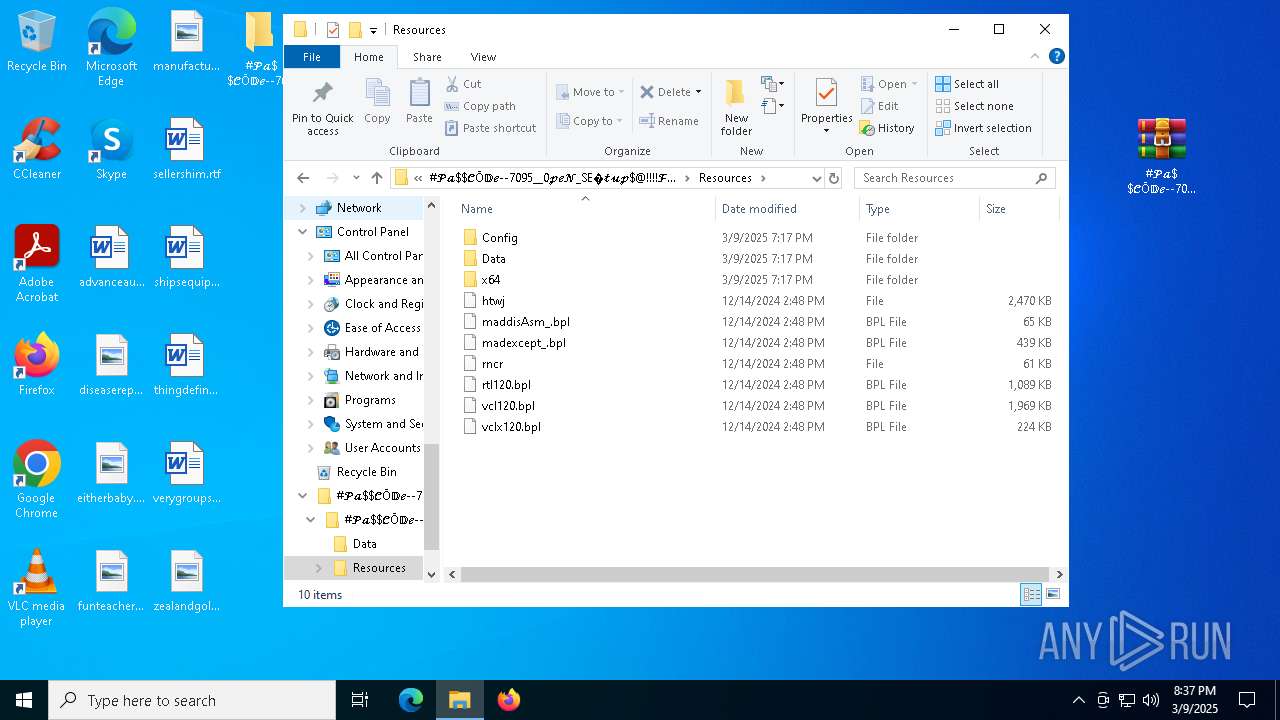
| 1184 | C:\Users\admin\AppData\Local\Temp\{F8255DAB-01BD-45DA-B184-1AF8311D335F}\setup.exe -package:"C:\Users\admin\Desktop\#𝓟𝓪$𝓒Ō𝔻𝓮--7095__0𝓹𝓮𝓝_SE�𝓽𝓾𝓹$@!!!!𝓕𝓾𝓵𝓵@\#𝓟𝓪$𝓒Ō𝔻𝓮--7095__0𝓹𝓮𝓝_SE�𝓽𝓾𝓹$@!!!!𝓕𝓾𝓵𝓵@\Setup.exe" -no_selfdeleter -IS_temp -media_path:"C:\Users\admin\AppData\Local\Temp\{F8255DAB-01BD-45DA-B184-1AF8311D335F}\Disk1\" -tempdisk1folder:"C:\Users\admin\AppData\Local\Temp\{F8255DAB-01BD-45DA-B184-1AF8311D335F}\" -IS_OriginalLauncher:"C:\Users\admin\AppData\Local\Temp\{F8255DAB-01BD-45DA-B184-1AF8311D335F}\Disk1\setup.exe" | C:\Users\admin\AppData\Local\Temp\{F8255DAB-01BD-45DA-B184-1AF8311D335F}\setup.exe | Setup.exe | ||||||||||||
User: admin Company: Donator Integrity Level: MEDIUM Description: InstallScript Setup Launcher Unicode Exit code: 2147753984 Version: 7.92.0000 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4112 --field-trial-handle=2332,i,5248598713767327106,9894521588116354950,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1764 | C:\Users\admin\AppData\Local\Temp\{9A7E8C56-047B-4467-88FF-47BD911D43A8}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{53D0A899-AE92-4E07-BD0C-D0B352772DAE} | C:\Users\admin\AppData\Local\Temp\{9A7E8C56-047B-4467-88FF-47BD911D43A8}\ISBEW64.exe | — | setup.exe | |||||||||||
User: admin Company: Flexera Integrity Level: MEDIUM Description: InstallShield (R) 64-bit Setup Engine Exit code: 0 Version: 27.0.58 Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=6132 --field-trial-handle=2236,i,11391443976092835164,3615685178703268766,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
14 595
Read events
14 484
Write events
65
Delete events
46
Modification events
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DC6AF616858E2F00 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7D7AFF16858E2F00 | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FB328B46-E5F3-4609-B5F7-9A60C62B9392} | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9F98D6EC-B2A9-4EB8-8417-AC030E870211} | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E96CFDD3-4E46-4ECC-BBC0-466A2FAC8E5A} | |||
| (PID) Process: | (2140) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197232 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {601AE038-EE6F-4173-A81D-A092C7A883EA} | |||
Executable files
75
Suspicious files
392
Text files
258
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b4db.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b4db.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b4db.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b4db.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b4ea.TMP | — | |
MD5:— | SHA256:— | |||
| 2140 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
123
DNS requests
119
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5668 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
9088 | svchost.exe | HEAD | 200 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/18de6d1e-49ab-46b6-96d3-7b7f75e58ad4?P1=1742112767&P2=404&P3=2&P4=ippiLazODpELBcx8Xs6B6reQv5Jry%2bFFc8yOVqplbGFH%2fbW7A8PHvK4N3kVjDNdihYpeYqy4TbxLdfnMSwwQrw%3d%3d | US | — | — | whitelisted |
2244 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
2244 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
9088 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/18de6d1e-49ab-46b6-96d3-7b7f75e58ad4?P1=1742112767&P2=404&P3=2&P4=ippiLazODpELBcx8Xs6B6reQv5Jry%2bFFc8yOVqplbGFH%2fbW7A8PHvK4N3kVjDNdihYpeYqy4TbxLdfnMSwwQrw%3d%3d | US | binary | 1.09 Kb | whitelisted |
9088 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/18de6d1e-49ab-46b6-96d3-7b7f75e58ad4?P1=1742112767&P2=404&P3=2&P4=ippiLazODpELBcx8Xs6B6reQv5Jry%2bFFc8yOVqplbGFH%2fbW7A8PHvK4N3kVjDNdihYpeYqy4TbxLdfnMSwwQrw%3d%3d | US | binary | 3.92 Kb | whitelisted |
9088 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/18de6d1e-49ab-46b6-96d3-7b7f75e58ad4?P1=1742112767&P2=404&P3=2&P4=ippiLazODpELBcx8Xs6B6reQv5Jry%2bFFc8yOVqplbGFH%2fbW7A8PHvK4N3kVjDNdihYpeYqy4TbxLdfnMSwwQrw%3d%3d | US | binary | 1.83 Kb | whitelisted |
9088 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/18de6d1e-49ab-46b6-96d3-7b7f75e58ad4?P1=1742112767&P2=404&P3=2&P4=ippiLazODpELBcx8Xs6B6reQv5Jry%2bFFc8yOVqplbGFH%2fbW7A8PHvK4N3kVjDNdihYpeYqy4TbxLdfnMSwwQrw%3d%3d | US | binary | 9.82 Kb | whitelisted |
9088 | svchost.exe | GET | 206 | 217.20.57.35:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/18de6d1e-49ab-46b6-96d3-7b7f75e58ad4?P1=1742112767&P2=404&P3=2&P4=ippiLazODpELBcx8Xs6B6reQv5Jry%2bFFc8yOVqplbGFH%2fbW7A8PHvK4N3kVjDNdihYpeYqy4TbxLdfnMSwwQrw%3d%3d | US | binary | 19.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7328 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7328 | msedge.exe | 104.21.18.46:443 | filespayouts.com | — | — | unknown |
7328 | msedge.exe | 188.114.97.3:443 | filespayout.com | — | — | unknown |
2140 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7328 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7328 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
filespayout.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
filespayouts.com |
| unknown |
bzib.nelreports.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7328 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
7328 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7328 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
7328 | msedge.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
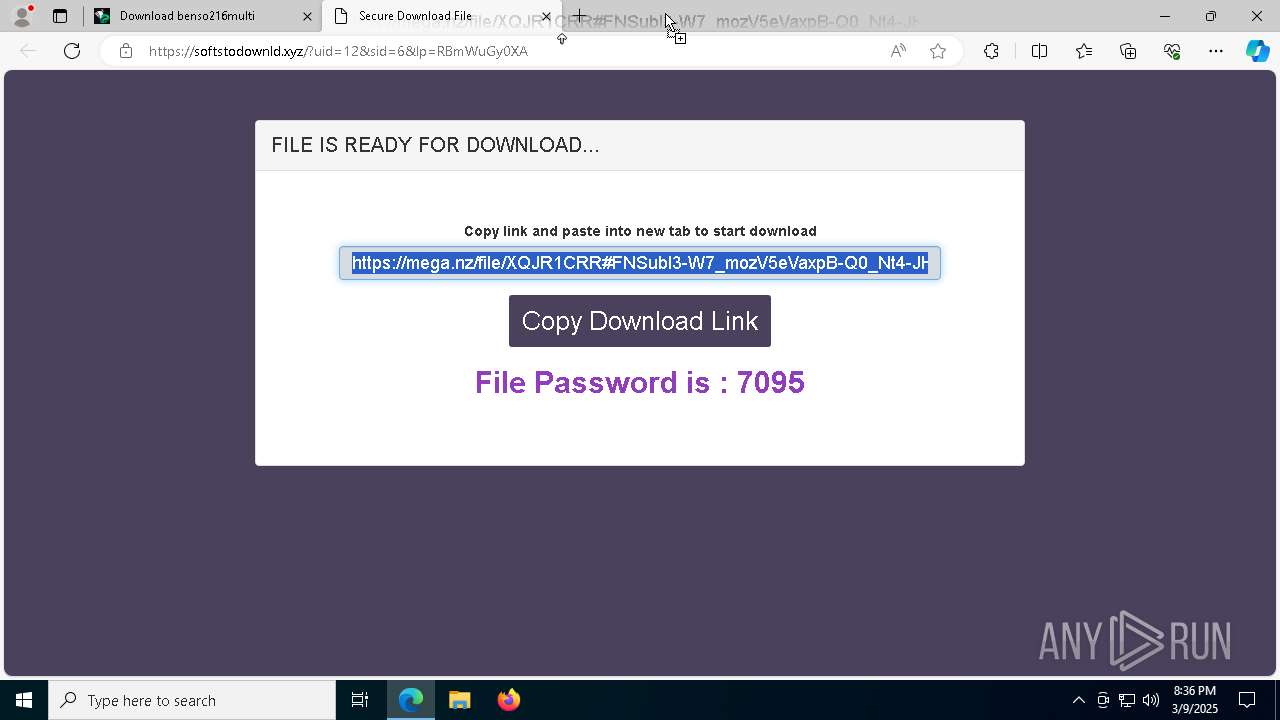
7328 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (softstodownld .xyz) |
7328 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain (softstodownld .xyz) |
7328 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |