| File name: | sample10.rtf |
| Full analysis: | https://app.any.run/tasks/03c5bb40-0eab-4c0f-9433-487681c5b81a |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | July 18, 2019, 13:27:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
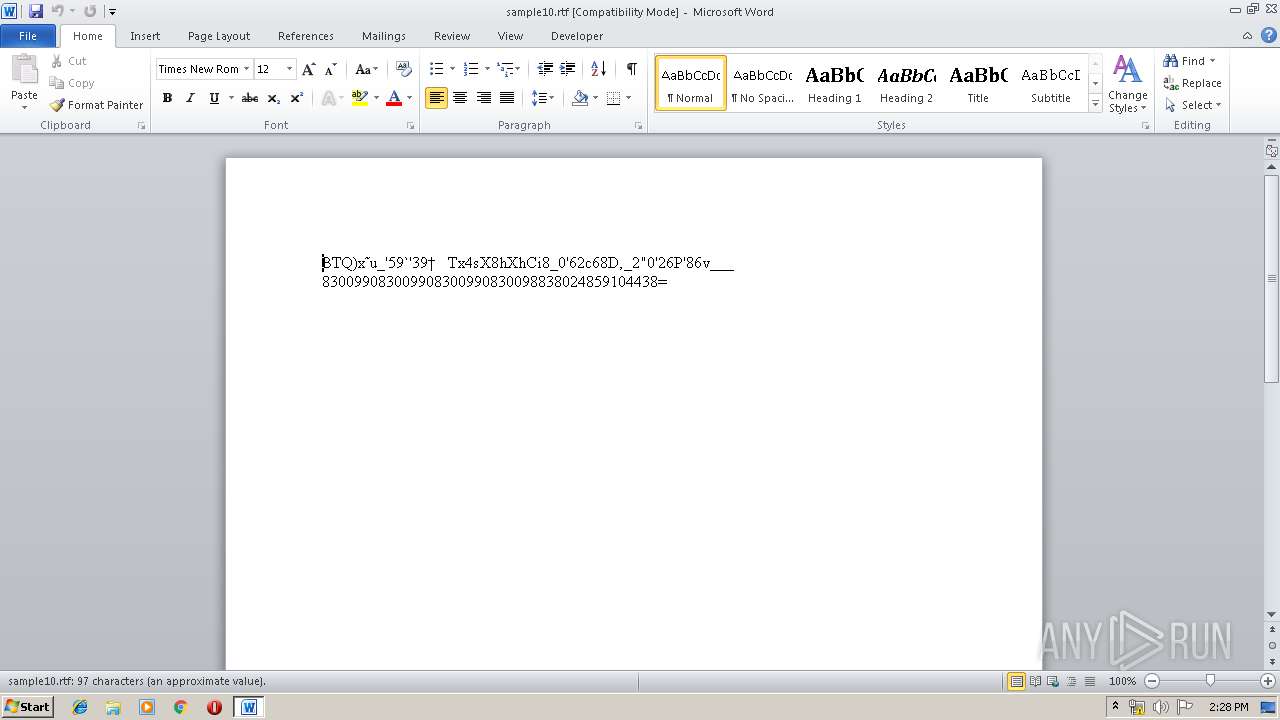
| MIME: | text/rtf |
| File info: | Rich Text Format data, unknown version |
| MD5: | A097E6900EDB297A78A38C7D681B585B |
| SHA1: | FFCECA5FC25DDF4ECB3EE54111765A8D9BCA6D9F |
| SHA256: | 34E4E0F2F24759CB5D28A949E0743A0005274C7B6B0A784ABA82CF3F7D308839 |
| SSDEEP: | 96:cf52n/WFyHCJeLAVbAbFyfQFsibh5naNg8H:k52nOYryfQmiXapH |
MALICIOUS
Loads the Task Scheduler COM API
- schtasks.exe (PID: 352)
Application was dropped or rewritten from another process
- asftrew.exe (PID: 3704)
- asftrew.exe (PID: 2276)
Uses Task Scheduler to run other applications
- asftrew.exe (PID: 2276)
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3680)
AGENTTESLA was detected
- asftrew.exe (PID: 3704)
Actions looks like stealing of personal data
- asftrew.exe (PID: 3704)
SUSPICIOUS
Checks for external IP
- asftrew.exe (PID: 3704)
Application launched itself
- asftrew.exe (PID: 2276)
Reads the cookies of Mozilla Firefox
- asftrew.exe (PID: 3704)
Executable content was dropped or overwritten
- asftrew.exe (PID: 2276)
- EQNEDT32.EXE (PID: 3680)
Executed via COM
- EQNEDT32.EXE (PID: 3680)
Creates files in the user directory
- asftrew.exe (PID: 2276)
- EQNEDT32.EXE (PID: 3680)
- asftrew.exe (PID: 3704)
Reads the cookies of Google Chrome
- asftrew.exe (PID: 3704)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3856)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (99.9) |
|---|
Total processes
43
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\RkwnOfYTEJ" /XML "C:\Users\admin\AppData\Local\Temp\tmpDC33.tmp" | C:\Windows\System32\schtasks.exe | — | asftrew.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | "C:\Users\admin\AppData\Roaming\asftrew.exe" | C:\Users\admin\AppData\Roaming\asftrew.exe | EQNEDT32.EXE | ||||||||||||
User: admin Company: Saab Integrity Level: MEDIUM Description: Platformer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3680 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3704 | "C:\Users\admin\AppData\Roaming\asftrew.exe" | C:\Users\admin\AppData\Roaming\asftrew.exe | asftrew.exe | ||||||||||||
User: admin Company: Saab Integrity Level: MEDIUM Description: Platformer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3856 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\sample10.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 336
Read events
949
Write events
382
Delete events
5
Modification events
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | w*= |
Value: 772A3D00100F0000010000000000000000000000 | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1324482590 | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482704 | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1324482705 | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 100F00000AAC58A76C3DD50100000000 | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | += |
Value: 202B3D00100F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | += |
Value: 202B3D00100F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3856) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF647.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2276 | asftrew.exe | C:\Users\admin\AppData\Local\Temp\tmpDC33.tmp | — | |
MD5:— | SHA256:— | |||
| 3856 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$mple10.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3680 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\neeel[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3680 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\asftrew.exe | executable | |
MD5:— | SHA256:— | |||
| 3704 | asftrew.exe | C:\Users\admin\AppData\Roaming\zdk3kolz.fqz.zip | compressed | |
MD5:— | SHA256:— | |||
| 3856 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3704 | asftrew.exe | C:\Users\admin\AppData\Local\Temp\636990570017072500_f1bba211-f608-496c-b23e-31de12d8b746.db | sqlite | |
MD5:— | SHA256:— | |||
| 3704 | asftrew.exe | C:\Users\admin\AppData\Roaming\zdk3kolz.fqz\Chrome\Default\Cookies | sqlite | |
MD5:— | SHA256:— | |||
| 3680 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
7
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3704 | asftrew.exe | GET | 200 | 34.233.102.38:80 | http://checkip.amazonaws.com/ | US | text | 15 b | malicious |
3704 | asftrew.exe | GET | 200 | 34.233.102.38:80 | http://checkip.amazonaws.com/ | US | text | 15 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | EQNEDT32.EXE | 112.213.89.40:443 | tfvn.com.vn | SUPERDATA | VN | malicious |
3704 | asftrew.exe | 34.233.102.38:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
3704 | asftrew.exe | 198.57.246.233:587 | mail.emtains.com | Unified Layer | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tfvn.com.vn |
| unknown |
checkip.amazonaws.com |
| malicious |
mail.emtains.com |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3704 | asftrew.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
3704 | asftrew.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3704 | asftrew.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3704 | asftrew.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
5 ETPRO signatures available at the full report