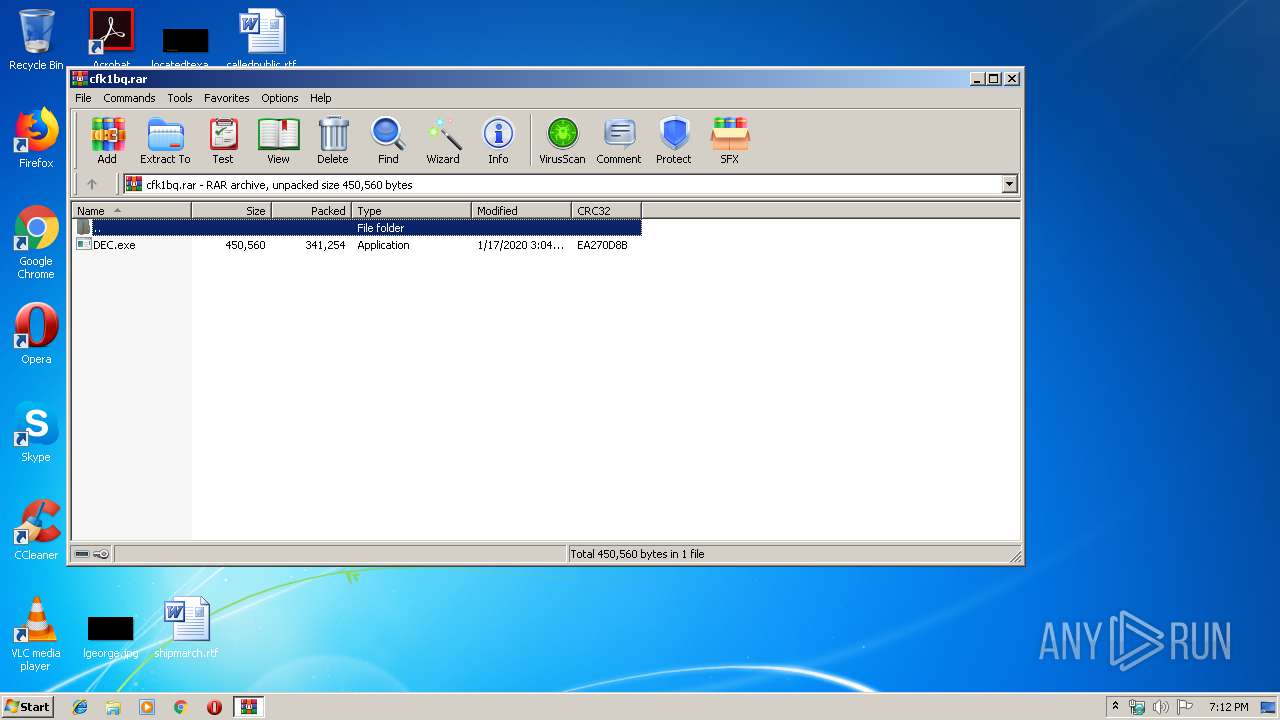
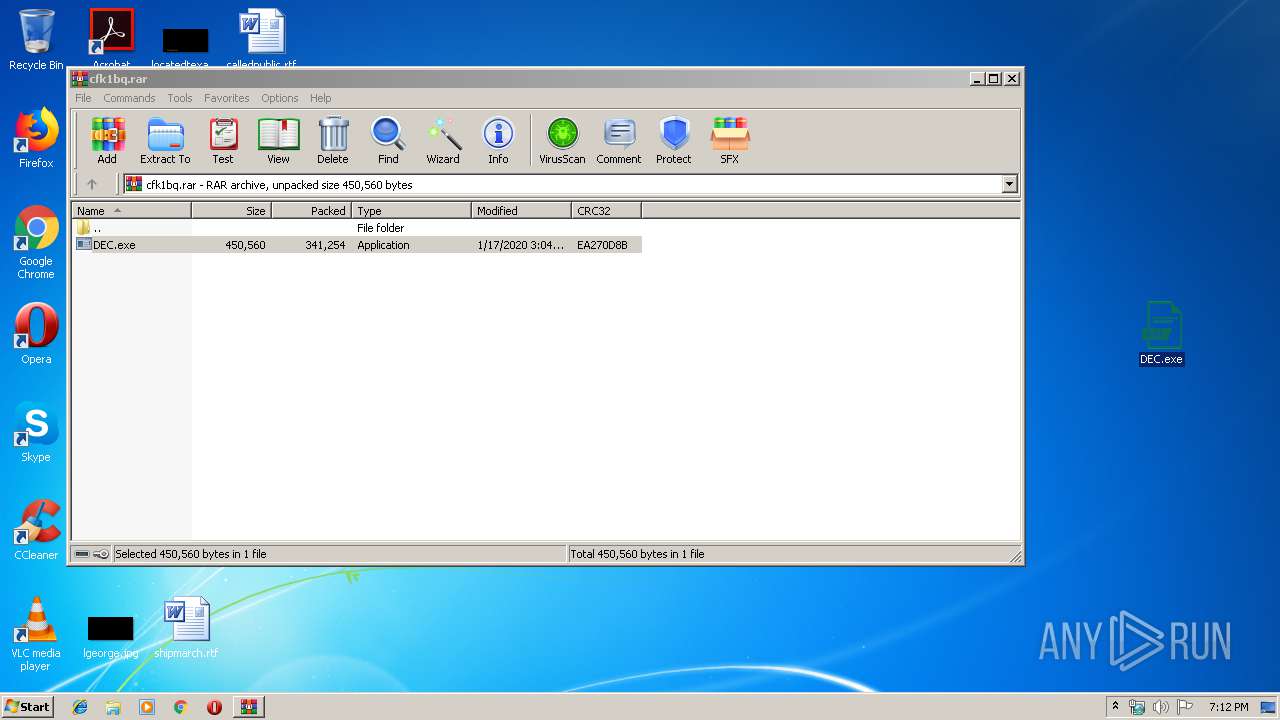
| download: | cfk1bq.rar |
| Full analysis: | https://app.any.run/tasks/8a027967-4bbd-4004-aba5-532dff264082 |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | January 17, 2020, 19:11:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 21C95BDC3C549B1C1F983DA4AD6E0FC8 |
| SHA1: | A0FEB1328D0D937C69AA5AEC37CEAC217F4F8F41 |
| SHA256: | 34BDDAF0A3D5DF5CCE7CAB316CE29C01A3594A5C2D3B259BCCD8F85B408BE5F2 |
| SSDEEP: | 6144:DABXXyLCOye7tto29vkSoJ2E4+Y/GQs8AQ8/HVh9x+I3KXf+JlXr7hX7:DAZXqtoKkSu2E4+Y48AP/HVnxov+J9Z |
MALICIOUS
Application was dropped or rewritten from another process
- DEC.exe (PID: 4976)
- Explorers.exe (PID: 444)
- DEC.exe (PID: 2684)
- Explorers.exe (PID: 5840)
- WHost.exe (PID: 4716)
- Explorers.exe (PID: 8100)
- Explorers.exe (PID: 7324)
Changes the autorun value in the registry
- Explorers.exe (PID: 444)
- Explorers.exe (PID: 5840)
- WHost.exe (PID: 4716)
NANOCORE was detected
- Explorers.exe (PID: 5840)
Connects to CnC server
- Explorers.exe (PID: 5840)
- Explorers.exe (PID: 8100)
- Explorers.exe (PID: 7324)
AVEMARIA was detected
- Explorers.exe (PID: 8100)
- Explorers.exe (PID: 7324)
Runs app for hidden code execution
- Explorers.exe (PID: 8100)
Loads dropped or rewritten executable
- dism.exe (PID: 6712)
SUSPICIOUS
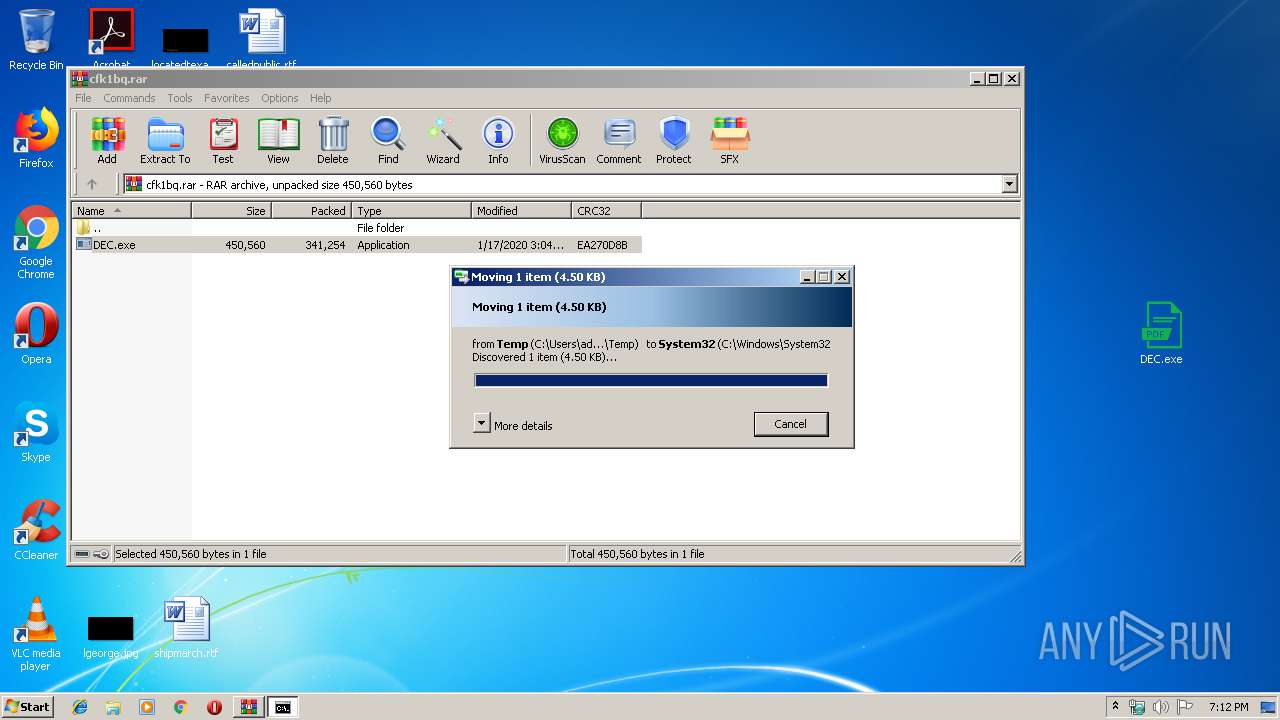
Executable content was dropped or overwritten
- DEC.exe (PID: 2684)
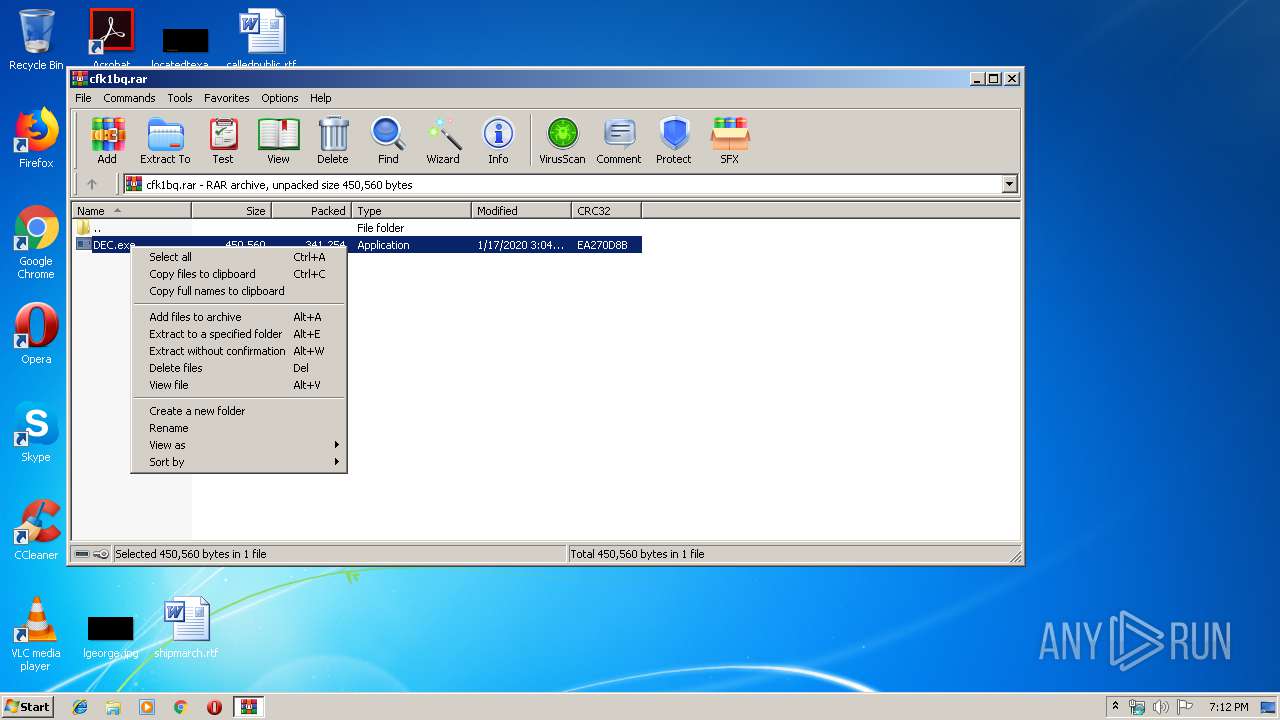
- WinRAR.exe (PID: 2548)
- Explorers.exe (PID: 444)
- Explorers.exe (PID: 5840)
- WHost.exe (PID: 4716)
- cmd.exe (PID: 11164)
- DllHost.exe (PID: 2884)
Starts itself from another location
- DEC.exe (PID: 2684)
- WHost.exe (PID: 4716)
Creates files in the user directory
- DEC.exe (PID: 2684)
- Explorers.exe (PID: 444)
- Explorers.exe (PID: 5840)
- WHost.exe (PID: 4716)
Application launched itself
- Explorers.exe (PID: 444)
Connects to unusual port
- Explorers.exe (PID: 5840)
- Explorers.exe (PID: 8100)
- Explorers.exe (PID: 7324)
Reads the machine GUID from the registry
- Explorers.exe (PID: 8100)
- Explorers.exe (PID: 7324)
Starts CMD.EXE for commands execution
- Explorers.exe (PID: 8100)
Executed via COM
- DllHost.exe (PID: 2884)
INFO
Manual execution by user
- DEC.exe (PID: 4976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
53
Monitored processes
13
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe" | C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe | DEC.exe | ||||||||||||
User: admin Company: enxzoli Integrity Level: MEDIUM Description: egiqmo Exit code: 0 Version: 2.6.81.71 Modules
| |||||||||||||||
| 2156 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2548 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\cfk1bq.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2548.34012\DEC.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2548.34012\DEC.exe | WinRAR.exe | ||||||||||||
User: admin Company: enxzoli Integrity Level: MEDIUM Description: egiqmo Exit code: 0 Version: 2.6.81.71 Modules
| |||||||||||||||
| 2884 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4716 | "C:\Users\admin\AppData\Roaming\Explorers\WHost.exe" | C:\Users\admin\AppData\Roaming\Explorers\WHost.exe | Explorers.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4880 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4976 | "C:\Users\admin\Desktop\DEC.exe" | C:\Users\admin\Desktop\DEC.exe | — | explorer.exe | |||||||||||
User: admin Company: enxzoli Integrity Level: MEDIUM Description: egiqmo Exit code: 0 Version: 2.6.81.71 Modules
| |||||||||||||||
| 5840 | "C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe" | C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe | Explorers.exe | ||||||||||||
User: admin Company: enxzoli Integrity Level: MEDIUM Description: egiqmo Exit code: 0 Version: 2.6.81.71 Modules
| |||||||||||||||
| 6712 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\system32\dism.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 782
Read events
1 686
Write events
96
Delete events
0
Modification events
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\cfk1bq.rar | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2548) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
8
Suspicious files
4
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5840 | Explorers.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\settings.bak | — | |
MD5:— | SHA256:— | |||
| 2548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2548.34012\DEC.exe | executable | |
MD5:— | SHA256:— | |||
| 5840 | Explorers.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\TCP Monitor\tcpmon.exe | executable | |
MD5:— | SHA256:— | |||
| 5840 | Explorers.exe | C:\Users\admin\AppData\Roaming\90059C37-1320-41A4-B58D-2B75A9850D2F\run.dat | binary | |
MD5:— | SHA256:— | |||
| 444 | Explorers.exe | C:\Users\admin\AppData\Roaming\Explorers\WHost.exe | executable | |
MD5:— | SHA256:— | |||
| 2684 | DEC.exe | C:\Users\admin\AppData\Roaming\Explorers\Explorers.exe | executable | |
MD5:— | SHA256:— | |||
| 444 | Explorers.exe | C:\Users\admin\AppData\Roaming\Explorers\egiqmo.url | text | |
MD5:— | SHA256:— | |||
| 4716 | WHost.exe | C:\Users\admin\AppData\Roaming\Explorers.exe | executable | |
MD5:— | SHA256:— | |||
| 2548 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2548.35434\DEC.exe | executable | |
MD5:— | SHA256:— | |||
| 2884 | DllHost.exe | C:\Windows\System32\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
39
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7324 | Explorers.exe | GET | — | 146.185.195.20:80 | http://146.185.195.20/upnp.exe | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2684 | DEC.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
5840 | Explorers.exe | 185.19.85.144:55190 | rubenbakerr.ddns.net | Datawire Ag | CH | malicious |
7324 | Explorers.exe | 149.202.110.30:18982 | meki.duckdns.org | OVH SAS | FR | malicious |
7324 | Explorers.exe | 146.185.195.20:80 | — | Petersburg Internet Network ltd. | RU | malicious |
8100 | Explorers.exe | 149.202.110.30:18982 | meki.duckdns.org | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
rubenbakerr.ddns.net |
| malicious |
meki.duckdns.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
5840 | Explorers.exe | A Network Trojan was detected | ET TROJAN Possible NanoCore C2 60B |
5840 | Explorers.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore.RAT |
5840 | Explorers.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore.RAT |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
8100 | Explorers.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
8100 | Explorers.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Encrypted Checkin |
8100 | Explorers.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
5840 | Explorers.exe | A Network Trojan was detected | REMOTE [PTsecurity] NanoCore.RAT |
7324 | Explorers.exe | A Network Trojan was detected | AV TROJAN Ave Maria RAT CnC Response |
15 ETPRO signatures available at the full report