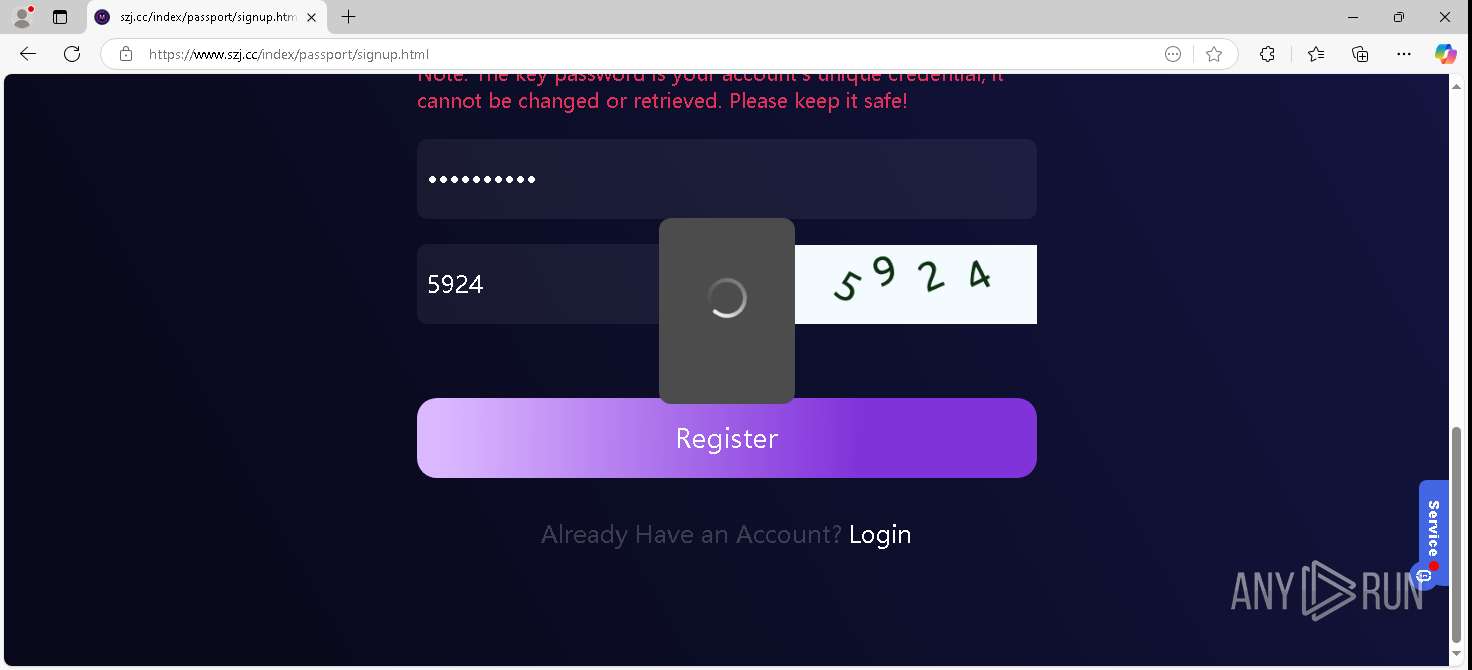
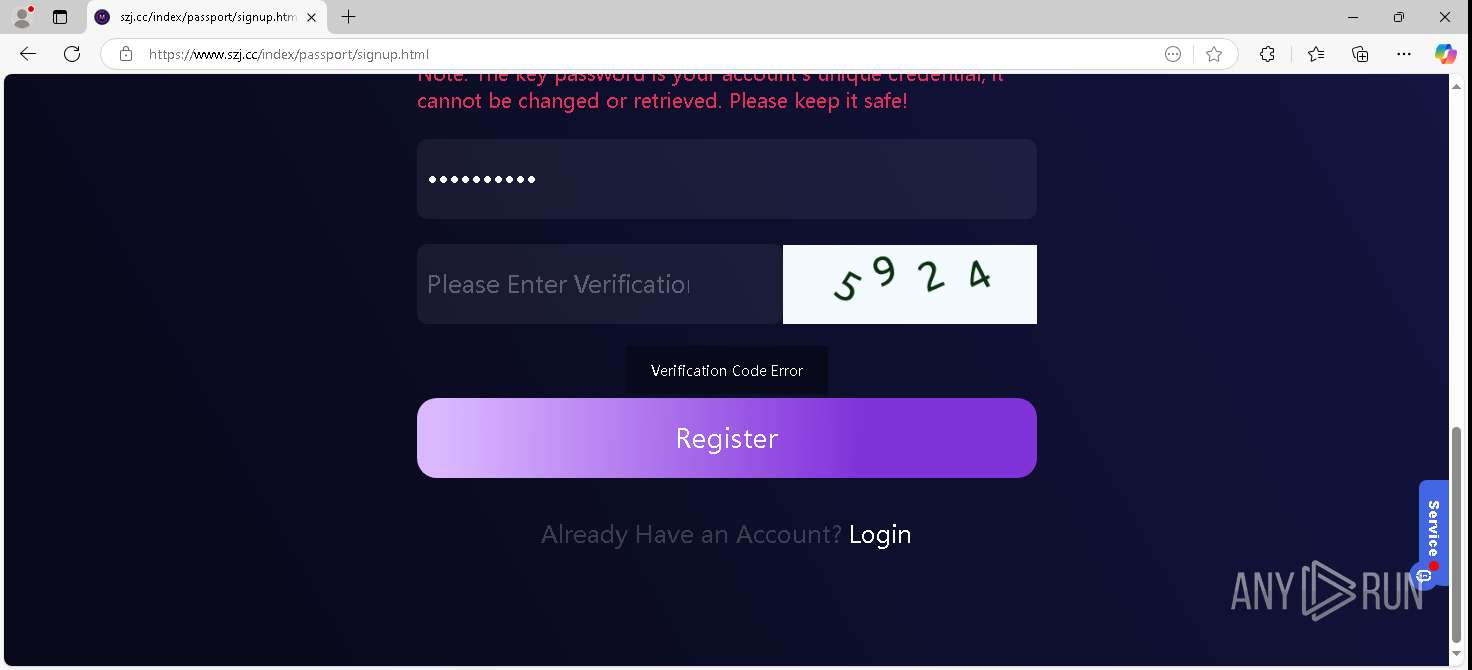
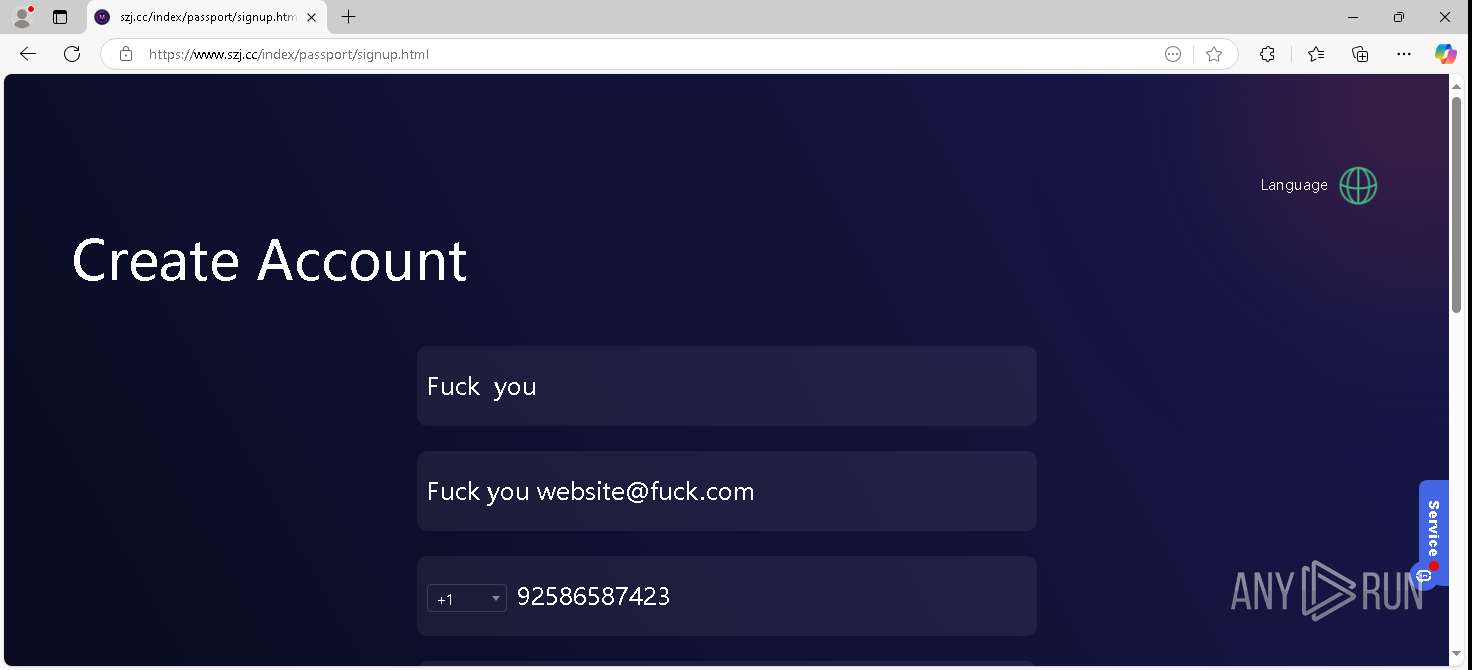
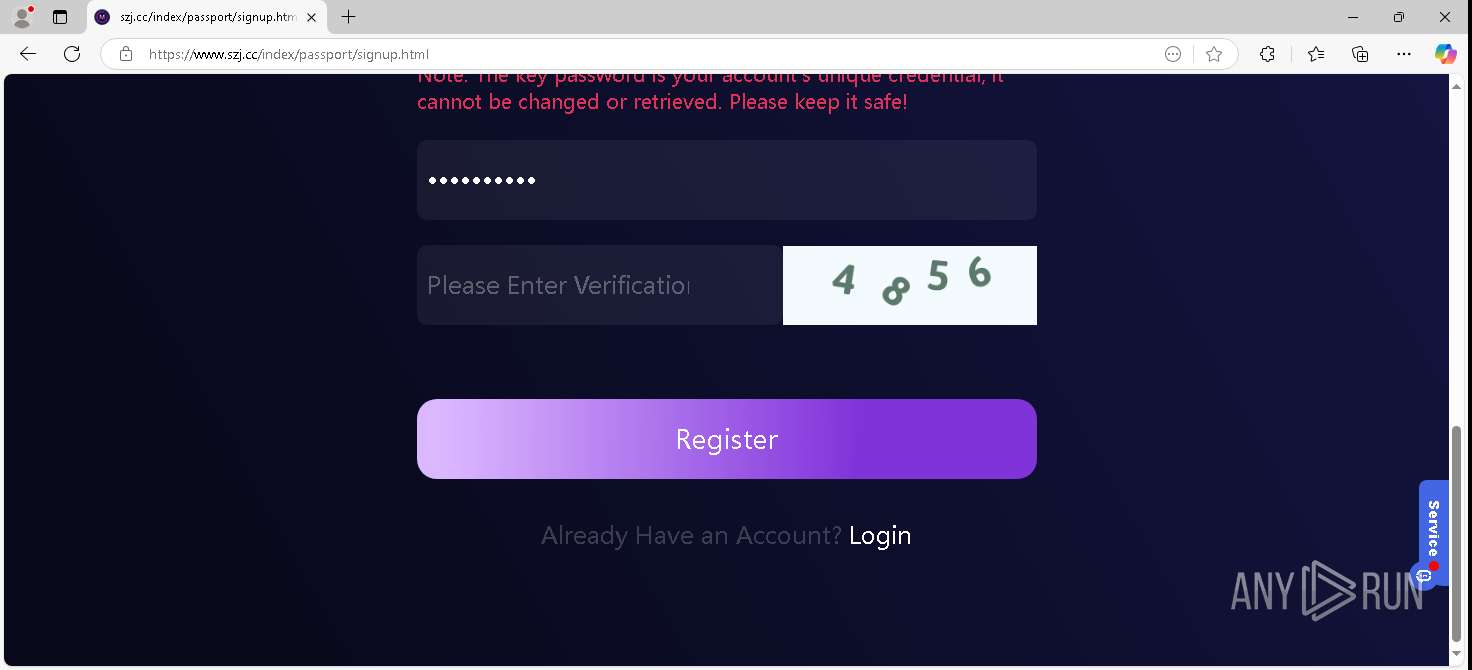
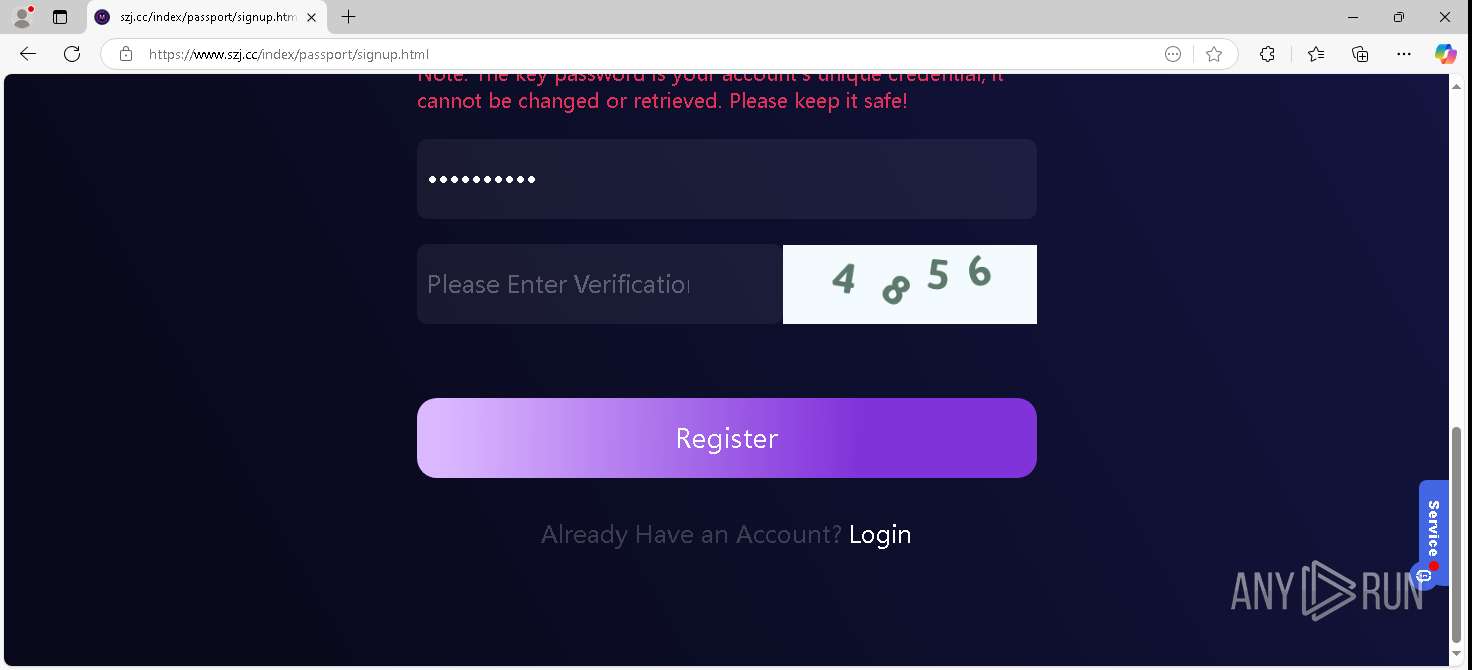
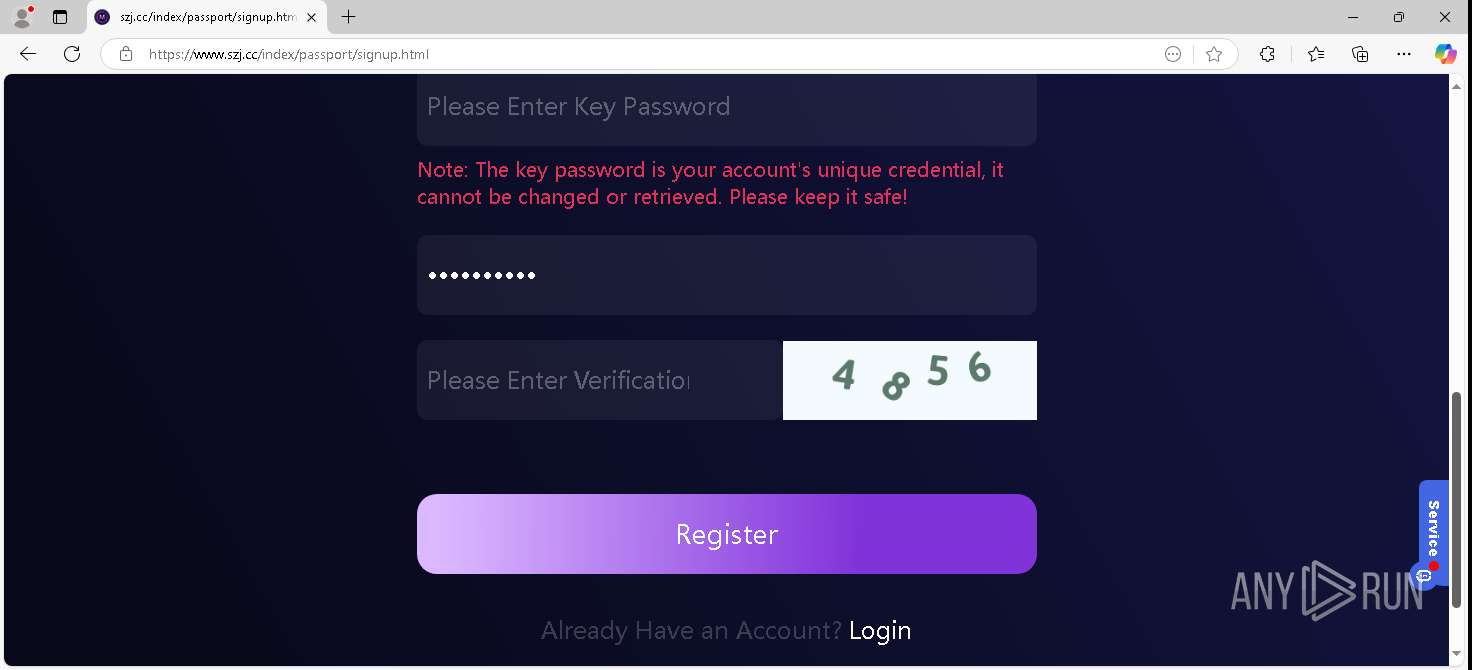
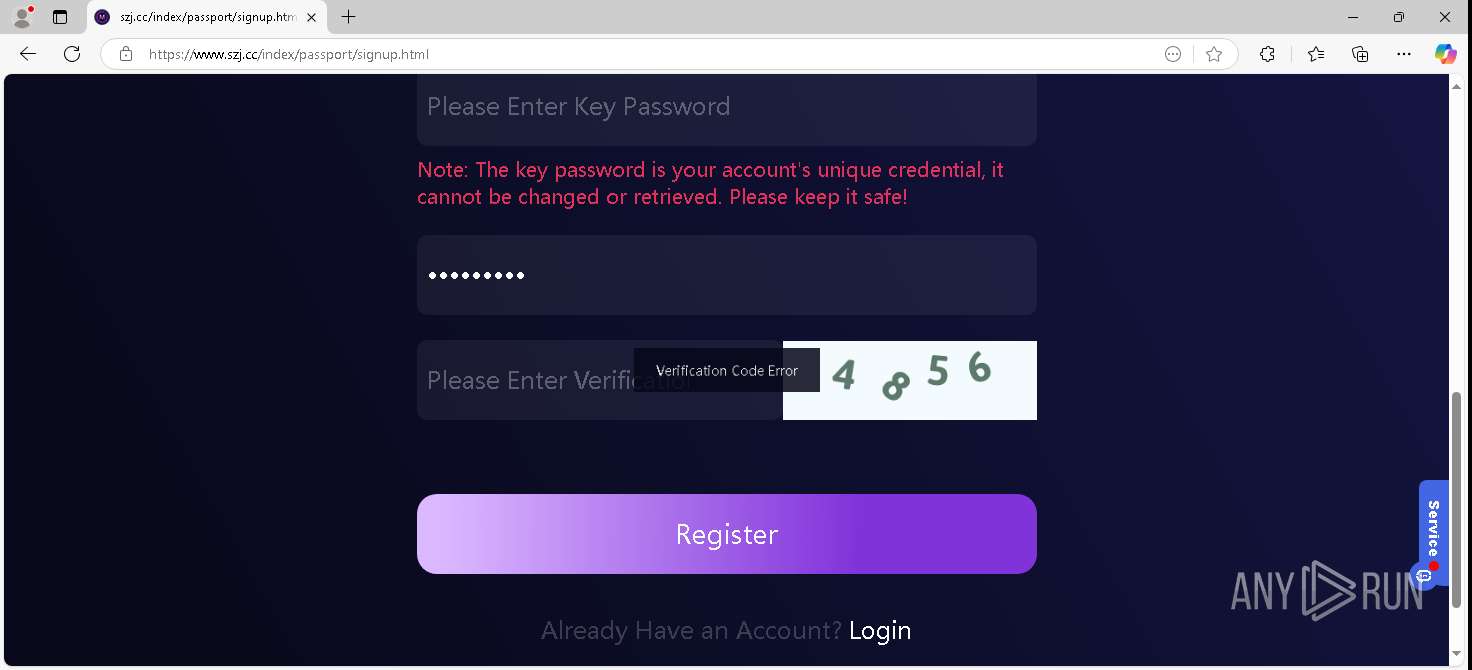
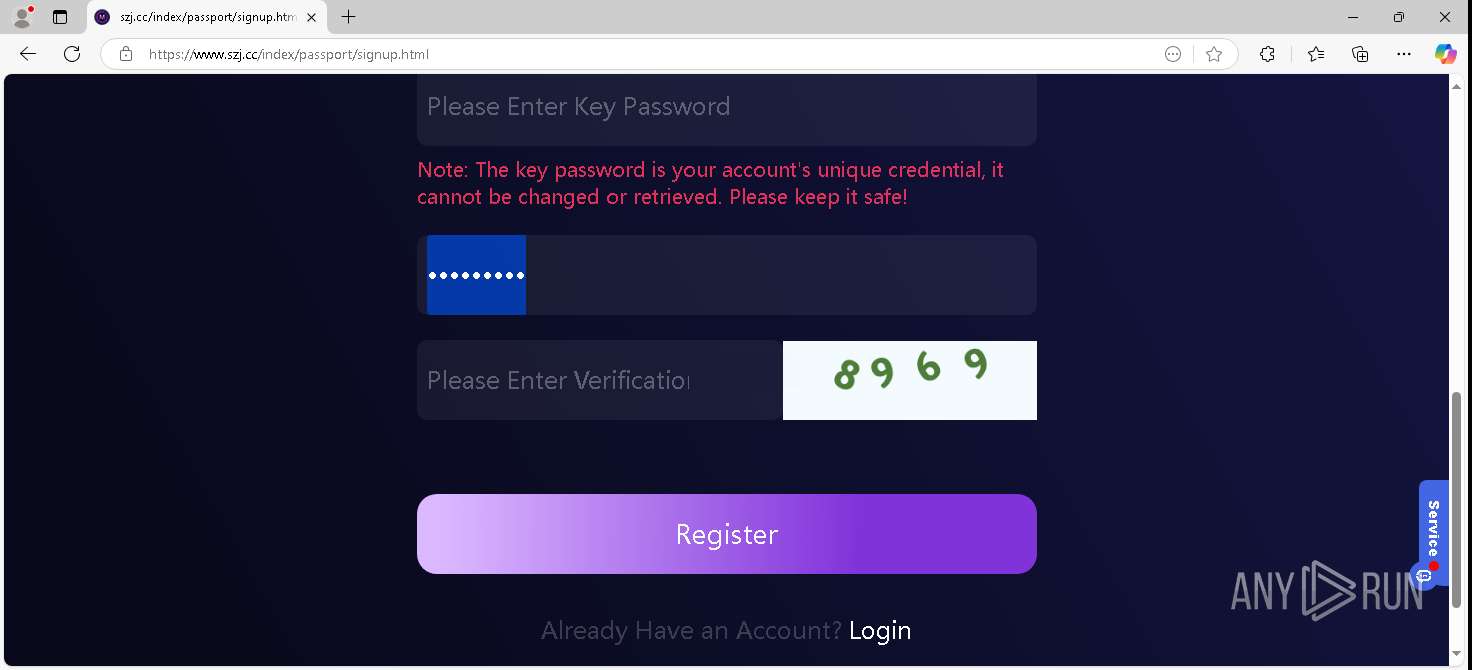
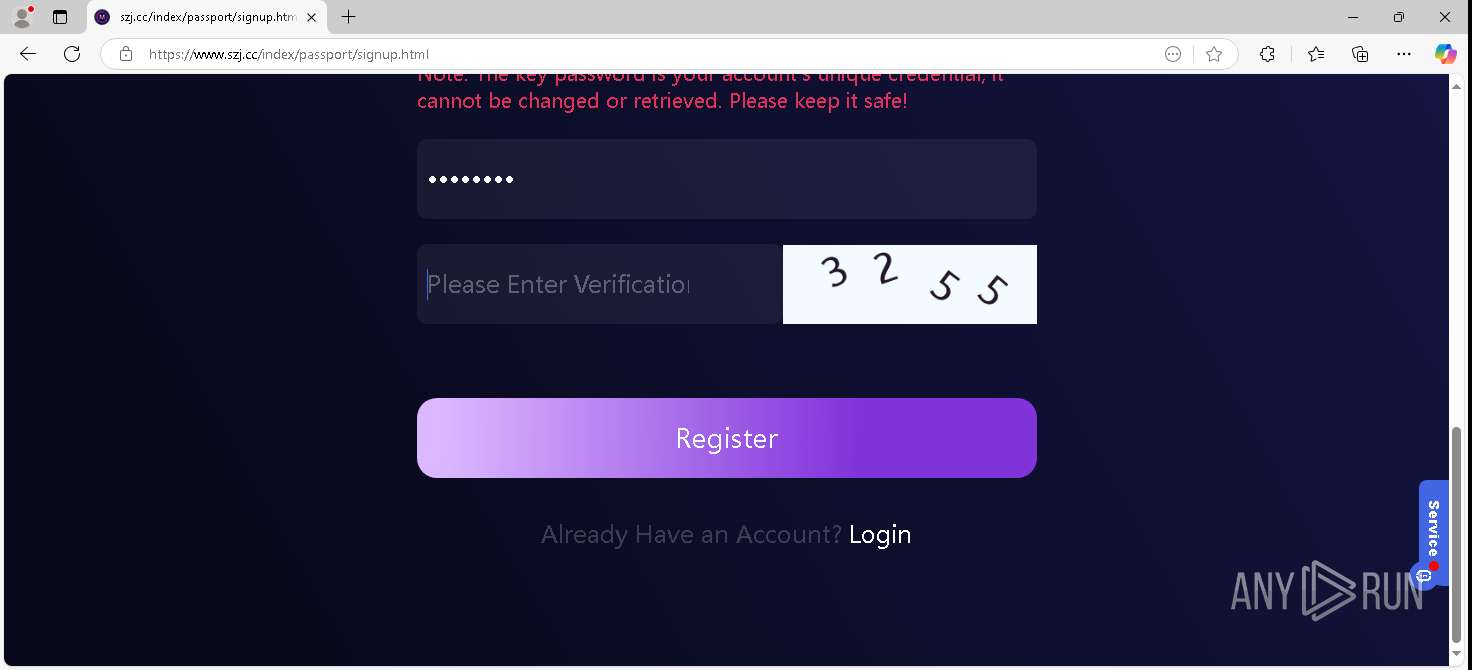
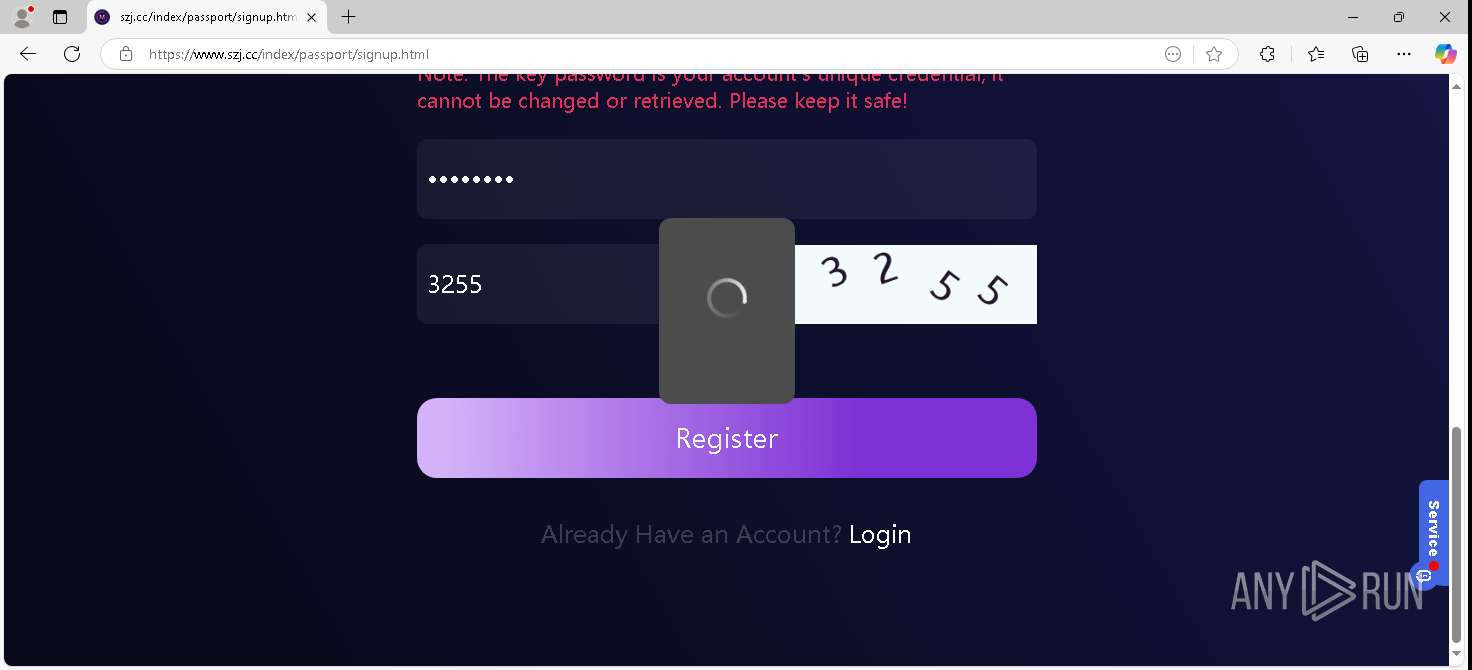
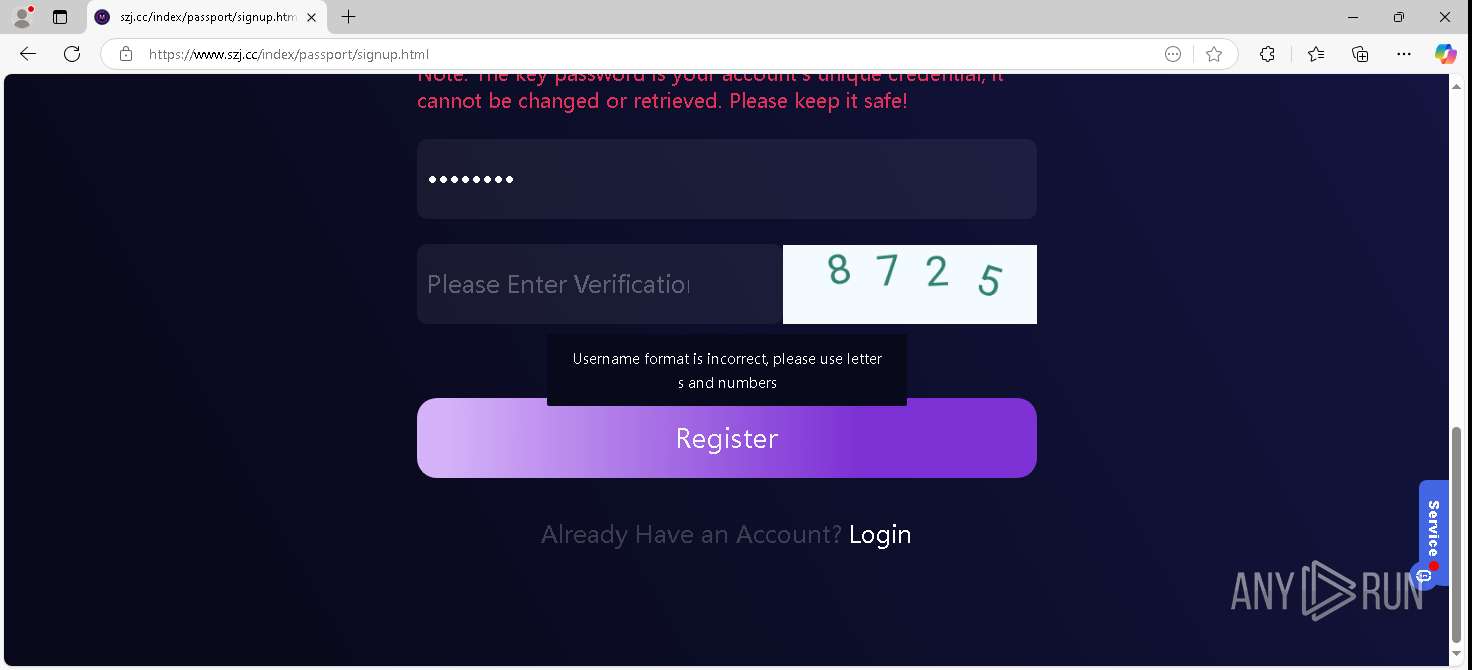
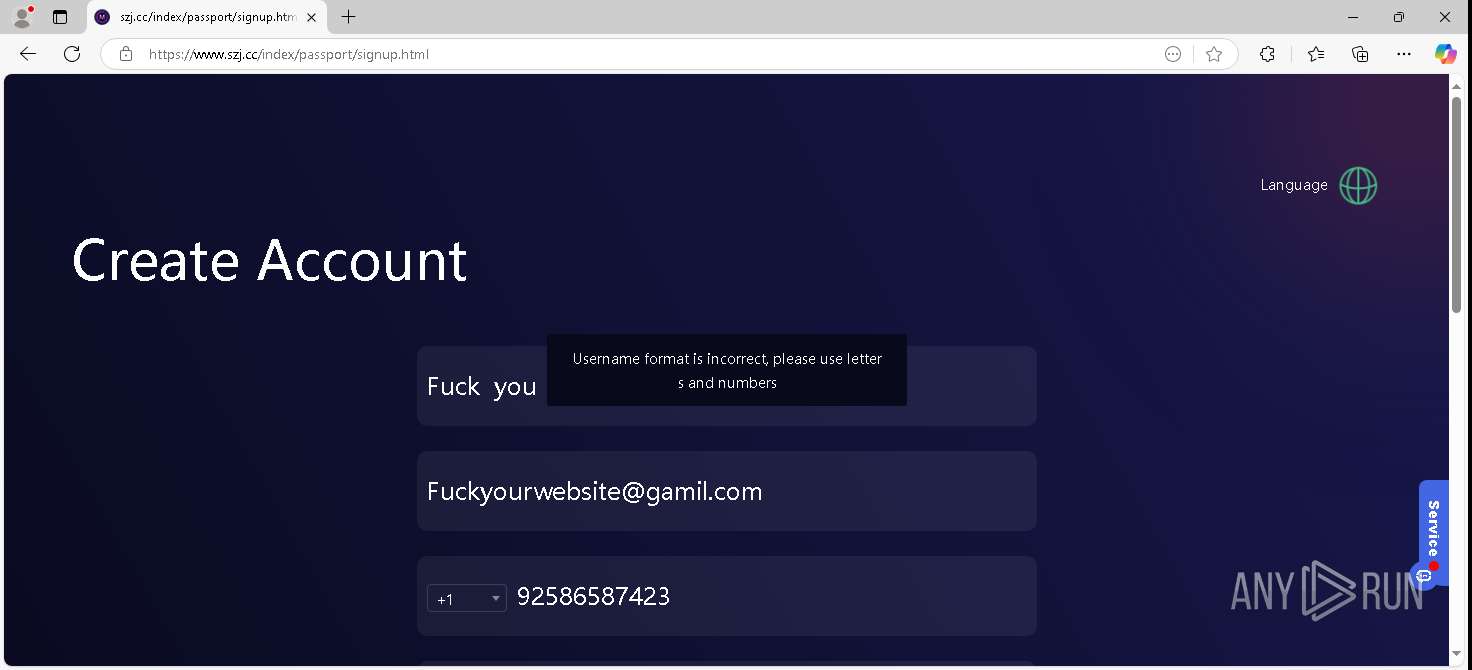
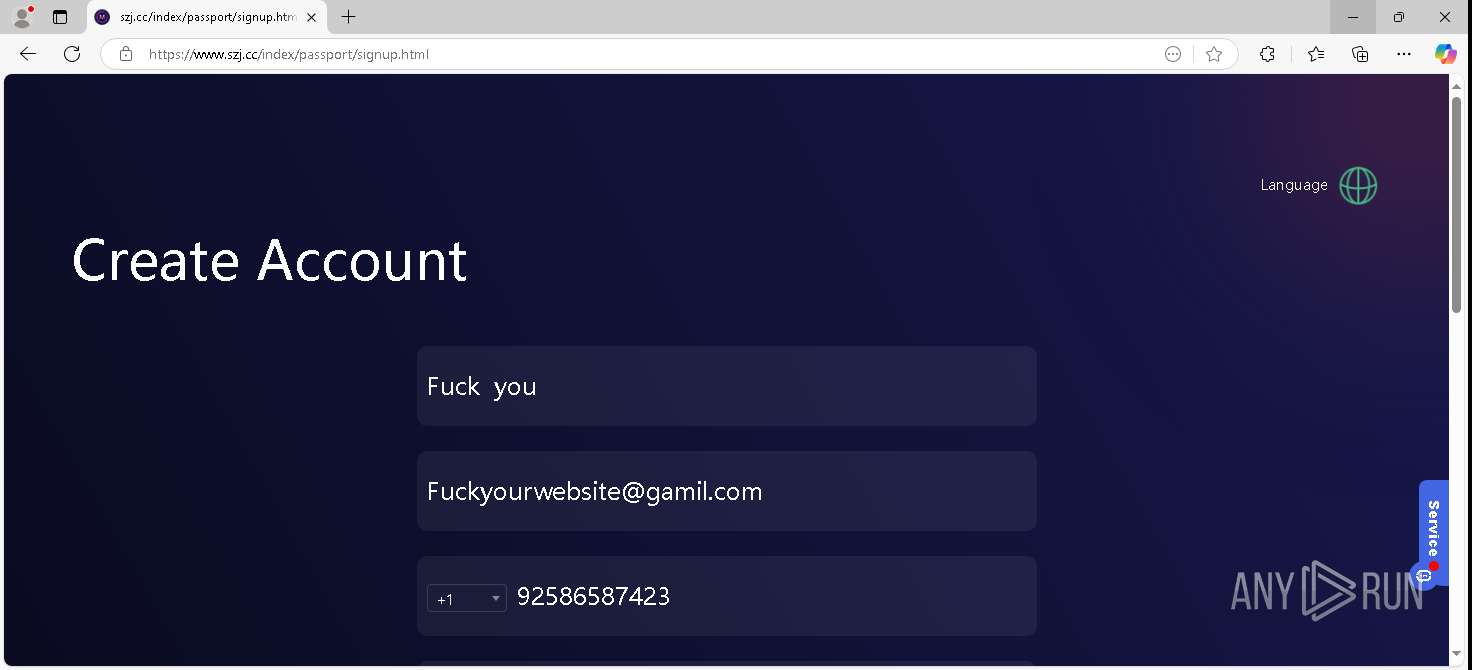
| URL: | www.szj.cc |
| Full analysis: | https://app.any.run/tasks/469b857f-7451-4e42-a7a8-7303d1ac9b8e |
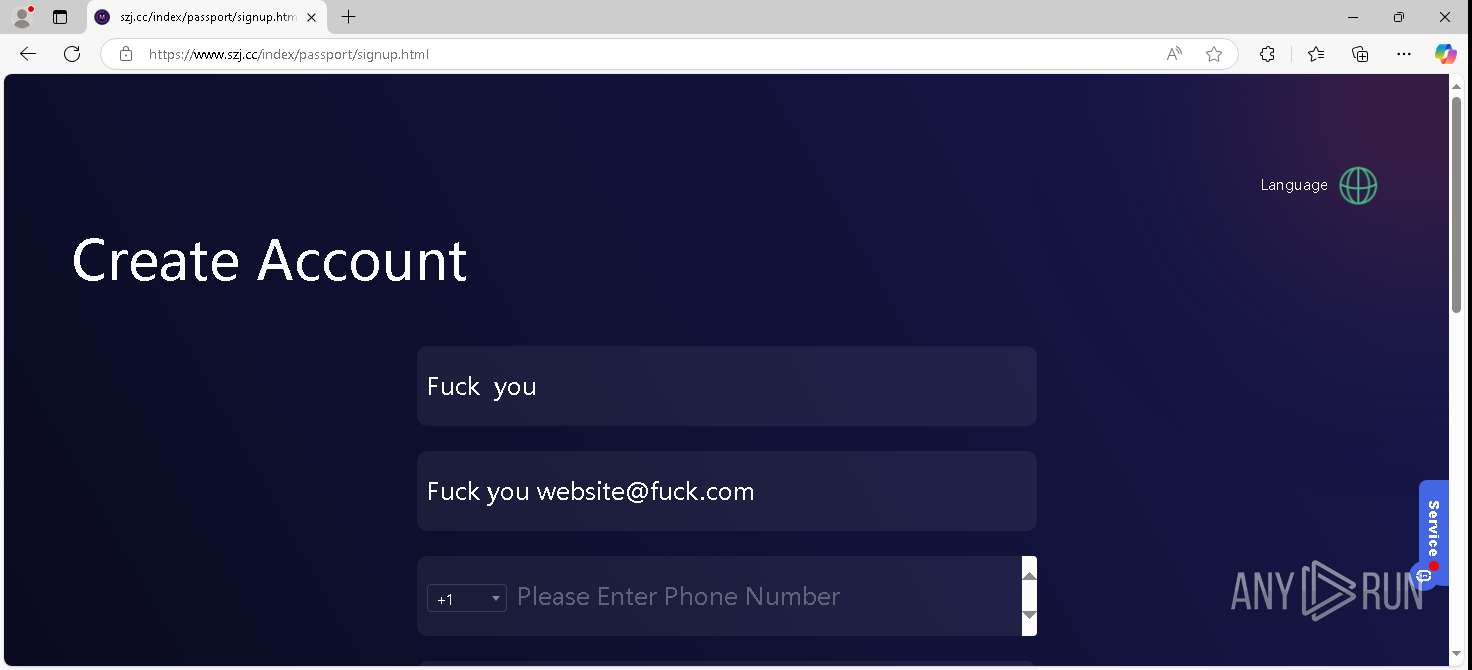
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | April 05, 2026, 09:36:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MD5: | FE4D77F7BBD7111429E5EC0444CE2EEC |
| SHA1: | 251B92723ADE21B6560C3FA00820A98357C79A26 |
| SHA256: | 34834A3F260C200BAB3BF57FBAF07A9AF2F85D2C92F43C8208F10CF19F160385 |
| SSDEEP: | 3:EeV:lV |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
155
Monitored processes
0
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
195
TCP/UDP connections
97
DNS requests
66
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6240 | RUXIMICS.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/RUXIM?os=Windows&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3623&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&FlightRing=Retail&AttrDataVer=188&App=RUXIM&AppVer=&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
5336 | MoUsoCoreWorker.exe | GET | 304 | 4.231.128.59:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3593&FlightIds=&UpdateOfferedDays=344&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%206%20Model%2014%20Stepping%203&sku=48&ActivationChannel=Retail&AttrDataVer=188&IsMDMEnrolled=0&ProcessorCores=4&ProcessorModel=Intel%28R%29%20Core%28TM%29%20i5-6400%20CPU%20%40%202.70GHz&TotalPhysicalRAM=4096&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260246&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
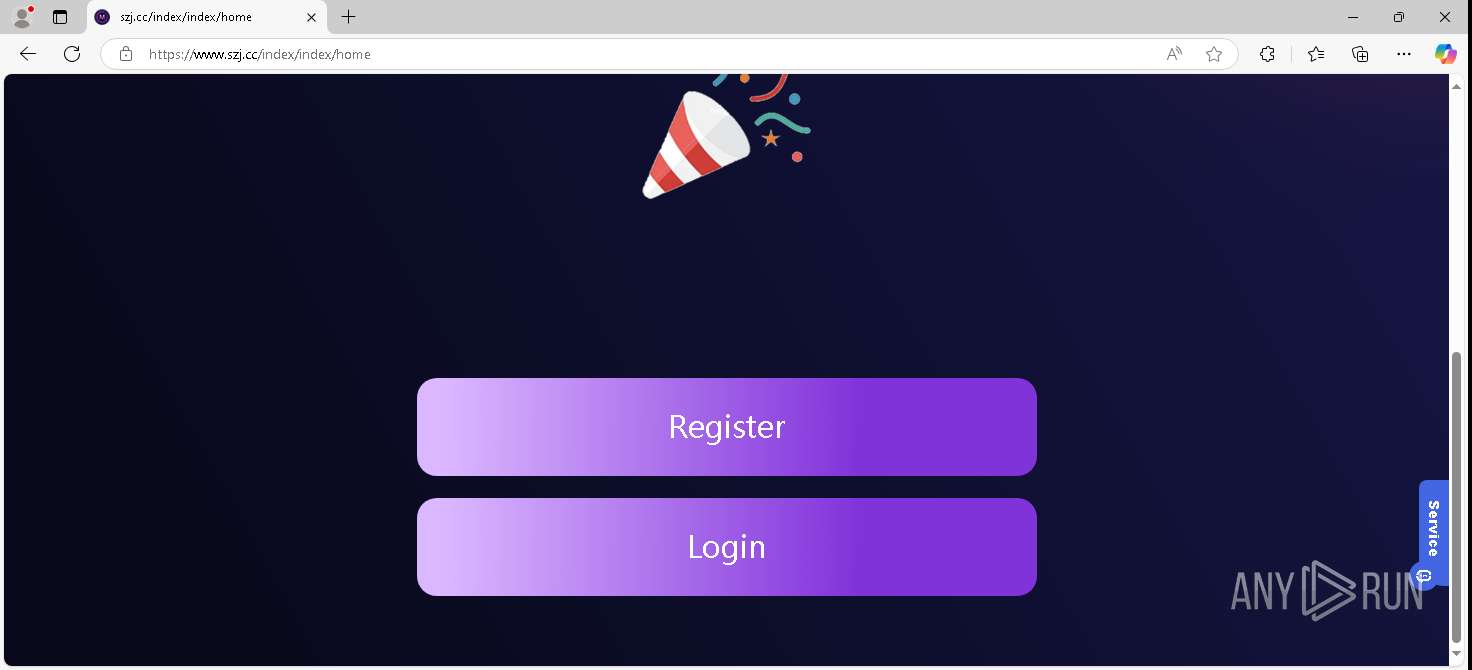
7028 | msedge.exe | GET | 302 | 188.114.96.3:443 | https://www.szj.cc/ | US | — | — | — |
7716 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7028 | msedge.exe | GET | 200 | 188.114.96.3:443 | https://www.szj.cc/index/index/home | US | text | 12.5 Kb | unknown |
6240 | RUXIMICS.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7028 | msedge.exe | GET | 200 | 188.114.96.3:443 | https://www.szj.cc/static/image/weui.css | US | binary | 153 Kb | unknown |
7028 | msedge.exe | GET | 200 | 92.123.104.51:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | unknown | binary | 665 Kb | whitelisted |
5336 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6240 | RUXIMICS.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7716 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6240 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5336 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | whitelisted |
7028 | msedge.exe | 92.123.104.52:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
7028 | msedge.exe | 188.114.96.3:443 | www.szj.cc | CLOUDFLARENET | US | whitelisted |
7716 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6240 | RUXIMICS.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5336 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7716 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.szj.cc |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
plugin-code.salesmartly.com |
| unknown |
login.live.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7028 | msedge.exe | Misc activity | INFO [ANY.RUN] .cc TLD domain request |
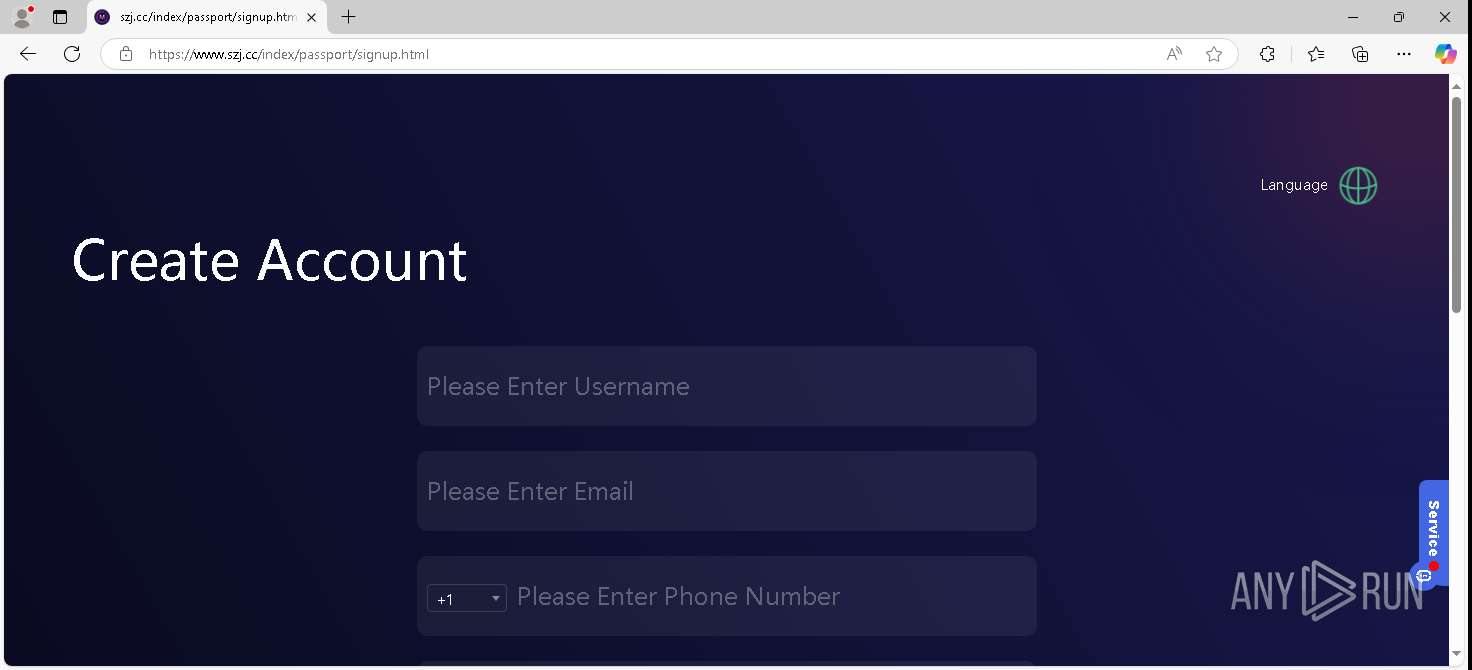
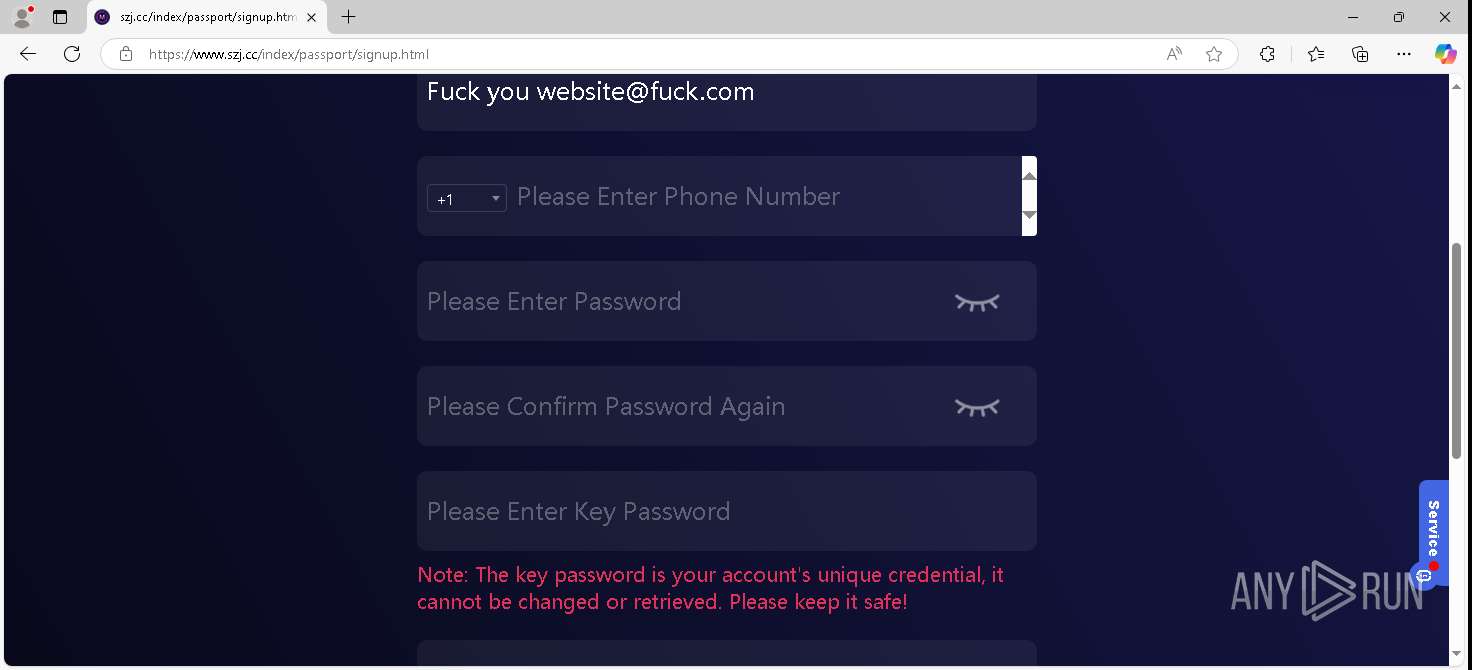
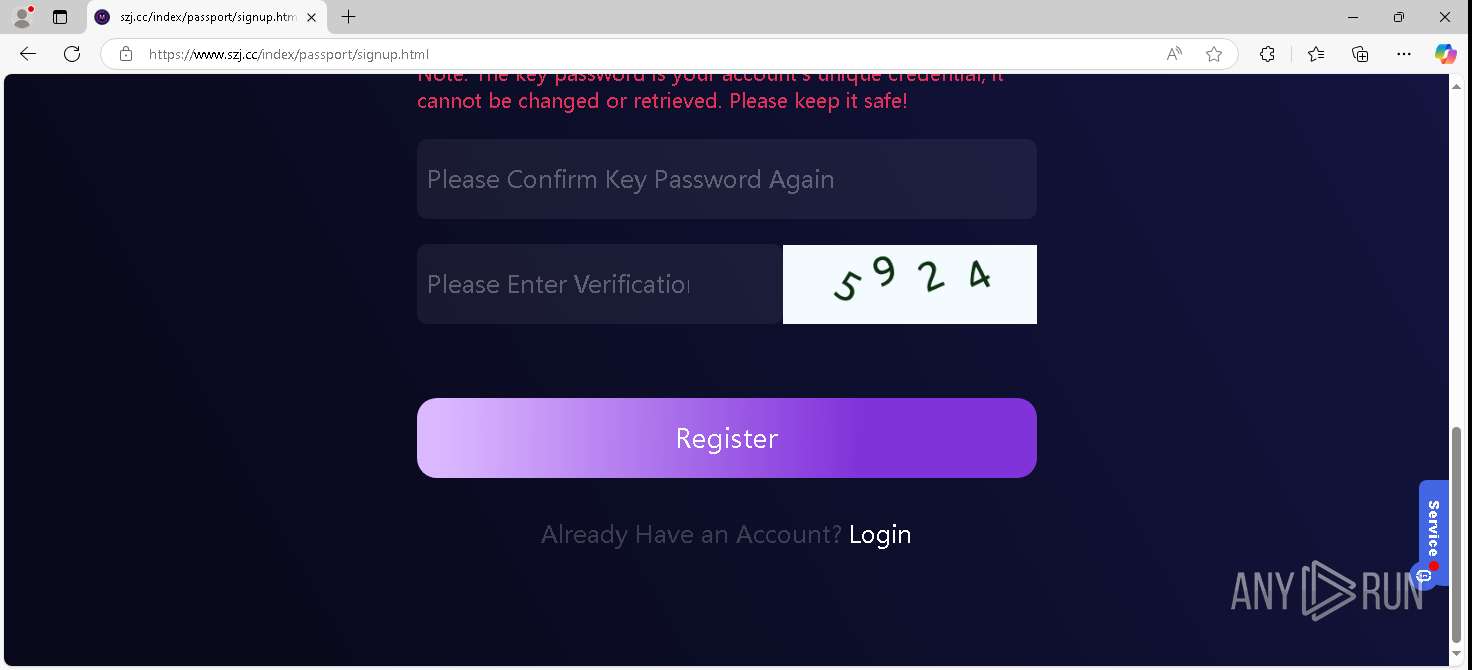
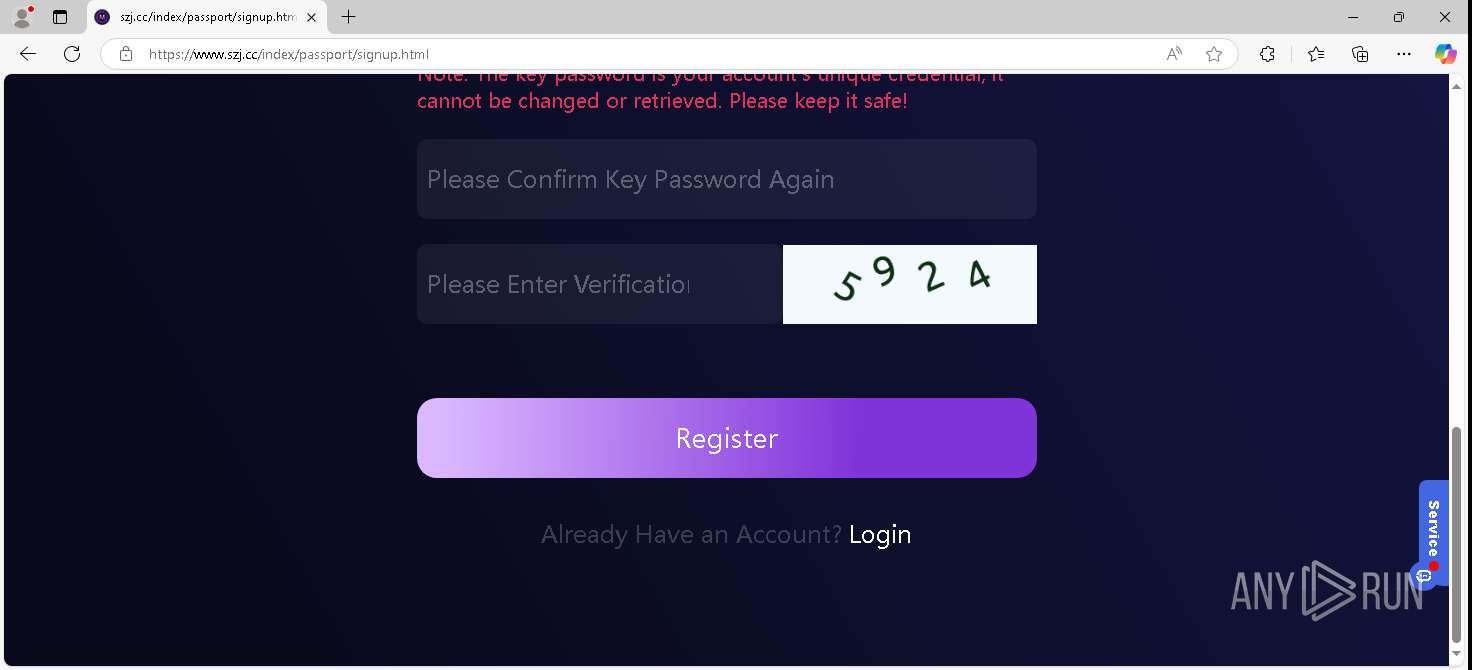
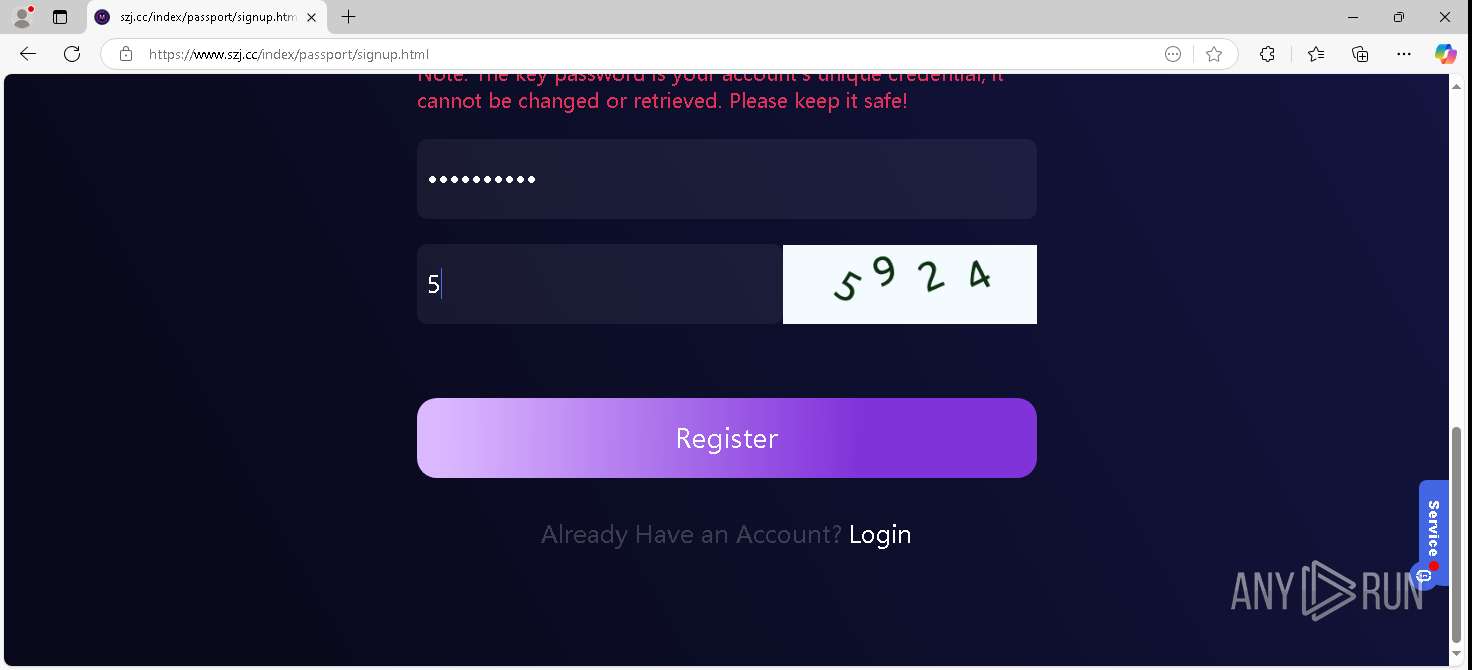
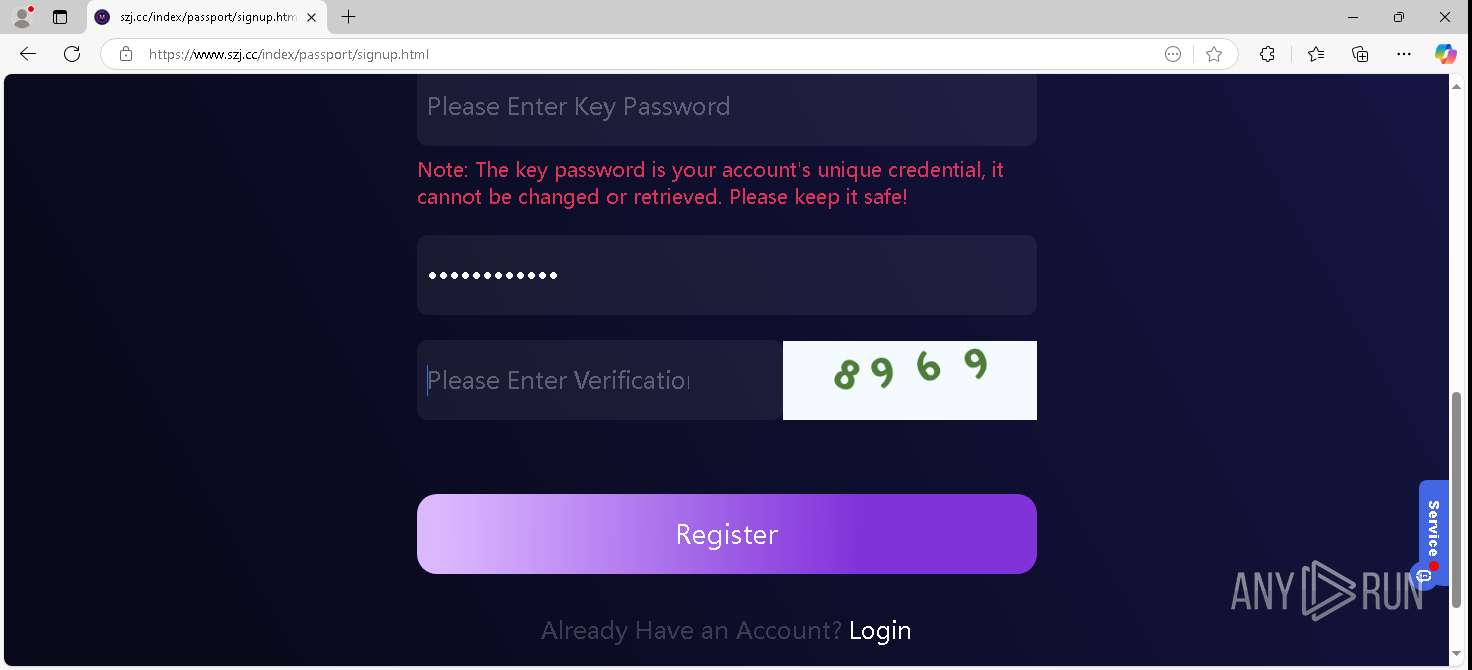
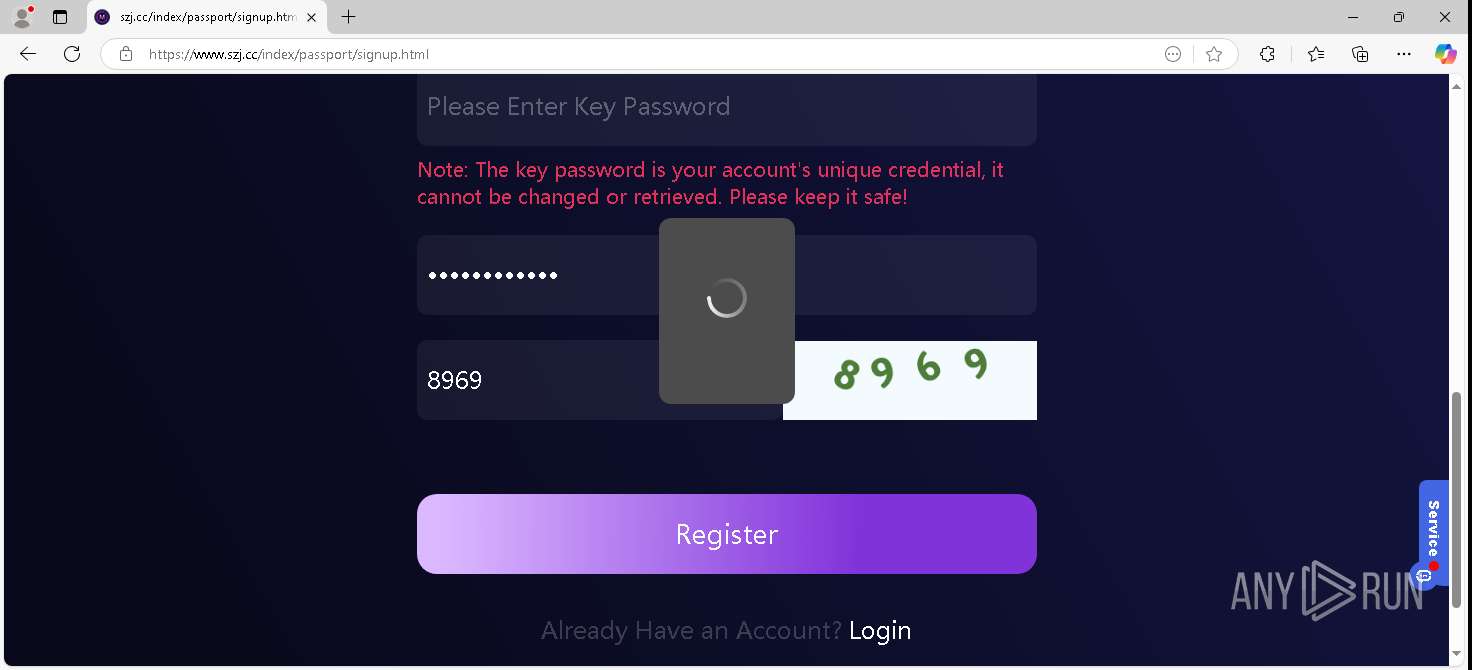
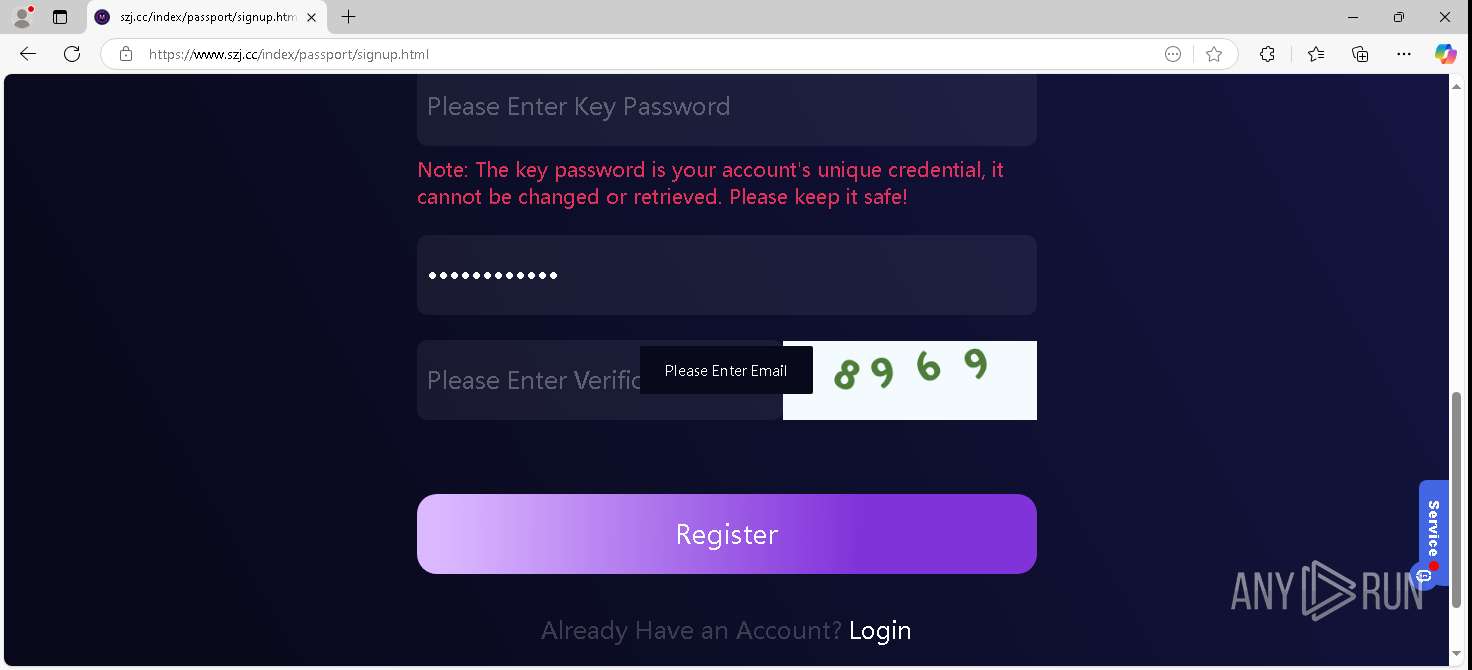
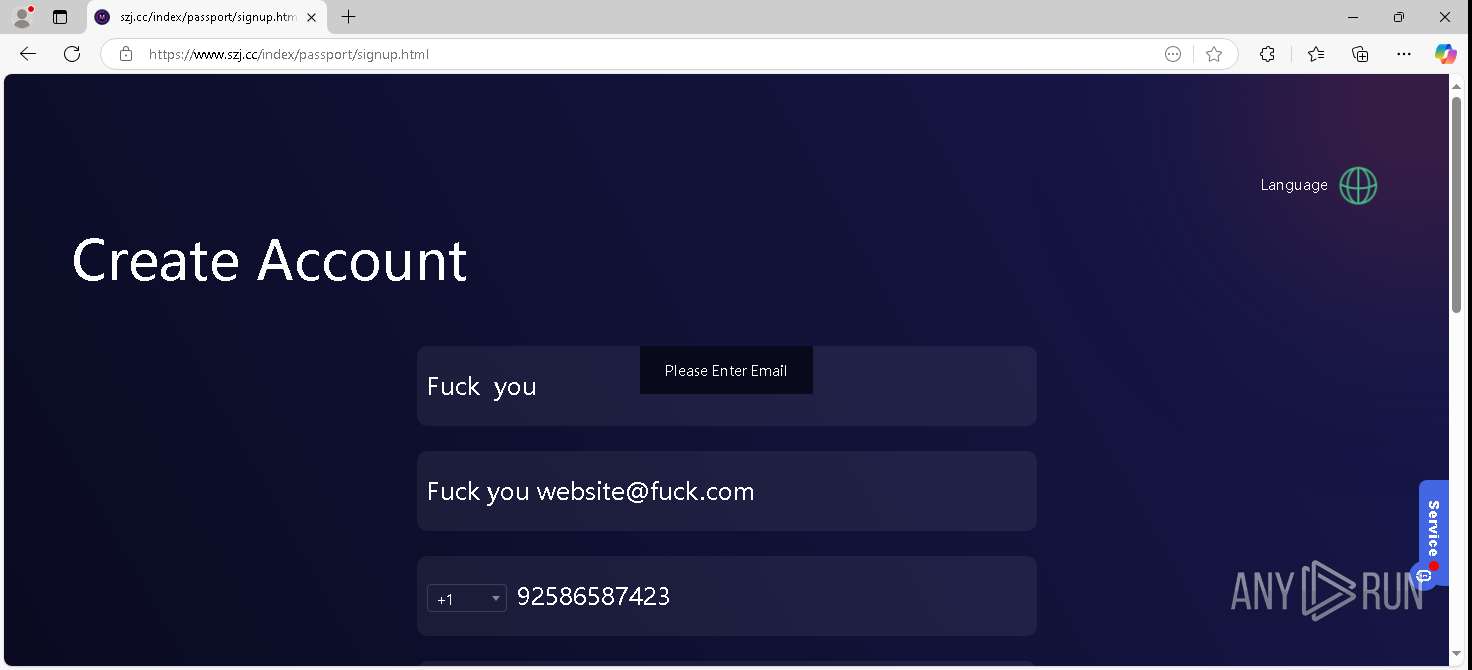
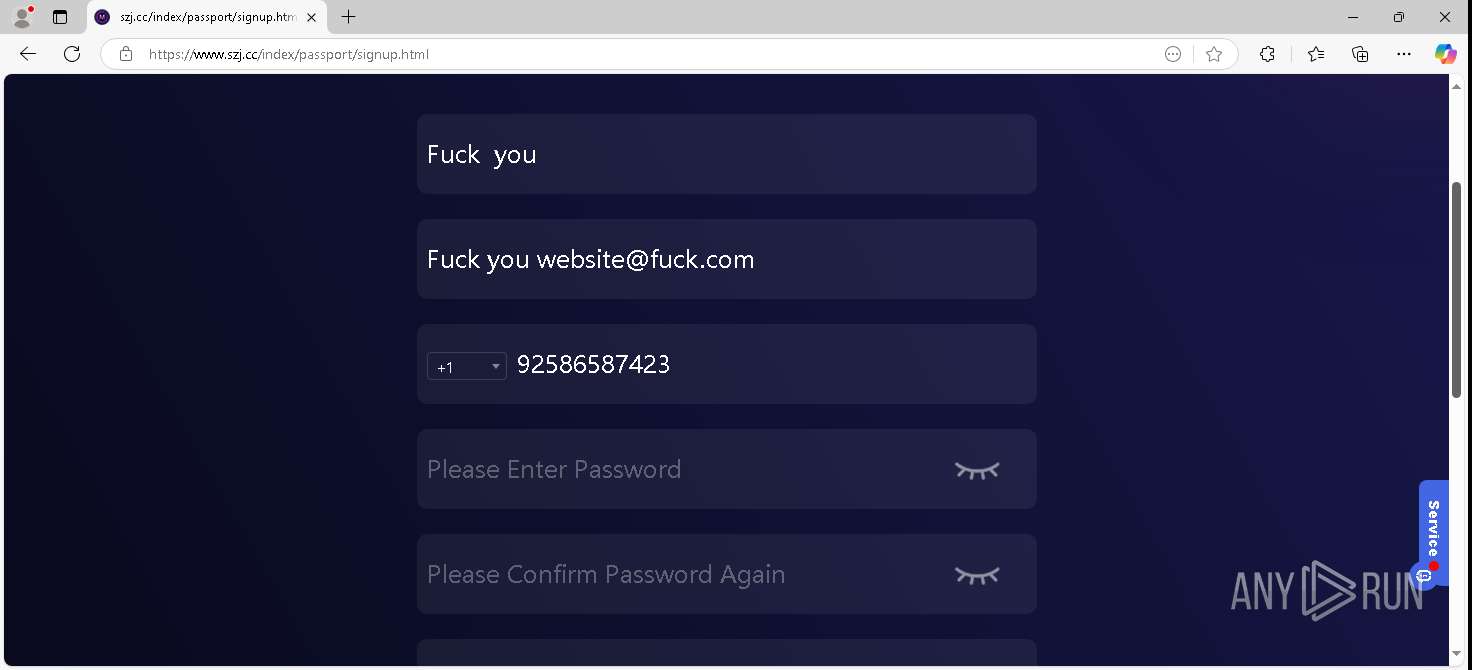
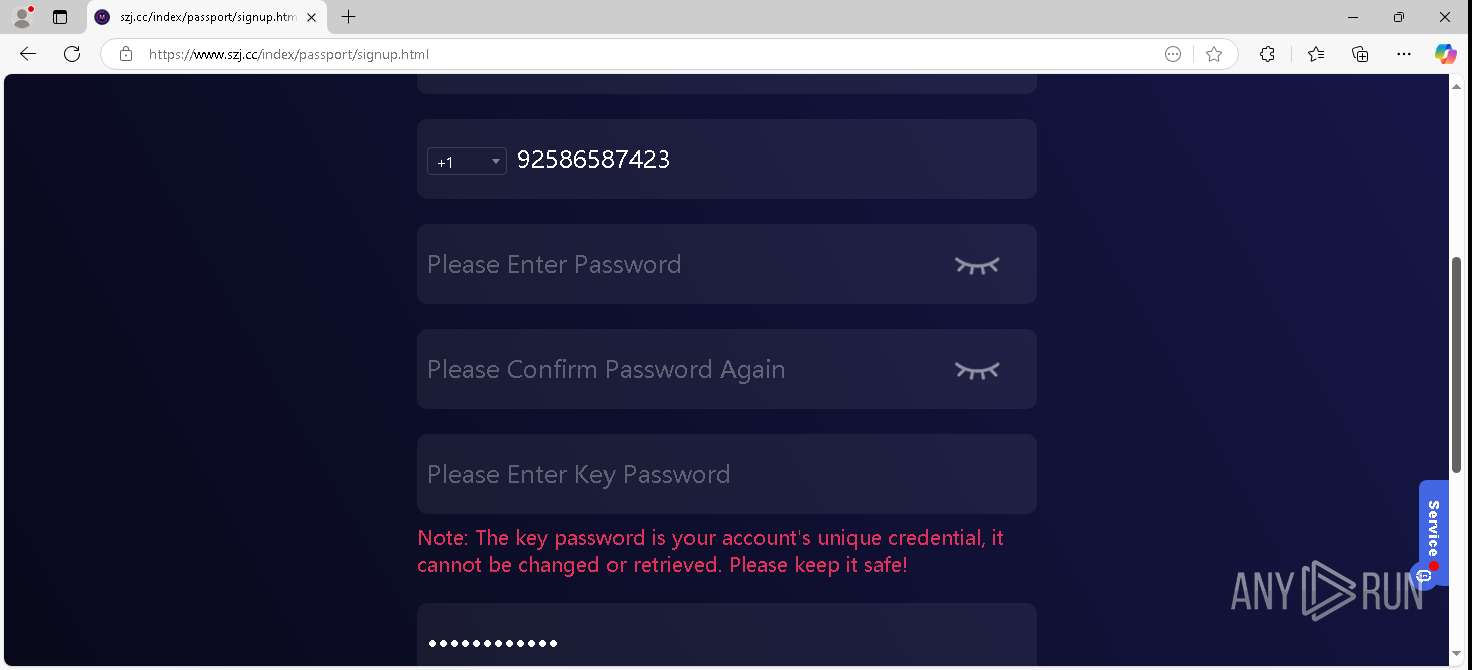
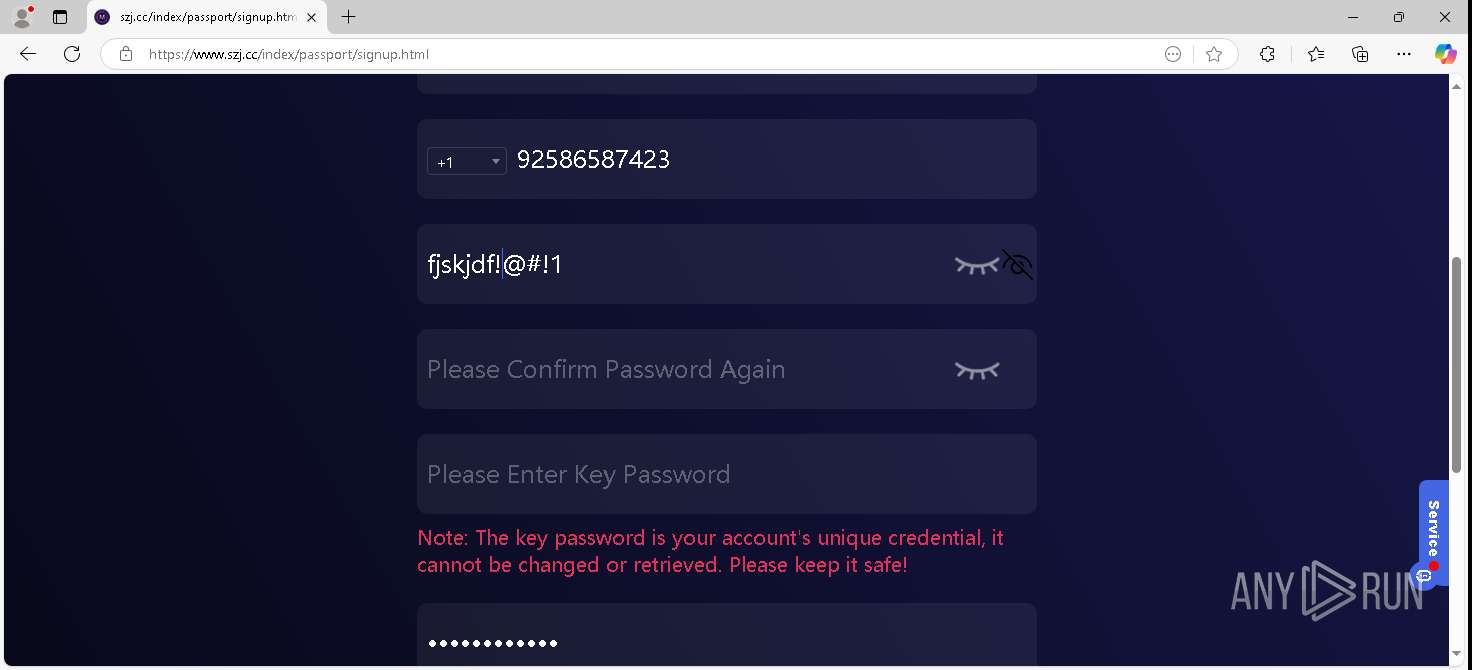
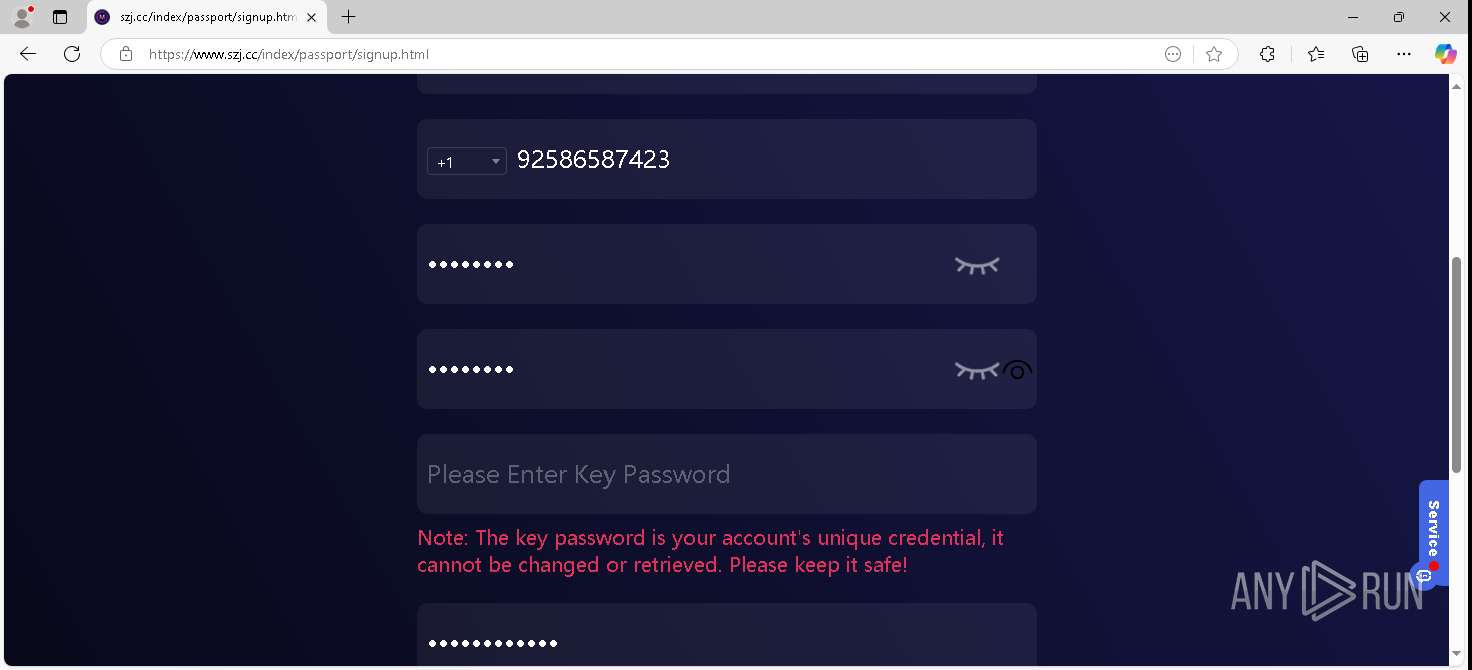
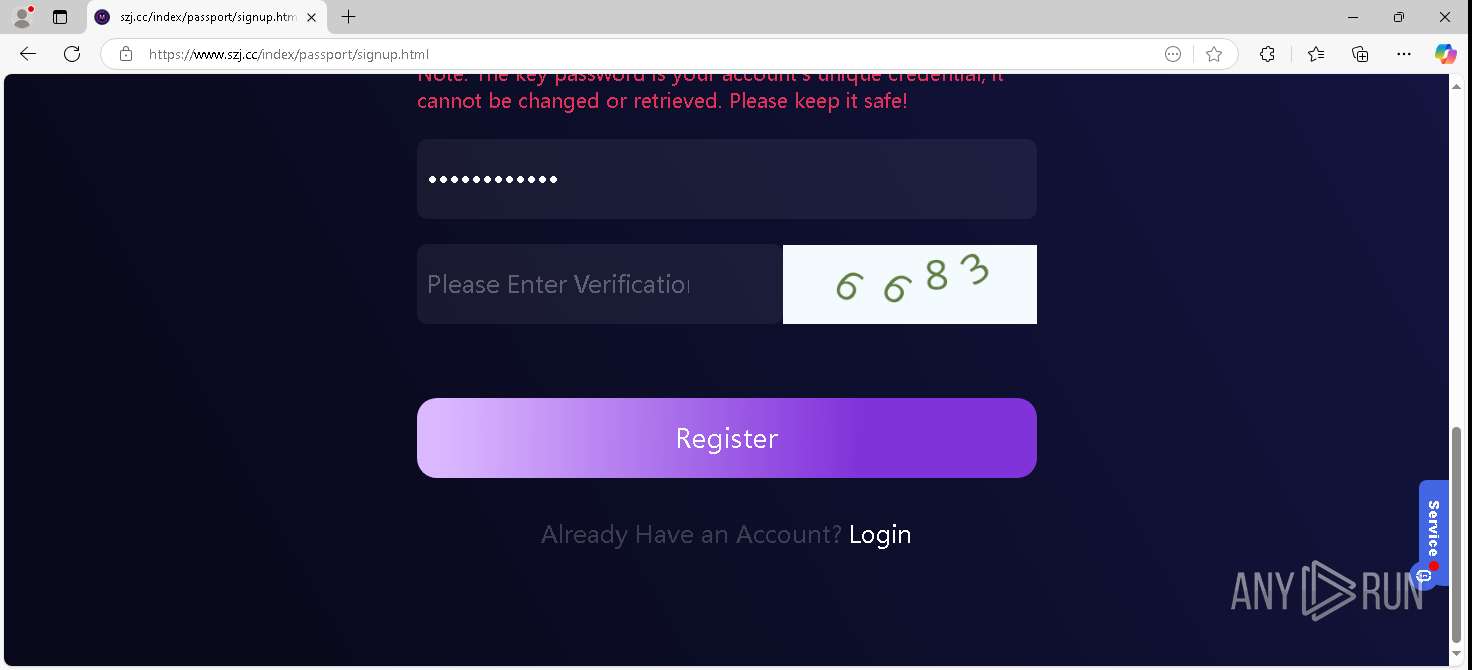
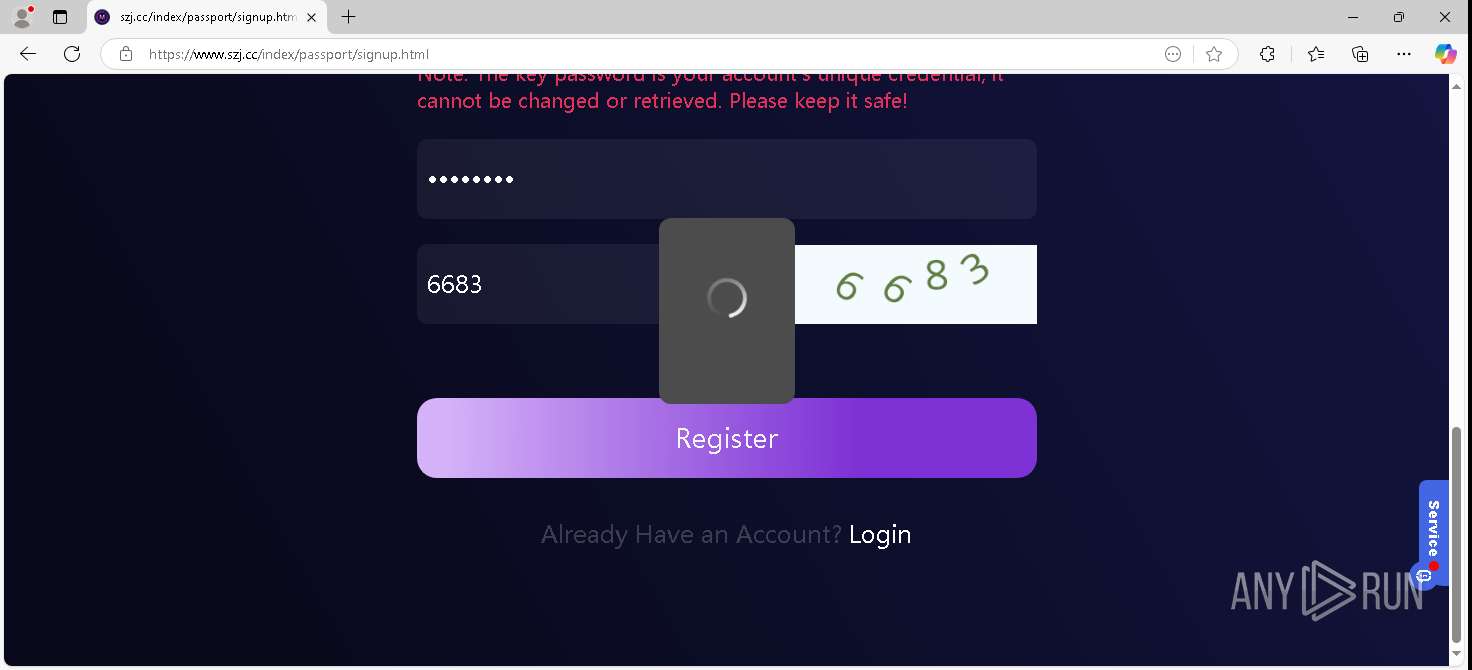
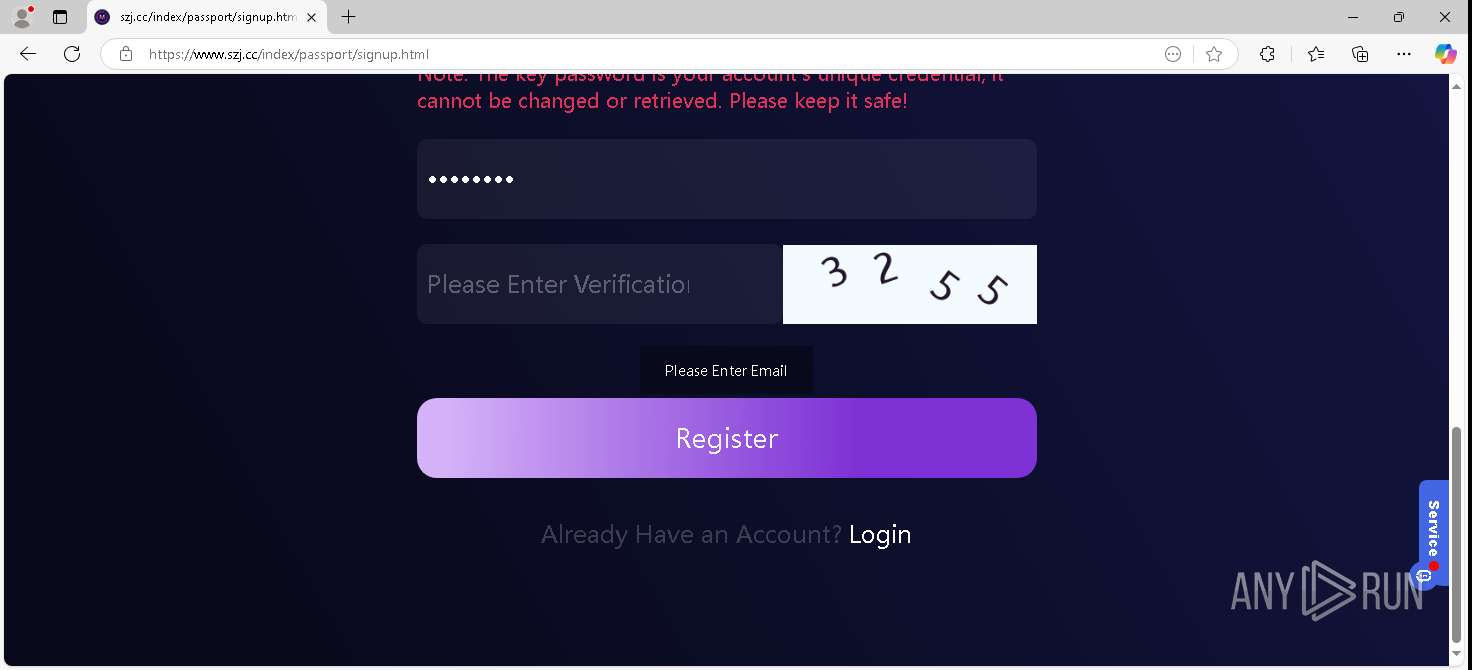
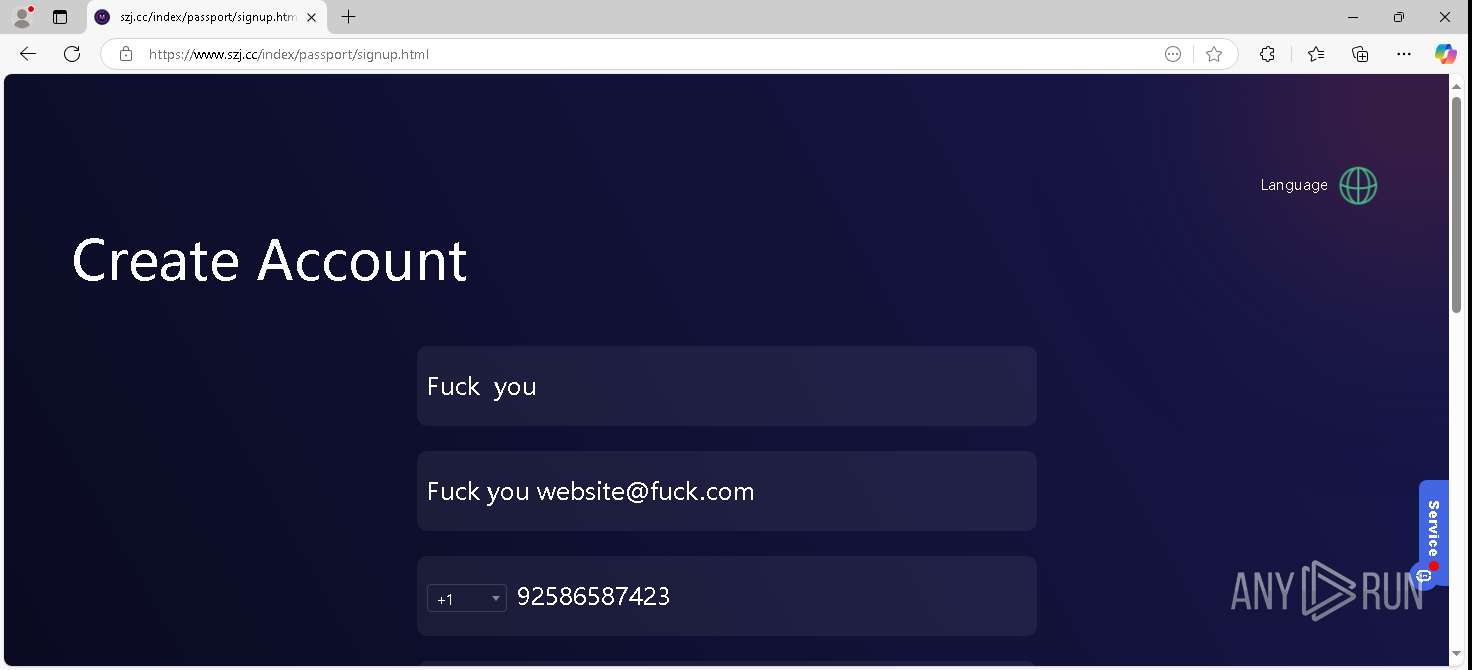
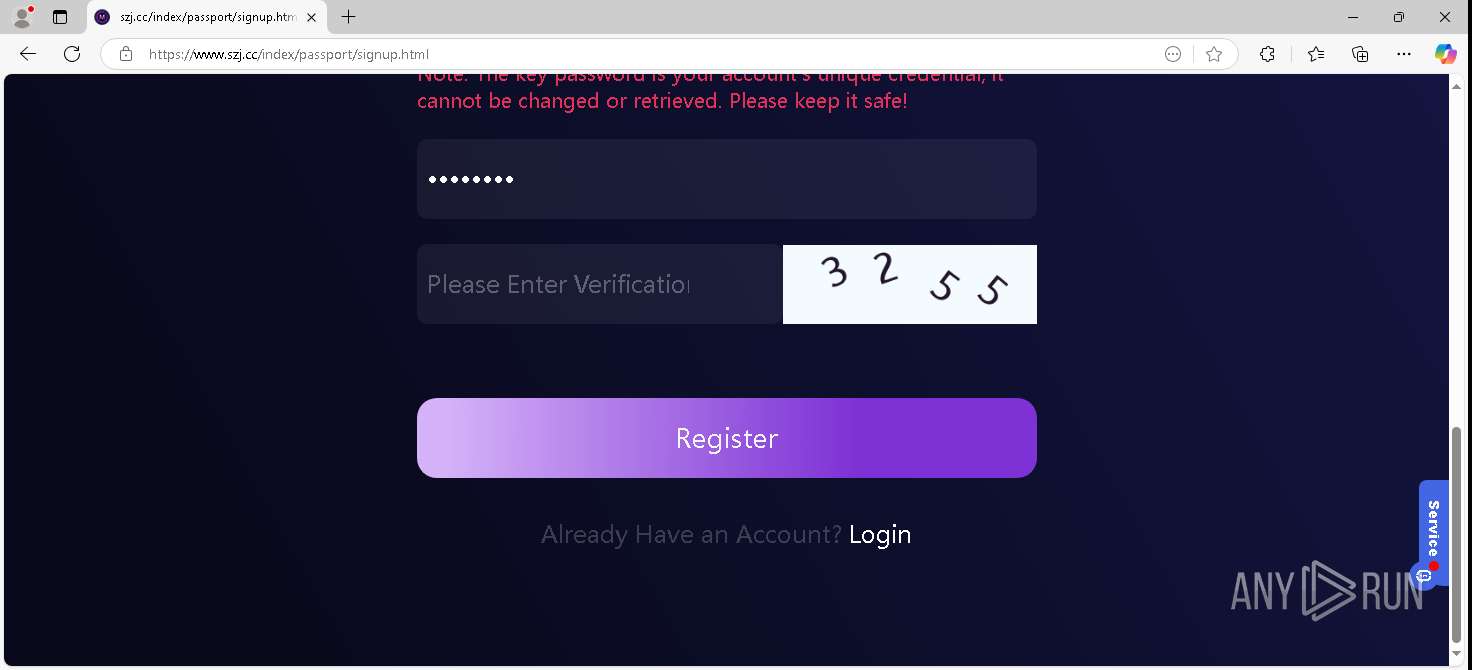
— | — | Possible Social Engineering Attempted | ET PHISHING Generic Crypto Phish Landing Page M2 2026-02-05 |
6240 | RUXIMICS.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Possible Social Engineering Attempted | ET PHISHING Successful Generic Crypto Phish Exfil M2 2026-02-05 |
— | — | Possible Social Engineering Attempted | ET PHISHING Successful Generic Crypto Phish Exfil M2 2026-02-05 |
— | — | Possible Social Engineering Attempted | ET PHISHING Successful Generic Crypto Phish Exfil M2 2026-02-05 |
— | — | Possible Social Engineering Attempted | ET PHISHING Successful Generic Crypto Phish Exfil M2 2026-02-05 |
— | — | Possible Social Engineering Attempted | ET PHISHING Successful Generic Crypto Phish Exfil M2 2026-02-05 |