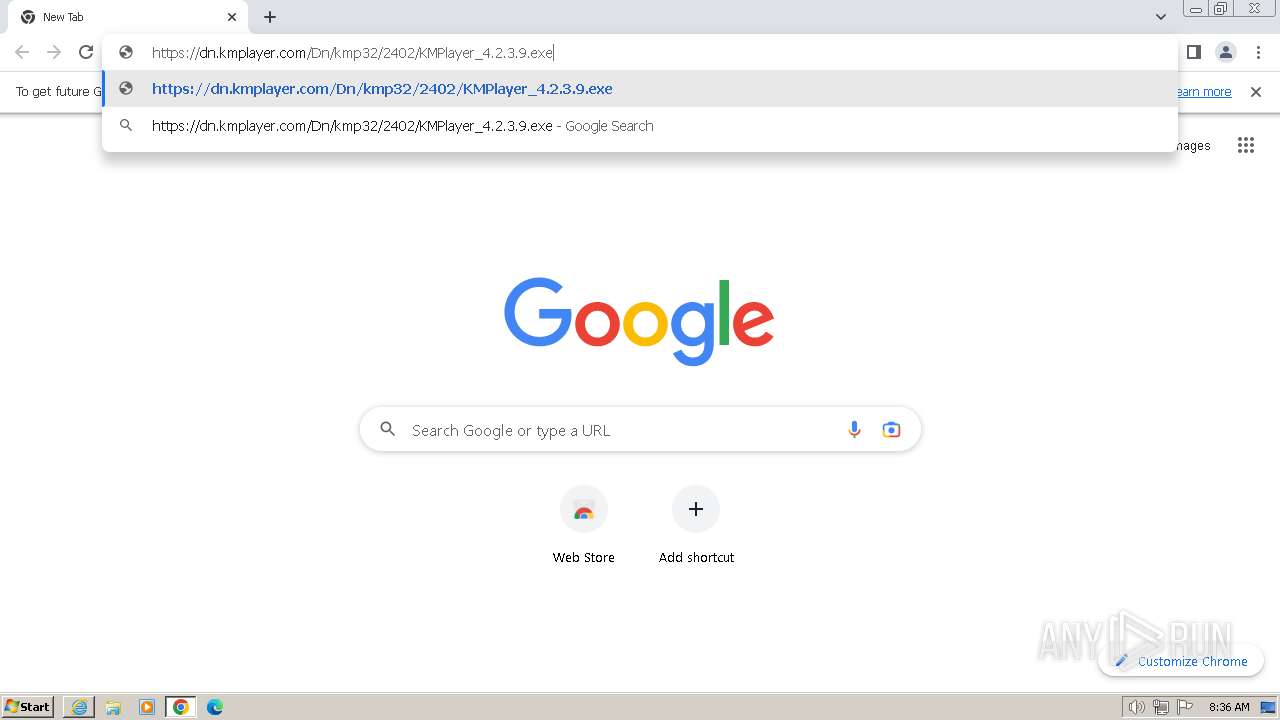
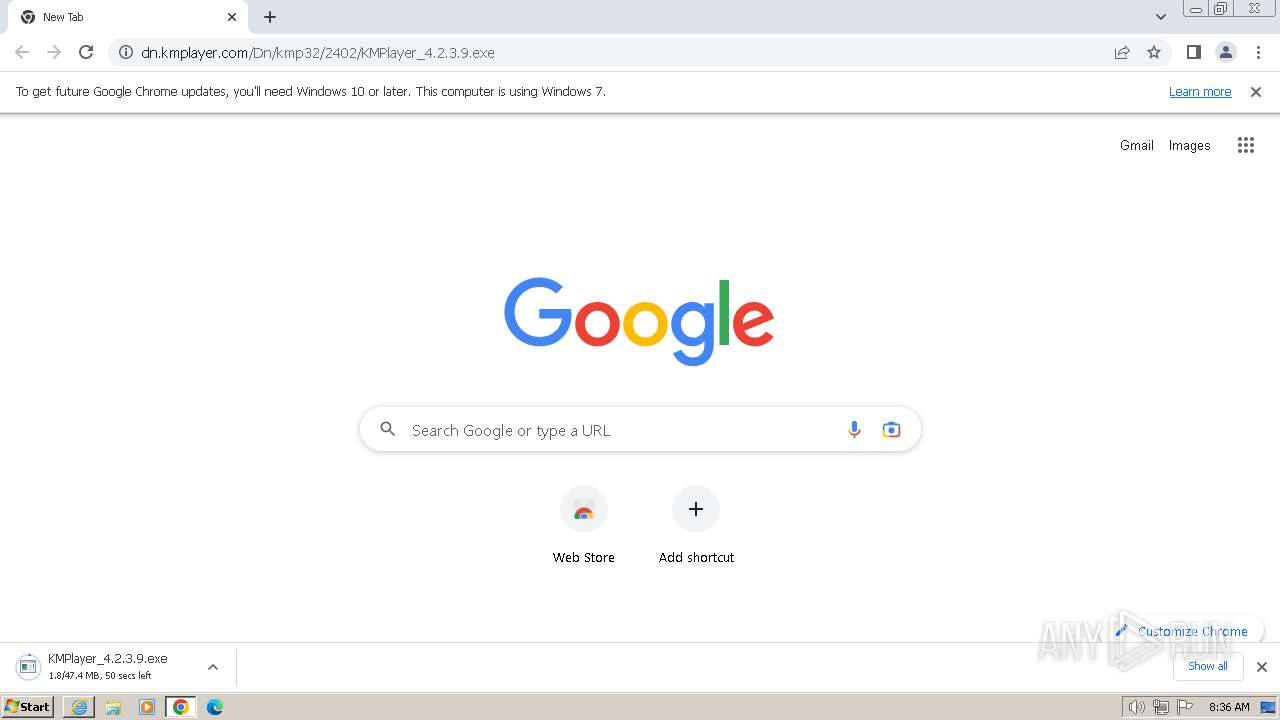
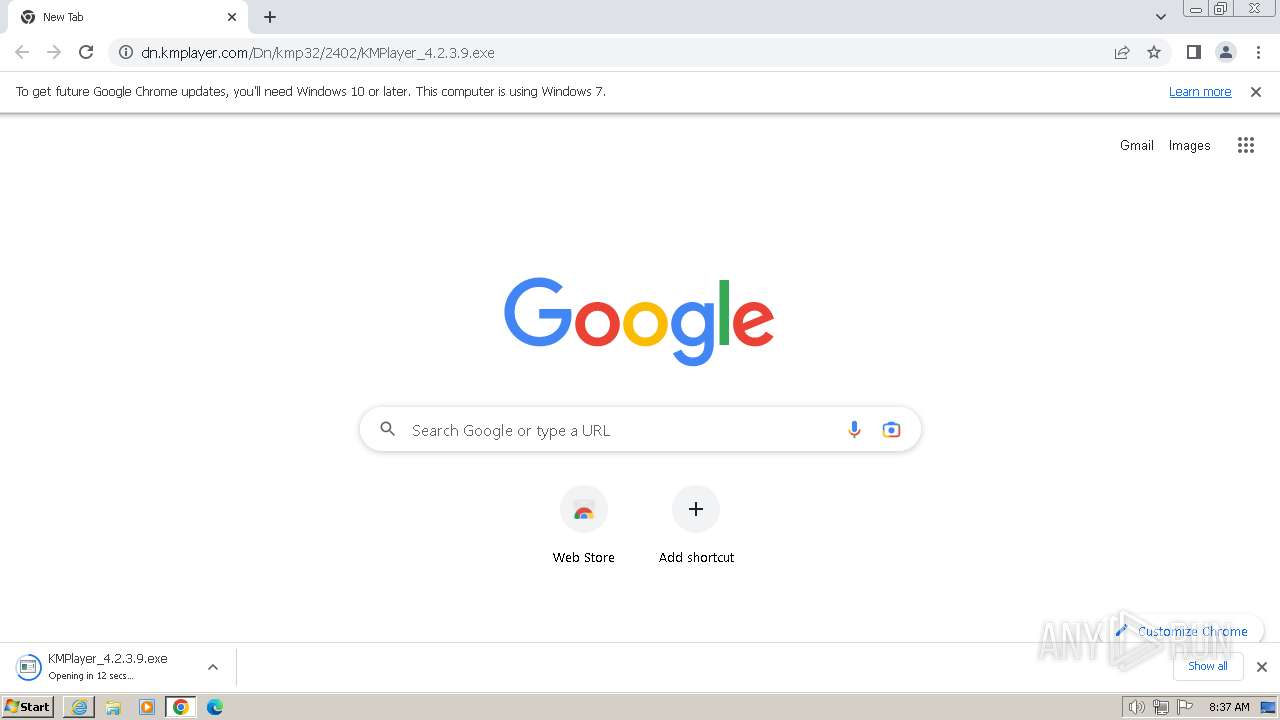
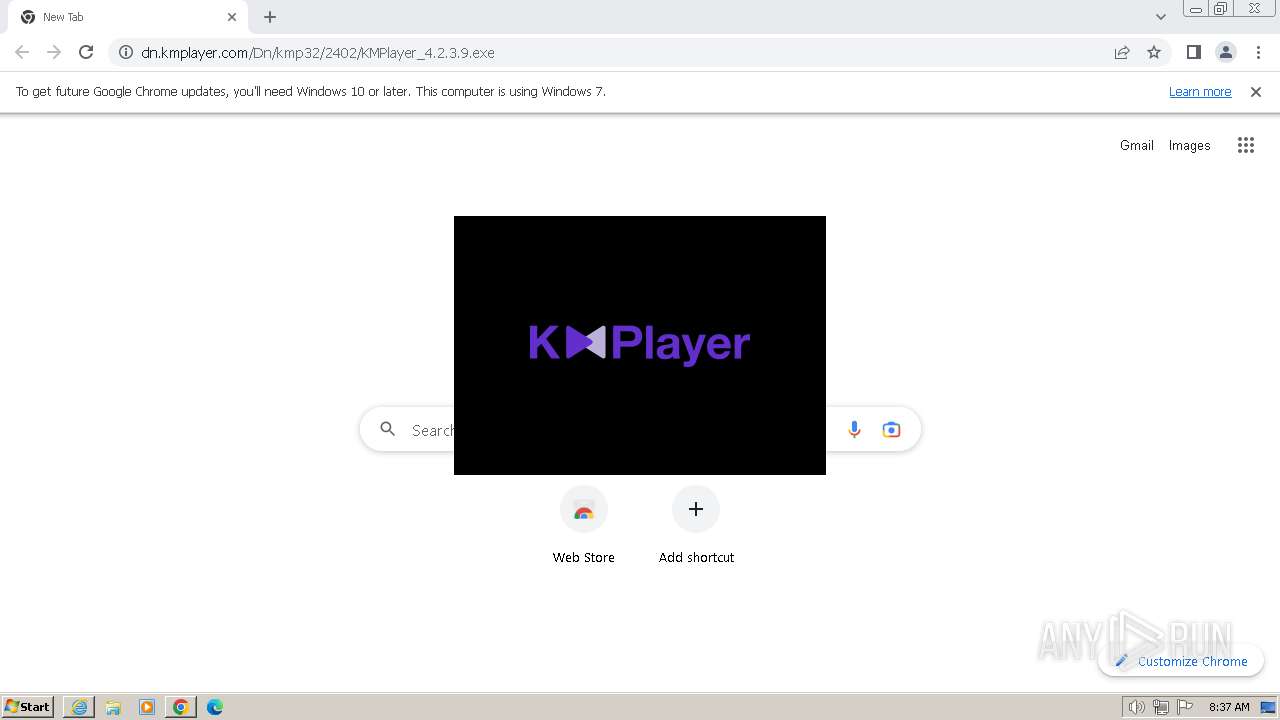
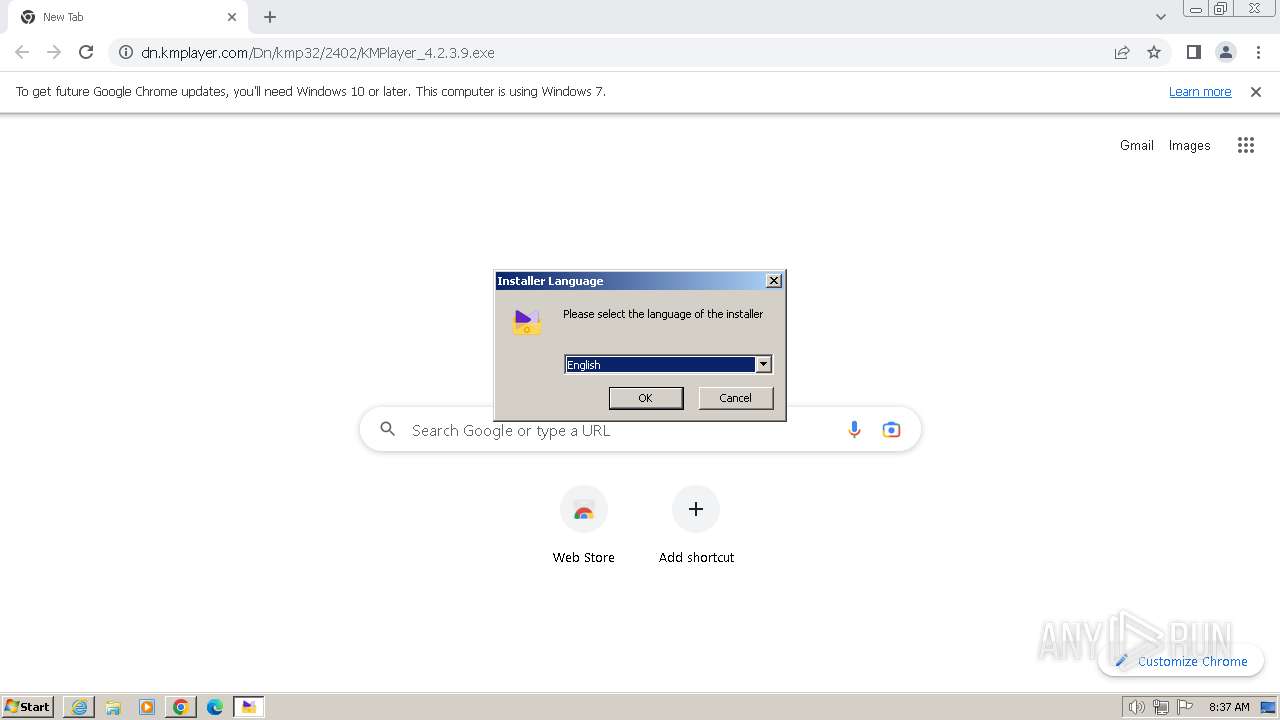
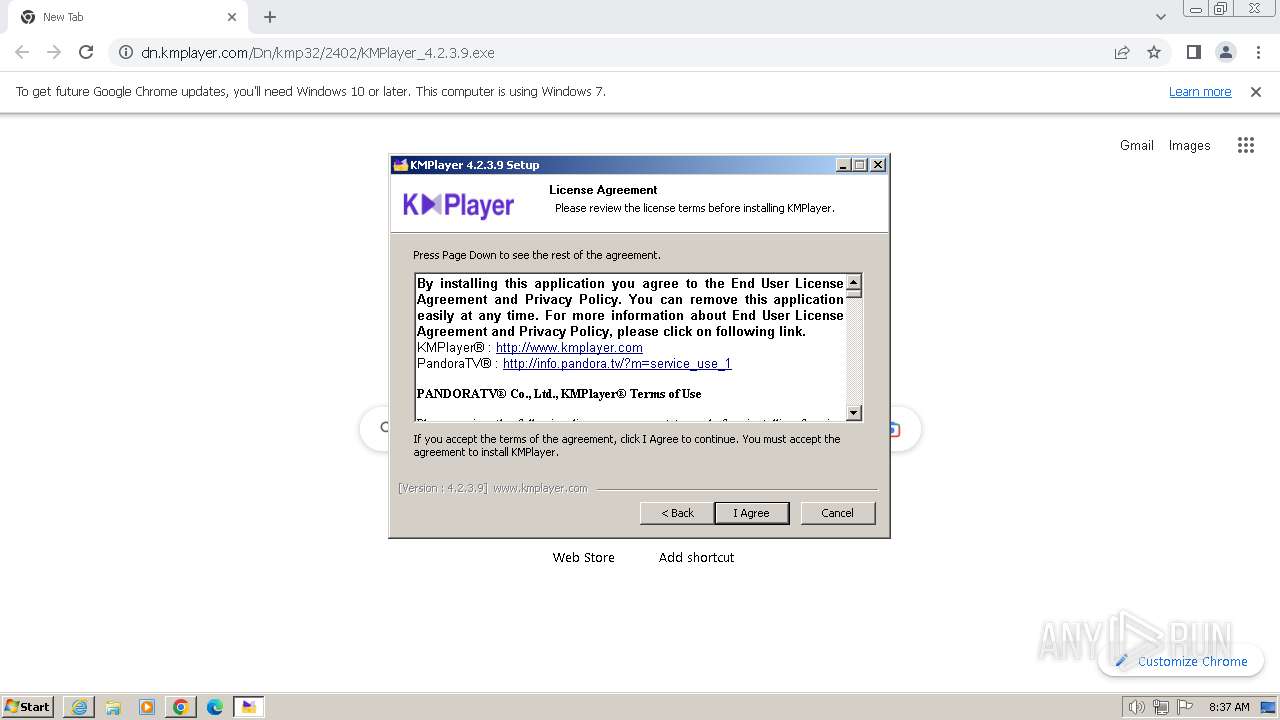
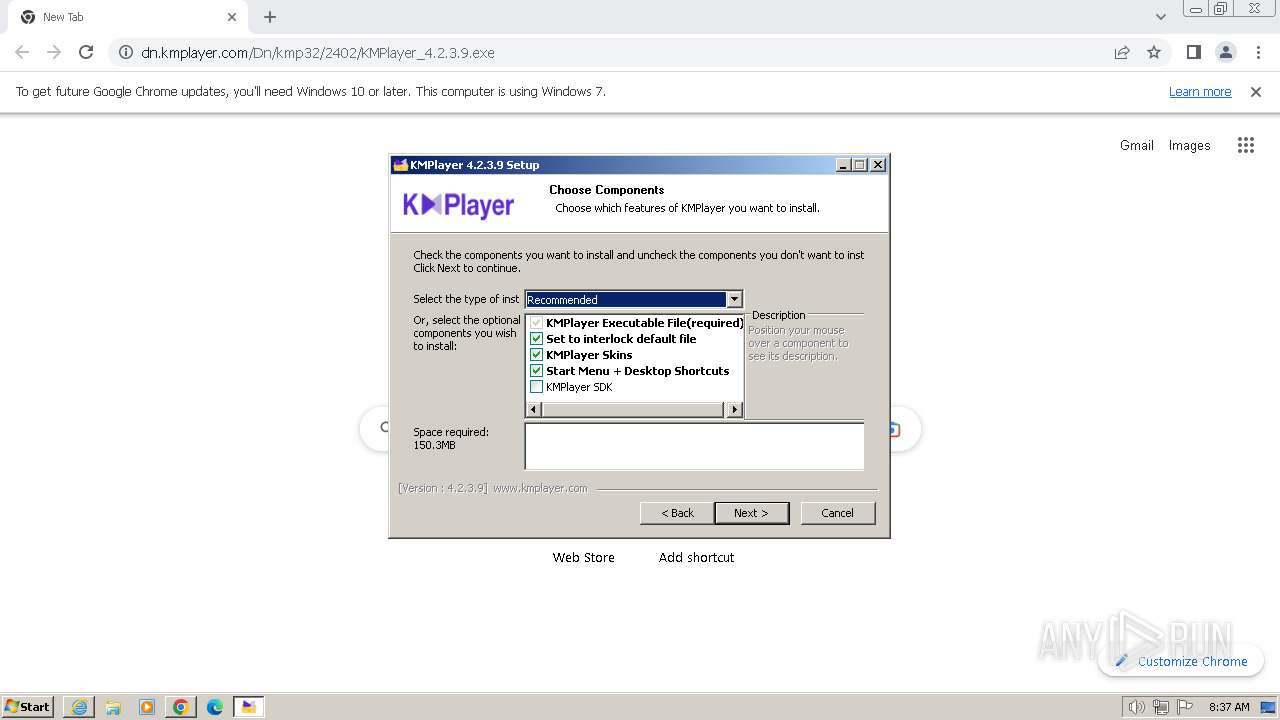
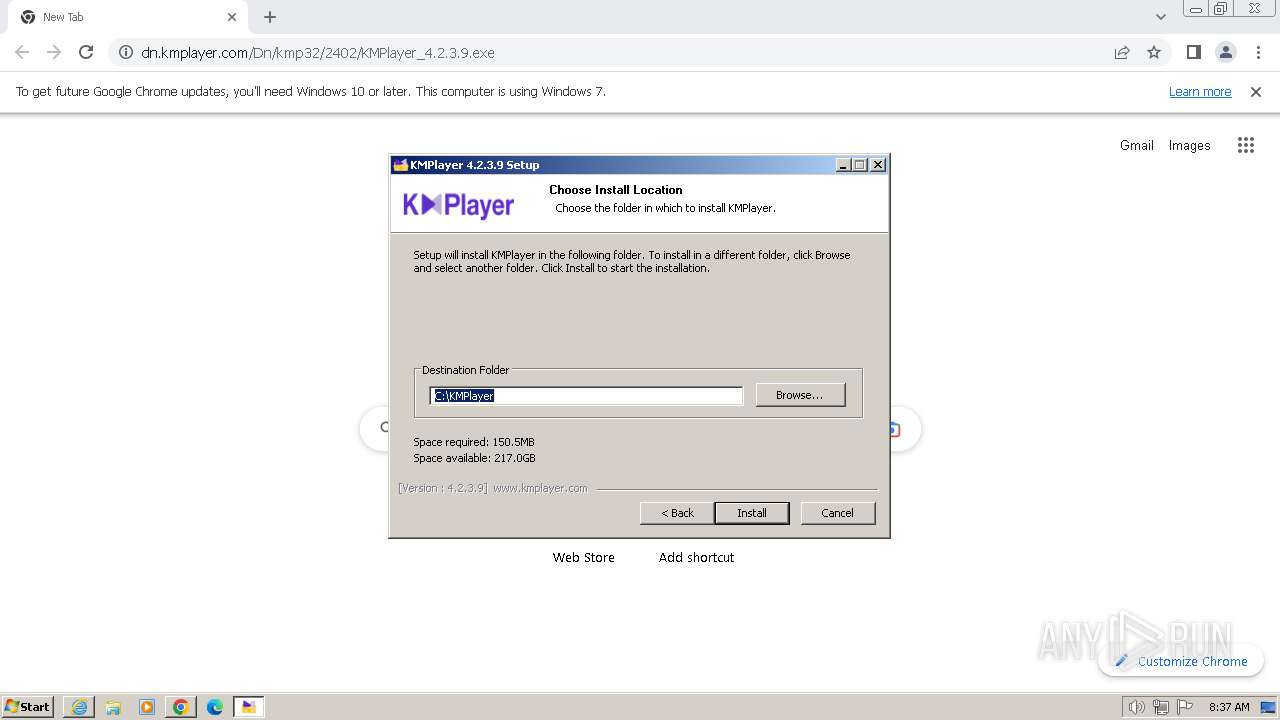
| URL: | https://dn.kmplayer.com/Dn/kmp32/2402/KMPlayer_4.2.3.9.exe |
| Full analysis: | https://app.any.run/tasks/46330f3f-650d-499e-88d8-ab951e1eeaa2 |
| Verdict: | Malicious activity |
| Threats: | Metamorfo is a trojan malware family that has been active since 2018. It remains a top threat, focusing on stealing victims’ financial information, including banking credentials and other data. The malware is known for targeting users in Brazil. |
| Analysis date: | February 23, 2024, 08:36:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E3CA632F0FD3C19A7B80DA973563385D |
| SHA1: | BEB4D1E1A0D3D6C630FFA4309A5285CDAF1931DE |
| SHA256: | 3478D786249DA2BB7BD29C821350D37C75AB716F85DE5FCB0F3778544ACCB09E |
| SSDEEP: | 3:N8TnExbH+OIVQAauoKxqtXLMO:2DKbeOIG6xwYO |
MALICIOUS
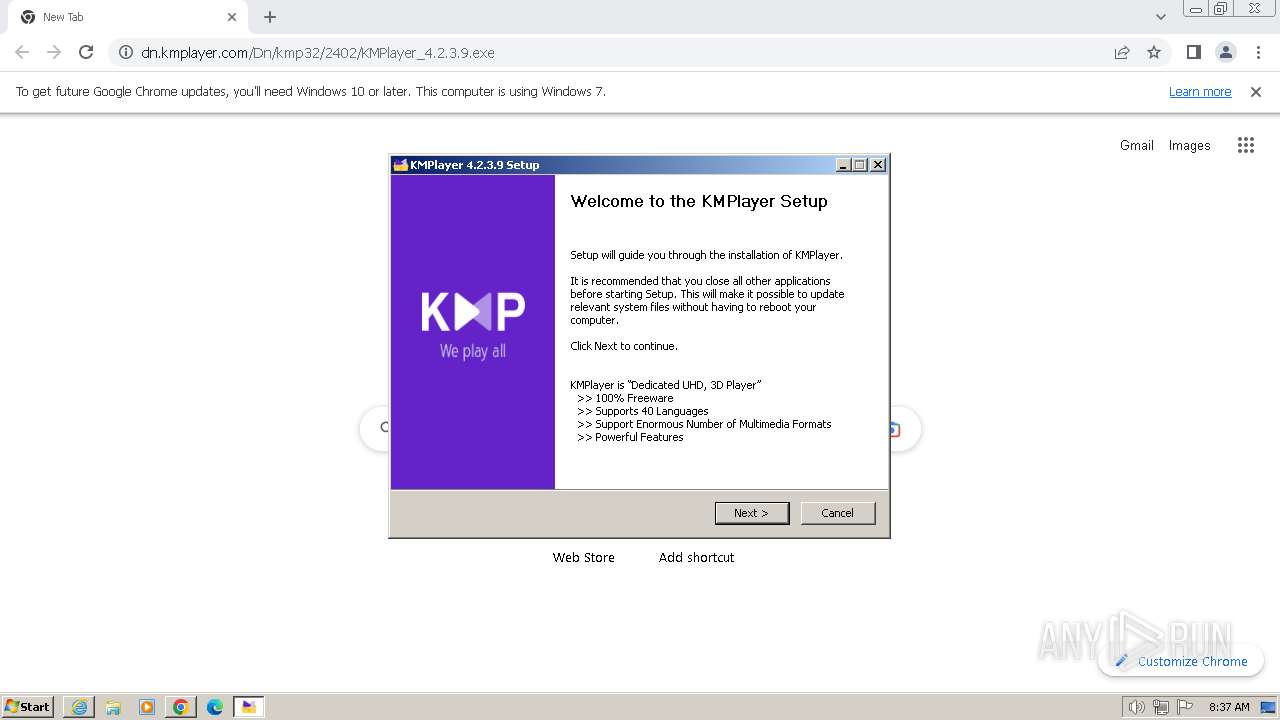
METAMORFO has been detected (YARA)
- KMPlayer.exe (PID: 1652)
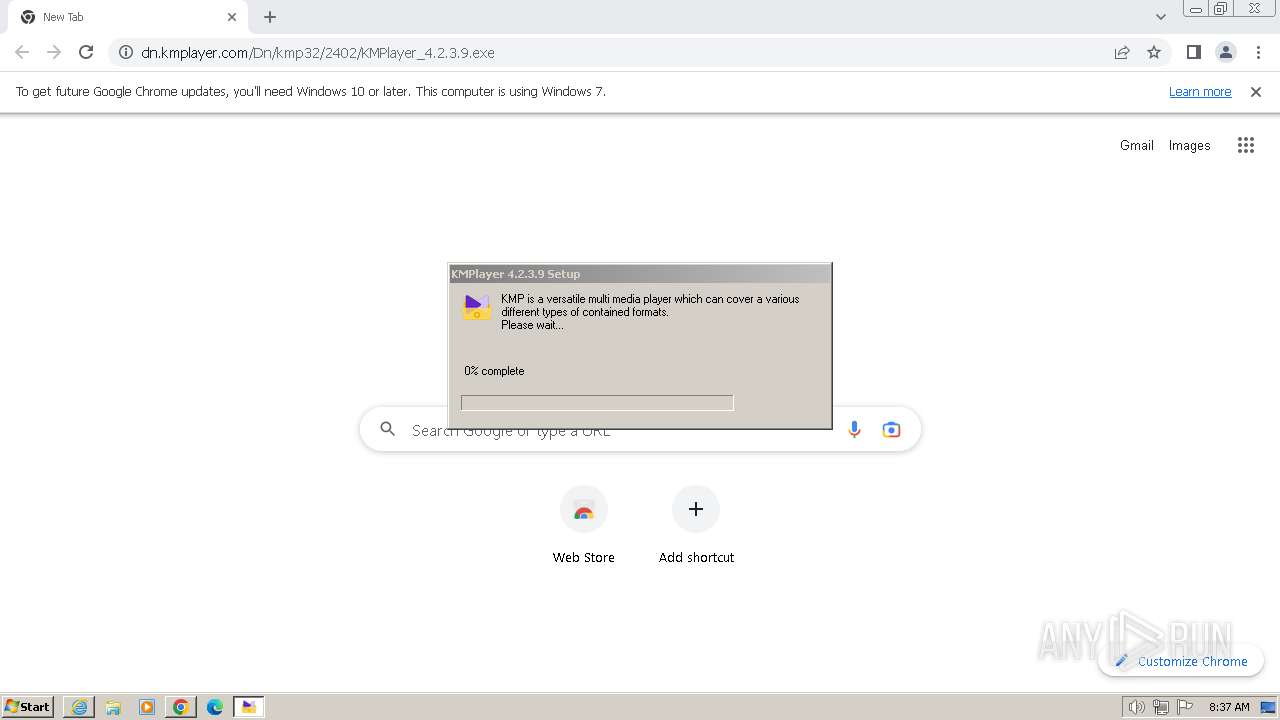
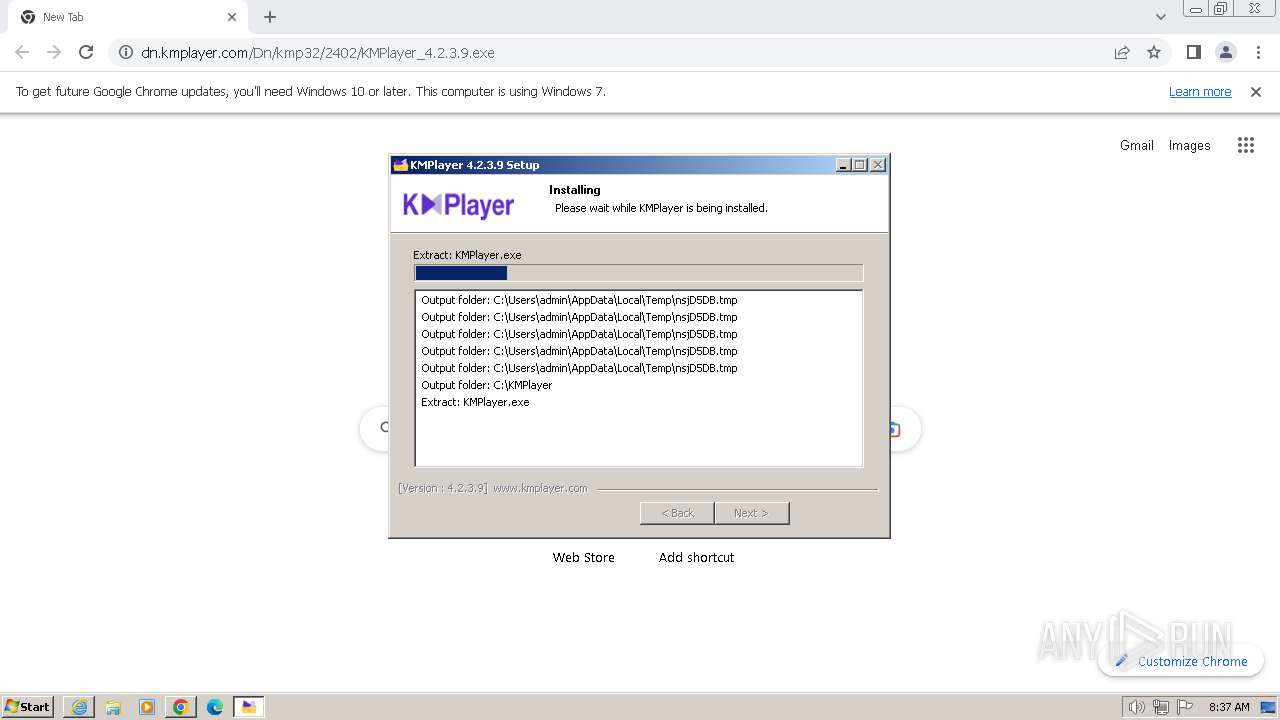
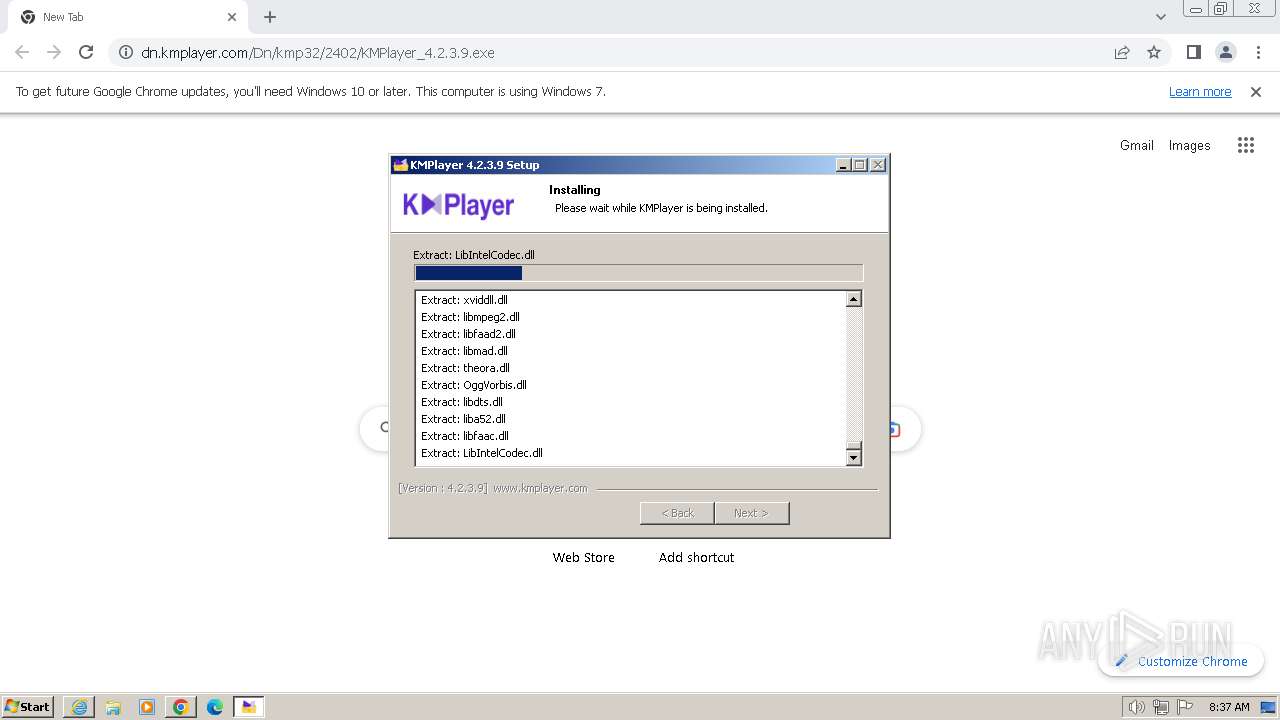
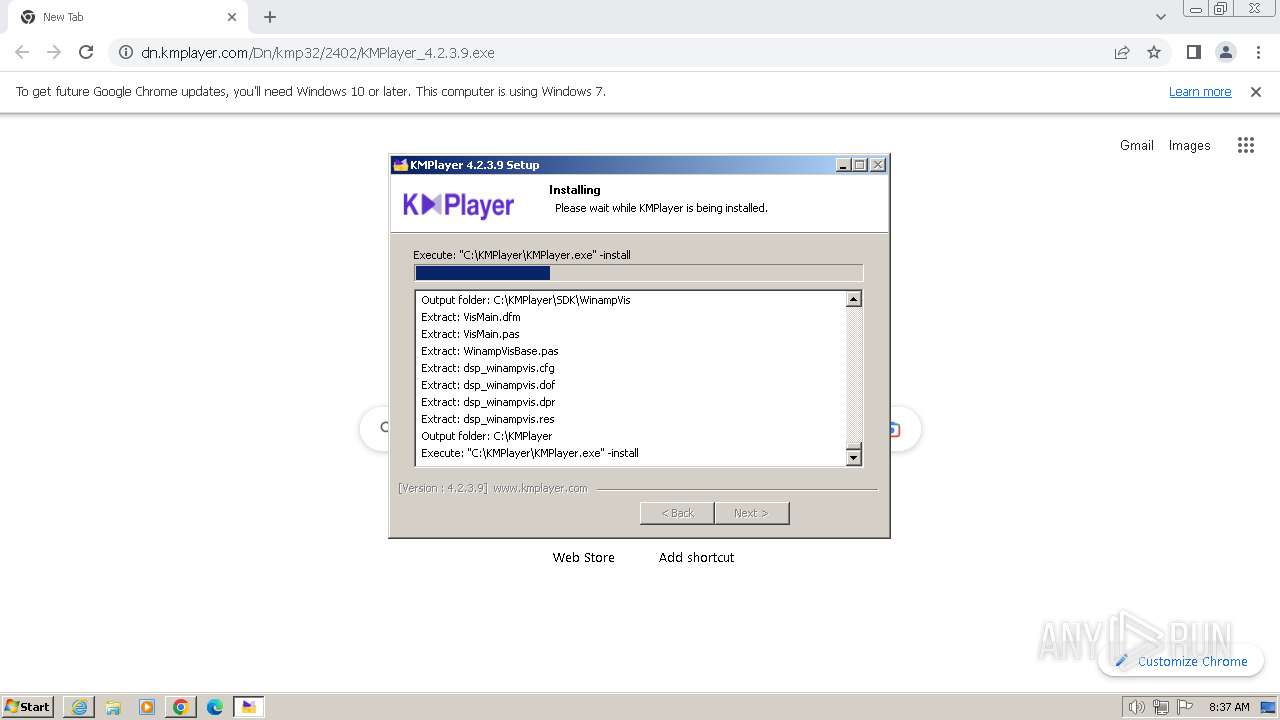
Drops the executable file immediately after the start
- KMPlayer_4.2.3.9.exe (PID: 1388)
SUSPICIOUS
Reads security settings of Internet Explorer
- KMPlayer_4.2.3.9.exe (PID: 1388)
- KMPlayer.exe (PID: 1652)
Drops 7-zip archiver for unpacking
- KMPlayer_4.2.3.9.exe (PID: 1388)
Process drops legitimate windows executable
- KMPlayer_4.2.3.9.exe (PID: 1388)
Searches for installed software
- KMPlayer_4.2.3.9.exe (PID: 1388)
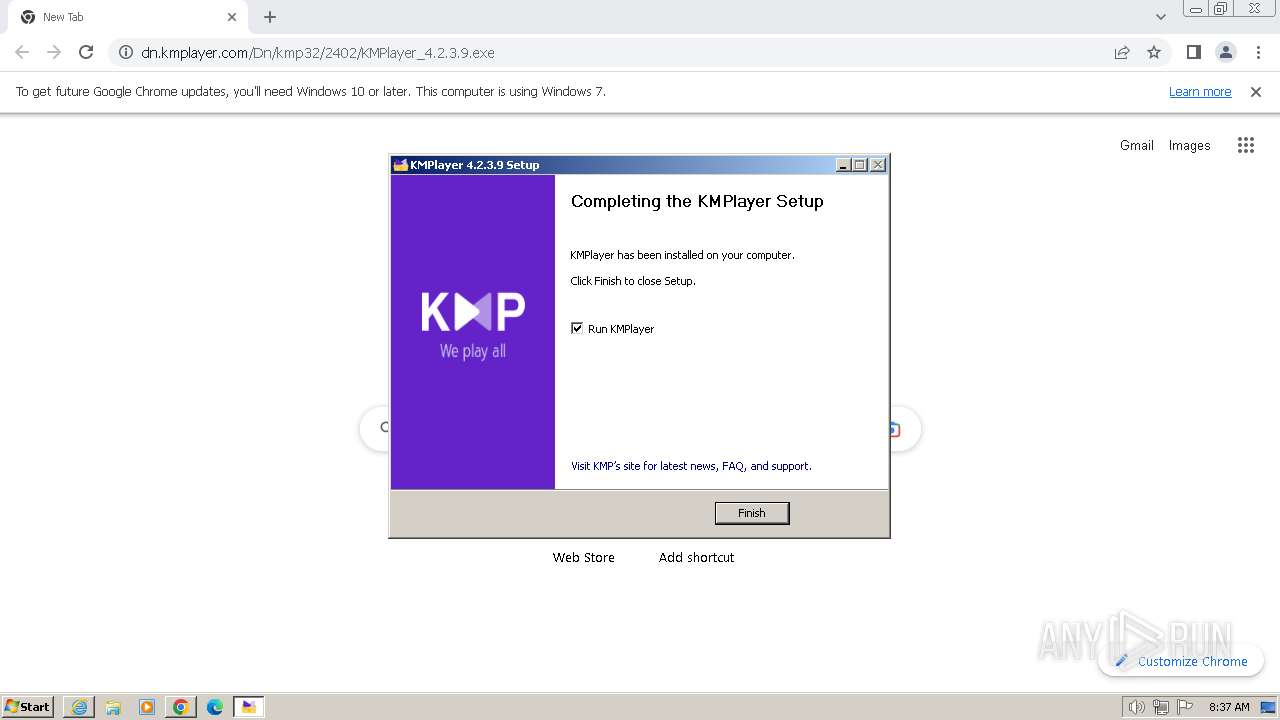
Creates a software uninstall entry
- KMPlayer_4.2.3.9.exe (PID: 1388)
Creates/Modifies COM task schedule object
- KMPlayer_4.2.3.9.exe (PID: 1388)
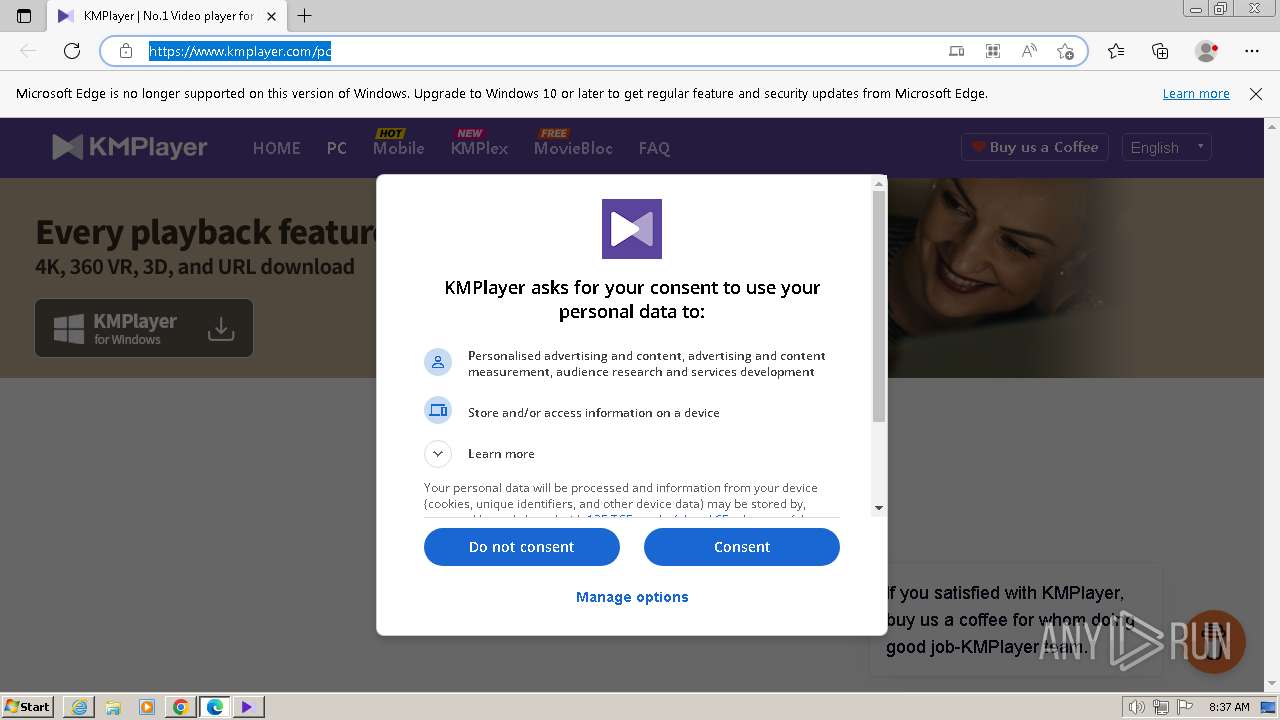
Changes Internet Explorer settings (feature browser emulation)
- KMPlayer_4.2.3.9.exe (PID: 1388)
- KMPlayer.exe (PID: 296)
Reads the Internet Settings
- KMPlayer.exe (PID: 1652)
- KMPlayer_4.2.3.9.exe (PID: 1388)
Reads Microsoft Outlook installation path
- KMPlayer.exe (PID: 1652)
Reads Internet Explorer settings
- KMPlayer.exe (PID: 1652)
Malware-specific behavior (creating "System.dll" in Temp)
- KMPlayer_4.2.3.9.exe (PID: 1388)
The process creates files with name similar to system file names
- KMPlayer_4.2.3.9.exe (PID: 1388)
Executable content was dropped or overwritten
- KMPlayer_4.2.3.9.exe (PID: 1388)
INFO
Application launched itself
- iexplore.exe (PID: 3864)
- chrome.exe (PID: 2292)
- msedge.exe (PID: 4092)
- msedge.exe (PID: 3376)
- msedge.exe (PID: 2856)
Reads Environment values
- KMPlayer_4.2.3.9.exe (PID: 1388)
Creates files or folders in the user directory
- KMPlayer_4.2.3.9.exe (PID: 1388)
- KMPlayer.exe (PID: 1652)
Checks proxy server information
- KMPlayer_4.2.3.9.exe (PID: 1388)
- KMPlayer.exe (PID: 1652)
Manual execution by a user
- chrome.exe (PID: 2292)
- msedge.exe (PID: 3376)
Reads the computer name
- KMPlayer_4.2.3.9.exe (PID: 1388)
- KMPlayer.exe (PID: 296)
- kmpFileAssociate_NO.exe (PID: 2468)
- kmpFileAssociate_NO.exe (PID: 2828)
- kmpFileAssociate.exe (PID: 1392)
- kmpFileAssociate.exe (PID: 2416)
- KMPlayer.exe (PID: 1652)
Drops the executable file immediately after the start
- chrome.exe (PID: 2292)
Checks supported languages
- KMPlayer_4.2.3.9.exe (PID: 1388)
- KMPlayer.exe (PID: 296)
- kmpFileAssociate.exe (PID: 1392)
- kmpFileAssociate_NO.exe (PID: 2468)
- kmpFileAssociate_NO.exe (PID: 2828)
- kmpFileAssociate.exe (PID: 2416)
- KMPlayer.exe (PID: 1652)
Executable content was dropped or overwritten
- chrome.exe (PID: 2292)
The process uses the downloaded file
- chrome.exe (PID: 3376)
- chrome.exe (PID: 2292)
Create files in a temporary directory
- KMPlayer_4.2.3.9.exe (PID: 1388)
- KMPlayer.exe (PID: 1652)
Reads the machine GUID from the registry
- KMPlayer.exe (PID: 1652)
- KMPlayer_4.2.3.9.exe (PID: 1388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
114
Monitored processes
71
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3728 --field-trial-handle=1028,i,9218314181070019102,2692225484045606753,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 296 | "C:\KMPlayer\KMPlayer.exe" -install | C:\KMPlayer\KMPlayer.exe | — | KMPlayer_4.2.3.9.exe | |||||||||||
User: admin Company: PandoraTV Integrity Level: HIGH Description: KMPlayer Exit code: 0 Version: 4.2.3.9 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1856 --field-trial-handle=1028,i,9218314181070019102,2692225484045606753,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3500 --field-trial-handle=1028,i,9218314181070019102,2692225484045606753,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 560 | "C:\Users\admin\Downloads\KMPlayer_4.2.3.9.exe" | C:\Users\admin\Downloads\KMPlayer_4.2.3.9.exe | — | chrome.exe | |||||||||||
User: admin Company: PandoraTV Integrity Level: MEDIUM Description: KMPlayer_Setup/Install_cdn Exit code: 3221226540 Version: 4.2.3.9 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0x120,0x6973f598,0x6973f5a8,0x6973f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4104 --field-trial-handle=1280,i,15627274738097694853,18209689062202057392,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3788 --field-trial-handle=1028,i,9218314181070019102,2692225484045606753,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3996 --field-trial-handle=1028,i,9218314181070019102,2692225484045606753,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3688 --field-trial-handle=1280,i,15627274738097694853,18209689062202057392,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
42 949
Read events
39 322
Write events
3 176
Delete events
451
Modification events
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31090227 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31090227 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3864) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
86
Suspicious files
197
Text files
242
Unknown types
123
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1835e0.TMP | — | |
MD5:— | SHA256:— | |||
| 2292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:9506EDEF12CED819B140A632021342E6 | SHA256:752CB696E98E571826F4141D1B059CCC218AA2662F255AEA11004ABEA7B952F1 | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:C9E698F4208D83CB2FCF21C47316BBDD | SHA256:5B1CBD5CBDE0DCE1AE75216A75EE6ED44E4954787E7AEF8CF3E9DD1FB9664DAE | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:DAB9CE5CE10CC2A00A62EAEB4AA8C499 | SHA256:30402AF5D847124A51E01D0B385F00331FC2C290263423179D5B8C3FF3C1F290 | |||
| 2292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2292 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
181
DNS requests
199
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3864 | iexplore.exe | GET | 304 | 23.32.238.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4dd617501e33218a | unknown | — | — | unknown |
3864 | iexplore.exe | GET | 304 | 23.32.238.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?bdc5ae628aaf0bd4 | unknown | — | — | unknown |
3864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
1080 | svchost.exe | GET | 304 | 23.32.238.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fc91d912a85a08d5 | unknown | compressed | 65.2 Kb | unknown |
3864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 200 | 23.32.238.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?624d1ab720bef5f8 | unknown | compressed | 65.2 Kb | unknown |
1388 | KMPlayer_4.2.3.9.exe | GET | 302 | 34.160.229.38:80 | http://update.kmpmedia.net/player/ini_goods/1/0?dummy=754 | unknown | — | — | unknown |
1388 | KMPlayer_4.2.3.9.exe | GET | 302 | 34.160.229.38:80 | http://update.kmpmedia.net/player/ini_goods/1/1 | unknown | — | — | unknown |
1388 | KMPlayer_4.2.3.9.exe | GET | 200 | 163.171.132.42:80 | http://cdn.kmplayer.com/KMP/player/ini/goods/old_00_unicode_20200207102938.7z | unknown | compressed | 4.73 Kb | unknown |
3864 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3692 | iexplore.exe | 18.245.46.62:443 | dn.kmplayer.com | — | US | unknown |
3864 | iexplore.exe | 92.123.104.26:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3864 | iexplore.exe | 23.32.238.240:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3864 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2156 | chrome.exe | 172.217.169.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2292 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
2156 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dn.kmplayer.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1388 | KMPlayer_4.2.3.9.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1388 | KMPlayer_4.2.3.9.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1388 | KMPlayer_4.2.3.9.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
1388 | KMPlayer_4.2.3.9.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2948 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |