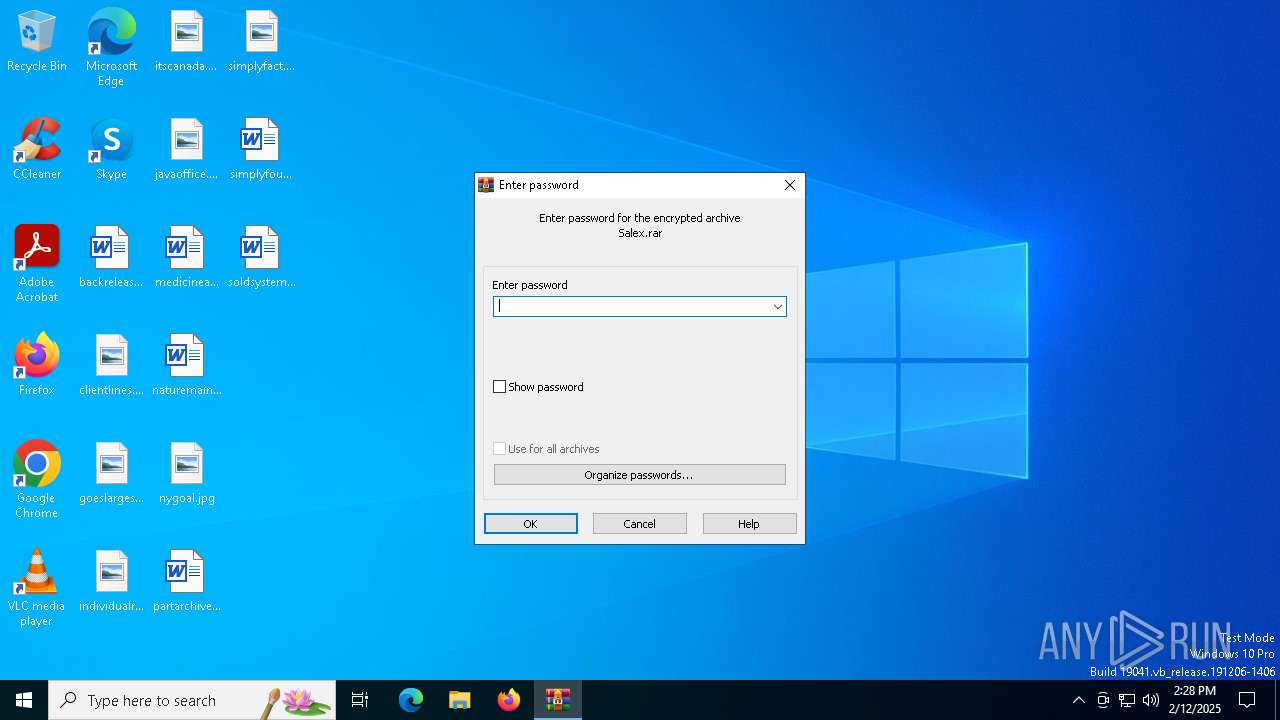
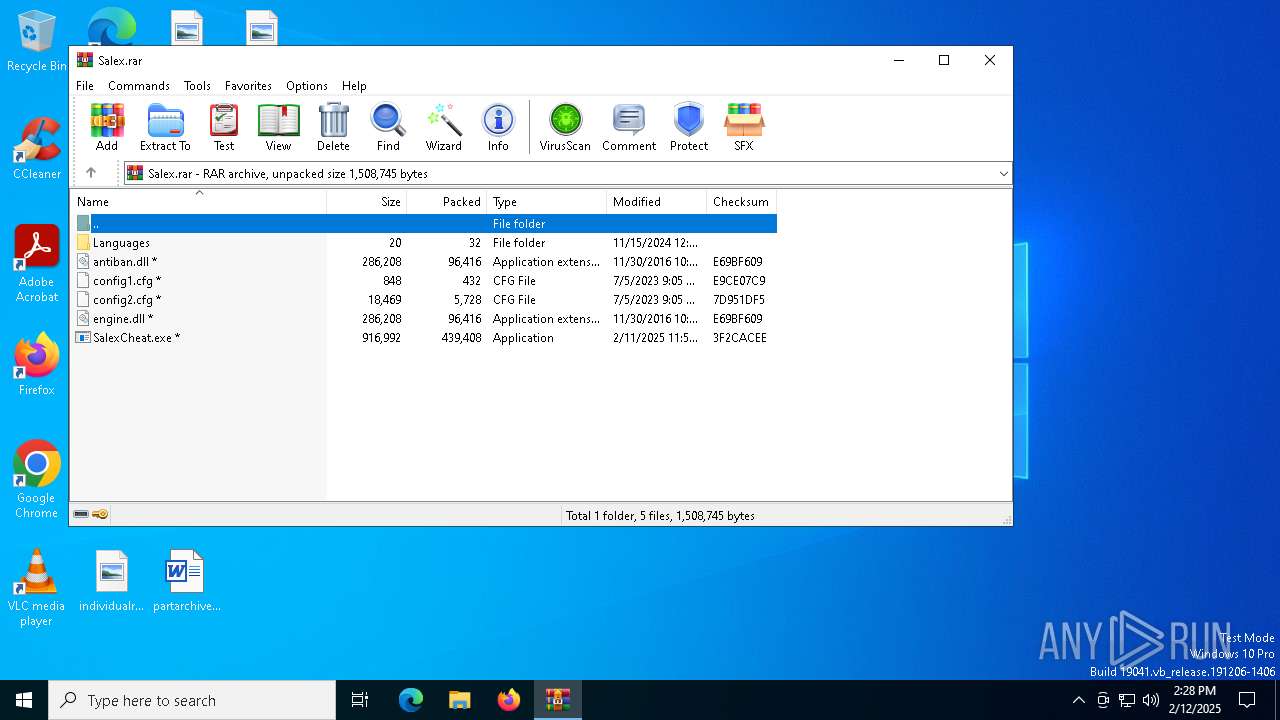
| File name: | Salex.rar |
| Full analysis: | https://app.any.run/tasks/542344e0-324e-499d-ab55-655676aaf952 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 12, 2025, 14:28:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
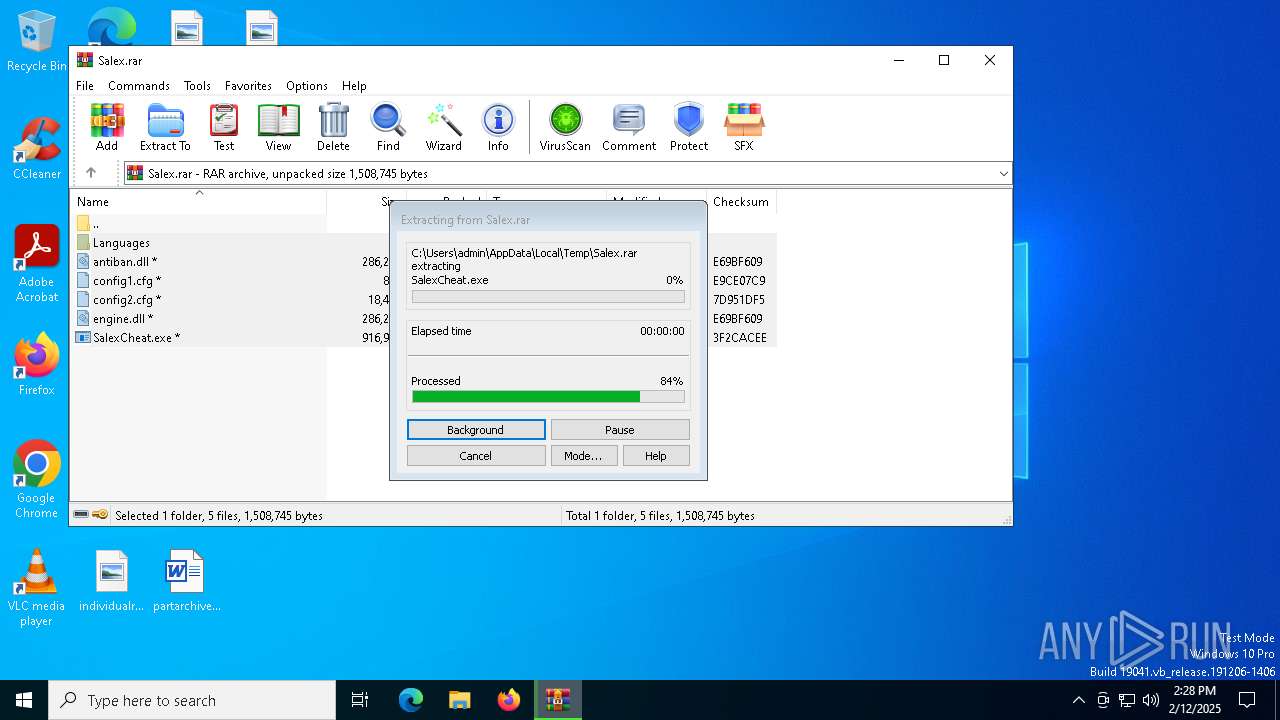
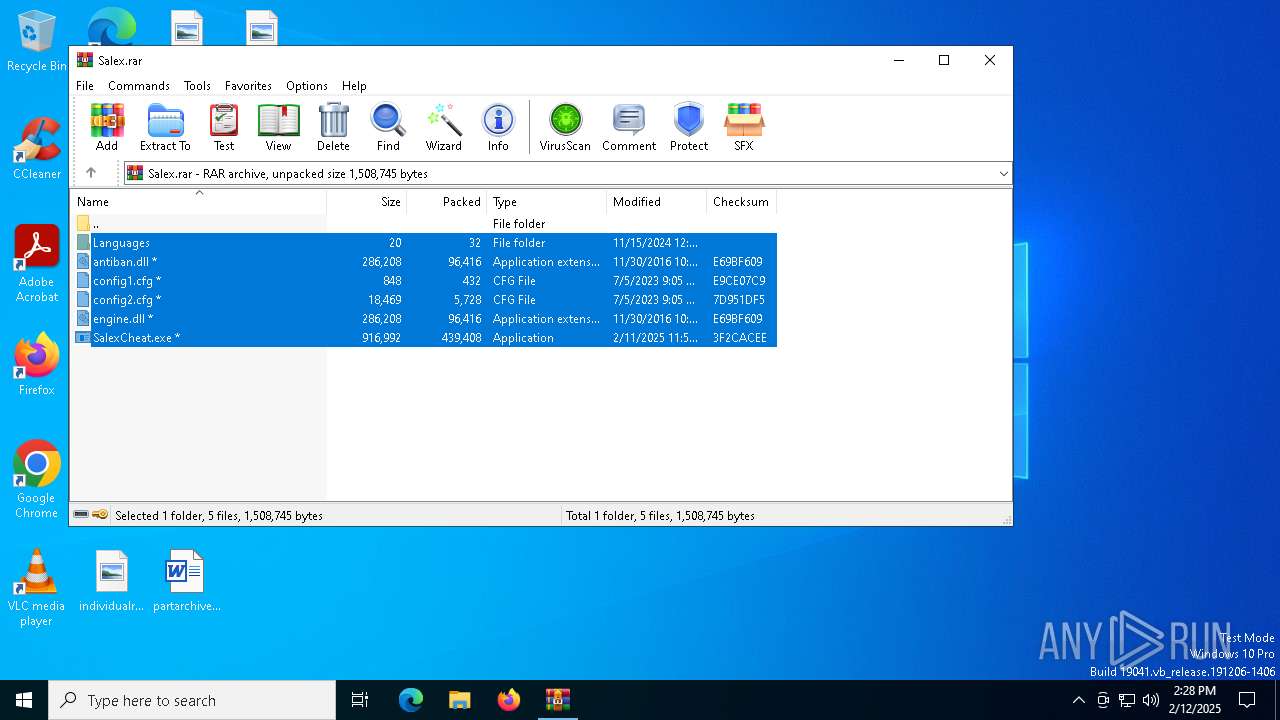
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 66F49C6D38689230FEA645B88125C4E4 |
| SHA1: | 9EF35700B7E41BEBDCB090416D10BB3592C38343 |
| SHA256: | 33CDE94F323D214B49AACB97845E70138142EBDBB944D44097315E6943C1891F |
| SSDEEP: | 24576:8LSlm1aN5w1LfxE9lQbznqNM3aE6GwzbXIrdUHN6lIBhO0Emm5X5:8LSlm1aN5w1DxE9lQbznqW3aEPwzbXS5 |
MALICIOUS
Connects to the CnC server
- svchost.exe (PID: 2192)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- SalexCheat.exe (PID: 3420)
- SalexCheat.exe (PID: 1904)
- SalexCheat.exe (PID: 6416)
- SalexCheat.exe (PID: 6828)
LUMMA mutex has been found
- SalexCheat.exe (PID: 1904)
- SalexCheat.exe (PID: 6416)
- SalexCheat.exe (PID: 6828)
- SalexCheat.exe (PID: 3420)
Actions looks like stealing of personal data
- SalexCheat.exe (PID: 3420)
SUSPICIOUS
Application launched itself
- SalexCheat.exe (PID: 7024)
- SalexCheat.exe (PID: 5544)
- SalexCheat.exe (PID: 3464)
- SalexCheat.exe (PID: 7016)
Executes application which crashes
- SalexCheat.exe (PID: 7024)
- SalexCheat.exe (PID: 5544)
- SalexCheat.exe (PID: 3464)
- SalexCheat.exe (PID: 7016)
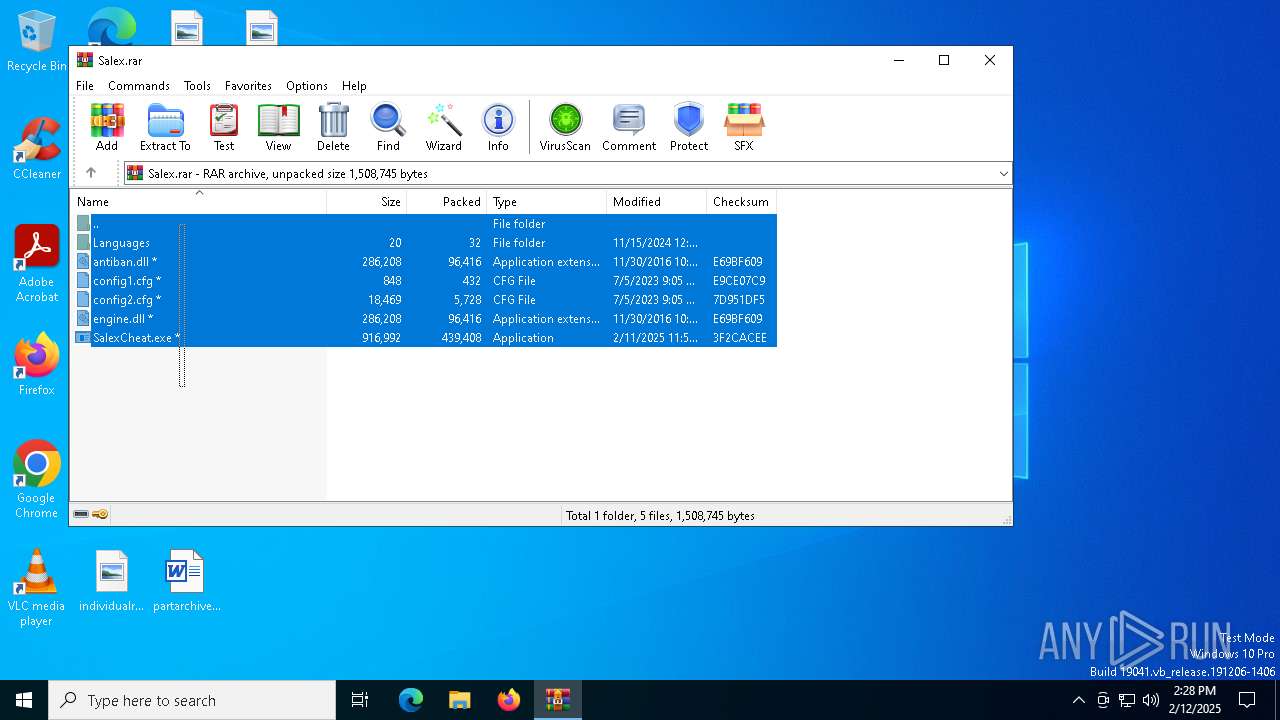
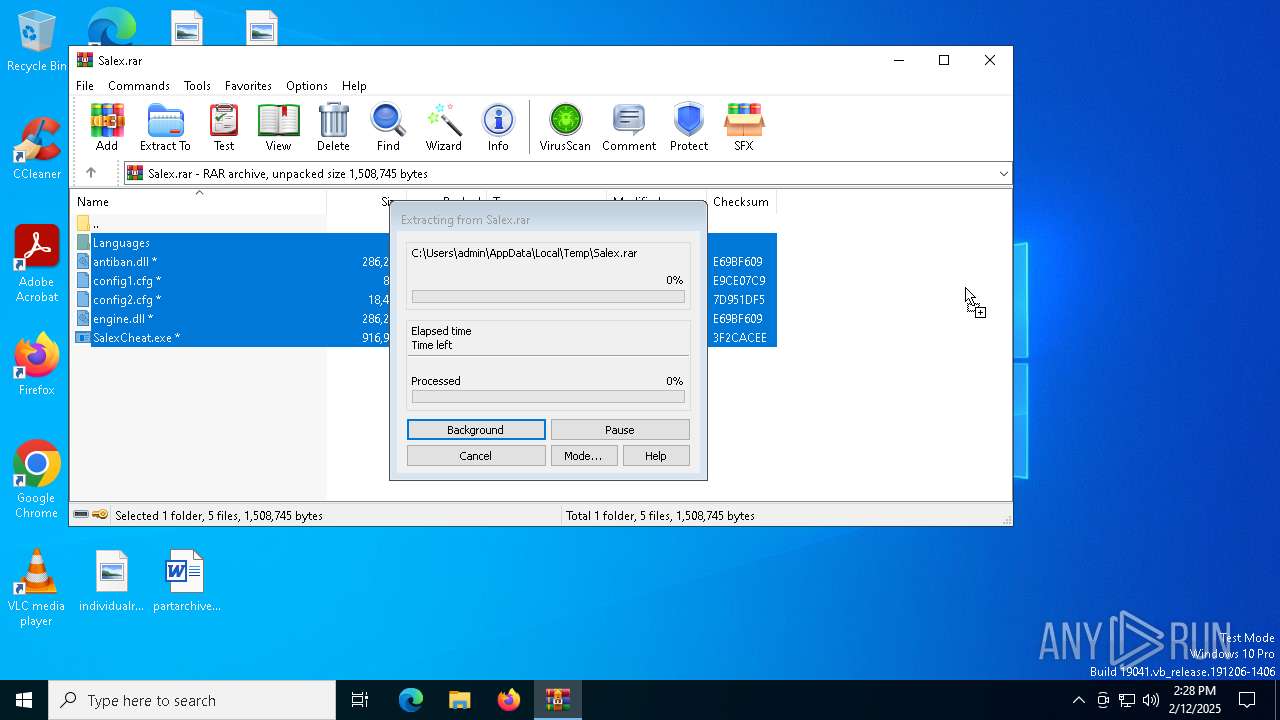
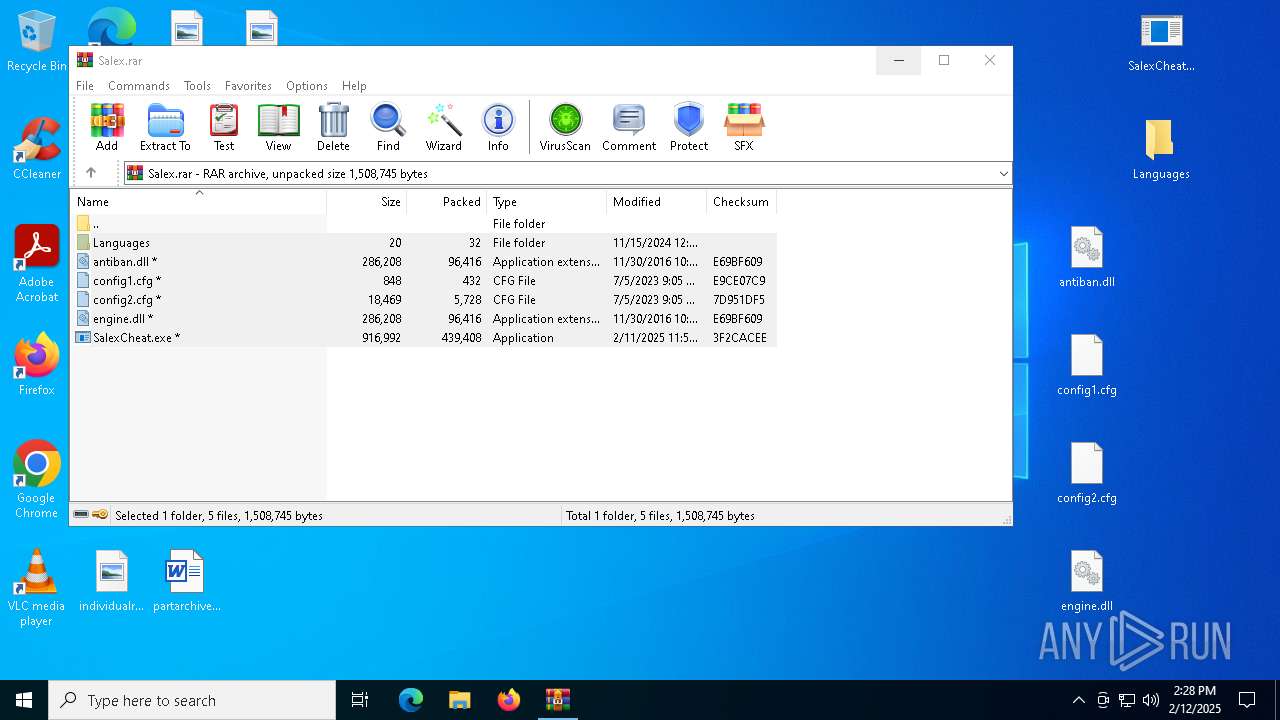
Process drops legitimate windows executable
- WinRAR.exe (PID: 3848)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2192)
- SalexCheat.exe (PID: 1904)
- SalexCheat.exe (PID: 3420)
- SalexCheat.exe (PID: 6416)
- SalexCheat.exe (PID: 6828)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3848)
The sample compiled with english language support
- WinRAR.exe (PID: 3848)
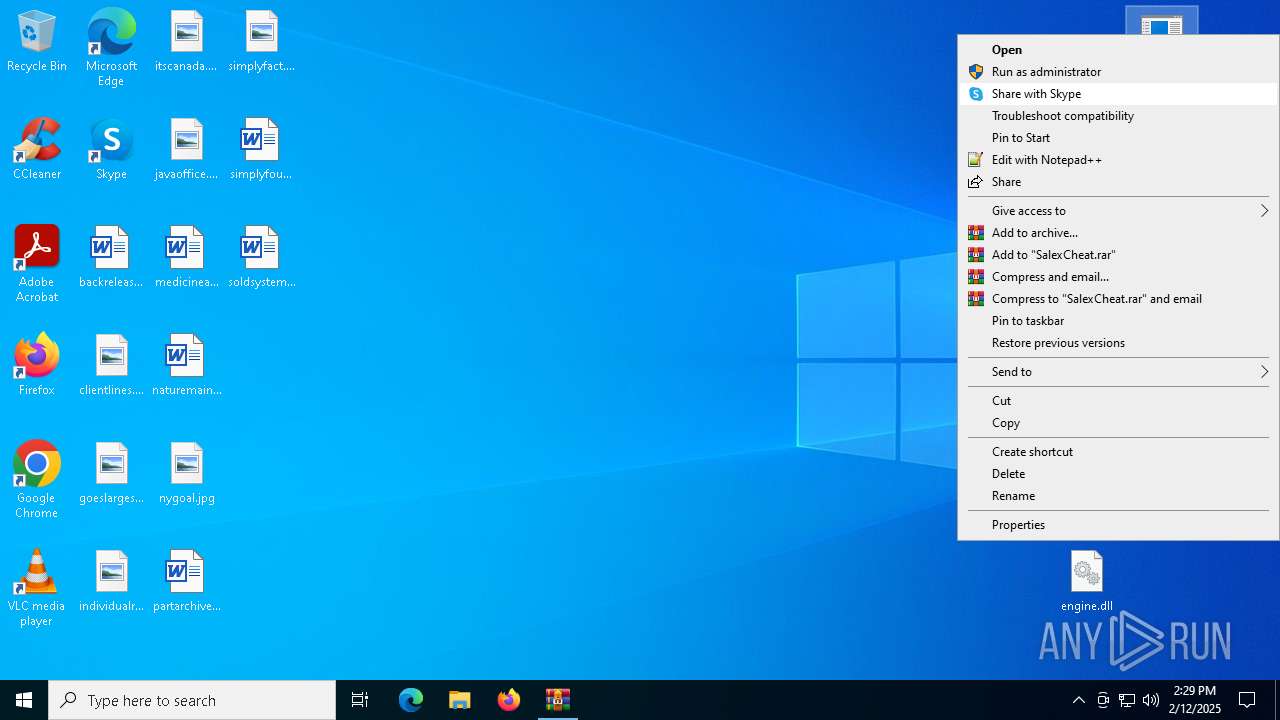
Manual execution by a user
- SalexCheat.exe (PID: 7024)
- SalexCheat.exe (PID: 5544)
- SalexCheat.exe (PID: 7016)
- SalexCheat.exe (PID: 3464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|
Total processes
150
Monitored processes
18
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1512 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7016 -s 832 | C:\Windows\SysWOW64\WerFault.exe | SalexCheat.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1904 | "C:\Users\admin\Desktop\SalexCheat.exe" | C:\Users\admin\Desktop\SalexCheat.exe | SalexCheat.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Meaning Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3420 | "C:\Users\admin\Desktop\SalexCheat.exe" | C:\Users\admin\Desktop\SalexCheat.exe | SalexCheat.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Meaning Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3464 | "C:\Users\admin\Desktop\SalexCheat.exe" | C:\Users\admin\Desktop\SalexCheat.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Meaning Exit code: 3221226505 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3744 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7024 -s 852 | C:\Windows\SysWOW64\WerFault.exe | SalexCheat.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3848 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Salex.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5544 | "C:\Users\admin\Desktop\SalexCheat.exe" | C:\Users\admin\Desktop\SalexCheat.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Meaning Exit code: 3221226505 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5568 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 5544 -s 828 | C:\Windows\SysWOW64\WerFault.exe | SalexCheat.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5684 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 3464 -s 272 | C:\Windows\SysWOW64\WerFault.exe | SalexCheat.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 179
Read events
16 156
Write events
17
Delete events
6
Modification events
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Salex.rar | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3848) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5568) WerFault.exe | Key: | \REGISTRY\A\{7354b023-5edd-ec2d-208b-502914a8a372}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
Executable files
3
Suspicious files
13
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5568 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_SalexCheat.exe_597c82c25694fb48df5d546fd5ca7d23ad29a_3d4d9362_019f1c55-538c-47e7-919b-0cc04dabcfc1\Report.wer | — | |
MD5:— | SHA256:— | |||
| 3744 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_SalexCheat.exe_597c82c25694fb48df5d546fd5ca7d23ad29a_3d4d9362_0ed28f9f-ed00-4fed-9695-c11a457d26d5\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5568 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\SalexCheat.exe.5544.dmp | — | |
MD5:— | SHA256:— | |||
| 3744 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\SalexCheat.exe.7024.dmp | — | |
MD5:— | SHA256:— | |||
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3848.34128\config1.cfg | text | |
MD5:660F059DE96AE650273EEDF2E871E978 | SHA256:B9ECD4CD9D045E6F6C446CAF4D1BCA1D150396BCFB71AA2CDBF8BCE7303D60BE | |||
| 5684 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_SalexCheat.exe_597c82c25694fb48df5d546fd5ca7d23ad29a_3d4d9362_9c3f4c80-4278-424c-8368-c89f07160571\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5684 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\SalexCheat.exe.3464.dmp | — | |
MD5:— | SHA256:— | |||
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3848.34128\SalexCheat.exe | executable | |
MD5:064CB2CBBF42FF195C8344037CFB8D76 | SHA256:E571AA999042295D9528C5427AEB65E700C2CFD77DBBD7F8523EDA24DBD8832A | |||
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3848.34128\config2.cfg | text | |
MD5:5FAB28899D2AD58CA0A7385ECD292DC0 | SHA256:8B407622142E523EF950FEB5899BE35061D03BA93E84972D2C72A156EB69430E | |||
| 3848 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3848.34128\Languages\eng.txt | text | |
MD5:6984CCDC90DFE005D053B0F028241585 | SHA256:AE32E5572C95B5FB5B23E528A4D844206C751BFC82A7C32723677BAADF805D3B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
69
DNS requests
17
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7136 | SIHClient.exe | GET | 200 | 23.211.226.110:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7136 | SIHClient.exe | GET | 200 | 23.211.226.110:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3744 | WerFault.exe | GET | 200 | 2.23.154.57:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5568 | WerFault.exe | GET | 200 | 2.23.154.57:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5568 | WerFault.exe | GET | 200 | 23.211.226.110:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6316 | backgroundTaskHost.exe | GET | 200 | 23.52.56.216:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3744 | WerFault.exe | GET | 200 | 23.211.226.110:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.56.216:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.211.226.110:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.211.226.110:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.41.248:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.41.248:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.23.64:443 | www.bing.com | Akamai International B.V. | AT | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.211.226.110:80 | www.microsoft.com | BHARTI Airtel Ltd. | IN | whitelisted |
— | — | 23.211.226.110:80 | www.microsoft.com | BHARTI Airtel Ltd. | IN | whitelisted |
— | — | 23.52.56.216:80 | ocsp.digicert.com | AKAMAI-AS | NL | whitelisted |
1076 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
ignoredshee.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (ignoredshee .com) |
3420 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |
1904 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |
3420 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |
3420 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |
3420 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |
3420 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |
3420 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |
1904 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |
1904 | SalexCheat.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (ignoredshee .com in TLS SNI) |