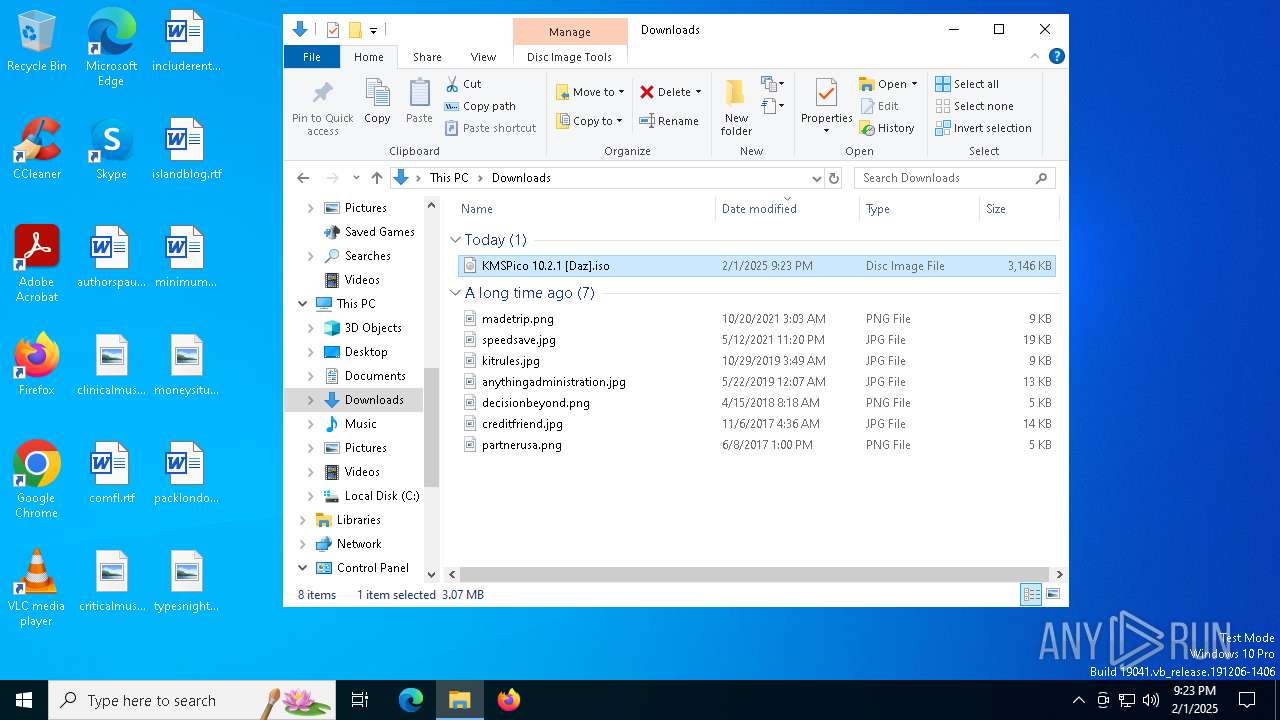
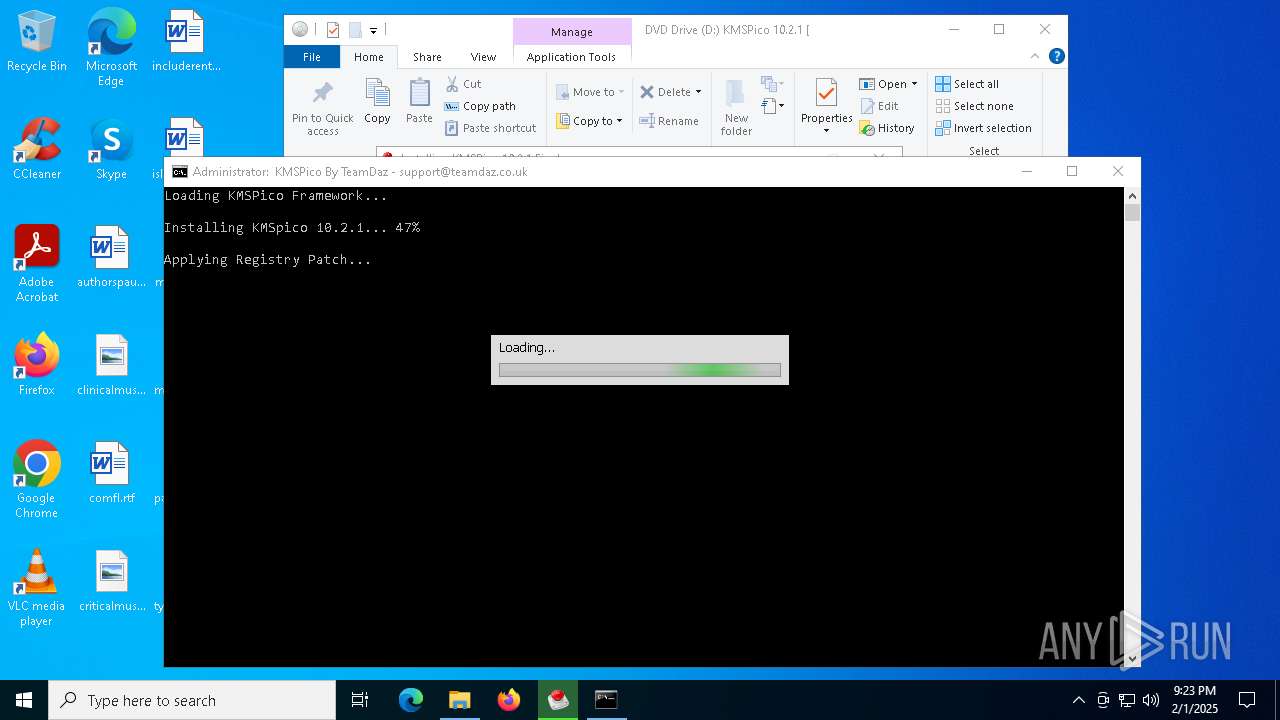
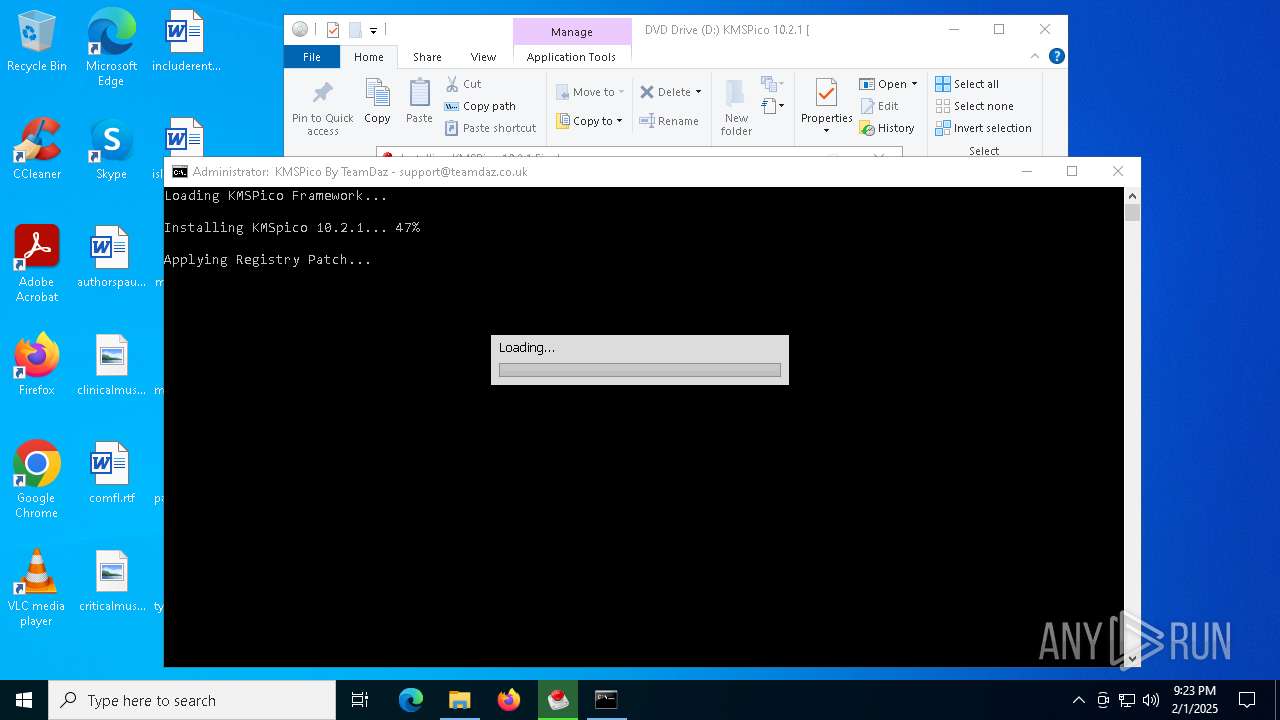
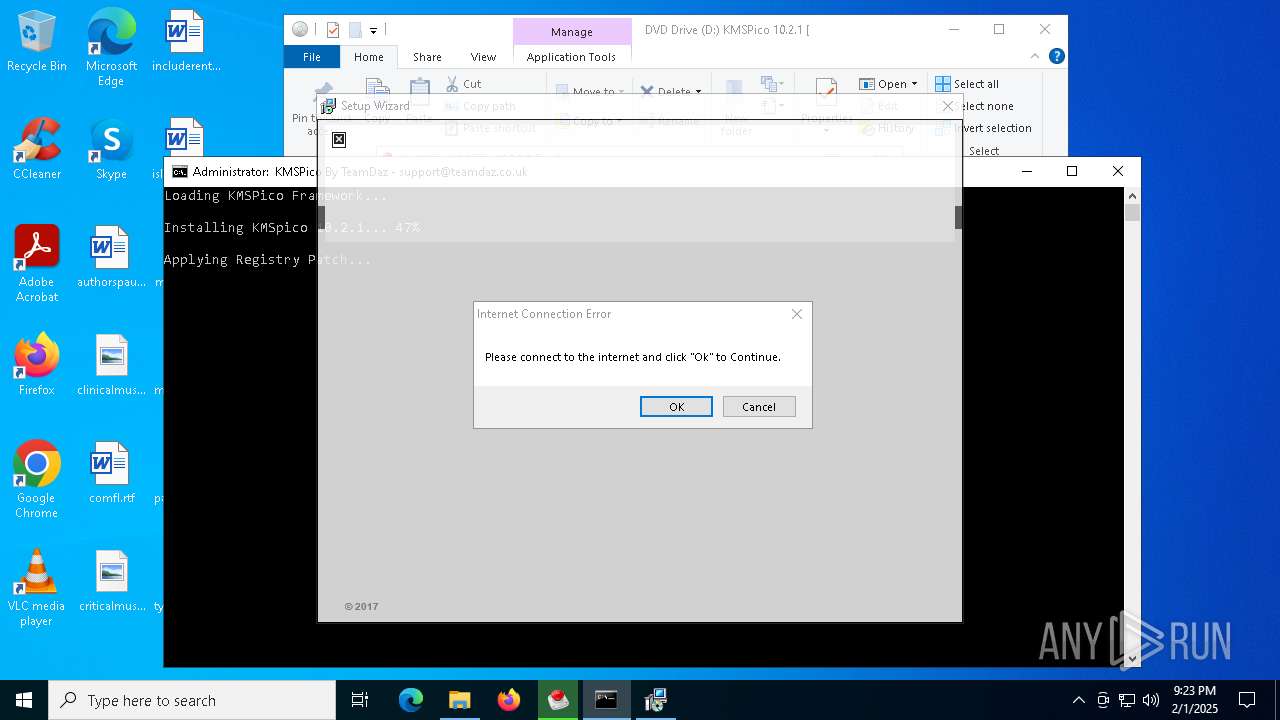
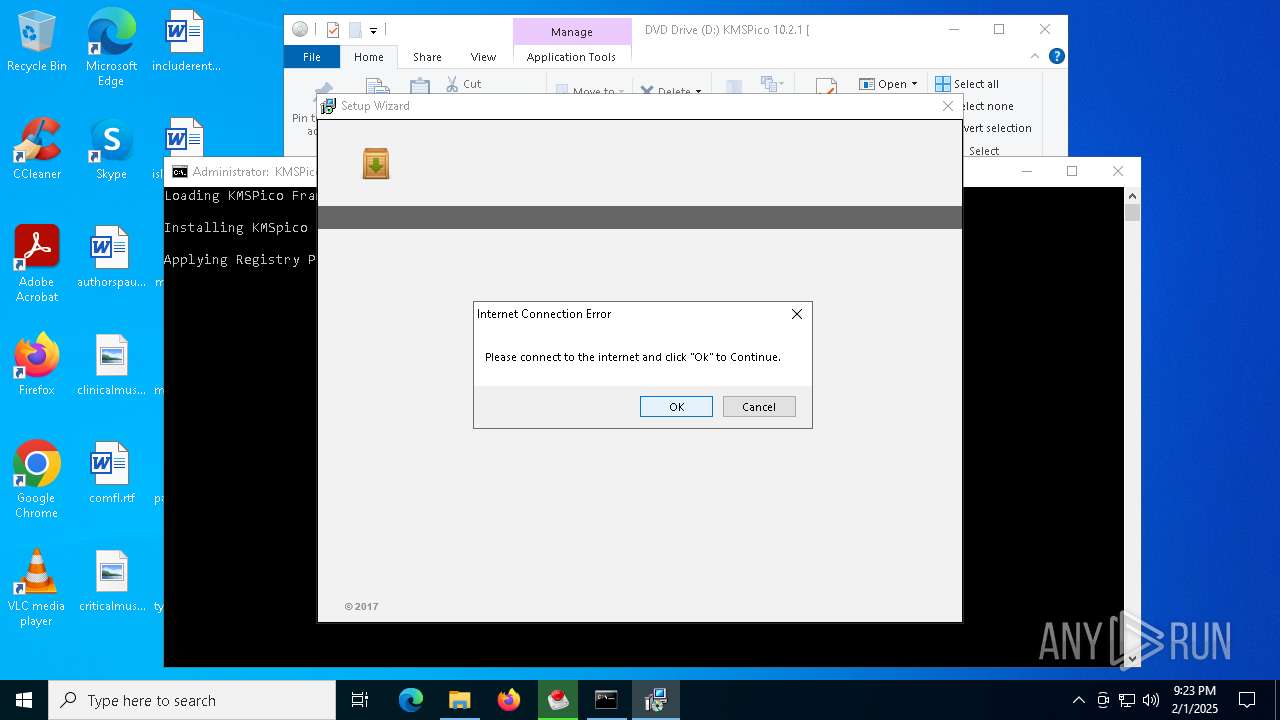
| File name: | KMSPico 10.2.1 [Daz].iso |
| Full analysis: | https://app.any.run/tasks/1538460b-99ac-4381-a952-19dce7c388fd |
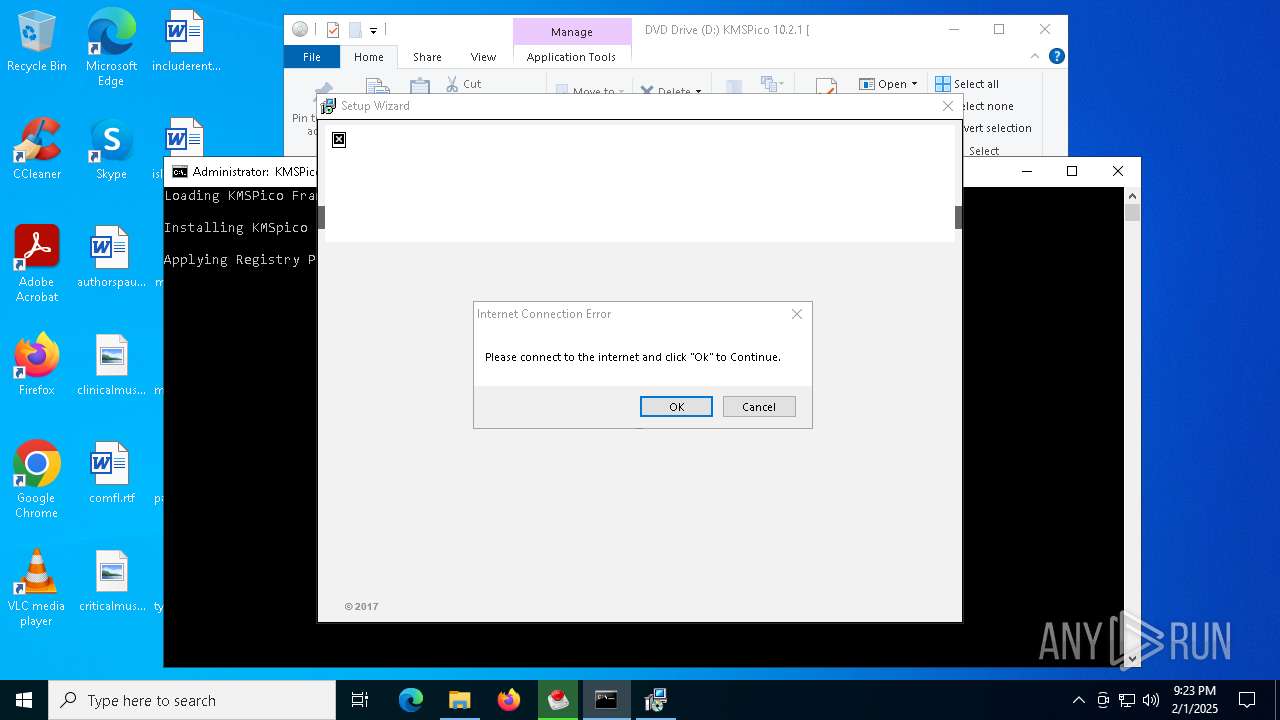
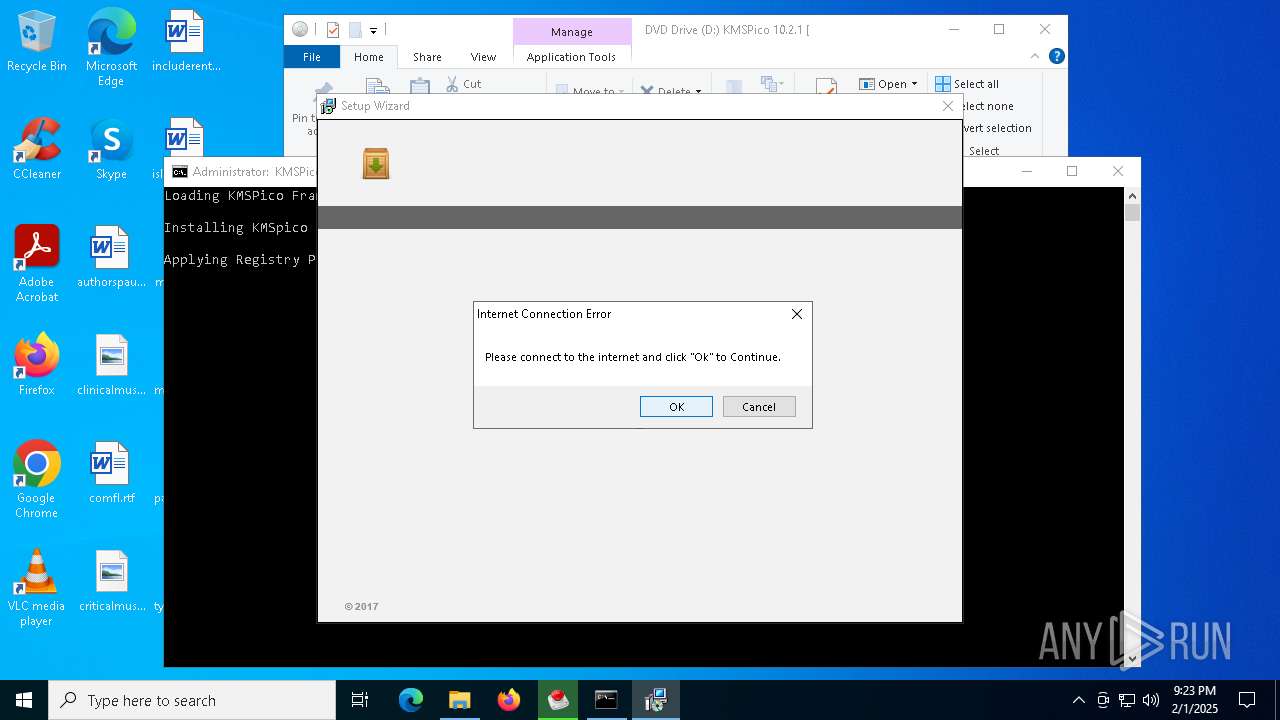
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | February 01, 2025, 21:23:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
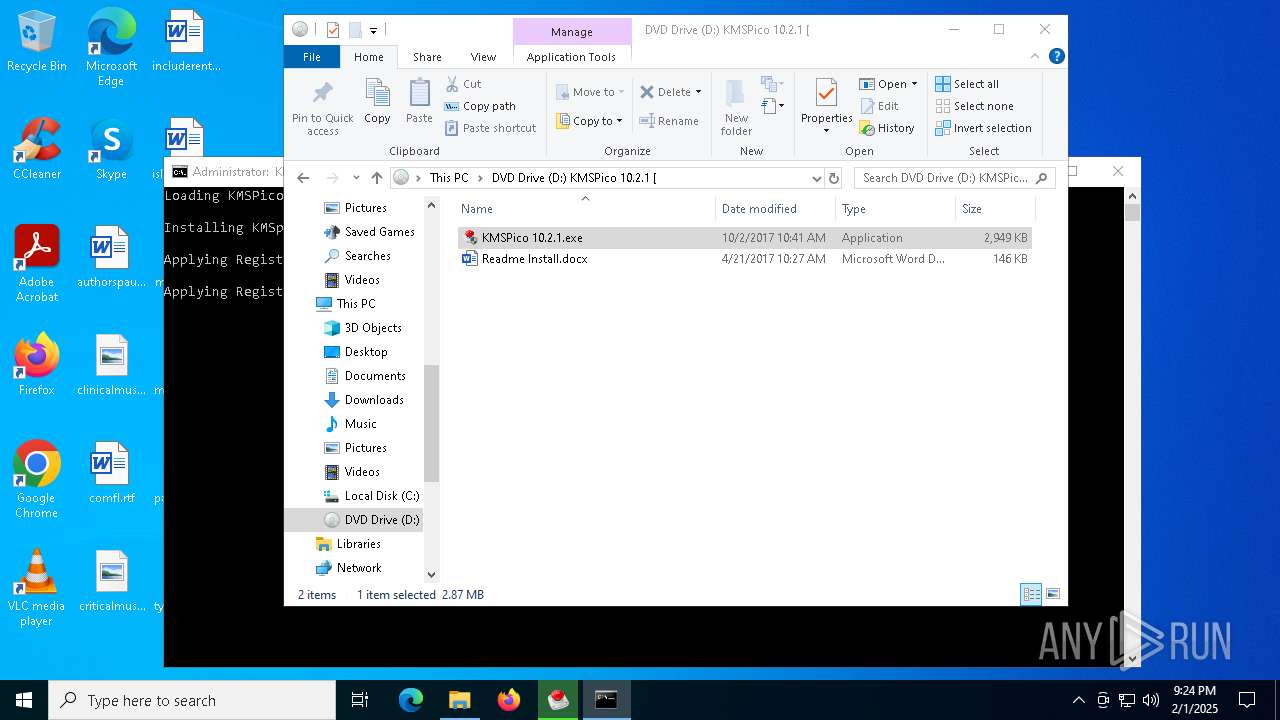
| MIME: | application/x-iso9660-image |
| File info: | ISO 9660 CD-ROM filesystem data 'KMSPico 10.2.1 [Daz]' |
| MD5: | 443E95EC28934B5FCABCE887F6D6BDB3 |
| SHA1: | B4A9EF47685D6E657C2EB7B49C813072657CDAA3 |
| SHA256: | 33BF6B8940F62CF225455BED50CBBEE1197FCEA888274F6749CE289F48F7D39B |
| SSDEEP: | 98304:EW/R3pWfYNX2SP+NFuxYJeFmL6s7MxJHcvUMPH7sAMJjL+WnUMLQeQDX7XYQqUbY:MumHKXGpCB |
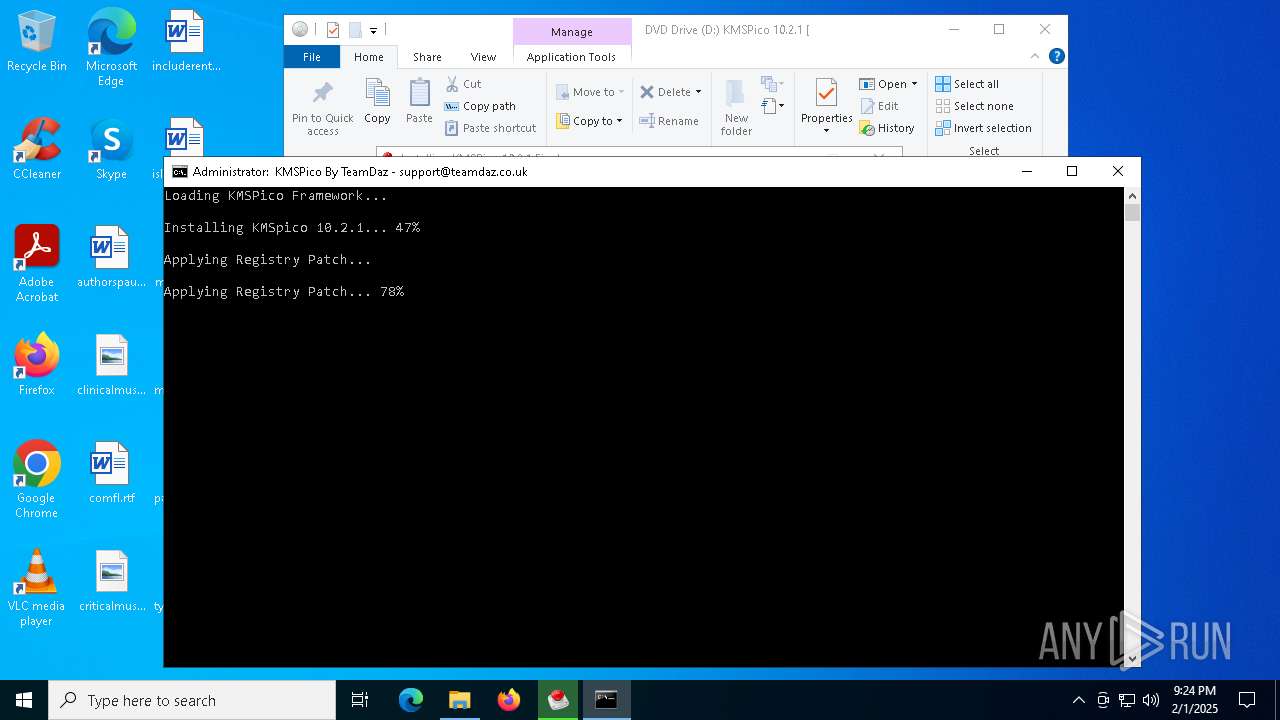
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 132)
Actions looks like stealing of personal data
- Registry_Activation.exe (PID: 3832)
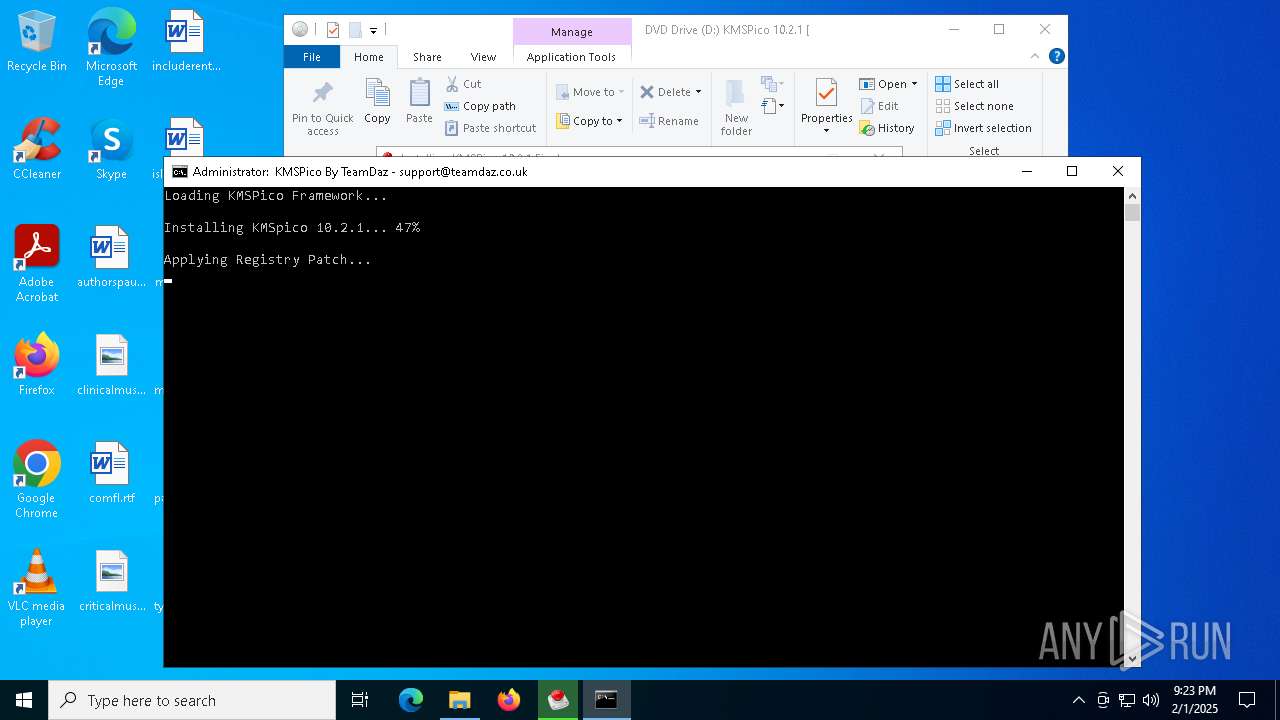
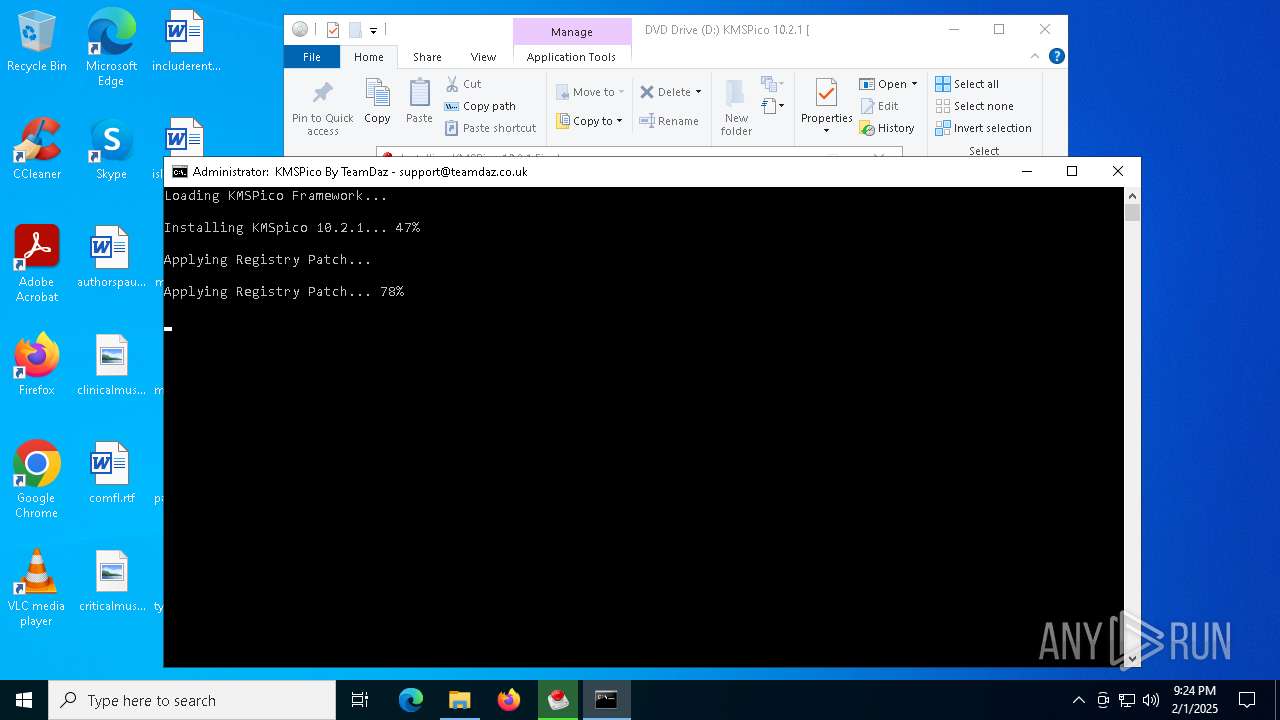
Changes the autorun value in the registry
- activation.exe (PID: 6624)
Looks like the application has launched a miner
- activation.exe (PID: 6624)
SUSPICIOUS
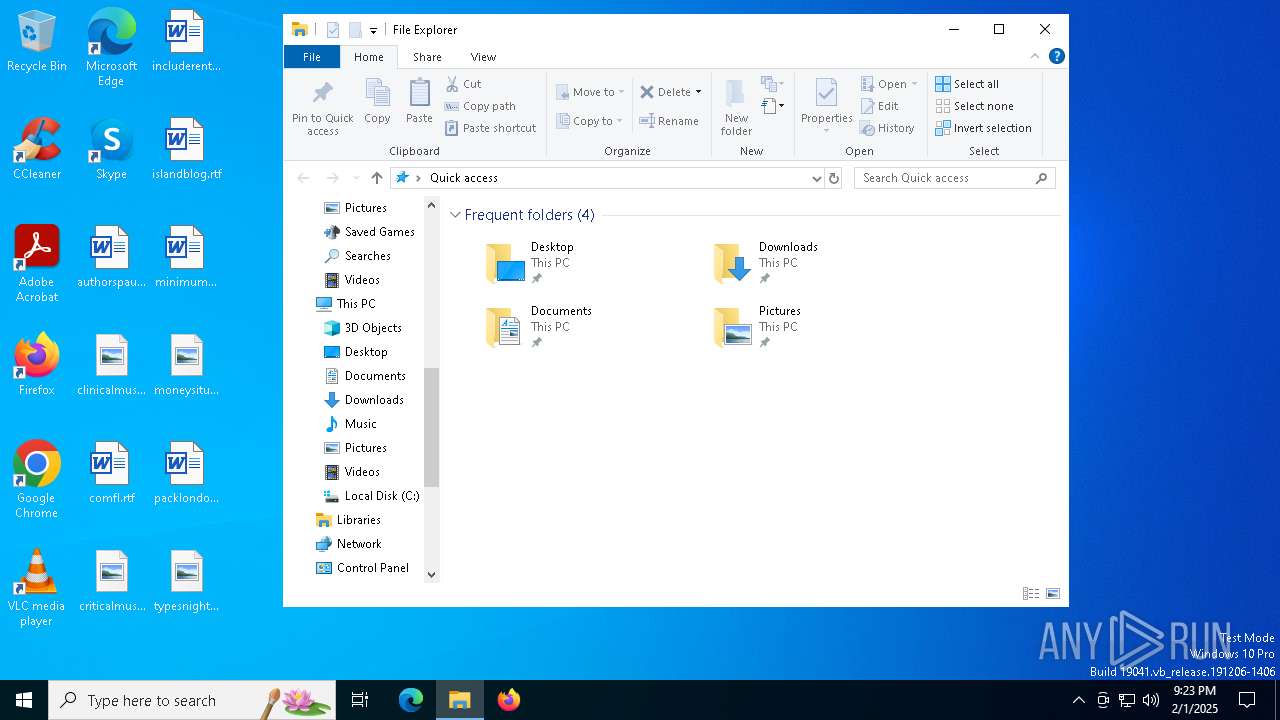
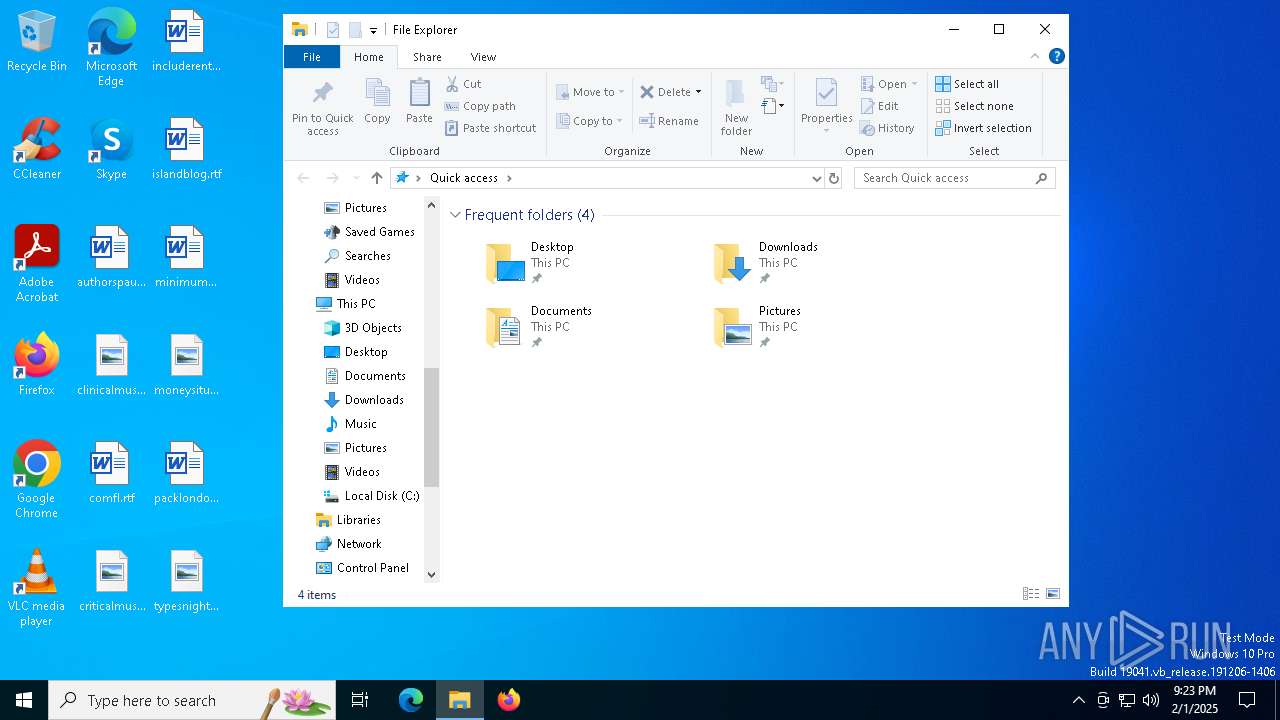
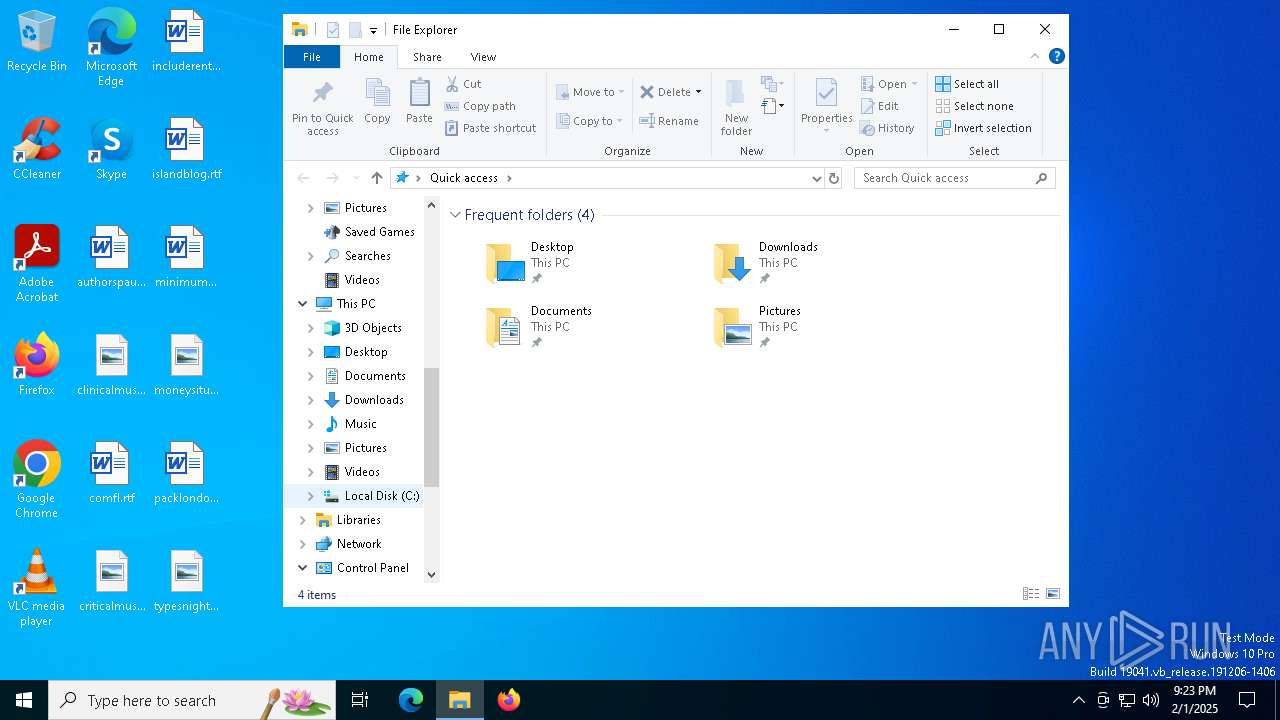
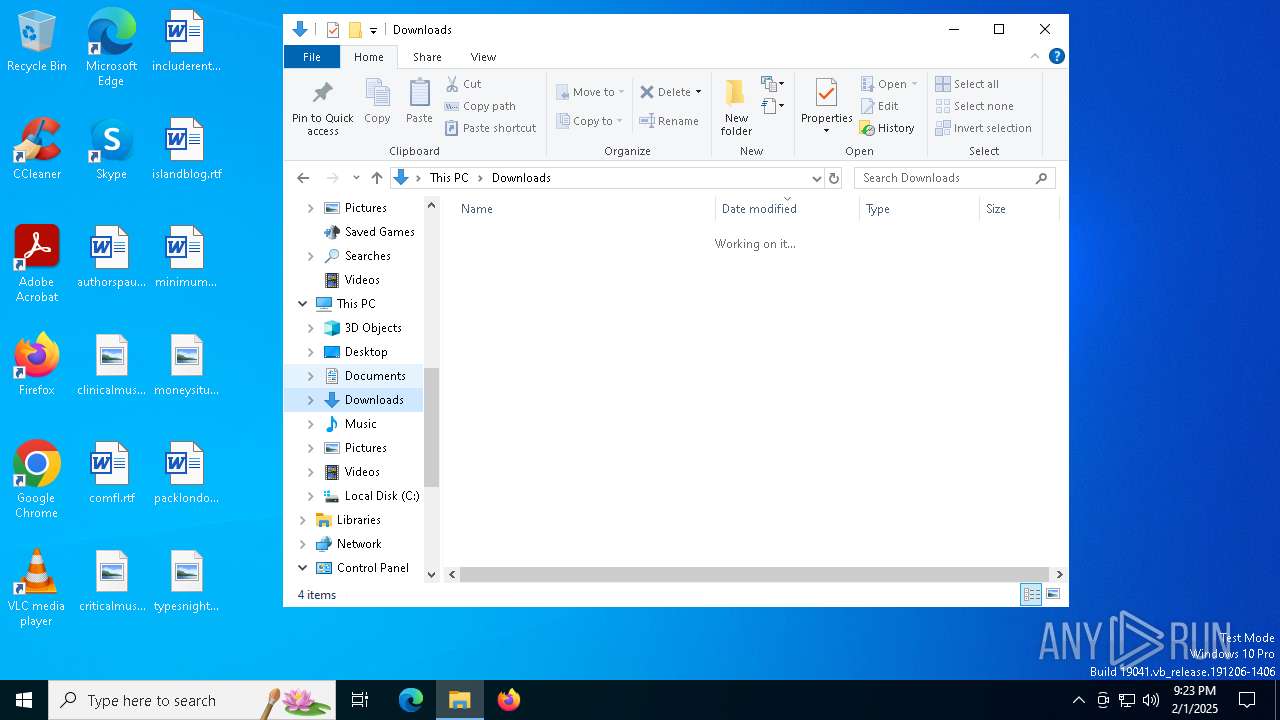
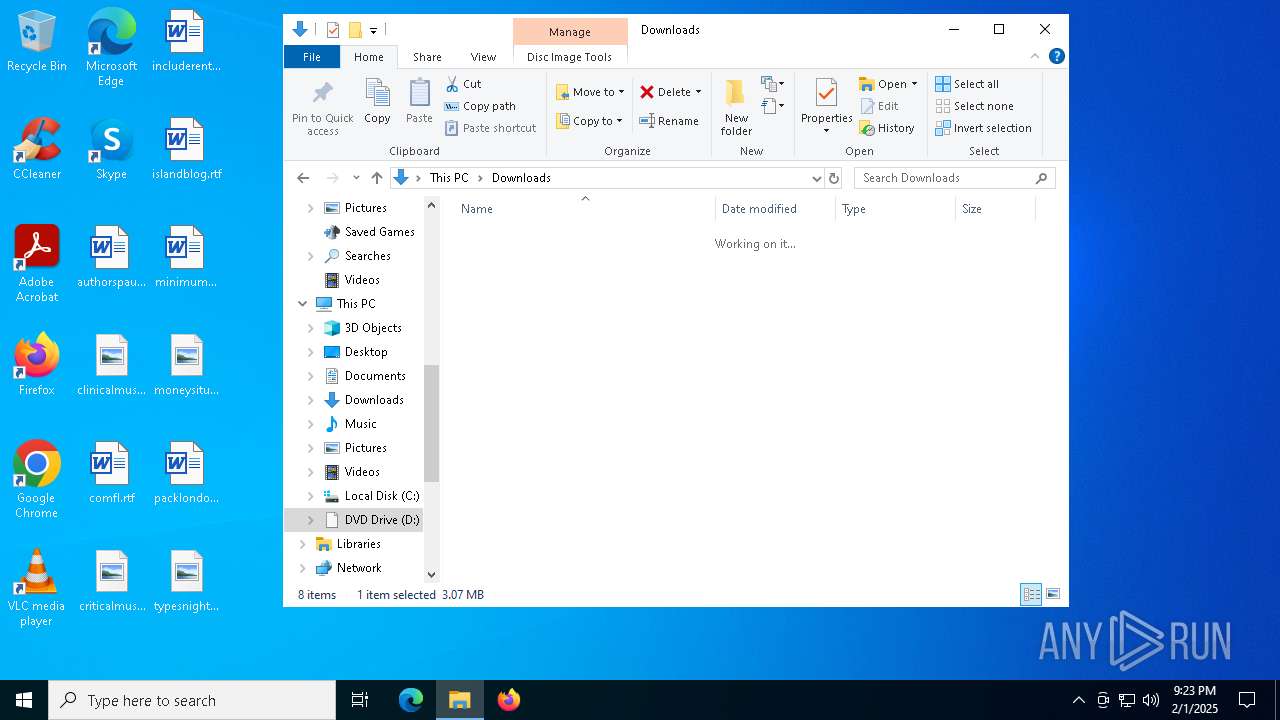
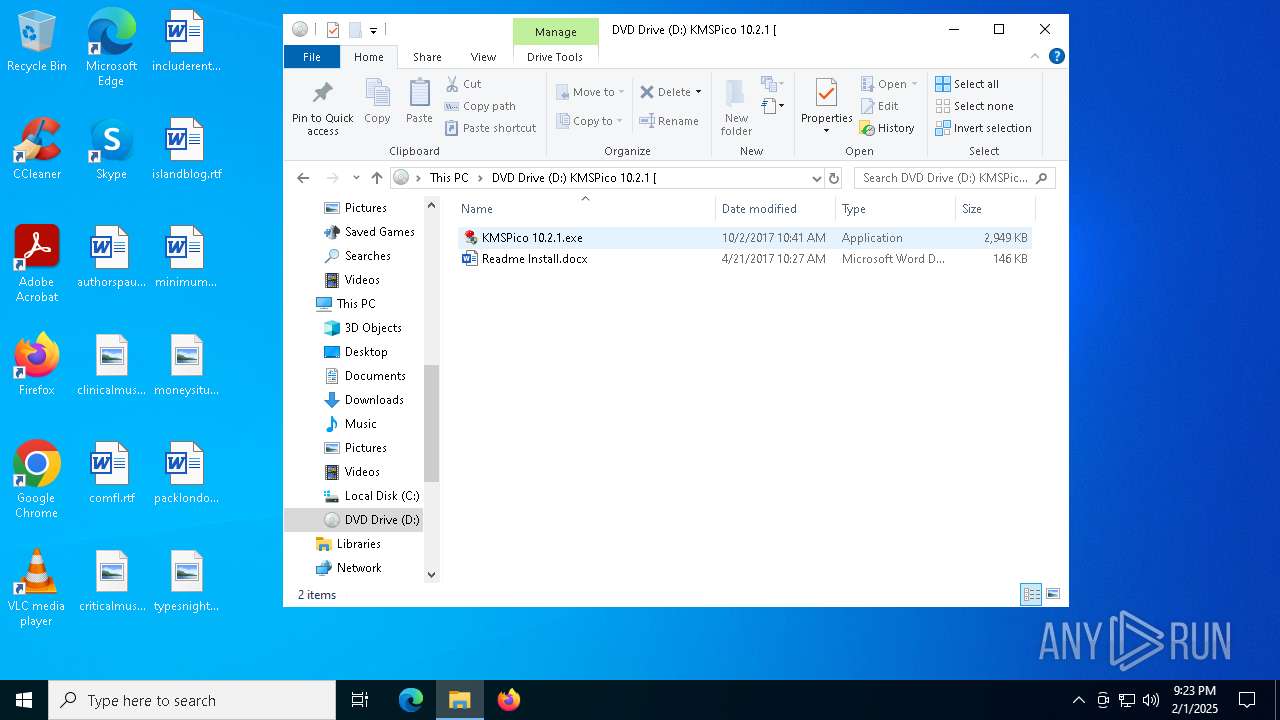
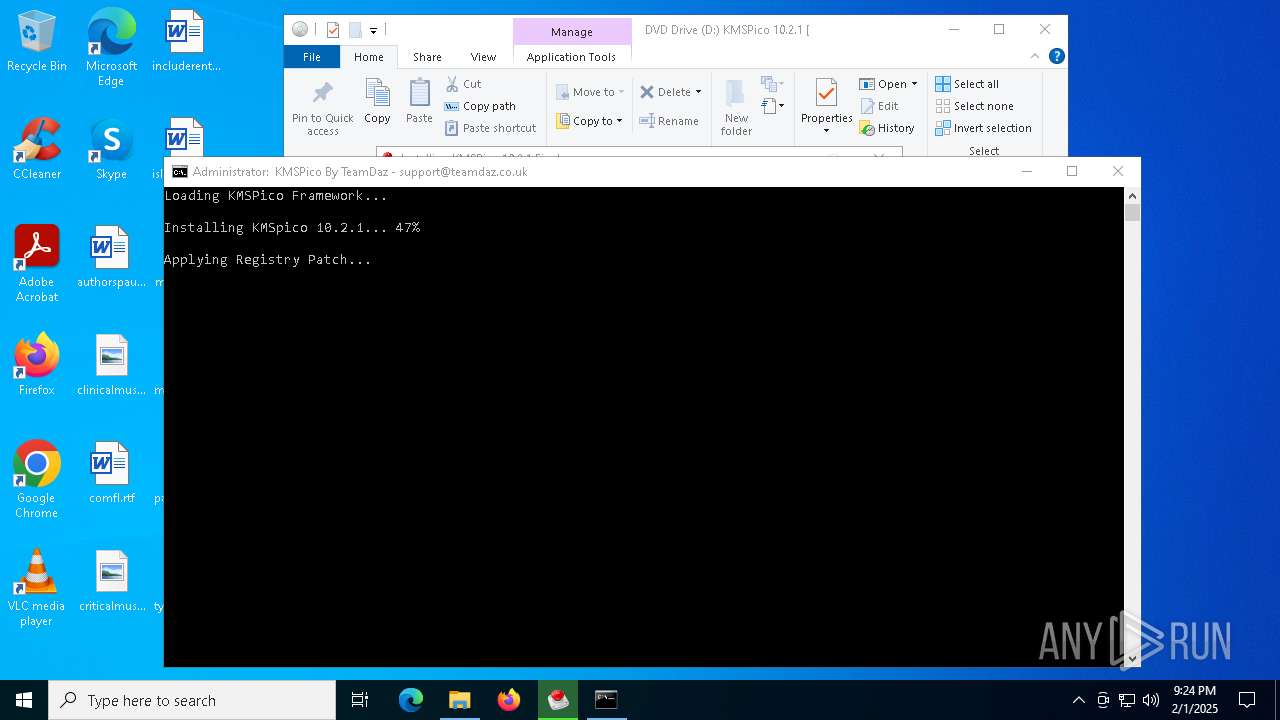
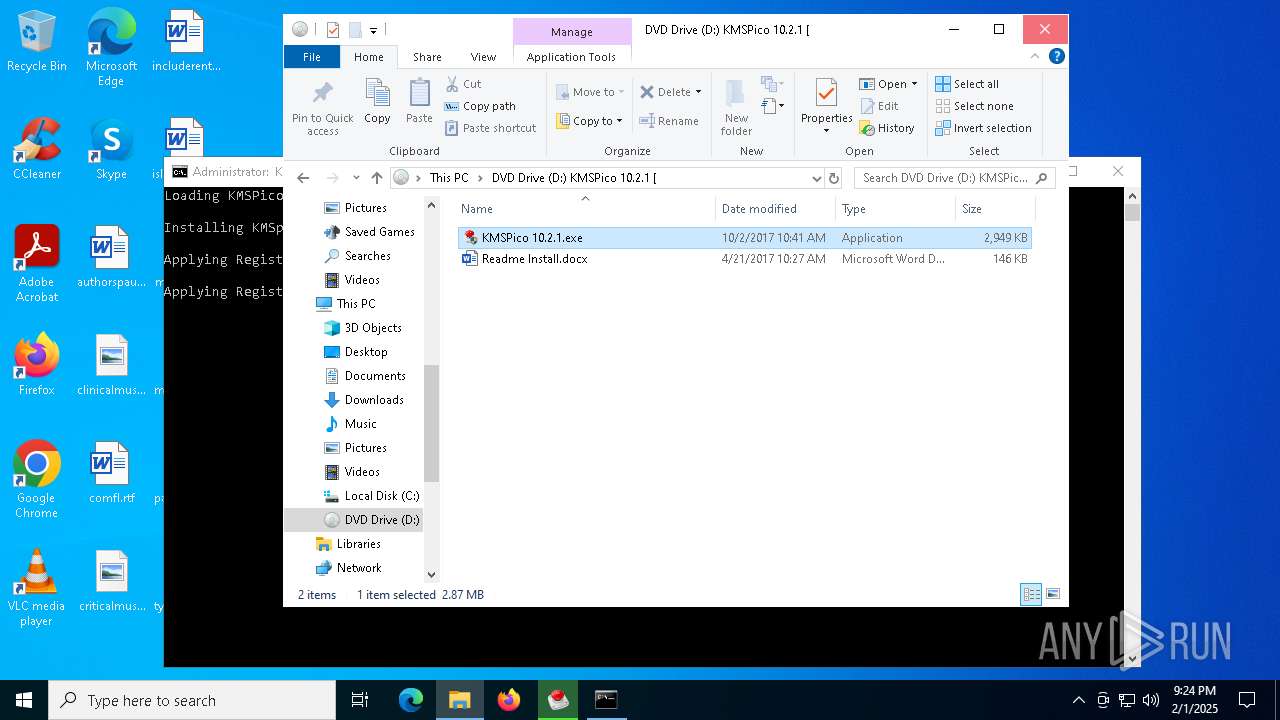
Image mount has been detect
- explorer.exe (PID: 4488)
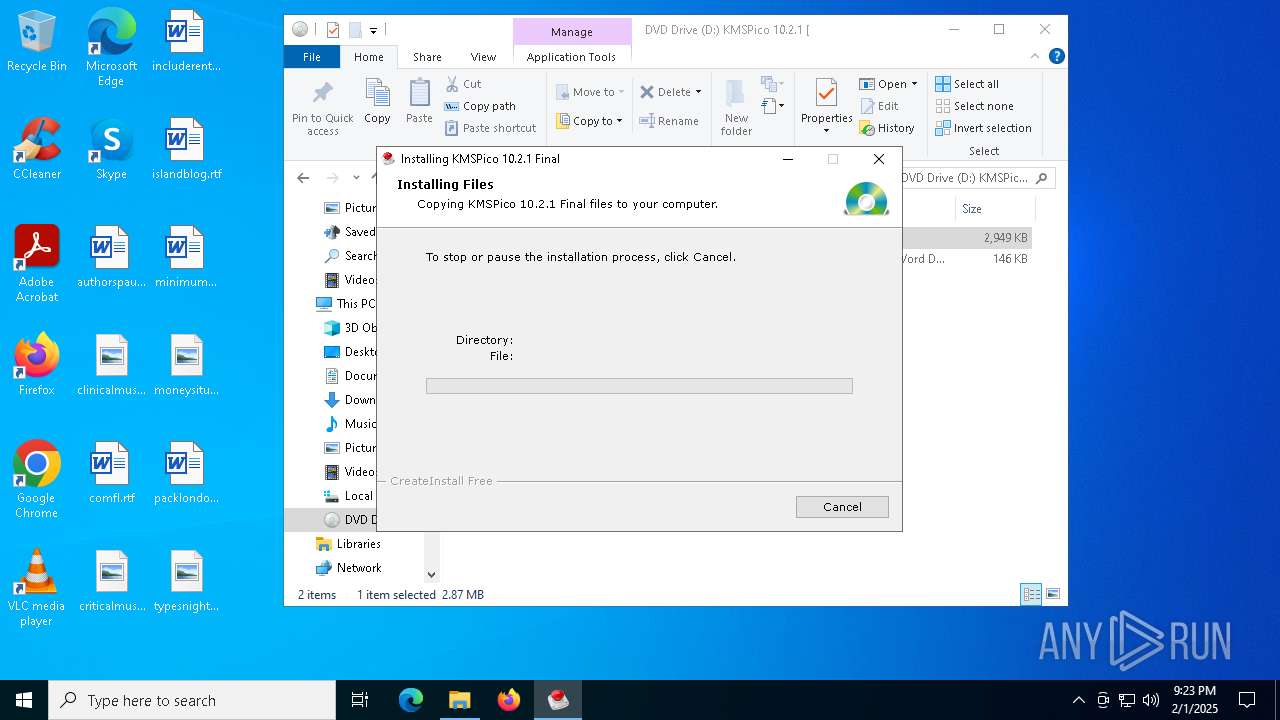
Executable content was dropped or overwritten
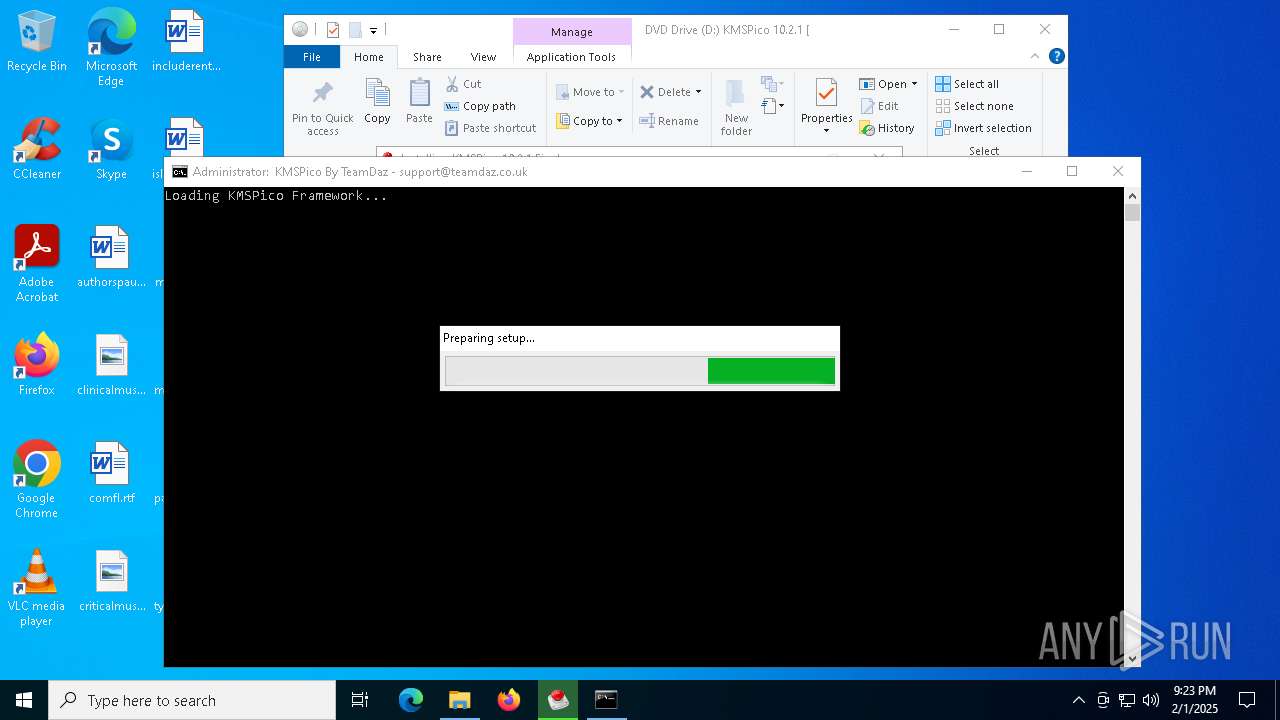
- KMSPico 10.2.1.exe (PID: 7132)
- activation.exe (PID: 6624)
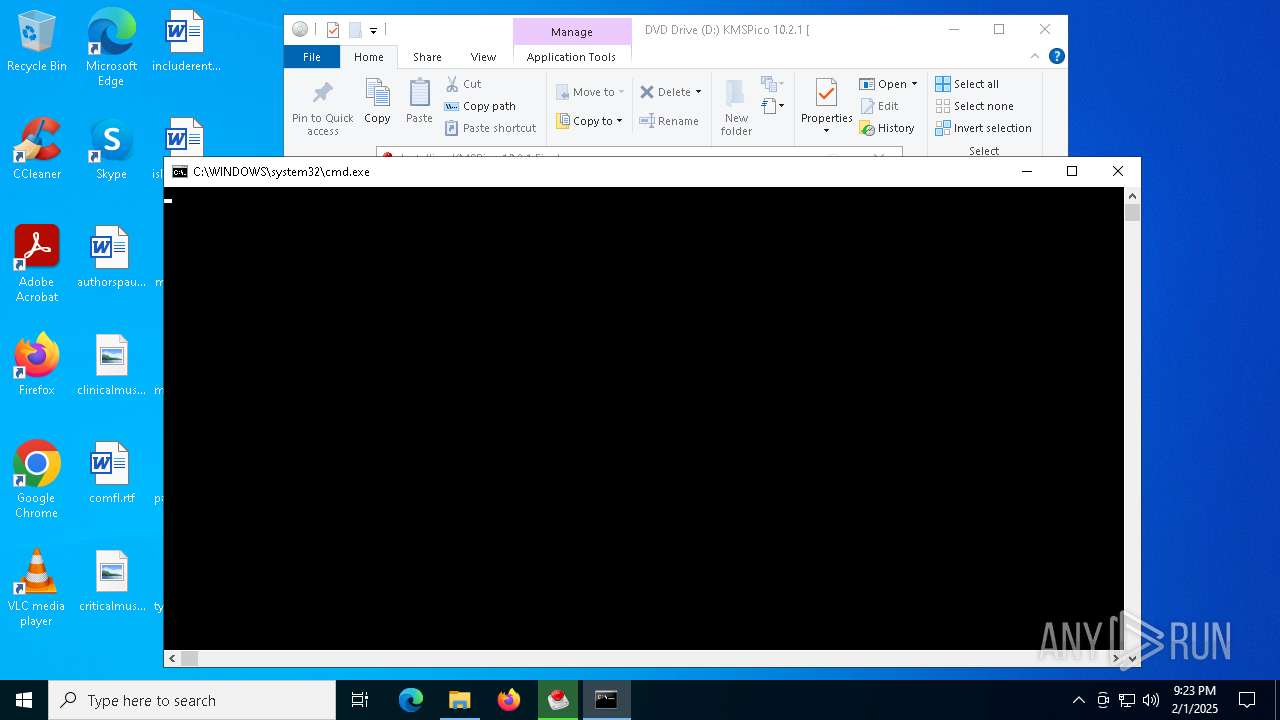
Starts CMD.EXE for commands execution
- KMSPico 10.2.1.exe (PID: 7132)
Executing commands from a ".bat" file
- KMSPico 10.2.1.exe (PID: 7132)
Reads security settings of Internet Explorer
- Registry_Activation.exe (PID: 3832)
- KMSPico 10.2.1.exe (PID: 7132)
Reads the BIOS version
- Registry_Activation.exe (PID: 3832)
Reads Microsoft Outlook installation path
- Registry_Activation.exe (PID: 3832)
Reads Internet Explorer settings
- Registry_Activation.exe (PID: 3832)
Reads the date of Windows installation
- KMSPicoActivator.exe (PID: 4824)
There is functionality for taking screenshot (YARA)
- KMSPico 10.2.1.exe (PID: 7132)
Start notepad (likely ransomware note)
- activation.exe (PID: 6624)
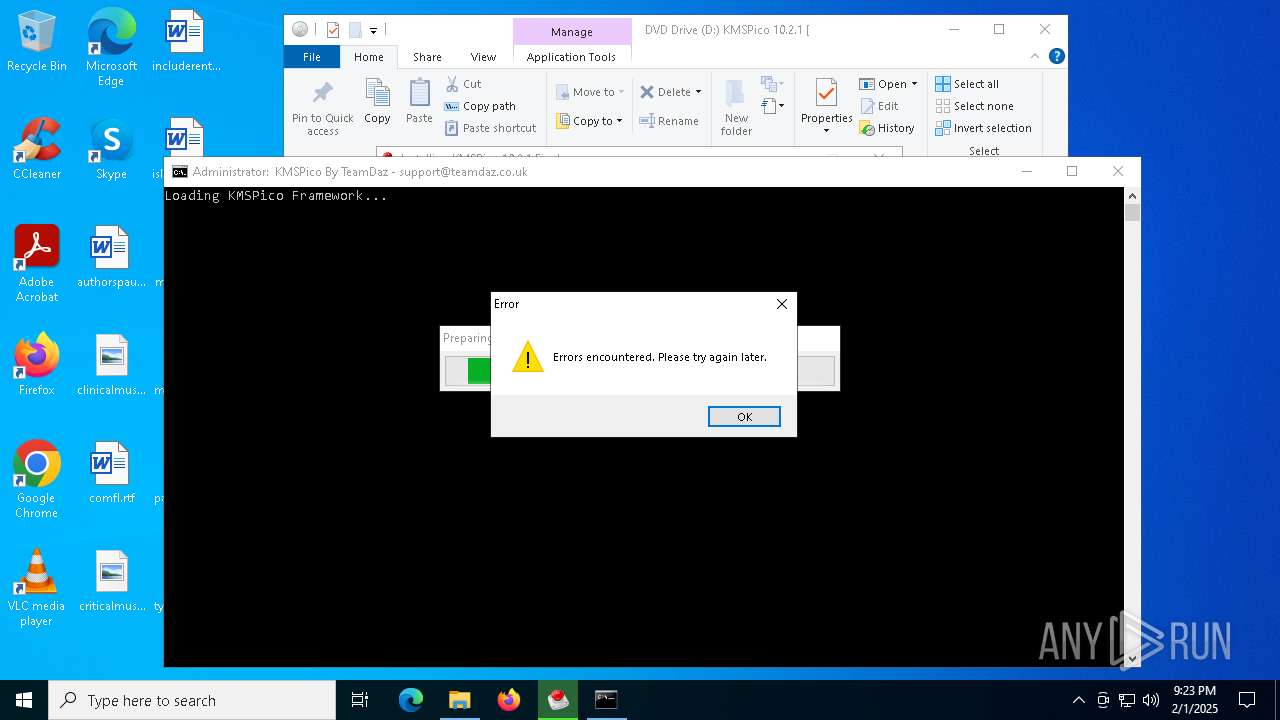
Executes application which crashes
- activation.exe (PID: 6624)
Application launched itself
- Registry_Activation.exe (PID: 3832)
INFO
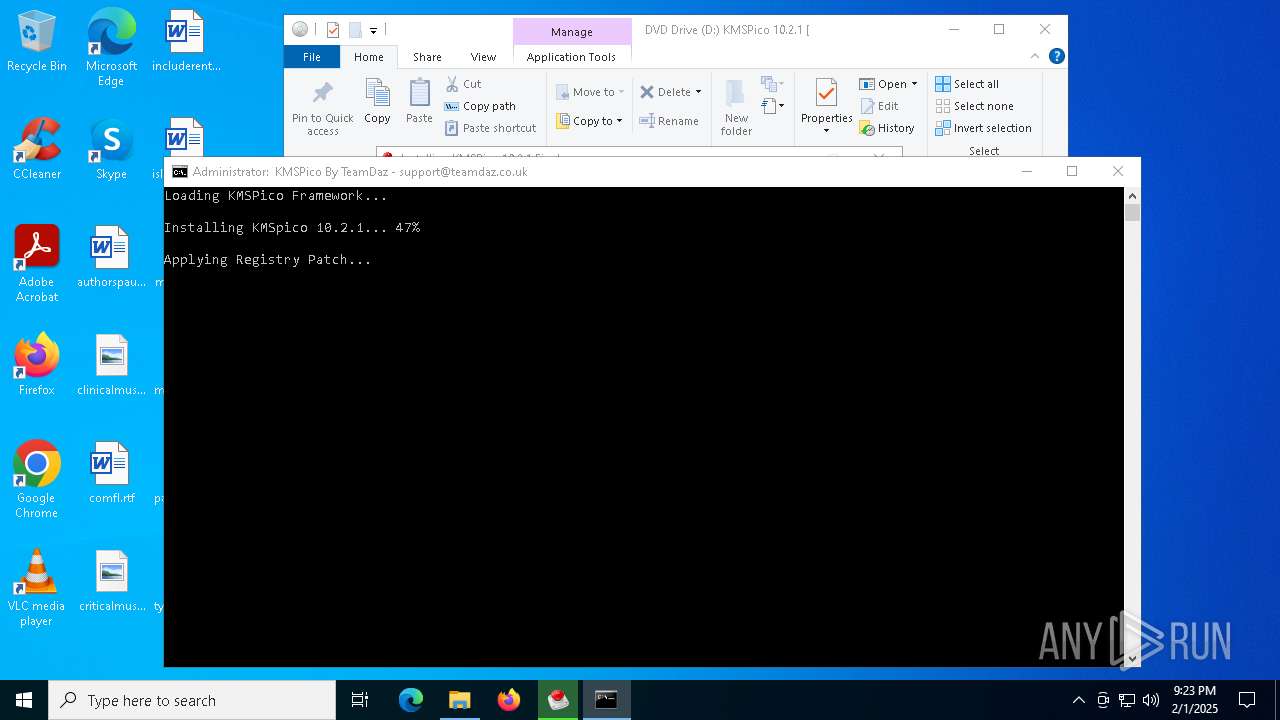
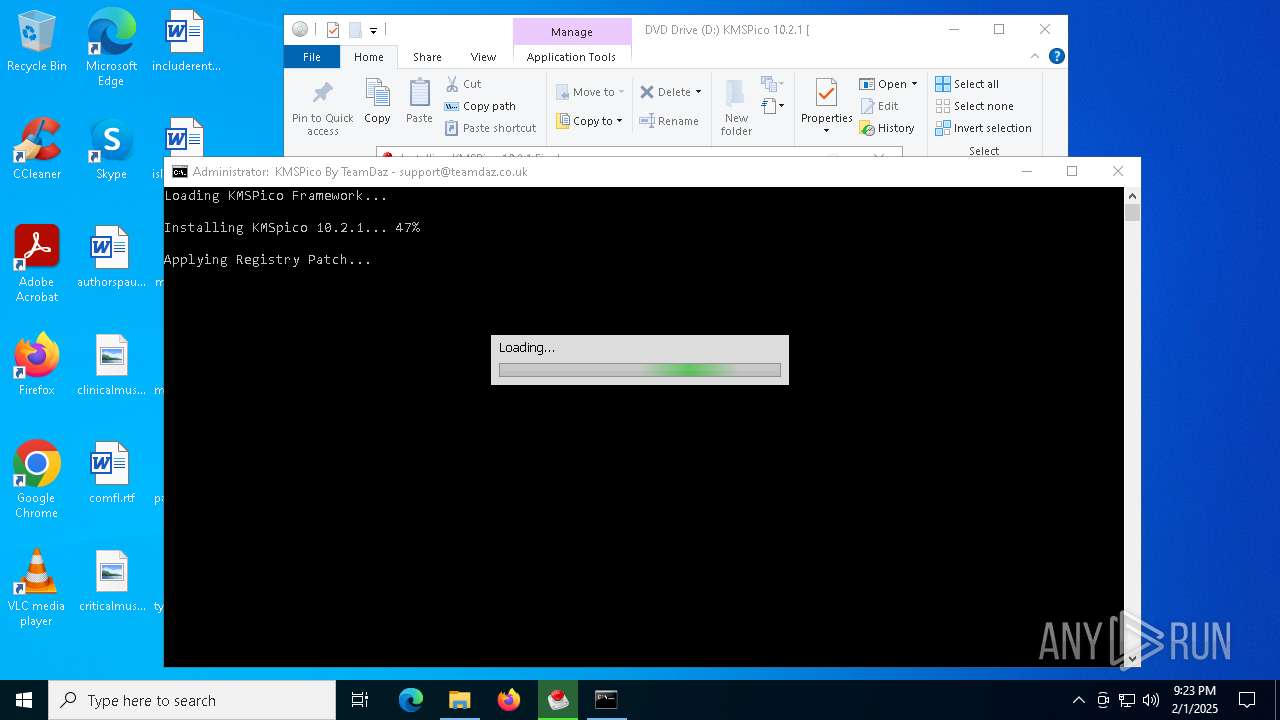
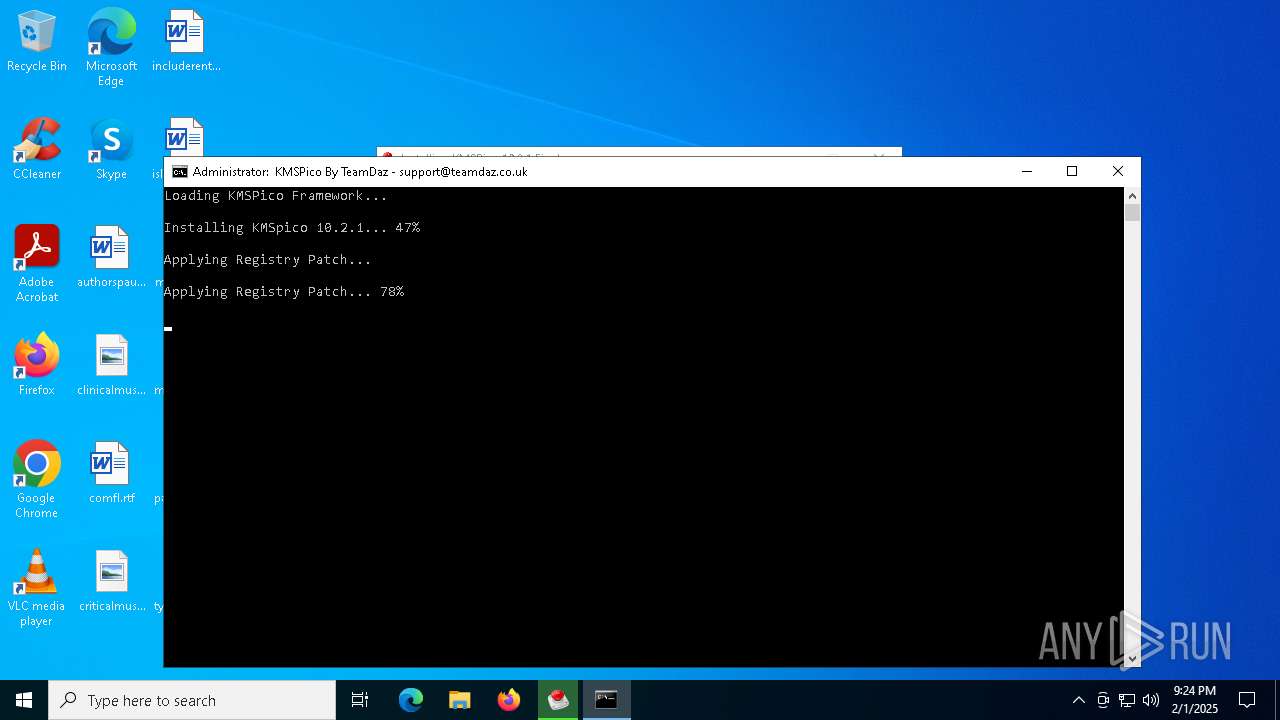
Manual execution by a user
- KMSPico 10.2.1.exe (PID: 7072)
- KMSPico 10.2.1.exe (PID: 7132)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4488)
The sample compiled with english language support
- KMSPico 10.2.1.exe (PID: 7132)
Checks supported languages
- KMSPico 10.2.1.exe (PID: 7132)
- KMSPicoActivator.exe (PID: 4824)
- Registry_Activation.exe (PID: 3832)
- activation.exe (PID: 6624)
- d2d634303ca9312a24bab137928b72fa.exe (PID: 3040)
- Registry_Activation.exe (PID: 4556)
Create files in a temporary directory
- KMSPico 10.2.1.exe (PID: 7132)
- Registry_Activation.exe (PID: 3832)
Reads the computer name
- KMSPico 10.2.1.exe (PID: 7132)
- KMSPicoActivator.exe (PID: 4824)
- Registry_Activation.exe (PID: 3832)
- d2d634303ca9312a24bab137928b72fa.exe (PID: 3040)
- Registry_Activation.exe (PID: 4556)
Creates files in the program directory
- KMSPico 10.2.1.exe (PID: 7132)
Reads Environment values
- Registry_Activation.exe (PID: 3832)
Process checks whether UAC notifications are on
- Registry_Activation.exe (PID: 3832)
Reads the machine GUID from the registry
- Registry_Activation.exe (PID: 3832)
- KMSPicoActivator.exe (PID: 4824)
- d2d634303ca9312a24bab137928b72fa.exe (PID: 3040)
Checks proxy server information
- Registry_Activation.exe (PID: 3832)
- WerFault.exe (PID: 5112)
- WerFault.exe (PID: 3664)
Reads Windows Product ID
- Registry_Activation.exe (PID: 3832)
Reads CPU info
- Registry_Activation.exe (PID: 3832)
Creates files or folders in the user directory
- activation.exe (PID: 6624)
- WerFault.exe (PID: 5112)
- WerFault.exe (PID: 3664)
Reads the software policy settings
- WerFault.exe (PID: 3664)
- WerFault.exe (PID: 5112)
Process checks computer location settings
- KMSPico 10.2.1.exe (PID: 7132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
EXIF
ISO
| VolumeName: | KMSPico 10.2.1 [Daz] |
|---|---|
| VolumeBlockCount: | 1573 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2017:04:21 12:27:24+02:00 |
| VolumeCreateDate: | 2017:11:03 23:20:57.45+02:00 |
| VolumeModifyDate: | 2017:11:03 23:20:57.45+02:00 |
| VolumeExpirationDate: | 1900:01:01 00:00:00.00+02:00 |
| VolumeEffectiveDate: | 1900:01:01 00:00:00.00+02:00 |
Composite
| VolumeSize: | 3.2 MB |
|---|
Total processes
149
Monitored processes
18
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\system32\cmd.exe /c ""C:\Program Files (x86)\KMSPico 10.2.1 Final\KMSPICO_SETUP.BAT"" | C:\Windows\SysWOW64\cmd.exe | — | KMSPico 10.2.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 204 | schtasks /create /tn "SVC Update" /tr "C:\WINDOWS\explorer.exe ""http://sh.st/AeotZ""" /sc DAILY | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2012 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3040 | "d2d634303ca9312a24bab137928b72fa.exe" | C:\Program Files (x86)\KMSPico 10.2.1 Final\d2d634303ca9312a24bab137928b72fa.exe | — | cmd.exe | |||||||||||
User: admin Company: InstallShield Software Corporation Integrity Level: HIGH Description: Lvi Carg Dcsexthome Gamergate Administrators Autohotkey Modules
| |||||||||||||||
| 3664 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6624 -s 564 | C:\Windows\SysWOW64\WerFault.exe | activation.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3832 | "Registry_Activation.exe" | C:\Program Files (x86)\KMSPico 10.2.1 Final\Registry_Activation.exe | cmd.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Facuge Setup Exit code: 4294967206 Version: 4.0.1.2 Modules
| |||||||||||||||
| 4144 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\deldll.bat" " | C:\Windows\SysWOW64\cmd.exe | — | KMSPico 10.2.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4488 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4556 | "C:\Program Files (x86)\KMSPico 10.2.1 Final\Registry_Activation.exe" /_ShowProgress /PrTxt:TG9hZGluZy4uLg== /mnl | C:\Program Files (x86)\KMSPico 10.2.1 Final\Registry_Activation.exe | — | Registry_Activation.exe | |||||||||||
User: admin Company: Integrity Level: HIGH Description: Facuge Setup Exit code: 259 Version: 4.0.1.2 Modules
| |||||||||||||||
| 4824 | "KMSPicoActivator.exe" | C:\Program Files (x86)\KMSPico 10.2.1 Final\KMSPicoActivator.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
21 314
Read events
21 144
Write events
154
Delete events
16
Modification events
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000602DE |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456A48A294F7A40804AB924005FF030B61F | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: C1909E6700000000 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000000000000000000 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 03000000040000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | MinimizedStateTabletModeOff |
Value: 0 | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | QatItems |
Value: 3C7369713A637573746F6D554920786D6C6E733A7369713D22687474703A2F2F736368656D61732E6D6963726F736F66742E636F6D2F77696E646F77732F323030392F726962626F6E2F716174223E3C7369713A726962626F6E206D696E696D697A65643D2266616C7365223E3C7369713A71617420706F736974696F6E3D2230223E3C7369713A736861726564436F6E74726F6C733E3C7369713A636F6E74726F6C206964513D227369713A3136313238222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3136313239222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333532222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333834222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333336222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333537222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C2F7369713A736861726564436F6E74726F6C733E3C2F7369713A7161743E3C2F7369713A726962626F6E3E3C2F7369713A637573746F6D55493E | |||
| (PID) Process: | (4488) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar\ShellBrowser |
| Operation: | write | Name: | ITBar7Layout |
Value: 13000000000000000000000020000000100000000000000001000000010700005E01000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5004) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A78039010000EE984C473DCFF54180E34AAB0AB04301FA000000 | |||
Executable files
11
Suspicious files
16
Text files
51
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7132 | KMSPico 10.2.1.exe | C:\Program Files (x86)\KMSPico 10.2.1 Final\d2d634303ca9312a24bab137928b72fa.exe | executable | |
MD5:D2D634303CA9312A24BAB137928B72FA | SHA256:9B1C1A49F5489C143C72EB1020C87274BA05261038822C52025279F2361BBF8A | |||
| 7132 | KMSPico 10.2.1.exe | C:\Users\admin\AppData\Local\Temp\genteeDD\setup_temp.gea | binary | |
MD5:2FA1359552D165A9B8D9E86FDCCED144 | SHA256:5192154AFDCE0E72326DD59FFB365A54CED7CB646D9125D7898C24AA0BBABCF8 | |||
| 7132 | KMSPico 10.2.1.exe | C:\Program Files (x86)\KMSPico 10.2.1 Final\KMSPICO_SETUP.BAT | text | |
MD5:F1EE828ADE6AF8693A1C5138BD0777FE | SHA256:532291F60926E625BA87BC6C815E59FDC65EEE2818E75CFA4AAEA08E025E4D93 | |||
| 7132 | KMSPico 10.2.1.exe | C:\Users\admin\AppData\Local\Temp\genteeDD\3default - 1.bmp | image | |
MD5:14A455E9EEF9FE7FEA4DE14D579A3E84 | SHA256:B666E6BD71EFF3547FB2F5580AC61C64527F6F9BE6A2178FA00F80E32431460A | |||
| 7132 | KMSPico 10.2.1.exe | C:\Users\admin\AppData\Local\Temp\genteert.dll | executable | |
MD5:6CE814FD1AD7AE07A9E462C26B3A0F69 | SHA256:54C0DA1735BB1CB02B60C321DE938488345F8D1D26BF389C8CB2ACAD5D01B831 | |||
| 4488 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 7132 | KMSPico 10.2.1.exe | C:\Program Files (x86)\KMSPico 10.2.1 Final\KMSPicoActivator.exe | executable | |
MD5:282CAC754134BE86386102A3831A60FD | SHA256:D56830E43A2396498F49D6E023B82FEB119A266DB61006EBD71A56ADA281508A | |||
| 7132 | KMSPico 10.2.1.exe | C:\Program Files (x86)\KMSPico 10.2.1 Final\Registry_Activation.exe | executable | |
MD5:22DC19D8A8BB223D650267FD7B76C122 | SHA256:34EA753EB0EBD2018851ECAFFDB7269F3681CD93D2B56F1563D175FBA0693C1F | |||
| 7132 | KMSPico 10.2.1.exe | C:\Users\admin\AppData\Local\Temp\genteeDD\guig.dll | executable | |
MD5:D3F8C0334C19198A109E44D074DAC5FD | SHA256:005C251C21D6A5BA1C3281E7B9F3B4F684D007E0C3486B34A545BB370D8420AA | |||
| 3832 | Registry_Activation.exe | C:\Users\admin\AppData\Local\Temp\inH129382848921\css\sdk-ui\browse.css | text | |
MD5:6009D6E864F60AEA980A9DF94C1F7E1C | SHA256:5EF48A8C8C3771B4F233314D50DD3B5AFDCD99DD4B74A9745C8FE7B22207056D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
37
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.19.198.194:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5000 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5000 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6700 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5112 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5112 | WerFault.exe | GET | 200 | 23.32.238.34:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.19.198.194:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.178:443 | — | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1076 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
empty.townbeef.bid |
| whitelisted |
gold.apparelflesh.bid |
| unknown |
rp.tadanadanet.com |
| unknown |
info.tadanadanet.com |
| unknown |