| File name: | 97DB5ED9FB98B6138F0D2889531BD5CC.exe |
| Full analysis: | https://app.any.run/tasks/1f081bac-d858-4adc-8c30-aa2ac1455382 |
| Verdict: | Malicious activity |
| Threats: | A backdoor is a type of cybersecurity threat that allows attackers to secretly compromise a system and conduct malicious activities, such as stealing data and modifying files. Backdoors can be difficult to detect, as they often use legitimate system applications to evade defense mechanisms. Threat actors often utilize special malware, such as PlugX, to establish backdoors on target devices. |
| Analysis date: | July 31, 2025, 14:47:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | 97DB5ED9FB98B6138F0D2889531BD5CC |
| SHA1: | 81559C3A1054F03C2D513010AA11A5167AD8F94E |
| SHA256: | 3321374DB373AD39679DE606EC29CF5EBE34CE632D8D2DD0C1C2988C07661B84 |
| SSDEEP: | 98304:VLVIF8P3n1BLHxtD59KEKjSvDKgpmR1nRULCjZiJlReaY1947r54F+6dd9snUQaL:nKgyGBG9hWqDlU+C4 |
MALICIOUS
Adds path to the Windows Defender exclusion list
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
Changes Windows Defender settings
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
Uses Task Scheduler to autorun other applications
- powershell.exe (PID: 1808)
Connects to the CnC server
- Update.exe (PID: 2324)
Changes the autorun value in the registry
- setup.exe (PID: 4832)
SILVERFOX has been detected (SURICATA)
- Update.exe (PID: 2324)
WINOS has been detected (YARA)
- Update.exe (PID: 2324)
SUSPICIOUS
Reads security settings of Internet Explorer
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 1392)
- updater.exe (PID: 3672)
Reads the Windows owner or organization settings
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
Executable content was dropped or overwritten
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 2388)
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 5716)
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
- updater.exe (PID: 3672)
- updater.exe (PID: 2808)
- setup.exe (PID: 4832)
- 138.0.7204.184_chrome_installer_uncompressed.exe (PID: 2228)
- updater.exe (PID: 7264)
- updater.exe (PID: 2964)
Process drops legitimate windows executable
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
The process drops C-runtime libraries
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
Starts POWERSHELL.EXE for commands execution
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
Script adds exclusion path to Windows Defender
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
Application launched itself
- updater.exe (PID: 2808)
- updater.exe (PID: 3672)
- updater.exe (PID: 1496)
- setup.exe (PID: 4832)
- setup.exe (PID: 2192)
- updater.exe (PID: 7264)
- updater.exe (PID: 2964)
Executes as Windows Service
- updater.exe (PID: 1496)
- updater.exe (PID: 2808)
- updater.exe (PID: 7264)
There is functionality for taking screenshot (YARA)
- Update.exe (PID: 2324)
Contacting a server suspected of hosting an CnC
- Update.exe (PID: 2324)
Searches for installed software
- setup.exe (PID: 4832)
Creates a software uninstall entry
- setup.exe (PID: 4832)
INFO
Create files in a temporary directory
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 5716)
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 2388)
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
- ChromeSetup.exe (PID: 3388)
- updater.exe (PID: 3672)
Reads the computer name
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 1392)
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 2388)
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
- ChromeSetup.exe (PID: 3388)
- updater.exe (PID: 2808)
- Update.exe (PID: 2324)
- updater.exe (PID: 3672)
- updater.exe (PID: 1496)
- 138.0.7204.184_chrome_installer_uncompressed.exe (PID: 2228)
- setup.exe (PID: 4832)
- setup.exe (PID: 2192)
- updater.exe (PID: 7264)
- elevation_service.exe (PID: 5884)
- updater.exe (PID: 2964)
- identity_helper.exe (PID: 3572)
Process checks computer location settings
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 1392)
Checks supported languages
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 5716)
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 1392)
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 2388)
- Client.exe (PID: 3556)
- ChromeSetup.exe (PID: 3388)
- Update.exe (PID: 2324)
- updater.exe (PID: 2808)
- updater.exe (PID: 1880)
- updater.exe (PID: 3672)
- updater.exe (PID: 856)
- updater.exe (PID: 4916)
- updater.exe (PID: 1496)
- setup.exe (PID: 1392)
- setup.exe (PID: 2192)
- 138.0.7204.184_chrome_installer_uncompressed.exe (PID: 2228)
- setup.exe (PID: 4832)
- setup.exe (PID: 5184)
- updater.exe (PID: 7268)
- updater.exe (PID: 7264)
- elevation_service.exe (PID: 5884)
- updater.exe (PID: 2964)
- UpdaterSetup.exe (PID: 6068)
- updater.exe (PID: 6572)
- identity_helper.exe (PID: 3572)
Creates files in the program directory
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
- updater.exe (PID: 3672)
- updater.exe (PID: 2808)
- updater.exe (PID: 856)
- updater.exe (PID: 1496)
- setup.exe (PID: 4832)
- setup.exe (PID: 2192)
- updater.exe (PID: 7264)
- updater.exe (PID: 2964)
- updater.exe (PID: 6572)
The sample compiled with english language support
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 7040)
- updater.exe (PID: 3672)
- updater.exe (PID: 2808)
- 138.0.7204.184_chrome_installer_uncompressed.exe (PID: 2228)
- setup.exe (PID: 4832)
- updater.exe (PID: 7264)
- updater.exe (PID: 2964)
Compiled with Borland Delphi (YARA)
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 5716)
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 1392)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6680)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6680)
Detects InnoSetup installer (YARA)
- 97DB5ED9FB98B6138F0D2889531BD5CC.exe (PID: 5716)
- 97DB5ED9FB98B6138F0D2889531BD5CC.tmp (PID: 1392)
Process checks whether UAC notifications are on
- updater.exe (PID: 3672)
- updater.exe (PID: 2808)
- updater.exe (PID: 1496)
- updater.exe (PID: 7264)
- updater.exe (PID: 2964)
Checks proxy server information
- updater.exe (PID: 3672)
- slui.exe (PID: 3960)
Reads the software policy settings
- updater.exe (PID: 1496)
- updater.exe (PID: 3672)
- updater.exe (PID: 7264)
- slui.exe (PID: 3960)
Creates files or folders in the user directory
- updater.exe (PID: 3672)
Reads Environment values
- Update.exe (PID: 2324)
- identity_helper.exe (PID: 3572)
Reads the machine GUID from the registry
- updater.exe (PID: 3672)
Reads product name
- Update.exe (PID: 2324)
Launching a file from a Registry key
- setup.exe (PID: 4832)
Application launched itself
- chrome.exe (PID: 3460)
- chrmstp.exe (PID: 4172)
- chrmstp.exe (PID: 3576)
- msedge.exe (PID: 1288)
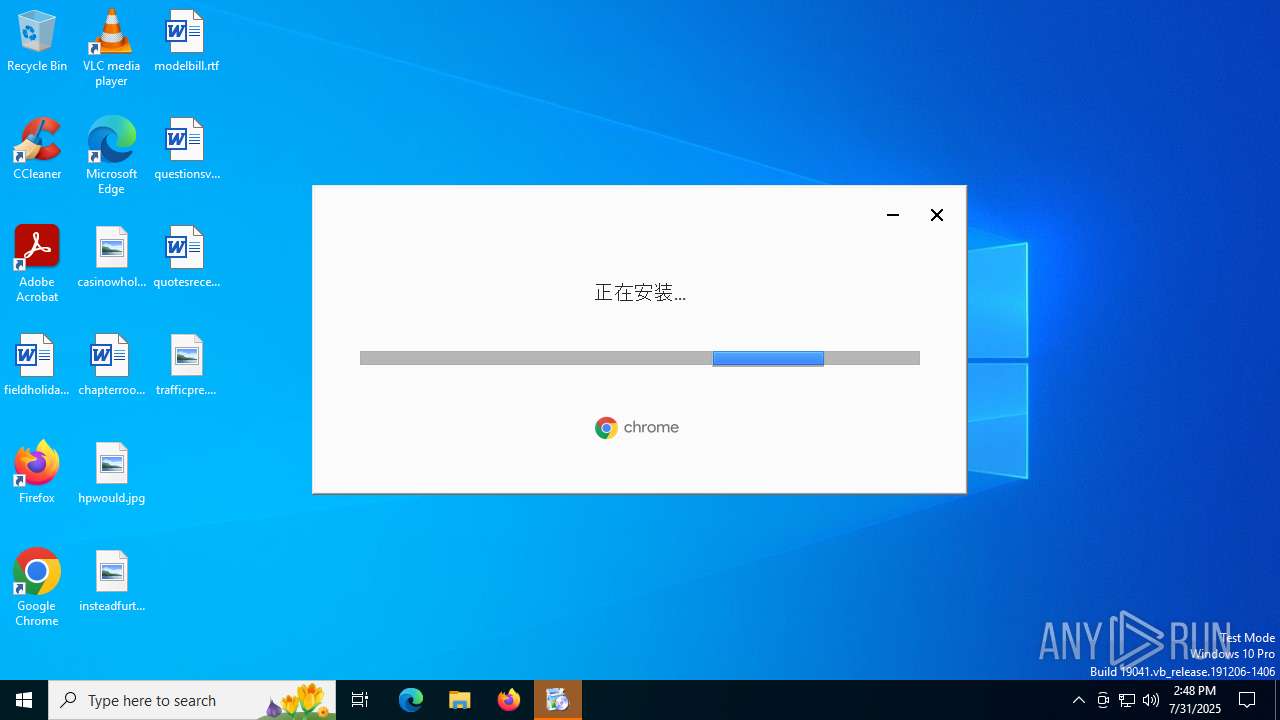
Manual execution by a user
- chrome.exe (PID: 3460)
- chrmstp.exe (PID: 4172)
- msedge.exe (PID: 1288)
- msedge.exe (PID: 6068)
Executes as Windows Service
- elevation_service.exe (PID: 5884)
Connects to unusual port
- chrome.exe (PID: 3476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:03 14:45:36+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 704512 |
| InitializedDataSize: | 116736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xacfe0 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.6.0 |
| ProductVersionNumber: | 3.2.6.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Chrome Setup |
| FileVersion: | 3.2.6.0 |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | |
| ProductVersion: | 3.2.6.0 |
Total processes
242
Monitored processes
101
Malicious processes
9
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | C:\Users\admin\AppData\Local\Temp\Google3388_807764974\bin\updater.exe --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\138.0.7194.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=138.0.7194.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x2b0,0x2b4,0x2b8,0x28c,0x2bc,0x7f29c0,0x7f29cc,0x7f29d8 | C:\Users\admin\AppData\Local\Temp\Google3388_807764974\bin\updater.exe | — | updater.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Updater (x86) Exit code: 0 Version: 138.0.7194.0 Modules
| |||||||||||||||
| 952 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --always-read-main-dll --field-trial-handle=4024,i,10243021390708086958,8465868640782672011,262144 --variations-seed-version --mojo-platform-channel-handle=6864 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 984 | "C:\WINDOWS\system32\schtasks.exe" /create /rl HIGHEST /sc ONLOGON /tn frthyr /tr C:\ProgramData\frthyr\Client.exe | C:\Windows\SysWOW64\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6784,i,10243021390708086958,8465868640782672011,262144 --variations-seed-version --mojo-platform-channel-handle=1660 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1100 | "powershell.exe" Copy-Item -Path C:\ProgramData\frthyr\data.bin -Destination C:\WINDOWS\System32\data.bin | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc40bcf208,0x7ffc40bcf214,0x7ffc40bcf220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --force-high-res-timeticks=disabled --field-trial-handle=1956,i,6998996897099980461,12341122561171660384,262144 --variations-seed-version --mojo-platform-channel-handle=5916 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 138.0.7204.184 Modules
| |||||||||||||||
| 1288 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" https://www.google.com/chrome/go-mobile/?campaign=desktop-chr-whats-new | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1392 | "C:\Users\admin\AppData\Local\Temp\is-INA71.tmp\97DB5ED9FB98B6138F0D2889531BD5CC.tmp" /SL5="$902DA,9751048,822272,C:\Users\admin\AppData\Local\Temp\97DB5ED9FB98B6138F0D2889531BD5CC.exe" | C:\Users\admin\AppData\Local\Temp\is-INA71.tmp\97DB5ED9FB98B6138F0D2889531BD5CC.tmp | — | 97DB5ED9FB98B6138F0D2889531BD5CC.exe | |||||||||||
User: admin Company: frthyr Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1392 | C:\WINDOWS\SystemTemp\chrome_Unpacker_BeginUnzipping1496_581353033\CR_E884F.tmp\setup.exe --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\WINDOWS\SystemTemp\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=138.0.7204.184 --initial-client-data=0x29c,0x2a0,0x2a4,0x278,0x2a8,0x7ff63cfa85a0,0x7ff63cfa85ac,0x7ff63cfa85b8 | C:\Windows\SystemTemp\chrome_Unpacker_BeginUnzipping1496_581353033\CR_E884F.tmp\setup.exe | — | setup.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Chrome Installer Exit code: 0 Version: 138.0.7204.184 Modules
| |||||||||||||||
Total events
39 885
Read events
39 665
Write events
207
Delete events
13
Modification events
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\Clients\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | pv |
Value: 138.0.7194.0 | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\Clients\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | name |
Value: GoogleUpdater | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientState\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | pv |
Value: 138.0.7194.0 | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientState\{44fc7fe2-65ce-487c-93f4-edee46eeaaab} |
| Operation: | write | Name: | name |
Value: GoogleUpdater | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\CLSID\{4A8EC270-ECA5-51BC-A8AB-551ED6D0CA26} |
| Operation: | write | Name: | AppID |
Value: {4A8EC270-ECA5-51BC-A8AB-551ED6D0CA26} | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{4A8EC270-ECA5-51BC-A8AB-551ED6D0CA26} |
| Operation: | write | Name: | LocalService |
Value: GoogleUpdaterInternalService138.0.7194.0 | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{4A8EC270-ECA5-51BC-A8AB-551ED6D0CA26} |
| Operation: | write | Name: | ServiceParameters |
Value: --com-service | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{D12C0CB6-7717-5083-8874-A3C30BB3C374}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{D12C0CB6-7717-5083-8874-A3C30BB3C374}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (3672) updater.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{48D40B89-9B8C-53BE-9B9E-BEB2AD53DE28}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
Executable files
28
Suspicious files
451
Text files
140
Unknown types
45
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7040 | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | C:\ProgramData\frthyr\ChromeSetup.exe | executable | |
MD5:EE4551ABD48DD3CFE70AFA78DA142123 | SHA256:30F3C9C54502A814099607F3FA1A9131DE8C3D305552CF8F08CF5EE942F093C0 | |||
| 2388 | 97DB5ED9FB98B6138F0D2889531BD5CC.exe | C:\Users\admin\AppData\Local\Temp\is-FOKQF.tmp\97DB5ED9FB98B6138F0D2889531BD5CC.tmp | executable | |
MD5:FEFEA09401E20AD60C58104E14D3677A | SHA256:53A57065C9BEBBA2A69C28BC193E310A4D28434BBFEDB1FC7298A8629FB1D416 | |||
| 5716 | 97DB5ED9FB98B6138F0D2889531BD5CC.exe | C:\Users\admin\AppData\Local\Temp\is-INA71.tmp\97DB5ED9FB98B6138F0D2889531BD5CC.tmp | executable | |
MD5:FEFEA09401E20AD60C58104E14D3677A | SHA256:53A57065C9BEBBA2A69C28BC193E310A4D28434BBFEDB1FC7298A8629FB1D416 | |||
| 7040 | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | C:\ProgramData\frthyr\is-O843D.tmp | executable | |
MD5:F4F0700B824AB6EB927282973E0A417F | SHA256:6344390FDC19C10A68CEF29AB1EB733D0ECFB9C883B195BE47FC37C07766149A | |||
| 7040 | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | C:\ProgramData\frthyr\is-POUSD.tmp | executable | |
MD5:EE4551ABD48DD3CFE70AFA78DA142123 | SHA256:30F3C9C54502A814099607F3FA1A9131DE8C3D305552CF8F08CF5EE942F093C0 | |||
| 7040 | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | C:\ProgramData\frthyr\Client.exe | executable | |
MD5:F4F0700B824AB6EB927282973E0A417F | SHA256:6344390FDC19C10A68CEF29AB1EB733D0ECFB9C883B195BE47FC37C07766149A | |||
| 7040 | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | C:\ProgramData\frthyr\is-66P4P.tmp | gpg | |
MD5:B7BF3C7C9E9B3A5738A9DA8601189DE8 | SHA256:C60E69CA233619F0E683C2DBB9F936095F0B84B467F82682F1F04CC3418D3215 | |||
| 7040 | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | C:\ProgramData\frthyr\is-L4H2Q.tmp | image | |
MD5:8FB05F27C2C8BD5096B83C1E3E4E5932 | SHA256:0FFC598DEEFA457344C9DB196470A9AA01834179F2670FFB0BF4166F9A8A3F05 | |||
| 7040 | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | C:\Users\admin\AppData\Local\Temp\is-2GLDA.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7040 | 97DB5ED9FB98B6138F0D2889531BD5CC.tmp | C:\ProgramData\frthyr\is-JRO6E.tmp | executable | |
MD5:F4F0700B824AB6EB927282973E0A417F | SHA256:6344390FDC19C10A68CEF29AB1EB733D0ECFB9C883B195BE47FC37C07766149A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
144
DNS requests
150
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1864 | svchost.exe | GET | 200 | 104.78.173.167:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | GB | binary | 471 b | whitelisted |
3656 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
3656 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
7264 | updater.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/%7B44fc7fe2-65ce-487c-93f4-edee46eeaaab%7D/e7d95a0cfbd762c8ada8f3788efdd6e79a086cc85e849d6bc9cc4e5e32170c77 | US | — | — | whitelisted |
3476 | chrome.exe | GET | 200 | 142.250.186.174:80 | http://clients2.google.com/time/1/current?cup2key=9:cbwFALHgI2pSLem5E4ADRg3ZogY73d8Cg3-G6EvIKnY&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 105 b | whitelisted |
7540 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:7NOcVumFn_xo-EC6j26yKKYWb1bpFSQ0iCMc7iziaYw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 98 b | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
6228 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/niikhdgajlphfehepabhhblakbdgeefj/97b4e68a7a79ae5be44033dbc869b57b36884d4ba50887521547c98b08363638 | US | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6388 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1864 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1864 | svchost.exe | 104.78.173.167:80 | ocsp.digicert.com | AKAMAI-AS | GB | whitelisted |
1268 | svchost.exe | 23.216.77.17:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2324 | Update.exe | 103.105.23.130:443 | wps.preech.top | Cloudie Limited | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
wps.preech.top |
| malicious |
update.googleapis.com |
| whitelisted |
dl.google.com |
| whitelisted |
c.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2324 | Update.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework CnC Login Message |
2324 | Update.exe | Malware Command and Control Activity Detected | BACKDOOR [ANY.RUN] SilverFox Keep-Alive Client Packet |
2324 | Update.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework CnC Login Message CnC Server Response |
2324 | Update.exe | Malware Command and Control Activity Detected | BACKDOOR [ANY.RUN] SilverFox Keep-Alive Client Packet |
2324 | Update.exe | Malware Command and Control Activity Detected | BACKDOOR [ANY.RUN] SilverFox Keep-Alive Client Packet |
2324 | Update.exe | Malware Command and Control Activity Detected | BACKDOOR [ANY.RUN] SilverFox Keep-Alive Client Packet |
2324 | Update.exe | Malware Command and Control Activity Detected | BACKDOOR [ANY.RUN] SilverFox Keep-Alive Client Packet |
3476 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3476 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
chrome.exe | I0000 00:00:1753973332.802772 2124 voice_transcription.cc:58] Registering VoiceTranscriptionCapability
|