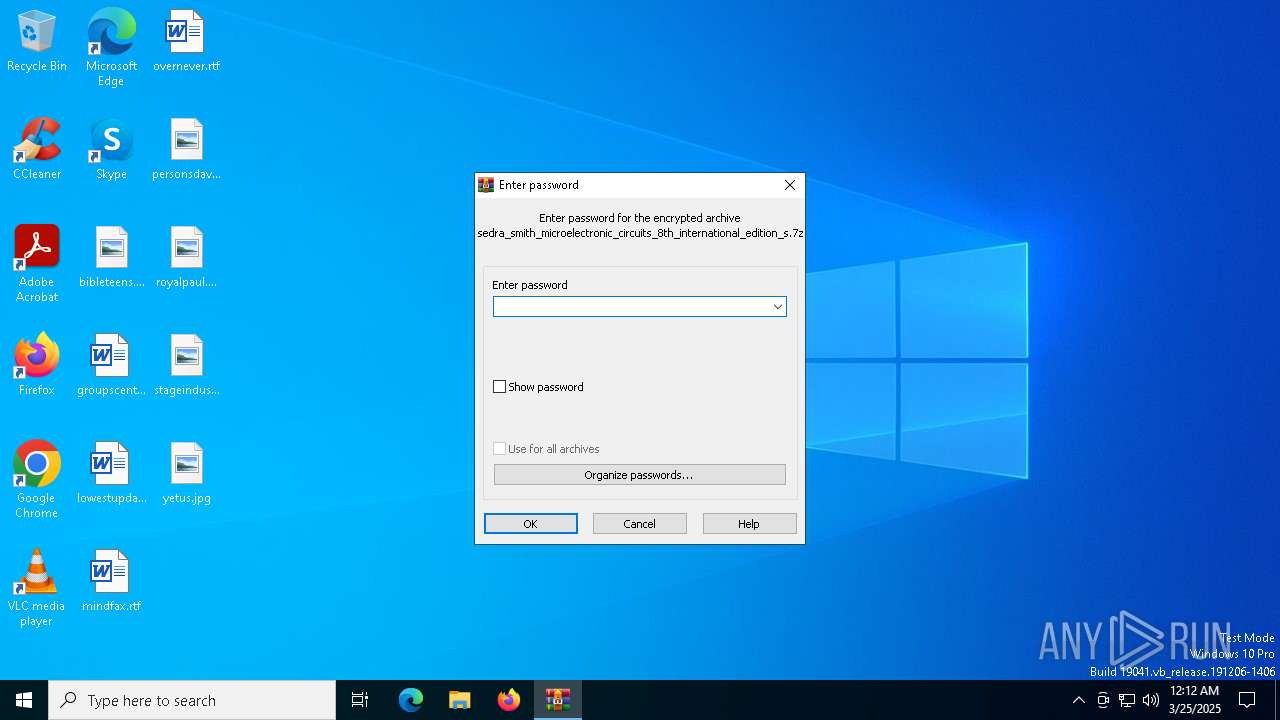
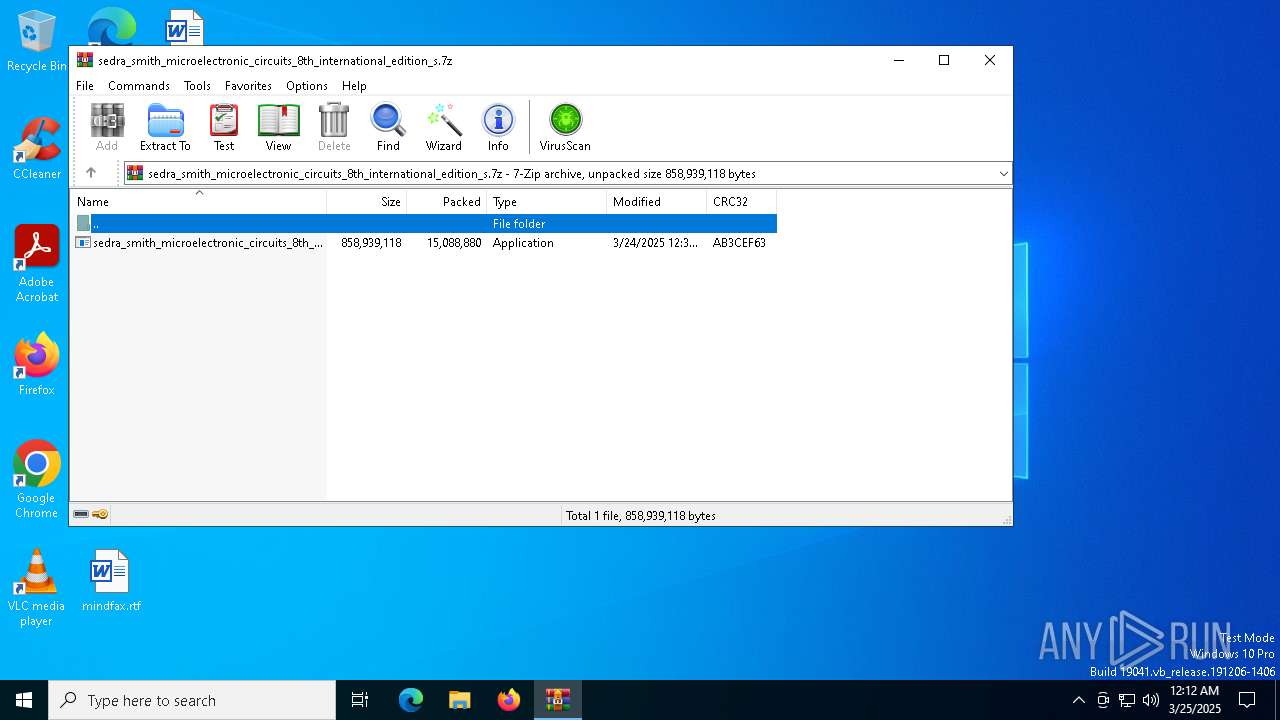
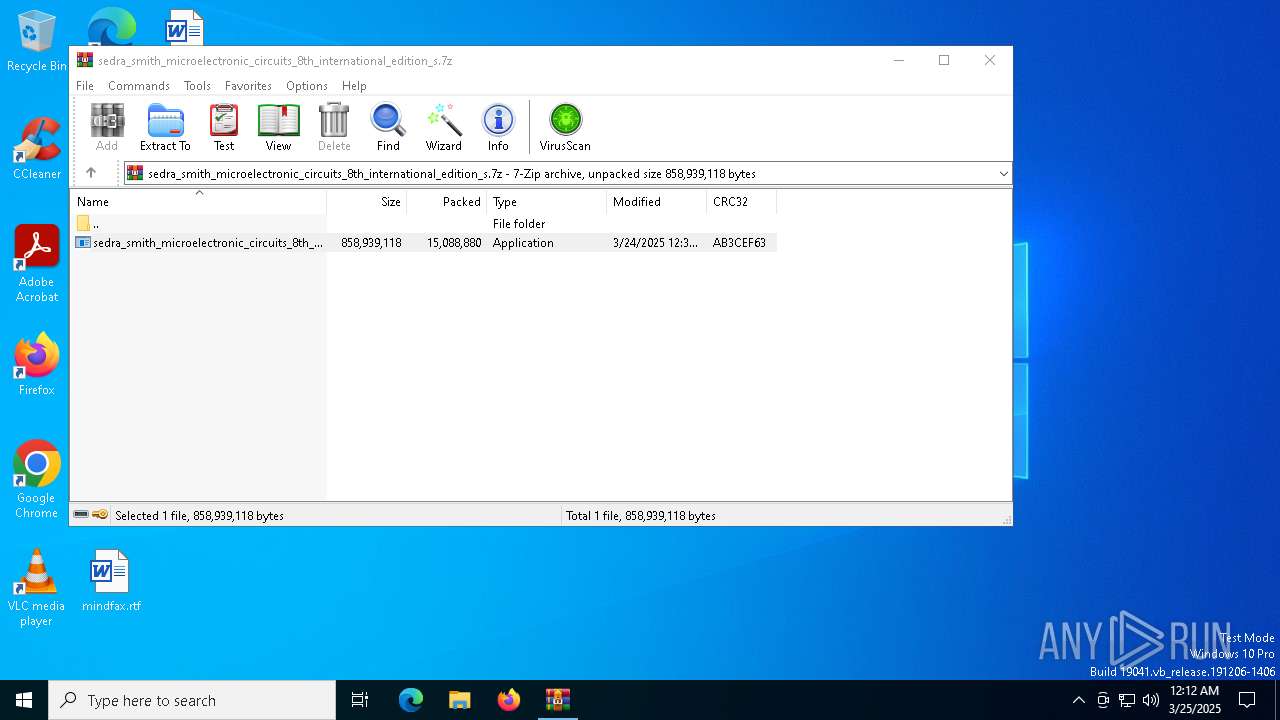
| File name: | sedra_smith_microelectronic_circuits_8th_international_edition_s.7z |
| Full analysis: | https://app.any.run/tasks/8c93bba5-6da8-4952-90df-c8ce5b86978d |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | March 25, 2025, 00:12:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 5DE3AC8D97A543F5F41F50A9DDB36814 |
| SHA1: | CE9B0C3F1FF34C94052EEC59D28408507C428A11 |
| SHA256: | 32C7D588294A79BE6C2009289C7795B8189D386F34FDE3FBC56EF4DCE2F6D309 |
| SSDEEP: | 98304:jeuZSAw/6il3c3rwbrRx38SvD43Pr0t7CQkS9DQX/yowwCZuSc558b35Rqp5E4Zb:YqUqFyzS+cv0WuNsR829LJfZuFV6Br7 |
MALICIOUS
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- Alter.com (PID: 8040)
Actions looks like stealing of personal data
- Alter.com (PID: 8040)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- Alter.com (PID: 8040)
Steals credentials from Web Browsers
- Alter.com (PID: 8040)
AutoIt loader has been detected (YARA)
- Alter.com (PID: 8040)
SUSPICIOUS
Reads security settings of Internet Explorer
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
Starts CMD.EXE for commands execution
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
- cmd.exe (PID: 7636)
Executing commands from a ".bat" file
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
Get information on the list of running processes
- cmd.exe (PID: 7636)
Application launched itself
- cmd.exe (PID: 7636)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7636)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7636)
The executable file from the user directory is run by the CMD process
- Alter.com (PID: 8040)
Starts application with an unusual extension
- cmd.exe (PID: 7636)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- Alter.com (PID: 8040)
There is functionality for taking screenshot (YARA)
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
- Alter.com (PID: 8040)
Searches for installed software
- Alter.com (PID: 8040)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4136)
INFO
Reads the computer name
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
- extrac32.exe (PID: 7928)
- Alter.com (PID: 8040)
- identity_helper.exe (PID: 7720)
- PLUGScheduler.exe (PID: 4136)
Checks supported languages
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
- extrac32.exe (PID: 7928)
- Alter.com (PID: 8040)
- PLUGScheduler.exe (PID: 4136)
- identity_helper.exe (PID: 7720)
Process checks computer location settings
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
Create files in a temporary directory
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
- extrac32.exe (PID: 7928)
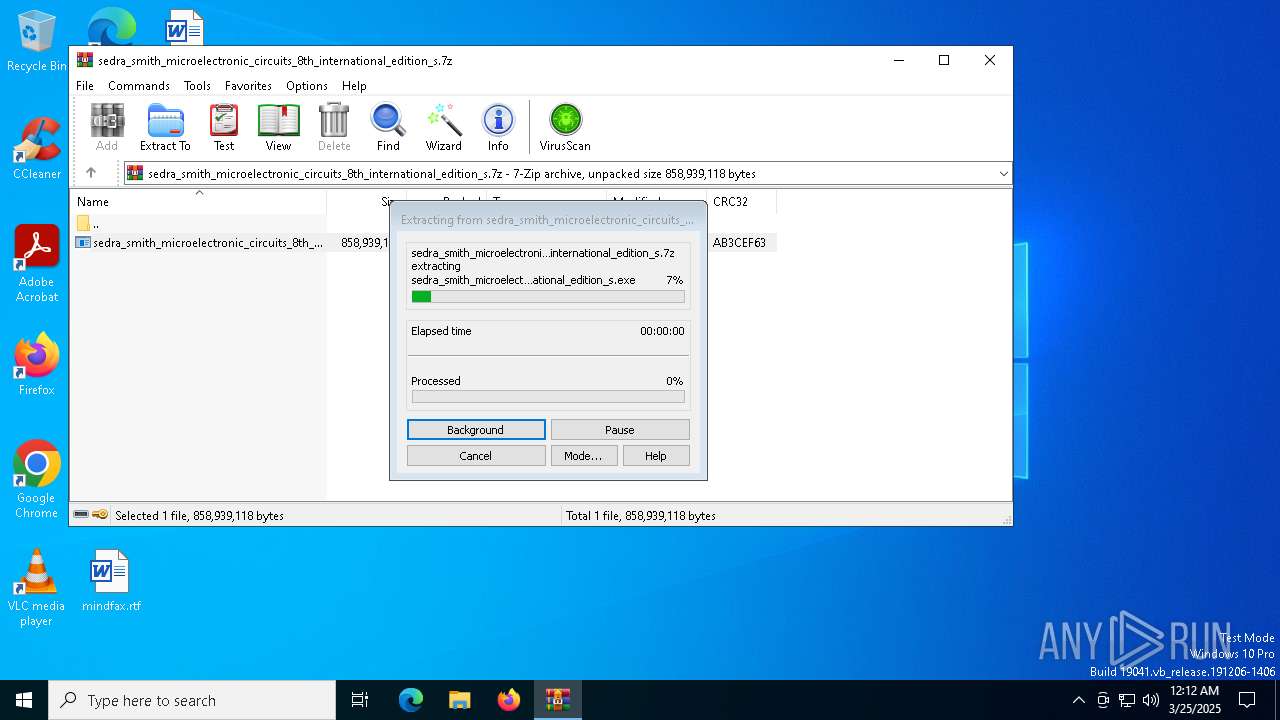
Manual execution by a user
- sedra_smith_microelectronic_circuits_8th_international_edition_s.exe (PID: 7552)
- msedge.exe (PID: 7180)
Creates a new folder
- cmd.exe (PID: 7904)
Reads the software policy settings
- Alter.com (PID: 8040)
- slui.exe (PID: 1272)
- slui.exe (PID: 7000)
Application launched itself
- msedge.exe (PID: 7180)
- msedge.exe (PID: 5972)
Reads Environment values
- identity_helper.exe (PID: 7720)
Checks proxy server information
- slui.exe (PID: 7000)
The sample compiled with english language support
- msedge.exe (PID: 5964)
Executable content was dropped or overwritten
- msedge.exe (PID: 5964)
Reads mouse settings
- Alter.com (PID: 8040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
313
Monitored processes
64
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6056 --field-trial-handle=2292,i,7581730410044387150,10333487763352743235,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4180 --field-trial-handle=2292,i,7581730410044387150,10333487763352743235,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 720 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2624 --field-trial-handle=2360,i,2669191824799184291,13357396772631536175,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6116 --field-trial-handle=2292,i,7581730410044387150,10333487763352743235,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3476 --field-trial-handle=2360,i,2669191824799184291,13357396772631536175,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4164 --field-trial-handle=2292,i,7581730410044387150,10333487763352743235,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1272 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --instant-process --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3560 --field-trial-handle=2360,i,2669191824799184291,13357396772631536175,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=3772 --field-trial-handle=2292,i,7581730410044387150,10333487763352743235,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
10 730
Read events
10 684
Write events
46
Delete events
0
Modification events
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sedra_smith_microelectronic_circuits_8th_international_edition_s.7z | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
39
Suspicious files
621
Text files
150
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb6620.37876\sedra_smith_microelectronic_circuits_8th_international_edition_s.exe | — | |
MD5:— | SHA256:— | |||
| 7928 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Magazine | binary | |
MD5:6789F277D37FD128BA994EC581C2D5A6 | SHA256:E932B6D893E9E979D5F0538D9C0C7B747F0A875101E18C404A2D6218C326843B | |||
| 7928 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Processors | binary | |
MD5:1DEB88D41D2F65D74A7CF8D4831D1CA0 | SHA256:CA1E822FF9BFD20B8EBE15396D9E1EF07A36AE7F39C25077AC9EE60C163CD593 | |||
| 7928 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Mechanics | binary | |
MD5:7EF9AE85DD74D250E634C9E48AE7F851 | SHA256:A991E2C521060A39A2011C201579EEECD3557A515A0A17805954EBCF4F05735A | |||
| 7928 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Wondering | binary | |
MD5:5600D0BB573CEBA44AFDFFCA88BCCD0F | SHA256:08AEC7084A77C3BEBBA37EA2665DDEF072C9FD77264F51F823964F483FDA813C | |||
| 7552 | sedra_smith_microelectronic_circuits_8th_international_edition_s.exe | C:\Users\admin\AppData\Local\Temp\Tales.xltm | text | |
MD5:77FD0F7861D606A4AA93E3945C23C9B8 | SHA256:B89487FCF123C688AB5C509116CD77018287451A053DE473B4D576385ACC0FA5 | |||
| 7928 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Know | binary | |
MD5:EE39409E4CCDFC1832E8ACC68565A2A4 | SHA256:6151DFD69FAC8EE2E4B46E7CB19C5284CE626E5E1E8B746B28C46217BB2332CB | |||
| 7552 | sedra_smith_microelectronic_circuits_8th_international_edition_s.exe | C:\Users\admin\AppData\Local\Temp\Enhancement.xltm | binary | |
MD5:321B7DEE2EF299DCC443E4EE59609E4B | SHA256:E05192FB4052DE63FFA5F1C536D20BA55A1BFF7BA0790E3AB68DC5AC9E22F60B | |||
| 7552 | sedra_smith_microelectronic_circuits_8th_international_edition_s.exe | C:\Users\admin\AppData\Local\Temp\Martial.xltm | binary | |
MD5:196AD2DF8D2AFF243F11197FCF3DFC12 | SHA256:F92692BC79D7AB36BC4D97425A07E8A5CCC27A7D612CA7730EC687B7A9084E05 | |||
| 7552 | sedra_smith_microelectronic_circuits_8th_international_edition_s.exe | C:\Users\admin\AppData\Local\Temp\Yea.xltm | compressed | |
MD5:FC64D73B3C09DD9040E11A1B566791CA | SHA256:19570E853515FF94F943782713DC6F13CD9280AE204C21E8D0C32D3CEE31C570 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
105
DNS requests
118
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3100 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7808 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7808 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7396 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742973156&P2=404&P3=2&P4=DGh0vRyDDGiF%2buHmUBWfHFotlJo62%2f%2b8vm1GxNqu2v3%2fMa7oC2DFUpmStt4VAG79v4o1jD3BbDRGh%2bgOhPYCvQ%3d%3d | unknown | — | — | whitelisted |
7396 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742973156&P2=404&P3=2&P4=DGh0vRyDDGiF%2buHmUBWfHFotlJo62%2f%2b8vm1GxNqu2v3%2fMa7oC2DFUpmStt4VAG79v4o1jD3BbDRGh%2bgOhPYCvQ%3d%3d | unknown | — | — | whitelisted |
7396 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742973156&P2=404&P3=2&P4=DGh0vRyDDGiF%2buHmUBWfHFotlJo62%2f%2b8vm1GxNqu2v3%2fMa7oC2DFUpmStt4VAG79v4o1jD3BbDRGh%2bgOhPYCvQ%3d%3d | unknown | — | — | whitelisted |
7396 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742973156&P2=404&P3=2&P4=DGh0vRyDDGiF%2buHmUBWfHFotlJo62%2f%2b8vm1GxNqu2v3%2fMa7oC2DFUpmStt4VAG79v4o1jD3BbDRGh%2bgOhPYCvQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3100 | backgroundTaskHost.exe | 20.223.36.55:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (travewlio .shop) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (esccapewz .run) |
8040 | Alter.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (travewlio .shop in TLS SNI) |
8040 | Alter.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (travewlio .shop in TLS SNI) |
8040 | Alter.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (travewlio .shop in TLS SNI) |
8040 | Alter.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (travewlio .shop in TLS SNI) |
8040 | Alter.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (travewlio .shop in TLS SNI) |
8040 | Alter.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (travewlio .shop in TLS SNI) |
8040 | Alter.com | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (travewlio .shop in TLS SNI) |