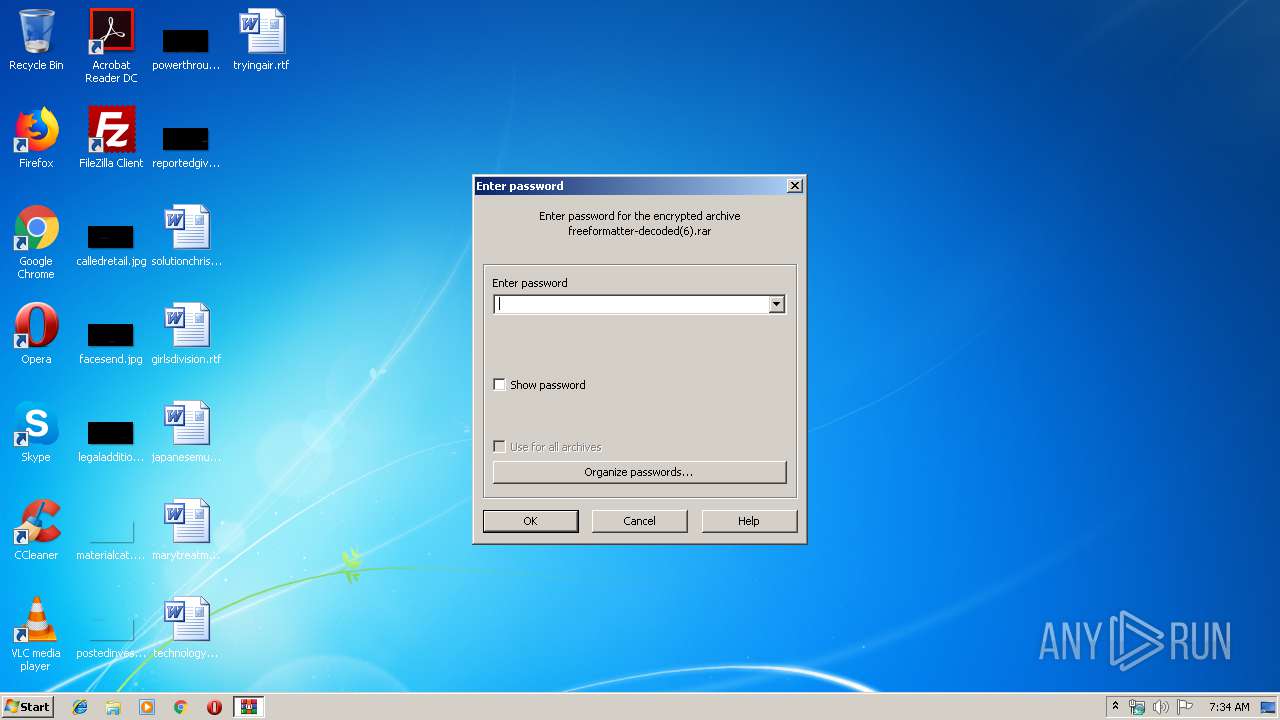
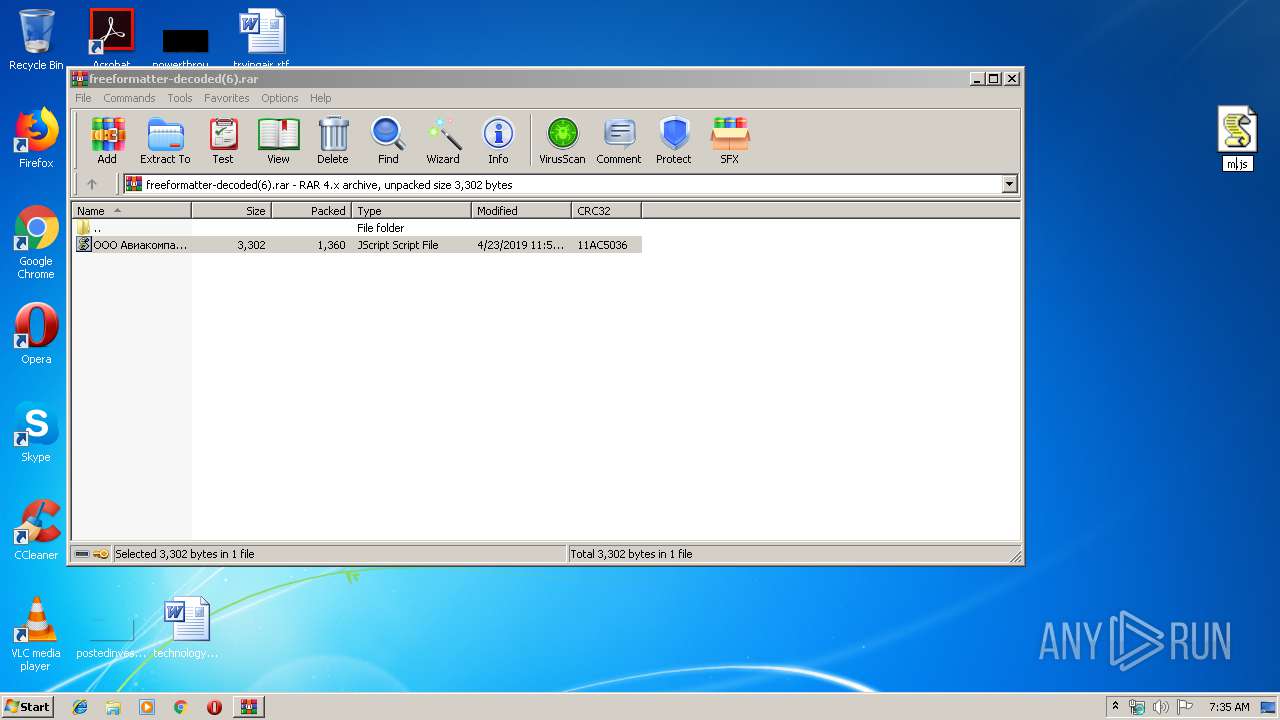
| File name: | freeformatter-decoded(6).rar |
| Full analysis: | https://app.any.run/tasks/0ae82b1e-b47e-4bc2-a3d5-9bf3b955b59d |
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
| Analysis date: | April 24, 2019, 06:34:34 |
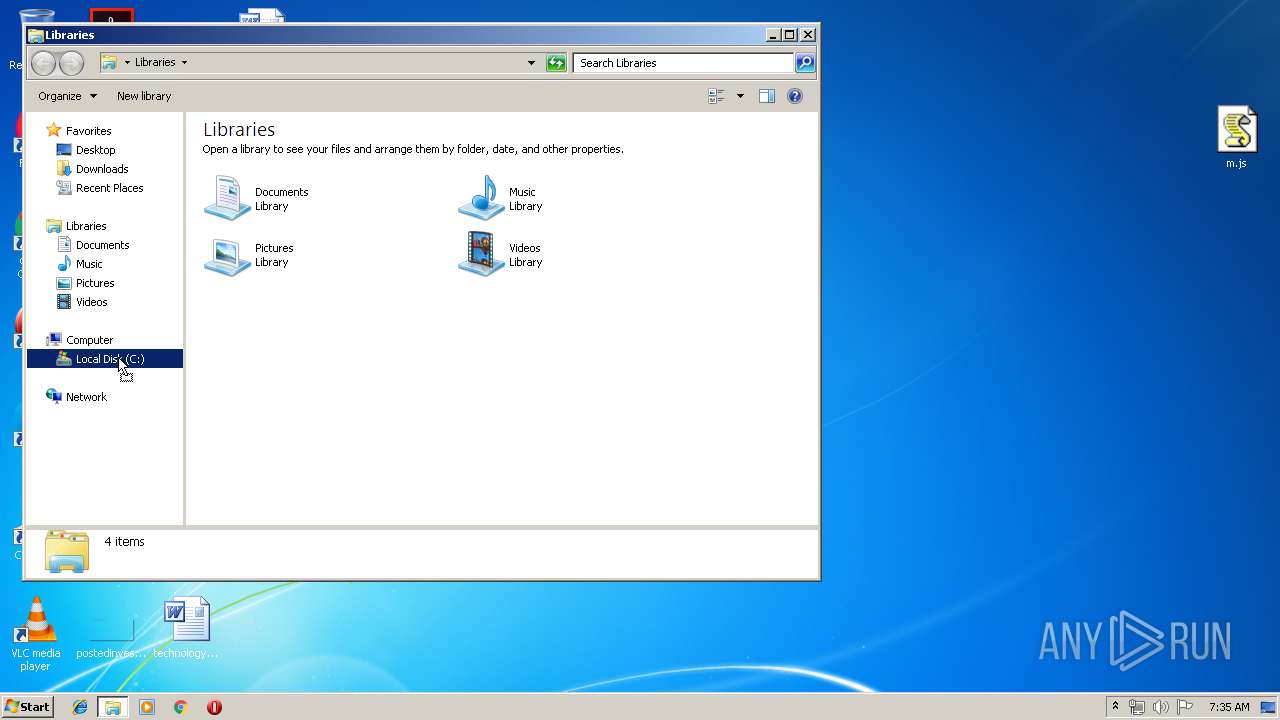
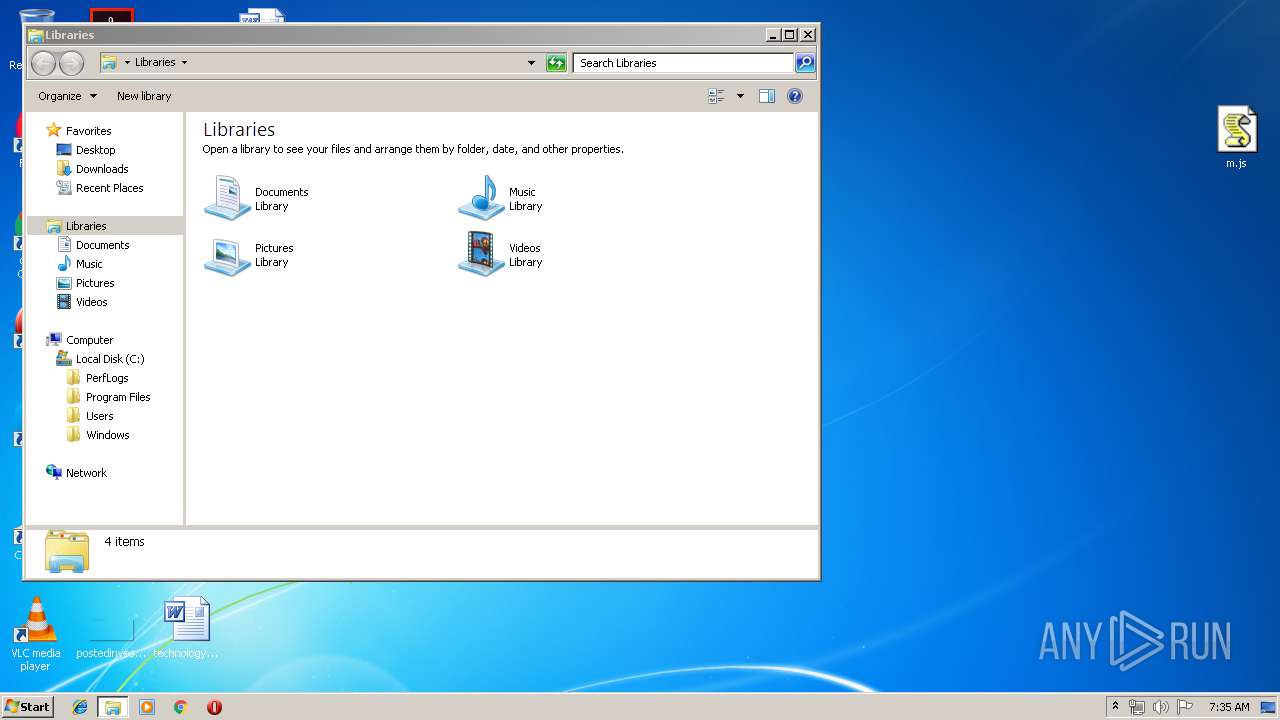
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, flags: EncryptedBlockHeader |
| MD5: | AEC597C054E18AC6FAABACDC6E3E43EA |
| SHA1: | 7EDEC9DD1FB9B11B9C73488F3AC2E4A3A20C7D8D |
| SHA256: | 32A0F4A9ED4CBB4F2A06EBA371A62B22B06059CAF3C396615A68B8CD1A2F7253 |
| SSDEEP: | 48:d7L4e2p6WFfxu9uq1oLlev/8Q8LfHMS34:d7L4ZvuLoLlSUQ8LP4 |
MALICIOUS
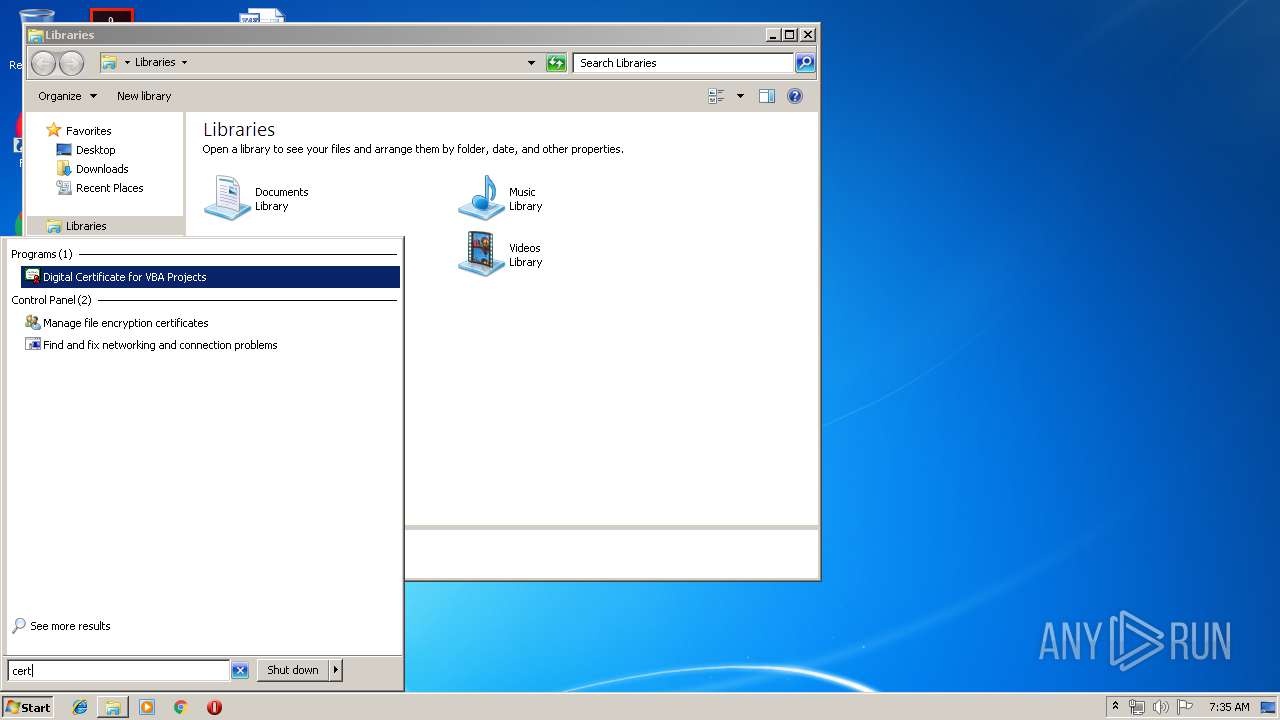
Changes settings of System certificates
- WScript.exe (PID: 2540)
Actions looks like stealing of personal data
- radB6D08.tmp (PID: 4028)
Modifies files in Chrome extension folder
- radB6D08.tmp (PID: 4028)
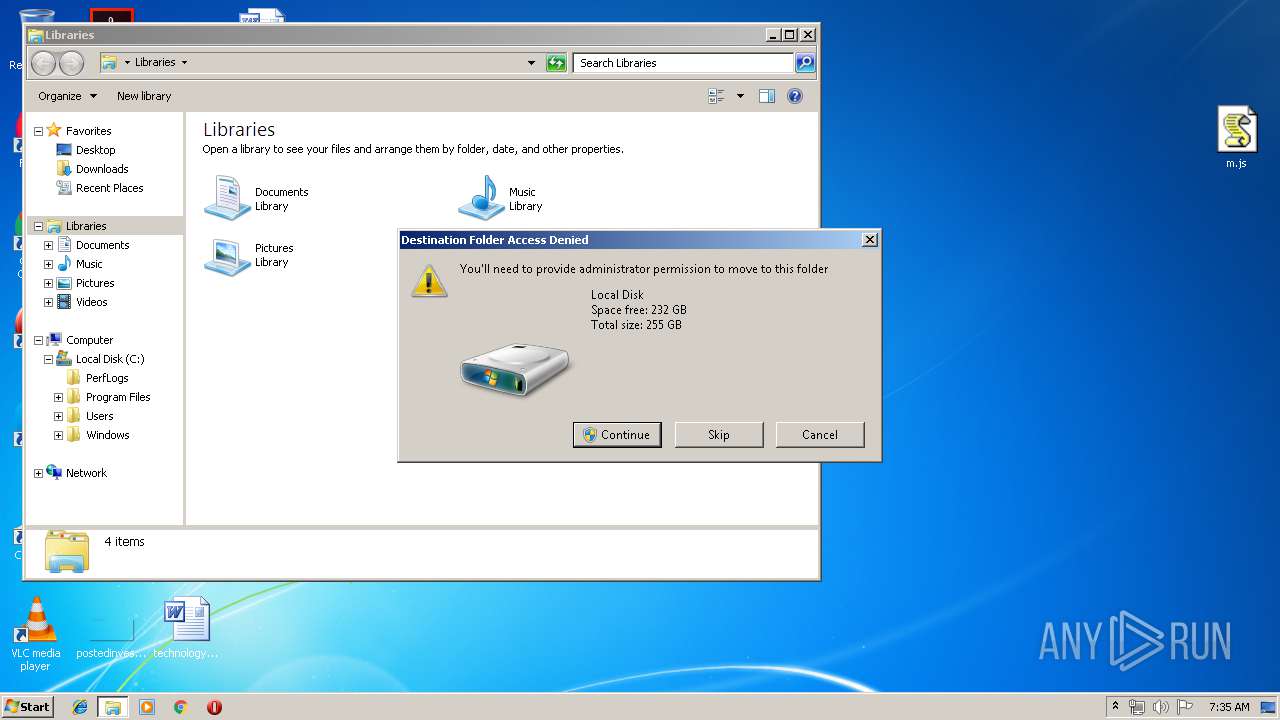
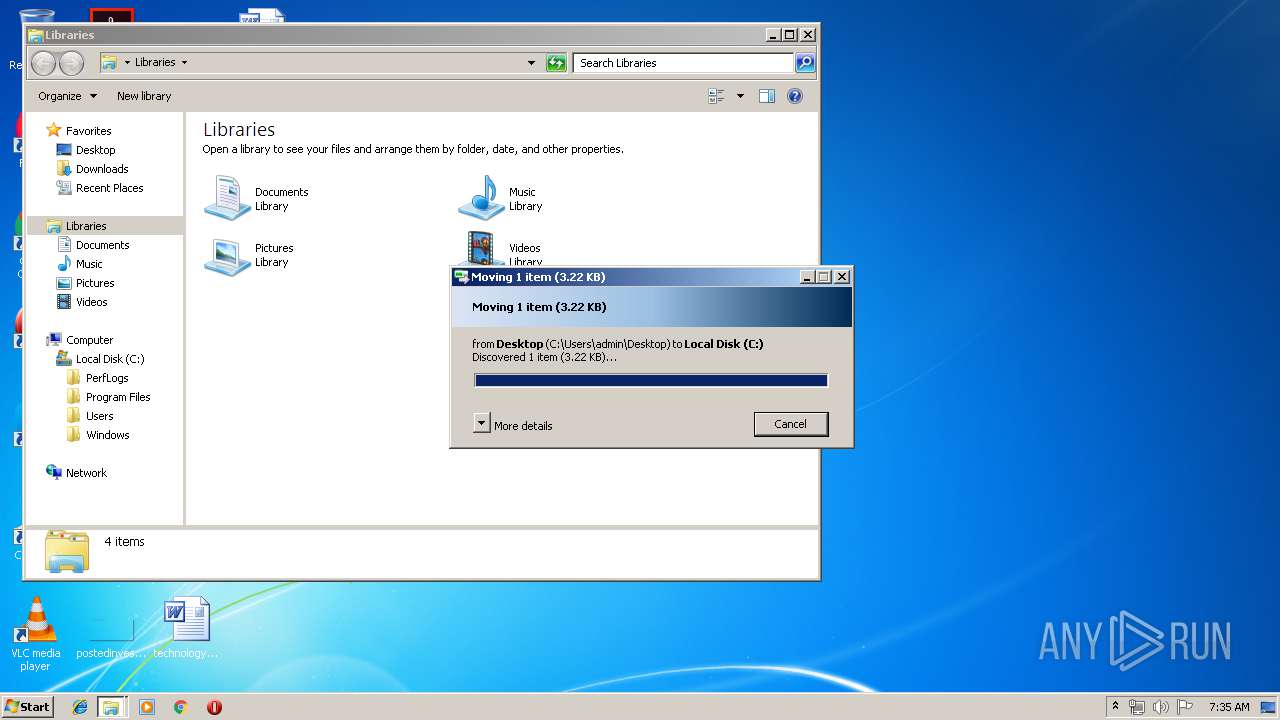
Application was dropped or rewritten from another process
- radB6D08.tmp (PID: 4028)
Changes the autorun value in the registry
- radB6D08.tmp (PID: 4028)
TROLDESH was detected
- radB6D08.tmp (PID: 4028)
SUSPICIOUS
Executable content was dropped or overwritten
- WScript.exe (PID: 2540)
- radB6D08.tmp (PID: 4028)
Creates files in the user directory
- WScript.exe (PID: 2540)
Checks for external IP
- radB6D08.tmp (PID: 4028)
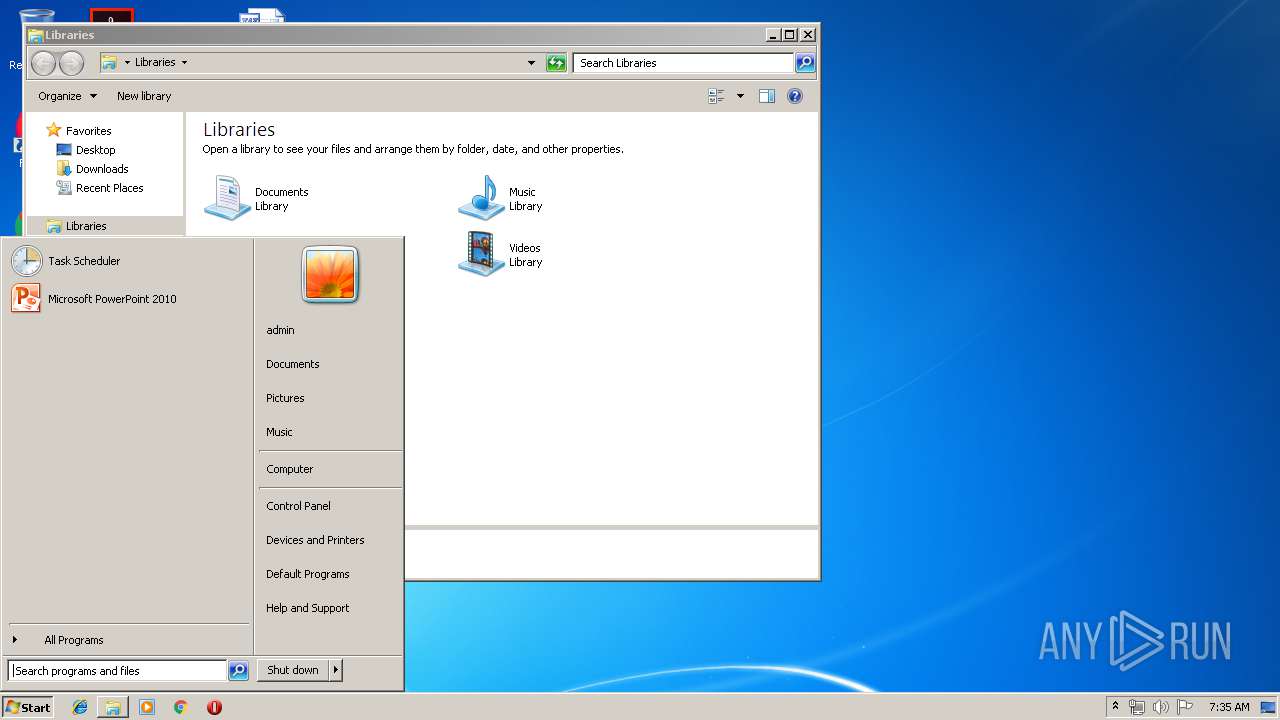
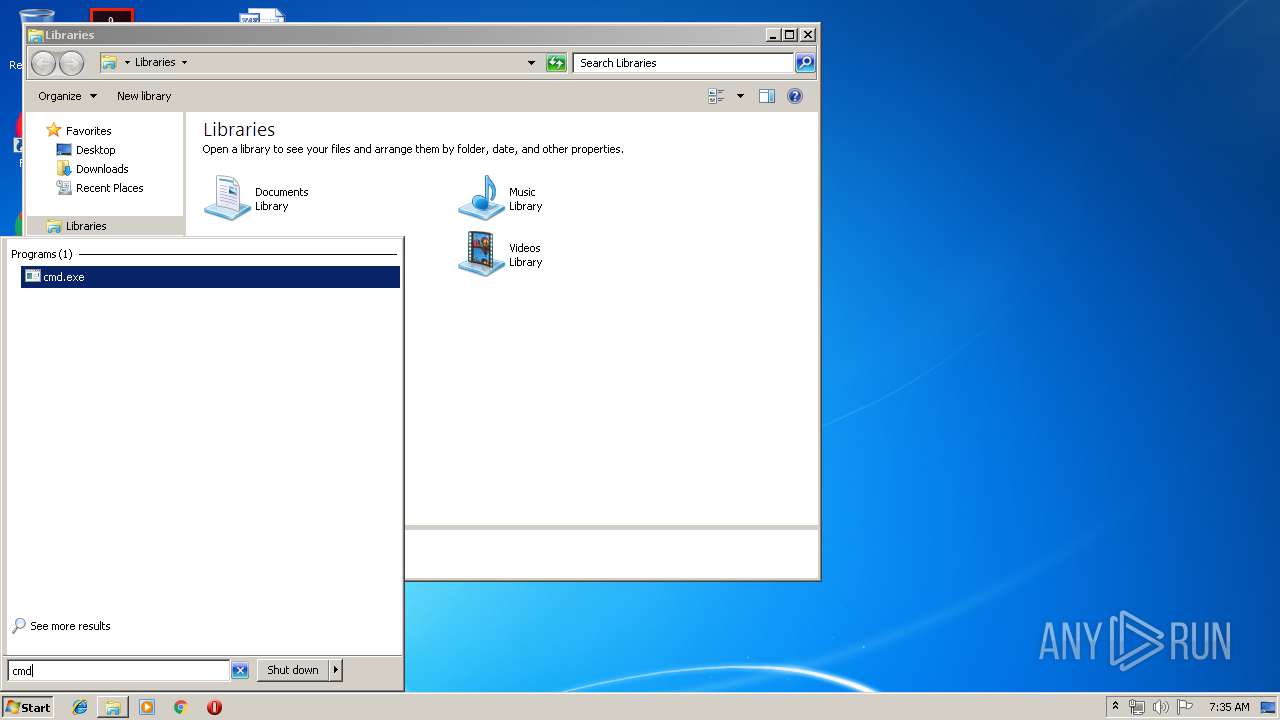
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2540)
Adds / modifies Windows certificates
- WScript.exe (PID: 2540)
Starts application with an unusual extension
- cmd.exe (PID: 3236)
Creates files in the program directory
- radB6D08.tmp (PID: 4028)
INFO
Dropped object may contain TOR URL's
- radB6D08.tmp (PID: 4028)
Dropped object may contain URL to Tor Browser
- radB6D08.tmp (PID: 4028)
Dropped object may contain Bitcoin addresses
- radB6D08.tmp (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
Total processes
53
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
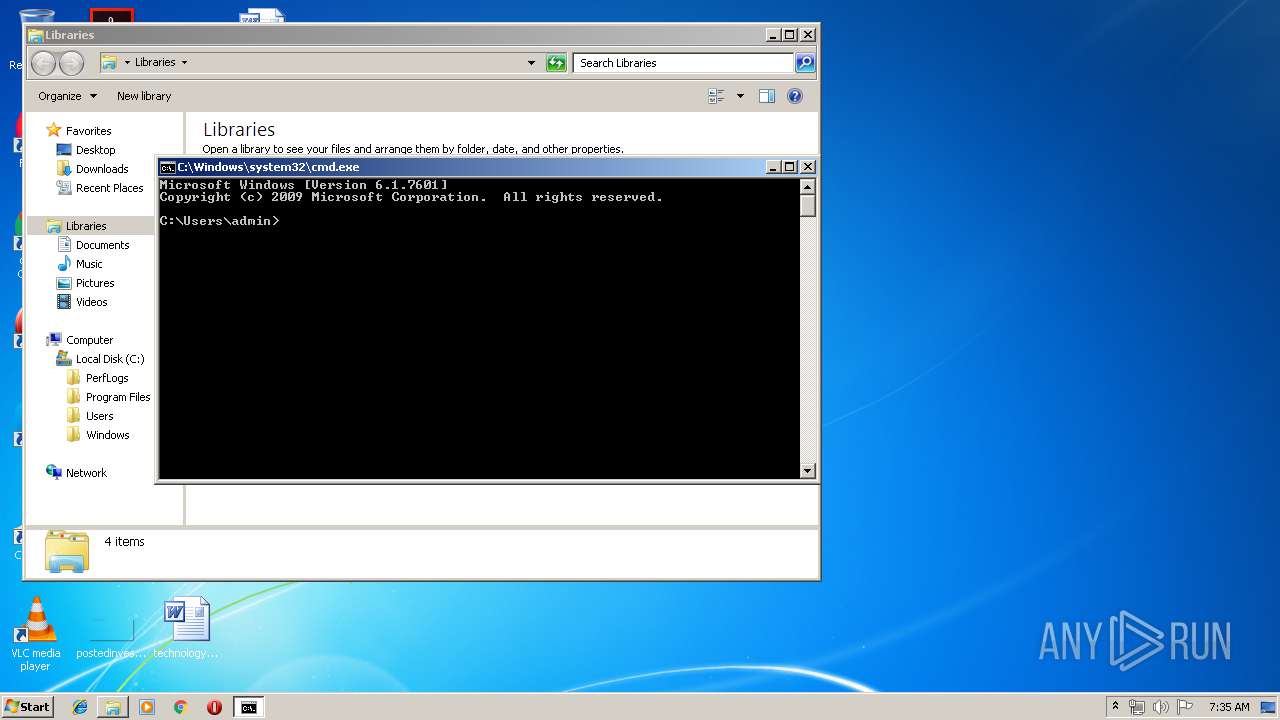
| 932 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1840 | C:\Windows\system32\vssadmin.exe List Shadows | C:\Windows\system32\vssadmin.exe | — | radB6D08.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
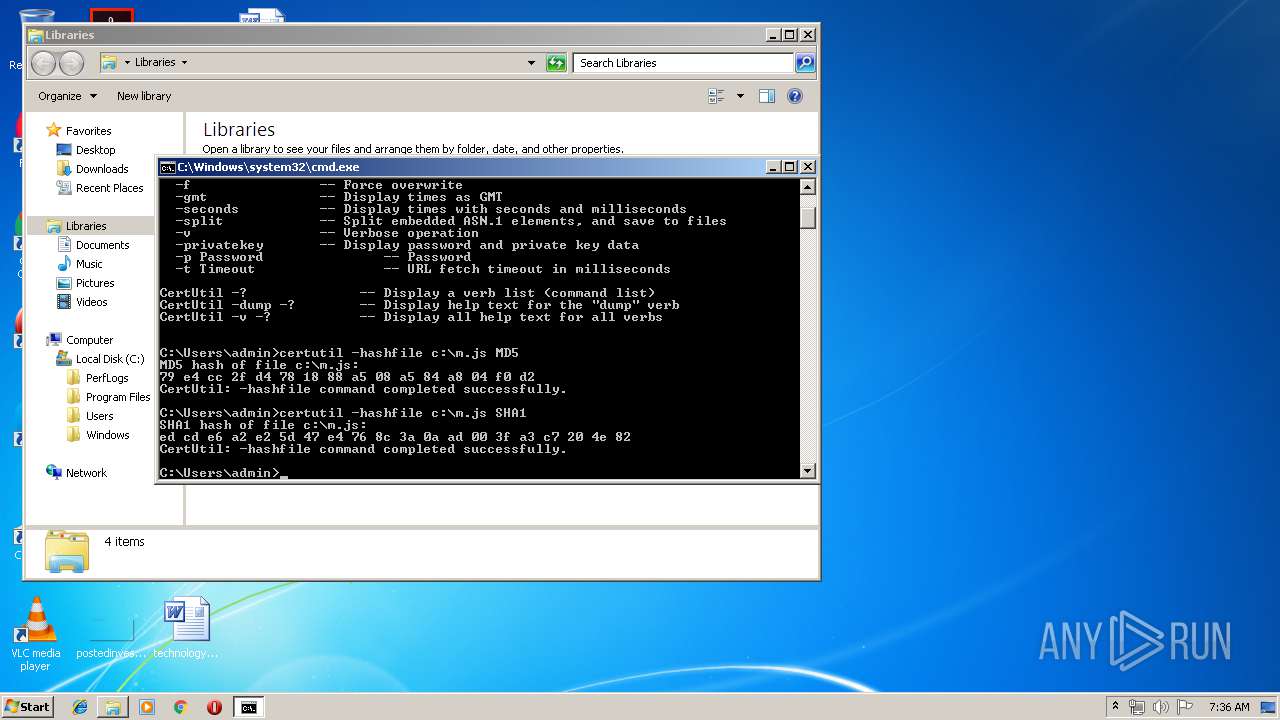
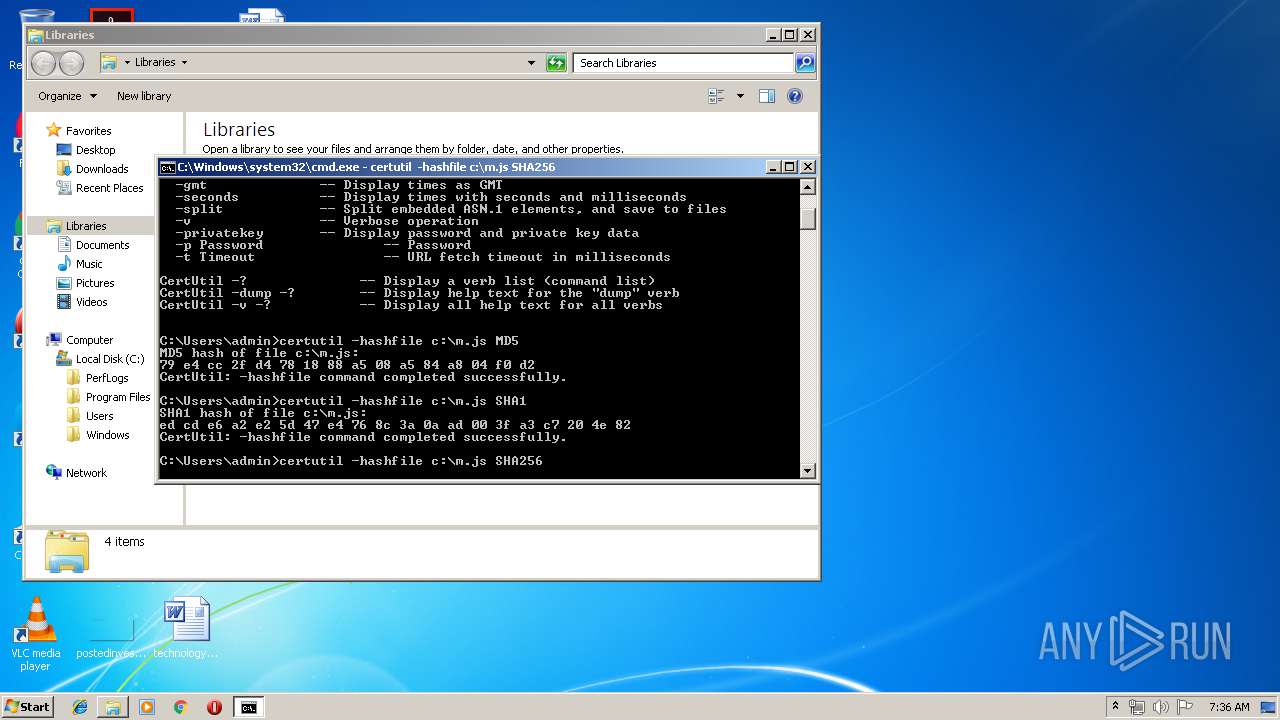
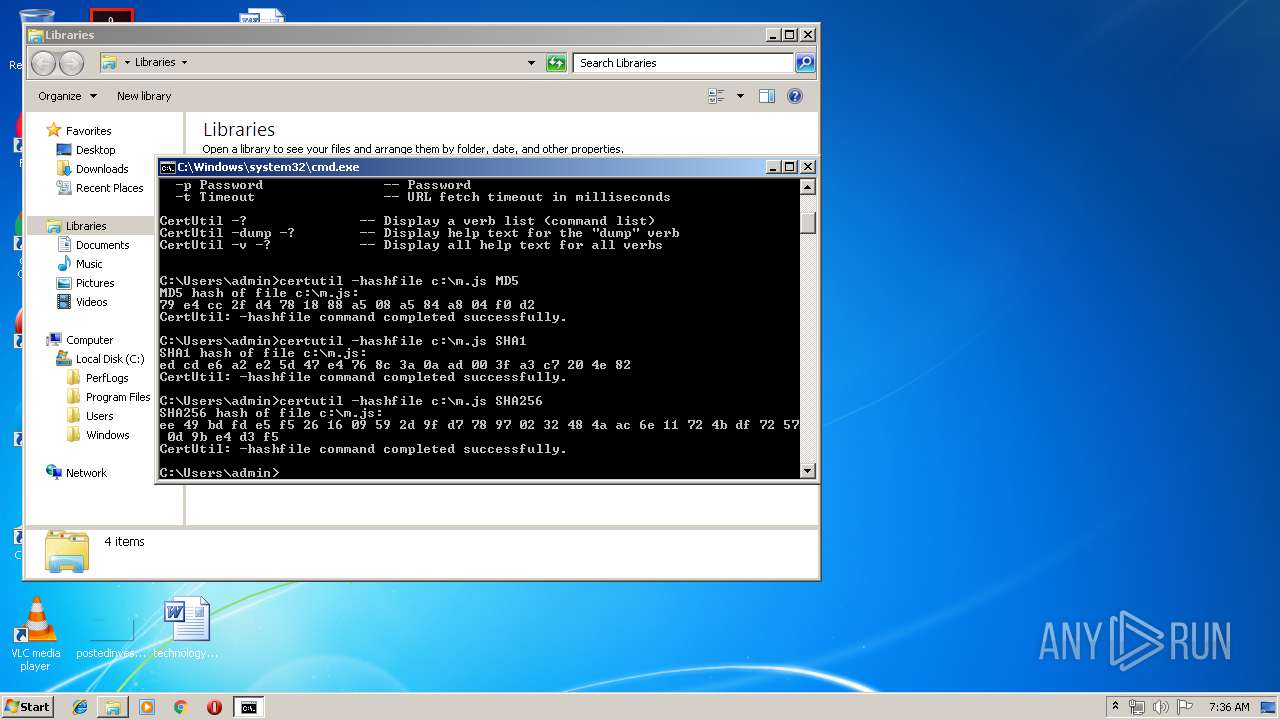
| 2408 | certutil -hashfile c:\m.js SHA1 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
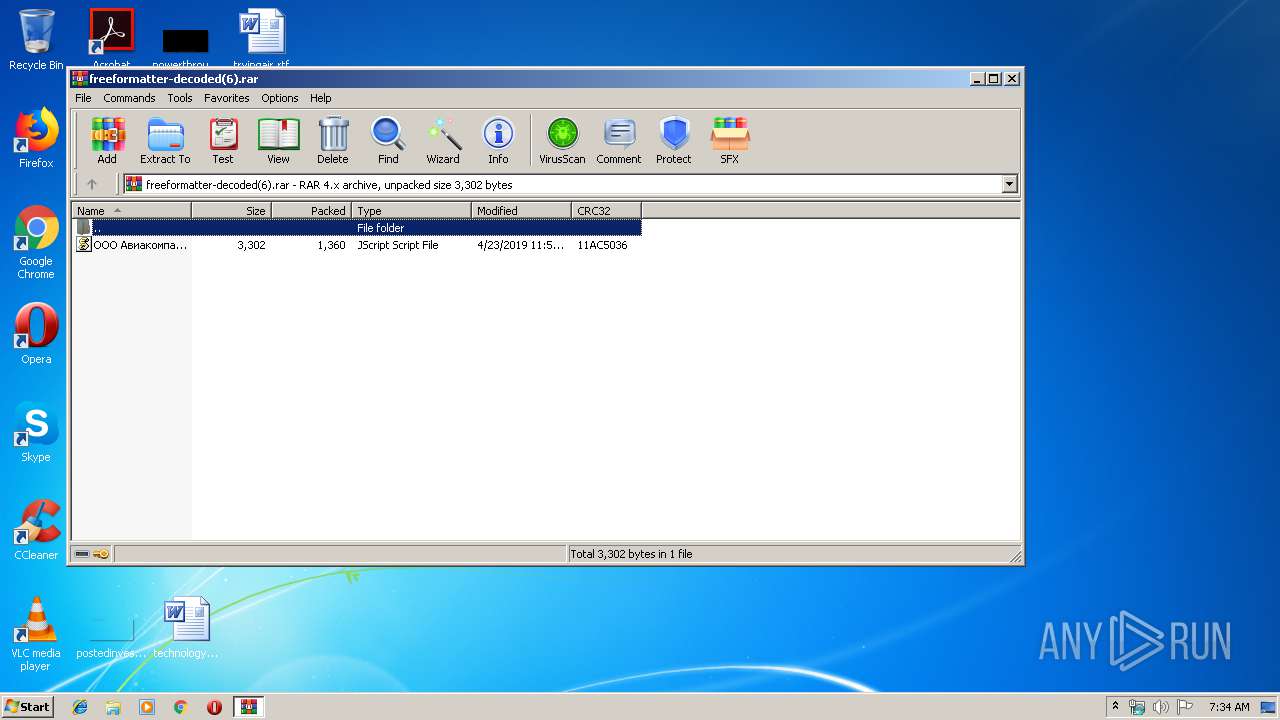
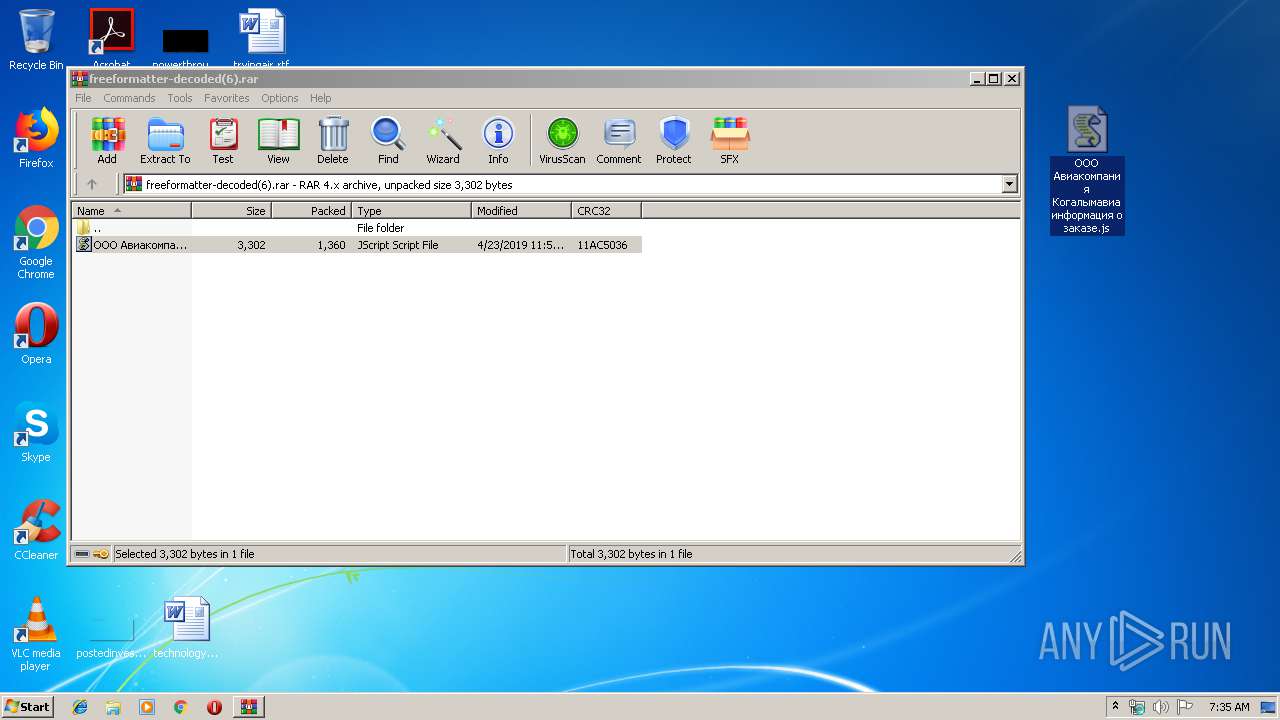
| 2540 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\ООО Авиакомпания Когалымавиа информация о заказе.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2564 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\freeformatter-decoded(6).rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
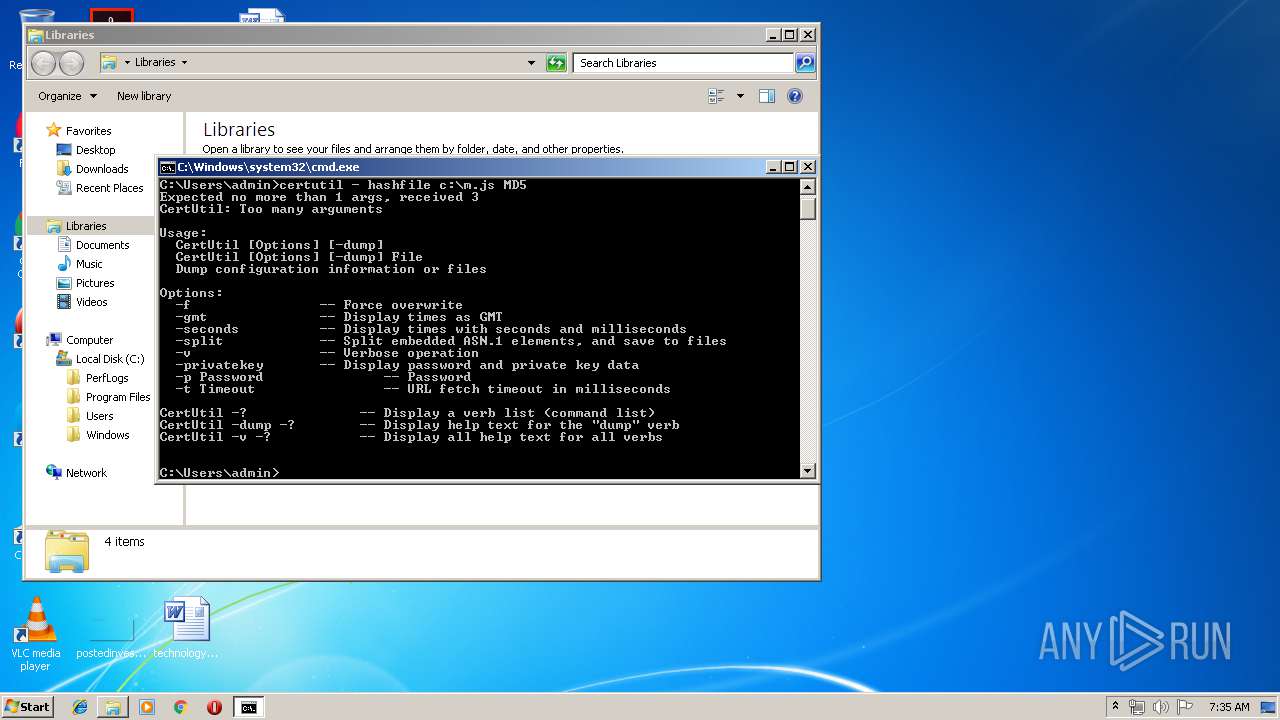
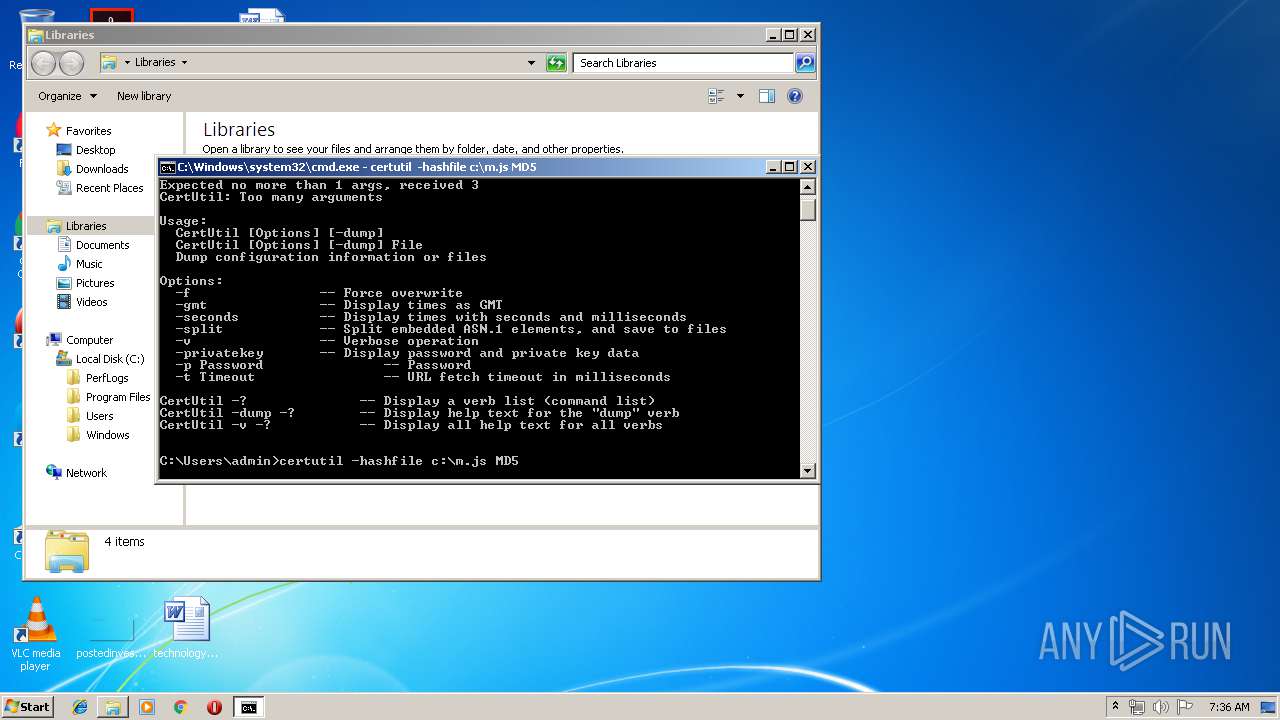
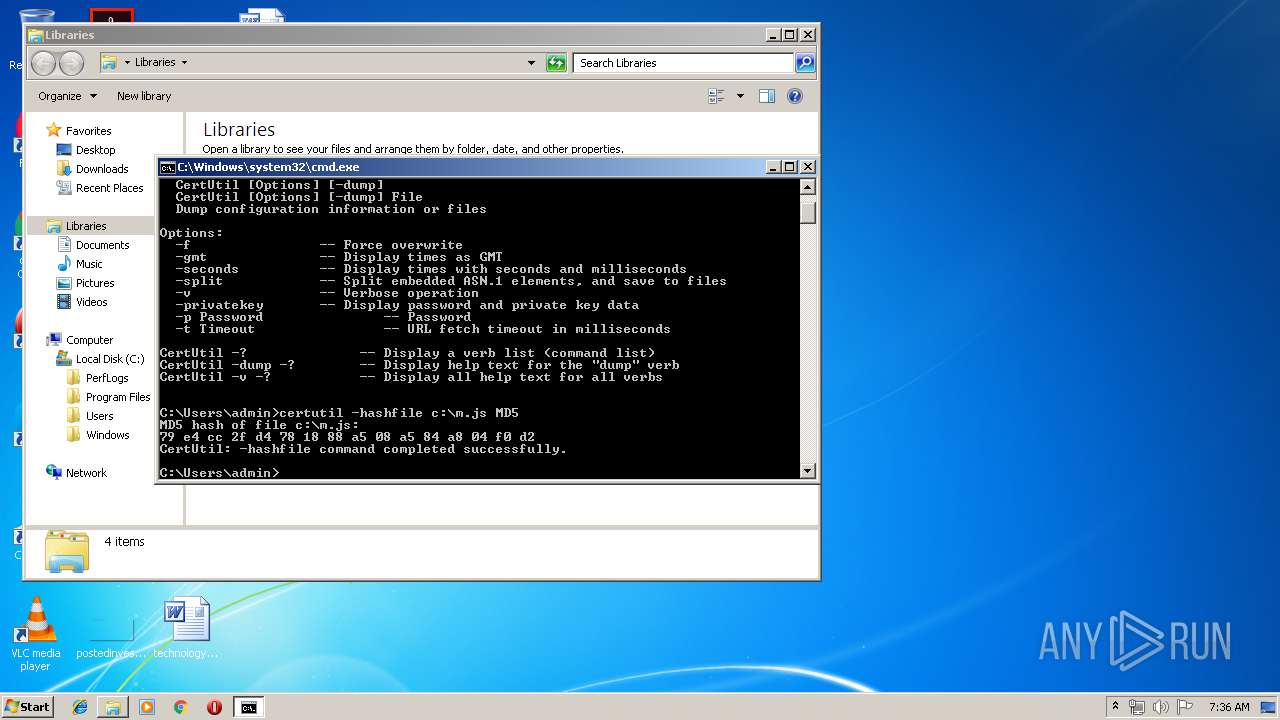
| 3160 | certutil -hashfile c:\m.js MD5 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | "C:\Windows\System32\cmd.exe" /c C:\Users\admin\AppData\Local\Temp\radB6D08.tmp | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3392 | certutil - hashfile c:\m.js MD5 | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
739
Read events
670
Write events
66
Delete events
3
Modification events
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\freeformatter-decoded(6).rar | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2936) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
Executable files
3
Suspicious files
49
Text files
35
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2936.20437\ООО Авиакомпания Когалымавиа информация о заказе.js | — | |
MD5:— | SHA256:— | |||
| 2936 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2936.21050\ООО Авиакомпания Когалымавиа информация о заказе.js | — | |
MD5:— | SHA256:— | |||
| 4028 | radB6D08.tmp | C:\Users\admin\AppData\Local\Temp\6893A5D897\state.tmp | — | |
MD5:— | SHA256:— | |||
| 4028 | radB6D08.tmp | C:\Users\admin\AppData\Local\Temp\6893A5D897\unverified-microdesc-consensus.tmp | — | |
MD5:— | SHA256:— | |||
| 4028 | radB6D08.tmp | C:\Users\admin\AppData\Local\Temp\6893A5D897\cached-certs.tmp | — | |
MD5:— | SHA256:— | |||
| 4028 | radB6D08.tmp | C:\Users\admin\AppData\Local\Temp\6893A5D897\cached-microdesc-consensus.tmp | — | |
MD5:— | SHA256:— | |||
| 4028 | radB6D08.tmp | C:\Users\admin\AppData\Local\Temp\6893A5~1\unverified-microdesc-consensus | text | |
MD5:— | SHA256:— | |||
| 4028 | radB6D08.tmp | C:\Users\Public\Videos\Sample Videos\Wildlife.wmv | — | |
MD5:— | SHA256:— | |||
| 4028 | radB6D08.tmp | C:\Users\Public\Videos\Sample Videos\vBwXLFGQpU6cL+JbCb4LX8fuds7tE1noNAhfhVLaFKo=.906D0F2E2F604F839E04.crypted000007 | — | |
MD5:— | SHA256:— | |||
| 4028 | radB6D08.tmp | C:\Users\Public\Pictures\Sample Pictures\Tulips.jpg | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
19
DNS requests
3
Threats
47
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
4028 | radB6D08.tmp | GET | 200 | 104.18.34.131:80 | http://whatsmyip.net/ | US | html | 7.35 Kb | shared |
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
4028 | radB6D08.tmp | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2540 | WScript.exe | 95.213.184.187:443 | jetstd.ru | OOO Network of data-centers Selectel | RU | malicious |
4028 | radB6D08.tmp | 76.73.17.194:9090 | — | Cogent Communications | US | malicious |
4028 | radB6D08.tmp | 154.35.32.5:443 | — | Rethem Hosting LLC | US | suspicious |
4028 | radB6D08.tmp | 128.31.0.39:9101 | — | Massachusetts Institute of Technology | US | malicious |
4028 | radB6D08.tmp | 185.225.17.173:443 | — | — | — | suspicious |
— | — | 193.23.244.244:443 | — | Chaos Computer Club e.V. | DE | malicious |
4028 | radB6D08.tmp | 212.8.243.229:9001 | — | Sivin Consult Ltd | RU | suspicious |
4028 | radB6D08.tmp | 136.243.4.139:8008 | — | Hetzner Online GmbH | DE | suspicious |
4028 | radB6D08.tmp | 104.16.155.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
4028 | radB6D08.tmp | 104.18.34.131:80 | whatsmyip.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jetstd.ru |
| malicious |
whatismyipaddress.com |
| shared |
whatsmyip.net |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2540 | WScript.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
4028 | radB6D08.tmp | Misc activity | ET POLICY TLS possible TOR SSL traffic |
4028 | radB6D08.tmp | Potential Corporate Privacy Violation | POLICY [PTsecurity] TOR SSL connection |
4028 | radB6D08.tmp | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 280 |
4028 | radB6D08.tmp | Potential Corporate Privacy Violation | POLICY [PTsecurity] TOR SSL connection |
4028 | radB6D08.tmp | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 239 |
4028 | radB6D08.tmp | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 128 |
4028 | radB6D08.tmp | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 352 |
4028 | radB6D08.tmp | Misc activity | ET POLICY TLS possible TOR SSL traffic |
4028 | radB6D08.tmp | Misc activity | ET POLICY TLS possible TOR SSL traffic |
23 ETPRO signatures available at the full report