| File name: | Loader.exe |
| Full analysis: | https://app.any.run/tasks/5e0b33f2-be94-4c62-b47f-fce704686d85 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 17, 2025, 08:28:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 11 sections |
| MD5: | 87B01259E342EAB112DEF3F9FA36260E |
| SHA1: | 601829FC9DA49B300ADF1C4A67A718D2A6D4D39E |
| SHA256: | 328A4CC8EFA309DC7849C68DB1948F0773ACEECD63E68C6683FA03A60D6DFC7C |
| SSDEEP: | 49152:gNRL7gjR7qNOK2RXvNviSNchJ9RHiLpJ5PboXOxOM7Zqf+SC37o77hsuTVOYdiMd:oRL7gJqNOK2RXvNviSNchJ9RHiT5Pboh |
MALICIOUS
Steals credentials from Web Browsers
- MSBuild.exe (PID: 7400)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 7400)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 7400)
SUSPICIOUS
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 7400)
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 7400)
INFO
Checks supported languages
- Loader.exe (PID: 7380)
- MSBuild.exe (PID: 7400)
Attempting to use instant messaging service
- MSBuild.exe (PID: 7400)
Reads the computer name
- MSBuild.exe (PID: 7400)
Reads the software policy settings
- MSBuild.exe (PID: 7400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(7400) MSBuild.exe
C2 (11)https://t.me/kz_prokla1
grxeasyw.digital/xxepw
travelilx.top/GSKAiz
krxspint.digital/kendwz
jrxsafer.top/shpaoz
advennture.top/GKsiio
xrfxcaseq.live/gspaz
rhxhube.run/pogrs
ecoexpanpd.live/tnbz
ywmedici.top/noagis
targett.top/dsANGt
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:03 15:20:21+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 504320 |
| InitializedDataSize: | 91648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x668e4 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
139
Monitored processes
2
Malicious processes
2
Suspicious processes
0
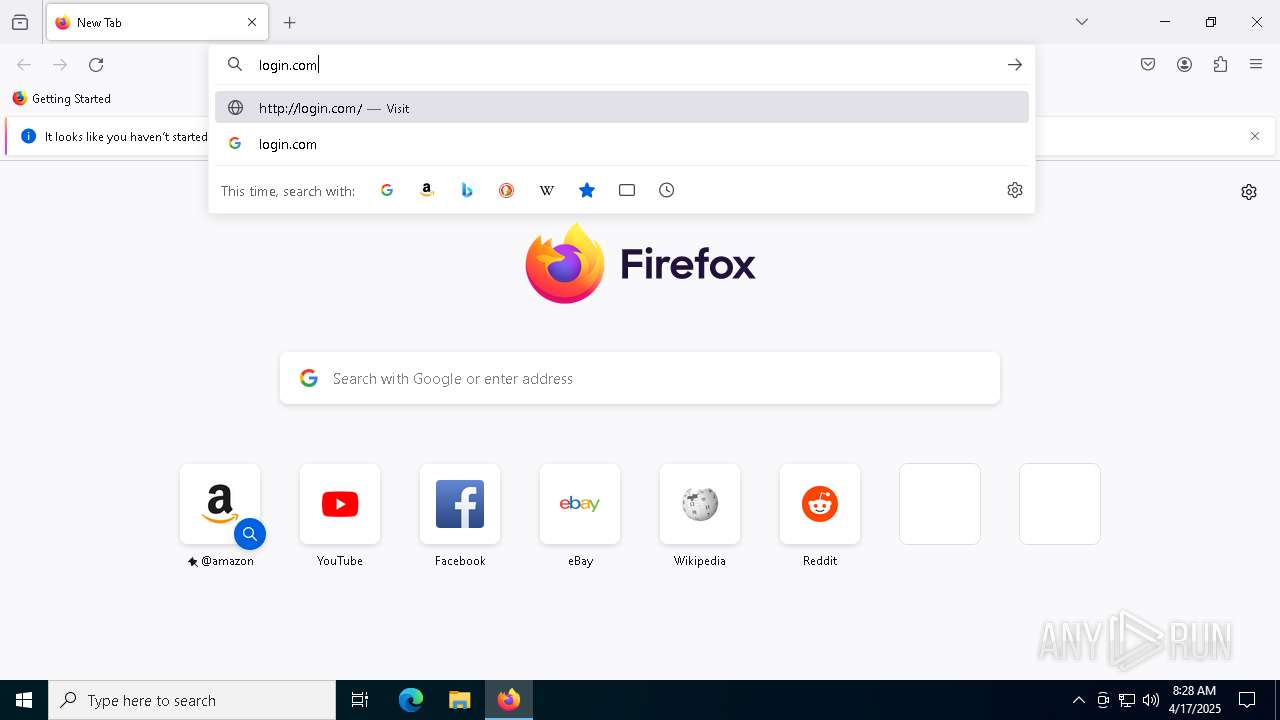
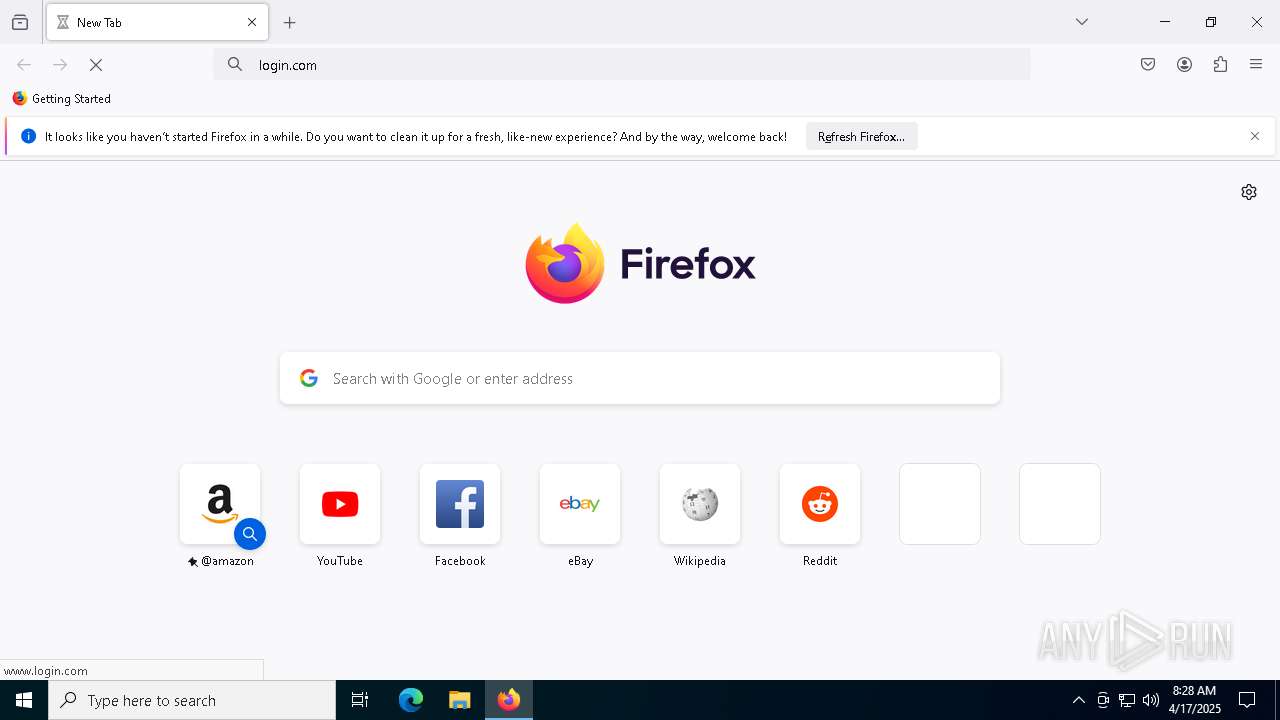
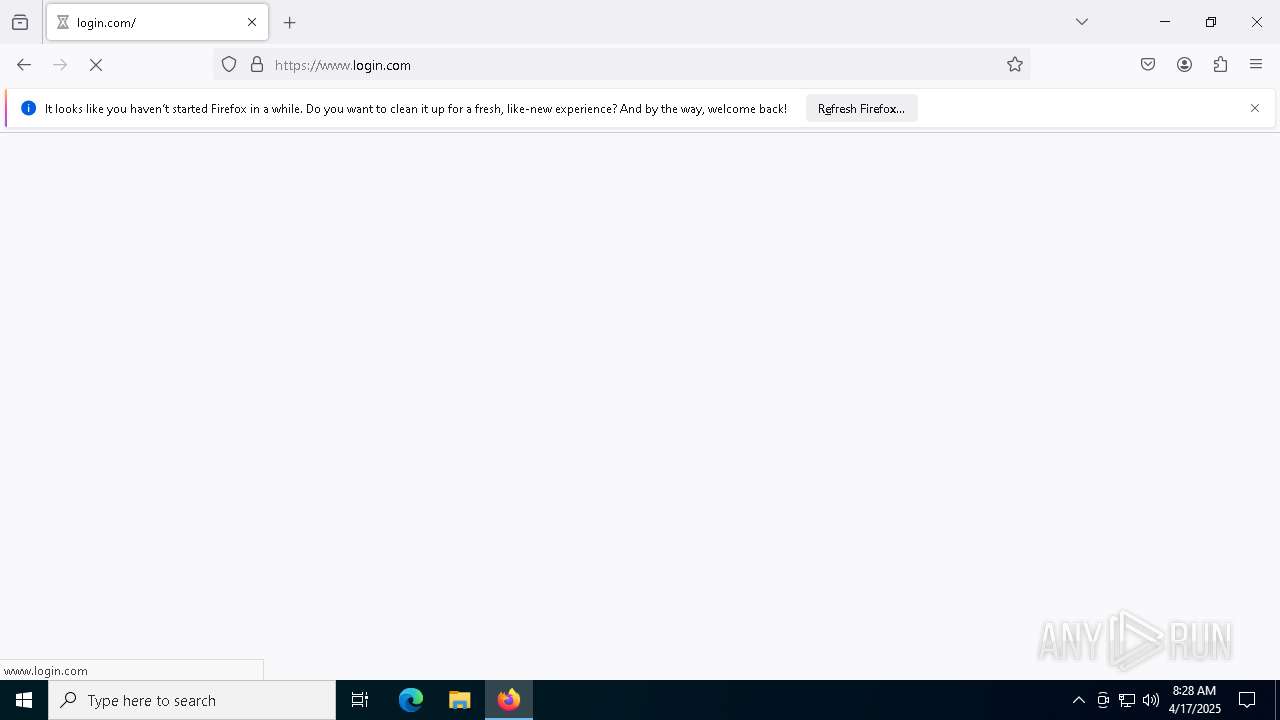
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7380 | "C:\Users\admin\AppData\Local\Temp\Loader.exe" | C:\Users\admin\AppData\Local\Temp\Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7400 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | Loader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
Lumma(PID) Process(7400) MSBuild.exe C2 (11)https://t.me/kz_prokla1 grxeasyw.digital/xxepw travelilx.top/GSKAiz krxspint.digital/kendwz jrxsafer.top/shpaoz advennture.top/GKsiio xrfxcaseq.live/gspaz rhxhube.run/pogrs ecoexpanpd.live/tnbz ywmedici.top/noagis targett.top/dsANGt | |||||||||||||||
Total events
412
Read events
412
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
115
DNS requests
122
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.65:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.131:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.131:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.114:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.114:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 95.101.54.114:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
7576 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.65:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
7400 | MSBuild.exe | 149.154.167.99:443 | t.me | Telegram Messenger Inc | GB | whitelisted |
7400 | MSBuild.exe | 188.114.96.3:443 | ecoexpanpd.live | CLOUDFLARENET | NL | unknown |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
— | — | 188.114.96.3:443 | ecoexpanpd.live | CLOUDFLARENET | NL | unknown |
— | — | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
t.me |
| whitelisted |
ecoexpanpd.live |
| unknown |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7400 | MSBuild.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |