| File name: | Galaxy Swapper 2.exe |
| Full analysis: | https://app.any.run/tasks/e7c6da29-e342-4070-9021-f74a770d16f8 |
| Verdict: | Malicious activity |
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | June 19, 2023, 15:36:32 |
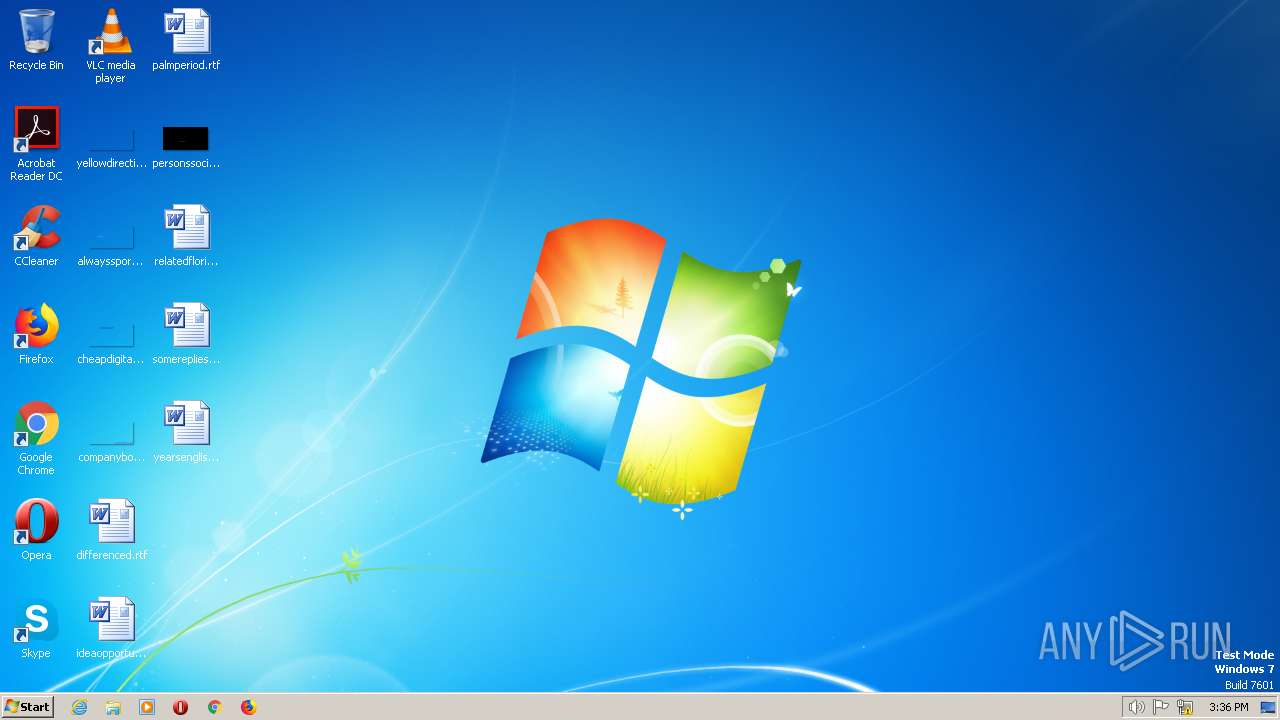
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 2720EC7DFC10E6F6F365D1A0D23A781C |
| SHA1: | F7E55EB8BA3A9886FDD80CB6E1A000F764857395 |
| SHA256: | 32891C01FD96BEC38BBF5127D7849F1B4E4CBB131F99D8DEDFCA9034B2657D2B |
| SSDEEP: | 6144:CseB0sEFZKczL/bhdfAOssju8+kwmiKi0m5d8Zo2A9yP2DeSvi:CKsEFZKcHZPnwmiKi0IdBmieSvi |
MALICIOUS
REDLINE detected by memory dumps
- InstallUtil.exe (PID: 2700)
SUSPICIOUS
No suspicious indicators.INFO
Reads the computer name
- InstallUtil.exe (PID: 2700)
Checks supported languages
- Galaxy Swapper 2.exe (PID: 2464)
- InstallUtil.exe (PID: 2700)
The process checks LSA protection
- InstallUtil.exe (PID: 2700)
Reads the machine GUID from the registry
- InstallUtil.exe (PID: 2700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows command line |
|---|---|
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x5aa2 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 209920 |
| CodeSize: | 137216 |
| LinkerVersion: | 14.34 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:05:29 15:25:02+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 29-May-2023 15:25:02 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-May-2023 15:25:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00021624 | 0x00021800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62985 |
.rdata | 0x00023000 | 0x0000D666 | 0x0000D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.51659 |
.data | 0x00031000 | 0x00023EFC | 0x00023200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.96774 |
.reloc | 0x00055000 | 0x00001B3C | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.50155 |
.Chacha | 0x00057000 | 0x000C5C10 | 0x000C5E00 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_TYPE_COPY | 0.000389967 |
Imports
KERNEL32.dll |
SHELL32.dll |
Total processes
32
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2464 | "C:\Users\admin\AppData\Local\Temp\Galaxy Swapper 2.exe" | C:\Users\admin\AppData\Local\Temp\Galaxy Swapper 2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2700 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | Galaxy Swapper 2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.7.2558.0 built by: NET471REL1 Modules
| |||||||||||||||
Total events
164
Read events
164
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report