| File name: | Client.exe |
| Full analysis: | https://app.any.run/tasks/af62ecde-acfe-4f8f-bdca-9b65cdbe12d1 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | June 27, 2022, 07:42:31 |
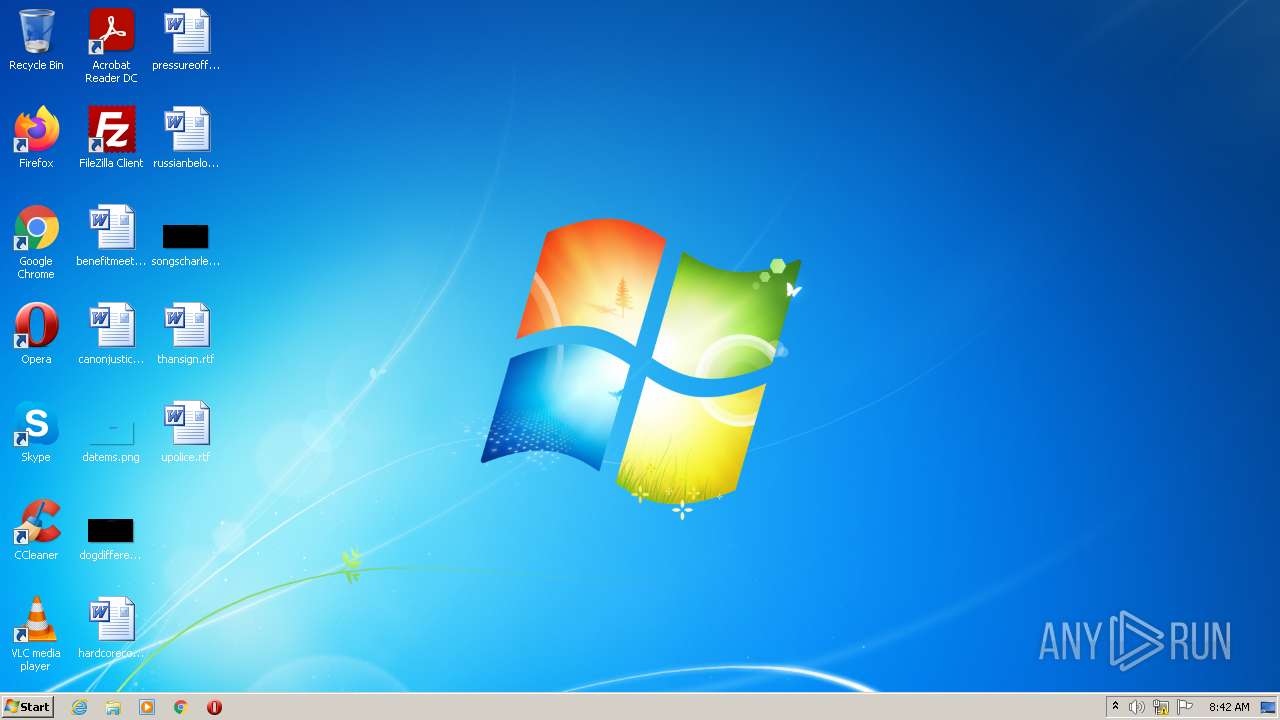
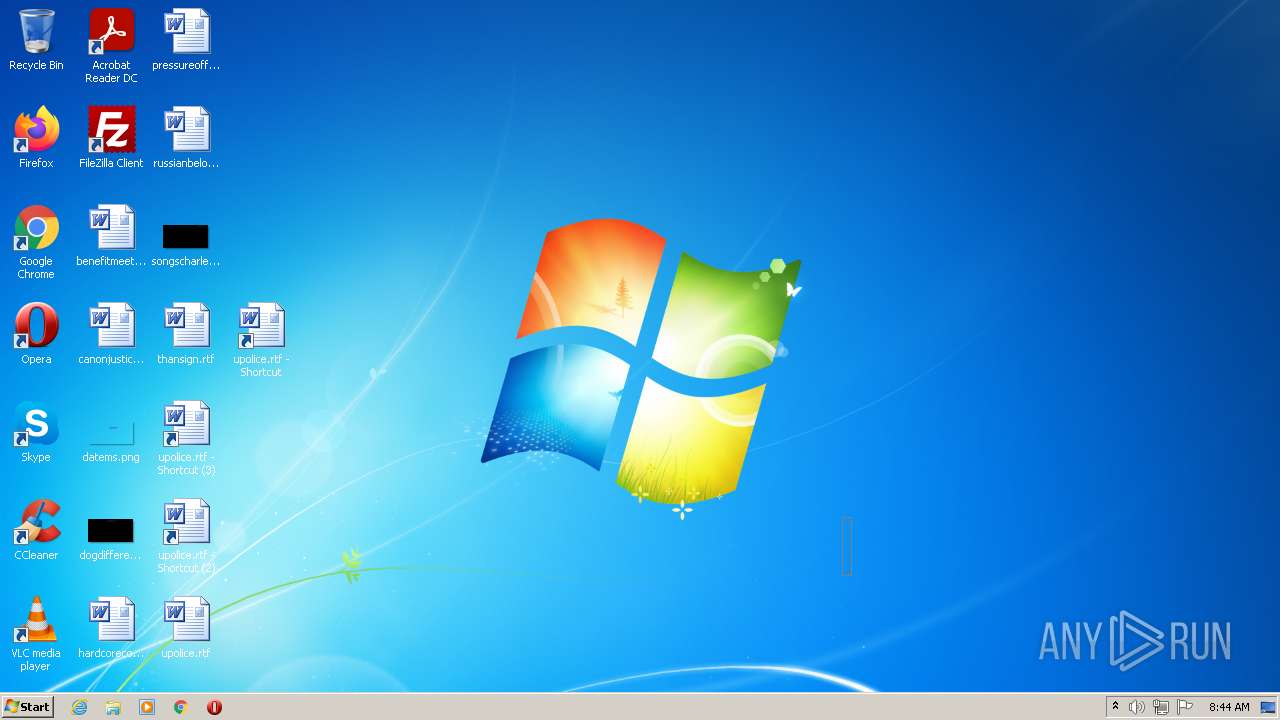
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 5285C7DB146BF8277CCC5A26091BAC2A |
| SHA1: | 20115CAB44F9F0876A25D89F0AA6AC7745CC03B8 |
| SHA256: | 318DCA306DAD422A35C456E787FC9FB92139CD4CC46481BF78CDC52491638CB4 |
| SSDEEP: | 1536:xsDUBtKDs4zb1IqQiinkJ4uFRje0CBZVclN:aDUBtQrzb13sIXuzY |
MALICIOUS
Changes the autorun value in the registry
- Client.exe (PID: 240)
- Update.exe (PID: 3308)
Drops executable file immediately after starts
- Client.exe (PID: 240)
- Update.exe (PID: 3308)
- chrome.exe (PID: 1276)
ASYNCRAT detected by memory dumps
- Update.exe (PID: 3308)
Loads the Task Scheduler COM API
- Update.exe (PID: 3308)
ASYNCRAT was detected
- Update.exe (PID: 3308)
SUSPICIOUS
Checks supported languages
- Client.exe (PID: 240)
- Update.exe (PID: 3308)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 2364)
Executable content was dropped or overwritten
- Client.exe (PID: 240)
- Update.exe (PID: 3308)
- chrome.exe (PID: 1276)
Drops a file with a compile date too recent
- Client.exe (PID: 240)
- Update.exe (PID: 3308)
- chrome.exe (PID: 1276)
Starts CMD.EXE for commands execution
- Client.exe (PID: 240)
- Update.exe (PID: 3308)
Reads the computer name
- Client.exe (PID: 240)
- Update.exe (PID: 3308)
Creates files in the user directory
- Client.exe (PID: 240)
Reads Environment values
- Update.exe (PID: 3308)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2556)
INFO
Checks supported languages
- timeout.exe (PID: 3424)
- chrome.exe (PID: 328)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 1528)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 1036)
- chrome.exe (PID: 2524)
- chrome.exe (PID: 2784)
- opera.exe (PID: 3688)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 1048)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 3848)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3660)
- chrome.exe (PID: 2012)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 3420)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 280)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 2044)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 964)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 892)
- chrome.exe (PID: 2840)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 820)
- chrome.exe (PID: 2944)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 300)
- chrome.exe (PID: 124)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2928)
- chrome.exe (PID: 1664)
- chrome.exe (PID: 1276)
- shutdown.exe (PID: 2856)
Reads settings of System Certificates
- Update.exe (PID: 3308)
- chrome.exe (PID: 328)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3288)
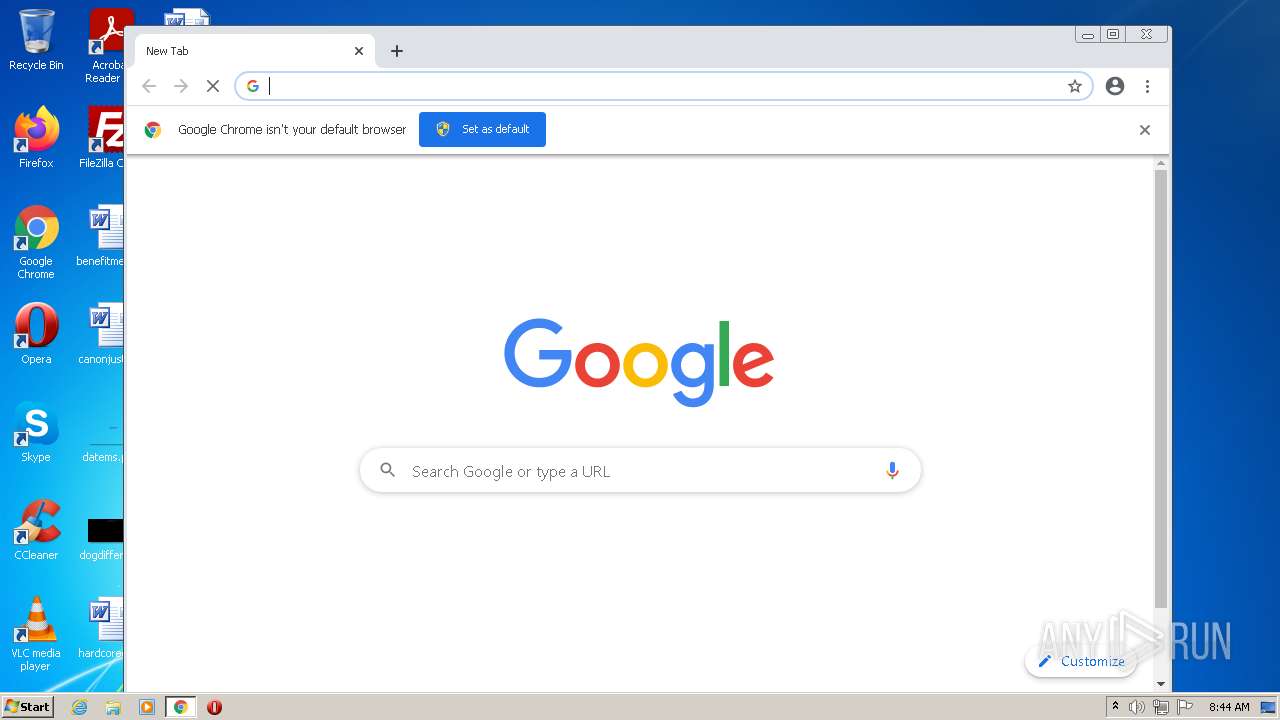
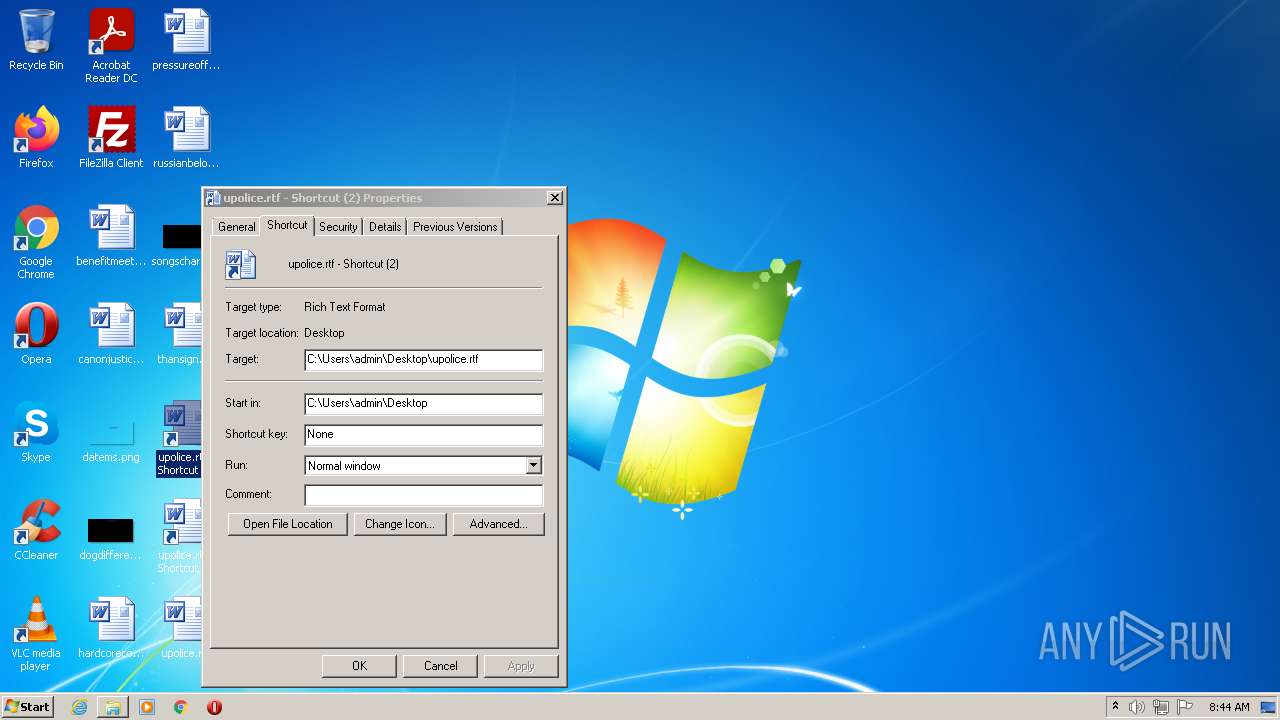
Manual execution by user
- chrome.exe (PID: 3252)
- opera.exe (PID: 3688)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 3288)
Reads the hosts file
- chrome.exe (PID: 3252)
- chrome.exe (PID: 328)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2004)
Application launched itself
- chrome.exe (PID: 3252)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 3288)
Reads the computer name
- chrome.exe (PID: 3252)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 328)
- chrome.exe (PID: 1528)
- opera.exe (PID: 3688)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2760)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 1128)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 124)
- chrome.exe (PID: 3188)
- shutdown.exe (PID: 2856)
Reads the date of Windows installation
- opera.exe (PID: 3688)
- chrome.exe (PID: 3172)
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 3688)
Check for Java to be installed
- opera.exe (PID: 3688)
Creates files in the user directory
- opera.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(3308) Update.exe
C2 (1)5.tcp.eu.ngrok.io
Ports (1)10336
Version1.0.7
Autoruntrue
MutexDcRatMutex_qwqdanchun
CertificateMIICMDCCAZmgAwIBAgIVAJUm72FoWO//rF5pIfNoQ4keK9p5MA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDERjUmF0IFNlcnZlcjETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTIxMDkxNDExMzI0M1oXDTMyMDYyMzExMzI0M1owEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_Signaturec6Wj1hNqkkqRUq4mjkef4T/UwTWQBA5B/eTABn/K8PtL0c8TXEYSdgCyHGEQase2Kw9GIcub0wpQzWpmCIpJUrsfMSSVJhBNziYF+kWTvuw7ovjADzKdVfjEKK6Db5w6RDd21QY96i8f6ZzGPc26Y87JzEIXJOiLN6BANz2Bg8c=
AntiVMfalse
PasteBinnull
bdosfalse
Botnetdefault
Aes_Keya5fa7b18eb4b820265697b61b4480fa34f290ae9f7252c1bbd975a965e399e95
SaltDcRatByqwqdanchun
Install_Folder%AppData%
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| AssemblyVersion: | 1.0.7.0 |
|---|---|
| ProductVersion: | 1.0.7.0 |
| ProductName: | - |
| OriginalFileName: | Client.exe |
| LegalTrademarks: | - |
| LegalCopyright: | - |
| InternalName: | Client.exe |
| FileVersion: | 1.0.7.0 |
| FileDescription: | - |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.7.0 |
| FileVersionNumber: | 1.0.7.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0xcbce |
| UninitializedDataSize: | - |
| InitializedDataSize: | 15872 |
| CodeSize: | 44032 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2021:05:05 23:11:39+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-May-2021 21:11:39 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.7.0 |
| InternalName: | Client.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Client.exe |
| ProductName: | - |
| ProductVersion: | 1.0.7.0 |
| Assembly Version: | 1.0.7.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 05-May-2021 21:11:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0000ABD4 | 0x0000AC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.6469 |
.rsrc | 0x0000E000 | 0x00003B1C | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.55564 |
.reloc | 0x00012000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13313 | 2691 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
104
Monitored processes
60
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,8810622342745104866,12105480097819429118,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1236 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 240 | "C:\Users\admin\AppData\Local\Temp\Client.exe" | C:\Users\admin\AppData\Local\Temp\Client.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.7.0 Modules
| |||||||||||||||
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,15326778557269143232,13802770507415129867,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3892 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --field-trial-handle=1024,8810622342745104866,12105480097819429118,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1416 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1064,689829347498831108,4627225464423618553,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1344 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1024,8810622342745104866,12105480097819429118,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8810622342745104866,12105480097819429118,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2380 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8810622342745104866,12105480097819429118,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1064,689829347498831108,4627225464423618553,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1940 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --field-trial-handle=1044,15326778557269143232,13802770507415129867,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1700 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
28 695
Read events
28 317
Write events
370
Delete events
8
Modification events
| (PID) Process: | (240) Client.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (240) Client.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Update |
Value: "C:\Users\admin\AppData\Roaming\Update.exe" | |||
| (PID) Process: | (3308) Update.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3308) Update.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Update |
Value: "C:\Users\admin\AppData\Roaming\Update.exe" | |||
| (PID) Process: | (3252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3252) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
Executable files
3
Suspicious files
180
Text files
256
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62B95FCA-CB4.pma | — | |
MD5:— | SHA256:— | |||
| 240 | Client.exe | C:\Users\admin\AppData\Roaming\Update.exe | executable | |
MD5:— | SHA256:— | |||
| 3308 | Update.exe | C:\Users\admin\AppData\Local\Temp\Update.exe | executable | |
MD5:— | SHA256:— | |||
| 3308 | Update.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 3308 | Update.exe | C:\Users\admin\AppData\Local\Temp\TarB4CC.tmp | cat | |
MD5:— | SHA256:— | |||
| 240 | Client.exe | C:\Users\admin\AppData\Local\Temp\tmp9AEA.tmp.bat | text | |
MD5:— | SHA256:— | |||
| 3308 | Update.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 3308 | Update.exe | C:\Users\admin\AppData\Local\Temp\CabB4CB.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3252 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
40
DNS requests
20
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acntlgljrcxocxiqsgdv37p2aqma_9.36.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.36.0_all_adsjzgv2ajqsor2rtb4vd53mblra.crx3 | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acntlgljrcxocxiqsgdv37p2aqma_9.36.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.36.0_all_adsjzgv2ajqsor2rtb4vd53mblra.crx3 | US | binary | 9.72 Kb | whitelisted |
3688 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 45.0 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acntlgljrcxocxiqsgdv37p2aqma_9.36.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.36.0_all_adsjzgv2ajqsor2rtb4vd53mblra.crx3 | US | binary | 9.73 Kb | whitelisted |
3688 | opera.exe | GET | 200 | 142.250.185.238:80 | http://clients1.google.com/complete/search?q=sadasdasdasdas&client=opera-suggest-omnibox&hl=de | US | text | 74 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acntlgljrcxocxiqsgdv37p2aqma_9.36.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.36.0_all_adsjzgv2ajqsor2rtb4vd53mblra.crx3 | US | binary | 9.72 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjE0QUFYTUR2NXNIakJsbE5jbXNrUkdfQQ/4.10.2391.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 4.13 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acntlgljrcxocxiqsgdv37p2aqma_9.36.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.36.0_all_adsjzgv2ajqsor2rtb4vd53mblra.crx3 | US | binary | 4.13 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acntlgljrcxocxiqsgdv37p2aqma_9.36.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.36.0_all_adsjzgv2ajqsor2rtb4vd53mblra.crx3 | US | binary | 5.65 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3308 | Update.exe | 67.27.158.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
328 | chrome.exe | 142.250.186.132:443 | www.google.com | Google Inc. | US | whitelisted |
328 | chrome.exe | 142.251.36.142:443 | clients2.google.com | Google Inc. | US | suspicious |
328 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
328 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3688 | opera.exe | 93.184.220.29:80 | crl3.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3688 | opera.exe | 142.250.185.238:80 | clients1.google.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
3320 | chrome.exe | 142.250.185.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 172.217.16.195:443 | update.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
5.tcp.eu.ngrok.io |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
3308 | Update.exe | A Network Trojan was detected | ET TROJAN Observed Malicious SSL Cert (AsyncRAT) |
1 ETPRO signatures available at the full report