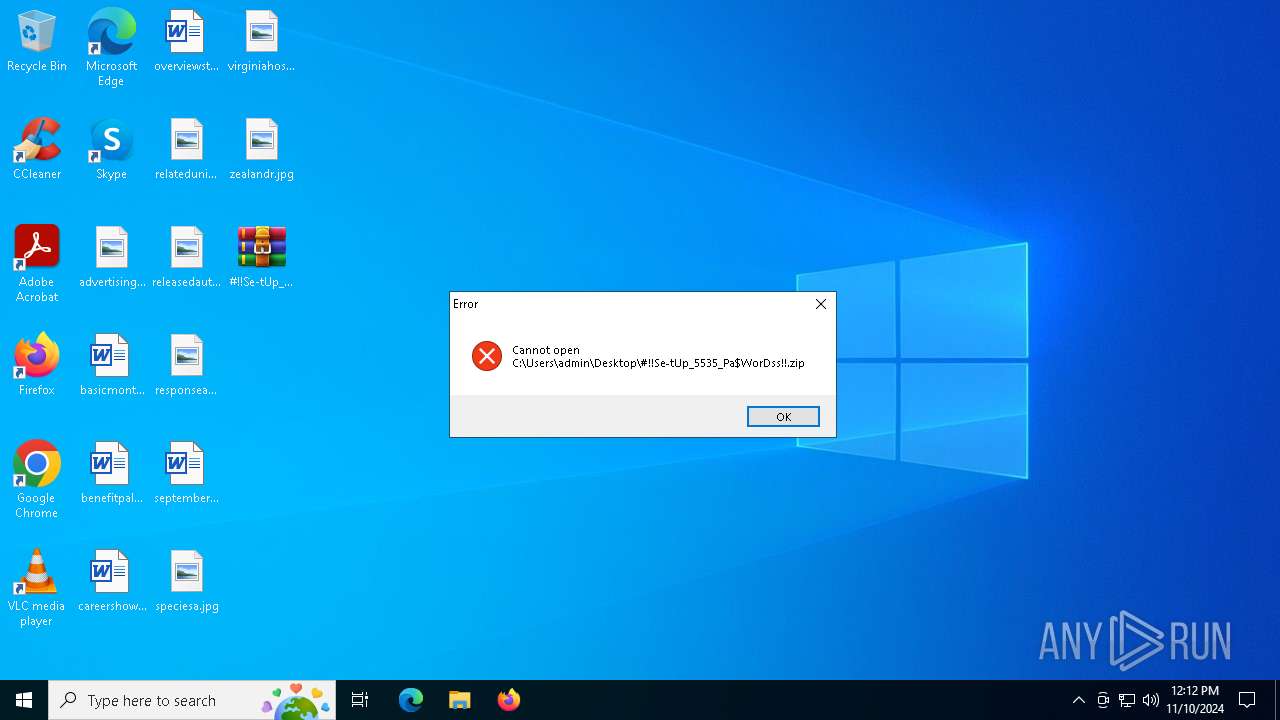
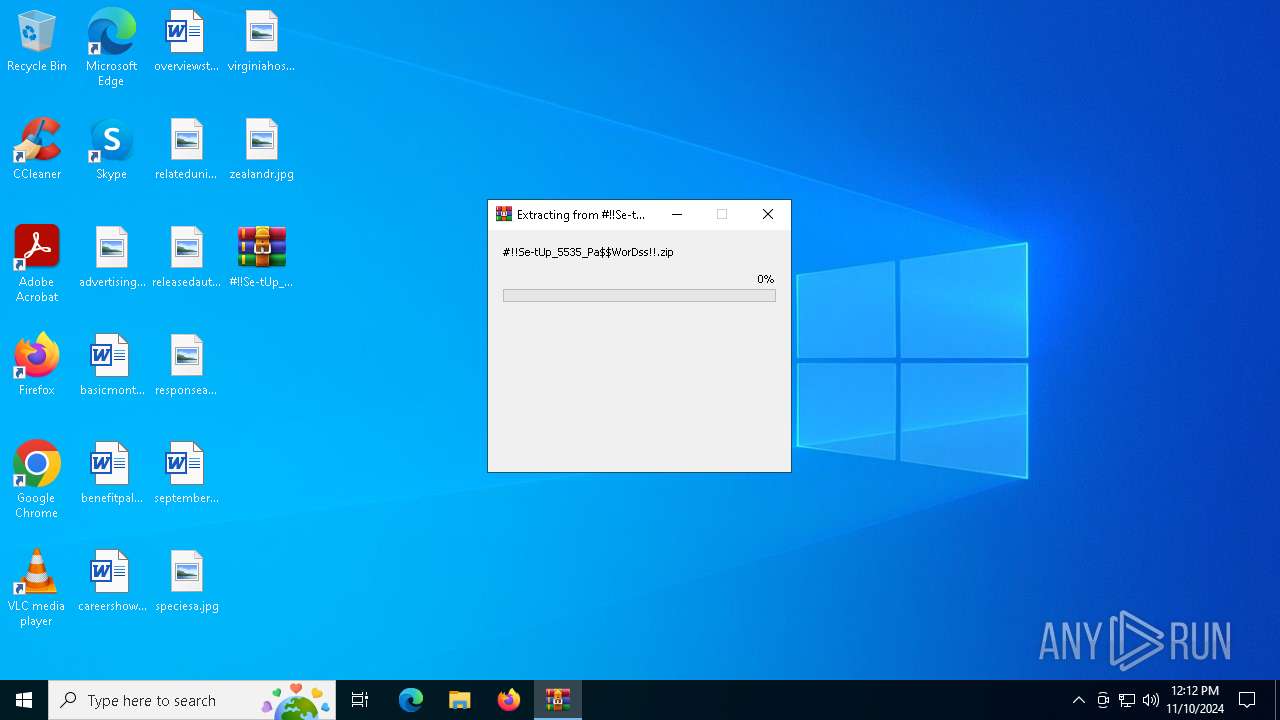
| File name: | #!!Se-tUp_5535_Pa$WorDss!!.zip |
| Full analysis: | https://app.any.run/tasks/db854e69-91d3-4c93-8f43-8ab20e07cb55 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | November 10, 2024, 12:12:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 4289CFF23FBEC05A14B48A348C2EAB9F |
| SHA1: | 680ECB32DBFC418ECC6BA16009320CEB7A456820 |
| SHA256: | 3116703902837436B688D28A4235BDB037DC9305DD0956D0A38BC59E83E1E758 |
| SSDEEP: | 98304:hUifXkyp4fs59uOwtkULUizM9MK0LZ3/eCwFh+WcaXn6F6LQOPaLJRULkJB0v4C3:Y/OemLj |
MALICIOUS
Changes powershell execution policy (Bypass)
- Boebera.pif (PID: 6356)
- powershell.exe (PID: 5400)
Bypass execution policy to execute commands
- powershell.exe (PID: 5400)
- powershell.exe (PID: 6248)
AMADEY has been detected (YARA)
- explorer.exe (PID: 632)
AMADEY has been detected (SURICATA)
- explorer.exe (PID: 632)
Actions looks like stealing of personal data
- Boebera.pif (PID: 6356)
Connects to the CnC server
- explorer.exe (PID: 632)
SUSPICIOUS
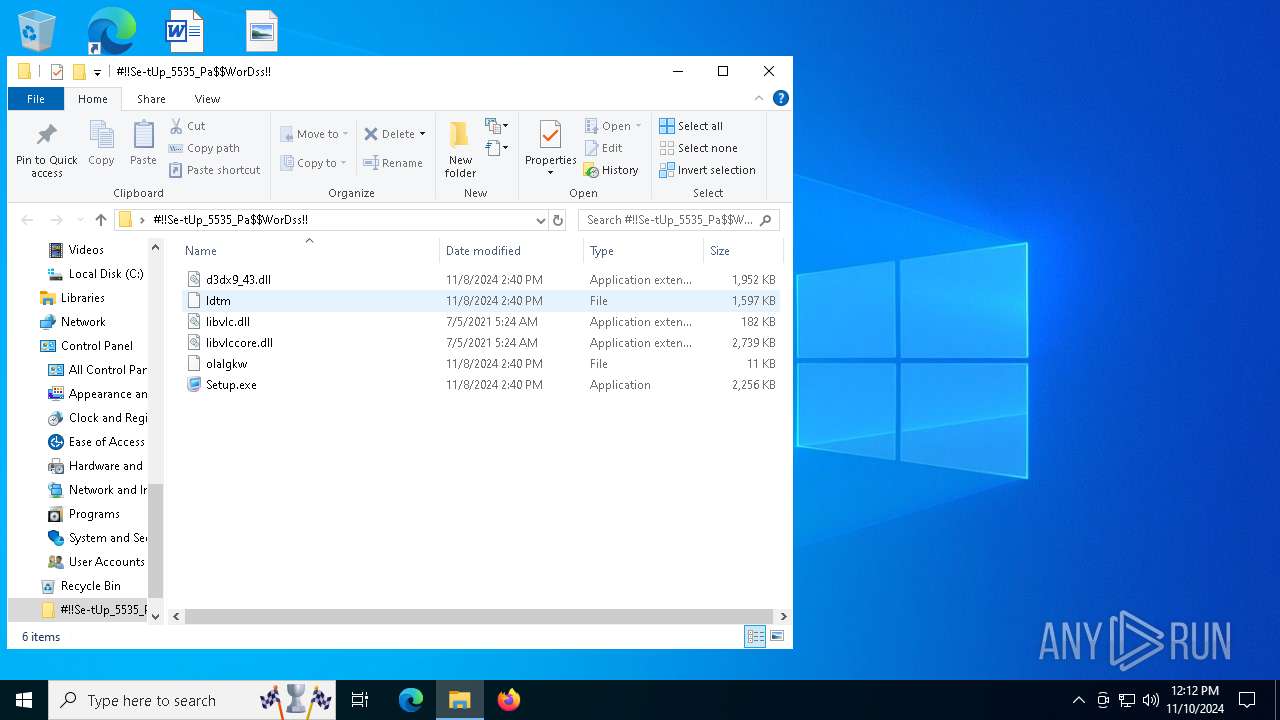
Process drops legitimate windows executable
- WinRAR.exe (PID: 5532)
- WinRAR.exe (PID: 6660)
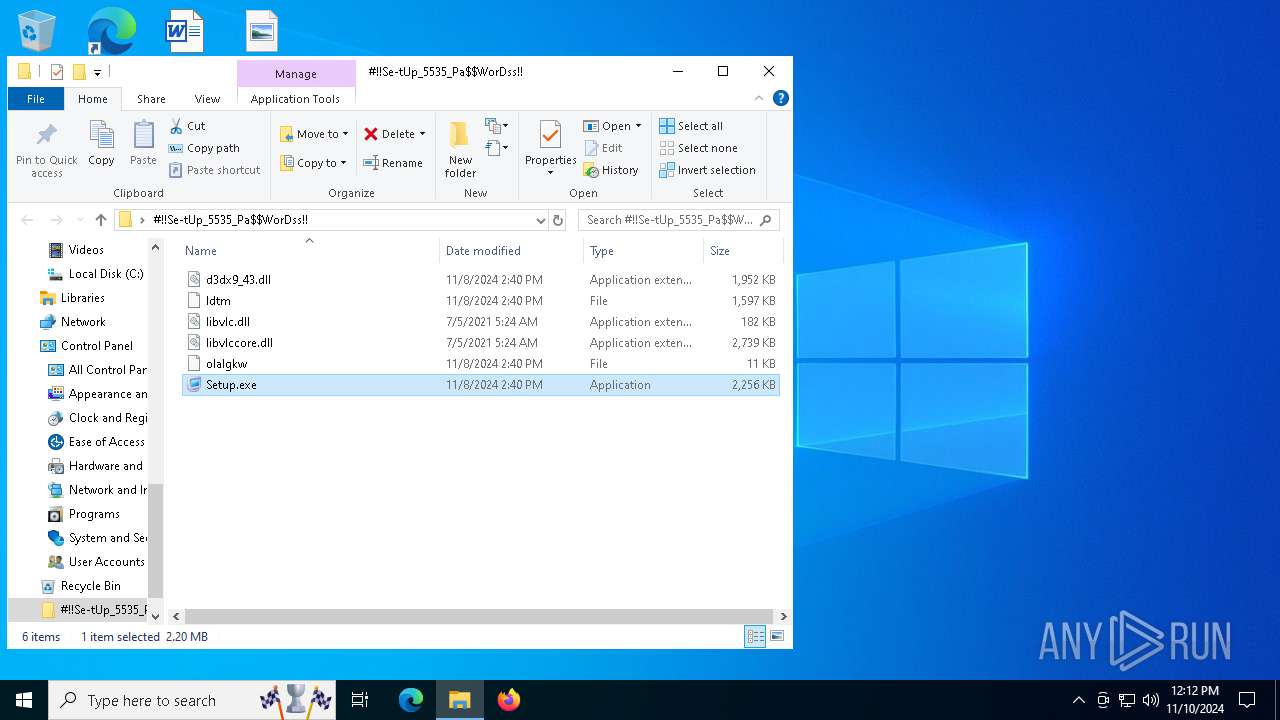
- Setup.exe (PID: 5832)
Executable content was dropped or overwritten
- Setup.exe (PID: 5832)
- choice.exe (PID: 6200)
- Boebera.pif (PID: 6356)
Checks for Java to be installed
- nc.exe (PID: 6256)
Drops a file with a rarely used extension (PIF)
- choice.exe (PID: 6200)
- Boebera.pif (PID: 6356)
Starts application with an unusual extension
- choice.exe (PID: 6200)
- Boebera.pif (PID: 6356)
Starts POWERSHELL.EXE for commands execution
- Boebera.pif (PID: 6356)
- powershell.exe (PID: 5400)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 5400)
Application launched itself
- powershell.exe (PID: 5400)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 5400)
Base64-obfuscated command line is found
- powershell.exe (PID: 5400)
There is functionality for communication over UDP network (YARA)
- G9UWOMZDMQ5S3T0CW.exe (PID: 3836)
The process executes Powershell scripts
- Boebera.pif (PID: 6356)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 5400)
Starts itself from another location
- Boebera.pif (PID: 6356)
There is functionality for enable RDP (YARA)
- explorer.exe (PID: 632)
Contacting a server suspected of hosting an CnC
- explorer.exe (PID: 632)
Checks whether the computer is part of a domain (POWERSHELL)
- powershell.exe (PID: 6248)
INFO
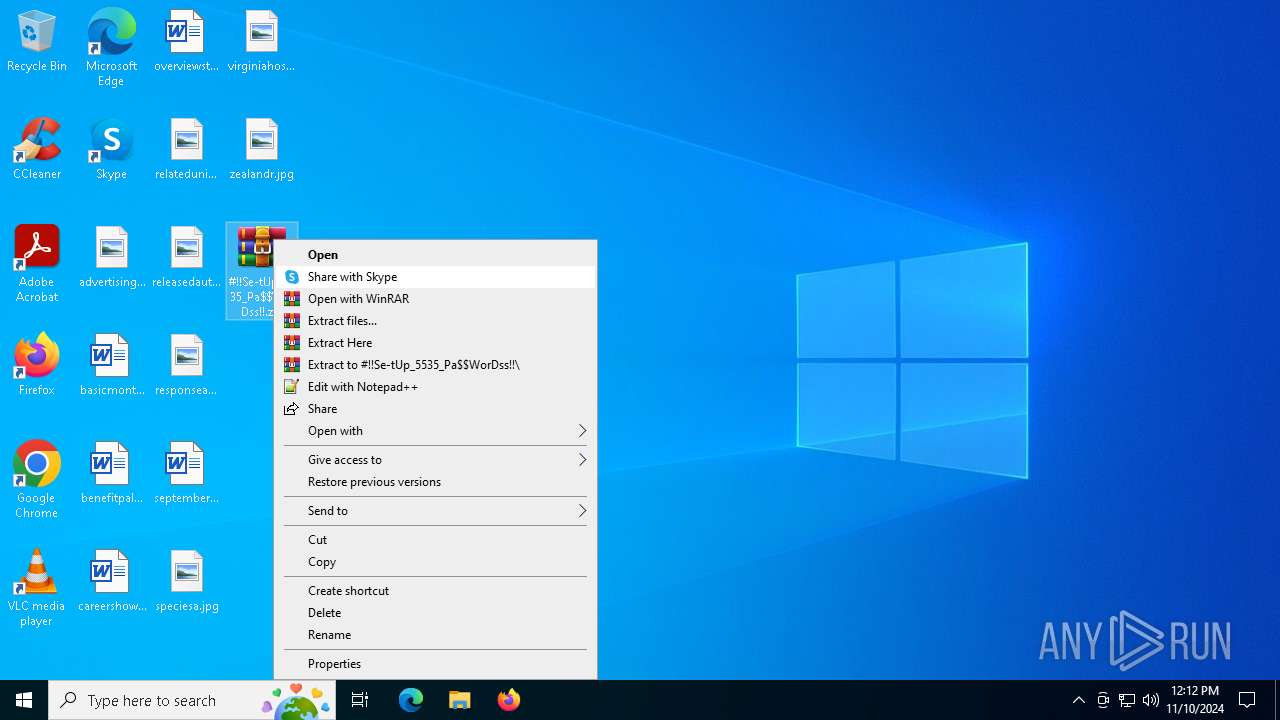
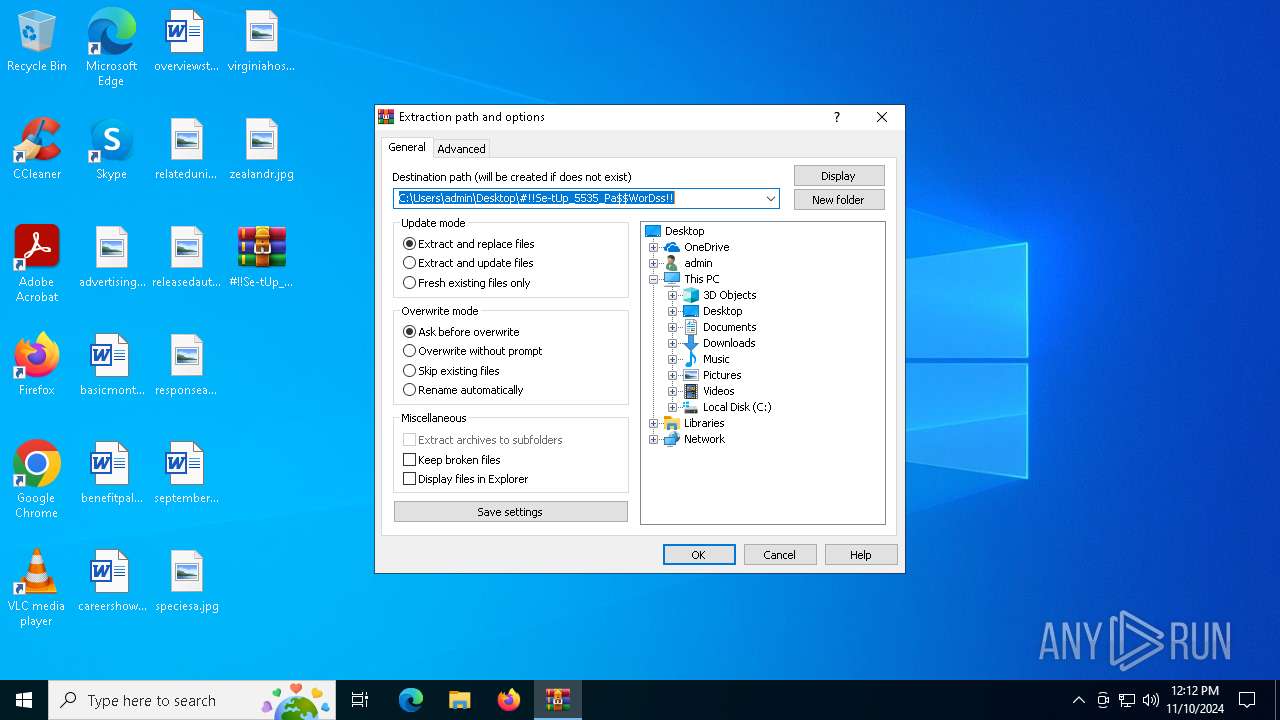
Manual execution by a user
- WinRAR.exe (PID: 6660)
- Setup.exe (PID: 5832)
The process uses the downloaded file
- WinRAR.exe (PID: 6660)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6660)
Checks supported languages
- Setup.exe (PID: 5832)
- nc.exe (PID: 6256)
- Boebera.pif (PID: 6356)
- G9UWOMZDMQ5S3T0CW.exe (PID: 3836)
- 75M4VU.pif (PID: 3568)
Reads the computer name
- Setup.exe (PID: 5832)
- Boebera.pif (PID: 6356)
- G9UWOMZDMQ5S3T0CW.exe (PID: 3836)
Creates files or folders in the user directory
- Setup.exe (PID: 5832)
- Boebera.pif (PID: 6356)
Create files in a temporary directory
- nc.exe (PID: 6256)
- choice.exe (PID: 6200)
- Setup.exe (PID: 5832)
- G9UWOMZDMQ5S3T0CW.exe (PID: 3836)
- Boebera.pif (PID: 6356)
- choice.exe (PID: 6688)
Creates files in the program directory
- nc.exe (PID: 6256)
- choice.exe (PID: 6200)
Disables trace logs
- powershell.exe (PID: 5400)
Reads the software policy settings
- Boebera.pif (PID: 6356)
Checks proxy server information
- powershell.exe (PID: 5400)
- explorer.exe (PID: 632)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6248)
Reads mouse settings
- 75M4VU.pif (PID: 3568)
Reads Windows Product ID
- 75M4VU.pif (PID: 3568)
Reads CPU info
- 75M4VU.pif (PID: 3568)
Reads security settings of Internet Explorer
- explorer.exe (PID: 632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:11:08 15:40:50 |
| ZipCRC: | 0x0356bb1d |
| ZipCompressedSize: | 893381 |
| ZipUncompressedSize: | 1998168 |
| ZipFileName: | d3dx9_43.dll |
Total processes
152
Monitored processes
19
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\SysWOW64\explorer.exe | C:\Windows\SysWOW64\explorer.exe | choice.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1792 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\AppData\Roaming\75M4VU.pif" "C:\Users\admin\AppData\Roaming\CSFES7.rar" | C:\Users\admin\AppData\Roaming\75M4VU.pif | — | Boebera.pif | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 3836 | "C:\Users\admin\AppData\Local\Temp\G9UWOMZDMQ5S3T0CW.exe" | C:\Users\admin\AppData\Local\Temp\G9UWOMZDMQ5S3T0CW.exe | Boebera.pif | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 4032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4224 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | nc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4448 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\SJAZAAMTYRDCYKK6ACGJ1SB.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | Boebera.pif | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5532 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\#!!Se-tUp_5535_Pa$WorDss!!.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
Total events
13 339
Read events
13 294
Write events
32
Delete events
13
Modification events
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000009E02050000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000880204000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (5532) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F0000000000000000000000000000000000000000000700205000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (6660) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
Executable files
9
Suspicious files
8
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6200 | choice.exe | C:\Users\admin\AppData\Local\Temp\nobpjfxa | — | |
MD5:— | SHA256:— | |||
| 6660 | WinRAR.exe | C:\Users\admin\Desktop\#!!Se-tUp_5535_Pa$WorDss!!\libvlc.dll | executable | |
MD5:606A798E56FA5E4477811D150A4917C6 | SHA256:5A6A1856AAA5FDCCEC2679A4E12FFFC948ED64677228FC1E0EB3710924892F26 | |||
| 6256 | nc.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:A558656305445C8B51B027DC903D4476 | SHA256:DD32D32D3F7147E91285823C9646749B09BA7CF70DDEAB81744D4F0771D3B02F | |||
| 6356 | Boebera.pif | C:\Users\admin\AppData\Roaming\CSFES7.rar | — | |
MD5:— | SHA256:— | |||
| 6660 | WinRAR.exe | C:\Users\admin\Desktop\#!!Se-tUp_5535_Pa$WorDss!!\olalgkw | binary | |
MD5:B8220007E0F79A66D341A46F19A8D82A | SHA256:9D1EB829A1E7B7C0DE093C7776C3FFB9EE355F006349FDC8830DFDF71DCF5FA9 | |||
| 5832 | Setup.exe | C:\Users\admin\AppData\Roaming\IPA\ldtm | abr | |
MD5:37DF3DE27068E21CF5D32EF328533457 | SHA256:690AA6FAE4216F7A7659C725EF2E5666EBB844FD5AA3B15B1E330D39546D5A64 | |||
| 5832 | Setup.exe | C:\Users\admin\AppData\Roaming\IPA\d3dx9_43.dll | executable | |
MD5:EED7D66199C8ADF3BB48AA2C991900D2 | SHA256:C27998FC2F30041F8FE194141CBCB637893D6B0A83C40D769058175F8EFF014C | |||
| 6688 | choice.exe | C:\Users\admin\AppData\Local\Temp\oqvsalqw | — | |
MD5:— | SHA256:— | |||
| 5832 | Setup.exe | C:\Users\admin\AppData\Roaming\IPA\SZWQZQZEVPKFGVMLJTMFNIZXI\nc.exe | executable | |
MD5:7FB44C5BCA4226D8AAB7398E836807A2 | SHA256:A64EAD73C06470BC5C84CFC231B0723D70D29FEC7D385A268BE2C590DC5EB1EF | |||
| 5832 | Setup.exe | C:\Users\admin\AppData\Roaming\IPA\olalgkw | binary | |
MD5:B8220007E0F79A66D341A46F19A8D82A | SHA256:9D1EB829A1E7B7C0DE093C7776C3FFB9EE355F006349FDC8830DFDF71DCF5FA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
52
DNS requests
28
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5196 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6152 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
632 | explorer.exe | POST | 200 | 172.67.213.173:80 | http://moviecentral-petparade.com/g9jvjfd73/index.php | unknown | — | — | malicious |
632 | explorer.exe | POST | 200 | 172.67.213.173:80 | http://moviecentral-petparade.com/g9jvjfd73/index.php | unknown | — | — | malicious |
2364 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6152 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1588 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2364 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2364 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4360 | SearchApp.exe | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious Domain by Cloudflare (moviecentral-petparade .com) |
632 | explorer.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
4 ETPRO signatures available at the full report