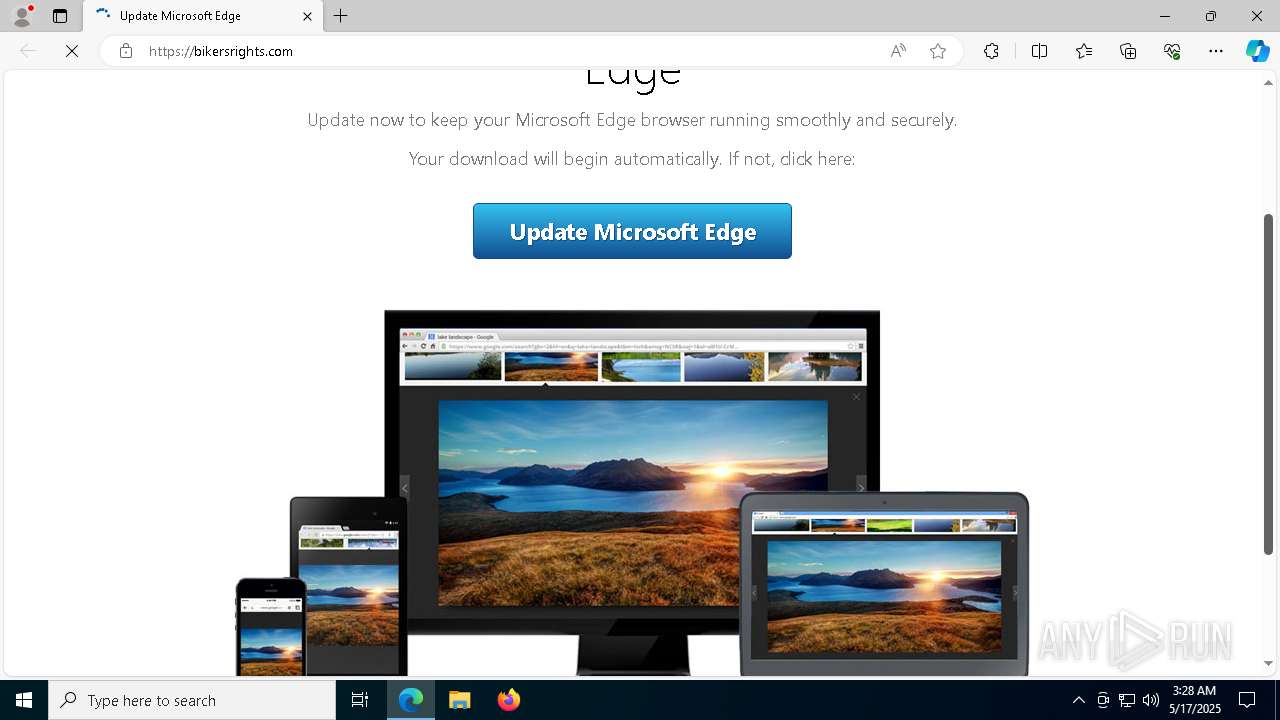
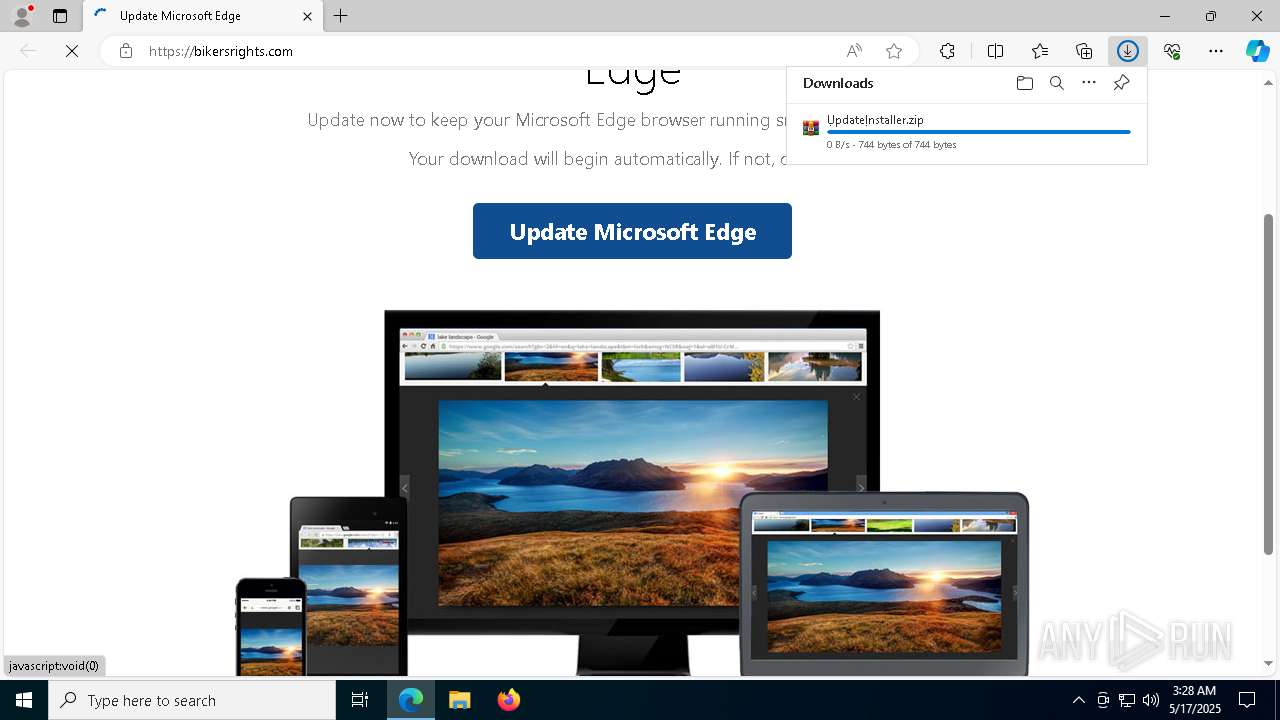
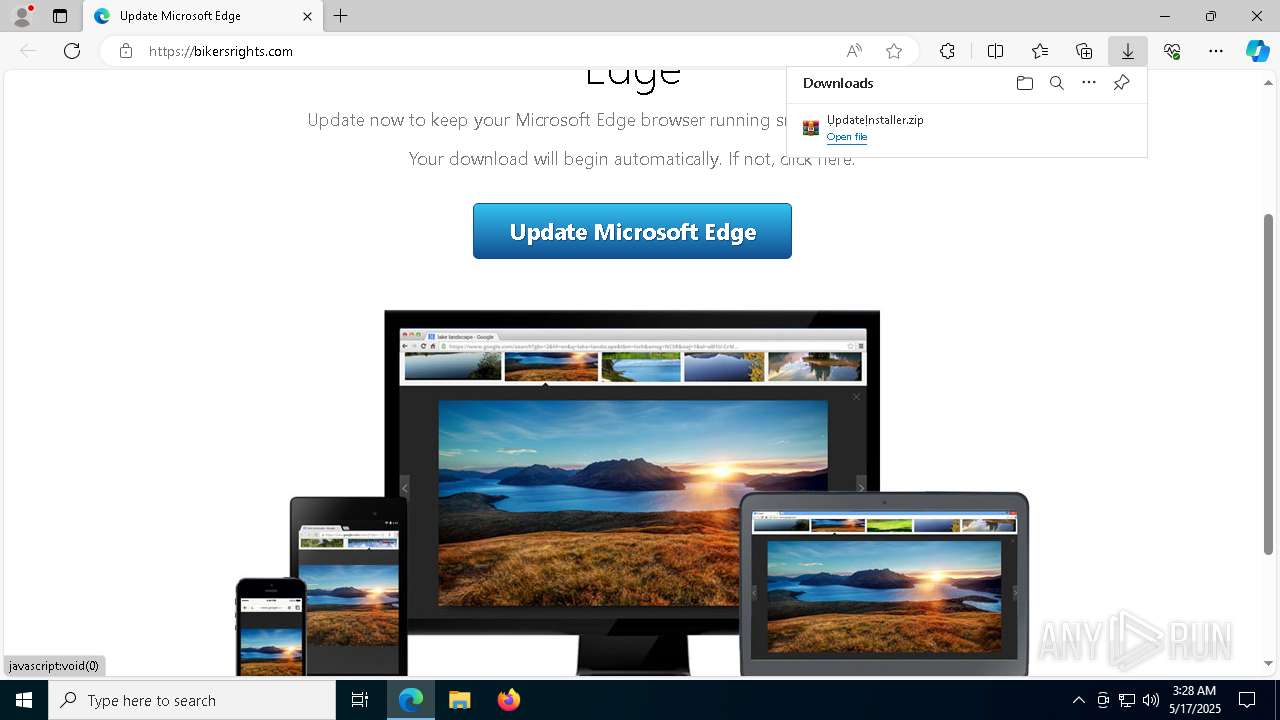
| URL: | https://bikersrights.com |
| Full analysis: | https://app.any.run/tasks/6a0169ff-738d-4df7-8026-ebf355196b42 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 17, 2025, 03:28:32 |
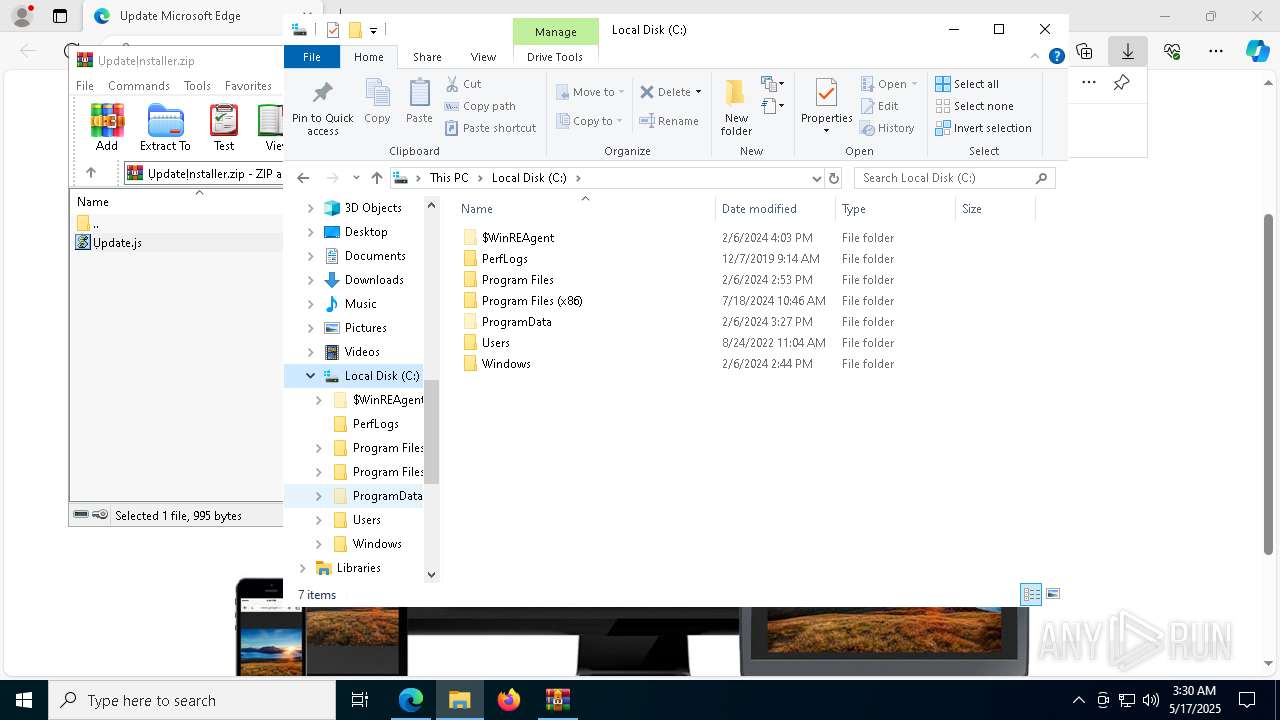
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C26CA69C472B4E275B3F401844B92AA7 |
| SHA1: | 92ADBA152749FB3D5B297EC0D7EE9F199E517A9C |
| SHA256: | 306CCB4B9B9812408EF050490117EF246170842F0BF2016845267B1EF84E799A |
| SSDEEP: | 3:N8fMCNRMK:2fRR |
MALICIOUS
SOCGHOLISH has been detected (SURICATA)
- msedge.exe (PID: 7588)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 1388)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 1388)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 1388)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 1388)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 1388)
Accesses BIOS(Win32_BIOS, may evade sandboxes) via WMI (SCRIPT)
- wscript.exe (PID: 1388)
Accesses information about the status of the installed antivirus(Win32_AntivirusProduct) via WMI (SCRIPT)
- wscript.exe (PID: 1388)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 1388)
Connects to the CnC server
- powershell.exe (PID: 8932)
ASYNCRAT has been detected (SURICATA)
- powershell.exe (PID: 8932)
Accesses name of a computer manufacturer via WMI (SCRIPT)
- wscript.exe (PID: 1388)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1132)
The process executes JS scripts
- WinRAR.exe (PID: 1132)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 1388)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 1388)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 1388)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- wscript.exe (PID: 1388)
Access Product Name via WMI (SCRIPT)
- wscript.exe (PID: 1388)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 1388)
Accesses WMI object display name (SCRIPT)
- wscript.exe (PID: 1388)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- wscript.exe (PID: 1388)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 1388)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1388)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 1388)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1388)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 1388)
Accesses antivirus product name via WMI (SCRIPT)
- wscript.exe (PID: 1388)
INFO
Application launched itself
- msedge.exe (PID: 7284)
Reads Environment values
- identity_helper.exe (PID: 6632)
Checks supported languages
- identity_helper.exe (PID: 6632)
Reads the computer name
- identity_helper.exe (PID: 6632)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7284)
- WinRAR.exe (PID: 1132)
Checks proxy server information
- wscript.exe (PID: 1388)
- powershell.exe (PID: 8932)
- slui.exe (PID: 616)
Disables trace logs
- powershell.exe (PID: 8932)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8932)
Reads the software policy settings
- slui.exe (PID: 8184)
- slui.exe (PID: 616)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8932)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
212
Monitored processes
79
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5616 --field-trial-handle=2436,i,8738418385624873269,18307135442237294217,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
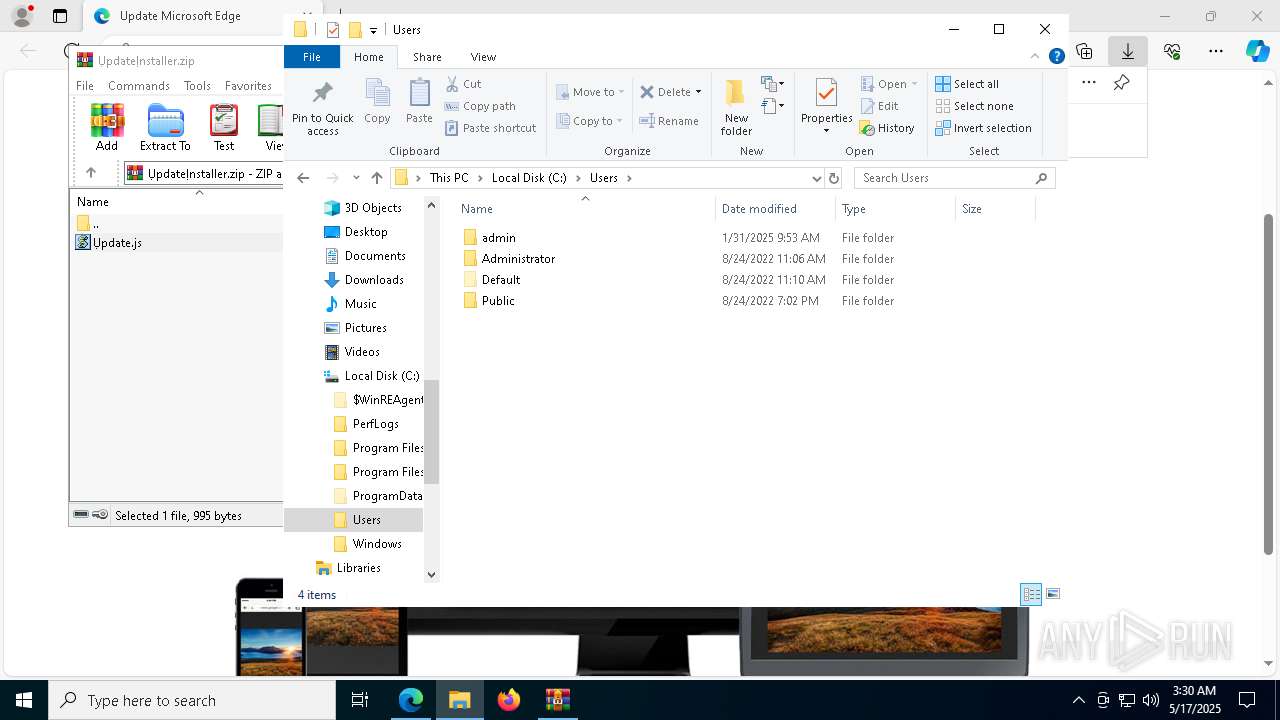
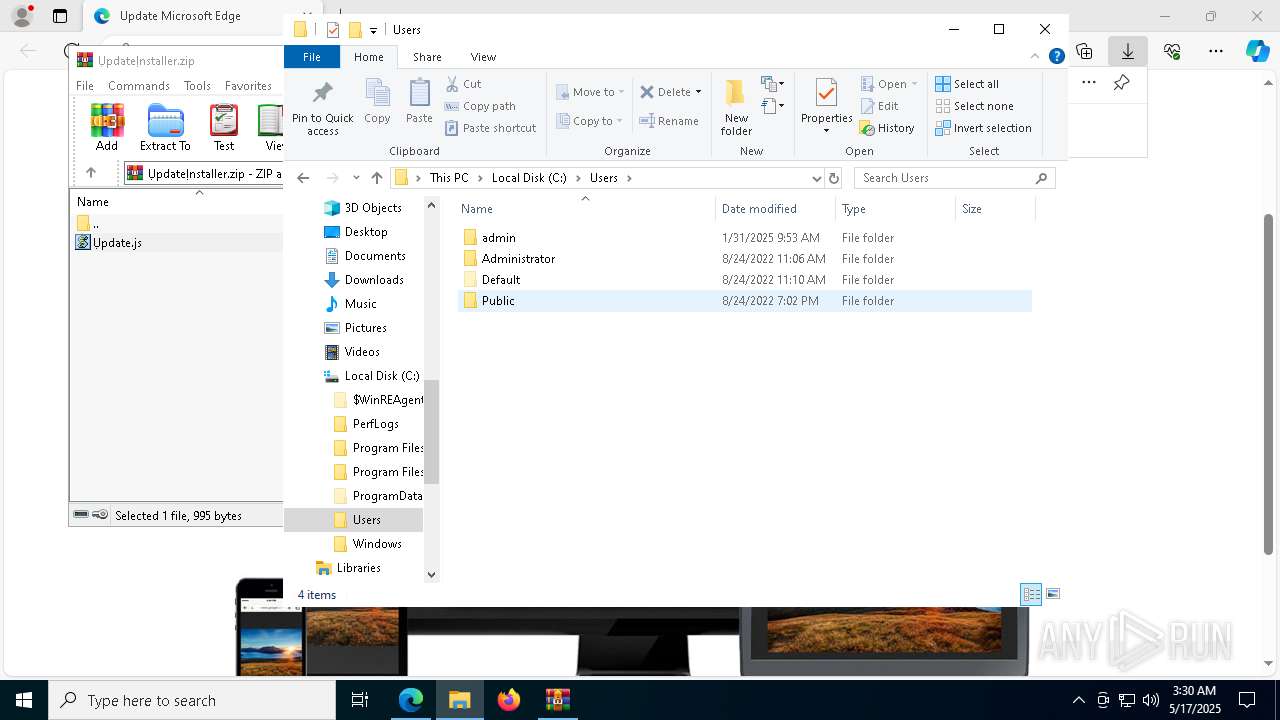
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4344 --field-trial-handle=2436,i,8738418385624873269,18307135442237294217,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=7944 --field-trial-handle=2436,i,8738418385624873269,18307135442237294217,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=5916 --field-trial-handle=2436,i,8738418385624873269,18307135442237294217,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
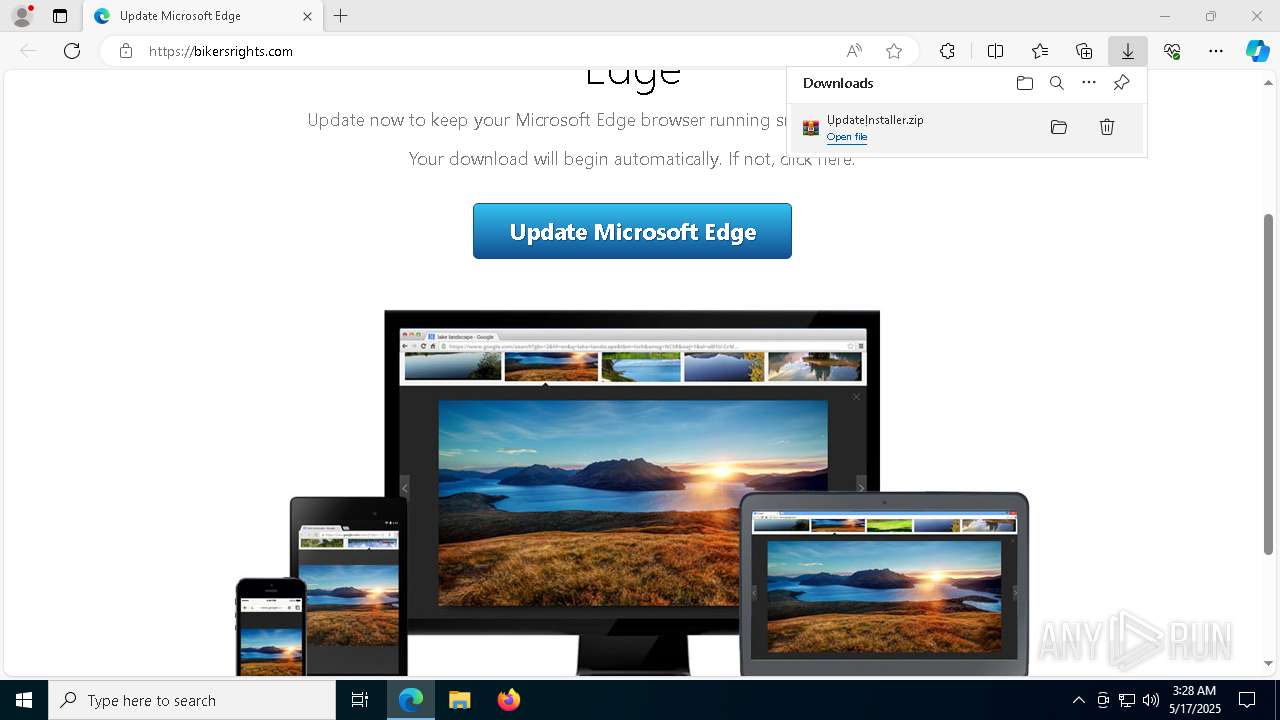
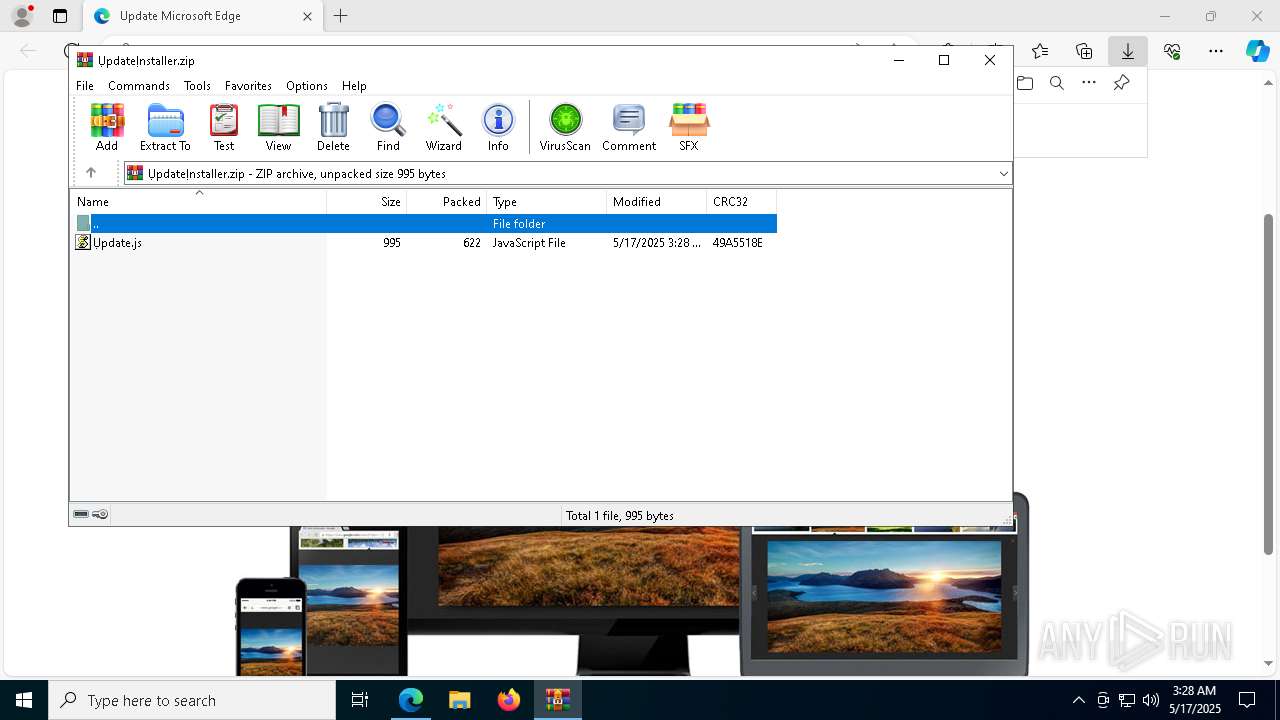
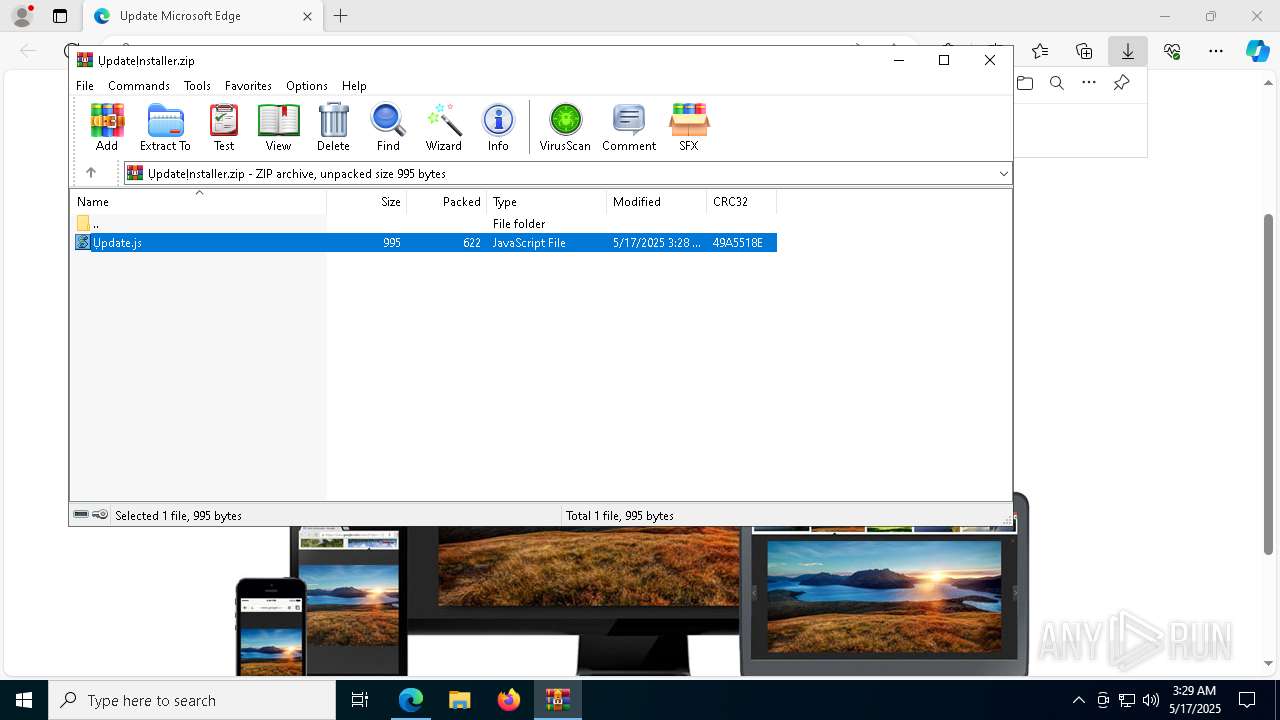
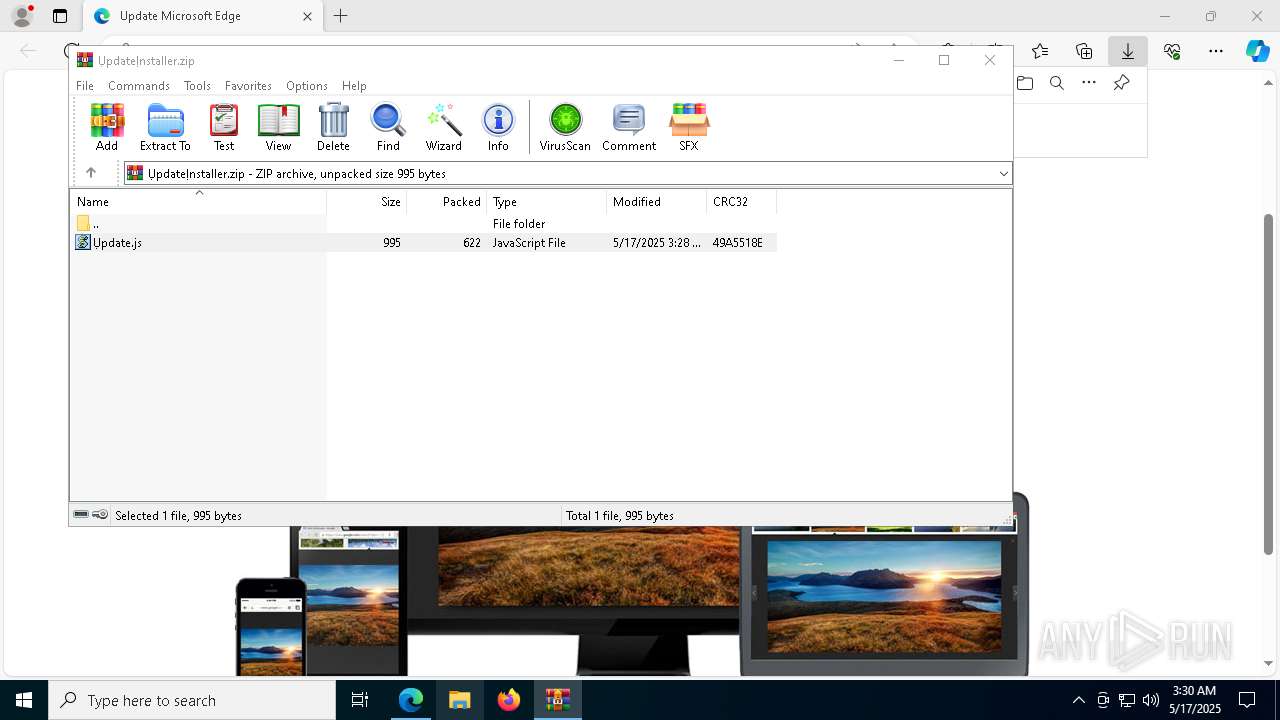
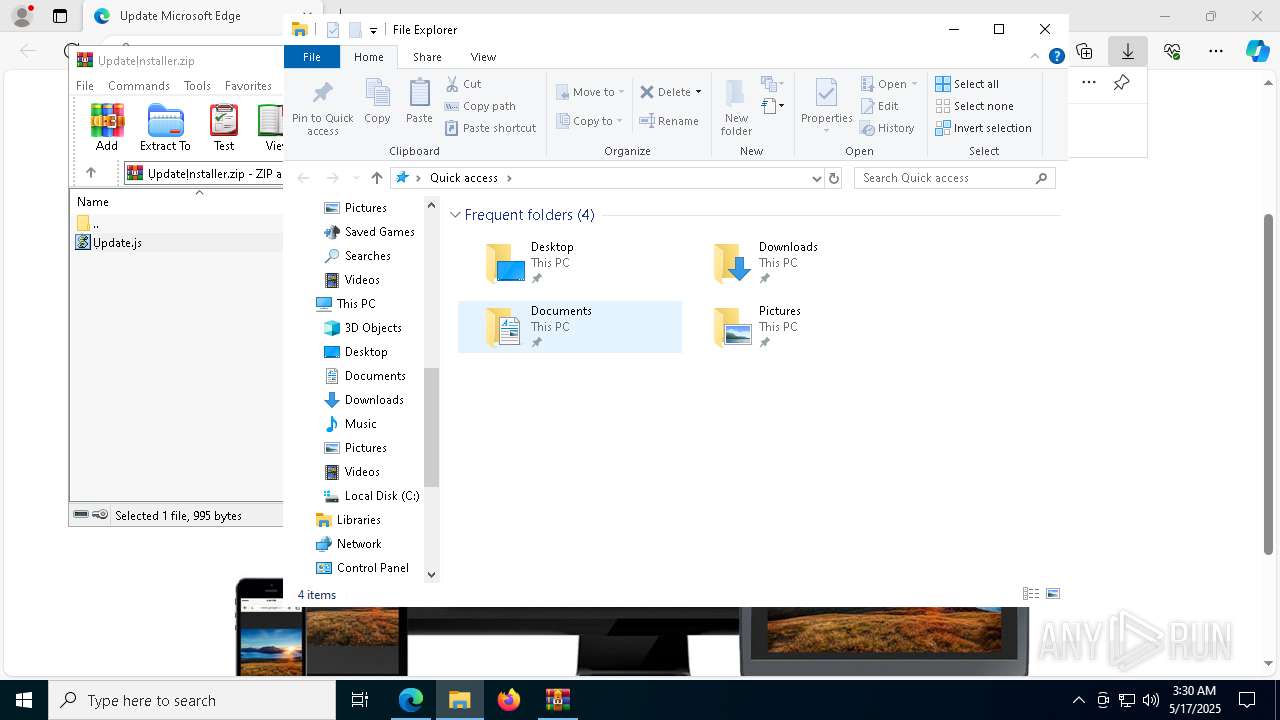
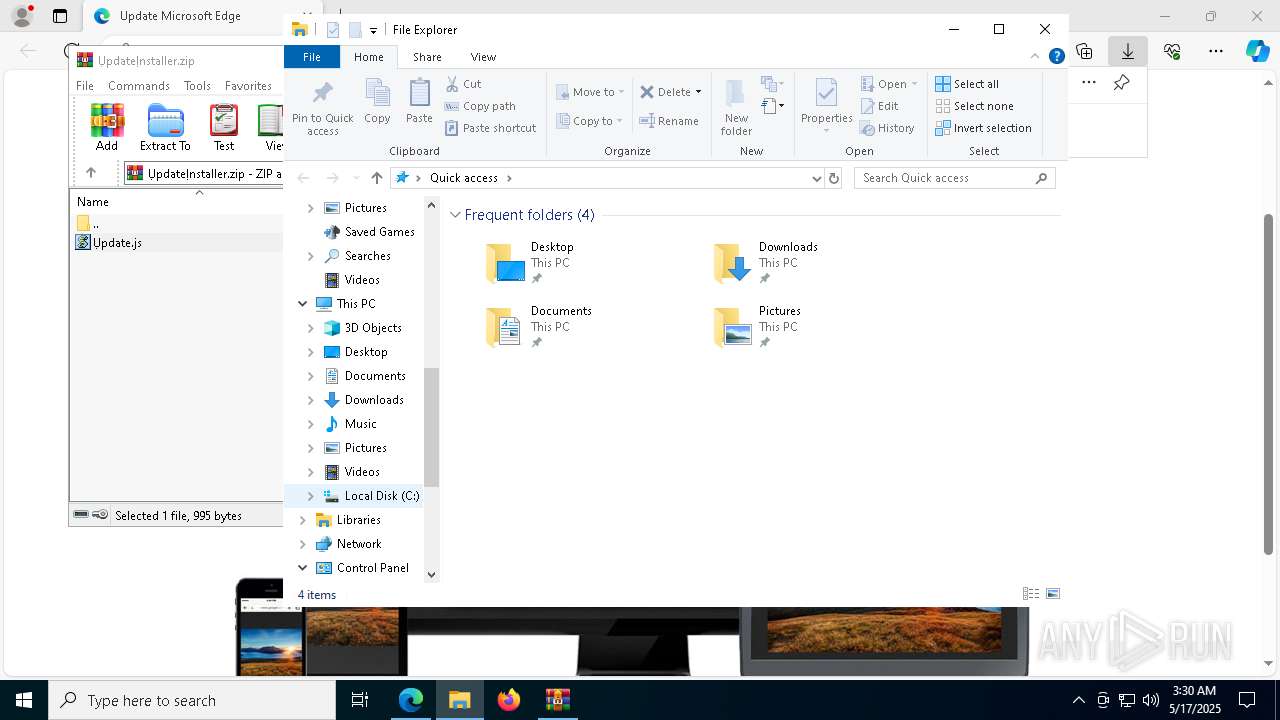
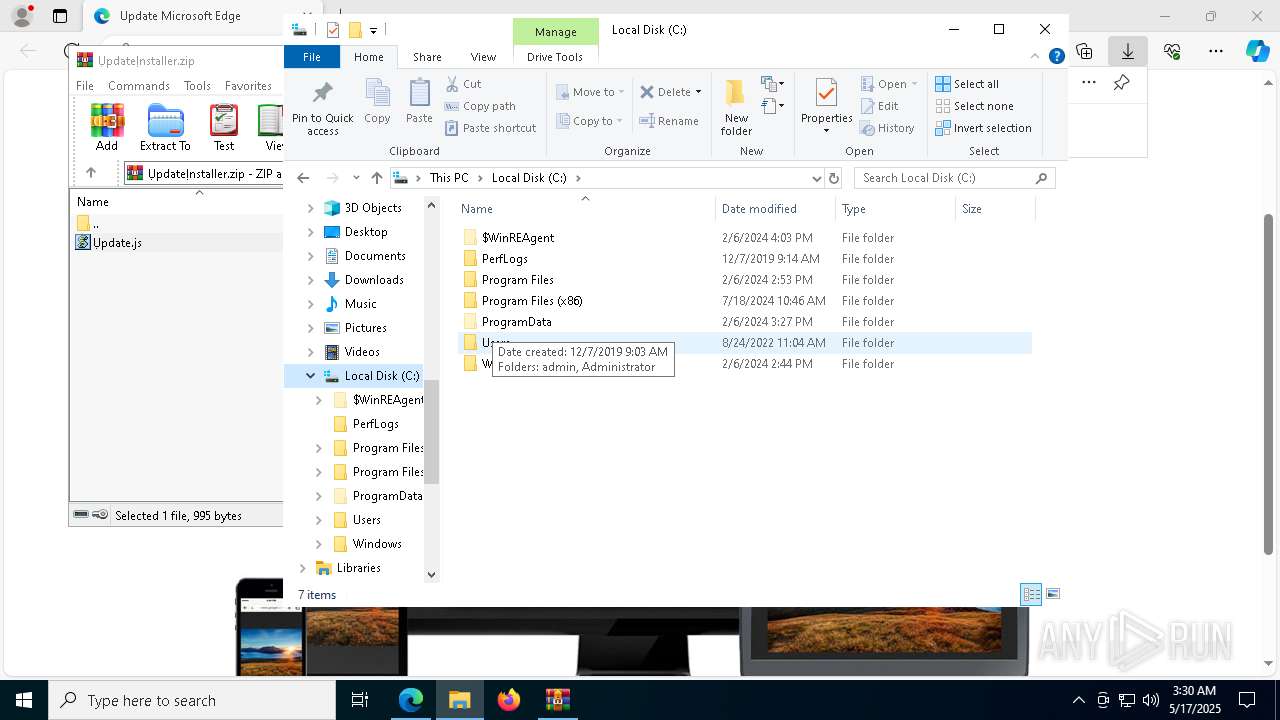
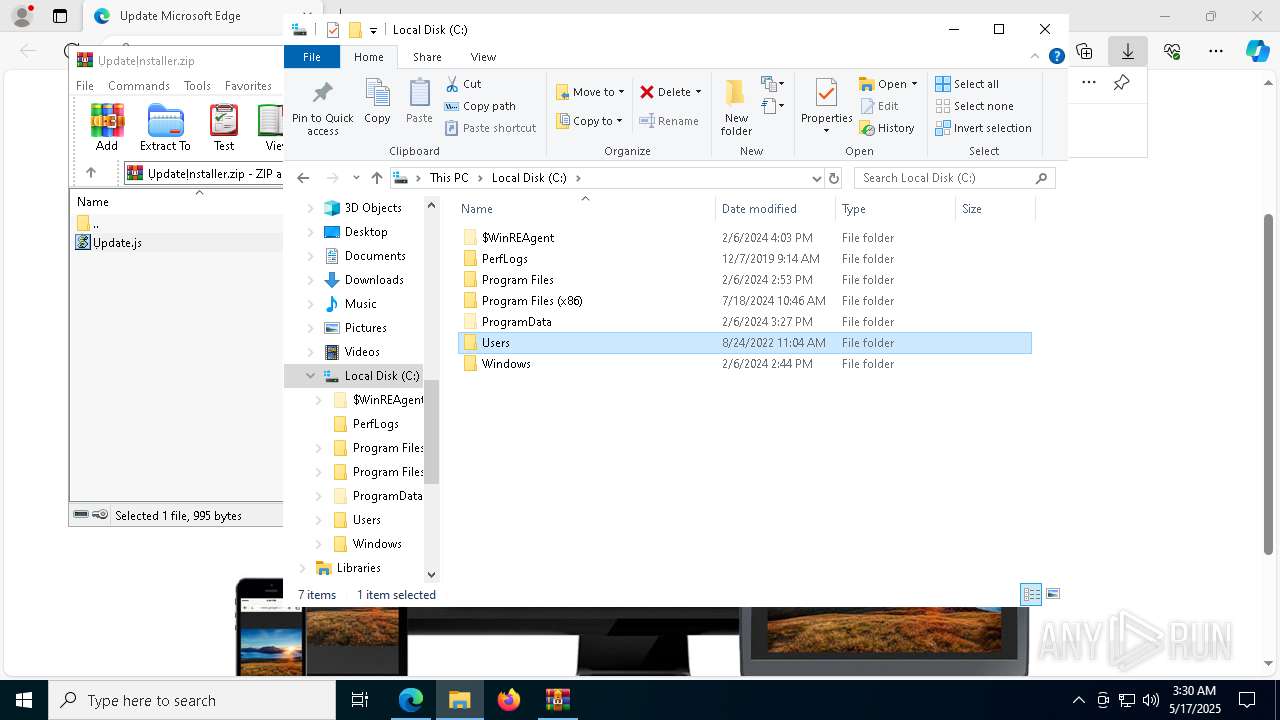
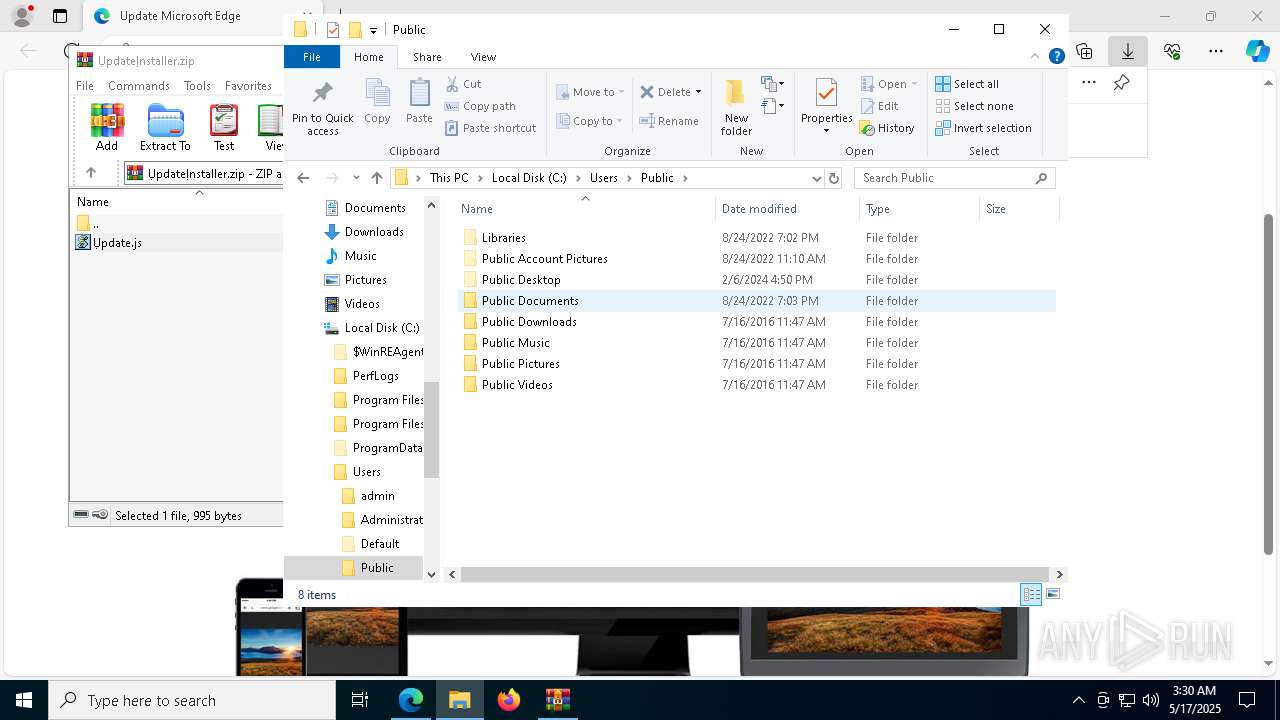
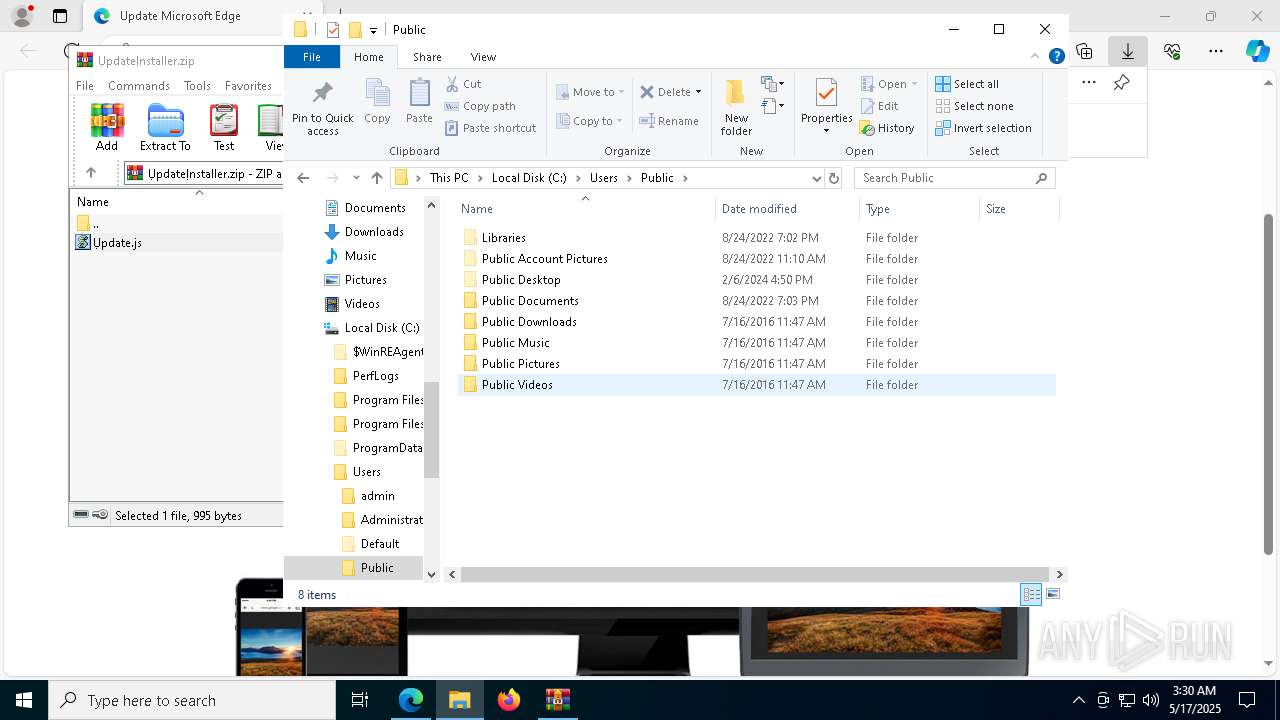
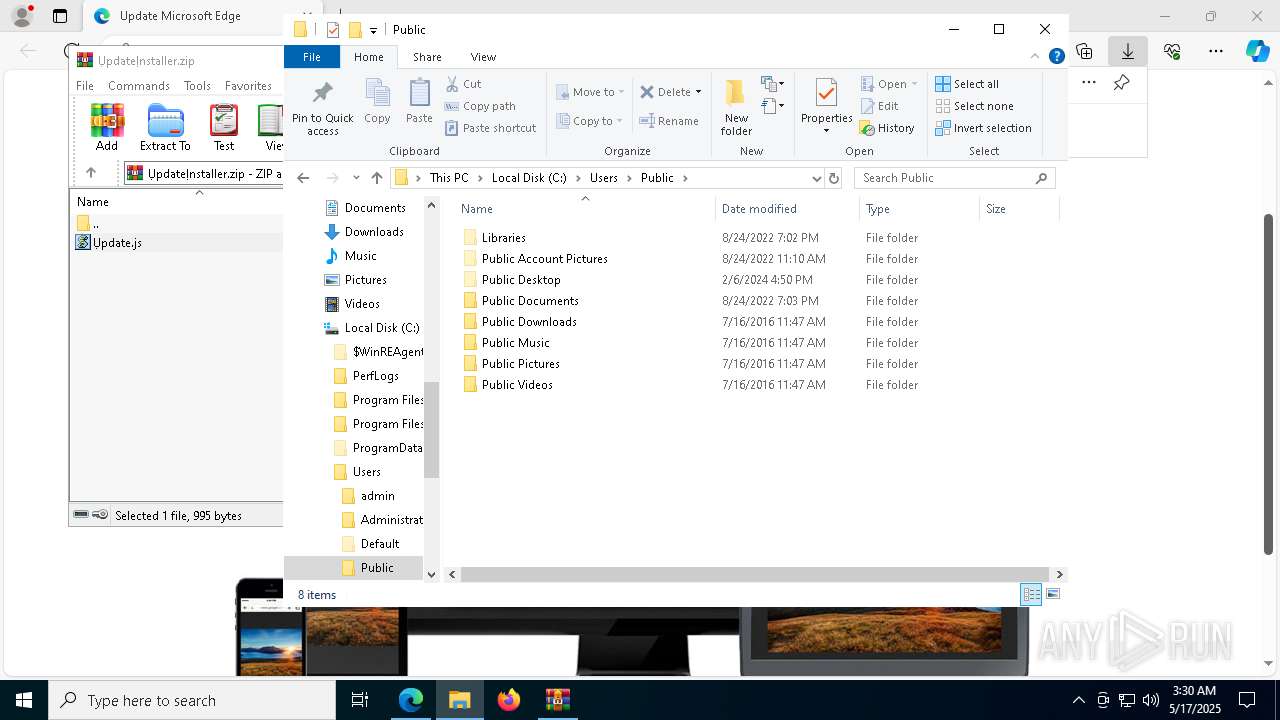
| 1132 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ỤрdateỊnstаӀӀer.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=9864 --field-trial-handle=2436,i,8738418385624873269,18307135442237294217,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa1132.35190\Ụрdate.js" | C:\Windows\System32\wscript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=10212 --field-trial-handle=2436,i,8738418385624873269,18307135442237294217,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5564 --field-trial-handle=2436,i,8738418385624873269,18307135442237294217,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 469
Read events
17 423
Write events
46
Delete events
0
Modification events
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 17C424C7E2932F00 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 760E2EC7E2932F00 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {319D4237-BE99-444E-A7BA-D401C6996EE0} | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {71C26AF9-1ED6-4FC9-BF90-7B747A8F4581} | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2AB49FC5-3C03-47E7-B698-5C952EF94BA7} | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262918 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5F3E6CD5-3EDE-439F-908C-9B7DD0C44B04} | |||
Executable files
14
Suspicious files
258
Text files
50
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b7f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b7f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
243
DNS requests
338
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7588 | msedge.exe | GET | 200 | 44.193.98.224:80 | http://classic.avantlink.com/affiliate_app_confirm.php?mode=js&authResponse=01d4b1c43253cc94b46817977f1dadeff1554aba | unknown | — | — | whitelisted |
1388 | wscript.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1388 | wscript.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCECO3bePBuysaUZYeCOq3ZOg%3D | unknown | — | — | whitelisted |
6740 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1388 | wscript.exe | GET | 200 | 172.64.149.23:80 | http://zerossl.ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQzH%2F4%2F%2FQuEFihPlI1WwH4Dktj2TQQUD2vmS845R672fpAeefAwkZLIX6MCEQDi1CBwdq0Cth2Kx2T1U3cl | unknown | — | — | whitelisted |
6740 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5116 | svchost.exe | HEAD | 200 | 2.22.242.122:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747702797&P2=404&P3=2&P4=CZoQoH5n48qfac2ihzLPmkraNu687N%2f%2b6sEN6BF%2bl9aq8uN0MP%2f1ckI3nYCtFFvuA%2bwXJAp%2bKHPc%2bGCZrnwOTg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7588 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7588 | msedge.exe | 45.40.149.75:443 | bikersrights.com | — | — | unknown |
7588 | msedge.exe | 172.217.18.8:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
7284 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
bikersrights.com |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
ads.adthrive.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7588 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7588 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7588 | msedge.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (customer .thewayofmoney .us) |
7588 | msedge.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (customer .thewayofmoney .us) |
7588 | msedge.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in TLS SNI (customer .thewayofmoney .us) |
7588 | msedge.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
7588 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7588 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7588 | msedge.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (customer .thewayofmoney .us) |
7588 | msedge.exe | A Network Trojan was detected | ET MALWARE SocGholish Domain in DNS Lookup (customer .thewayofmoney .us) |