| File name: | chrome.exe |
| Full analysis: | https://app.any.run/tasks/538cd4be-1822-4580-a36a-ae010eef33ec |
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
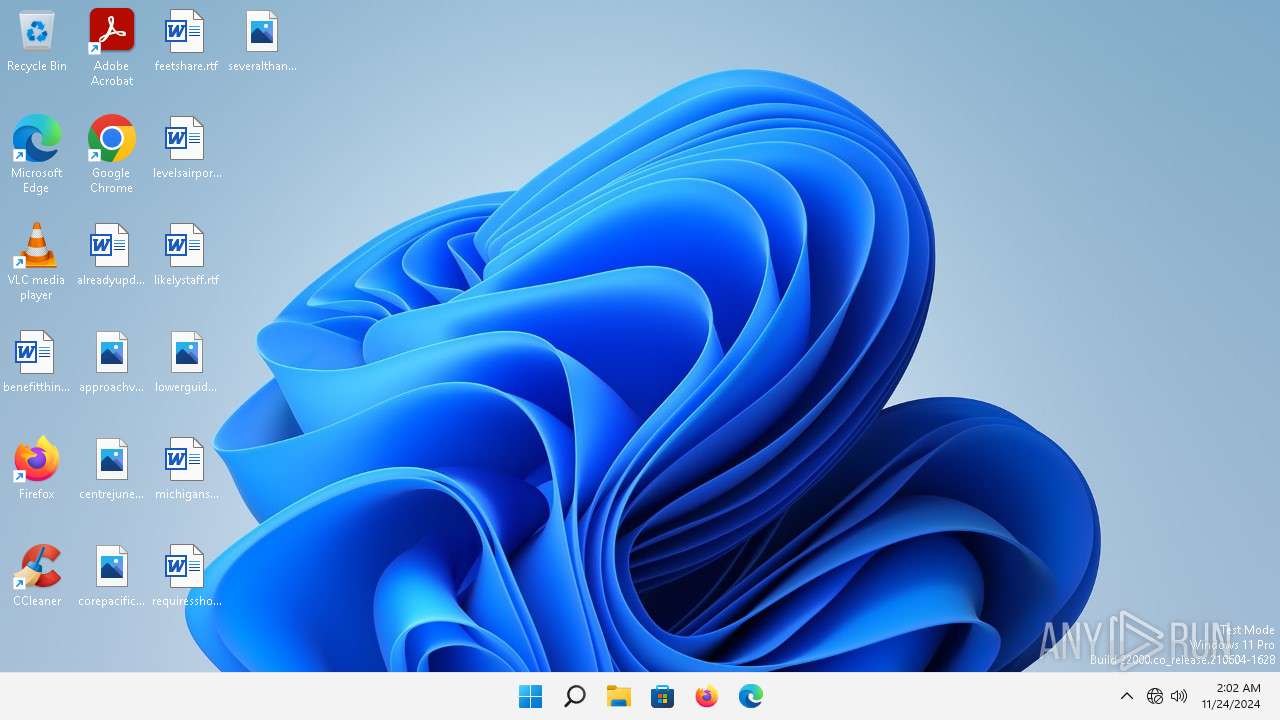
| Analysis date: | November 24, 2024, 02:02:24 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | EA6D73FE2F7FBA7318D12626A0AB4DBB |
| SHA1: | 3B37DC8A1028E2B145D48593092852D4F0D2D2B1 |
| SHA256: | 302E4ADBA81CFD49955664B2FDCD207A0E5DA8BBBECFC1F4EB789603001C80D2 |
| SSDEEP: | 98304:NJ3zxT+GmE/ZsG6TRAXfjE+DkVkFOBNdtL6aMvZA4OF8SA2ibMlq0TlATkO36fqs:fqxqeLLB44a+bAdjRUbdUe |
MALICIOUS
Executing a file with an untrusted certificate
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5452)
- chrome.exe (PID: 5092)
- chrome.exe (PID: 740)
BlankGrabber has been detected
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5092)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 2984)
- MpCmdRun.exe (PID: 7928)
Adds path to the Windows Defender exclusion list
- chrome.exe (PID: 740)
- cmd.exe (PID: 1832)
- cmd.exe (PID: 6500)
Changes Controlled Folder Access settings
- powershell.exe (PID: 3896)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 3896)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 3896)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 3896)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 3896)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 3896)
Changes settings for real-time protection
- powershell.exe (PID: 3896)
Bypass execution policy to execute commands
- powershell.exe (PID: 7632)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7288)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 7928)
GROWTOPIA has been detected (YARA)
- chrome.exe (PID: 740)
DISCORDGRABBER has been detected (YARA)
- chrome.exe (PID: 740)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5092)
- chrome.exe (PID: 740)
Starts a Microsoft application from unusual location
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5452)
- chrome.exe (PID: 5092)
- chrome.exe (PID: 740)
Executable content was dropped or overwritten
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5092)
- chrome.exe (PID: 740)
- csc.exe (PID: 1384)
Process drops python dynamic module
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5092)
The process drops C-runtime libraries
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5092)
Reads the date of Windows installation
- chrome.exe (PID: 5452)
Application launched itself
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5452)
- chrome.exe (PID: 5092)
Reads the Internet Settings
- chrome.exe (PID: 5452)
Reads security settings of Internet Explorer
- chrome.exe (PID: 5452)
Get information on the list of running processes
- chrome.exe (PID: 740)
- cmd.exe (PID: 3324)
- cmd.exe (PID: 5060)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 2836)
- cmd.exe (PID: 3664)
Found strings related to reading or modifying Windows Defender settings
- chrome.exe (PID: 740)
Starts CMD.EXE for commands execution
- chrome.exe (PID: 740)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 2984)
Script disables Windows Defender's IPS
- cmd.exe (PID: 2984)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2984)
- cmd.exe (PID: 1832)
- cmd.exe (PID: 6500)
- cmd.exe (PID: 3464)
- cmd.exe (PID: 7288)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 4316)
- cmd.exe (PID: 1484)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 32)
- cmd.exe (PID: 2100)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 1832)
- cmd.exe (PID: 6500)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2428)
- cmd.exe (PID: 7988)
- cmd.exe (PID: 7328)
Starts application with an unusual extension
- cmd.exe (PID: 5960)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 6340)
- cmd.exe (PID: 4544)
Base64-obfuscated command line is found
- cmd.exe (PID: 7288)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 7288)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 7288)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7264)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 3524)
CSC.EXE is used to compile C# code
- csc.exe (PID: 1384)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7864)
- cmd.exe (PID: 756)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7944)
INFO
Reads the computer name
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5452)
- chrome.exe (PID: 5092)
Create files in a temporary directory
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5452)
- chrome.exe (PID: 5092)
Checks supported languages
- chrome.exe (PID: 1540)
- chrome.exe (PID: 5452)
- chrome.exe (PID: 5092)
The process uses the downloaded file
- chrome.exe (PID: 5452)
Checks the directory tree
- tree.com (PID: 7448)
- tree.com (PID: 7800)
- tree.com (PID: 8012)
- tree.com (PID: 8188)
- tree.com (PID: 1584)
- tree.com (PID: 3172)
The Powershell gets current clipboard
- powershell.exe (PID: 7308)
PyInstaller has been detected (YARA)
- chrome.exe (PID: 5092)
Found Base64 encoded reflection usage via PowerShell (YARA)
- chrome.exe (PID: 740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:11:22 23:28:06+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 172032 |
| InitializedDataSize: | 123392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce20 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10.0.19041.1 |
| ProductVersionNumber: | 10.0.19041.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Command Line Interface for Microsoft® Volume Shadow Copy Service |
| FileVersion: | 10.0.19041.1 (WinBuild.160101.0800) |
| InternalName: | VSSADMIN.EXE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | VSSADMIN.EXE |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 10.0.19041.1 |
Total processes
225
Monitored processes
110
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | C:\Windows\system32\cmd.exe /c "wmic path win32_VideoController get name" | C:\Windows\System32\cmd.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) | |||||||||||||||
| 464 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 740 | "C:\Users\admin\Desktop\chrome.exe" C:\Users\admin\Desktop\chrome.exe | C:\Users\admin\Desktop\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | C:\Windows\system32\cmd.exe /c "taskkill /F /PID 5092" | C:\Windows\System32\cmd.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) | |||||||||||||||
| 1148 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) | |||||||||||||||
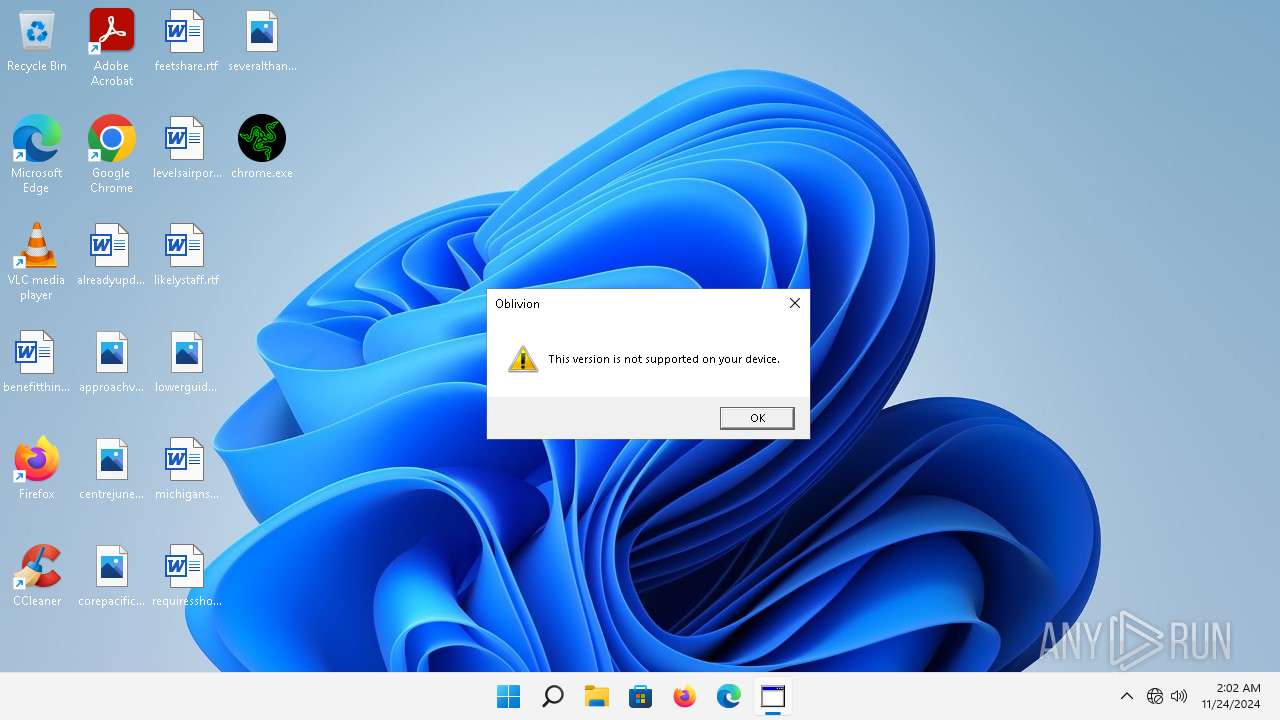
| 1316 | mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('This version is not supported on your device.', 0, 'Oblivion', 32+16);close()" | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Version: 11.00.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1384 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\n0iuruus\n0iuruus.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 | |||||||||||||||
| 1416 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) | |||||||||||||||
| 1484 | C:\Windows\system32\cmd.exe /c "WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntivirusProduct Get displayName" | C:\Windows\System32\cmd.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) | |||||||||||||||
| 1516 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) | |||||||||||||||
Total events
6 313
Read events
6 297
Write events
16
Delete events
0
Modification events
| (PID) Process: | (5452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1316) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1316) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1316) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1316) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
116
Suspicious files
16
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\_ctypes.pyd | executable | |
MD5:79879C679A12FAC03F472463BB8CEFF7 | SHA256:8D1A21192112E13913CB77708C105034C5F251D64517017975AF8E0C4999EBA3 | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\_lzma.pyd | executable | |
MD5:055EB9D91C42BB228A72BF5B7B77C0C8 | SHA256:DE342275A648207BEF9B9662C9829AF222B160975AD8925CC5612CD0F182414E | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\_queue.pyd | executable | |
MD5:513DCE65C09B3ABC516687F99A6971D8 | SHA256:D4BE41574C3E17792A25793E6F5BF171BAEEB4255C08CB6A5CD7705A91E896FC | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\_socket.pyd | executable | |
MD5:14392D71DFE6D6BDC3EBCDBDE3C4049C | SHA256:A1E39E2386634069070903E2D9C2B51A42CB0D59C20B7BE50EF95C89C268DEB2 | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\_hashlib.pyd | executable | |
MD5:D6F123C4453230743ADCC06211236BC0 | SHA256:7A904FA6618157C34E24AAAC33FDF84035215D82C08EEC6983C165A49D785DC9 | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\VCRUNTIME140.dll | executable | |
MD5:862F820C3251E4CA6FC0AC00E4092239 | SHA256:36585912E5EAF83BA9FEA0631534F690CCDC2D7BA91537166FE53E56C221E153 | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\_bz2.pyd | executable | |
MD5:58FC4C56F7F400DE210E98CCB8FDC4B2 | SHA256:DFC195EBB59DC5E365EFD3853D72897B8838497E15C0977B6EDB1EB347F13150 | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:71F1D24C7659171EAFEF4774E5623113 | SHA256:C45034620A5BB4A16E7DD0AFF235CC695A5516A4194F4FEC608B89EABD63EEEF | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\_ssl.pyd | executable | |
MD5:7EF27CD65635DFBA6076771B46C1B99F | SHA256:6EF0EF892DC9AD68874E2743AF7985590BB071E8AFE3BBF8E716F3F4B10F19B4 | |||
| 1540 | chrome.exe | C:\Users\admin\AppData\Local\Temp\_MEI15402\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:BCB8B9F6606D4094270B6D9B2ED92139 | SHA256:FA18D63A117153E2ACE5400ED89B0806E96F0627D9DB935906BE9294A3038118 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
29
DNS requests
36
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3820 | rundll32.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e25750385f8706c6 | unknown | — | — | whitelisted |
3452 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
3452 | firefox.exe | POST | 200 | 2.18.121.69:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
3452 | firefox.exe | POST | 200 | 2.18.121.71:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
3452 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | whitelisted |
— | — | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?fd5a1b7975a5d4dc | unknown | — | — | whitelisted |
— | — | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?838da79f34b29c7d | unknown | — | — | whitelisted |
— | — | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?c8be12605aaef0f9 | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 23.53.114.19:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
— | — | GET | 204 | 142.250.185.227:443 | https://gstatic.com/generate_204 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3820 | rundll32.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2432 | OfficeC2RClient.exe | 52.109.89.18:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3452 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3452 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
— | — | 2.18.121.80:80 | — | AKAMAI-AS | FR | unknown |
3820 | rundll32.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
3452 | firefox.exe | 2.18.121.69:80 | r10.o.lencr.org | AKAMAI-AS | FR | whitelisted |
3452 | firefox.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
r10.o.lencr.org |
| whitelisted |
a1887.dscq.akamai.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
— | — | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
— | — | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
— | — | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |