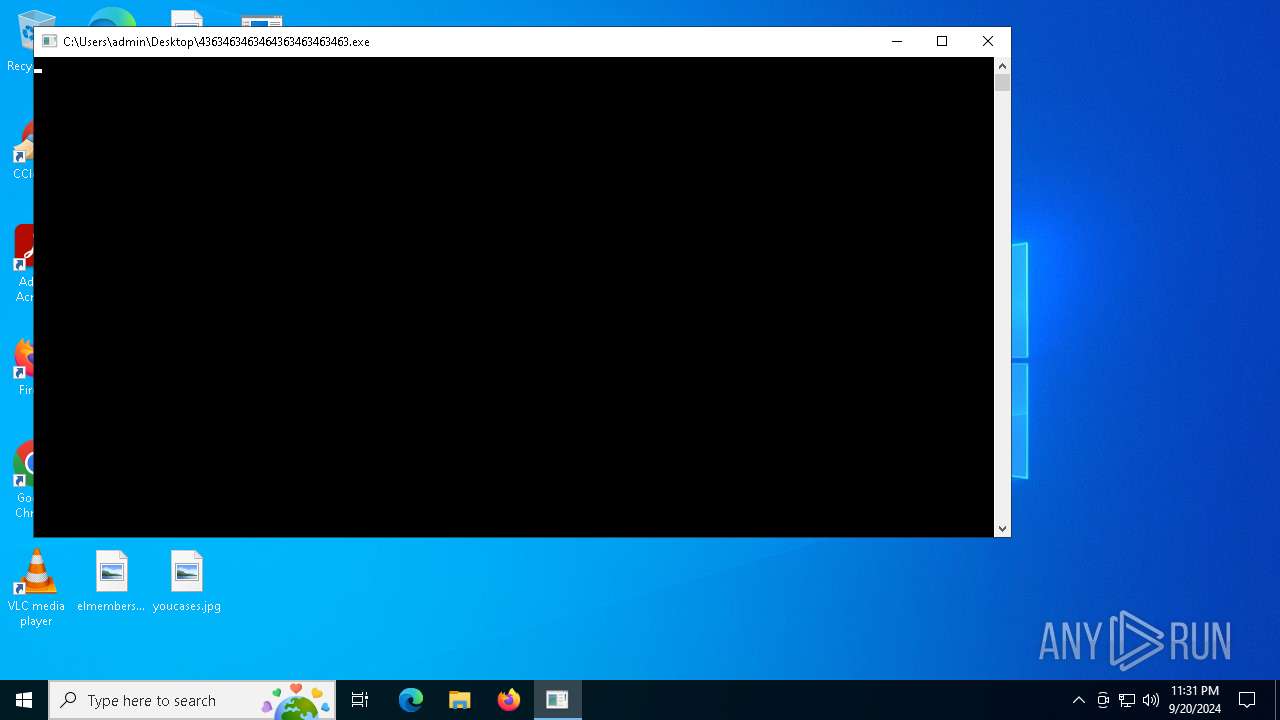
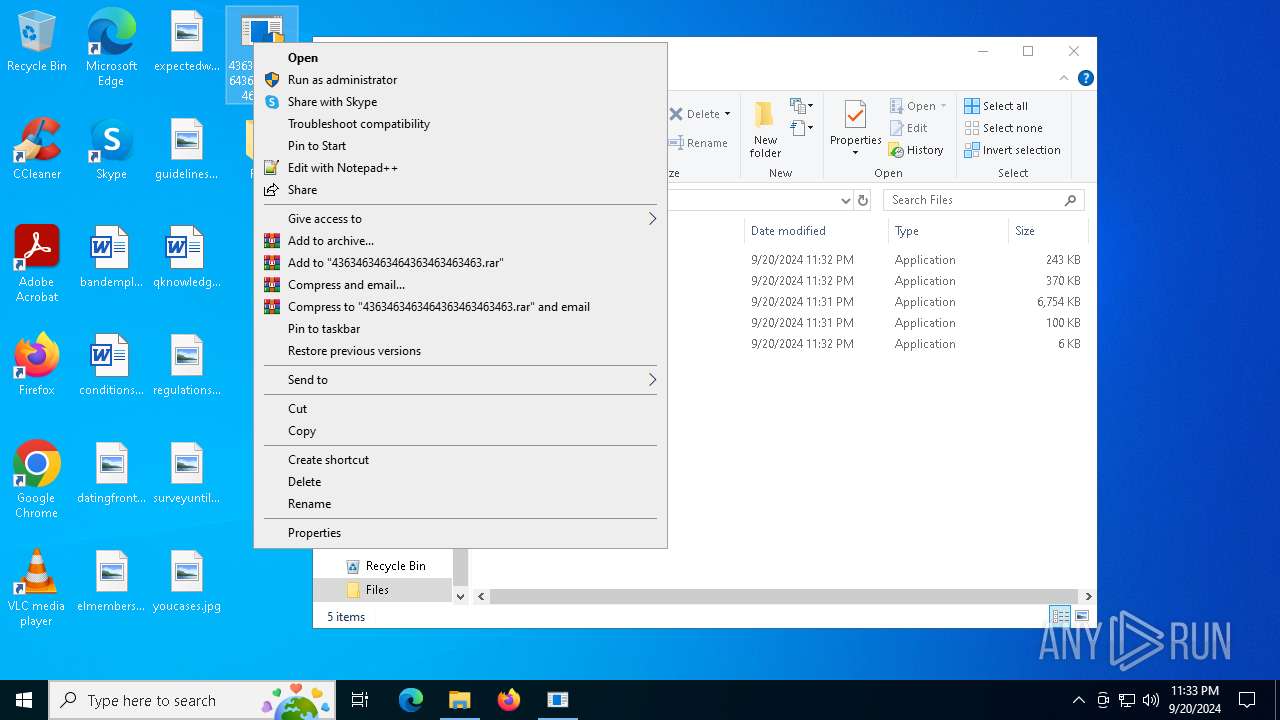
| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/f83005a7-7284-45ff-addd-fcfbf634ce50 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | September 20, 2024, 23:31:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
Changes the autorun value in the registry
- newtpp.exe (PID: 6044)
- t.exe (PID: 3924)
Changes appearance of the Explorer extensions
- syscapvbrd.exe (PID: 4072)
- sysarddrvs.exe (PID: 6800)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7052)
- syscapvbrd.exe (PID: 4072)
- sysarddrvs.exe (PID: 6800)
- cmd.exe (PID: 5472)
Changes the Windows auto-update feature
- syscapvbrd.exe (PID: 4072)
- sysarddrvs.exe (PID: 6800)
Changes Security Center notification settings
- syscapvbrd.exe (PID: 4072)
- sysarddrvs.exe (PID: 6800)
Creates or modifies Windows services
- syscapvbrd.exe (PID: 4072)
- sysarddrvs.exe (PID: 6800)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 1108)
- 4363463463464363463463463.exe (PID: 6880)
DCRAT has been detected (YARA)
- 4363463463464363463463463.exe (PID: 1108)
- 4363463463464363463463463.exe (PID: 6880)
Connects to the CnC server
- syscapvbrd.exe (PID: 4072)
- svoutse.exe (PID: 7108)
PHORPIEX has been detected (SURICATA)
- syscapvbrd.exe (PID: 4072)
- 4363463463464363463463463.exe (PID: 1108)
- svchost.exe (PID: 2256)
- 4363463463464363463463463.exe (PID: 6880)
PHORPIEX has been detected (YARA)
- syscapvbrd.exe (PID: 4072)
- sysarddrvs.exe (PID: 6800)
Changes powershell execution policy (RemoteSigned)
- svoutse.exe (PID: 7108)
AMADEY has been detected (YARA)
- svoutse.exe (PID: 7108)
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 8976)
- findstr.exe (PID: 9084)
VIDAR has been detected (YARA)
- RegAsm.exe (PID: 2536)
AMADEY has been detected (SURICATA)
- svoutse.exe (PID: 7108)
PUREHVNC has been detected (YARA)
- InstallUtil.exe (PID: 7504)
Attempt to connect to SMB server
- System (PID: 4)
SUSPICIOUS
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 1108)
- syscapvbrd.exe (PID: 4072)
- DownSysSoft.exe (PID: 2572)
- tpeinf.exe (PID: 5268)
- 4363463463464363463463463.exe (PID: 6880)
- random.exe (PID: 5180)
- svoutse.exe (PID: 7108)
- sysarddrvs.exe (PID: 6800)
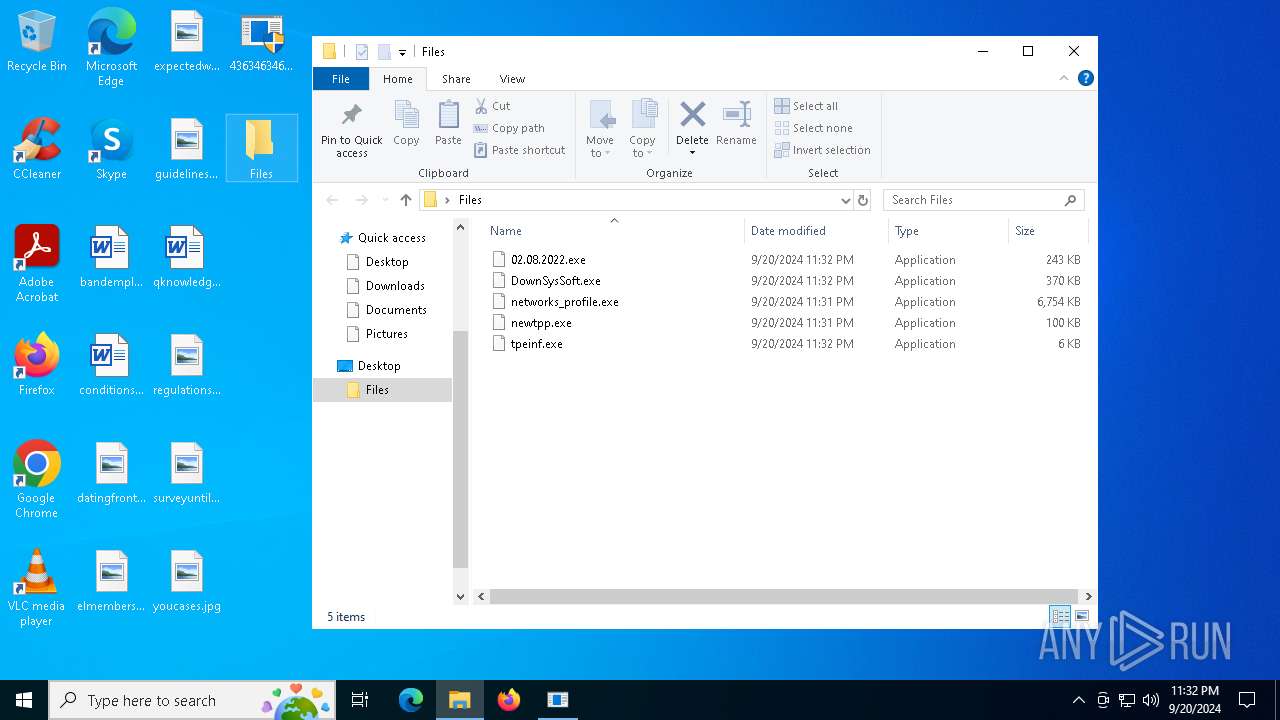
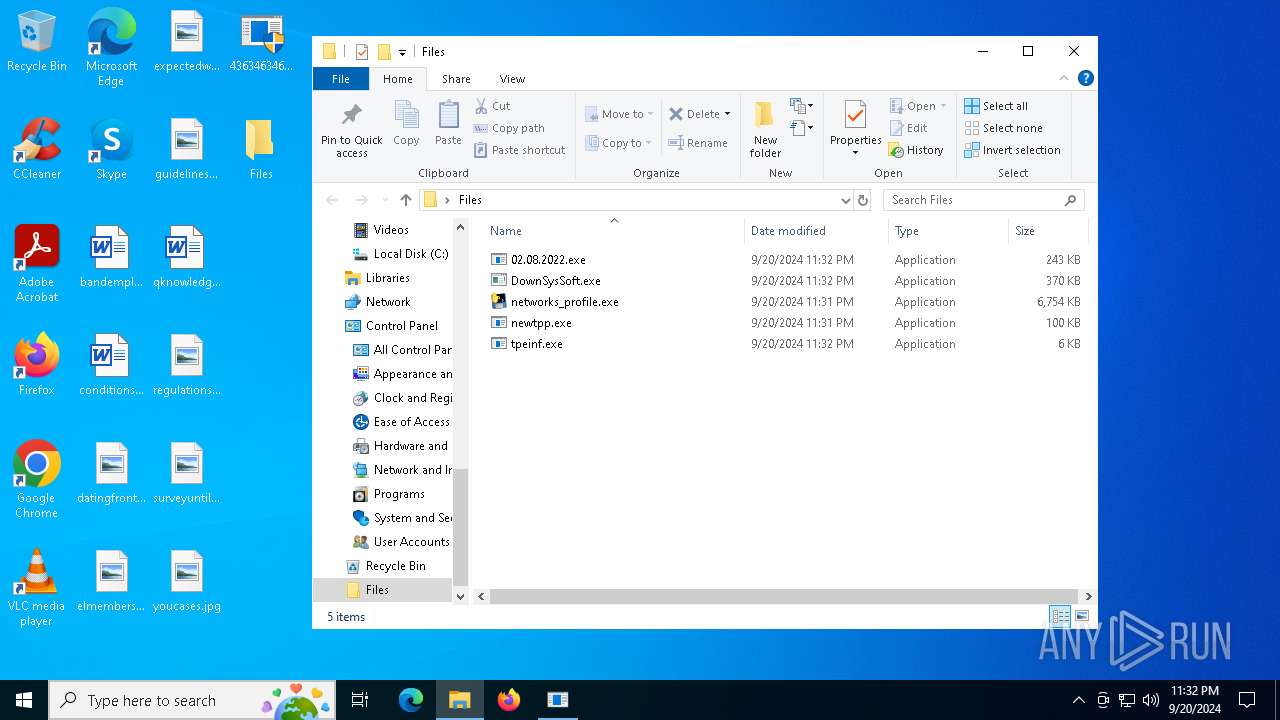
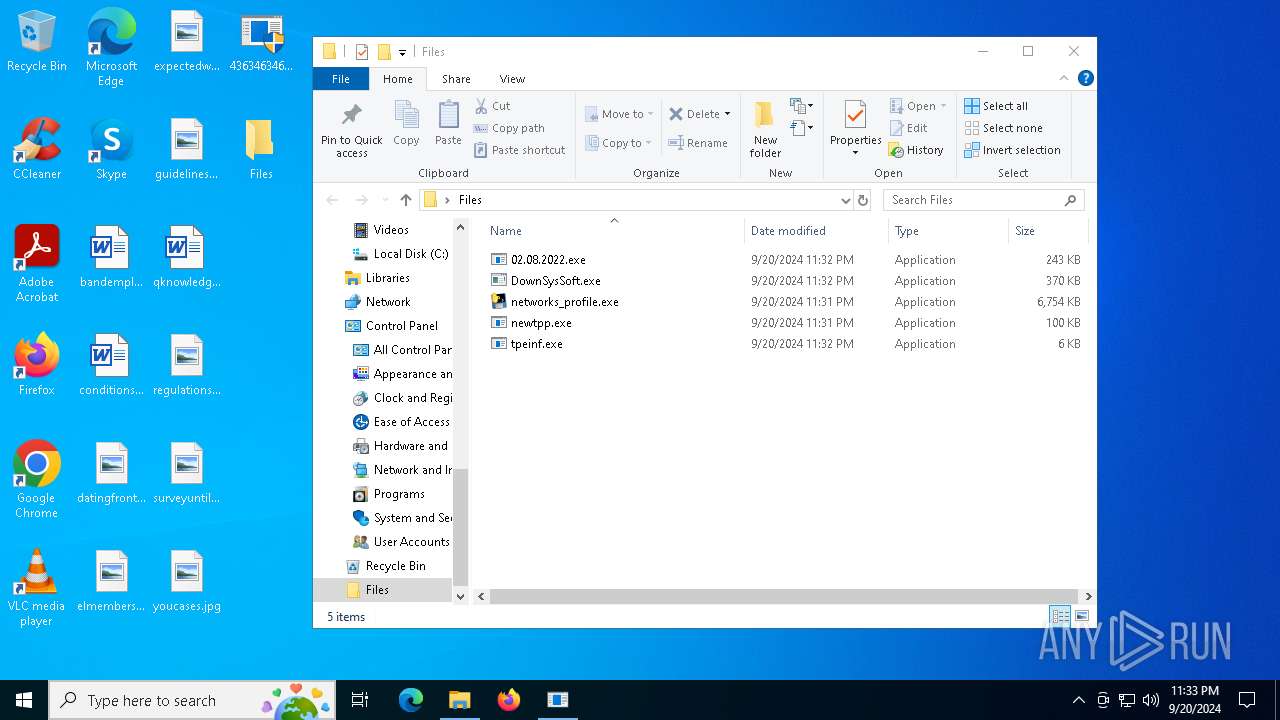
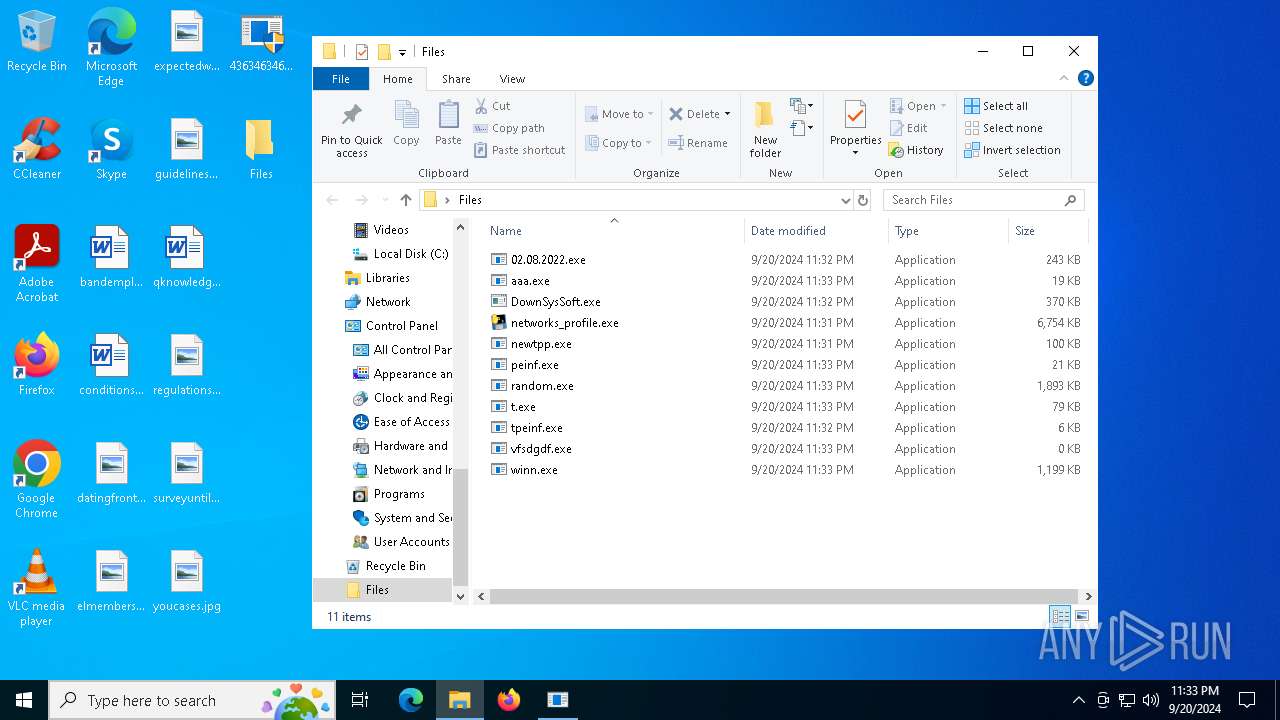
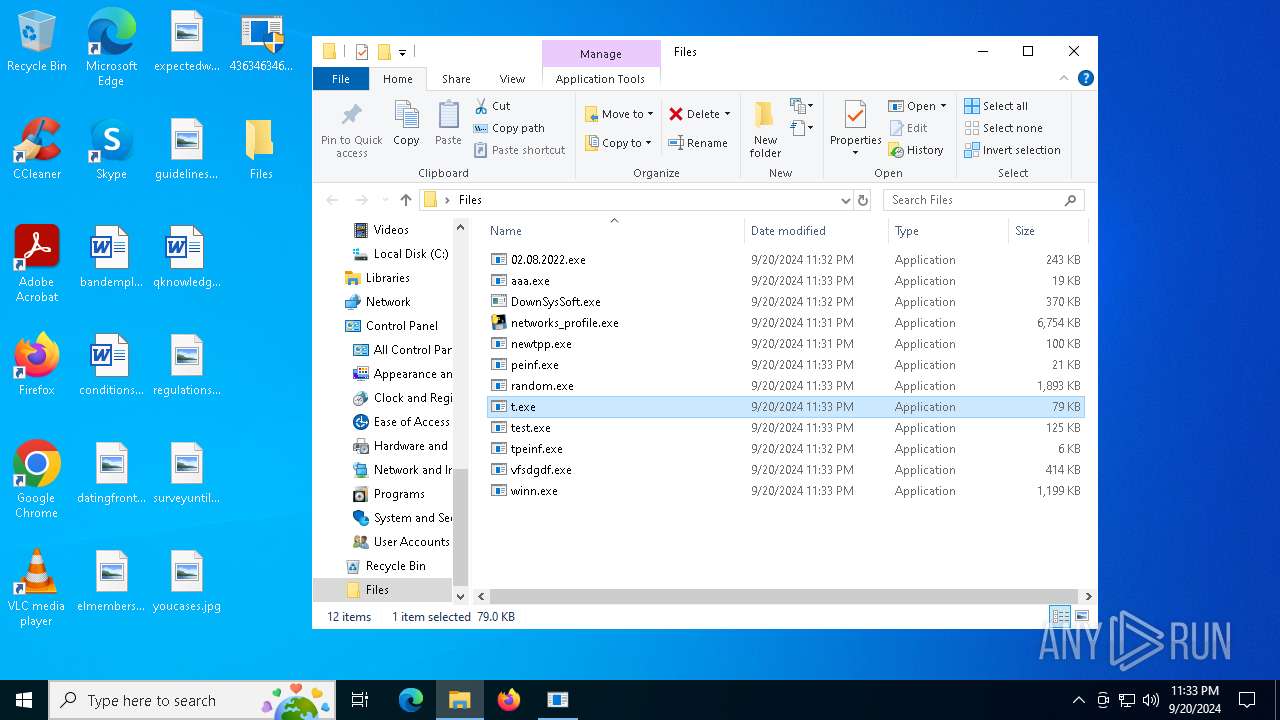
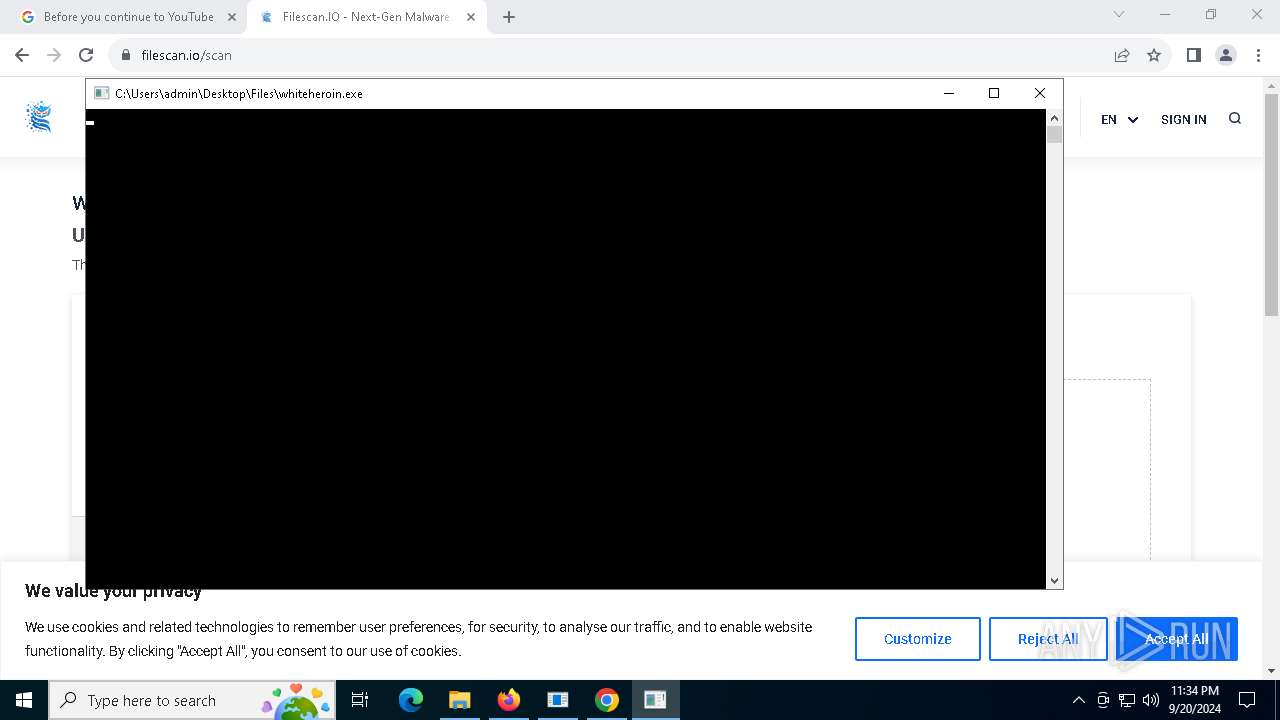
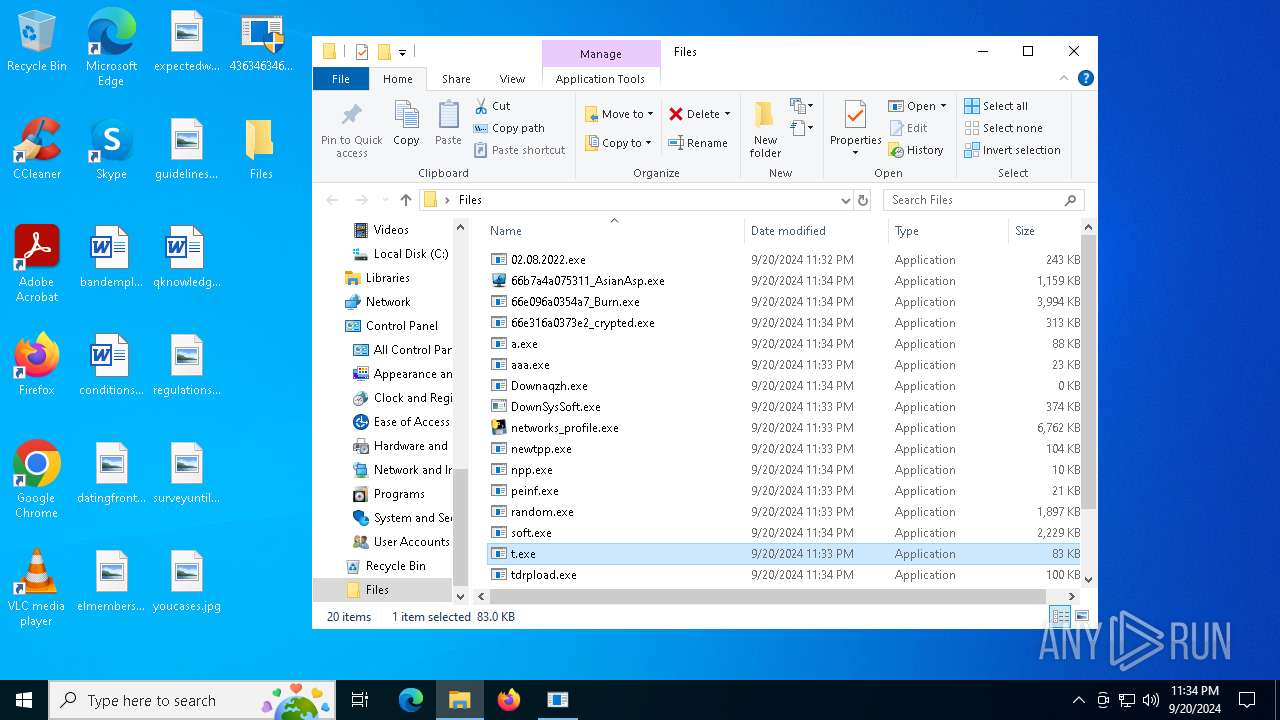
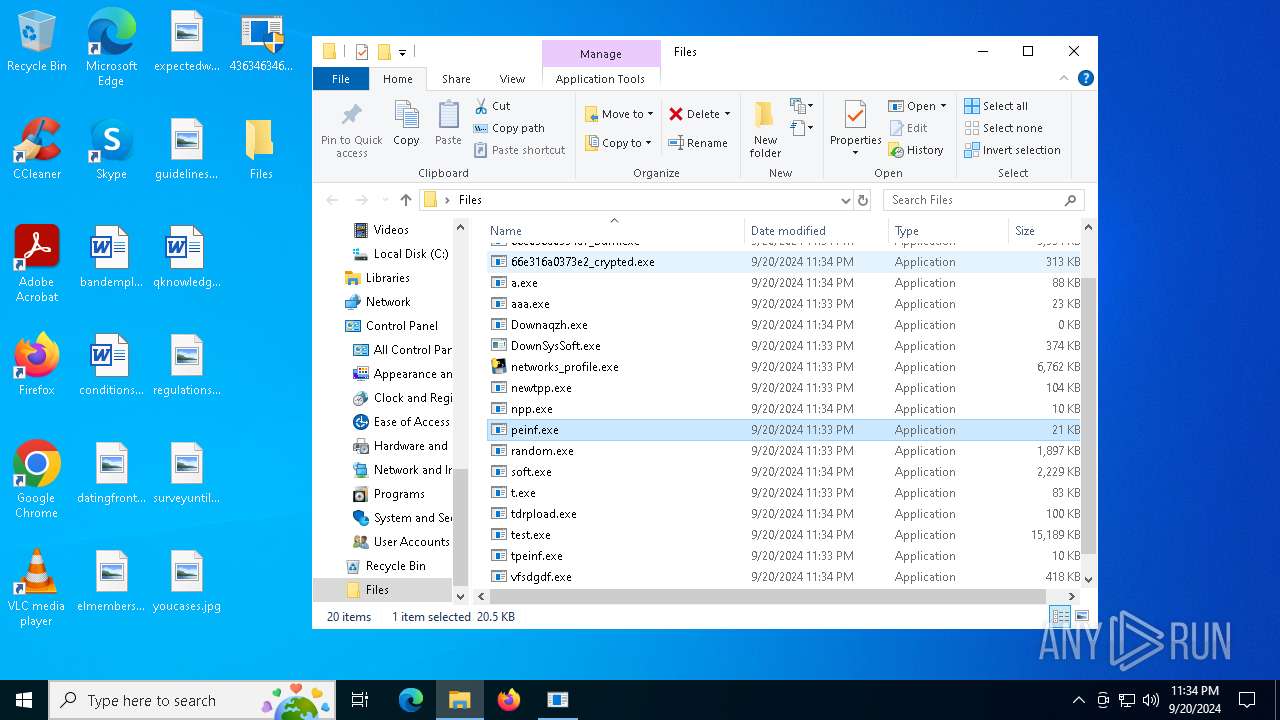
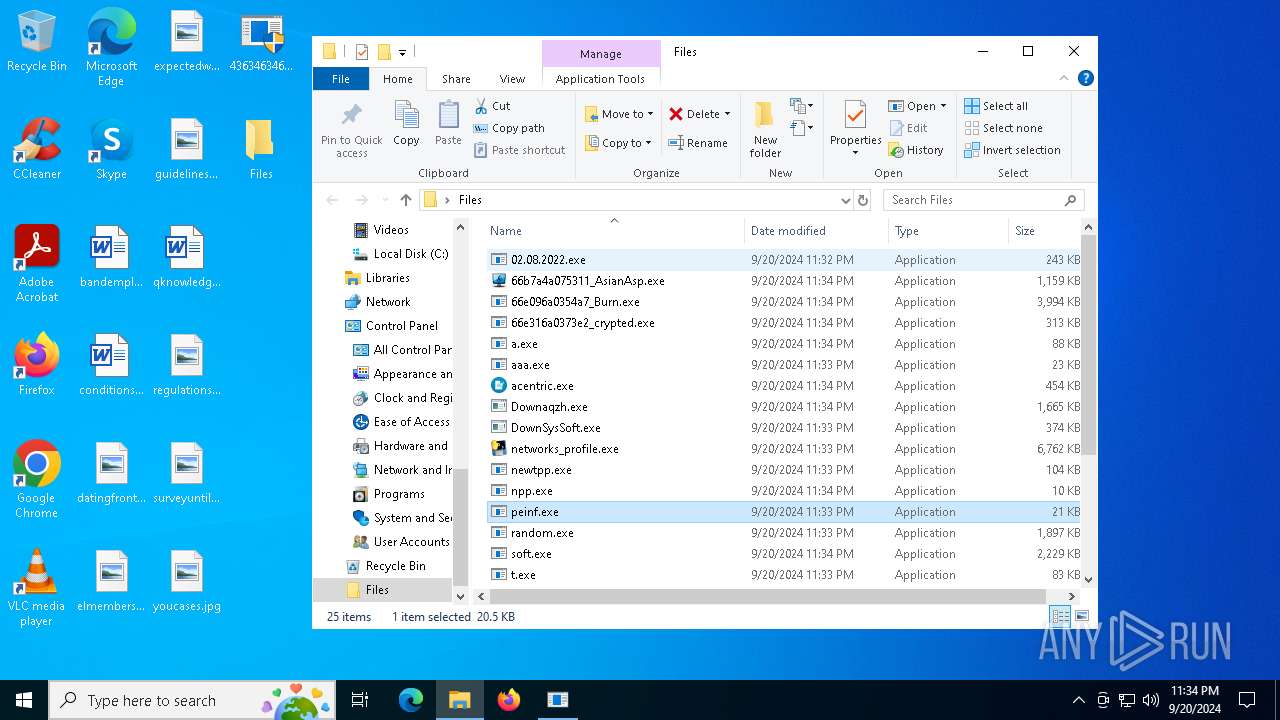
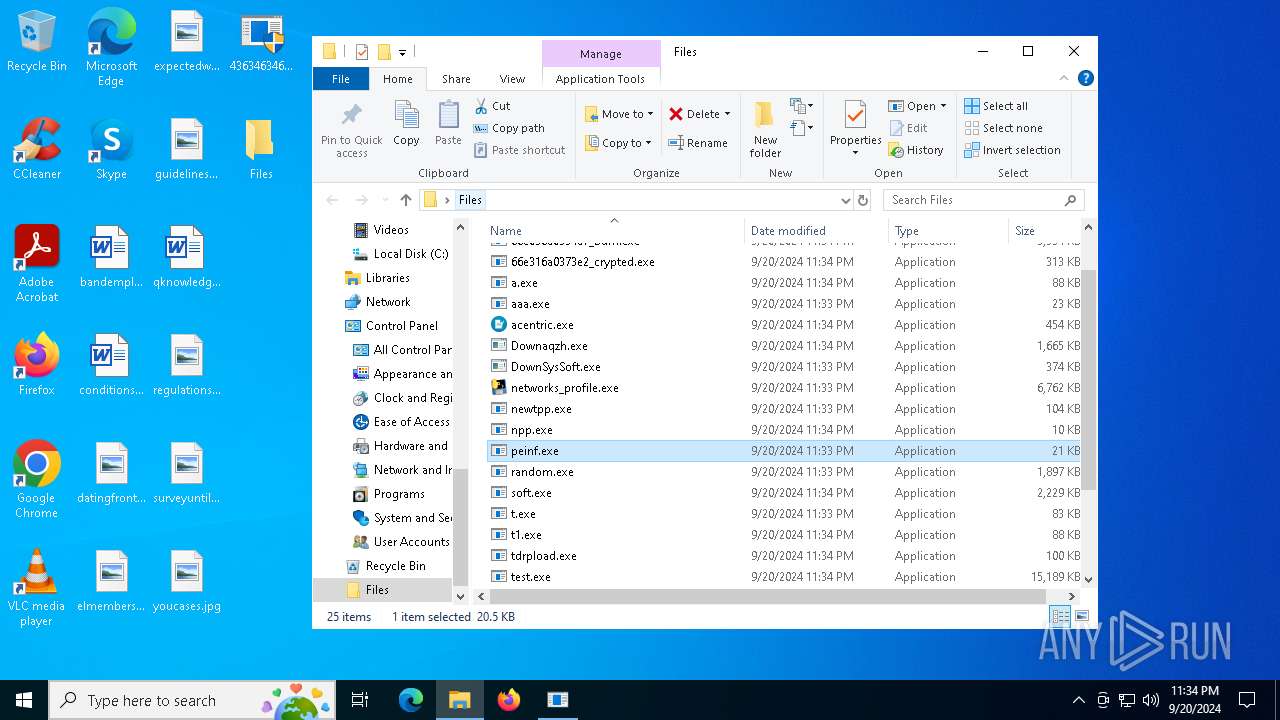
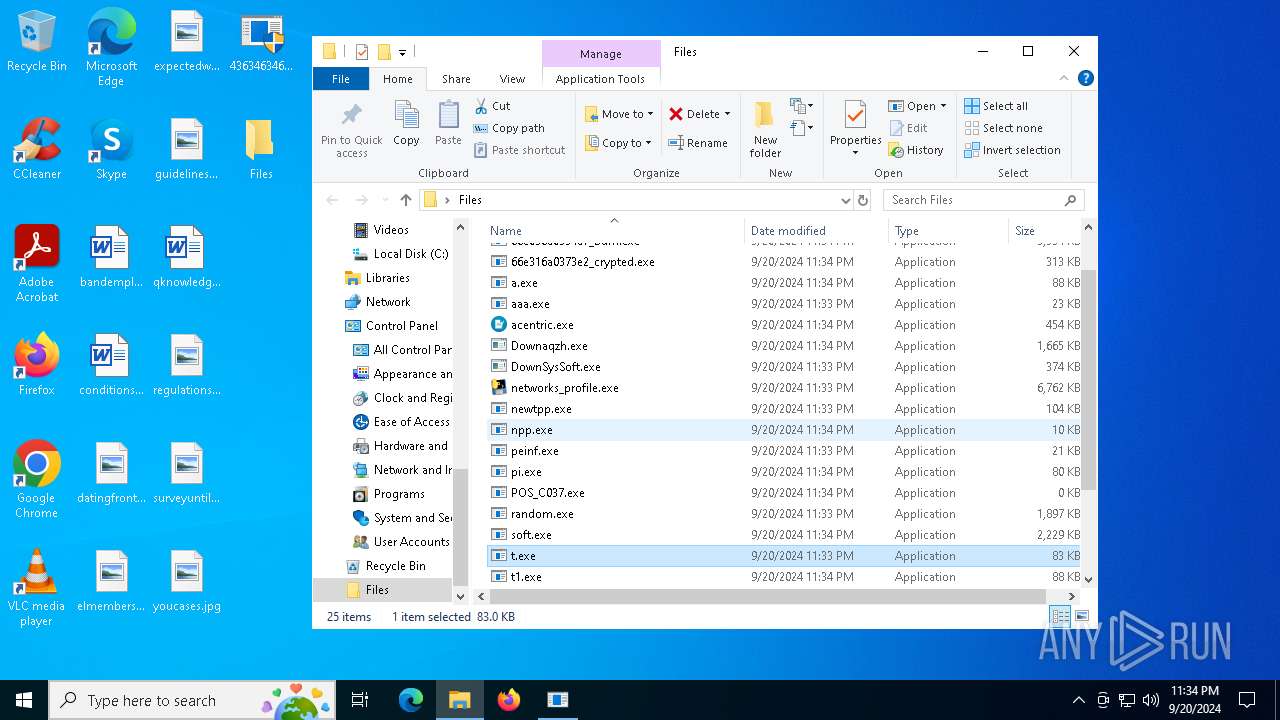
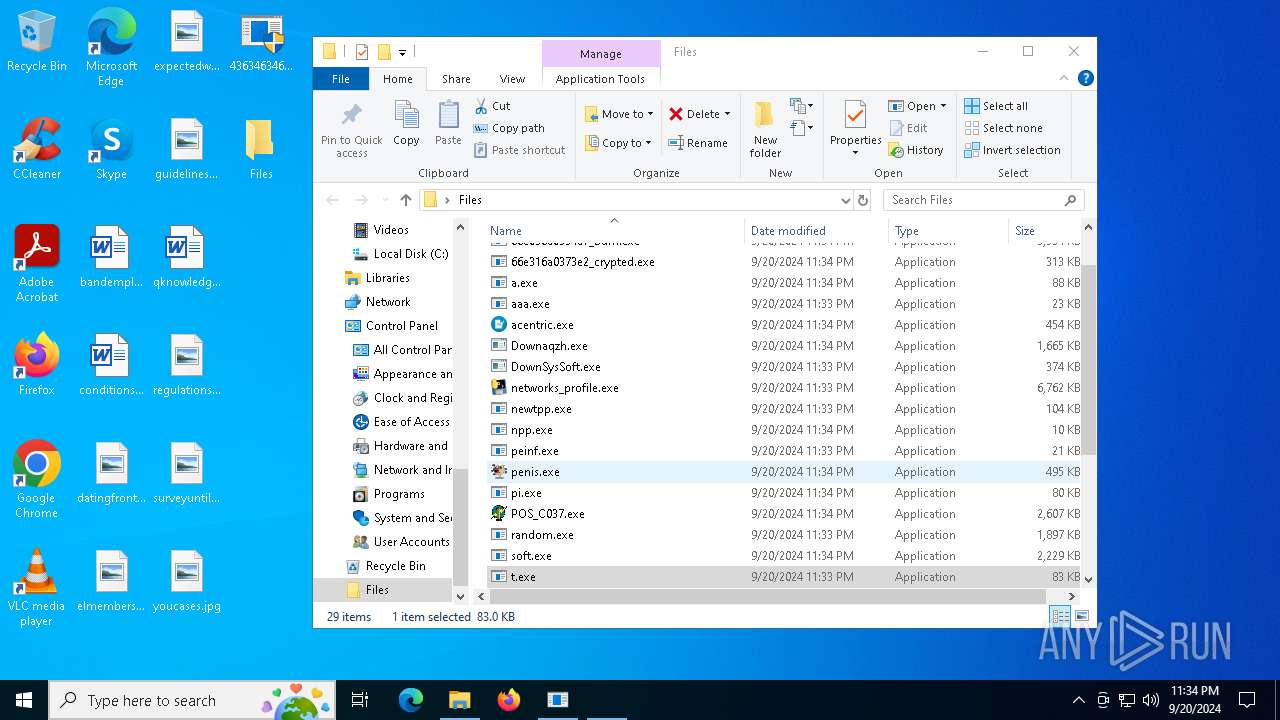
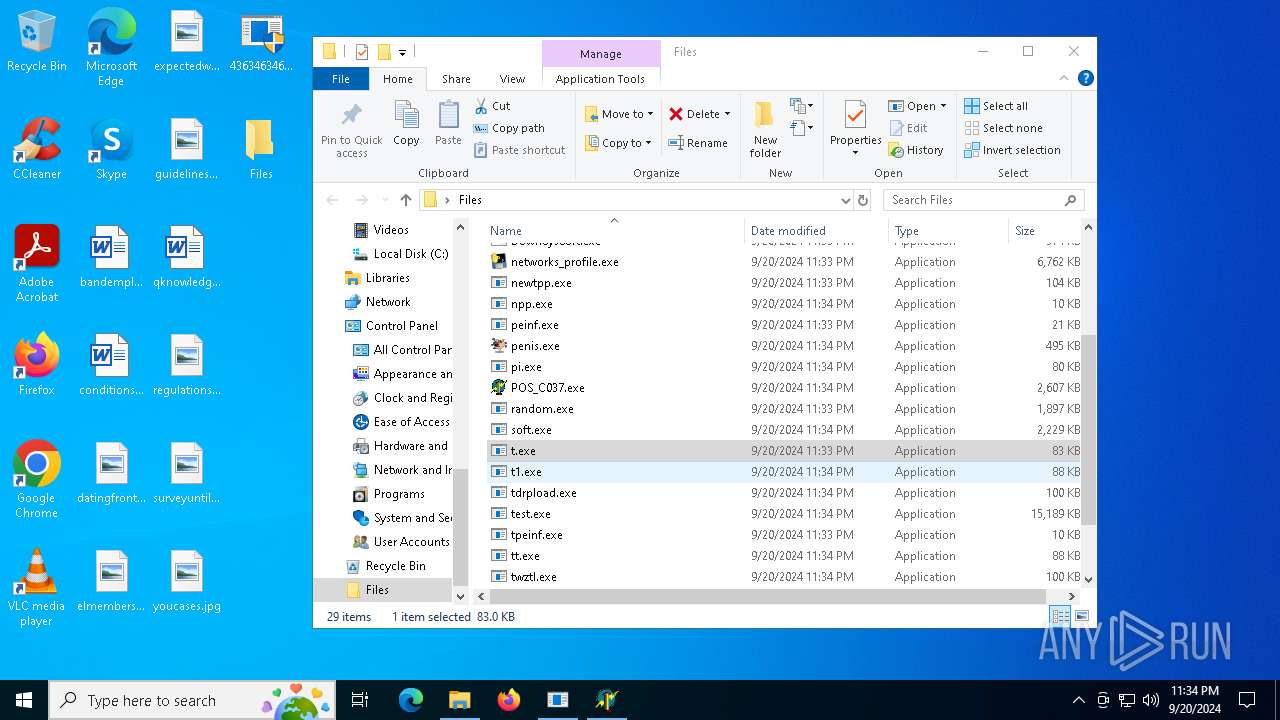
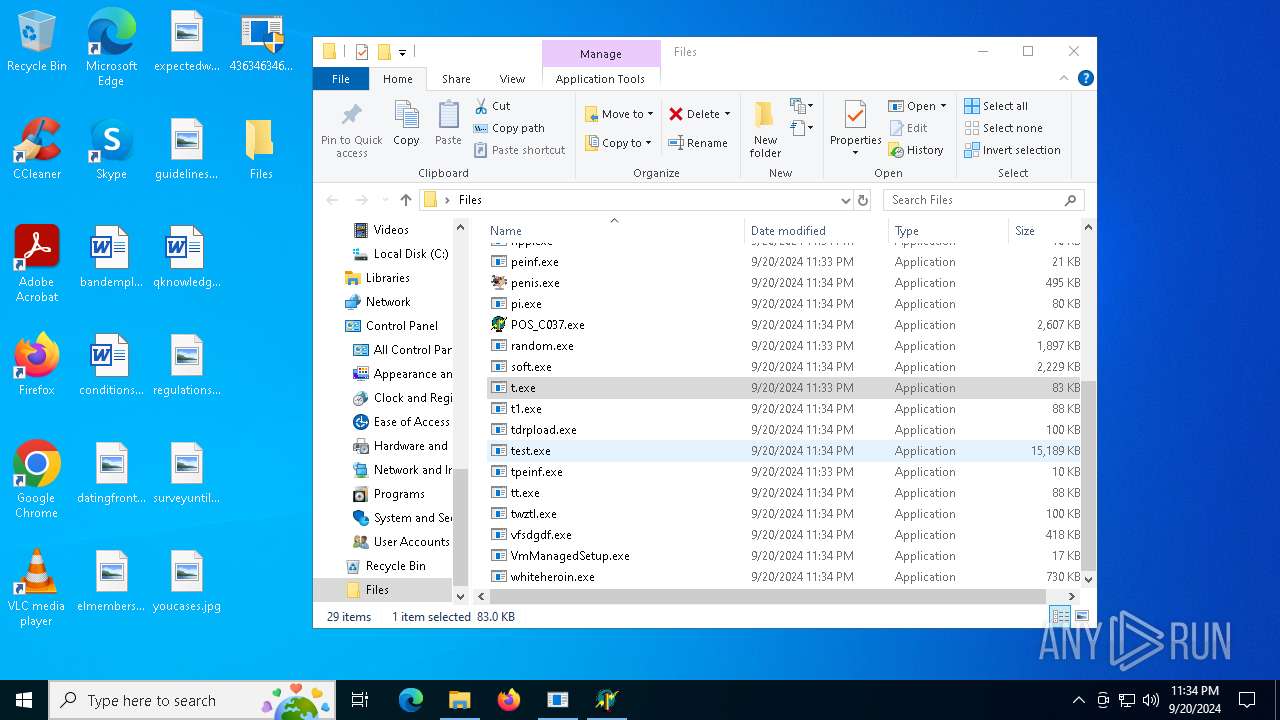
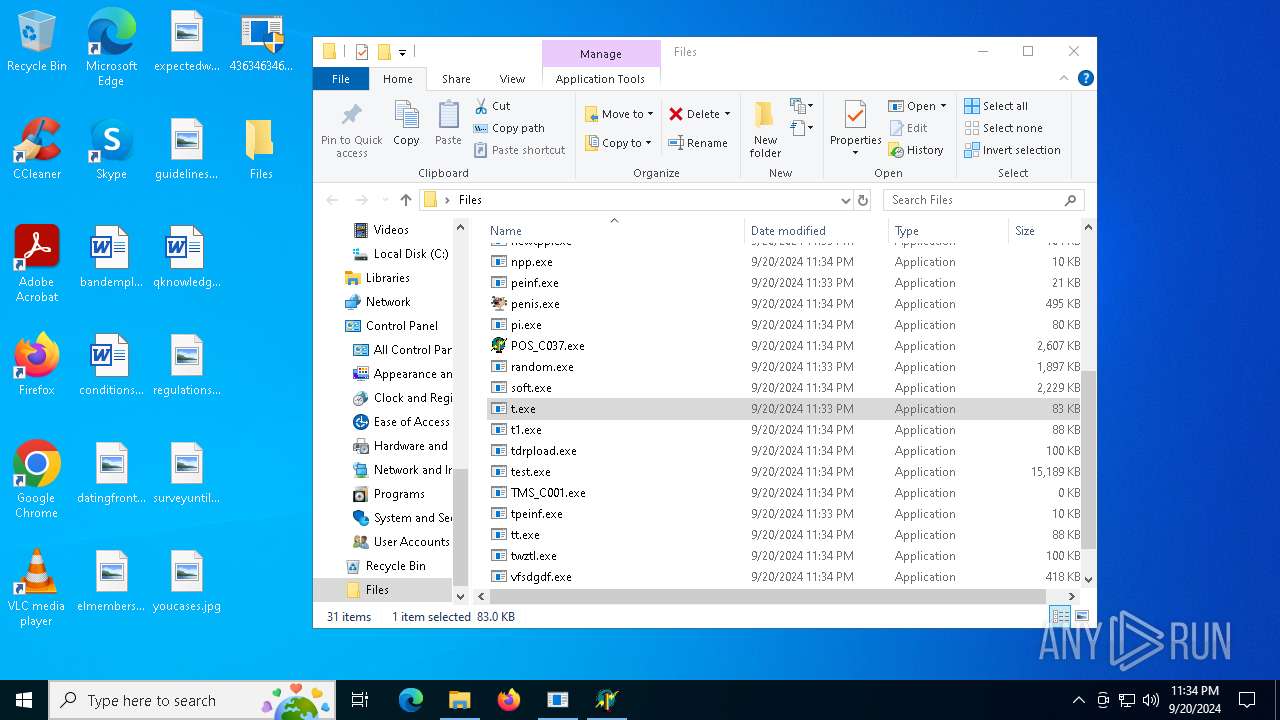
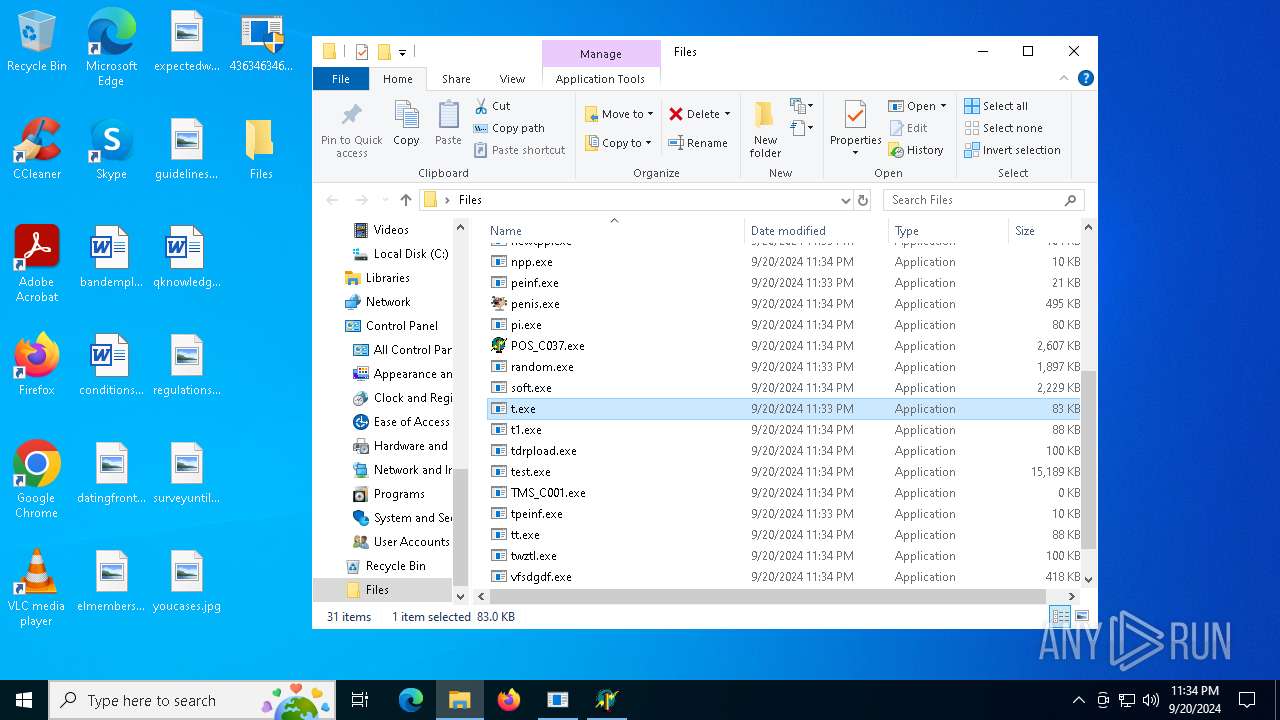
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 1108)
- newtpp.exe (PID: 6044)
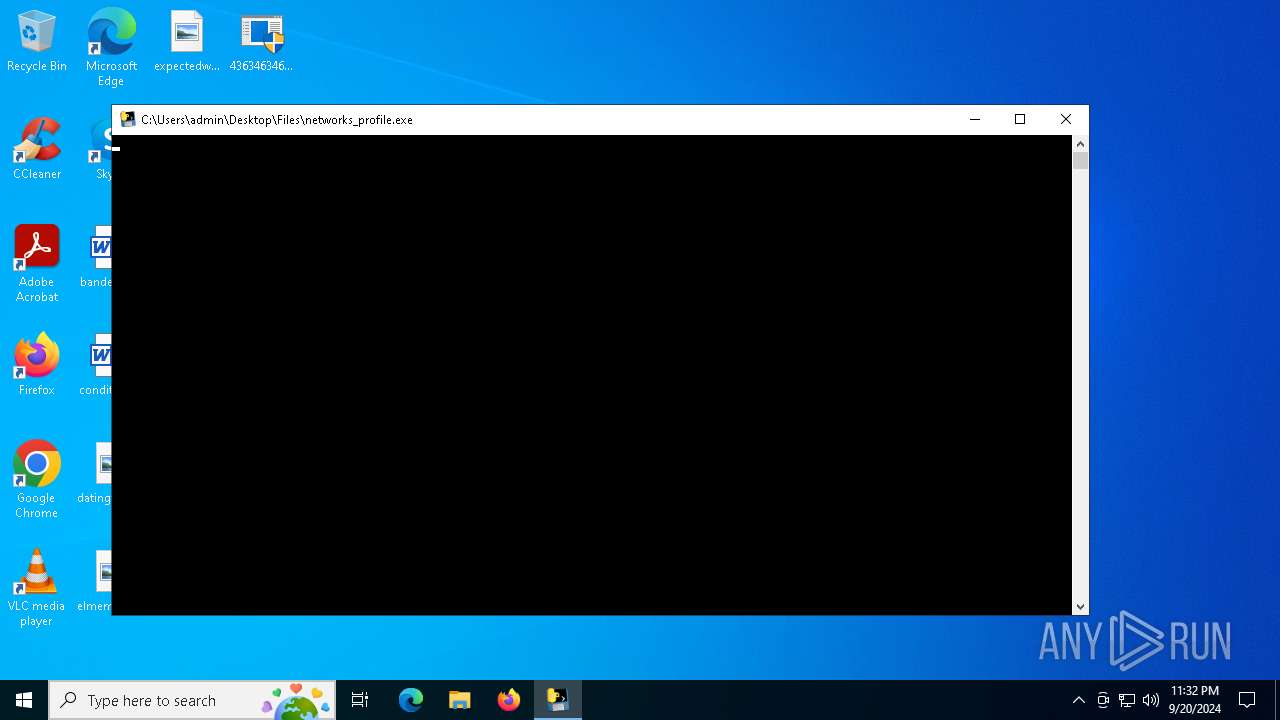
- networks_profile.exe (PID: 6512)
- tpeinf.exe (PID: 5268)
- 4363463463464363463463463.exe (PID: 6880)
- t.exe (PID: 3924)
- random.exe (PID: 5180)
- svoutse.exe (PID: 7108)
- peinf.exe (PID: 4284)
- whiteheroin.exe (PID: 8636)
- a.exe (PID: 5540)
- pi.exe (PID: 8004)
- npp.exe (PID: 8760)
- cmd.exe (PID: 7592)
- 3.exe (PID: 8592)
- 2.exe (PID: 7824)
Starts itself from another location
- newtpp.exe (PID: 6044)
- random.exe (PID: 5180)
- t.exe (PID: 3924)
- a.exe (PID: 5540)
- pi.exe (PID: 8004)
Starts CMD.EXE for commands execution
- syscapvbrd.exe (PID: 4072)
- networks_profile.exe (PID: 6868)
- sysarddrvs.exe (PID: 6800)
- 66b7a4a075311_AsianAsp.exe (PID: 7604)
- cmd.exe (PID: 7592)
Creates or modifies Windows services
- syscapvbrd.exe (PID: 4072)
- sysarddrvs.exe (PID: 6800)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7052)
- cmd.exe (PID: 5472)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7052)
- svoutse.exe (PID: 7108)
- cmd.exe (PID: 5472)
- winn.exe (PID: 6876)
Process drops legitimate windows executable
- networks_profile.exe (PID: 6512)
- peinf.exe (PID: 4284)
Loads Python modules
- networks_profile.exe (PID: 6868)
Uses NETSH.EXE to obtain data on the network
- networks_profile.exe (PID: 6868)
The process drops C-runtime libraries
- networks_profile.exe (PID: 6512)
Process drops python dynamic module
- networks_profile.exe (PID: 6512)
Application launched itself
- networks_profile.exe (PID: 6512)
- cmd.exe (PID: 7592)
- soft.exe (PID: 6744)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 1108)
- DownSysSoft.exe (PID: 2572)
- tpeinf.exe (PID: 5268)
- 4363463463464363463463463.exe (PID: 6880)
- svoutse.exe (PID: 7108)
- System (PID: 4)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 1108)
- DownSysSoft.exe (PID: 2572)
- syscapvbrd.exe (PID: 4072)
- aaa.exe (PID: 2892)
Reads the BIOS version
- random.exe (PID: 5180)
- svoutse.exe (PID: 7108)
The process checks if it is being run in the virtual environment
- 4363463463464363463463463.exe (PID: 6880)
The process executes Powershell scripts
- svoutse.exe (PID: 7108)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 7480)
The process executes via Task Scheduler
- svoutse.exe (PID: 8344)
The executable file from the user directory is run by the CMD process
- Executives.pif (PID: 8344)
Executing commands from ".cmd" file
- 66b7a4a075311_AsianAsp.exe (PID: 7604)
Get information on the list of running processes
- cmd.exe (PID: 7592)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7592)
Starts application with an unusual extension
- cmd.exe (PID: 7592)
Contacting a server suspected of hosting an CnC
- svoutse.exe (PID: 7108)
INFO
Checks supported languages
- 4363463463464363463463463.exe (PID: 1108)
- newtpp.exe (PID: 6044)
- syscapvbrd.exe (PID: 4072)
- networks_profile.exe (PID: 6512)
- tpeinf.exe (PID: 5268)
- networks_profile.exe (PID: 6868)
- DownSysSoft.exe (PID: 2572)
- 2999915100.exe (PID: 3164)
- 4363463463464363463463463.exe (PID: 6880)
- winn.exe (PID: 6876)
- random.exe (PID: 5180)
- t.exe (PID: 3924)
- peinf.exe (PID: 4284)
- aaa.exe (PID: 2892)
- vfsdgdf.exe (PID: 1128)
- svoutse.exe (PID: 7108)
- sysarddrvs.exe (PID: 6800)
- RegAsm.exe (PID: 2536)
Disables trace logs
- 4363463463464363463463463.exe (PID: 1108)
- 4363463463464363463463463.exe (PID: 6880)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 1108)
- networks_profile.exe (PID: 6868)
- syscapvbrd.exe (PID: 4072)
- 4363463463464363463463463.exe (PID: 6880)
- winn.exe (PID: 6876)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 1108)
- 4363463463464363463463463.exe (PID: 6880)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 1108)
- DownSysSoft.exe (PID: 2572)
- syscapvbrd.exe (PID: 4072)
- tpeinf.exe (PID: 5268)
- 4363463463464363463463463.exe (PID: 6880)
- svoutse.exe (PID: 7108)
Reads the computer name
- 4363463463464363463463463.exe (PID: 1108)
- syscapvbrd.exe (PID: 4072)
- networks_profile.exe (PID: 6512)
- DownSysSoft.exe (PID: 2572)
- tpeinf.exe (PID: 5268)
- 4363463463464363463463463.exe (PID: 6880)
- random.exe (PID: 5180)
- winn.exe (PID: 6876)
- svoutse.exe (PID: 7108)
- vfsdgdf.exe (PID: 1128)
- RegAsm.exe (PID: 2536)
- sysarddrvs.exe (PID: 6800)
- aaa.exe (PID: 2892)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 1108)
- syscapvbrd.exe (PID: 4072)
- 4363463463464363463463463.exe (PID: 6880)
- random.exe (PID: 5180)
- sysarddrvs.exe (PID: 6800)
Sends debugging messages
- 4363463463464363463463463.exe (PID: 1108)
- random.exe (PID: 5180)
- svoutse.exe (PID: 7108)
The process uses the downloaded file
- newtpp.exe (PID: 6044)
- 4363463463464363463463463.exe (PID: 1108)
- syscapvbrd.exe (PID: 4072)
- tpeinf.exe (PID: 5268)
- powershell.exe (PID: 1612)
- 4363463463464363463463463.exe (PID: 6880)
- random.exe (PID: 5180)
- t.exe (PID: 3924)
- sysarddrvs.exe (PID: 6800)
Create files in a temporary directory
- networks_profile.exe (PID: 6512)
- tpeinf.exe (PID: 5268)
- syscapvbrd.exe (PID: 4072)
- DownSysSoft.exe (PID: 2572)
- random.exe (PID: 5180)
- svoutse.exe (PID: 7108)
- RegAsm.exe (PID: 2536)
Reads mouse settings
- DownSysSoft.exe (PID: 2572)
Checks operating system version
- networks_profile.exe (PID: 6868)
Creates files or folders in the user directory
- tpeinf.exe (PID: 5268)
- syscapvbrd.exe (PID: 4072)
- DownSysSoft.exe (PID: 2572)
- svoutse.exe (PID: 7108)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1612)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1612)
Connecting to InterPlanetary File System domains
- 4363463463464363463463463.exe (PID: 1108)
- svchost.exe (PID: 2256)
Manual execution by a user
- 4363463463464363463463463.exe (PID: 6880)
- firefox.exe (PID: 7060)
- firefox.exe (PID: 2272)
- InstallUtil.exe (PID: 6864)
- InstallUtil.exe (PID: 7280)
- InstallUtil.exe (PID: 7444)
- InstallUtil.exe (PID: 7456)
- InstallUtil.exe (PID: 7504)
- InstallUtil.exe (PID: 7172)
- InstallUtil.exe (PID: 7508)
- InstallUtil.exe (PID: 7436)
Application launched itself
- chrome.exe (PID: 2524)
- firefox.exe (PID: 7060)
- chrome.exe (PID: 3896)
- firefox.exe (PID: 2272)
- firefox.exe (PID: 3448)
Themida protector has been detected
- svoutse.exe (PID: 7108)
.NET Reactor protector has been detected
- InstallUtil.exe (PID: 7504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(7108) svoutse.exe
C231.41.244.10
URLhttp://31.41.244.10/Dem7kTu/index.php
Version4.41
Options
Drop directory0e8d0864aa
Drop namesvoutse.exe
Strings (119)VideoID
st=s
id:
"
Content-Type: application/octet-stream
2022
0e8d0864aa
exe
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
-unicode-
svoutse.exe
<d>
Doctor Web
AVG
4.41
dll
Main
Norton
" && ren
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
&unit=
/Plugins/
rb
cred.dll
#
ProgramData\
rundll32.exe
cmd
--
vs:
DefaultSettings.XResolution
random
?scr=1
GetNativeSystemInfo
%-lu
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
og:
Powershell.exe
" && timeout 1 && del
/quiet
r=
AVAST Software
360TotalSecurity
dm:
Comodo
Sophos
GET
=
wb
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
/Dem7kTu/index.php
lv:
Rem
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
Bitdefender
DefaultSettings.YResolution
un:
https://
SYSTEM\ControlSet001\Services\BasicDisplay\Video
shutdown -s -t 0
ProductName
sd:
"taskkill /f /im "
&& Exit"
Panda Security
http://
POST
Content-Type: application/x-www-form-urlencoded
ComputerName
------
0123456789
CurrentBuild
rundll32
cred.dll|clip.dll|
.jpg
clip.dll
kernel32.dll
:::
S-%lu-
WinDefender
ar:
Kaspersky Lab
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
\App
SOFTWARE\Microsoft\Windows NT\CurrentVersion
\0000
e2
"
|
-%lu
os:
-executionpolicy remotesigned -File "
ESET
------
pc:
+++
Content-Type: multipart/form-data; boundary=----
av:
\
cmd /C RMDIR /s/q
ps1
Programs
%USERPROFILE%
e0
&&
zip
<c>
e1
bi:
msi
Startup
Avira
d1
shell32.dll
31.41.244.10
abcdefghijklmnopqrstuvwxyz0123456789-_
2016
2019
/k
Vidar
(PID) Process(2536) RegAsm.exe
C2https://t.me/ae5ed
URLhttps://steamcommunity.com/profiles/76561199780418869
RC40123456789ABCDEF
TRiD
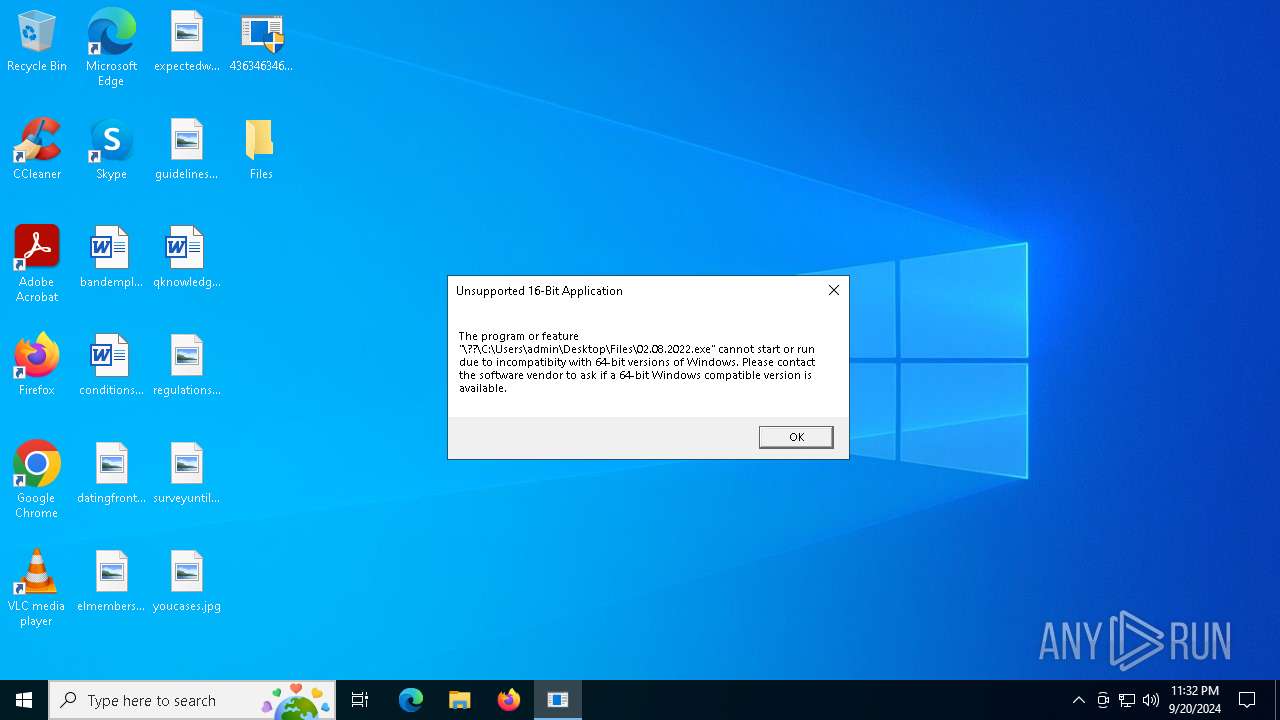
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
286
Monitored processes
158
Malicious processes
15
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 448 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://www.youtube.com/account | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 | |||||||||||||||
| 740 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | networks_profile.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2276 -parentBuildID 20240213221259 -prefsHandle 2268 -prefMapHandle 2248 -prefsLen 30537 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c89dd580-d07a-4081-94b5-0b2be03d5b44} 3448 "\\.\pipe\gecko-crash-server-pipe.3448" 24bf0284f10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 4294967295 Version: 123.0 | |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x210,0x214,0x218,0x1ec,0x21c,0x7fffd56fdc40,0x7fffd56fdc4c,0x7fffd56fdc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 4294967295 Version: 122.0.6261.70 | |||||||||||||||
| 1108 | "C:\Users\admin\Desktop\4363463463464363463463463.exe" | C:\Users\admin\Desktop\4363463463464363463463463.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | "C:\Users\admin\Desktop\Files\vfsdgdf.exe" | C:\Users\admin\Desktop\Files\vfsdgdf.exe | — | 4363463463464363463463463.exe | |||||||||||
User: admin Company: listening triskelion Integrity Level: HIGH Description: outfawned Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1612 | powershell -Command "Add-MpPreference -ExclusionPath $env:windir; Add-MpPreference -ExclusionPath $env:TEMP; Add-MpPreference -ExclusionPath $env:USERPROFILE" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 374
Read events
14 316
Write events
58
Delete events
0
Modification events
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
62
Suspicious files
319
Text files
189
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1108 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\newtpp.exe | executable | |
MD5:CE554FE53B2620C56F6ABB264A588616 | SHA256:93237A51BB710BD488B0E5BFA8288751445EAFCC795364DF7652535F3C210431 | |||
| 6512 | networks_profile.exe | C:\Users\admin\AppData\Local\Temp\_MEI65122\_ctypes.pyd | executable | |
MD5:7322F8245B5C8551D67C337C0DC247C9 | SHA256:4FCF4C9C98B75A07A7779C52E1F7DFF715AE8A2F8A34574E9DAC66243FB86763 | |||
| 1108 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\networks_profile.exe | executable | |
MD5:7306ABCF62C8EE10A1692A6A85AF9297 | SHA256:37C9A26FAEC0BB21171B3968D2E4254F6AE10FF7AE0D0B1493226685BC5D3B4B | |||
| 6512 | networks_profile.exe | C:\Users\admin\AppData\Local\Temp\_MEI65122\libcrypto-1_1.dll | executable | |
MD5:89511DF61678BEFA2F62F5025C8C8448 | SHA256:296426E7CE11BC3D1CFA9F2AEB42F60C974DA4AF3B3EFBEB0BA40E92E5299FDF | |||
| 6512 | networks_profile.exe | C:\Users\admin\AppData\Local\Temp\_MEI65122\_ssl.pyd | executable | |
MD5:CF7886B3AC590D2EA1A6EFE4EE47DC20 | SHA256:3D183C1B3A24D634387CCE3835F58B8E1322BF96AB03F9FE9F02658FB17D1F8C | |||
| 6044 | newtpp.exe | C:\Windows\syscapvbrd.exe | executable | |
MD5:CE554FE53B2620C56F6ABB264A588616 | SHA256:93237A51BB710BD488B0E5BFA8288751445EAFCC795364DF7652535F3C210431 | |||
| 6512 | networks_profile.exe | C:\Users\admin\AppData\Local\Temp\_MEI65122\_asyncio.pyd | executable | |
MD5:C89B5EC34A76D00543D55748A7275CB1 | SHA256:3E521E119CFAD53C8FCF67BBF26DE2ECFFE24CB13079F36A22339F0F8AD297A6 | |||
| 6512 | networks_profile.exe | C:\Users\admin\AppData\Local\Temp\_MEI65122\libssl-1_1.dll | executable | |
MD5:50BCFB04328FEC1A22C31C0E39286470 | SHA256:FDDD0DA02DCD41786E9AA04BA17BA391CE39DAE6B1F54CFA1E2BB55BC753FCE9 | |||
| 6512 | networks_profile.exe | C:\Users\admin\AppData\Local\Temp\_MEI65122\_lzma.pyd | executable | |
MD5:CDD13B537DAD6A910CB9CBB932770DC9 | SHA256:638CD8C336F90629A6260E67827833143939497D542838846F4FC94B2475BB3E | |||
| 6512 | networks_profile.exe | C:\Users\admin\AppData\Local\Temp\_MEI65122\_bz2.pyd | executable | |
MD5:A991152FD5B8F2A0EB6C34582ADF7111 | SHA256:7301FC2447E7E6D599472D2C52116FBE318A9FF9259B8A85981C419BFD20E3EF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
92
TCP/UDP connections
246
DNS requests
201
Threats
762
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1108 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://loeghaiofiehfihf.to/newtpp.exe | unknown | — | — | suspicious |
3812 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1108 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://app.aefiabeuodbauobfafoebbf.net/tpeinf.exe | unknown | — | — | suspicious |
1108 | 4363463463464363463463463.exe | GET | 200 | 36.249.46.172:8765 | http://36.249.46.172:8765/DownSysSoft.exe | unknown | — | — | unknown |
2572 | DownSysSoft.exe | GET | 200 | 58.23.215.23:8765 | http://wieie.cn:8765/Down/List | unknown | — | — | malicious |
4072 | syscapvbrd.exe | GET | — | 185.215.113.66:80 | http://185.215.113.66/1 | unknown | — | — | unknown |
5268 | tpeinf.exe | GET | 200 | 185.215.113.66:80 | http://twizt.net/peinstall.php | unknown | — | — | malicious |
6880 | 4363463463464363463463463.exe | GET | 200 | 31.41.244.9:80 | http://31.41.244.9/mine/random.exe | unknown | — | — | suspicious |
4072 | syscapvbrd.exe | GET | 200 | 185.215.113.66:80 | http://185.215.113.66/1 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
608 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2272 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3812 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3812 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4324 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
loeghaiofiehfihf.to |
| unknown |
bafybeicnmx2fcaolinpdaiqjo7hgsourg3qzaxf57psdrbqic4qrm4pf3i.ipfs.dweb.link |
| malicious |
raw.githubusercontent.com |
| shared |
app.aefiabeuodbauobfafoebbf.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1108 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1108 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1108 | 4363463463464363463463463.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 32 |
2256 | svchost.exe | Misc activity | ET HUNTING IPFS Gateway Domain in DNS Lookup (ipfs .dweb .link) |
1108 | 4363463463464363463463463.exe | Misc activity | ET HUNTING Observed IPFS Gateway Domain (ipfs .dweb .link) in TLS SNI |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] IPFS/IPNS Gateway (dweb .link) |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1108 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
1108 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
27 ETPRO signatures available at the full report
Process | Message |
|---|---|
4363463463464363463463463.exe | The remote server returned an error: (410) Gone.
|
random.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
svoutse.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|