| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/e94f0166-ebdb-460b-8049-768586d08d63 |
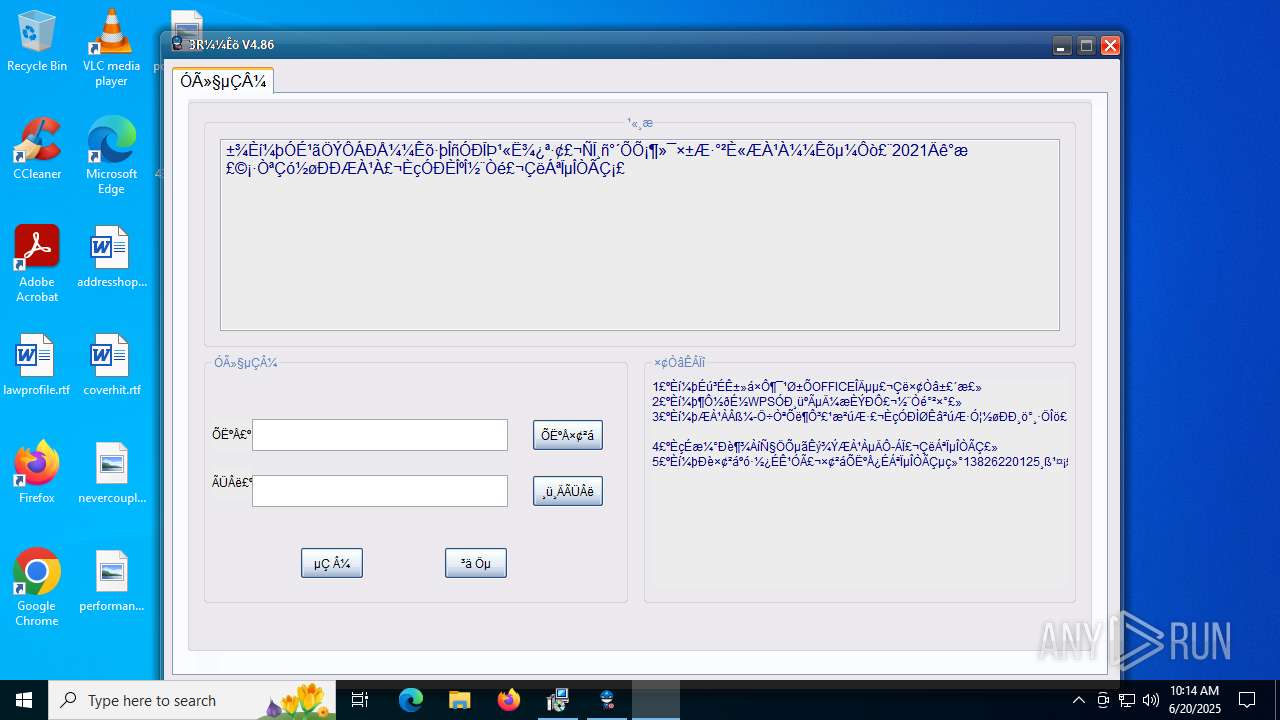
| Verdict: | Malicious activity |
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | June 20, 2025, 10:14:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
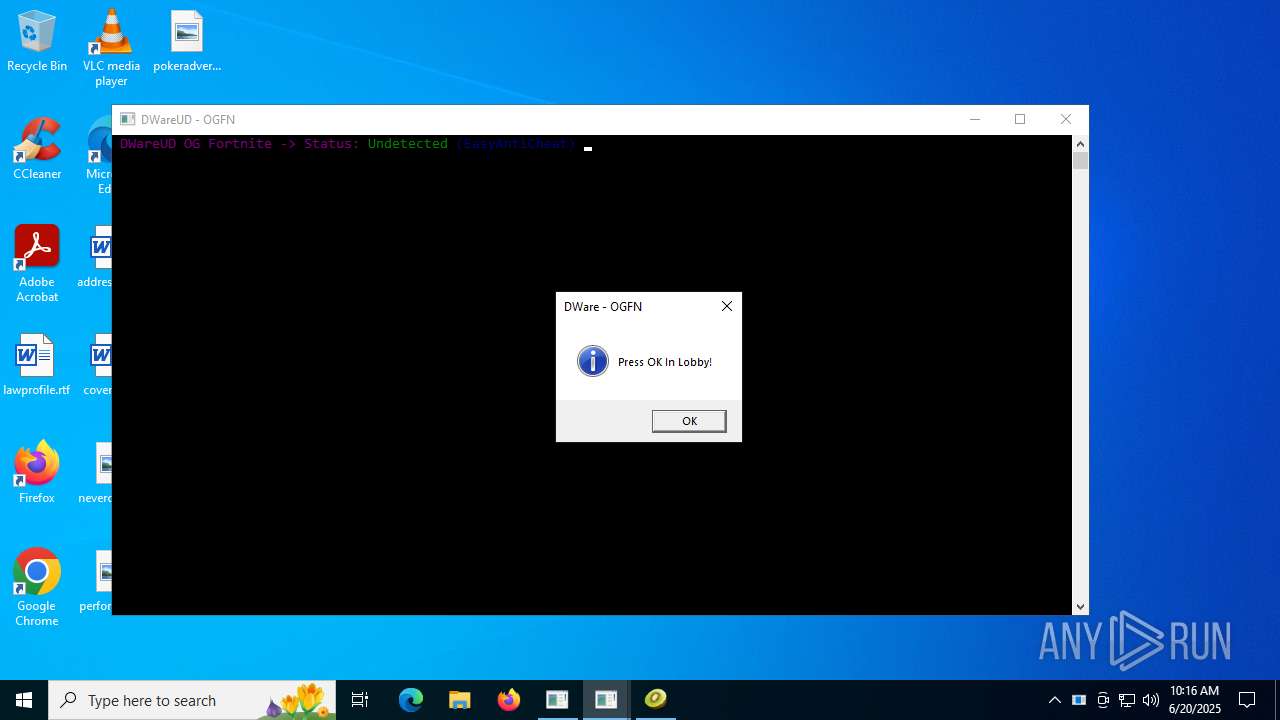
MALICIOUS
STEALERIUM has been found (auto)
- 4363463463464363463463463.exe (PID: 6684)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6684)
Steals credentials from Web Browsers
- S.exe (PID: 6980)
- test.exe (PID: 7560)
- RegSvcs.exe (PID: 10172)
Actions looks like stealing of personal data
- S.exe (PID: 6980)
- test.exe (PID: 7560)
- RegSvcs.exe (PID: 10172)
STEALERIUM has been detected (YARA)
- S.exe (PID: 6980)
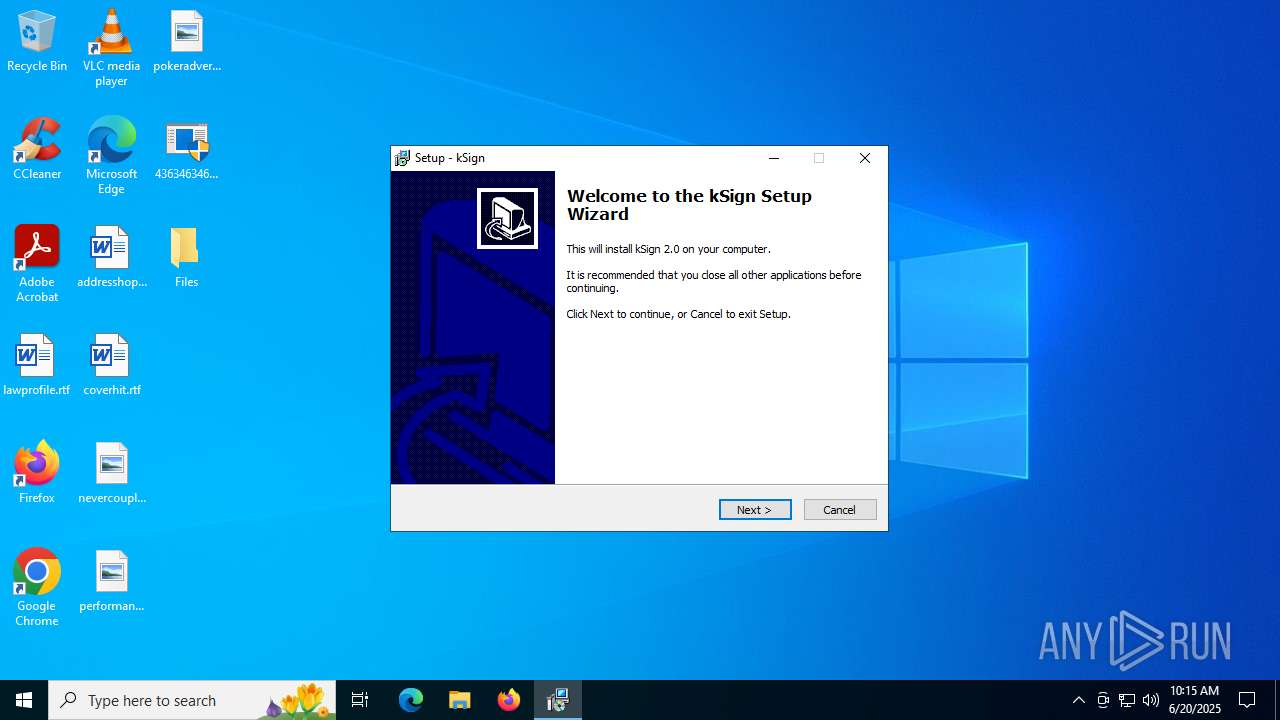
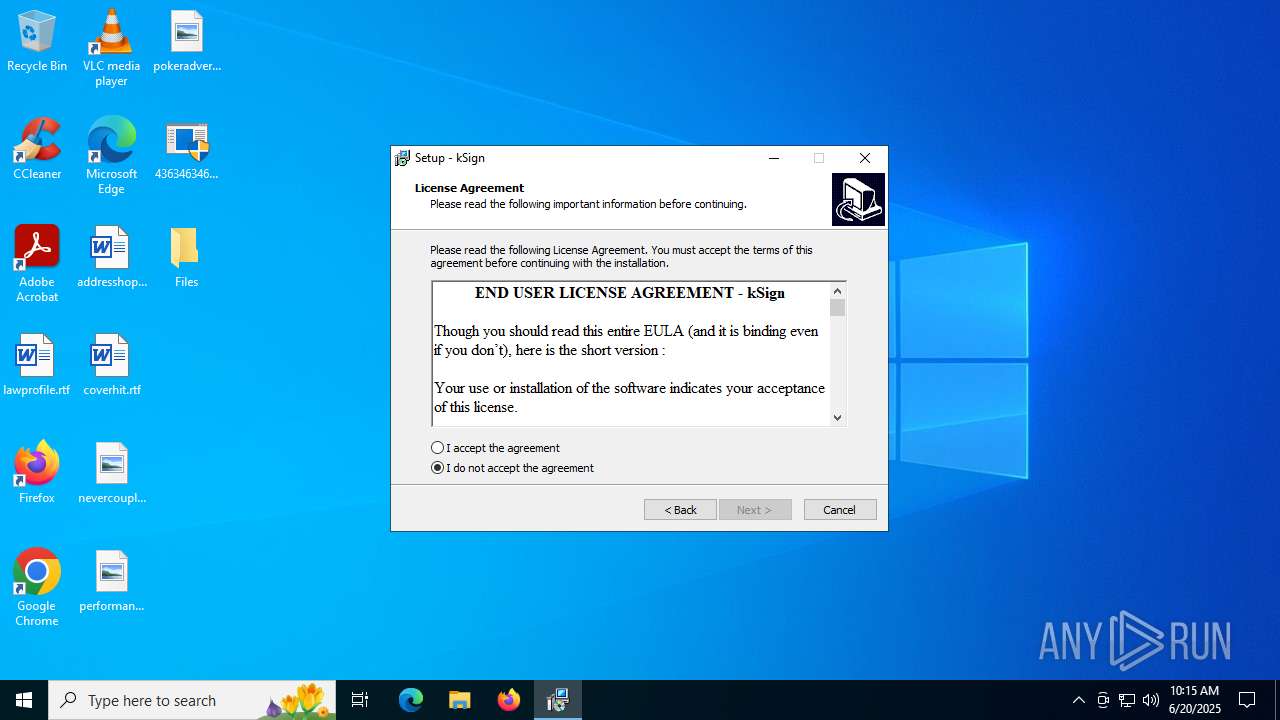
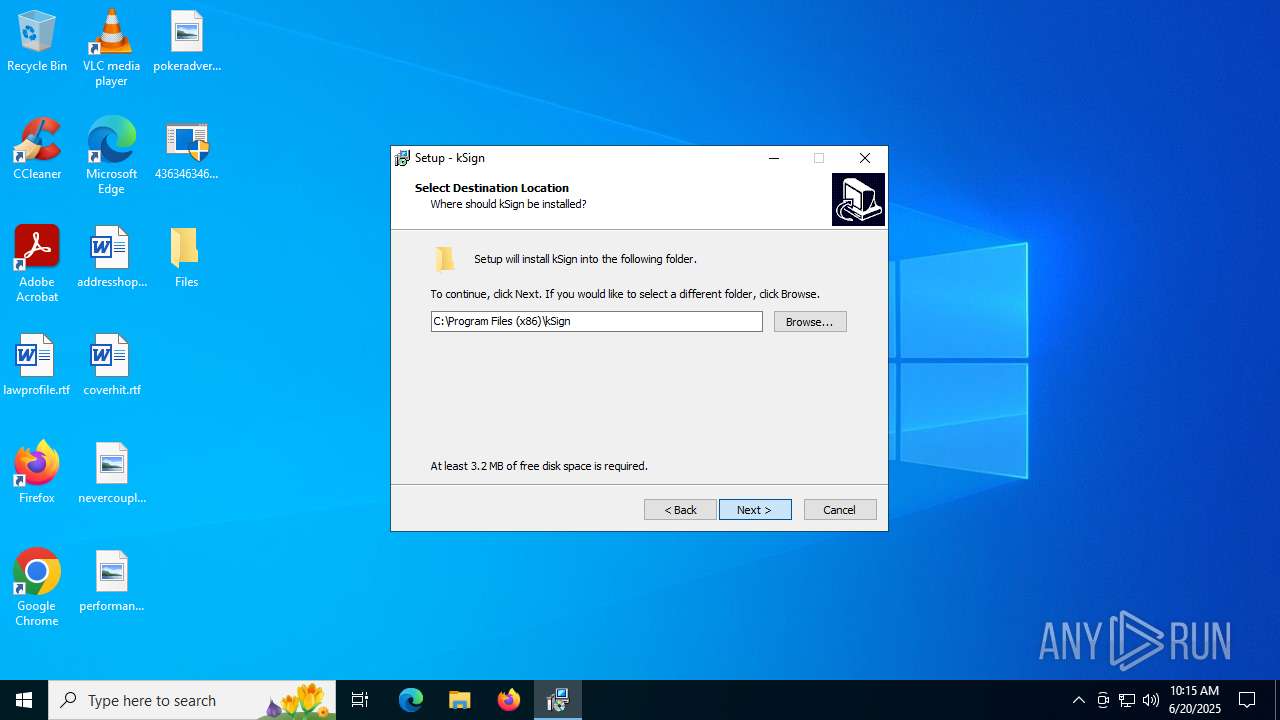
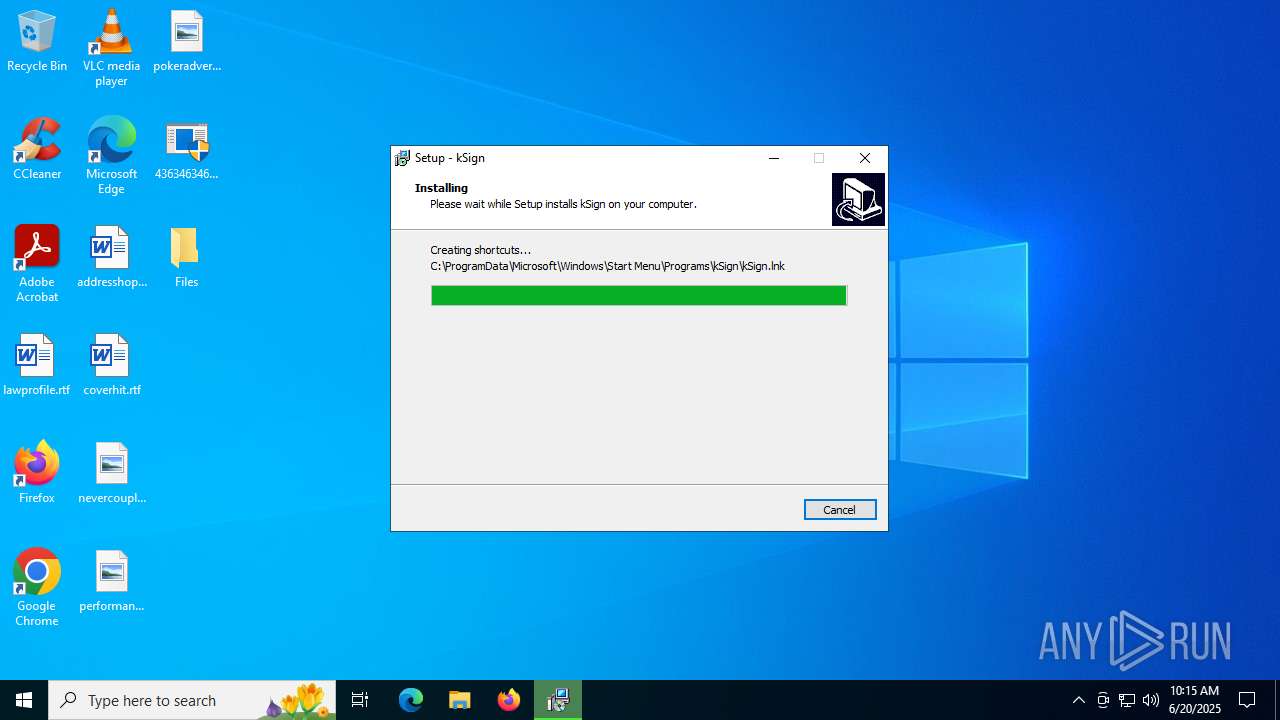
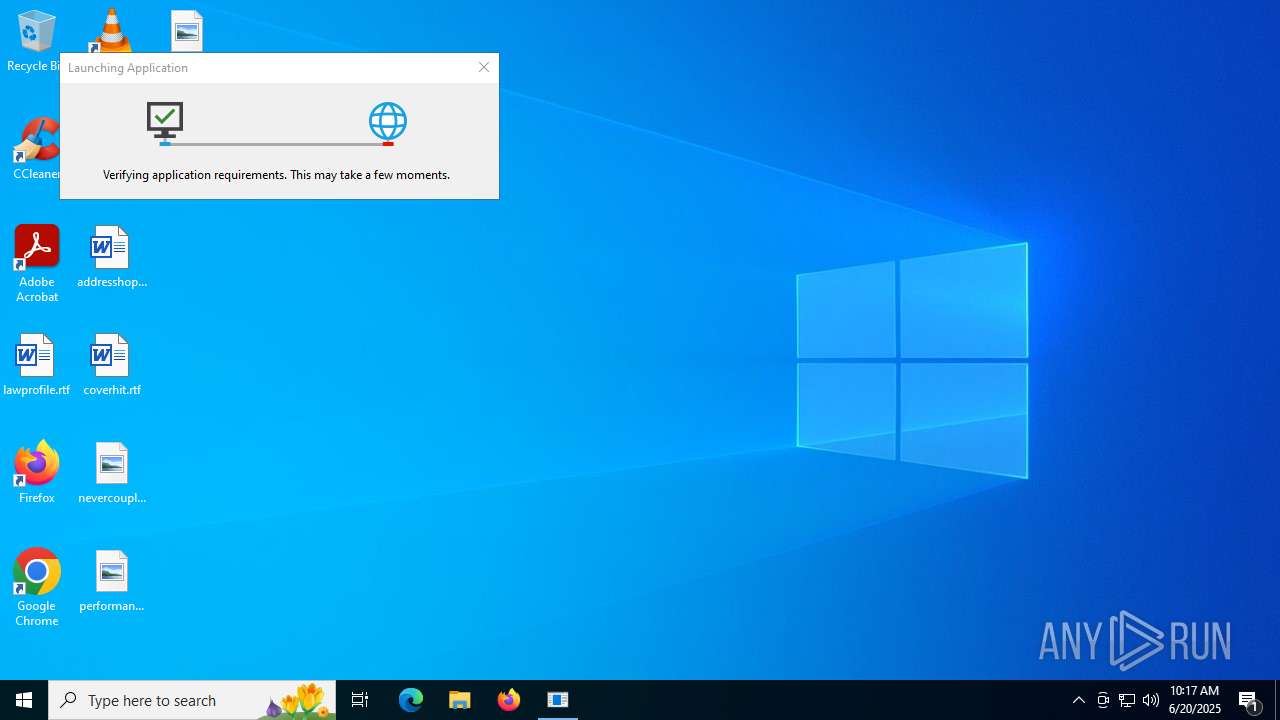
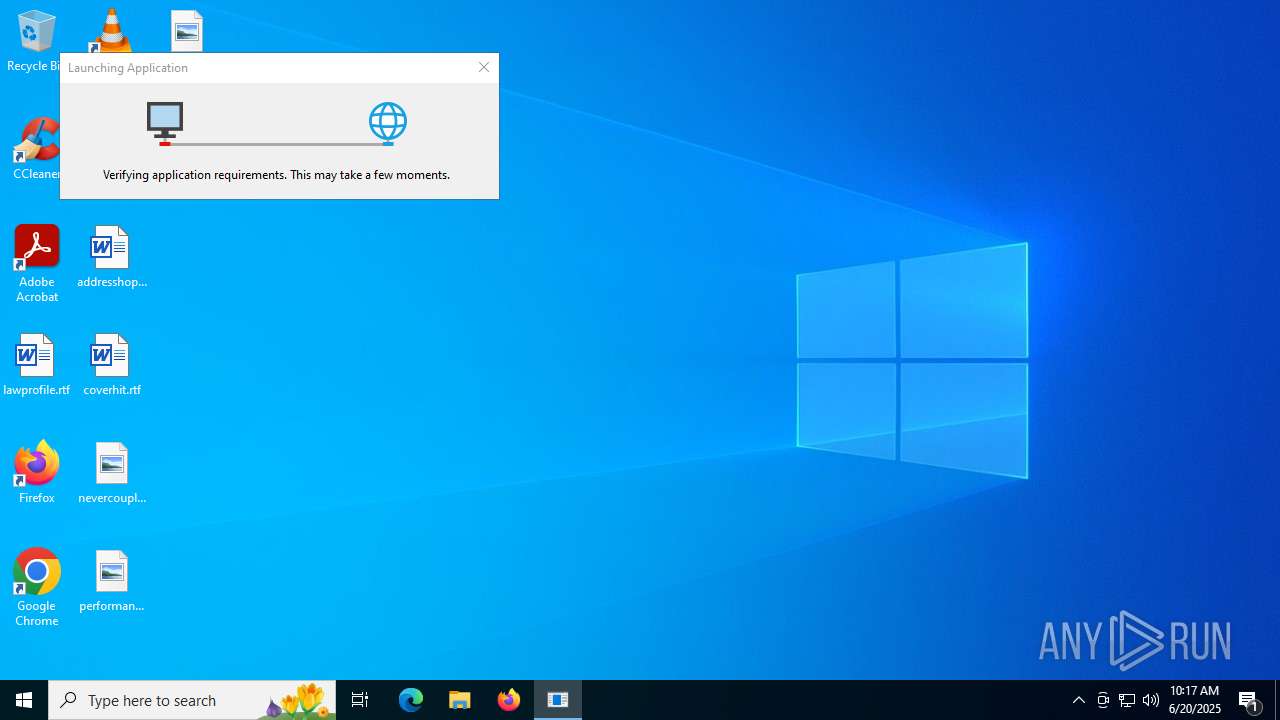
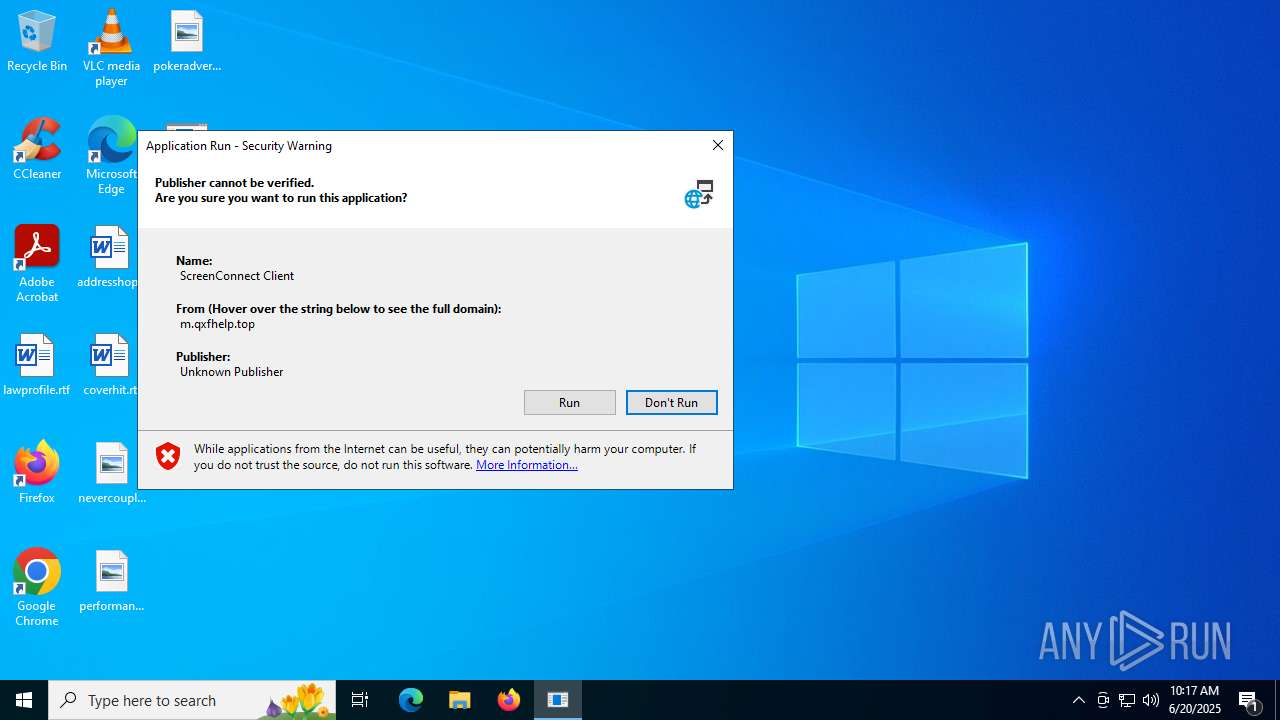
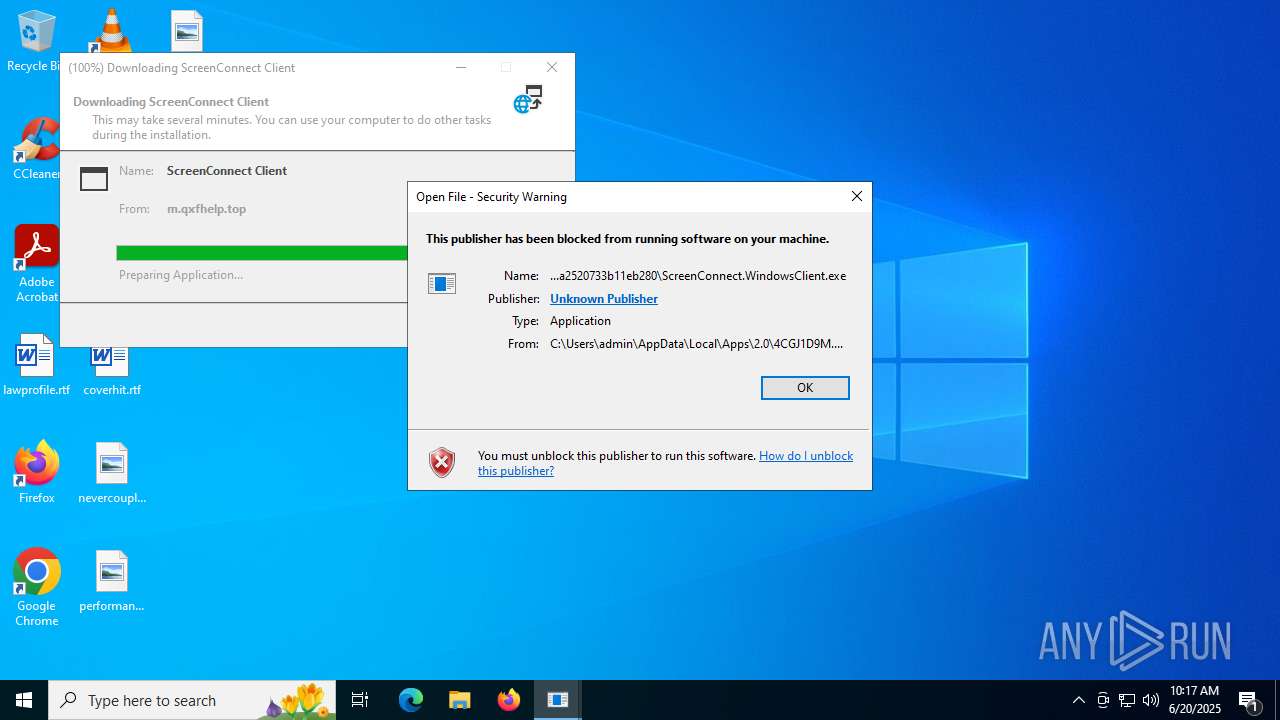
Executing a file with an untrusted certificate
- PrivacyPolicy.exe (PID: 7868)
- kSign.exe (PID: 7504)
- ClientRun.exe (PID: 8256)
- SeetrolClient.exe (PID: 5480)
- PhilipPatrol.exe (PID: 9060)
Uses Task Scheduler to autorun other applications
- bootstrapper.exe (PID: 7820)
- bootstrapper.exe (PID: 6896)
- Client-built.exe (PID: 7272)
- RuntimeBroker.exe (PID: 7932)
- Client.exe (PID: 7404)
- Client.exe (PID: 1080)
- svhost.exe (PID: 7560)
- svhost.exe (PID: 6216)
- Client.exe (PID: 5240)
- Client.exe (PID: 7392)
- Sentil.exe (PID: 1808)
- Client1.exe (PID: 8084)
- Client.exe (PID: 1512)
- Client.exe (PID: 9132)
- Client.exe (PID: 7648)
- Client.exe (PID: 8544)
- Quas_Autre_ncrypt.exe (PID: 1268)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Clients.exe (PID: 8548)
- Clients.exe (PID: 8748)
- Client.exe (PID: 6380)
- Discord.exe (PID: 7488)
- Client.exe (PID: 8744)
- Client.exe (PID: 2380)
- cmd.exe (PID: 3704)
- Client.exe (PID: 1704)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- Client.exe (PID: 7600)
- Clients.exe (PID: 1332)
- Client.exe (PID: 7500)
- Clients.exe (PID: 1236)
- cmd.exe (PID: 436)
- Client.exe (PID: 7180)
- cmd.exe (PID: 9284)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- Clients.exe (PID: 8996)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
QUASARRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 6684)
- Client-built.exe (PID: 7272)
- RuntimeBroker.exe (PID: 7308)
- 4363463463464363463463463.exe (PID: 6684)
- svhost.exe (PID: 7560)
- Sentil.exe (PID: 1808)
- 4363463463464363463463463.exe (PID: 6684)
- Quas_Autre_ncrypt.exe (PID: 1268)
Create files in the Startup directory
- Cloudy.exe (PID: 8072)
- IMG001.exe (PID: 5712)
Bypass execution policy to execute commands
- powershell.exe (PID: 7548)
- powershell.exe (PID: 8032)
- powershell.exe (PID: 8104)
- powershell.exe (PID: 7488)
Adds path to the Windows Defender exclusion list
- XClient.exe (PID: 1192)
- test.exe (PID: 7560)
Changes powershell execution policy (Bypass)
- XClient.exe (PID: 1192)
Changes Windows Defender settings
- XClient.exe (PID: 1192)
- test.exe (PID: 7560)
Adds process to the Windows Defender exclusion list
- XClient.exe (PID: 1192)
Uses Task Scheduler to run other applications
- XClient.exe (PID: 1192)
Changes the autorun value in the registry
- XClient.exe (PID: 1192)
- Dark_Autre_ncrypt.exe (PID: 8464)
- msdcsc.exe (PID: 8868)
- client.exe (PID: 8500)
- klass.exe (PID: 9016)
- budiao.exe (PID: 1044)
- rmd_en_1.exe (PID: 8264)
- FreeYoutubeDownloader.exe (PID: 1800)
Registers / Runs the DLL via REGSVR32.EXE
- PrivacyPolicy.tmp (PID: 504)
XWORM has been detected (YARA)
- Cloudy.exe (PID: 8072)
- XClient.exe (PID: 1192)
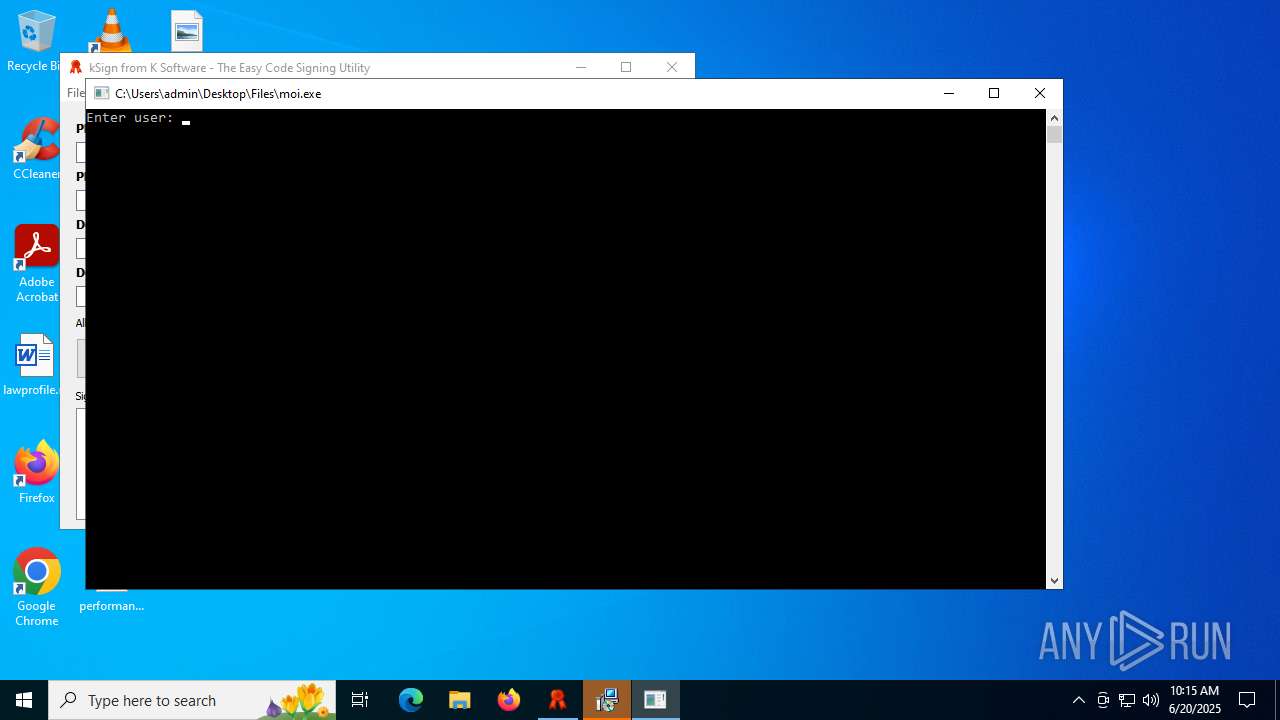
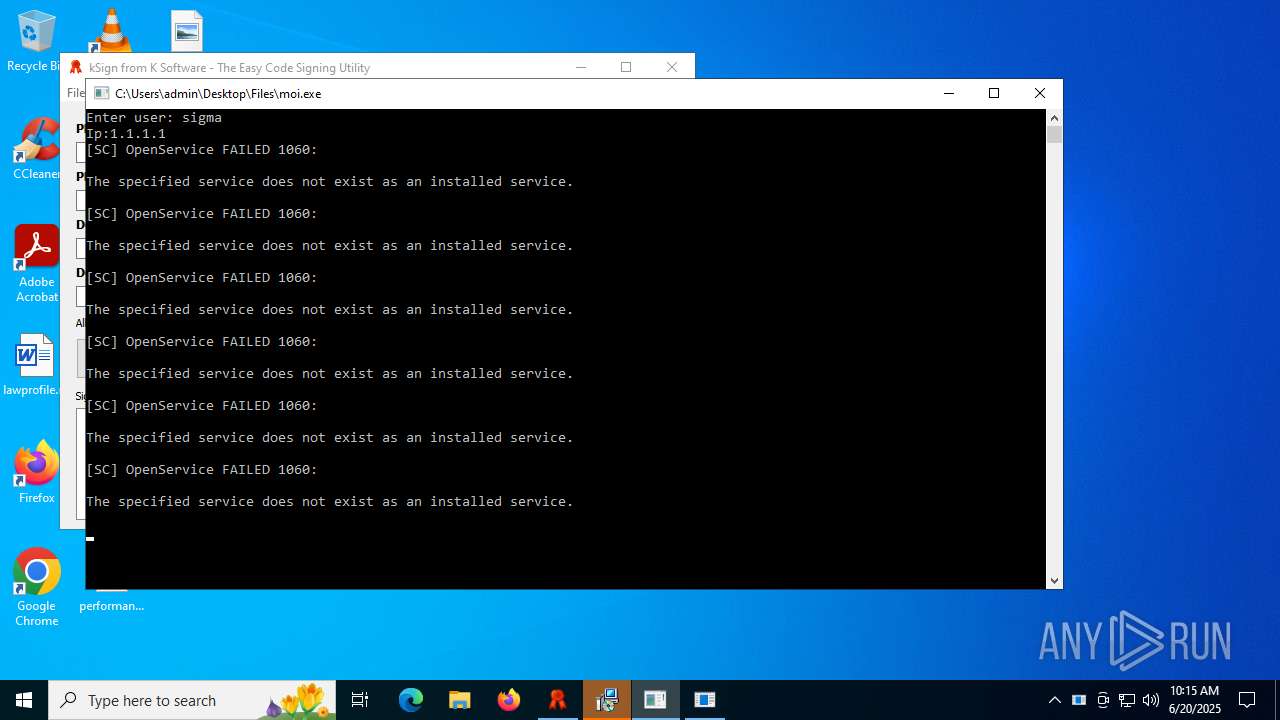
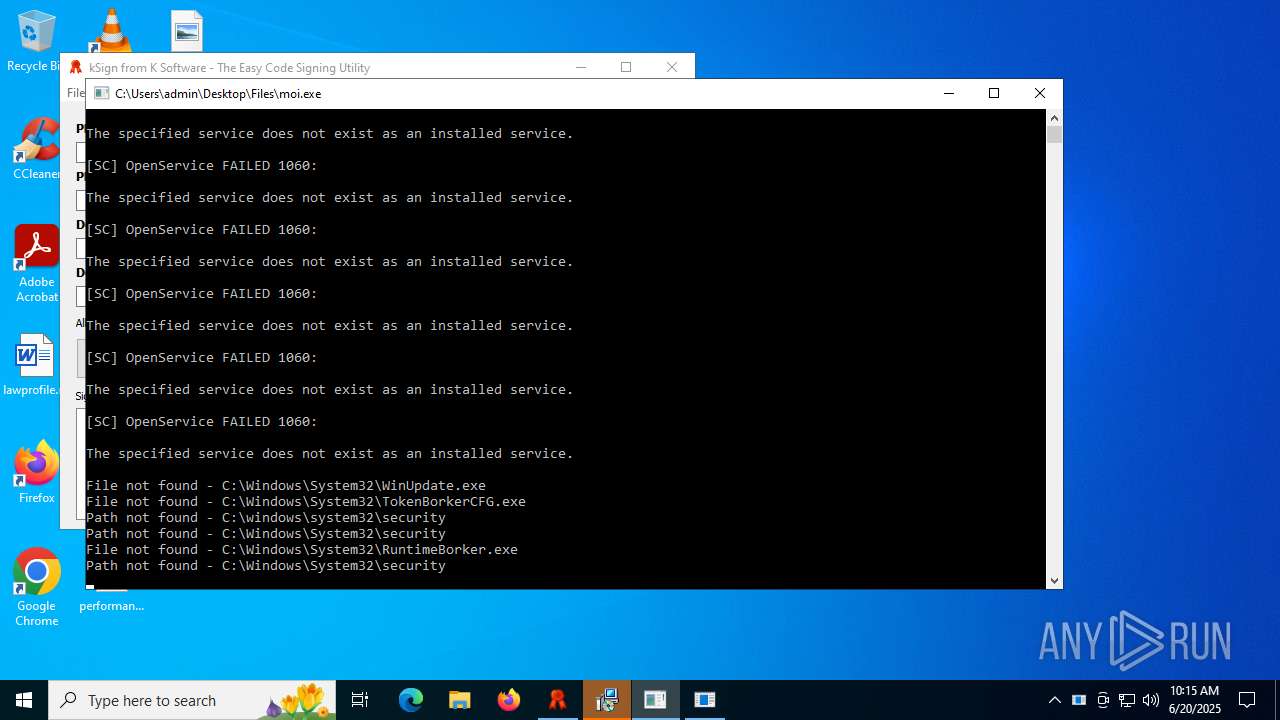
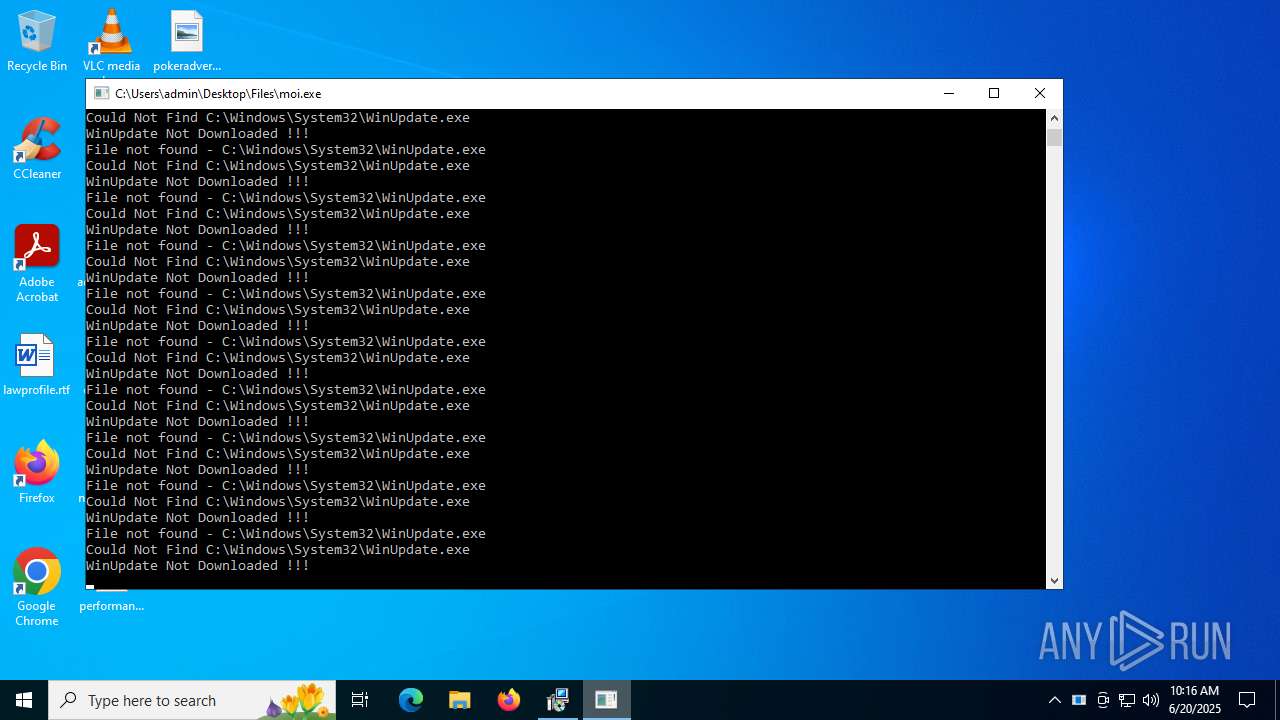
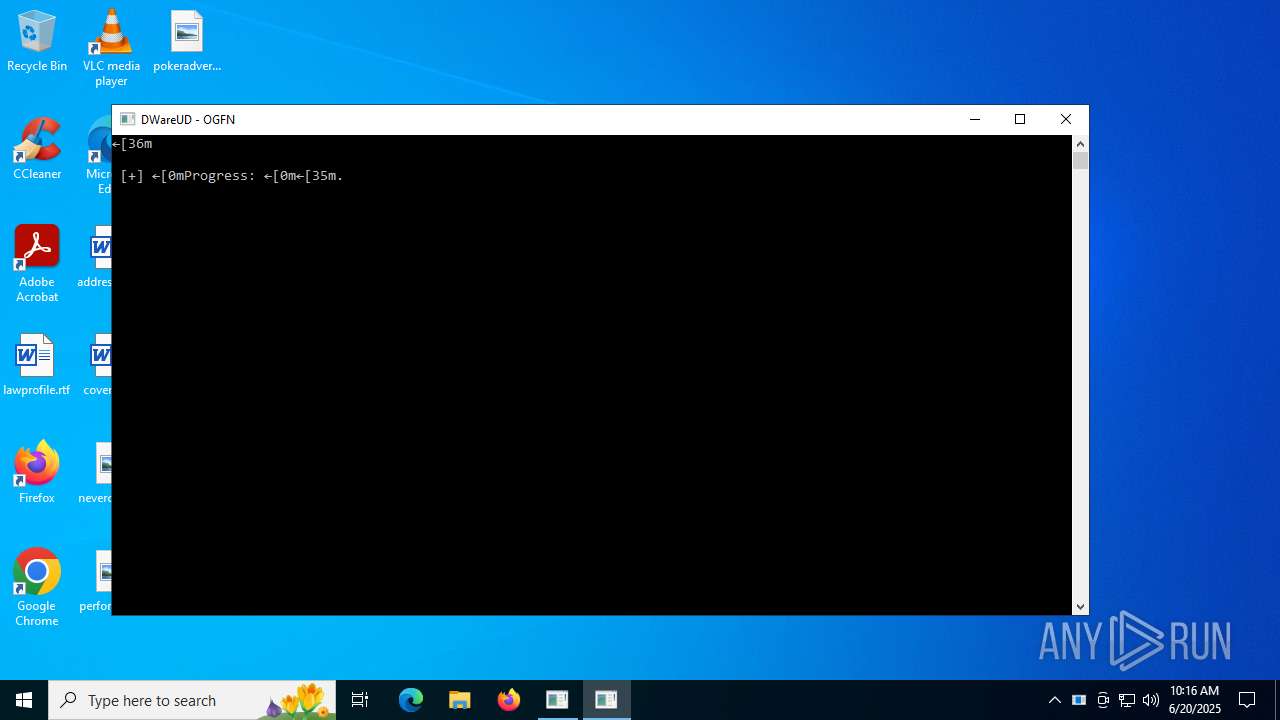
GENERIC has been found (auto)
- 4363463463464363463463463.exe (PID: 6684)
- 4363463463464363463463463.exe (PID: 6684)
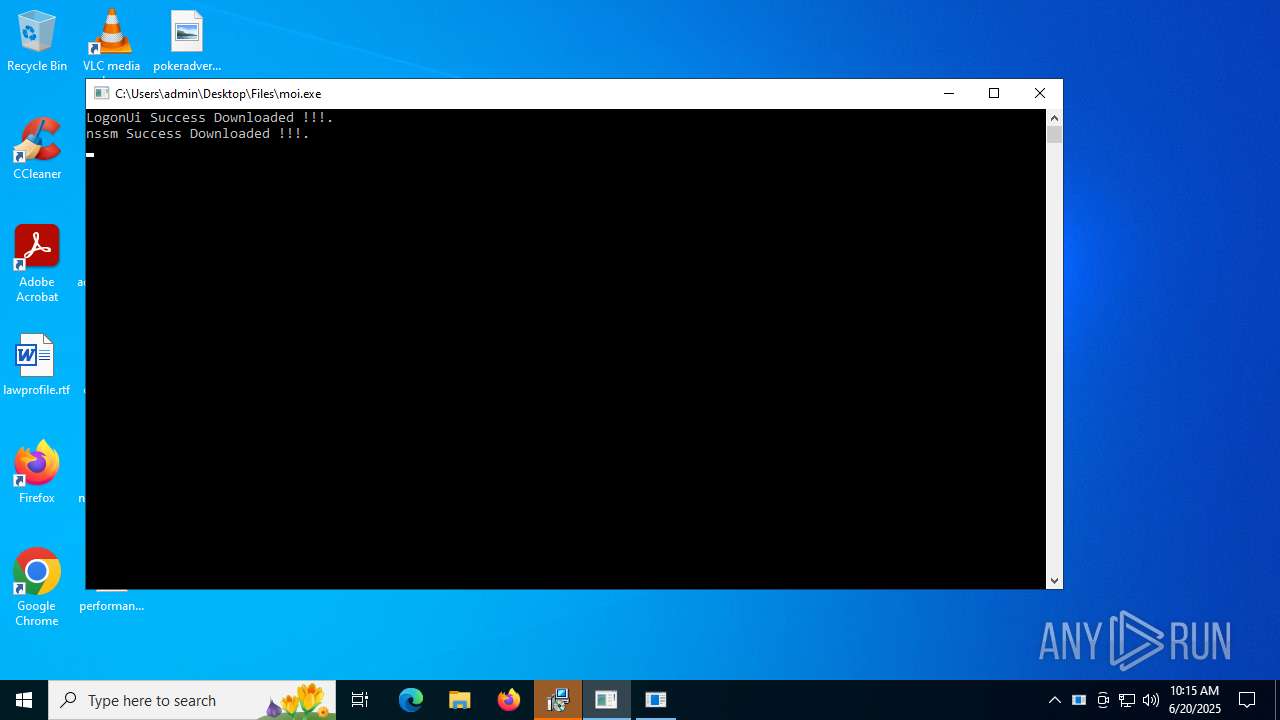
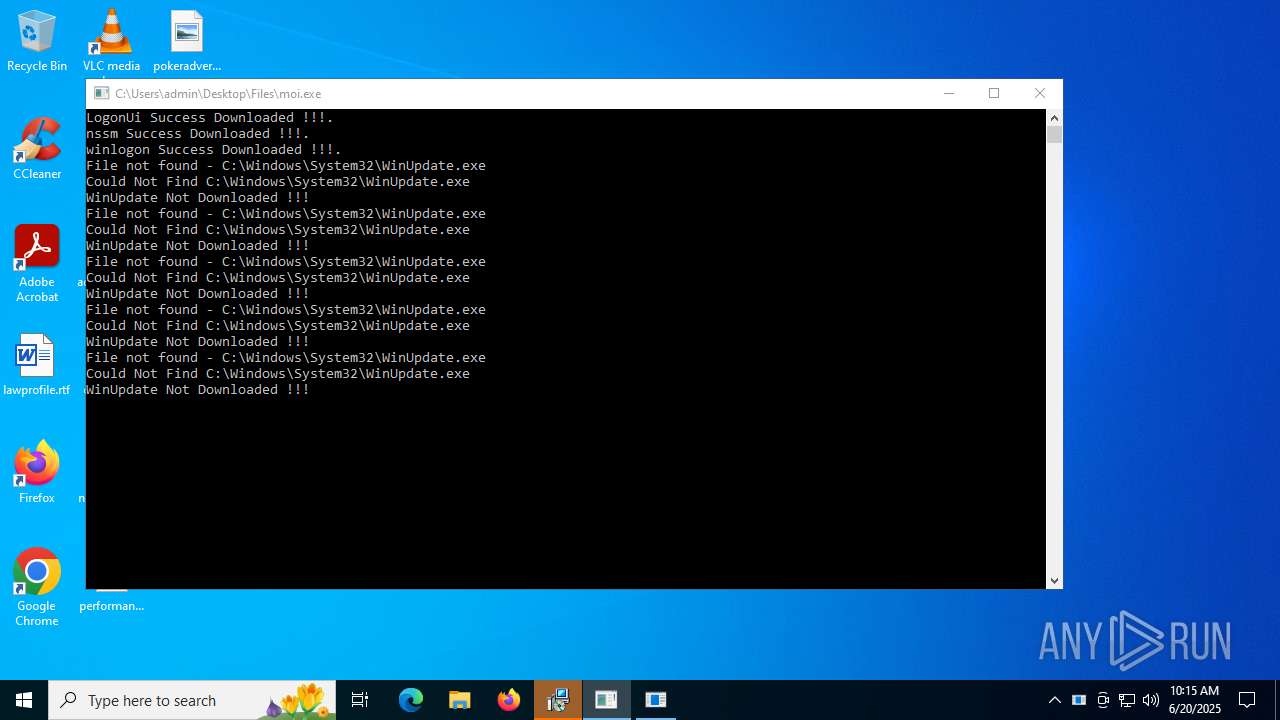
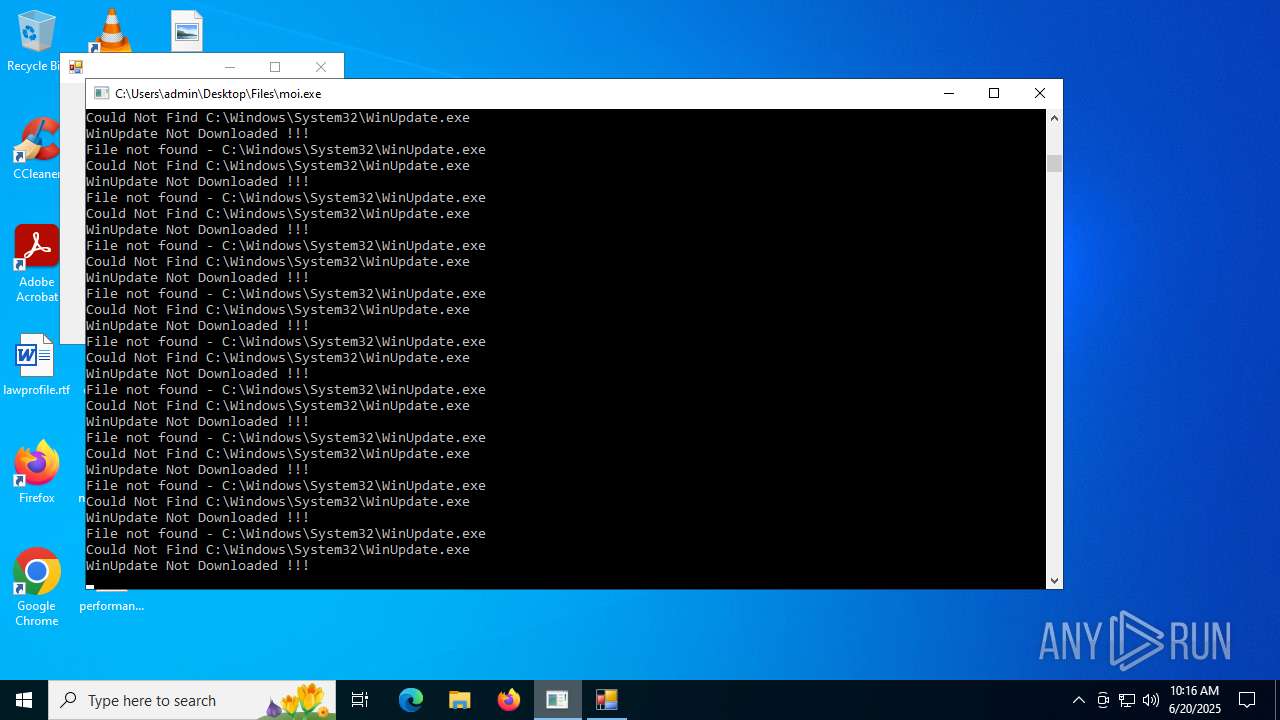
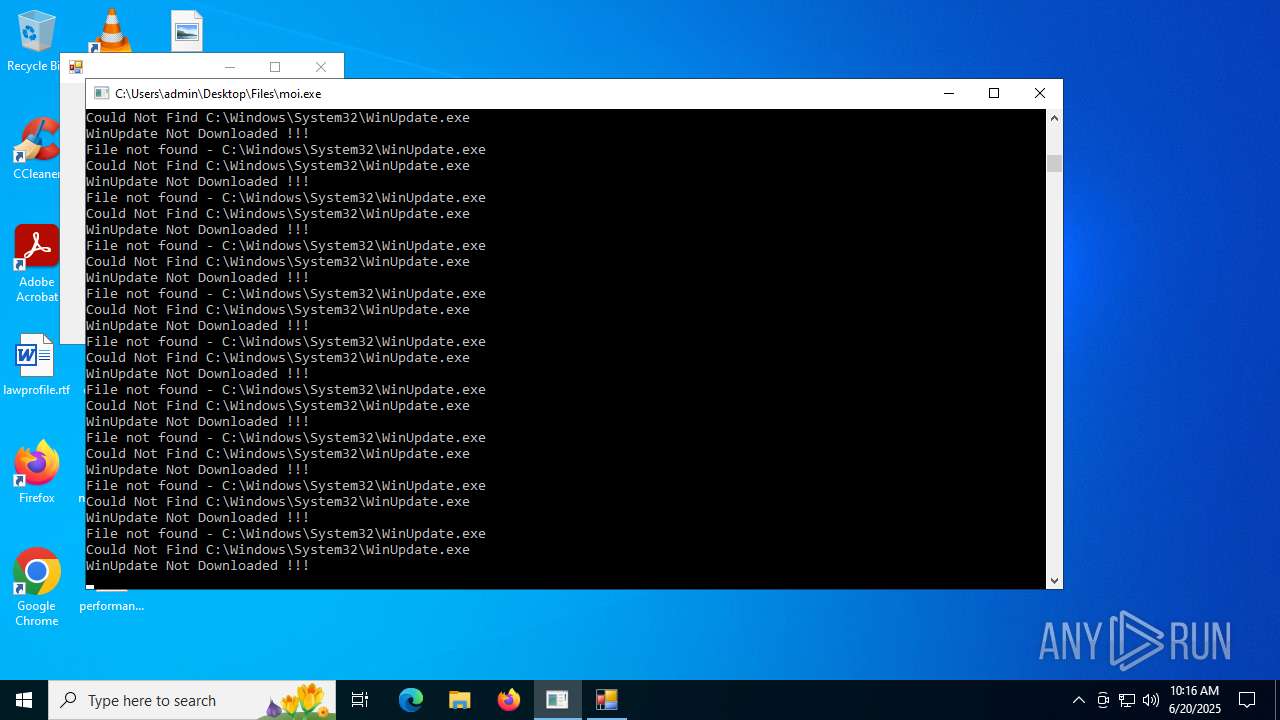
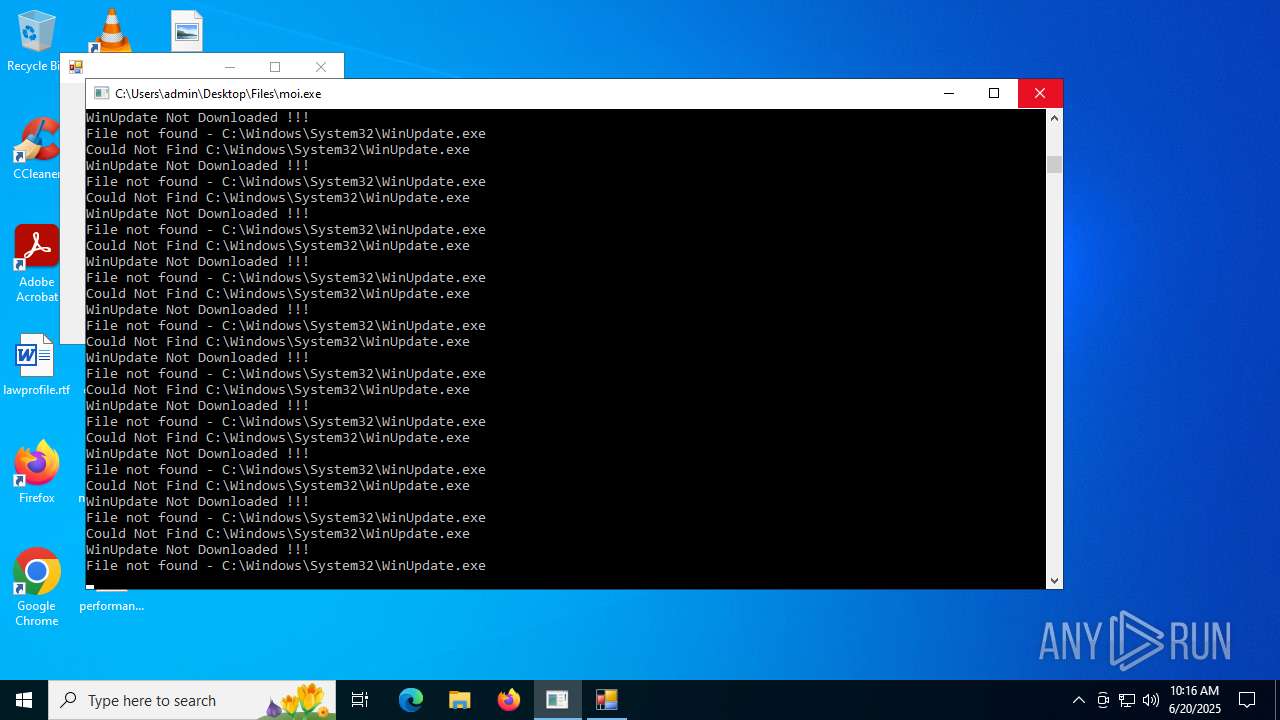
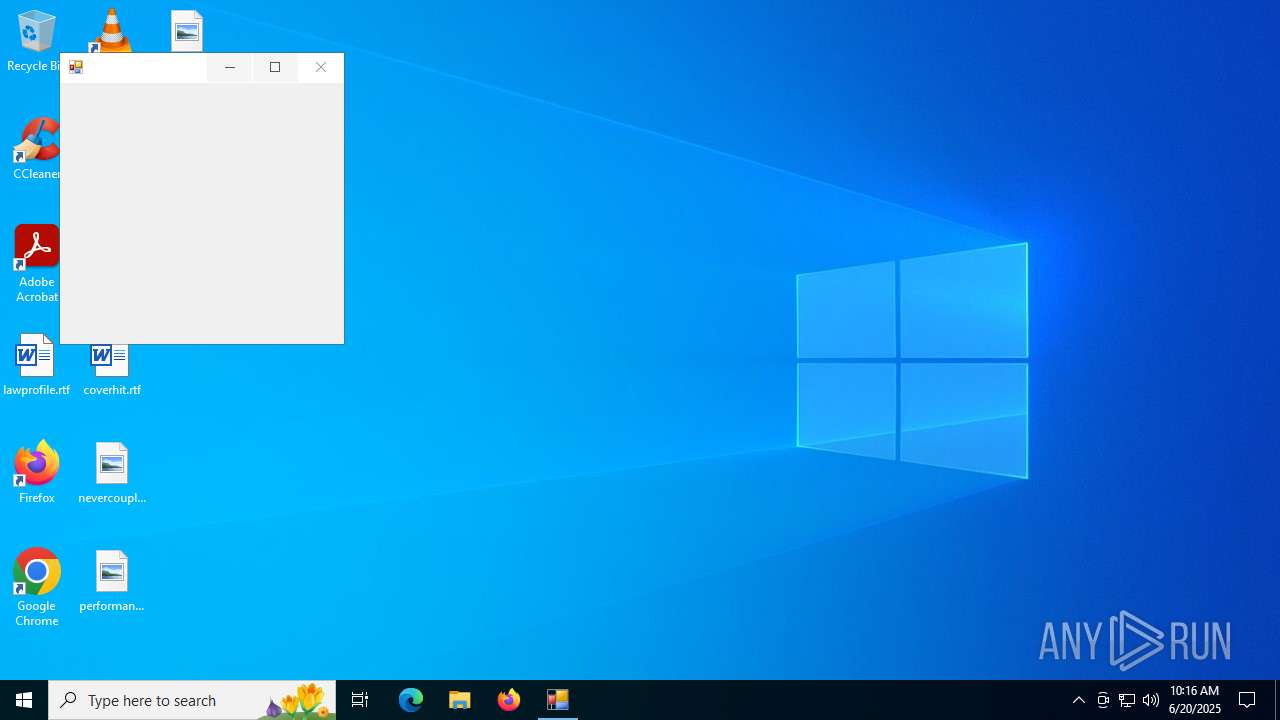
- moi.exe (PID: 1800)
- 4363463463464363463463463.exe (PID: 6684)
- Ganja3.exe (PID: 8404)
- 4363463463464363463463463.exe (PID: 6684)
- budiao.exe (PID: 1044)
XWORM has been detected (SURICATA)
- XClient.exe (PID: 1192)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2200)
Connects to the CnC server
- svchost.exe (PID: 2200)
- 4363463463464363463463463.exe (PID: 6684)
METASPLOIT has been detected (SURICATA)
- XClient.exe (PID: 1192)
QUASAR has been detected (YARA)
- RuntimeBroker.exe (PID: 7932)
- svhost.exe (PID: 6216)
Run PowerShell with an invisible window
- powershell.exe (PID: 7340)
- powershell.exe (PID: 8432)
DARKCOMET has been found (auto)
- 4363463463464363463463463.exe (PID: 6684)
- Dark_Autre_ncrypt.exe (PID: 8464)
Changes firewall settings
- msdcsc.exe (PID: 8868)
Disables Windows firewall
- msdcsc.exe (PID: 8868)
Changes the login/logoff helper path in the registry
- Dark_Autre_ncrypt.exe (PID: 8464)
DARKCOMET mutex has been found
- msdcsc.exe (PID: 8868)
- notepad.exe (PID: 8412)
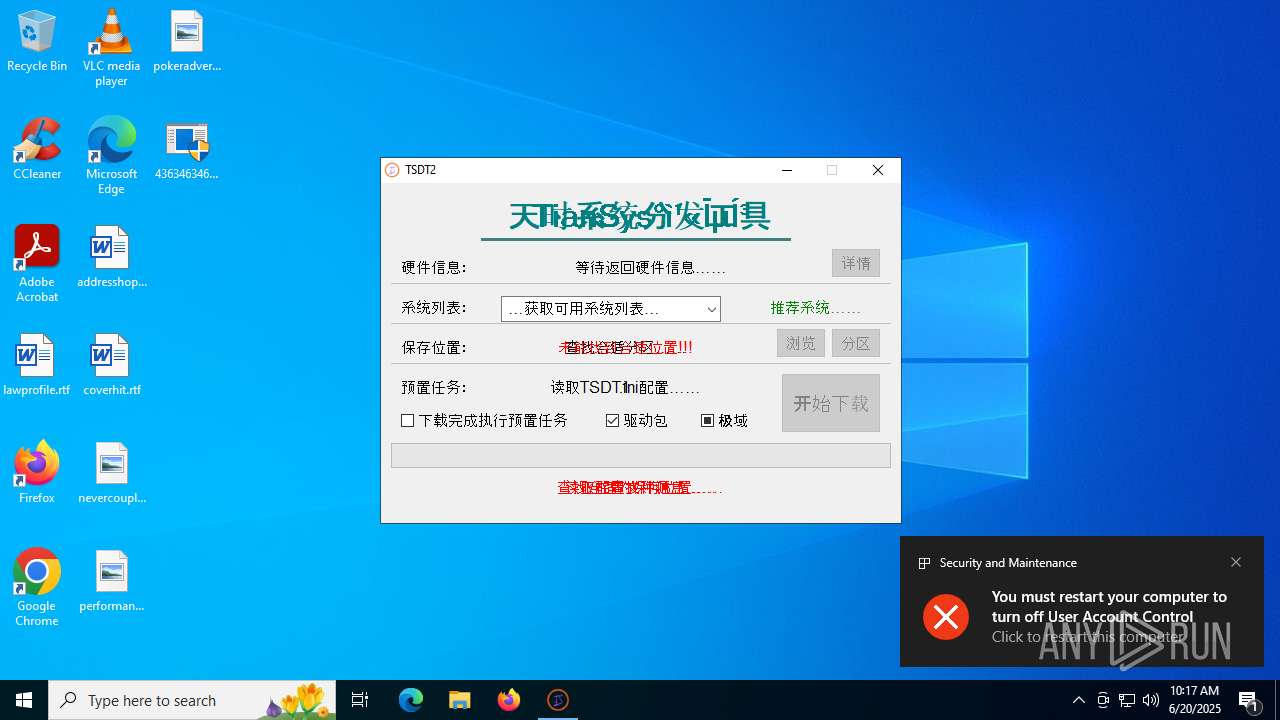
UAC/LUA settings modification
- msdcsc.exe (PID: 8868)
- SeetrolClient.exe (PID: 5480)
- reg.exe (PID: 1380)
Changes Security Center notification settings
- msdcsc.exe (PID: 8868)
ASYNCRAT has been found (auto)
- Terminal_9235.exe (PID: 6700)
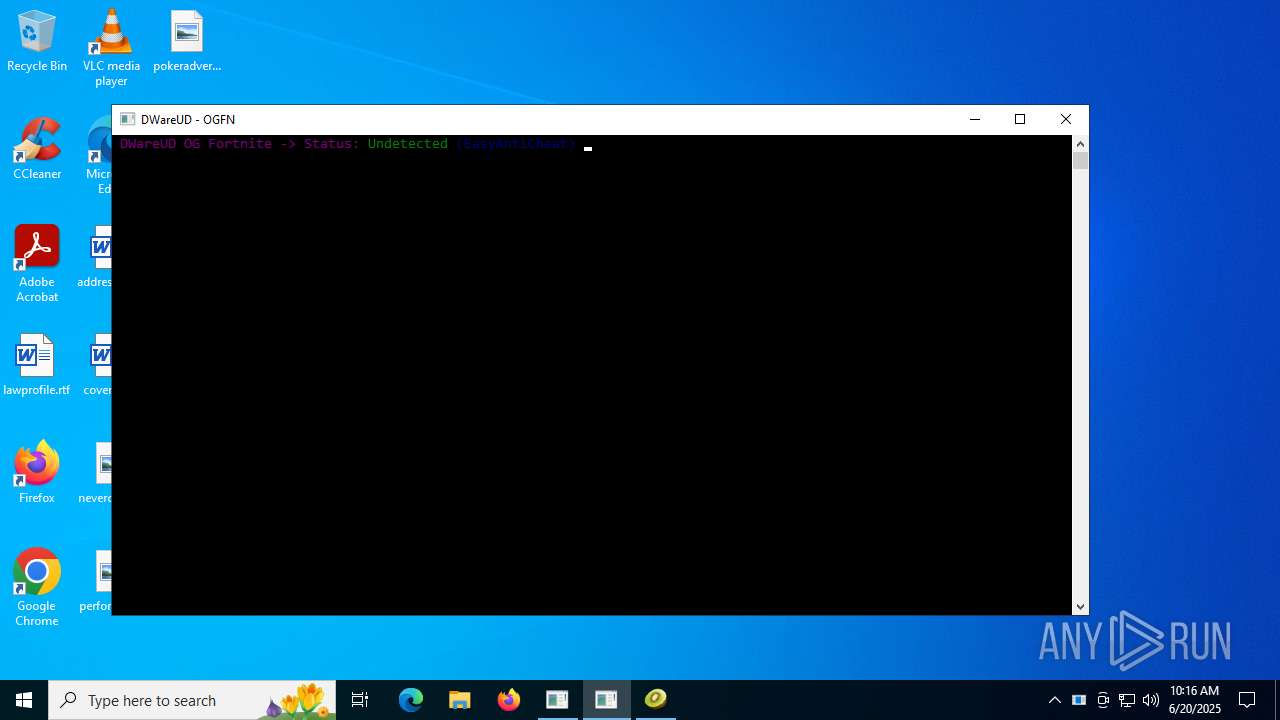
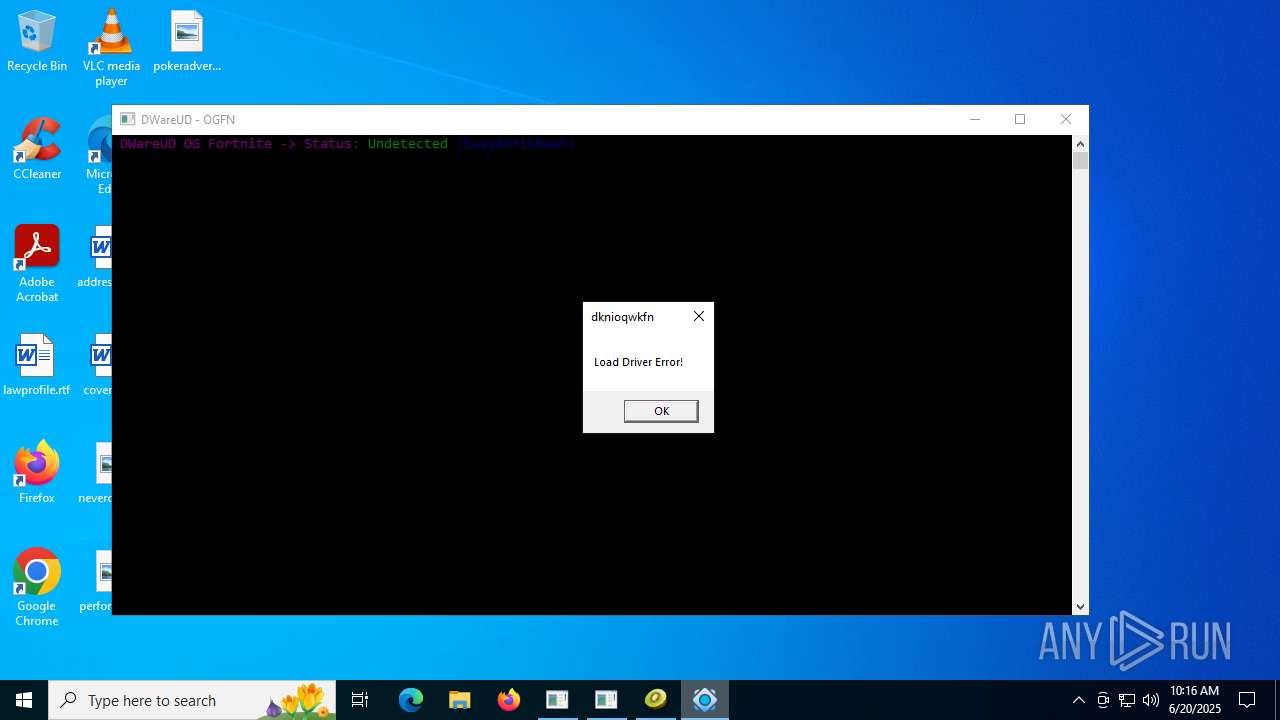
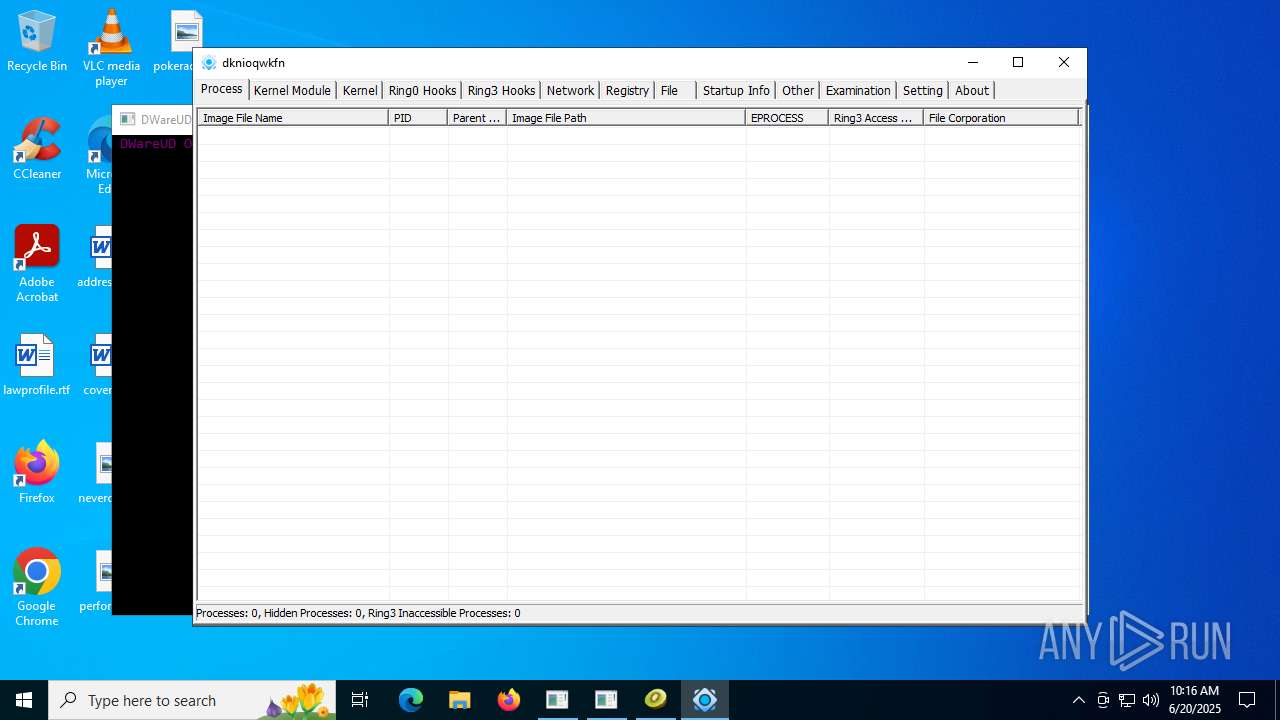
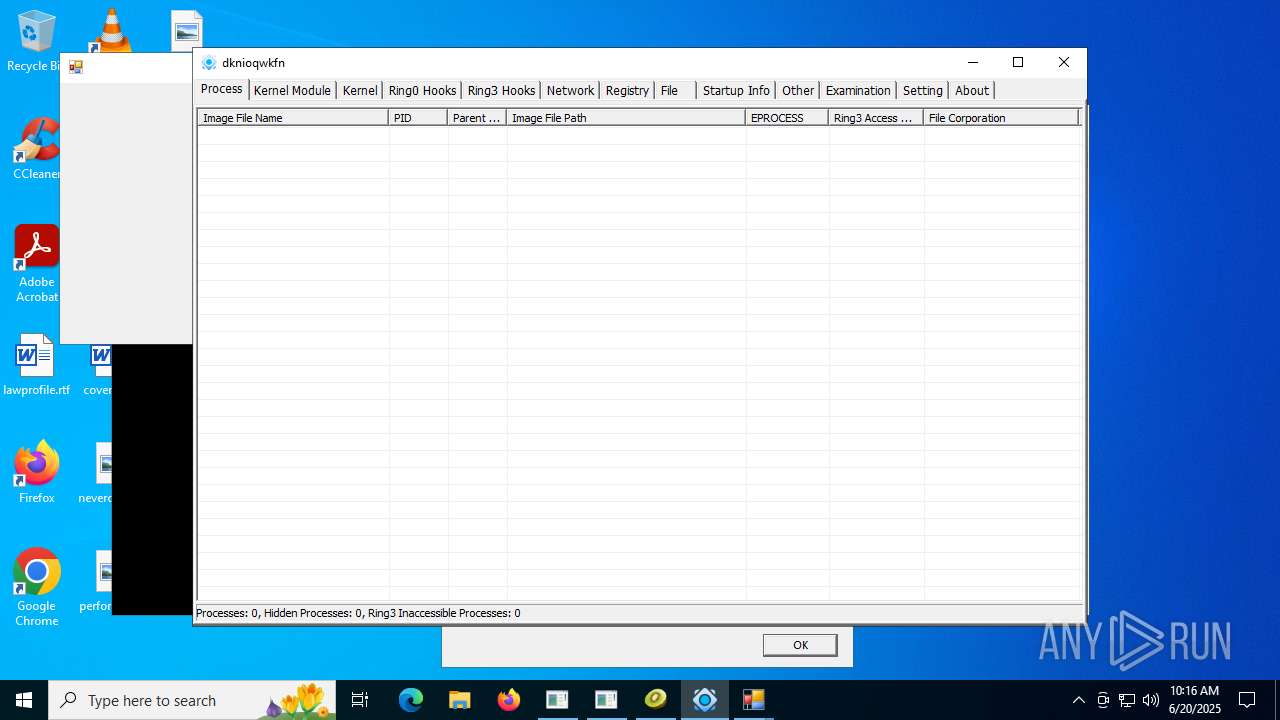
PCHUNTER mutex has been found
- PCHunter64.exe (PID: 4580)
COBALTSTRIKE has been detected (SURICATA)
- Lee.exe (PID: 7948)
SECTOPRAT has been detected
- cmd.exe (PID: 9152)
XRED mutex has been found
- budiao.exe (PID: 1044)
- Synaptics.exe (PID: 8680)
Creates or modifies Windows services
- svchocl.exe (PID: 8364)
REDDRIVER has been detected (SURICATA)
- svchost.exe (PID: 5240)
- DmOmaCpMo.exe (PID: 10108)
- appidcertstorecheck.exe (PID: 9448)
Runs injected code in another process
- celkadrobitel.exe (PID: 10044)
Application was injected by another process
- explorer.exe (PID: 4772)
LimeRAT is detected
- Wsystem.exe (PID: 2716)
SNAKEKEYLOGGER has been detected (SURICATA)
- RegSvcs.exe (PID: 10172)
DANABOT has been detected (SURICATA)
- nslookup.exe (PID: 3396)
SUSPICIOUS
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 6684)
- update.exe (PID: 4172)
- S.exe (PID: 6980)
- BootstrapperNew.exe (PID: 7900)
- Client.exe (PID: 640)
- Client.exe (PID: 7404)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- Client.exe (PID: 1080)
- XClient.exe (PID: 1192)
- Client.exe (PID: 5240)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 7392)
- Client1.exe (PID: 8084)
- Client.exe (PID: 1512)
- test.exe (PID: 7560)
- Client.exe (PID: 9132)
- Client.exe (PID: 7648)
- Dark_Autre_ncrypt.exe (PID: 8464)
- Terminal_9235.exe (PID: 6700)
- Client.exe (PID: 1508)
- SeetrolClient.exe (PID: 5480)
- ClientRun.exe (PID: 8256)
- Client.exe (PID: 8544)
- Clients.exe (PID: 8724)
- Client.exe (PID: 1268)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Client.exe (PID: 7824)
- Clients.exe (PID: 8548)
- Lee.exe (PID: 7948)
- Clients.exe (PID: 8748)
- av_downloader1.1.exe (PID: 5884)
- av_downloader1.1.exe (PID: 8148)
- ShellExperienceHost.exe (PID: 3948)
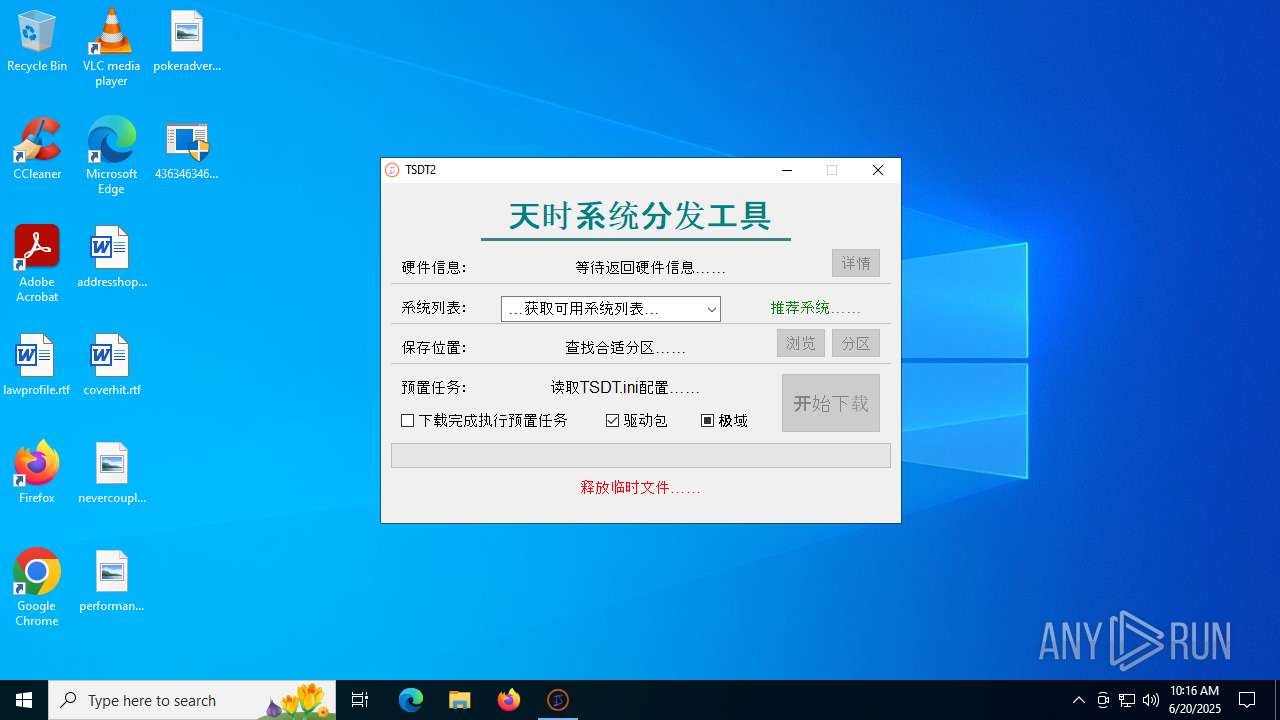
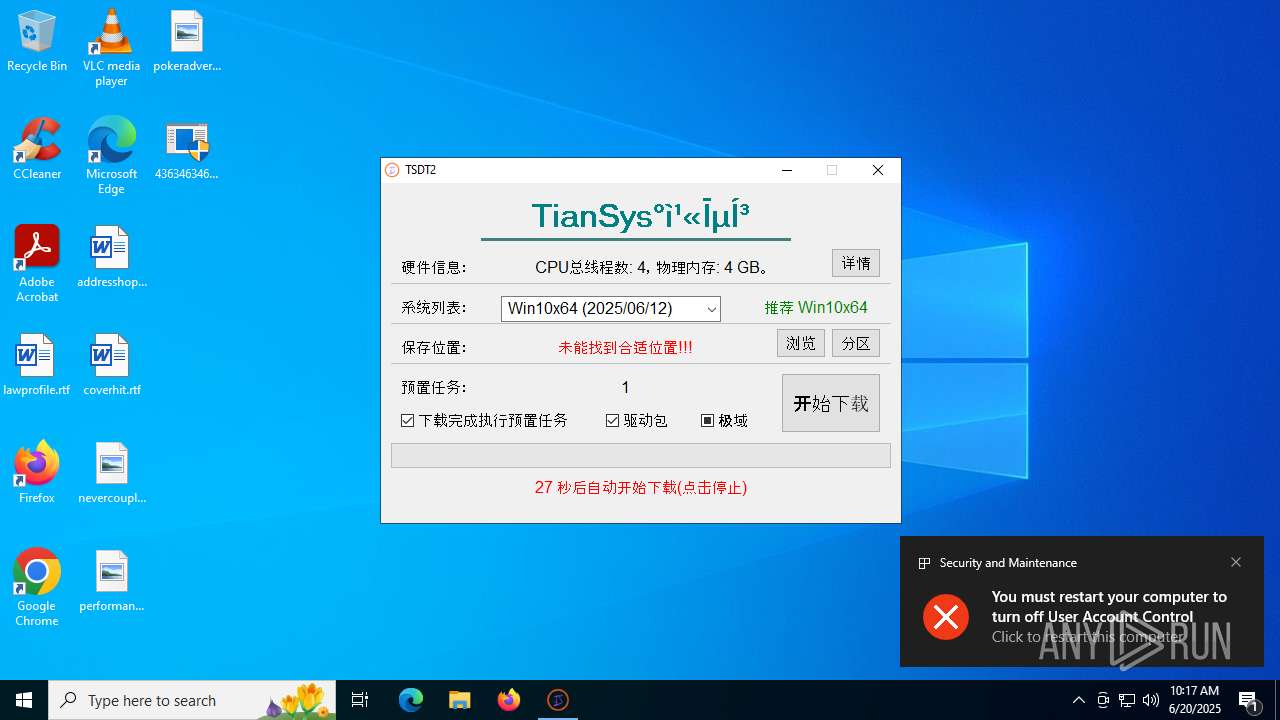
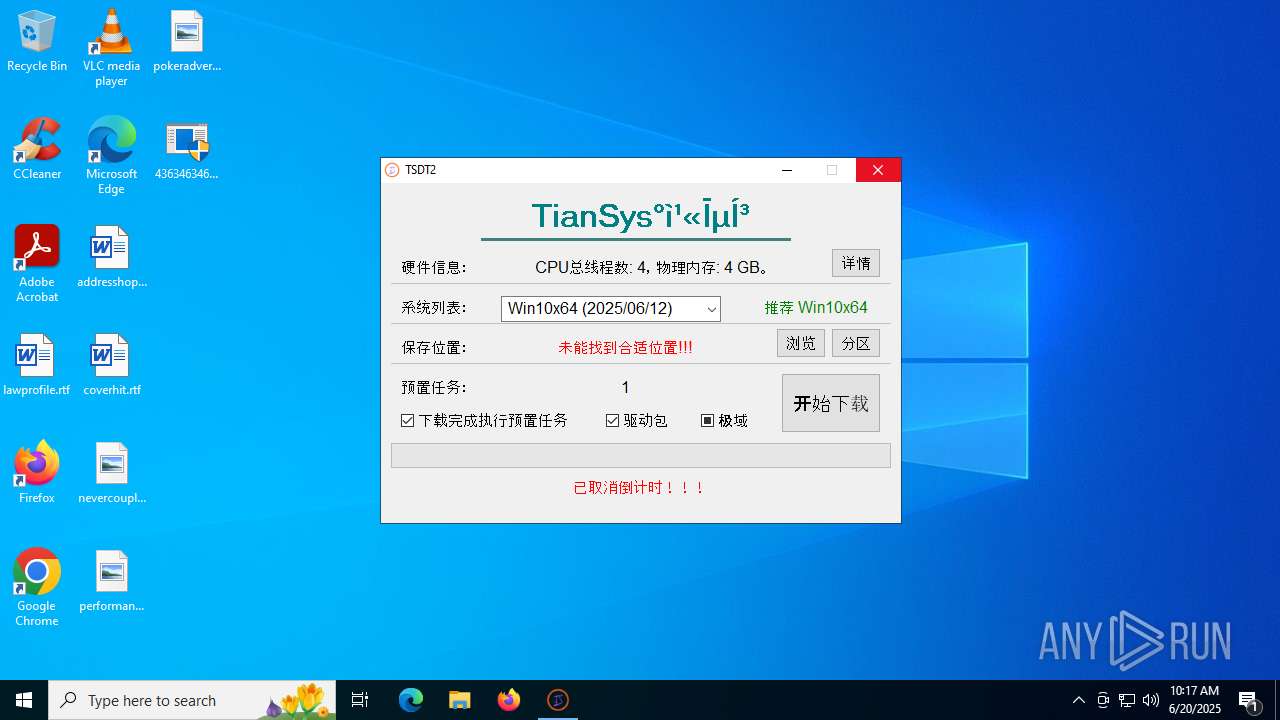
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- Client.exe (PID: 6380)
- 80.exe (PID: 8832)
- Clients.exe (PID: 1268)
- Client.exe (PID: 8744)
- Clients.exe (PID: 6524)
- PhilipPatrol.exe (PID: 9060)
- dfsvc.exe (PID: 3972)
- Client.exe (PID: 2380)
- 80.exe (PID: 8488)
- budiao.exe (PID: 1044)
- Synaptics.exe (PID: 8680)
- Clients.exe (PID: 7600)
- Client.exe (PID: 1704)
- svchocl.exe (PID: 8364)
- Clients.exe (PID: 6412)
- Wsystem.exe (PID: 6192)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- Client.exe (PID: 7600)
- IMG001.exe (PID: 9628)
- Clients.exe (PID: 1332)
- Client.exe (PID: 7500)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- IMG001.exe (PID: 5712)
- r-mail.exe (PID: 8352)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- tftp.exe (PID: 8040)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- FreeYoutubeDownloader.exe (PID: 1800)
- Clients.exe (PID: 8996)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 6684)
- S.exe (PID: 6980)
- 3R%BC%BC%CA%F5.exe (PID: 7796)
- PrivacyPolicy.tmp (PID: 504)
- PrivacyPolicy.exe (PID: 7868)
- bootstrapper.exe (PID: 7820)
- Client-built.exe (PID: 7272)
- RuntimeBroker.exe (PID: 7308)
- Cloudy.exe (PID: 8072)
- BootstrapperNew.exe (PID: 7900)
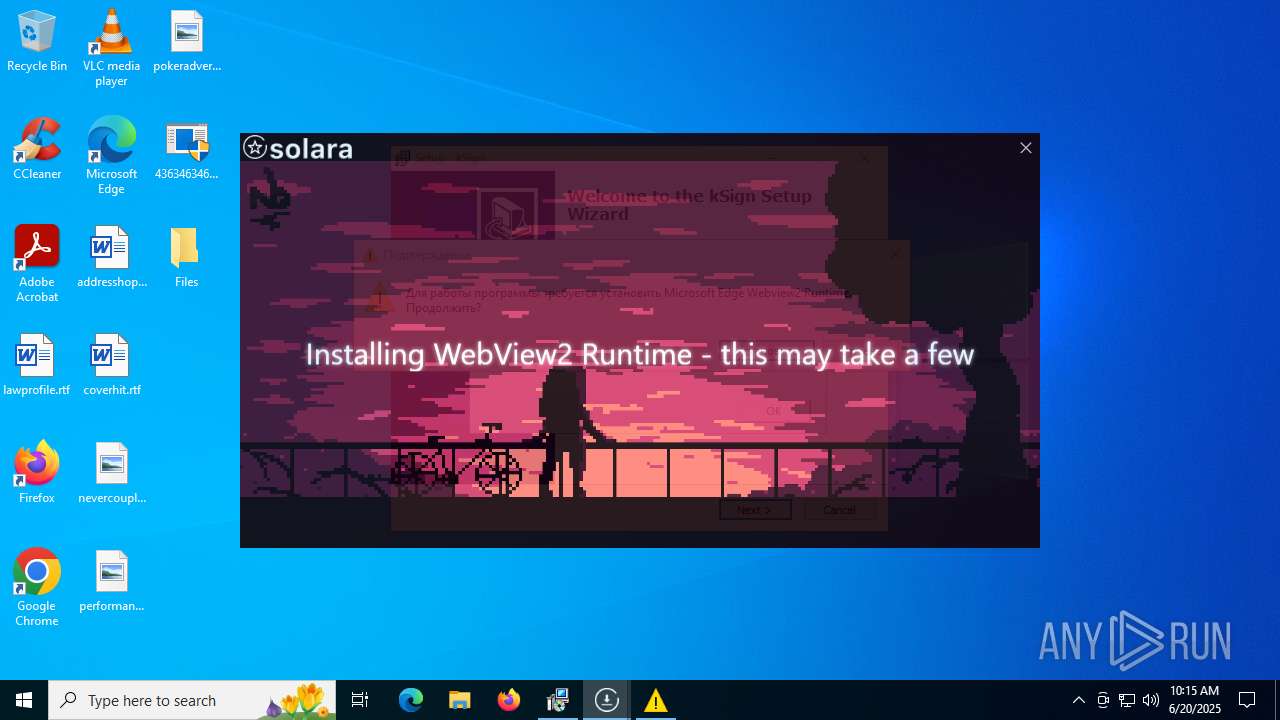
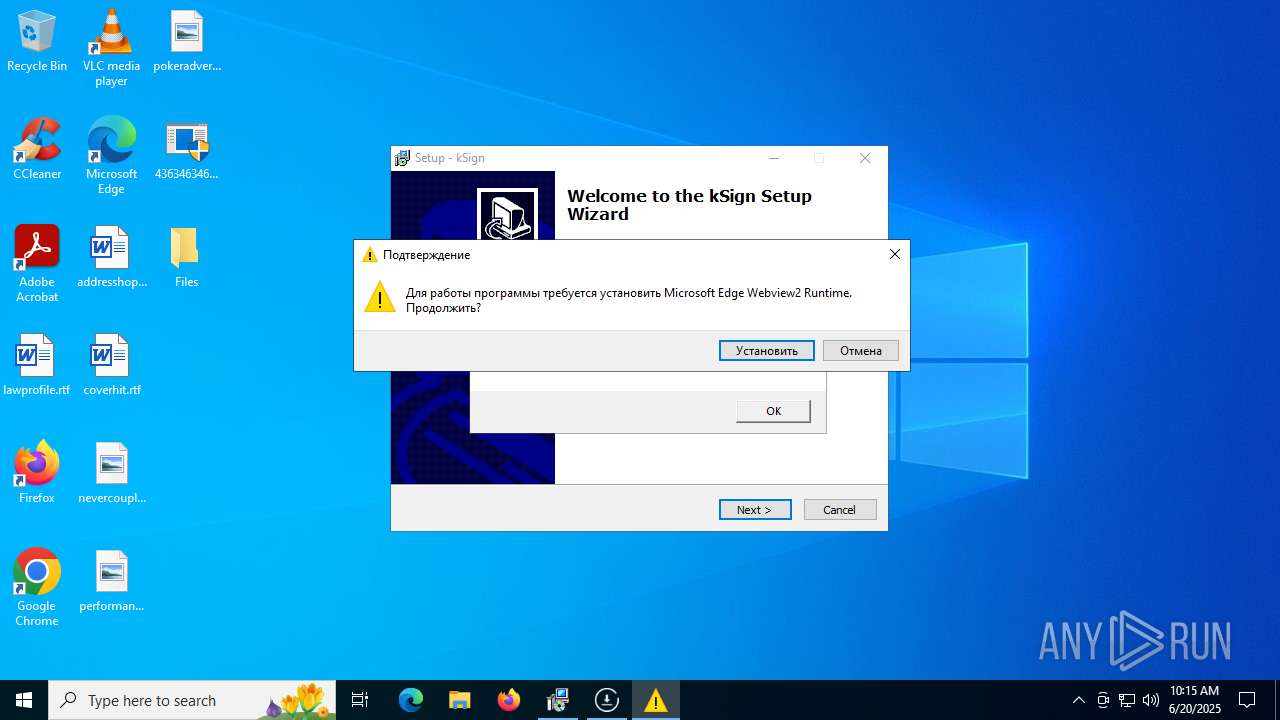
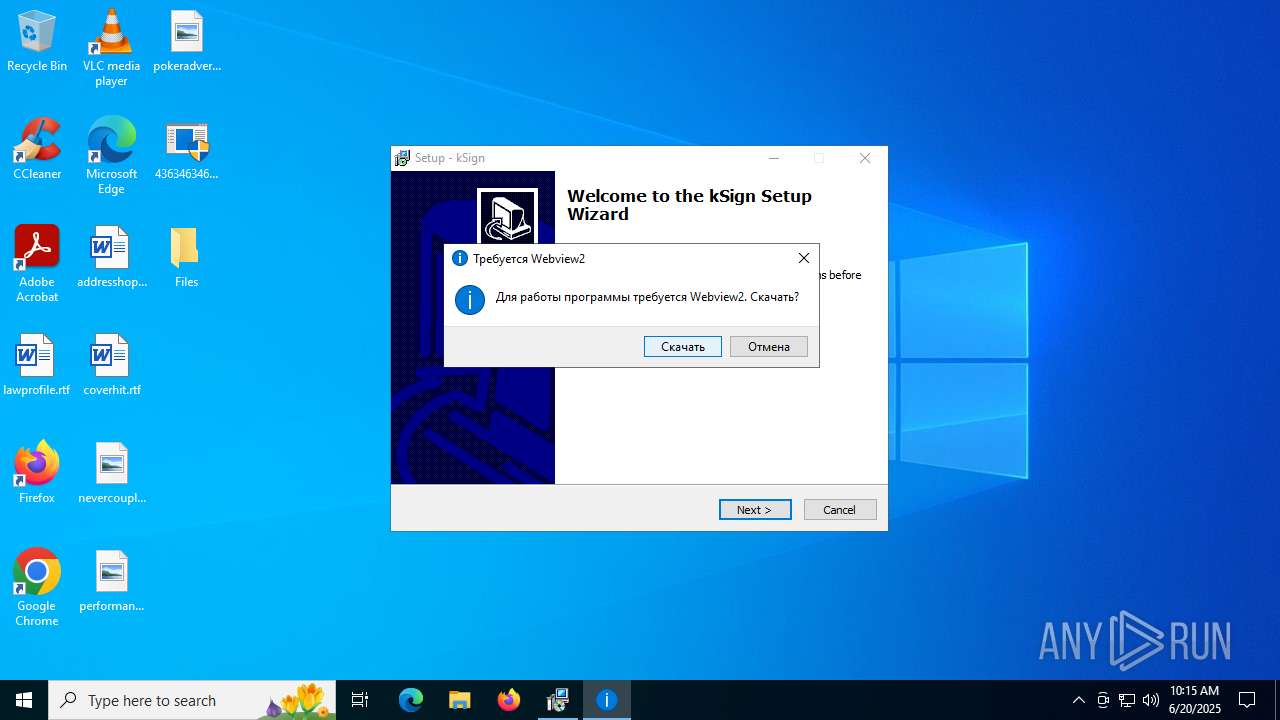
- MicrosoftEdgeWebview2Setup.exe (PID: 7340)
- svhost.exe (PID: 7560)
- XClient.exe (PID: 1192)
- barren.exe (PID: 420)
- Sentil.exe (PID: 1808)
- test.exe (PID: 7560)
- moi.exe (PID: 1800)
- fleetdeck_agent_svc.exe (PID: 2612)
- Dark_Autre_ncrypt.exe (PID: 8464)
- Terminal_9235.exe (PID: 6700)
- ClientRun.exe (PID: 8256)
- client.exe (PID: 8500)
- PCHunter64.exe (PID: 4580)
- Ganja3.exe (PID: 8404)
- Quas_Autre_ncrypt.exe (PID: 1268)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- 7zG.exe (PID: 8928)
- stealinfo.exe (PID: 8828)
- Discord.exe (PID: 6572)
- fw.exe (PID: 7824)
- 80.exe (PID: 8488)
- budiao.exe (PID: 1044)
- Synaptics.exe (PID: 8680)
- ._cache_budiao.exe (PID: 8596)
- csrss2.exe (PID: 1472)
- spoofer.exe (PID: 8404)
- dfsvc.exe (PID: 3972)
- svchocl.exe (PID: 8364)
- Destover.exe (PID: 8668)
- svchost.exe (PID: 5240)
- rmd_en_1.exe (PID: 8264)
- is-ED97J.tmp (PID: 9976)
- setup.exe (PID: 9984)
- IMG001.exe (PID: 9628)
- IMG001.exe (PID: 5712)
- FreeYoutubeDownloader.exe (PID: 1800)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 6684)
- update.exe (PID: 4172)
- moi.exe (PID: 1800)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 6684)
Contacting a server suspected of hosting an Exploit Kit
- 4363463463464363463463463.exe (PID: 6684)
Multiple wallet extension IDs have been found
- 4363463463464363463463463.exe (PID: 6684)
- S.exe (PID: 6980)
Found regular expressions for crypto-addresses (YARA)
- 4363463463464363463463463.exe (PID: 6684)
- S.exe (PID: 6980)
- bootstrapper.exe (PID: 6896)
Starts CMD.EXE for commands execution
- S.exe (PID: 6980)
- Client.exe (PID: 640)
- Client.exe (PID: 7404)
- Client.exe (PID: 1080)
- Client.exe (PID: 5240)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 7392)
- CCD-LAUNCHER.exe (PID: 7764)
- Client.exe (PID: 1512)
- moi.exe (PID: 1800)
- Client.exe (PID: 9132)
- test.exe (PID: 7560)
- Client.exe (PID: 7648)
- Dark_Autre_ncrypt.exe (PID: 8464)
- Terminal_9235.exe (PID: 6700)
- Client.exe (PID: 1508)
- injectorOld.exe (PID: 3588)
- Client.exe (PID: 8544)
- Clients.exe (PID: 8724)
- Client.exe (PID: 1268)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Clients.exe (PID: 8548)
- Client.exe (PID: 7824)
- Clients.exe (PID: 8748)
- av_downloader1.1.exe (PID: 5884)
- av_downloader1.1.exe (PID: 8148)
- cmd.exe (PID: 3704)
- Client.exe (PID: 6380)
- Clients.exe (PID: 1268)
- 80.exe (PID: 8832)
- Client.exe (PID: 8744)
- Clients.exe (PID: 6524)
- PhilipPatrol.exe (PID: 9060)
- Client.exe (PID: 2380)
- cmd.exe (PID: 9152)
- fw.exe (PID: 7824)
- Clients.exe (PID: 7600)
- svchocl.exe (PID: 8364)
- Wsystem.exe (PID: 6192)
- Client.exe (PID: 1704)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- nslookup.exe (PID: 3396)
- Clients.exe (PID: 9912)
- spoofer.exe (PID: 9652)
- Client.exe (PID: 7600)
- IMG001.exe (PID: 9628)
- Clients.exe (PID: 1332)
- Client.exe (PID: 7500)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- IMG001.exe (PID: 5712)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- Clients.exe (PID: 8996)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
Starts application with an unusual extension
- cmd.exe (PID: 3624)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 6368)
- cmd.exe (PID: 4580)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 8344)
- cmd.exe (PID: 4824)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 9044)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 9000)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 5340)
- cmd.exe (PID: 9060)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 8720)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 9152)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 6548)
- cmd.exe (PID: 9792)
- cmd.exe (PID: 10084)
- cmd.exe (PID: 10000)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 10216)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 9880)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 1704)
- cmd.exe (PID: 8992)
- cmd.exe (PID: 9604)
- cmd.exe (PID: 8648)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 10032)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 3624)
- cmd.exe (PID: 6228)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3624)
- cmd.exe (PID: 9152)
MS Edge headless start
- msedge.exe (PID: 3288)
- msedge.exe (PID: 6900)
- msedge.exe (PID: 6264)
- msedge.exe (PID: 6356)
- msedge.exe (PID: 3048)
Checks for external IP
- S.exe (PID: 6980)
- svchost.exe (PID: 2200)
- Cloudy.exe (PID: 8072)
- XClient.exe (PID: 1192)
- update.exe (PID: 4172)
- test.exe (PID: 7560)
- RegSvcs.exe (PID: 10172)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 6684)
- moi.exe (PID: 1800)
- SeetrolClient.exe (PID: 5480)
Loads DLL from Mozilla Firefox
- S.exe (PID: 6980)
Process drops legitimate windows executable
- PrivacyPolicy.tmp (PID: 504)
- BootstrapperNew.exe (PID: 7900)
- MicrosoftEdgeWebview2Setup.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- 4363463463464363463463463.exe (PID: 6684)
- client.exe (PID: 8500)
- ClientRun.exe (PID: 8256)
- 7zG.exe (PID: 8928)
- stealinfo.exe (PID: 8828)
- spoofer.exe (PID: 8404)
- Destover.exe (PID: 8668)
- is-ED97J.tmp (PID: 9976)
Connects to unusual port
- 3R%BC%BC%CA%F5.exe (PID: 7796)
- bootstrapper.exe (PID: 6896)
- RuntimeBroker.exe (PID: 7932)
- Cloudy.exe (PID: 8072)
- svhost.exe (PID: 6216)
- XClient.exe (PID: 1192)
- 4363463463464363463463463.exe (PID: 6684)
- Client1.exe (PID: 8084)
- test.exe (PID: 7560)
- Server1.exe (PID: 8812)
- Lee.exe (PID: 7948)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- powershell.exe (PID: 4500)
- Discord.exe (PID: 7488)
- 1.exe (PID: 9088)
- fw.exe (PID: 7824)
- svchocl.exe (PID: 8364)
- svchost.exe (PID: 5240)
- InstallUtil.exe (PID: 9412)
- appidcertstorecheck.exe (PID: 9448)
- DmOmaCpMo.exe (PID: 10108)
Reads the Windows owner or organization settings
- PrivacyPolicy.tmp (PID: 504)
- msiexec.exe (PID: 1052)
Starts itself from another location
- bootstrapper.exe (PID: 7820)
- Client-built.exe (PID: 7272)
- RuntimeBroker.exe (PID: 7308)
- svhost.exe (PID: 7560)
- Sentil.exe (PID: 1808)
- Dark_Autre_ncrypt.exe (PID: 8464)
- Quas_Autre_ncrypt.exe (PID: 1268)
- Ganja3.exe (PID: 8404)
- Discord.exe (PID: 6572)
- 80.exe (PID: 8488)
- IMG001.exe (PID: 9628)
Connects to SMTP port
- S.exe (PID: 6980)
Executing commands from a ".bat" file
- S.exe (PID: 6980)
- Client.exe (PID: 640)
- Client.exe (PID: 7404)
- Client.exe (PID: 1080)
- Client.exe (PID: 5240)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 7392)
- Client.exe (PID: 1512)
- Client.exe (PID: 9132)
- Client.exe (PID: 7648)
- Terminal_9235.exe (PID: 6700)
- Client.exe (PID: 1508)
- Client.exe (PID: 8544)
- Clients.exe (PID: 8724)
- Client.exe (PID: 1268)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Clients.exe (PID: 8548)
- Client.exe (PID: 7824)
- Clients.exe (PID: 8748)
- av_downloader1.1.exe (PID: 8148)
- av_downloader1.1.exe (PID: 5884)
- Client.exe (PID: 6380)
- Clients.exe (PID: 1268)
- Client.exe (PID: 8744)
- Clients.exe (PID: 6524)
- Client.exe (PID: 2380)
- fw.exe (PID: 7824)
- Clients.exe (PID: 7600)
- Client.exe (PID: 1704)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- Client.exe (PID: 7600)
- Clients.exe (PID: 1332)
- Client.exe (PID: 7500)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- Clients.exe (PID: 8996)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
Reads the date of Windows installation
- Client.exe (PID: 640)
- Client.exe (PID: 7404)
- Client.exe (PID: 1080)
- XClient.exe (PID: 1192)
- Client.exe (PID: 5240)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 7392)
- Client.exe (PID: 1512)
- test.exe (PID: 7560)
- Client.exe (PID: 9132)
- Client.exe (PID: 7648)
- Client.exe (PID: 1508)
- Client.exe (PID: 8544)
- Clients.exe (PID: 8724)
- Client.exe (PID: 1268)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Client.exe (PID: 7824)
- Clients.exe (PID: 8548)
- Clients.exe (PID: 8748)
- Client.exe (PID: 6380)
- Clients.exe (PID: 1268)
- Client.exe (PID: 8744)
- Clients.exe (PID: 6524)
- Client.exe (PID: 2380)
- Clients.exe (PID: 7600)
- Client.exe (PID: 1704)
- svchocl.exe (PID: 8364)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- Client.exe (PID: 7600)
- Clients.exe (PID: 1332)
- Client.exe (PID: 7500)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- Clients.exe (PID: 8996)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8080)
- cmd.exe (PID: 6368)
- cmd.exe (PID: 9608)
- cmd.exe (PID: 5780)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 4580)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 8344)
- cmd.exe (PID: 4824)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 9044)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 9000)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 5340)
- cmd.exe (PID: 9060)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 8720)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 6548)
- cmd.exe (PID: 9792)
- cmd.exe (PID: 10084)
- cmd.exe (PID: 10000)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 10216)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 9880)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 1704)
- cmd.exe (PID: 8992)
- cmd.exe (PID: 9604)
- cmd.exe (PID: 8648)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 10032)
- cmd.exe (PID: 1336)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8080)
- cmd.exe (PID: 6368)
- cmd.exe (PID: 7588)
The executable file from the user directory is run by the CMD process
- Client.exe (PID: 7404)
- Client.exe (PID: 1080)
- Client.exe (PID: 5240)
- Client.exe (PID: 7392)
- Client.exe (PID: 1512)
- Client.exe (PID: 9132)
- Client.exe (PID: 7648)
- Client.exe (PID: 1508)
- client.exe (PID: 7028)
- Client.exe (PID: 8544)
- Client.exe (PID: 1268)
- Client.exe (PID: 7468)
- Client.exe (PID: 7824)
- Client.exe (PID: 6380)
- Client.exe (PID: 8744)
- Client.exe (PID: 2380)
- Beverly.com (PID: 2168)
- Client.exe (PID: 1704)
- Client.exe (PID: 1984)
- Client.exe (PID: 9928)
- Client.exe (PID: 8844)
- Client.exe (PID: 7600)
- Client.exe (PID: 7500)
- Client.exe (PID: 5060)
- Client.exe (PID: 7180)
- Client.exe (PID: 5372)
- Client.exe (PID: 2876)
- Client.exe (PID: 9096)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- client.exe (PID: 8500)
- fw.exe (PID: 7824)
- Destover.exe (PID: 8668)
- rmd_en_1.exe (PID: 8264)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 4528)
The process creates files with name similar to system file names
- 4363463463464363463463463.exe (PID: 6684)
- svhost.exe (PID: 7560)
- 7zG.exe (PID: 8928)
- 80.exe (PID: 8488)
- dfsvc.exe (PID: 3972)
- cmd.exe (PID: 1752)
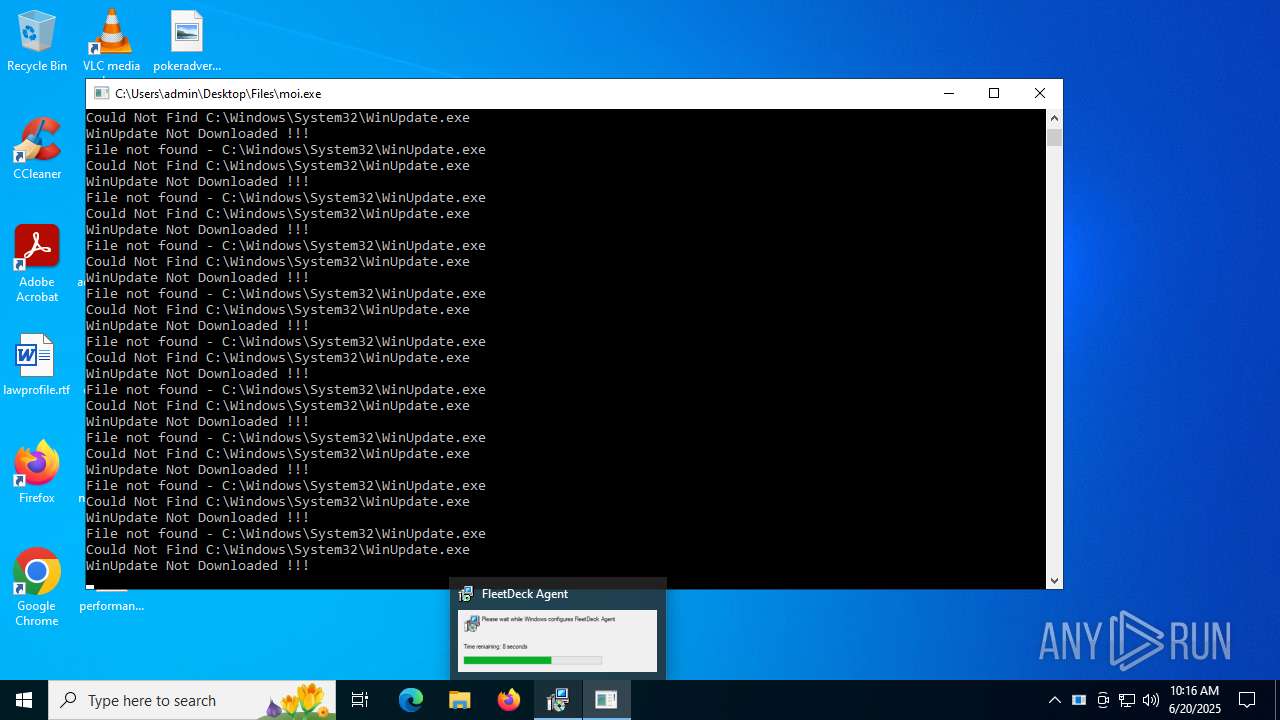
Starts POWERSHELL.EXE for commands execution
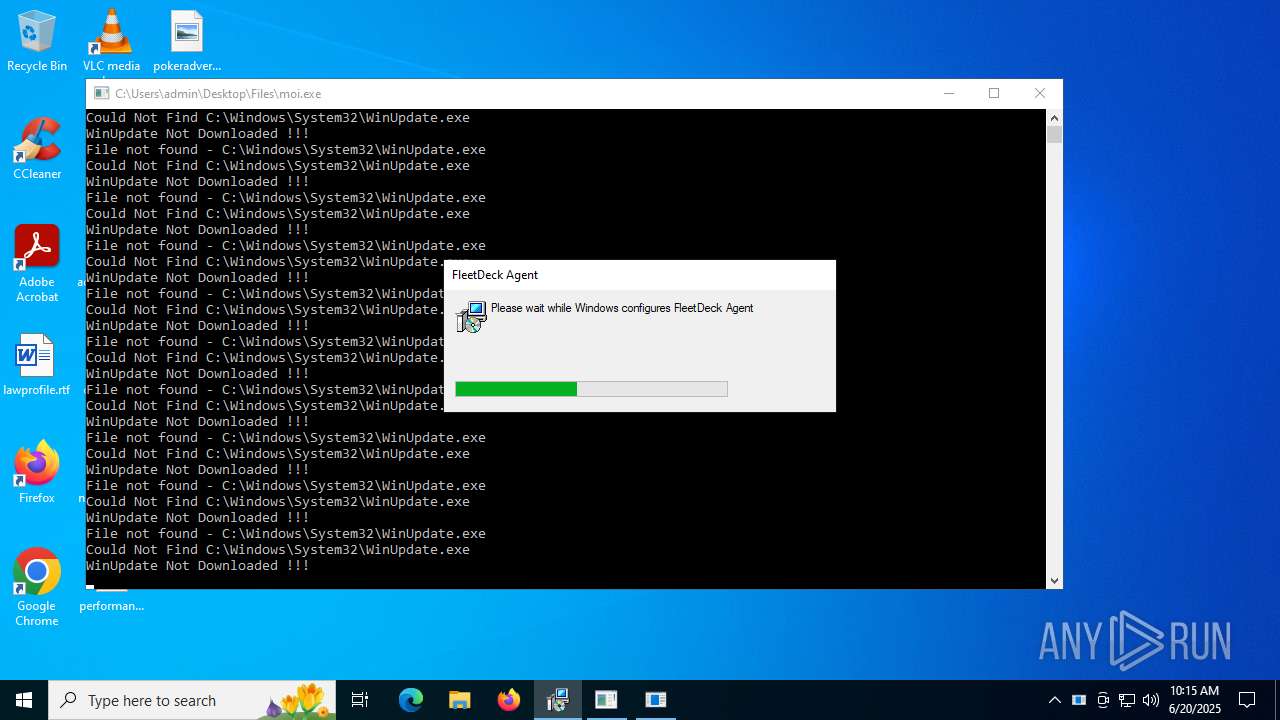
- XClient.exe (PID: 1192)
- test.exe (PID: 7560)
- fleetdeck_agent_svc.exe (PID: 8240)
- fleetdeck_agent_svc.exe (PID: 2612)
- fleetdeck_agent_svc.exe (PID: 6496)
- cmd.exe (PID: 3704)
Script adds exclusion path to Windows Defender
- XClient.exe (PID: 1192)
- test.exe (PID: 7560)
Script adds exclusion process to Windows Defender
- XClient.exe (PID: 1192)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- buildnew.exe (PID: 6160)
- RegSvcs.exe (PID: 10172)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1356)
Application launched itself
- TORRENTOLD-1.exe (PID: 7744)
- RegAsm.exe (PID: 3160)
- cmd.exe (PID: 3704)
- stealinfo.exe (PID: 8828)
- 80.exe (PID: 8832)
- cmd.exe (PID: 9152)
- Wsystem.exe (PID: 6192)
- spoofer.exe (PID: 8404)
Contacting a server suspected of hosting an CnC
- XClient.exe (PID: 1192)
- svchost.exe (PID: 2200)
- 4363463463464363463463463.exe (PID: 6684)
- nslookup.exe (PID: 3396)
Executes as Windows Service
- VSSVC.exe (PID: 2276)
- fleetdeck_agent_svc.exe (PID: 2612)
- fleetdeck_agent_svc.exe (PID: 6496)
Block-list domains
- 4363463463464363463463463.exe (PID: 6684)
- moi.exe (PID: 1800)
The process checks if it is being run in the virtual environment
- 4363463463464363463463463.exe (PID: 6684)
Starts SC.EXE for service management
- cmd.exe (PID: 8312)
- cmd.exe (PID: 8392)
- cmd.exe (PID: 8440)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8552)
- cmd.exe (PID: 8352)
Stops a currently running service
- sc.exe (PID: 8328)
- sc.exe (PID: 8368)
- sc.exe (PID: 8412)
Windows service management via SC.EXE
- sc.exe (PID: 8468)
- sc.exe (PID: 8524)
- sc.exe (PID: 8572)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 8668)
- cmd.exe (PID: 8708)
- cmd.exe (PID: 8880)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 8792)
- cmd.exe (PID: 8836)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 8728)
- cmd.exe (PID: 8592)
- cmd.exe (PID: 8756)
- cmd.exe (PID: 9000)
- cmd.exe (PID: 8924)
- cmd.exe (PID: 2612)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 6688)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 3396)
- cmd.exe (PID: 4824)
- cmd.exe (PID: 8408)
- cmd.exe (PID: 8812)
- cmd.exe (PID: 8880)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 9144)
- cmd.exe (PID: 9144)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 8340)
- cmd.exe (PID: 8424)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 8868)
- cmd.exe (PID: 8712)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 8816)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 8432)
- cmd.exe (PID: 6780)
- cmd.exe (PID: 8704)
- cmd.exe (PID: 9040)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 8560)
- cmd.exe (PID: 5252)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 8900)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 9192)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 9208)
- cmd.exe (PID: 9100)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 8356)
- cmd.exe (PID: 8572)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 7028)
- cmd.exe (PID: 1328)
- cmd.exe (PID: 4552)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 8332)
- cmd.exe (PID: 8324)
- cmd.exe (PID: 9180)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 8588)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 9140)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 3636)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 8340)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 9184)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 9004)
- cmd.exe (PID: 4748)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 8548)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 2536)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 9128)
- cmd.exe (PID: 8836)
- cmd.exe (PID: 8552)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 9160)
- cmd.exe (PID: 2132)
- cmd.exe (PID: 2460)
- cmd.exe (PID: 9204)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 8288)
- cmd.exe (PID: 4748)
- cmd.exe (PID: 1576)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 1040)
- cmd.exe (PID: 8328)
- cmd.exe (PID: 8268)
- cmd.exe (PID: 4048)
- cmd.exe (PID: 8884)
- cmd.exe (PID: 8268)
- cmd.exe (PID: 9164)
- cmd.exe (PID: 1508)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 8672)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 7436)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 8720)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 6840)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 3584)
- cmd.exe (PID: 2648)
- cmd.exe (PID: 6412)
- cmd.exe (PID: 6524)
- cmd.exe (PID: 9208)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 8796)
- cmd.exe (PID: 8812)
- cmd.exe (PID: 4748)
- cmd.exe (PID: 2864)
- cmd.exe (PID: 8776)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 9084)
- cmd.exe (PID: 1236)
- cmd.exe (PID: 3972)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 9144)
- cmd.exe (PID: 3752)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 9004)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 8756)
- cmd.exe (PID: 2064)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 8932)
- cmd.exe (PID: 9212)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 1712)
- cmd.exe (PID: 8268)
- cmd.exe (PID: 7052)
- cmd.exe (PID: 7060)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 5248)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 8416)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 8280)
- cmd.exe (PID: 6188)
- cmd.exe (PID: 8888)
- cmd.exe (PID: 3568)
- cmd.exe (PID: 3752)
- cmd.exe (PID: 3608)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 1576)
- cmd.exe (PID: 6220)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 1576)
- cmd.exe (PID: 3704)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 9028)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 8552)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 5504)
- cmd.exe (PID: 8328)
- cmd.exe (PID: 8816)
- cmd.exe (PID: 8420)
- cmd.exe (PID: 8284)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 3608)
- cmd.exe (PID: 8264)
- cmd.exe (PID: 4048)
- cmd.exe (PID: 8748)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 8804)
- cmd.exe (PID: 1236)
- cmd.exe (PID: 1508)
- cmd.exe (PID: 8364)
- cmd.exe (PID: 3488)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 3752)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 7420)
- cmd.exe (PID: 2368)
- cmd.exe (PID: 640)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 8352)
- cmd.exe (PID: 7128)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 2272)
- cmd.exe (PID: 9144)
- cmd.exe (PID: 9064)
- cmd.exe (PID: 5764)
- cmd.exe (PID: 8928)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 8492)
- cmd.exe (PID: 4680)
- cmd.exe (PID: 9088)
- cmd.exe (PID: 8728)
- cmd.exe (PID: 8796)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 3704)
There is functionality for taking screenshot (YARA)
- bootstrapper.exe (PID: 6896)
- RuntimeBroker.exe (PID: 7932)
- svhost.exe (PID: 6216)
The process received data that can be interpreted as shellcode
- XClient.exe (PID: 1192)
The process executes via Task Scheduler
- XClient.exe (PID: 8792)
- XClient.exe (PID: 8484)
- XClient.exe (PID: 10188)
- XClient.exe (PID: 2708)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 8432)
Start notepad (likely ransomware note)
- Dark_Autre_ncrypt.exe (PID: 8464)
- msdcsc.exe (PID: 8868)
Access to an unwanted program domain was detected
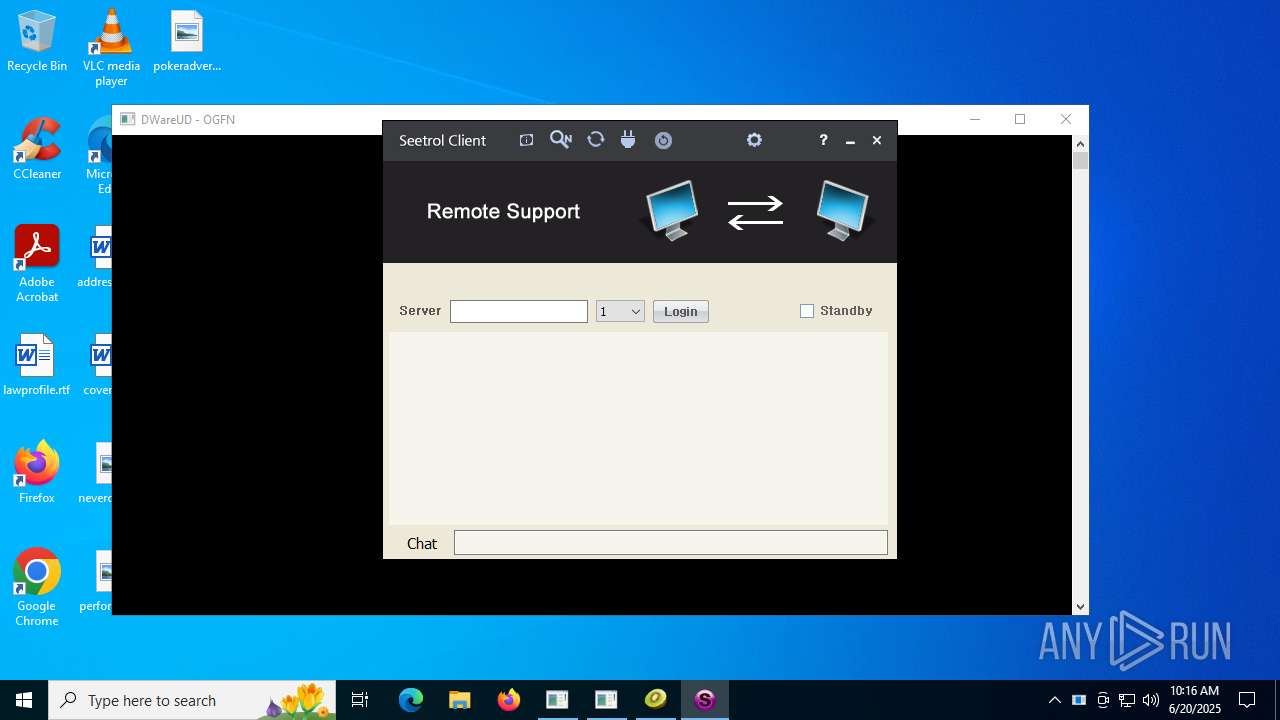
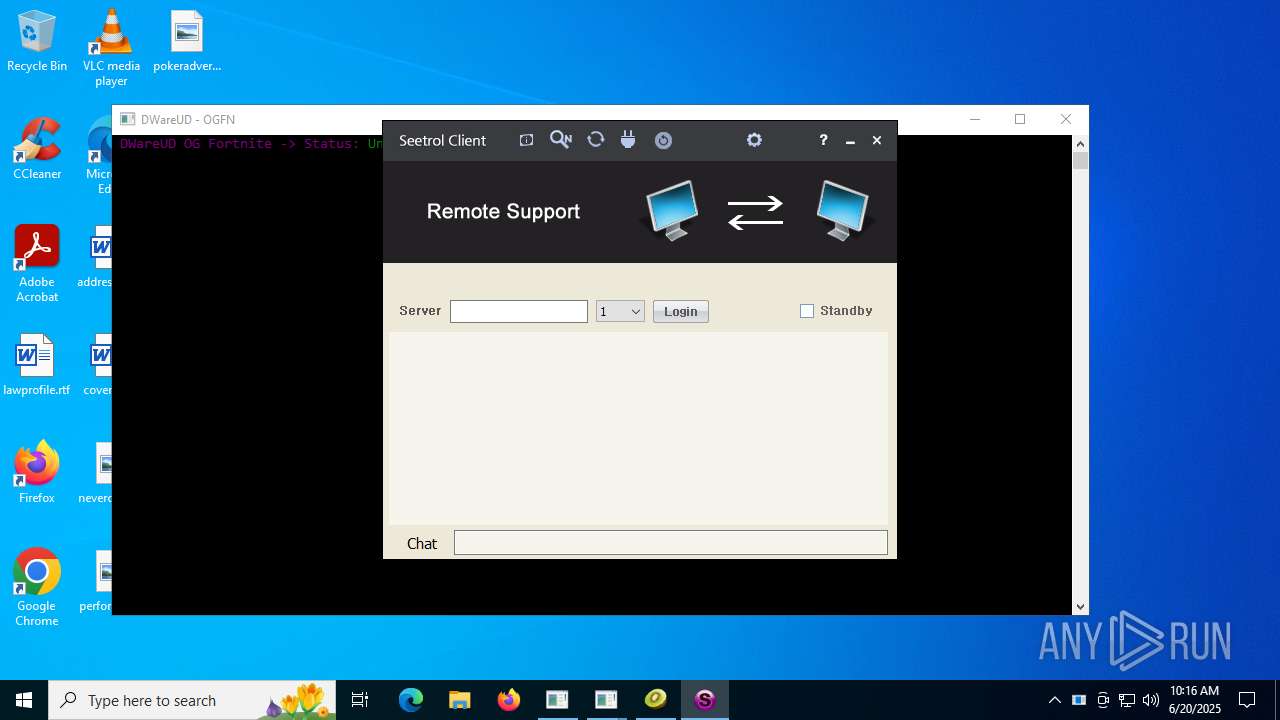
- SeetrolClient.exe (PID: 5480)
- Lee.exe (PID: 7948)
Process uses IPCONFIG to clear DNS cache
- SeetrolClient.exe (PID: 5480)
Drops a system driver (possible attempt to evade defenses)
- PCHunter64.exe (PID: 4580)
Creates or modifies Windows services
- PCHunter64.exe (PID: 4580)
Creates file in the systems drive root
- explorer.exe (PID: 4772)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Server1.exe (PID: 8812)
Drops 7-zip archiver for unpacking
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
Runs shell command (SCRIPT)
- mshta.exe (PID: 8364)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3704)
- cmd.exe (PID: 9104)
Downloads file from URI via Powershell
- powershell.exe (PID: 4500)
Found IP address in command line
- powershell.exe (PID: 4500)
The process drops C-runtime libraries
- stealinfo.exe (PID: 8828)
- spoofer.exe (PID: 8404)
Process drops python dynamic module
- stealinfo.exe (PID: 8828)
- spoofer.exe (PID: 8404)
Loads Python modules
- stealinfo.exe (PID: 9144)
- spoofer.exe (PID: 9652)
Adds/modifies Windows certificates
- support.client.exe (PID: 6128)
Identifying current user with WHOAMI command
- 1.exe (PID: 9088)
Executing commands from ".cmd" file
- PhilipPatrol.exe (PID: 9060)
Reads Internet Explorer settings
- dfsvc.exe (PID: 3972)
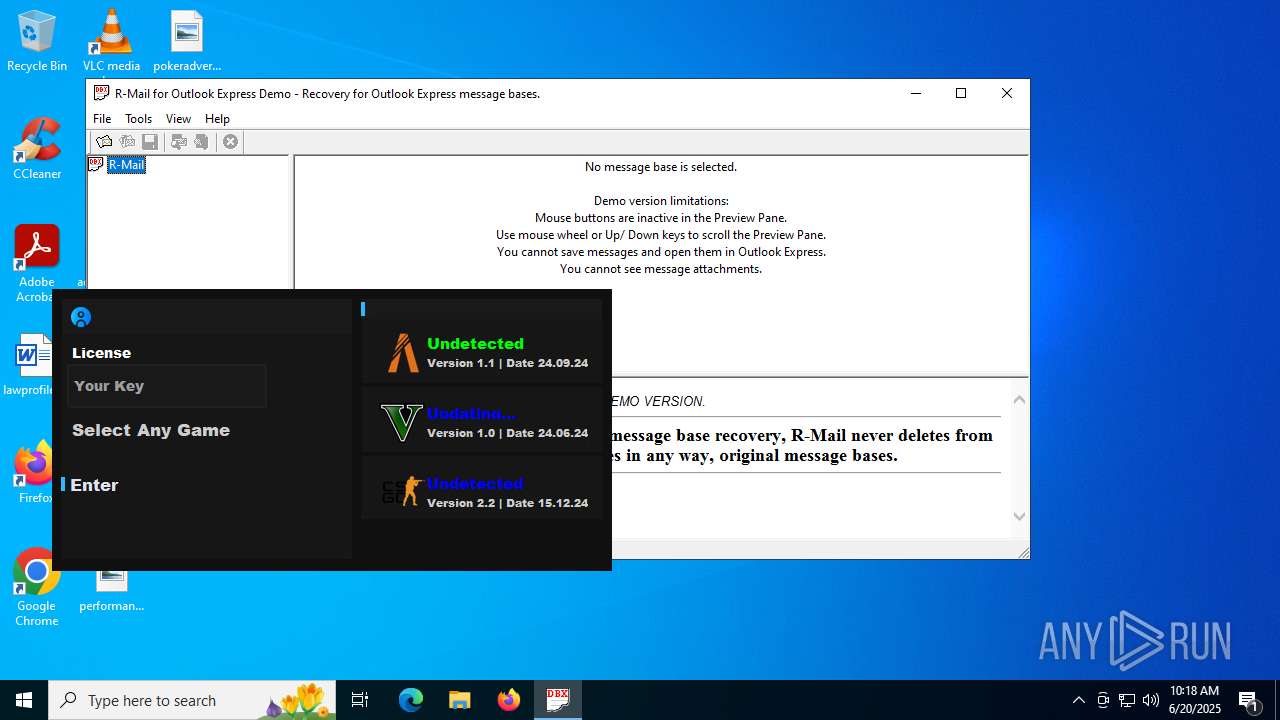
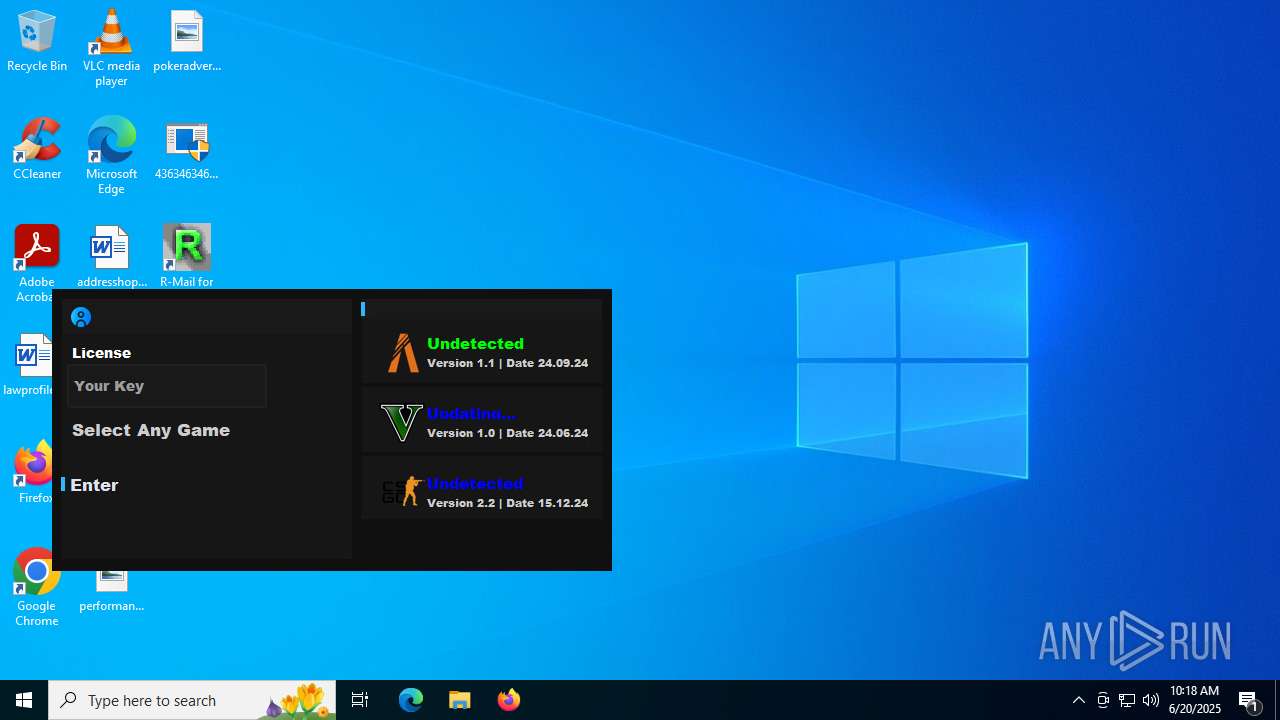
- r-mail.exe (PID: 8352)
Get information on the list of running processes
- cmd.exe (PID: 9152)
Starts the AutoIt3 executable file
- cmd.exe (PID: 9152)
Read disk information to detect sandboxing environments
- 80.exe (PID: 8488)
- Wsystem.exe (PID: 2716)
Hides command output
- cmd.exe (PID: 3956)
Found strings related to reading or modifying Windows Defender settings
- Wsystem.exe (PID: 6192)
Uses NSLOOKUP.EXE to check DNS info
- Beverly.com (PID: 2168)
Executes application which crashes
- support.client.exe (PID: 6128)
- plugmanff2.exe (PID: 4920)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 8400)
The process verifies whether the antivirus software is installed
- RegSvcs.exe (PID: 10172)
Working with threads in the GNU C Compiler (GCC) libraries related mutex has been found
- tftp.exe (PID: 8212)
- tftp.exe (PID: 8040)
Reads Microsoft Outlook installation path
- r-mail.exe (PID: 8352)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 9764)
Connects to FTP
- tftp.exe (PID: 8040)
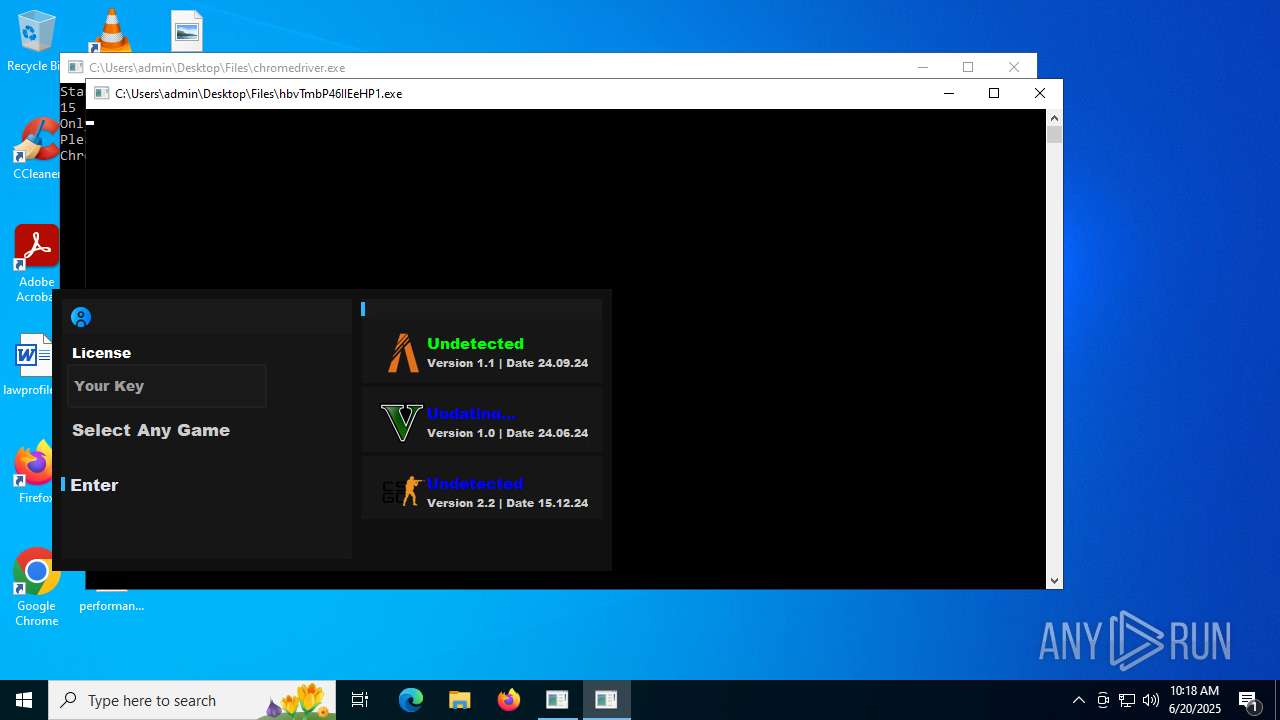
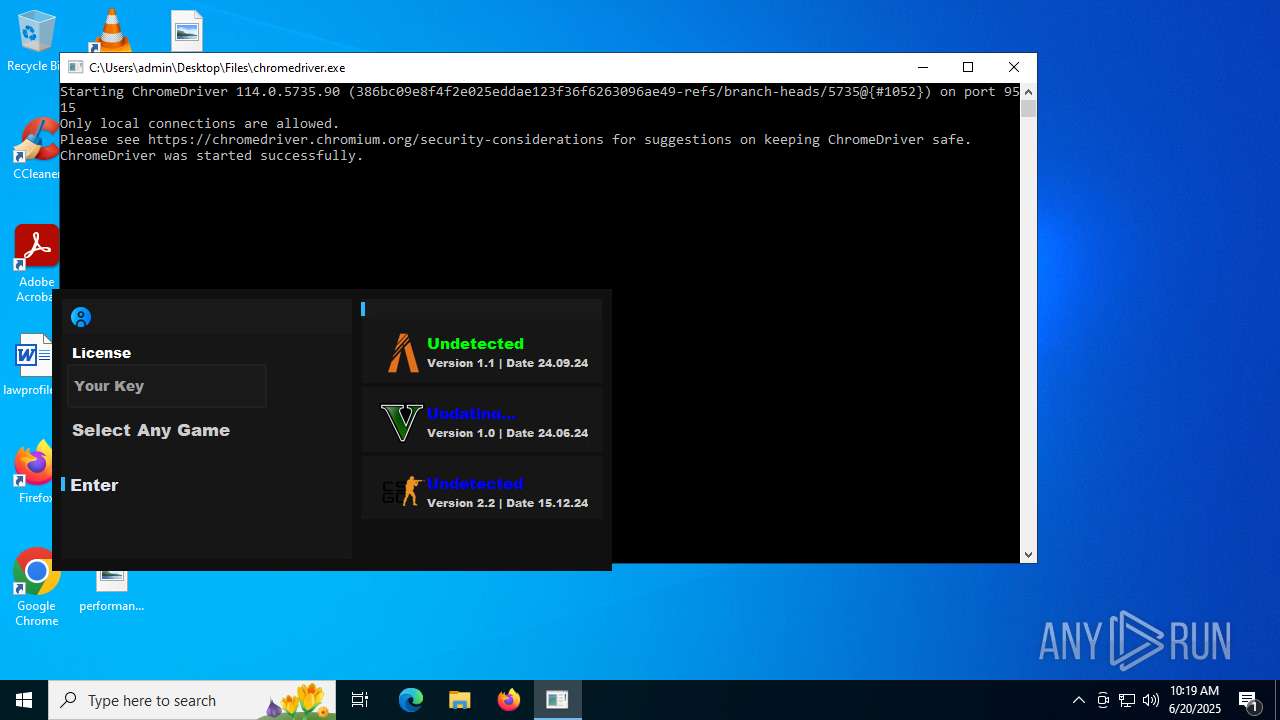
Reads the BIOS version
- hbvTmbP46IIEeHP1.exe (PID: 9572)
Creates a software uninstall entry
- FreeYoutubeDownloader.exe (PID: 1800)
INFO
Reads the computer name
- 4363463463464363463463463.exe (PID: 6684)
- S.exe (PID: 6980)
- msiexec.exe (PID: 1052)
- update.exe (PID: 4172)
- identity_helper.exe (PID: 2320)
- bootstrapper.exe (PID: 7820)
- BootstrapperNew.exe (PID: 7900)
- PrivacyPolicy.tmp (PID: 504)
- Cloudy.exe (PID: 8072)
- 3R%BC%BC%CA%F5.exe (PID: 7796)
- bootstrapper.exe (PID: 6896)
- RuntimeBroker.exe (PID: 7308)
- Client.exe (PID: 640)
- RuntimeBroker.exe (PID: 7932)
- Client.exe (PID: 7404)
- Client-built.exe (PID: 7272)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- Client.exe (PID: 1080)
- XClient.exe (PID: 1192)
- CCD-LAUNCHER.exe (PID: 7764)
- svhost.exe (PID: 7560)
- svhost.exe (PID: 6216)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 5240)
- Client.exe (PID: 7392)
- kSign.exe (PID: 7504)
- TORRENTOLD-1.exe (PID: 7744)
- TORRENTOLD-1.exe (PID: 7808)
- barren.exe (PID: 420)
- Sentil.exe (PID: 1808)
- Client1.exe (PID: 8084)
- Client.exe (PID: 1512)
- test.exe (PID: 7560)
- Chrome_boostrap.exe (PID: 8420)
- moi.exe (PID: 1800)
- msiexec.exe (PID: 9156)
- Client.exe (PID: 9132)
- fleetdeck_agent_svc.exe (PID: 8240)
- msiexec.exe (PID: 9080)
- fleetdeck_agent_svc.exe (PID: 2612)
- Client.exe (PID: 7648)
- XClient.exe (PID: 8792)
- fleetdeck_agent_svc.exe (PID: 6496)
- Dark_Autre_ncrypt.exe (PID: 8464)
- msdcsc.exe (PID: 8868)
- Terminal_9235.exe (PID: 6700)
- baboon.exe (PID: 6812)
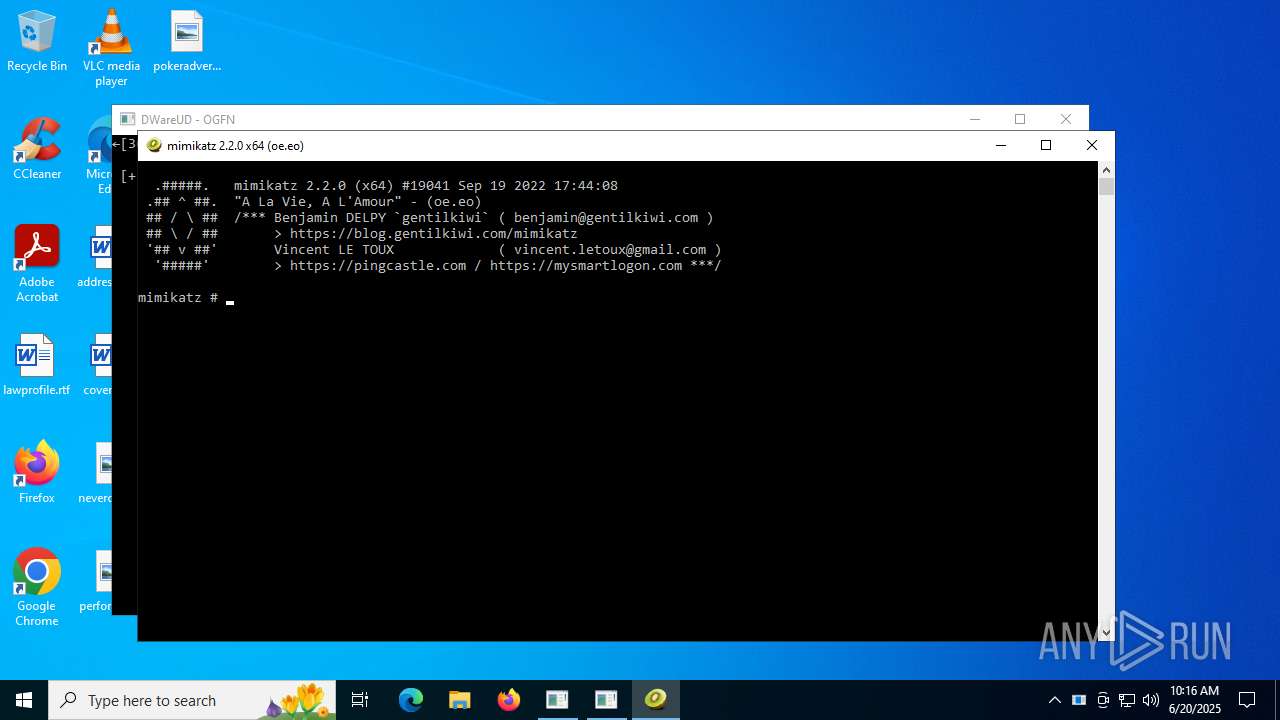
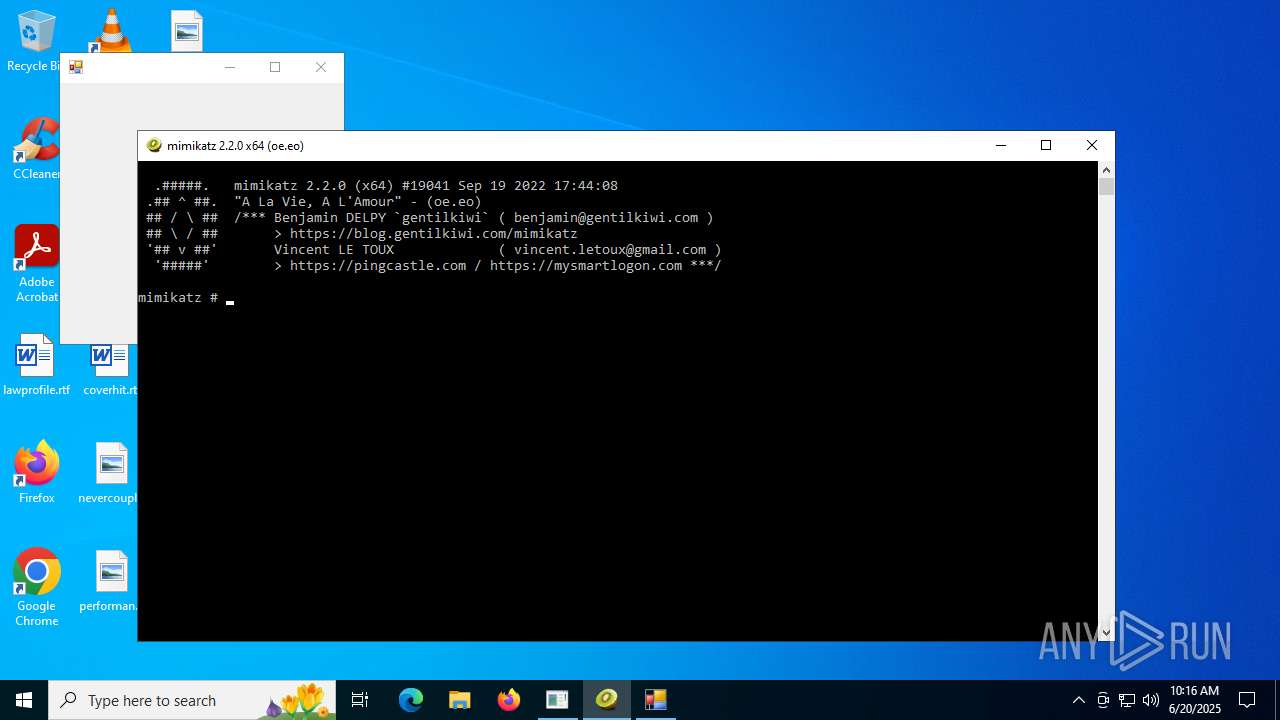
- mimikatz.exe (PID: 8588)
- Client.exe (PID: 1508)
- ClientRun.exe (PID: 8256)
- client.exe (PID: 7028)
- SeetrolClient.exe (PID: 5480)
- injectorOld.exe (PID: 3588)
- Client.exe (PID: 8544)
- PCHunter64.exe (PID: 4580)
- RegAsm.exe (PID: 3160)
- Quas_Autre_ncrypt.exe (PID: 1268)
- Clients.exe (PID: 8724)
- Ganja3.exe (PID: 8404)
- Server1.exe (PID: 8812)
- RegAsm.exe (PID: 9168)
- klass.exe (PID: 9016)
- Client.exe (PID: 1268)
- pkexU0YtxaR3.exe (PID: 7588)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Clients.exe (PID: 8548)
- Client.exe (PID: 7824)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- 7zG.exe (PID: 8928)
- Clients.exe (PID: 8748)
- XClient.exe (PID: 8484)
- av_downloader1.1.exe (PID: 8148)
- Lee.exe (PID: 7948)
- 80.exe (PID: 8832)
- av_downloader1.1.exe (PID: 5884)
- ShellExperienceHost.exe (PID: 3948)
- nwinfo.exe (PID: 8748)
- nwinfo.exe (PID: 8488)
- Client.exe (PID: 6380)
- nwinfo.exe (PID: 1268)
- stealinfo.exe (PID: 8828)
- Discord.exe (PID: 6572)
- Discord.exe (PID: 7488)
- stealinfo.exe (PID: 9144)
- Clients.exe (PID: 1268)
- Client.exe (PID: 8744)
- 1.exe (PID: 9088)
- PhilipPatrol.exe (PID: 9060)
- Clients.exe (PID: 6524)
- dfsvc.exe (PID: 3972)
- support.client.exe (PID: 6128)
- Client.exe (PID: 2380)
- mport.exe (PID: 3028)
- 80.exe (PID: 8488)
- fw.exe (PID: 7824)
- extrac32.exe (PID: 8400)
- Wsystem.exe (PID: 6192)
- Beverly.com (PID: 2168)
- Clients.exe (PID: 7600)
- budiao.exe (PID: 1044)
- Synaptics.exe (PID: 8680)
- csrss2.exe (PID: 1472)
- spoofer.exe (PID: 8404)
- Client.exe (PID: 1704)
- svchocl.exe (PID: 8364)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Wsystem.exe (PID: 2716)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- XClient.exe (PID: 10188)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- Client.exe (PID: 7600)
- spoofer.exe (PID: 9652)
- InstallUtil.exe (PID: 9412)
- rmd_en_1.exe (PID: 8264)
- IMG001.exe (PID: 9628)
- is-ED97J.tmp (PID: 9976)
- Clients.exe (PID: 1332)
- RegSvcs.exe (PID: 10172)
- Client.exe (PID: 7500)
- IMG001.exe (PID: 5712)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- r-mail.exe (PID: 8352)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- tftp.exe (PID: 8040)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
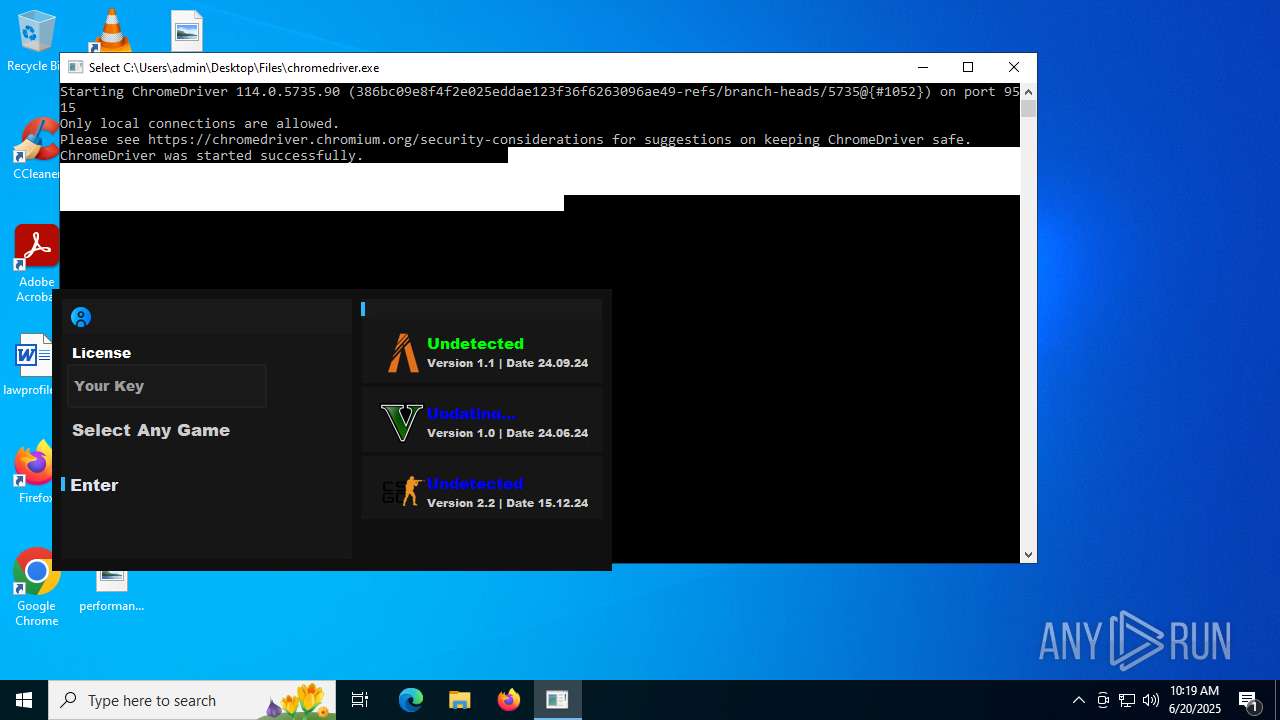
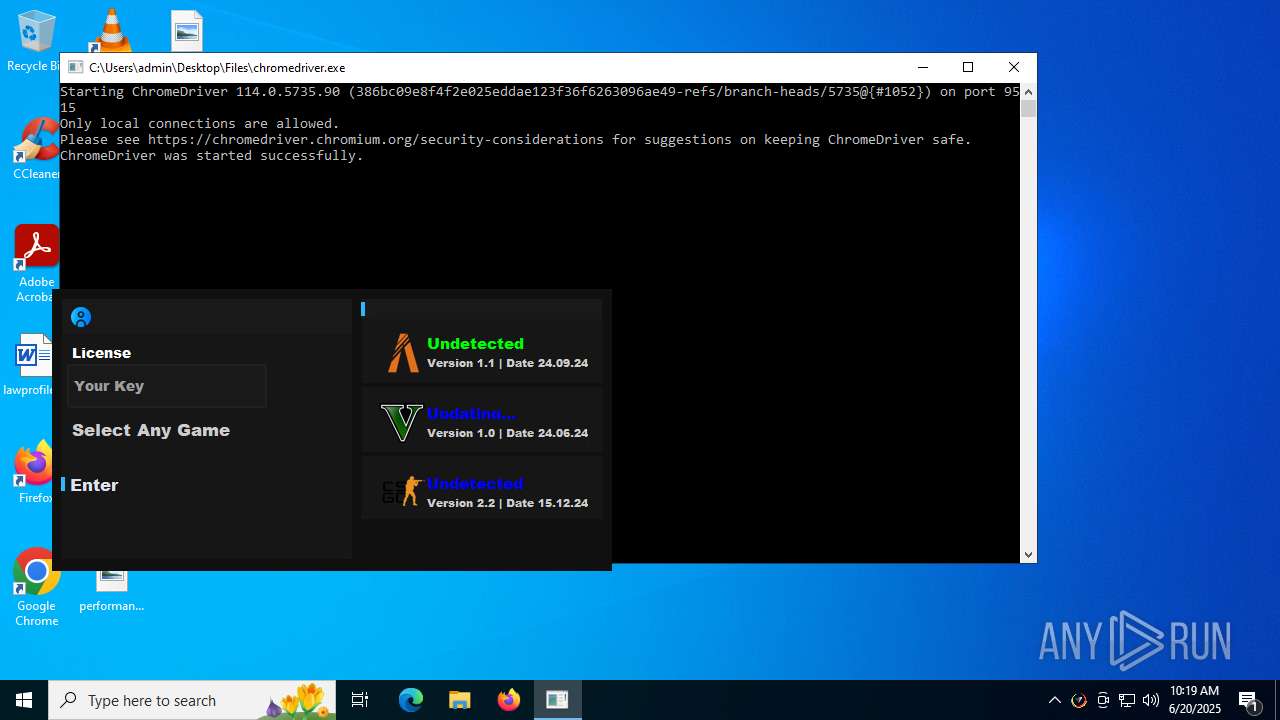
- chromedriver.exe (PID: 7184)
- XClient.exe (PID: 2708)
- Clients.exe (PID: 8996)
- FreeYoutubeDownloader.exe (PID: 1800)
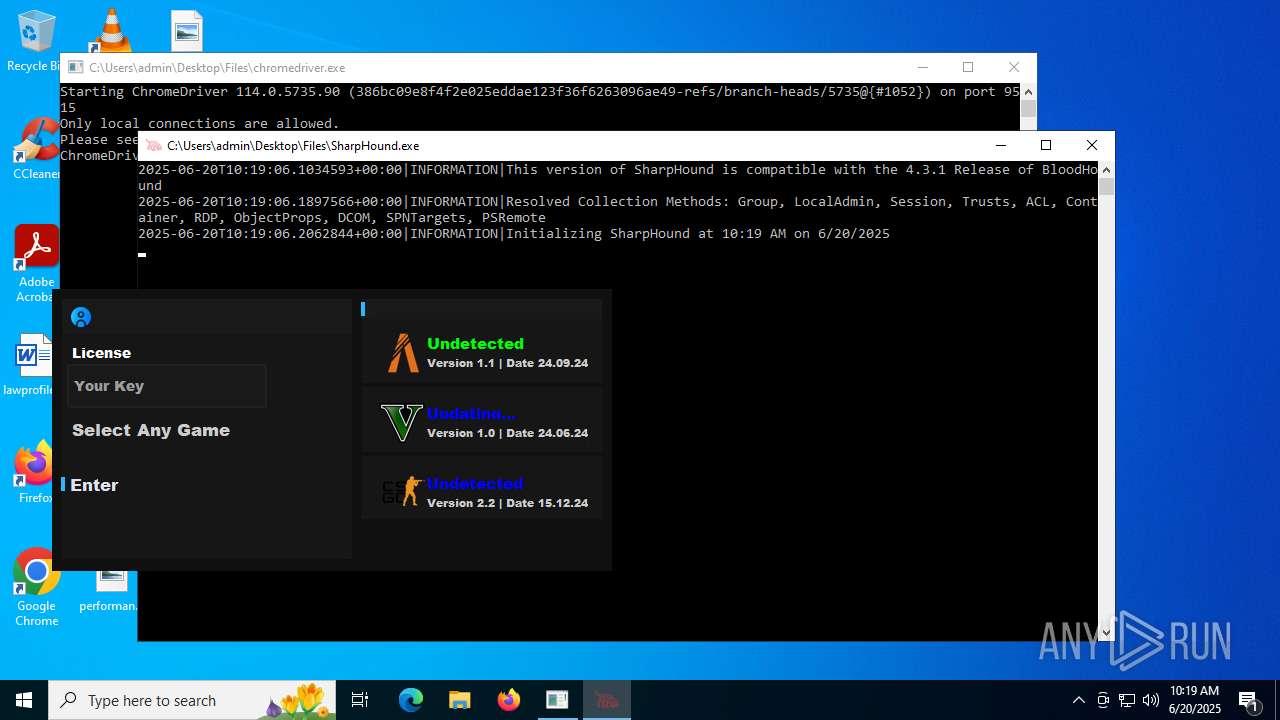
- SharpHound.exe (PID: 6732)
- Free YouTube Downloader.exe (PID: 9956)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
Disables trace logs
- 4363463463464363463463463.exe (PID: 6684)
- S.exe (PID: 6980)
- Cloudy.exe (PID: 8072)
- BootstrapperNew.exe (PID: 7900)
- XClient.exe (PID: 1192)
- buildnew.exe (PID: 6160)
- test.exe (PID: 7560)
- powershell.exe (PID: 4500)
- dfsvc.exe (PID: 3972)
- Wsystem.exe (PID: 2716)
- RegSvcs.exe (PID: 10172)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 6684)
- S.exe (PID: 6980)
- BootstrapperNew.exe (PID: 7900)
- Cloudy.exe (PID: 8072)
- bootstrapper.exe (PID: 7820)
- bootstrapper.exe (PID: 6896)
- Client-built.exe (PID: 7272)
- RuntimeBroker.exe (PID: 7308)
- Client.exe (PID: 640)
- RuntimeBroker.exe (PID: 7932)
- Client.exe (PID: 7404)
- Client.exe (PID: 1080)
- svhost.exe (PID: 7560)
- svhost.exe (PID: 6216)
- XClient.exe (PID: 1192)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 5240)
- Client.exe (PID: 7392)
- TORRENTOLD-1.exe (PID: 7744)
- Sentil.exe (PID: 1808)
- Client1.exe (PID: 8084)
- Client.exe (PID: 1512)
- test.exe (PID: 7560)
- msiexec.exe (PID: 1052)
- Client.exe (PID: 9132)
- XClient.exe (PID: 8792)
- Client.exe (PID: 7648)
- Terminal_9235.exe (PID: 6700)
- Client.exe (PID: 1508)
- client.exe (PID: 7028)
- Client.exe (PID: 8544)
- Quas_Autre_ncrypt.exe (PID: 1268)
- RegAsm.exe (PID: 3160)
- Clients.exe (PID: 8724)
- RegAsm.exe (PID: 9168)
- Client.exe (PID: 1268)
- Server1.exe (PID: 8812)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Clients.exe (PID: 8548)
- Client.exe (PID: 7824)
- XClient.exe (PID: 8484)
- Clients.exe (PID: 8748)
- Lee.exe (PID: 7948)
- Client.exe (PID: 6380)
- Discord.exe (PID: 7488)
- Discord.exe (PID: 6572)
- Clients.exe (PID: 1268)
- 80.exe (PID: 8832)
- Client.exe (PID: 8744)
- Clients.exe (PID: 6524)
- support.client.exe (PID: 6128)
- dfsvc.exe (PID: 3972)
- Client.exe (PID: 2380)
- 80.exe (PID: 8488)
- Clients.exe (PID: 7600)
- Client.exe (PID: 1704)
- Wsystem.exe (PID: 6192)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Client.exe (PID: 9928)
- Wsystem.exe (PID: 2716)
- Clients.exe (PID: 9728)
- XClient.exe (PID: 10188)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- spoofer.exe (PID: 9652)
- Client.exe (PID: 7600)
- InstallUtil.exe (PID: 9412)
- Clients.exe (PID: 1332)
- RegSvcs.exe (PID: 10172)
- Client.exe (PID: 7500)
- Synaptics.exe (PID: 8680)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- SharpHound.exe (PID: 6732)
- Clients.exe (PID: 8996)
- XClient.exe (PID: 2708)
- Free YouTube Downloader.exe (PID: 9956)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 6684)
- update.exe (PID: 4172)
- S.exe (PID: 6980)
- Cloudy.exe (PID: 8072)
- BootstrapperNew.exe (PID: 7900)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- wermgr.exe (PID: 1328)
- XClient.exe (PID: 1192)
- buildnew.exe (PID: 6160)
- test.exe (PID: 7560)
- baboon.exe (PID: 6812)
- slui.exe (PID: 7352)
- SeetrolClient.exe (PID: 5480)
- Lee.exe (PID: 7948)
- mshta.exe (PID: 8364)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- powershell.exe (PID: 4500)
- stealinfo.exe (PID: 9144)
- dfsvc.exe (PID: 3972)
- Synaptics.exe (PID: 8680)
- explorer.exe (PID: 4772)
- WerFault.exe (PID: 9676)
- Wsystem.exe (PID: 2716)
- spoofer.exe (PID: 9652)
- RegSvcs.exe (PID: 10172)
- WerFault.exe (PID: 5132)
- r-mail.exe (PID: 8352)
- tftp.exe (PID: 8040)
Checks supported languages
- 4363463463464363463463463.exe (PID: 6684)
- S.exe (PID: 6980)
- chcp.com (PID: 5348)
- msiexec.exe (PID: 1052)
- chcp.com (PID: 4768)
- update.exe (PID: 4172)
- identity_helper.exe (PID: 2320)
- bootstrapper.exe (PID: 7820)
- 3R%BC%BC%CA%F5.exe (PID: 7796)
- PrivacyPolicy.exe (PID: 7868)
- BootstrapperNew.exe (PID: 7900)
- PrivacyPolicy.tmp (PID: 504)
- Cloudy.exe (PID: 8072)
- bootstrapper.exe (PID: 6896)
- Client-built.exe (PID: 7272)
- RuntimeBroker.exe (PID: 7308)
- Client.exe (PID: 640)
- chcp.com (PID: 6472)
- RuntimeBroker.exe (PID: 7932)
- chcp.com (PID: 7716)
- Client.exe (PID: 7404)
- chcp.com (PID: 8084)
- MicrosoftEdgeWebview2Setup.exe (PID: 7340)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- Client.exe (PID: 1080)
- XClient.exe (PID: 1192)
- CCD-LAUNCHER.exe (PID: 7764)
- svhost.exe (PID: 7560)
- svhost.exe (PID: 6216)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 5240)
- chcp.com (PID: 3760)
- chcp.com (PID: 7744)
- chcp.com (PID: 6776)
- Client.exe (PID: 7392)
- chcp.com (PID: 7376)
- kSign.exe (PID: 7504)
- solsniper.exe (PID: 6960)
- TORRENTOLD-1.exe (PID: 7744)
- TORRENTOLD-1.exe (PID: 7808)
- barren.exe (PID: 420)
- Sentil.exe (PID: 1808)
- moi.exe (PID: 1800)
- Client1.exe (PID: 8084)
- Client.exe (PID: 1512)
- lvjs.exe (PID: 1080)
- test.exe (PID: 7560)
- chcp.com (PID: 7228)
- Chrome_boostrap.exe (PID: 8420)
- Client.exe (PID: 9132)
- fleetdeck_agent_svc.exe (PID: 8240)
- msiexec.exe (PID: 9156)
- chcp.com (PID: 8388)
- XClient.exe (PID: 8792)
- msiexec.exe (PID: 9080)
- Client.exe (PID: 7648)
- fleetdeck_agent_svc.exe (PID: 2612)
- chcp.com (PID: 5768)
- fleetdeck_agent_svc.exe (PID: 6496)
- Dark_Autre_ncrypt.exe (PID: 8464)
- fmt_01.exe (PID: 8252)
- shell.exe (PID: 7484)
- msdcsc.exe (PID: 8868)
- Terminal_9235.exe (PID: 6700)
- injectorOld.exe (PID: 3588)
- mimikatz.exe (PID: 8588)
- baboon.exe (PID: 6812)
- Client.exe (PID: 1508)
- chcp.com (PID: 7052)
- client.exe (PID: 8500)
- client.exe (PID: 7028)
- ClientRun.exe (PID: 8256)
- SeetrolClient.exe (PID: 5480)
- Client.exe (PID: 8544)
- PCHunter64.exe (PID: 4580)
- chcp.com (PID: 8668)
- RambledMime.exe (PID: 8252)
- RegAsm.exe (PID: 3160)
- Quas_Autre_ncrypt.exe (PID: 1268)
- Clients.exe (PID: 8724)
- Ganja3.exe (PID: 8404)
- klass.exe (PID: 9016)
- Server1.exe (PID: 8812)
- chcp.com (PID: 8120)
- RegAsm.exe (PID: 9168)
- Client.exe (PID: 1268)
- pkexU0YtxaR3.exe (PID: 7588)
- chcp.com (PID: 6412)
- Clients.exe (PID: 8928)
- chcp.com (PID: 8252)
- Client.exe (PID: 7468)
- chcp.com (PID: 8580)
- Clients.exe (PID: 8548)
- Client.exe (PID: 7824)
- chcp.com (PID: 8516)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- 7zG.exe (PID: 8928)
- chcp.com (PID: 7408)
- Lee.exe (PID: 7948)
- Clients.exe (PID: 8748)
- XClient.exe (PID: 8484)
- chcp.com (PID: 9100)
- av_downloader1.1.exe (PID: 8148)
- av_downloader1.1.exe (PID: 5884)
- 80.exe (PID: 8832)
- ShellExperienceHost.exe (PID: 3948)
- nwinfo.exe (PID: 8748)
- nwinfo.exe (PID: 1268)
- nwinfo.exe (PID: 8488)
- stealinfo.exe (PID: 8828)
- Client.exe (PID: 6380)
- Discord.exe (PID: 6572)
- chcp.com (PID: 2168)
- Discord.exe (PID: 7488)
- Clients.exe (PID: 1268)
- stealinfo.exe (PID: 9144)
- chcp.com (PID: 2076)
- Client.exe (PID: 8744)
- chcp.com (PID: 8532)
- PhilipPatrol.exe (PID: 9060)
- 1.exe (PID: 9088)
- Clients.exe (PID: 6524)
- dfsvc.exe (PID: 3972)
- chcp.com (PID: 8356)
- support.client.exe (PID: 6128)
- mport.exe (PID: 3028)
- Client.exe (PID: 2380)
- 80.exe (PID: 8488)
- fw.exe (PID: 7824)
- chcp.com (PID: 9080)
- Beverly.com (PID: 2168)
- extrac32.exe (PID: 8400)
- Wsystem.exe (PID: 6192)
- svchocl.exe (PID: 8364)
- budiao.exe (PID: 1044)
- ._cache_budiao.exe (PID: 8596)
- Clients.exe (PID: 7600)
- csrss2.exe (PID: 1472)
- Synaptics.exe (PID: 8680)
- chcp.com (PID: 3488)
- spoofer.exe (PID: 8404)
- Client.exe (PID: 1704)
- winsetaccess64.exe (PID: 5140)
- chcp.com (PID: 2040)
- chcp.com (PID: 9132)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- chcp.com (PID: 7576)
- Wsystem.exe (PID: 2716)
- Client.exe (PID: 9928)
- chcp.com (PID: 9844)
- XClient.exe (PID: 10188)
- celkadrobitel.exe (PID: 10044)
- chcp.com (PID: 10136)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- chcp.com (PID: 9948)
- chcp.com (PID: 9824)
- Clients.exe (PID: 9912)
- chcp.com (PID: 5132)
- spoofer.exe (PID: 9652)
- Client.exe (PID: 7600)
- Destover.exe (PID: 8668)
- cock.exe (PID: 7500)
- InstallUtil.exe (PID: 9412)
- chcp.com (PID: 8380)
- rmd_en_1.exe (PID: 8264)
- IMG001.exe (PID: 9628)
- Clients.exe (PID: 1332)
- plugmanff2.exe (PID: 4920)
- setup.exe (PID: 9984)
- is-ED97J.tmp (PID: 9976)
- RegSvcs.exe (PID: 10172)
- chcp.com (PID: 3752)
- chcp.com (PID: 8000)
- Client.exe (PID: 7500)
- tftp.exe (PID: 8212)
- Clients.exe (PID: 7116)
- chcp.com (PID: 1136)
- IMG001.exe (PID: 5712)
- Client.exe (PID: 5060)
- r-mail.exe (PID: 8352)
- tftp.exe (PID: 8040)
- Clients.exe (PID: 1236)
- chcp.com (PID: 7512)
- chcp.com (PID: 8060)
- Client.exe (PID: 7180)
- chcp.com (PID: 7684)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- chromedriver.exe (PID: 7184)
- chcp.com (PID: 436)
- hbvTmbP46IIEeHP1.exe (PID: 9572)
- XClient.exe (PID: 2708)
- chcp.com (PID: 3980)
- FreeYoutubeDownloader.exe (PID: 1800)
- Clients.exe (PID: 8996)
- SharpHound.exe (PID: 6732)
- chcp.com (PID: 9732)
- Free YouTube Downloader.exe (PID: 9956)
- Client.exe (PID: 2876)
- chcp.com (PID: 9404)
- chcp.com (PID: 4984)
- Clients.exe (PID: 7432)
- chcp.com (PID: 8824)
- Client.exe (PID: 9096)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 6684)
- S.exe (PID: 6980)
- Client.exe (PID: 640)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- Client.exe (PID: 1080)
- XClient.exe (PID: 1192)
- Client.exe (PID: 7404)
- Client.exe (PID: 5240)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 7392)
- Client.exe (PID: 1512)
- test.exe (PID: 7560)
- Client.exe (PID: 9132)
- Client.exe (PID: 7648)
- Dark_Autre_ncrypt.exe (PID: 8464)
- Terminal_9235.exe (PID: 6700)
- Client.exe (PID: 1508)
- ClientRun.exe (PID: 8256)
- SeetrolClient.exe (PID: 5480)
- Client.exe (PID: 8544)
- Clients.exe (PID: 8724)
- Client.exe (PID: 1268)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Clients.exe (PID: 8548)
- Client.exe (PID: 7824)
- Clients.exe (PID: 8748)
- av_downloader1.1.exe (PID: 5884)
- av_downloader1.1.exe (PID: 8148)
- Client.exe (PID: 6380)
- 80.exe (PID: 8832)
- Clients.exe (PID: 1268)
- Client.exe (PID: 8744)
- Clients.exe (PID: 6524)
- PhilipPatrol.exe (PID: 9060)
- Client.exe (PID: 2380)
- 80.exe (PID: 8488)
- budiao.exe (PID: 1044)
- Clients.exe (PID: 7600)
- Client.exe (PID: 1704)
- Wsystem.exe (PID: 6192)
- svchocl.exe (PID: 8364)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- Client.exe (PID: 7600)
- IMG001.exe (PID: 9628)
- Clients.exe (PID: 1332)
- Client.exe (PID: 7500)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- IMG001.exe (PID: 5712)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- Clients.exe (PID: 8996)
- FreeYoutubeDownloader.exe (PID: 1800)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 4932)
- cmd.exe (PID: 3704)
- WMIC.exe (PID: 3540)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 6684)
- bootstrapper.exe (PID: 6896)
- BootstrapperNew.exe (PID: 7900)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- wermgr.exe (PID: 1328)
- buildnew.exe (PID: 6160)
- TORRENTOLD-1.exe (PID: 7808)
- msiexec.exe (PID: 1052)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 4932)
- powershell.exe (PID: 7340)
- powershell.exe (PID: 8432)
- slui.exe (PID: 7352)
- dfsvc.exe (PID: 3972)
- WerFault.exe (PID: 9676)
- Wsystem.exe (PID: 2716)
- explorer.exe (PID: 4772)
- WerFault.exe (PID: 5132)
- RegSvcs.exe (PID: 10172)
- Synaptics.exe (PID: 8680)
The sample compiled with chinese language support
- 4363463463464363463463463.exe (PID: 6684)
- 7zG.exe (PID: 8928)
Creates files or folders in the user directory
- S.exe (PID: 6980)
- bootstrapper.exe (PID: 7820)
- Client-built.exe (PID: 7272)
- Cloudy.exe (PID: 8072)
- explorer.exe (PID: 4772)
- wermgr.exe (PID: 1328)
- svhost.exe (PID: 7560)
- XClient.exe (PID: 1192)
- Sentil.exe (PID: 1808)
- msiexec.exe (PID: 1052)
- RuntimeBroker.exe (PID: 7932)
- Terminal_9235.exe (PID: 6700)
- Server1.exe (PID: 8812)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- dfsvc.exe (PID: 3972)
- 80.exe (PID: 8488)
- WerFault.exe (PID: 9676)
- Discord.exe (PID: 7488)
- WerFault.exe (PID: 5132)
- IMG001.exe (PID: 9628)
- Synaptics.exe (PID: 8680)
- r-mail.exe (PID: 8352)
- IMG001.exe (PID: 5712)
Changes the display of characters in the console
- cmd.exe (PID: 3624)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 6368)
- cmd.exe (PID: 4580)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 8344)
- cmd.exe (PID: 4824)
- cmd.exe (PID: 9032)
- cmd.exe (PID: 9044)
- cmd.exe (PID: 6612)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 9000)
- cmd.exe (PID: 8500)
- cmd.exe (PID: 5340)
- cmd.exe (PID: 9060)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 8720)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 4036)
- cmd.exe (PID: 9112)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 6548)
- cmd.exe (PID: 9792)
- cmd.exe (PID: 10084)
- cmd.exe (PID: 10000)
- cmd.exe (PID: 8292)
- cmd.exe (PID: 10216)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 9880)
- cmd.exe (PID: 3028)
- cmd.exe (PID: 6656)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 1704)
- cmd.exe (PID: 8992)
- cmd.exe (PID: 9604)
- cmd.exe (PID: 8648)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 3628)
- cmd.exe (PID: 1336)
- cmd.exe (PID: 10032)
Application launched itself
- msedge.exe (PID: 3288)
- msedge.exe (PID: 6900)
- msedge.exe (PID: 3048)
- msedge.exe (PID: 7760)
Create files in a temporary directory
- S.exe (PID: 6980)
- PrivacyPolicy.exe (PID: 7868)
- PrivacyPolicy.tmp (PID: 504)
- Client.exe (PID: 640)
- Client.exe (PID: 7404)
- BootstrapperNew.exe (PID: 7900)
- Client.exe (PID: 1080)
- Client.exe (PID: 5240)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 7392)
- barren.exe (PID: 420)
- Client.exe (PID: 1512)
- XClient.exe (PID: 1192)
- Client.exe (PID: 9132)
- Client.exe (PID: 7648)
- Terminal_9235.exe (PID: 6700)
- Client.exe (PID: 1508)
- client.exe (PID: 8500)
- Client.exe (PID: 8544)
- Server1.exe (PID: 8812)
- Clients.exe (PID: 8724)
- Client.exe (PID: 1268)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Clients.exe (PID: 8548)
- Client.exe (PID: 7824)
- 7zG.exe (PID: 8928)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- av_downloader1.1.exe (PID: 8148)
- Clients.exe (PID: 8748)
- av_downloader1.1.exe (PID: 5884)
- stealinfo.exe (PID: 8828)
- Client.exe (PID: 6380)
- stealinfo.exe (PID: 9144)
- Clients.exe (PID: 1268)
- Client.exe (PID: 8744)
- Clients.exe (PID: 6524)
- PhilipPatrol.exe (PID: 9060)
- dfsvc.exe (PID: 3972)
- Client.exe (PID: 2380)
- extrac32.exe (PID: 8400)
- Clients.exe (PID: 7600)
- Synaptics.exe (PID: 8680)
- ._cache_budiao.exe (PID: 8596)
- spoofer.exe (PID: 8404)
- Client.exe (PID: 1704)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- Client.exe (PID: 7600)
- rmd_en_1.exe (PID: 8264)
- is-ED97J.tmp (PID: 9976)
- plugmanff2.exe (PID: 4920)
- setup.exe (PID: 9984)
- Clients.exe (PID: 1332)
- IMG001.exe (PID: 9628)
- Client.exe (PID: 7500)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- IMG001.exe (PID: 5712)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- FreeYoutubeDownloader.exe (PID: 1800)
- Clients.exe (PID: 8996)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
Manual execution by a user
- msedge.exe (PID: 3048)
- appidcertstorecheck.exe (PID: 9448)
- DmOmaCpMo.exe (PID: 10108)
Reads Environment values
- identity_helper.exe (PID: 2320)
- bootstrapper.exe (PID: 7820)
- bootstrapper.exe (PID: 6896)
- RuntimeBroker.exe (PID: 7308)
- Client-built.exe (PID: 7272)
- Client.exe (PID: 640)
- RuntimeBroker.exe (PID: 7932)
- Cloudy.exe (PID: 8072)
- Client.exe (PID: 7404)
- BootstrapperNew.exe (PID: 7900)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- Client.exe (PID: 1080)
- svhost.exe (PID: 7560)
- svhost.exe (PID: 6216)
- XClient.exe (PID: 1192)
- buildnew.exe (PID: 6160)
- Client.exe (PID: 5240)
- Client.exe (PID: 7392)
- Sentil.exe (PID: 1808)
- Client1.exe (PID: 8084)
- Client.exe (PID: 1512)
- Client.exe (PID: 9132)
- test.exe (PID: 7560)
- Client.exe (PID: 7648)
- Client.exe (PID: 1508)
- Client.exe (PID: 8544)
- Quas_Autre_ncrypt.exe (PID: 1268)
- Clients.exe (PID: 8724)
- PCHunter64.exe (PID: 4580)
- Client.exe (PID: 1268)
- Clients.exe (PID: 8928)
- Client.exe (PID: 7468)
- Clients.exe (PID: 8548)
- Client.exe (PID: 7824)
- Clients.exe (PID: 8748)
- Client.exe (PID: 6380)
- Discord.exe (PID: 6572)
- Discord.exe (PID: 7488)
- Clients.exe (PID: 1268)
- Client.exe (PID: 8744)
- Clients.exe (PID: 6524)
- dfsvc.exe (PID: 3972)
- Client.exe (PID: 2380)
- Clients.exe (PID: 7600)
- Client.exe (PID: 1704)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Client.exe (PID: 9928)
- Clients.exe (PID: 9728)
- Client.exe (PID: 8844)
- Clients.exe (PID: 9912)
- Client.exe (PID: 7600)
- Clients.exe (PID: 1332)
- Client.exe (PID: 7500)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
- Clients.exe (PID: 1236)
- Client.exe (PID: 7180)
- Clients.exe (PID: 10044)
- Client.exe (PID: 5372)
- Clients.exe (PID: 8996)
- Client.exe (PID: 2876)
- Clients.exe (PID: 7432)
- Client.exe (PID: 9096)
The sample compiled with english language support
- 3R%BC%BC%CA%F5.exe (PID: 7796)
- PrivacyPolicy.tmp (PID: 504)
- BootstrapperNew.exe (PID: 7900)
- MicrosoftEdgeUpdate.exe (PID: 4528)
- MicrosoftEdgeWebview2Setup.exe (PID: 7340)
- moi.exe (PID: 1800)
- 4363463463464363463463463.exe (PID: 6684)
- Dark_Autre_ncrypt.exe (PID: 8464)
- client.exe (PID: 8500)
- ClientRun.exe (PID: 8256)
- PCHunter64.exe (PID: 4580)
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- 7zG.exe (PID: 8928)
- stealinfo.exe (PID: 8828)
- spoofer.exe (PID: 8404)
- Destover.exe (PID: 8668)
- rmd_en_1.exe (PID: 8264)
- is-ED97J.tmp (PID: 9976)
- setup.exe (PID: 9984)
- svchost.exe (PID: 5240)
Reads CPU info
- S.exe (PID: 6980)
- test.exe (PID: 7560)
- nwinfo.exe (PID: 8748)
Creates files in the program directory
- BootstrapperNew.exe (PID: 7900)
- MicrosoftEdgeWebview2Setup.exe (PID: 7340)
- PrivacyPolicy.tmp (PID: 504)
- test.exe (PID: 7560)
- fleetdeck_agent_svc.exe (PID: 8240)
- fleetdeck_agent_svc.exe (PID: 2612)
- ClientRun.exe (PID: 8256)
- SeetrolClient.exe (PID: 5480)
- Ganja3.exe (PID: 8404)
- Quas_Autre_ncrypt.exe (PID: 1268)
- Discord.exe (PID: 6572)
- budiao.exe (PID: 1044)
- Synaptics.exe (PID: 8680)
- is-ED97J.tmp (PID: 9976)
- SharpHound.exe (PID: 6732)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- RuntimeBroker.exe (PID: 7308)
- Client.exe (PID: 640)
- Client.exe (PID: 1508)
- cmd.exe (PID: 1812)
- Clients.exe (PID: 8724)
- Client.exe (PID: 1268)
- Client.exe (PID: 7824)
- Discord.exe (PID: 6572)
- Clients.exe (PID: 1268)
- Clients.exe (PID: 6524)
- 80.exe (PID: 8488)
- Clients.exe (PID: 7600)
- Clients.exe (PID: 6412)
- Client.exe (PID: 1984)
- Clients.exe (PID: 9664)
- Clients.exe (PID: 7116)
- Client.exe (PID: 5060)
Launching a file from the Startup directory
- Cloudy.exe (PID: 8072)
- IMG001.exe (PID: 5712)
Checks if a key exists in the options dictionary (POWERSHELL)
- BootstrapperNew.exe (PID: 7900)
- powershell.exe (PID: 7548)
- powershell.exe (PID: 8104)
- powershell.exe (PID: 8032)
- powershell.exe (PID: 7488)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 5008)
- powershell.exe (PID: 4932)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7548)
- powershell.exe (PID: 8104)
- powershell.exe (PID: 8032)
- powershell.exe (PID: 7488)
- powershell.exe (PID: 7828)
- powershell.exe (PID: 8432)
- powershell.exe (PID: 4500)
Compiled with Borland Delphi (YARA)
- PrivacyPolicy.tmp (PID: 504)
- bootstrapper.exe (PID: 6896)
Launching a file from a Registry key
- XClient.exe (PID: 1192)
- Dark_Autre_ncrypt.exe (PID: 8464)
- msdcsc.exe (PID: 8868)
- client.exe (PID: 8500)
- klass.exe (PID: 9016)
- budiao.exe (PID: 1044)
- rmd_en_1.exe (PID: 8264)
- FreeYoutubeDownloader.exe (PID: 1800)
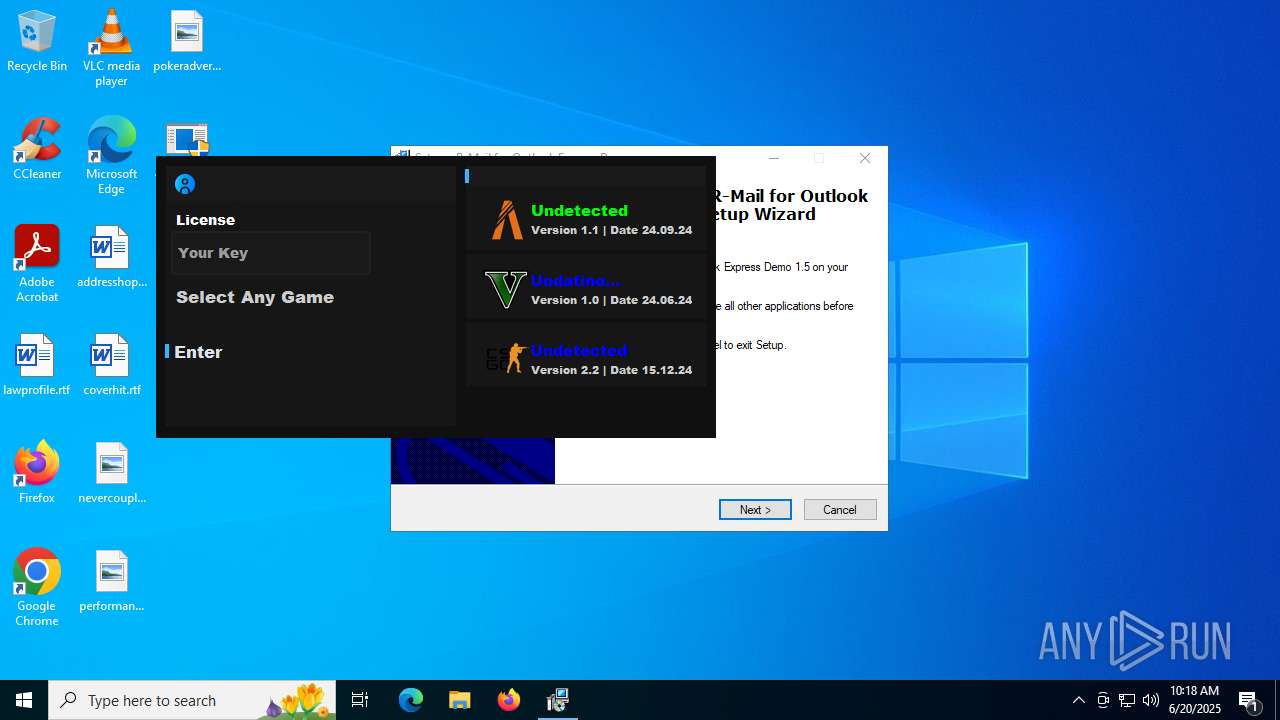
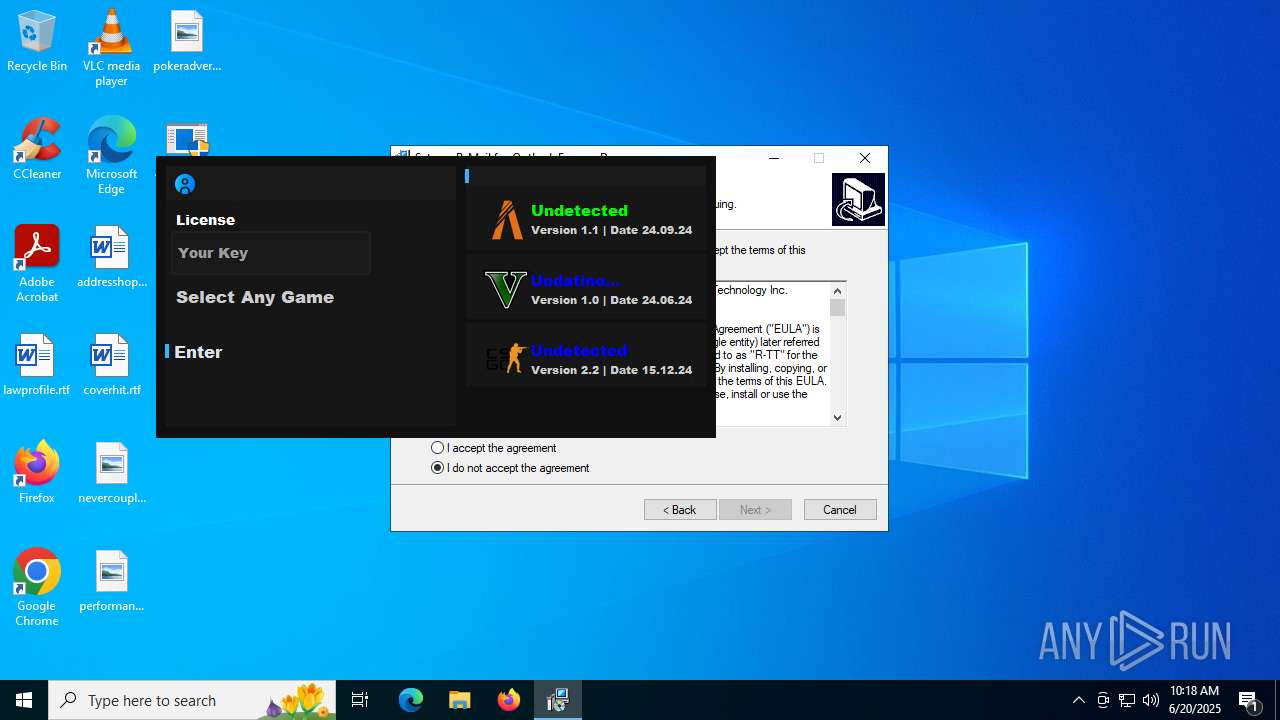
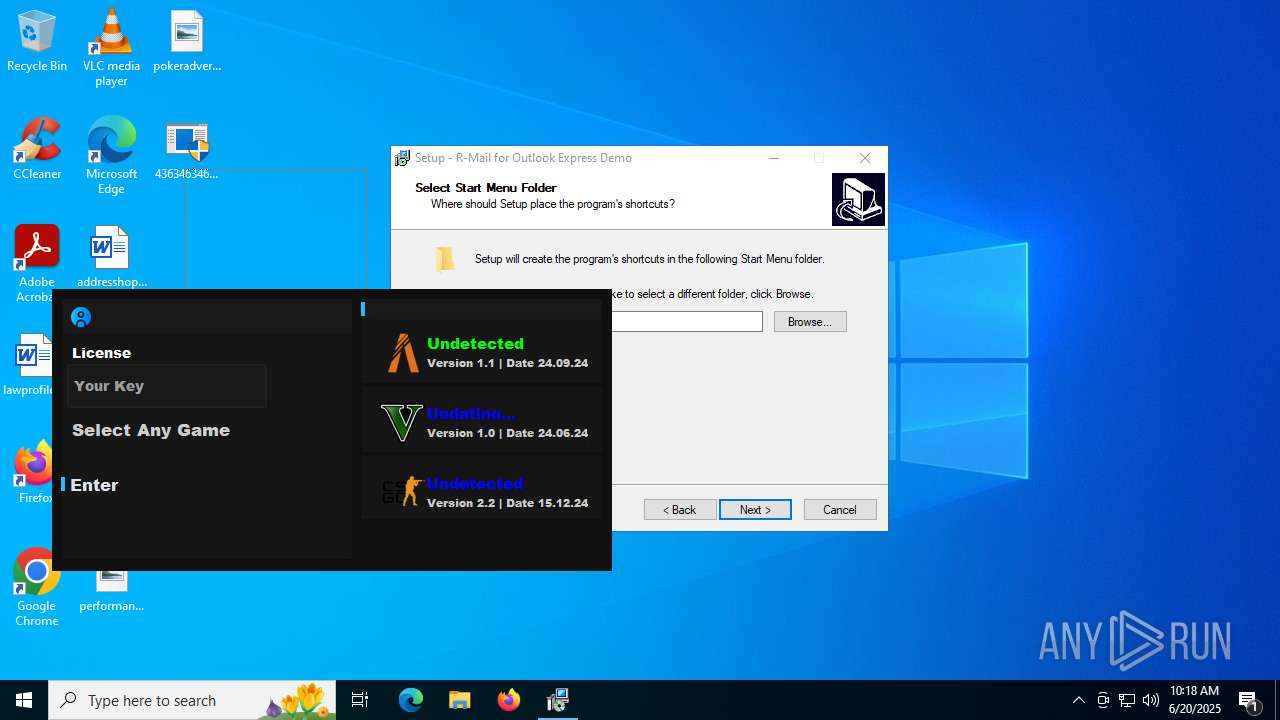
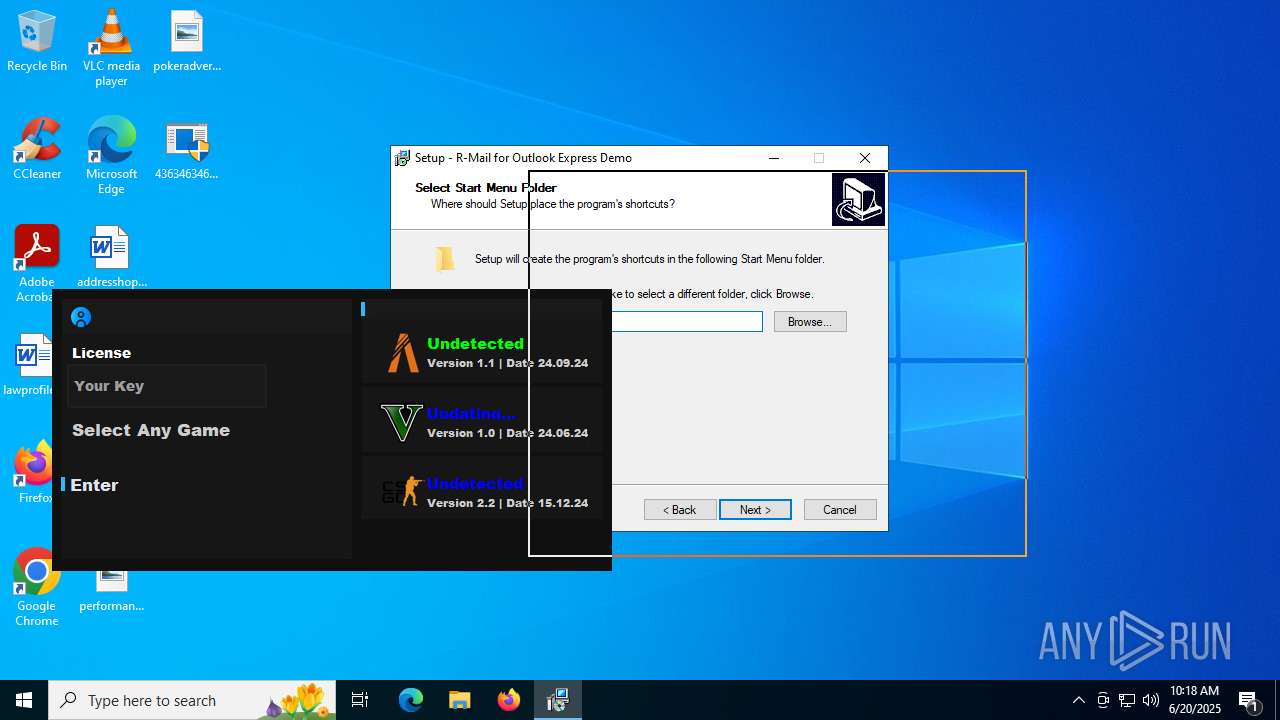
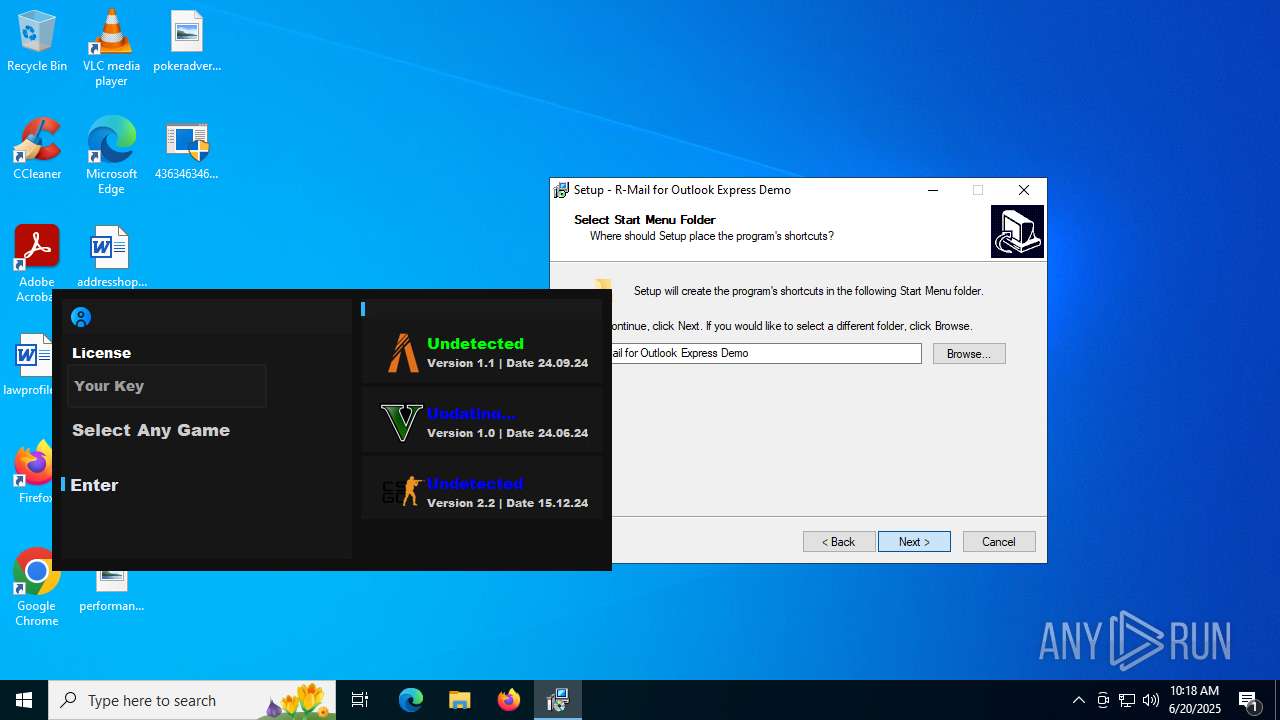
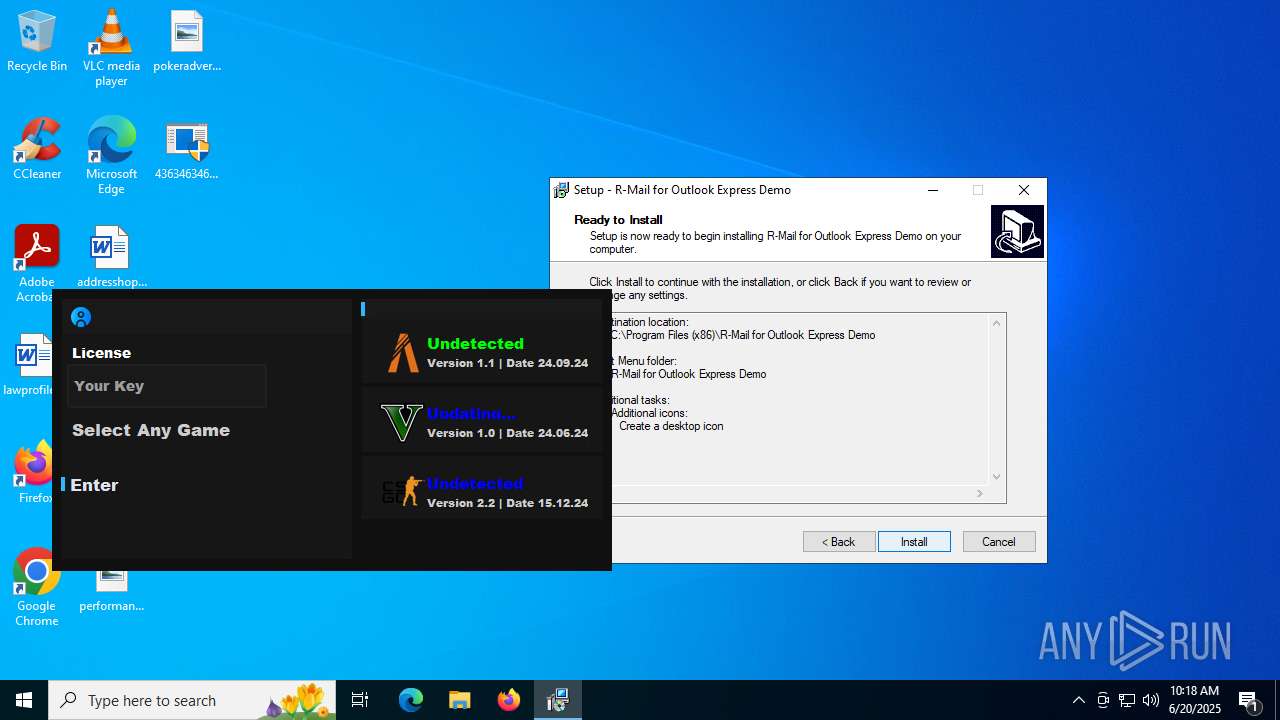
Detects InnoSetup installer (YARA)
- PrivacyPolicy.tmp (PID: 504)
- PrivacyPolicy.exe (PID: 7868)
Creates a software uninstall entry
- PrivacyPolicy.tmp (PID: 504)
- msiexec.exe (PID: 1052)
- is-ED97J.tmp (PID: 9976)
Manages system restore points
- SrTasks.exe (PID: 8988)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1052)
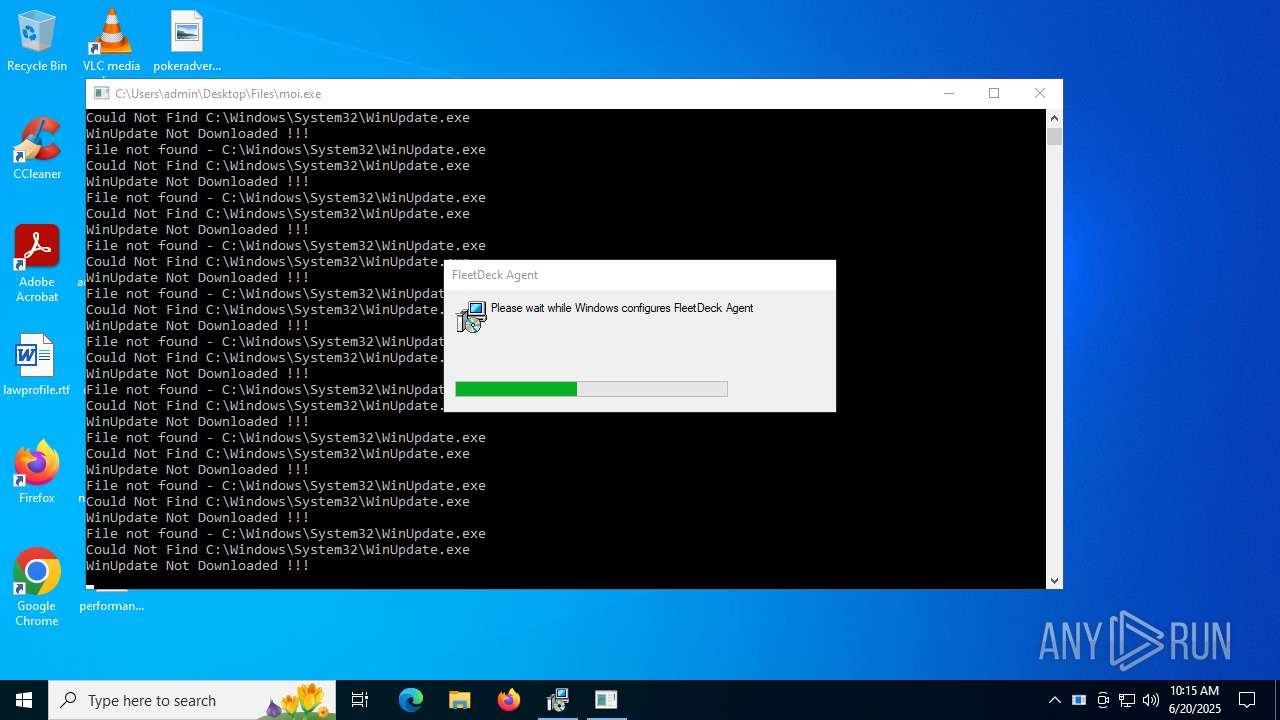
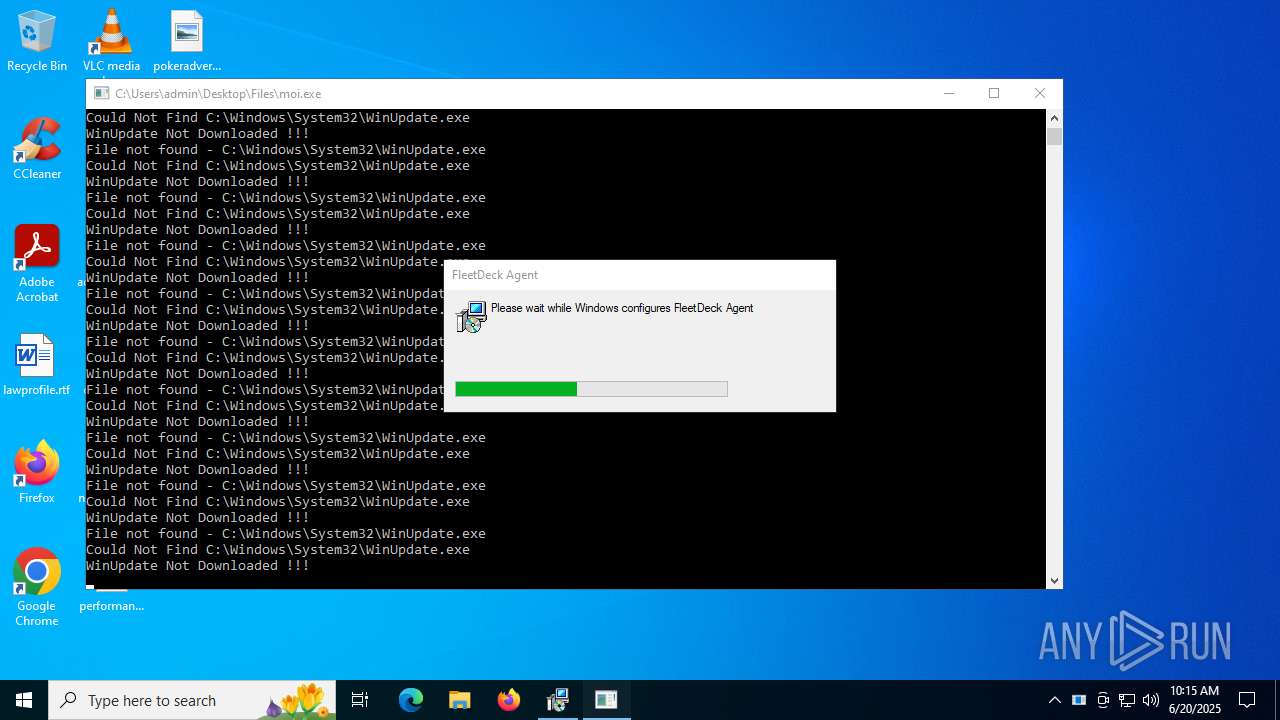
FLEETDECK has been detected
- msiexec.exe (PID: 1052)
- msiexec.exe (PID: 1052)
- fleetdeck_agent_svc.exe (PID: 8240)
- conhost.exe (PID: 5928)
- powershell.exe (PID: 5008)
- conhost.exe (PID: 8828)
- powershell.exe (PID: 4932)
- fleetdeck_agent_svc.exe (PID: 2612)
- powershell.exe (PID: 7340)
- conhost.exe (PID: 8276)
- fleetdeck_agent_svc.exe (PID: 6496)
- powershell.exe (PID: 8432)
- conhost.exe (PID: 8512)
- mport.exe (PID: 3028)
- svchost.exe (PID: 5240)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8432)
The sample compiled with korean language support
- 4363463463464363463463463.exe (PID: 6684)
- client.exe (PID: 8500)
- ClientRun.exe (PID: 8256)
SEETROL has been detected
- ClientRun.exe (PID: 8256)
- SeetrolClient.exe (PID: 5480)
- ipconfig.exe (PID: 9208)
- conhost.exe (PID: 4196)
- explorer.exe (PID: 4772)
Process checks whether UAC notifications are on
- SeetrolClient.exe (PID: 5480)
- dfsvc.exe (PID: 3972)
- hbvTmbP46IIEeHP1.exe (PID: 9572)
Reads mouse settings
- TianSys(XP%E4%B8%93%E7%94%A8).exe (PID: 1216)
- Beverly.com (PID: 2168)
- plugmanff2.exe (PID: 4920)
Reads Internet Explorer settings
- mshta.exe (PID: 8364)
Attempting to use instant messaging service
- svchost.exe (PID: 2200)
Drops encrypted JS script (Microsoft Script Encoder)
- 1.exe (PID: 9088)
Failed to connect to remote server (POWERSHELL)
- powershell.exe (PID: 4500)
Creates a new folder
- cmd.exe (PID: 5416)
The sample compiled with turkish language support
- 4363463463464363463463463.exe (PID: 6684)
- budiao.exe (PID: 1044)
- Synaptics.exe (PID: 8680)
Reads Windows Product ID
- nslookup.exe (PID: 3396)
Checks operating system version
- spoofer.exe (PID: 9652)
The sample compiled with russian language support
- is-ED97J.tmp (PID: 9976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
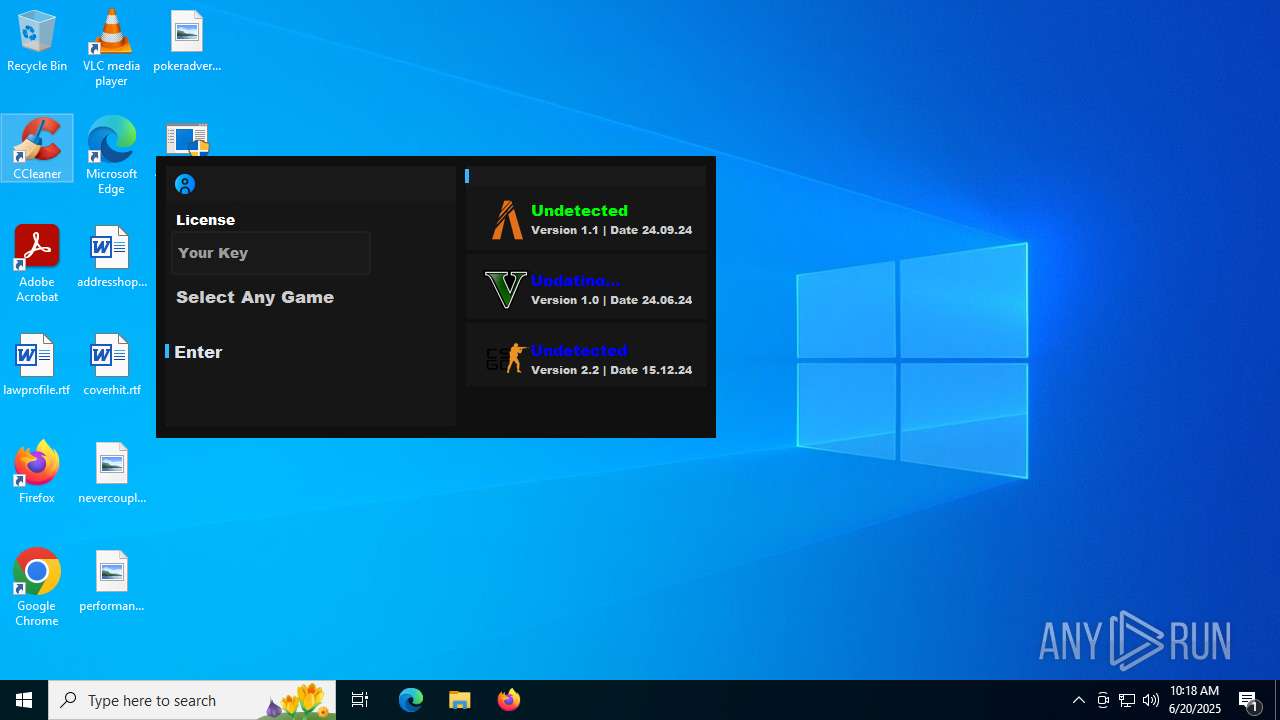
XWorm
(PID) Process(8072) Cloudy.exe
C2147.185.221.27:31149
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.6
MutexhxaYslHcvrRwLqPZ
(PID) Process(1192) XClient.exe
C20.tcp.eu.ngrok.io,6.tcp.eu.ngrok.io,4.tcp.eu.ngrok.io:10358
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.2
MutexQvDYkhYsc5WBgCcl
Quasar
(PID) Process(7932) RuntimeBroker.exe
Version1.4.1
C2 (2)qrpn9be.localto.net:2810
Sub_Dira7
Install_NameRuntimeBroker.exe
Mutexfc5edab1-6e8f-4963-98aa-bd077e08750f
StartupRuntimeBroker
TagRuntimeBroker
LogDirLogs
SignatureZZC28eBl+NFymysV8J6e7PwYbTZdG+ghMNW3nwLjkwmbg2pnNu1EL8MO3SaW/vxGLLQHwZDo45I0EIpQduUE6sroC66Ym5i+a5NZpPwtnRXERrnbzVSb1jGwq981QXkwVBdxUrwxcx6unBX9GQjJ0xovMuUUDowwUVL6qpR9dxuuJo5lX+b3XQmMIxt86uENhFOeD4TO2GrY/ozK06TQiz2DBThVnfKUTjMXsAp3hKq0kLOEeo5xBYgm6MaUrZoIwvWP0fSD2/MUZe87GPmRY1npwJKlxj2aWszG3hYafCHP...
CertificateMIIE9DCCAtygAwIBAgIQAJKyZhVo23+clMB02PDTKzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MTEyODEyNTQzMloYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAwYv1YHO81nj7Tx+B0CNWo6sTWe7WpuY0EXxOAIwQYbwhKU00tP5p8tQCR7AKMAQO/zUcDAfl...
(PID) Process(6216) svhost.exe
Version1.4.0
C2 (2)151.177.61.79:4782
Sub_Dirsvhost
Install_Namesvhost.exe
Mutexa148a6d8-1253-4e62-bc5f-c0242dd62e69
Startupsvhost
Tagsvhost
LogDirLogs
SignatureFiHplcBrV3S97M+7U8Wkv2OAUt8PgnZIpuptBCDmcV3pFCoNQMGru4y6fV4vlwM/qWOV6CUP402T365DHIPm+6uj+1+vgzHGFfiR7S/L+/lpirBGRMTeHcZhxJzbykEf03VPu+8sHMP4tw2JwiJxdryS9YfIuKQufusBaH0ML1oD+gCJoYiH2J1gluHBKSiZAKHI9pdYN7CJN5LNrm41d9IDcibaRPDEiB1m+MVRrQfkHuJZQmYDBxKx3tJF1EBhs5FoUNcpEcF0CWvkWO/psUToSydby8u8lhLv2k962B8w...
CertificateMIIE9DCCAtygAwIBAgIQAMlib63Pu5Cv0/jbVZpvUzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTIwMTAwNTAyMTAzM1oYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAlo+RQClgYhgaYwiwVrdvbvyE47OD8EJLOY/MXs9Z6hD3wx89223nnET+I8zcZNGYn80cgt+q...
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
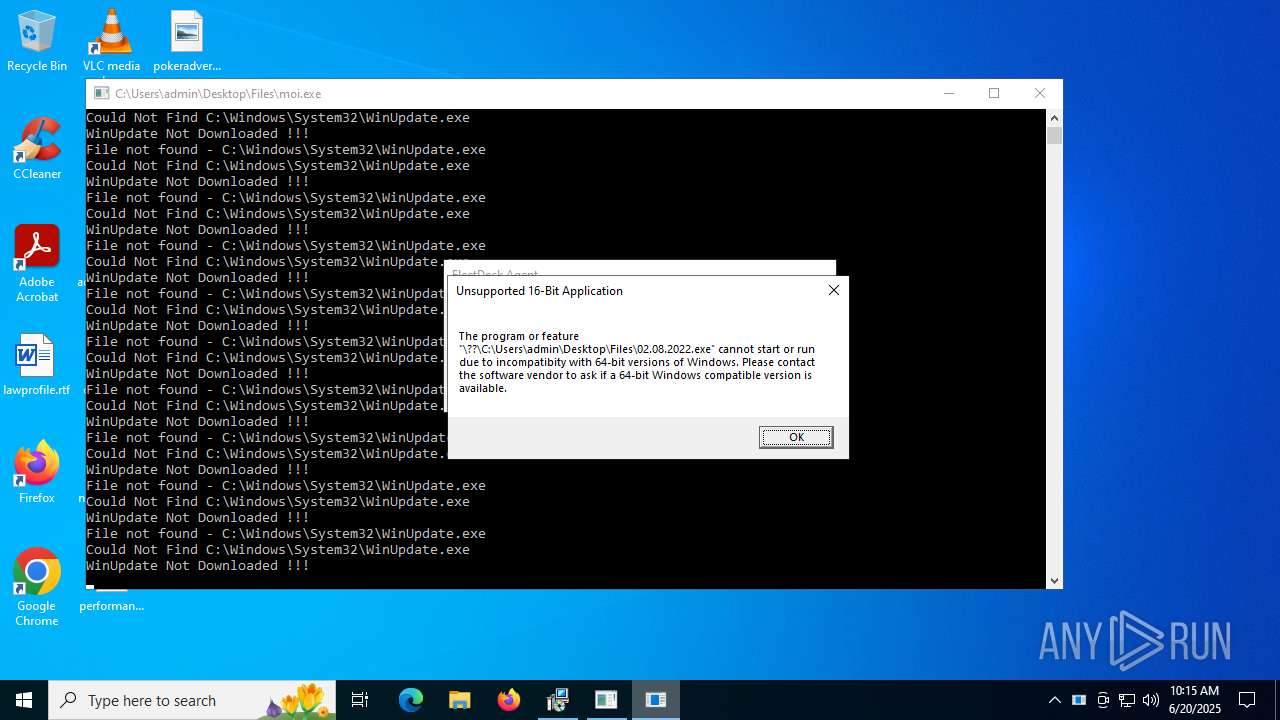
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
1 484
Monitored processes
1 329
Malicious processes
86
Suspicious processes
78
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | "C:\Users\admin\Desktop\Files\barren.exe" | C:\Users\admin\Desktop\Files\barren.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Company: FleetDeck Inc. Integrity Level: HIGH Description: FleetDeck Agent Exit code: 0 Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 424 | "schtasks" /create /tn "Windows_Host_Process" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\RealTekAudio\bootstrapper.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | "schtasks" /create /tn "Discord" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | "schtasks" /create /tn "Discord" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | "C:\WINDOWS\system32\cmd.exe" /c schtasks /create /tn "UAC" /RU "SYSTEM" /SC ONLOGON /F /V1 /RL HIGHEST /TR "C:\Users\admin\AppData\Roaming\NsMiner\IMG001.exe" | C:\Windows\SysWOW64\cmd.exe | IMG001.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
210 807
Read events
209 130
Write events
1 439
Delete events
238
Modification events
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F0062000000000000000000000001000000C0030000C0030000 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 0000000000000000000000000000000003000100010001000E000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C00000012000000000000006C0061007700700072006F00660069006C0065002E007200740066003E002000200000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000001300000000000000610064006400720065007300730068006F00700065002E007200740066003E00200020000000100000000000000063006F007600650072006800690074002E007200740066003E0020002000000013000000000000006E00650076006500720063006F00750070006C0065002E0070006E0067003E002000200000001A0000000000000070006500720066006F0072006D0061006E006300650068006F007300740069006E0067002E006A00700067003E00200020000000180000000000000070006F006B00650072006100640076006500720074006900730069006E0067002E0070006E0067003E00200020000000210000000000000034003300360033003400360033003400360033003400360034003300360033003400360033003400360033003400360033002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000000E00000000000000000000000000000000000000803F0000004008000000803F000040400900000000000000404003000000803F000080400A000000803F0000A0400B0000000040000000000C00000000000000803F01000000000000000040020000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F0700000000400000803F0D00 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 7934556800000000 | |||
| (PID) Process: | (6684) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6684) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6684) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6684) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6684) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6684) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
601
Suspicious files
650
Text files
1 361
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6980 | S.exe | C:\Users\admin\AppData\Local\8f369494f3294276228810eb857762e1\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Desktop\performancehosting.jpg | image | |
MD5:C3D00E793252349768215A1F6368B7FD | SHA256:4E965AB59EA60AB106C3DCC62F9A8A00138688661843F8CB8BD42E43ECD43199 | |||
| 6980 | S.exe | C:\Users\admin\Desktop\Files\3R%BC%BC%CA%F5.exe | executable | |
MD5:72B418C46912C0EE672AAB58B0A13F2B | SHA256:F307BA8ED6E64B2196D5D71D38A2C24A5EF3386FD46057FED76895FEF2BA804D | |||
| 6980 | S.exe | C:\Users\admin\AppData\Local\8f369494f3294276228810eb857762e1\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Pictures\regulationsbased.png | image | |
MD5:225EC614E061007E0CEC85AAADC1E715 | SHA256:1BB2CCBA1921586035B2566EBF95683BBFD2240EC3A66003FF6D02D3B53A1931 | |||
| 6980 | S.exe | C:\Users\admin\AppData\Local\Temp\Phantom-Latest.log | text | |
MD5:95FF7D63EA504685E2D4D0557BE5A7F5 | SHA256:40999827CF6531F6747D7B53FCE14B2C9A2BE417BDA8460AF685CE8D3639156D | |||
| 6980 | S.exe | C:\Users\admin\AppData\Local\8f369494f3294276228810eb857762e1\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Pictures\lotfit.jpg | image | |
MD5:AEF06784839C1ADF991D24D24796DECD | SHA256:8A819AB3CAF82215C8B0C3E59E9E793B6BB0E25AB46073AB2E44903E28F17B50 | |||
| 6980 | S.exe | C:\Users\admin\AppData\Local\8f369494f3294276228810eb857762e1\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Desktop\addresshope.rtf | text | |
MD5:53017A2F353CD1BB491CB1F816C88183 | SHA256:69CF17304786AF47D323F7643960C2F9A2C976C5A4315F7DEA5883959A702090 | |||
| 6980 | S.exe | C:\Users\admin\AppData\Local\8f369494f3294276228810eb857762e1\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Documents\checkwindow.rtf | text | |
MD5:308E195831CB2B40E87AAE6F9A2BC243 | SHA256:D08978A67EC8CD53381910FB3EA7C20F2CB462756CCCB5E137F2A6C5B19D3E1C | |||
| 6980 | S.exe | C:\Users\admin\AppData\Local\8f369494f3294276228810eb857762e1\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Desktop\lawprofile.rtf | text | |
MD5:A6EC5286EA2302D3CD24B6FAA54967A4 | SHA256:839C83A156AA7967233F12DFA1AFC25C523CE9C9ED05986B094350ECBBD07CE8 | |||
| 6980 | S.exe | C:\Users\admin\AppData\Local\8f369494f3294276228810eb857762e1\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Pictures\toolslittle.jpg | image | |
MD5:E1806C05D60CA54FAEA243E60105F55C | SHA256:288372116A9147C3ACF78490BC2FAA0BAA4B94C1BA505A5D7E30FBC6225E6110 | |||
| 6980 | S.exe | C:\Users\admin\AppData\Local\8f369494f3294276228810eb857762e1\admin@DESKTOP-JGLLJLD_en-US\Grabber\DRIVE-C\Users\admin\Pictures\artistshosting.png | image | |
MD5:201A930073396490B708B1CB6752DE5A | SHA256:3E2A13EFAC9C876C92F98E126DD500392E98A1ABB894600FA0C24D6D8E0E0399 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
345
TCP/UDP connections
1 293
DNS requests
247
Threats
556
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6684 | 4363463463464363463463463.exe | GET | — | 172.245.123.11:80 | http://172.245.123.11/new/S.exe | unknown | — | — | malicious |
3884 | WmiPrvSE.exe | GET | 200 | 184.25.54.100:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
2464 | svchost.exe | GET | 200 | 23.40.158.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4172 | update.exe | GET | 200 | 39.100.254.136:80 | http://www.zhikey.com/crm/xinjiancegengxin.txt | unknown | — | — | unknown |
3884 | WmiPrvSE.exe | GET | 200 | 2.18.244.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
6684 | 4363463463464363463463463.exe | GET | 200 | 8.138.182.17:80 | http://8.138.182.17/3R%BC%BC%CA%F5.exe | unknown | — | — | unknown |
3884 | WmiPrvSE.exe | GET | 200 | 2.18.244.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6684 | 4363463463464363463463463.exe | GET | 200 | 39.100.254.136:80 | http://www.zhikey.com/crm/exe/update.exe | unknown | — | — | unknown |
6980 | S.exe | GET | 200 | 104.16.184.241:80 | http://icanhazip.com/ | unknown | — | — | whitelisted |
3884 | WmiPrvSE.exe | GET | 200 | 184.25.54.100:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2140 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6684 | 4363463463464363463463463.exe | 151.101.194.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6684 | 4363463463464363463463463.exe | 172.245.123.11:80 | — | AS-COLOCROSSING | US | malicious |
6684 | 4363463463464363463463463.exe | 39.100.254.136:80 | www.zhikey.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2464 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
www.zhikey.com |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
icanhazip.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6684 | 4363463463464363463463463.exe | A Network Trojan was detected | ET MALWARE Single char EXE direct download likely trojan (multiple families) |
6684 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6684 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6684 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
6684 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6684 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
6684 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4172 | update.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
6684 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6684 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Microsoft\Edge\User Data directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Microsoft\Edge\User Data directory exists )
|
4363463463464363463463463.exe | Unable to connect to the remote server
|
4363463463464363463463463.exe | Unable to connect to the remote server
|
4363463463464363463463463.exe | The specified executable is not a valid application for this OS platform.
|
4363463463464363463463463.exe | The remote server returned an error: (404) Not Found.
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: onecore\com\netfx\windowsbuilt\iso_legacy\base\isolation\hier_hierarchy.cpp, line 230
|