| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/e5a4c0f8-fd37-4f5c-9a90-5fa082f18f9e |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | July 07, 2024, 19:58:46 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
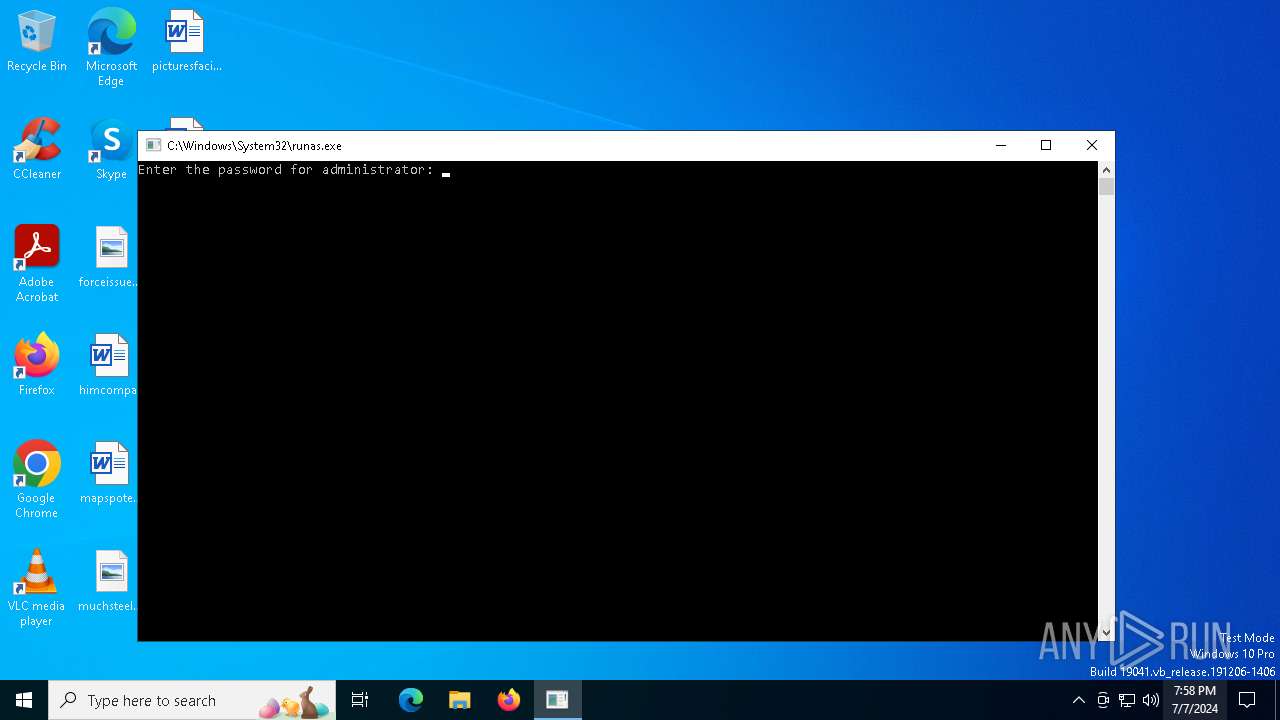
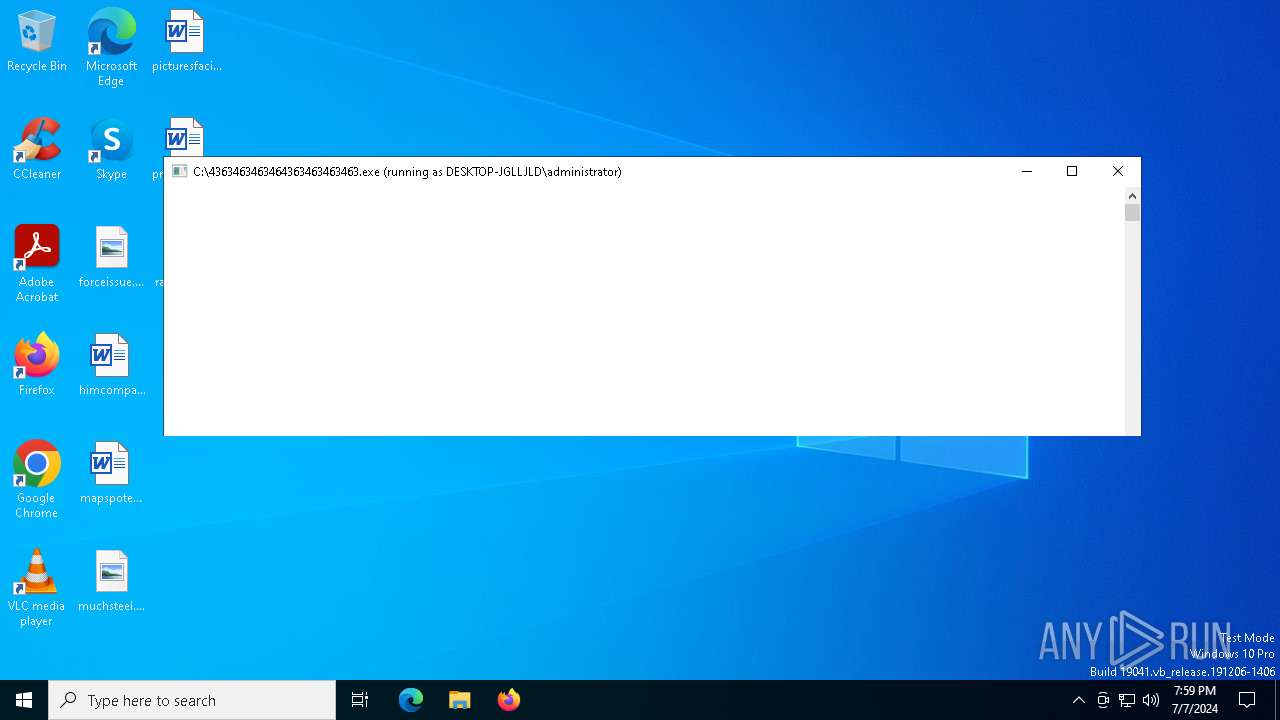
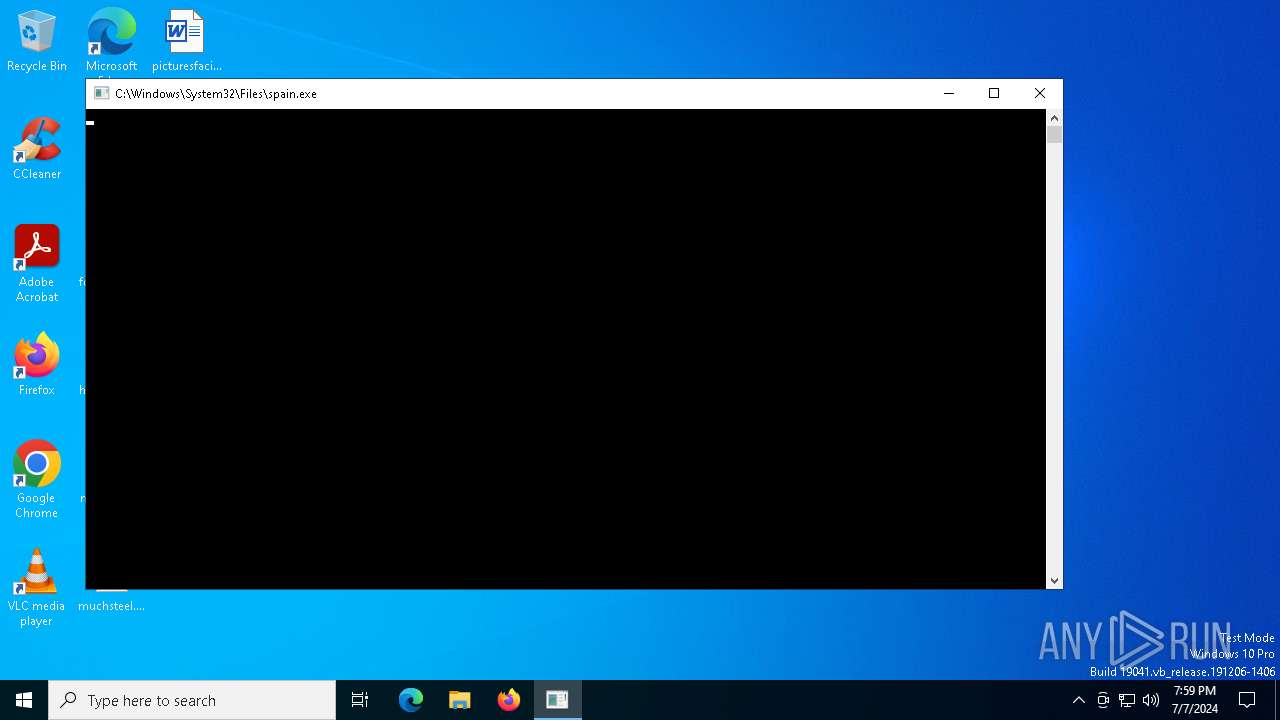
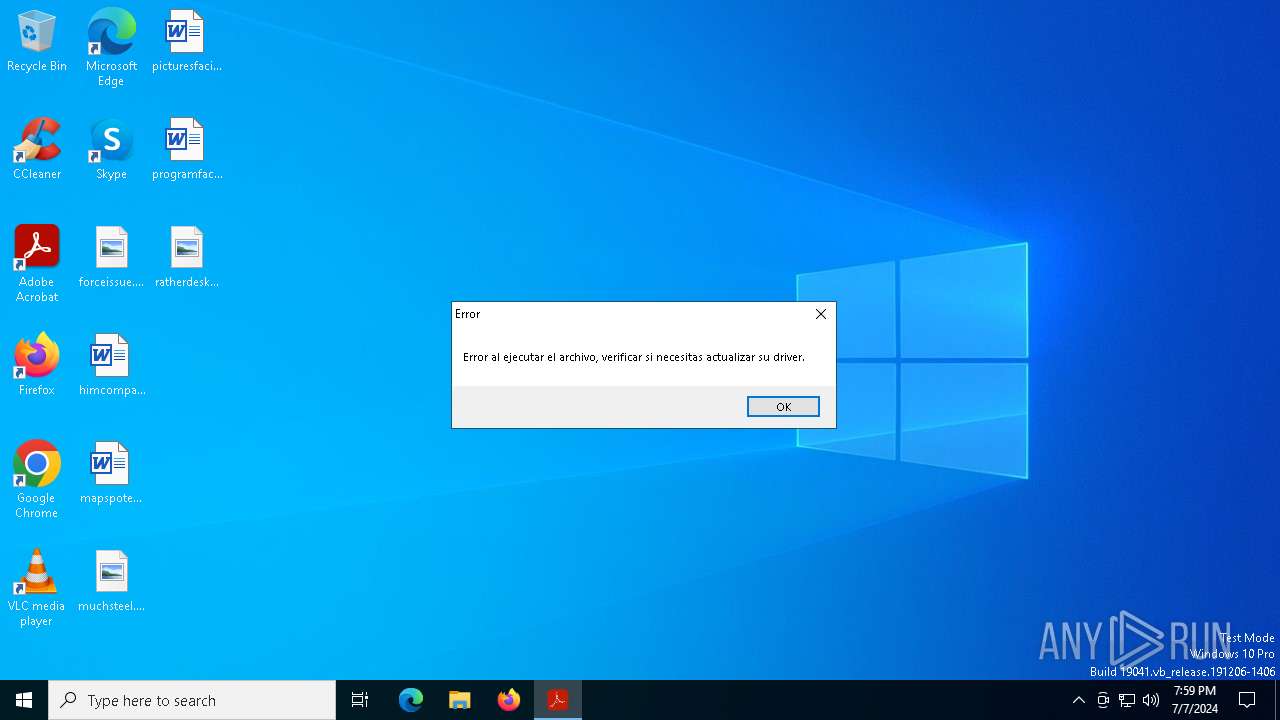
MALICIOUS
Drops the executable file immediately after the start
- runas.exe (PID: 1048)
- 4363463463464363463463463.exe (PID: 6420)
- zxcvb.exe (PID: 6744)
- BLueHvffhw.exe (PID: 6892)
- spain.exe (PID: 4980)
- 8$gs3AYhd.exe (PID: 4820)
- o9Wg44$.exe (PID: 6932)
- hv.exe (PID: 6556)
- buildjudit.exe (PID: 6880)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- 8fc809.exe (PID: 7016)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- amadka.exe (PID: 6404)
- sunset1.exe (PID: 188)
- Dctooux.exe (PID: 4440)
- PresentationFontCache.exe (PID: 2056)
- lrthijawd.exe (PID: 6556)
- work.exe (PID: 7020)
- jergs.exe (PID: 7140)
Creates a writable file in the system directory
- 4363463463464363463463463.exe (PID: 6420)
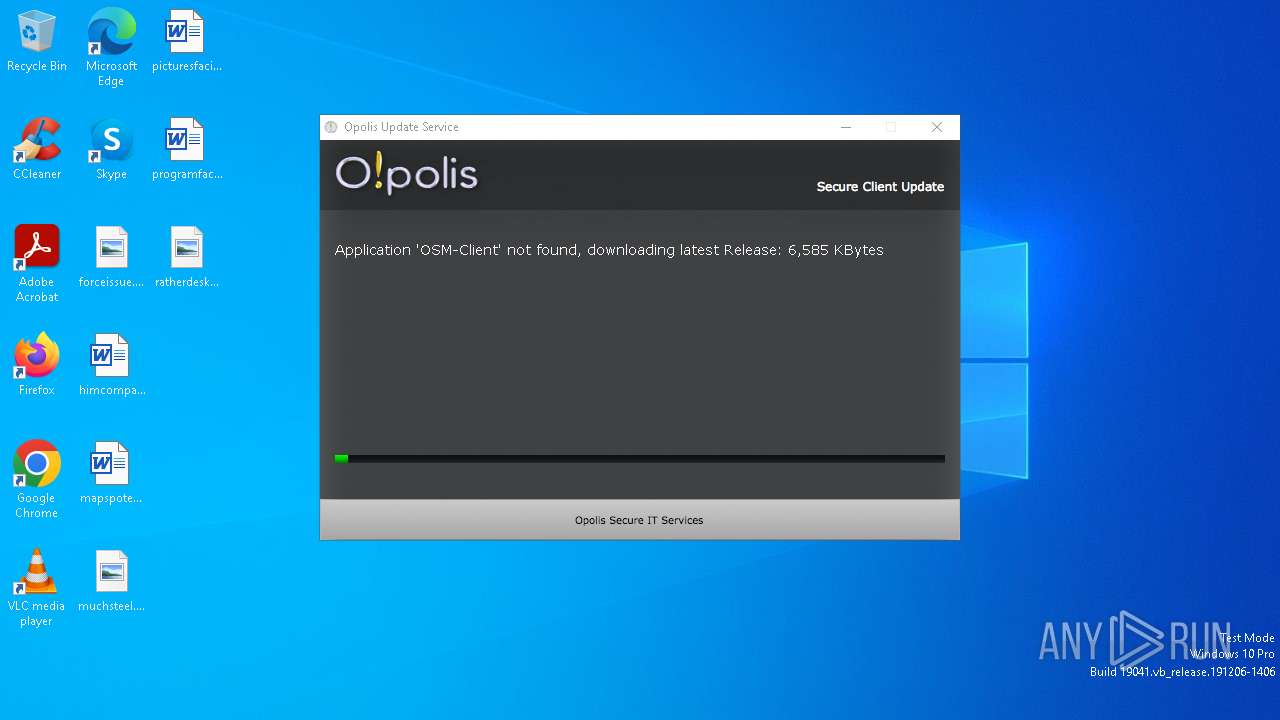
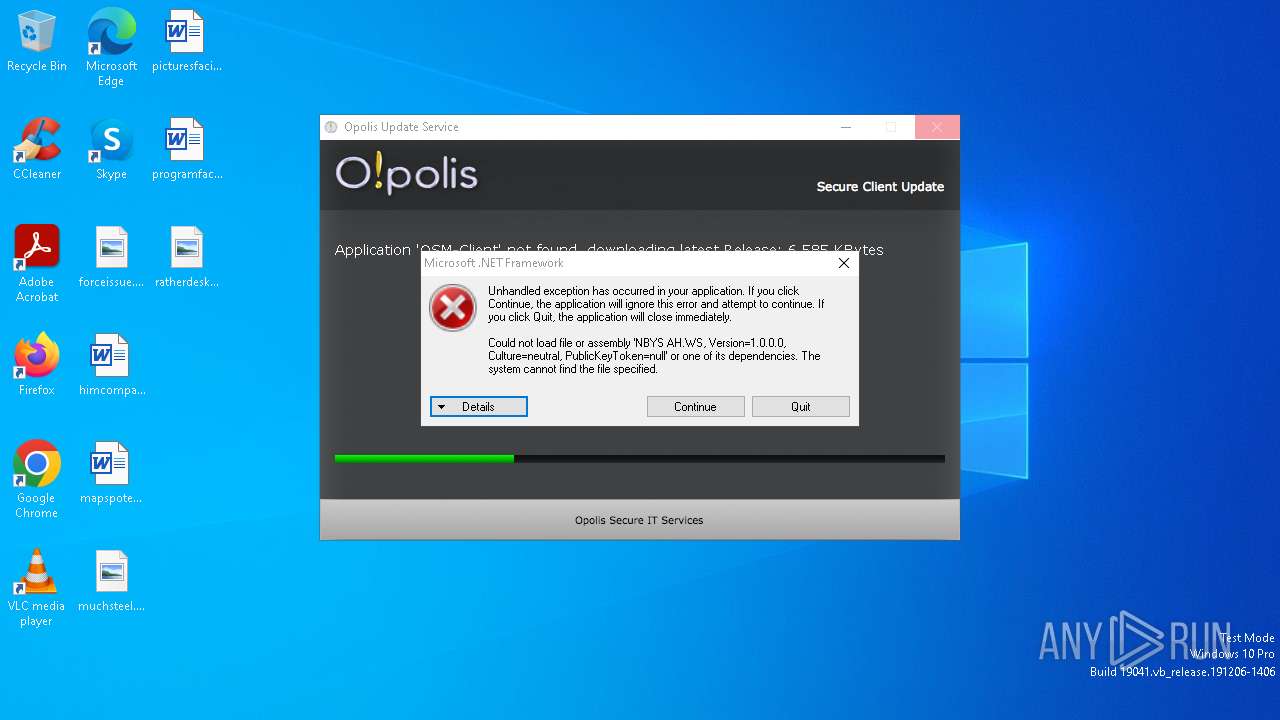
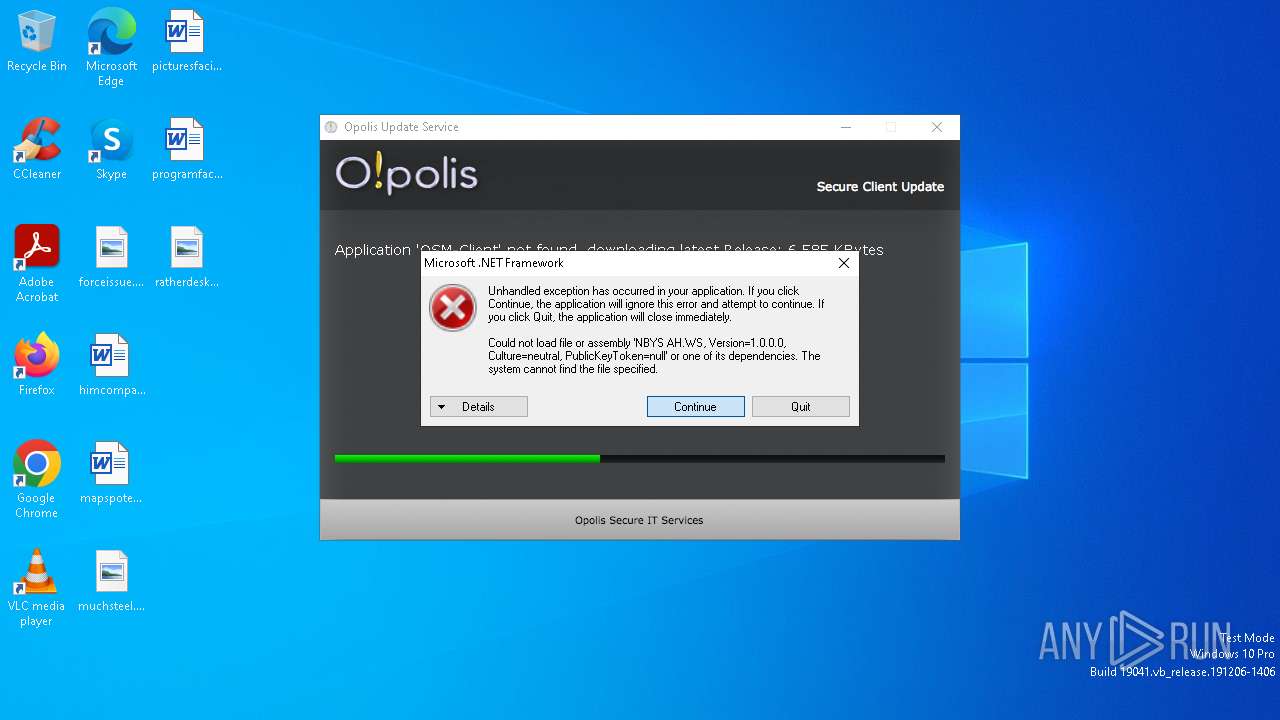
- Opolis.exe (PID: 1064)
Bypass execution policy to execute commands
- powershell.exe (PID: 2272)
- powershell.exe (PID: 6768)
- powershell.exe (PID: 836)
- powershell.exe (PID: 4216)
- powershell.exe (PID: 2044)
- powershell.exe (PID: 4020)
Run PowerShell with an invisible window
- powershell.exe (PID: 2272)
- powershell.exe (PID: 6768)
RHADAMANTHYS has been detected (SURICATA)
- OpenWith.exe (PID: 6924)
- OOBE-Maintenance.exe (PID: 6204)
- OpenWith.exe (PID: 5112)
- OOBE-Maintenance.exe (PID: 7160)
- OpenWith.exe (PID: 5868)
- OpenWith.exe (PID: 6980)
- OOBE-Maintenance.exe (PID: 6748)
- OOBE-Maintenance.exe (PID: 6340)
- OpenWith.exe (PID: 6916)
- OOBE-Maintenance.exe (PID: 1520)
- OOBE-Maintenance.exe (PID: 1140)
- OpenWith.exe (PID: 3888)
- OpenWith.exe (PID: 2828)
- OpenWith.exe (PID: 2416)
- OOBE-Maintenance.exe (PID: 7004)
- OOBE-Maintenance.exe (PID: 2612)
Adds path to the Windows Defender exclusion list
- spain.exe (PID: 3716)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- IerLRtXpEcMnUjz.exe (PID: 5884)
AZORULT has been detected (SURICATA)
- o9Wg44$.exe (PID: 6932)
- eW[}J50.exe (PID: 6932)
- {N1tA.exe (PID: 5104)
- r459`GR~h.exe (PID: 6256)
Actions looks like stealing of personal data
- OOBE-Maintenance.exe (PID: 6204)
- OOBE-Maintenance.exe (PID: 6748)
- PACKAGE_DEMO.exe (PID: 2060)
- OOBE-Maintenance.exe (PID: 6340)
- OOBE-Maintenance.exe (PID: 7160)
- OOBE-Maintenance.exe (PID: 1520)
- 123.exe (PID: 6480)
- rundll32.exe (PID: 2012)
- OOBE-Maintenance.exe (PID: 7004)
- OOBE-Maintenance.exe (PID: 2612)
- rundll32.exe (PID: 6600)
- OOBE-Maintenance.exe (PID: 1140)
- rundll32.exe (PID: 6944)
Connects to the CnC server
- o9Wg44$.exe (PID: 6932)
- eW[}J50.exe (PID: 6932)
- intalls555.exe (PID: 6652)
- 123.exe (PID: 6480)
- pG`jQ0tIj2.exe (PID: 4264)
- Dctooux.exe (PID: 4440)
- {N1tA.exe (PID: 5104)
- r459`GR~h.exe (PID: 6256)
XWORM has been detected (SURICATA)
- intalls555.exe (PID: 6652)
Starts CMD.EXE for self-deleting
- o9Wg44$.exe (PID: 6932)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6420)
DCRAT has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6420)
MEDUZASTEALER has been detected (SURICATA)
- PACKAGE_DEMO.exe (PID: 2060)
Generic malware mutex has been detected
- hv.exe (PID: 6556)
Uses Task Scheduler to run other applications
- IerLRtXpEcMnUjz.exe (PID: 3580)
- IerLRtXpEcMnUjz.exe (PID: 5884)
Adds process to the Windows Defender exclusion list
- IerLRtXpEcMnUjz.exe (PID: 5884)
Changes powershell execution policy (Bypass)
- IerLRtXpEcMnUjz.exe (PID: 5884)
XWORM has been detected (YARA)
- intalls555.exe (PID: 6652)
- server.exe (PID: 5220)
- IerLRtXpEcMnUjz.exe (PID: 5884)
METASTEALER has been detected (SURICATA)
- 123.exe (PID: 6480)
REDLINE has been detected (SURICATA)
- 123.exe (PID: 6480)
Changes the autorun value in the registry
- IerLRtXpEcMnUjz.exe (PID: 5884)
Create files in the Startup directory
- IerLRtXpEcMnUjz.exe (PID: 5884)
Steals credentials from Web Browsers
- 123.exe (PID: 6480)
- rundll32.exe (PID: 2012)
- rundll32.exe (PID: 6600)
- rundll32.exe (PID: 6944)
[YARA] zgRAT detected by memory dumps
- MSBuild.exe (PID: 6824)
AMADEY has been detected (SURICATA)
- Dctooux.exe (PID: 4440)
- explorti.exe (PID: 6020)
Modifies registry (POWERSHELL)
- powershell.exe (PID: 6980)
PUREMINER has been detected (YARA)
- MSBuild.exe (PID: 6824)
REDLINE has been detected (YARA)
- RegAsm.exe (PID: 6436)
- 123.exe (PID: 6480)
AMADEY has been detected (YARA)
- Dctooux.exe (PID: 4440)
- explorti.exe (PID: 6020)
SUSPICIOUS
Creates file in the systems drive root
- runas.exe (PID: 1048)
- 4363463463464363463463463.exe (PID: 6420)
- PACKAGE_DEMO.exe (PID: 2060)
- rundll32.exe (PID: 2012)
- rundll32.exe (PID: 6600)
- rundll32.exe (PID: 6944)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 6420)
- zxcvb.exe (PID: 6744)
- DownSysSoft.exe (PID: 7140)
- o9Wg44$.exe (PID: 6932)
- eW[}J50.exe (PID: 6932)
- PACKAGE_DEMO.exe (PID: 2060)
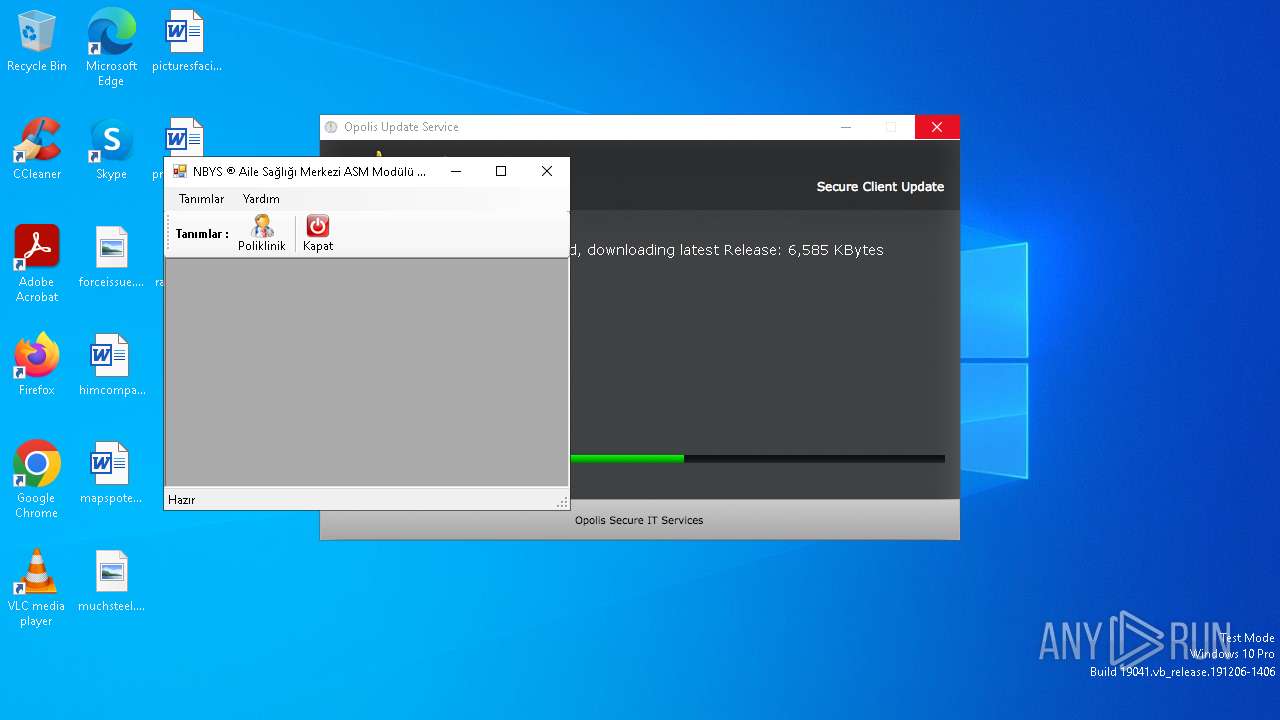
- NBYS%20ASM.NET.exe (PID: 6920)
- buildjudit.exe (PID: 6880)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- pG`jQ0tIj2.exe (PID: 4264)
- 8fc809.exe (PID: 7016)
- Dctooux.exe (PID: 4440)
- amadka.exe (PID: 6404)
- Downaqzh.exe (PID: 6248)
- explorti.exe (PID: 6020)
- sunset1.exe (PID: 188)
- {N1tA.exe (PID: 5104)
- r459`GR~h.exe (PID: 6256)
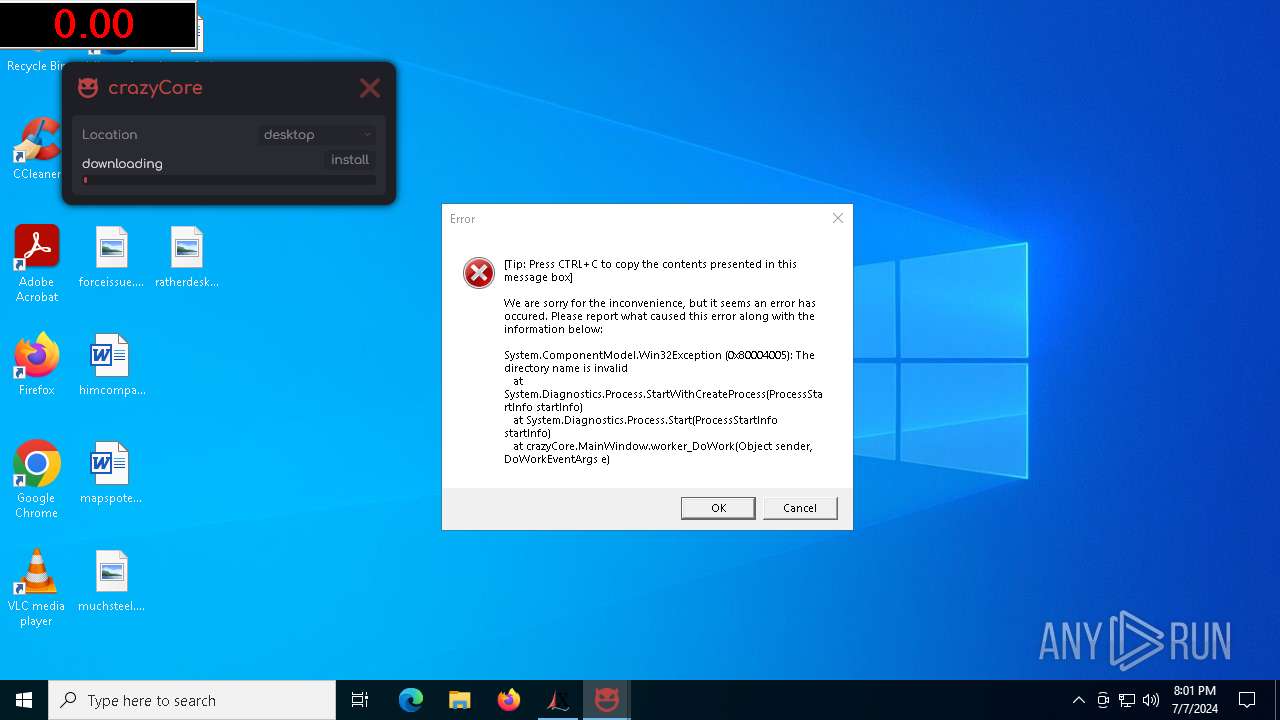
- crazyCore.exe (PID: 3884)
- lrthijawd.exe (PID: 6556)
- work.exe (PID: 7020)
- ShellExperienceHost.exe (PID: 1648)
Reads the date of Windows installation
- 4363463463464363463463463.exe (PID: 6420)
- zxcvb.exe (PID: 6744)
- o9Wg44$.exe (PID: 6932)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- 8fc809.exe (PID: 7016)
- amadka.exe (PID: 6404)
- Dctooux.exe (PID: 4440)
- lrthijawd.exe (PID: 6556)
- work.exe (PID: 7020)
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 6420)
- BLueHvffhw.exe (PID: 6892)
- spain.exe (PID: 4980)
- OOBE-Maintenance.exe (PID: 6204)
- OOBE-Maintenance.exe (PID: 7160)
- zxcvb.exe (PID: 6744)
- 8$gs3AYhd.exe (PID: 4820)
- o9Wg44$.exe (PID: 6932)
- OOBE-Maintenance.exe (PID: 6748)
- OOBE-Maintenance.exe (PID: 6340)
- hv.exe (PID: 6556)
- OOBE-Maintenance.exe (PID: 1520)
- buildjudit.exe (PID: 6880)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- OOBE-Maintenance.exe (PID: 1140)
- 8fc809.exe (PID: 7016)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- amadka.exe (PID: 6404)
- sunset1.exe (PID: 188)
- Dctooux.exe (PID: 4440)
- OOBE-Maintenance.exe (PID: 7004)
- OOBE-Maintenance.exe (PID: 2612)
- PresentationFontCache.exe (PID: 2056)
- lrthijawd.exe (PID: 6556)
- work.exe (PID: 7020)
- jergs.exe (PID: 7140)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 6420)
- DownSysSoft.exe (PID: 7140)
- Dctooux.exe (PID: 4440)
- Downaqzh.exe (PID: 6248)
Application launched itself
- zxcvb.exe (PID: 6744)
- BLueHvffhw.exe (PID: 6820)
- native.exe (PID: 6436)
- zxcvb.exe (PID: 6860)
- 8$gs3AYhd.exe (PID: 3164)
- spain.exe (PID: 4980)
- 5P%9(QJ.exe (PID: 4264)
- native.exe (PID: 3168)
- ghjkl.exe (PID: 2356)
- o9Wg44$.exe (PID: 6760)
- OxNbFsL8.exe (PID: 6168)
- MSBuild.exe (PID: 6916)
- asdfg.exe (PID: 4072)
- net.exe (PID: 6440)
- eW[}J50.exe (PID: 7140)
- native.exe (PID: 6900)
- FTO{.exe (PID: 5220)
- ~BC82ZFrr.exe (PID: 7040)
- ]%df.exe (PID: 1992)
- net.exe (PID: 3068)
- (_MifxBg$[.exe (PID: 5880)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- net.exe (PID: 7096)
- ghjk.exe (PID: 4764)
- pG`jQ0tIj2.exe (PID: 6268)
- I{9uGVeaM.exe (PID: 6980)
- net.exe (PID: 2404)
- realtekaft.exe (PID: 5872)
- {N1tA.exe (PID: 3716)
- qtN49E].exe (PID: 6768)
- r459`GR~h.exe (PID: 6564)
- 7TP.exe (PID: 6224)
- PresentationFontCache.exe (PID: 2056)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 6420)
The process checks if it is being run in the virtual environment
- OpenWith.exe (PID: 6924)
- OpenWith.exe (PID: 5112)
- OpenWith.exe (PID: 5868)
- OpenWith.exe (PID: 6980)
- OpenWith.exe (PID: 6916)
- OpenWith.exe (PID: 2828)
- OpenWith.exe (PID: 3888)
- OpenWith.exe (PID: 2416)
The process executes via Task Scheduler
- powershell.exe (PID: 2272)
- powershell.exe (PID: 6768)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 6420)
- DownSysSoft.exe (PID: 7140)
- intalls555.exe (PID: 6652)
- MSBuild.exe (PID: 6824)
- PACKAGE_DEMO.exe (PID: 2060)
- server.exe (PID: 5220)
- jsc.exe (PID: 1672)
- RegAsm.exe (PID: 6436)
- 123.exe (PID: 6480)
- Downaqzh.exe (PID: 6248)
- IerLRtXpEcMnUjz.exe (PID: 5884)
Contacting a server suspected of hosting an CnC
- OpenWith.exe (PID: 6924)
- OOBE-Maintenance.exe (PID: 6204)
- OpenWith.exe (PID: 5112)
- OOBE-Maintenance.exe (PID: 7160)
- 4363463463464363463463463.exe (PID: 6420)
- o9Wg44$.exe (PID: 6932)
- OpenWith.exe (PID: 5868)
- intalls555.exe (PID: 6652)
- OOBE-Maintenance.exe (PID: 6748)
- OpenWith.exe (PID: 6980)
- eW[}J50.exe (PID: 6932)
- OOBE-Maintenance.exe (PID: 6340)
- OpenWith.exe (PID: 6916)
- OOBE-Maintenance.exe (PID: 1520)
- OpenWith.exe (PID: 2828)
- OOBE-Maintenance.exe (PID: 1140)
- OpenWith.exe (PID: 3888)
- pG`jQ0tIj2.exe (PID: 4264)
- OOBE-Maintenance.exe (PID: 7004)
- OpenWith.exe (PID: 2416)
- explorti.exe (PID: 6020)
- Dctooux.exe (PID: 4440)
- OOBE-Maintenance.exe (PID: 2612)
- {N1tA.exe (PID: 5104)
- r459`GR~h.exe (PID: 6256)
Loads DLL from Mozilla Firefox
- OOBE-Maintenance.exe (PID: 6204)
- OOBE-Maintenance.exe (PID: 7160)
- OOBE-Maintenance.exe (PID: 6748)
- OOBE-Maintenance.exe (PID: 6340)
- OOBE-Maintenance.exe (PID: 1520)
- OOBE-Maintenance.exe (PID: 1140)
- OOBE-Maintenance.exe (PID: 7004)
- OOBE-Maintenance.exe (PID: 2612)
- rundll32.exe (PID: 2012)
- rundll32.exe (PID: 6600)
- rundll32.exe (PID: 6944)
Searches for installed software
- OOBE-Maintenance.exe (PID: 6204)
- OOBE-Maintenance.exe (PID: 7160)
- o9Wg44$.exe (PID: 6932)
- OOBE-Maintenance.exe (PID: 6748)
- OOBE-Maintenance.exe (PID: 6340)
- OOBE-Maintenance.exe (PID: 1520)
- PACKAGE_DEMO.exe (PID: 2060)
- OOBE-Maintenance.exe (PID: 1140)
- OOBE-Maintenance.exe (PID: 7004)
- OOBE-Maintenance.exe (PID: 2612)
Process drops python dynamic module
- spain.exe (PID: 4980)
- buildjudit.exe (PID: 6880)
- PresentationFontCache.exe (PID: 2056)
Process drops legitimate windows executable
- spain.exe (PID: 4980)
- o9Wg44$.exe (PID: 6932)
- buildjudit.exe (PID: 6880)
- PresentationFontCache.exe (PID: 2056)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 6420)
The process drops C-runtime libraries
- spain.exe (PID: 4980)
- o9Wg44$.exe (PID: 6932)
- buildjudit.exe (PID: 6880)
- PresentationFontCache.exe (PID: 2056)
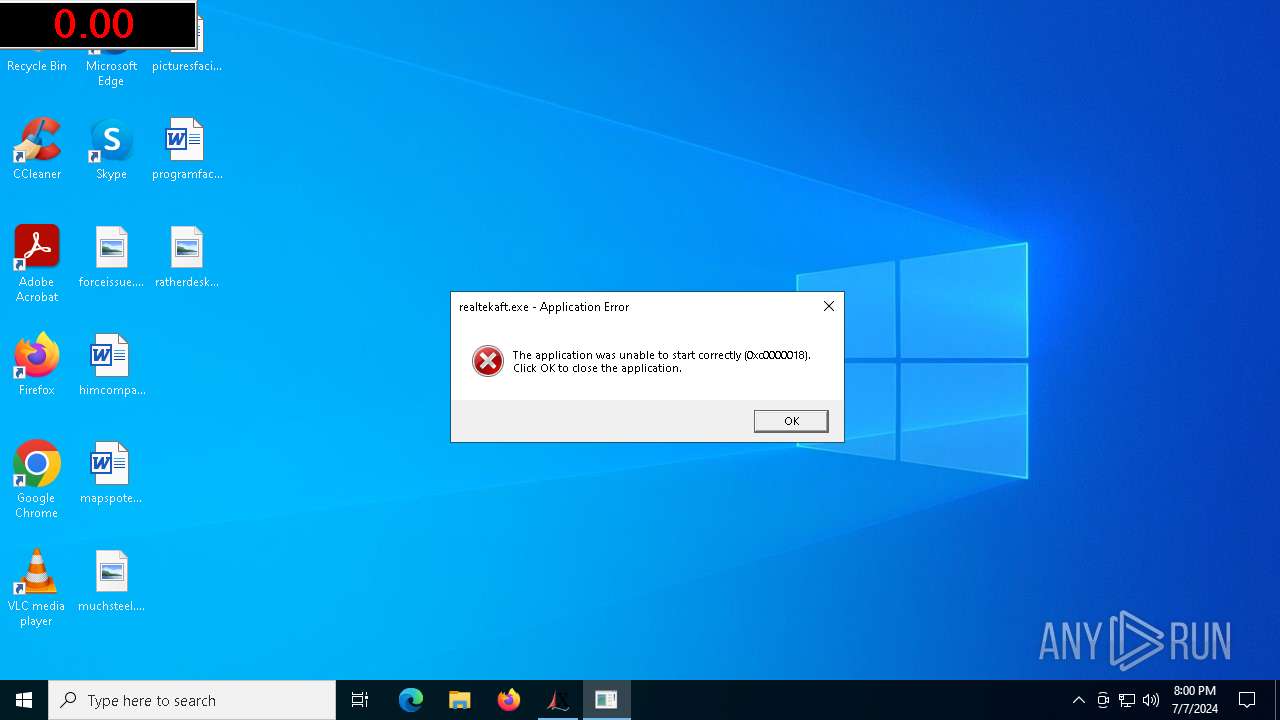
Executes application which crashes
- sapsan.exe (PID: 5912)
- crypt6.exe (PID: 6636)
- 8fc809.exe (PID: 7016)
- Dctooux.exe (PID: 4440)
Starts CMD.EXE for commands execution
- spain.exe (PID: 3716)
- o9Wg44$.exe (PID: 6932)
- stub.exe (PID: 4208)
- dmshell.exe (PID: 4020)
- lrthijawd.exe (PID: 6556)
Loads Python modules
- spain.exe (PID: 3716)
- stub.exe (PID: 4208)
- PresentationFontCache.exe (PID: 6340)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- intalls555.exe (PID: 6652)
- IerLRtXpEcMnUjz.exe (PID: 5884)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1068)
The process drops Mozilla's DLL files
- o9Wg44$.exe (PID: 6932)
Checks Windows Trust Settings
- PACKAGE_DEMO.exe (PID: 2060)
Checks for external IP
- PACKAGE_DEMO.exe (PID: 2060)
The process connected to a server suspected of theft
- PACKAGE_DEMO.exe (PID: 2060)
Starts POWERSHELL.EXE for commands execution
- hv.exe (PID: 6556)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- rundll32.exe (PID: 2012)
- rundll32.exe (PID: 6600)
- rundll32.exe (PID: 6944)
Get information on the list of running processes
- stub.exe (PID: 4208)
The process creates files with name similar to system file names
- IerLRtXpEcMnUjz.exe (PID: 3580)
- 4363463463464363463463463.exe (PID: 6420)
- IerLRtXpEcMnUjz.exe (PID: 5884)
Script adds exclusion path to Windows Defender
- IerLRtXpEcMnUjz.exe (PID: 3580)
- IerLRtXpEcMnUjz.exe (PID: 5884)
Script adds exclusion process to Windows Defender
- IerLRtXpEcMnUjz.exe (PID: 5884)
Starts itself from another location
- 8fc809.exe (PID: 7016)
- amadka.exe (PID: 6404)
Reads the BIOS version
- amadka.exe (PID: 6404)
- explorti.exe (PID: 6020)
Uses NETSH.EXE to obtain data on the network
- rundll32.exe (PID: 2012)
- rundll32.exe (PID: 6600)
- rundll32.exe (PID: 6944)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 5100)
- rundll32.exe (PID: 1220)
- rundll32.exe (PID: 7096)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 5284)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 2632)
- powershell.exe (PID: 1616)
Executing commands from a ".bat" file
- lrthijawd.exe (PID: 6556)
Found regular expressions for crypto-addresses (YARA)
- IerLRtXpEcMnUjz.exe (PID: 5884)
INFO
Checks supported languages
- 4363463463464363463463463.exe (PID: 6420)
- zxcvb.exe (PID: 6744)
- DownSysSoft.exe (PID: 7140)
- BLueHvffhw.exe (PID: 6820)
- zxcvb.exe (PID: 6848)
- BLueHvffhw.exe (PID: 6892)
- native.exe (PID: 6436)
- zxcvb.exe (PID: 6860)
- native.exe (PID: 6452)
- zxcvb.exe (PID: 6872)
- Downdd.exe (PID: 6992)
- spain.exe (PID: 4980)
- intalls555.exe (PID: 6652)
- 8$gs3AYhd.exe (PID: 3164)
- sapsan.exe (PID: 5912)
- 8$gs3AYhd.exe (PID: 4820)
- 5P%9(QJ.exe (PID: 608)
- 5P%9(QJ.exe (PID: 4264)
- spain.exe (PID: 3716)
- native.exe (PID: 3168)
- native.exe (PID: 3584)
- o9Wg44$.exe (PID: 6760)
- ghjkl.exe (PID: 2356)
- ghjkl.exe (PID: 4372)
- o9Wg44$.exe (PID: 6932)
- OxNbFsL8.exe (PID: 6168)
- OxNbFsL8.exe (PID: 6448)
- MSBuild.exe (PID: 6916)
- MSBuild.exe (PID: 6824)
- asdfg.exe (PID: 5220)
- hv.exe (PID: 6556)
- net.exe (PID: 6440)
- asdfg.exe (PID: 4072)
- net.exe (PID: 4928)
- eW[}J50.exe (PID: 6932)
- eW[}J50.exe (PID: 7140)
- native.exe (PID: 6900)
- FTO{.exe (PID: 5220)
- native.exe (PID: 1572)
- FTO{.exe (PID: 4400)
- Opolis.exe (PID: 1064)
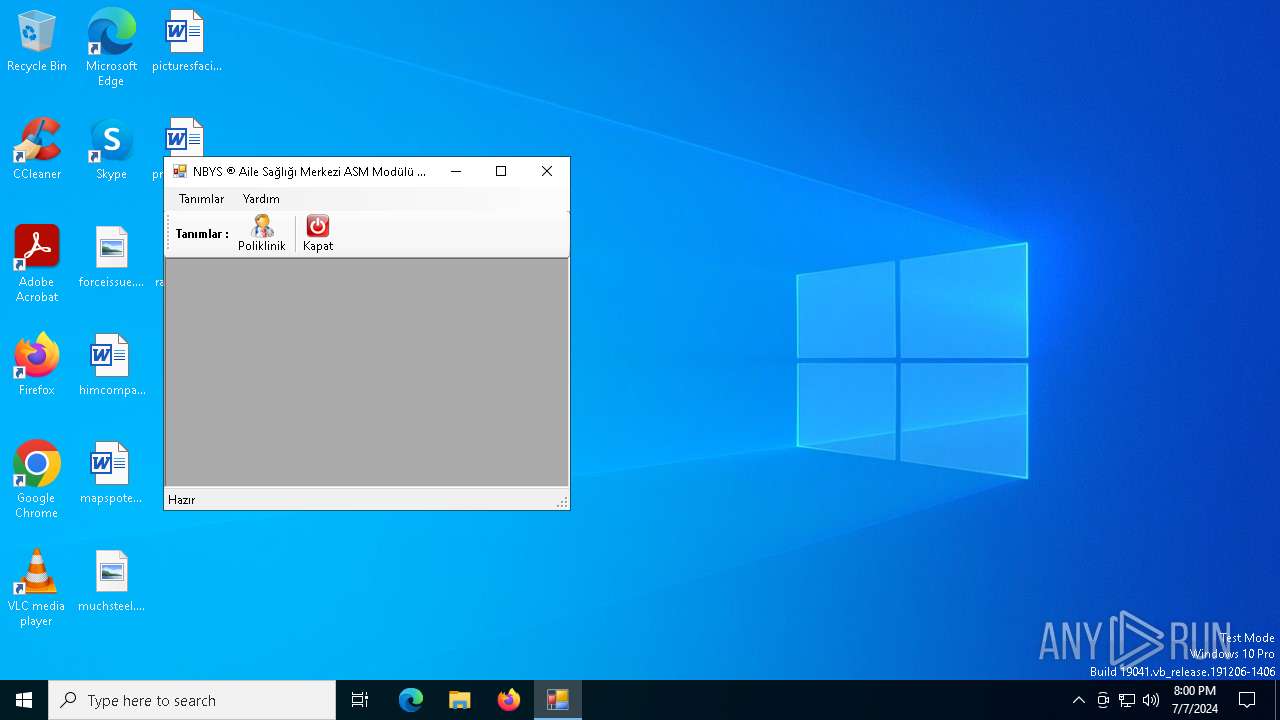
- NBYS%20ASM.NET.exe (PID: 6920)
- PACKAGE_DEMO.exe (PID: 2060)
- taskweaker.exe (PID: 6492)
- crypt6.exe (PID: 6636)
- server.exe (PID: 5220)
- RegAsm.exe (PID: 6436)
- ]%df.exe (PID: 2120)
- ~BC82ZFrr.exe (PID: 7040)
- ]%df.exe (PID: 1992)
- net.exe (PID: 4788)
- jsc.exe (PID: 1672)
- ~BC82ZFrr.exe (PID: 5316)
- net.exe (PID: 3068)
- (_MifxBg$[.exe (PID: 1992)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- DelHosts.exe (PID: 2400)
- (_MifxBg$[.exe (PID: 5880)
- buildjudit.exe (PID: 6880)
- realtekaft.exe (PID: 5872)
- stub.exe (PID: 4208)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- net.exe (PID: 7096)
- net.exe (PID: 6788)
- BitLockerToGo.exe (PID: 3628)
- 8fc809.exe (PID: 7016)
- ghjk.exe (PID: 4764)
- ghjk.exe (PID: 6180)
- 123.exe (PID: 6480)
- pG`jQ0tIj2.exe (PID: 6268)
- pG`jQ0tIj2.exe (PID: 4264)
- Balanza.exe (PID: 5152)
- I{9uGVeaM.exe (PID: 6980)
- I{9uGVeaM.exe (PID: 1828)
- 5d3e8177e87cc.exe (PID: 6684)
- Dctooux.exe (PID: 4440)
- net.exe (PID: 2632)
- net.exe (PID: 2404)
- quickaccesspopup.exe (PID: 2356)
- amadka.exe (PID: 6404)
- Downaqzh.exe (PID: 6248)
- sunset1.exe (PID: 188)
- explorti.exe (PID: 6020)
- {N1tA.exe (PID: 3716)
- {N1tA.exe (PID: 5104)
- qtN49E].exe (PID: 6176)
- r459`GR~h.exe (PID: 6564)
- r459`GR~h.exe (PID: 6256)
- 7TP.exe (PID: 6224)
- 7TP.exe (PID: 6768)
- BitLockerToGo.exe (PID: 2112)
- crazyCore.exe (PID: 3884)
- lrthijawd.exe (PID: 6556)
- PresentationFontCache.exe (PID: 6340)
- PresentationFontCache.exe (PID: 2056)
- work.exe (PID: 7020)
- jergs.exe (PID: 7140)
- ShellExperienceHost.exe (PID: 1648)
- qtN49E].exe (PID: 6768)
Reads the computer name
- 4363463463464363463463463.exe (PID: 6420)
- zxcvb.exe (PID: 6744)
- BLueHvffhw.exe (PID: 6820)
- zxcvb.exe (PID: 6848)
- BLueHvffhw.exe (PID: 6892)
- DownSysSoft.exe (PID: 7140)
- native.exe (PID: 6436)
- native.exe (PID: 6452)
- zxcvb.exe (PID: 6860)
- zxcvb.exe (PID: 6872)
- spain.exe (PID: 4980)
- intalls555.exe (PID: 6652)
- 8$gs3AYhd.exe (PID: 3164)
- sapsan.exe (PID: 5912)
- 8$gs3AYhd.exe (PID: 4820)
- spain.exe (PID: 3716)
- 5P%9(QJ.exe (PID: 4264)
- native.exe (PID: 3168)
- native.exe (PID: 3584)
- o9Wg44$.exe (PID: 6760)
- o9Wg44$.exe (PID: 6932)
- ghjkl.exe (PID: 2356)
- OxNbFsL8.exe (PID: 6168)
- OxNbFsL8.exe (PID: 6448)
- MSBuild.exe (PID: 6916)
- ghjkl.exe (PID: 4372)
- MSBuild.exe (PID: 6824)
- asdfg.exe (PID: 4072)
- asdfg.exe (PID: 5220)
- hv.exe (PID: 6556)
- net.exe (PID: 4928)
- eW[}J50.exe (PID: 7140)
- eW[}J50.exe (PID: 6932)
- net.exe (PID: 6440)
- FTO{.exe (PID: 5220)
- native.exe (PID: 6900)
- native.exe (PID: 1572)
- Opolis.exe (PID: 1064)
- FTO{.exe (PID: 4400)
- NBYS%20ASM.NET.exe (PID: 6920)
- PACKAGE_DEMO.exe (PID: 2060)
- server.exe (PID: 5220)
- RegAsm.exe (PID: 6436)
- ~BC82ZFrr.exe (PID: 7040)
- ]%df.exe (PID: 1992)
- net.exe (PID: 4788)
- jsc.exe (PID: 1672)
- ~BC82ZFrr.exe (PID: 5316)
- net.exe (PID: 3068)
- (_MifxBg$[.exe (PID: 5880)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- (_MifxBg$[.exe (PID: 1992)
- realtekaft.exe (PID: 5872)
- buildjudit.exe (PID: 6880)
- net.exe (PID: 7096)
- net.exe (PID: 6788)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- ghjk.exe (PID: 4764)
- ghjk.exe (PID: 6180)
- 8fc809.exe (PID: 7016)
- 123.exe (PID: 6480)
- pG`jQ0tIj2.exe (PID: 6268)
- pG`jQ0tIj2.exe (PID: 4264)
- Balanza.exe (PID: 5152)
- I{9uGVeaM.exe (PID: 6980)
- I{9uGVeaM.exe (PID: 1828)
- 5d3e8177e87cc.exe (PID: 6684)
- Dctooux.exe (PID: 4440)
- net.exe (PID: 2632)
- net.exe (PID: 2404)
- amadka.exe (PID: 6404)
- Downaqzh.exe (PID: 6248)
- sunset1.exe (PID: 188)
- explorti.exe (PID: 6020)
- {N1tA.exe (PID: 3716)
- {N1tA.exe (PID: 5104)
- qtN49E].exe (PID: 6768)
- qtN49E].exe (PID: 6176)
- r459`GR~h.exe (PID: 6564)
- r459`GR~h.exe (PID: 6256)
- 7TP.exe (PID: 6224)
- 7TP.exe (PID: 6768)
- BitLockerToGo.exe (PID: 2112)
- BitLockerToGo.exe (PID: 3628)
- crazyCore.exe (PID: 3884)
- lrthijawd.exe (PID: 6556)
- PresentationFontCache.exe (PID: 2056)
- work.exe (PID: 7020)
- jergs.exe (PID: 7140)
- PresentationFontCache.exe (PID: 6340)
- ShellExperienceHost.exe (PID: 1648)
Reads Environment values
- 4363463463464363463463463.exe (PID: 6420)
- intalls555.exe (PID: 6652)
- o9Wg44$.exe (PID: 6932)
- eW[}J50.exe (PID: 6932)
- jsc.exe (PID: 1672)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- 8fc809.exe (PID: 7016)
- pG`jQ0tIj2.exe (PID: 4264)
- 123.exe (PID: 6480)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- Dctooux.exe (PID: 4440)
- amadka.exe (PID: 6404)
- {N1tA.exe (PID: 5104)
- r459`GR~h.exe (PID: 6256)
- explorti.exe (PID: 6020)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 6420)
- zxcvb.exe (PID: 6744)
- BLueHvffhw.exe (PID: 6820)
- BLueHvffhw.exe (PID: 6892)
- zxcvb.exe (PID: 6860)
- native.exe (PID: 6436)
- 8$gs3AYhd.exe (PID: 3164)
- 8$gs3AYhd.exe (PID: 4820)
- 5P%9(QJ.exe (PID: 4264)
- intalls555.exe (PID: 6652)
- native.exe (PID: 3168)
- o9Wg44$.exe (PID: 6760)
- o9Wg44$.exe (PID: 6932)
- ghjkl.exe (PID: 2356)
- OxNbFsL8.exe (PID: 6168)
- OxNbFsL8.exe (PID: 6448)
- MSBuild.exe (PID: 6916)
- MSBuild.exe (PID: 6824)
- asdfg.exe (PID: 4072)
- net.exe (PID: 6440)
- eW[}J50.exe (PID: 7140)
- eW[}J50.exe (PID: 6932)
- native.exe (PID: 6900)
- FTO{.exe (PID: 4400)
- FTO{.exe (PID: 5220)
- PACKAGE_DEMO.exe (PID: 2060)
- NBYS%20ASM.NET.exe (PID: 6920)
- RegAsm.exe (PID: 6436)
- ]%df.exe (PID: 1992)
- server.exe (PID: 5220)
- ~BC82ZFrr.exe (PID: 7040)
- ~BC82ZFrr.exe (PID: 5316)
- hv.exe (PID: 6556)
- jsc.exe (PID: 1672)
- net.exe (PID: 3068)
- (_MifxBg$[.exe (PID: 5880)
- (_MifxBg$[.exe (PID: 1992)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- realtekaft.exe (PID: 5872)
- stub.exe (PID: 4208)
- net.exe (PID: 7096)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- ghjk.exe (PID: 4764)
- 123.exe (PID: 6480)
- pG`jQ0tIj2.exe (PID: 6268)
- pG`jQ0tIj2.exe (PID: 4264)
- I{9uGVeaM.exe (PID: 6980)
- I{9uGVeaM.exe (PID: 1828)
- net.exe (PID: 2404)
- {N1tA.exe (PID: 3716)
- {N1tA.exe (PID: 5104)
- qtN49E].exe (PID: 6768)
- qtN49E].exe (PID: 6176)
- r459`GR~h.exe (PID: 6564)
- r459`GR~h.exe (PID: 6256)
- 7TP.exe (PID: 6224)
- 7TP.exe (PID: 6768)
- crazyCore.exe (PID: 3884)
Disables trace logs
- 4363463463464363463463463.exe (PID: 6420)
- intalls555.exe (PID: 6652)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- jsc.exe (PID: 1672)
- IerLRtXpEcMnUjz.exe (PID: 5884)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 6420)
- DownSysSoft.exe (PID: 7140)
- intalls555.exe (PID: 6652)
- WerFault.exe (PID: 6832)
- o9Wg44$.exe (PID: 6932)
- eW[}J50.exe (PID: 6932)
- spain.exe (PID: 3716)
- PACKAGE_DEMO.exe (PID: 2060)
- WerFault.exe (PID: 1852)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- jsc.exe (PID: 1672)
- pG`jQ0tIj2.exe (PID: 4264)
- WerFault.exe (PID: 6592)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- Dctooux.exe (PID: 4440)
- Downaqzh.exe (PID: 6248)
- slui.exe (PID: 1160)
- explorti.exe (PID: 6020)
- rundll32.exe (PID: 2012)
- {N1tA.exe (PID: 5104)
- r459`GR~h.exe (PID: 6256)
- rundll32.exe (PID: 6600)
- rundll32.exe (PID: 6944)
- rundll32.exe (PID: 6840)
- PresentationFontCache.exe (PID: 6340)
- rundll32.exe (PID: 5488)
- rundll32.exe (PID: 6300)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 6420)
- WerFault.exe (PID: 6832)
- intalls555.exe (PID: 6652)
- slui.exe (PID: 6576)
- PACKAGE_DEMO.exe (PID: 2060)
- WerFault.exe (PID: 1852)
- IerLRtXpEcMnUjz.exe (PID: 3580)
- jsc.exe (PID: 1672)
- WerFault.exe (PID: 6592)
- IerLRtXpEcMnUjz.exe (PID: 5884)
- slui.exe (PID: 1160)
Reads mouse settings
- DownSysSoft.exe (PID: 7140)
- Downdd.exe (PID: 6992)
- DelHosts.exe (PID: 2400)
- Downaqzh.exe (PID: 6248)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2272)
- powershell.exe (PID: 6768)
- powershell.exe (PID: 6980)
- powershell.exe (PID: 5104)
- powershell.exe (PID: 5956)
- powershell.exe (PID: 836)
- powershell.exe (PID: 4216)
- powershell.exe (PID: 2044)
- powershell.exe (PID: 4020)
Drops the executable file immediately after the start
- OOBE-Maintenance.exe (PID: 6204)
- OOBE-Maintenance.exe (PID: 7160)
- OOBE-Maintenance.exe (PID: 6748)
- OOBE-Maintenance.exe (PID: 6340)
- OOBE-Maintenance.exe (PID: 1520)
- OOBE-Maintenance.exe (PID: 1140)
- OOBE-Maintenance.exe (PID: 7004)
- OOBE-Maintenance.exe (PID: 2612)
Reads CPU info
- o9Wg44$.exe (PID: 6932)
Process checks computer location settings
- PACKAGE_DEMO.exe (PID: 2060)
- sunset1.exe (PID: 188)
Reads the time zone
- PACKAGE_DEMO.exe (PID: 2060)
Checks operating system version
- stub.exe (PID: 4208)
Creates files in the program directory
- IerLRtXpEcMnUjz.exe (PID: 5884)
- sunset1.exe (PID: 188)
- jergs.exe (PID: 7140)
Reads security settings of Internet Explorer
- rundll32.exe (PID: 2012)
- rundll32.exe (PID: 6600)
- rundll32.exe (PID: 6840)
- rundll32.exe (PID: 6944)
- rundll32.exe (PID: 6300)
- rundll32.exe (PID: 5488)
Reads Microsoft Office registry keys
- sunset1.exe (PID: 188)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 2632)
- powershell.exe (PID: 1616)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5284)
- powershell.exe (PID: 2632)
- powershell.exe (PID: 1616)
.NET Reactor protector has been detected
- MSBuild.exe (PID: 6824)
Themida protector has been detected
- explorti.exe (PID: 6020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
XWorm
(PID) Process(6652) intalls555.exe
C245.74.8.236:5355
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameXWorm V5.6
MutexcEyzqXDyec8SgvAp
(PID) Process(5220) server.exe
C2185.91.127.220:7000
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameUSB.exe
Mutex0liuzqSbSYrrf5nM
(PID) Process(5884) IerLRtXpEcMnUjz.exe
C2127.0.0.1,beshomandotestbesnd.run.place:7000
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameCPA
MutexNaaoYRQUhZUcuIdA
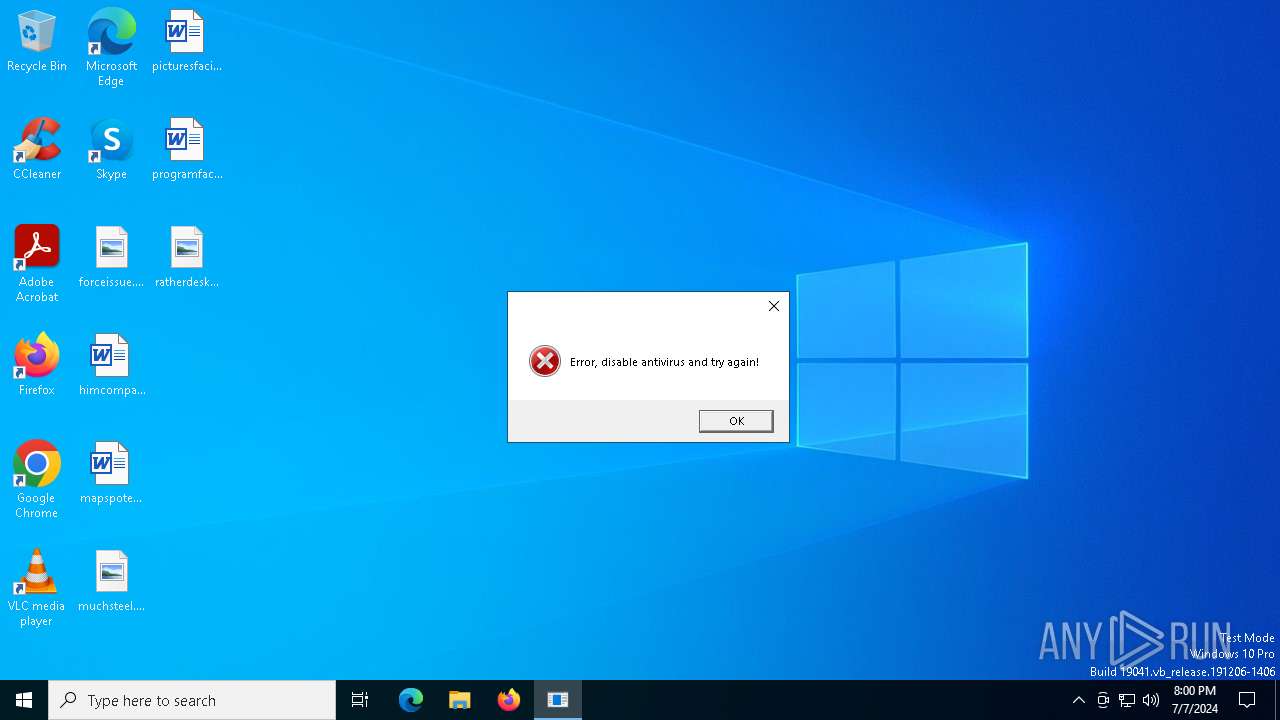
RedLine
(PID) Process(6436) RegAsm.exe
C2 (1)4.185.56.82:42687
BotnetLiveTraffoc
Options
ErrorMessageError, disable antivirus and try again!
Keys
XorUglied
(PID) Process(6480) 123.exe
C2 (1)185.215.113.67:40960
Botnet123
Options
ErrorMessage
Keys
XorSycophancy
Amadey
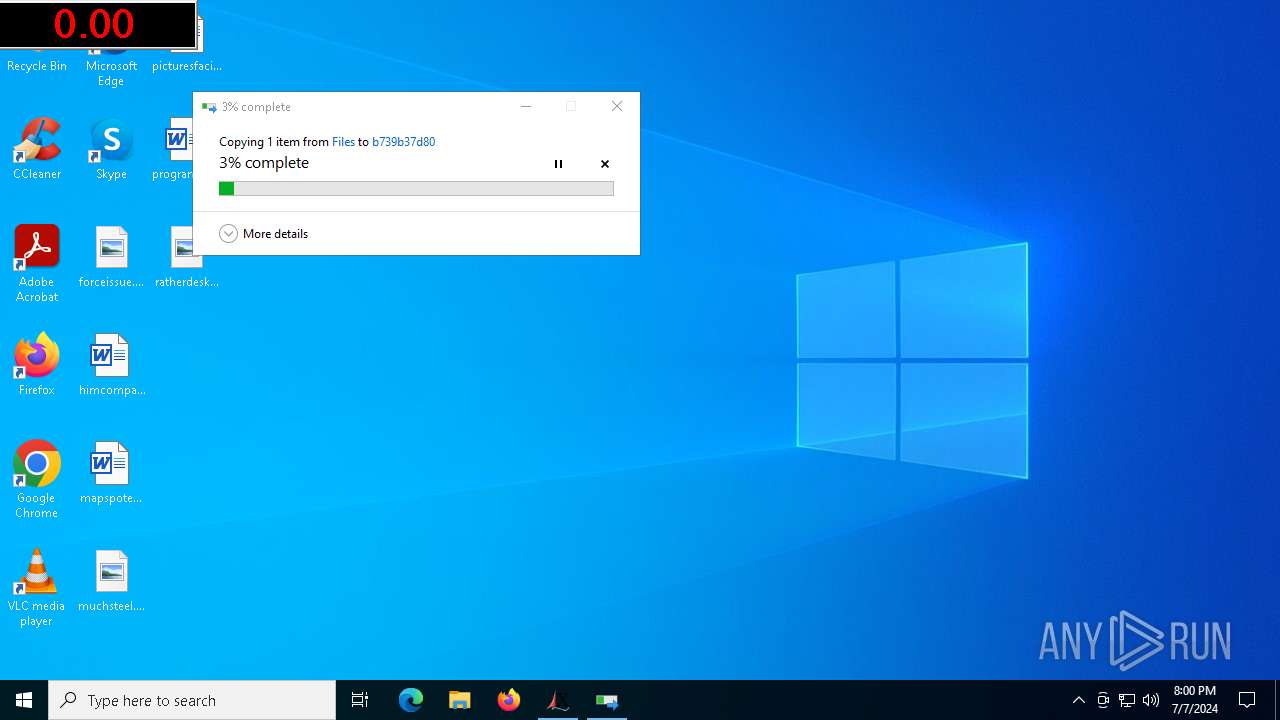
(PID) Process(4440) Dctooux.exe
C2selltix.org
Strings (117)Content-Disposition: form-data; name="data"; filename="
ar:
/k
DefaultSettings.XResolution
SOFTWARE\Microsoft\Windows NT\CurrentVersion
abcdefghijklmnopqrstuvwxyz0123456789-_
random
Norton
rb
sd:
Doctor Web
2022
\0000
id:
#
kernel32.dll
.jpg
AVAST Software
"taskkill /f /im "
nudump.com
lv:
S-%lu-
shutdown -s -t 0
b739b37d80
&& Exit"
e0
ProgramData\
\
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
dm:
pc:
av:
st=s
Kaspersky Lab
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
/forum2/index.php
4.19
Avira
Startup
exe
|
+++
http://
-unicode-
2016
Programs
\App
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
og:
vs:
rundll32
d1
un:
AVG
Bitdefender
Content-Type: application/x-www-form-urlencoded
-%lu
"
Content-Type: application/octet-stream
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
otyt.ru
VideoID
cmd
<c>
ComputerName
Sophos
GetNativeSystemInfo
------
Content-Type: multipart/form-data; boundary=----
Panda Security
" && timeout 1 && del
:::
https://
/forum3/index.php
/forum/index.php
selltix.org
2019
POST
SYSTEM\ControlSet001\Services\BasicDisplay\Video
GET
CurrentBuild
------
bi:
ProductName
"
360TotalSecurity
Powershell.exe
ESET
DefaultSettings.YResolution
%-lu
cmd /C RMDIR /s/q
Dctooux.exe
%USERPROFILE%
ps1
dll
/Plugins/
" && ren
<d>
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
cred.dll|clip.dll|
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
Comodo
&&
Main
wb
rundll32.exe
Rem
os:
shell32.dll
--
WinDefender
?scr=1
0123456789
e1
-executionpolicy remotesigned -File "
=
r=
&unit=
(PID) Process(6020) explorti.exe
C277.91.77.82
URLhttp://77.91.77.82/Hun4Ko/index.php
Version4.30
Options
Drop directoryad40971b6b
Drop nameexplorti.exe
Strings (113)Content-Disposition: form-data; name="data"; filename="
ar:
/k
DefaultSettings.XResolution
SOFTWARE\Microsoft\Windows NT\CurrentVersion
abcdefghijklmnopqrstuvwxyz0123456789-_
random
Norton
rb
sd:
Doctor Web
2022
\0000
id:
/Hun4Ko/index.php
#
kernel32.dll
.jpg
AVAST Software
"taskkill /f /im "
lv:
S-%lu-
shutdown -s -t 0
&& Exit"
e0
ProgramData\
\
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
explorti.exe
dm:
pc:
av:
st=s
Kaspersky Lab
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
Avira
Startup
exe
|
+++
http://
-unicode-
2016
Programs
\App
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
og:
vs:
rundll32
d1
un:
AVG
Bitdefender
Content-Type: application/x-www-form-urlencoded
-%lu
"
Content-Type: application/octet-stream
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
VideoID
cmd
<c>
ComputerName
Sophos
GetNativeSystemInfo
------
77.91.77.82
Content-Type: multipart/form-data; boundary=----
Panda Security
" && timeout 1 && del
:::
https://
2019
POST
4.30
SYSTEM\ControlSet001\Services\BasicDisplay\Video
GET
CurrentBuild
------
bi:
ProductName
"
360TotalSecurity
Powershell.exe
ESET
DefaultSettings.YResolution
%-lu
cmd /C RMDIR /s/q
%USERPROFILE%
ps1
dll
/Plugins/
" && ren
<d>
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
cred.dll|clip.dll|
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
Comodo
&&
Main
wb
rundll32.exe
ad40971b6b
Rem
os:
shell32.dll
--
WinDefender
?scr=1
0123456789
e1
-executionpolicy remotesigned -File "
=
r=
&unit=
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
396
Monitored processes
225
Malicious processes
51
Suspicious processes
9
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Windows\System32\Files\sunset1.exe" | C:\Windows\SysWOW64\Files\sunset1.exe | 4363463463464363463463463.exe | ||||||||||||
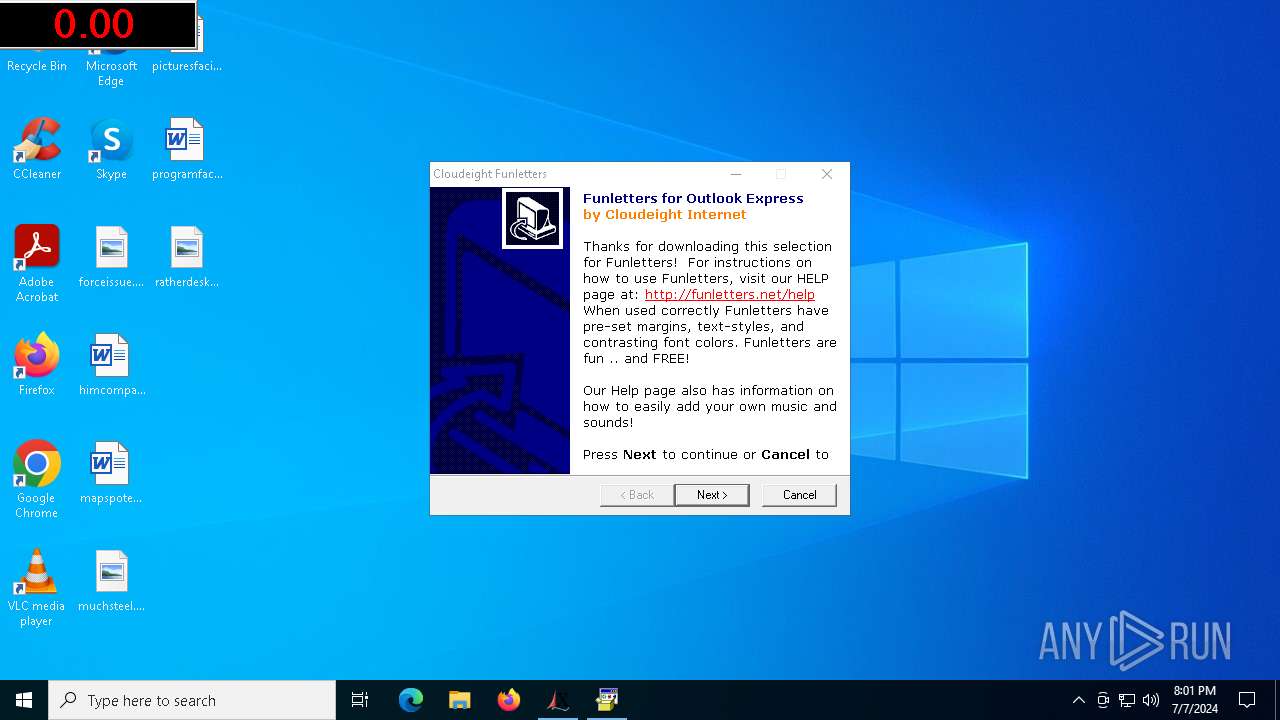
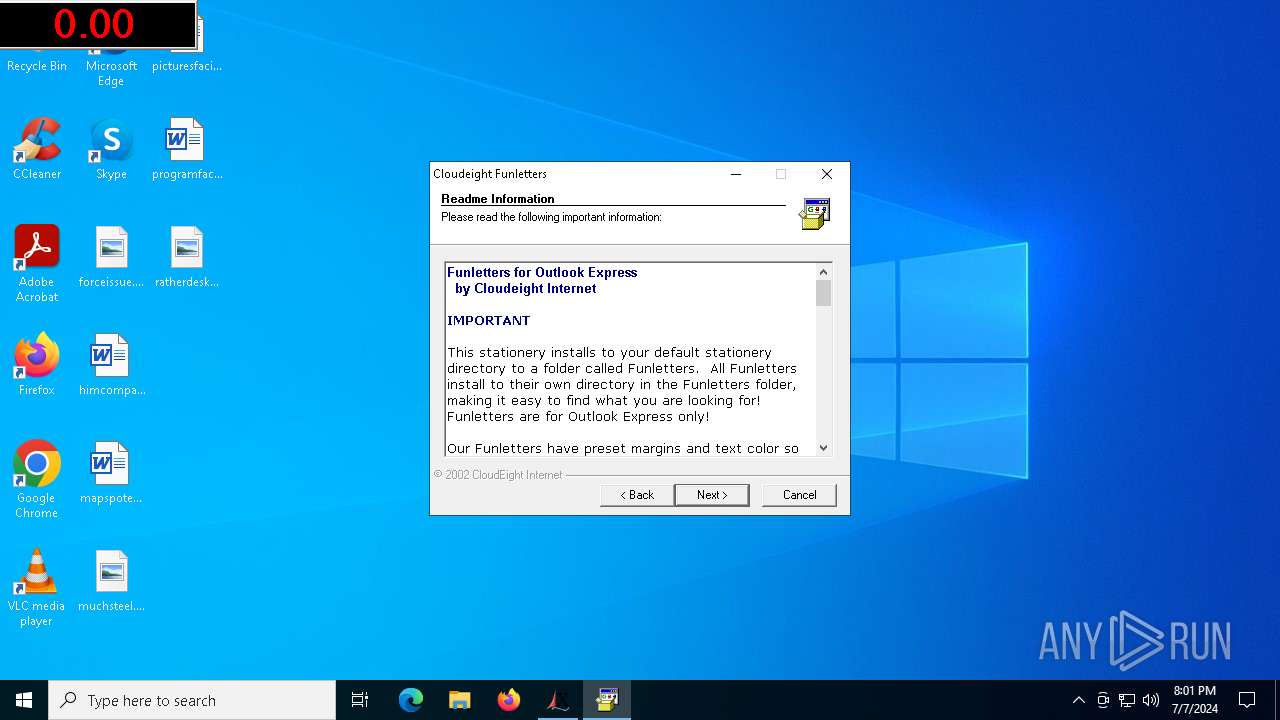
User: Administrator Company: CloudEight Funletters Integrity Level: HIGH Description: Funletters Exit code: 0 Version: 1, 0, 1, 0 Modules
| |||||||||||||||
| 444 | "C:\Windows\SysWOW64\Files\IerLRtXpEcMnUjz.exe" | C:\Windows\SysWOW64\Files\IerLRtXpEcMnUjz.exe | — | IerLRtXpEcMnUjz.exe | |||||||||||
User: Administrator Company: explorer Integrity Level: HIGH Description: explorer Exit code: 4294967295 Version: 1.1.0.0 Modules
| |||||||||||||||
| 480 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 608 | "C:\Users\Administrator\AppData\Local\Microsoft\5P%9(QJ.exe" | C:\Users\Administrator\AppData\Local\Microsoft\5P%9(QJ.exe | — | 5P%9(QJ.exe | |||||||||||
User: Administrator Integrity Level: HIGH Description: AZOIpeigrxzjv Exit code: 3221225477 Version: 1.0.0.0 Modules
| |||||||||||||||
| 740 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4440 -s 972 | C:\Windows\SysWOW64\WerFault.exe | — | Dctooux.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7016 -s 1288 | C:\Windows\SysWOW64\WerFault.exe | — | 8fc809.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Windows\SysWOW64\Files\IerLRtXpEcMnUjz.exe' | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | IerLRtXpEcMnUjz.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | netsh wlan show profiles | C:\Windows\System32\netsh.exe | — | rundll32.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 884 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4440 -s 1520 | C:\Windows\SysWOW64\WerFault.exe | — | Dctooux.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
247 789
Read events
246 824
Write events
863
Delete events
102
Modification events
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6420) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
227
Suspicious files
88
Text files
140
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6420 | 4363463463464363463463463.exe | C:\WINDOWS\SysWOW64\Files\zxcvb.exe | executable | |
MD5:A2A9C309C5300A53D2C2FC41B71B174B | SHA256:7CCFAE8644C3BC7439B88F2DC0DE06BB5082DE09B0BF5E143DE17487FF252224 | |||
| 6420 | 4363463463464363463463463.exe | C:\WINDOWS\SysWOW64\Files\DownSysSoft.exe | executable | |
MD5:50CC1AA14F6C5B5920B72E522297839F | SHA256:1146991BAE4755D762CE256080B8E0618B435F027DD6F872D3106EA665C05050 | |||
| 7140 | DownSysSoft.exe | C:\Users\ADMINI~1\AppData\Local\Temp\List | text | |
MD5:FC23051837F44A36F5E703A468766DBE | SHA256:CCE751048E0D0C230C84F9D95537F34E568D68F80358EC747C5F024EE9926627 | |||
| 2272 | powershell.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_5hqjsxf0.a2l.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6420 | 4363463463464363463463463.exe | C:\WINDOWS\SysWOW64\Files\Downdd.exe | executable | |
MD5:F6BE85B0254A308F77189FC96FA6F38E | SHA256:6DB6A1F73E471E2068A0A420FE6134327171E9A11BBD1A5B360298C5B6A1B069 | |||
| 2272 | powershell.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_df1rrr1j.a4d.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2272 | powershell.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_dl2ytezb.45h.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6892 | BLueHvffhw.exe | C:\Users\Administrator\AppData\Local\Current\shaoexcfj\FallbackBuffer.exe | executable | |
MD5:ABF2DA5B3E7845F50463A72F8B6E6AAA | SHA256:2A4B1AE0AE67CD31F85680E6351BD5B92FF61E246C158DECB1A43A3EF01D9F2C | |||
| 6420 | 4363463463464363463463463.exe | C:\WINDOWS\SysWOW64\Files\native.exe | executable | |
MD5:A2A9C309C5300A53D2C2FC41B71B174B | SHA256:7CCFAE8644C3BC7439B88F2DC0DE06BB5082DE09B0BF5E143DE17487FF252224 | |||
| 2272 | powershell.exe | C:\Users\Administrator\AppData\Local\Temp\__PSScriptPolicyTest_i212moqr.2md.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
231
DNS requests
121
Threats
402
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1764 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
6420 | 4363463463464363463463463.exe | GET | 200 | 91.215.85.223:80 | http://www.dgkhj.ru/zxcvb.exe | unknown | — | — | unknown |
5524 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
3808 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6420 | 4363463463464363463463463.exe | GET | 200 | 58.23.215.67:8765 | http://58.23.215.67:8765/DownSysSoft.exe | unknown | — | — | unknown |
6420 | 4363463463464363463463463.exe | GET | 200 | 91.215.85.223:80 | http://ns2.timekeeper.ug/native.exe | unknown | — | — | unknown |
7140 | DownSysSoft.exe | GET | 200 | 58.23.215.23:8765 | http://wieie.cn:8765/Down/List | unknown | — | — | unknown |
4296 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6420 | 4363463463464363463463463.exe | GET | 200 | 91.215.85.223:80 | http://www.triathlethe.ug/zxcvb.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3676 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2064 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4656 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | unknown |
4656 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1764 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1764 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1060 | svchost.exe | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
3040 | OfficeClickToRun.exe | 52.111.227.11:443 | nexusrules.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
www.dgkhj.ru |
| unknown |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6420 | 4363463463464363463463463.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 13 |
6420 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6420 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6420 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6420 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6420 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6420 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6420 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6420 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7140 | DownSysSoft.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
56 ETPRO signatures available at the full report
Process | Message |
|---|---|
amadka.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
explorti.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|