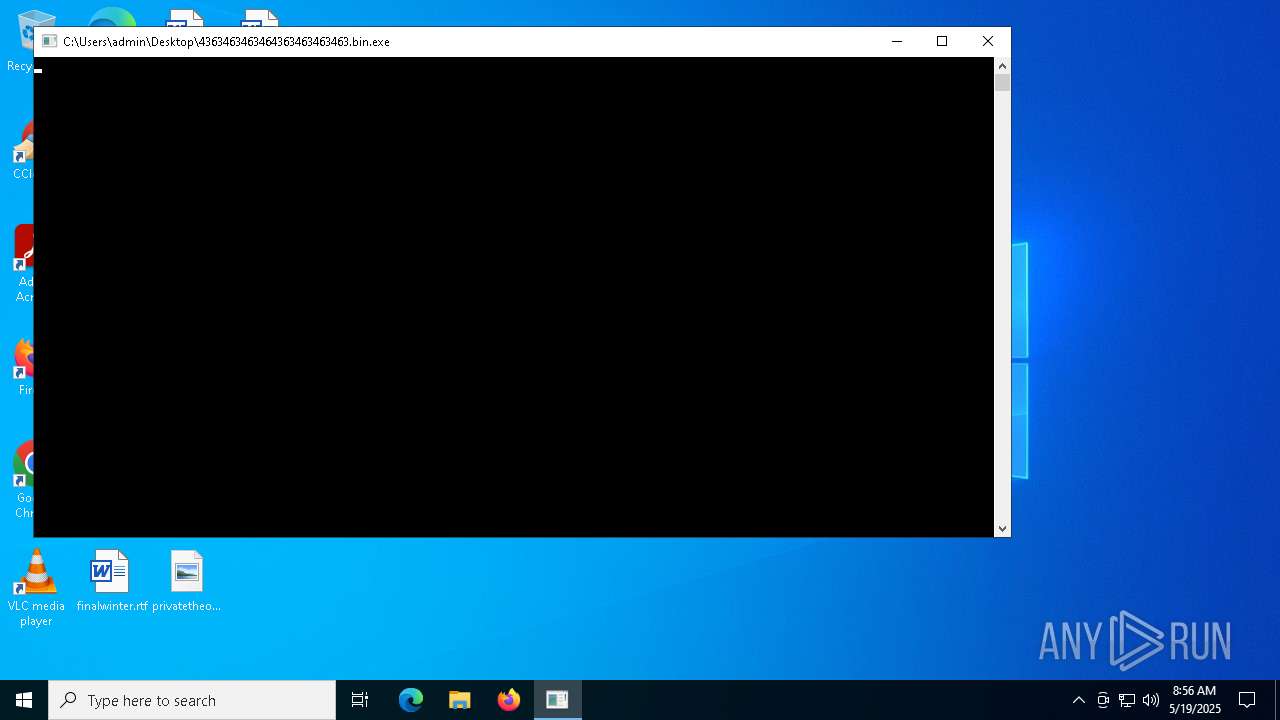
| File name: | 4363463463464363463463463.bin |
| Full analysis: | https://app.any.run/tasks/d6d2bf63-d7cb-420b-ba42-23aa8cb991e5 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 19, 2025, 08:56:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 2288)
QUASARRAT has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
- Quas_Brout_ncrypt.exe (PID: 2096)
- Client-built.exe (PID: 5936)
Uses Task Scheduler to autorun other applications
- Clients.exe (PID: 5352)
- Quas_Brout_ncrypt.exe (PID: 2096)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- Clients.exe (PID: 4200)
- cmd.exe (PID: 6852)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 1764)
- Clients.exe (PID: 7216)
- Client-built.exe (PID: 5936)
- Clients.exe (PID: 7964)
- Client.exe (PID: 7576)
- Clients.exe (PID: 7284)
- XtuService.exe (PID: 8780)
- XtuService.exe (PID: 8460)
- cmd.exe (PID: 9108)
- Clients.exe (PID: 9080)
- Clients.exe (PID: 3620)
- Clients.exe (PID: 9876)
- Clients.exe (PID: 10344)
- Clients.exe (PID: 12172)
- Clients.exe (PID: 3344)
Create files in the Startup directory
- server.exe (PID: 5400)
- ckjg.exe (PID: 900)
- Bloxflip%20Predictor.exe (PID: 2092)
Connects to the CnC server
- server.exe (PID: 5400)
- svchost.exe (PID: 2196)
- SearchUII.exe (PID: 1004)
NJRAT has been detected (SURICATA)
- server.exe (PID: 5400)
- SearchUII.exe (PID: 1004)
NJRAT has been detected (YARA)
- server.exe (PID: 5400)
- Bloxflip Predictor.exe (PID: 4228)
ASYNCRAT has been detected (YARA)
- ckjg.exe (PID: 900)
- Windows.exe (PID: 1388)
ASYNCRAT has been detected (SURICATA)
- ckjg.exe (PID: 900)
NJRAT has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
- Bloxflip%20Predictor.exe (PID: 2092)
- Bloxflip Predictor.exe (PID: 4228)
- 4363463463464363463463463.bin.exe (PID: 6620)
- Client.exe (PID: 7548)
- njrat.exe (PID: 11236)
- svchost.exe (PID: 8624)
- njSilent.exe (PID: 9636)
- Server.exe (PID: 4604)
QUASAR has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 2288)
- Test2.exe (PID: 5512)
Actions looks like stealing of personal data
- k360.exe (PID: 6980)
RAT has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 6620)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4164)
Starts CMD.EXE for self-deleting
- addon2.exe (PID: 968)
Registers / Runs the DLL via REGSVR32.EXE
- esign-app.tmp (PID: 6744)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5588)
- MSBuild.exe (PID: 7540)
- MSBuild.exe (PID: 3896)
- MSBuild.exe (PID: 8596)
Executing a file with an untrusted certificate
- core.exe (PID: 3968)
- sm.exe (PID: 7936)
- _na.exe (PID: 8028)
- inferno.exe (PID: 8140)
- Setup.exe (PID: 6476)
- ChromeSetup.exe (PID: 7800)
- Setup.exe (PID: 4180)
- GoogleUpdate.exe (PID: 7696)
- FOi.exe (PID: 8740)
- td.exe (PID: 9900)
- LatelyStated.2.exe (PID: 9884)
- Kr.NEG.exe (PID: 9372)
- dahuanverguo_kr.exe (PID: 6300)
- dpinst_amd64.exe (PID: 7296)
STEALER has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 6620)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
Stealers network behavior
- svchost.exe (PID: 2196)
GENERIC has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 6620)
- ChromeSetup.exe (PID: 7800)
- 4363463463464363463463463.bin.exe (PID: 6620)
DCRAT has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
ASYNCRAT has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
- Syncing.exe (PID: 7328)
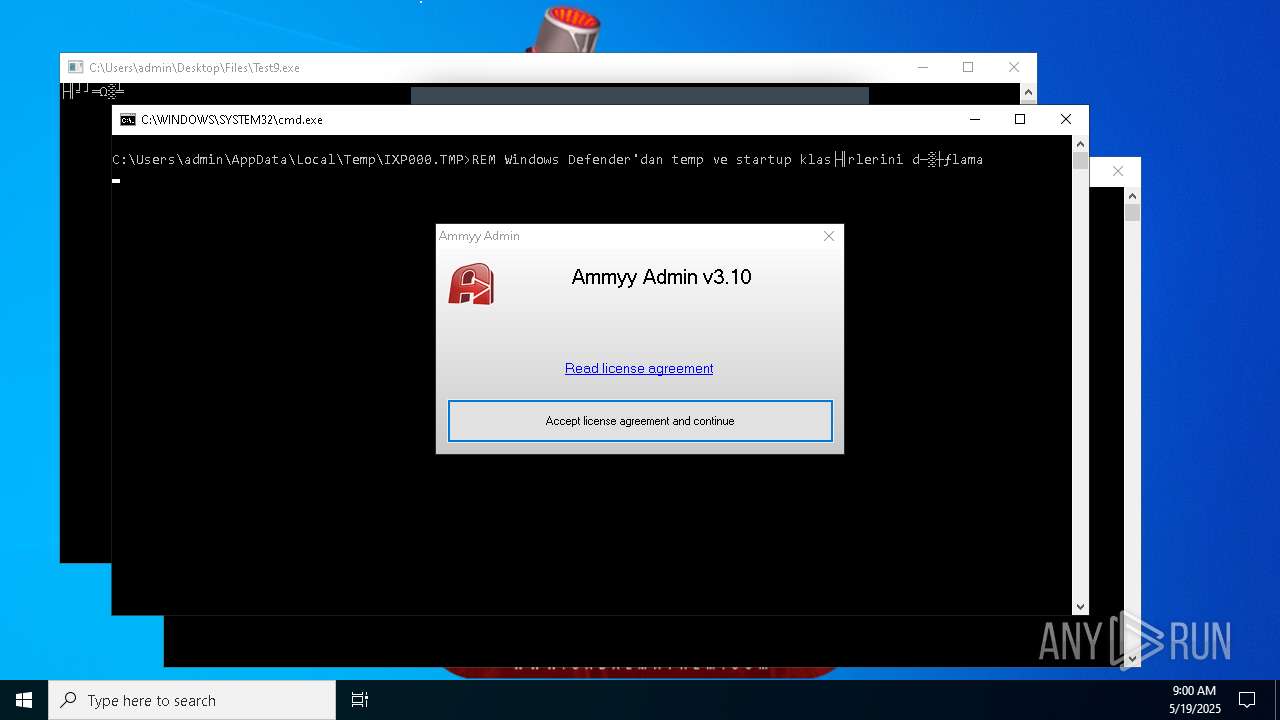
Changes powershell execution policy (Bypass)
- core.exe (PID: 3968)
- Yi-.exe (PID: 10296)
- XClient.exe (PID: 10512)
- jucheck.exe (PID: 3952)
Bypass execution policy to execute commands
- powershell.exe (PID: 9200)
- powershell.exe (PID: 10792)
- powershell.exe (PID: 9592)
- powershell.exe (PID: 2620)
- powershell.exe (PID: 11148)
- powershell.exe (PID: 9112)
Starts REAGENTC.EXE to disable the Windows Recovery Environment
- ReAgentc.exe (PID: 680)
RHADAMANTHYS has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 2288)
GHOSTSOCKS has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
ADESSTEALER has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 6620)
Adds path to the Windows Defender exclusion list
- Yi-.exe (PID: 10296)
- XClient.exe (PID: 10512)
- cmd.exe (PID: 9132)
- jucheck.exe (PID: 3952)
Changes Windows Defender settings
- Yi-.exe (PID: 10296)
- XClient.exe (PID: 10512)
- cmd.exe (PID: 9132)
- jucheck.exe (PID: 3952)
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 512)
Adds process to the Windows Defender exclusion list
- XClient.exe (PID: 10512)
SUSPICIOUS
Reads security settings of Internet Explorer
- 4363463463464363463463463.bin.exe (PID: 6620)
- 99999.exe (PID: 1452)
- Clients.exe (PID: 5352)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- 4363463463464363463463463.bin.exe (PID: 2288)
- Clients.exe (PID: 4200)
- Client.exe (PID: 4000)
Executable content was dropped or overwritten
- 4363463463464363463463463.bin.exe (PID: 6620)
- 99999.exe (PID: 1452)
- Quas_Brout_ncrypt.exe (PID: 2096)
- server.exe (PID: 5400)
- 4363463463464363463463463.bin.exe (PID: 2288)
- Test2.exe (PID: 5512)
- Solara_Protect.exe (PID: 2064)
- Bloxflip%20Predictor.exe (PID: 2092)
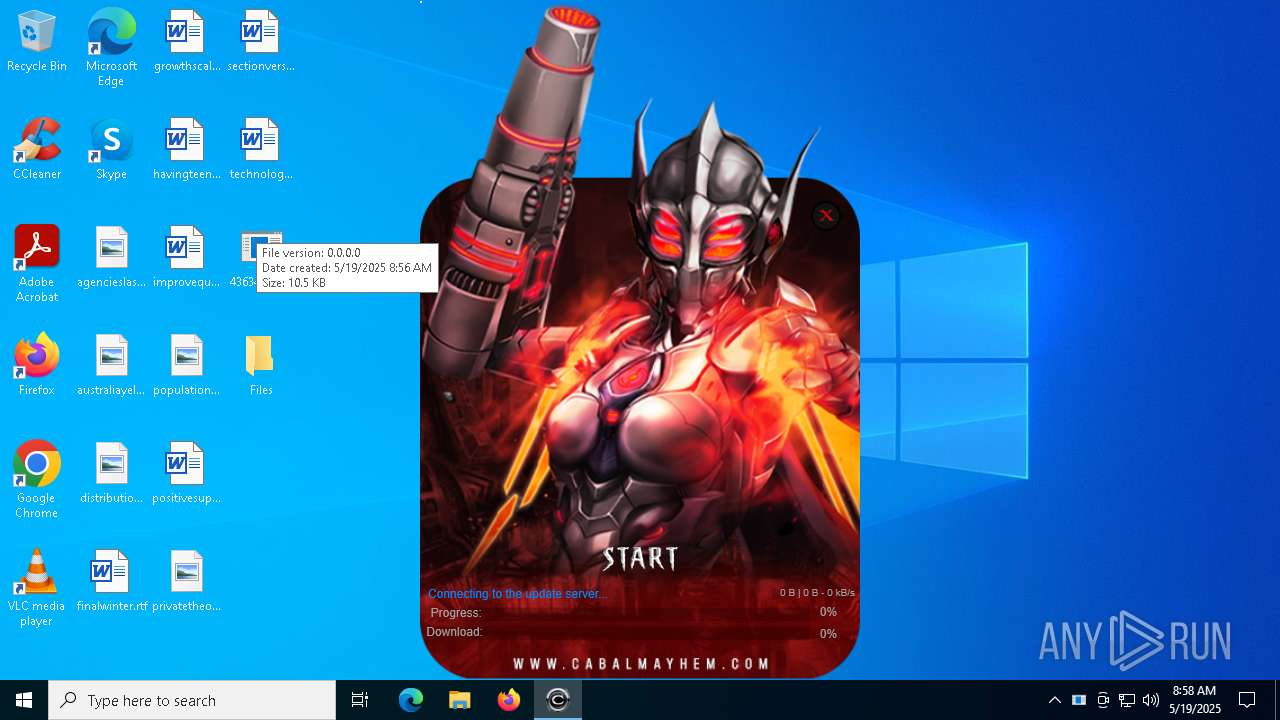
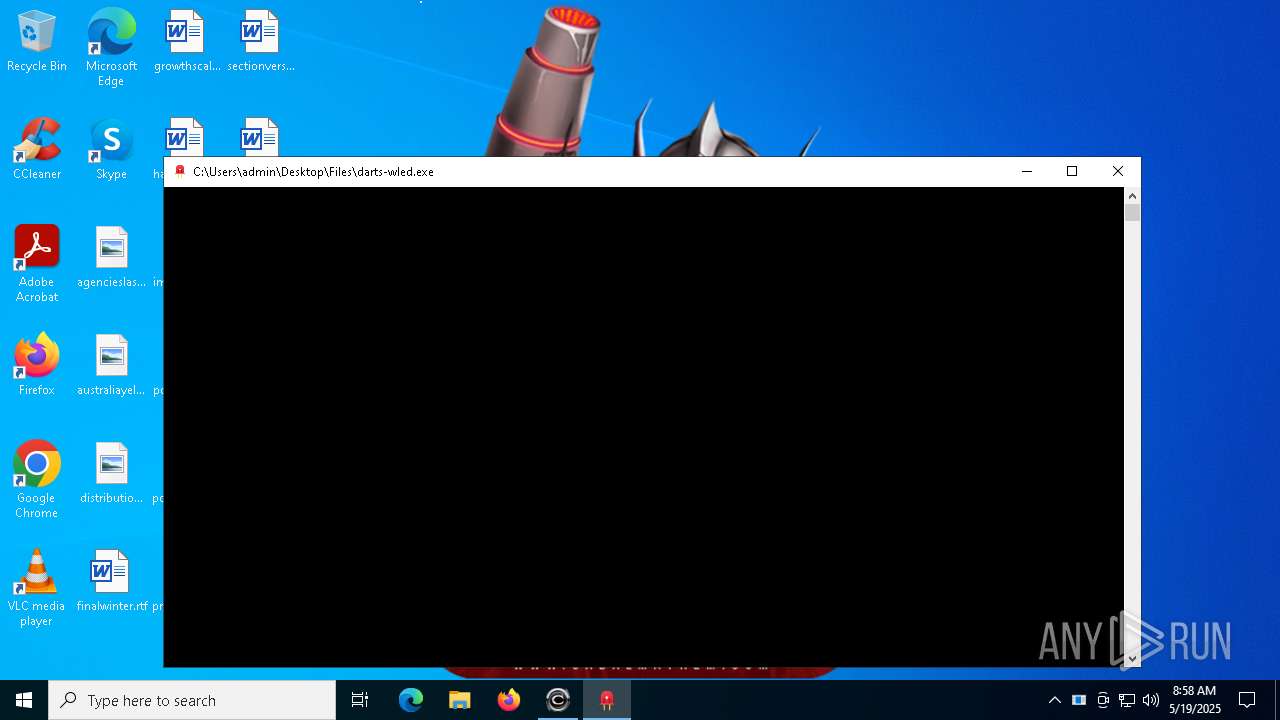
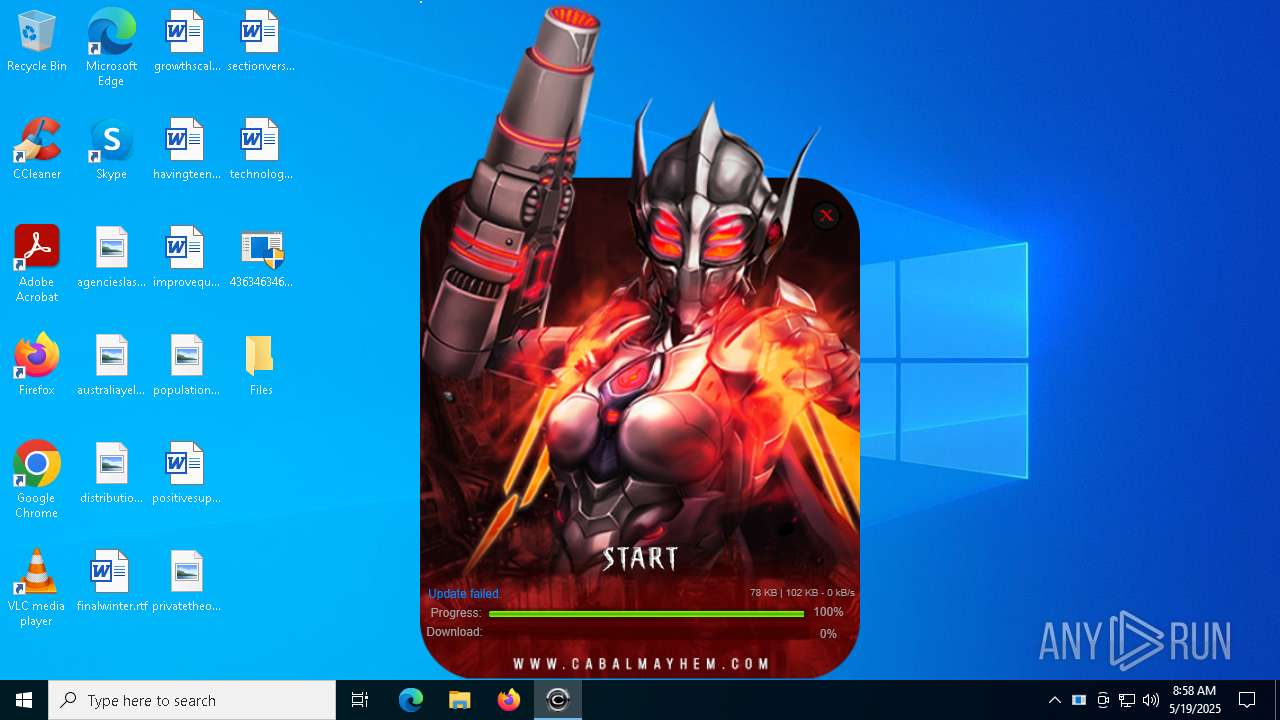
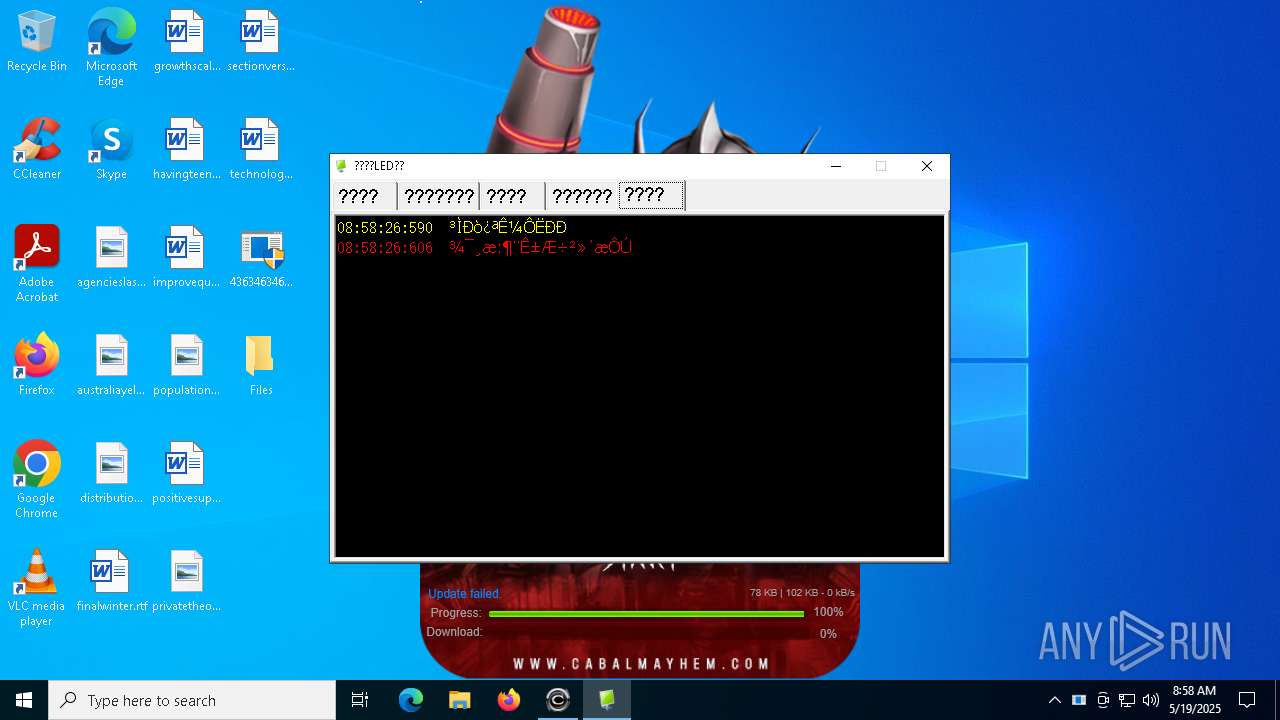
- darts-wled.exe (PID: 6876)
- addon2.exe (PID: 968)
- update.exe (PID: 7152)
- esign-app.exe (PID: 5020)
- Bloxflip Predictor.exe (PID: 4228)
- esign-app.tmp (PID: 6248)
- esign-app.exe (PID: 4164)
- esign-app.tmp (PID: 6744)
- 6.exe (PID: 5892)
- 6.tmp (PID: 5588)
- sm.exe (PID: 7936)
- l.exe (PID: 7876)
- Client-built.exe (PID: 5936)
- WindowsServices.exe (PID: 8112)
- Agentnov.exe (PID: 1676)
- _xj.exe (PID: 7488)
- ChromeSetup.exe (PID: 7800)
- wininit.exe (PID: 7360)
- myapp.exe (PID: 864)
- XtuService.exe (PID: 8460)
- WindowsServices.exe (PID: 2108)
- WinIntoruntime.exe (PID: 8976)
- Syncing.exe (PID: 7328)
- main1.exe (PID: 8652)
- FOi.exe (PID: 8740)
- Client.exe (PID: 7548)
- vncgroups.exe (PID: 9540)
- taskmoder.exe (PID: 9724)
- rah.exe (PID: 9288)
- p5Y.exe (PID: 7372)
- hyperWeb.exe (PID: 9920)
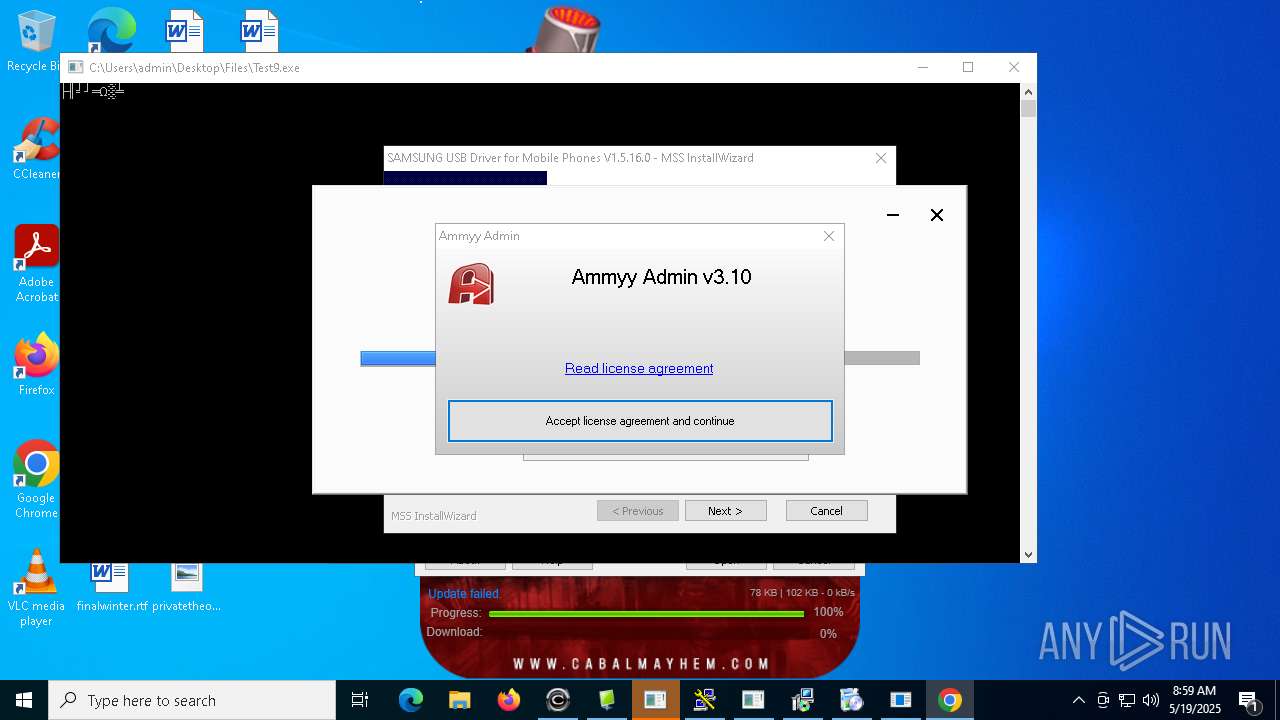
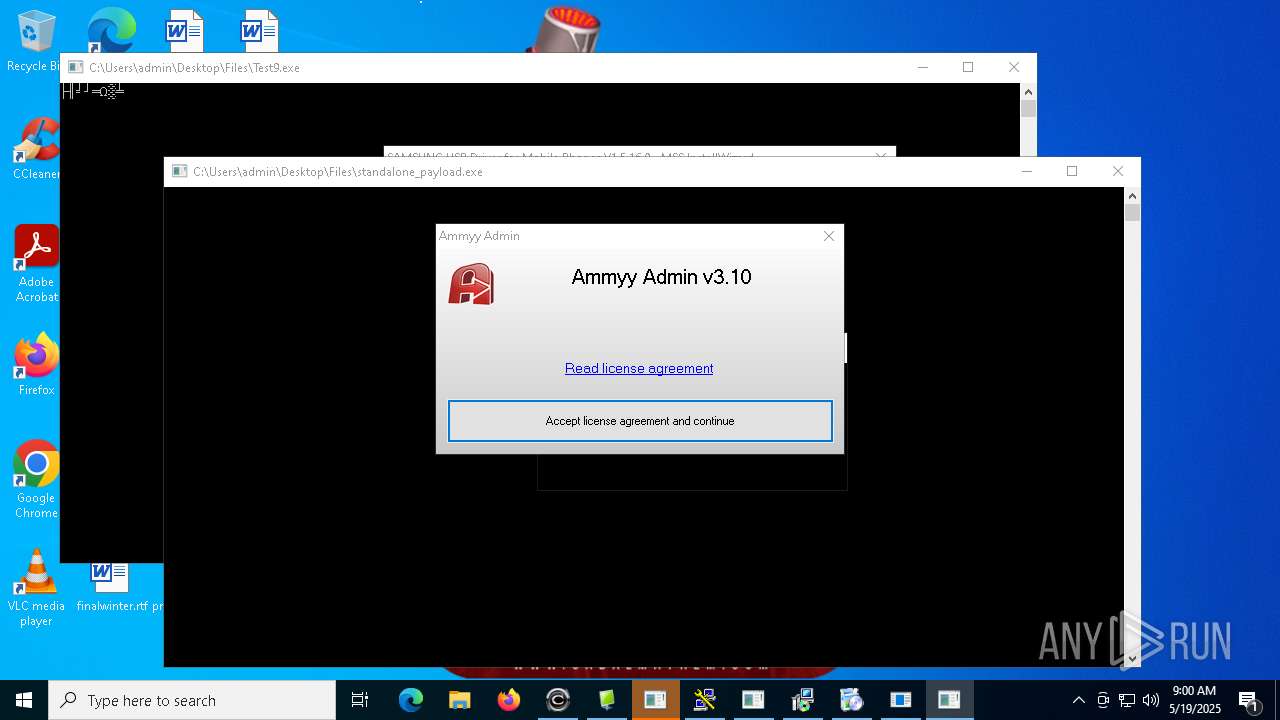
- standalone_payload.exe (PID: 5740)
- td.exe (PID: 9900)
- Yi-.exe (PID: 10296)
- NOTallowedtocrypt.exe (PID: 10832)
- njrat.exe (PID: 11236)
- Kr.NEG.exe (PID: 9372)
- dahuanverguo_kr.exe (PID: 6300)
- njSilent.exe (PID: 9636)
- svchost.exe (PID: 8624)
- 1465810408079_502.exe (PID: 10784)
- rlol.tmp (PID: 11420)
- Server.exe (PID: 4604)
- rlol.exe (PID: 12244)
- 136.0.7103.114_chrome_installer.exe (PID: 4864)
Process requests binary or script from the Internet
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 2288)
- update.exe (PID: 7152)
- svchost.exe (PID: 7764)
- td.exe (PID: 9900)
Starts itself from another location
- 99999.exe (PID: 1452)
- Quas_Brout_ncrypt.exe (PID: 2096)
- Test2.exe (PID: 5512)
- Bloxflip%20Predictor.exe (PID: 2092)
- Client-built.exe (PID: 5936)
- _xj.exe (PID: 7488)
- WindowsServices.exe (PID: 8112)
- wininit.exe (PID: 7360)
- XtuService.exe (PID: 8460)
- Client.exe (PID: 7548)
- vncgroups.exe (PID: 9540)
- rah.exe (PID: 9288)
- NOTallowedtocrypt.exe (PID: 10832)
- njrat.exe (PID: 11236)
- njSilent.exe (PID: 9636)
Connects to the server without a host name
- 4363463463464363463463463.bin.exe (PID: 6620)
- update.exe (PID: 7152)
- 4363463463464363463463463.bin.exe (PID: 2288)
Potential Corporate Privacy Violation
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 2288)
- svchost.exe (PID: 2196)
- update.exe (PID: 7152)
- svchost.exe (PID: 7764)
Starts CMD.EXE for commands execution
- Clients.exe (PID: 5352)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 2392)
- Clients.exe (PID: 4200)
- Client.exe (PID: 4000)
- Solara_Protect.exe (PID: 2064)
- addon2.exe (PID: 968)
- Clients.exe (PID: 4628)
- Client.exe (PID: 4304)
- Client.exe (PID: 5136)
- Clients.exe (PID: 1764)
- Client.exe (PID: 7244)
- Clients.exe (PID: 7216)
- Clients.exe (PID: 7964)
- Client.exe (PID: 7972)
- Clients.exe (PID: 7284)
- Syncing.exe (PID: 7328)
- wscript.exe (PID: 7188)
- Clients.exe (PID: 9080)
- WinIntoruntime.exe (PID: 8976)
- Clients.exe (PID: 3620)
- UserOOBEBroker.exe (PID: 7392)
- Clients.exe (PID: 9876)
- staticfile.exe (PID: 5008)
- wscript.exe (PID: 8352)
- standalone_payload.exe (PID: 5740)
- LatelyStated.2.exe (PID: 9884)
- hyperWeb.exe (PID: 9920)
- NOTallowedtocrypt.exe (PID: 10832)
- CrSpoof.exe (PID: 6908)
- Clients.exe (PID: 10344)
- 76y5trfed675ytg.exe (PID: 8624)
- b4ihfrwq.tyn.scr (PID: 5548)
- staticfile.exe (PID: 10528)
- Clients.exe (PID: 12172)
- staticfile.exe (PID: 11300)
- staticfile.exe (PID: 6600)
Executing commands from a ".bat" file
- Clients.exe (PID: 5352)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 2392)
- Clients.exe (PID: 4628)
- Client.exe (PID: 4000)
- Clients.exe (PID: 4200)
- Solara_Protect.exe (PID: 2064)
- Client.exe (PID: 4304)
- Clients.exe (PID: 4628)
- Client.exe (PID: 5136)
- Clients.exe (PID: 1764)
- Clients.exe (PID: 7216)
- Client.exe (PID: 7244)
- Client.exe (PID: 7972)
- Clients.exe (PID: 7964)
- Clients.exe (PID: 7284)
- wscript.exe (PID: 7188)
- Syncing.exe (PID: 7328)
- Clients.exe (PID: 9080)
- WinIntoruntime.exe (PID: 8976)
- Clients.exe (PID: 3620)
- Clients.exe (PID: 9876)
- staticfile.exe (PID: 5008)
- wscript.exe (PID: 8352)
- LatelyStated.2.exe (PID: 9884)
- hyperWeb.exe (PID: 9920)
- Clients.exe (PID: 10344)
- b4ihfrwq.tyn.scr (PID: 5548)
- CrSpoof.exe (PID: 6908)
- staticfile.exe (PID: 10528)
- staticfile.exe (PID: 11300)
- Clients.exe (PID: 12172)
- staticfile.exe (PID: 6600)
Uses NETSH.EXE to add a firewall rule or allowed programs
- server.exe (PID: 5400)
- SearchUII.exe (PID: 1004)
- Server1.exe (PID: 1512)
- WindowsServices.exe (PID: 2108)
- WindowsServices.exe (PID: 8736)
- fusca%20game.exe (PID: 8760)
- svchost.exe (PID: 8624)
- Server.exe (PID: 4604)
Starts application with an unusual extension
- cmd.exe (PID: 5228)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 864)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 3180)
- cmd.exe (PID: 4868)
- cmd.exe (PID: 5024)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 2908)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 7444)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 8580)
- cmd.exe (PID: 9432)
- cmd.exe (PID: 9764)
- cmd.exe (PID: 10224)
- taskmoder.exe (PID: 9724)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 10496)
- cmd.exe (PID: 6976)
- cmd.exe (PID: 11760)
- cmd.exe (PID: 10760)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 5228)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 864)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 3180)
- cmd.exe (PID: 4868)
- cmd.exe (PID: 5024)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 2908)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 7444)
- cmd.exe (PID: 8580)
- cmd.exe (PID: 9432)
- cmd.exe (PID: 10224)
- cmd.exe (PID: 9764)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 6976)
- cmd.exe (PID: 11760)
Probably fake Windows Update file has been dropped
- server.exe (PID: 5400)
The process creates files with name similar to system file names
- server.exe (PID: 5400)
Creates file in the systems drive root
- server.exe (PID: 5400)
Reads the date of Windows installation
- Clients.exe (PID: 5352)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- Client.exe (PID: 4000)
- Clients.exe (PID: 4200)
Contacting a server suspected of hosting an CnC
- server.exe (PID: 5400)
- ckjg.exe (PID: 900)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5588)
- SearchUII.exe (PID: 1004)
- MSBuild.exe (PID: 7540)
- MSBuild.exe (PID: 3896)
- MSBuild.exe (PID: 8596)
Connects to unusual port
- server.exe (PID: 5400)
- ckjg.exe (PID: 900)
- 4363463463464363463463463.bin.exe (PID: 2288)
- Windows.exe (PID: 1388)
- systempreter.exe (PID: 1324)
- Bloxflip Predictor.exe (PID: 4228)
- SearchUII.exe (PID: 1004)
- Server1.exe (PID: 1512)
- regsvr32.exe (PID: 660)
- CPDB.exe (PID: 8036)
- 4363463463464363463463463.bin.exe (PID: 6620)
- Client.exe (PID: 7576)
- Server.exe (PID: 8136)
- XtuService.exe (PID: 8780)
- sync.exe (PID: 8964)
- idmans.exe (PID: 9844)
- crack.exe (PID: 10960)
- dahuanverguo_kr.exe (PID: 6300)
- SubDir.exe (PID: 9916)
- svchost.exe (PID: 8624)
- dialer.exe (PID: 10676)
- Server.exe (PID: 4604)
Uses WMIC.EXE to obtain computer system information
- ckjg.exe (PID: 900)
Accesses domain name via WMI (SCRIPT)
- WMIC.exe (PID: 6872)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5212)
- cmd.exe (PID: 5740)
- cmd.exe (PID: 9128)
Uses ATTRIB.EXE to modify file attributes
- Bloxflip%20Predictor.exe (PID: 2092)
- Bloxflip Predictor.exe (PID: 4228)
The executable file from the user directory is run by the CMD process
- Windows.exe (PID: 1388)
- Client.exe (PID: 4304)
- Client.exe (PID: 5136)
- Client.exe (PID: 7244)
- Client.exe (PID: 7972)
- Client.exe (PID: 7340)
- WinIntoruntime.exe (PID: 8976)
- staticfile.exe (PID: 5008)
- sync.exe (PID: 8964)
- staticfile.exe (PID: 10528)
- staticfile.exe (PID: 11300)
- staticfile.exe (PID: 6600)
Starts a Microsoft application from unusual location
- addon2.exe (PID: 968)
- ale22.exe (PID: 4488)
- inferno.exe (PID: 8140)
- alee12.exe (PID: 8352)
- CrSpoof.exe (PID: 6908)
- dpinst_amd64.exe (PID: 7296)
Process drops legitimate windows executable
- addon2.exe (PID: 968)
- 4363463463464363463463463.bin.exe (PID: 6620)
- darts-wled.exe (PID: 6876)
- esign-app.tmp (PID: 6248)
- esign-app.tmp (PID: 6744)
- l.exe (PID: 7876)
- 4363463463464363463463463.bin.exe (PID: 2288)
- sm.exe (PID: 7936)
- main1.exe (PID: 8652)
- td.exe (PID: 9900)
- 1465810408079_502.exe (PID: 10784)
- rlol.tmp (PID: 11420)
The process drops C-runtime libraries
- darts-wled.exe (PID: 6876)
- l.exe (PID: 7876)
- main1.exe (PID: 8652)
- td.exe (PID: 9900)
Process drops python dynamic module
- darts-wled.exe (PID: 6876)
- l.exe (PID: 7876)
- main1.exe (PID: 8652)
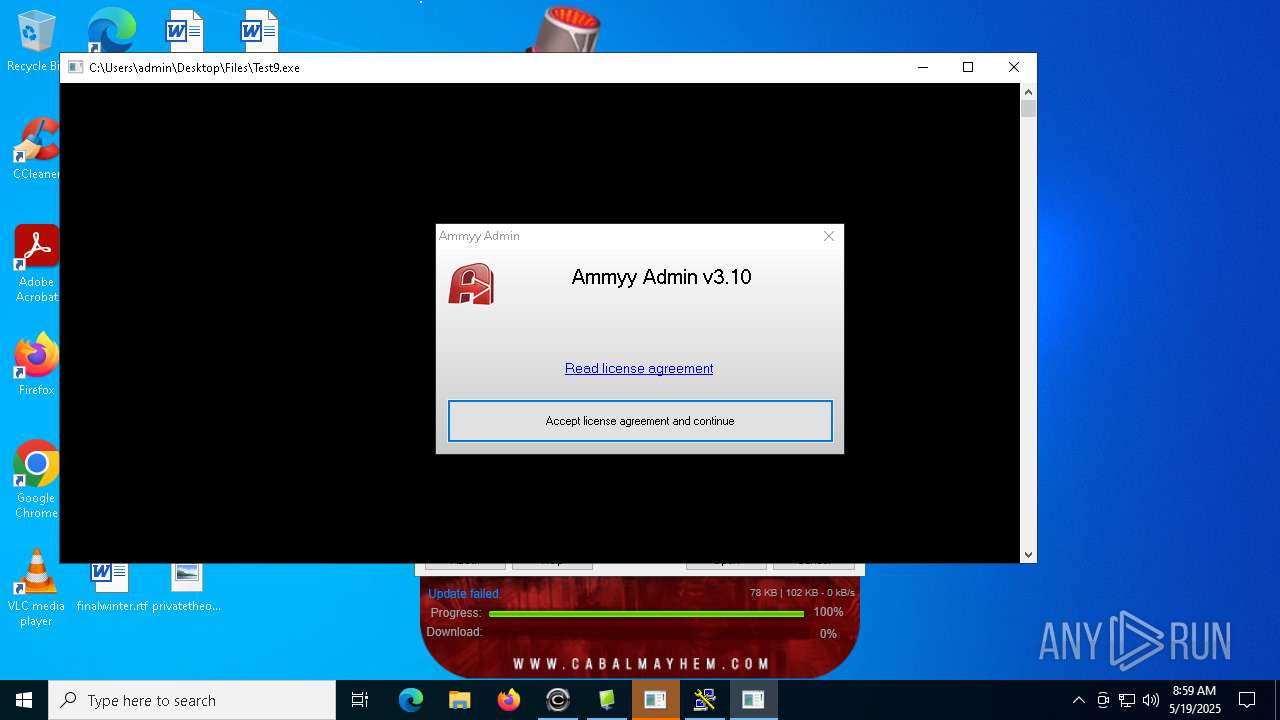
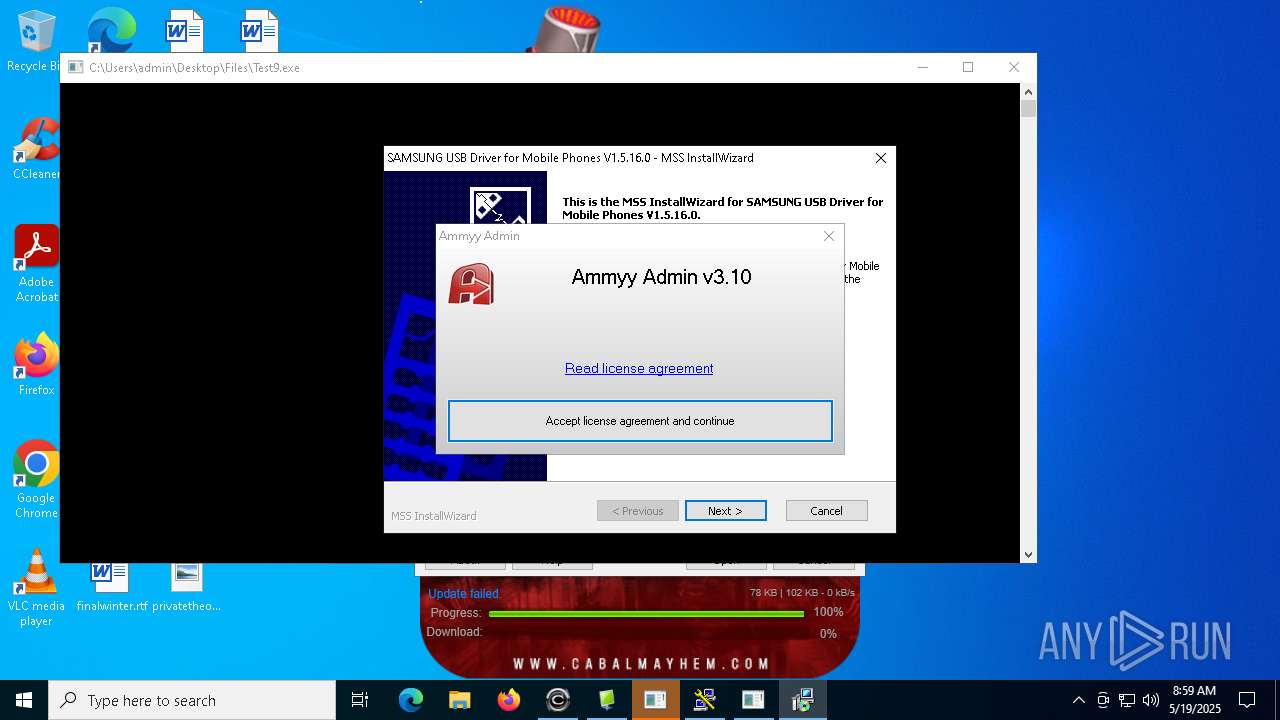
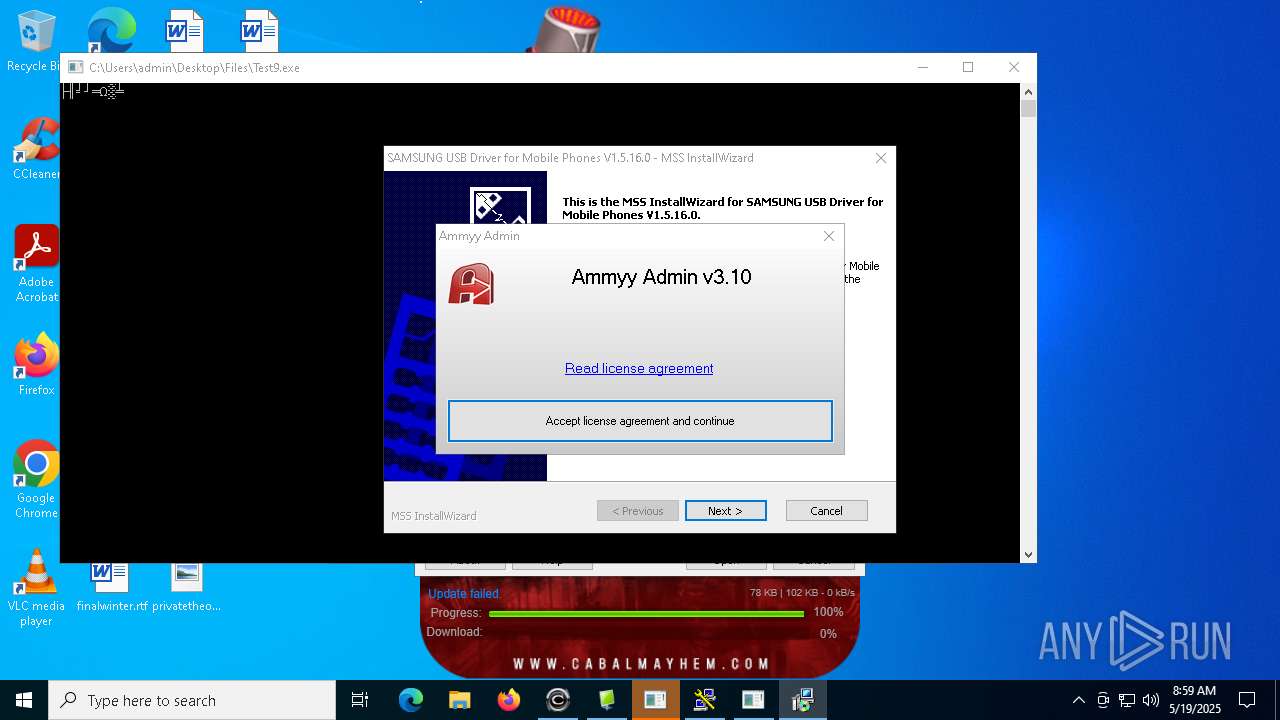
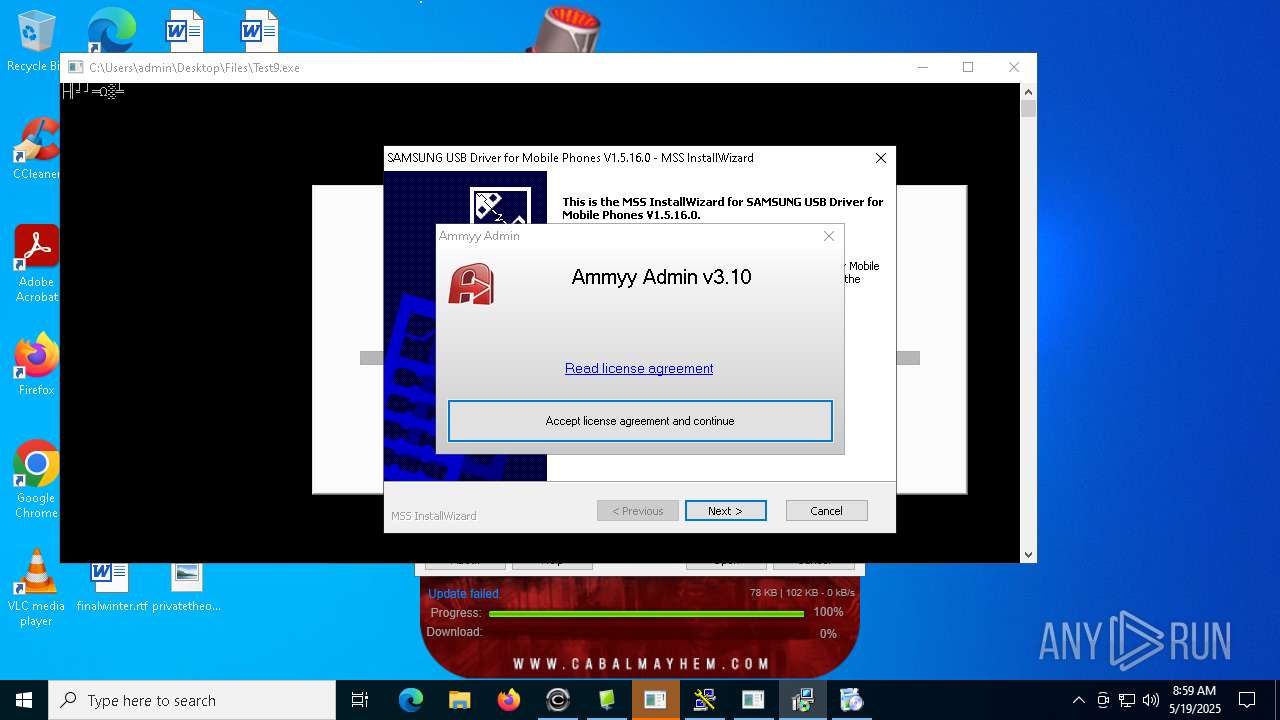
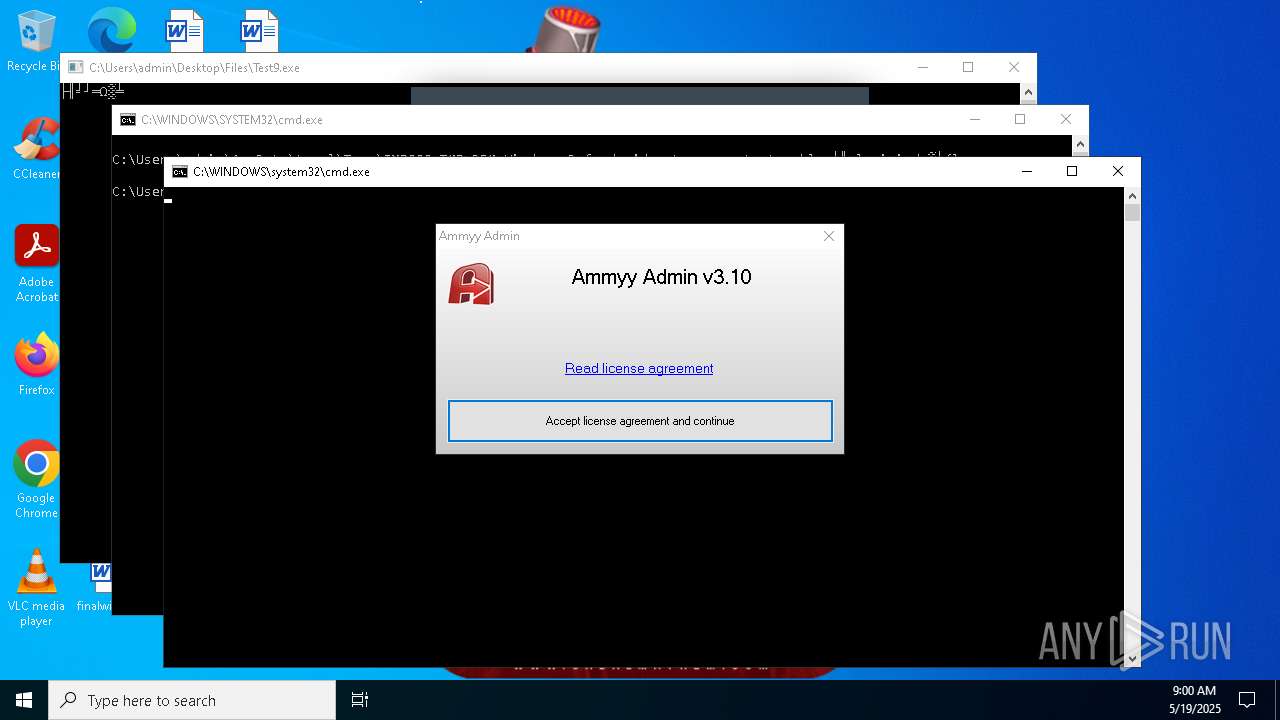
Application launched itself
- darts-wled.exe (PID: 6876)
- AA_v3.exe (PID: 4488)
- l.exe (PID: 7876)
- main1.exe (PID: 8652)
- alex.exe (PID: 9248)
- setup.exe (PID: 11900)
Hides command output
- cmd.exe (PID: 5740)
Starts POWERSHELL.EXE for commands execution
- regsvr32.exe (PID: 660)
- wininit.exe (PID: 7360)
- core.exe (PID: 3968)
- regsvr32.exe (PID: 1272)
- Yi-.exe (PID: 10296)
- XClient.exe (PID: 10512)
- cmd.exe (PID: 9132)
- jucheck.exe (PID: 3952)
Possible usage of Discord/Telegram API has been detected (YARA)
- Bloxflip Predictor.exe (PID: 4228)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 4008)
- MSBuild.exe (PID: 3896)
- MSBuild.exe (PID: 8596)
Executes as Windows Service
- AA_v3.exe (PID: 4488)
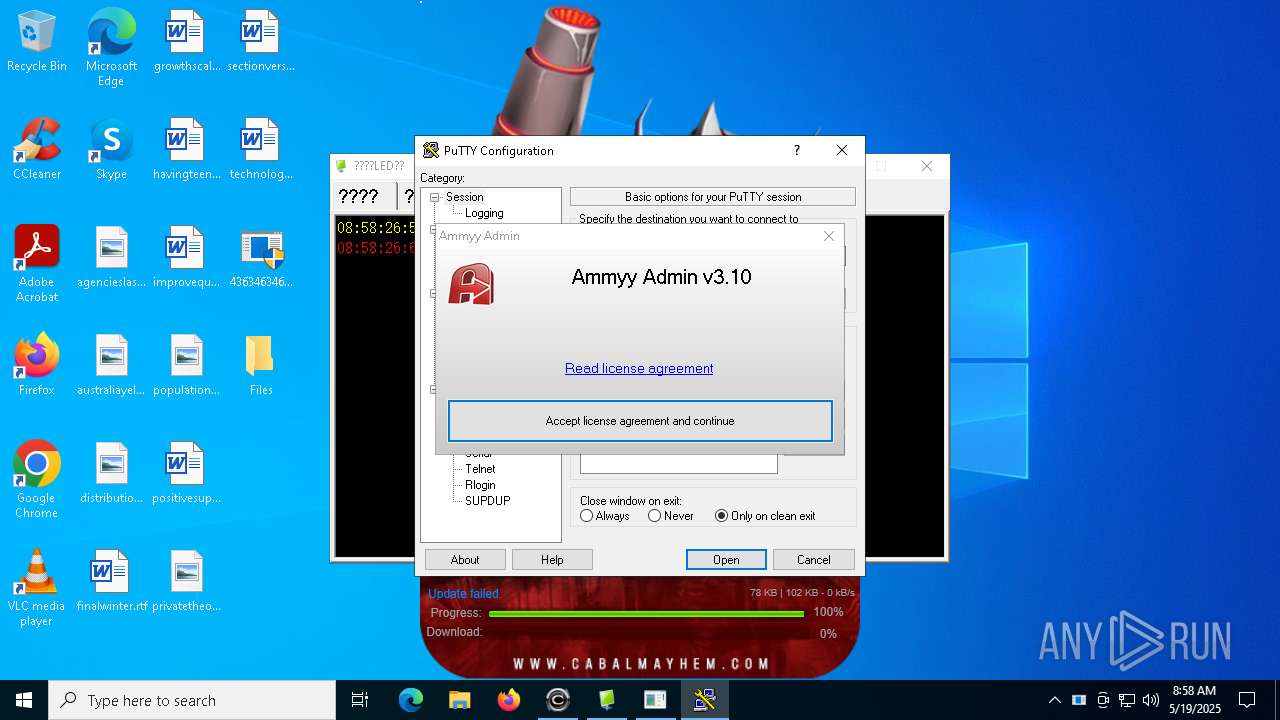
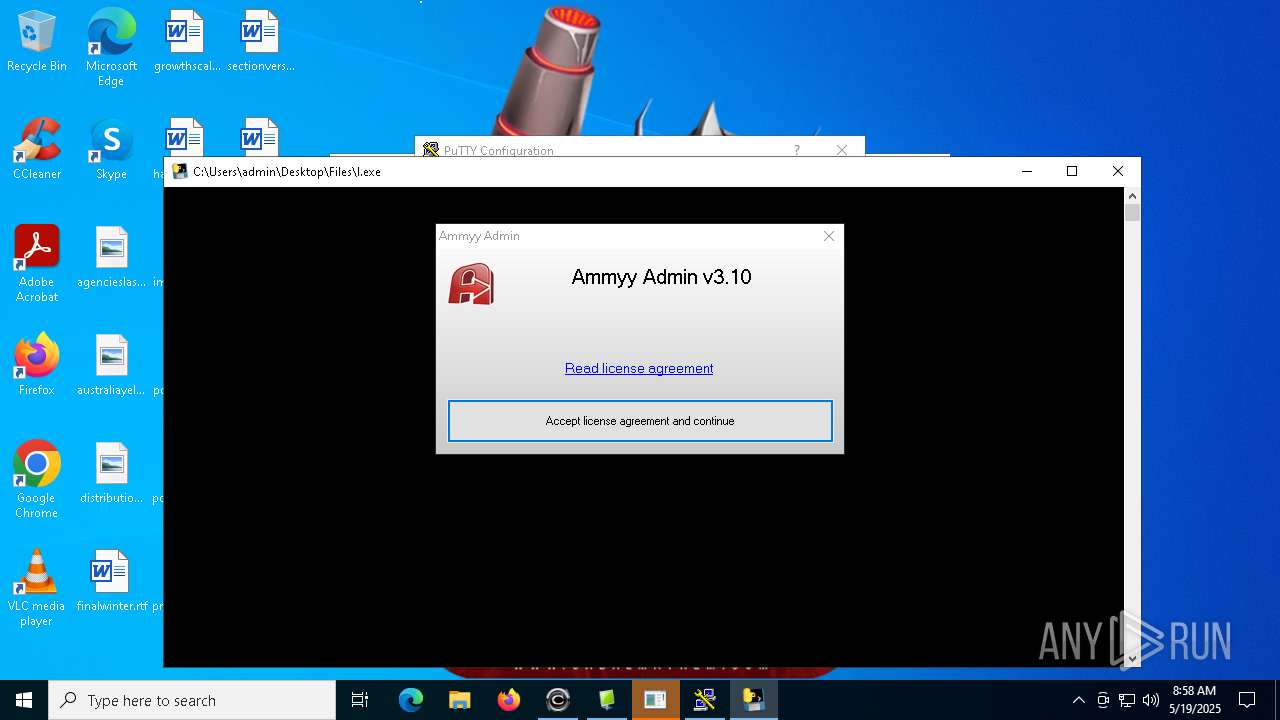
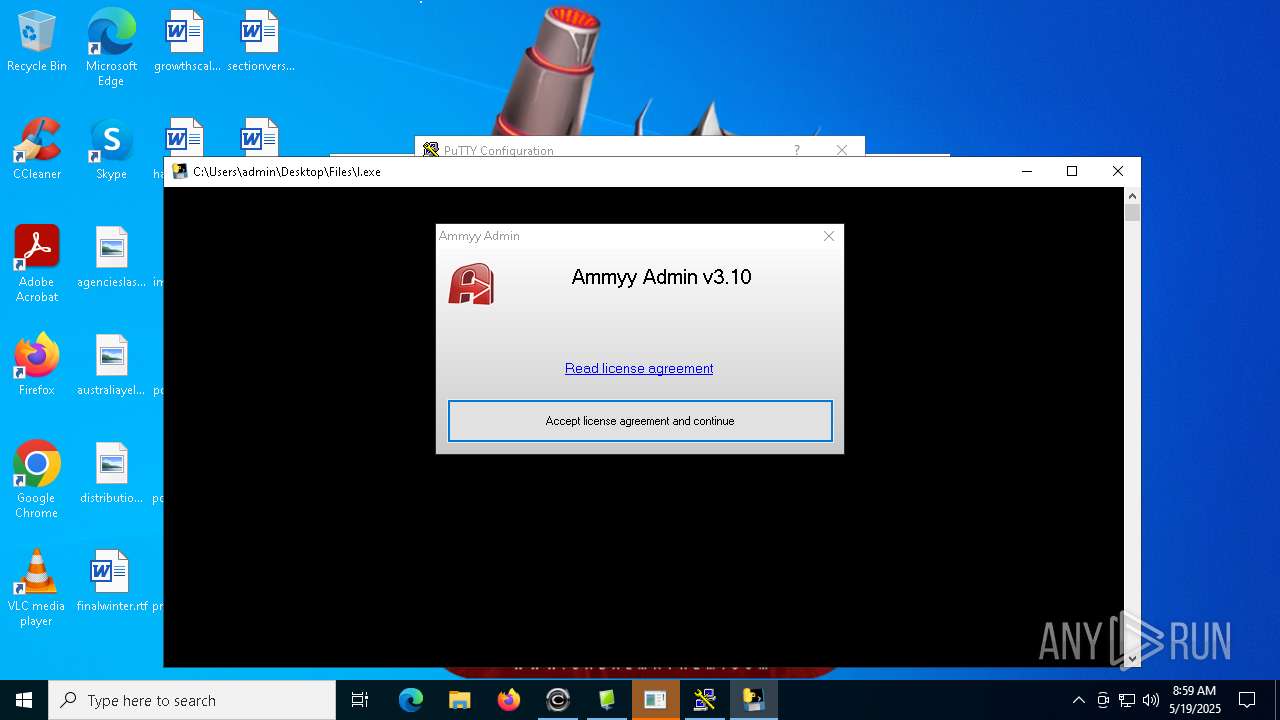
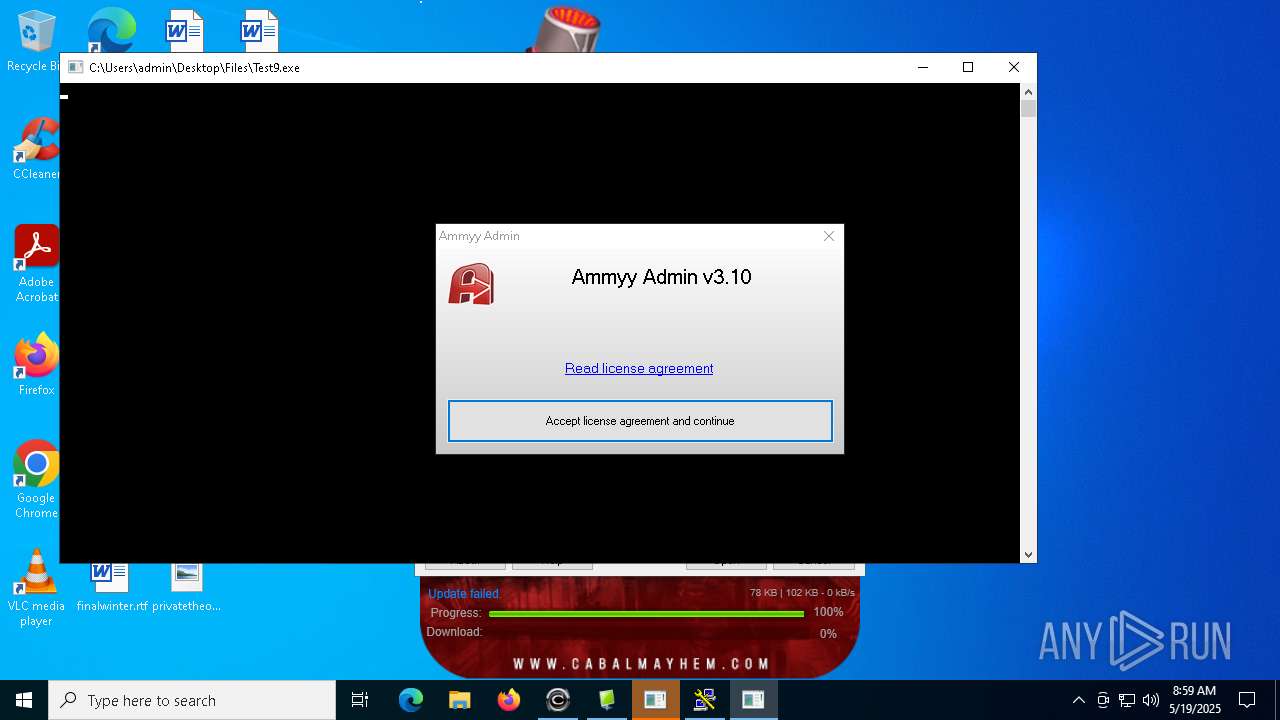
PUTTY has been detected
- putty.exe (PID: 2096)
Checks for external IP
- Network.exe (PID: 3192)
- svchost.exe (PID: 2196)
- e0llfx2x.huk.exe (PID: 8680)
- build.exe (PID: 10448)
Executes application which crashes
- Network.exe (PID: 3192)
- e0llfx2x.huk.exe (PID: 8680)
- alex.exe (PID: 9248)
- build.exe (PID: 10448)
Malware-specific behavior (creating "System.dll" in Temp)
- sm.exe (PID: 7936)
The process executes via Task Scheduler
- UserOOBEBroker.exe (PID: 7392)
- regsvr32.exe (PID: 1272)
Drops a system driver (possible attempt to evade defenses)
- sm.exe (PID: 7936)
Connects to SSH
- myapp.exe (PID: 864)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 2800)
- cmd.exe (PID: 8624)
- cmd.exe (PID: 10496)
Uses TASKKILL.EXE to kill Browsers
- main1.exe (PID: 8436)
Uses TASKKILL.EXE to kill process
- wscript.exe (PID: 10044)
Lists all scheduled tasks
- schtasks.exe (PID: 9620)
The process executes VB scripts
- taskmoder.exe (PID: 9724)
Executed via WMI
- schtasks.exe (PID: 7876)
- schtasks.exe (PID: 10172)
- schtasks.exe (PID: 8388)
- schtasks.exe (PID: 7264)
- schtasks.exe (PID: 7364)
- schtasks.exe (PID: 9252)
- schtasks.exe (PID: 8976)
- schtasks.exe (PID: 904)
- schtasks.exe (PID: 7276)
- schtasks.exe (PID: 9648)
- schtasks.exe (PID: 8628)
- schtasks.exe (PID: 3008)
- schtasks.exe (PID: 8396)
- schtasks.exe (PID: 8216)
- schtasks.exe (PID: 8504)
- schtasks.exe (PID: 3132)
- schtasks.exe (PID: 8976)
- schtasks.exe (PID: 9112)
- schtasks.exe (PID: 7264)
- schtasks.exe (PID: 10172)
- schtasks.exe (PID: 9648)
Script adds exclusion path to Windows Defender
- XClient.exe (PID: 10512)
- Yi-.exe (PID: 10296)
- cmd.exe (PID: 9132)
- jucheck.exe (PID: 3952)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 9468)
- cmd.exe (PID: 10904)
- cmd.exe (PID: 8328)
Manipulates environment variables
- powershell.exe (PID: 10268)
Connects to FTP
- wblog.exe (PID: 11244)
Script adds exclusion process to Windows Defender
- XClient.exe (PID: 10512)
INFO
Checks supported languages
- 4363463463464363463463463.bin.exe (PID: 6620)
- Quas_Brout_ncrypt.exe (PID: 2096)
- 99999.exe (PID: 1452)
- server.exe (PID: 5400)
- Clients.exe (PID: 5352)
- chcp.com (PID: 5392)
- Clients.exe (PID: 2772)
- chcp.com (PID: 6656)
- Clients.exe (PID: 680)
- chcp.com (PID: 6040)
- ckjg.exe (PID: 900)
- Clients.exe (PID: 5772)
- chcp.com (PID: 5392)
- Clients.exe (PID: 1300)
- chcp.com (PID: 1748)
- Clients.exe (PID: 1660)
- chcp.com (PID: 5232)
- Clients.exe (PID: 6632)
- chcp.com (PID: 2852)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- chcp.com (PID: 5132)
- chcp.com (PID: 5228)
- 4363463463464363463463463.bin.exe (PID: 2288)
- Bloxflip%20Predictor.exe (PID: 2092)
- Test2.exe (PID: 5512)
- Solara_Protect.exe (PID: 2064)
- k360.exe (PID: 6980)
- Client.exe (PID: 4000)
- Clients.exe (PID: 4200)
- chcp.com (PID: 5044)
Reads the machine GUID from the registry
- 4363463463464363463463463.bin.exe (PID: 6620)
- Quas_Brout_ncrypt.exe (PID: 2096)
- Clients.exe (PID: 5352)
- server.exe (PID: 5400)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- ckjg.exe (PID: 900)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- 4363463463464363463463463.bin.exe (PID: 2288)
- Test2.exe (PID: 5512)
- Clients.exe (PID: 4200)
- Client.exe (PID: 4000)
Disables trace logs
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 2288)
Reads the computer name
- 4363463463464363463463463.bin.exe (PID: 6620)
- Quas_Brout_ncrypt.exe (PID: 2096)
- 99999.exe (PID: 1452)
- Clients.exe (PID: 5352)
- server.exe (PID: 5400)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- ckjg.exe (PID: 900)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- Bloxflip%20Predictor.exe (PID: 2092)
- 4363463463464363463463463.bin.exe (PID: 2288)
- k360.exe (PID: 6980)
- Test2.exe (PID: 5512)
- Solara_Protect.exe (PID: 2064)
- Client.exe (PID: 4000)
- Clients.exe (PID: 4200)
Checks proxy server information
- 4363463463464363463463463.bin.exe (PID: 6620)
- 4363463463464363463463463.bin.exe (PID: 2288)
Process checks computer location settings
- 4363463463464363463463463.bin.exe (PID: 6620)
- 99999.exe (PID: 1452)
- Clients.exe (PID: 5352)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- 4363463463464363463463463.bin.exe (PID: 2288)
- Client.exe (PID: 4000)
- Clients.exe (PID: 4200)
Creates files in the program directory
- Quas_Brout_ncrypt.exe (PID: 2096)
Reads Environment values
- Quas_Brout_ncrypt.exe (PID: 2096)
- Clients.exe (PID: 5352)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- ckjg.exe (PID: 900)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- Test2.exe (PID: 5512)
- Client.exe (PID: 4000)
- Clients.exe (PID: 4200)
Create files in a temporary directory
- 99999.exe (PID: 1452)
- server.exe (PID: 5400)
- Clients.exe (PID: 5352)
- Clients.exe (PID: 2772)
- Clients.exe (PID: 680)
- Clients.exe (PID: 5772)
- Clients.exe (PID: 1300)
- Clients.exe (PID: 1660)
- Clients.exe (PID: 6632)
- Clients.exe (PID: 4628)
- Clients.exe (PID: 2392)
- Clients.exe (PID: 4200)
- Client.exe (PID: 4000)
Creates files or folders in the user directory
- 99999.exe (PID: 1452)
- server.exe (PID: 5400)
- ckjg.exe (PID: 900)
- Bloxflip%20Predictor.exe (PID: 2092)
- Test2.exe (PID: 5512)
Reads the software policy settings
- 4363463463464363463463463.bin.exe (PID: 6620)
- ckjg.exe (PID: 900)
- 4363463463464363463463463.bin.exe (PID: 2288)
Changes the display of characters in the console
- cmd.exe (PID: 5228)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 864)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 3180)
- cmd.exe (PID: 4868)
- cmd.exe (PID: 5024)
- cmd.exe (PID: 3176)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 6184)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 6972)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 2516)
- cmd.exe (PID: 2908)
- cmd.exe (PID: 7444)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 8580)
- cmd.exe (PID: 9432)
- cmd.exe (PID: 9764)
- cmd.exe (PID: 10224)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 10496)
- cmd.exe (PID: 6976)
- cmd.exe (PID: 11760)
- cmd.exe (PID: 10760)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6872)
Manual execution by a user
- 4363463463464363463463463.bin.exe (PID: 1616)
- 4363463463464363463463463.bin.exe (PID: 2288)
- msedge.exe (PID: 3620)
- msedge.exe (PID: 10092)
The sample compiled with english language support
- darts-wled.exe (PID: 6876)
- addon2.exe (PID: 968)
- 4363463463464363463463463.bin.exe (PID: 6620)
- esign-app.tmp (PID: 6248)
- esign-app.tmp (PID: 6744)
- 6.tmp (PID: 5588)
- l.exe (PID: 7876)
- 4363463463464363463463463.bin.exe (PID: 2288)
- ChromeSetup.exe (PID: 7800)
- main1.exe (PID: 8652)
- p5Y.exe (PID: 7372)
- hyperWeb.exe (PID: 9920)
- td.exe (PID: 9900)
- sm.exe (PID: 7936)
- Kr.NEG.exe (PID: 9372)
- rlol.tmp (PID: 11420)
- 136.0.7103.114_chrome_installer.exe (PID: 4864)
Attempting to use instant messaging service
- Bloxflip Predictor.exe (PID: 4228)
- MSBuild.exe (PID: 8596)
The sample compiled with chinese language support
- 4363463463464363463463463.bin.exe (PID: 6620)
- ChromeSetup.exe (PID: 7800)
- td.exe (PID: 9900)
- 4363463463464363463463463.bin.exe (PID: 2288)
- Kr.NEG.exe (PID: 9372)
- dahuanverguo_kr.exe (PID: 6300)
- rlol.exe (PID: 12244)
Compiled with Borland Delphi (YARA)
- conhost.exe (PID: 7104)
- Bloxflip Predictor.exe (PID: 4228)
- update.exe (PID: 7152)
- Windows.exe (PID: 1388)
The sample compiled with japanese language support
- sm.exe (PID: 7936)
- ChromeSetup.exe (PID: 7800)
The sample compiled with korean language support
- sm.exe (PID: 7936)
- ChromeSetup.exe (PID: 7800)
The sample compiled with arabic language support
- ChromeSetup.exe (PID: 7800)
- 1465810408079_502.exe (PID: 10784)
The sample compiled with bulgarian language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with czech language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with polish language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with russian language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with portuguese language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with turkish language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with slovak language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with swedish language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with german language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with french language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with Indonesian language support
- ChromeSetup.exe (PID: 7800)
The sample compiled with Italian language support
- ChromeSetup.exe (PID: 7800)
Application launched itself
- chrome.exe (PID: 9188)
- chrome.exe (PID: 9256)
- msedge.exe (PID: 9656)
- msedge.exe (PID: 9888)
- msedge.exe (PID: 6380)
- msedge.exe (PID: 6312)
Connects to unusual port
- iexplore.exe (PID: 512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(5400) server.exe
C20.tcp.eu.ngrok.io
Ports16872
BotnetHacKed
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\ef9410a92d1077d89c94b9208aa74f96
Splitter|'|'|
Version0.7d
(PID) Process(4228) Bloxflip Predictor.exe
C2quite-cs.at.ply.gg
Ports10397
BotnetHaCkEd
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\Windows
Splitter|-F-|
Versionnull
AsyncRat
(PID) Process(900) ckjg.exe
C2 (5)hkfasfsafg.click
hfjwfheiwf.click
jfhaowhfjk.click
hfjaohf9q3.click
fshjaifhajfa.click
Ports (1)7777
VersionLoaderPanel
Options
AutoRunfalse
Mutexdxrfuhttmneigievnhg
InstallFolder%AppData%
Certificates
Cert1MIICMDCCAZmgAwIBAgIVALJH4bdfPPE5dyMevD9KJERdSx3xMA0GCSqGSIb3DQEBDQUAMGQxFTATBgNVBAMMDExvYWRlciBQYW5lbDETMBEGA1UECwwKcXdxZGFuY2h1bjEcMBoGA1UECgwTRGNSYXQgQnkgcXdxZGFuY2h1bjELMAkGA1UEBwwCU0gxCzAJBgNVBAYTAkNOMB4XDTI0MDczMDE2NDgyM1oXDTM1MDUwOTE2NDgyM1owEDEOMAwGA1UEAwwFRGNSYXQwgZ8wDQYJKoZIhvcNAQEBBQADgY0A...
Server_SignaturemoARP2ilwwb46Uu1bzWUZTVB0GP7xM1q5BnrWDDw/ApLcb7eUPvM2UqnQm36fmkch/34sLs3cF2TQ83qC33yp5CHQOErcSBGropIhfXoUeA33XKMACcksz/aLy4PuEXsPY3ksQgefpI86mp1dHrGy2H9yJpEhouz4mfmkakhbD8=
Keys
AESdafd84b99a3f7311fddcf50b1199ddec6bb1f973d6f536a98a289a9af59b0c98
SaltLoaderPanel
(PID) Process(1388) Windows.exe
C2 (1)anyone-blogging.gl.at.ply.gg
Ports (1)22284
Version| CRACKED BY https://t.me/xworm_v2
Options
AutoRuntrue
MutexAsyncMutex_6SI8OkPnk
InstallFolder%Temp%
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAOQb7nA/hP/L1XXxqdDJNzANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjMwNTI1MDUyMTIyWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAIykAVxs0s6rZ/dwP6ujJtpnj6RSsCsZN6Cfj1InZxSIswX+zNiKJys8xyLlyexoya3ebLp5gOSz...
Server_SignatureUIeKsq8FTvB20ZCQ0bPYnM9E03AtqOZ8dUfHU0hr3TmGGhwfdIryp62gPj79UN3BI7VZ6KLYcmyTjASy+OtLscjdtHVrt+CTZhTnIu2IsOyAR4wiacg6EcJYXdLoYx09eu2KuJfYDaOLgocti+cMu29r7+5xQFqpaxit5r1wyE0T9Dm7hqFdWRJtofJdgRejwhj+5y9wSuHv3qn3QnwA1pscd+8aLcq4NdakgxwAa4RlNQtDxsSXDkjmOcL6dZHFVHudbWWfBwuCpr07h2DNE1HMmZqHC7MQPlSeEnl0LCKA...
Keys
AES2674d00a7bd03523741e9f183917d7f5238967a0a29311ccb30f2d3db7ac3f54
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
ims-api
(PID) Process(4228) Bloxflip Predictor.exe
Discord-Webhook-Tokens (1)1040048109578895410/ewZ0edyfPb3PSo10z3bgM05aZex7uX3D_NzU6Fq1aA_P8lZYDHIuWHv2Qzzn-JTgsdIp
Discord-Info-Links
1040048109578895410/ewZ0edyfPb3PSo10z3bgM05aZex7uX3D_NzU6Fq1aA_P8lZYDHIuWHv2Qzzn-JTgsdIp
Get Webhook Infohttps://discord.com/api/webhooks/1040048109578895410/ewZ0edyfPb3PSo10z3bgM05aZex7uX3D_NzU6Fq1aA_P8lZYDHIuWHv2Qzzn-JTgsdIp
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
743
Monitored processes
581
Malicious processes
66
Suspicious processes
59
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | "c:\program files (x86)\internet explorer\iexplore.exe" | C:\Program Files (x86)\Internet Explorer\iexplore.exe | 76y5trfed675ytg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | /s /i:SYNC "C:\Users\admin\AppData\Roaming\\6fwpuclnt_9.drv" | C:\Windows\System32\regsvr32.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | ping -n 10 localhost | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files\SubDare\Clients.exe" | C:\Program Files\SubDare\Clients.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Quasar Client Exit code: 0 Version: 1.4.1 Modules
| |||||||||||||||
| 680 | "C:\WINDOWS\system32\ReAgentc.exe" /disable | C:\Windows\SysWOW64\ReAgentc.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Windows Recovery Agent Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
223 036
Read events
217 972
Write events
4 977
Delete events
87
Modification events
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6620) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
807
Suspicious files
233
Text files
304
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | 4363463463464363463463463.bin.exe | C:\Users\admin\Desktop\Files\Quas_Brout_ncrypt.exe | executable | |
MD5:DF7B0E428B11F8AA5102168E65156A3B | SHA256:F853596287C8F345EBA943ACDC0747F19BED0E5EBC041BC0AB1AA61413D970D9 | |||
| 6620 | 4363463463464363463463463.bin.exe | C:\Users\admin\Desktop\Files\99999.exe | executable | |
MD5:CD49DEA59EFE62D7288C76280C38F134 | SHA256:FA536D889AFFB81391EE202980D417E82CEE0B46D97DA4070B4A4E2052D33D82 | |||
| 1452 | 99999.exe | C:\Users\admin\AppData\Roaming\server.exe | executable | |
MD5:CD49DEA59EFE62D7288C76280C38F134 | SHA256:FA536D889AFFB81391EE202980D417E82CEE0B46D97DA4070B4A4E2052D33D82 | |||
| 2096 | Quas_Brout_ncrypt.exe | C:\Program Files\SubDare\Clients.exe | executable | |
MD5:DF7B0E428B11F8AA5102168E65156A3B | SHA256:F853596287C8F345EBA943ACDC0747F19BED0E5EBC041BC0AB1AA61413D970D9 | |||
| 1300 | Clients.exe | C:\Users\admin\AppData\Local\Temp\WukzgMWirZg3.bat | text | |
MD5:9514A0A0B355DB94F78A8201C10A1E10 | SHA256:BE05EDFD575F0BDCFD251F1B7FDA8210ED3C211BF2C4B2E47942F60E23A5ED98 | |||
| 5352 | Clients.exe | C:\Users\admin\AppData\Local\Temp\H2OYOcacMZ0w.bat | text | |
MD5:5B00521D27F8DBDDCBEFB8040C434C5E | SHA256:430570FDA846B79A3BDA52274FFA6BB061A72D0FF577B11BB68628D4E397A36C | |||
| 5400 | server.exe | C:\Notepad.exe | executable | |
MD5:CD49DEA59EFE62D7288C76280C38F134 | SHA256:FA536D889AFFB81391EE202980D417E82CEE0B46D97DA4070B4A4E2052D33D82 | |||
| 2772 | Clients.exe | C:\Users\admin\AppData\Local\Temp\pEYjYiWpnY4F.bat | text | |
MD5:A3B8A591E08244953008C9B1B2D9A1C9 | SHA256:730570E0B8BD7C722B03AB8D7B8C08F76970210900F034D6F1748A242A027CC1 | |||
| 680 | Clients.exe | C:\Users\admin\AppData\Local\Temp\uWjjHBO5o6Su.bat | text | |
MD5:E3FF23E3FA53C64FC7BBF5E9B30056FB | SHA256:3EDE748D49F0A738AD3FFF7577E3B126605A88192CEDCD69245BB413D9783935 | |||
| 6620 | 4363463463464363463463463.bin.exe | C:\Users\admin\Desktop\Files\ckjg.exe | executable | |
MD5:962D2A0880C5325328930B66BB4E2CF1 | SHA256:08037DE4A729634FA818DDF03DDD27C28C89F42158AF5EDE71CF0AE2D78FA198 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
483
DNS requests
191
Threats
333
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6620 | 4363463463464363463463463.bin.exe | GET | 200 | 93.176.52.107:80 | http://93.176.52.107/Quas_Brout_ncrypt.exe | unknown | — | — | malicious |
6620 | 4363463463464363463463463.bin.exe | GET | 200 | 193.46.217.4:80 | http://gettsveriff.com/bgj3/ckjg.exe | unknown | — | — | unknown |
5772 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5772 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6620 | 4363463463464363463463463.bin.exe | GET | 301 | 140.82.121.3:80 | http://github.com/mentaliczz/BloxflipPredictor-V2/raw/refs/heads/main/Bloxflip%20Predictor.exe | unknown | — | — | whitelisted |
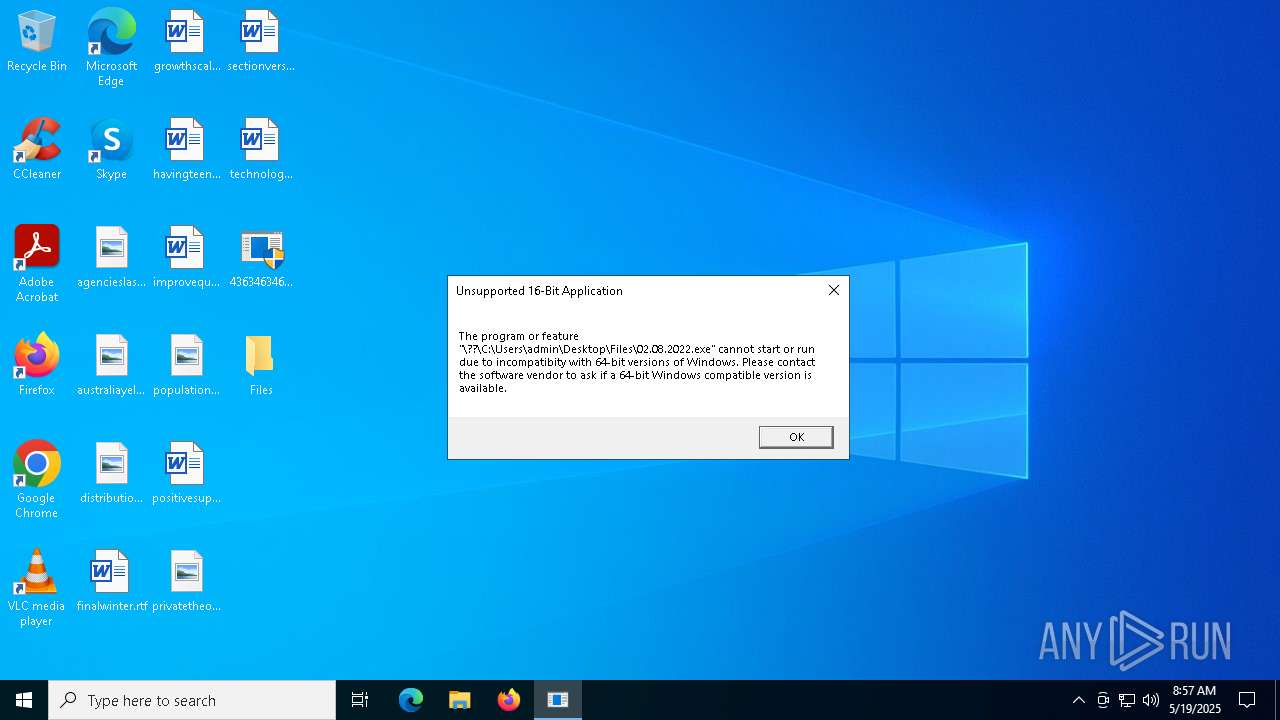
6620 | 4363463463464363463463463.bin.exe | GET | 200 | 101.126.144.111:80 | http://101.126.144.111/02.08.2022.exe | unknown | — | — | unknown |
2288 | 4363463463464363463463463.bin.exe | GET | 301 | 140.82.121.3:80 | http://github.com/NullSpectre/WhyAreYouHere-/raw/4bed170d797d5d2077bfc312d8badcd3c1dbaa74/Test2.exe | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6620 | 4363463463464363463463463.bin.exe | 151.101.130.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
6620 | 4363463463464363463463463.bin.exe | 93.176.52.107:80 | — | — | MQ | malicious |
6544 | svchost.exe | 20.190.159.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
gettsveriff.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6620 | 4363463463464363463463463.bin.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6620 | 4363463463464363463463463.bin.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
6620 | 4363463463464363463463463.bin.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6620 | 4363463463464363463463463.bin.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6620 | 4363463463464363463463463.bin.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
6620 | 4363463463464363463463463.bin.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DNS Query to DynDNS Domain *.ddns .net |
2196 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
5400 | server.exe | Misc activity | ET INFO Possible Host Profile Exfiltration In Pipe Delimited Format |