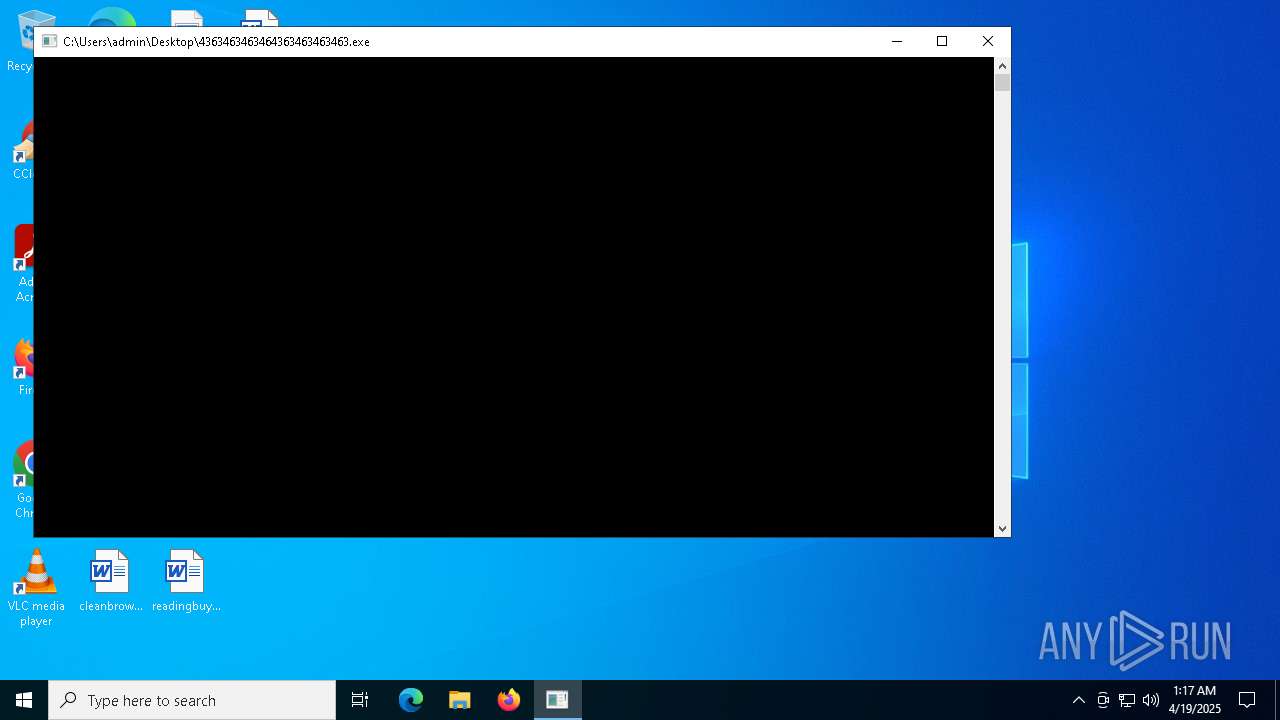
| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/9d7b8676-4266-42cb-b18d-20077b16e9cf |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 19, 2025, 01:16:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
LUMMA has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- 4363463463464363463463463.exe (PID: 6108)
METERPRETER has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 6108)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6108)
NJRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- main.exe (PID: 10648)
- dllhost.exe (PID: 11248)
QUASARRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- Client-built.exe (PID: 6656)
- 4363463463464363463463463.exe (PID: 6108)
- built.exe (PID: 5116)
- Quas_Brout_ncrypt.exe (PID: 8164)
- Sentil.exe (PID: 8016)
- discord.exe (PID: 5380)
- RuntimeBroker.exe (PID: 11084)
- CleanerV2.exe (PID: 8328)
- spectrum.exe (PID: 9236)
- 4363463463464363463463463.exe (PID: 6108)
- CollosalLoader.exe (PID: 7136)
Uses Task Scheduler to autorun other applications
- Client-built.exe (PID: 6656)
- built.exe (PID: 5116)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- Quas_Brout_ncrypt.exe (PID: 8164)
- cmd.exe (PID: 7956)
- Clients.exe (PID: 7420)
- diskutil.exe (PID: 8120)
- diskutil.exe (PID: 7416)
- Client.exe (PID: 7448)
- PerfWatson1.exe (PID: 7404)
- msgde.exe (PID: 8528)
- Clients.exe (PID: 9000)
- Client.exe (PID: 9072)
- PerfWatson1.exe (PID: 9160)
- cmd.exe (PID: 3396)
- JJSPLOIT.V2.exe (PID: 9024)
- windows 3543.exe (PID: 7380)
- Sentil.exe (PID: 8016)
- Client1.exe (PID: 10144)
- PerfWatson1.exe (PID: 9012)
- Client.exe (PID: 5964)
- Clients.exe (PID: 5188)
- discord.exe (PID: 5380)
- Client.exe (PID: 10116)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 6824)
- PerfWatson1.exe (PID: 840)
- Clients.exe (PID: 4880)
- Mph.pif (PID: 6656)
- windows 3543.exe (PID: 9280)
- PerfWatson1.exe (PID: 11224)
- Clients.exe (PID: 10360)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- Clients.exe (PID: 10280)
- PerfWatson1.exe (PID: 9852)
- RuntimeBroker.exe (PID: 11084)
- CleanerV2.exe (PID: 8328)
- cmd.exe (PID: 11108)
- spectrum.exe (PID: 9236)
- JUSCHED.EXE (PID: 12172)
- Clients.exe (PID: 11292)
- CollosalLoader.exe (PID: 7136)
- PerfWatson1.exe (PID: 12044)
- cmd.exe (PID: 11528)
- windows 3543.exe (PID: 8032)
- Clients.exe (PID: 12092)
- PerfWatson1.exe (PID: 5176)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 12148)
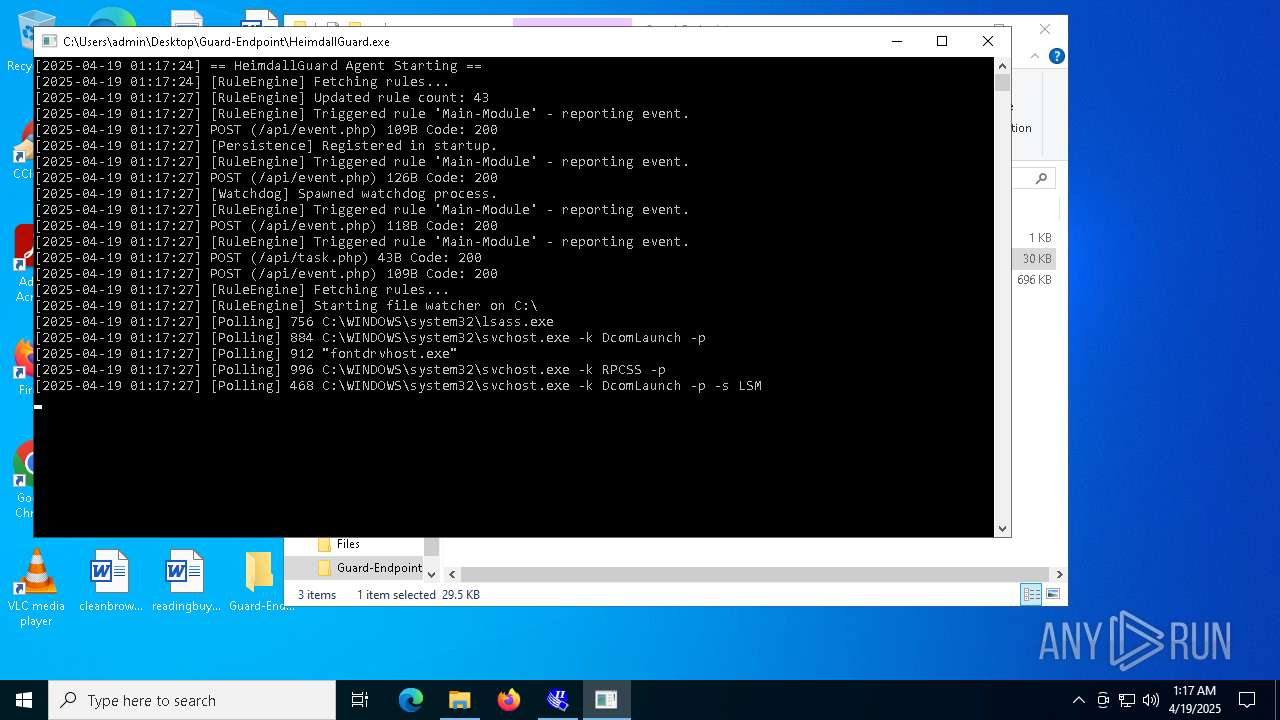
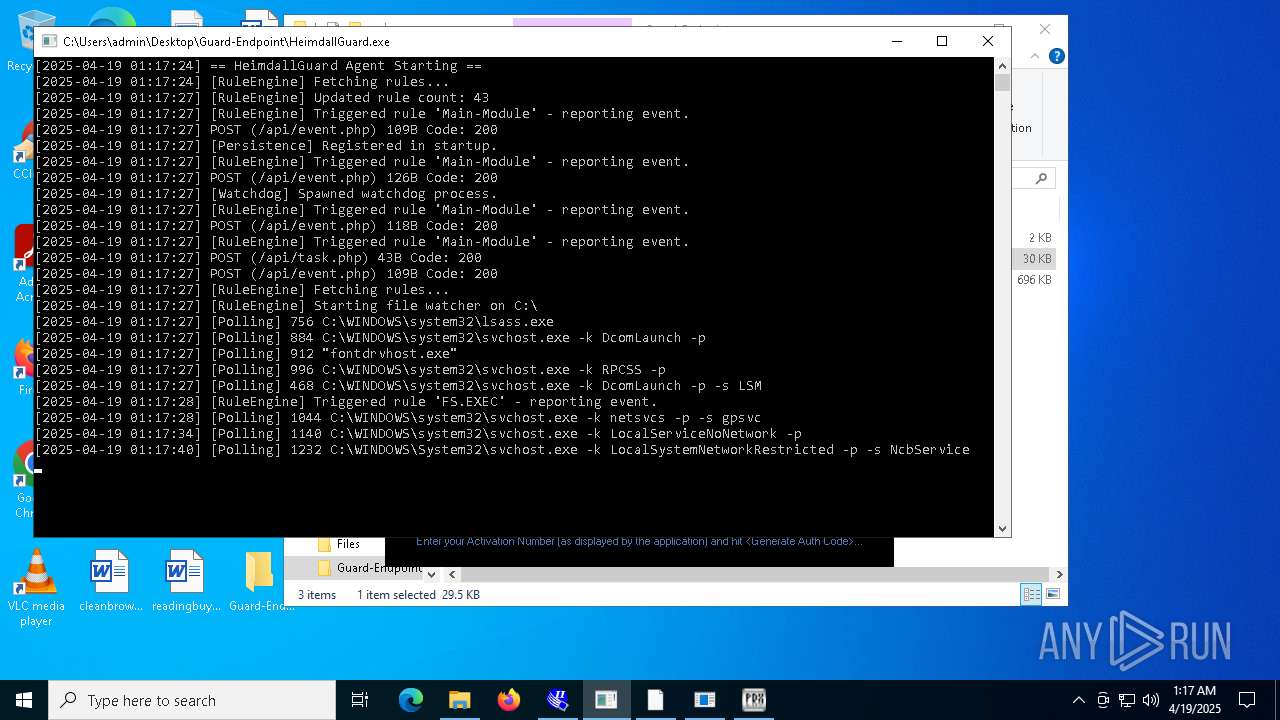
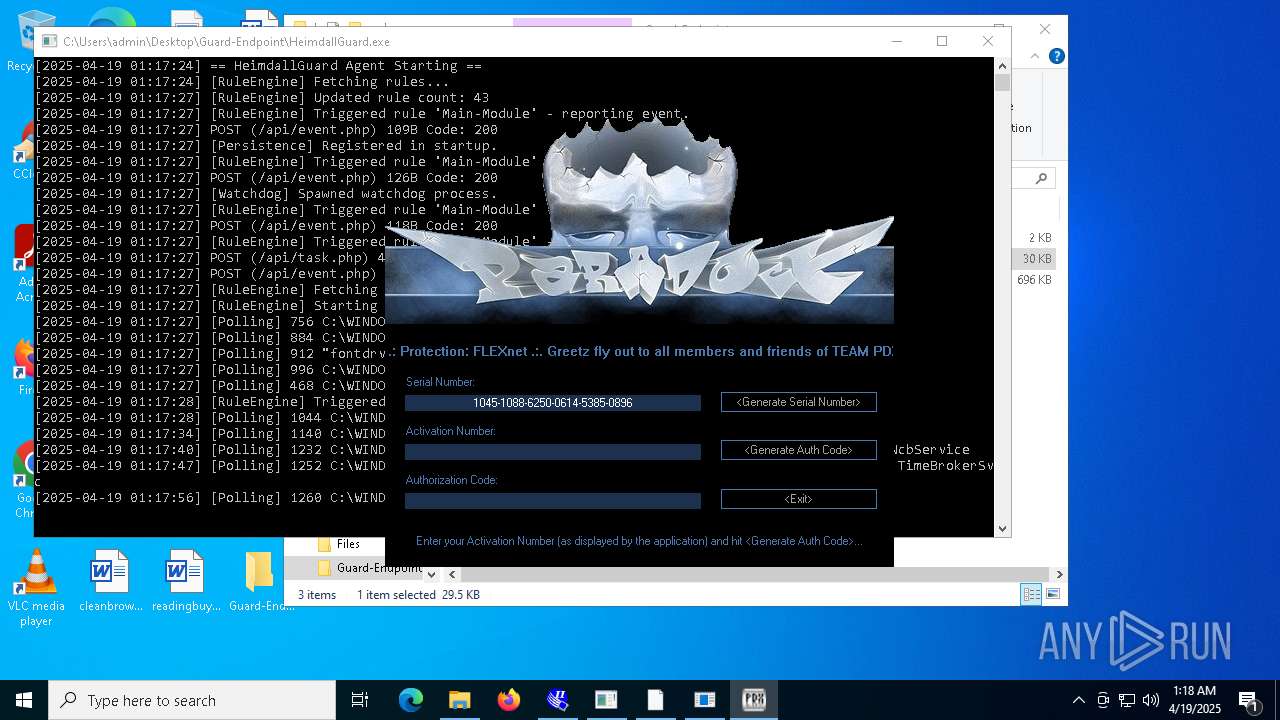
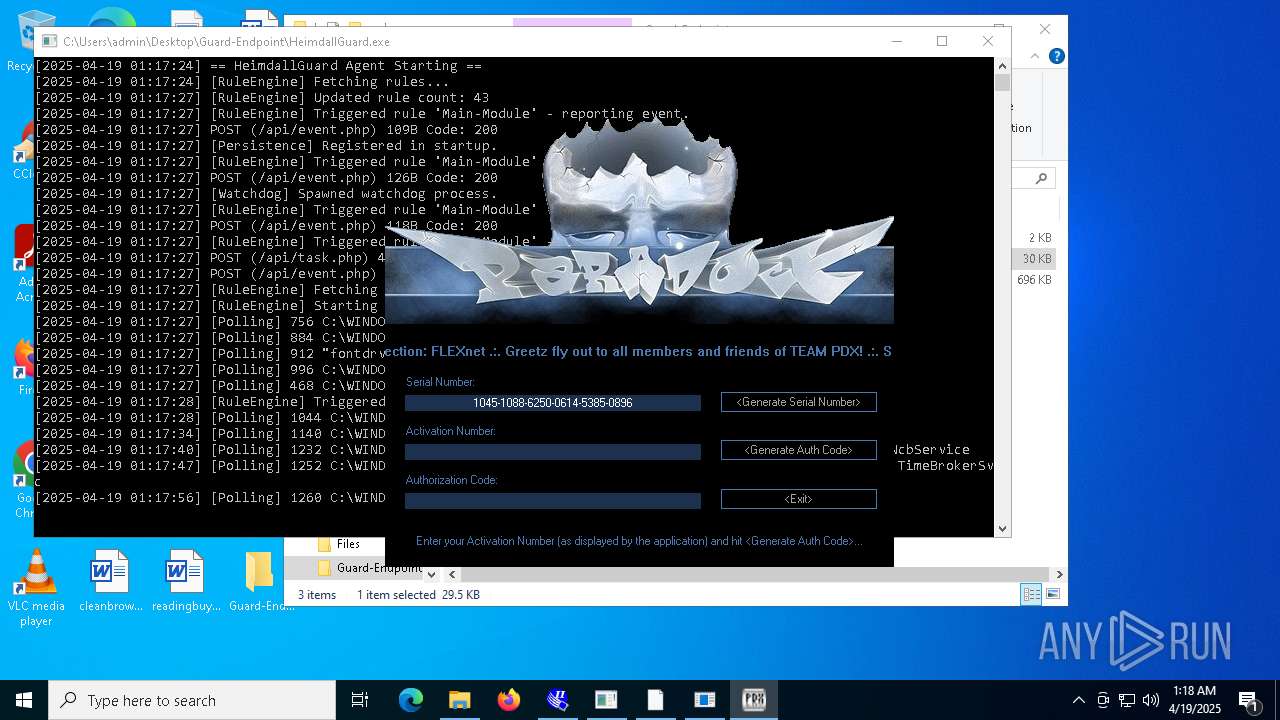
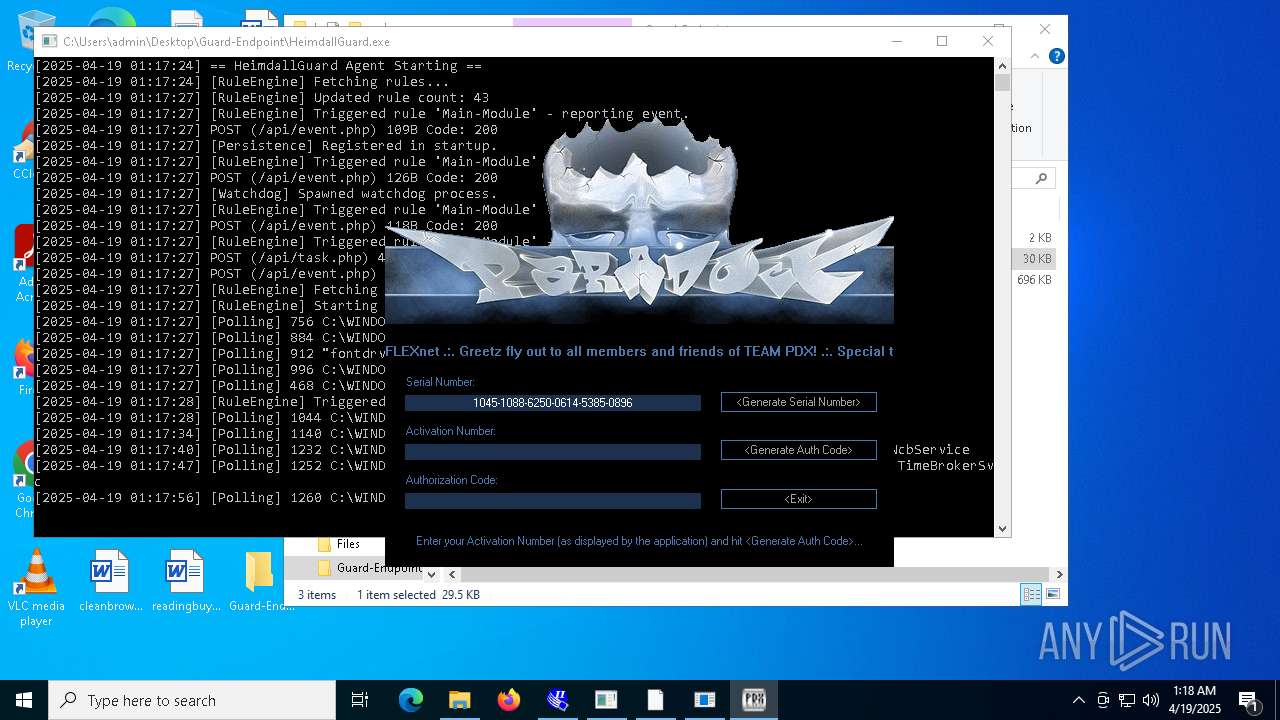
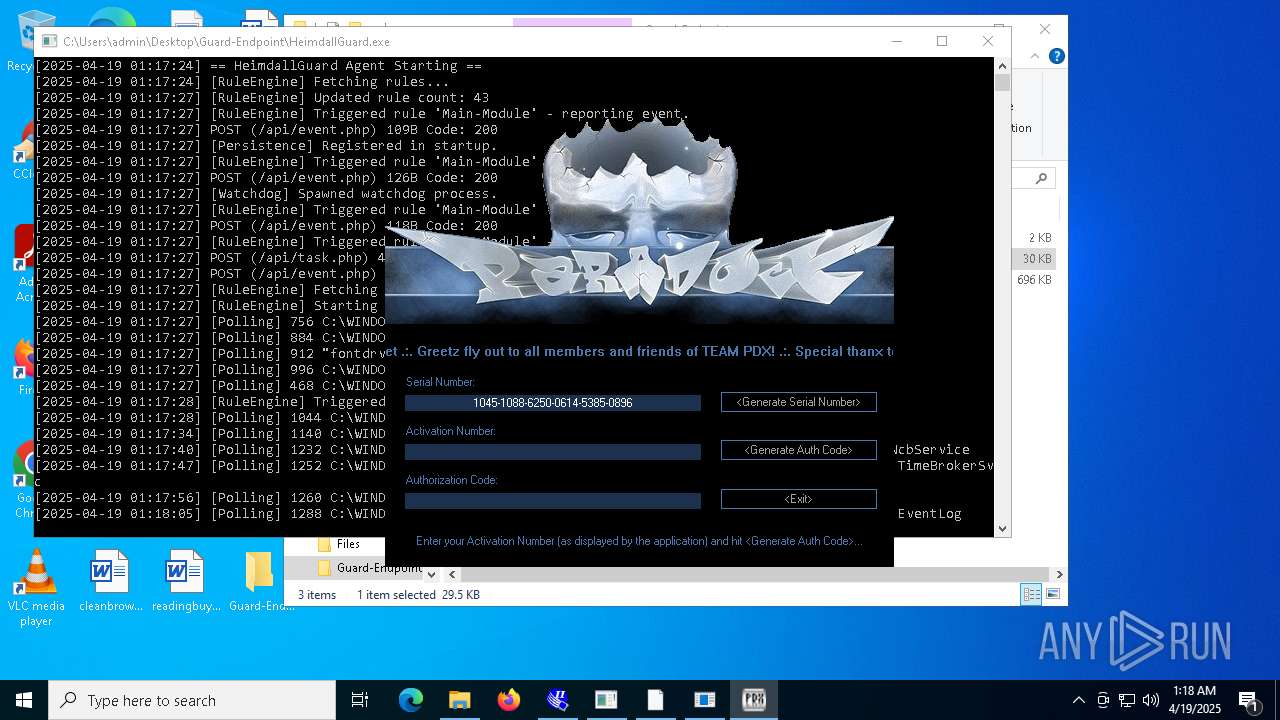
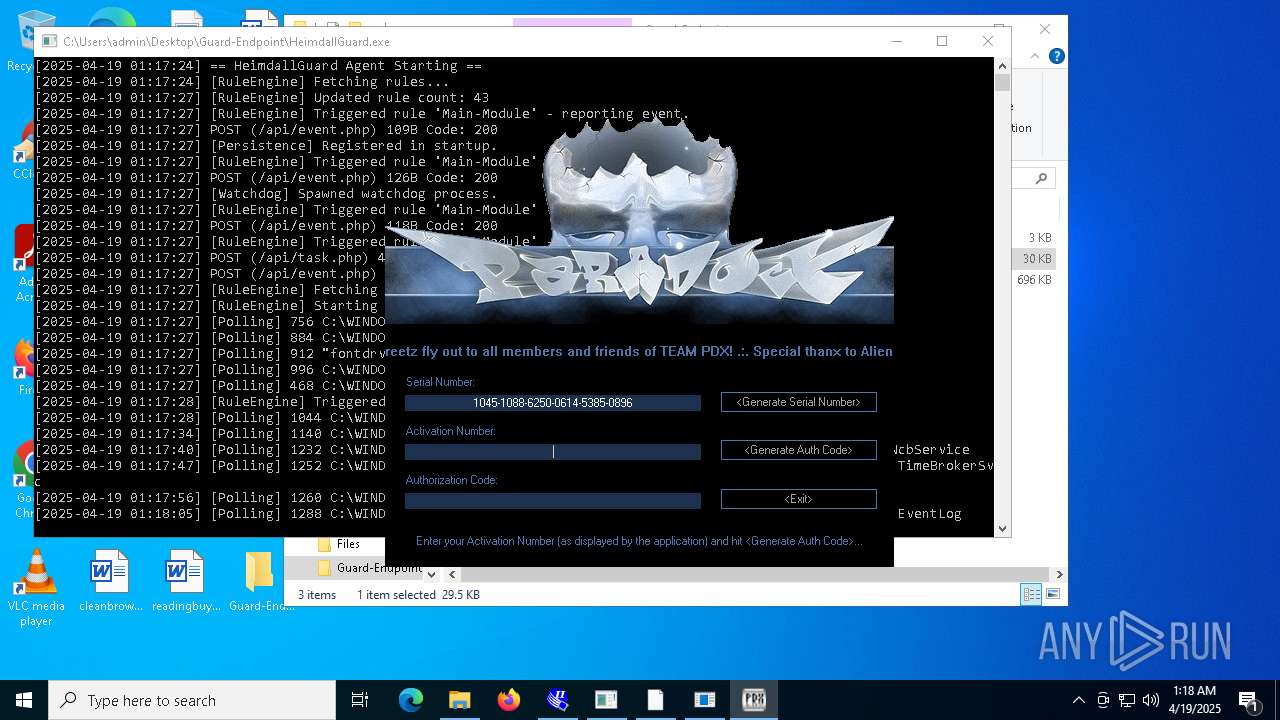
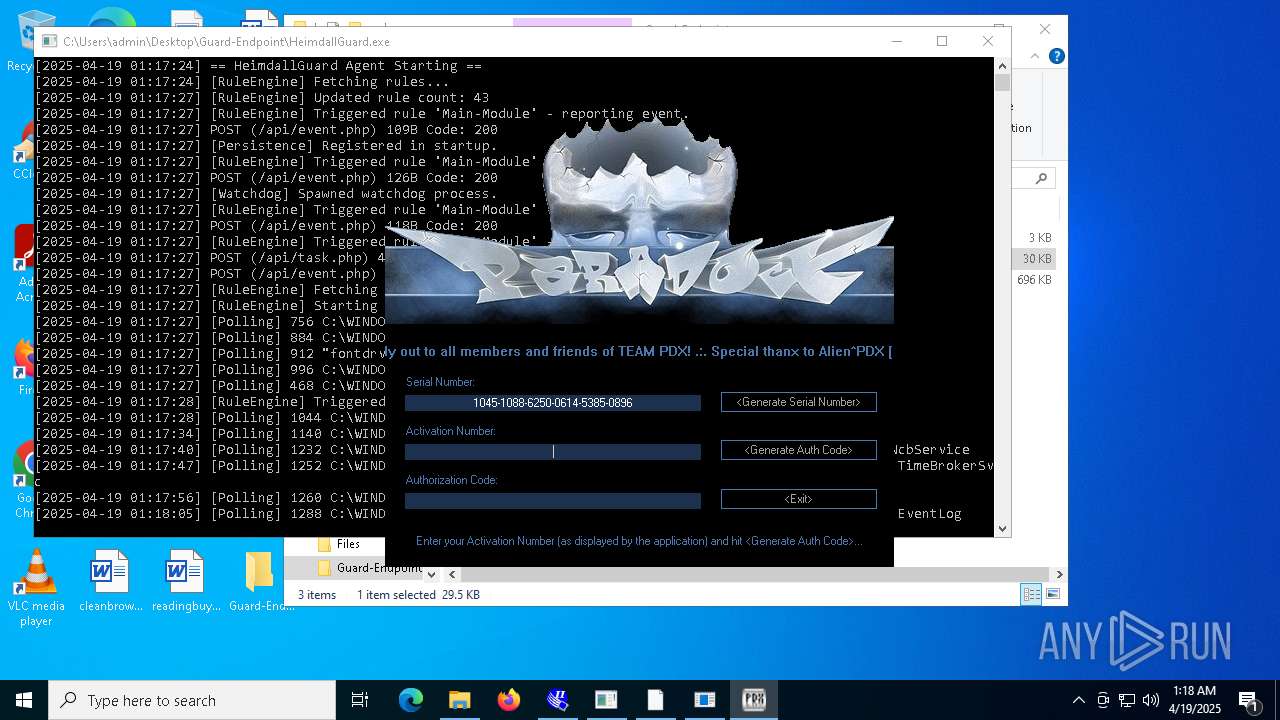
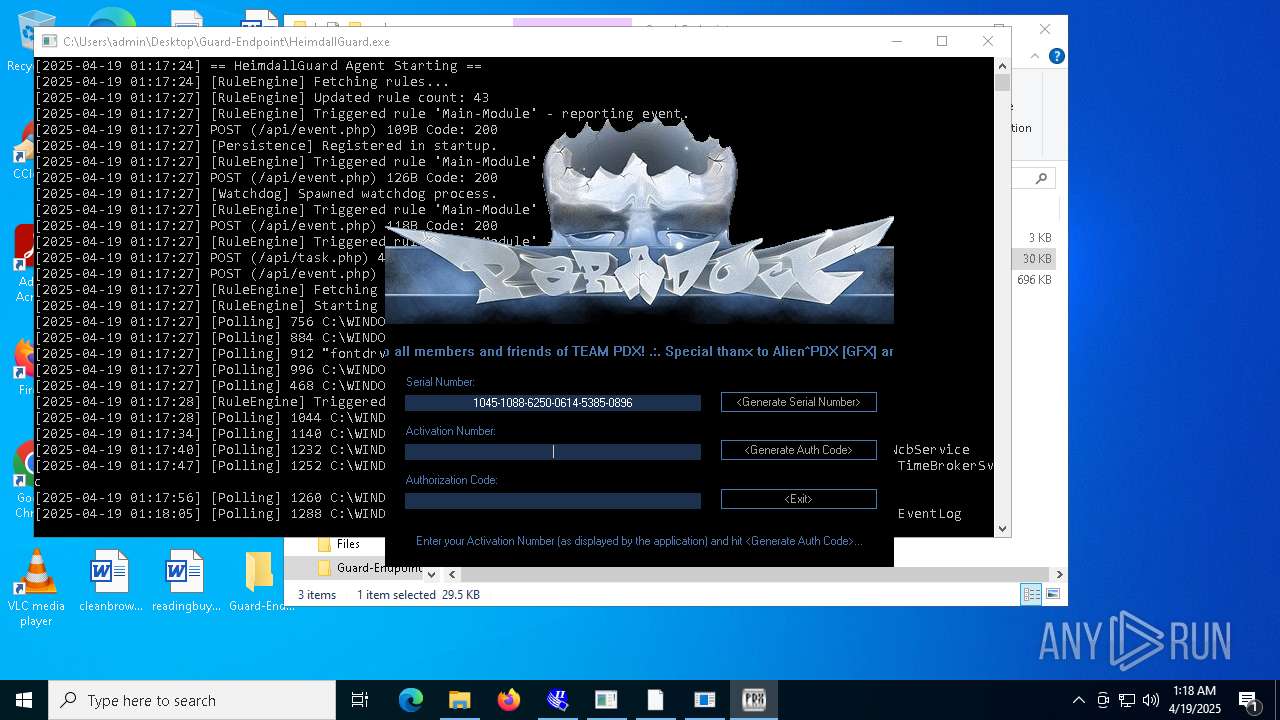
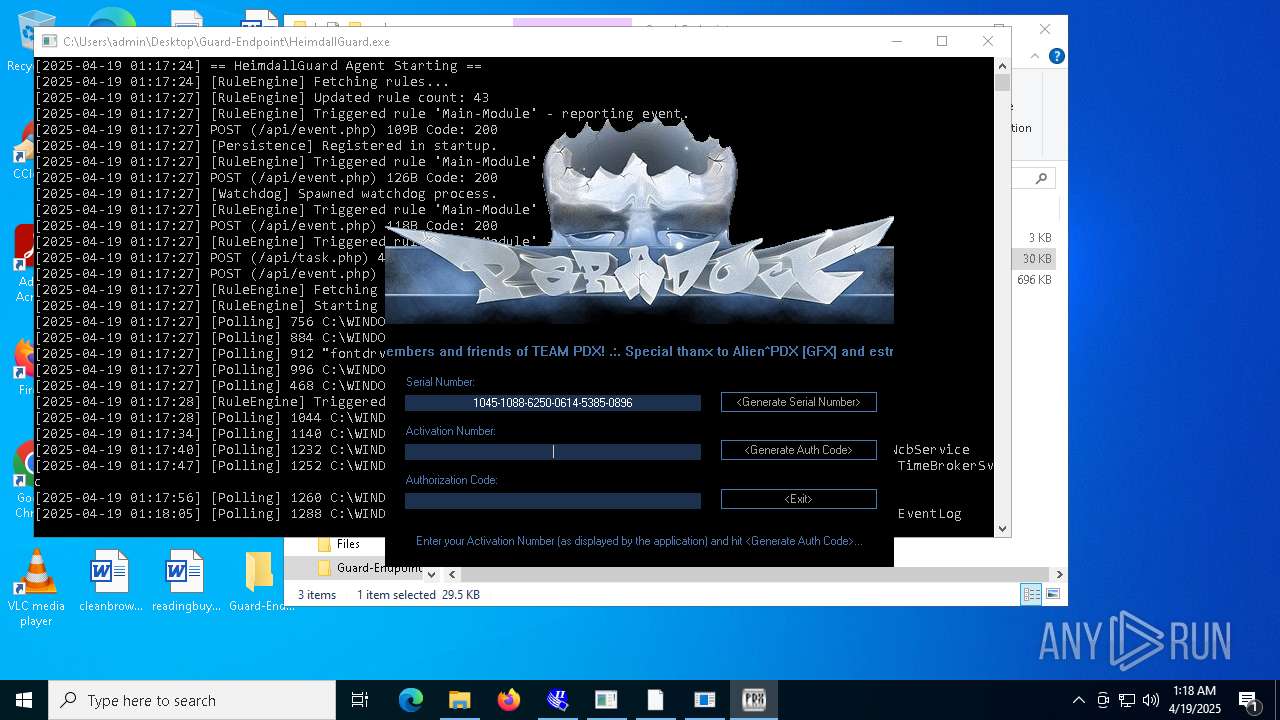
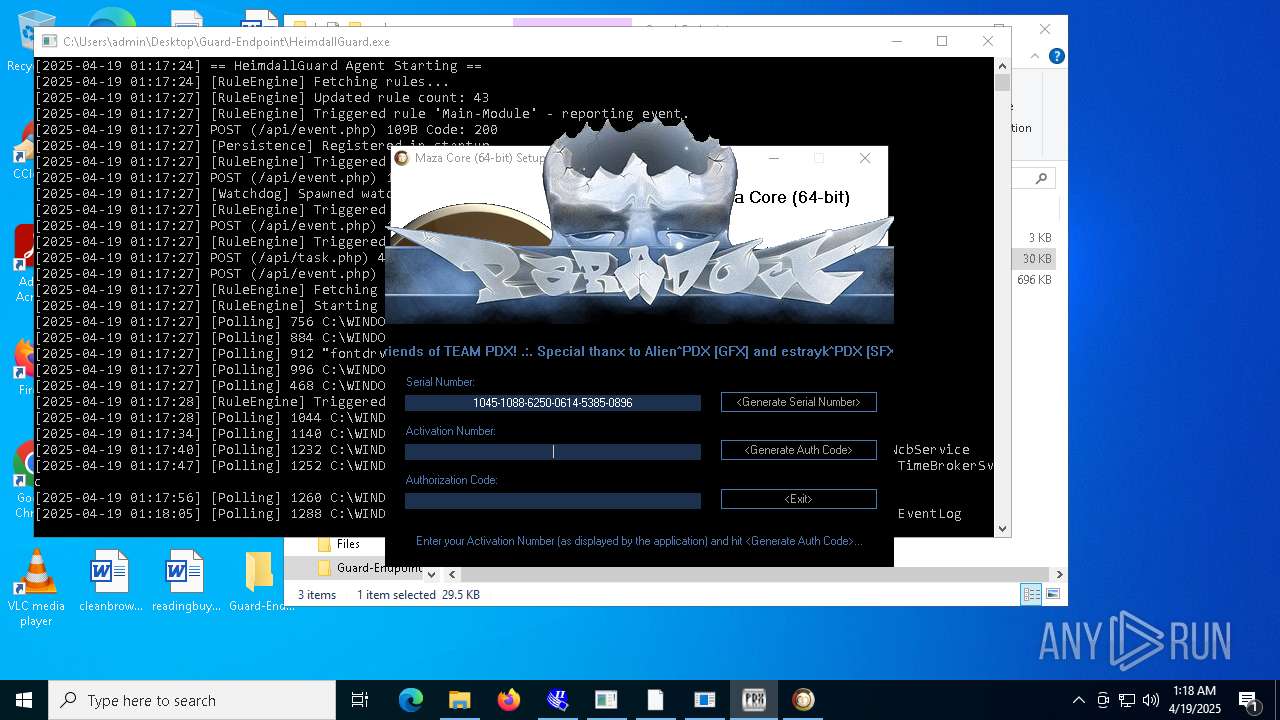
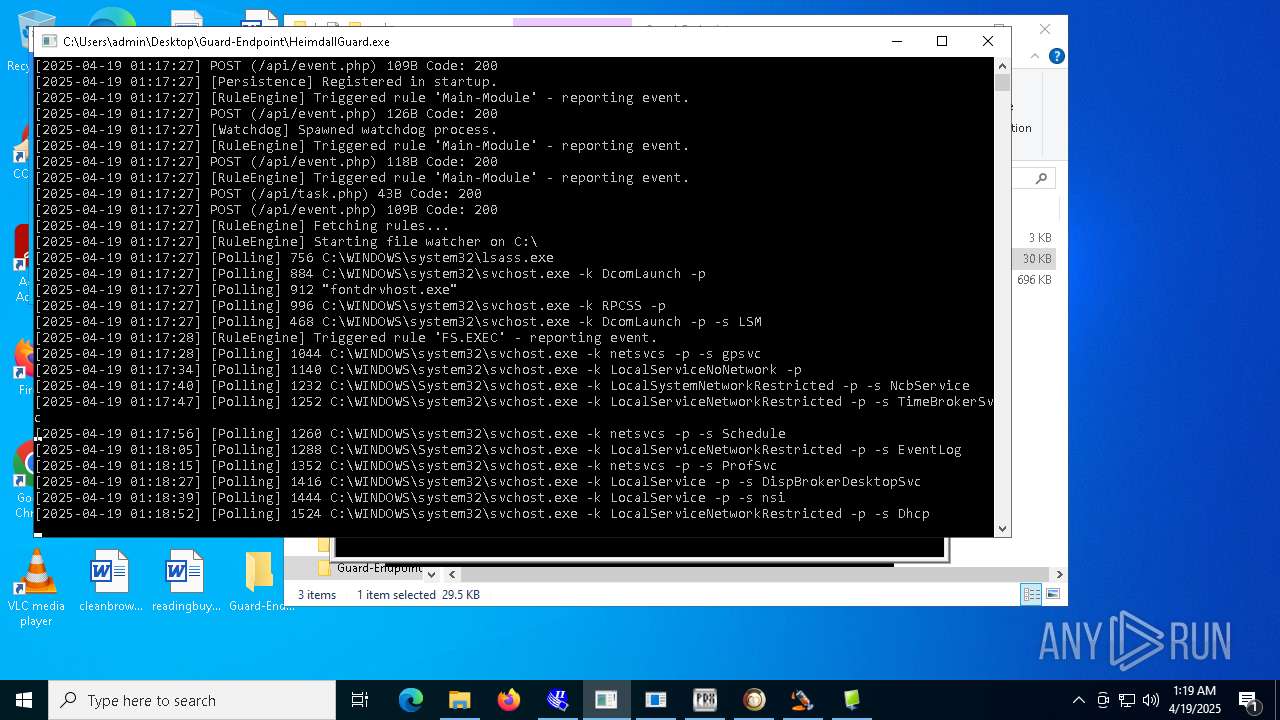
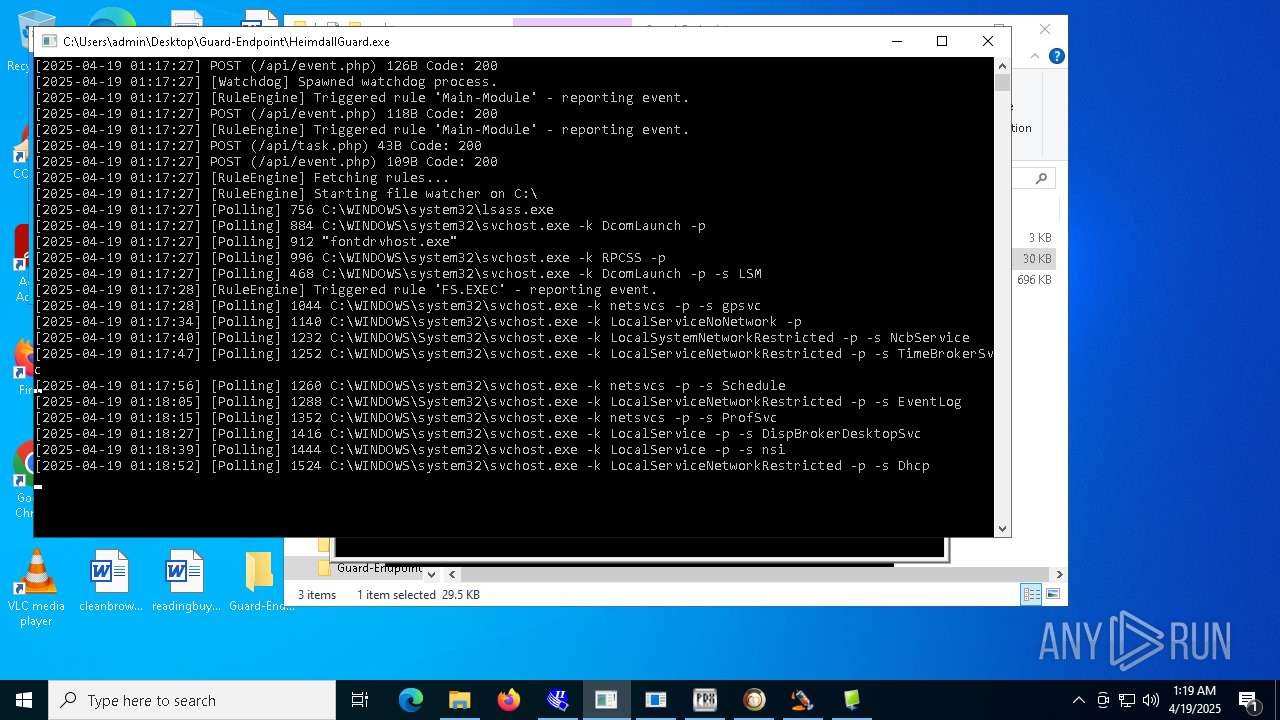
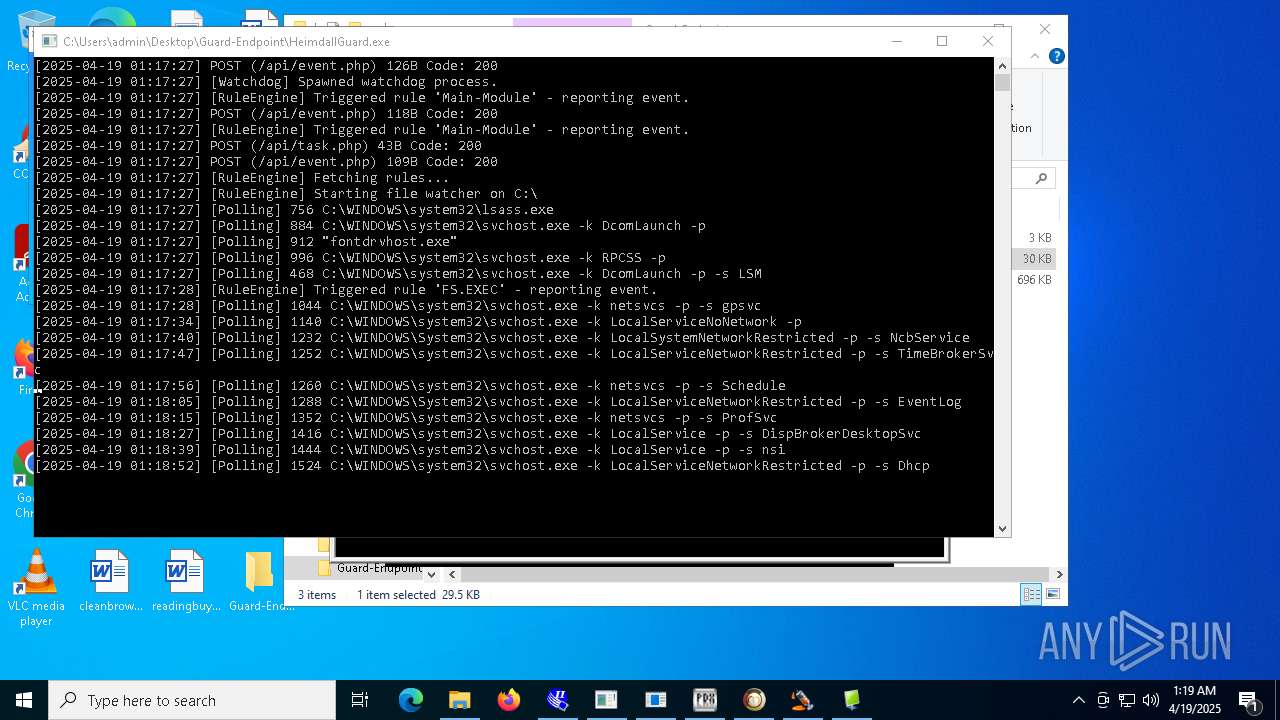
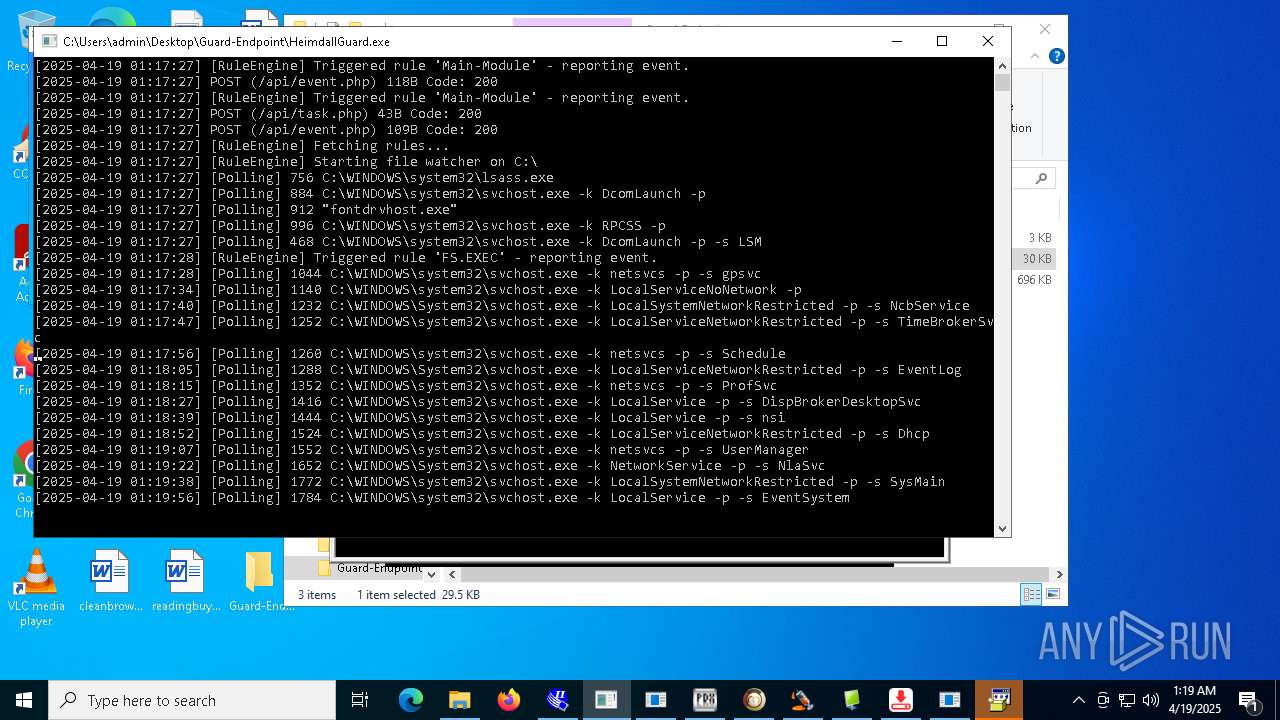
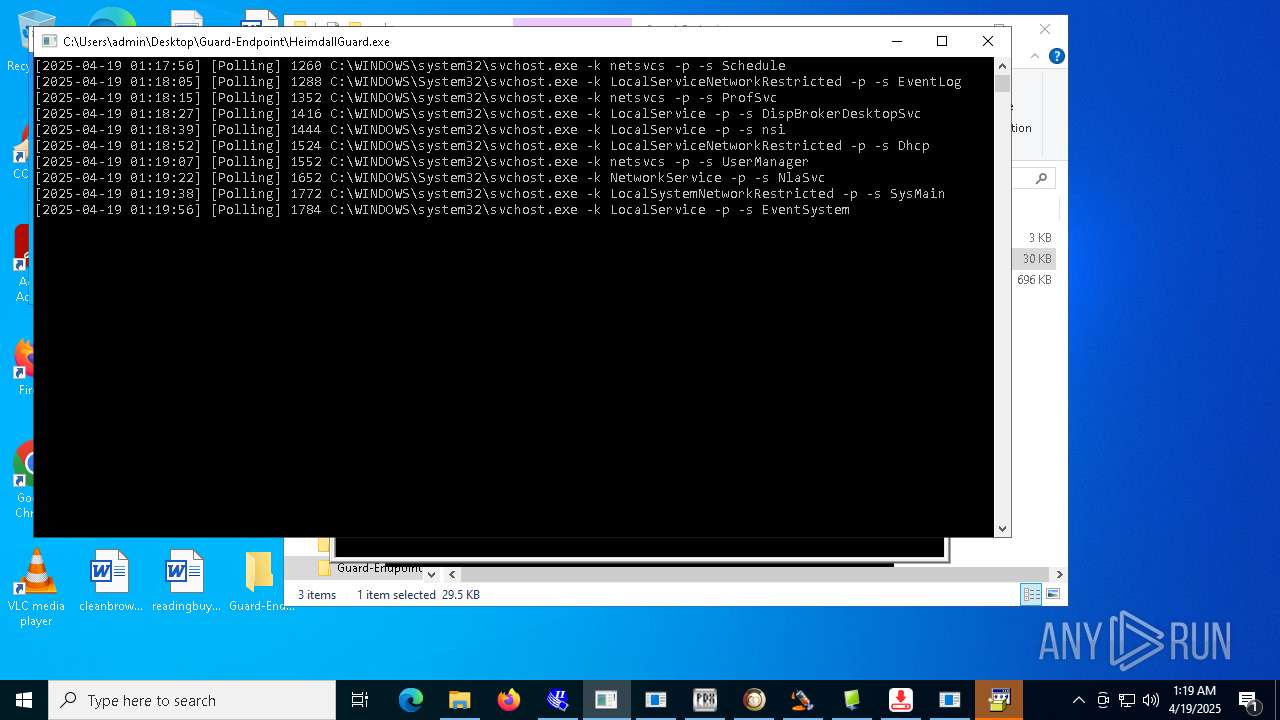
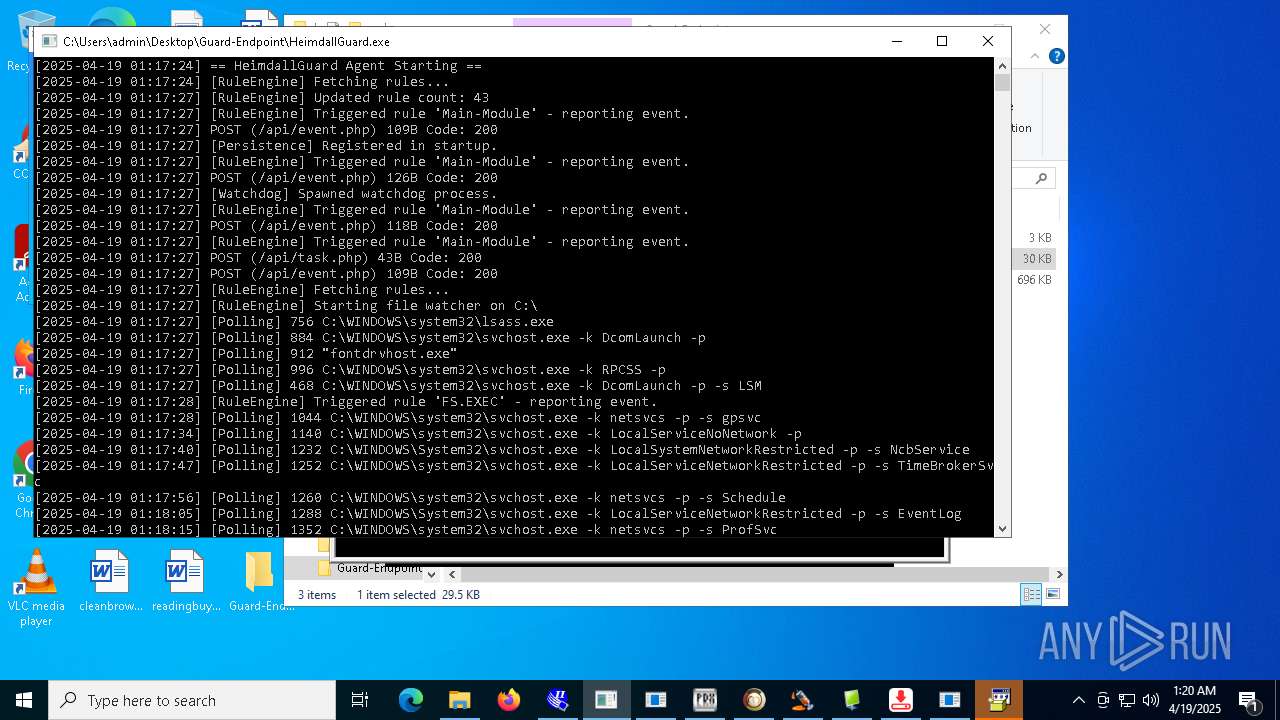
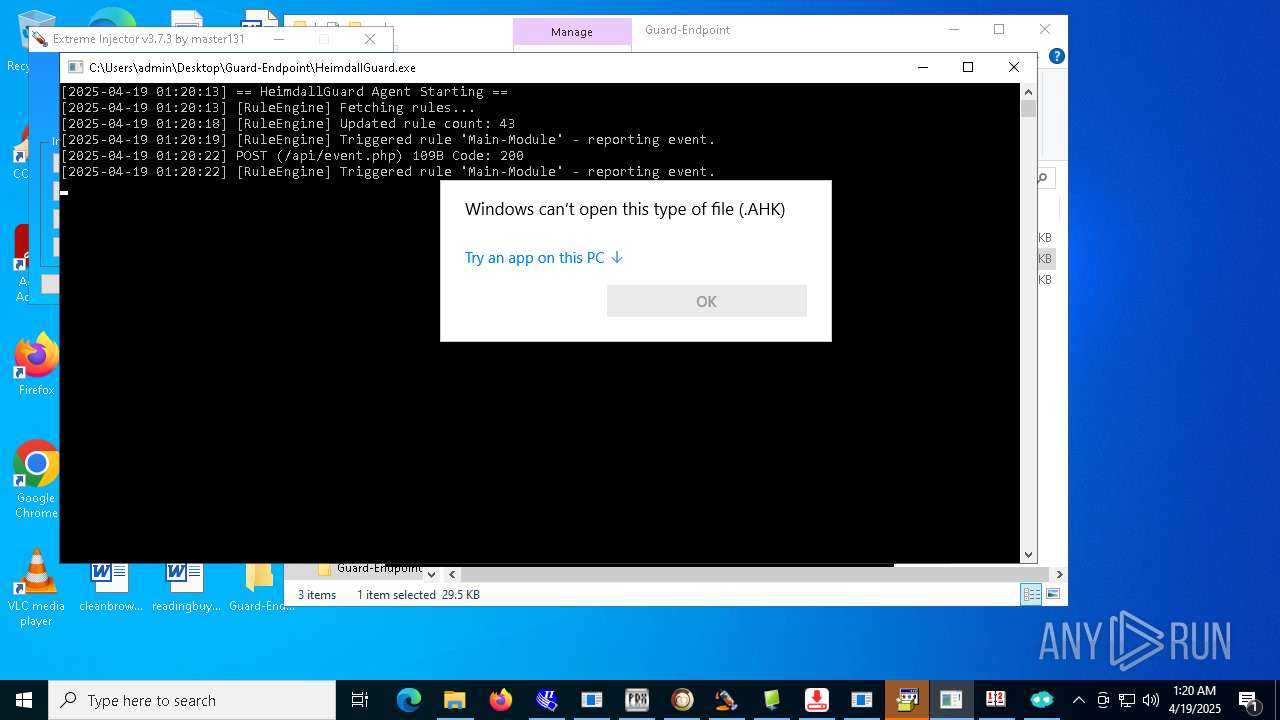
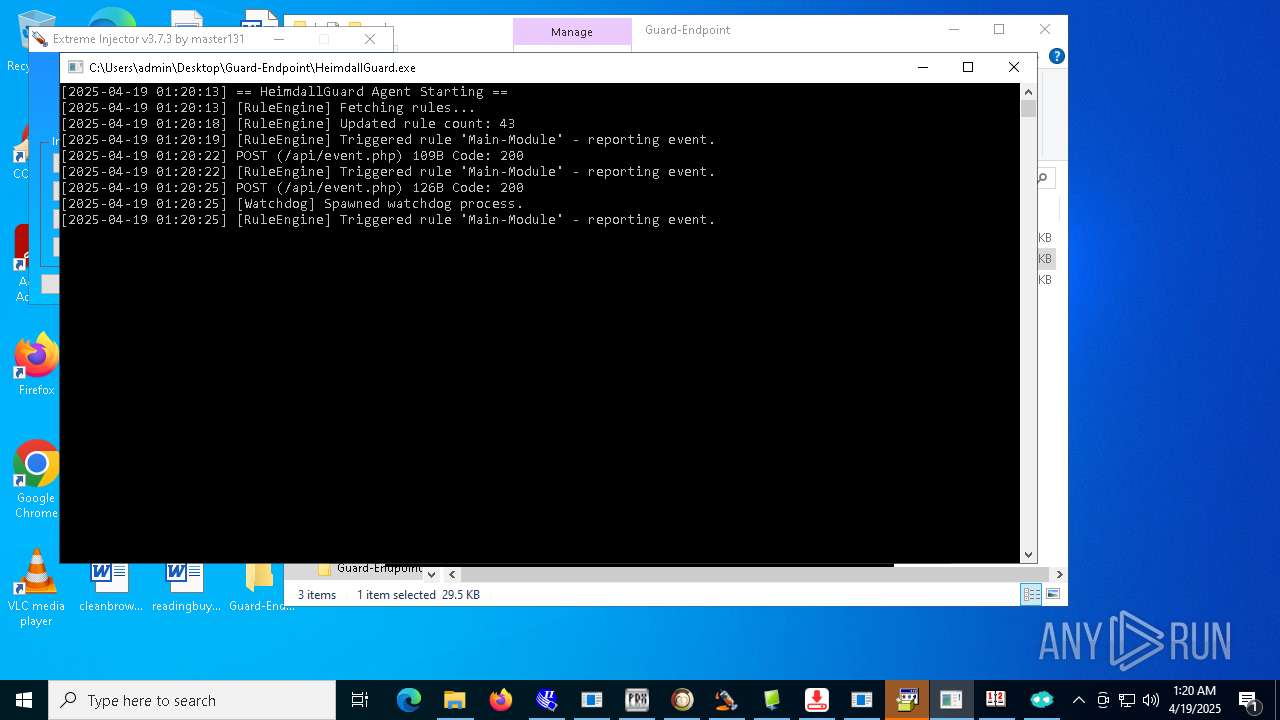
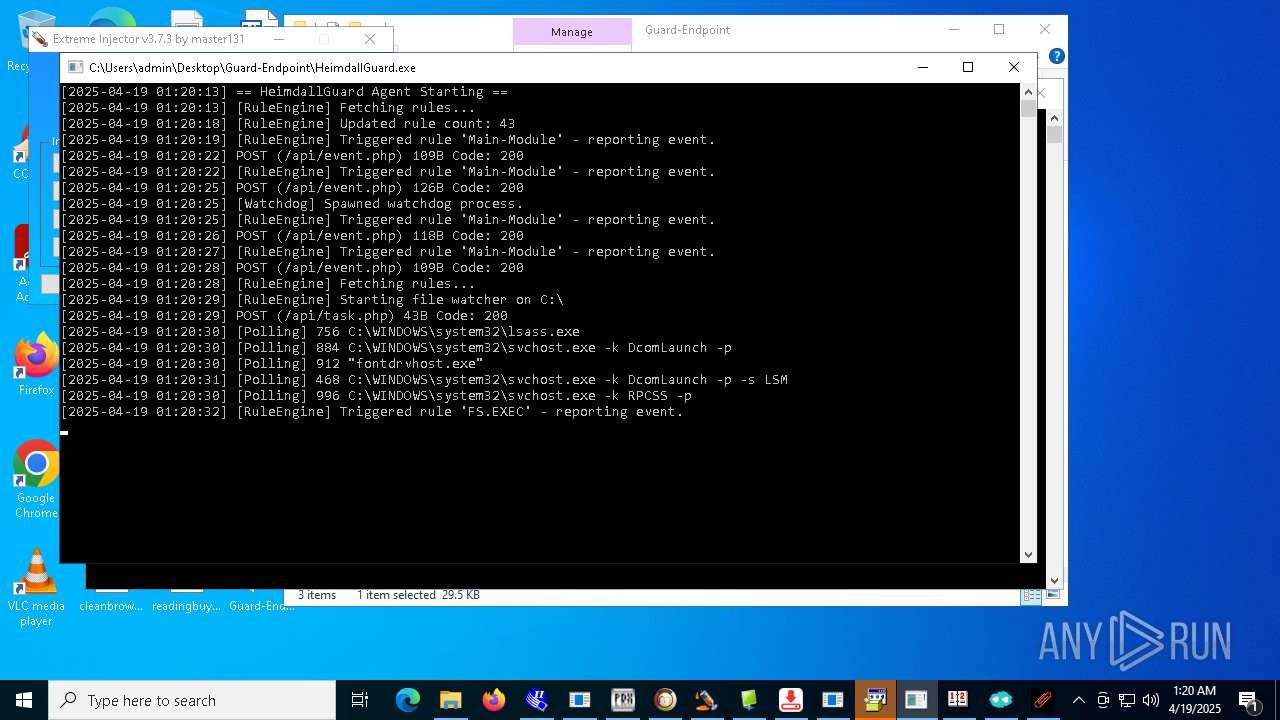
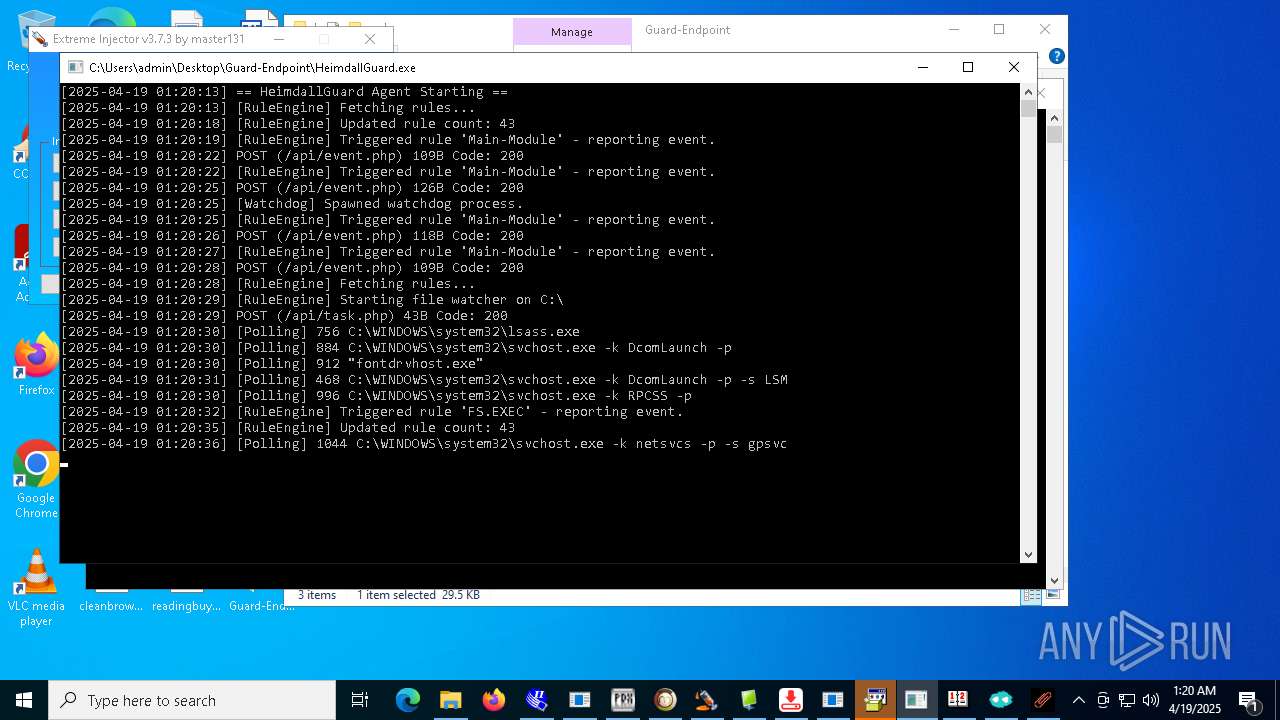
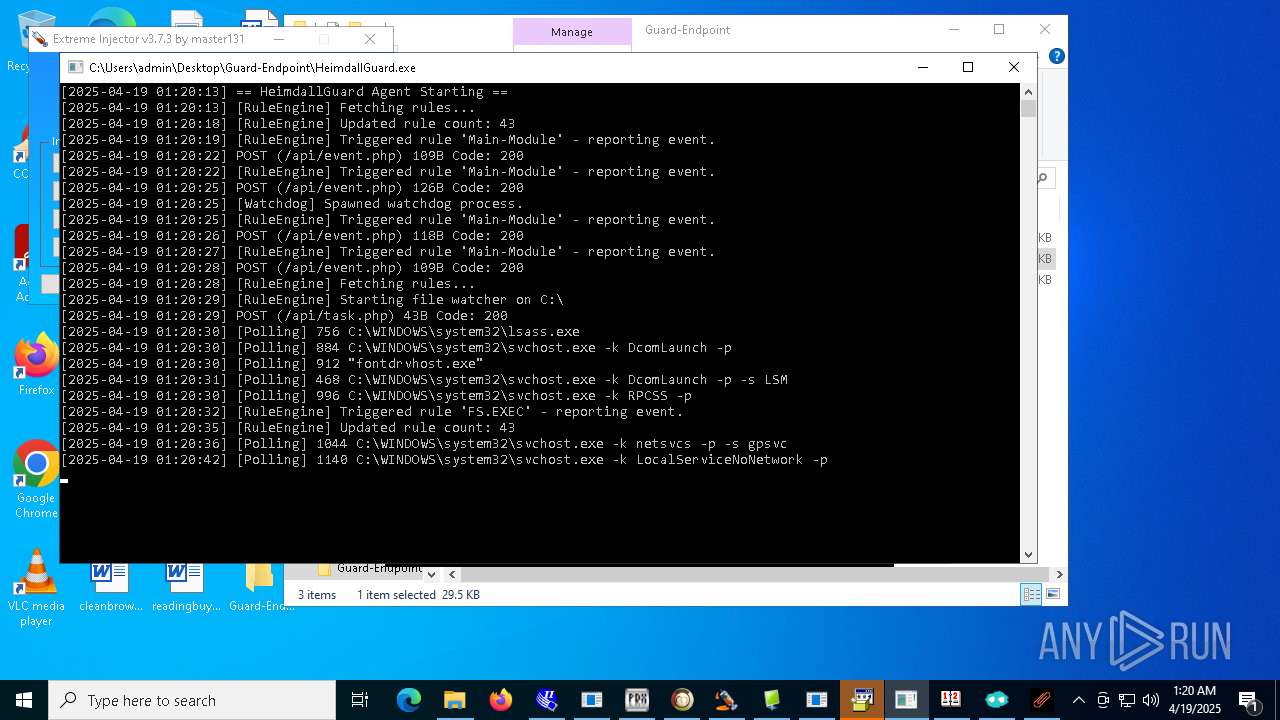
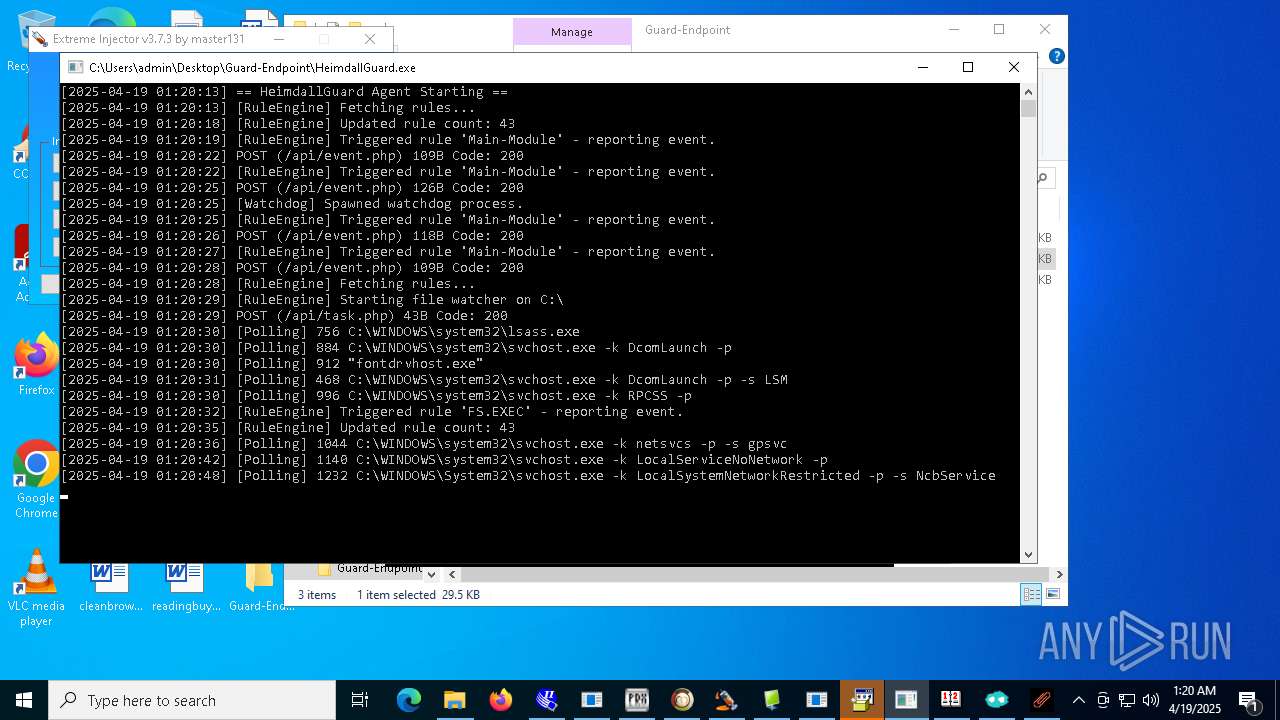
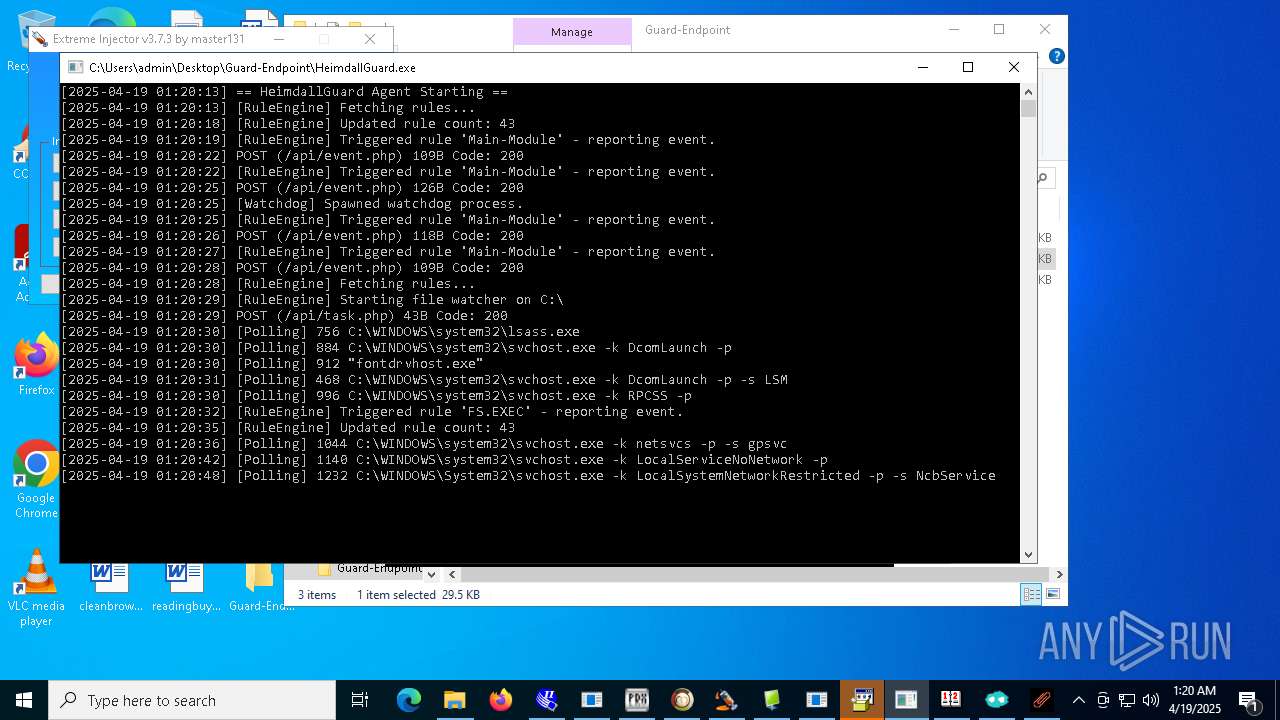
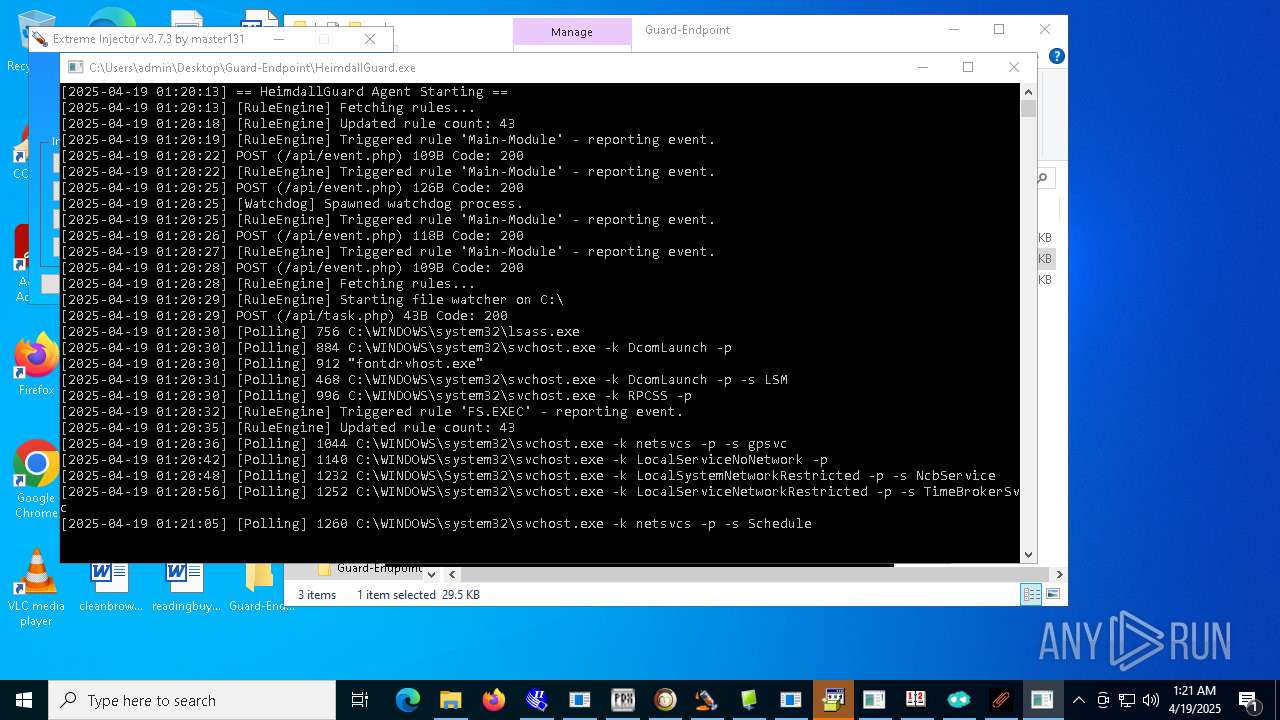
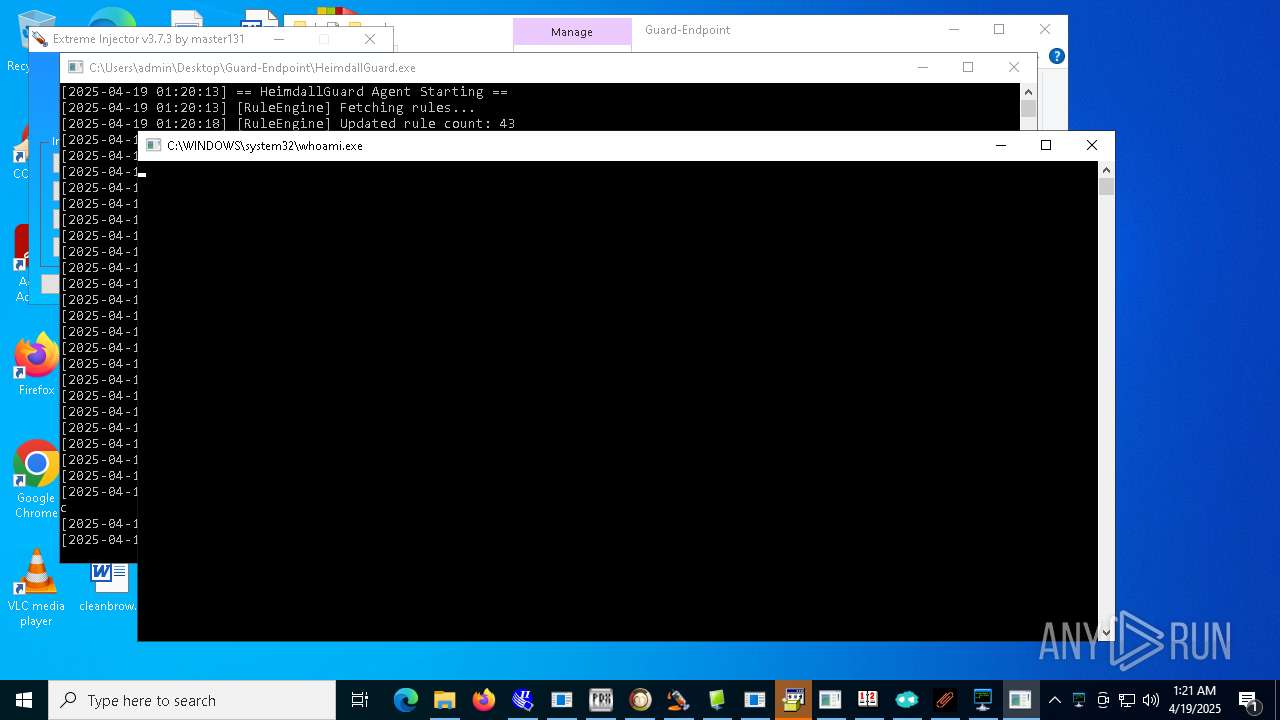
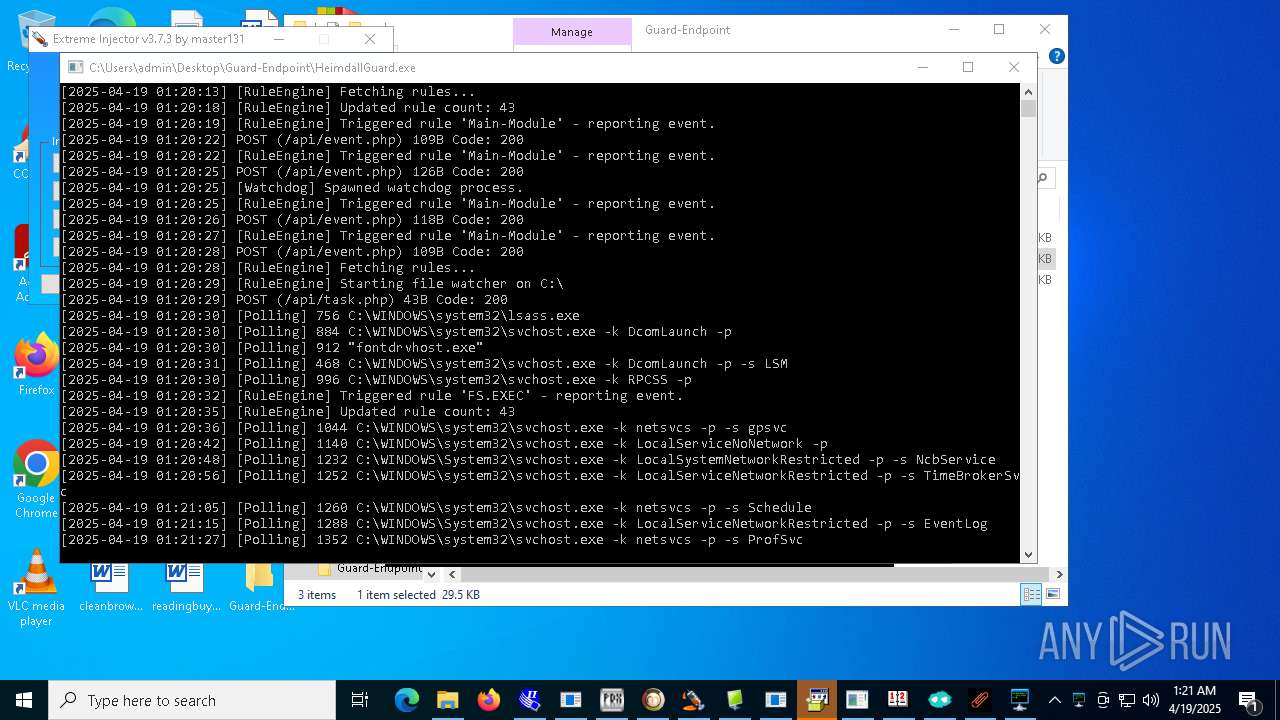
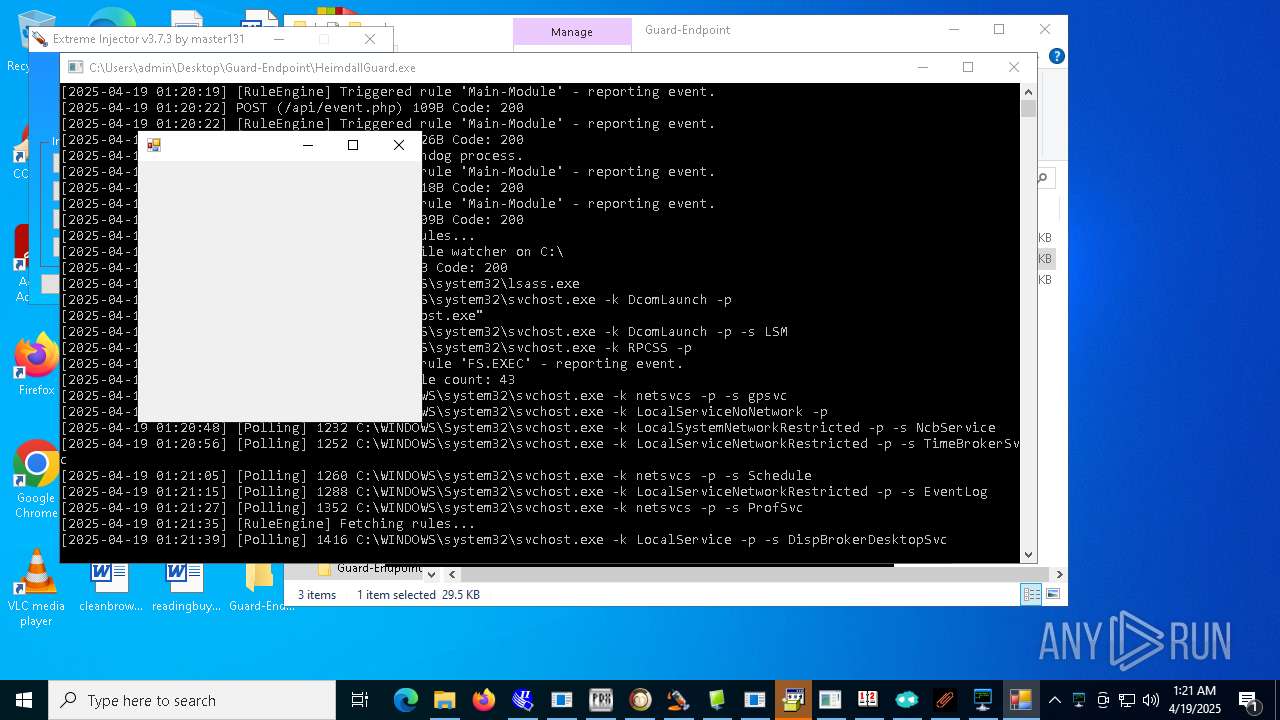
Connects to the CnC server
- svchost.exe (PID: 2196)
- 4363463463464363463463463.exe (PID: 6108)
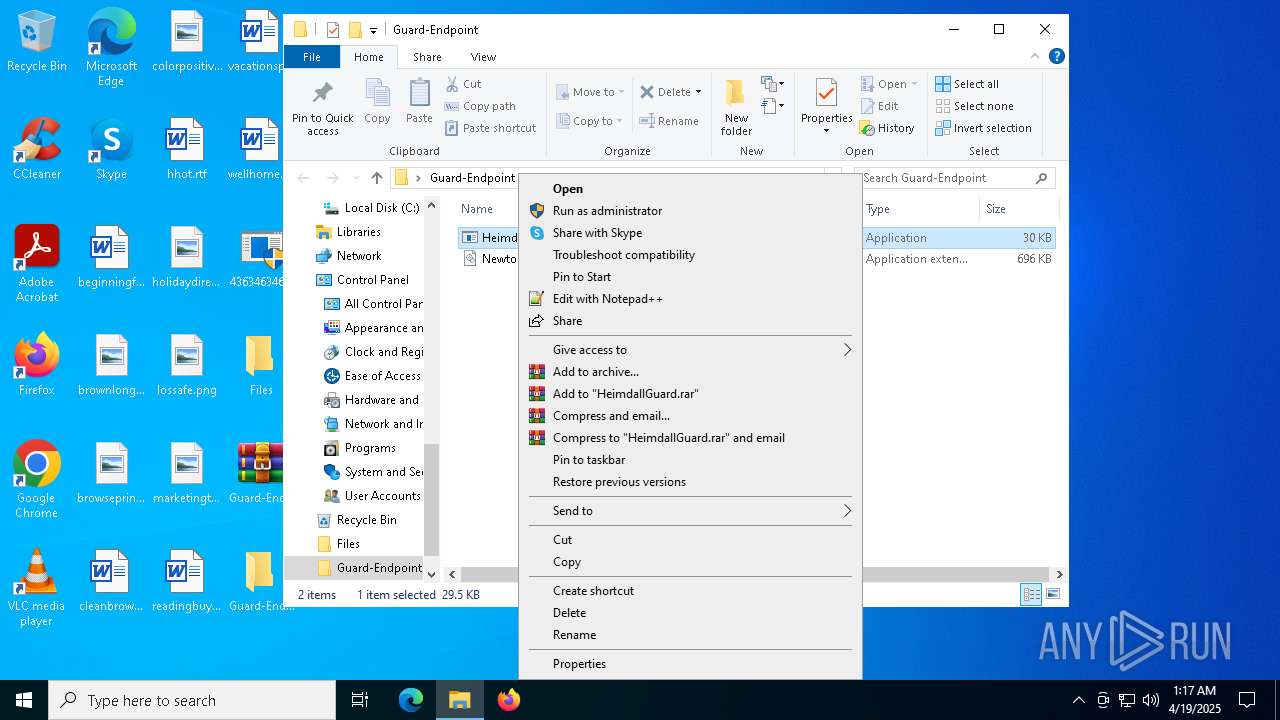
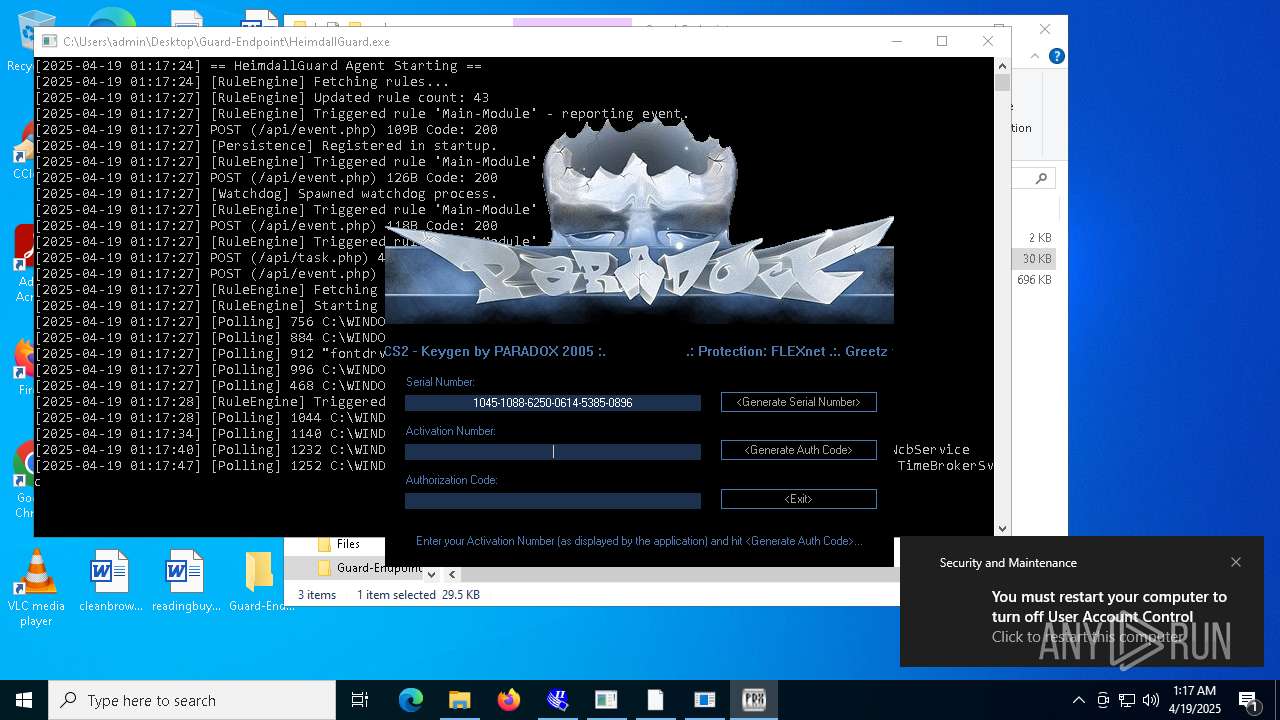
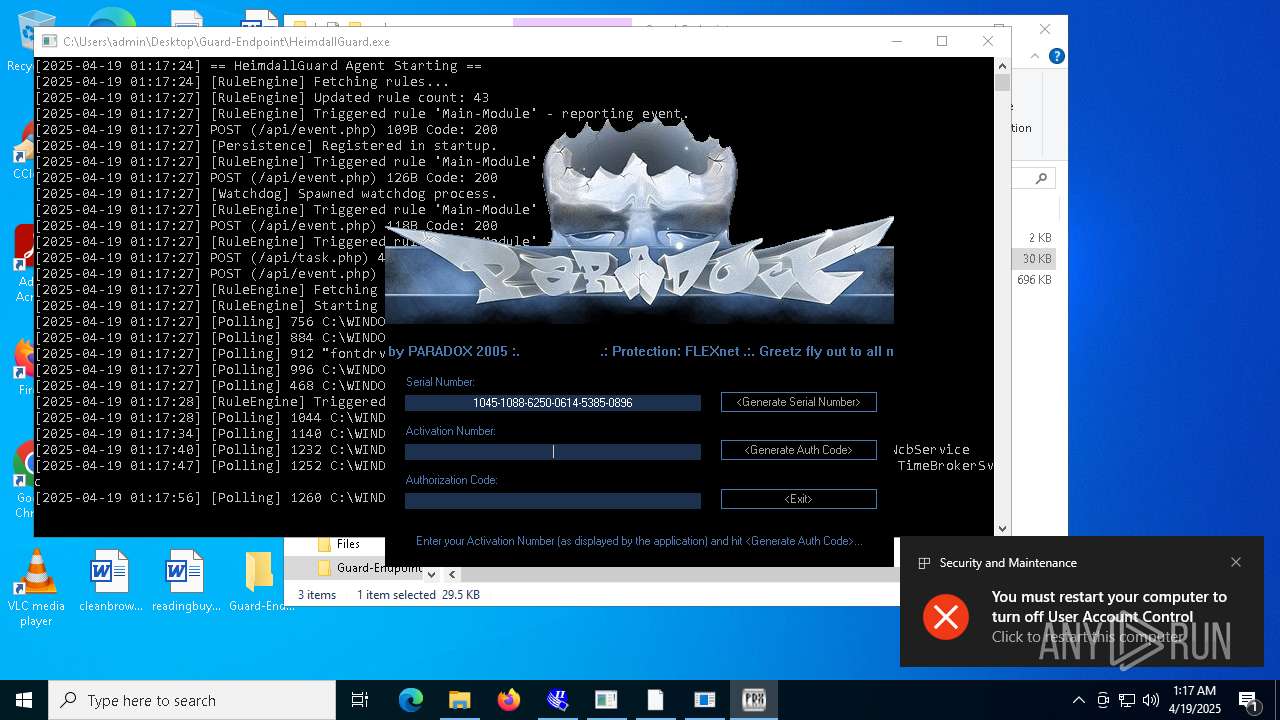
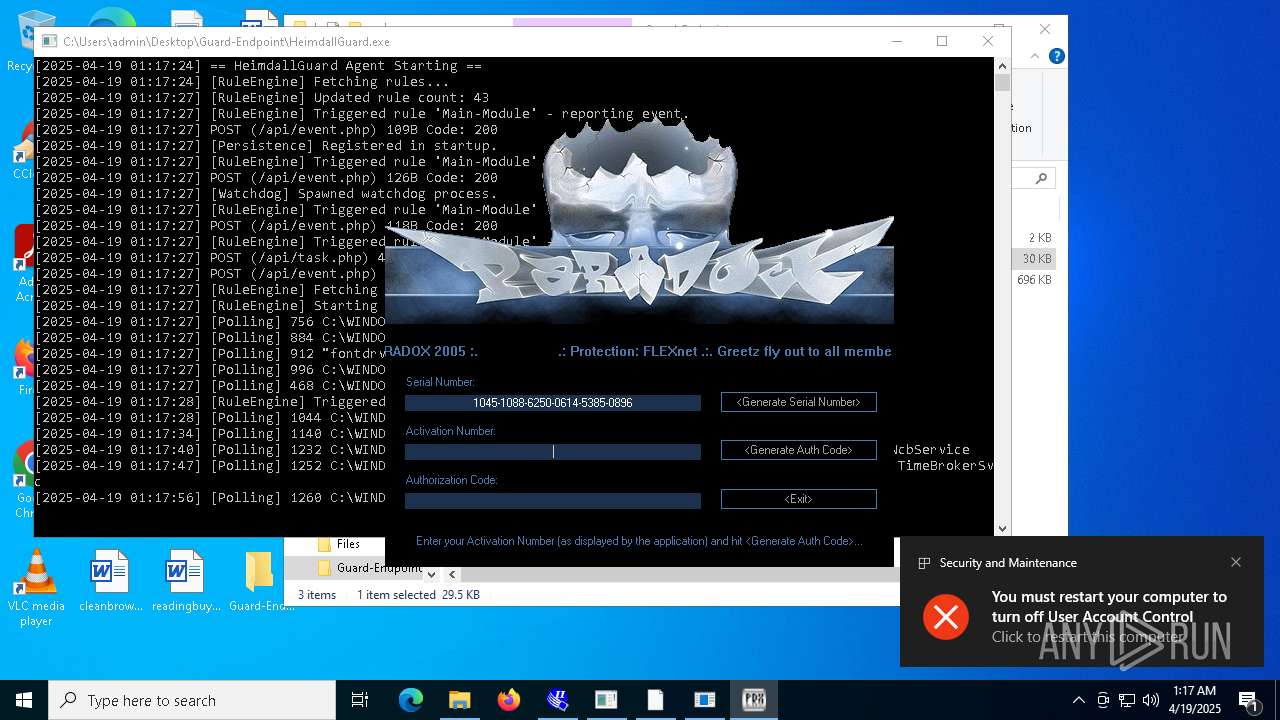
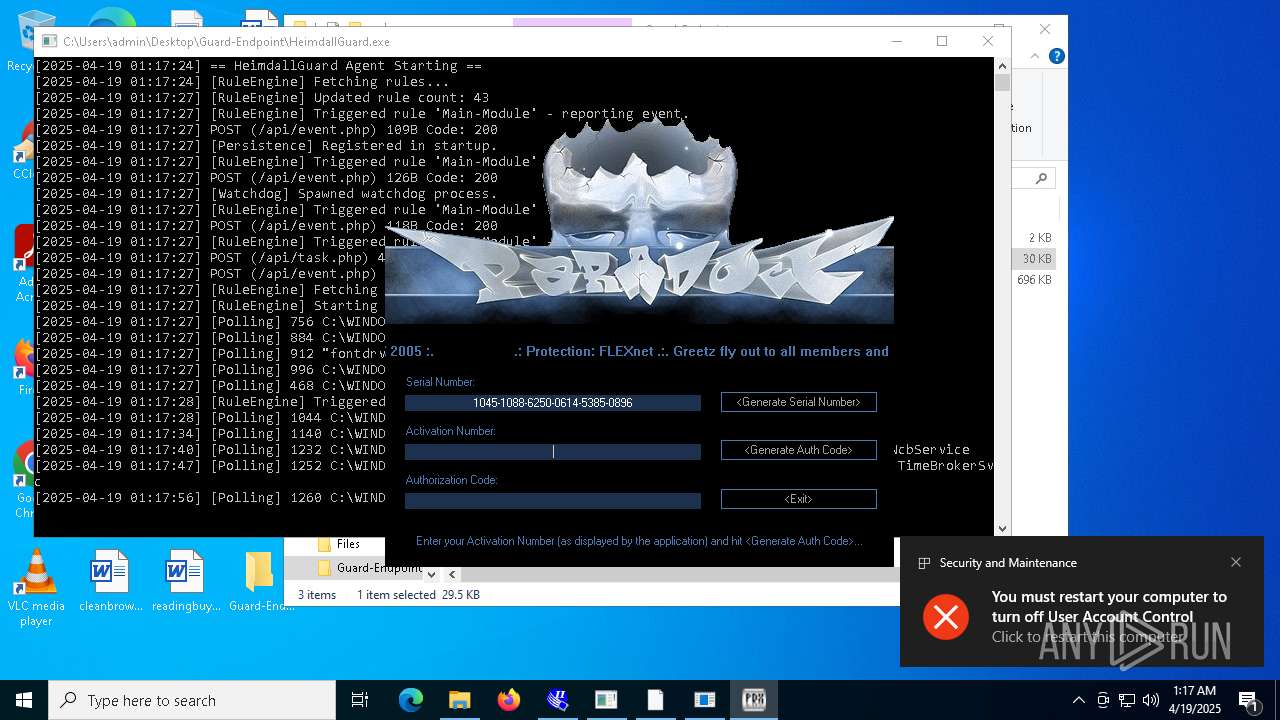
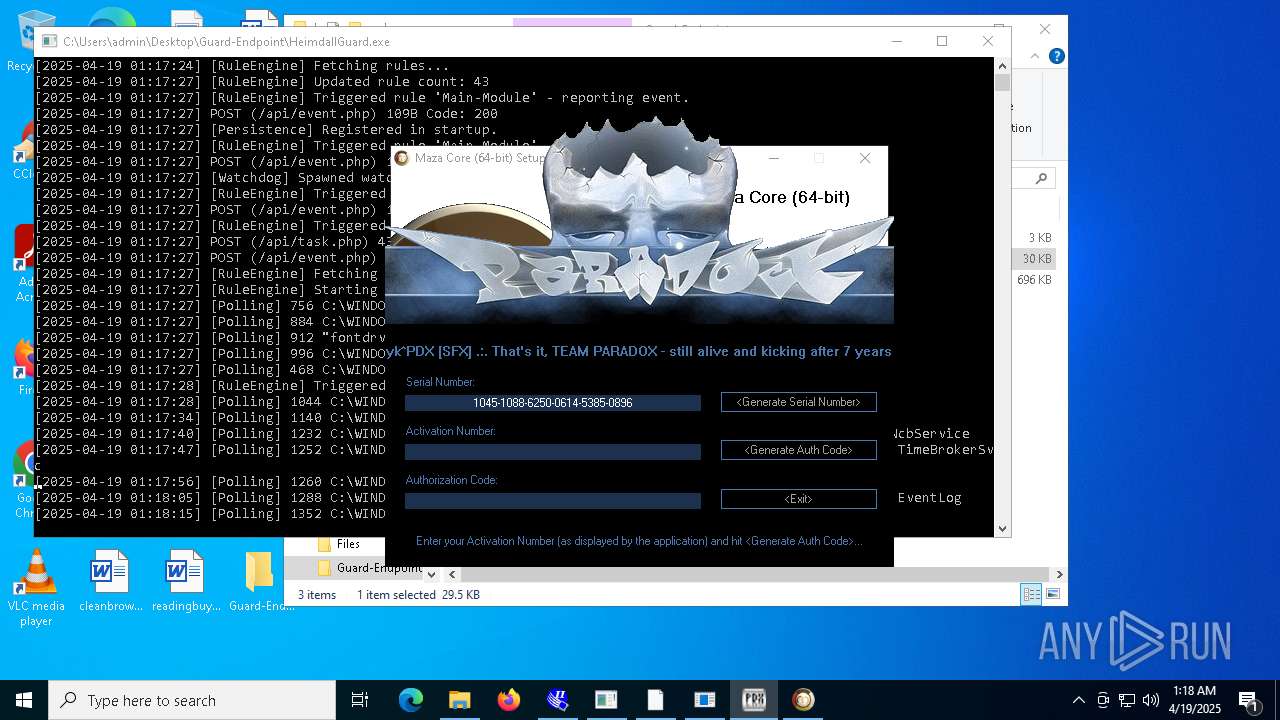
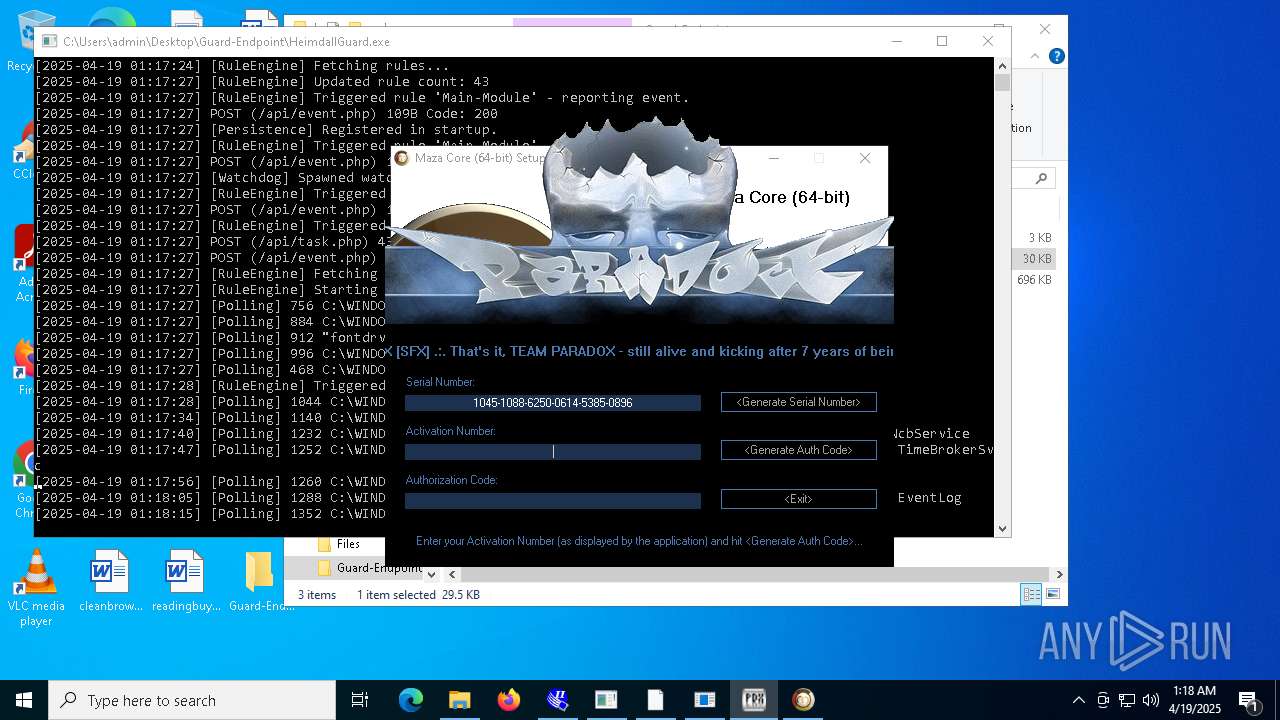
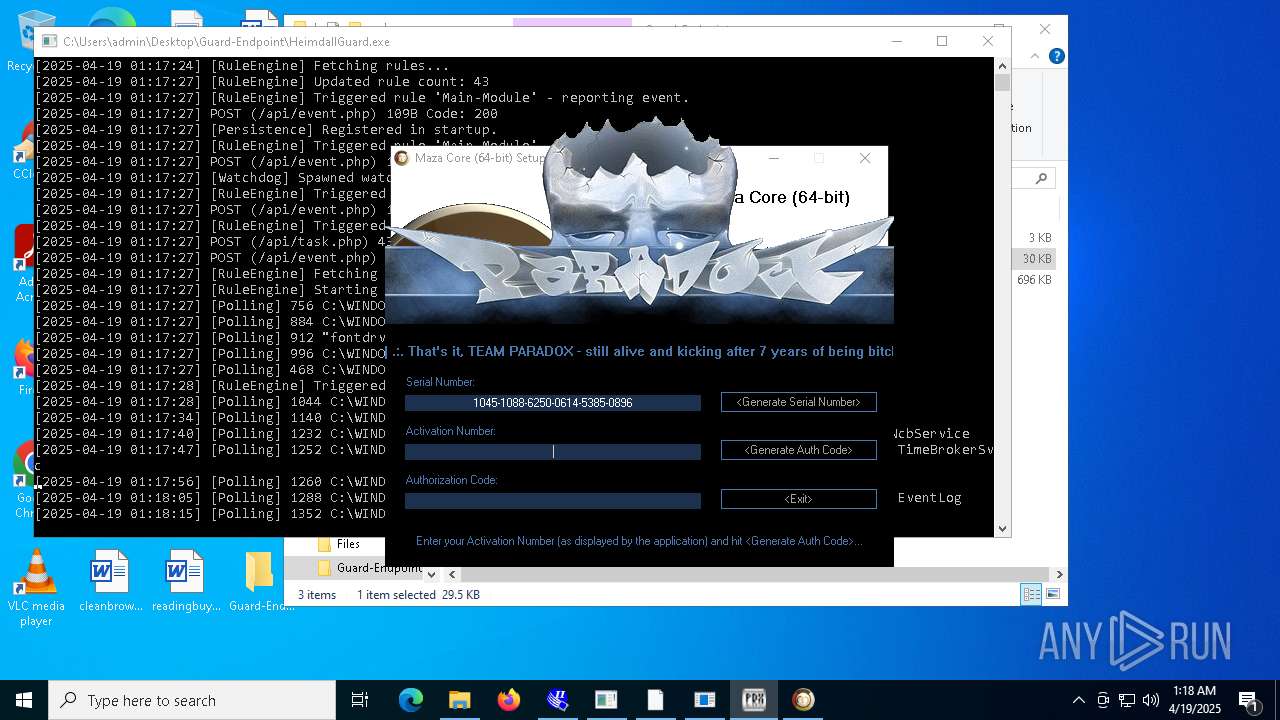
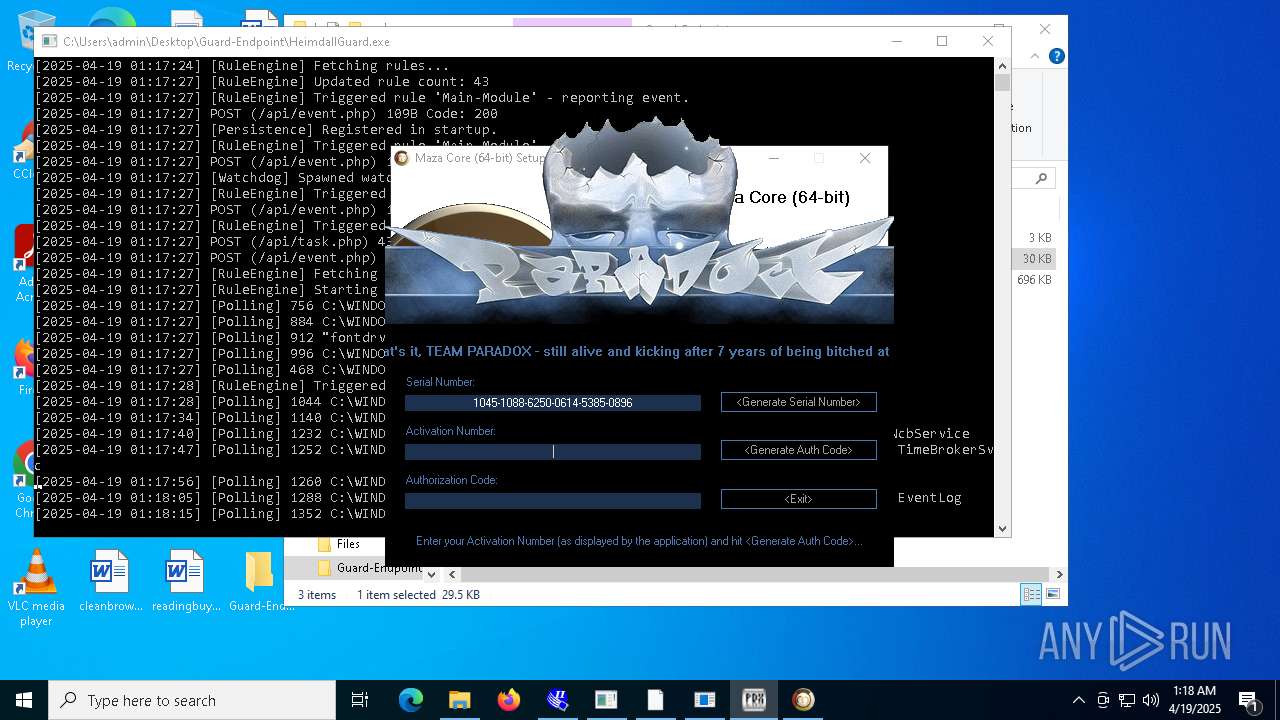
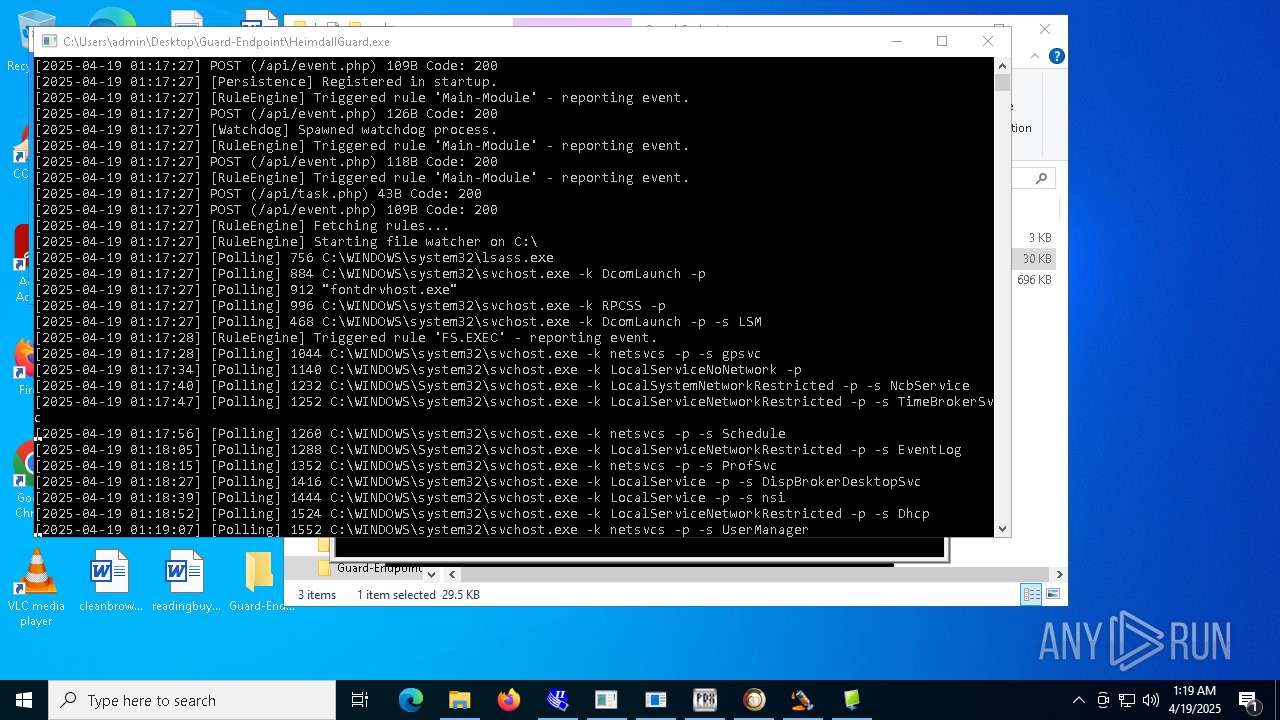
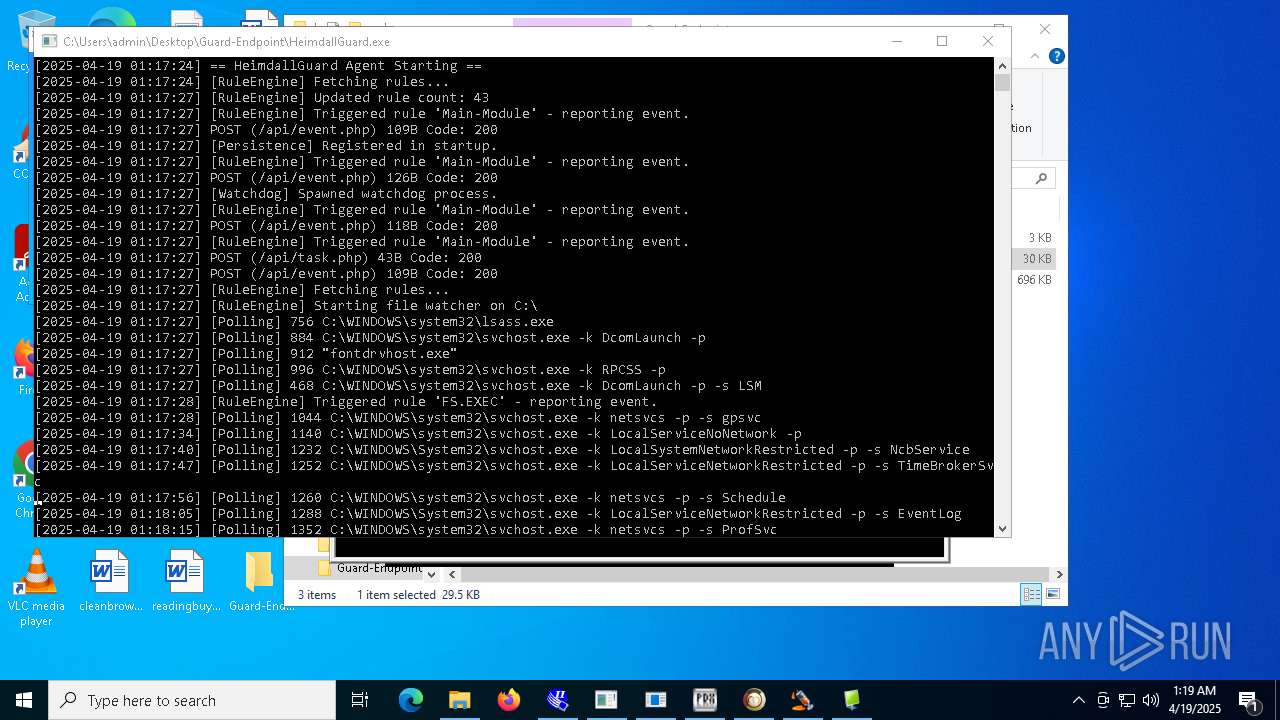
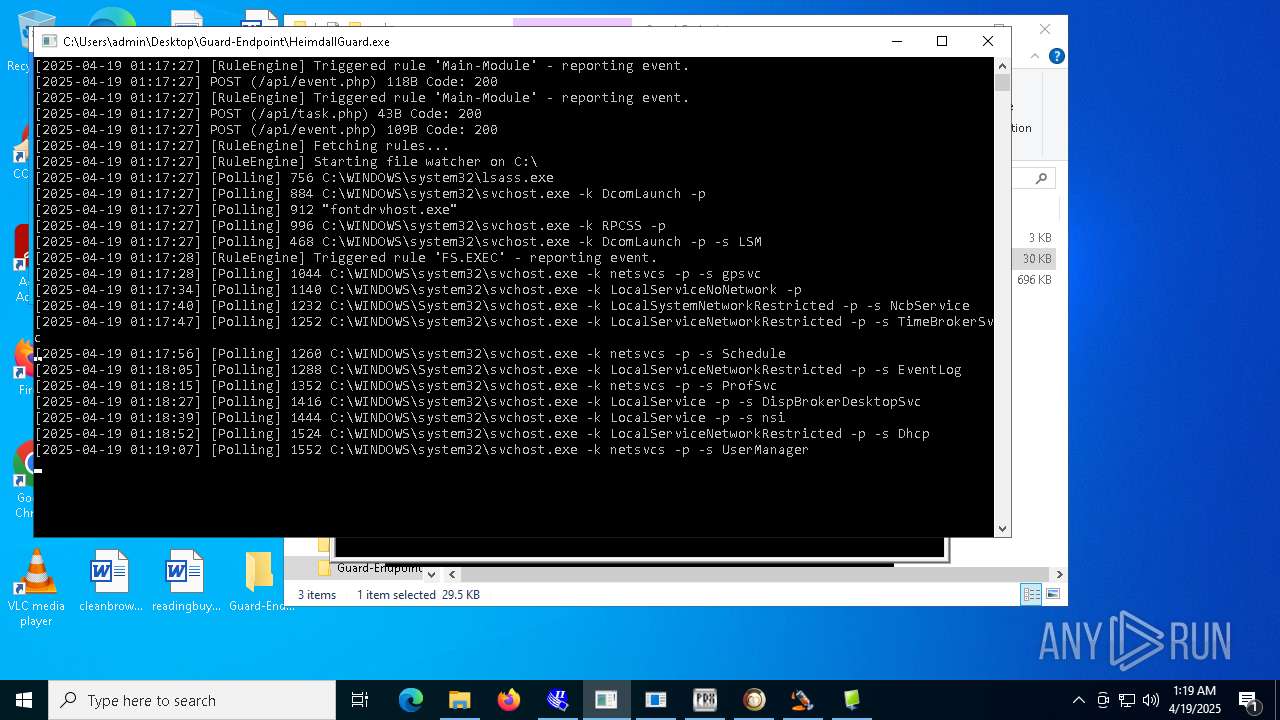
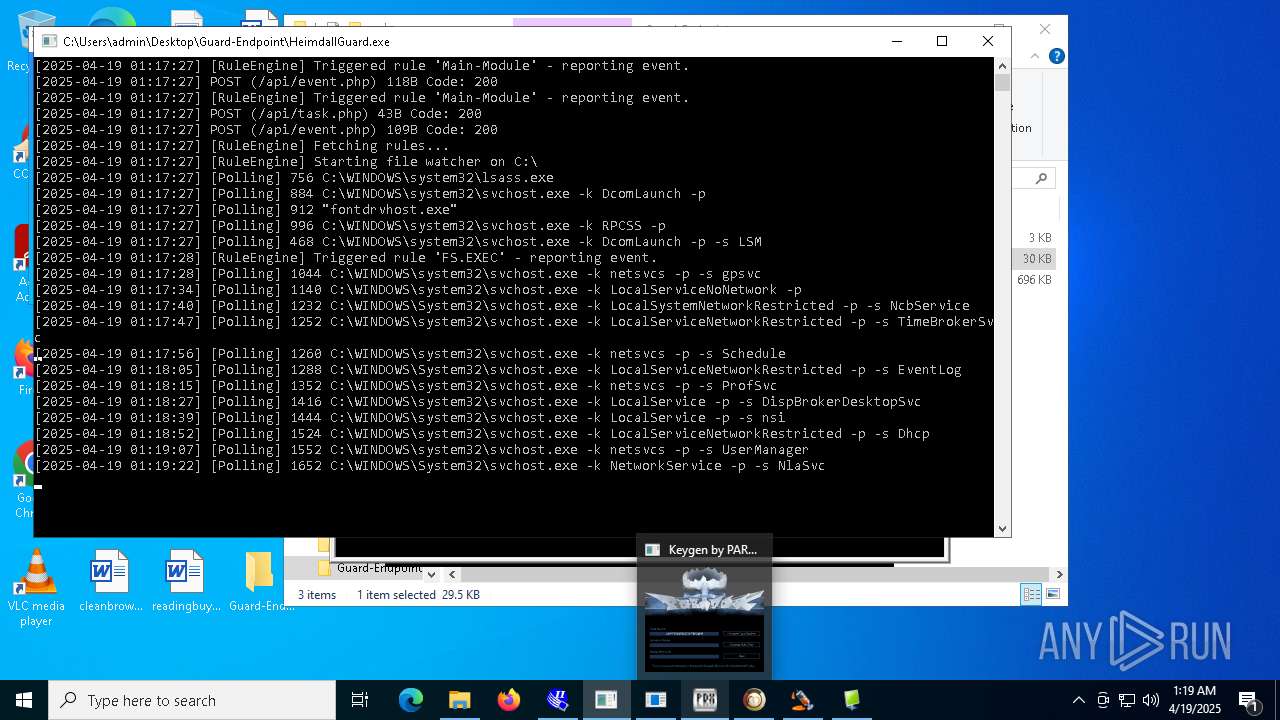
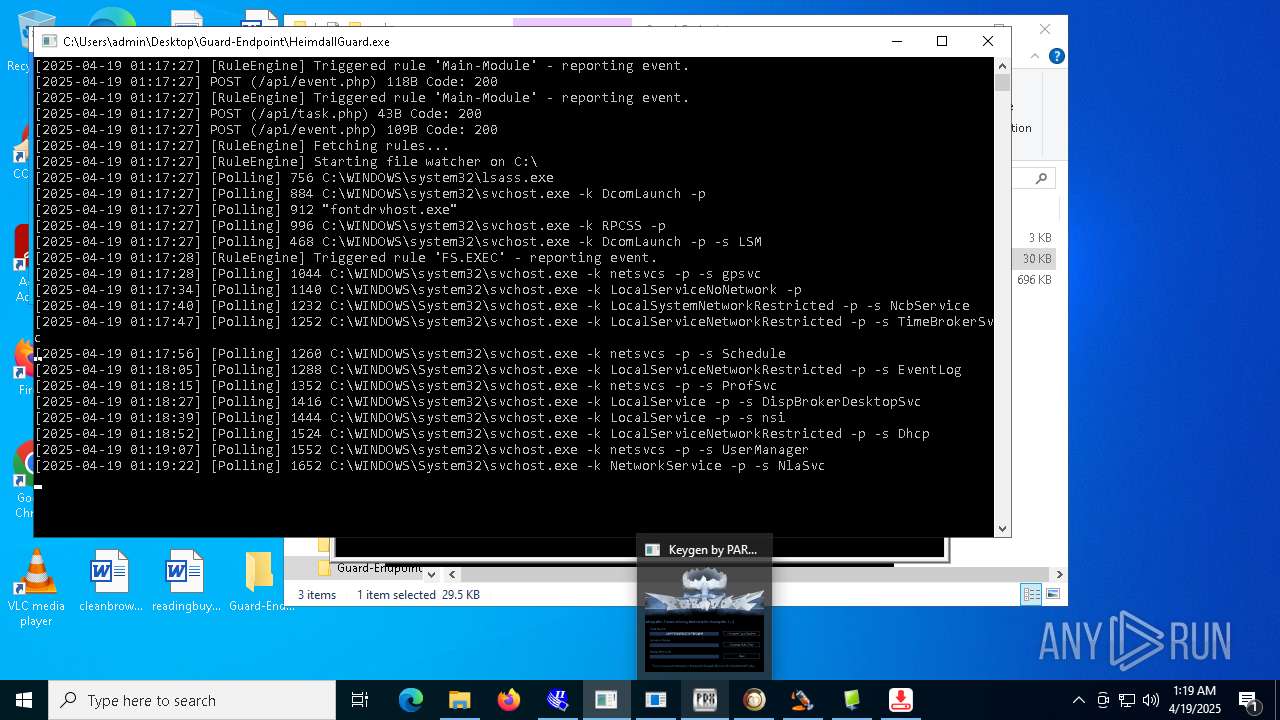
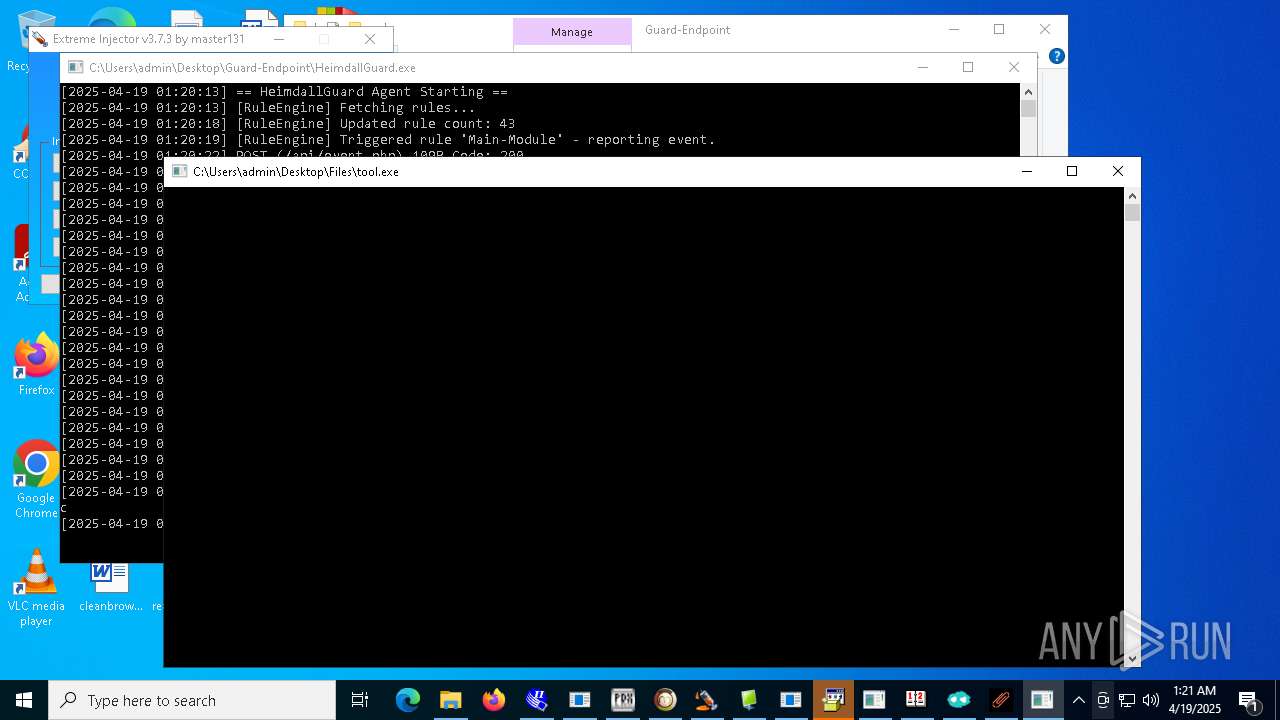
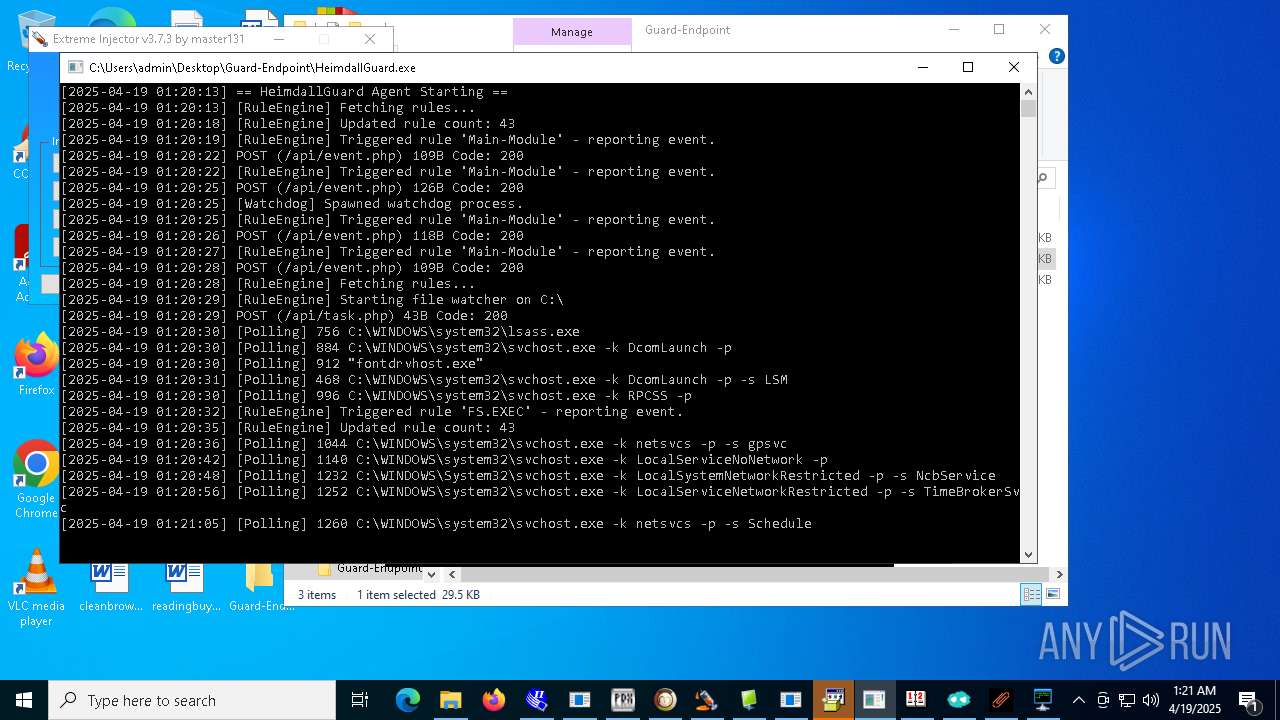
- HeimdallGuard.exe (PID: 6564)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- crypted.exe (PID: 10384)
- server.exe (PID: 12672)
LUMMA mutex has been found
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 10908)
- MSBuild.exe (PID: 12148)
- MSBuild.exe (PID: 10036)
Steals credentials from Web Browsers
- MSBuild.exe (PID: 5964)
- crypted.exe (PID: 10384)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- Build.exe (PID: 3396)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- MSBuild.exe (PID: 12148)
- MSBuild.exe (PID: 10036)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 10908)
- comp.exe (PID: 3976)
- crypted.exe (PID: 10384)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- Build.exe (PID: 3396)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- MSBuild.exe (PID: 12148)
- MSBuild.exe (PID: 10036)
Changes the autorun value in the registry
- MSystem32.exe (PID: 2772)
- HeimdallGuard.exe (PID: 6564)
- FXServer.exe (PID: 8272)
- GoogleUpdate.exe (PID: 8316)
- Server.exe (PID: 5156)
- Network.exe (PID: 7652)
- XClient.exe (PID: 2516)
- new.exe (PID: 8952)
- stub.exe (PID: 11160)
- dllhost.exe (PID: 11248)
- crypted.exe (PID: 10384)
- NOTallowedtocrypt.exe (PID: 12800)
- 76y5trfed675ytg.exe (PID: 10580)
Create files in the Startup directory
- Fast%20Download.exe (PID: 4040)
- Network.exe (PID: 7652)
- XClient.exe (PID: 2516)
- Loader.exe (PID: 10980)
- new.exe (PID: 8952)
- dllhost.exe (PID: 11248)
- server.exe (PID: 12672)
STEALER has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- wnsc.exe (PID: 11692)
Uses Task Scheduler to run other applications
- MSystem32.exe (PID: 2772)
- Network.exe (PID: 7652)
- XClient.exe (PID: 2516)
- Loader.exe (PID: 10980)
- new.exe (PID: 8952)
- dllhost.exe (PID: 11248)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
Stealers network behavior
- svchost.exe (PID: 2196)
Changes Windows Defender settings
- Network.exe (PID: 7652)
- cheese.exe (PID: 7920)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- payload.exe (PID: 3304)
Adds path to the Windows Defender exclusion list
- Network.exe (PID: 7652)
- cheese.exe (PID: 7920)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- payload.exe (PID: 3304)
Changes powershell execution policy (Bypass)
- Network.exe (PID: 7652)
- crypted.exe (PID: 10384)
- NJRAT%20DANGEROUS.exe (PID: 11104)
Bypass execution policy to execute commands
- powershell.exe (PID: 7824)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 9716)
- powershell.exe (PID: 7524)
- powershell.exe (PID: 11776)
QUASAR has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- diskutil.exe (PID: 8120)
- 4363463463464363463463463.exe (PID: 6108)
- msgde.exe (PID: 8528)
ASYNCRAT has been found (auto)
- AsyncClient.exe (PID: 7740)
NJRAT mutex has been found
- Fast%20Download.exe (PID: 4040)
- Server.exe (PID: 5156)
- main.exe (PID: 10648)
- dllhost.exe (PID: 11248)
GENERIC has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- 4363463463464363463463463.exe (PID: 6108)
- 4363463463464363463463463.exe (PID: 6108)
- 4363463463464363463463463.exe (PID: 6108)
- 4363463463464363463463463.exe (PID: 6108)
- 4363463463464363463463463.exe (PID: 6108)
- 4363463463464363463463463.exe (PID: 6108)
RAT has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
Adds process to the Windows Defender exclusion list
- Network.exe (PID: 7652)
REMCOS has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- FXServer.exe (PID: 8272)
REMCOS mutex has been found
- FXServer.exe (PID: 8272)
- GoogleUpdate.exe (PID: 8316)
- svchost.exe (PID: 8696)
- benpolatalemdar.exe (PID: 11488)
- prueba.exe (PID: 12660)
Attempting to scan the network
- Meredrop.exe (PID: 7356)
SMBSCAN has been detected (SURICATA)
- Meredrop.exe (PID: 7356)
UAC/LUA settings modification
- reg.exe (PID: 8660)
- reg.exe (PID: 7244)
- reg.exe (PID: 12292)
- reg.exe (PID: 12960)
- reg.exe (PID: 10248)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 8436)
Deletes a file (SCRIPT)
- wscript.exe (PID: 8436)
NJRAT has been detected (YARA)
- Microsoft_Hardware_Launch.exe (PID: 1180)
REMCOS has been detected
- GoogleUpdate.exe (PID: 8316)
- benpolatalemdar.exe (PID: 11488)
- prueba.exe (PID: 12660)
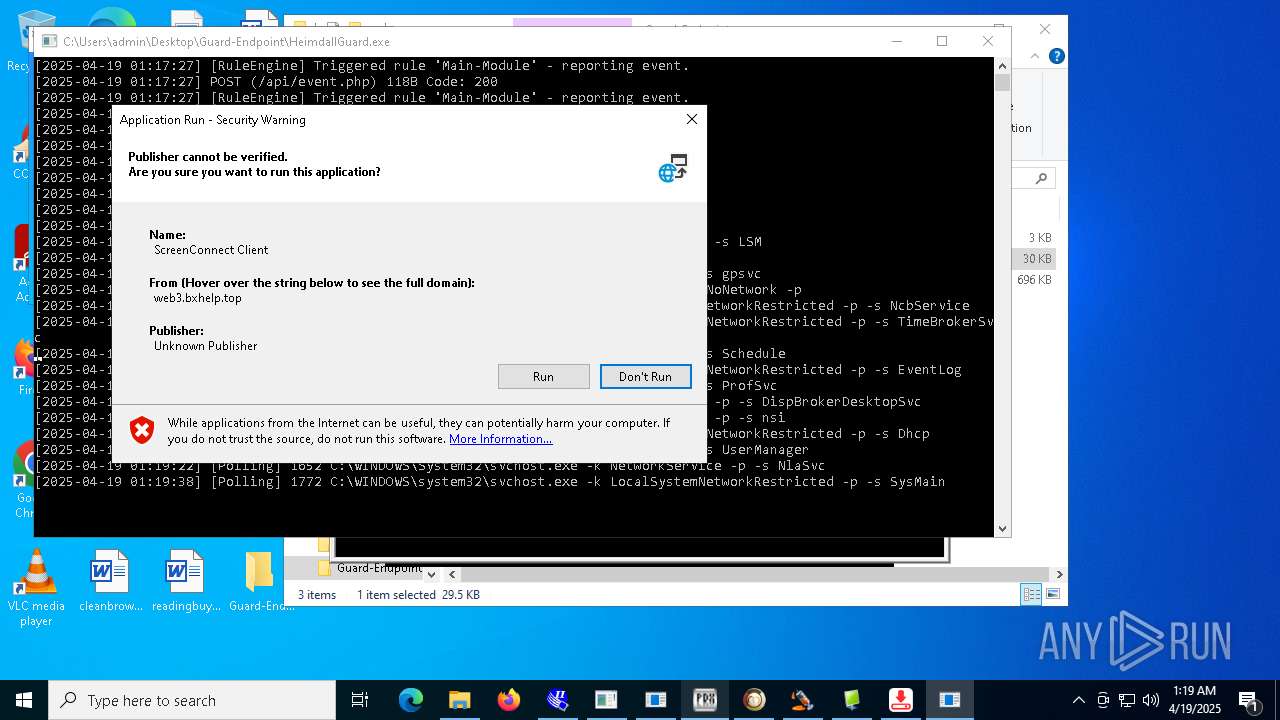
Executing a file with an untrusted certificate
- begin.exe (PID: 8412)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- KZMount2.exe (PID: 11300)
- InstallerPack_20.1.23770_win64.exe (PID: 10828)
- KZMount2.exe (PID: 6248)
- KuaiZip.exe (PID: 832)
- KZReport.exe (PID: 8028)
XWORM has been detected (SURICATA)
- Network.exe (PID: 7652)
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 10600)
- findstr.exe (PID: 10796)
CVE-2024-43451 has been detected
- dllhost.exe (PID: 11248)
FORMBOOK has been detected (SURICATA)
- HeimdallGuard.exe (PID: 6564)
RANSOMWARE has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
PURELOGS has been found (auto)
- 4363463463464363463463463.exe (PID: 6108)
- crypted.exe (PID: 10384)
Attempt to connect to SMB server
- System (PID: 4)
LOKIBOT mutex has been found
- M7XQmz2DgtiyE3f.exe (PID: 4220)
WebDav connection (SURICATA)
- Meredrop.exe (PID: 7356)
Scans artifacts that could help determine the target
- M7XQmz2DgtiyE3f.exe (PID: 4220)
Lokibot is detected
- M7XQmz2DgtiyE3f.exe (PID: 4220)
LOKIBOT has been detected (SURICATA)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
PURELOGS has been detected (SURICATA)
- crypted.exe (PID: 10384)
METASPLOIT has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 6108)
ASYNCRAT has been detected (MUTEX)
- Solara_Protect.exe (PID: 11996)
- Windows.exe (PID: 13028)
AZORULT mutex has been detected
- onetap.exe (PID: 12320)
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 12560)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 12284)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 12284)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 12284)
Changes settings for real-time protection
- powershell.exe (PID: 12284)
Changes Controlled Folder Access settings
- powershell.exe (PID: 12284)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 12284)
Signed with known abused certificate
- 4363463463464363463463463.exe (PID: 6108)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 12284)
Registers / Runs the DLL via REGSVR32.EXE
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
NjRAT is detected
- client.exe (PID: 12108)
Creates or modifies Windows services
- regsvr32.exe (PID: 13192)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 7932)
NESHTA mutex has been found
- wnsc.exe (PID: 11692)
- svchost.com (PID: 10288)
WANNACRY has been detected
- WannaCry.exe (PID: 12760)
WANNACRY mutex has been found
- WannaCry.exe (PID: 12760)
NJRAT has been detected (SURICATA)
- server.exe (PID: 12672)
SUSPICIOUS
Reads security settings of Internet Explorer
- InstructionalPostings.exe (PID: 1116)
- 4363463463464363463463463.exe (PID: 6108)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- Network.exe (PID: 7652)
- Clients.exe (PID: 7420)
- AsyncClient.exe (PID: 7740)
- Client.exe (PID: 7448)
- PerfWatson1.exe (PID: 7404)
- alphaTweaks.exe (PID: 7808)
- cheese.exe (PID: 7920)
- FXServer.exe (PID: 8272)
- RuntimeBrokerSvc.exe (PID: 7404)
- ShellExperienceHost.exe (PID: 8216)
- Client.exe (PID: 9072)
- Clients.exe (PID: 9000)
- PerfWatson1.exe (PID: 9160)
- Client1.exe (PID: 10144)
- Clients.exe (PID: 5188)
- Client.exe (PID: 5964)
- PerfWatson1.exe (PID: 9012)
- XClient.exe (PID: 2516)
- OfferedBuilt.exe (PID: 8544)
- Clients.exe (PID: 6824)
- PerfWatson1.exe (PID: 9012)
- windows 3543.exe (PID: 7380)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- main.exe (PID: 10648)
- Clients.exe (PID: 10360)
- Loader.exe (PID: 10980)
- new.exe (PID: 8952)
- PerfWatson1.exe (PID: 11224)
- PerfWatson1.exe (PID: 10812)
- Clients.exe (PID: 10100)
- Clients.exe (PID: 10280)
- dfsvc.exe (PID: 540)
- PerfWatson1.exe (PID: 9852)
- windows 3543.exe (PID: 9280)
- crypted.exe (PID: 10384)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- CritScript.exe (PID: 11900)
- Clients.exe (PID: 11292)
- HeimdallGuard.exe (PID: 7992)
- Solara_Protect.exe (PID: 11996)
- PerfWatson1.exe (PID: 12044)
- Meredrop.exe (PID: 7356)
- 99999.exe (PID: 12028)
- onetap.exe (PID: 12320)
- NOTallowedtocrypt.exe (PID: 12800)
- ENP.exe (PID: 6744)
- Clients.exe (PID: 12092)
- windows 3543.exe (PID: 8032)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- tstory.exe (PID: 2204)
- PerfWatson1.exe (PID: 5176)
- wnsc.exe (PID: 11692)
Executing commands from a ".bat" file
- InstructionalPostings.exe (PID: 1116)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- AsyncClient.exe (PID: 7740)
- Clients.exe (PID: 7420)
- Client.exe (PID: 7448)
- PerfWatson1.exe (PID: 7404)
- Clients.exe (PID: 9000)
- Client.exe (PID: 9072)
- RuntimeBrokerSvc.exe (PID: 7404)
- PerfWatson1.exe (PID: 9160)
- Client.exe (PID: 5964)
- Clients.exe (PID: 5188)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 6824)
- PerfWatson1.exe (PID: 9012)
- windows 3543.exe (PID: 7380)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- Clients.exe (PID: 10360)
- PerfWatson1.exe (PID: 11224)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- Clients.exe (PID: 10280)
- PerfWatson1.exe (PID: 9852)
- windows 3543.exe (PID: 9280)
- Clients.exe (PID: 11292)
- Solara_Protect.exe (PID: 11996)
- PerfWatson1.exe (PID: 12044)
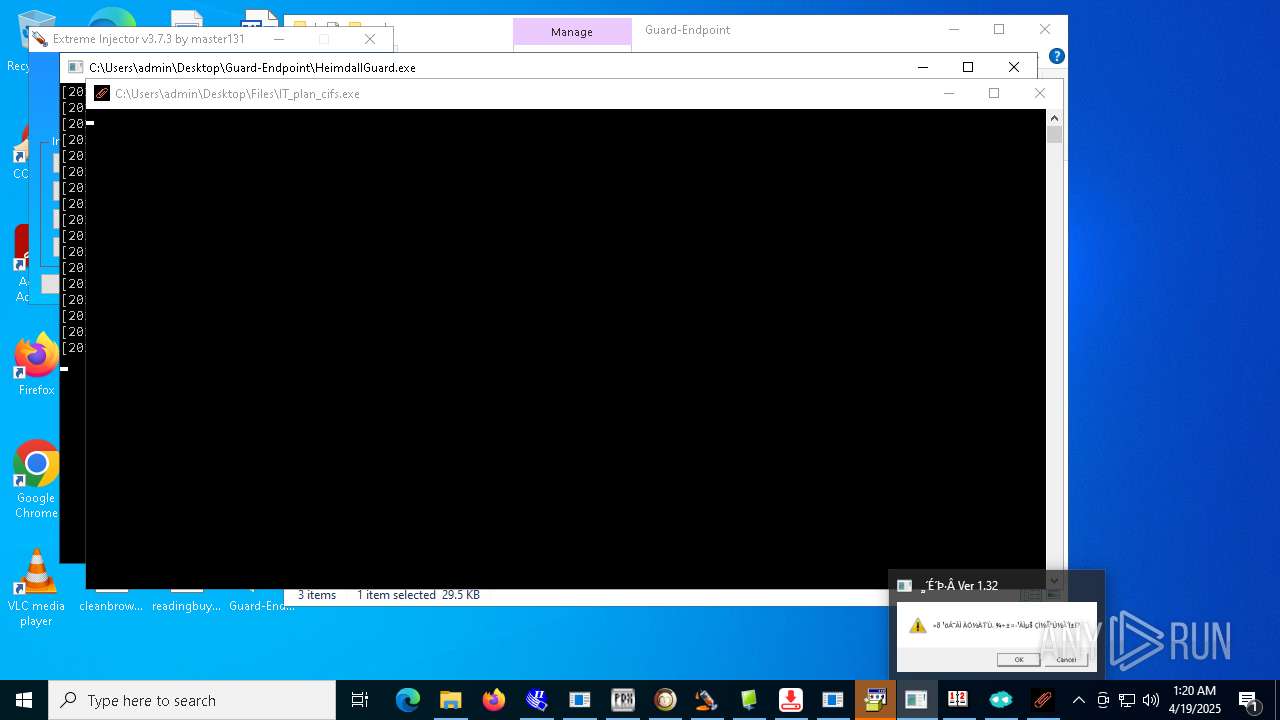
- IT_plan_cifs.exe (PID: 10684)
- Clients.exe (PID: 12092)
- windows 3543.exe (PID: 8032)
- PerfWatson1.exe (PID: 5176)
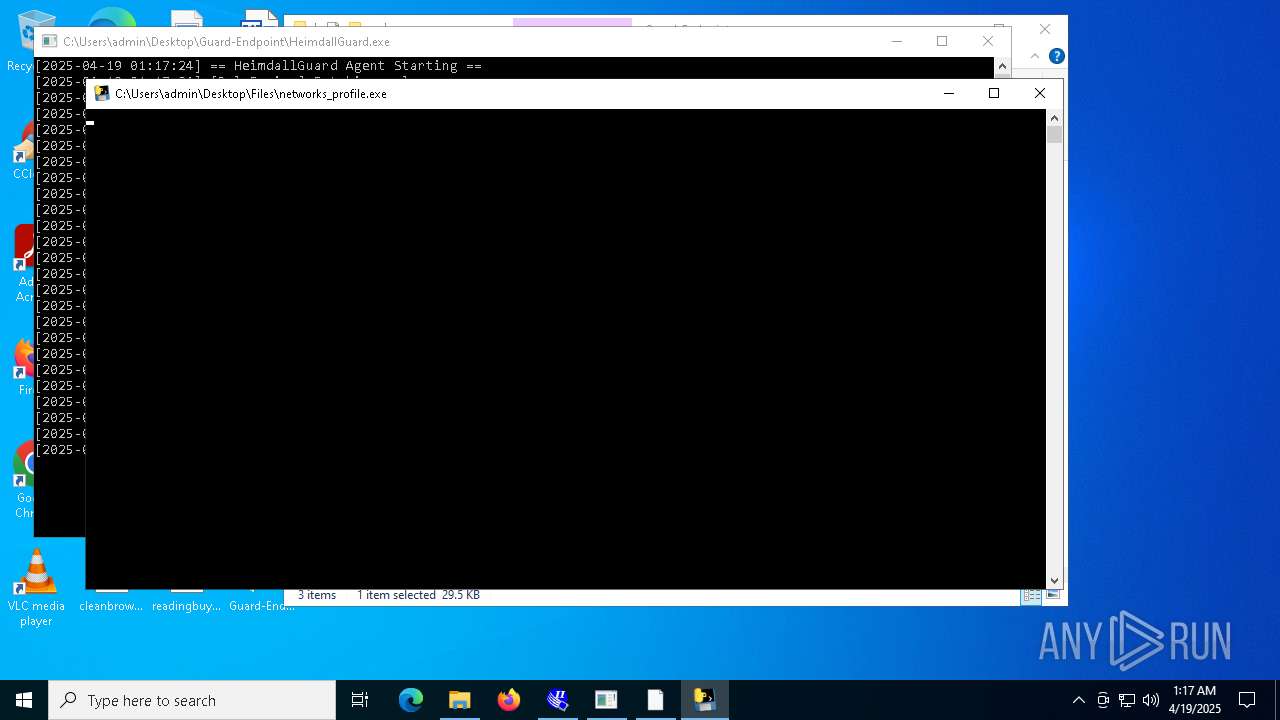
Starts CMD.EXE for commands execution
- InstructionalPostings.exe (PID: 1116)
- cmd.exe (PID: 2384)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- AsyncClient.exe (PID: 7740)
- Clients.exe (PID: 7420)
- PerfWatson1.exe (PID: 7404)
- Client.exe (PID: 7448)
- networks_profile.exe (PID: 2332)
- FXServer.exe (PID: 8272)
- cheese.exe (PID: 7920)
- svchost.exe (PID: 7860)
- wscript.exe (PID: 8436)
- GoogleUpdate.exe (PID: 8316)
- RuntimeBrokerSvc.exe (PID: 7404)
- Clients.exe (PID: 9000)
- Client.exe (PID: 9072)
- PerfWatson1.exe (PID: 9160)
- Client.exe (PID: 5964)
- Clients.exe (PID: 5188)
- PerfWatson1.exe (PID: 9012)
- OfferedBuilt.exe (PID: 8544)
- Clients.exe (PID: 6824)
- PerfWatson1.exe (PID: 9012)
- windows 3543.exe (PID: 7380)
- cmd.exe (PID: 9420)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- main.exe (PID: 10648)
- Clients.exe (PID: 10360)
- PerfWatson1.exe (PID: 11224)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- Clients.exe (PID: 10280)
- PerfWatson1.exe (PID: 9852)
- windows 3543.exe (PID: 9280)
- crypted.exe (PID: 10384)
- Build.exe (PID: 3396)
- Clients.exe (PID: 11292)
- Solara_Protect.exe (PID: 11996)
- PerfWatson1.exe (PID: 12044)
- NOTallowedtocrypt.exe (PID: 12800)
- 76y5trfed675ytg.exe (PID: 10580)
- IT_plan_cifs.exe (PID: 10684)
- Clients.exe (PID: 12092)
- windows 3543.exe (PID: 8032)
- PerfWatson1.exe (PID: 5176)
- wnsc.exe (PID: 12740)
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 6108)
- Client-built.exe (PID: 6656)
- built.exe (PID: 5116)
- MSystem32.exe (PID: 2772)
- Quas_Brout_ncrypt.exe (PID: 8164)
- AsyncClient.exe (PID: 7740)
- diskutil.exe (PID: 8120)
- svchost.exe (PID: 7804)
- networks_profile.exe (PID: 7268)
- FXServer.exe (PID: 8272)
- msgde.exe (PID: 8528)
- RuntimeBrokerSvc.exe (PID: 7404)
- JJSPLOIT.V2.exe (PID: 9024)
- Sentil.exe (PID: 8016)
- Network.exe (PID: 7652)
- maza-0.16.3-win64-setup-unsigned.exe (PID: 8464)
- discord.exe (PID: 5380)
- XClient.exe (PID: 2516)
- NdisInstaller3.2.32.1.exe (PID: 9040)
- snetcfg.exe (PID: 8524)
- drvinst.exe (PID: 9820)
- cmd.exe (PID: 9420)
- Mph.pif (PID: 6656)
- main.exe (PID: 10648)
- new.exe (PID: 8952)
- Loader.exe (PID: 10980)
- cheet.exe (PID: 10744)
- dllhost.exe (PID: 11248)
- Load.exe (PID: 9076)
- Update.exe (PID: 1184)
- RuntimeBroker.exe (PID: 11084)
- crypted.exe (PID: 10384)
- CleanerV2.exe (PID: 8328)
- spectrum.exe (PID: 9236)
- CritScript.exe (PID: 11900)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- JUSCHED.EXE (PID: 12172)
- CollosalLoader.exe (PID: 7136)
- Solara_Protect.exe (PID: 11996)
- 99999.exe (PID: 12028)
- NOTallowedtocrypt.exe (PID: 12800)
- server.exe (PID: 12672)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- KZMount2.exe (PID: 6248)
- wnsc.exe (PID: 11692)
- 4.exe (PID: 11512)
- WannaCry.exe (PID: 12760)
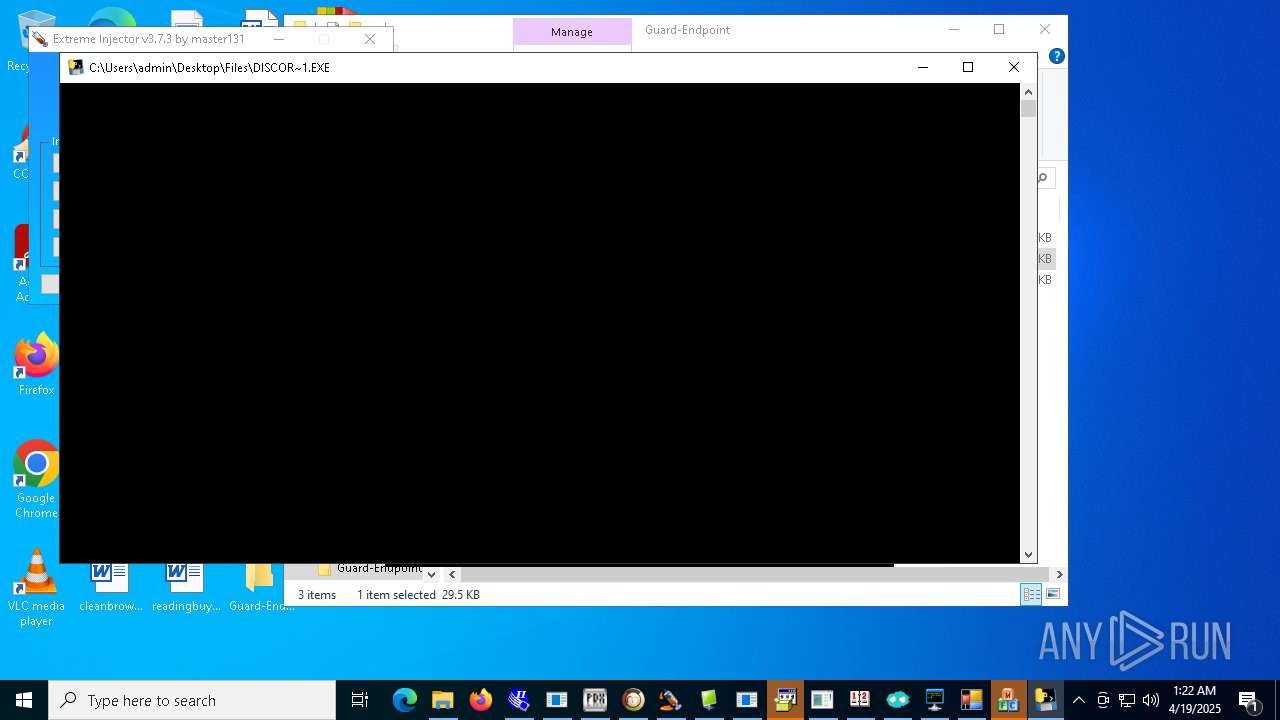
- DiscordNitroGenerator.exe (PID: 2316)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 6108)
- Meredrop.exe (PID: 7356)
- svchost.exe (PID: 2196)
- System (PID: 4)
- Update.exe (PID: 1184)
- calendar.exe (PID: 12012)
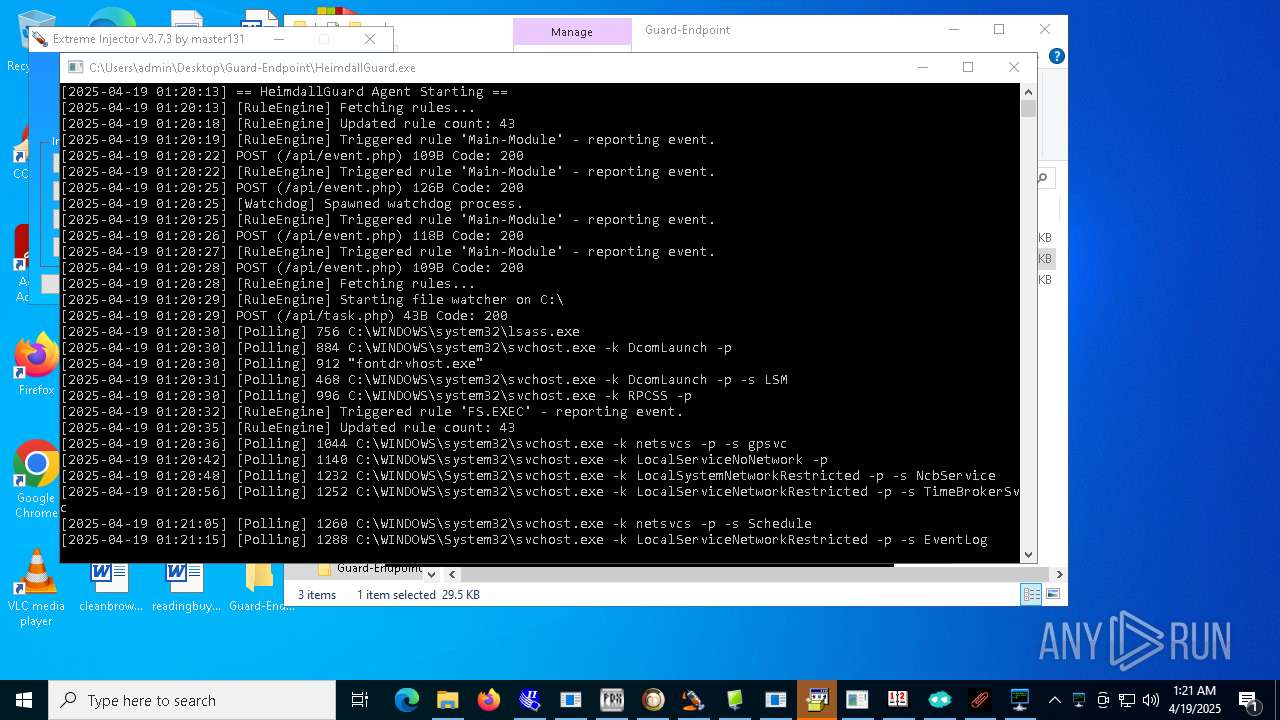
- tool.exe (PID: 11972)
Process drops legitimate windows executable
- 4363463463464363463463463.exe (PID: 6108)
- diskutil.exe (PID: 8120)
- svchost.exe (PID: 7804)
- networks_profile.exe (PID: 7268)
- Load.exe (PID: 9076)
- 4.exe (PID: 11512)
- WannaCry.exe (PID: 12760)
- DiscordNitroGenerator.exe (PID: 2316)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 6108)
- Update.exe (PID: 1184)
Starts a Microsoft application from unusual location
- TORRENTOLD-1.exe (PID: 4408)
- diskutil.exe (PID: 8120)
- cleanup_tool.exe (PID: 11628)
- TPB-ACTIVATOR-1.exe (PID: 13056)
- TPB-1.exe (PID: 12948)
- WannaCry.exe (PID: 12760)
Starts itself from another location
- Client-built.exe (PID: 6656)
- built.exe (PID: 5116)
- Quas_Brout_ncrypt.exe (PID: 8164)
- diskutil.exe (PID: 8120)
- JJSPLOIT.V2.exe (PID: 9024)
- Sentil.exe (PID: 8016)
- discord.exe (PID: 5380)
- main.exe (PID: 10648)
- 99999.exe (PID: 12028)
- NOTallowedtocrypt.exe (PID: 12800)
Get information on the list of running processes
- cmd.exe (PID: 2384)
- svchost.exe (PID: 7860)
- cmd.exe (PID: 8588)
- cmd.exe (PID: 3968)
- cmd.exe (PID: 8520)
- cmd.exe (PID: 7344)
- cmd.exe (PID: 9420)
- cmd.exe (PID: 10688)
- cmd.exe (PID: 10512)
- cmd.exe (PID: 11132)
- cmd.exe (PID: 10392)
- cmd.exe (PID: 9836)
- cmd.exe (PID: 9760)
- cmd.exe (PID: 10816)
- cmd.exe (PID: 5172)
- cmd.exe (PID: 8752)
- cmd.exe (PID: 3620)
- cmd.exe (PID: 10332)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 10724)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2384)
- cmd.exe (PID: 9420)
- cmd.exe (PID: 11448)
PSEXEC has been detected
- PsExec64.exe (PID: 4608)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 5964)
- 4363463463464363463463463.exe (PID: 6108)
- Network.exe (PID: 7652)
- HeimdallGuard.exe (PID: 6564)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- server.exe (PID: 12672)
- MSBuild.exe (PID: 12148)
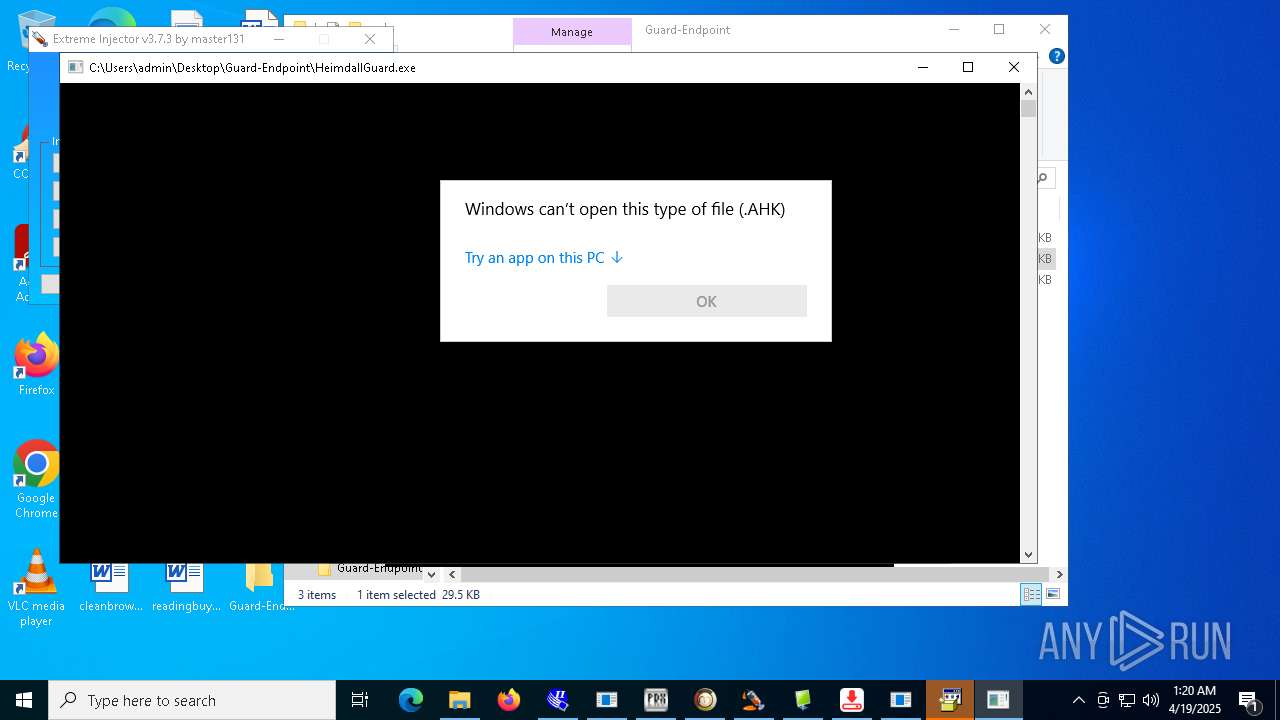
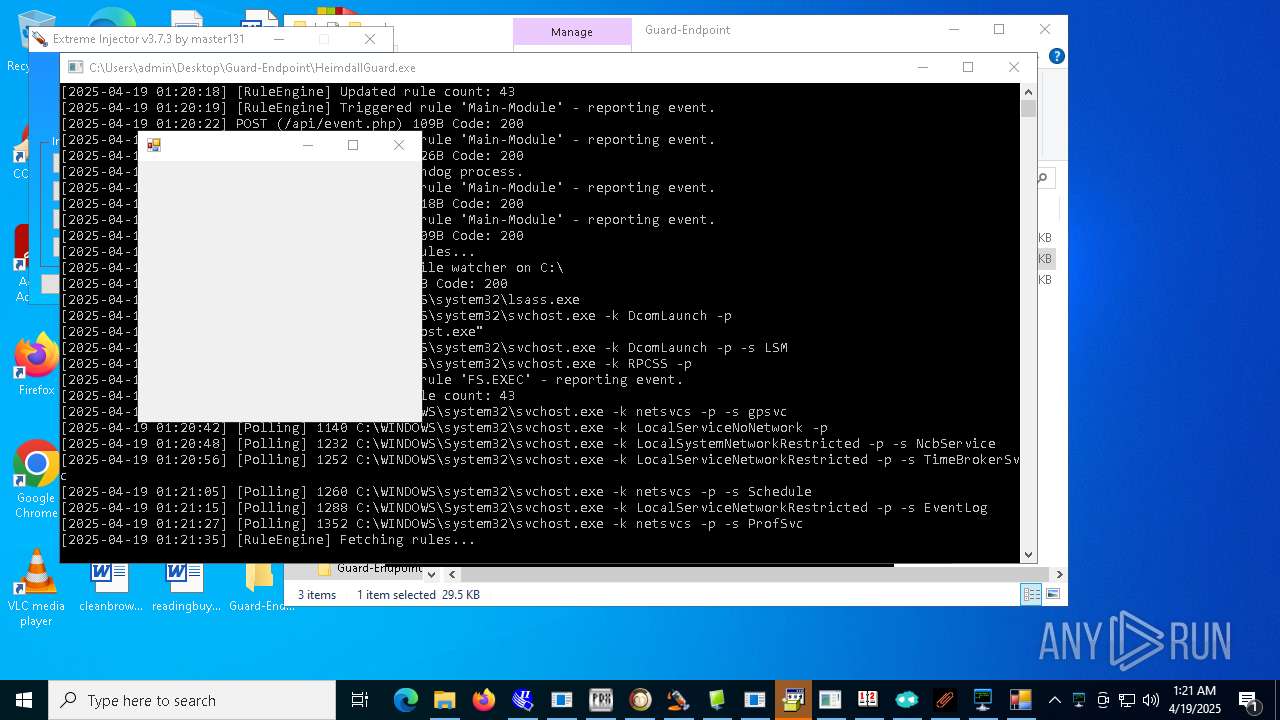
Application launched itself
- cmd.exe (PID: 2384)
- con12312211221.exe (PID: 7240)
- HeimdallGuard.exe (PID: 6564)
- networks_profile.exe (PID: 7268)
- svchost.exe (PID: 7804)
- cmd.exe (PID: 9420)
- Load.exe (PID: 9076)
- crypted.exe (PID: 8520)
- M7XQmz2DgtiyE3f.exe (PID: 6712)
- HeimdallGuard.exe (PID: 7992)
- HeimdallGuard.exe (PID: 12252)
- RegAsm.exe (PID: 11508)
Reads the date of Windows installation
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- Network.exe (PID: 7652)
- Clients.exe (PID: 7420)
- PerfWatson1.exe (PID: 7404)
- Client.exe (PID: 7448)
- cheese.exe (PID: 7920)
- Client.exe (PID: 9072)
- Clients.exe (PID: 9000)
- PerfWatson1.exe (PID: 9160)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 5188)
- Client.exe (PID: 5964)
- XClient.exe (PID: 2516)
- Clients.exe (PID: 6824)
- PerfWatson1.exe (PID: 9012)
- windows 3543.exe (PID: 7380)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- Clients.exe (PID: 10360)
- Loader.exe (PID: 10980)
- new.exe (PID: 8952)
- PerfWatson1.exe (PID: 11224)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- Clients.exe (PID: 10280)
- PerfWatson1.exe (PID: 9852)
- windows 3543.exe (PID: 9280)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- Clients.exe (PID: 11292)
- PerfWatson1.exe (PID: 12044)
- Clients.exe (PID: 12092)
- windows 3543.exe (PID: 8032)
- PerfWatson1.exe (PID: 5176)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 6108)
- MSystem32.exe (PID: 2772)
- Microsoft_Hardware_Launch.exe (PID: 1180)
- update.exe (PID: 8104)
- Fast%20Download.exe (PID: 4040)
- Server.exe (PID: 5156)
- 1.exe (PID: 10092)
- RuntimeBrokerSvc.exe (PID: 10020)
- windows 3543.exe (PID: 7380)
- fern_wifi_recon%252.34.exe (PID: 3156)
- Client1.exe (PID: 10144)
- msf.exe (PID: 4024)
- Network.exe (PID: 7652)
- Client.exe (PID: 10116)
- XClient.exe (PID: 2516)
- crack.exe (PID: 11128)
- shell.exe (PID: 10912)
- windows 3543.exe (PID: 9280)
- Loader.exe (PID: 10980)
- stub.exe (PID: 11160)
- Server1.exe (PID: 11244)
- dllhost.exe (PID: 11248)
- Load.exe (PID: 4268)
- benpolatalemdar.exe (PID: 11488)
- elf.exe (PID: 11416)
- crypted.exe (PID: 10384)
- client.exe (PID: 12108)
- OpenArk32.exe (PID: 11100)
- windows 3543.exe (PID: 8032)
- Windows.exe (PID: 13028)
- server.exe (PID: 12672)
- tool.exe (PID: 11972)
- prueba.exe (PID: 12660)
- connector1.exe (PID: 12340)
Starts application with an unusual extension
- cmd.exe (PID: 1164)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 8256)
- cmd.exe (PID: 9068)
- cmd.exe (PID: 9320)
- cmd.exe (PID: 9324)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 9924)
- cmd.exe (PID: 9672)
- cmd.exe (PID: 10920)
- cmd.exe (PID: 9420)
- cmd.exe (PID: 10880)
- cmd.exe (PID: 10860)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 10676)
- cmd.exe (PID: 10620)
- cmd.exe (PID: 11080)
- cmd.exe (PID: 10972)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 11448)
- cmd.exe (PID: 9740)
- cmd.exe (PID: 10504)
- cmd.exe (PID: 7100)
- cmd.exe (PID: 11904)
- cmd.exe (PID: 5708)
- cmd.exe (PID: 1584)
- 4363463463464363463463463.exe (PID: 6108)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 1164)
- cmd.exe (PID: 1812)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 9320)
- cmd.exe (PID: 9068)
- cmd.exe (PID: 8256)
- cmd.exe (PID: 9324)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 9924)
- cmd.exe (PID: 9672)
- cmd.exe (PID: 10920)
- cmd.exe (PID: 10880)
- cmd.exe (PID: 10860)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 10676)
- cmd.exe (PID: 10620)
- cmd.exe (PID: 11080)
- cmd.exe (PID: 10972)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 10504)
- cmd.exe (PID: 7100)
- cmd.exe (PID: 5708)
- cmd.exe (PID: 11904)
The process creates files with name similar to system file names
- MSystem32.exe (PID: 2772)
- 4363463463464363463463463.exe (PID: 6108)
- maza-0.16.3-win64-setup-unsigned.exe (PID: 8464)
- main.exe (PID: 10648)
- Loader.exe (PID: 10980)
- dllhost.exe (PID: 11248)
- server.exe (PID: 12672)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
Uses NETSH.EXE to add a firewall rule or allowed programs
- Microsoft_Hardware_Launch.exe (PID: 1180)
- Server1.exe (PID: 11244)
- client.exe (PID: 12108)
- server.exe (PID: 12672)
- testme.exe (PID: 12208)
- mos%20ssssttttt.exe (PID: 12468)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 7764)
- XClient.exe (PID: 2516)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 6108)
- Meredrop.exe (PID: 7356)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
The executable file from the user directory is run by the CMD process
- Piss.com (PID: 7984)
- Client.exe (PID: 7448)
- PerfWatson1.exe (PID: 7404)
- update.exe (PID: 8104)
- PerfWatson1.exe (PID: 9160)
- Client.exe (PID: 9072)
- RuntimeBrokerSvc.exe (PID: 10020)
- Client.exe (PID: 5964)
- PerfWatson1.exe (PID: 9012)
- Client.exe (PID: 8220)
- PerfWatson1.exe (PID: 9012)
- PerfWatson1.exe (PID: 840)
- Mph.pif (PID: 6656)
- windows 3543.exe (PID: 9280)
- PerfWatson1.exe (PID: 11224)
- PerfWatson1.exe (PID: 10812)
- PerfWatson1.exe (PID: 9852)
- PerfWatson1.exe (PID: 12044)
- windows 3543.exe (PID: 8032)
- Windows.exe (PID: 13028)
- PerfWatson1.exe (PID: 5176)
Starts the AutoIt3 executable file
- cmd.exe (PID: 2384)
- cmd.exe (PID: 9420)
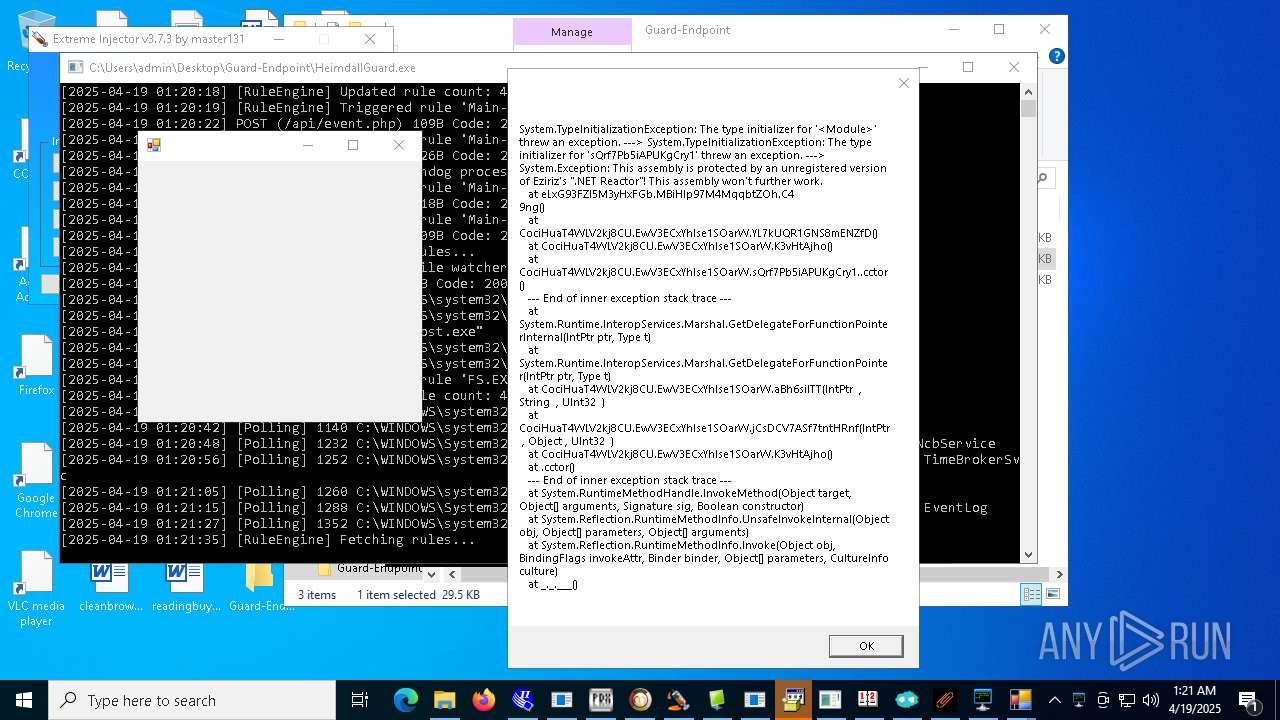
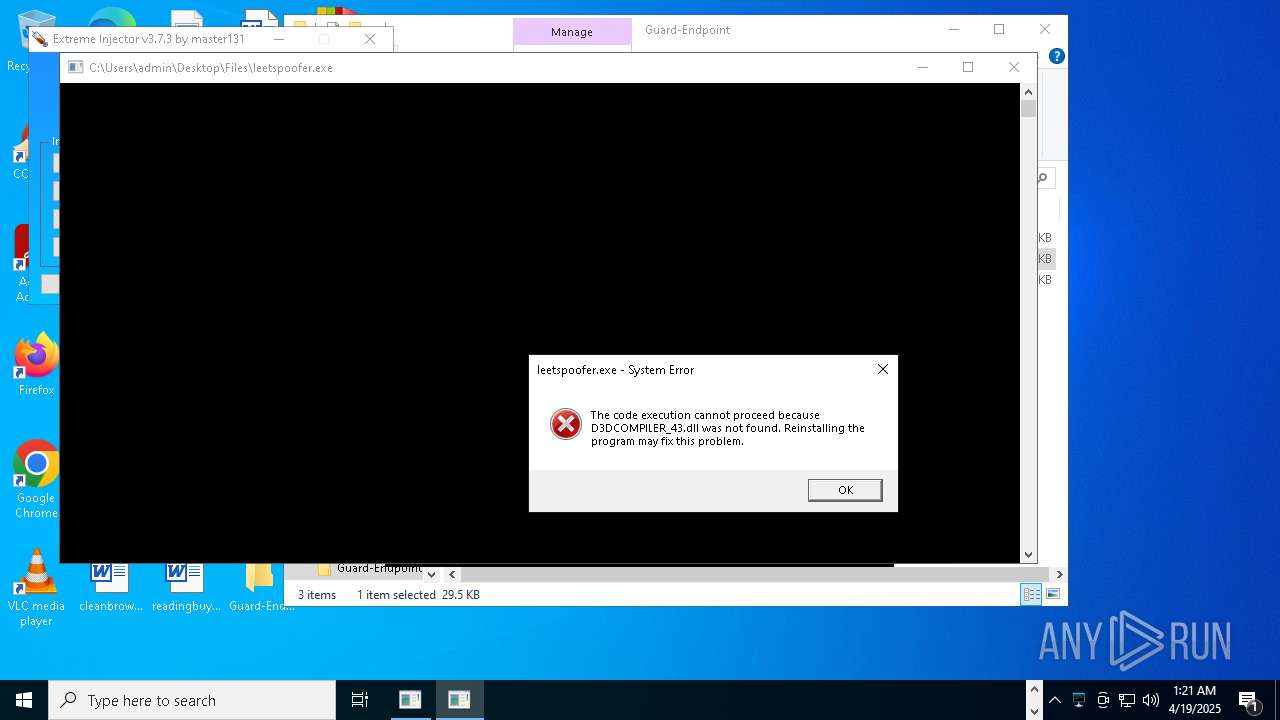
Executes application which crashes
- con12312211221.exe (PID: 7240)
- cheet.exe (PID: 10744)
- crypted.exe (PID: 8520)
- support.client.exe (PID: 4056)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
Searches for installed software
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 10908)
- MSBuild.exe (PID: 12148)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- MSBuild.exe (PID: 10036)
Checks for external IP
- Network.exe (PID: 7652)
- svchost.exe (PID: 2196)
- Build.exe (PID: 3396)
- crypted.exe (PID: 10384)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
Starts POWERSHELL.EXE for commands execution
- Network.exe (PID: 7652)
- cheese.exe (PID: 7920)
- crypted.exe (PID: 10384)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- payload.exe (PID: 3304)
Script adds exclusion path to Windows Defender
- Network.exe (PID: 7652)
- cheese.exe (PID: 7920)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- payload.exe (PID: 3304)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 976)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 9420)
- cmd.exe (PID: 11108)
Process drops python dynamic module
- svchost.exe (PID: 7804)
- networks_profile.exe (PID: 7268)
- Load.exe (PID: 9076)
- DiscordNitroGenerator.exe (PID: 2316)
The process drops C-runtime libraries
- svchost.exe (PID: 7804)
- networks_profile.exe (PID: 7268)
- Load.exe (PID: 9076)
- DiscordNitroGenerator.exe (PID: 2316)
Uses ATTRIB.EXE to modify file attributes
- Fast%20Download.exe (PID: 4040)
- WannaCry.exe (PID: 12760)
Script adds exclusion process to Windows Defender
- Network.exe (PID: 7652)
Uses NETSH.EXE to obtain data on the network
- networks_profile.exe (PID: 2332)
- cmd.exe (PID: 11448)
- cmd.exe (PID: 9740)
Loads Python modules
- networks_profile.exe (PID: 2332)
- svchost.exe (PID: 7860)
- Load.exe (PID: 4268)
The process executes VB scripts
- FXServer.exe (PID: 8272)
Execution of CURL command
- cheese.exe (PID: 7920)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8296)
- cmd.exe (PID: 8348)
- cmd.exe (PID: 12848)
- cmd.exe (PID: 12556)
- cmd.exe (PID: 12400)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8436)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 8436)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8436)
Probably fake Windows Update file has been dropped
- JJSPLOIT.V2.exe (PID: 9024)
- server.exe (PID: 12672)
Probably fake Windows Update
- schtasks.exe (PID: 8140)
- windows 3543.exe (PID: 7380)
- schtasks.exe (PID: 10180)
- windows 3543.exe (PID: 9280)
- schtasks.exe (PID: 10604)
- windows 3543.exe (PID: 8032)
- schtasks.exe (PID: 13156)
- cmd.exe (PID: 13560)
Identifying current user with WHOAMI command
- 1.exe (PID: 10092)
- tool.exe (PID: 11972)
Malware-specific behavior (creating "System.dll" in Temp)
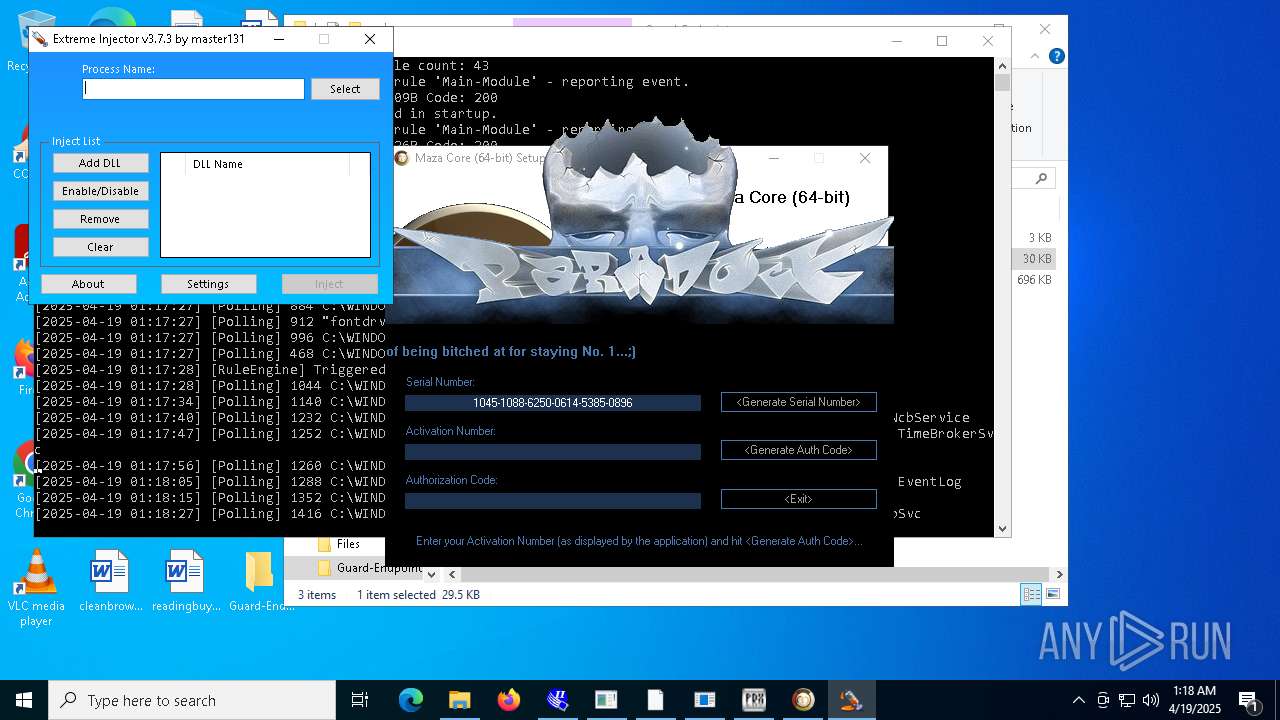
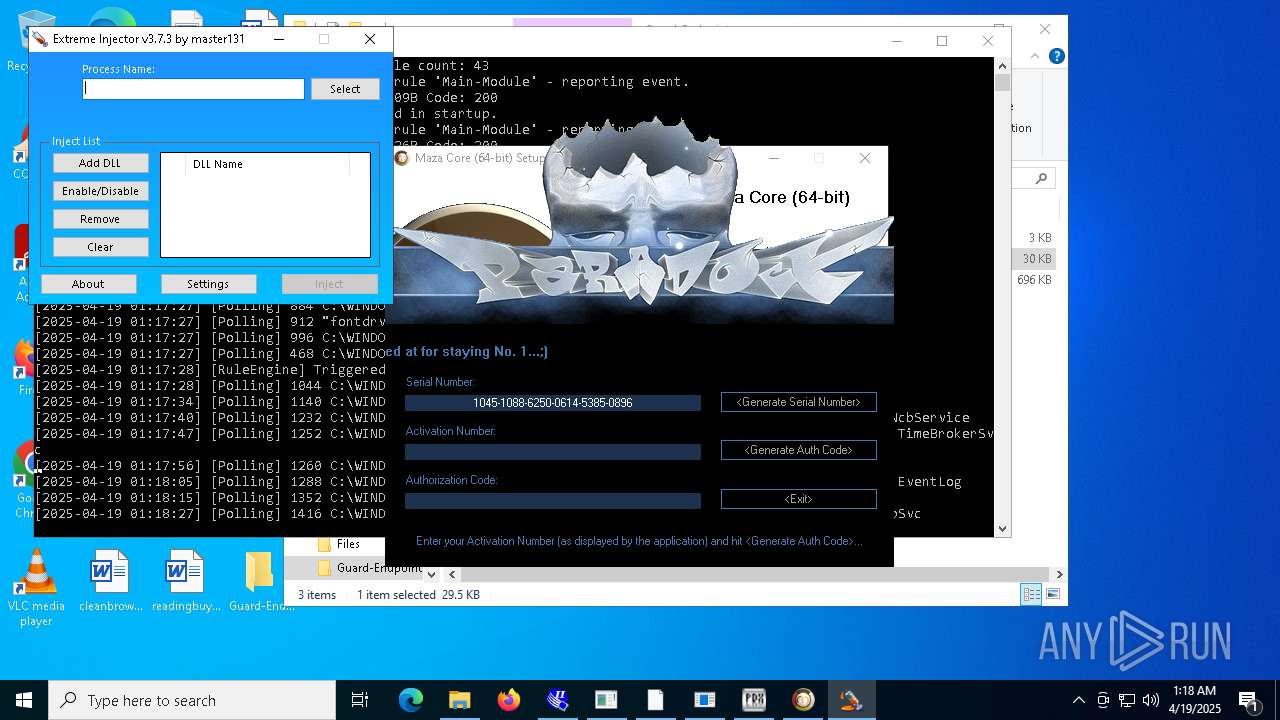
- maza-0.16.3-win64-setup-unsigned.exe (PID: 8464)
Executing commands from ".cmd" file
- OfferedBuilt.exe (PID: 8544)
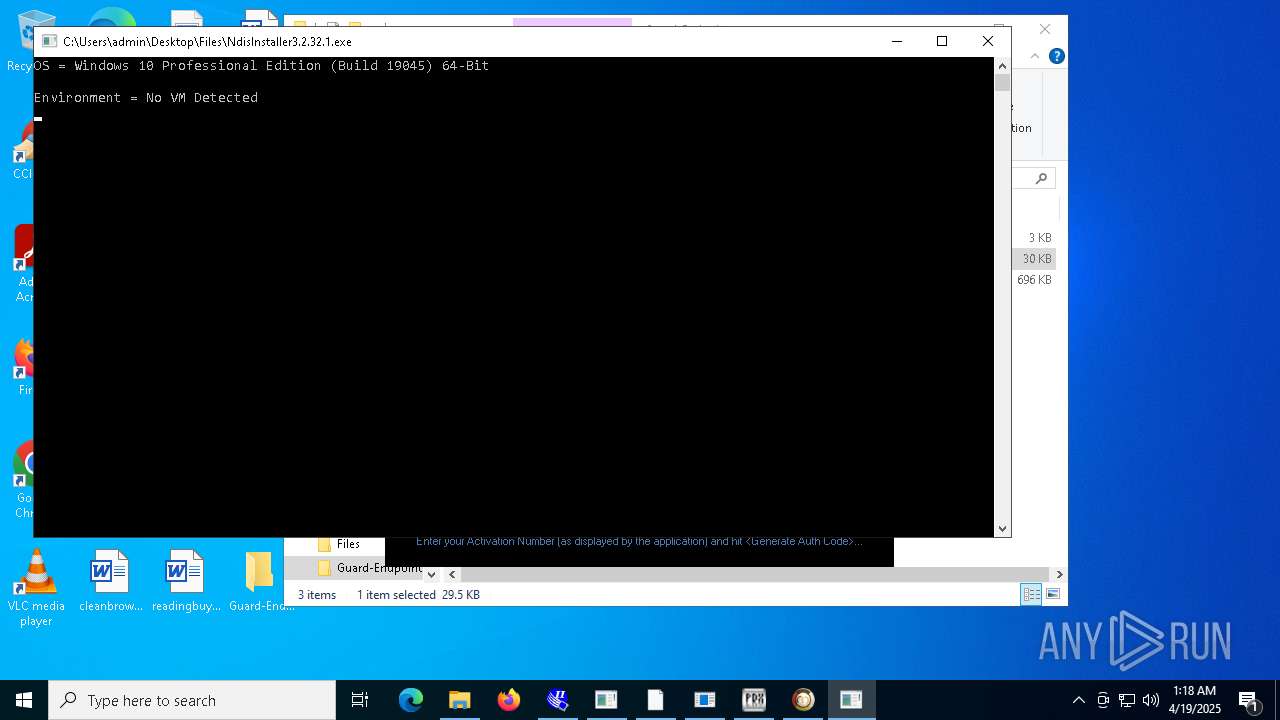
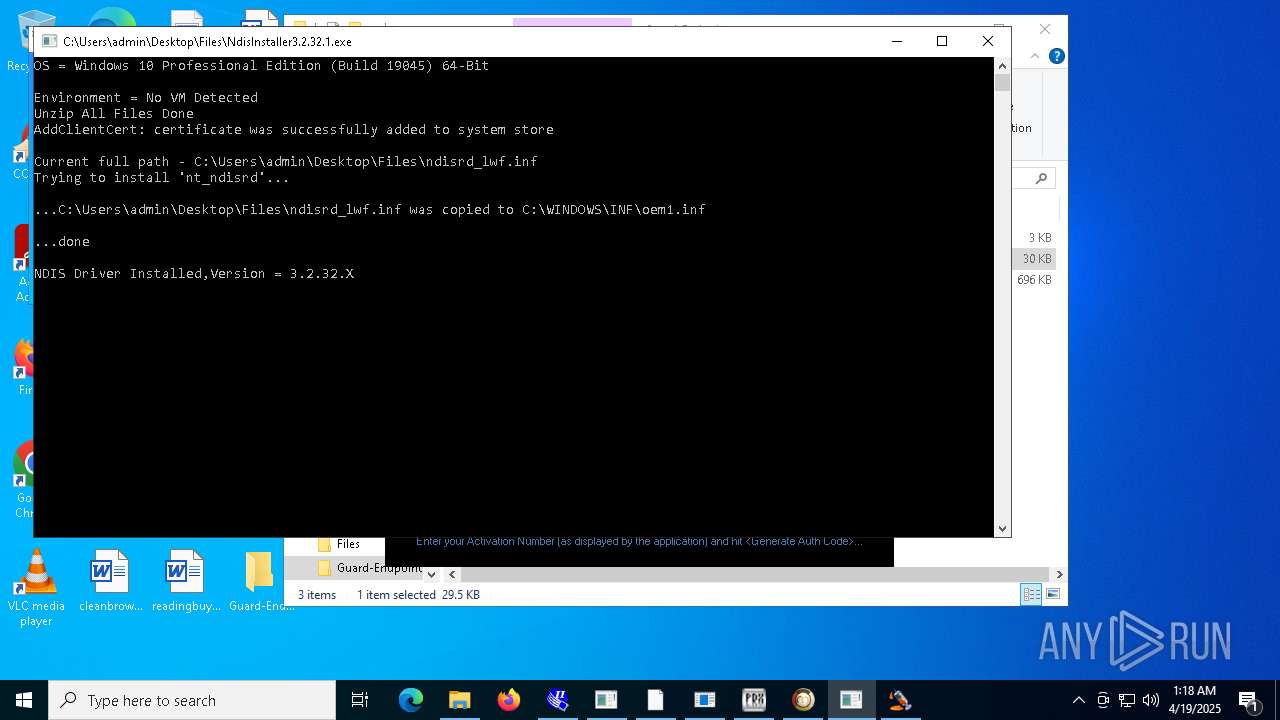
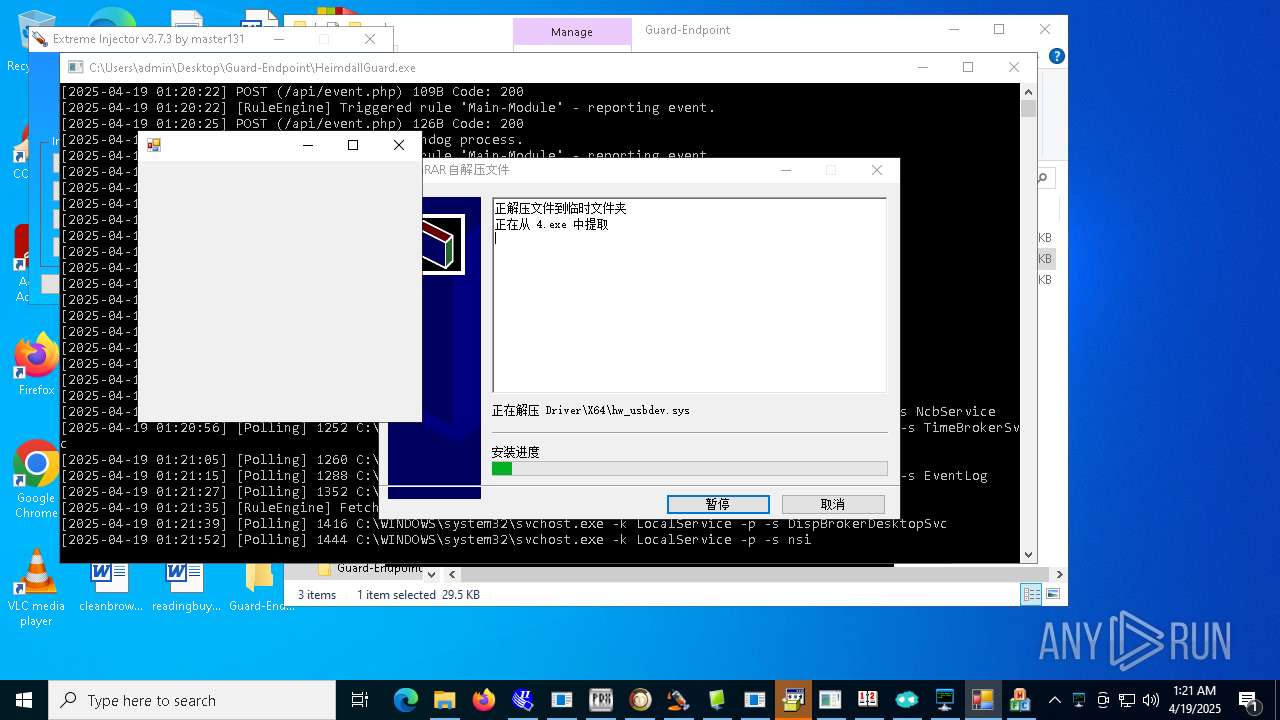
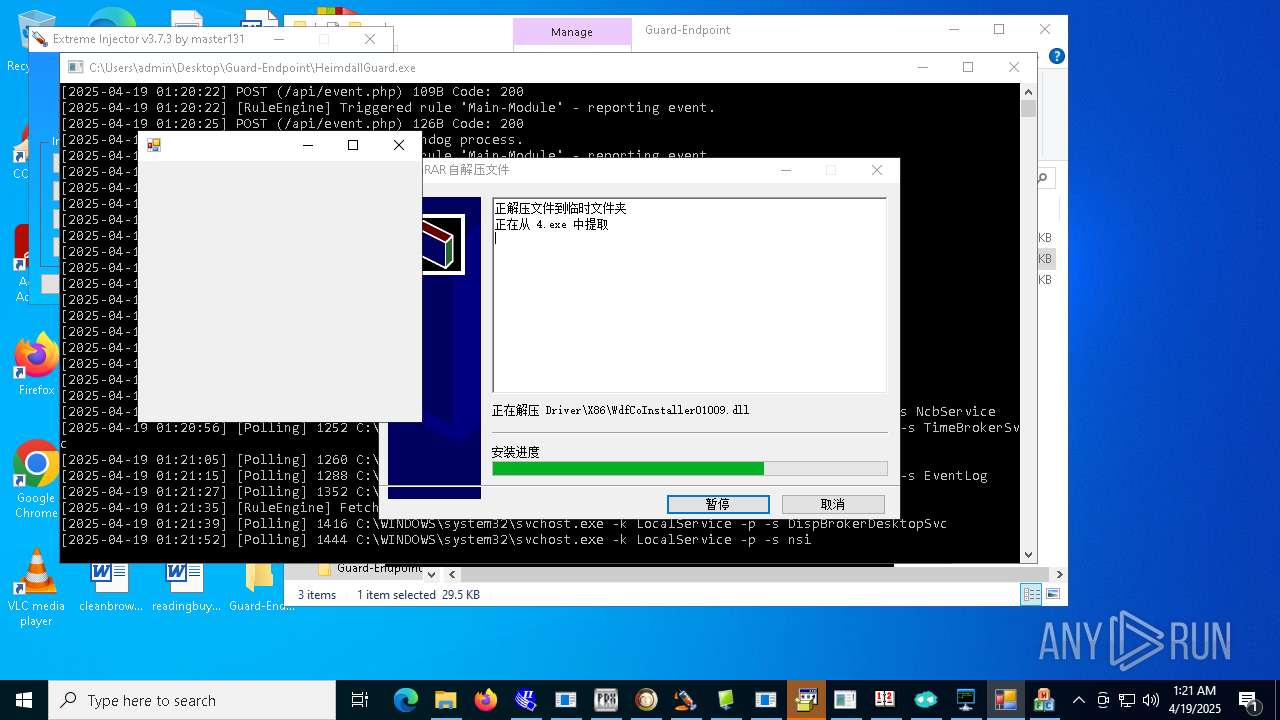
Drops a system driver (possible attempt to evade defenses)
- NdisInstaller3.2.32.1.exe (PID: 9040)
- snetcfg.exe (PID: 8524)
- drvinst.exe (PID: 9820)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- KZMount2.exe (PID: 6248)
- 4.exe (PID: 11512)
Adds/modifies Windows certificates
- certinst.exe (PID: 4776)
- support.client.exe (PID: 4056)
Creates files in the driver directory
- drvinst.exe (PID: 9820)
- snetcfg.exe (PID: 8524)
- KZMount2.exe (PID: 6248)
The process checks if it is being run in the virtual environment
- 4363463463464363463463463.exe (PID: 6108)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 9420)
- Mph.pif (PID: 6656)
Suspicious file concatenation
- cmd.exe (PID: 8656)
ANYDESK has been found
- 4363463463464363463463463.exe (PID: 6108)
The process executes via Task Scheduler
- WindowsSecurity (PID: 10900)
- new.exe (PID: 6244)
- System.exe (PID: 8320)
- Network.exe (PID: 3796)
- dllhost.exe (PID: 11288)
- new.exe (PID: 9072)
- dllhost.exe (PID: 12452)
- System.exe (PID: 9812)
- WindowsSecurity (PID: 8188)
- dllhost.exe (PID: 8104)
Uses TASKKILL.EXE to kill process
- dllhost.exe (PID: 11248)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 5868)
- schtasks.exe (PID: 10464)
- schtasks.exe (PID: 12888)
- schtasks.exe (PID: 12924)
- schtasks.exe (PID: 12744)
- schtasks.exe (PID: 10796)
Reads Internet Explorer settings
- dfsvc.exe (PID: 540)
The process bypasses the loading of PowerShell profile settings
- crypted.exe (PID: 10384)
Loads DLL from Mozilla Firefox
- Build.exe (PID: 3396)
Script disables Windows Defender's real-time protection
- payload.exe (PID: 3304)
Script disables Windows Defender's IPS
- payload.exe (PID: 3304)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- mos%20ssssttttt.exe (PID: 12468)
Creates file in the systems drive root
- server.exe (PID: 12672)
- wnsc.exe (PID: 11692)
- svchost.com (PID: 10288)
Starts NET.EXE to map network drives
- cmd.exe (PID: 7932)
Drops 7-zip archiver for unpacking
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
Creates a software uninstall entry
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
Creates or modifies Windows services
- regsvr32.exe (PID: 13044)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1584)
Detected use of alternative data streams (AltDS)
- stub.exe (PID: 11160)
AUTOHOTKEY mutex has been found
- tstory.exe (PID: 2204)
Mutex name with non-standard characters
- wnsc.exe (PID: 11692)
- svchost.com (PID: 10288)
Uses ICACLS.EXE to modify access control lists
- WannaCry.exe (PID: 12760)
Hides command output
- cmd.exe (PID: 13560)
INFO
Checks supported languages
- 4363463463464363463463463.exe (PID: 6108)
- InstructionalPostings.exe (PID: 1116)
- expand.exe (PID: 5800)
- Client-built.exe (PID: 6656)
- TORRENTOLD-1.exe (PID: 4408)
- Microsoft_Hardware_Launch.exe (PID: 1180)
- built.exe (PID: 5116)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- PsExec64.exe (PID: 4608)
- MSBuild.exe (PID: 5964)
- qt51crk.exe (PID: 2564)
- MSystem32.exe (PID: 2772)
- Fast%20Download.exe (PID: 4040)
- HeimdallGuard.exe (PID: 6564)
- chcp.com (PID: 5008)
- chcp.com (PID: 6872)
- extrac32.exe (PID: 7192)
- con12312211221.exe (PID: 7240)
- con12312211221.exe (PID: 7568)
- alex12312321.exe (PID: 7608)
- Network.exe (PID: 7652)
- MSBuild.exe (PID: 7764)
- AsyncClient.exe (PID: 7740)
- HeimdallGuard.exe (PID: 7992)
- Piss.com (PID: 7984)
- Quas_Brout_ncrypt.exe (PID: 8164)
- Wait.exe (PID: 7324)
- Clients.exe (PID: 7420)
- diskutil.exe (PID: 8120)
- diskutil.exe (PID: 7416)
- PerfWatson1.exe (PID: 7404)
- chcp.com (PID: 8112)
- update.exe (PID: 8104)
- Client.exe (PID: 7448)
- chcp.com (PID: 4336)
- chcp.com (PID: 7608)
- alphaTweaks.exe (PID: 7808)
- svchost.exe (PID: 7804)
- Meredrop.exe (PID: 7356)
- cheese.exe (PID: 7920)
- networks_profile.exe (PID: 7268)
- Server.exe (PID: 5156)
- keygen.exe (PID: 4336)
- networks_profile.exe (PID: 2332)
- FXServer.exe (PID: 8272)
- svchost.exe (PID: 7860)
- RuntimeBrokerSvc.exe (PID: 7404)
- msgde.exe (PID: 8528)
- curl.exe (PID: 8860)
- Clients.exe (PID: 9000)
- Client.exe (PID: 9072)
- PerfWatson1.exe (PID: 9160)
- ShellExperienceHost.exe (PID: 8216)
- svchost.exe (PID: 8696)
- GoogleUpdate.exe (PID: 8316)
- chcp.com (PID: 9580)
- RuntimeBrokerSvc.exe (PID: 10020)
- 1.exe (PID: 10092)
- JJSPLOIT.V2.exe (PID: 9024)
- chcp.com (PID: 9592)
- chcp.com (PID: 9616)
- begin.exe (PID: 8412)
- windows 3543.exe (PID: 7380)
- Sentil.exe (PID: 8016)
- Client1.exe (PID: 10144)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 5188)
- Client.exe (PID: 5964)
- fern_wifi_recon%252.34.exe (PID: 3156)
- file.exe (PID: 1764)
- discord.exe (PID: 5380)
- maza-0.16.3-win64-setup-unsigned.exe (PID: 8464)
- chcp.com (PID: 10072)
- chcp.com (PID: 8688)
- XClient.exe (PID: 2516)
- msf.exe (PID: 4024)
- Client.exe (PID: 10116)
- OfferedBuilt.exe (PID: 8544)
- Konsol.exe (PID: 1020)
- chcp.com (PID: 6572)
- NdisInstaller3.2.32.1.exe (PID: 9040)
- Clients.exe (PID: 6824)
- Client.exe (PID: 8220)
- Test2.exe (PID: 9152)
- snetcfg.exe (PID: 8524)
- certinst.exe (PID: 4776)
- PerfWatson1.exe (PID: 9012)
- drvinst.exe (PID: 9820)
- Extreme%20Injector%20v3.exe (PID: 9796)
- chcp.com (PID: 8220)
- chcp.com (PID: 2268)
- alex1212.exe (PID: 10836)
- chcp.com (PID: 11044)
- MSBuild.exe (PID: 10908)
- Mph.pif (PID: 6656)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- AddInProcess32.exe (PID: 6132)
- chcp.com (PID: 10764)
- chcp.com (PID: 11048)
- ledshow1.exe (PID: 10564)
- main.exe (PID: 10648)
- windows 3543.exe (PID: 9280)
- shell.exe (PID: 10912)
- new.exe (PID: 8952)
- Clients.exe (PID: 10360)
- cs-daili.exe (PID: 10776)
- crack.exe (PID: 11128)
- Loader.exe (PID: 10980)
- dllhost.exe (PID: 11248)
- PerfWatson1.exe (PID: 11224)
- chcp.com (PID: 8712)
- chcp.com (PID: 8988)
- Server1.exe (PID: 11244)
- ledshowa.exe (PID: 11096)
- cheet.exe (PID: 10744)
- stub.exe (PID: 11160)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- aspnet_regiis.exe (PID: 2268)
- WindowsSecurity (PID: 10900)
- System.exe (PID: 8320)
- Network.exe (PID: 3796)
- chcp.com (PID: 10784)
- chcp.com (PID: 8620)
- new.exe (PID: 6244)
- M7XQmz2DgtiyE3f.exe (PID: 6712)
- Load.exe (PID: 4268)
- Load.exe (PID: 9076)
- PerfWatson1.exe (PID: 9852)
- Update.exe (PID: 1184)
- support.client.exe (PID: 4056)
- Clients.exe (PID: 10280)
- dfsvc.exe (PID: 540)
- RuntimeBroker.exe (PID: 11084)
- chcp.com (PID: 9896)
- NJRAT%20DANGEROUS.exe (PID: 11104)
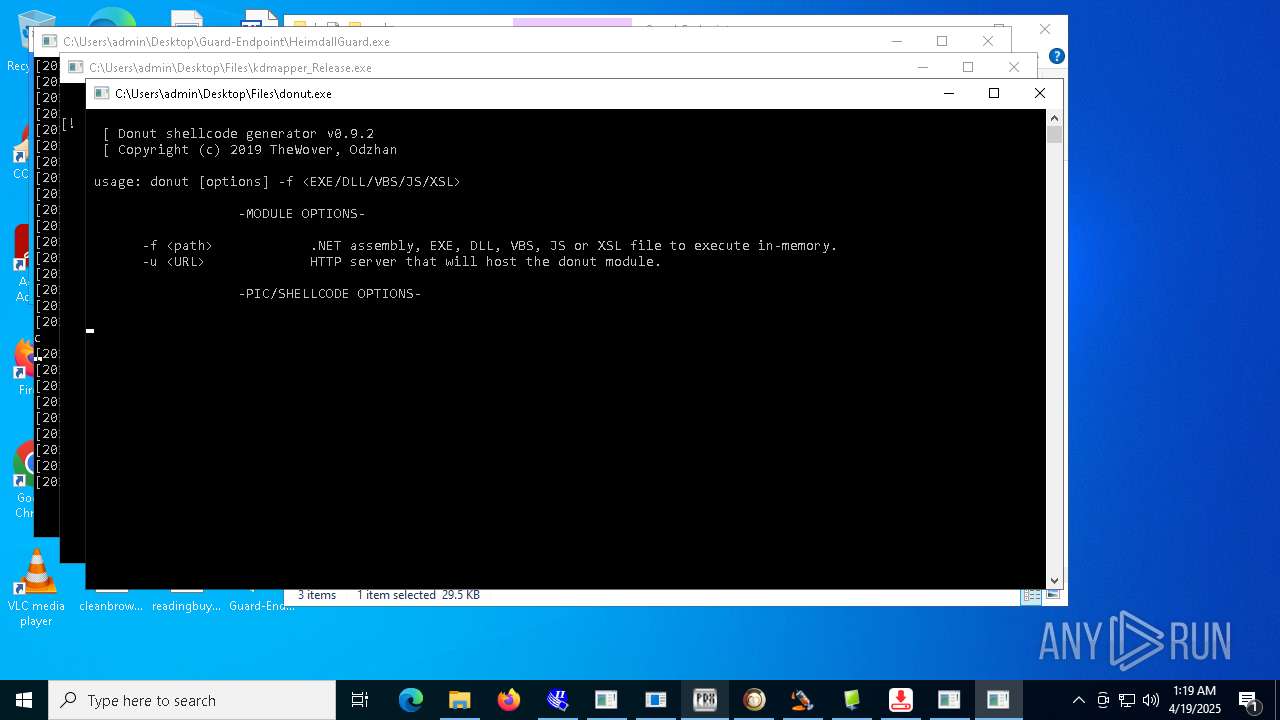
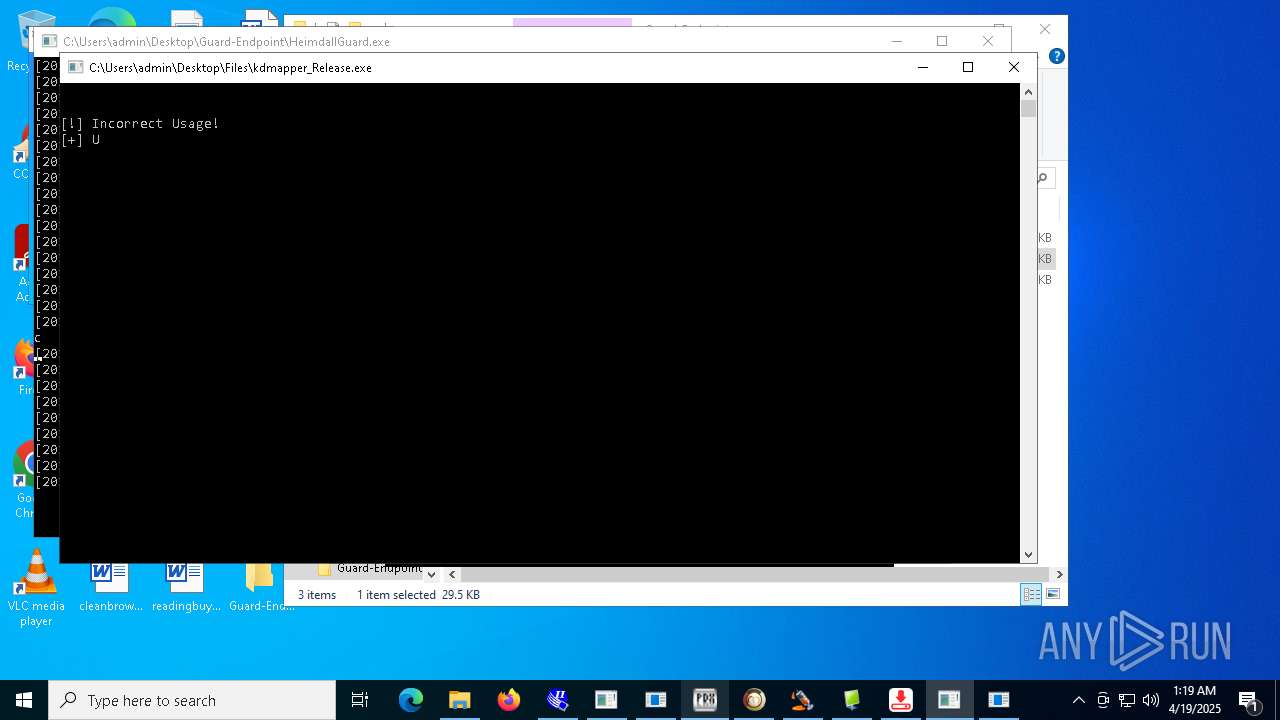
- kdmapper_Release.exe (PID: 9332)
- chcp.com (PID: 9076)
- crypted.exe (PID: 8520)
- crypted.exe (PID: 10384)
- donut.exe (PID: 10940)
- CleanerV2.exe (PID: 8328)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- builder.exe (PID: 10680)
- spectrum.exe (PID: 9236)
- Build.exe (PID: 3396)
- payload.exe (PID: 3304)
- Hive%20Ransomware.exe (PID: 11328)
- chcp.com (PID: 11368)
- benpolatalemdar.exe (PID: 11488)
- cleanup_tool.exe (PID: 11628)
- chcp.com (PID: 11844)
- Solara_Protect.exe (PID: 11996)
- client.exe (PID: 12108)
- CritScript.exe (PID: 11900)
- JUSCHED.EXE (PID: 12172)
- CollosalLoader.exe (PID: 7136)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- Clients.exe (PID: 11292)
- elf.exe (PID: 11416)
- PerfWatson1.exe (PID: 12044)
- chcp.com (PID: 8496)
- HeimdallGuard.exe (PID: 12252)
- OpenArk32.exe (PID: 11100)
- dllhost.exe (PID: 11288)
- calendar.exe (PID: 12012)
- 3601_2042.exe (PID: 6240)
- 99999.exe (PID: 12028)
- windows 3543.exe (PID: 8032)
- chcp.com (PID: 11464)
- mos%20ssssttttt.exe (PID: 12468)
- onetap.exe (PID: 12320)
- NOTallowedtocrypt.exe (PID: 12800)
- server.exe (PID: 12672)
- TPB-ACTIVATOR-1.exe (PID: 13056)
- 76y5trfed675ytg.exe (PID: 10580)
- chcp.com (PID: 13188)
- IT_plan_cifs.exe (PID: 10684)
- Windows.exe (PID: 13028)
- HeimdallGuard.exe (PID: 13252)
- svchost.exe (PID: 12604)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- ENP.exe (PID: 6744)
- TPB-1.exe (PID: 12948)
- payload1.exe (PID: 10640)
- MSBuild.exe (PID: 10036)
- writedat.exe (PID: 10344)
- Clients.exe (PID: 12092)
- prueba.exe (PID: 12660)
- KZMount2.exe (PID: 6248)
- tool.exe (PID: 11972)
- KZMount2.exe (PID: 11300)
- InstallerPack_20.1.23770_win64.exe (PID: 10828)
- PerfWatson1.exe (PID: 5176)
- dllhost.exe (PID: 12452)
- new.exe (PID: 9072)
- Neverlose%20Loader.exe (PID: 1176)
- RambledMime.exe (PID: 12164)
- testme.exe (PID: 12208)
- RegAsm.exe (PID: 11508)
- KuaiZip.exe (PID: 832)
- tstory.exe (PID: 2204)
- KZReport.exe (PID: 8028)
- chcp.com (PID: 12116)
- RegAsm.exe (PID: 6072)
- chcp.com (PID: 10468)
- 4.exe (PID: 11512)
- chcp.com (PID: 12084)
- wnsc.exe (PID: 12740)
- wnsc.exe (PID: 11692)
- svchost.com (PID: 8964)
- connector1.exe (PID: 12340)
- WannaCry.exe (PID: 12760)
- svchost.com (PID: 5112)
- svchost.com (PID: 10288)
- svchost.com (PID: 1244)
- fusca%20game.exe (PID: 8128)
- DiscordNitroGenerator.exe (PID: 2316)
- svchost.com (PID: 13500)
- MSBuild.exe (PID: 12148)
Disables trace logs
- 4363463463464363463463463.exe (PID: 6108)
- HeimdallGuard.exe (PID: 6564)
- Network.exe (PID: 7652)
- alphaTweaks.exe (PID: 7808)
- XClient.exe (PID: 2516)
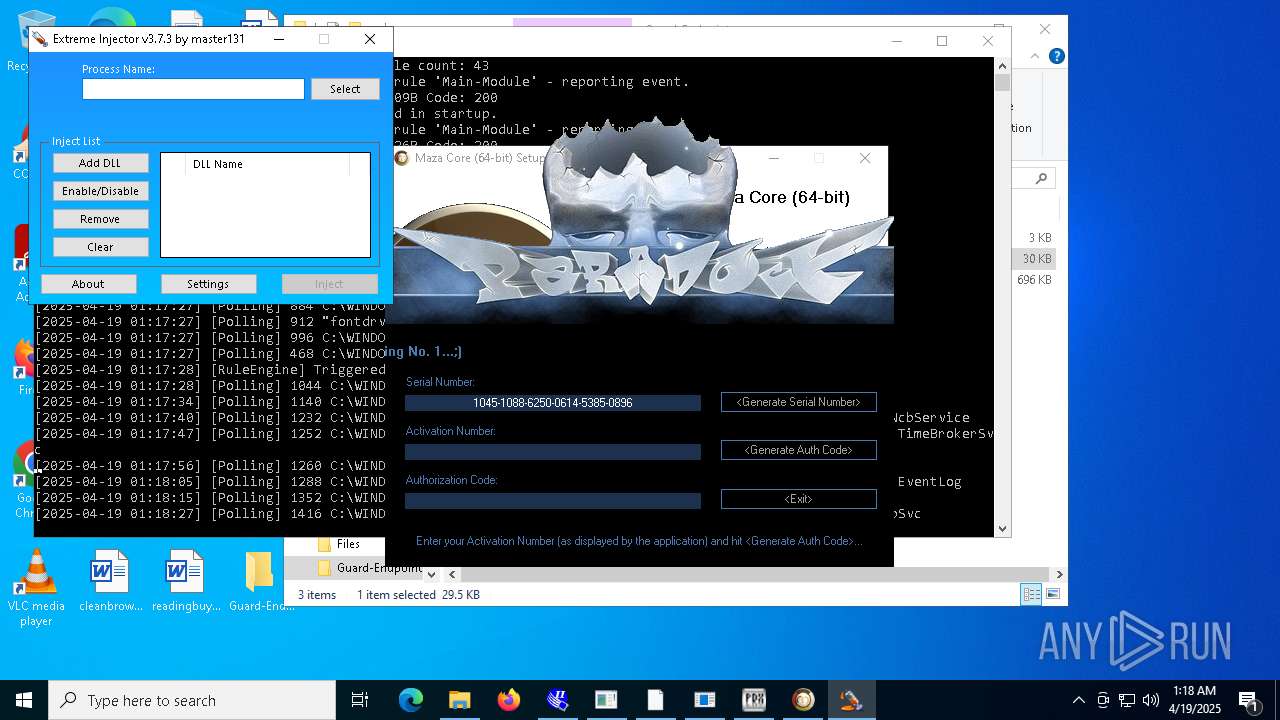
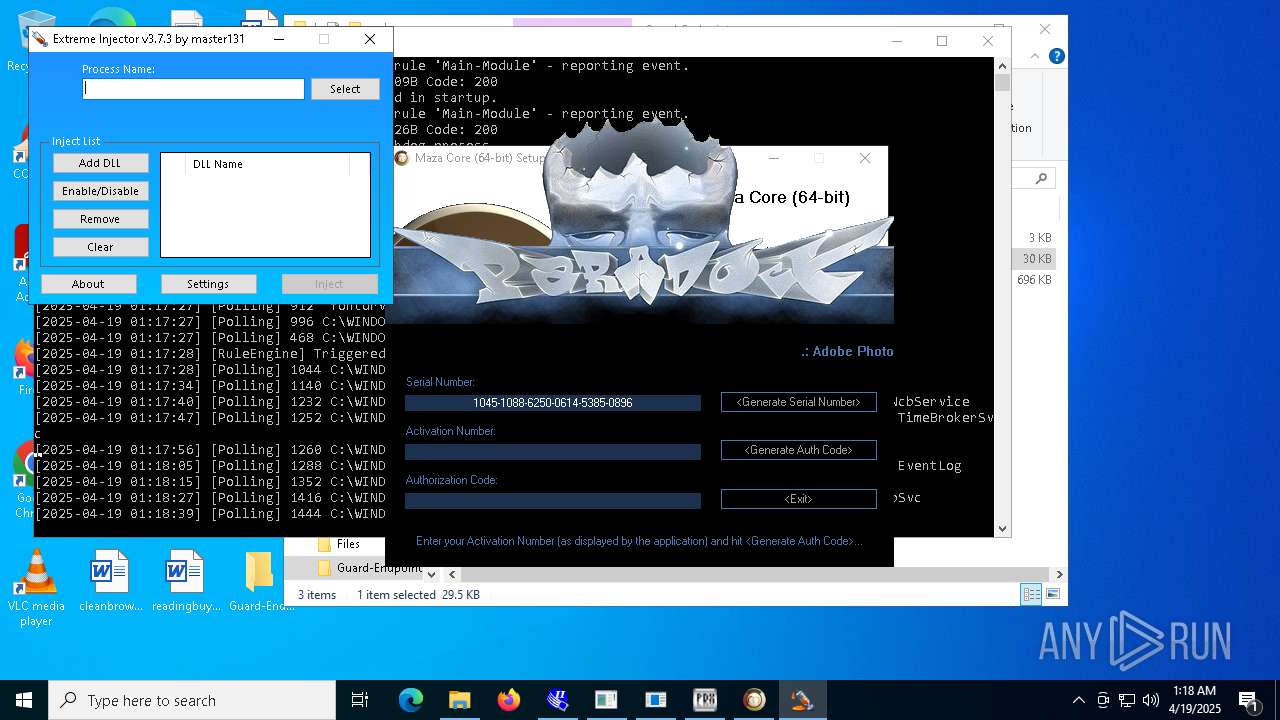
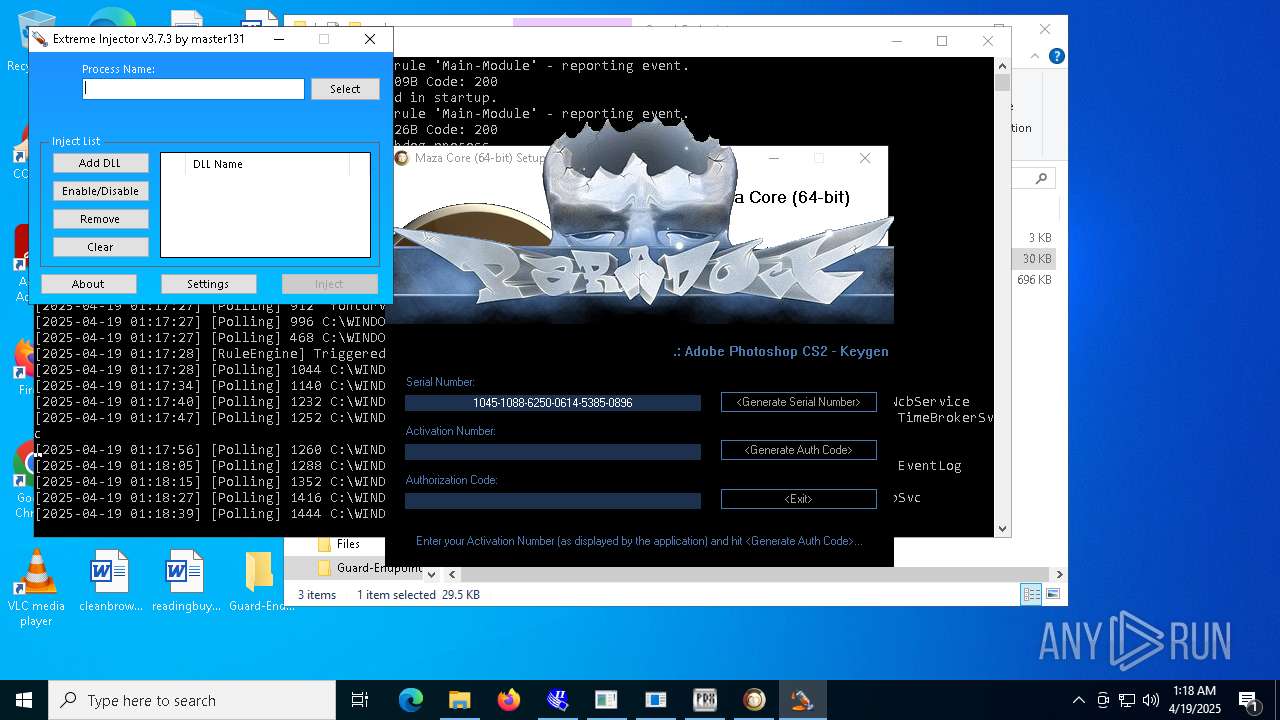
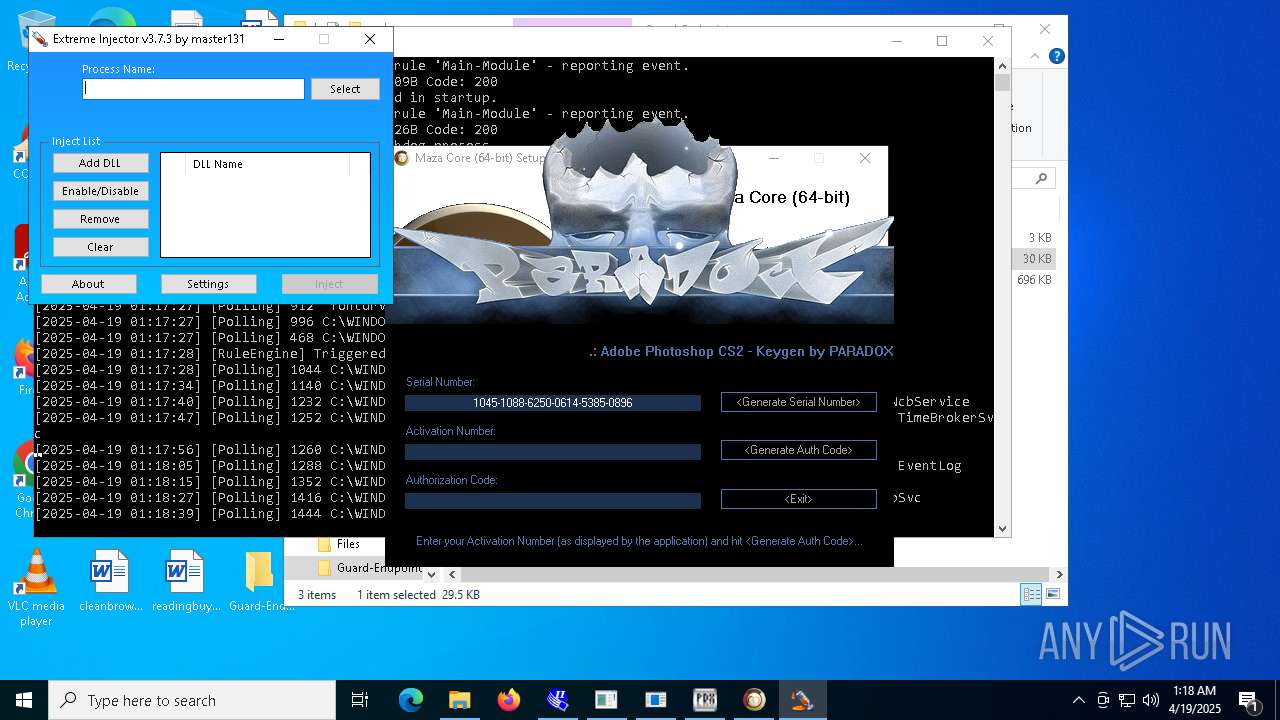
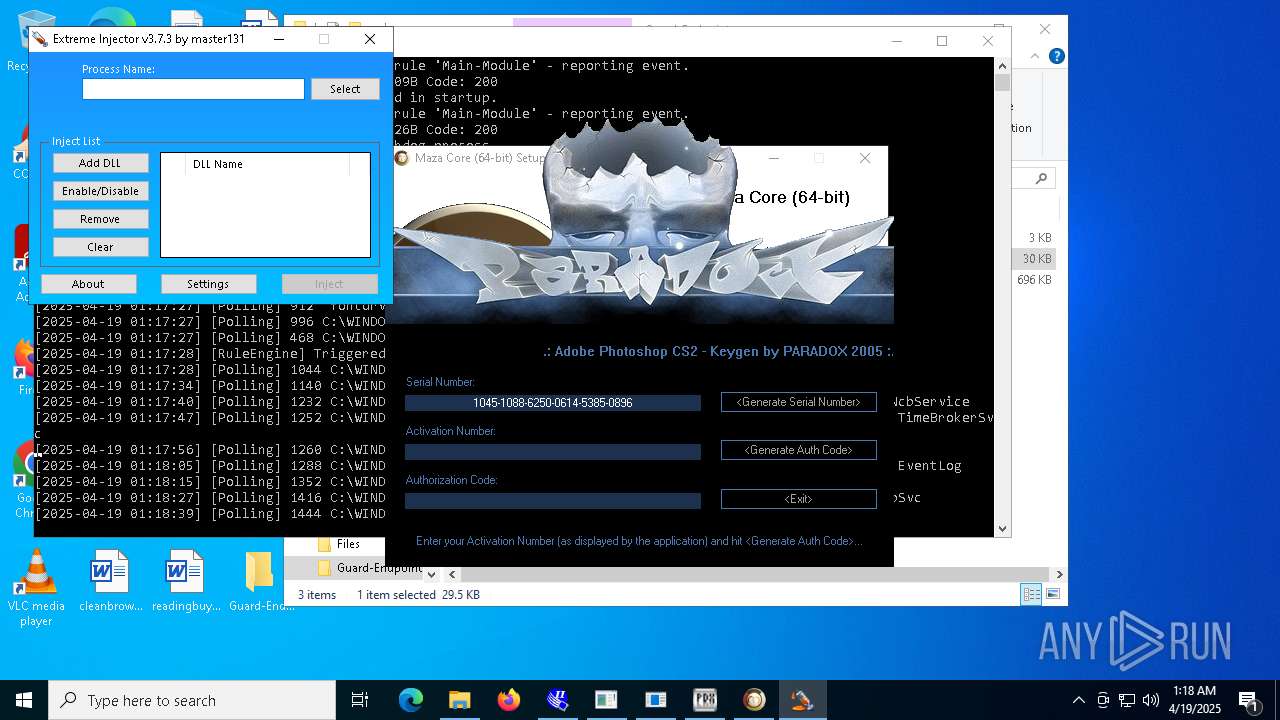
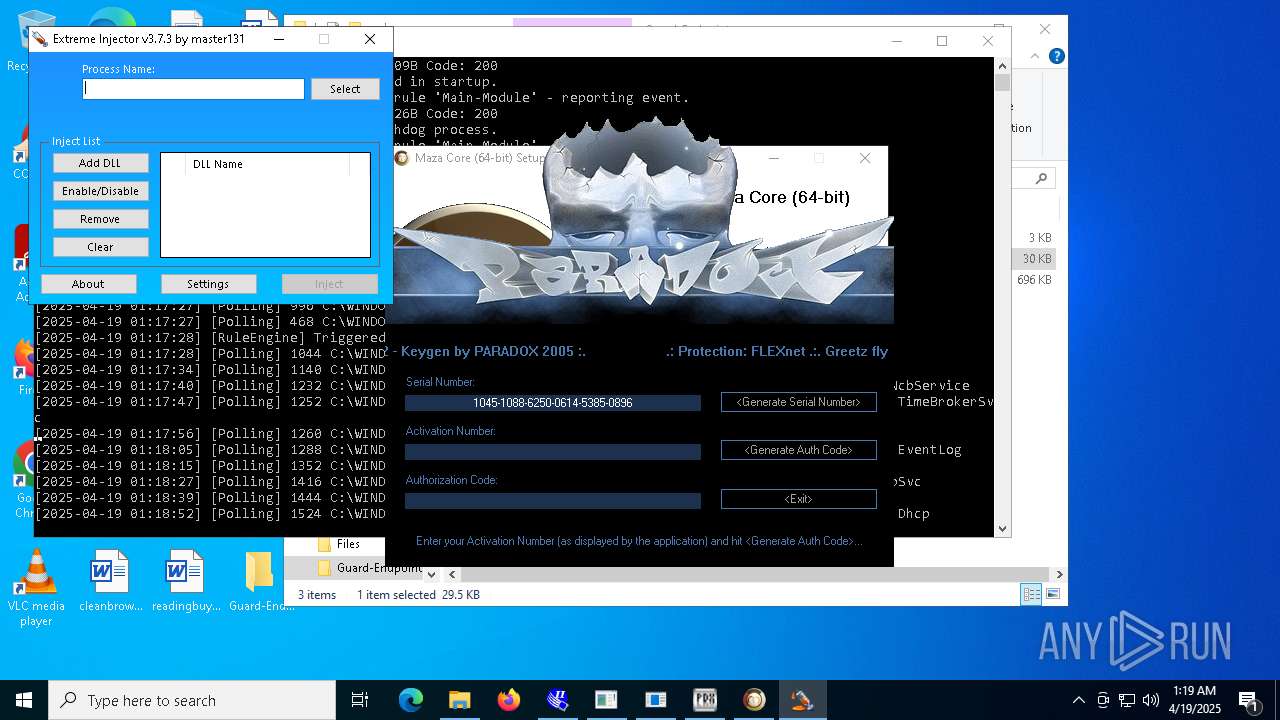
- Extreme%20Injector%20v3.exe (PID: 9796)
- dfsvc.exe (PID: 540)
- Build.exe (PID: 3396)
- payload.exe (PID: 3304)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- crypted.exe (PID: 10384)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- HeimdallGuard.exe (PID: 12252)
- wnsc.exe (PID: 12740)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 6108)
- HeimdallGuard.exe (PID: 6564)
- Network.exe (PID: 7652)
- alphaTweaks.exe (PID: 7808)
- Meredrop.exe (PID: 7356)
- XClient.exe (PID: 2516)
- Extreme%20Injector%20v3.exe (PID: 9796)
- slui.exe (PID: 8164)
- Load.exe (PID: 4268)
- dfsvc.exe (PID: 540)
- Build.exe (PID: 3396)
- payload.exe (PID: 3304)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- crypted.exe (PID: 10384)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- HeimdallGuard.exe (PID: 12252)
- onetap.exe (PID: 12320)
- ENP.exe (PID: 6744)
- net.exe (PID: 11156)
- tstory.exe (PID: 2204)
- wnsc.exe (PID: 12740)
Process checks computer location settings
- InstructionalPostings.exe (PID: 1116)
- 4363463463464363463463463.exe (PID: 6108)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- Network.exe (PID: 7652)
- AsyncClient.exe (PID: 7740)
- Clients.exe (PID: 7420)
- Client.exe (PID: 7448)
- PerfWatson1.exe (PID: 7404)
- cheese.exe (PID: 7920)
- FXServer.exe (PID: 8272)
- RuntimeBrokerSvc.exe (PID: 7404)
- Client.exe (PID: 9072)
- Clients.exe (PID: 9000)
- PerfWatson1.exe (PID: 9160)
- Client.exe (PID: 5964)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 5188)
- XClient.exe (PID: 2516)
- OfferedBuilt.exe (PID: 8544)
- Clients.exe (PID: 6824)
- PerfWatson1.exe (PID: 9012)
- windows 3543.exe (PID: 7380)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- main.exe (PID: 10648)
- Loader.exe (PID: 10980)
- Clients.exe (PID: 10360)
- PerfWatson1.exe (PID: 11224)
- new.exe (PID: 8952)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- Clients.exe (PID: 10280)
- PerfWatson1.exe (PID: 9852)
- windows 3543.exe (PID: 9280)
- crypted.exe (PID: 10384)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- CritScript.exe (PID: 11900)
- Clients.exe (PID: 11292)
- HeimdallGuard.exe (PID: 7992)
- Solara_Protect.exe (PID: 11996)
- PerfWatson1.exe (PID: 12044)
- 99999.exe (PID: 12028)
- NOTallowedtocrypt.exe (PID: 12800)
- Clients.exe (PID: 12092)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- windows 3543.exe (PID: 8032)
- PerfWatson1.exe (PID: 5176)
- wnsc.exe (PID: 11692)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 6108)
- Client-built.exe (PID: 6656)
- built.exe (PID: 5116)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- MSystem32.exe (PID: 2772)
- HeimdallGuard.exe (PID: 6564)
- Network.exe (PID: 7652)
- HeimdallGuard.exe (PID: 7992)
- Microsoft_Hardware_Launch.exe (PID: 1180)
- AsyncClient.exe (PID: 7740)
- Quas_Brout_ncrypt.exe (PID: 8164)
- Clients.exe (PID: 7420)
- diskutil.exe (PID: 8120)
- diskutil.exe (PID: 7416)
- Client.exe (PID: 7448)
- PerfWatson1.exe (PID: 7404)
- alphaTweaks.exe (PID: 7808)
- update.exe (PID: 8104)
- Fast%20Download.exe (PID: 4040)
- networks_profile.exe (PID: 2332)
- svchost.exe (PID: 7860)
- RuntimeBrokerSvc.exe (PID: 7404)
- msgde.exe (PID: 8528)
- Client.exe (PID: 9072)
- PerfWatson1.exe (PID: 9160)
- Clients.exe (PID: 9000)
- Server.exe (PID: 5156)
- JJSPLOIT.V2.exe (PID: 9024)
- RuntimeBrokerSvc.exe (PID: 10020)
- begin.exe (PID: 8412)
- Sentil.exe (PID: 8016)
- windows 3543.exe (PID: 7380)
- Client.exe (PID: 5964)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 5188)
- Client1.exe (PID: 10144)
- file.exe (PID: 1764)
- discord.exe (PID: 5380)
- Client.exe (PID: 10116)
- XClient.exe (PID: 2516)
- Client.exe (PID: 8220)
- certinst.exe (PID: 4776)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 6824)
- NdisInstaller3.2.32.1.exe (PID: 9040)
- drvinst.exe (PID: 9820)
- Test2.exe (PID: 9152)
- Extreme%20Injector%20v3.exe (PID: 9796)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- windows 3543.exe (PID: 9280)
- Loader.exe (PID: 10980)
- new.exe (PID: 8952)
- PerfWatson1.exe (PID: 11224)
- Clients.exe (PID: 10360)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- Server1.exe (PID: 11244)
- dllhost.exe (PID: 11248)
- M7XQmz2DgtiyE3f.exe (PID: 6712)
- Update.exe (PID: 1184)
- Clients.exe (PID: 10280)
- PerfWatson1.exe (PID: 9852)
- support.client.exe (PID: 4056)
- dfsvc.exe (PID: 540)
- RuntimeBroker.exe (PID: 11084)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- crypted.exe (PID: 10384)
- CleanerV2.exe (PID: 8328)
- spectrum.exe (PID: 9236)
- Build.exe (PID: 3396)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- payload.exe (PID: 3304)
- Clients.exe (PID: 11292)
- Solara_Protect.exe (PID: 11996)
- CollosalLoader.exe (PID: 7136)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- JUSCHED.EXE (PID: 12172)
- PerfWatson1.exe (PID: 12044)
- HeimdallGuard.exe (PID: 12252)
- client.exe (PID: 12108)
- new.exe (PID: 6244)
- windows 3543.exe (PID: 8032)
- onetap.exe (PID: 12320)
- HeimdallGuard.exe (PID: 13252)
- Windows.exe (PID: 13028)
- mos%20ssssttttt.exe (PID: 12468)
- server.exe (PID: 12672)
- WindowsSecurity (PID: 10900)
- payload1.exe (PID: 10640)
- System.exe (PID: 8320)
- Clients.exe (PID: 12092)
- Neverlose%20Loader.exe (PID: 1176)
- PerfWatson1.exe (PID: 5176)
- RegAsm.exe (PID: 11508)
- KuaiZip.exe (PID: 832)
- Network.exe (PID: 3796)
- testme.exe (PID: 12208)
- RegAsm.exe (PID: 6072)
- wnsc.exe (PID: 12740)
- WannaCry.exe (PID: 12760)
Reads the computer name
- InstructionalPostings.exe (PID: 1116)
- 4363463463464363463463463.exe (PID: 6108)
- Client-built.exe (PID: 6656)
- Microsoft_Hardware_Launch.exe (PID: 1180)
- built.exe (PID: 5116)
- Client.exe (PID: 4024)
- PsExec64.exe (PID: 4608)
- PerfWatson1.exe (PID: 3888)
- MSBuild.exe (PID: 5964)
- qt51crk.exe (PID: 2564)
- HeimdallGuard.exe (PID: 6564)
- Fast%20Download.exe (PID: 4040)
- extrac32.exe (PID: 7192)
- con12312211221.exe (PID: 7240)
- MSystem32.exe (PID: 2772)
- Network.exe (PID: 7652)
- con12312211221.exe (PID: 7568)
- AsyncClient.exe (PID: 7740)
- MSBuild.exe (PID: 7764)
- Wait.exe (PID: 7324)
- HeimdallGuard.exe (PID: 7992)
- Quas_Brout_ncrypt.exe (PID: 8164)
- Piss.com (PID: 7984)
- Clients.exe (PID: 7420)
- diskutil.exe (PID: 8120)
- diskutil.exe (PID: 7416)
- Client.exe (PID: 7448)
- update.exe (PID: 8104)
- PerfWatson1.exe (PID: 7404)
- alphaTweaks.exe (PID: 7808)
- svchost.exe (PID: 7804)
- Meredrop.exe (PID: 7356)
- Server.exe (PID: 5156)
- networks_profile.exe (PID: 7268)
- keygen.exe (PID: 4336)
- cheese.exe (PID: 7920)
- RuntimeBrokerSvc.exe (PID: 7404)
- svchost.exe (PID: 7860)
- msgde.exe (PID: 8528)
- FXServer.exe (PID: 8272)
- Client.exe (PID: 9072)
- PerfWatson1.exe (PID: 9160)
- ShellExperienceHost.exe (PID: 8216)
- Clients.exe (PID: 9000)
- GoogleUpdate.exe (PID: 8316)
- curl.exe (PID: 8860)
- RuntimeBrokerSvc.exe (PID: 10020)
- JJSPLOIT.V2.exe (PID: 9024)
- 1.exe (PID: 10092)
- begin.exe (PID: 8412)
- Sentil.exe (PID: 8016)
- windows 3543.exe (PID: 7380)
- Client1.exe (PID: 10144)
- Client.exe (PID: 5964)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 5188)
- maza-0.16.3-win64-setup-unsigned.exe (PID: 8464)
- file.exe (PID: 1764)
- discord.exe (PID: 5380)
- XClient.exe (PID: 2516)
- Konsol.exe (PID: 1020)
- Client.exe (PID: 10116)
- OfferedBuilt.exe (PID: 8544)
- NdisInstaller3.2.32.1.exe (PID: 9040)
- Clients.exe (PID: 6824)
- Client.exe (PID: 8220)
- PerfWatson1.exe (PID: 9012)
- snetcfg.exe (PID: 8524)
- Test2.exe (PID: 9152)
- drvinst.exe (PID: 9820)
- Extreme%20Injector%20v3.exe (PID: 9796)
- MSBuild.exe (PID: 10908)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- Mph.pif (PID: 6656)
- windows 3543.exe (PID: 9280)
- ledshow1.exe (PID: 10564)
- main.exe (PID: 10648)
- new.exe (PID: 8952)
- Clients.exe (PID: 10360)
- Loader.exe (PID: 10980)
- dllhost.exe (PID: 11248)
- PerfWatson1.exe (PID: 11224)
- ledshowa.exe (PID: 11096)
- Server1.exe (PID: 11244)
- cheet.exe (PID: 10744)
- stub.exe (PID: 11160)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- aspnet_regiis.exe (PID: 2268)
- M7XQmz2DgtiyE3f.exe (PID: 6712)
- Load.exe (PID: 9076)
- PerfWatson1.exe (PID: 9852)
- Update.exe (PID: 1184)
- support.client.exe (PID: 4056)
- Clients.exe (PID: 10280)
- dfsvc.exe (PID: 540)
- RuntimeBroker.exe (PID: 11084)
- crypted.exe (PID: 8520)
- crypted.exe (PID: 10384)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- CleanerV2.exe (PID: 8328)
- spectrum.exe (PID: 9236)
- Build.exe (PID: 3396)
- WindowsSecurity (PID: 10900)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- payload.exe (PID: 3304)
- benpolatalemdar.exe (PID: 11488)
- new.exe (PID: 6244)
- System.exe (PID: 8320)
- cleanup_tool.exe (PID: 11628)
- Solara_Protect.exe (PID: 11996)
- CritScript.exe (PID: 11900)
- JUSCHED.EXE (PID: 12172)
- Clients.exe (PID: 11292)
- CollosalLoader.exe (PID: 7136)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- elf.exe (PID: 11416)
- PerfWatson1.exe (PID: 12044)
- OpenArk32.exe (PID: 11100)
- HeimdallGuard.exe (PID: 12252)
- Network.exe (PID: 3796)
- calendar.exe (PID: 12012)
- windows 3543.exe (PID: 8032)
- 99999.exe (PID: 12028)
- onetap.exe (PID: 12320)
- client.exe (PID: 12108)
- mos%20ssssttttt.exe (PID: 12468)
- server.exe (PID: 12672)
- NOTallowedtocrypt.exe (PID: 12800)
- MSBuild.exe (PID: 12148)
- HeimdallGuard.exe (PID: 13252)
- Windows.exe (PID: 13028)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- ENP.exe (PID: 6744)
- payload1.exe (PID: 10640)
- MSBuild.exe (PID: 10036)
- Clients.exe (PID: 12092)
- KZMount2.exe (PID: 6248)
- prueba.exe (PID: 12660)
- PerfWatson1.exe (PID: 5176)
- Neverlose%20Loader.exe (PID: 1176)
- InstallerPack_20.1.23770_win64.exe (PID: 10828)
- tool.exe (PID: 11972)
- testme.exe (PID: 12208)
- RegAsm.exe (PID: 11508)
- tstory.exe (PID: 2204)
- new.exe (PID: 9072)
- KZReport.exe (PID: 8028)
- RegAsm.exe (PID: 6072)
- 4.exe (PID: 11512)
- wnsc.exe (PID: 11692)
- wnsc.exe (PID: 12740)
- WannaCry.exe (PID: 12760)
- DiscordNitroGenerator.exe (PID: 2316)
Create files in a temporary directory
- InstructionalPostings.exe (PID: 1116)
- expand.exe (PID: 5800)
- Microsoft_Hardware_Launch.exe (PID: 1180)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- MSystem32.exe (PID: 2772)
- extrac32.exe (PID: 7192)
- AsyncClient.exe (PID: 7740)
- Clients.exe (PID: 7420)
- Client.exe (PID: 7448)
- PerfWatson1.exe (PID: 7404)
- svchost.exe (PID: 7804)
- alphaTweaks.exe (PID: 7808)
- networks_profile.exe (PID: 7268)
- svchost.exe (PID: 7860)
- FXServer.exe (PID: 8272)
- RuntimeBrokerSvc.exe (PID: 7404)
- Clients.exe (PID: 9000)
- PerfWatson1.exe (PID: 9160)
- Client.exe (PID: 9072)
- maza-0.16.3-win64-setup-unsigned.exe (PID: 8464)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 5188)
- Client.exe (PID: 5964)
- OfferedBuilt.exe (PID: 8544)
- Clients.exe (PID: 6824)
- PerfWatson1.exe (PID: 9012)
- snetcfg.exe (PID: 8524)
- windows 3543.exe (PID: 7380)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- cs-daili.exe (PID: 10776)
- PerfWatson1.exe (PID: 11224)
- Clients.exe (PID: 10360)
- Server1.exe (PID: 11244)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- comp.exe (PID: 3976)
- Load.exe (PID: 9076)
- Clients.exe (PID: 10280)
- PerfWatson1.exe (PID: 9852)
- dfsvc.exe (PID: 540)
- windows 3543.exe (PID: 9280)
- crypted.exe (PID: 10384)
- Build.exe (PID: 3396)
- powershell.exe (PID: 7524)
- CritScript.exe (PID: 11900)
- Clients.exe (PID: 11292)
- Solara_Protect.exe (PID: 11996)
- PerfWatson1.exe (PID: 12044)
- 99999.exe (PID: 12028)
- mos%20ssssttttt.exe (PID: 12468)
- server.exe (PID: 12672)
- IT_plan_cifs.exe (PID: 10684)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- Clients.exe (PID: 12092)
- testme.exe (PID: 12208)
- windows 3543.exe (PID: 8032)
- PerfWatson1.exe (PID: 5176)
- wnsc.exe (PID: 11692)
- 4.exe (PID: 11512)
- DiscordNitroGenerator.exe (PID: 2316)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 6108)
- MSBuild.exe (PID: 5964)
- MSBuild.exe (PID: 7764)
- HeimdallGuard.exe (PID: 6564)
- con12312211221.exe (PID: 7568)
- slui.exe (PID: 2432)
- XClient.exe (PID: 2516)
- drvinst.exe (PID: 9820)
- Piss.com (PID: 7984)
- MSBuild.exe (PID: 10908)
- aspnet_regiis.exe (PID: 2268)
- slui.exe (PID: 8164)
- dfsvc.exe (PID: 540)
- Build.exe (PID: 3396)
- powershell.exe (PID: 7524)
- payload.exe (PID: 3304)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- HeimdallGuard.exe (PID: 12252)
- MSBuild.exe (PID: 12148)
- MSBuild.exe (PID: 10036)
- InstallerPack_20.1.23770_win64.exe (PID: 10828)
The sample compiled with english language support
- 4363463463464363463463463.exe (PID: 6108)
- svchost.exe (PID: 7804)
- networks_profile.exe (PID: 7268)
- Mph.pif (PID: 6656)
- Load.exe (PID: 9076)
- Update.exe (PID: 1184)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- KZMount2.exe (PID: 6248)
- 4.exe (PID: 11512)
- WannaCry.exe (PID: 12760)
- DiscordNitroGenerator.exe (PID: 2316)
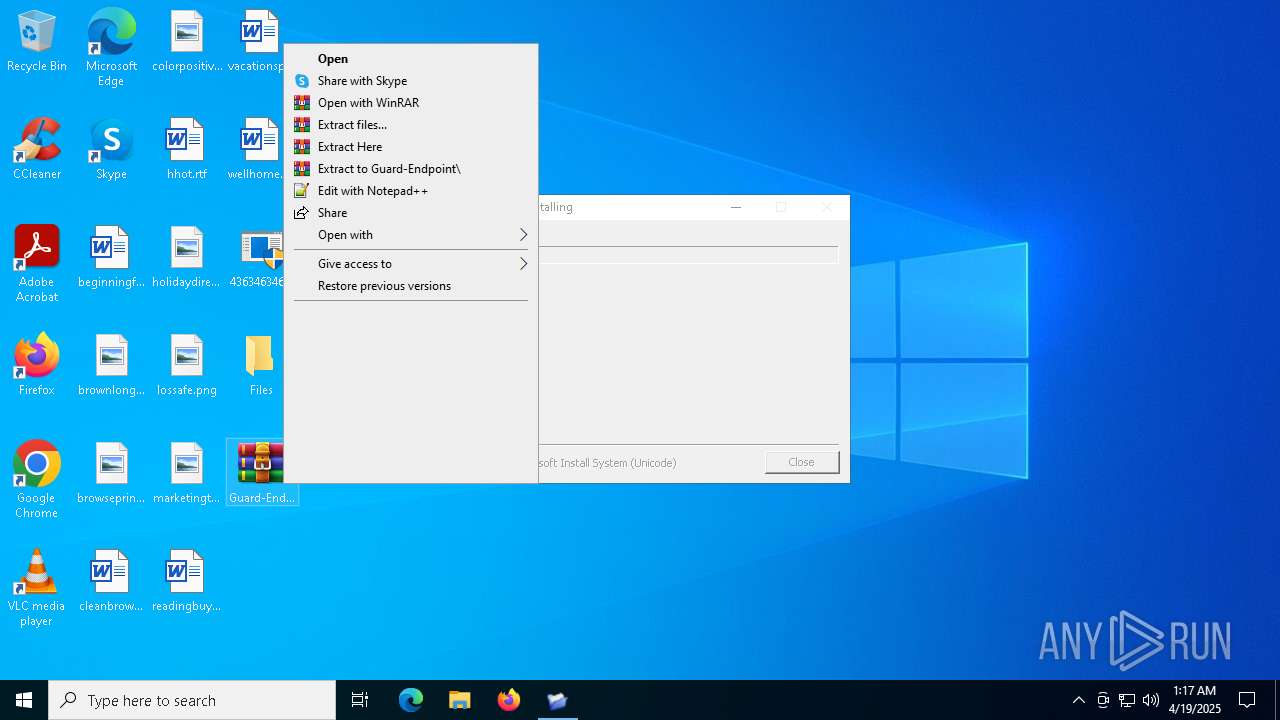
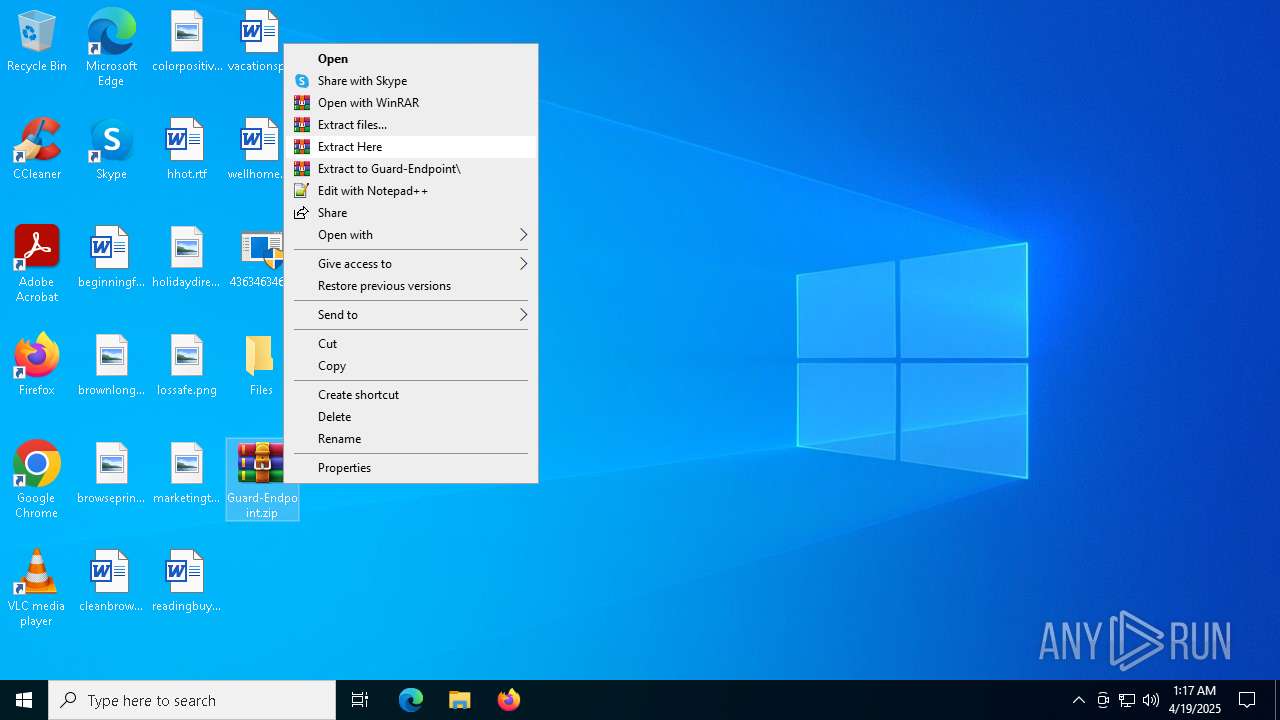
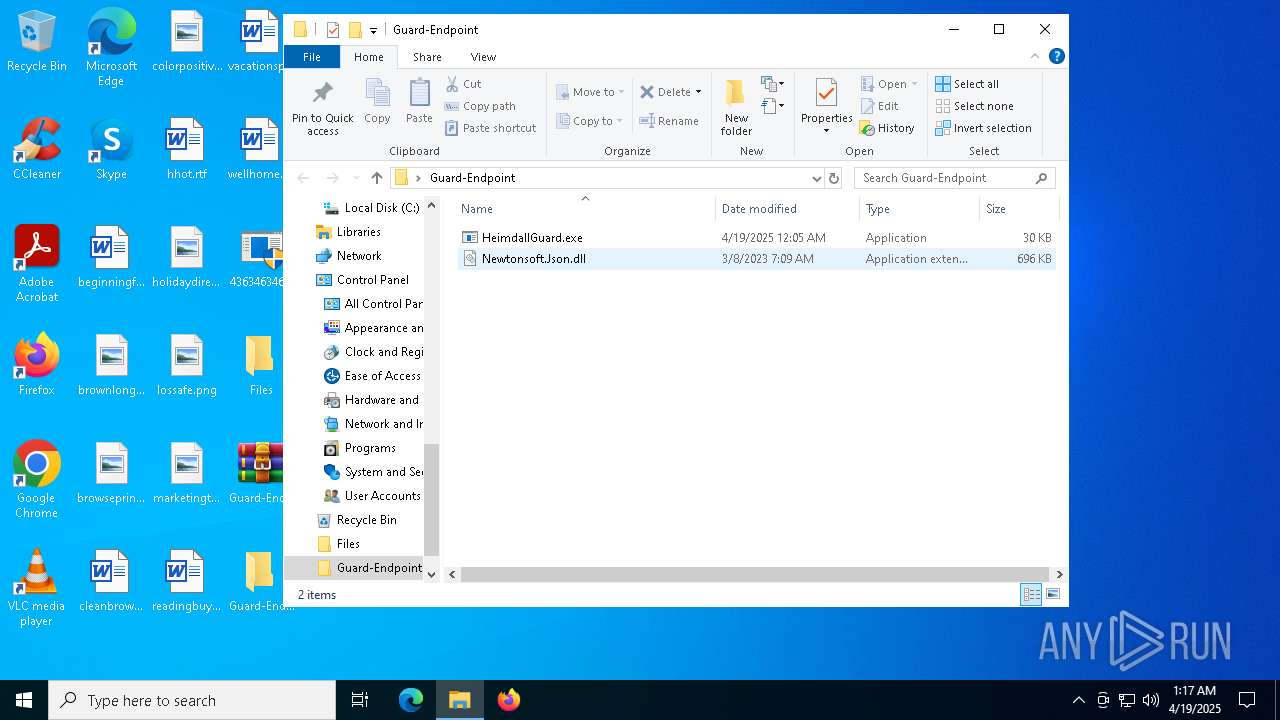
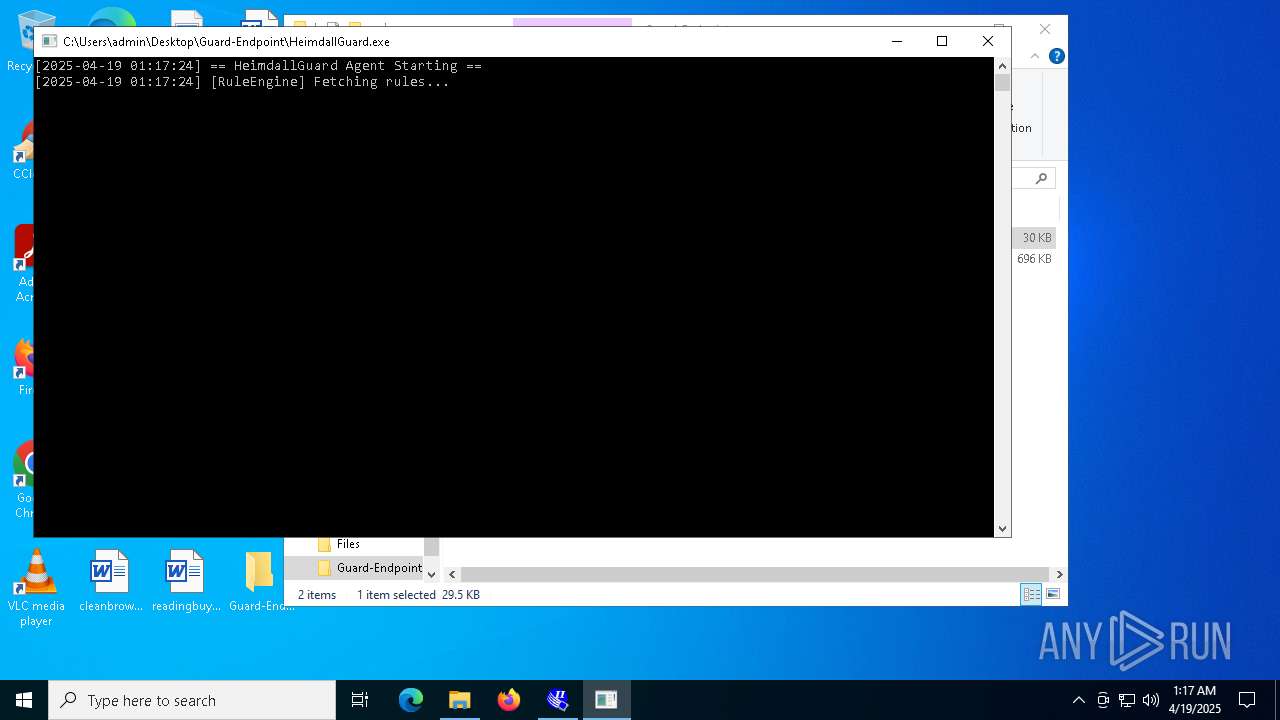
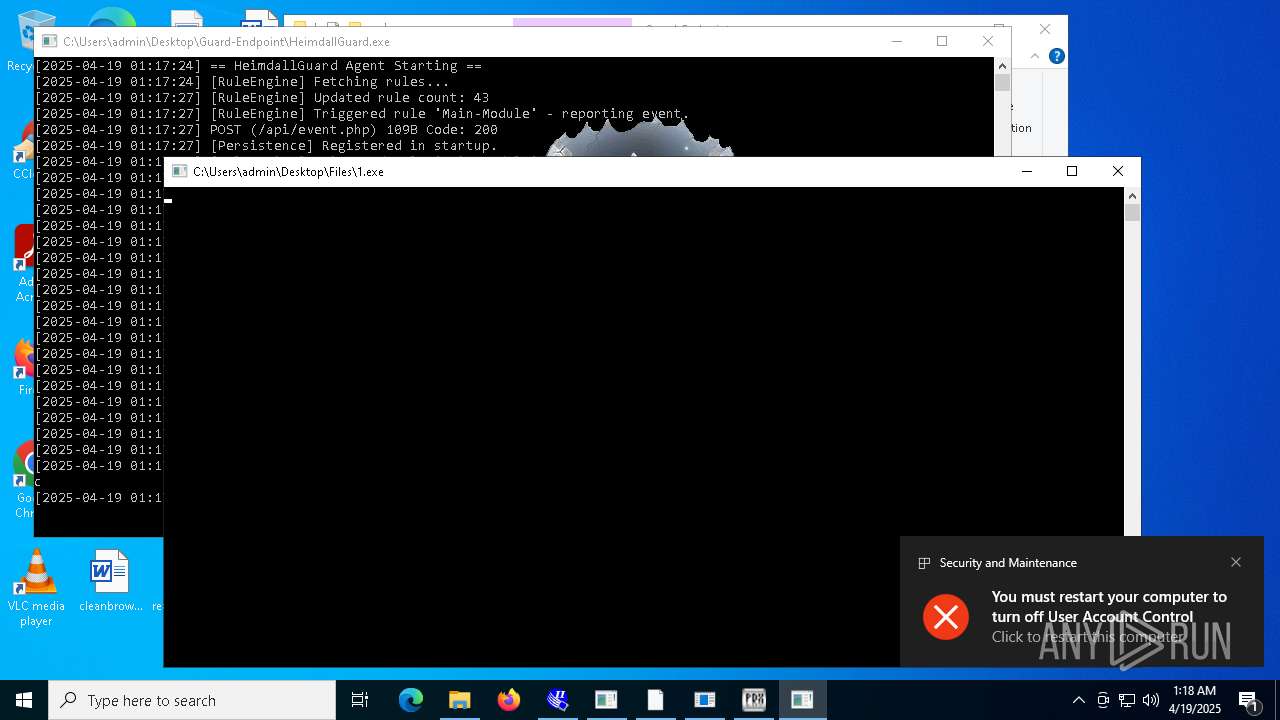
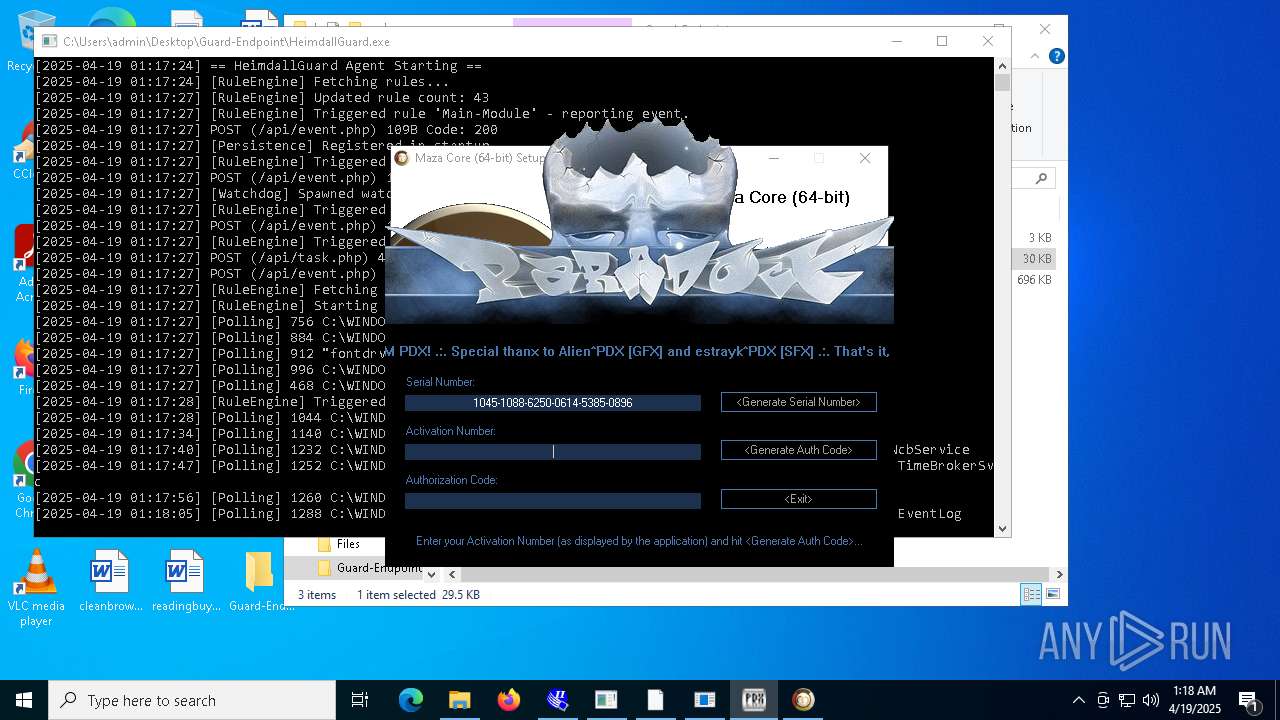
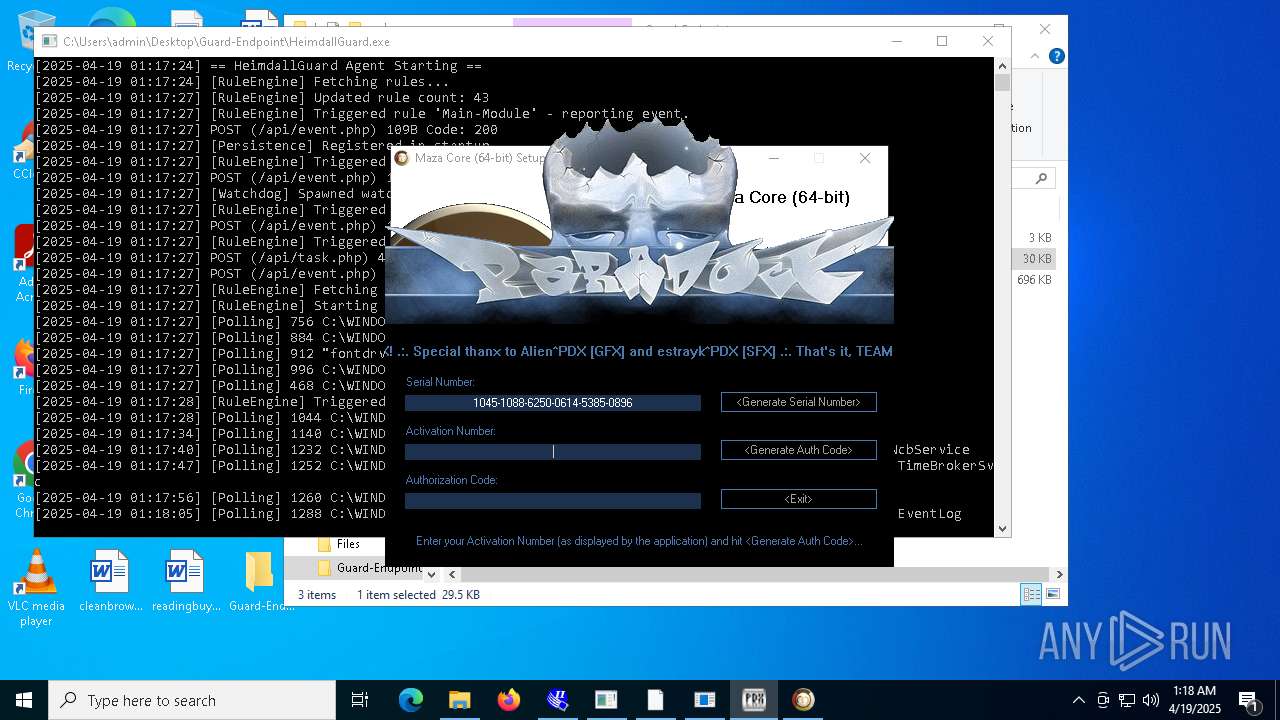
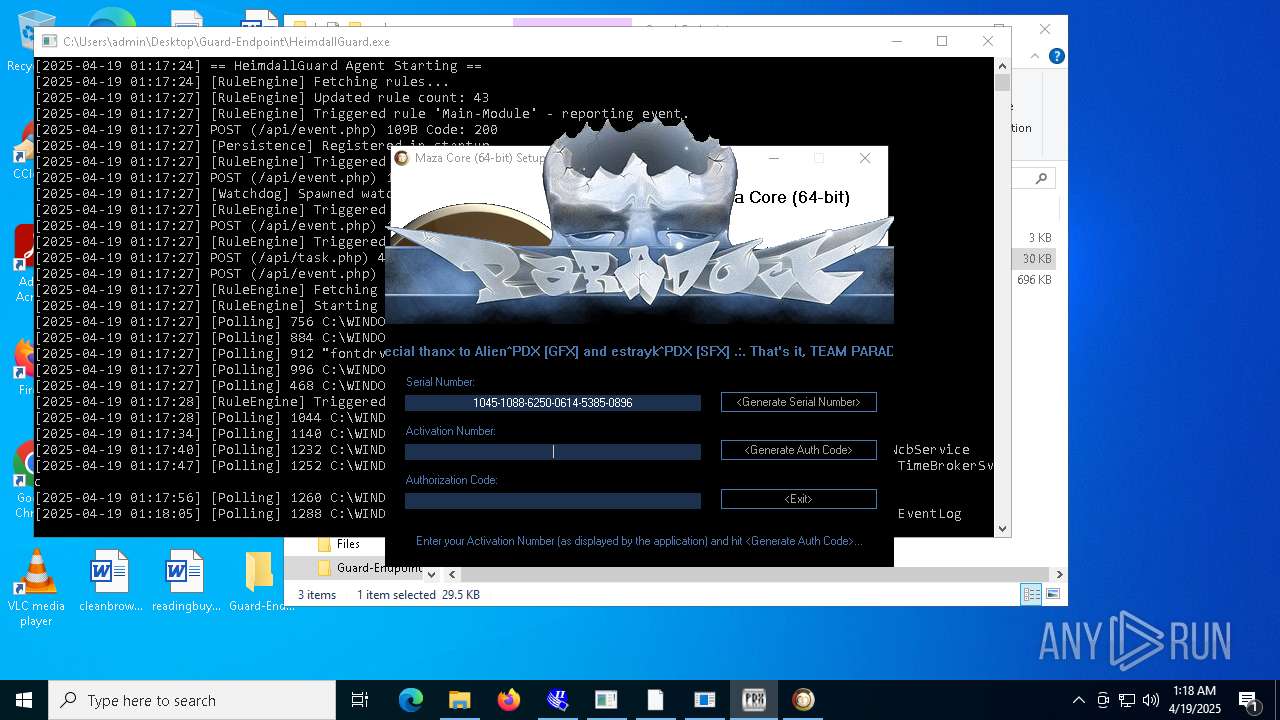
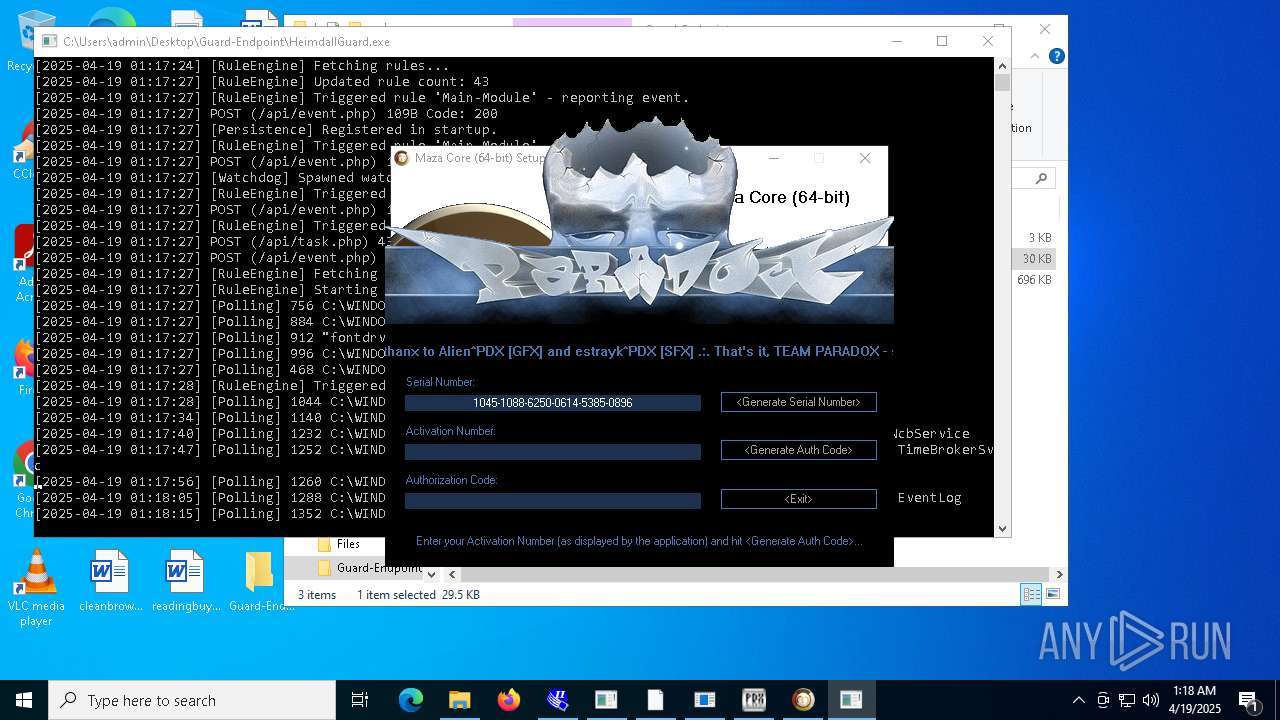
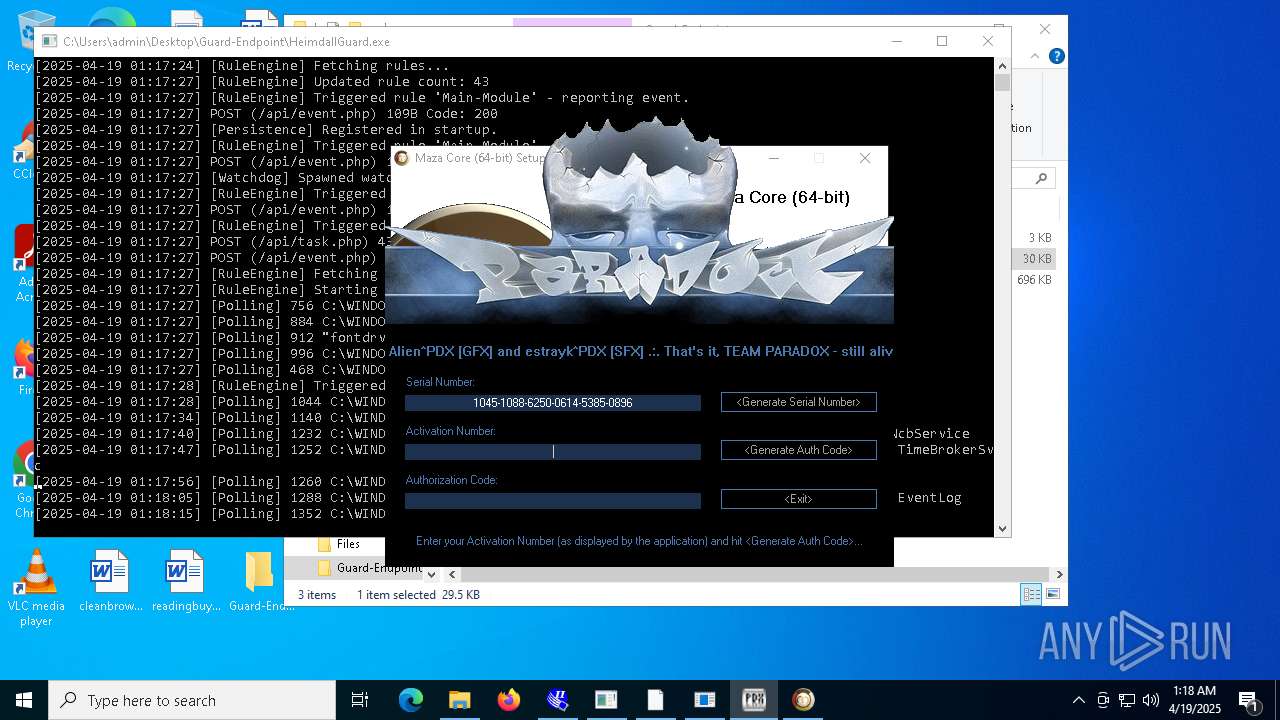
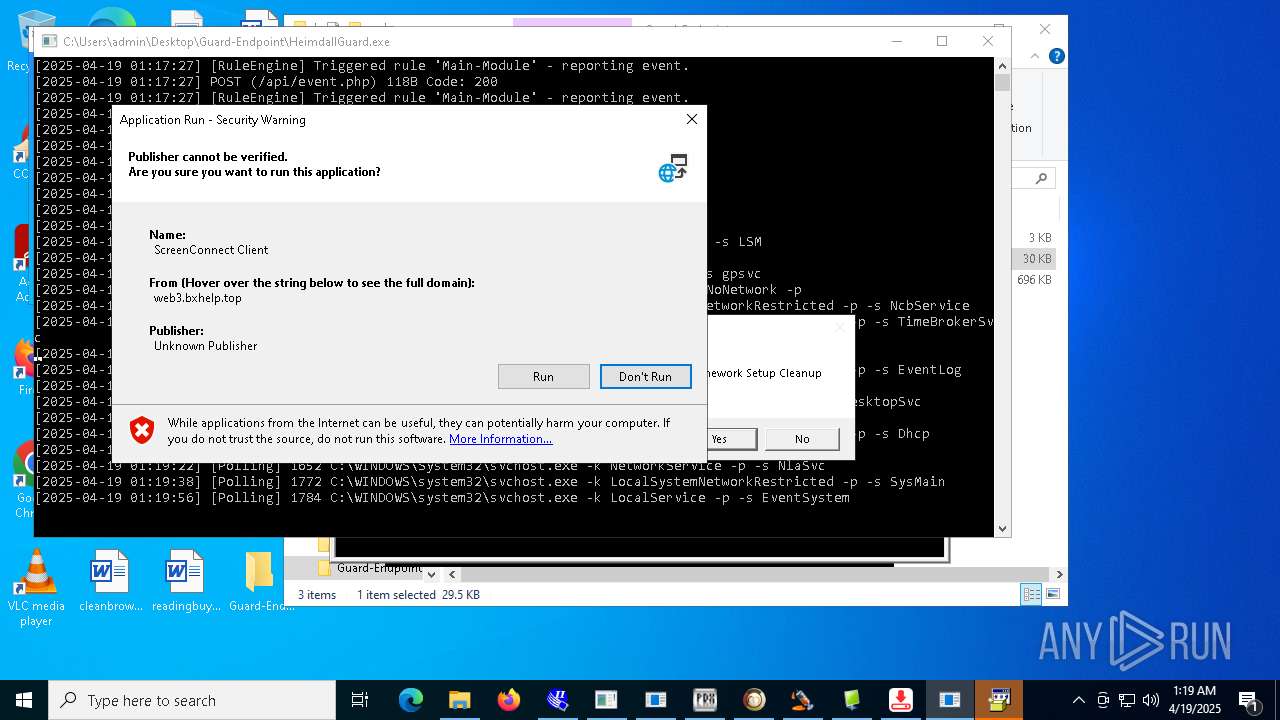
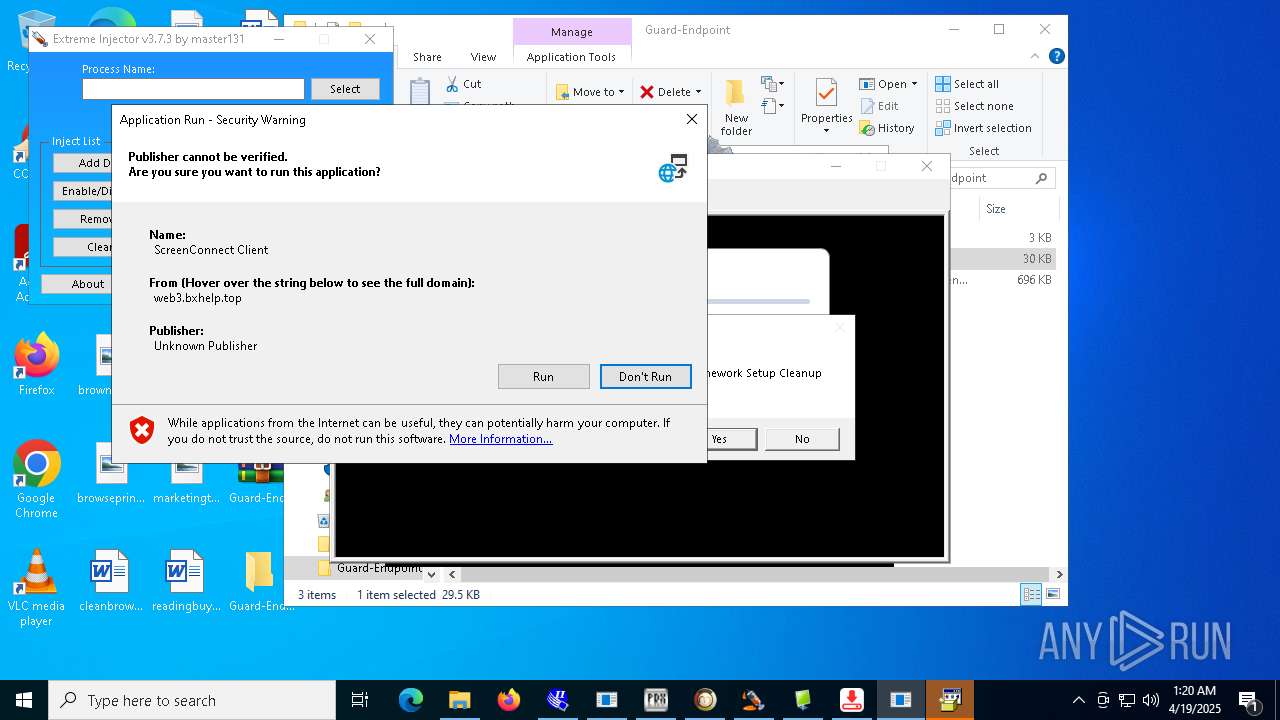
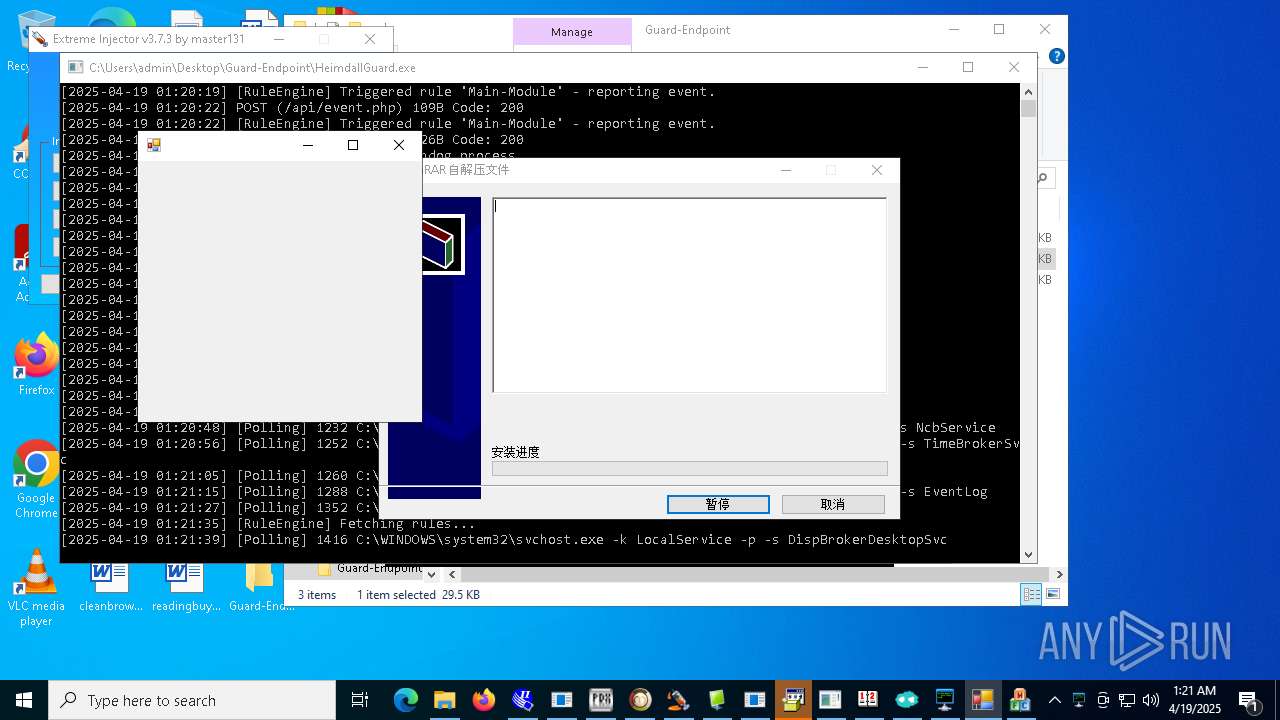
Manual execution by a user
- WinRAR.exe (PID: 6564)
- HeimdallGuard.exe (PID: 6564)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6564)
Reads Environment values
- Client-built.exe (PID: 6656)
- built.exe (PID: 5116)
- Client.exe (PID: 4024)
- PerfWatson1.exe (PID: 3888)
- Quas_Brout_ncrypt.exe (PID: 8164)
- Network.exe (PID: 7652)
- Clients.exe (PID: 7420)
- diskutil.exe (PID: 8120)
- diskutil.exe (PID: 7416)
- PerfWatson1.exe (PID: 7404)
- Client.exe (PID: 7448)
- alphaTweaks.exe (PID: 7808)
- msgde.exe (PID: 8528)
- Client.exe (PID: 9072)
- PerfWatson1.exe (PID: 9160)
- Clients.exe (PID: 9000)
- JJSPLOIT.V2.exe (PID: 9024)
- Sentil.exe (PID: 8016)
- Client1.exe (PID: 10144)
- windows 3543.exe (PID: 7380)
- Client.exe (PID: 5964)
- PerfWatson1.exe (PID: 9012)
- Clients.exe (PID: 5188)
- discord.exe (PID: 5380)
- Client.exe (PID: 10116)
- Clients.exe (PID: 6824)
- XClient.exe (PID: 2516)
- Client.exe (PID: 8220)
- PerfWatson1.exe (PID: 9012)
- Test2.exe (PID: 9152)
- Extreme%20Injector%20v3.exe (PID: 9796)
- Clients.exe (PID: 4880)
- PerfWatson1.exe (PID: 840)
- windows 3543.exe (PID: 9280)
- PerfWatson1.exe (PID: 11224)
- Clients.exe (PID: 10360)
- Clients.exe (PID: 10100)
- PerfWatson1.exe (PID: 10812)
- Clients.exe (PID: 10280)
- PerfWatson1.exe (PID: 9852)
- dfsvc.exe (PID: 540)
- RuntimeBroker.exe (PID: 11084)
- CleanerV2.exe (PID: 8328)
- spectrum.exe (PID: 9236)
- NJRAT%20DANGEROUS.exe (PID: 11104)
- payload.exe (PID: 3304)
- JUSCHED.EXE (PID: 12172)
- CollosalLoader.exe (PID: 7136)
- Clients.exe (PID: 11292)
- PerfWatson1.exe (PID: 12044)
- windows 3543.exe (PID: 8032)
- Clients.exe (PID: 12092)
- PerfWatson1.exe (PID: 5176)
- Neverlose%20Loader.exe (PID: 1176)
Creates files or folders in the user directory
- Microsoft_Hardware_Launch.exe (PID: 1180)
- Client-built.exe (PID: 6656)
- built.exe (PID: 5116)
- MSystem32.exe (PID: 2772)
- Fast%20Download.exe (PID: 4040)
- WerFault.exe (PID: 7788)
- diskutil.exe (PID: 8120)
- RuntimeBrokerSvc.exe (PID: 7404)
- JJSPLOIT.V2.exe (PID: 9024)
- Sentil.exe (PID: 8016)
- Network.exe (PID: 7652)
- discord.exe (PID: 5380)
- XClient.exe (PID: 2516)
- Mph.pif (PID: 6656)
- new.exe (PID: 8952)
- Loader.exe (PID: 10980)
- WerFault.exe (PID: 4144)
- cheet.exe (PID: 10744)
- dllhost.exe (PID: 11248)
- Update.exe (PID: 1184)
- dfsvc.exe (PID: 540)
- RuntimeBroker.exe (PID: 11084)
- WerFault.exe (PID: 10408)
- CleanerV2.exe (PID: 8328)
- spectrum.exe (PID: 9236)
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- JUSCHED.EXE (PID: 12172)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
- CollosalLoader.exe (PID: 7136)
- OpenArk32.exe (PID: 11100)
- 99999.exe (PID: 12028)
- NOTallowedtocrypt.exe (PID: 12800)
- WerFault.exe (PID: 7236)
- WerFault.exe (PID: 11048)
- server.exe (PID: 12672)
- ENP.exe (PID: 6744)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- stub.exe (PID: 11160)
- diskutil.exe (PID: 7416)
- KZReport.exe (PID: 8028)
Creates a new folder
- cmd.exe (PID: 1164)
- cmd.exe (PID: 11232)
Changes the display of characters in the console
- cmd.exe (PID: 1812)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 3240)
- cmd.exe (PID: 8256)
- cmd.exe (PID: 9068)
- cmd.exe (PID: 9320)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 9324)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 9924)
- cmd.exe (PID: 9672)
- cmd.exe (PID: 10920)
- cmd.exe (PID: 10880)
- cmd.exe (PID: 10860)
- cmd.exe (PID: 5116)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 10620)
- cmd.exe (PID: 10676)
- cmd.exe (PID: 11080)
- cmd.exe (PID: 10972)
- cmd.exe (PID: 8536)
- cmd.exe (PID: 11448)
- cmd.exe (PID: 9740)
- cmd.exe (PID: 10504)
- cmd.exe (PID: 7100)
- cmd.exe (PID: 11904)
- cmd.exe (PID: 1584)
- cmd.exe (PID: 5708)
Process checks whether UAC notifications are on
- MSystem32.exe (PID: 2772)
- dfsvc.exe (PID: 540)
Creates files in the program directory
- MSystem32.exe (PID: 2772)
- Quas_Brout_ncrypt.exe (PID: 8164)
- FXServer.exe (PID: 8272)
- GoogleUpdate.exe (PID: 8316)
- main.exe (PID: 10648)
- Loader.exe (PID: 10980)
- iexplore.exe (PID: 12560)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
Reads mouse settings
- Piss.com (PID: 7984)
- Mph.pif (PID: 6656)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7824)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8460)
- powershell.exe (PID: 9716)
- powershell.exe (PID: 11776)
- powershell.exe (PID: 11836)
- powershell.exe (PID: 7524)
Checks operating system version
- networks_profile.exe (PID: 2332)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7824)
- powershell.exe (PID: 1272)
- powershell.exe (PID: 8460)
- powershell.exe (PID: 9716)
- powershell.exe (PID: 11836)
- powershell.exe (PID: 12284)
Execution of CURL command
- cmd.exe (PID: 8500)
Drops encrypted JS script (Microsoft Script Encoder)
- 1.exe (PID: 10092)
- tool.exe (PID: 11972)
Reads CPU info
- NdisInstaller3.2.32.1.exe (PID: 9040)
- Build.exe (PID: 3396)
- crypted.exe (PID: 10384)
- CefSharp.BrowsersSubprocess.exe (PID: 9752)
The sample compiled with chinese language support
- 4363463463464363463463463.exe (PID: 6108)
- KuaiZip_Setup_-808202126_xiaopeng2_001.exe (PID: 5620)
- 4.exe (PID: 11512)
Reads security settings of Internet Explorer
- comp.exe (PID: 3976)
- powershell.exe (PID: 7524)
- net.exe (PID: 11156)
Reads Microsoft Office registry keys
- M7XQmz2DgtiyE3f.exe (PID: 4220)
- OpenWith.exe (PID: 12216)
Connects to unusual port
- iexplore.exe (PID: 12560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(1180) Microsoft_Hardware_Launch.exe
C2micrsoft.con-ip.com
Ports8888
BotnetVicTam :D
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\67ff3a880cd1a5cd235418c7516e5812
Splitter|'|'|
Version0.7d
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
861
Monitored processes
674
Malicious processes
113
Suspicious processes
47
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 540 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\dfsvc.exe | support.client.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: ClickOnce Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 616 | "schtasks" /create /tn "Discord" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Client-built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | schtasks /create /sc minute /mo 1 /tn "MicrosoftEdgeUpdateTaskMachine" /tr C:\ProgramData\dllhost.exe | C:\Windows\SysWOW64\schtasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "schtasks" /create /tn "Discord" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 832 | "C:\Program Files\¿ìѹ\X86\KuaiZip.exe" -AssociateAll | C:\Program Files\¿ìѹ\X86\KuaiZip.exe | — | KuaiZip_Setup_-808202126_xiaopeng2_001.exe | |||||||||||
User: admin Integrity Level: HIGH Description: KuaiZip Application Exit code: 0 Version: 2, 8, 2, 28 Modules
| |||||||||||||||
| 840 | "C:\Users\admin\AppData\Roaming\KDOT\PerfWatson1.exe" | C:\Users\admin\AppData\Roaming\KDOT\PerfWatson1.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PerfWatson1.exe Exit code: 0 Version: 17.0.33413.361 Modules
| |||||||||||||||
| 856 | findstr "bdservicehost AvastUI AVGUI nsWscSvc ekrn SophosHealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
189 901
Read events
187 874
Write events
1 749
Delete events
278
Modification events
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6108) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
413
Suspicious files
293
Text files
188
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6108 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\InstructionalPostings.exe | executable | |
MD5:C8F28FF2F4E935729188FE583E2BAD12 | SHA256:751C27BEF3D94BF3FCCC780E6658D1441DC1EFC01FCD9F56F82CBE2C43668C16 | |||
| 1116 | InstructionalPostings.exe | C:\Users\admin\AppData\Local\Temp\Dive.midi | binary | |
MD5:88A1327587B0838544A26F5CA8A3A152 | SHA256:372B4857157569A1FD17FDAE43D91467D77B07E19DEAECBC672DCB1E67A6A28A | |||
| 1116 | InstructionalPostings.exe | C:\Users\admin\AppData\Local\Temp\Stack.midi | binary | |
MD5:64DB348DC3EA432D5A0EAD6F116C3A62 | SHA256:F4AA9C1A48415EAB41F373BB93CAA18BF76D62CE02075DCCAFA32314F066C23A | |||
| 1116 | InstructionalPostings.exe | C:\Users\admin\AppData\Local\Temp\Studied.midi | binary | |
MD5:363C0B83697C424E12FC5185F1BDBFED | SHA256:DF100FC19F1248FDA479DC3EF16FB83D85BF506071F9970C6B9848F1D8E343FE | |||
| 1116 | InstructionalPostings.exe | C:\Users\admin\AppData\Local\Temp\Perfect.midi | binary | |
MD5:15E045D31DB97F3B9A83B763137576A1 | SHA256:E8EC7AB89F6219B2ECD82F62456DEBFAEE80F9D9F138666DAFFB1D21965A5202 | |||
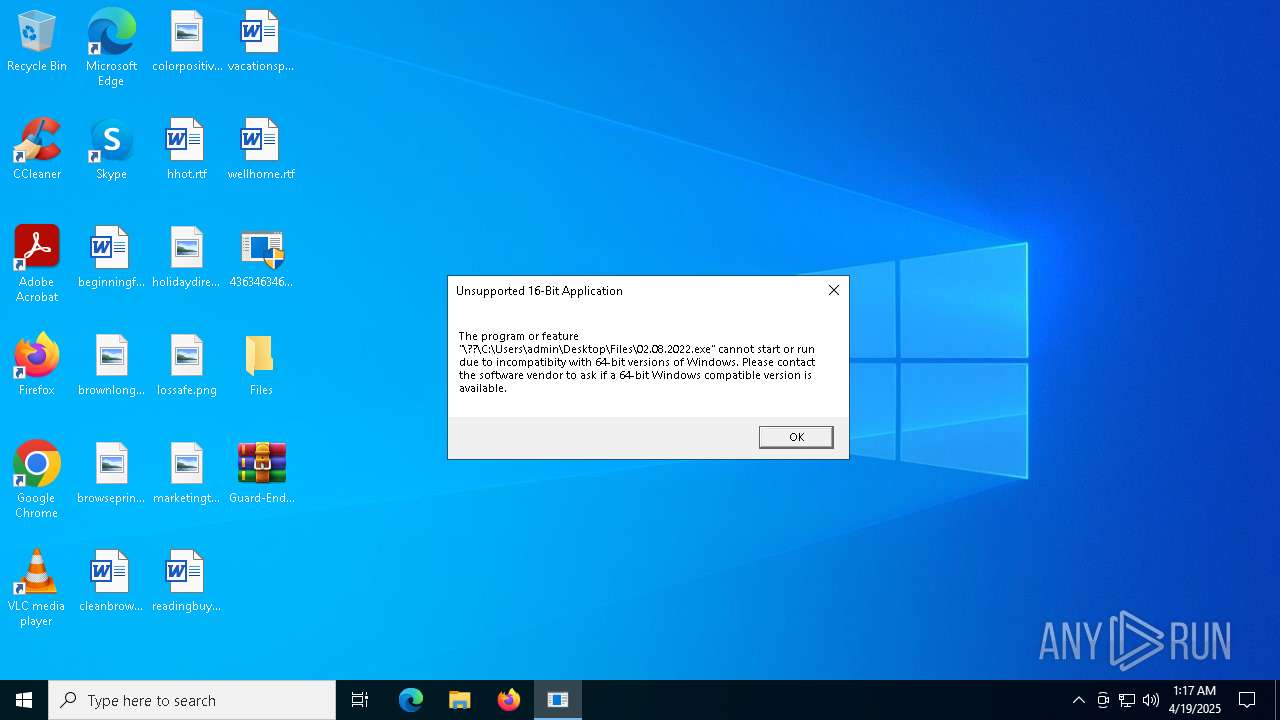
| 6108 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\02.08.2022.exe | binary | |
MD5:12B566F028B1DA014115EBED2A1EA1AF | SHA256:F66A00A74DB41EFD445913B28A49AEF2186F80AB5AE8F2F21A04FCDFE04A1B78 | |||
| 1116 | InstructionalPostings.exe | C:\Users\admin\AppData\Local\Temp\Und.midi | binary | |
MD5:BABFBB6B6F62E47F91F6B98EC80E286E | SHA256:7FBCD2D3344AF8029ABCAF2230133EBD2BE18310C680D4275CEB17A195436753 | |||
| 1116 | InstructionalPostings.exe | C:\Users\admin\AppData\Local\Temp\Laptop.midi | text | |
MD5:1DFD61902E836C24681CD48E96BDA1C5 | SHA256:CC51E4029128714712FDE438D8DA46C48438E637AB32FD97BEEA6200D641D3F3 | |||
| 1116 | InstructionalPostings.exe | C:\Users\admin\AppData\Local\Temp\Worker.midi | compressed | |
MD5:5FF4D0C7986CB75A03AEC9C8CFBA840F | SHA256:BA1035CA1FF4F2AD5DE529866551D0F32A4D5E24B79098071013DD7D953A01C2 | |||
| 1116 | InstructionalPostings.exe | C:\Users\admin\AppData\Local\Temp\Rapids.midi | binary | |
MD5:E3CE45CD8F91903AA2DFEC21A636C752 | SHA256:1265017F7F6FC4C201D322267D5920D7DE6BCB28E1A9544C82D0D0C54E97F8F2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
147
TCP/UDP connections
46 920
DNS requests
208
Threats
840
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6108 | 4363463463464363463463463.exe | GET | 301 | 140.82.121.4:80 | http://github.com/XCocGT/priv1/raw/refs/heads/main/Microsoft_Hardware_Launch.exe | unknown | — | — | whitelisted |
6108 | 4363463463464363463463463.exe | GET | 200 | 87.121.84.254:80 | http://microsoft-auth-network.cc/1337/TORRENTOLD-1.exe | unknown | — | — | unknown |
6108 | 4363463463464363463463463.exe | GET | 200 | 210.216.165.152:80 | http://storage.soowim.co.kr/PsExec64.exe | unknown | — | — | unknown |
6108 | 4363463463464363463463463.exe | GET | 301 | 140.82.121.4:80 | http://github.com/ff245185/payload/raw/refs/heads/main/Fast%20Download.exe | unknown | — | — | whitelisted |
6108 | 4363463463464363463463463.exe | GET | — | 93.176.52.107:80 | http://93.176.52.107/Quas_Brout_ncrypt.exe | unknown | — | — | malicious |
6108 | 4363463463464363463463463.exe | GET | 200 | 106.42.31.65:8088 | http://106.42.31.65:8088/Wait.exe | unknown | — | — | unknown |
6108 | 4363463463464363463463463.exe | GET | 200 | 211.149.230.178:80 | http://www.hseda.com/download/qt51crk.exe | unknown | — | — | malicious |
7652 | Network.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6108 | 4363463463464363463463463.exe | 151.101.66.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
6108 | 4363463463464363463463463.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
6544 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6108 | 4363463463464363463463463.exe | 185.199.108.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
github.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
microsoft-auth-network.cc |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6108 | 4363463463464363463463463.exe | Targeted Malicious Activity was Detected | ET HUNTING Suspicious Empty SSL Certificate - Observed in Cobalt Strike |
6108 | 4363463463464363463463463.exe | A Network Trojan was detected | ET MALWARE Meterpreter or Other Reverse Shell SSL Cert |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6108 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
6108 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6108 | 4363463463464363463463463.exe | Misc activity | ET INFO Packed Executable Download |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6108 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
6108 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |