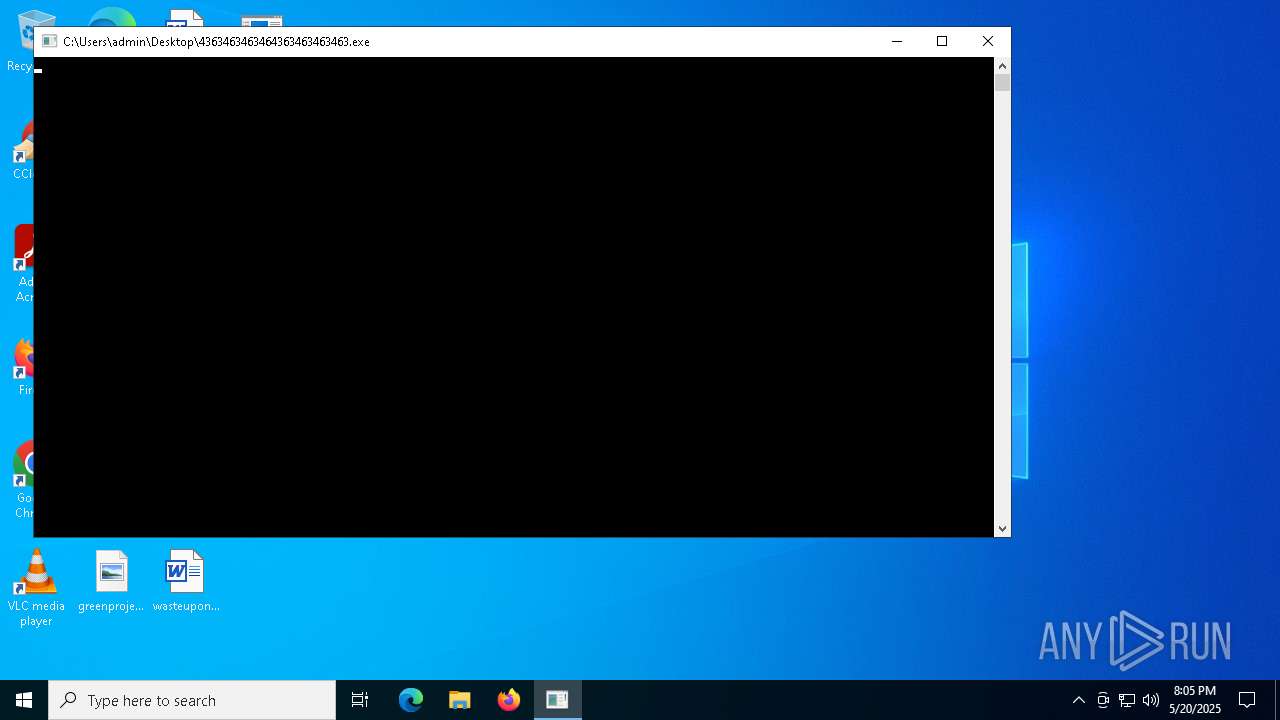
| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/65a6d1ed-8638-4ede-b53a-59326b900e48 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 20, 2025, 20:05:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
DISCORDRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
STEALER has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
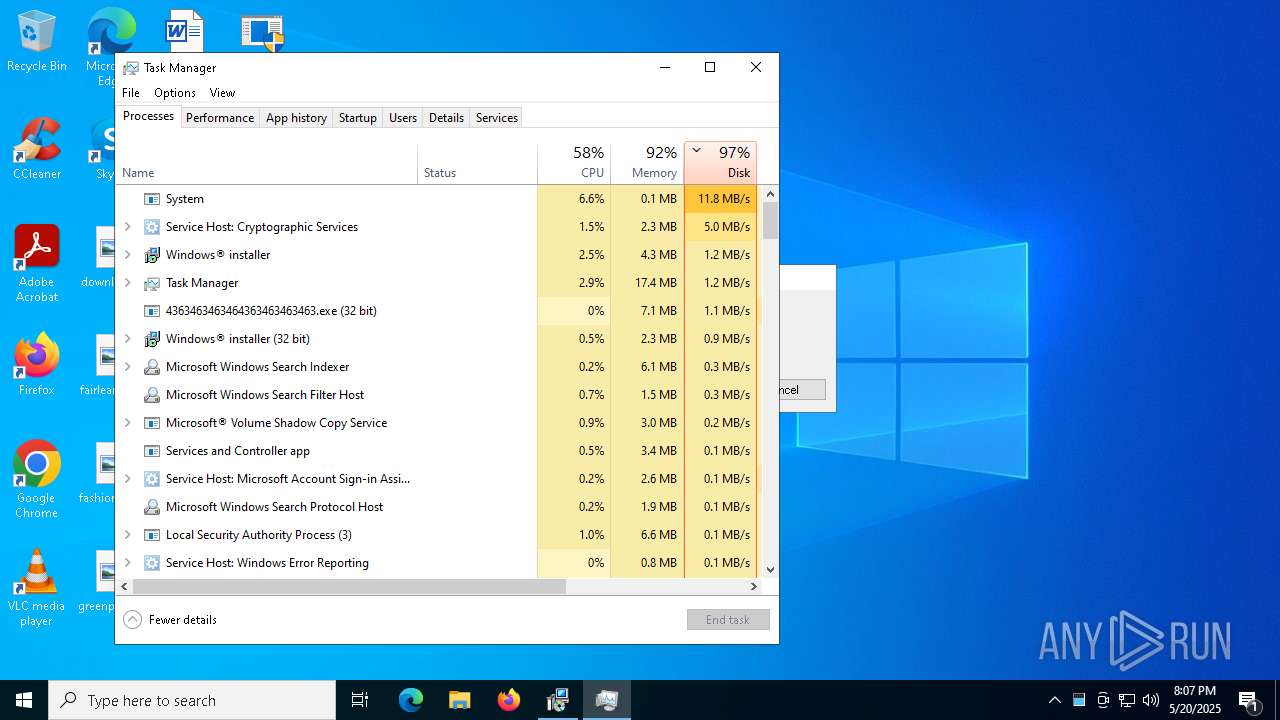
Connects to the CnC server
- svchost.exe (PID: 2196)
- dwm.exe (PID: 2416)
- 4363463463464363463463463.exe (PID: 7528)
- syscrondvr.exe (PID: 9508)
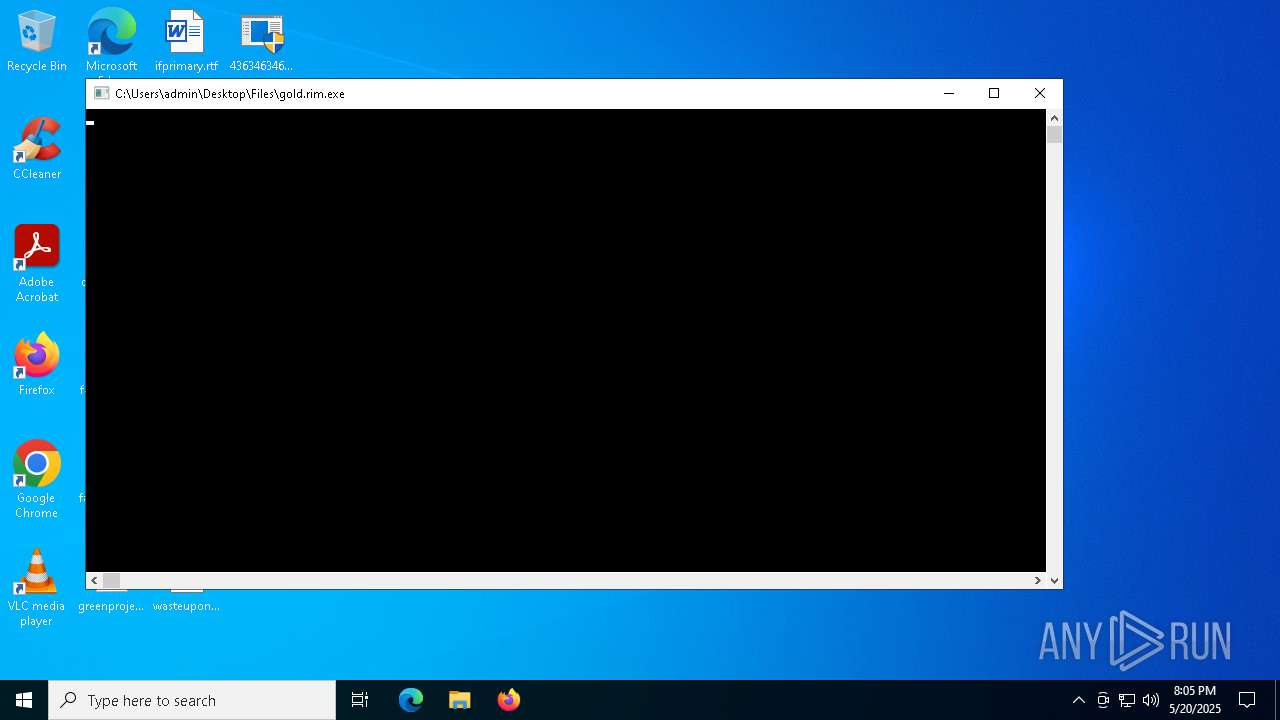
LUMMA has been detected (SURICATA)
- gold.rim.exe (PID: 8096)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 8812)
- MSBuild.exe (PID: 8932)
- MSBuild.exe (PID: 10112)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 7528)
GENERIC has been found (auto)
- update.exe (PID: 496)
- 4363463463464363463463463.exe (PID: 7528)
- 4363463463464363463463463.exe (PID: 7528)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6372)
DISCORDRAT has been detected (YARA)
- Client-built.exe (PID: 7836)
MINER has been detected (SURICATA)
- dwm.exe (PID: 2416)
GHOSTSOCKS has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
Vulnerable driver has been detected
- sysmtdrav.exe (PID: 2084)
Starts CertUtil for downloading files
- cmd.exe (PID: 9068)
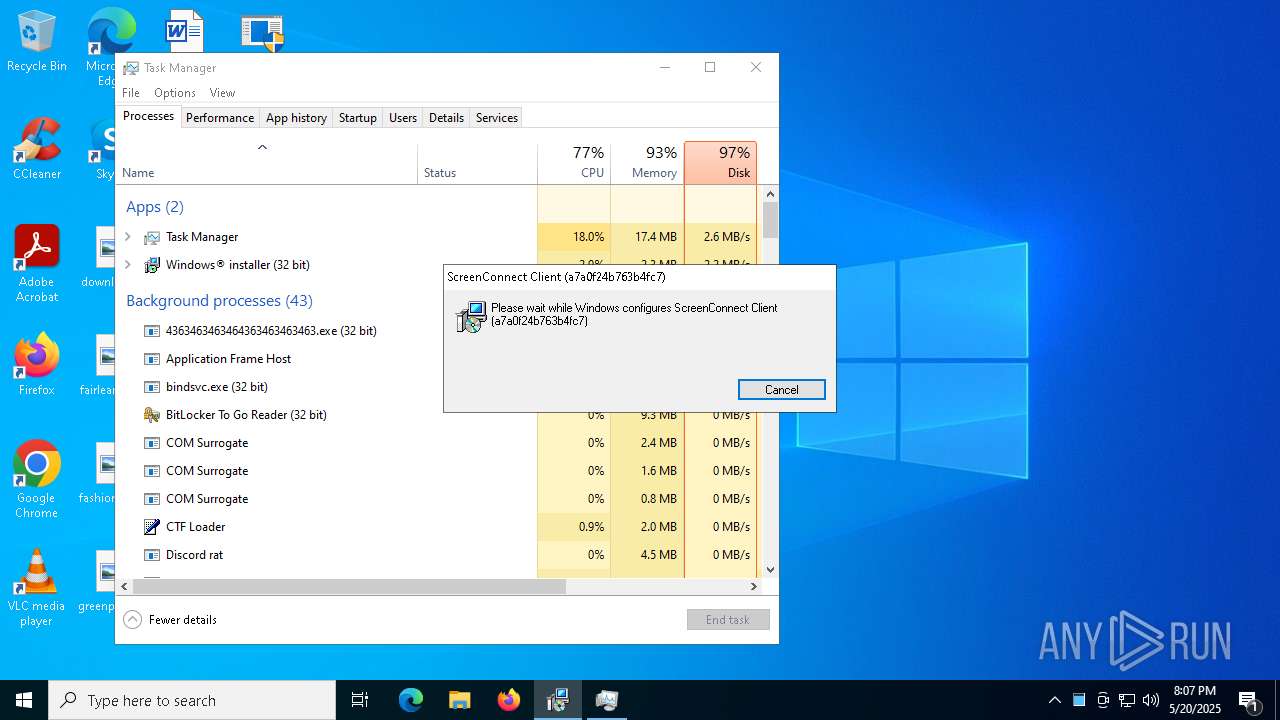
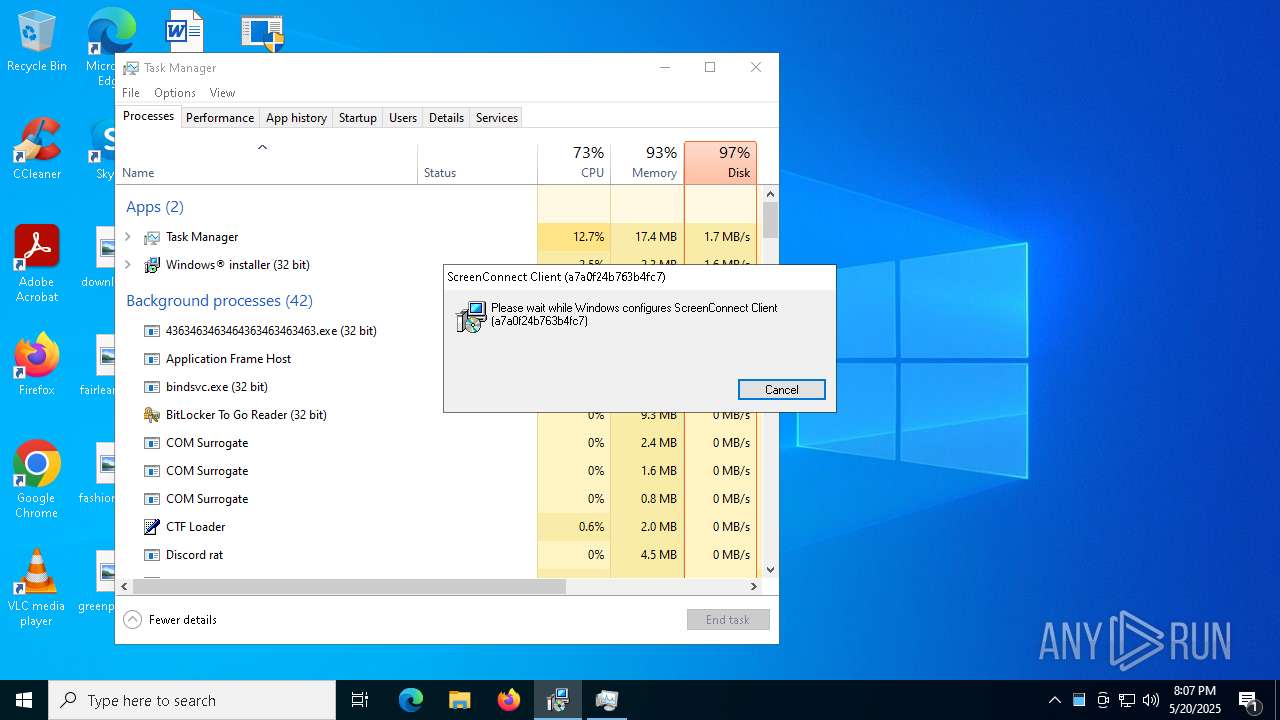
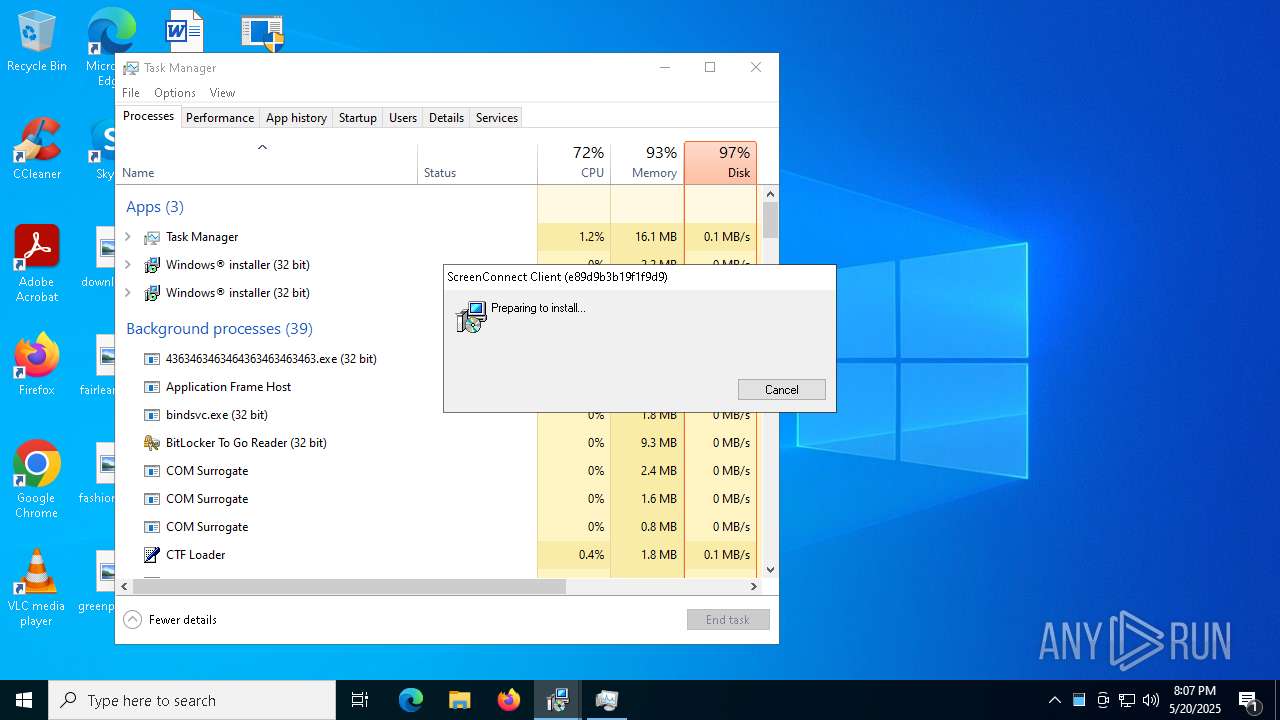
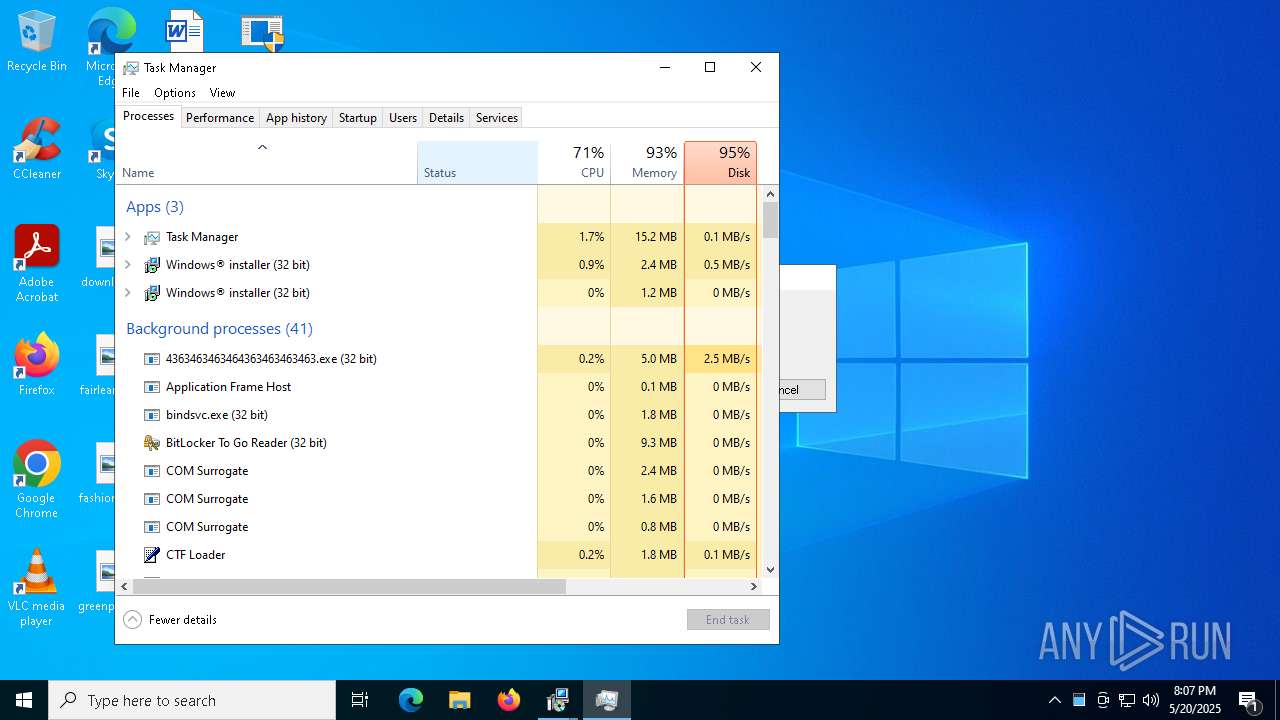
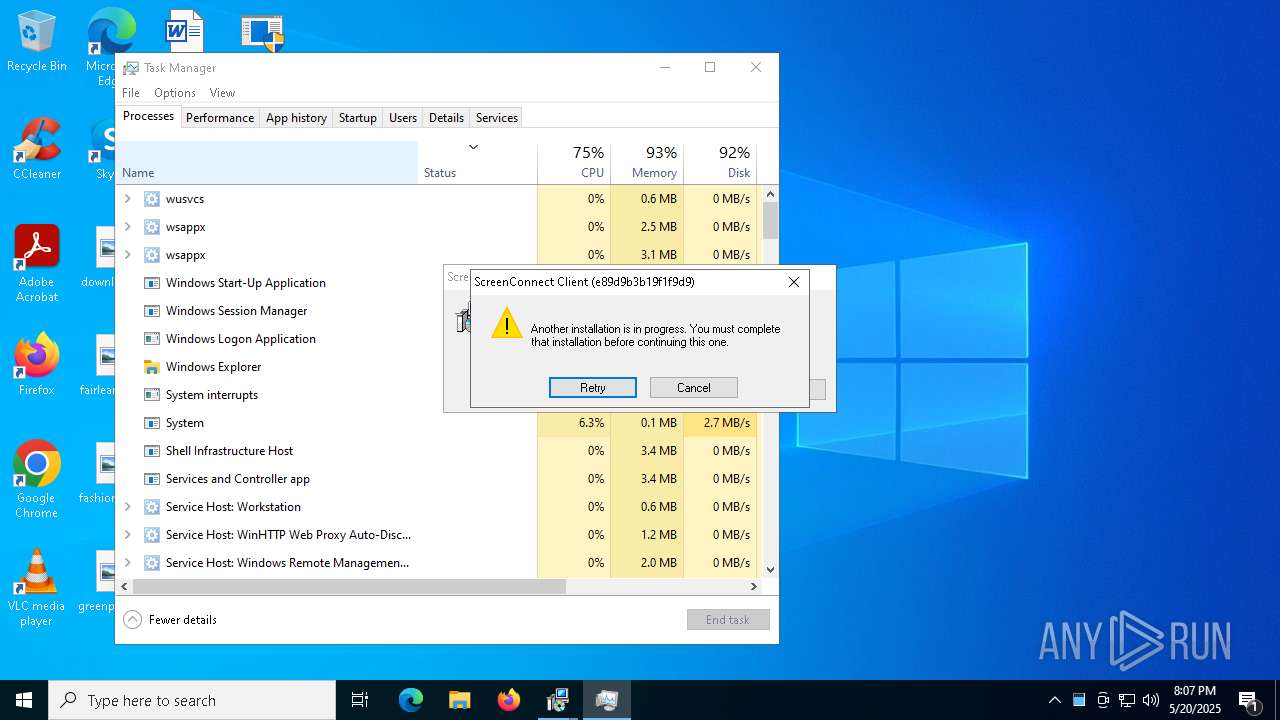
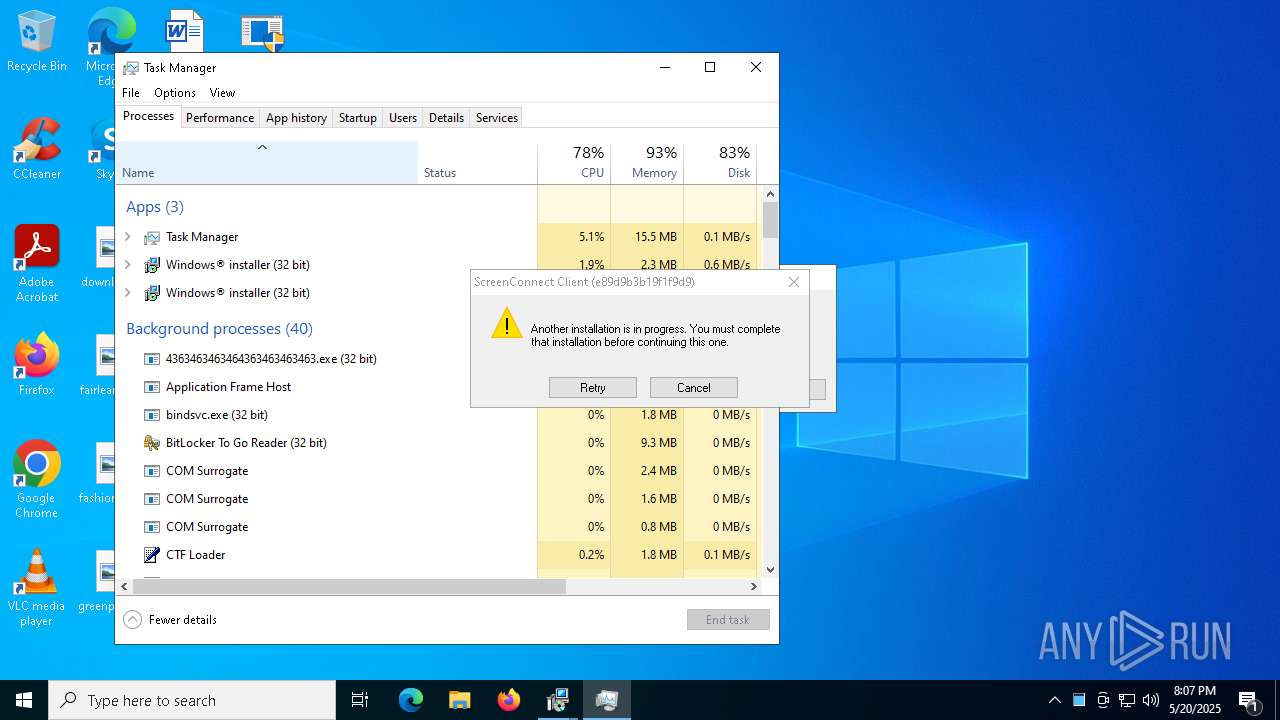
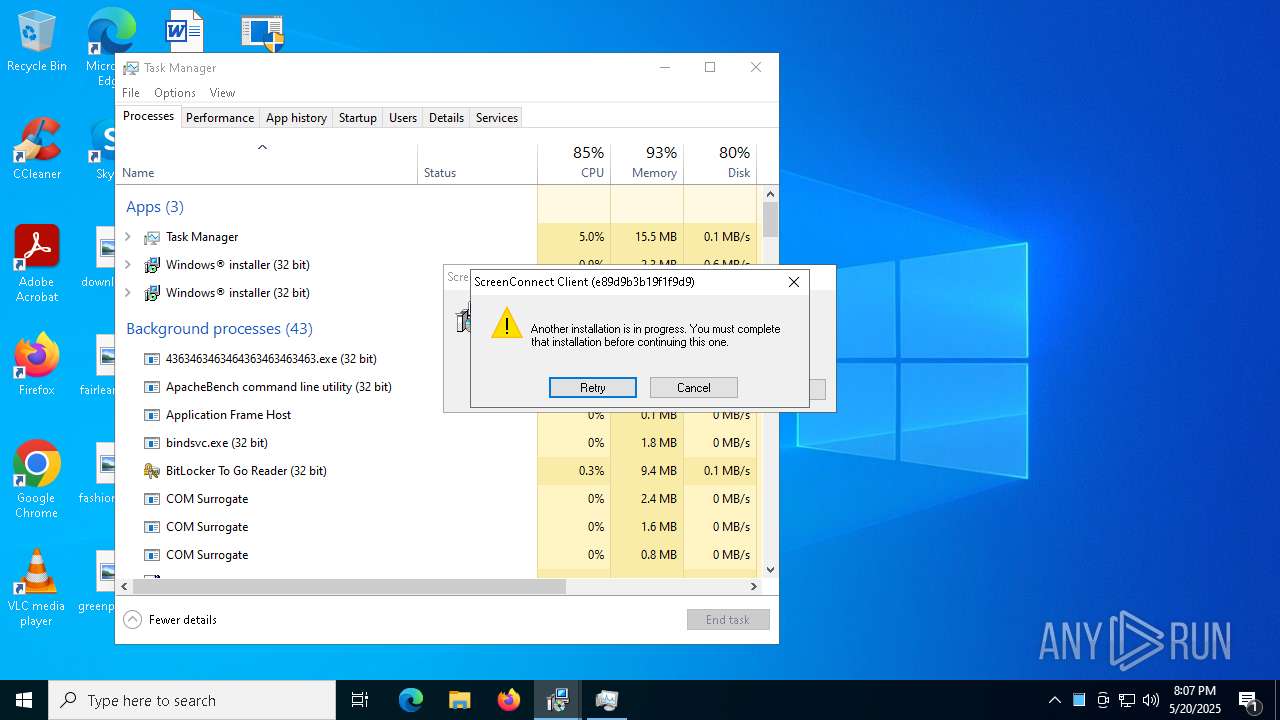
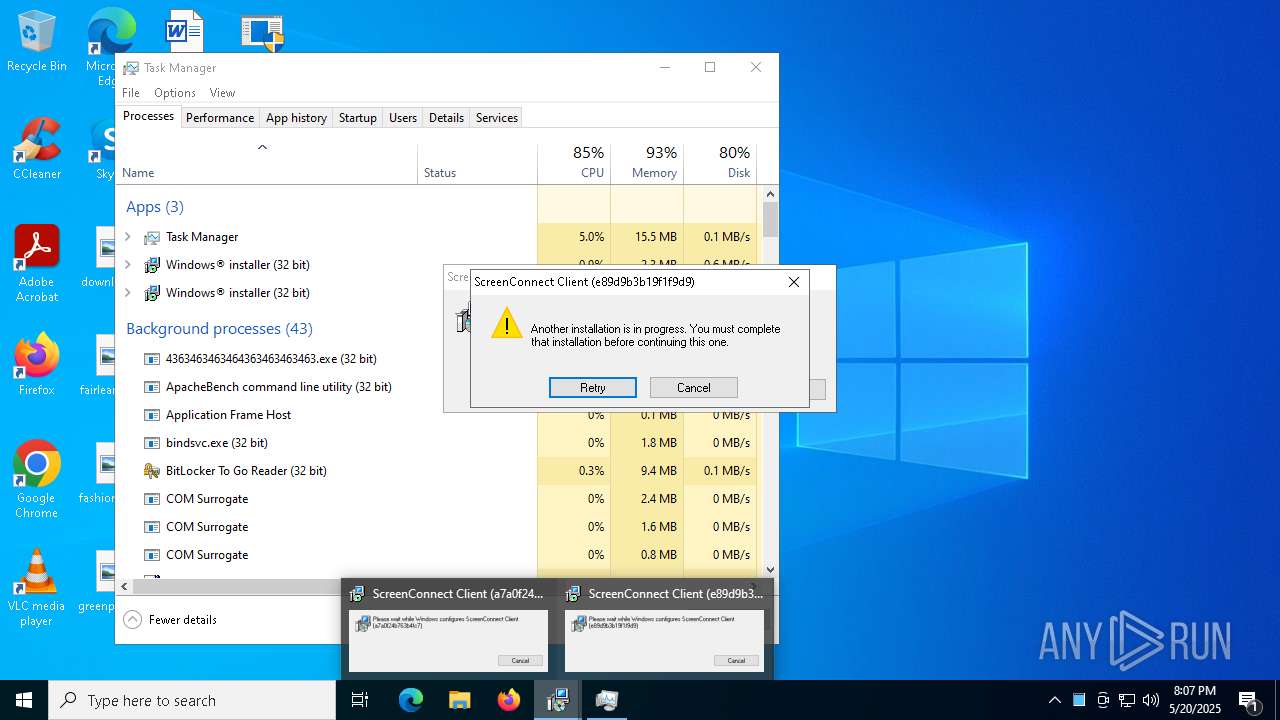
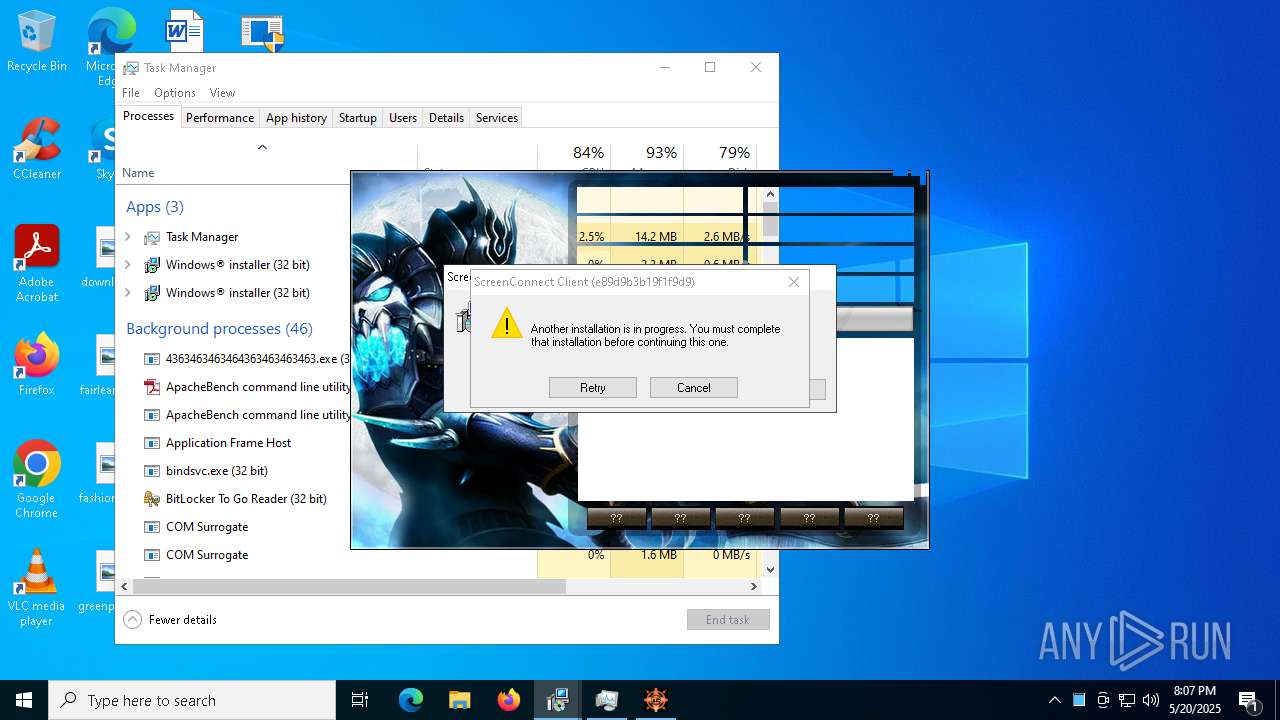
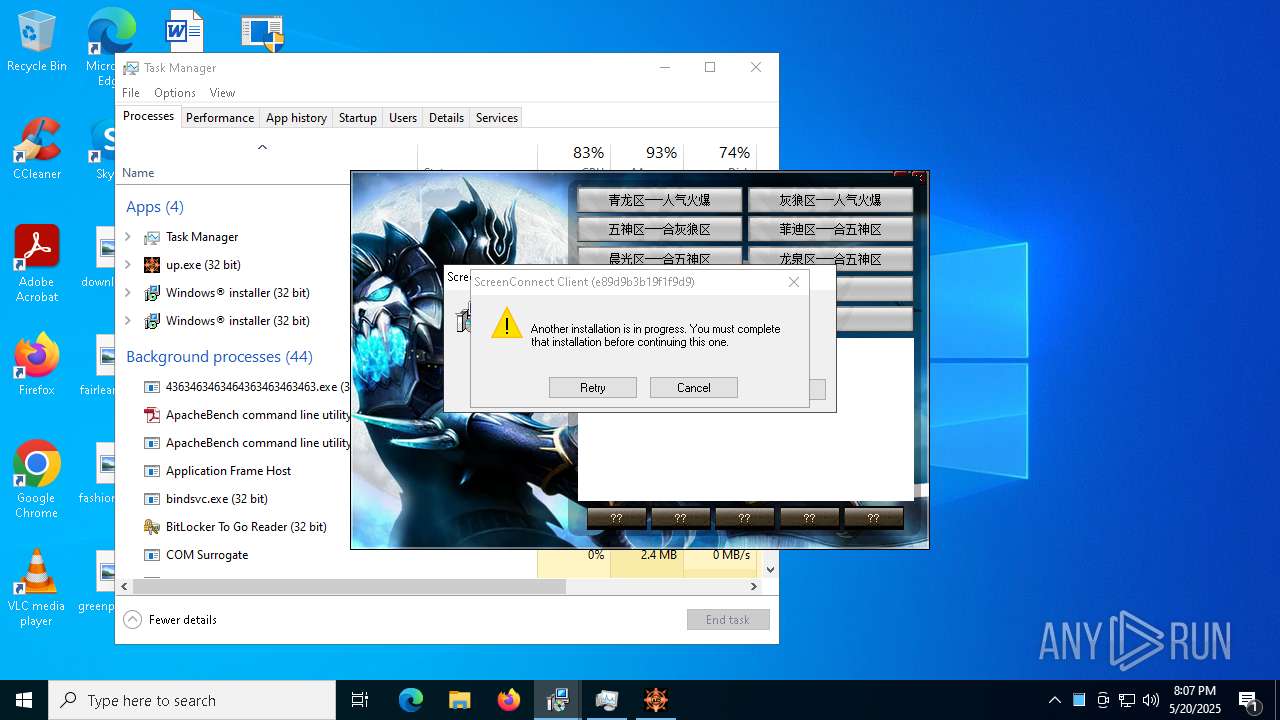
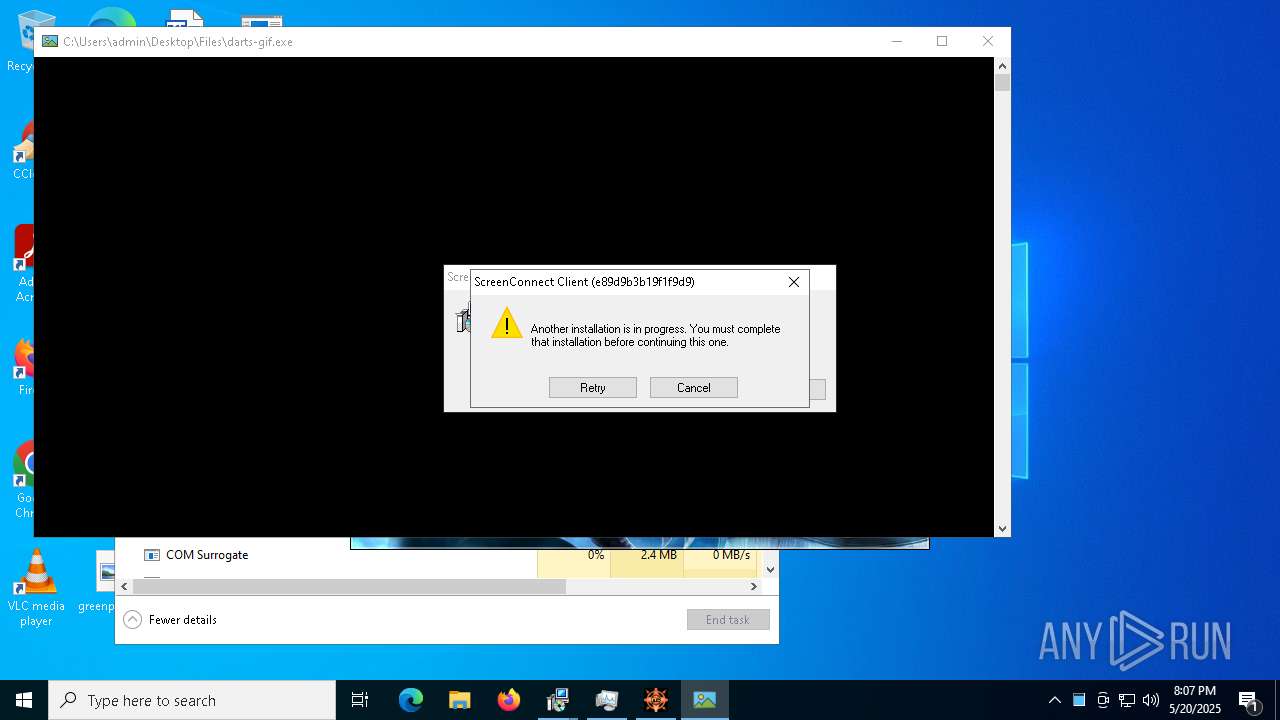
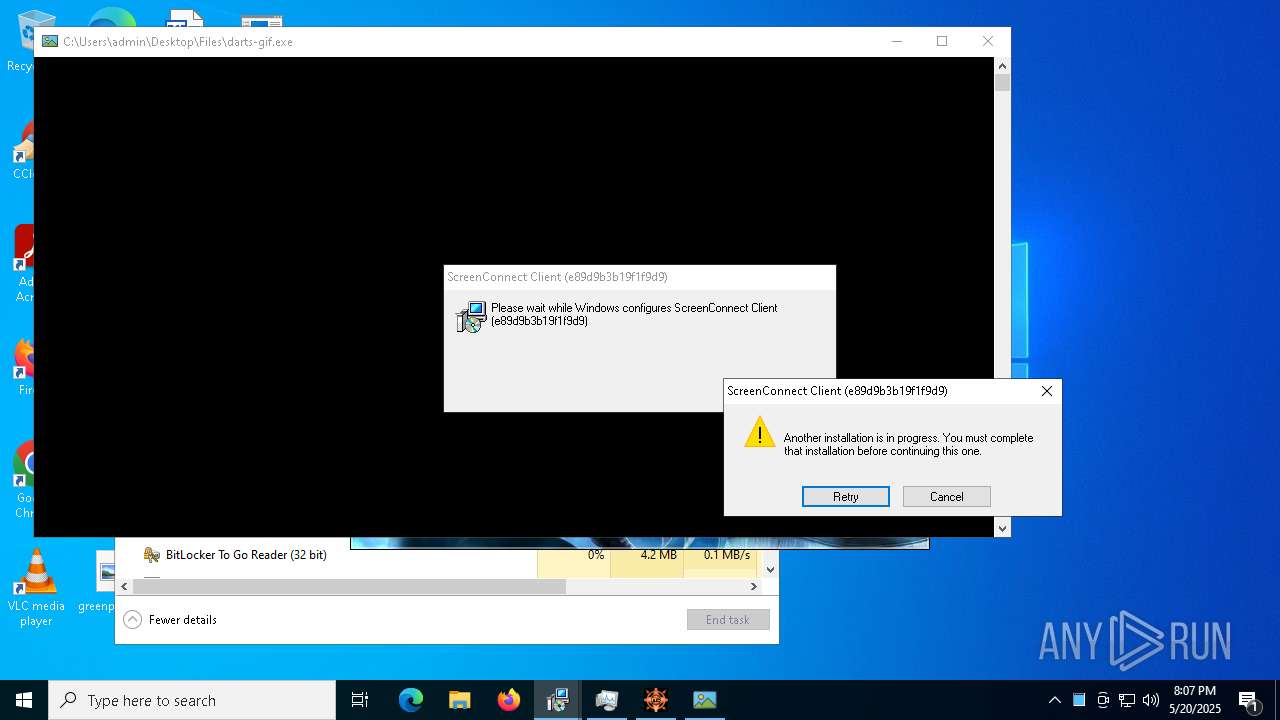
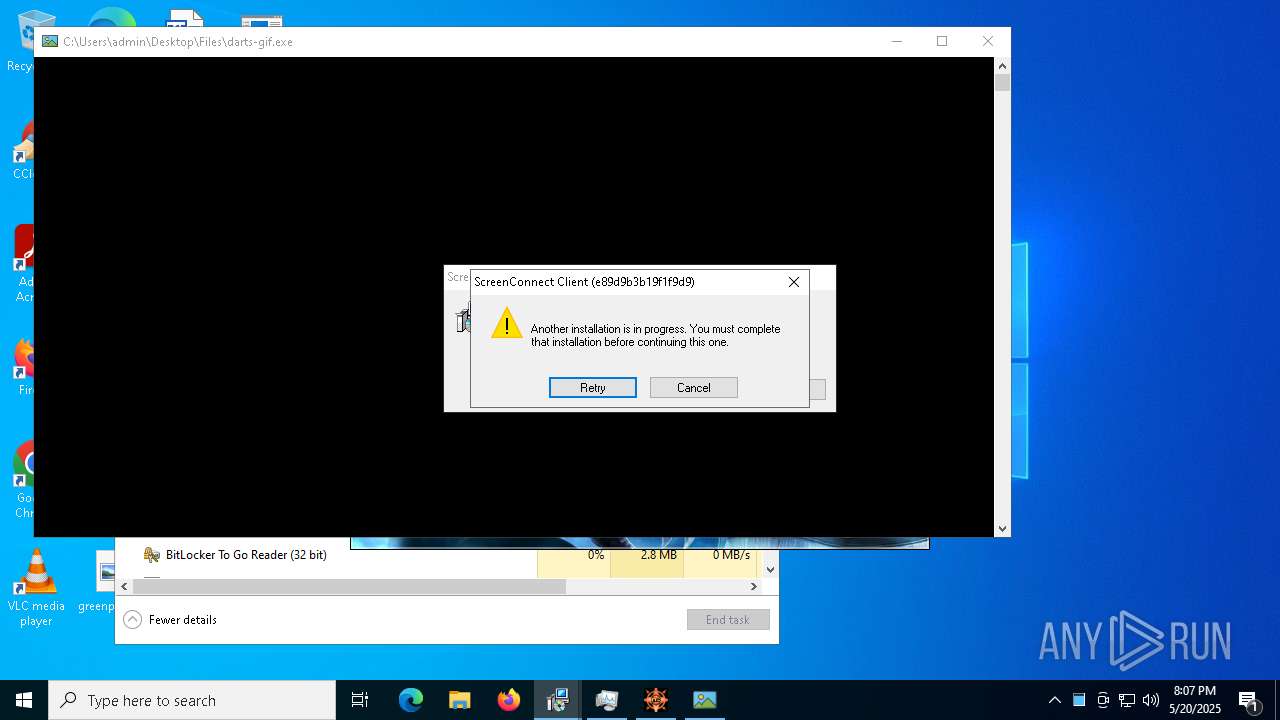
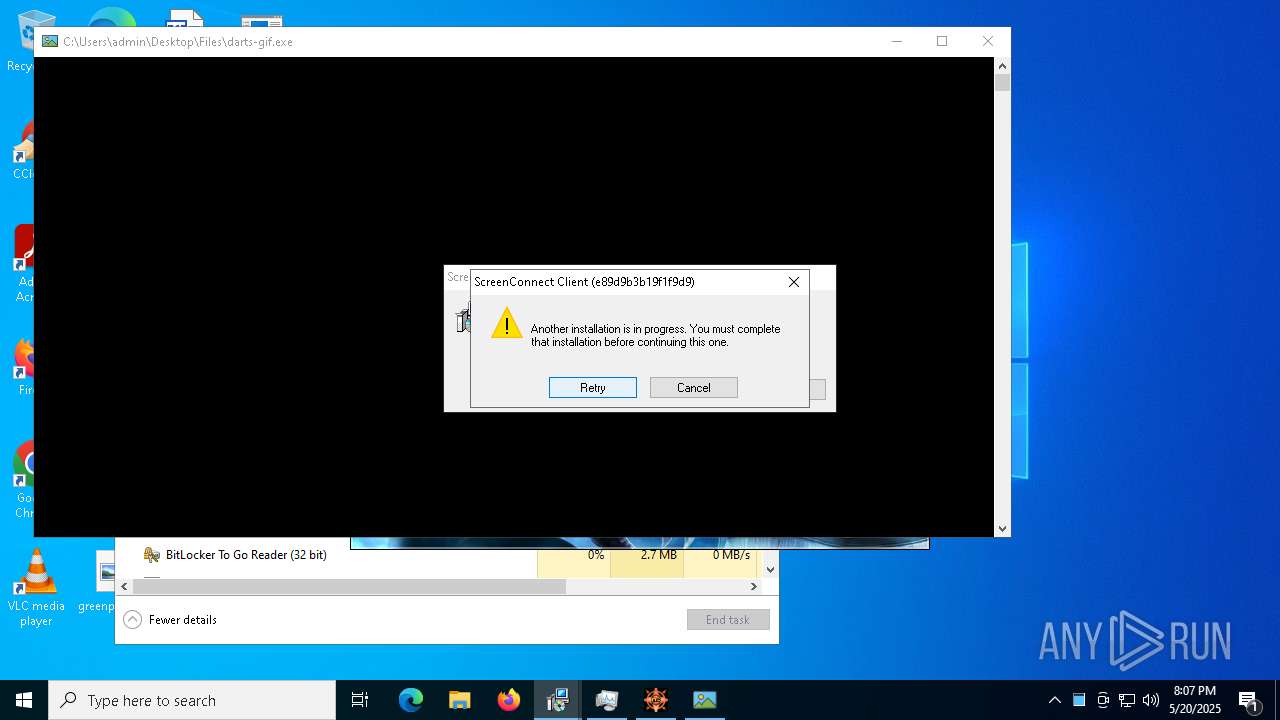
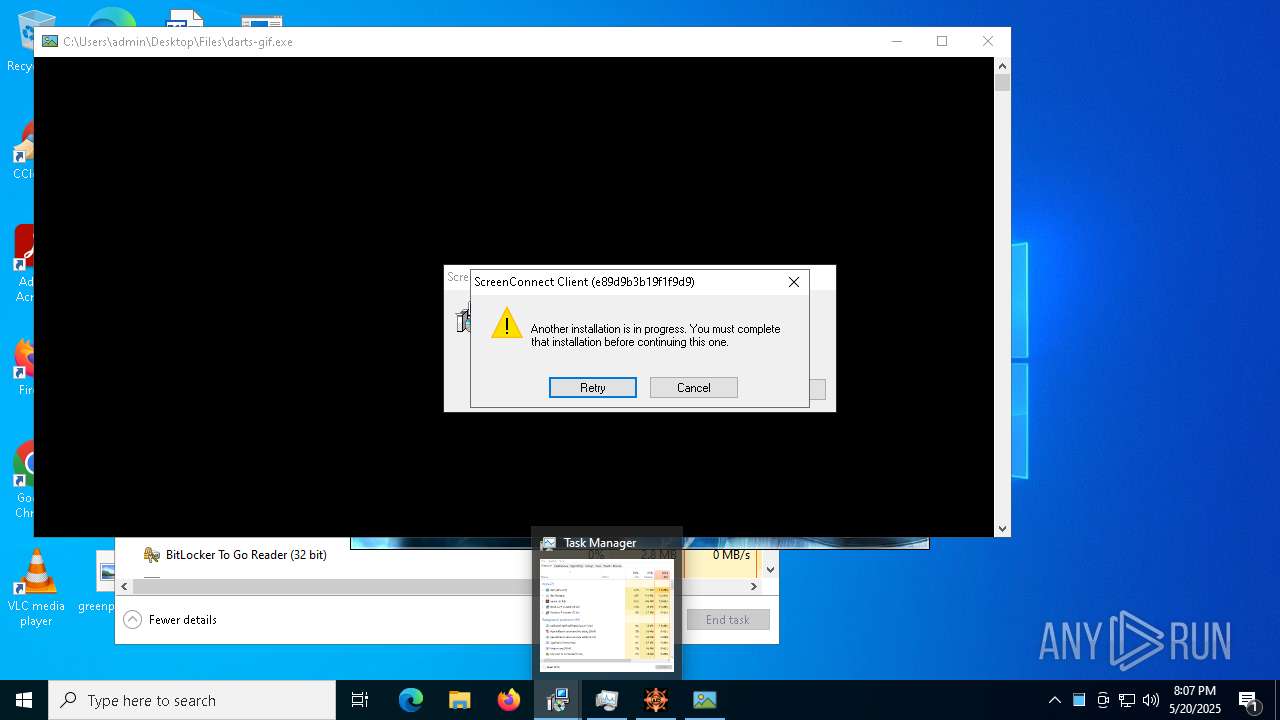
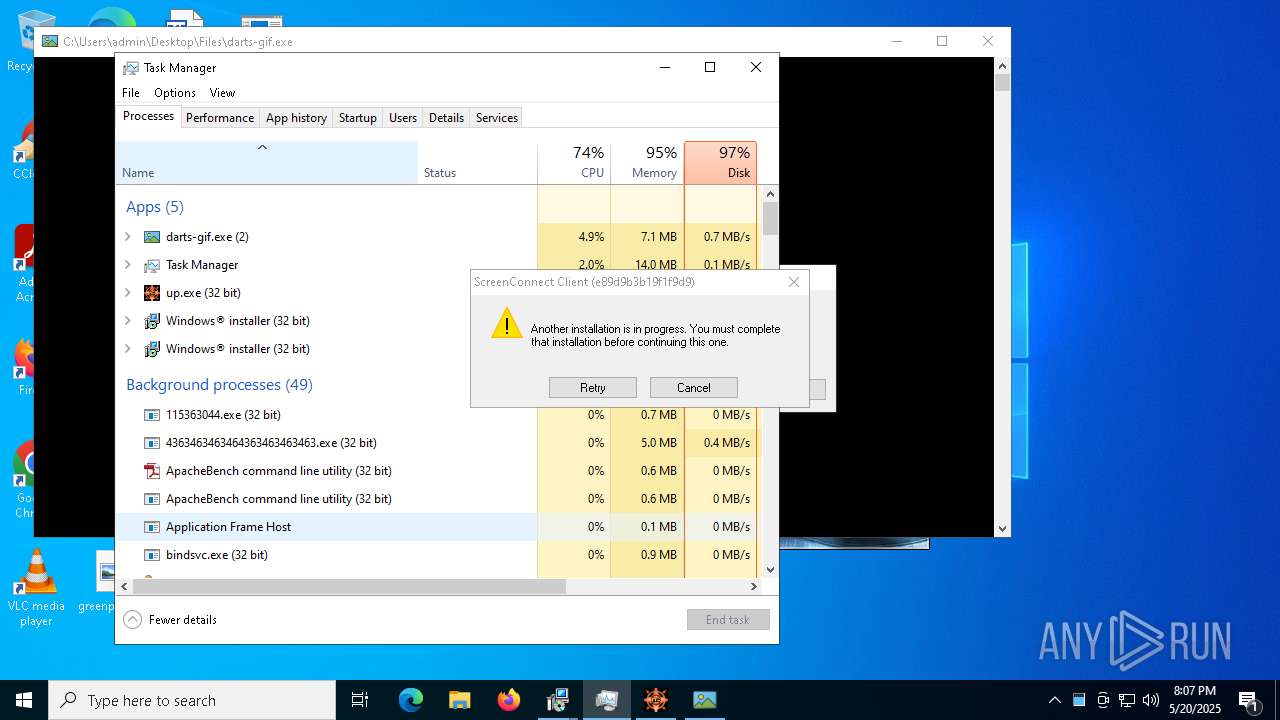
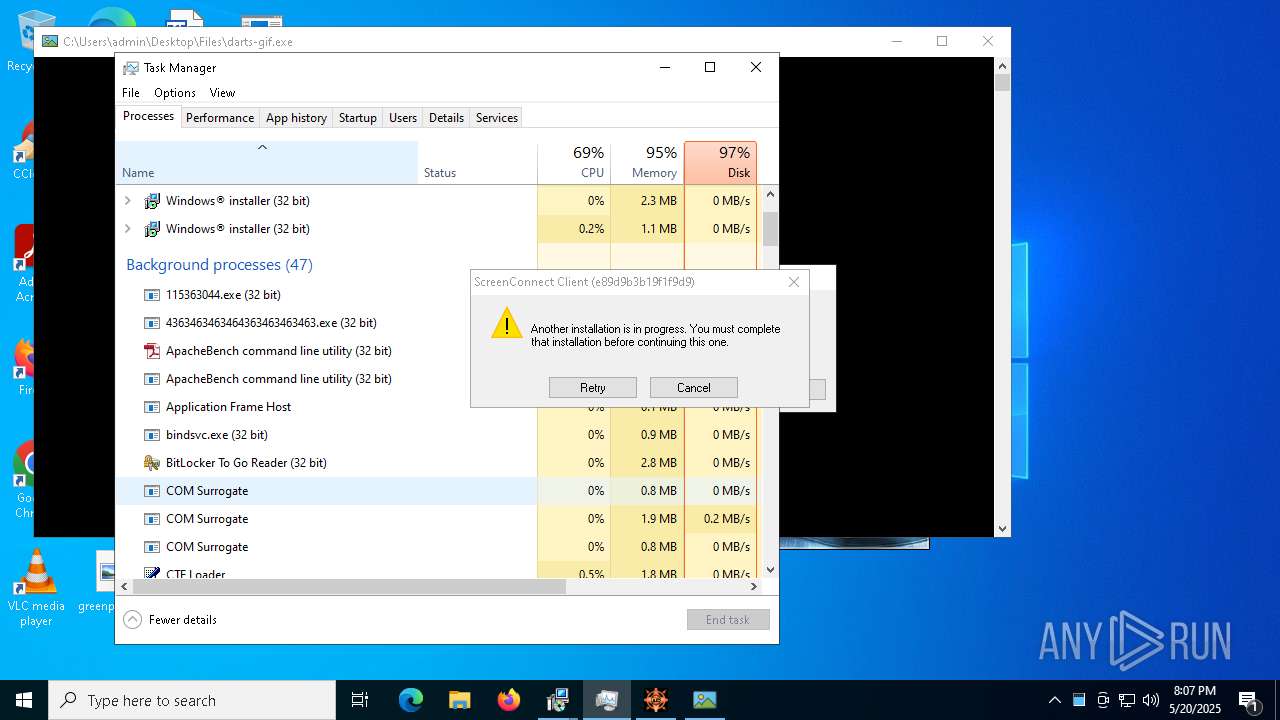
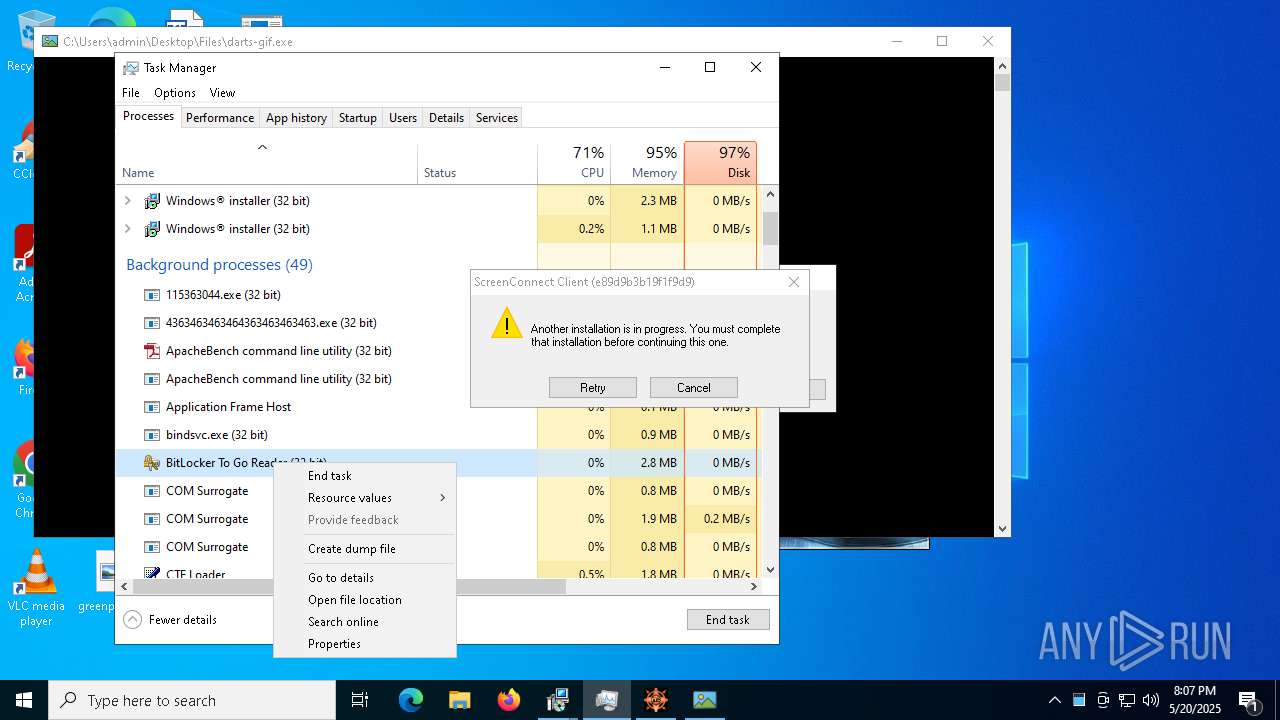
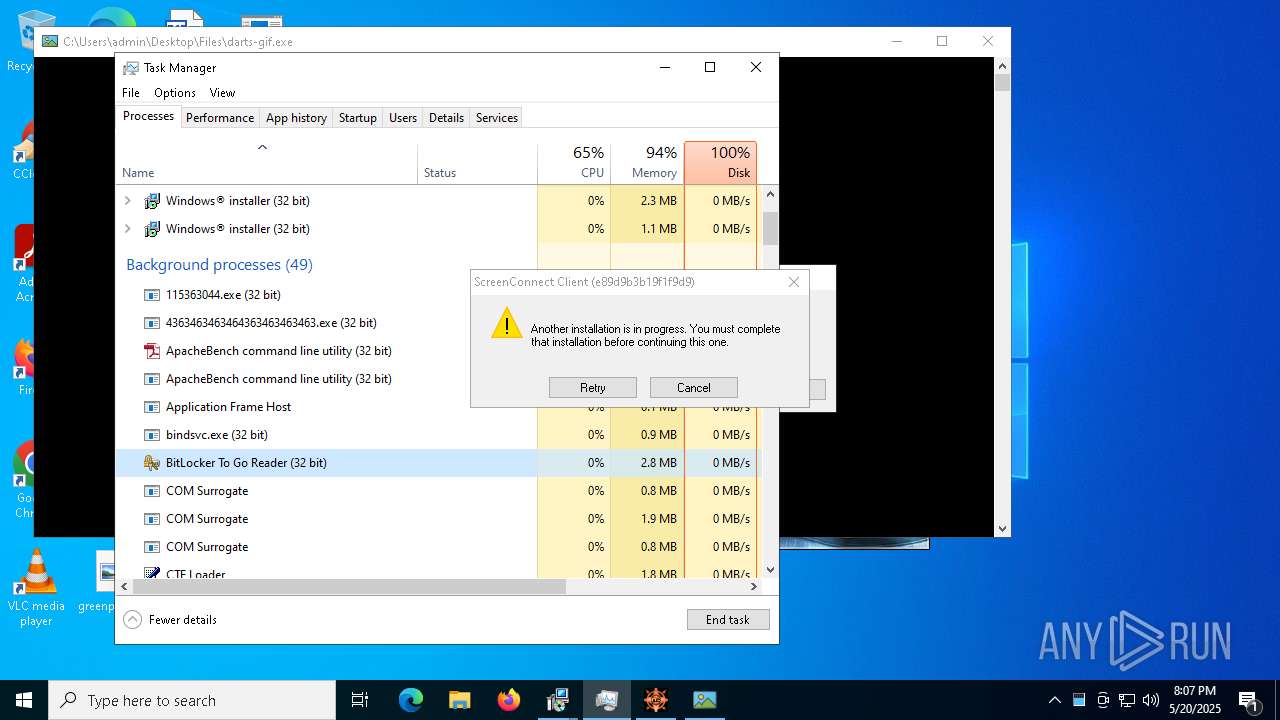
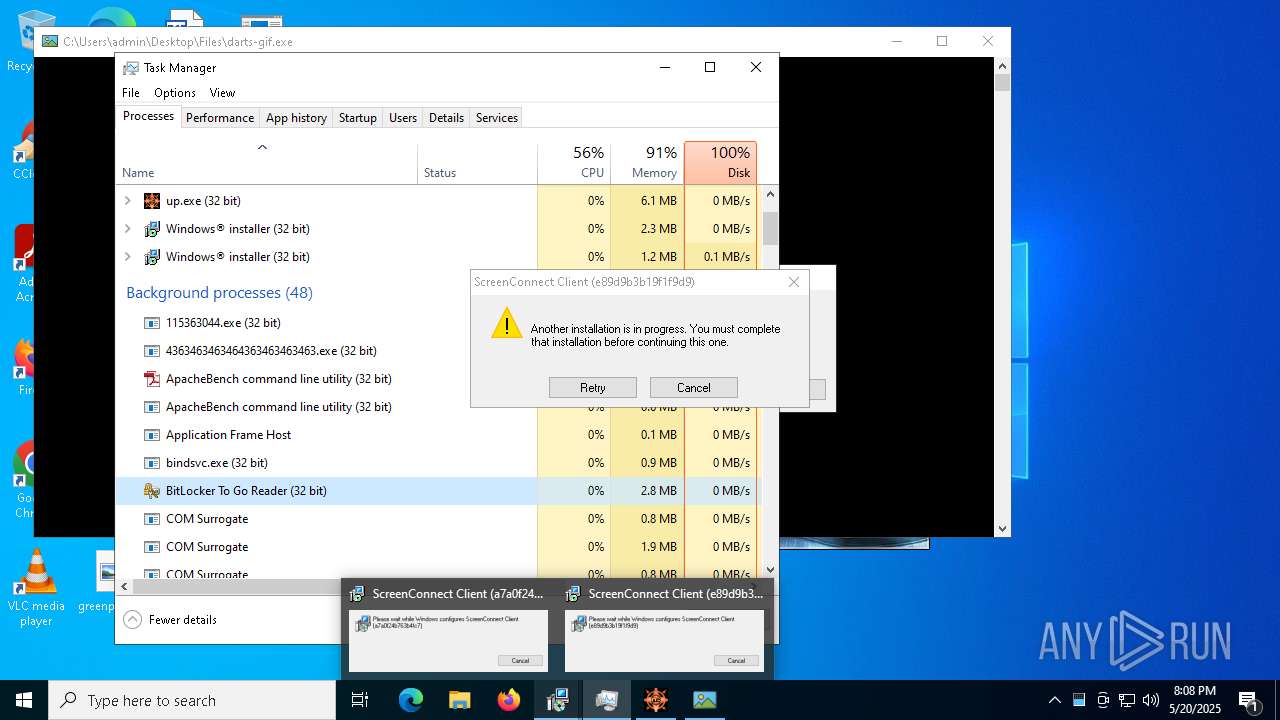
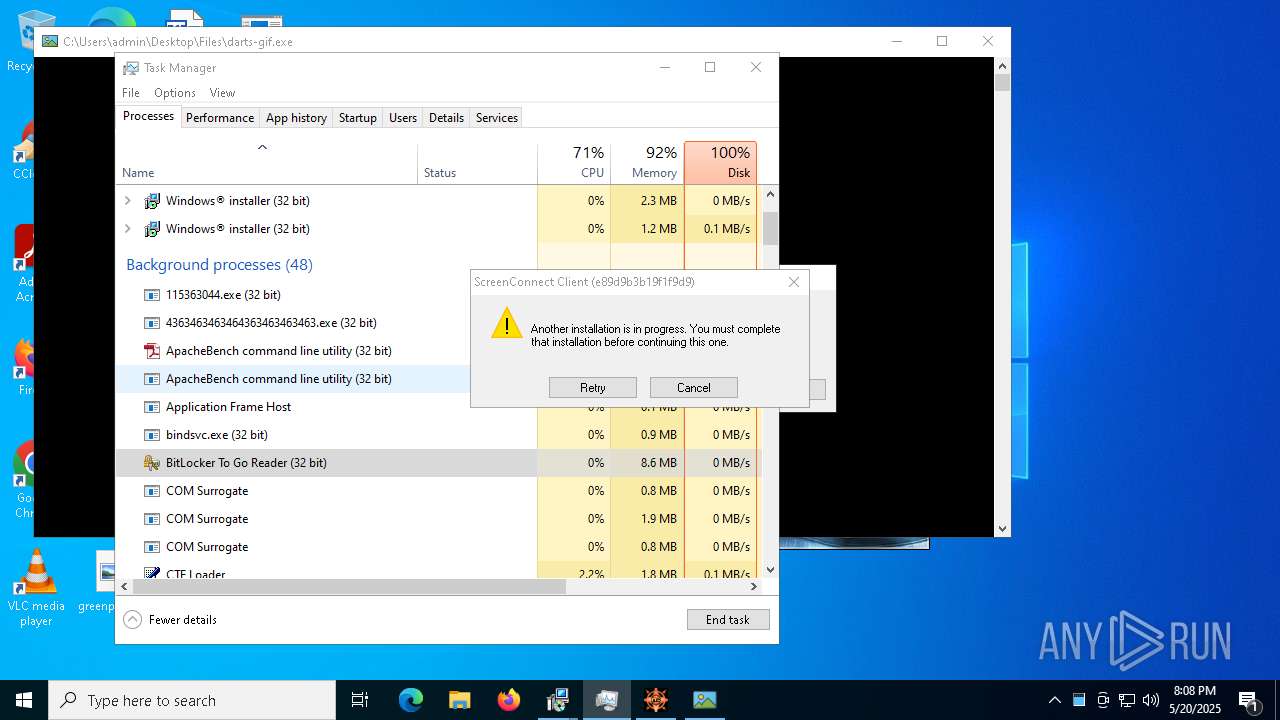
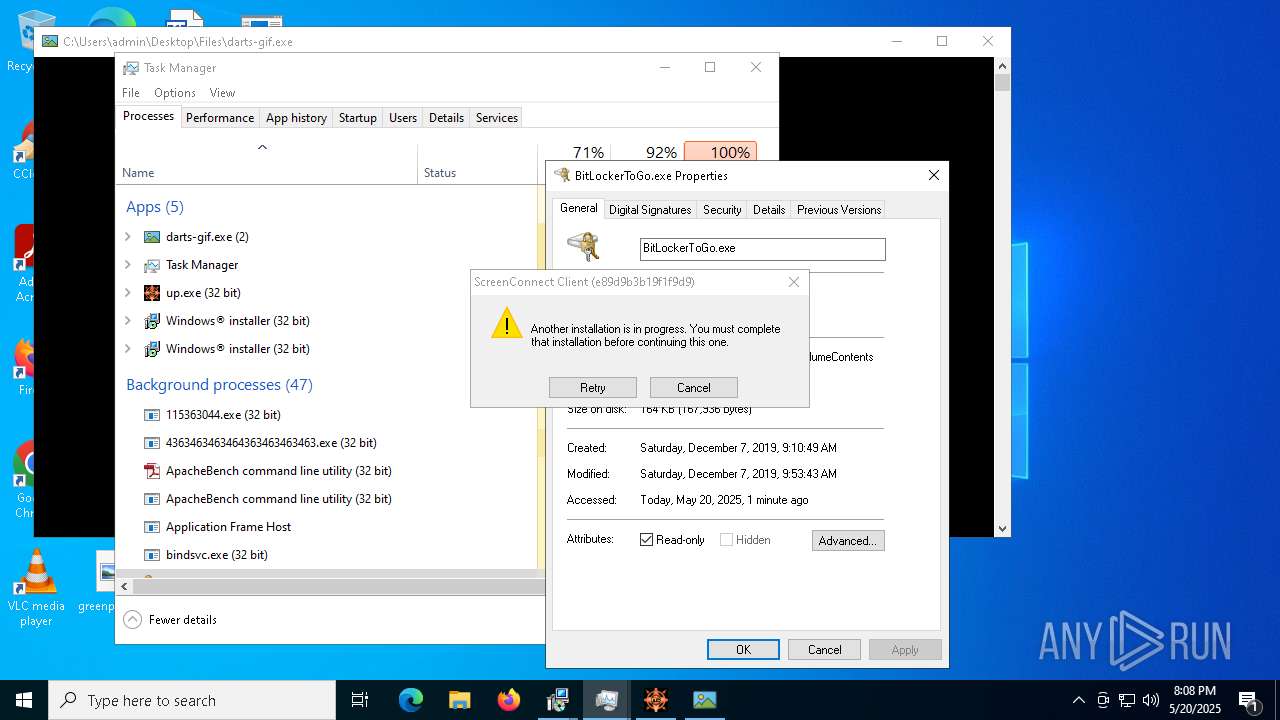
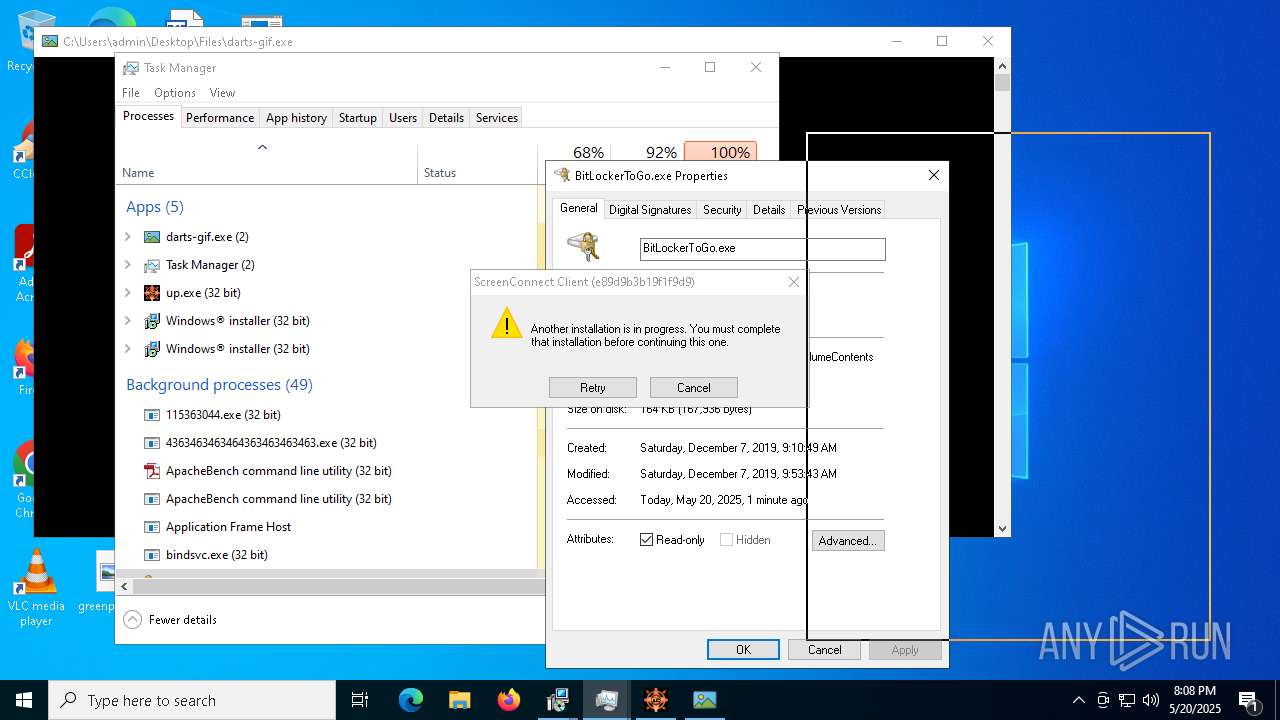
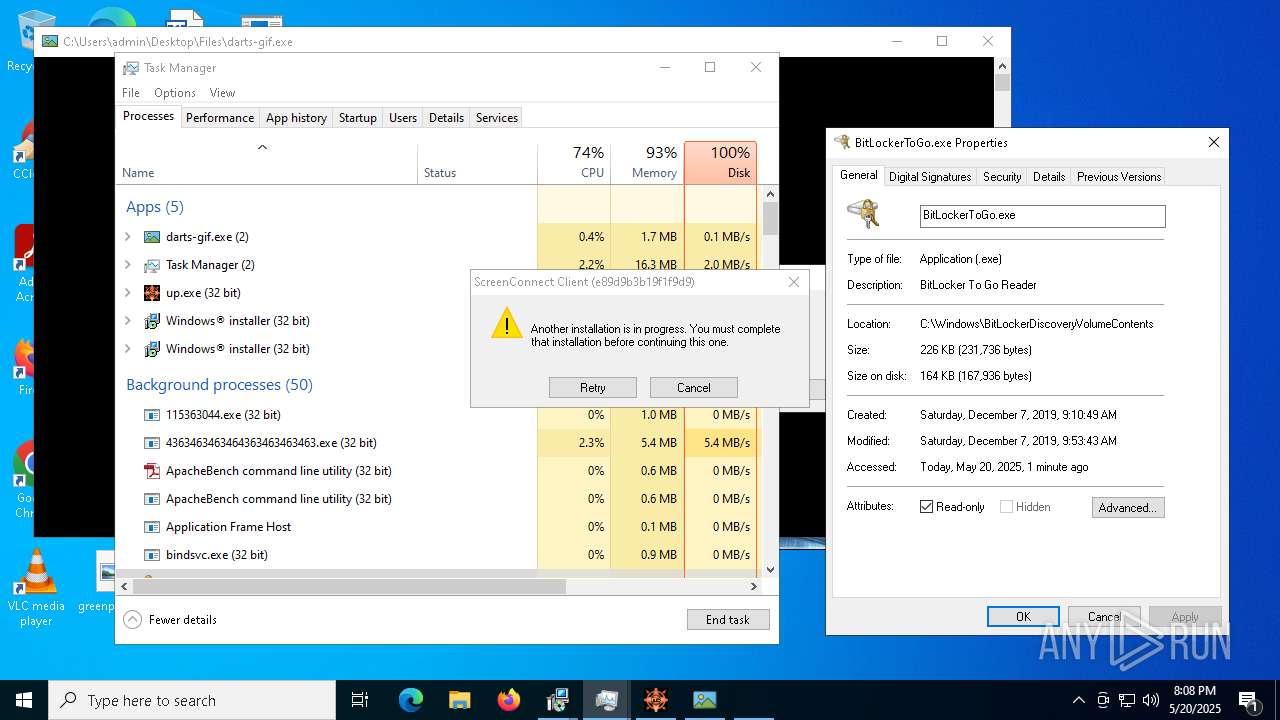
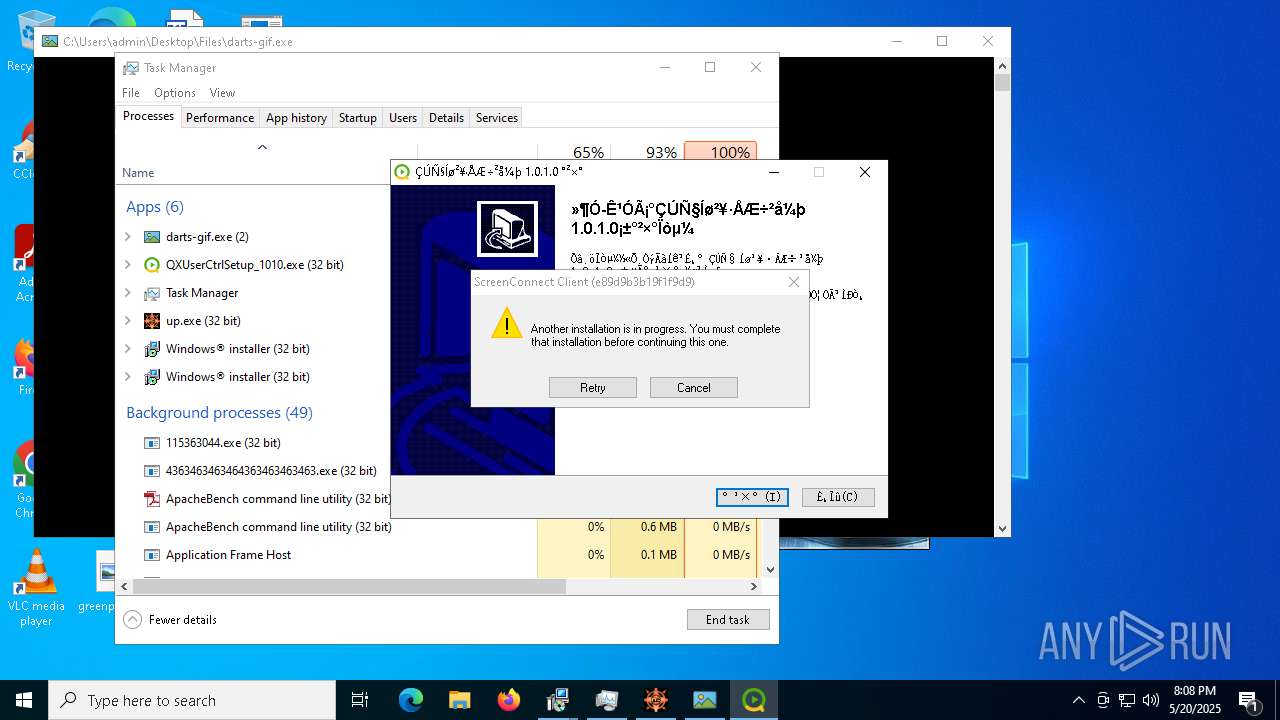
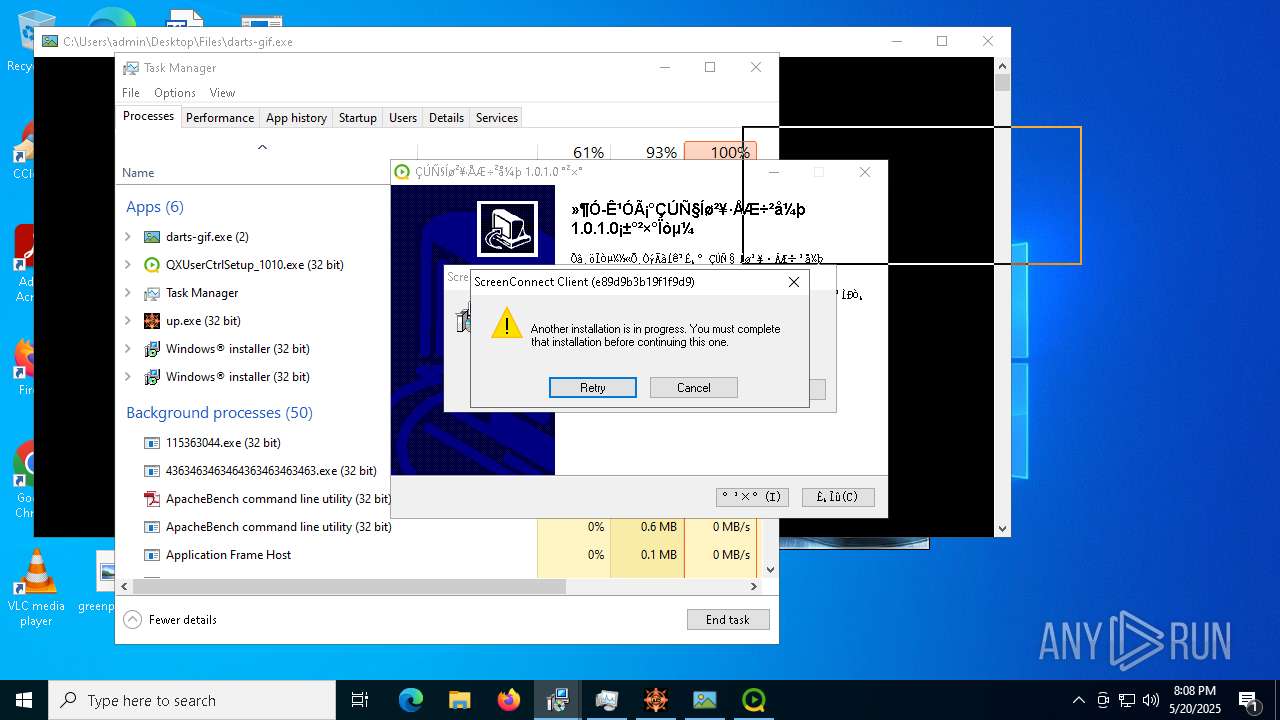
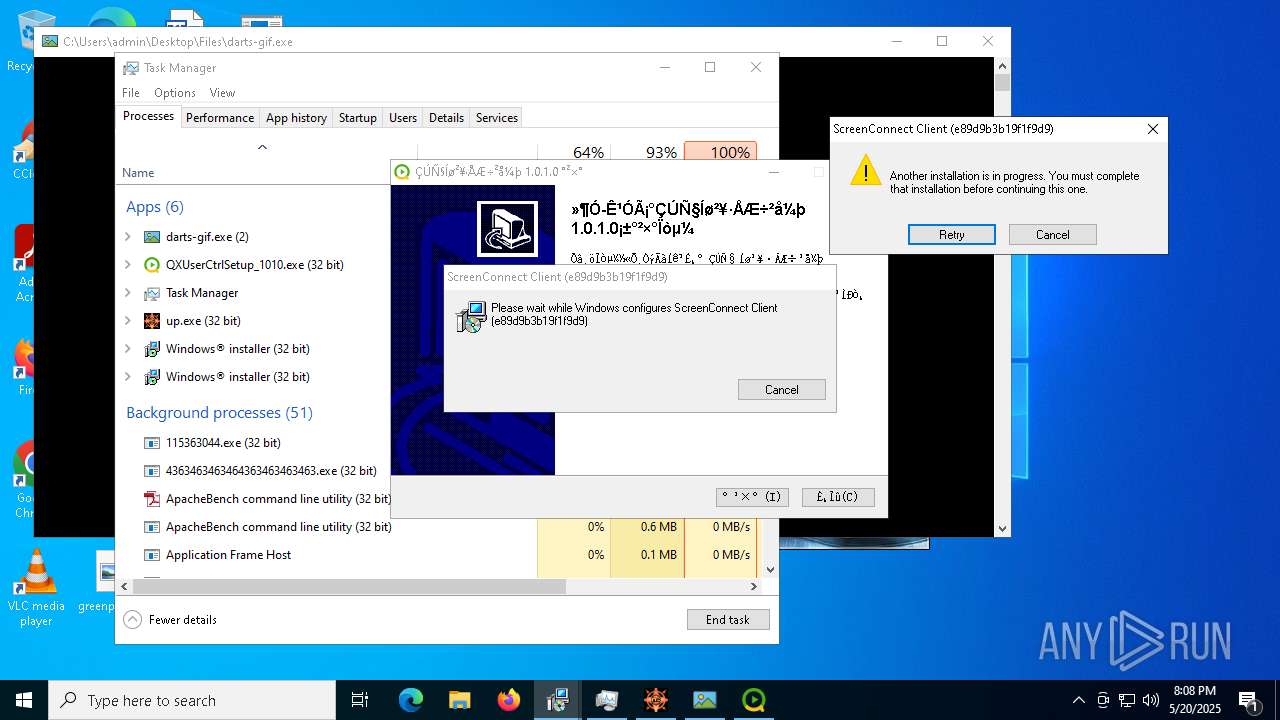
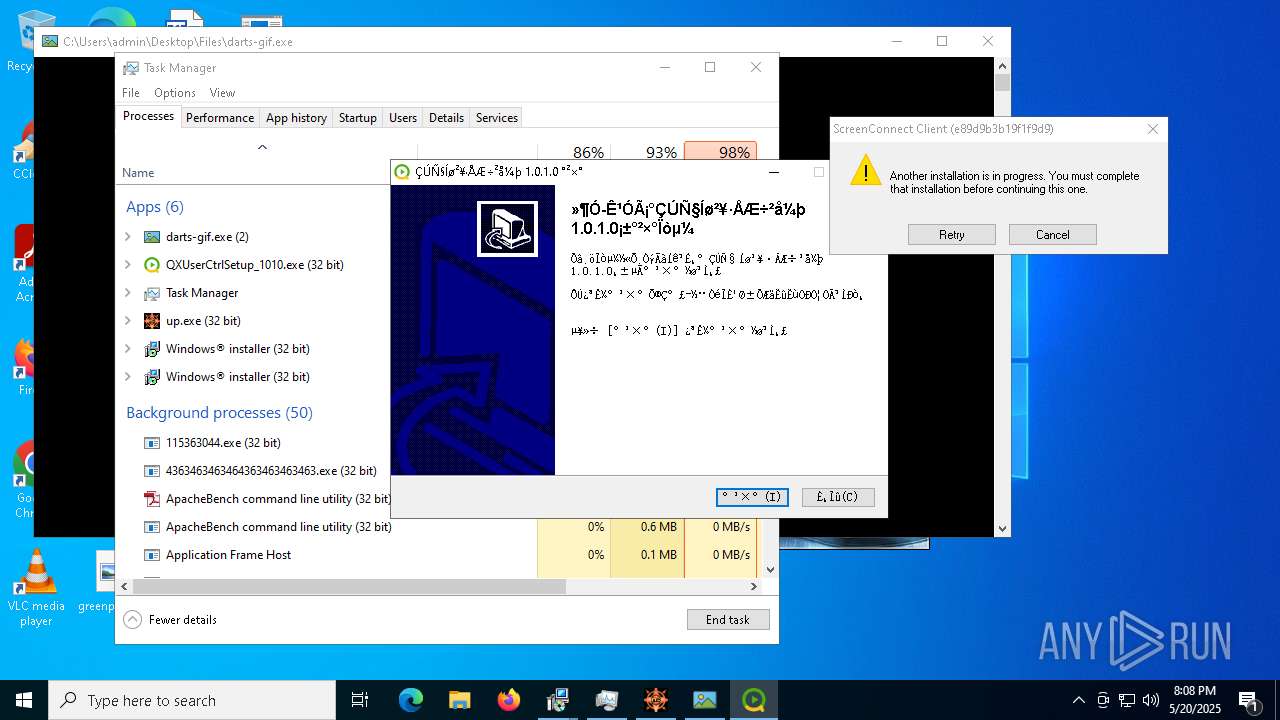
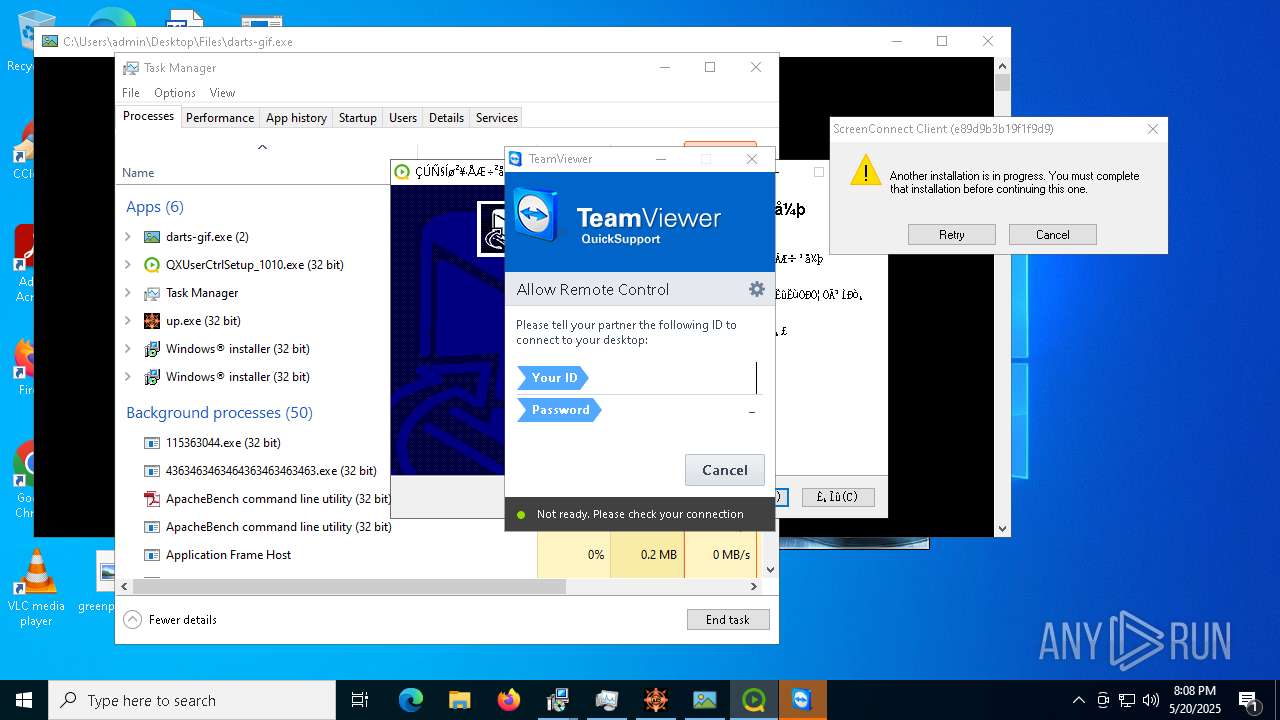
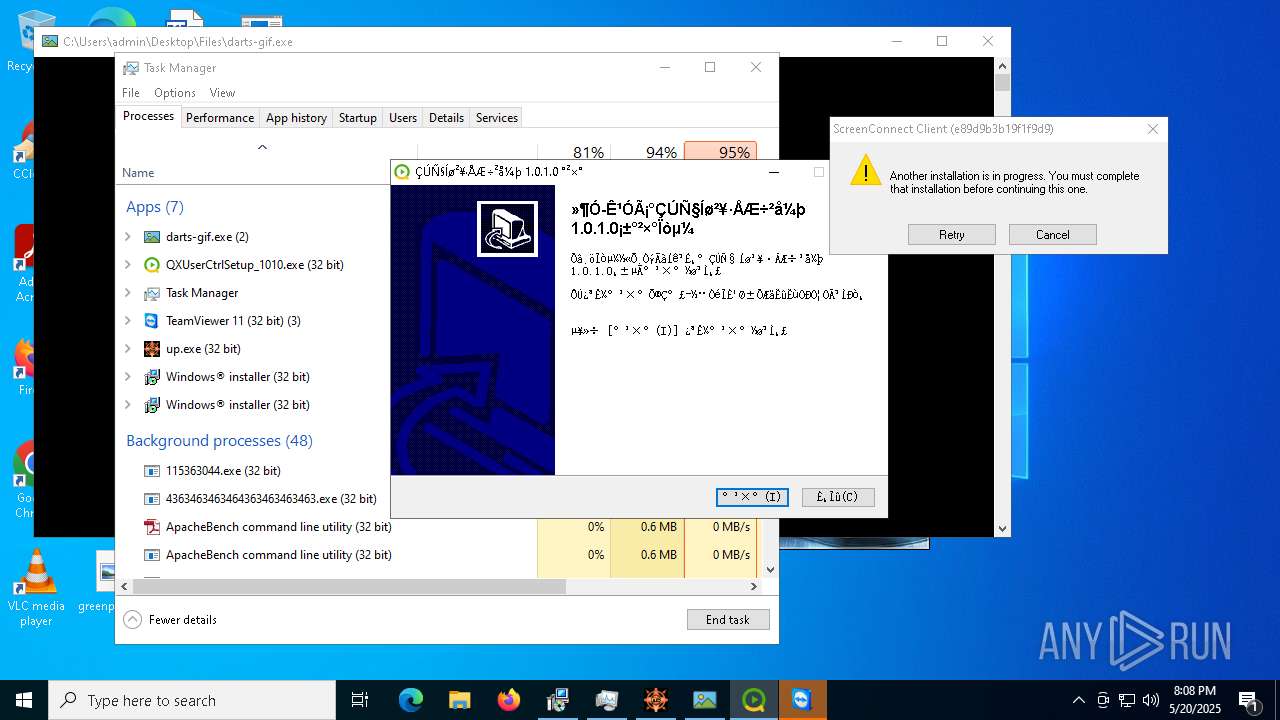
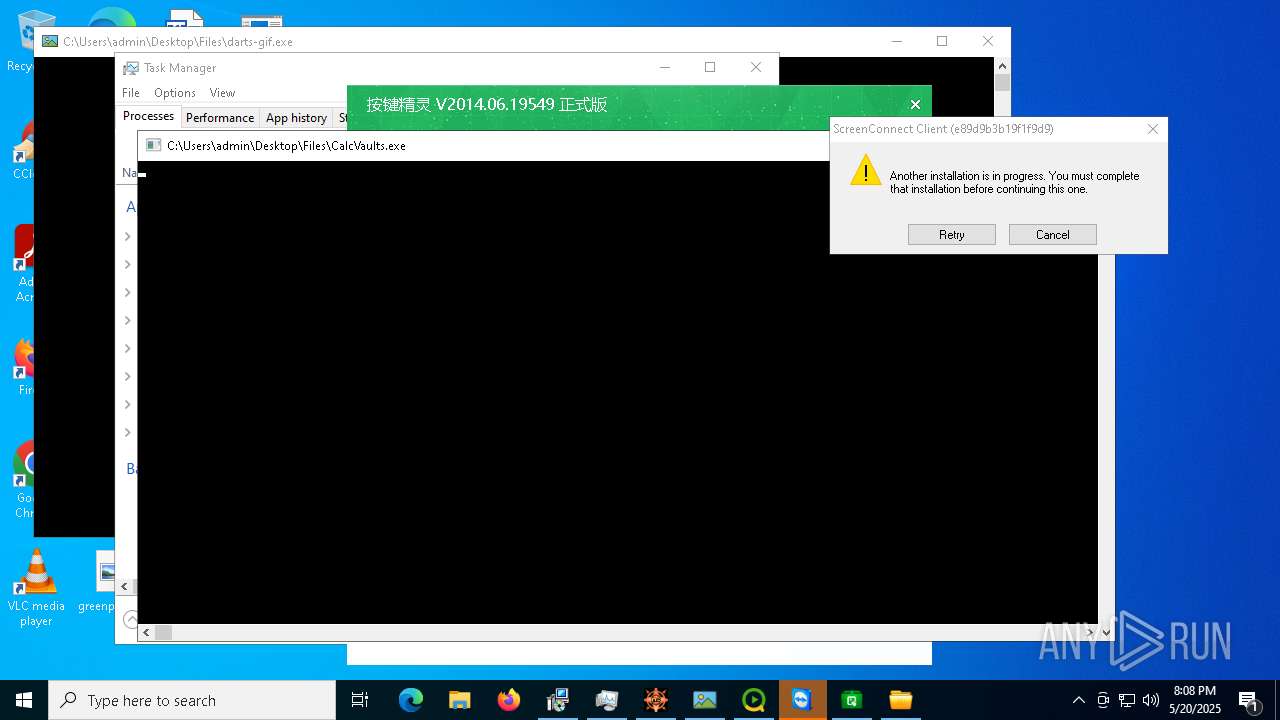
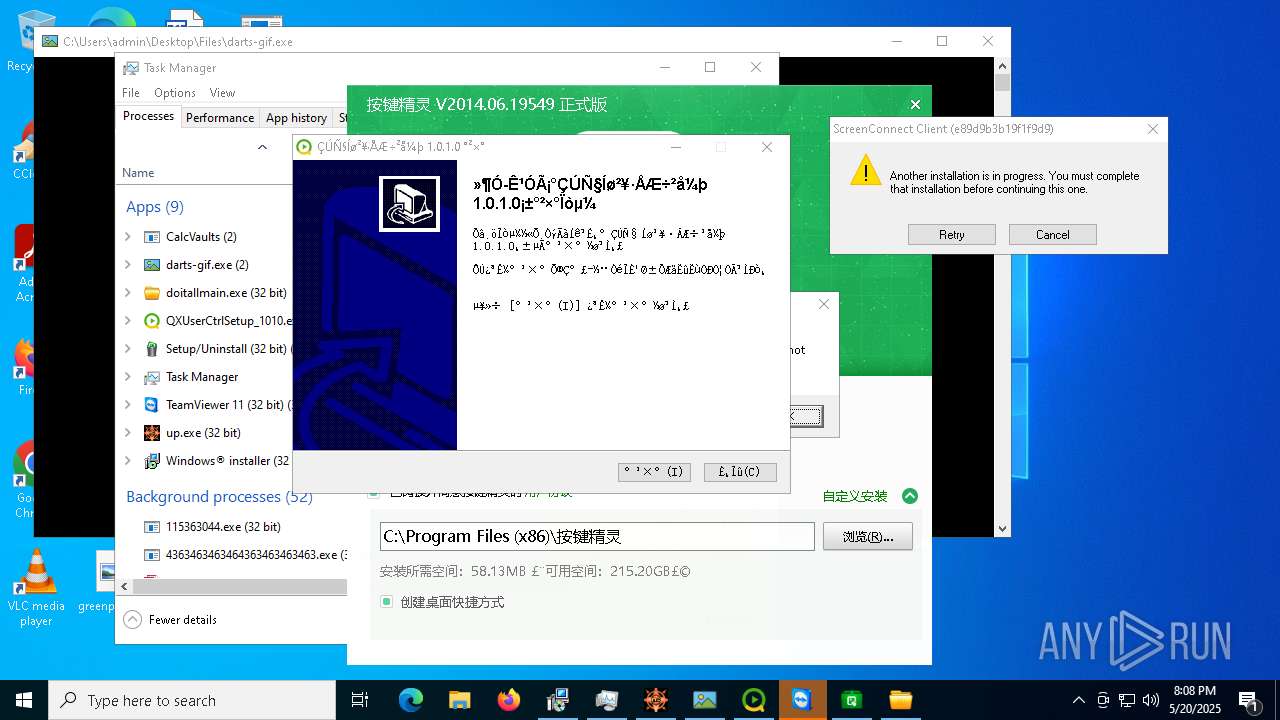
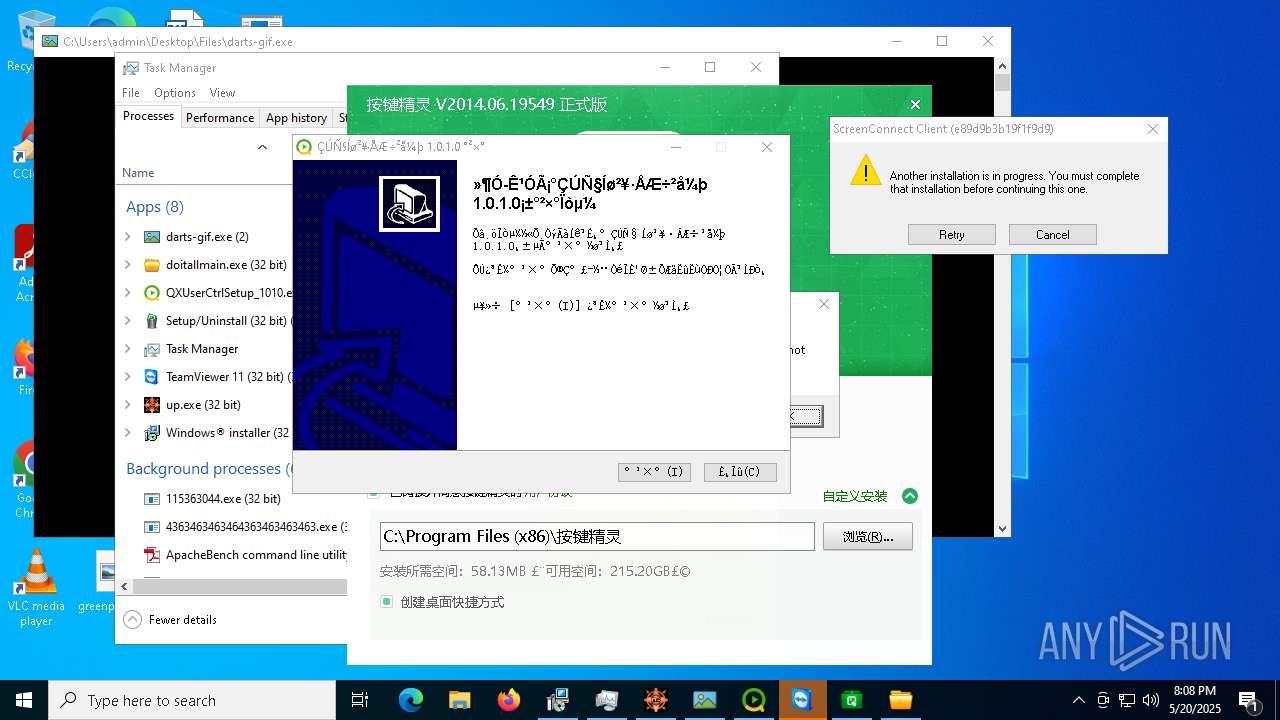
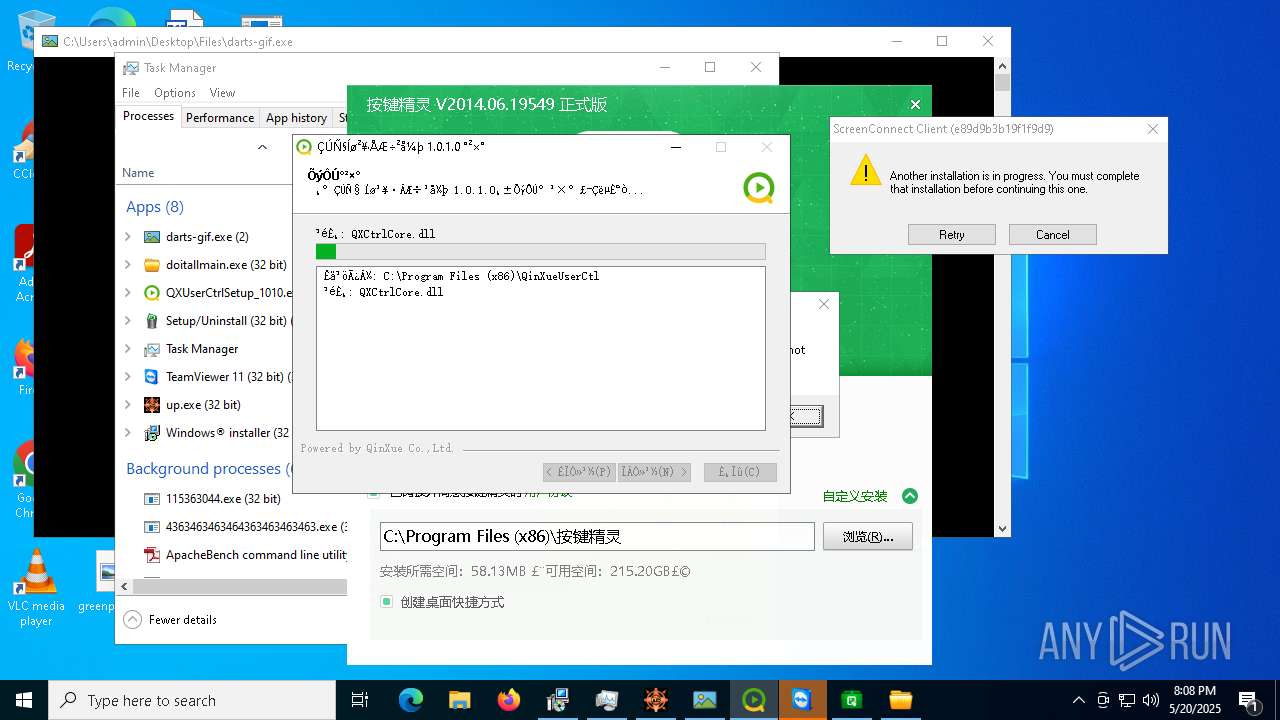
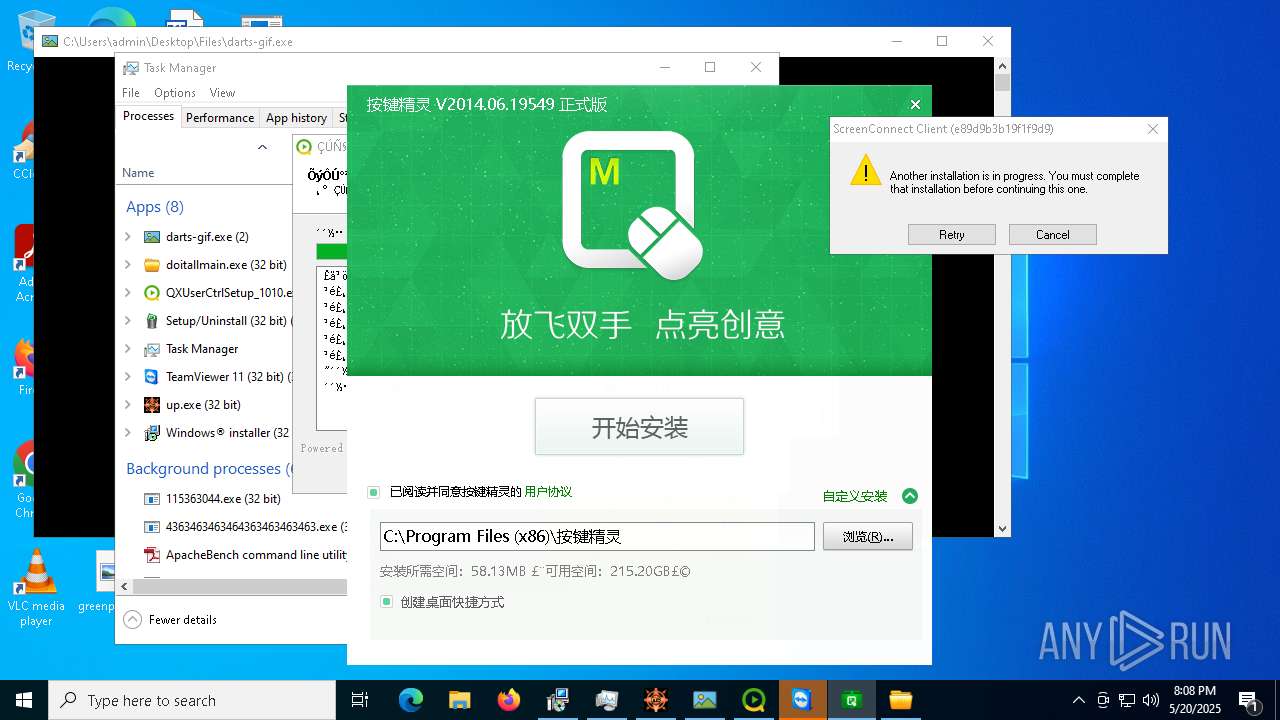
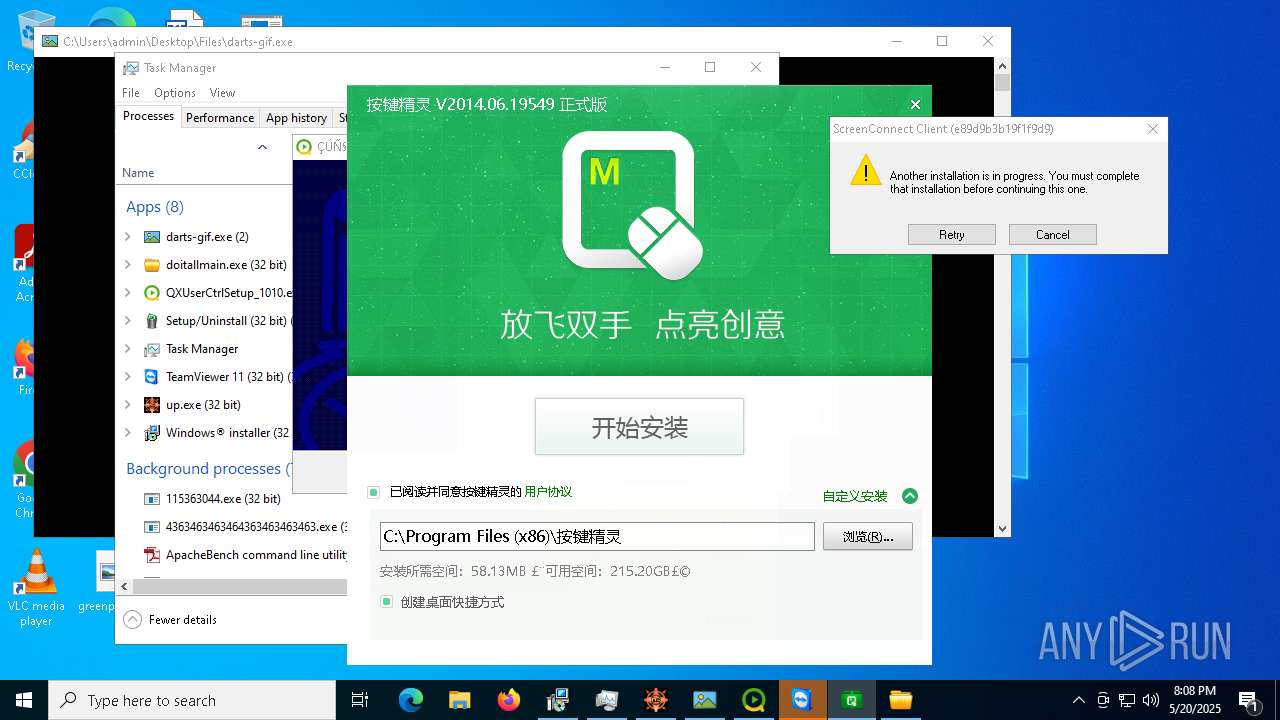
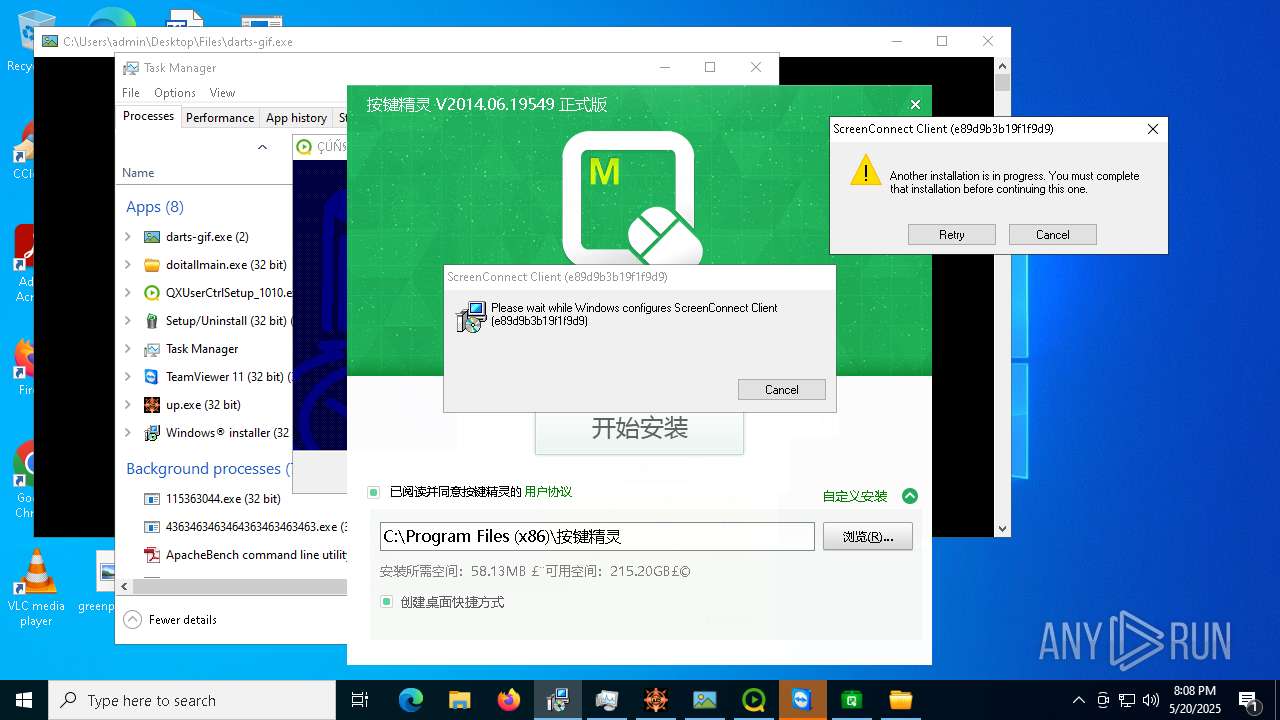
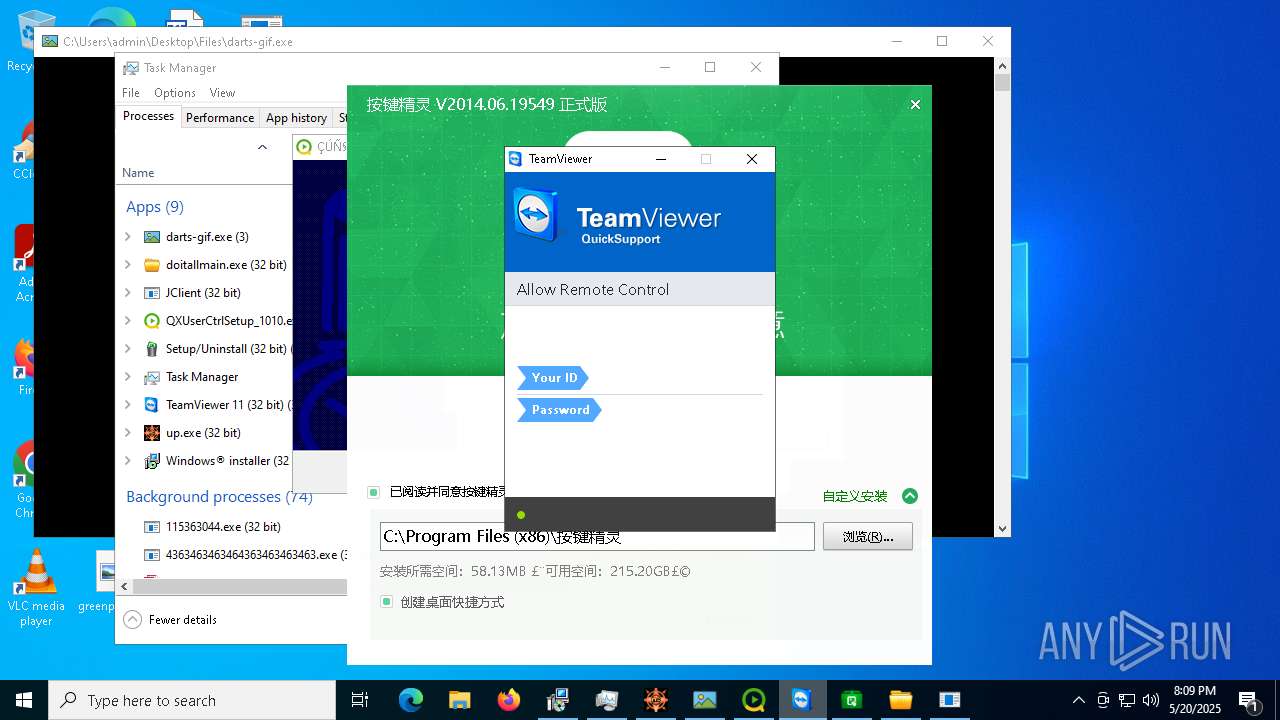
SCREENCONNECT has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
METASPLOIT has been detected (SURICATA)
- 4363463463464363463463463.exe (PID: 7528)
METASPLOIT has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
METERPRETER has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
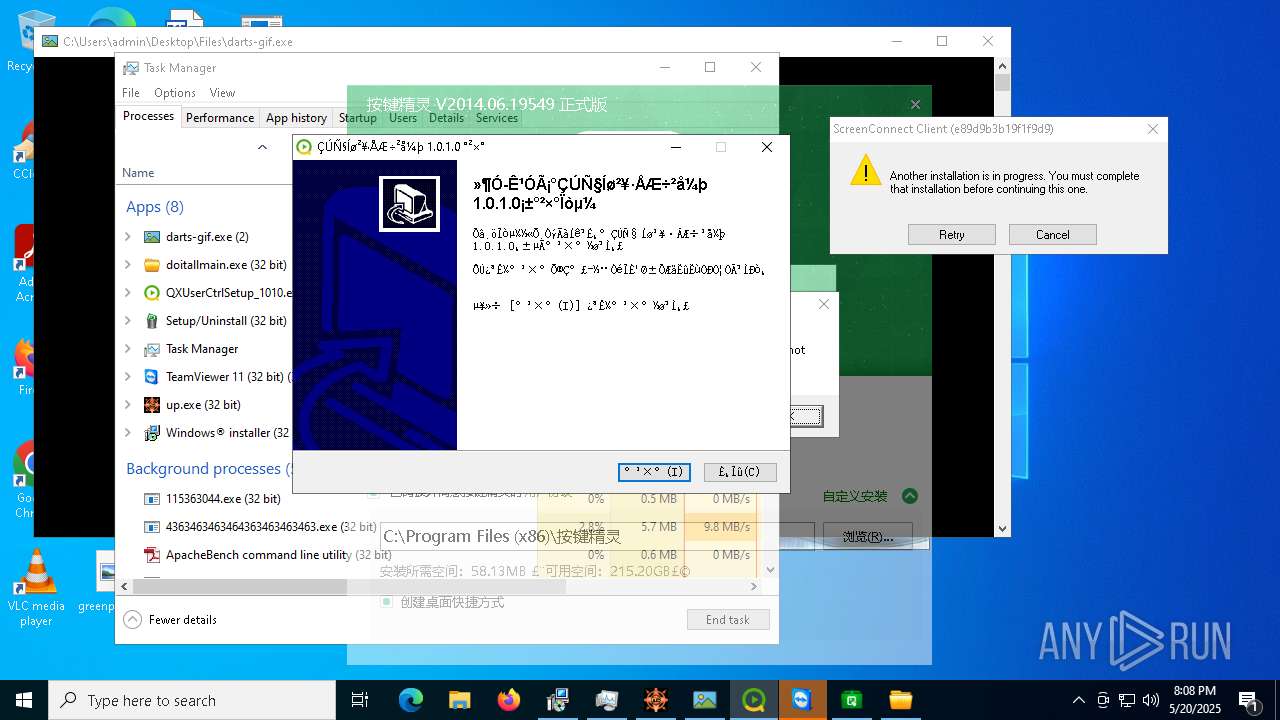
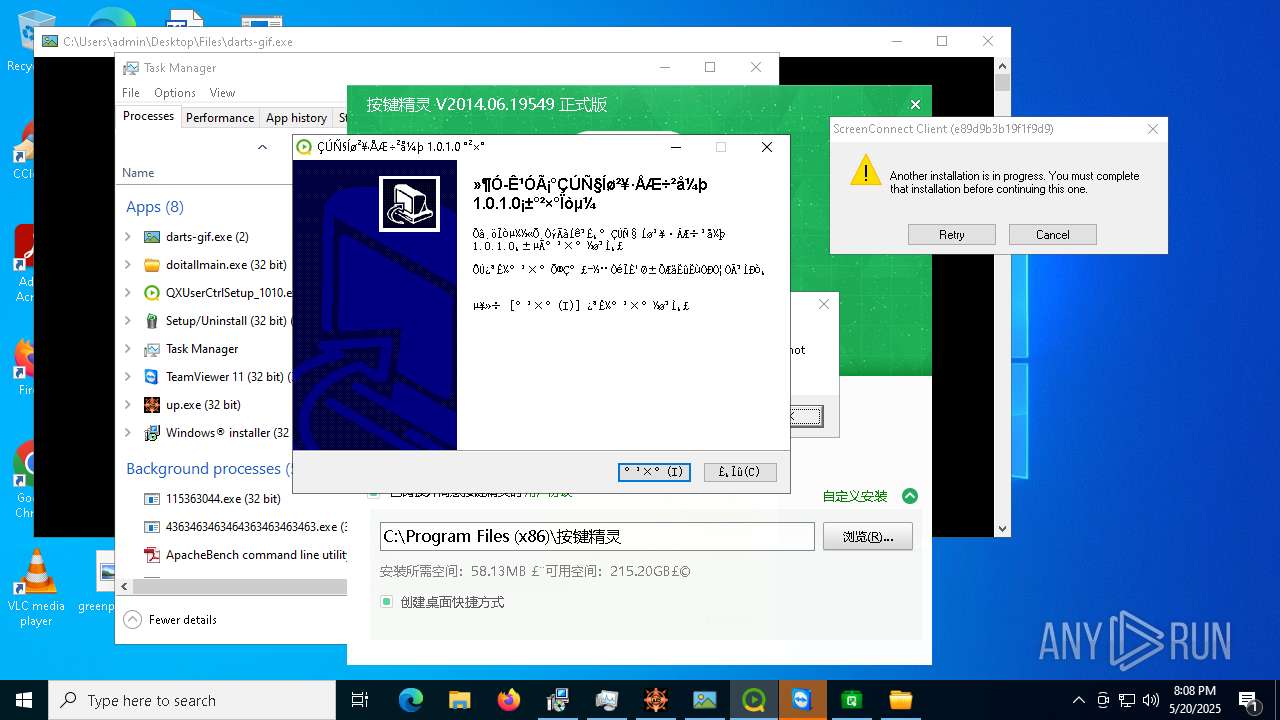
Uses Task Scheduler to autorun other applications
- RuntimeBroker.exe (PID: 2852)
- RuntimeBroker.exe (PID: 9752)
- installer.exe.exe (PID: 9888)
- Client.exe (PID: 9476)
- CollosalLoader.exe (PID: 6256)
- MSWinpreference.exe (PID: 10156)
- cmd.exe (PID: 12112)
PHORPIEX has been detected (SURICATA)
- syscrondvr.exe (PID: 9508)
QUASARRAT has been found (auto)
- installer.exe.exe (PID: 9888)
- 4363463463464363463463463.exe (PID: 7528)
- CollosalLoader.exe (PID: 6256)
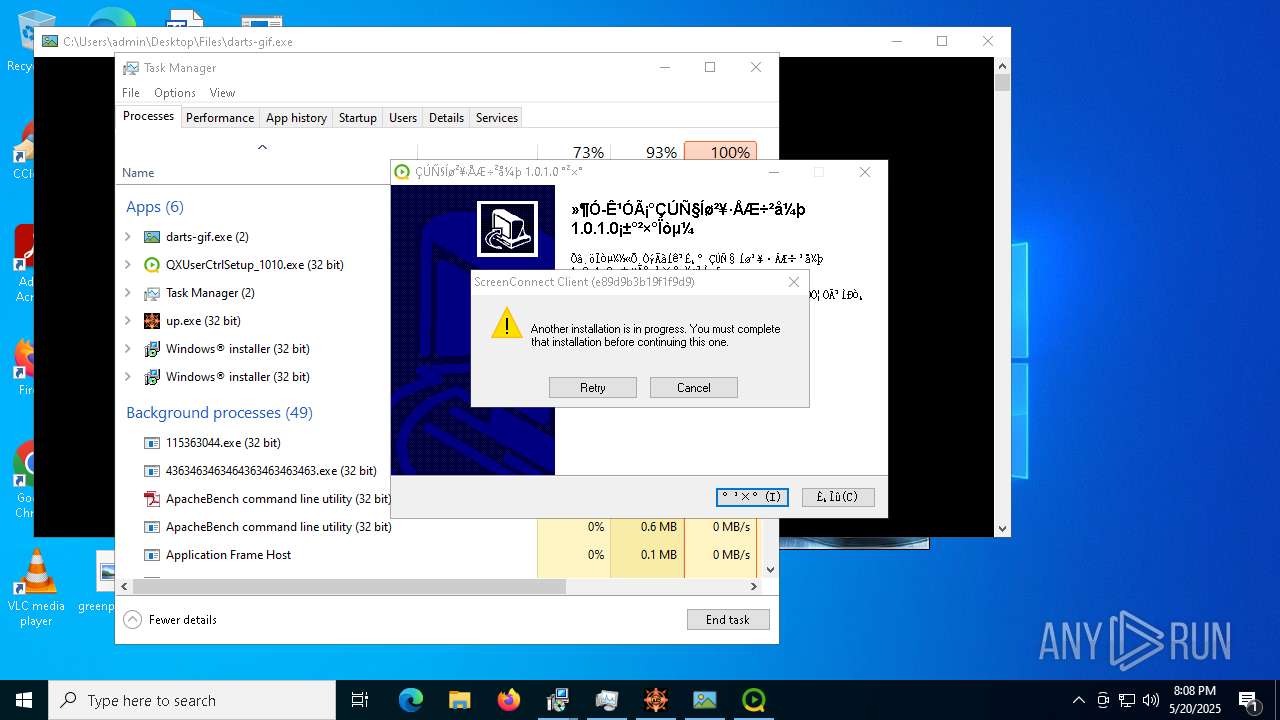
Executing a file with an untrusted certificate
- BQ4m0sD.exe (PID: 10072)
- QXUserCtrlSetup_1010.exe (PID: 928)
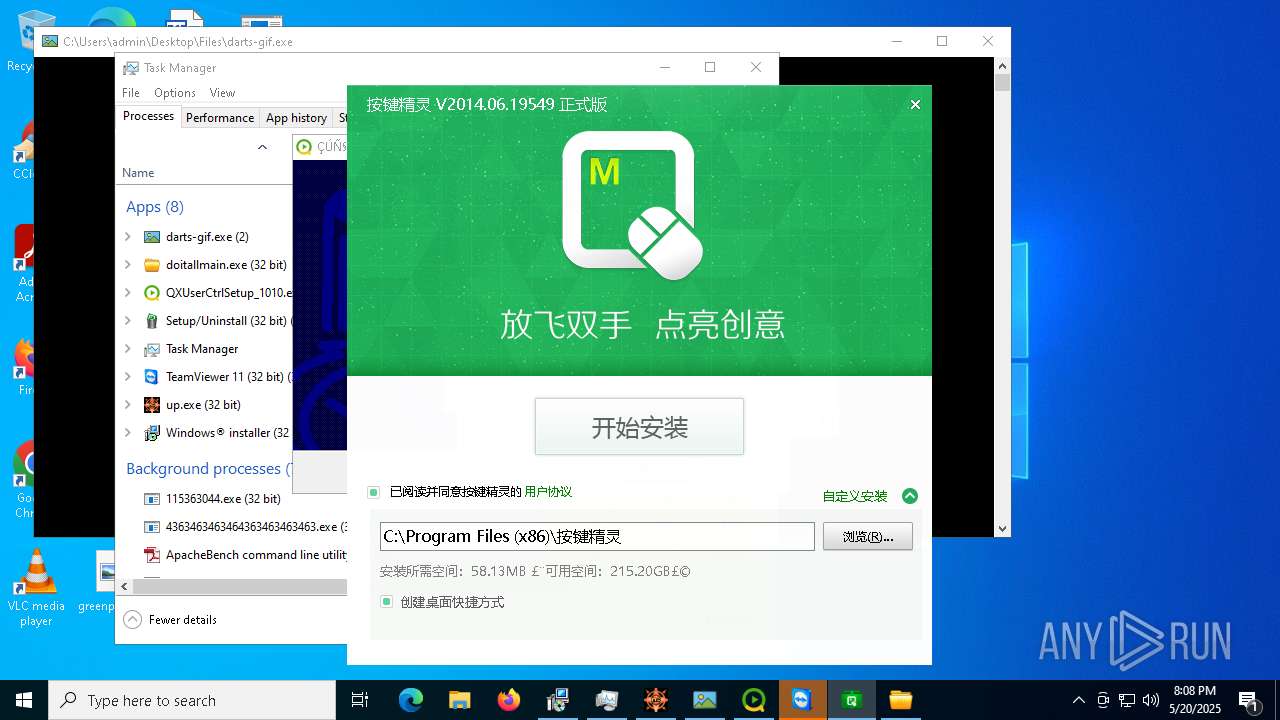
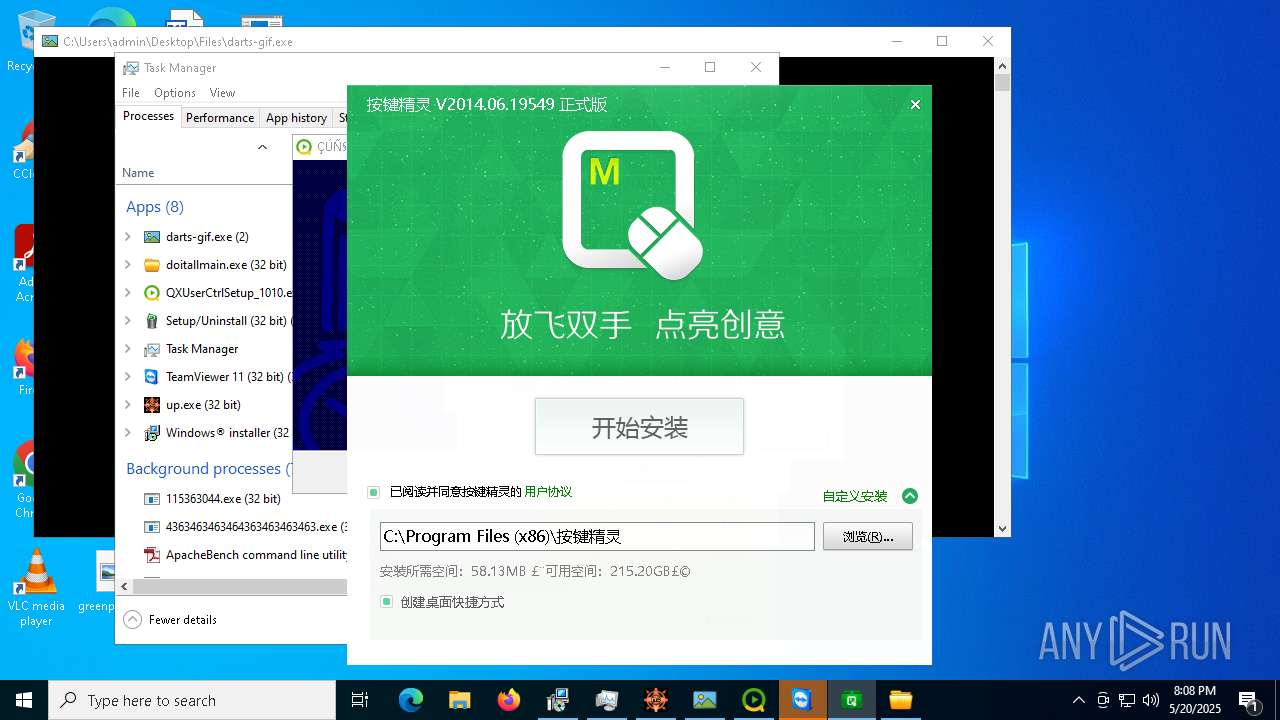
TEAMVIEWER has been detected (SURICATA)
- svchost.exe (PID: 2196)
- TeamViewer.exe (PID: 9296)
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6668)
RAT has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
- WinPlugins.exe (PID: 10456)
- 4363463463464363463463463.exe (PID: 7528)
Adds path to the Windows Defender exclusion list
- cheese.exe (PID: 10400)
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Changes Windows Defender settings
- cheese.exe (PID: 10400)
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
NJRAT has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
- Server.exe (PID: 11484)
ASYNCRAT has been found (auto)
- Krishna33.exe (PID: 10552)
Starts NET.EXE for service management
- net.exe (PID: 11436)
- net.exe (PID: 12052)
- cmd.exe (PID: 10556)
LUMMA has been found (auto)
- 4363463463464363463463463.exe (PID: 7528)
Adds process to the Windows Defender exclusion list
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Adds extension to the Windows Defender exclusion list
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Stealers network behavior
- svchost.exe (PID: 2196)
SUSPICIOUS
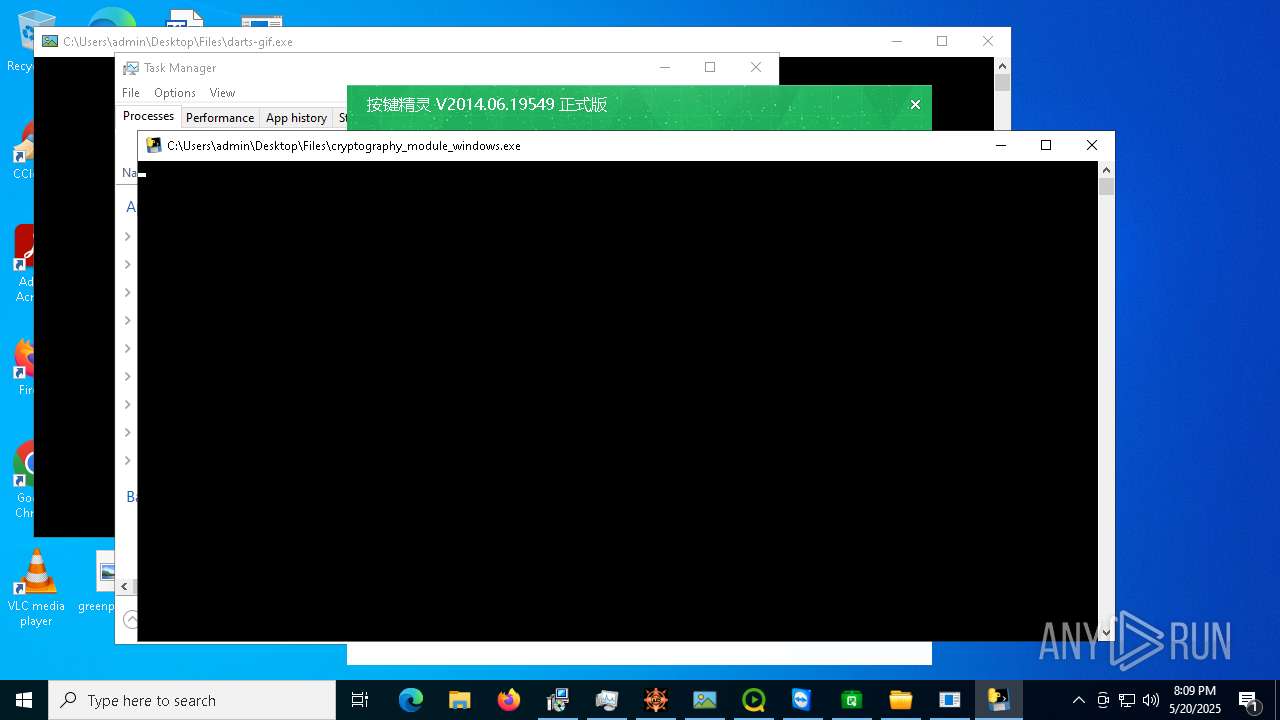
Executable content was dropped or overwritten
- 4363463463464363463463463.exe (PID: 7528)
- update.exe (PID: 496)
- icxtcyndmh.exe (PID: 7408)
- loader.exe (PID: 1164)
- rhsgn_protected.exe (PID: 5608)
- ARA.exe (PID: 6192)
- update.exe (PID: 2616)
- Msblockreview.exe (PID: 7380)
- x.exe (PID: 6208)
- sysmtdrav.exe (PID: 2084)
- gold.rim.exe (PID: 2596)
- javaw.exe (PID: 8624)
- rundll32.exe (PID: 1660)
- rundll32.exe (PID: 5576)
- cmd.exe (PID: 9552)
- newtpp.exe (PID: 9276)
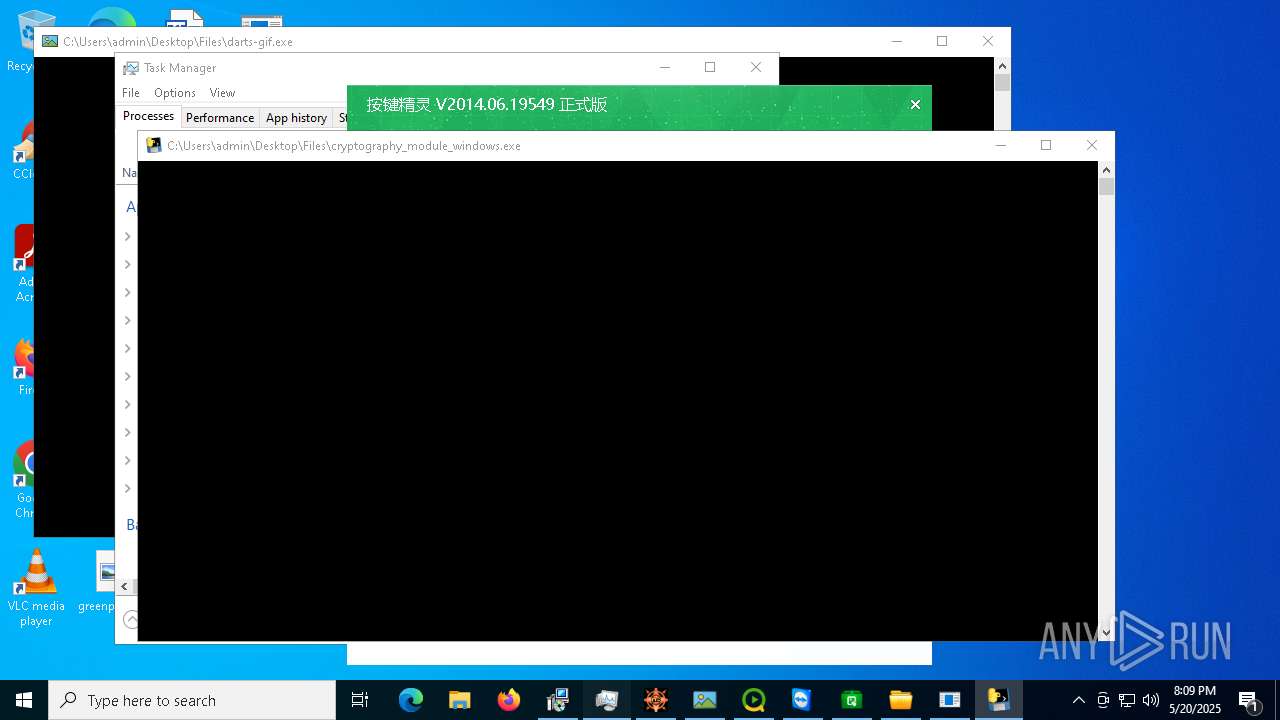
- darts-gif.exe (PID: 9684)
- installer.exe.exe (PID: 9888)
- RuntimeBroker.exe (PID: 9752)
- viewpoint_support.exe (PID: 9420)
- QXUserCtrlSetup_1010.exe (PID: 928)
- CollosalLoader.exe (PID: 6256)
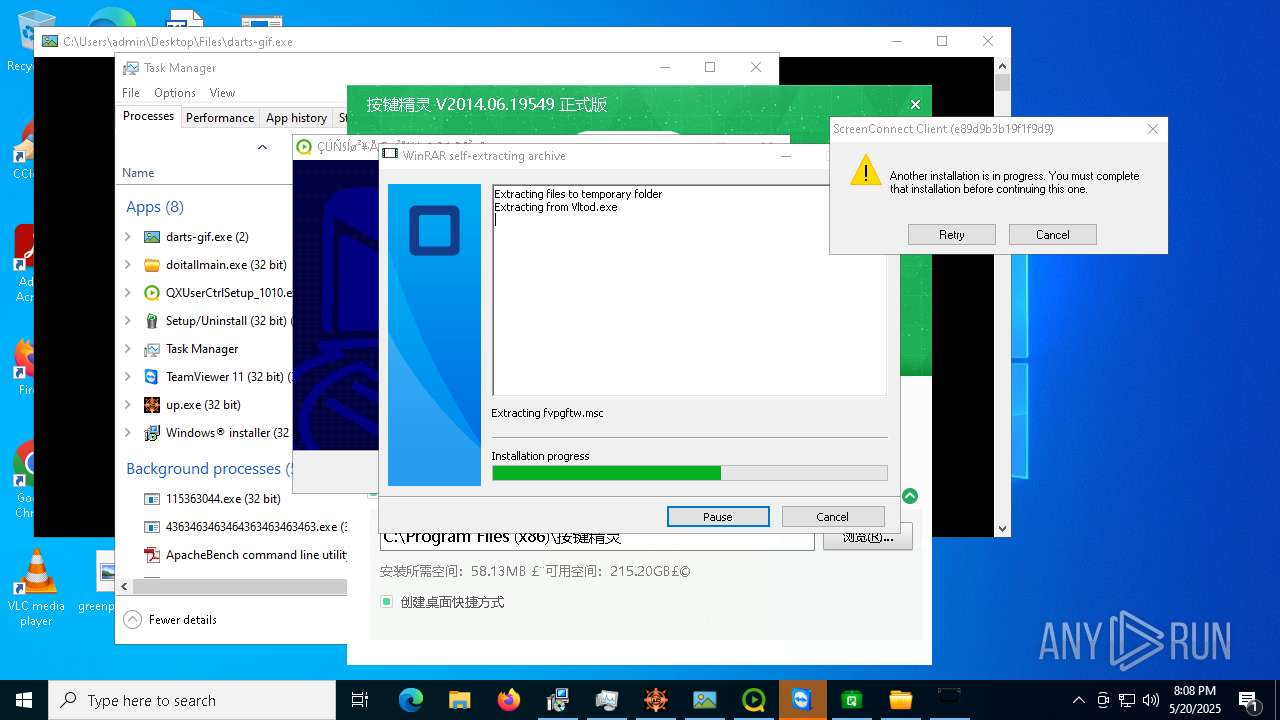
- qm2014chs.exe (PID: 4180)
- qm2014chs.tmp (PID: 6820)
- ServerX.exe (PID: 10304)
- WinPlugins.exe (PID: 10456)
- XLtod.exe (PID: 10748)
- Vltod.exe (PID: 10740)
- server.exe (PID: 10568)
- tb.exe (PID: 10956)
- rtsf.exe (PID: 10724)
- Krishna33.exe (PID: 10552)
- Server.exe (PID: 11484)
- cryptography_module_windows.exe (PID: 11824)
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 7528)
- update.exe (PID: 496)
- loader.exe (PID: 1164)
- obdkbemdem.exe (PID: 7144)
- ARA.exe (PID: 6192)
- update.exe (PID: 2616)
- rhsgn_protected.exe (PID: 5608)
- Msblockreview.exe (PID: 7380)
- ShellExperienceHost.exe (PID: 5800)
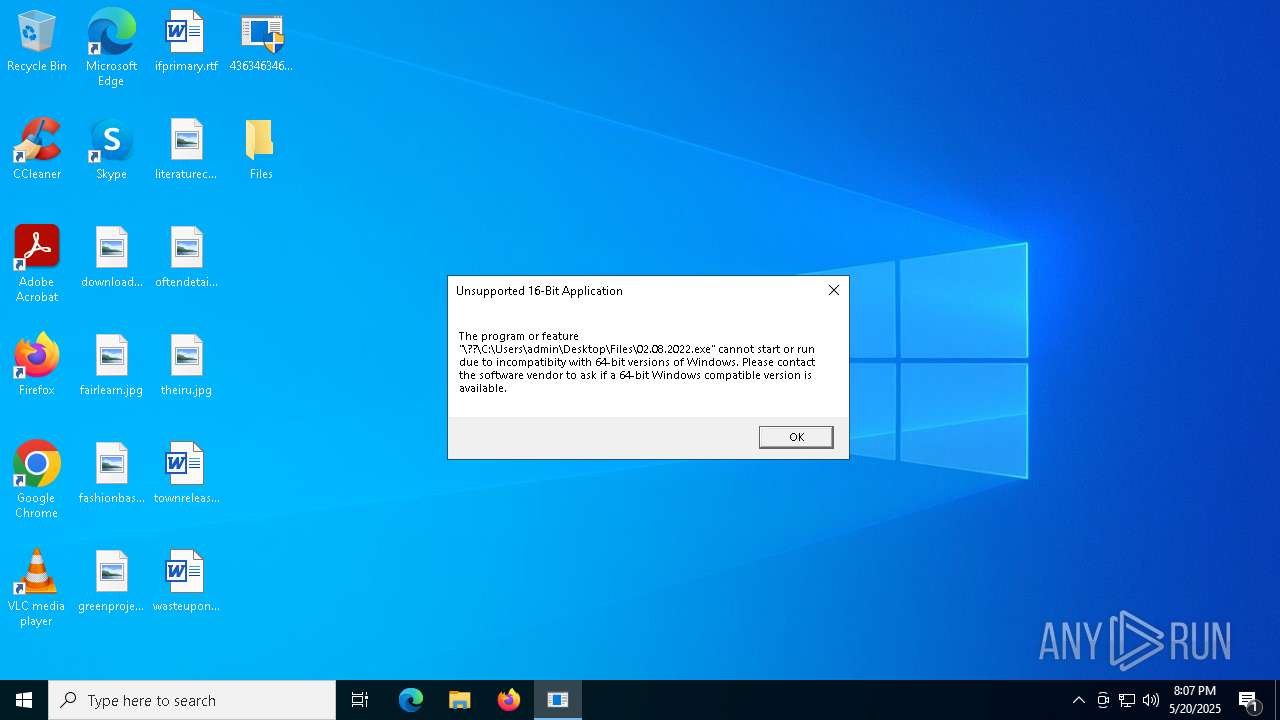
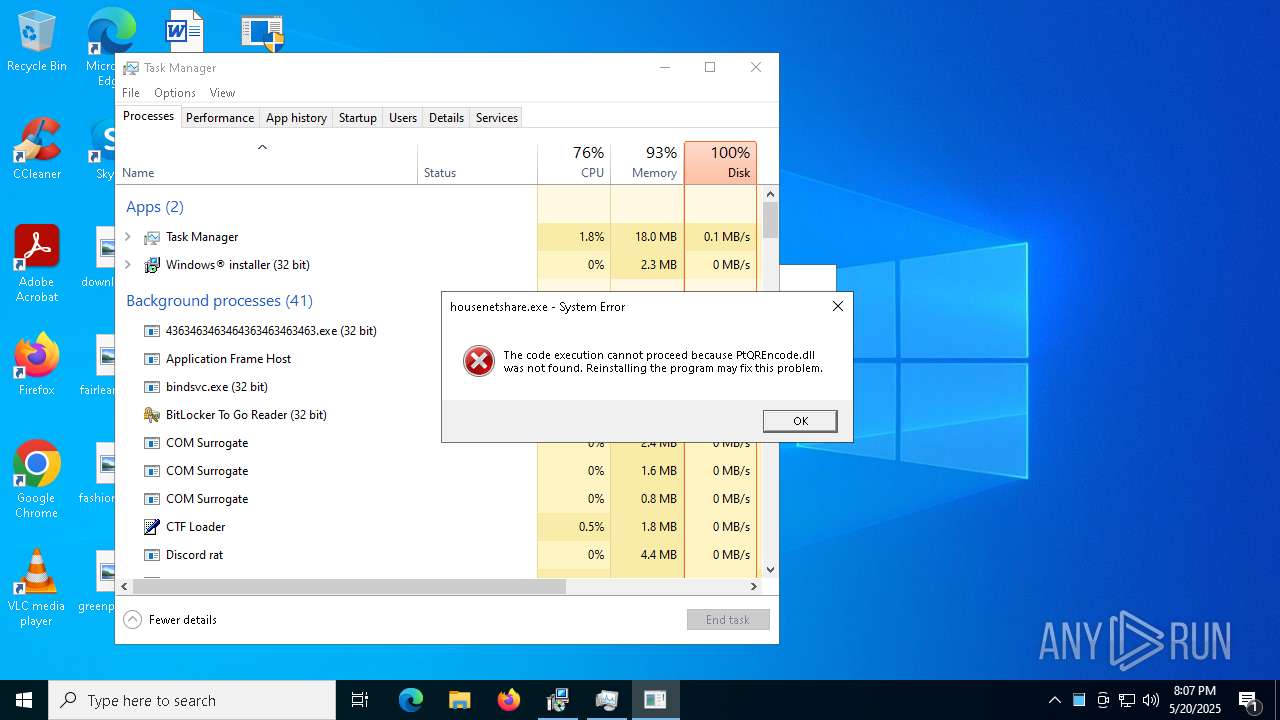
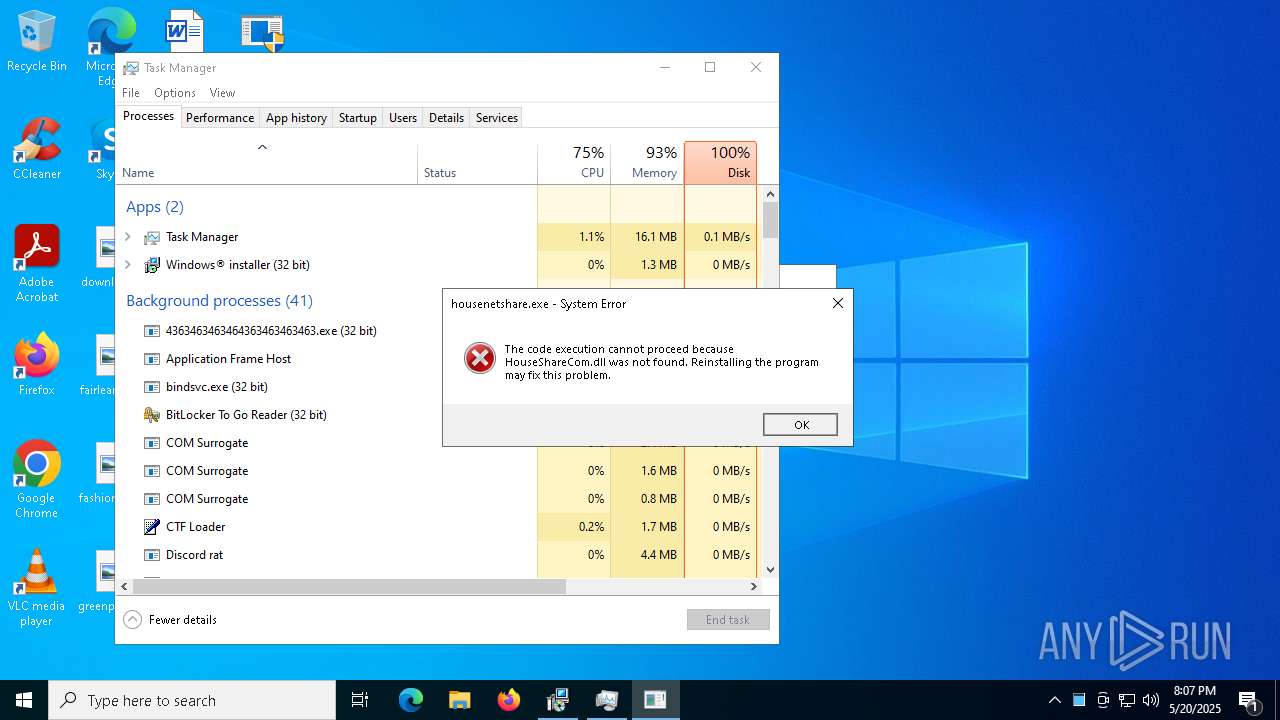
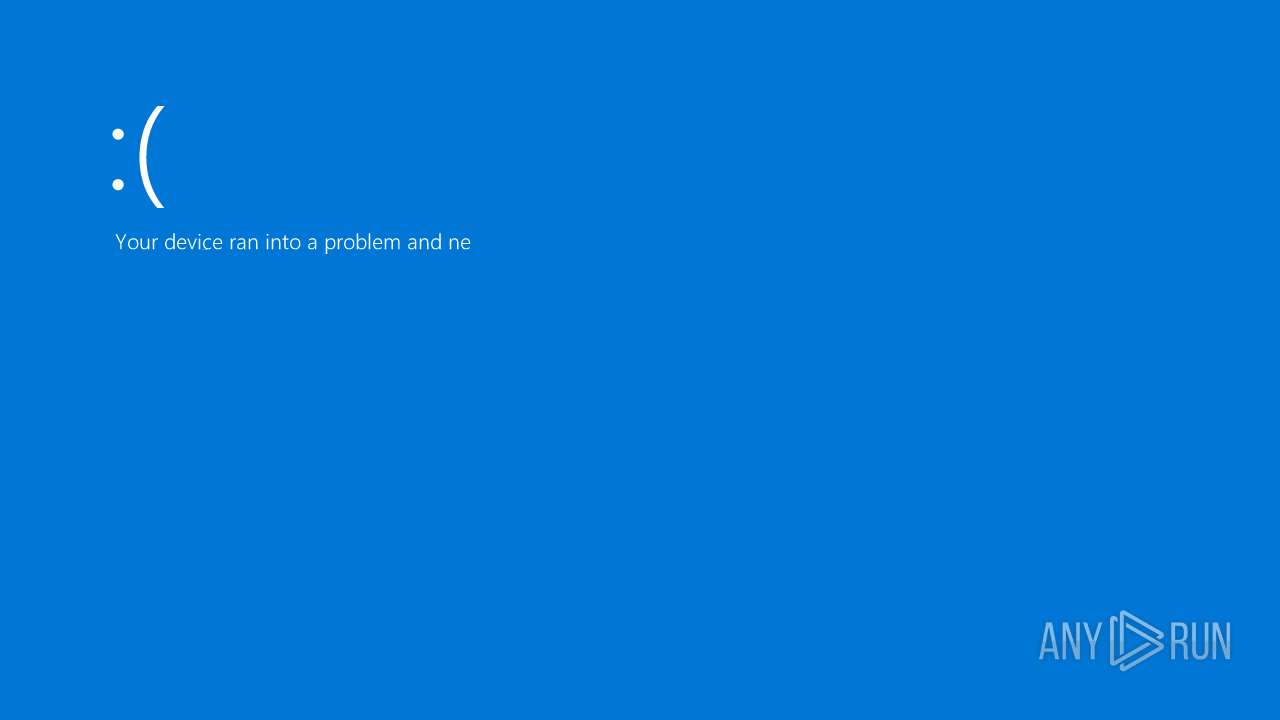
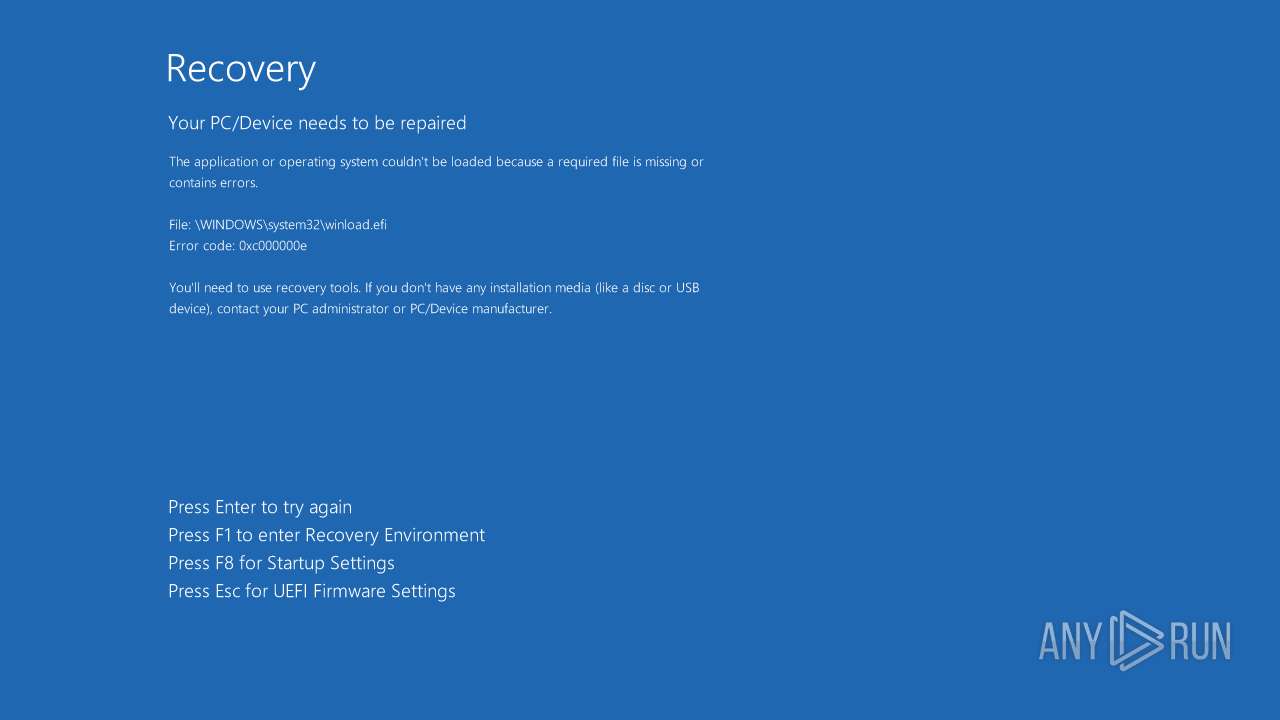
Executes application which crashes
- gold.rim.exe (PID: 8008)
- alex.exe (PID: 8360)
- XClient.exe (PID: 8880)
- alex1231231123.exe (PID: 4144)
Contacting a server suspected of hosting an CnC
- gold.rim.exe (PID: 8096)
- svchost.exe (PID: 2196)
- MSBuild.exe (PID: 8812)
- 4363463463464363463463463.exe (PID: 7528)
- MSBuild.exe (PID: 8932)
- syscrondvr.exe (PID: 9508)
- MSBuild.exe (PID: 10112)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 7528)
- update.exe (PID: 2616)
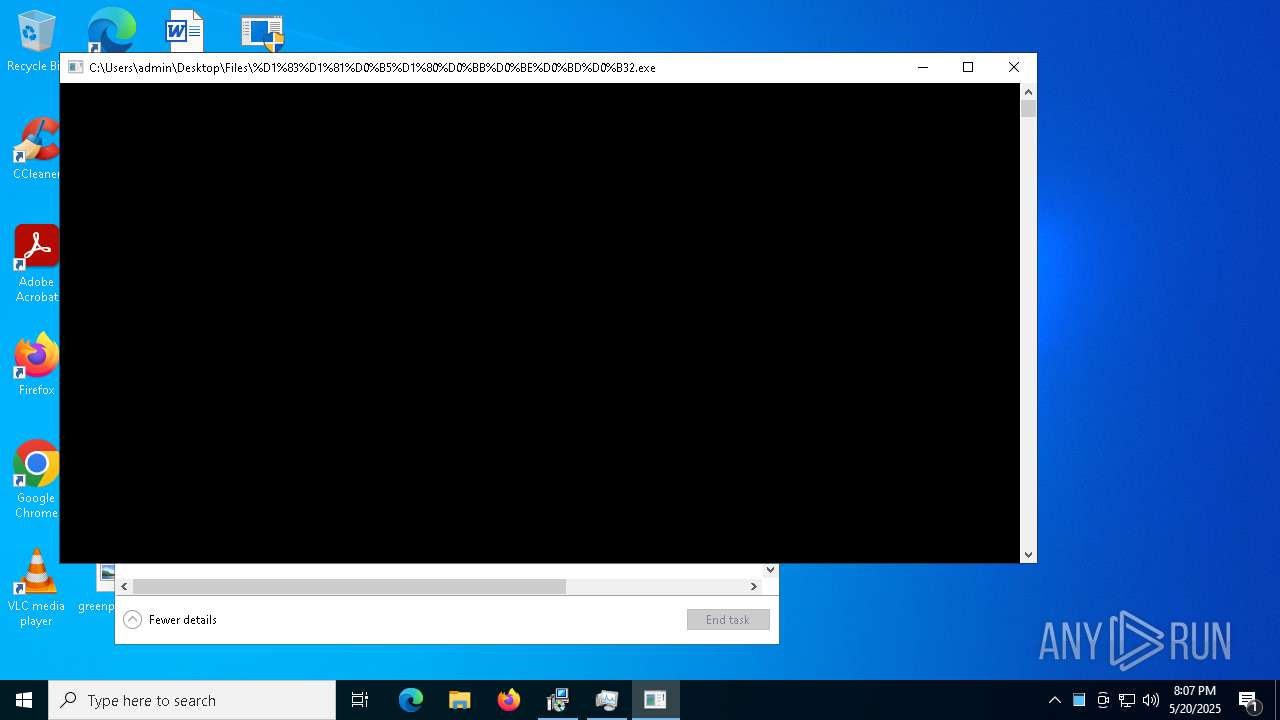
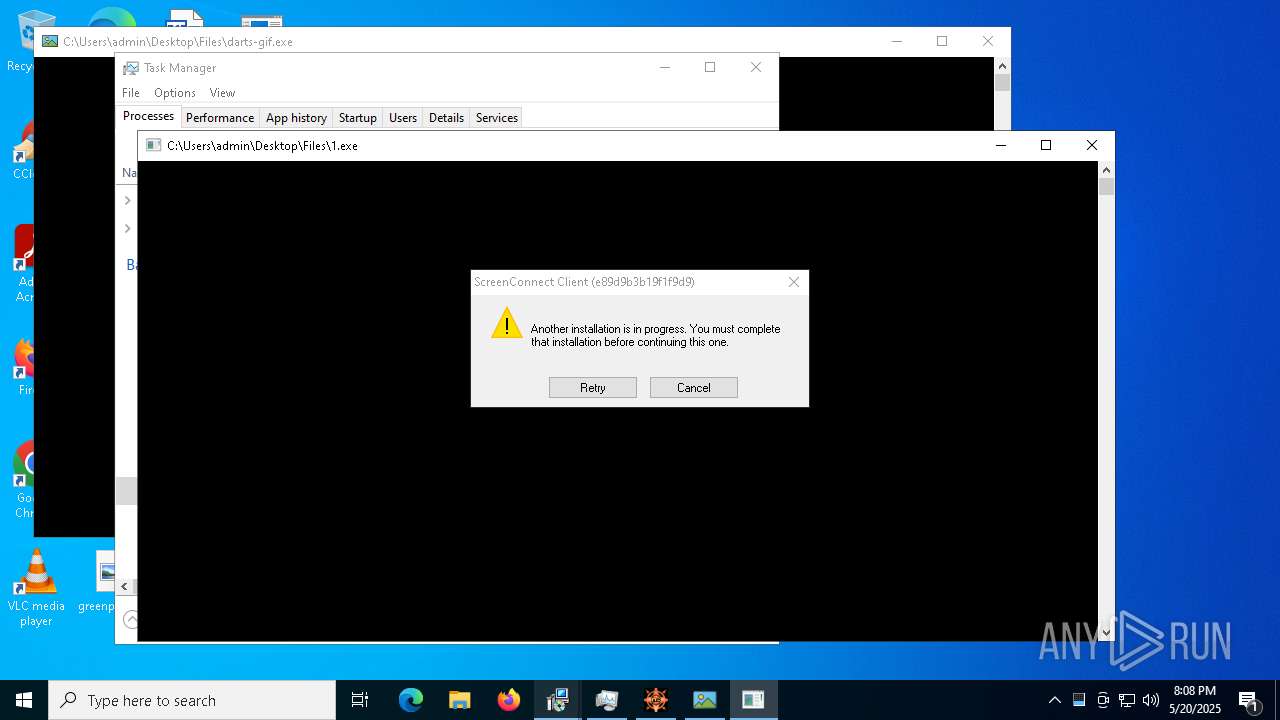
Application launched itself
- gold.rim.exe (PID: 8008)
- alex.exe (PID: 8360)
- %D1%83%D1%81%D0%B5%D1%80%D0%BB%D0%BE%D0%BD%D0%B32.exe (PID: 6572)
- Lamno.exe (PID: 5392)
- alex1231231123.exe (PID: 4144)
- 1.exe (PID: 9296)
- cmd.exe (PID: 10556)
- darts-gif.exe (PID: 9684)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 7528)
- update.exe (PID: 2616)
- dwm.exe (PID: 2416)
- %D1%83%D1%81%D0%B5%D1%80%D0%BB%D0%BE%D0%BD%D0%B32.exe (PID: 4056)
- svchost.exe (PID: 2196)
- TeamViewer.exe (PID: 9296)
- ScreenConnect.ClientService.exe (PID: 6668)
Process drops legitimate windows executable
- update.exe (PID: 496)
- icxtcyndmh.exe (PID: 7408)
- rhsgn_protected.exe (PID: 5608)
- 4363463463464363463463463.exe (PID: 7528)
- darts-gif.exe (PID: 9684)
- qm2014chs.tmp (PID: 6820)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 7528)
- update.exe (PID: 2616)
- Lamno.exe (PID: 5392)
- BitLockerToGo.exe (PID: 6228)
- syscrondvr.exe (PID: 9508)
Starts a Microsoft application from unusual location
- icxtcyndmh.exe (PID: 7408)
- alex1221121212.exe (PID: 8520)
- BQ4m0sD.exe (PID: 10072)
- tb.exe (PID: 10956)
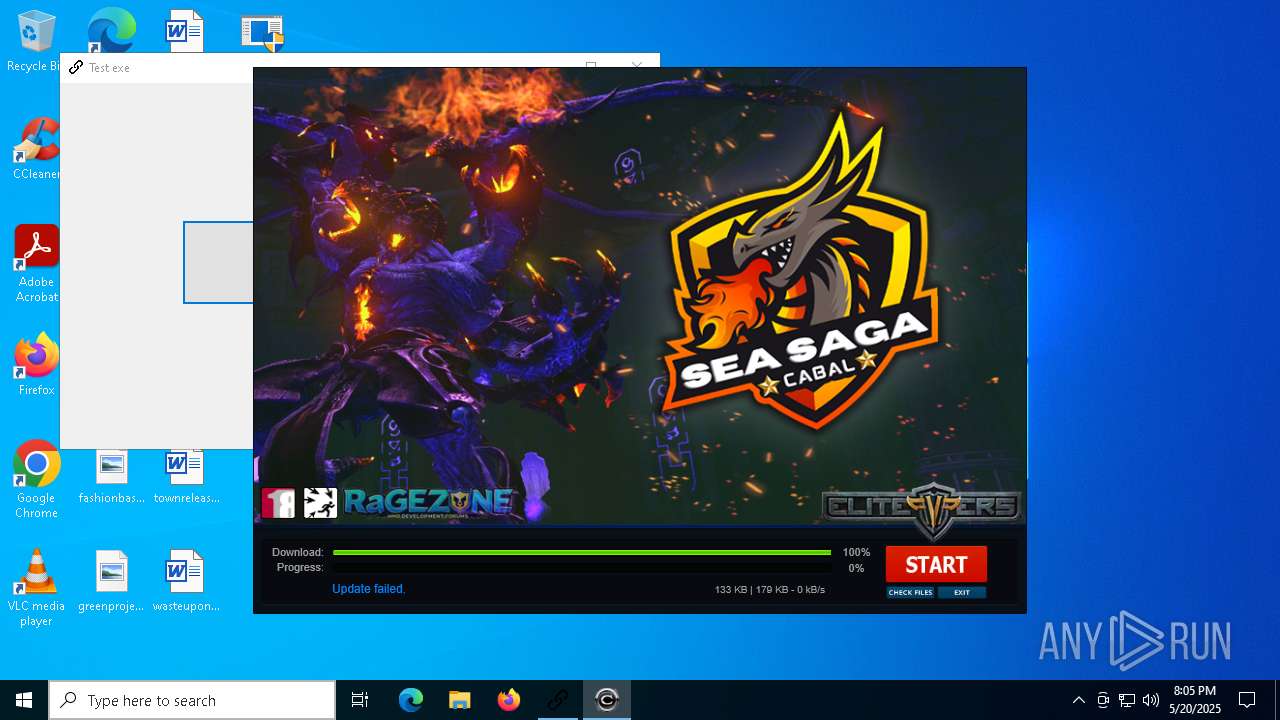
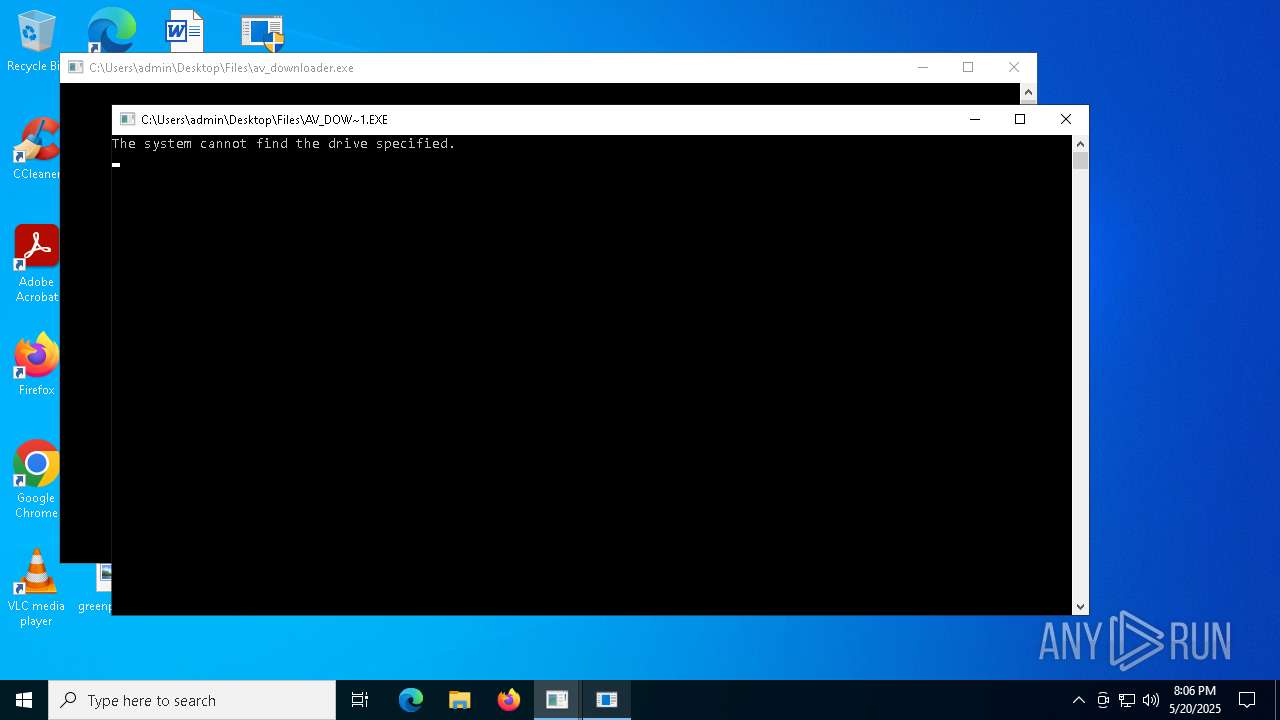
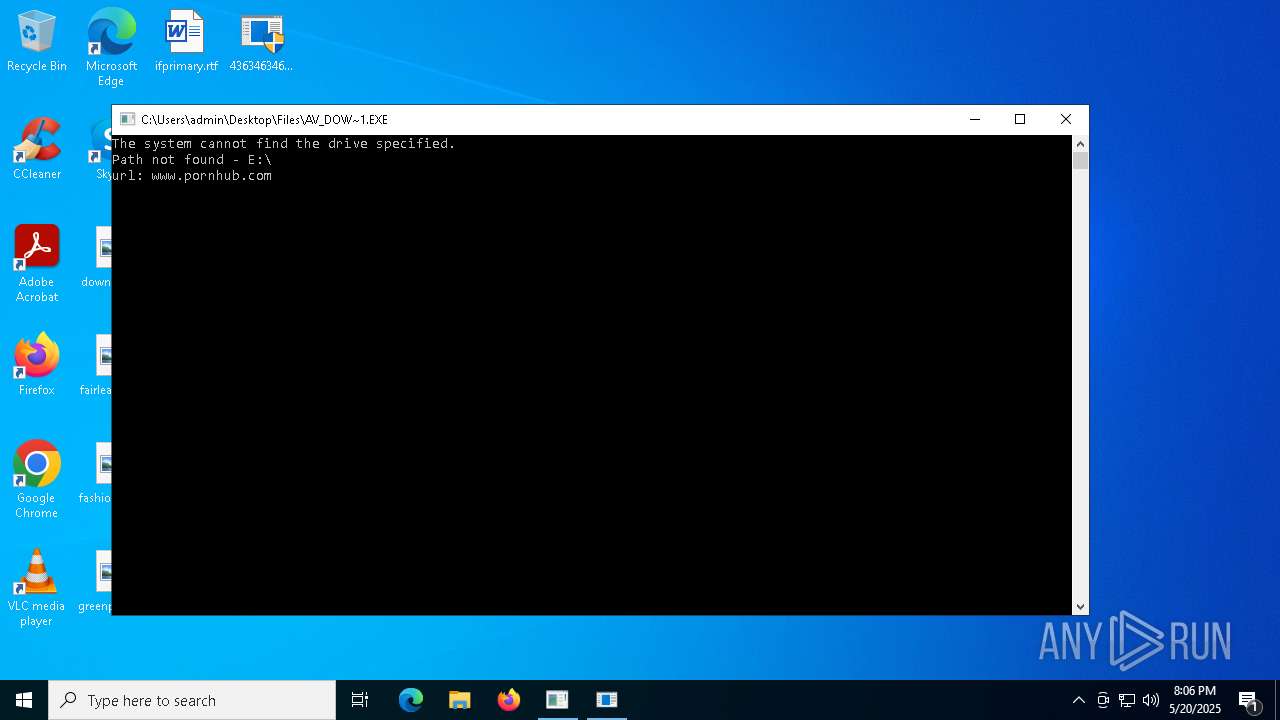
Executing commands from a ".bat" file
- wscript.exe (PID: 6372)
- icxtcyndmh.exe (PID: 7408)
- Msblockreview.exe (PID: 7380)
- av_downloader.exe (PID: 8724)
- av_downloader.exe (PID: 9016)
- tb.exe (PID: 10956)
- Krishna33.exe (PID: 10552)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6372)
- Msblockreview.exe (PID: 7380)
- icxtcyndmh.exe (PID: 7408)
- av_downloader.exe (PID: 8724)
- av_downloader.exe (PID: 9016)
- Lamno.exe (PID: 5392)
- cheese.exe (PID: 10400)
- wscript.exe (PID: 10320)
- tb.exe (PID: 10956)
- cmd.exe (PID: 10556)
- Krishna33.exe (PID: 10552)
- wscript.exe (PID: 8604)
- wscript.exe (PID: 10356)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6372)
The executable file from the user directory is run by the CMD process
- Msblockreview.exe (PID: 7380)
- wscmnoqdwk.3gp (PID: 11316)
- ilrcphdp.jpg (PID: 11800)
- koemhx.mp2 (PID: 11808)
- chrome.exe (PID: 12108)
Executed via WMI
- schtasks.exe (PID: 856)
- schtasks.exe (PID: 8156)
- schtasks.exe (PID: 8164)
- schtasks.exe (PID: 7236)
- schtasks.exe (PID: 7284)
- schtasks.exe (PID: 7904)
- schtasks.exe (PID: 7304)
- schtasks.exe (PID: 6652)
- schtasks.exe (PID: 7296)
- schtasks.exe (PID: 4812)
- schtasks.exe (PID: 8016)
- schtasks.exe (PID: 7276)
- schtasks.exe (PID: 7548)
- schtasks.exe (PID: 5576)
- schtasks.exe (PID: 2236)
- schtasks.exe (PID: 6712)
- schtasks.exe (PID: 7228)
- schtasks.exe (PID: 6744)
Starts SC.EXE for service management
- cmd.exe (PID: 780)
- x.exe (PID: 6208)
Windows service management via SC.EXE
- sc.exe (PID: 1512)
- sc.exe (PID: 6960)
- sc.exe (PID: 4120)
The process creates files with name similar to system file names
- Msblockreview.exe (PID: 7380)
Reads the date of Windows installation
- Msblockreview.exe (PID: 7380)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 7924)
Uses pipe srvsvc via SMB (transferring data)
- bindsvc.exe (PID: 4724)
Reads the BIOS version
- gcmgr_tw.exe (PID: 8052)
Stops a currently running service
- sc.exe (PID: 4868)
Drops a system driver (possible attempt to evade defenses)
- sysmtdrav.exe (PID: 2084)
Executes as Windows Service
- sysmtdrav.exe (PID: 2084)
- VSSVC.exe (PID: 7800)
- ScreenConnect.ClientService.exe (PID: 6668)
Connects to unusual port
- dwm.exe (PID: 2416)
- RegAsm.exe (PID: 1676)
- certutil.exe (PID: 9184)
- 4363463463464363463463463.exe (PID: 7528)
- %D1%83%D1%81%D0%B5%D1%80%D0%BB%D0%BE%D0%BD%D0%B32.exe (PID: 4056)
- OpenWith.exe (PID: 8832)
- crack.exe (PID: 9304)
- up.exe (PID: 9256)
- Lamno.exe (PID: 9632)
- Client.exe (PID: 9476)
- 1.exe (PID: 10180)
- RuntimeBroker.exe (PID: 2852)
- ScreenConnect.ClientService.exe (PID: 6668)
- MSWinpreference.exe (PID: 10156)
- TeamViewer.exe (PID: 9296)
- syscrondvr.exe (PID: 9508)
- tb.exe (PID: 10956)
- ConsoleApp1.exe (PID: 9984)
- sela.exe (PID: 11048)
Creates a new Windows service
- sc.exe (PID: 6424)
Starts itself from another location
- javaw.exe (PID: 8624)
- gold.rim.exe (PID: 2596)
- newtpp.exe (PID: 9276)
- RuntimeBroker.exe (PID: 9752)
- installer.exe.exe (PID: 9888)
- CollosalLoader.exe (PID: 6256)
- ServerX.exe (PID: 10304)
- Server.exe (PID: 11484)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 9068)
- cmd.exe (PID: 9368)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 9068)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 8812)
- MSBuild.exe (PID: 10112)
Starts POWERSHELL.EXE for commands execution
- gold.rim.exe (PID: 2596)
- cheese.exe (PID: 10400)
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Checks for external IP
- XClient.exe (PID: 8880)
- svchost.exe (PID: 2196)
Process drops python dynamic module
- darts-gif.exe (PID: 9684)
- cryptography_module_windows.exe (PID: 11824)
The process drops C-runtime libraries
- darts-gif.exe (PID: 9684)
- qm2014chs.tmp (PID: 6820)
Malware-specific behavior (creating "System.dll" in Temp)
- viewpoint_support.exe (PID: 9420)
Identifying current user with WHOAMI command
- 1.exe (PID: 10180)
- %D1%83%D1%81%D0%B5%D1%80%D0%BB%D0%BE%D0%BD%D0%B32.exe (PID: 4056)
Drops 7-zip archiver for unpacking
- viewpoint_support.exe (PID: 9420)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 6668)
Script adds exclusion path to Windows Defender
- cheese.exe (PID: 10400)
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Execution of CURL command
- cheese.exe (PID: 10400)
Uses NETSH.EXE to add a firewall rule or allowed programs
- server.exe (PID: 10568)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- server.exe (PID: 10568)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 9648)
- cmd.exe (PID: 9644)
- cmd.exe (PID: 11492)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 10556)
Starts application with an unusual extension
- cmd.exe (PID: 10868)
- cmd.exe (PID: 11568)
- cmd.exe (PID: 11608)
Starts the AutoIt3 executable file
- cmd.exe (PID: 10868)
- cmd.exe (PID: 11568)
- cmd.exe (PID: 11608)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 11524)
- cmd.exe (PID: 11156)
- cmd.exe (PID: 11532)
Process uses IPCONFIG to renew DHCP configuration
- cmd.exe (PID: 11716)
- cmd.exe (PID: 12068)
- cmd.exe (PID: 12060)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 10984)
Uses TASKKILL.EXE to kill process
- qm2014chs.tmp (PID: 6820)
Script adds exclusion process to Windows Defender
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Script adds exclusion extension to Windows Defender
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 10556)
INFO
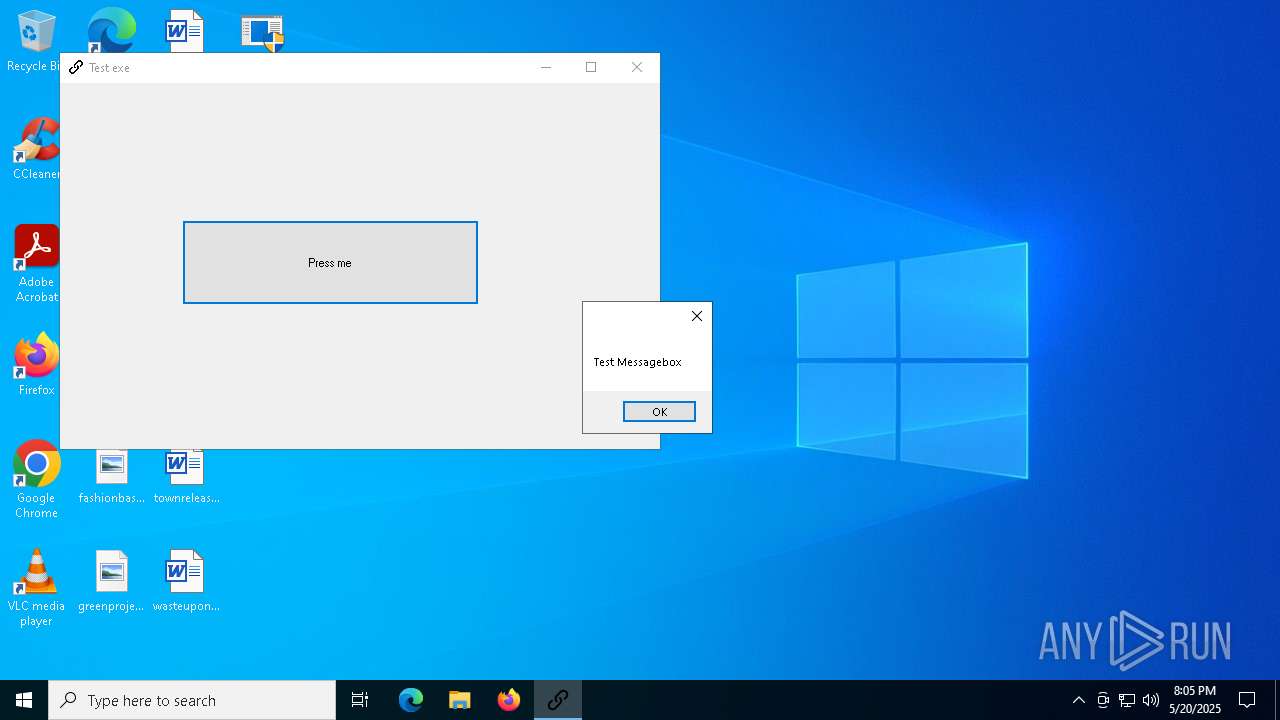
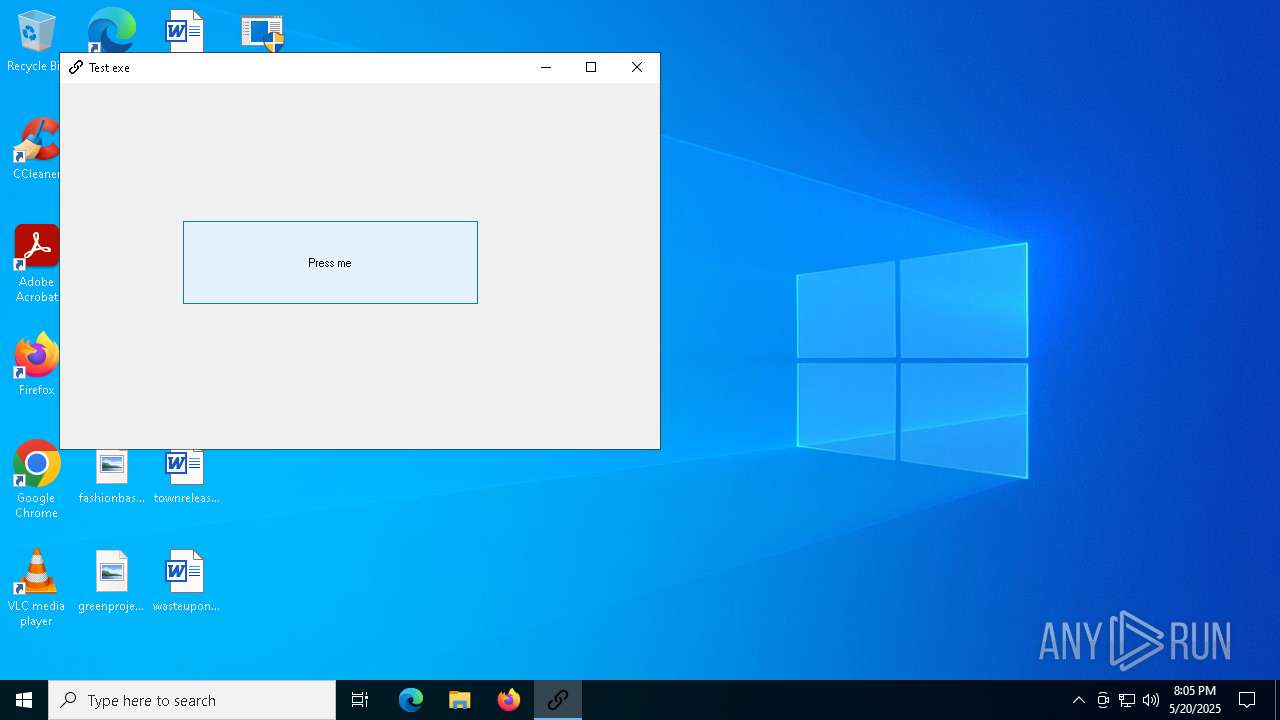
Reads the computer name
- 4363463463464363463463463.exe (PID: 7528)
- TestExe.exe (PID: 7804)
- Client-built.exe (PID: 7836)
- gold.rim.exe (PID: 8008)
- gold.rim.exe (PID: 8096)
- icxtcyndmh.exe (PID: 7408)
- update.exe (PID: 496)
- update.exe (PID: 2616)
- loader.exe (PID: 1164)
- rhsgn_protected.exe (PID: 5608)
- obdkbemdem.exe (PID: 7144)
- ARA.exe (PID: 6192)
- Msblockreview.exe (PID: 7380)
- bindsvc.exe (PID: 4724)
- ShellExperienceHost.exe (PID: 5800)
- gcmgr_tw.exe (PID: 8052)
- gold.rim.exe (PID: 6572)
Disables trace logs
- 4363463463464363463463463.exe (PID: 7528)
- Client-built.exe (PID: 7836)
- update.exe (PID: 2616)
- gold.rim.exe (PID: 6572)
Reads the machine GUID from the registry
- 4363463463464363463463463.exe (PID: 7528)
- TestExe.exe (PID: 7804)
- Client-built.exe (PID: 7836)
- update.exe (PID: 2616)
- Msblockreview.exe (PID: 7380)
- gold.rim.exe (PID: 6572)
- gcmgr_tw.exe (PID: 8052)
Checks proxy server information
- 4363463463464363463463463.exe (PID: 7528)
- Client-built.exe (PID: 7836)
- update.exe (PID: 2616)
- gold.rim.exe (PID: 6572)
Checks supported languages
- Client-built.exe (PID: 7836)
- TestExe.exe (PID: 7804)
- 4363463463464363463463463.exe (PID: 7528)
- gold.rim.exe (PID: 8008)
- update.exe (PID: 496)
- gold.rim.exe (PID: 8096)
- obdkbemdem.exe (PID: 7144)
- icxtcyndmh.exe (PID: 7408)
- update.exe (PID: 2616)
- rhsgn_protected.exe (PID: 5608)
- loader.exe (PID: 1164)
- ARA.exe (PID: 6192)
- Msblockreview.exe (PID: 7380)
- bindsvc.exe (PID: 4724)
- gold.rim.exe (PID: 6572)
- ShellExperienceHost.exe (PID: 5800)
- gcmgr_tw.exe (PID: 8052)
- crypted_c360a5b7.exe (PID: 8008)
- x.exe (PID: 6208)
- RegAsm.exe (PID: 1676)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 7528)
- update.exe (PID: 496)
- obdkbemdem.exe (PID: 7144)
- loader.exe (PID: 1164)
- ARA.exe (PID: 6192)
- rhsgn_protected.exe (PID: 5608)
- Msblockreview.exe (PID: 7380)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 7528)
- Client-built.exe (PID: 7836)
- gold.rim.exe (PID: 8096)
Reads Environment values
- Client-built.exe (PID: 7836)
- Msblockreview.exe (PID: 7380)
- gold.rim.exe (PID: 6572)
Attempting to use instant messaging service
- svchost.exe (PID: 2196)
- Client-built.exe (PID: 7836)
- MSBuild.exe (PID: 8812)
Creates files or folders in the user directory
- WerFault.exe (PID: 1276)
- ARA.exe (PID: 6192)
- bindsvc.exe (PID: 4724)
The sample compiled with english language support
- update.exe (PID: 496)
- icxtcyndmh.exe (PID: 7408)
- rhsgn_protected.exe (PID: 5608)
- ARA.exe (PID: 6192)
- Msblockreview.exe (PID: 7380)
- 4363463463464363463463463.exe (PID: 7528)
- darts-gif.exe (PID: 9684)
- viewpoint_support.exe (PID: 9420)
- qm2014chs.tmp (PID: 6820)
- Vltod.exe (PID: 10740)
- rtsf.exe (PID: 10724)
- XLtod.exe (PID: 10748)
- QXUserCtrlSetup_1010.exe (PID: 928)
- koemhx.mp2 (PID: 11808)
- wscmnoqdwk.3gp (PID: 11316)
Executes as Windows Service
- SearchIndexer.exe (PID: 7508)
Creates files in the program directory
- SearchIndexer.exe (PID: 7508)
- Msblockreview.exe (PID: 7380)
Create files in a temporary directory
- update.exe (PID: 496)
- loader.exe (PID: 1164)
- rhsgn_protected.exe (PID: 5608)
- update.exe (PID: 2616)
- icxtcyndmh.exe (PID: 7408)
- Msblockreview.exe (PID: 7380)
Drops encrypted VBS script (Microsoft Script Encoder)
- ARA.exe (PID: 6192)
The sample compiled with japanese language support
- sysmtdrav.exe (PID: 2084)
The sample compiled with chinese language support
- 4363463463464363463463463.exe (PID: 7528)
- qm2014chs.tmp (PID: 6820)
- tb.exe (PID: 10956)
- QXUserCtrlSetup_1010.exe (PID: 928)
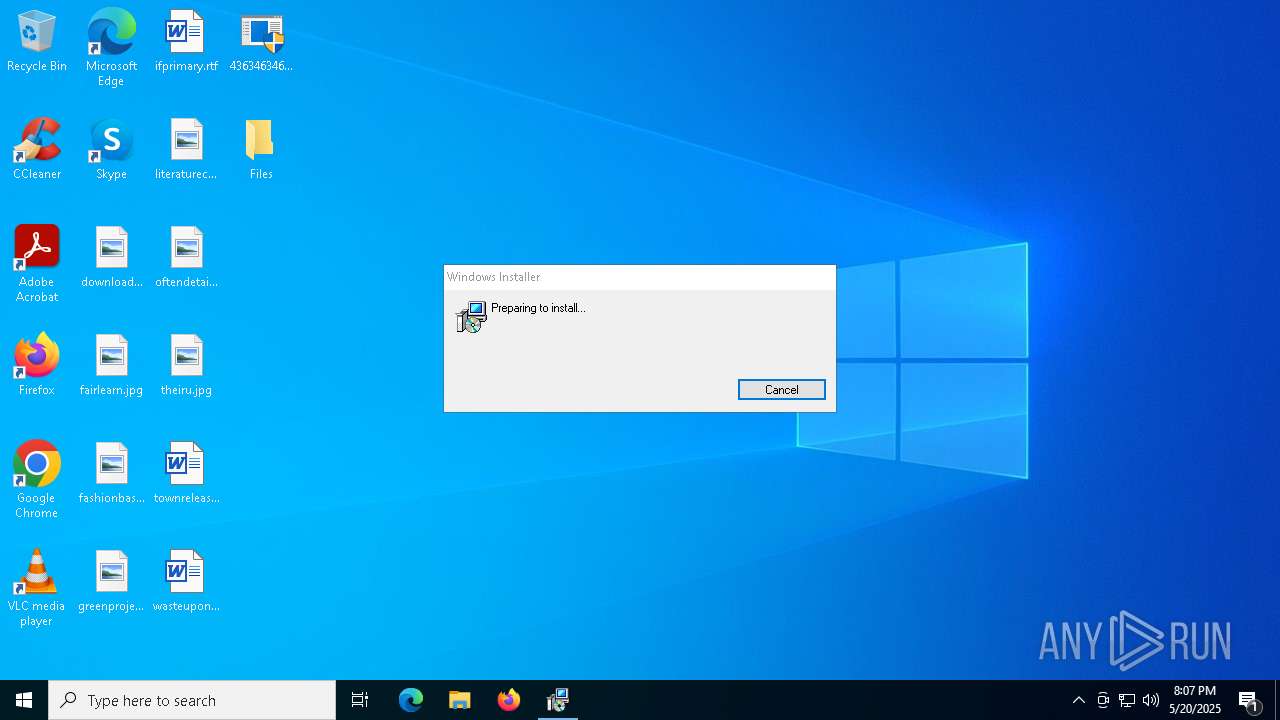
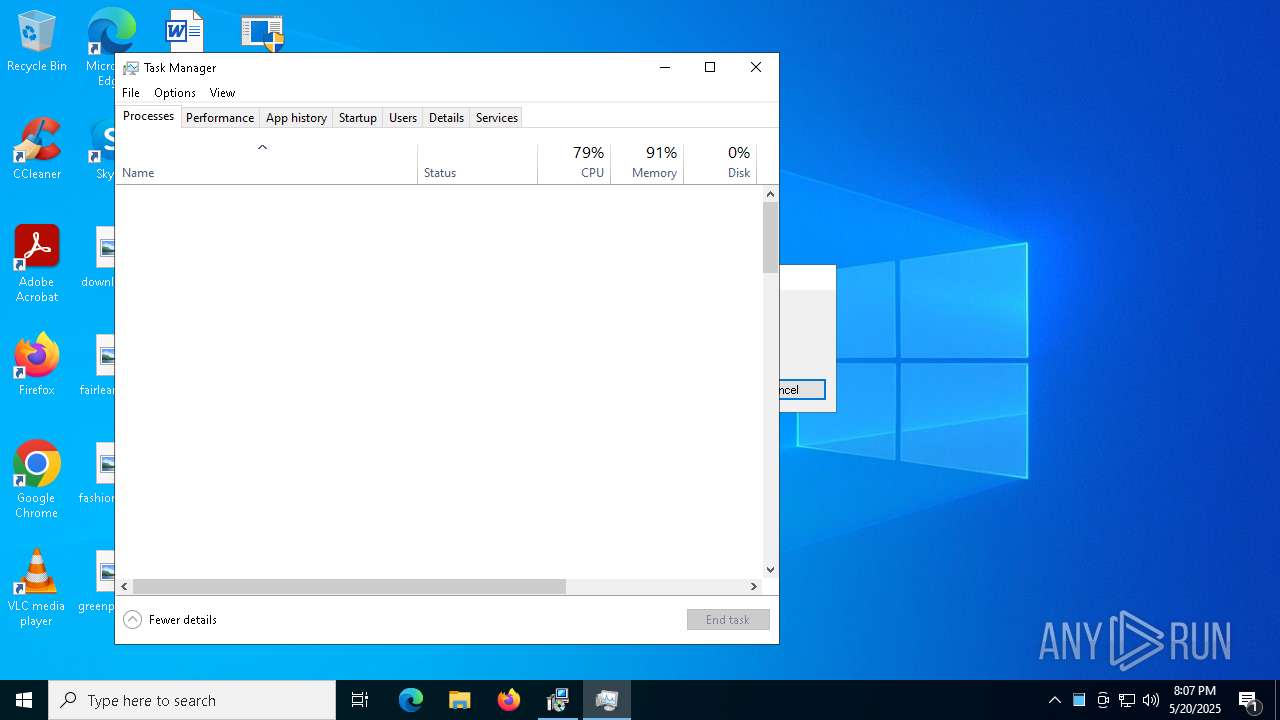
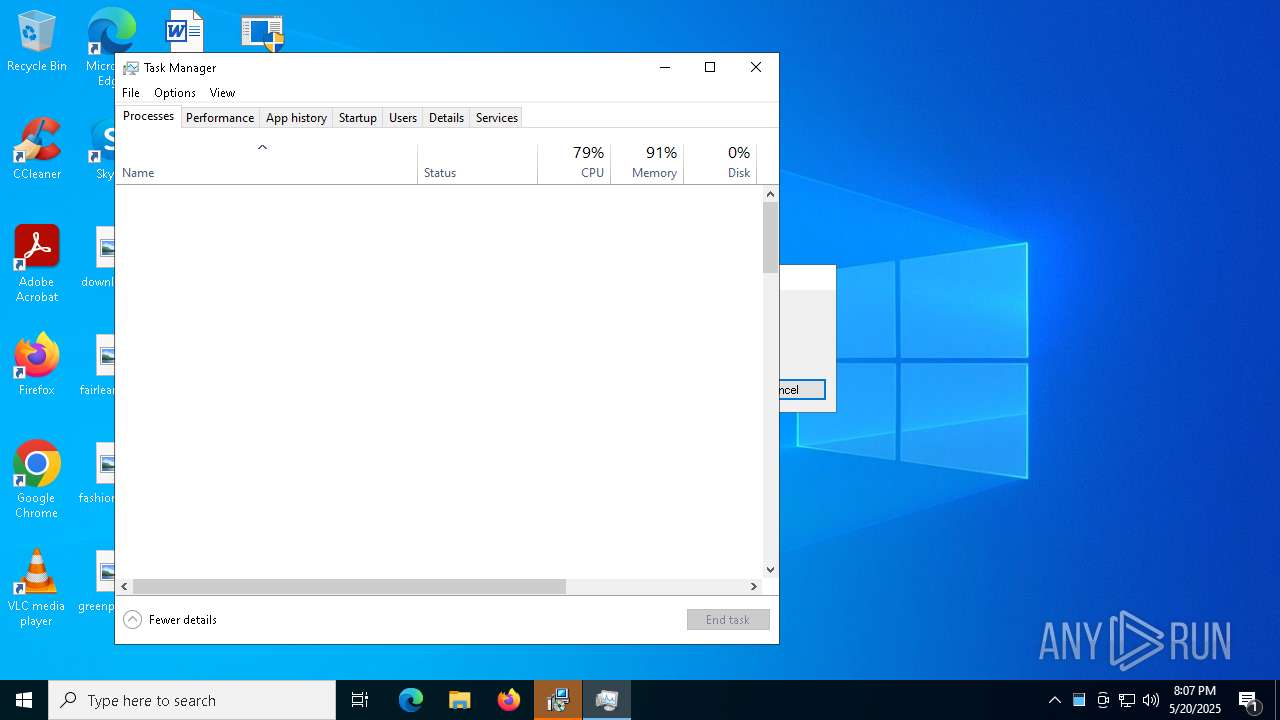
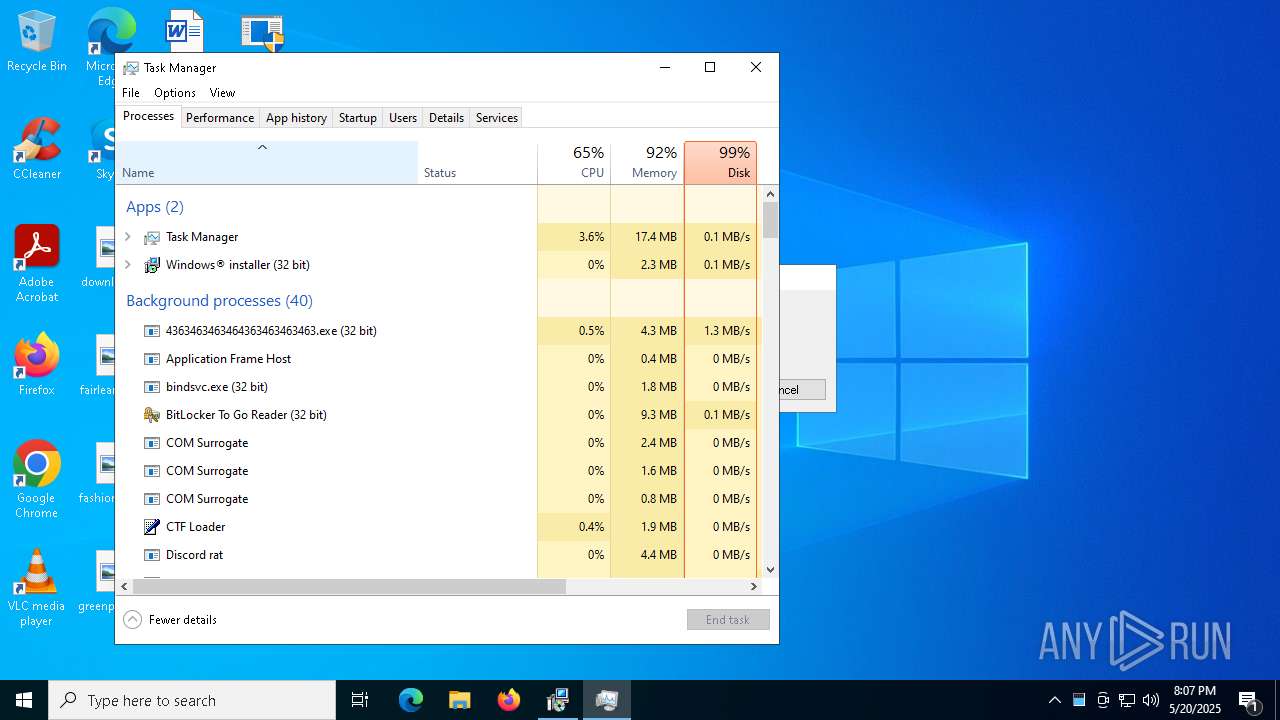
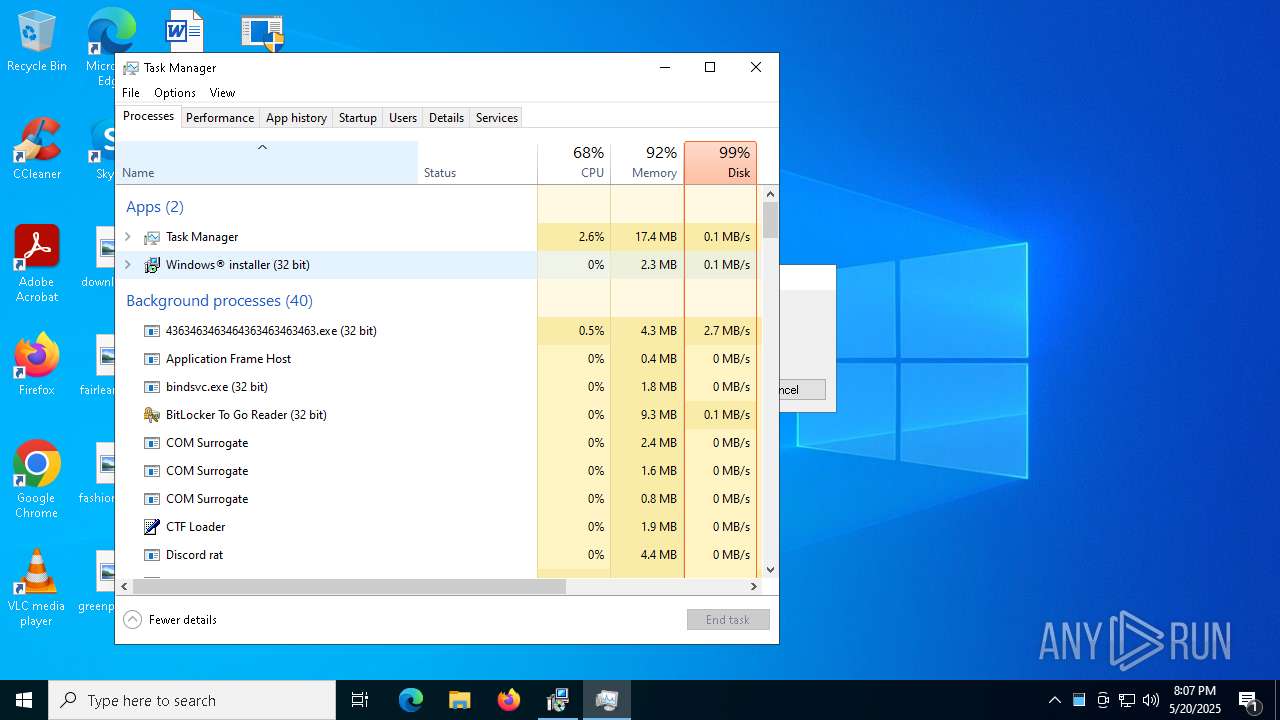
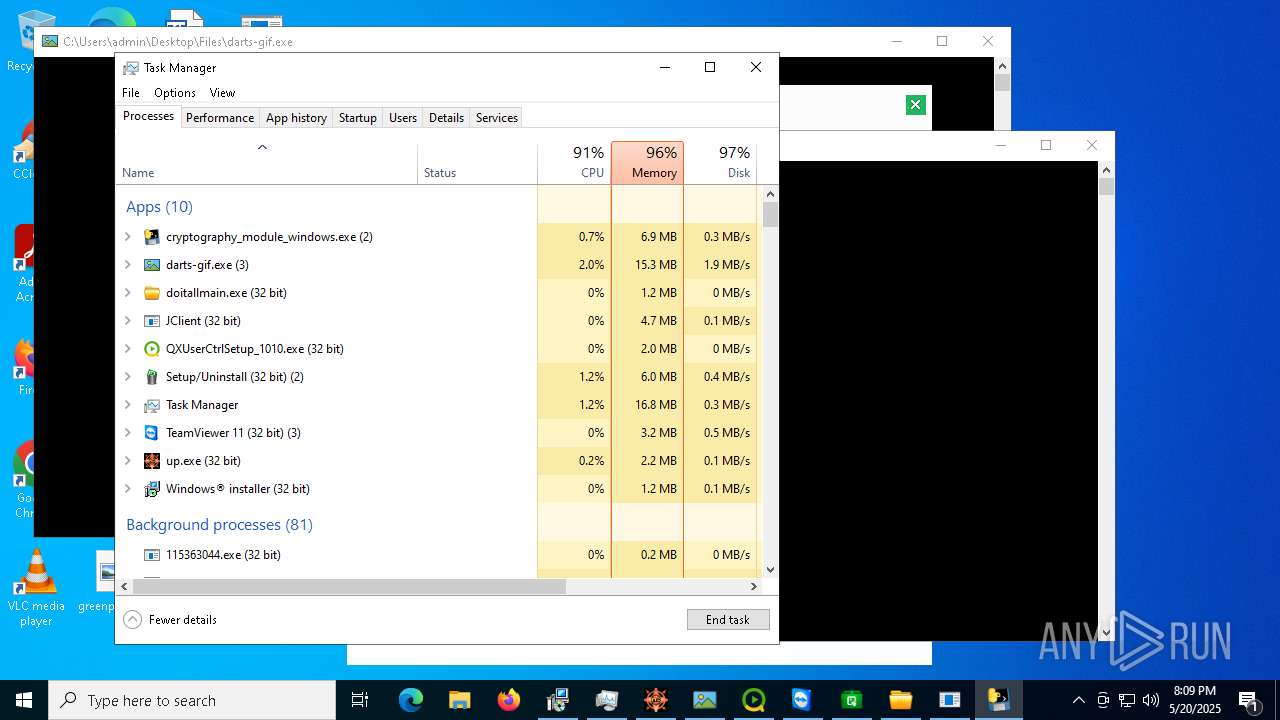
Manual execution by a user
- Taskmgr.exe (PID: 9164)
- Taskmgr.exe (PID: 2136)
Executable content was dropped or overwritten
- msiexec.exe (PID: 680)
- msiexec.exe (PID: 7188)
- msiexec.exe (PID: 7296)
UPX packer has been detected
- bindsvc.exe (PID: 4724)
Manages system restore points
- SrTasks.exe (PID: 4348)
The sample compiled with russian language support
- qm2014chs.tmp (PID: 6820)
Execution of CURL command
- cmd.exe (PID: 11080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
468
Monitored processes
320
Malicious processes
52
Suspicious processes
18
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "C:\Users\admin\Desktop\Files\update.exe" | C:\Users\admin\Desktop\Files\update.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 680 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\a7a0f24b763b4fc7\ScreenConnect.ClientSetup.msi" | C:\Windows\SysWOW64\msiexec.exe | elitepartyinfo.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\reviewintobrokerHost\WJgXY0RCE6WdWGoPyLk7f.bat" " | C:\Windows\SysWOW64\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | /c sc config msdtc obj= LocalSystem | C:\Windows\System32\cmd.exe | — | icxtcyndmh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | schtasks.exe /create /tn "RuntimeBrokerR" /sc MINUTE /mo 5 /tr "'C:\Users\Default User\RuntimeBroker.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 928 | "C:\Users\admin\Desktop\Files\QXUserCtrlSetup_1010.exe" | C:\Users\admin\Desktop\Files\QXUserCtrlSetup_1010.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1004 | "C:\Users\admin\Desktop\Files\alex1231231123.exe" | C:\Users\admin\Desktop\Files\alex1231231123.exe | alex1231231123.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Purpose Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1164 | "C:\Users\admin\Desktop\Files\loader.exe" | C:\Users\admin\Desktop\Files\loader.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1272 | "schtasks" /create /tn "Skype" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\SubDir\MSWinpreference.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | MSWinpreference.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1276 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 8008 -s 136 | C:\Windows\SysWOW64\WerFault.exe | — | gold.rim.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
102 919
Read events
102 219
Write events
630
Delete events
70
Modification events
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7528) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
292
Suspicious files
62
Text files
1 079
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_gold.rim.exe_2ee34f48f96d11ec483313f1e6de8cbfdde572_e5f72d93_798bd350-fba7-469b-8243-cdad238eab60\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1276 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\gold.rim.exe.8008.dmp | — | |
MD5:— | SHA256:— | |||
| 7508 | SearchIndexer.exe | C:\ProgramData\Microsoft\Search\Data\Applications\Windows\Windows.edb | — | |
MD5:— | SHA256:— | |||
| 1276 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERE68A.tmp.WERInternalMetadata.xml | binary | |
MD5:1CF8E93B4F38122C53B70E9ECBB68E3A | SHA256:0C2B58148843495EE1F8EA1E985DF6460205BCCAE5155904A762724237C73CB4 | |||
| 7528 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\loader.exe | executable | |
MD5:EB562E873C0D6BA767964D0DE55AC5A9 | SHA256:E8E3CDDCC753E66757C3D6A47B63117F718103F03A039B40A4553849E04B8AEC | |||
| 7408 | icxtcyndmh.exe | C:\Windows\SysWOW64\bindsvc.exe | executable | |
MD5:7C5B397FB54D5AA06BD2A6FB99C62FEE | SHA256:D032BDC64C9451BBB653B346C5BD6AC9F83A91EDEB0155497F098C8D6182DDEE | |||
| 5608 | rhsgn_protected.exe | C:\Users\admin\AppData\Local\Temp\eamsi.dll | executable | |
MD5:CCFE48E3AAF6A7ADF5643D90CDE3439C | SHA256:5E1F9CBC0F1CA645183F26E25463679AA89CD22A29D427C000AEA0E1E9C11903 | |||
| 7408 | icxtcyndmh.exe | C:\Windows\SysWOW64\racfg.exe | executable | |
MD5:DC0222F1E0868C3612A93BA2D83B99BE | SHA256:6BC4497B86DF521B413E4574F4CD4289C986348D2A69DA1945FF1A1784DB05DB | |||
| 7408 | icxtcyndmh.exe | C:\Windows\SysWOW64\wimsvc.exe | executable | |
MD5:2C2029588AD8B86759C17B7AE885EE03 | SHA256:3AB288C47914E33CC61985E46502158400FAA9D7187B55C19039B8795504A290 | |||
| 496 | update.exe | C:\Users\admin\AppData\Local\Temp\obdkbemdem.exe | executable | |
MD5:E48B89715BF5E4C55EB5A1FED67865D9 | SHA256:C25D90168FC2026D8ED2A69C066BD5A7E11004C3899928A7DB24CB7636FC4D9E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
1 346
DNS requests
153
Threats
265
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.142:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7528 | 4363463463464363463463463.exe | GET | 200 | 168.138.162.78:80 | http://168.138.162.78/output0/client/update.exe | unknown | — | — | unknown |
7528 | 4363463463464363463463463.exe | GET | 200 | 210.19.94.140:80 | http://www.maxmoney.com/opencart/system/library/cache/.cache/loader.exe | unknown | — | — | unknown |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
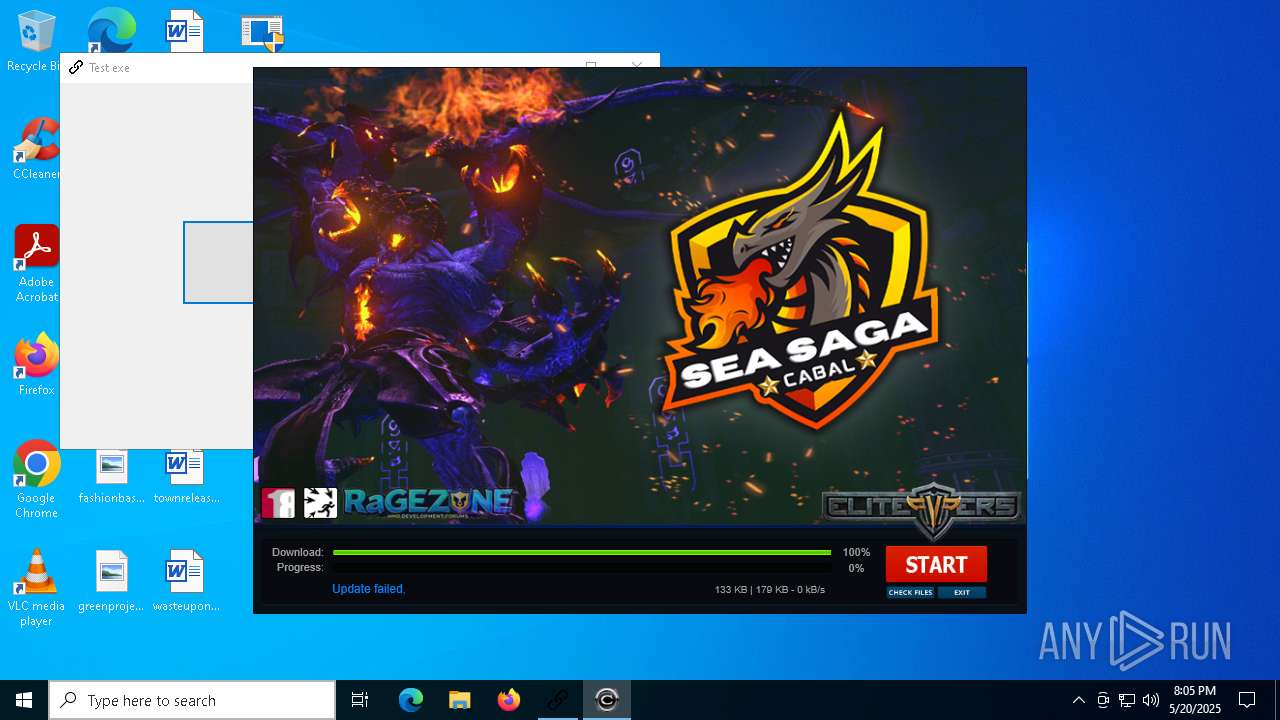
2616 | update.exe | GET | 200 | 168.138.162.78:80 | http://168.138.162.78/output0//resources0.xml | unknown | — | — | unknown |
2616 | update.exe | GET | 200 | 168.138.162.78:80 | http://168.138.162.78/output0/client/cabal.exe | unknown | — | — | unknown |
2616 | update.exe | GET | 200 | 168.138.162.78:80 | http://168.138.162.78/output0/updates/update_1.7z | unknown | — | — | unknown |
7760 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7760 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.142:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7528 | 4363463463464363463463463.exe | 151.101.130.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
7528 | 4363463463464363463463463.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
7528 | 4363463463464363463463463.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
github.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (gateway .discord .gg) |
7836 | Client-built.exe | Misc activity | ET INFO Observed Discord Service Domain (gateway .discord .gg) in TLS SNI |
7528 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7528 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7528 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7528 | 4363463463464363463463463.exe | Misc activity | ET INFO Packed Executable Download |
7528 | 4363463463464363463463463.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
7528 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |