| File name: | 4363463463464363463463463.bin |
| Full analysis: | https://app.any.run/tasks/552605d2-7815-4dda-b60f-a579051e7b1c |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 19, 2025, 08:07:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
NJRAT has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 7380)
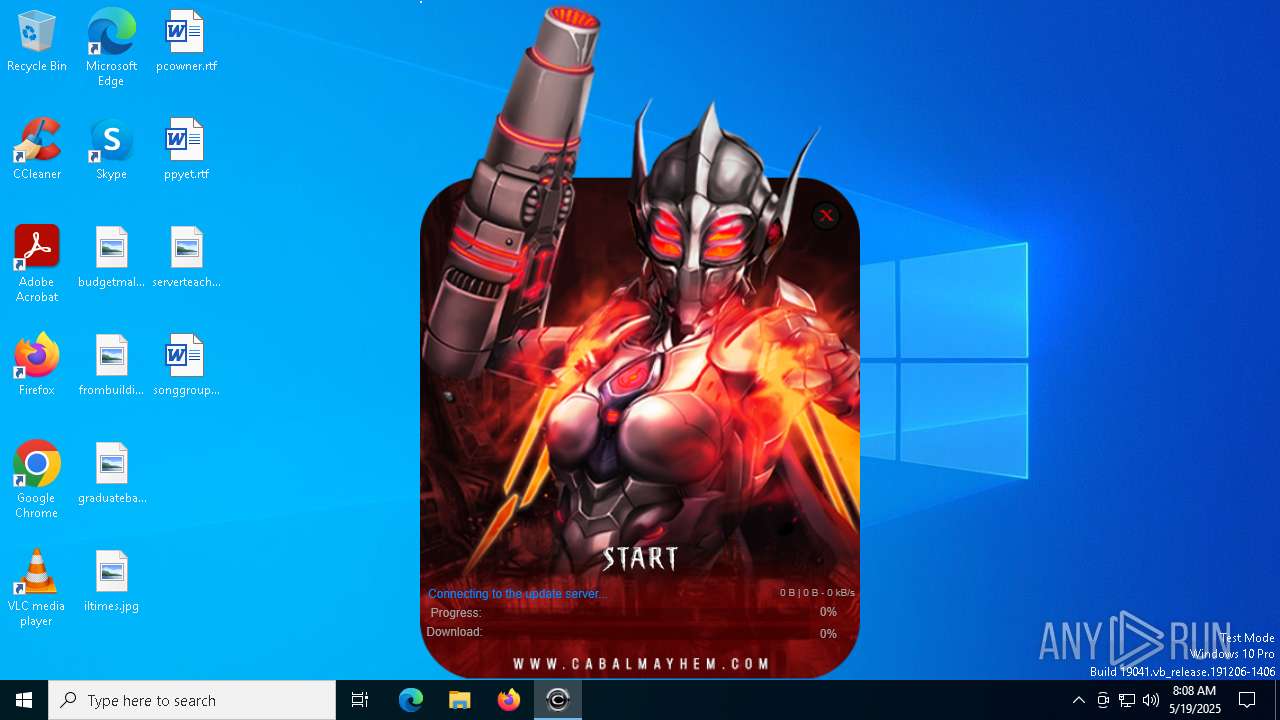
AMADEY has been detected (SURICATA)
- tgvazx.exe (PID: 7792)
NjRAT is detected
- fusca%20game.exe (PID: 7692)
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.bin.exe (PID: 7380)
Connects to the CnC server
- tgvazx.exe (PID: 7792)
NJRAT has been detected (YARA)
- fusca%20game.exe (PID: 7692)
Changes the autorun value in the registry
- fusca%20game.exe (PID: 7692)
AMADEY has been detected (YARA)
- tgvazx.exe (PID: 7792)
ARECHCLIENT2 has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 7380)
Executing a file with an untrusted certificate
- Blue-Cloner-Signed.exe (PID: 6388)
- Blue-Cloner-Signed.exe (PID: 4200)
SCREENCONNECT has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 7380)
QUASARRAT has been found (auto)
- 4363463463464363463463463.bin.exe (PID: 7380)
- testingfile.exe (PID: 6272)
Uses Task Scheduler to autorun other applications
- testingfile.exe (PID: 6272)
- Client.exe (PID: 7784)
- Client.exe (PID: 4920)
- Client.exe (PID: 728)
- Client.exe (PID: 1544)
- Client.exe (PID: 2780)
- Client.exe (PID: 8084)
- Client.exe (PID: 6228)
- Client.exe (PID: 7800)
- Client.exe (PID: 4488)
- Client.exe (PID: 6816)
- Client.exe (PID: 6028)
- Client.exe (PID: 1164)
- Client.exe (PID: 4448)
- Client.exe (PID: 8136)
- Client.exe (PID: 6068)
ARECHCLIENT2 has been detected (SURICATA)
- jsc.exe (PID: 3016)
SUSPICIOUS
Executable content was dropped or overwritten
- 4363463463464363463463463.bin.exe (PID: 7380)
- Amadey.2.exe (PID: 7736)
- update.exe (PID: 6108)
- Blue-Cloner-Signed.exe (PID: 4200)
- Blue-Cloner-Signed.tmp (PID: 6824)
- Blue-Cloner-Signed.exe (PID: 6388)
- Blue-Cloner-Signed.tmp (PID: 6988)
- rundll32.exe (PID: 6040)
- testingfile.exe (PID: 6272)
- AutoIt3.exe (PID: 7268)
Process requests binary or script from the Internet
- 4363463463464363463463463.bin.exe (PID: 7380)
- update.exe (PID: 6108)
Reads security settings of Internet Explorer
- 4363463463464363463463463.bin.exe (PID: 7380)
- Amadey.2.exe (PID: 7736)
- tgvazx.exe (PID: 7792)
- update.exe (PID: 6108)
- Blue-Cloner-Signed.tmp (PID: 6824)
- Invoice4231284.exe (PID: 744)
- Client.exe (PID: 7784)
Starts itself from another location
- Amadey.2.exe (PID: 7736)
- testingfile.exe (PID: 6272)
Potential Corporate Privacy Violation
- 4363463463464363463463463.bin.exe (PID: 7380)
- update.exe (PID: 6108)
- svchost.exe (PID: 2196)
Connects to the server without a host name
- 4363463463464363463463463.bin.exe (PID: 7380)
- tgvazx.exe (PID: 7792)
- update.exe (PID: 6108)
Contacting a server suspected of hosting an CnC
- tgvazx.exe (PID: 7792)
Uses NETSH.EXE to add a firewall rule or allowed programs
- fusca%20game.exe (PID: 7692)
There is functionality for taking screenshot (YARA)
- tgvazx.exe (PID: 7792)
Reads Microsoft Outlook installation path
- update.exe (PID: 6108)
Reads Internet Explorer settings
- update.exe (PID: 6108)
The process executes via Task Scheduler
- tgvazx.exe (PID: 6028)
- tgvazx.exe (PID: 2316)
- tgvazx.exe (PID: 2084)
- tgvazx.exe (PID: 7420)
- tgvazx.exe (PID: 1812)
There is functionality for enable RDP (YARA)
- tgvazx.exe (PID: 7792)
Reads the Windows owner or organization settings
- Blue-Cloner-Signed.tmp (PID: 6824)
- Blue-Cloner-Signed.tmp (PID: 6988)
Executes as Windows Service
- VSSVC.exe (PID: 5352)
- ScreenConnect.ClientService.exe (PID: 7404)
Executing commands from a ".bat" file
- Client.exe (PID: 7784)
- Client.exe (PID: 7156)
- Client.exe (PID: 4008)
- Client.exe (PID: 7764)
- Client.exe (PID: 6660)
- Client.exe (PID: 1544)
- Client.exe (PID: 4920)
- Client.exe (PID: 728)
- Client.exe (PID: 4620)
- Client.exe (PID: 6872)
- Client.exe (PID: 1804)
- Client.exe (PID: 2780)
- Client.exe (PID: 8084)
- Client.exe (PID: 7800)
- Client.exe (PID: 4488)
- Client.exe (PID: 6228)
- Client.exe (PID: 3956)
- Client.exe (PID: 6816)
- Client.exe (PID: 1164)
- Client.exe (PID: 7372)
- Client.exe (PID: 8136)
- Client.exe (PID: 4448)
- Client.exe (PID: 6028)
- Client.exe (PID: 6068)
Starts application with an unusual extension
- cmd.exe (PID: 1568)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 928)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 4152)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 5608)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 3744)
- cmd.exe (PID: 6112)
Starts CMD.EXE for commands execution
- Client.exe (PID: 7784)
- Client.exe (PID: 7156)
- Client.exe (PID: 4008)
- Client.exe (PID: 7764)
- Client.exe (PID: 6660)
- Client.exe (PID: 1544)
- Client.exe (PID: 4920)
- Client.exe (PID: 728)
- Client.exe (PID: 6872)
- Client.exe (PID: 4620)
- Client.exe (PID: 1804)
- Client.exe (PID: 2780)
- Client.exe (PID: 8084)
- Client.exe (PID: 7800)
- Client.exe (PID: 6228)
- Client.exe (PID: 3956)
- Client.exe (PID: 6816)
- Client.exe (PID: 4488)
- Client.exe (PID: 7372)
- Client.exe (PID: 1164)
- Client.exe (PID: 8136)
- Client.exe (PID: 4448)
- Client.exe (PID: 6028)
- Client.exe (PID: 6068)
The executable file from the user directory is run by the CMD process
- Client.exe (PID: 7156)
- Client.exe (PID: 4008)
- Client.exe (PID: 7764)
- Client.exe (PID: 6660)
- Client.exe (PID: 4920)
- Client.exe (PID: 728)
- Client.exe (PID: 1544)
- Client.exe (PID: 4620)
- Client.exe (PID: 6872)
- Client.exe (PID: 8084)
- Client.exe (PID: 1804)
- Client.exe (PID: 2780)
- Client.exe (PID: 7800)
- Client.exe (PID: 6228)
- Client.exe (PID: 4488)
- Client.exe (PID: 3956)
- Client.exe (PID: 6816)
- Client.exe (PID: 7372)
- Client.exe (PID: 6028)
- Client.exe (PID: 1164)
- Client.exe (PID: 8136)
- Client.exe (PID: 4448)
- Client.exe (PID: 6068)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 1568)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 928)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 4152)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 5608)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 3744)
- cmd.exe (PID: 6112)
Reads the date of Windows installation
- Client.exe (PID: 7784)
Process drops legitimate windows executable
- Blue-Cloner-Signed.tmp (PID: 6988)
- AutoIt3.exe (PID: 7268)
Drops 7-zip archiver for unpacking
- Blue-Cloner-Signed.tmp (PID: 6988)
- AutoIt3.exe (PID: 7268)
Starts the AutoIt3 executable file
- Blue-Cloner-Signed.tmp (PID: 6988)
Connects to unusual port
- jsc.exe (PID: 3016)
INFO
Disables trace logs
- 4363463463464363463463463.bin.exe (PID: 7380)
- update.exe (PID: 6108)
Checks supported languages
- 4363463463464363463463463.bin.exe (PID: 7380)
- fusca%20game.exe (PID: 7692)
- Amadey.2.exe (PID: 7736)
- tgvazx.exe (PID: 7792)
- fusca%20game.exe (PID: 7976)
- update.exe (PID: 6108)
- tgvazx.exe (PID: 6028)
- Blue-Cloner-Signed.tmp (PID: 6824)
- Blue-Cloner-Signed.exe (PID: 4200)
- Blue-Cloner-Signed.exe (PID: 6388)
- Blue-Cloner-Signed.tmp (PID: 6988)
- msiexec.exe (PID: 6540)
- testingfile.exe (PID: 6272)
- msiexec.exe (PID: 7460)
- Invoice4231284.exe (PID: 744)
- Client.exe (PID: 7784)
- Client.exe (PID: 7740)
- chcp.com (PID: 7996)
Reads the computer name
- 4363463463464363463463463.bin.exe (PID: 7380)
- Amadey.2.exe (PID: 7736)
- tgvazx.exe (PID: 7792)
- fusca%20game.exe (PID: 7976)
- fusca%20game.exe (PID: 7692)
- update.exe (PID: 6108)
- Blue-Cloner-Signed.tmp (PID: 6824)
- Blue-Cloner-Signed.tmp (PID: 6988)
- Invoice4231284.exe (PID: 744)
- msiexec.exe (PID: 6540)
- testingfile.exe (PID: 6272)
- msiexec.exe (PID: 7460)
- Client.exe (PID: 7784)
- Client.exe (PID: 7740)
Checks proxy server information
- 4363463463464363463463463.bin.exe (PID: 7380)
- tgvazx.exe (PID: 7792)
- update.exe (PID: 6108)
Reads the machine GUID from the registry
- 4363463463464363463463463.bin.exe (PID: 7380)
- fusca%20game.exe (PID: 7692)
- update.exe (PID: 6108)
- testingfile.exe (PID: 6272)
- Invoice4231284.exe (PID: 744)
- Client.exe (PID: 7784)
- Client.exe (PID: 7740)
Reads the software policy settings
- 4363463463464363463463463.bin.exe (PID: 7380)
- slui.exe (PID: 7420)
Process checks computer location settings
- 4363463463464363463463463.bin.exe (PID: 7380)
- Amadey.2.exe (PID: 7736)
- Blue-Cloner-Signed.tmp (PID: 6824)
- Invoice4231284.exe (PID: 744)
- Client.exe (PID: 7784)
Create files in a temporary directory
- Amadey.2.exe (PID: 7736)
- 4363463463464363463463463.bin.exe (PID: 7380)
- update.exe (PID: 6108)
- Blue-Cloner-Signed.exe (PID: 4200)
- Blue-Cloner-Signed.tmp (PID: 6824)
- Blue-Cloner-Signed.exe (PID: 6388)
- Blue-Cloner-Signed.tmp (PID: 6988)
- Invoice4231284.exe (PID: 744)
- rundll32.exe (PID: 6040)
- Client.exe (PID: 7784)
Auto-launch of the file from Registry key
- fusca%20game.exe (PID: 7692)
Manual execution by a user
- fusca%20game.exe (PID: 7976)
- Client.exe (PID: 7740)
Creates files or folders in the user directory
- update.exe (PID: 6108)
- testingfile.exe (PID: 6272)
Reads Environment values
- testingfile.exe (PID: 6272)
- Client.exe (PID: 7784)
- Client.exe (PID: 7740)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4688)
- msiexec.exe (PID: 6540)
CONNECTWISE has been detected
- msiexec.exe (PID: 4688)
Changes the display of characters in the console
- cmd.exe (PID: 1568)
- cmd.exe (PID: 6136)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 1804)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 4572)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 8104)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 928)
- cmd.exe (PID: 6480)
- cmd.exe (PID: 4152)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 4224)
- cmd.exe (PID: 3760)
- cmd.exe (PID: 5608)
- cmd.exe (PID: 3744)
- cmd.exe (PID: 6112)
Compiled with Borland Delphi (YARA)
- Blue-Cloner-Signed.exe (PID: 6388)
- Blue-Cloner-Signed.tmp (PID: 6988)
Uses Task Scheduler to autorun other applications (AUTOMATE)
- Client.exe (PID: 7156)
- Client.exe (PID: 4008)
- Client.exe (PID: 7764)
- Client.exe (PID: 6660)
- Client.exe (PID: 4620)
- Client.exe (PID: 6872)
- Client.exe (PID: 1804)
- Client.exe (PID: 3956)
- Client.exe (PID: 7372)
Manages system restore points
- SrTasks.exe (PID: 4056)
The sample compiled with english language support
- Blue-Cloner-Signed.tmp (PID: 6988)
- AutoIt3.exe (PID: 7268)
Detects InnoSetup installer (YARA)
- Blue-Cloner-Signed.tmp (PID: 6988)
- Blue-Cloner-Signed.exe (PID: 6388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(7692) fusca%20game.exe
C2127.0.0.1
Ports2022
BotnetClient
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\220fe34d4dcc4a99fe35d2fb7ce78939
Splitter|'|'|
Versionim523
Amadey
(PID) Process(7792) tgvazx.exe
C2176.65.143.173
URLhttp://176.65.143.173/M0XmDru/index.php
Version5.33
Options
Drop directorydbf9c9b26f
Drop nametgvazx.exe
Strings (125)lv:
msi
Kaspersky Lab
av:
|
#
"
\App
00000422
dm:
Powershell.exe
ProgramData\
ps1
rundll32
http://
Content-Disposition: form-data; name="data"; filename="
SOFTWARE\Microsoft\Windows NT\CurrentVersion
dll
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
id:
VideoID
cred.dll|clip.dll|
0000043f
cmd
00000423
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
-executionpolicy remotesigned -File "
2022
------
2016
og:
\0000
CurrentBuild
2019
:::
S-%lu-
" && timeout 1 && del
ProductName
Panda Security
ESET
/M0XmDru/index.php
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
/k
+++
176.65.143.173
?scr=1
Doctor Web
GET
SYSTEM\ControlSet001\Services\BasicDisplay\Video
/quiet
.jpg
dbf9c9b26f
vs:
sd:
rundll32.exe
"taskkill /f /im "
pc:
random
=
360TotalSecurity
tgvazx.exe
<d>
wb
Content-Type: multipart/form-data; boundary=----
Startup
Norton
&& Exit"
os:
https://
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
2025
Avira
%-lu
zip
POST
"
Content-Type: application/octet-stream
Rem
------
<c>
clip.dll
AVAST Software
\
shell32.dll
" && ren
e3
kernel32.dll
DefaultSettings.XResolution
d1
DefaultSettings.YResolution
r=
cred.dll
--
GetNativeSystemInfo
-%lu
ComputerName
&unit=
Keyboard Layout\Preload
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
ar:
Sophos
%USERPROFILE%
exe
e1
e2
st=s
Programs
0123456789
un:
rb
bi:
abcdefghijklmnopqrstuvwxyz0123456789-_
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
cmd /C RMDIR /s/q
Bitdefender
5.33
-unicode-
AVG
WinDefender
&&
shutdown -s -t 0
Comodo
00000419
Content-Type: application/x-www-form-urlencoded
/Plugins/
Main
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
344
Monitored processes
209
Malicious processes
28
Suspicious processes
28
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" | C:\Users\admin\AppData\Roaming\SubDir\Client.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: wo2 Exit code: 0 Version: 1.2.3.4 Modules
| |||||||||||||||
| 744 | "C:\Users\admin\AppData\Local\Temp\Files\Invoice4231284.exe" | C:\Users\admin\AppData\Local\Temp\Files\Invoice4231284.exe | — | 4363463463464363463463463.bin.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "schtasks" /create /tn "wod2" /sc ONLOGON /tr "C:\Users\admin\AppData\Roaming\SubDir\Client.exe" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 928 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\IFmTJBmQ92iZ.bat" " | C:\Windows\System32\cmd.exe | — | Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 181
Read events
41 206
Write events
957
Delete events
18
Modification events
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7380) 4363463463464363463463463.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
143
Suspicious files
25
Text files
32
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 744 | Invoice4231284.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\e89d9b3b19f1f9d9\ScreenConnect.ClientSetup.msi | — | |
MD5:— | SHA256:— | |||
| 7380 | 4363463463464363463463463.bin.exe | C:\Users\admin\AppData\Local\Temp\Files\update.exe | executable | |
MD5:61E593D86E0E279FA79C2FF106883F9E | SHA256:953E26D45C5104521EDFA54D8CF8F1531DAA5DC9DCBEE33B029CA84861FB8BE2 | |||
| 6108 | update.exe | C:\Users\admin\AppData\Local\Temp\Files\cabal.exe | executable | |
MD5:EE98BFEAAAAD43B8BE2B929EB8F1642F | SHA256:D93A9963C5A6C9FFAD9D1CCB2C869D77DEDF03014926D956B2EFAB3CF9C4AC9F | |||
| 7736 | Amadey.2.exe | C:\Windows\Tasks\tgvazx.job | binary | |
MD5:624DED263884F965778BC9D0DF7636C4 | SHA256:29EF2298645D32BF92E03FAFDC37BCA56525A13BF611283933F4EC40437BFBD4 | |||
| 7380 | 4363463463464363463463463.bin.exe | C:\Users\admin\AppData\Local\Temp\Files\fusca%20game.exe | executable | |
MD5:6932B7496923927A168F33E9C584DF04 | SHA256:6CBEEC3D5E443ABF3DD88847FA7BA3E4CC716CEB39F1BB514E32B9295DBC8529 | |||
| 6988 | Blue-Cloner-Signed.tmp | C:\Users\admin\AppData\Local\Temp\is-8O52I.tmp\_isetup\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 7380 | 4363463463464363463463463.bin.exe | C:\Users\admin\AppData\Local\Temp\Files\Amadey.2.exe | executable | |
MD5:E4D1C9E8C2B3B6CEC83DB5605D513C33 | SHA256:FCA0C4F784C098FC6D185BB4A47F5D22B81B6B2CB6E4054FE2911874FD64B8AE | |||
| 7736 | Amadey.2.exe | C:\Users\admin\AppData\Local\Temp\dbf9c9b26f\tgvazx.exe | executable | |
MD5:E4D1C9E8C2B3B6CEC83DB5605D513C33 | SHA256:FCA0C4F784C098FC6D185BB4A47F5D22B81B6B2CB6E4054FE2911874FD64B8AE | |||
| 6824 | Blue-Cloner-Signed.tmp | C:\Users\admin\AppData\Local\Temp\is-QHF45.tmp\_isetup\_isdecmp.dll | executable | |
MD5:077CB4461A2767383B317EB0C50F5F13 | SHA256:8287D0E287A66EE78537C8D1D98E426562B95C50F569B92CEA9CE36A9FA57E64 | |||
| 7380 | 4363463463464363463463463.bin.exe | C:\Users\admin\AppData\Local\Temp\Files\Blue-Cloner-Signed.exe | executable | |
MD5:45C6EA5DE0D4568F38C425B8B084FF38 | SHA256:992CFE9E799108C442281C19748EE8BCB77A3FE8DFB808AE0CBF81D9F590731C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
47
DNS requests
54
Threats
83
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7380 | 4363463463464363463463463.bin.exe | GET | 301 | 140.82.121.3:80 | http://github.com/sohpierainxz/Fnaf-1/raw/refs/heads/main/fusca%20game.exe | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7380 | 4363463463464363463463463.bin.exe | GET | 200 | 217.15.164.94:80 | http://217.15.164.94/update/client/update.exe | unknown | — | — | malicious |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7792 | tgvazx.exe | POST | 200 | 176.65.143.173:80 | http://176.65.143.173/M0XmDru/index.php | unknown | — | — | malicious |
8136 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7380 | 4363463463464363463463463.bin.exe | 151.101.194.49:443 | urlhaus.abuse.ch | FASTLY | US | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7380 | 4363463463464363463463463.bin.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
7380 | 4363463463464363463463463.bin.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
7380 | 4363463463464363463463463.bin.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
7380 | 4363463463464363463463463.bin.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
7792 | tgvazx.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 31 |
7792 | tgvazx.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
7792 | tgvazx.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
6108 | update.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6108 | update.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |