| File name: | 4363463463464363463463463.exe |
| Full analysis: | https://app.any.run/tasks/44fb1274-4e92-4c93-9cf2-4efe84f0c5a8 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | August 22, 2024, 21:27:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 2A94F3960C58C6E70826495F76D00B85 |
| SHA1: | E2A1A5641295F5EBF01A37AC1C170AC0814BB71A |
| SHA256: | 2FCAD226B17131DA4274E1B9F8F31359BDD325C9568665F08FD1F6C5D06A23CE |
| SSDEEP: | 192:2we8sGKE6MqyG7c20L7BIW12n/ePSmzkTInu8stYcFwVc03KY:9e8sGKfMqyGg20PKn/cRaInuptYcFwVY |
MALICIOUS
HAUSBOMBER has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6732)
DCRAT has been detected (YARA)
- 4363463463464363463463463.exe (PID: 6732)
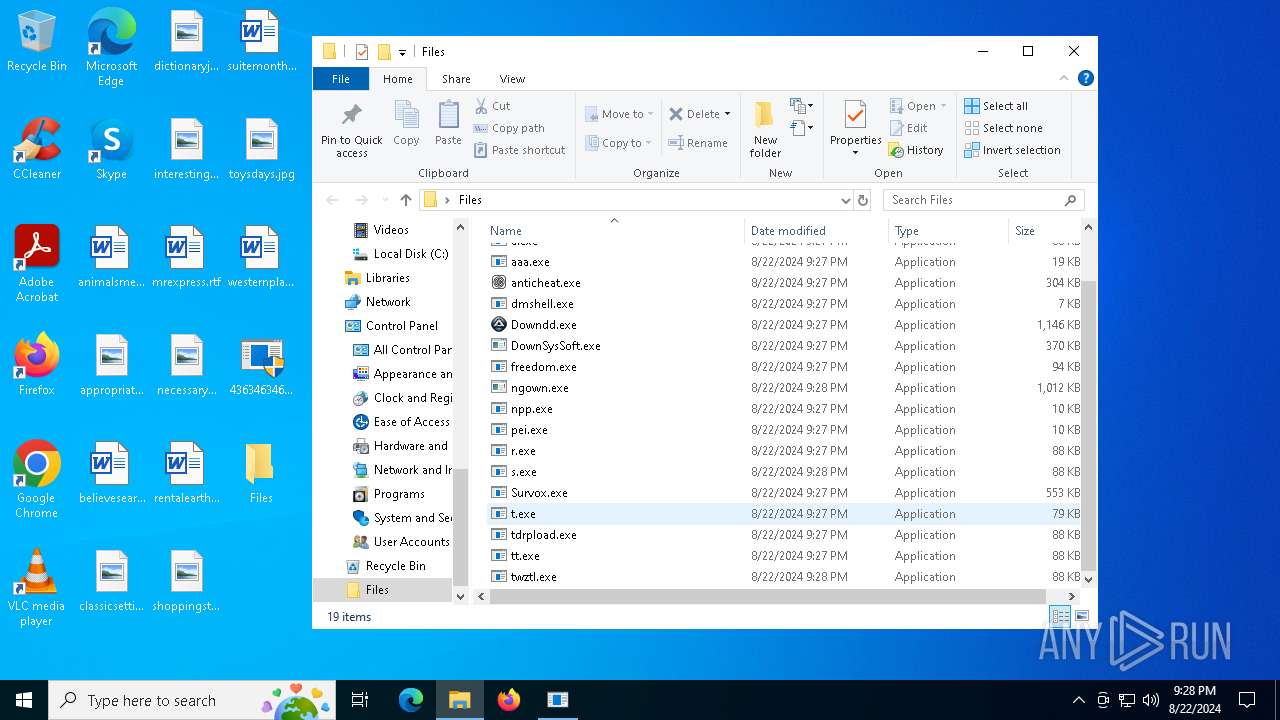
Changes the autorun value in the registry
- r.exe (PID: 6468)
- Survox.exe (PID: 1076)
- tt.exe (PID: 6692)
- 1804925973.exe (PID: 6488)
- t.exe (PID: 6264)
- 2978130666.exe (PID: 6600)
Attempt to connect to SMB server
- System (PID: 4)
Changes Security Center notification settings
- sysmablsvr.exe (PID: 5880)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
Changes the Windows auto-update feature
- sysmablsvr.exe (PID: 5880)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
Creates or modifies Windows services
- sysmablsvr.exe (PID: 5880)
- sysmysldrv.exe (PID: 6440)
- sysarddrvs.exe (PID: 6416)
Changes appearance of the Explorer extensions
- sysmablsvr.exe (PID: 5880)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 1048)
- sysmysldrv.exe (PID: 6440)
- cmd.exe (PID: 7556)
- sysarddrvs.exe (PID: 6416)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 6880)
- MSBuild.exe (PID: 7956)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 6880)
- MSBuild.exe (PID: 7956)
Scans artifacts that could help determine the target
- RegSvcs.exe (PID: 6880)
PHORPIEX has been detected (SURICATA)
- sysmablsvr.exe (PID: 5880)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
- 4363463463464363463463463.exe (PID: 6732)
- svchost.exe (PID: 2256)
Connects to the CnC server
- sysmablsvr.exe (PID: 5880)
- sysmysldrv.exe (PID: 6440)
- sysarddrvs.exe (PID: 6416)
REDLINE has been detected (YARA)
- anticheat.exe (PID: 6932)
Application was injected by another process
- explorer.exe (PID: 4552)
Runs injected code in another process
- 1.exe (PID: 6708)
XWORM has been detected (YARA)
- freedom.exe (PID: 6564)
NANOCORE has been detected (YARA)
- Survox.exe (PID: 1076)
SMOKE has been detected (SURICATA)
- explorer.exe (PID: 4552)
AGENTTESLA has been detected (YARA)
- RegSvcs.exe (PID: 6880)
PHORPIEX has been detected (YARA)
- sysmablsvr.exe (PID: 5880)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
SUSPICIOUS
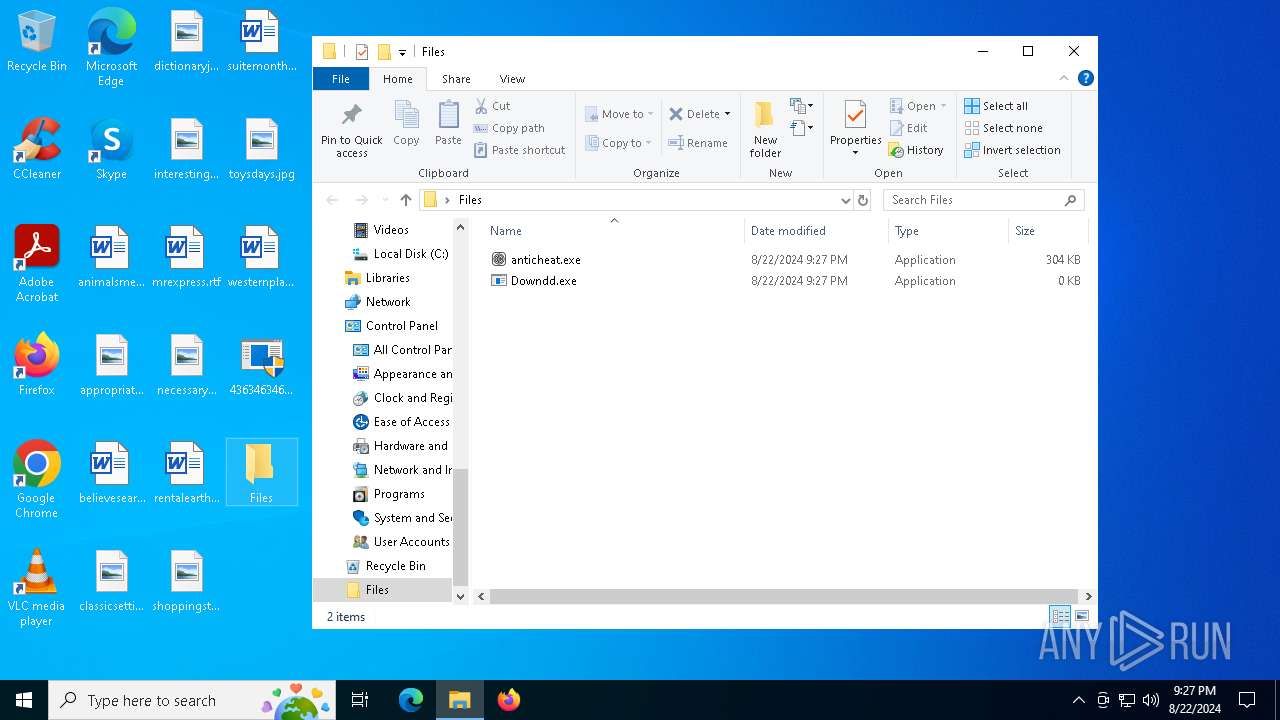
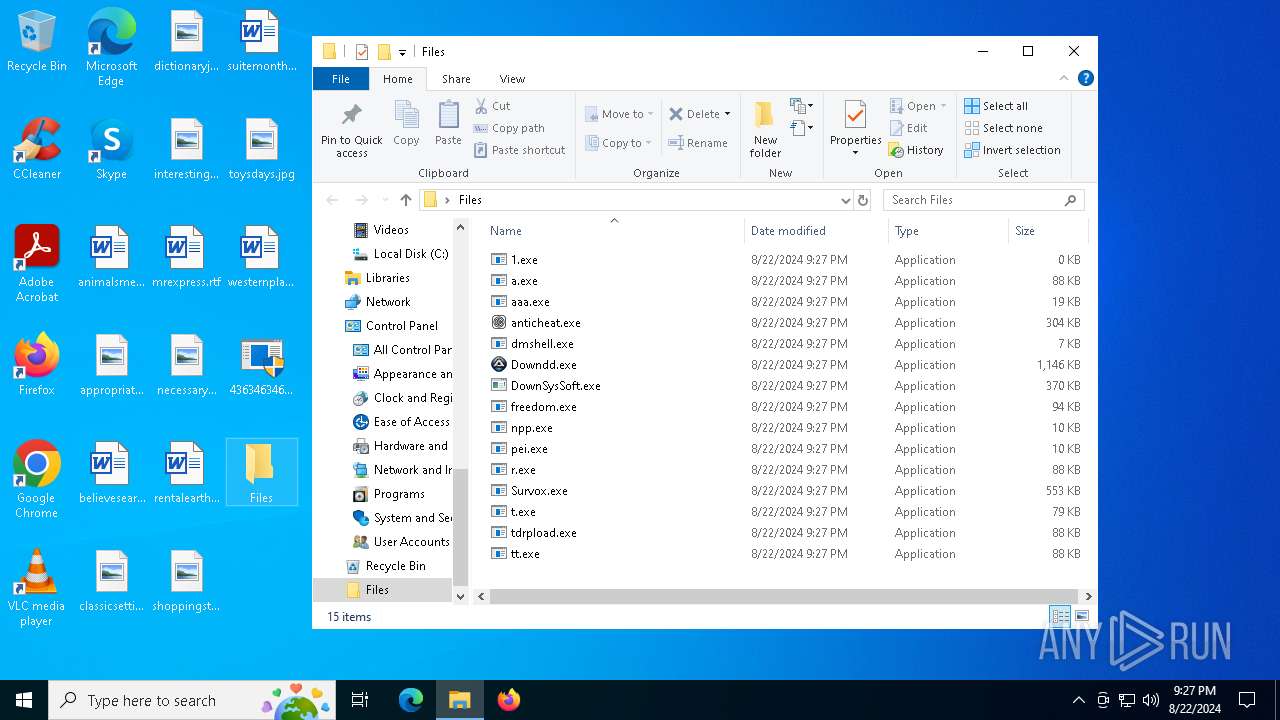
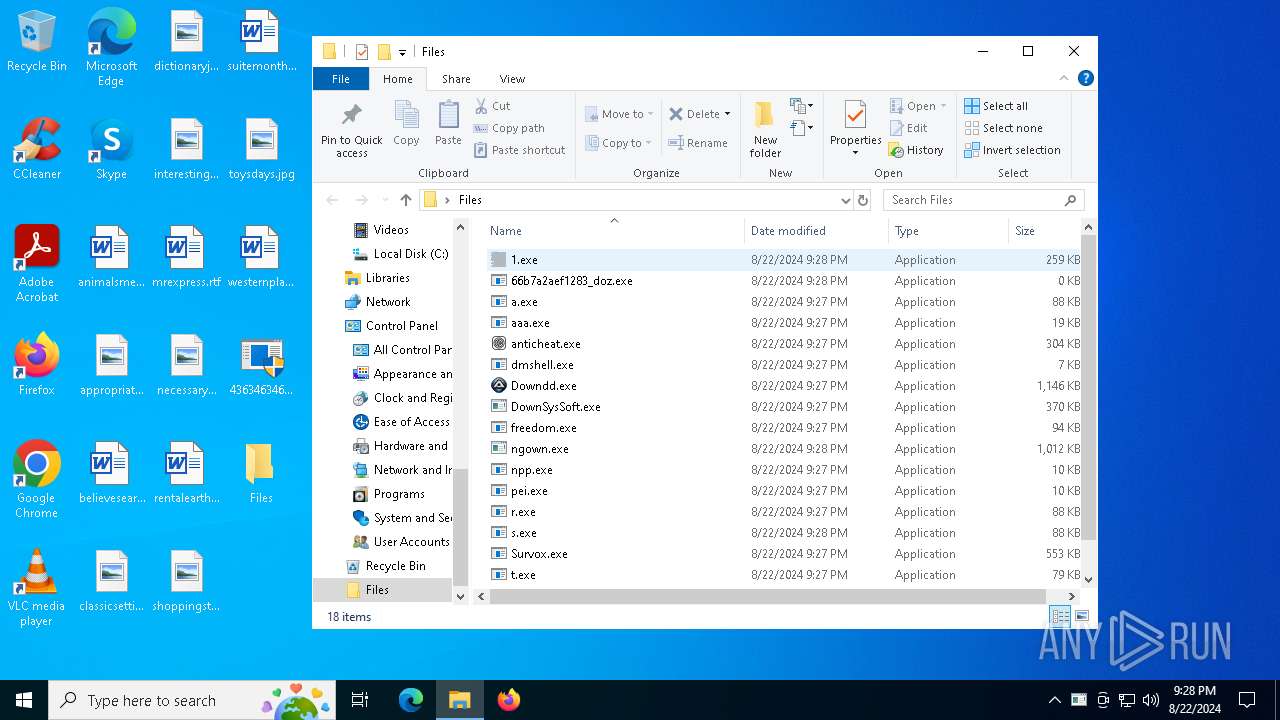
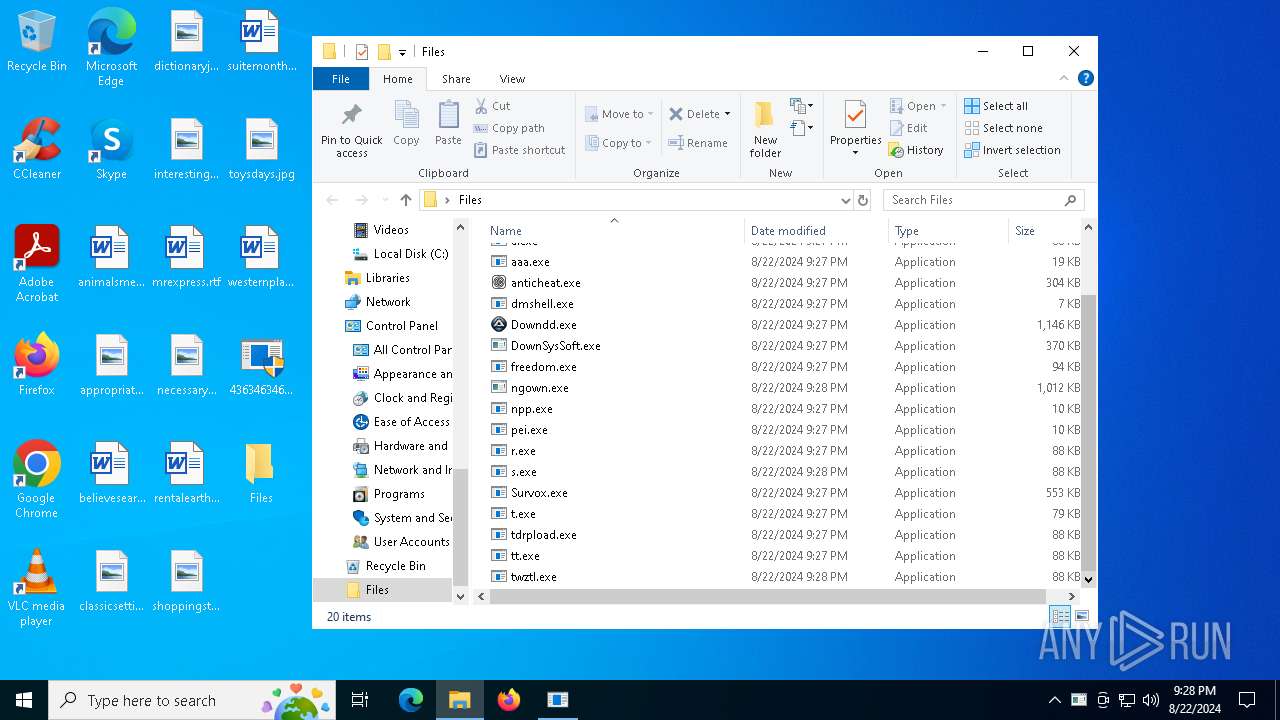
Drops the executable file immediately after the start
- 4363463463464363463463463.exe (PID: 6732)
- pei.exe (PID: 6476)
- r.exe (PID: 6468)
- npp.exe (PID: 6720)
- Survox.exe (PID: 1076)
- tt.exe (PID: 6692)
- 1804925973.exe (PID: 6488)
- 2978130666.exe (PID: 6600)
- t.exe (PID: 6264)
- Destover.exe (PID: 7944)
- MSBuild.exe (PID: 7956)
Reads security settings of Internet Explorer
- 4363463463464363463463463.exe (PID: 6732)
- pei.exe (PID: 6476)
- npp.exe (PID: 6720)
- DownSysSoft.exe (PID: 6352)
- sysmablsvr.exe (PID: 5880)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
- MSBuild.exe (PID: 7956)
Adds/modifies Windows certificates
- anticheat.exe (PID: 6932)
Connects to unusual port
- 4363463463464363463463463.exe (PID: 6732)
- anticheat.exe (PID: 6932)
- Survox.exe (PID: 1076)
- DownSysSoft.exe (PID: 6352)
- aaa.exe (PID: 6764)
- sysmablsvr.exe (PID: 5880)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
The process creates files with name similar to system file names
- 4363463463464363463463463.exe (PID: 6732)
- Survox.exe (PID: 1076)
Starts CMD.EXE for commands execution
- dmshell.exe (PID: 6432)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
- MSBuild.exe (PID: 7956)
Executable content was dropped or overwritten
- pei.exe (PID: 6476)
- r.exe (PID: 6468)
- npp.exe (PID: 6720)
- 4363463463464363463463463.exe (PID: 6732)
- Survox.exe (PID: 1076)
- tt.exe (PID: 6692)
- t.exe (PID: 6264)
- 2978130666.exe (PID: 6600)
- Destover.exe (PID: 7944)
- MSBuild.exe (PID: 7956)
- explorer.exe (PID: 4552)
- 1804925973.exe (PID: 6488)
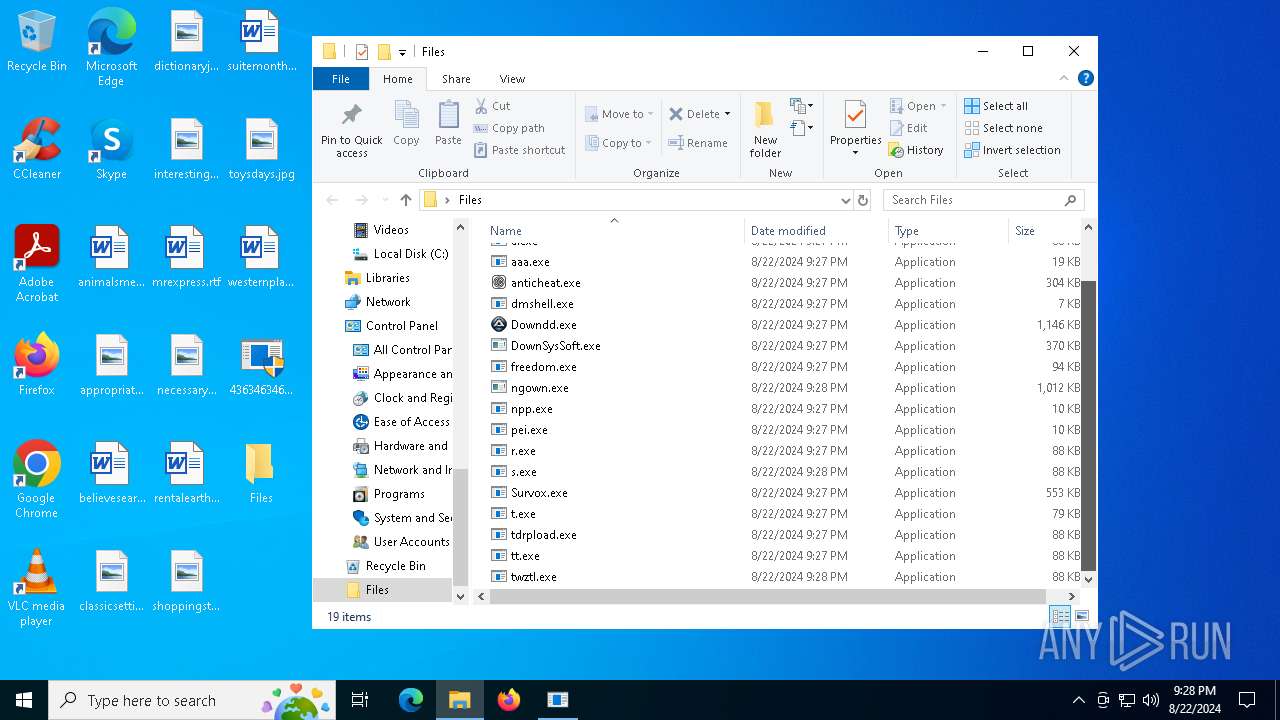
Starts itself from another location
- r.exe (PID: 6468)
- tt.exe (PID: 6692)
- 1804925973.exe (PID: 6488)
- 2978130666.exe (PID: 6600)
- t.exe (PID: 6264)
Reads the date of Windows installation
- 4363463463464363463463463.exe (PID: 6732)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
- MSBuild.exe (PID: 7956)
Potential Corporate Privacy Violation
- 4363463463464363463463463.exe (PID: 6732)
- System (PID: 4)
- pei.exe (PID: 6476)
- DownSysSoft.exe (PID: 6352)
Creates or modifies Windows services
- sysmablsvr.exe (PID: 5880)
- sysmysldrv.exe (PID: 6440)
- sysarddrvs.exe (PID: 6416)
Executes application which crashes
- ngown.exe (PID: 4816)
- freedom.exe (PID: 6564)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 1048)
- cmd.exe (PID: 7556)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1048)
- cmd.exe (PID: 7556)
Process drops legitimate windows executable
- 4363463463464363463463463.exe (PID: 6732)
- Destover.exe (PID: 7944)
- MSBuild.exe (PID: 7956)
Starts a Microsoft application from unusual location
- Destover.exe (PID: 7944)
Checks Windows Trust Settings
- MSBuild.exe (PID: 7956)
Process requests binary or script from the Internet
- 4363463463464363463463463.exe (PID: 6732)
Connects to the server without a host name
- 4363463463464363463463463.exe (PID: 6732)
- sysmablsvr.exe (PID: 5880)
Searches for installed software
- MSBuild.exe (PID: 7956)
The process drops Mozilla's DLL files
- MSBuild.exe (PID: 7956)
The process drops C-runtime libraries
- MSBuild.exe (PID: 7956)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7596)
Connects to SMTP port
- RegSvcs.exe (PID: 6880)
Found regular expressions for crypto-addresses (YARA)
- freedom.exe (PID: 6564)
Checks for external IP
- svchost.exe (PID: 2256)
- freedom.exe (PID: 6564)
The process executes via Task Scheduler
- bjcgshj (PID: 7580)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 4552)
Reads Environment values
- 4363463463464363463463463.exe (PID: 6732)
- Survox.exe (PID: 1076)
- RegSvcs.exe (PID: 6880)
- MSBuild.exe (PID: 7956)
- freedom.exe (PID: 6564)
Reads the computer name
- anticheat.exe (PID: 6932)
- 4363463463464363463463463.exe (PID: 6732)
- freedom.exe (PID: 6564)
- pei.exe (PID: 6476)
- npp.exe (PID: 6720)
- aaa.exe (PID: 6764)
- Survox.exe (PID: 1076)
- DownSysSoft.exe (PID: 6352)
- RegSvcs.exe (PID: 6880)
- sysmablsvr.exe (PID: 5880)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
- 66b7a2aef1283_doz.exe (PID: 7856)
- MSBuild.exe (PID: 7956)
Reads the software policy settings
- 4363463463464363463463463.exe (PID: 6732)
- WerFault.exe (PID: 3384)
- MSBuild.exe (PID: 7956)
- RegSvcs.exe (PID: 6880)
- WerFault.exe (PID: 3540)
Process checks computer location settings
- 4363463463464363463463463.exe (PID: 6732)
- sysarddrvs.exe (PID: 6416)
- sysmysldrv.exe (PID: 6440)
- MSBuild.exe (PID: 7956)
Reads the machine GUID from the registry
- anticheat.exe (PID: 6932)
- freedom.exe (PID: 6564)
- Survox.exe (PID: 1076)
- 4363463463464363463463463.exe (PID: 6732)
- RegSvcs.exe (PID: 6880)
- 66b7a2aef1283_doz.exe (PID: 7856)
- MSBuild.exe (PID: 7956)
- sysmablsvr.exe (PID: 5880)
- sysmysldrv.exe (PID: 6440)
- sysarddrvs.exe (PID: 6416)
Checks supported languages
- anticheat.exe (PID: 6932)
- 4363463463464363463463463.exe (PID: 6732)
- Downdd.exe (PID: 6376)
- pei.exe (PID: 6476)
- freedom.exe (PID: 6564)
- r.exe (PID: 6468)
- aaa.exe (PID: 6764)
- npp.exe (PID: 6720)
- tdrpload.exe (PID: 6252)
- tt.exe (PID: 6692)
- a.exe (PID: 460)
- Survox.exe (PID: 1076)
- sysmablsvr.exe (PID: 6000)
- sysmablsvr.exe (PID: 5880)
- 1804925973.exe (PID: 6488)
- DownSysSoft.exe (PID: 6352)
- t.exe (PID: 6264)
- 2978130666.exe (PID: 6600)
- 1.exe (PID: 6708)
- sysarddrvs.exe (PID: 6416)
- ngown.exe (PID: 4816)
- s.exe (PID: 3292)
- RegSvcs.exe (PID: 6880)
- sysmysldrv.exe (PID: 6440)
- 66b7a2aef1283_doz.exe (PID: 7856)
- Destover.exe (PID: 7944)
- MSBuild.exe (PID: 7956)
- twztl.exe (PID: 8080)
- bjcgshj (PID: 7580)
- sysmysldrv.exe (PID: 6676)
Creates files or folders in the user directory
- explorer.exe (PID: 4552)
- anticheat.exe (PID: 6932)
- pei.exe (PID: 6476)
- Survox.exe (PID: 1076)
- DownSysSoft.exe (PID: 6352)
- WerFault.exe (PID: 3384)
- MSBuild.exe (PID: 7956)
- WerFault.exe (PID: 3540)
Reads mouse settings
- Downdd.exe (PID: 6376)
- DownSysSoft.exe (PID: 6352)
- ngown.exe (PID: 4816)
Checks proxy server information
- pei.exe (PID: 6476)
- npp.exe (PID: 6720)
- 4363463463464363463463463.exe (PID: 6732)
- DownSysSoft.exe (PID: 6352)
- sysmablsvr.exe (PID: 5880)
- WerFault.exe (PID: 3384)
- MSBuild.exe (PID: 7956)
- sysmysldrv.exe (PID: 6440)
- explorer.exe (PID: 4552)
- freedom.exe (PID: 6564)
- WerFault.exe (PID: 3540)
- sysarddrvs.exe (PID: 6416)
Create files in a temporary directory
- pei.exe (PID: 6476)
- npp.exe (PID: 6720)
- DownSysSoft.exe (PID: 6352)
- ngown.exe (PID: 4816)
Process checks whether UAC notifications are on
- Survox.exe (PID: 1076)
Creates files in the program directory
- Survox.exe (PID: 1076)
- MSBuild.exe (PID: 7956)
Disables trace logs
- 4363463463464363463463463.exe (PID: 6732)
- freedom.exe (PID: 6564)
Reads Microsoft Office registry keys
- RegSvcs.exe (PID: 6880)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7248)
- powershell.exe (PID: 7640)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7640)
- powershell.exe (PID: 7248)
Reads product name
- MSBuild.exe (PID: 7956)
Reads CPU info
- MSBuild.exe (PID: 7956)
Attempt to transmit an email message via SMTP
- RegSvcs.exe (PID: 6880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(6932) anticheat.exe
C2 (1)38.180.203.208:14238
Options
ErrorMessage
Version1
XWorm
(PID) Process(6564) freedom.exe
C2exonic-hacks.com:1920
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep timeNewAged
USB drop nameUSB.exe
MutexQGOn8xsapkNWVjl5
Nanocore
(PID) Process(1076) Survox.exe
KeyboardLoggingTrue
BuildTime2024-08-16 18:00:35.335880
Version1.2.2.0
Mutexd9a2690c-d972-4399-8b23-c0fc8e2ac7c3
DefaultGroupDefault
PrimaryConnectionHostvowquybcw.org
BackupConnectionHost127.0.0.1
ConnectionPort34587
RunOnStartupTrue
RequestElevationFalse
BypassUserAccountControlFalse
ClearZoneIdentifierTrue
ClearAccessControlTrue
SetCriticalProcessFalse
PreventSystemSleepTrue
ActivateAwayModeTrue
EnableDebugModeFalse
RunDelay0
ConnectDelay3985
RestartDelay5000
TimeoutInterval5000
KeepAliveTimeout30000
MutexTimeout5000
LanTimeout2500
WanTimeout8000
BufferSize65535
MaxPacketSize10485760
GCThreshold10485760
UseCustomDnsServerTrue
PrimaryDnsServer8.8.8.8
BackupDnsServer8.8.4.4
AgentTesla
(PID) Process(6880) RegSvcs.exe
Protocolsmtp
Hostmail.worlorderbillions.top
Port587
Usernameniggabown22jan2024@worlorderbillions.top
Password3^?r?mtxk(kt
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:22 08:29:10+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 5632 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3552 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | 4363463463464363463463463.exe |
| LegalCopyright: | |
| OriginalFileName: | 4363463463464363463463463.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
200
Monitored processes
64
Malicious processes
21
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4 | System | [System Process] | |||||||||||||
User: SYSTEM Integrity Level: SYSTEM | |||||||||||||||
| 460 | "C:\Users\admin\Desktop\Files\a.exe" | C:\Users\admin\Desktop\Files\a.exe | — | 4363463463464363463463463.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1048 | "C:\Windows\System32\cmd.exe" /c powershell -Command "Add-MpPreference -ExclusionPath $env:windir; Add-MpPreference -ExclusionPath $env:TEMP; Add-MpPreference -ExclusionPath $env:USERPROFILE" | C:\Windows\SysWOW64\cmd.exe | — | sysarddrvs.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1076 | "C:\Users\admin\Desktop\Files\Survox.exe" | C:\Users\admin\Desktop\Files\Survox.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
Nanocore(PID) Process(1076) Survox.exe KeyboardLoggingTrue BuildTime2024-08-16 18:00:35.335880 Version1.2.2.0 Mutexd9a2690c-d972-4399-8b23-c0fc8e2ac7c3 DefaultGroupDefault PrimaryConnectionHostvowquybcw.org BackupConnectionHost127.0.0.1 ConnectionPort34587 RunOnStartupTrue RequestElevationFalse BypassUserAccountControlFalse ClearZoneIdentifierTrue ClearAccessControlTrue SetCriticalProcessFalse PreventSystemSleepTrue ActivateAwayModeTrue EnableDebugModeFalse RunDelay0 ConnectDelay3985 RestartDelay5000 TimeoutInterval5000 KeepAliveTimeout30000 MutexTimeout5000 LanTimeout2500 WanTimeout8000 BufferSize65535 MaxPacketSize10485760 GCThreshold10485760 UseCustomDnsServerTrue PrimaryDnsServer8.8.8.8 BackupDnsServer8.8.4.4 | |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3292 | "C:\Users\admin\Desktop\Files\s.exe" | C:\Users\admin\Desktop\Files\s.exe | — | 4363463463464363463463463.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3384 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4816 -s 768 | C:\Windows\SysWOW64\WerFault.exe | ngown.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3540 | C:\WINDOWS\system32\WerFault.exe -u -p 6564 -s 1788 | C:\Windows\System32\WerFault.exe | freedom.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4552 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4816 | "C:\Users\admin\Desktop\Files\ngown.exe" | C:\Users\admin\Desktop\Files\ngown.exe | 4363463463464363463463463.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
Total events
76 516
Read events
76 242
Write events
263
Delete events
11
Modification events
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010016000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C0000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C0000000D0000000000000053006B007900700065002E006C006E006B003E0020007C000000170000000000000061006E0069006D0061006C0073006D0065007300730061006700650073002E007200740066003E00200020000000160000000000000061007000700072006F007000720069006100740065006200650064002E006A00700067003E002000200000001700000000000000620065006C006900650076006500730065006100720063006800650073002E007200740066003E00200020000000170000000000000063006C0061007300730069006300730065007400740069006E00670073002E006A00700067003E002000200000001600000000000000640069006300740069006F006E006100720079006A0075006E0065002E0070006E0067003E002000200000001B0000000000000069006E0074006500720065007300740069006E006700700072006F006700720061006D0073002E0070006E0067003E0020002000000011000000000000006D00720065007800700072006500730073002E007200740066003E0020002000000016000000000000006E00650063006500730073006100720079006D0069006C00650073002E0070006E0067003E002000200000001300000000000000720065006E00740061006C00650061007200740068002E007200740066003E002000200000001800000000000000730068006F007000700069006E0067007300740061007200740069006E0067002E0070006E0067003E002000200000001400000000000000730075006900740065006D006F006E00740068006C0079002E007200740066003E00200020000000100000000000000074006F007900730064006100790073002E006A00700067003E0020002000000015000000000000007700650073007400650072006E0070006C0061007900650072002E007200740066003E00200020000000210000000000000034003300360033003400360033003400360033003400360034003300360033003400360033003400360033003400360033002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001600000000000000000000000000000000000000803F0000004008000000803F0000404009000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F0000000040000080401000000000400000A040110000004040000000001200000040400000803F130000004040000000401400000000000000803F0100000000000000004002000000000000004040030000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000004040000040401500 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 4EADC76600000000 | |||
| (PID) Process: | (4552) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Security and Maintenance\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F0062000000000000000000000001000000FFFFFFFFFFFF0000 | |||
| (PID) Process: | (6732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6732) 4363463463464363463463463.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\4363463463464363463463463_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
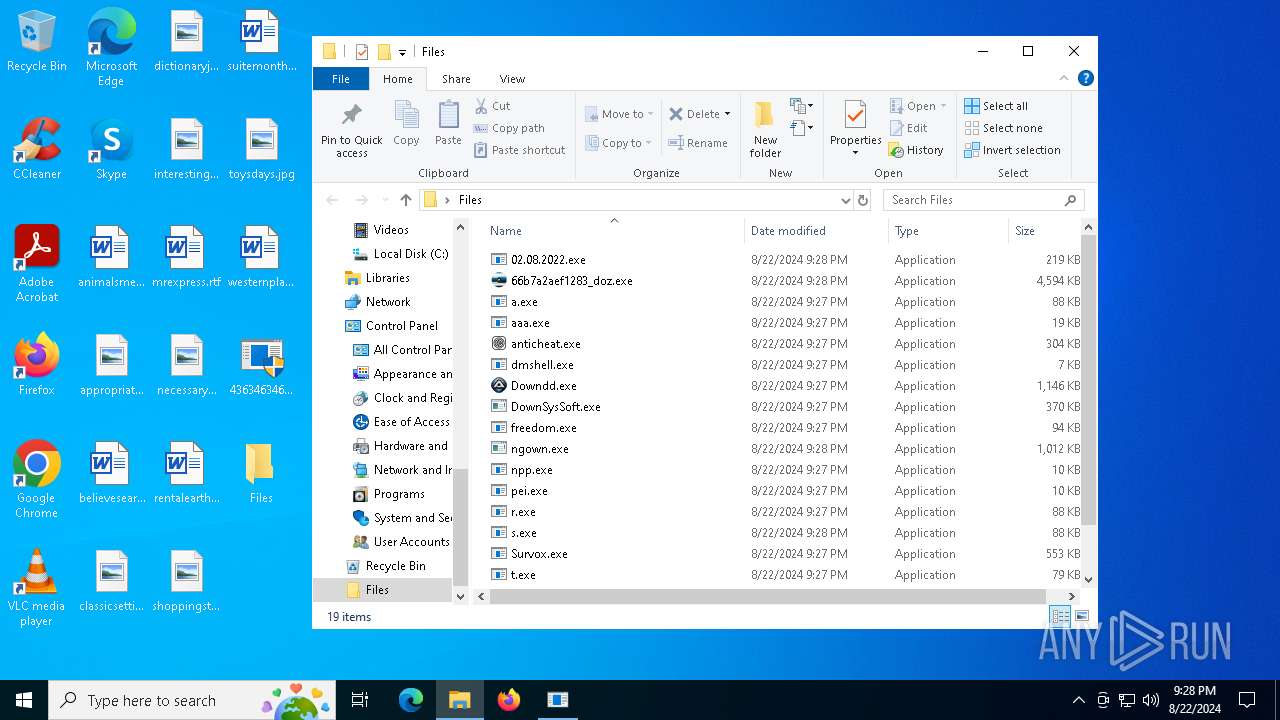
Executable files
37
Suspicious files
26
Text files
18
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4552 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 4552 | explorer.exe | C:\Users\admin\Desktop\Files\Downdd.exe | executable | |
MD5:C2B59AF47AF63068FBA9F72206AA477D | SHA256:68B64E2C7EE3665B60678B698B59EF3953A974D77622E50FC1F806E62D568C5D | |||
| 6932 | anticheat.exe | C:\Users\Public\Desktop\Google Chrome.lnk | lnk | |
MD5:BE0F6E574127D7FFA7539F0C862BF8C1 | SHA256:9BB43669741962052FBD438637B8C2827A91CC7D8044CE3869090860E3ADDD6F | |||
| 6932 | anticheat.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\76b53b3ec448f7ccdda2063b15d2bfc3_bb926e54-e3ca-40fd-ae90-2764341e7792 | dbf | |
MD5:BBC8DA7D36DF3F91C460984C2ABE8419 | SHA256:0399CCF5E780949A63400736A46CCE7D1879903D0F45C6B7D194C960BA4DDDC2 | |||
| 6932 | anticheat.exe | C:\Users\admin\AppData\Local\Temp\TmpEAAB.tmp | der | |
MD5:1420D30F964EAC2C85B2CCFE968EEBCE | SHA256:F3327793E3FD1F3F9A93F58D033ED89CE832443E2695BECA9F2B04ADBA049ED9 | |||
| 6732 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\anticheat.exe | executable | |
MD5:B3342D61145EF64D216FD5CBC36C7E20 | SHA256:C6E60D86605F4CA71680245ADED21B05F6306E5C52ACE4A5EFEC28E14F36DB5F | |||
| 6932 | anticheat.exe | C:\Users\Public\Desktop\Microsoft Edge.lnk | lnk | |
MD5:B5B1C756B73978D2DDE2F895F1007F2A | SHA256:7AAD92562A4E9A2D368490442CE75A2793AC0033D0B39C8EF466724863A3B27F | |||
| 6732 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\tdrpload.exe | executable | |
MD5:ABABCA6D12D96E8DD2F1D7114B406FAE | SHA256:A992920E64A64763F3DD8C2A431A0F5E56E5B3782A1496DE92BC80EE71CCA5BA | |||
| 6732 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\npp.exe | executable | |
MD5:8D8E6C7952A9DC7C0C73911C4DBC5518 | SHA256:FEB4C3AE4566F0ACBB9E0F55417B61FEFD89DC50A4E684DF780813FB01D61278 | |||
| 6732 | 4363463463464363463463463.exe | C:\Users\admin\Desktop\Files\freedom.exe | executable | |
MD5:DB5717FD494495EEA3C8F7D4AB29D6B0 | SHA256:6B59309AB12F1859A94FB2CE1C98639B2A538E6E098FFAC127E45C29733BD993 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
377
DNS requests
45
Threats
144
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/inc/anticheat.exe | unknown | — | — | unknown |
6732 | 4363463463464363463463463.exe | GET | 200 | 172.105.66.118:80 | http://172.105.66.118/payloads/dmshell.exe | unknown | — | — | unknown |
5940 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.84:80 | http://72ec8d09-fce8-4272-9829-f4a17ae33269.random.tsrv1.ws/r.exe | unknown | — | — | malicious |
6732 | 4363463463464363463463463.exe | GET | 200 | 58.23.215.156:8765 | http://58.23.215.156:8765/Downdd.exe | unknown | — | — | unknown |
6732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://privacy.aefiabeuodbauobfafoebbf.net/npp.exe | unknown | — | — | malicious |
6732 | 4363463463464363463463463.exe | GET | 200 | 185.216.214.225:80 | http://185.216.214.225/freedom.exe | unknown | — | — | malicious |
6732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.84:80 | http://1855e8b9-5b39-418e-b53e-3259c2f0c3fc.random.tsrv1.ws/a.exe | unknown | — | — | malicious |
6732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.84:80 | http://yzcplsibdtq.tsrv1.ws/pei.exe | unknown | — | — | malicious |
6732 | 4363463463464363463463463.exe | GET | 200 | 185.215.113.66:80 | http://skyjsihnqew.fihsifuiiusuiuduf.com/tdrpload.exe | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4436 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3412 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6732 | 4363463463464363463463463.exe | 151.101.2.49:443 | urlhaus.abuse.ch | FASTLY | US | unknown |
6732 | 4363463463464363463463463.exe | 185.215.113.16:80 | — | 1337team Limited | SC | malicious |
6732 | 4363463463464363463463463.exe | 58.23.215.156:8765 | — | CHINA UNICOM China169 Backbone | CN | malicious |
6932 | anticheat.exe | 38.180.203.208:14238 | — | COGENT-174 | US | malicious |
3412 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
urlhaus.abuse.ch |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
yzcplsibdtq.tsrv1.ws |
| malicious |
72ec8d09-fce8-4272-9829-f4a17ae33269.random.tsrv1.ws |
| malicious |
skyjsihnqew.fihsifuiiusuiuduf.com |
| unknown |
blog.tsrv1.ws |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6732 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6732 | 4363463463464363463463463.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6732 | 4363463463464363463463463.exe | Potentially Bad Traffic | ET MALWARE Terse alphanumeric executable downloader high likelihood of being hostile |
20 ETPRO signatures available at the full report
Process | Message |
|---|---|
freedom.exe | CLR: Managed code called FailFast without specifying a reason.
|